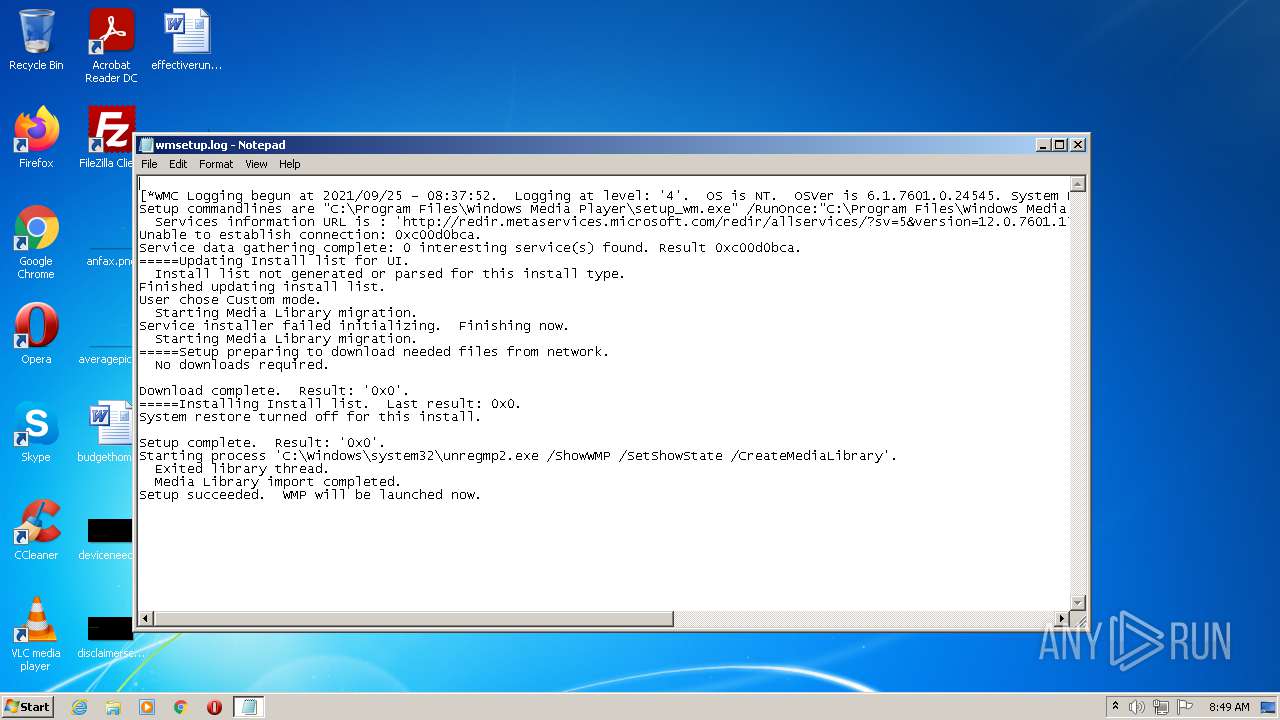
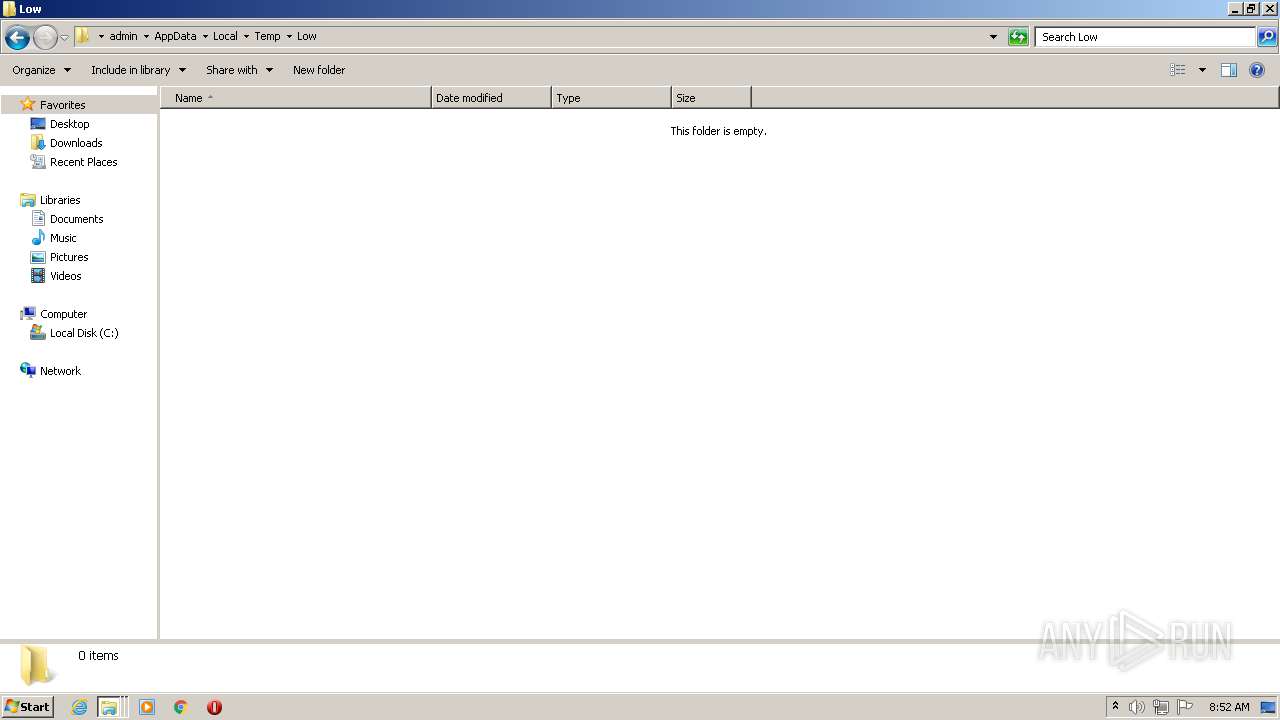
| File name: | C:\Users\admin\AppData\Local\Temp\wmsetup.log |
| Full analysis: | https://app.any.run/tasks/c41cd9c4-4450-46a4-956f-aad1aa6c39da |
| Verdict: | Malicious activity |
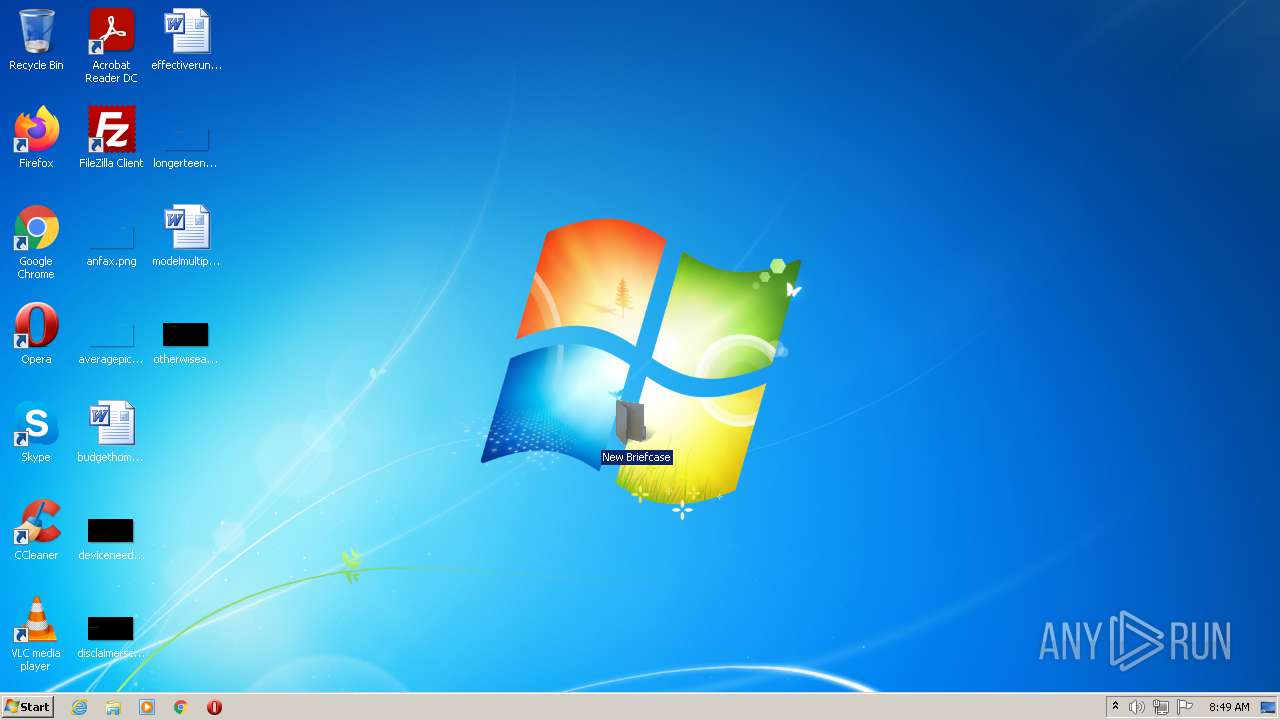
| Analysis date: | September 25, 2021, 07:49:13 |
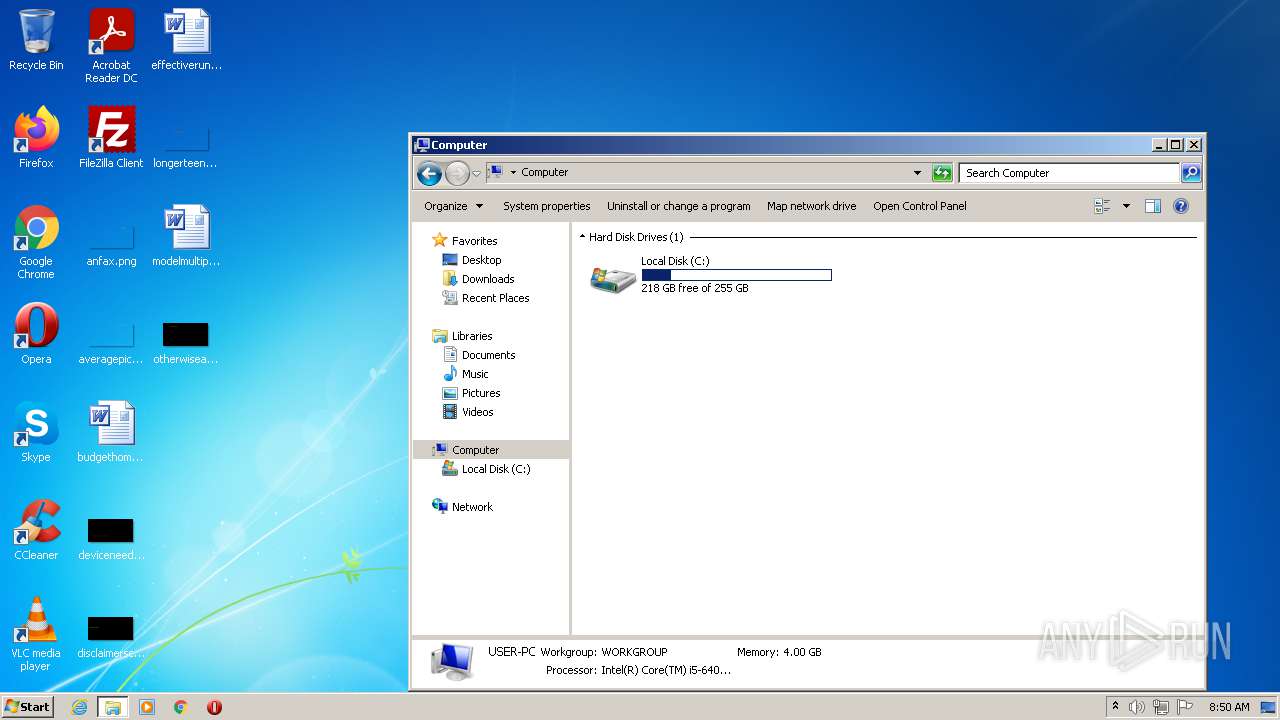
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 4F99381112AC062D19BB96CCC9F4C39F |
| SHA1: | 0B3C406E5868B1C15E1AB5C2692333A098AE6D2A |
| SHA256: | 40FD8820647EFC3E181E45CA4D97A9DE4E1E58383E7B759DBED745A84A61794A |
| SSDEEP: | 24:ttIO8Rs2WOk4411sSlxMGTuzGlmw7IBn9QrwVuas5K4310KfA/E0NLb9sKQrv/Eh:4Okdk448u9uzGIDBFVZq3RKE0dWKE3Eh |
MALICIOUS
Drops executable file immediately after starts
- msdt.exe (PID: 3740)
Application was injected by another process
- svchost.exe (PID: 360)
- svchost.exe (PID: 852)
- SearchIndexer.exe (PID: 3012)
Runs injected code in another process
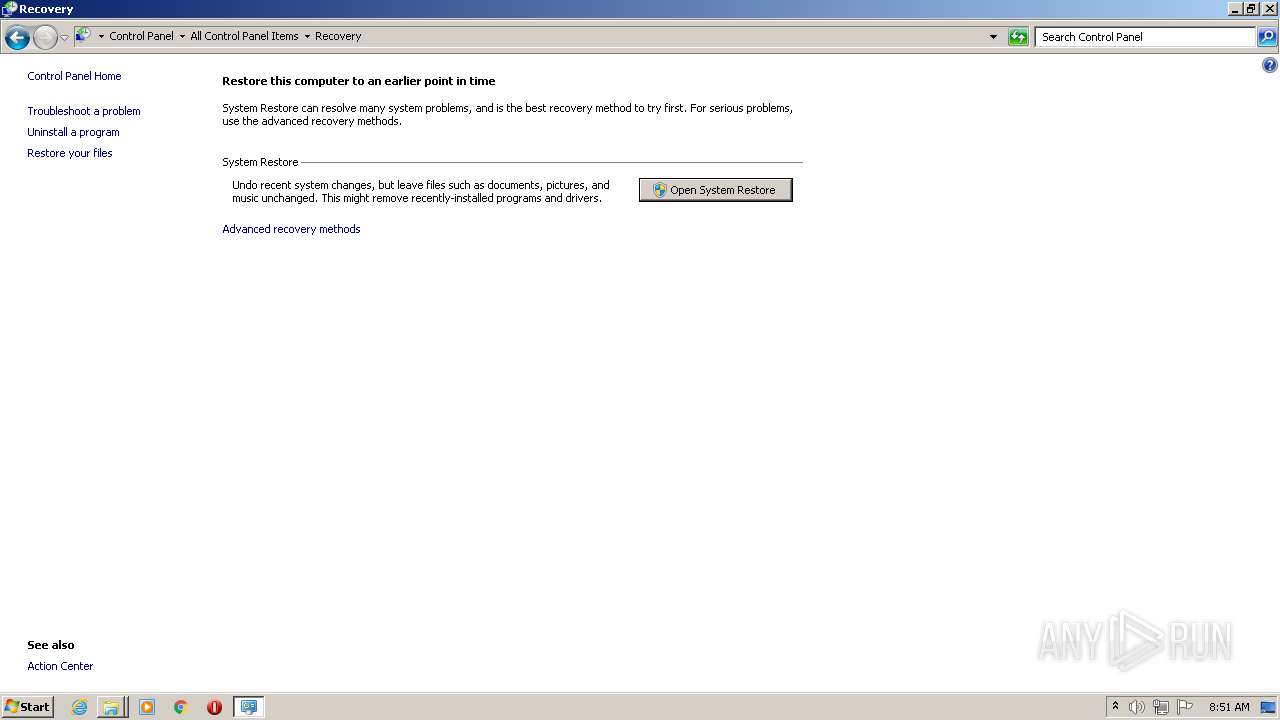
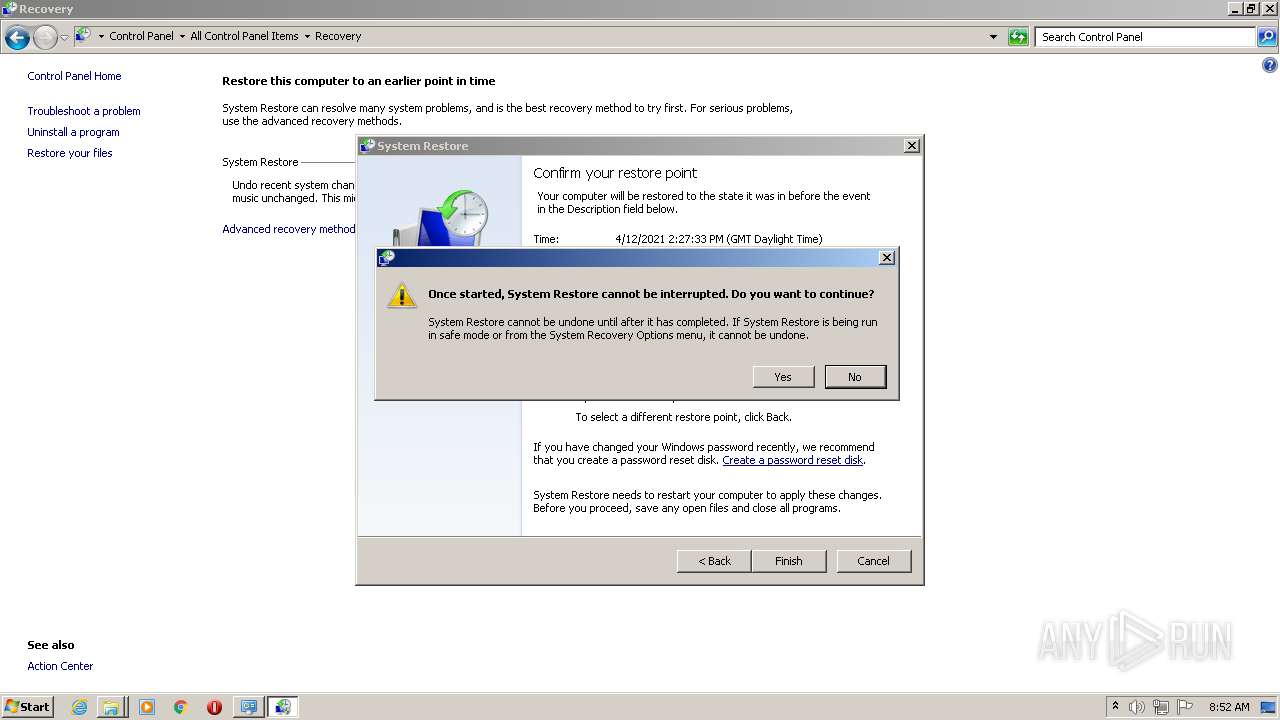
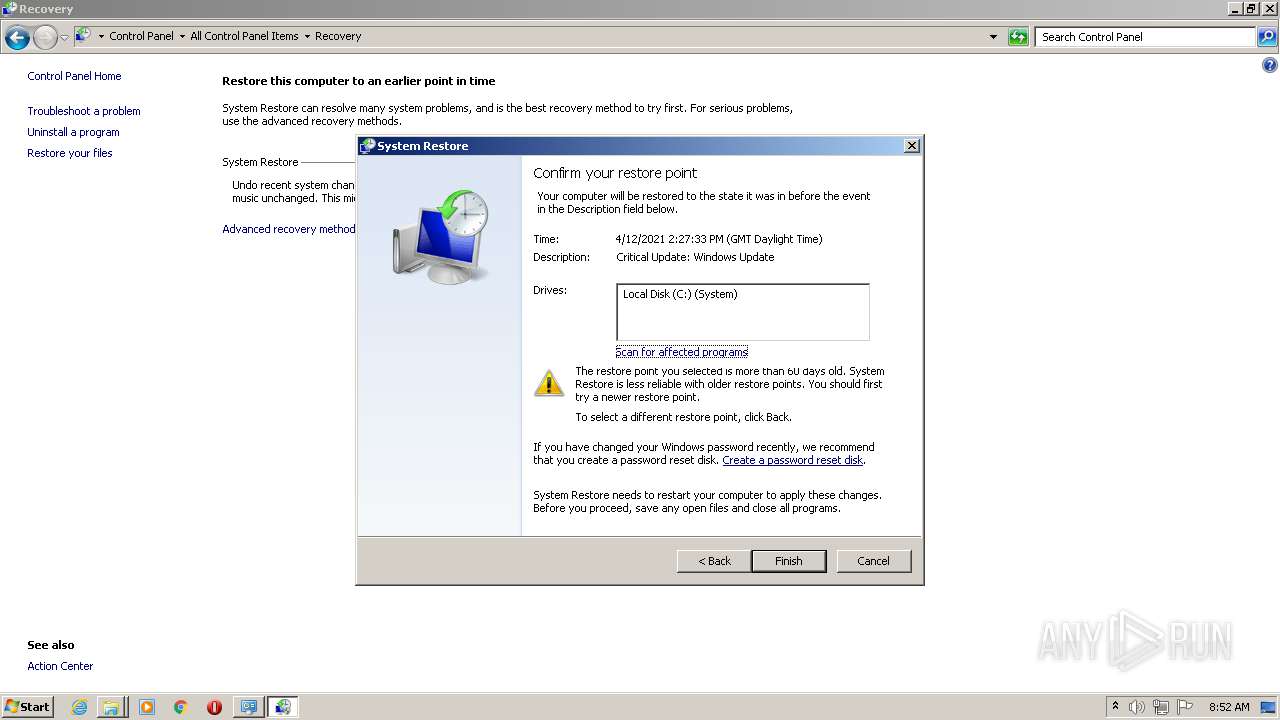
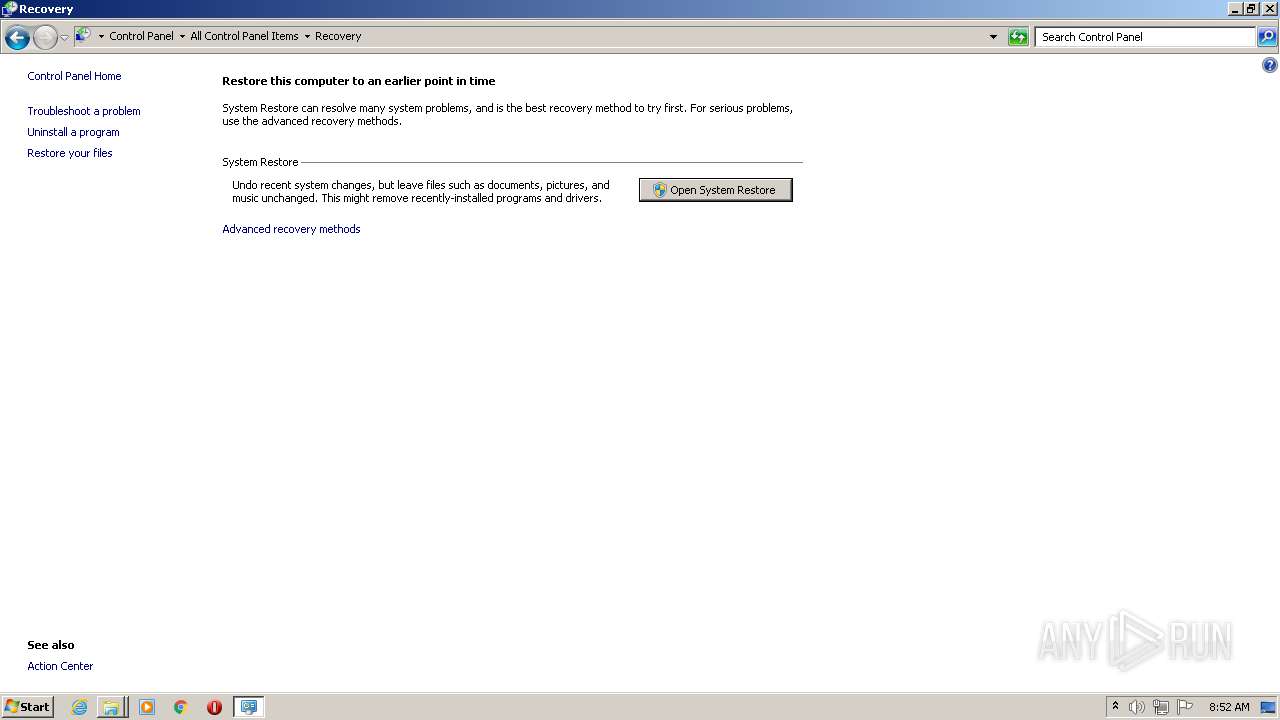
- rstrui.exe (PID: 2308)
Changes settings of System certificates
- svchost.exe (PID: 360)
SUSPICIOUS
Executable content was dropped or overwritten
- msdt.exe (PID: 3740)
Drops a file with too old compile date
- msdt.exe (PID: 3740)
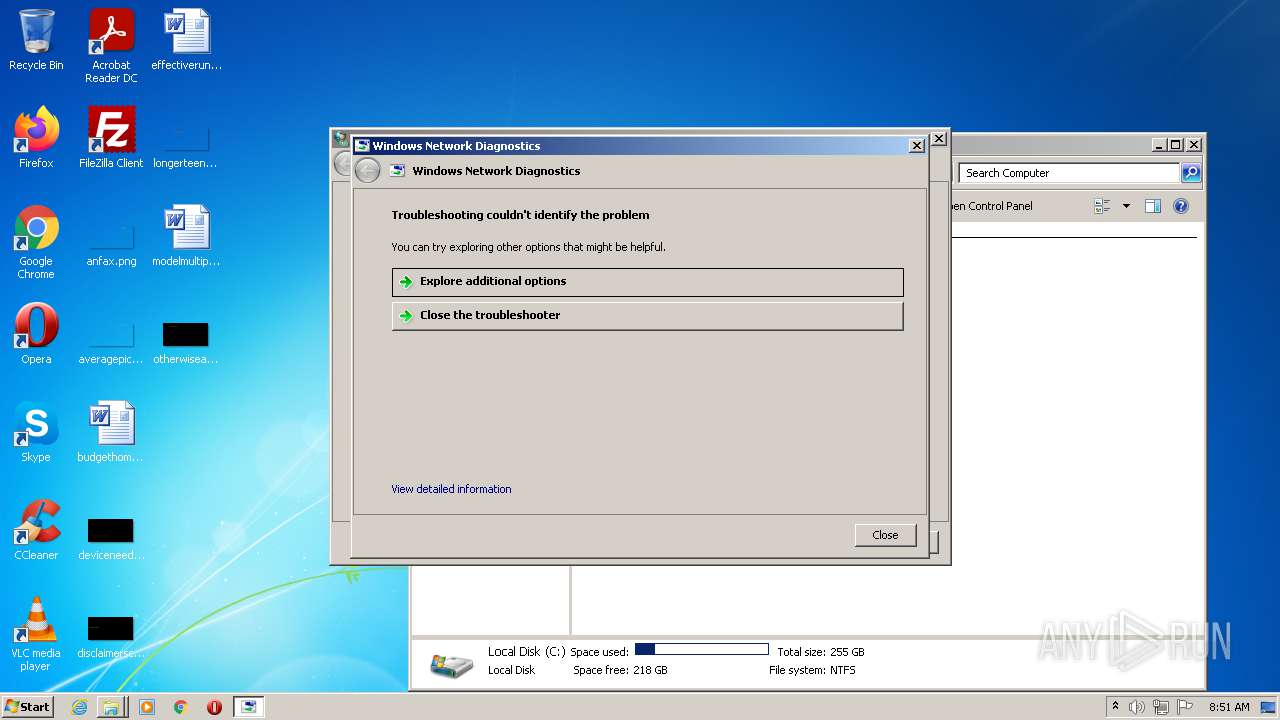
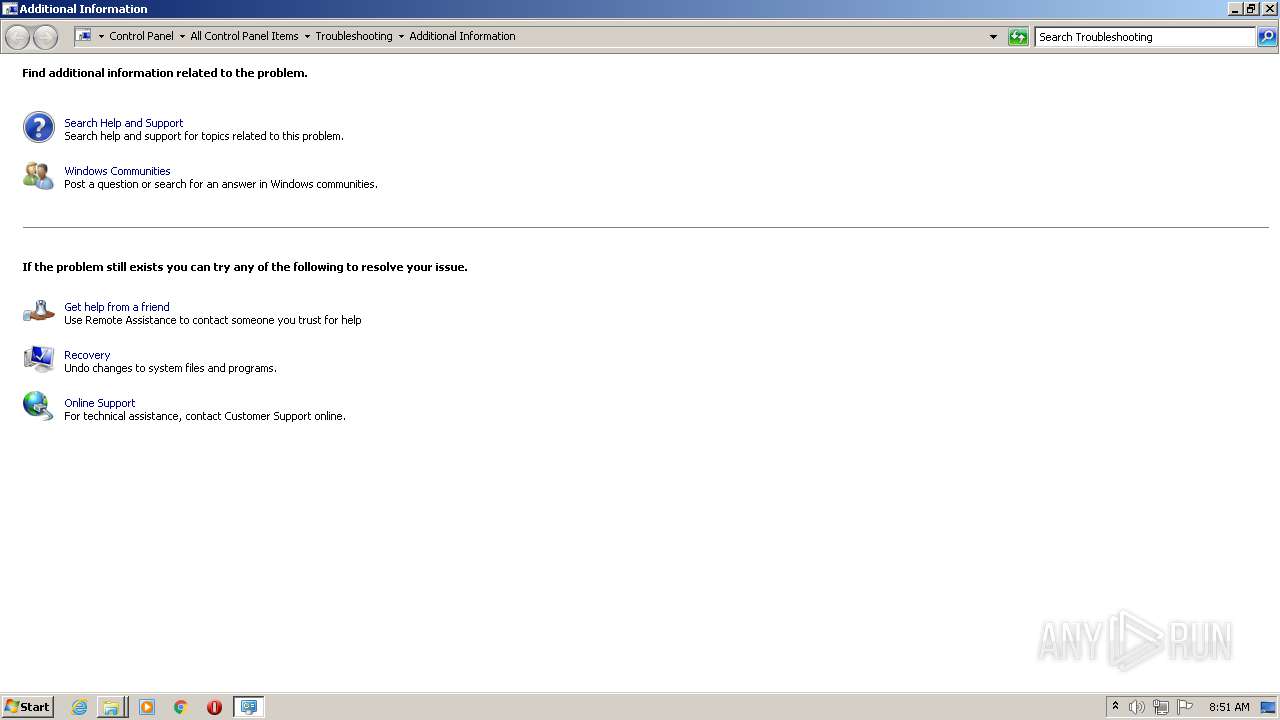
Executed via COM
- sdiagnhost.exe (PID: 3488)
- vdsldr.exe (PID: 408)
Executed as Windows Service
- wbengine.exe (PID: 3624)
- vssvc.exe (PID: 2468)
- vds.exe (PID: 4040)
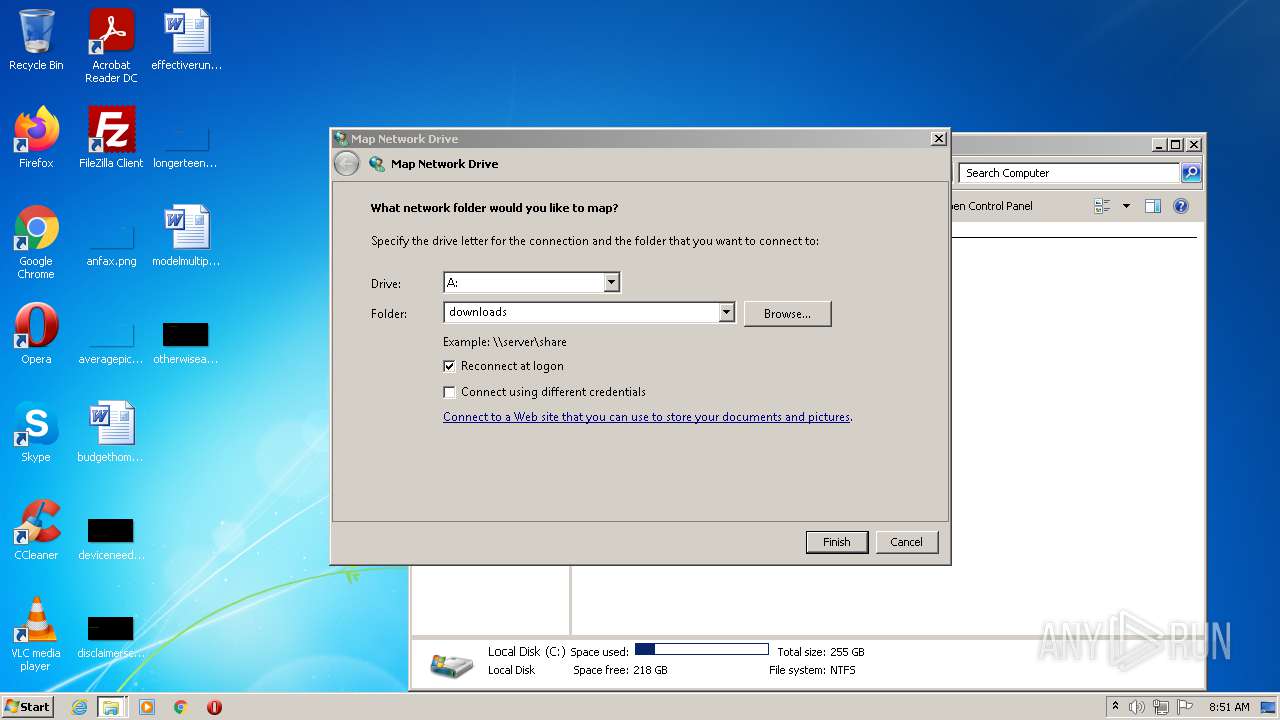
Creates files in the Windows directory
- rstrui.exe (PID: 2308)
- svchost.exe (PID: 360)
Starts Internet Explorer
- rundll32.exe (PID: 2208)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 596)
Removes files from Windows directory
- svchost.exe (PID: 360)
Creates files in the program directory
- SearchIndexer.exe (PID: 3012)
Checks supported languages
- svchost.exe (PID: 852)
INFO
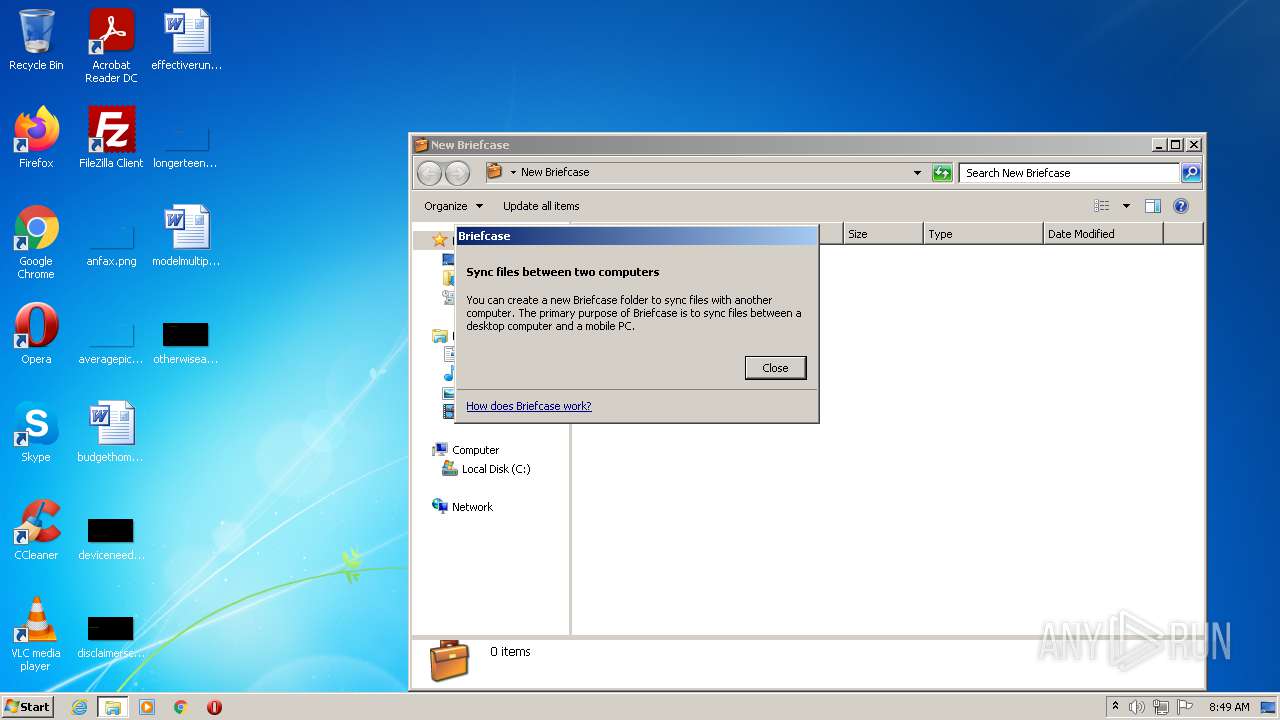
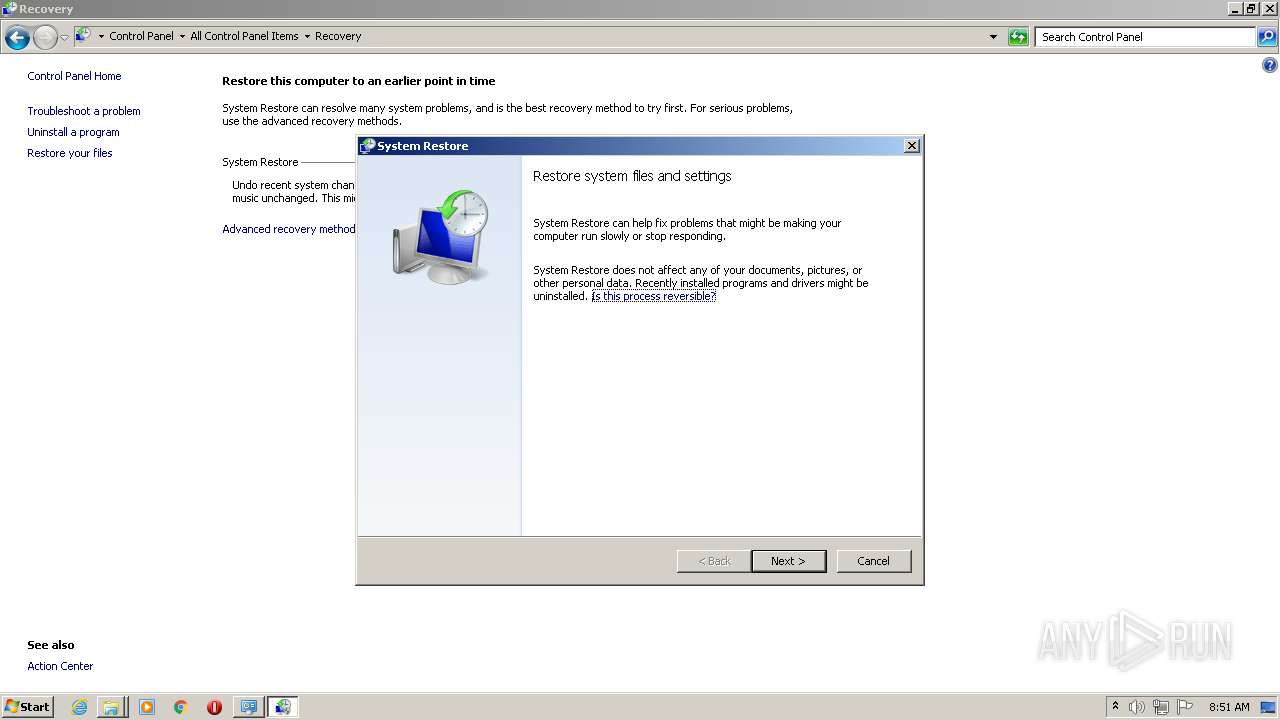
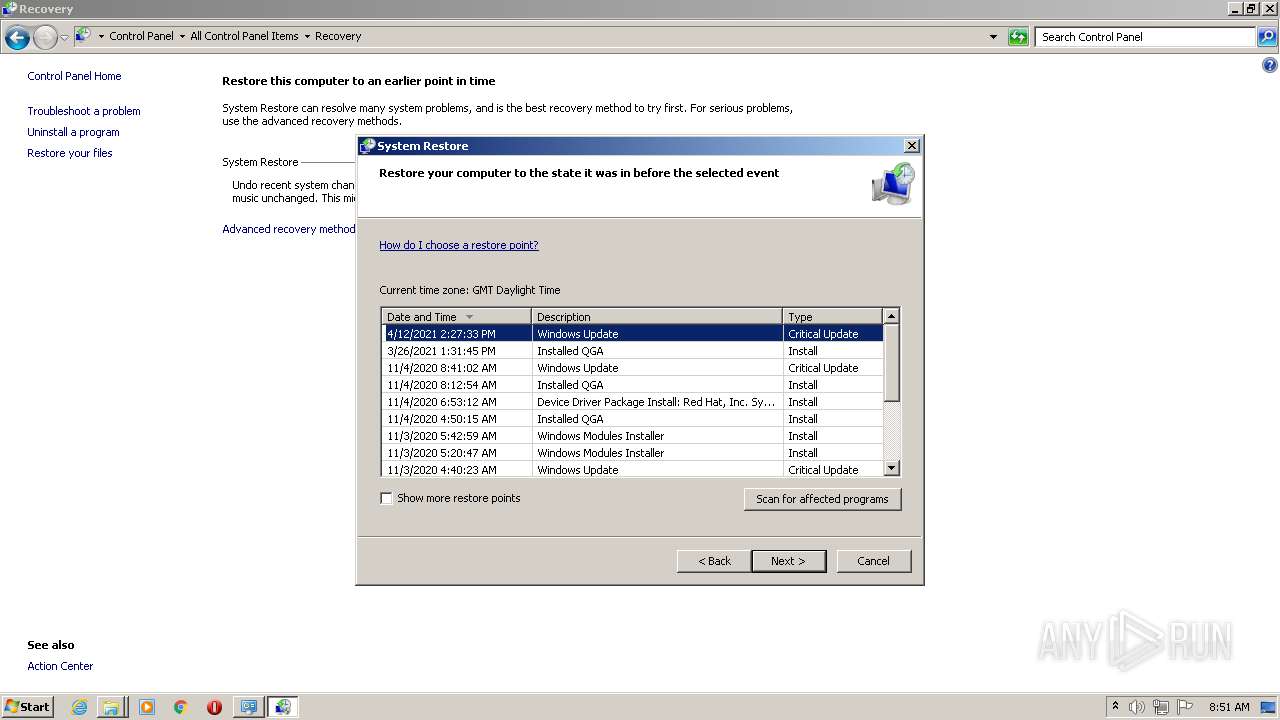
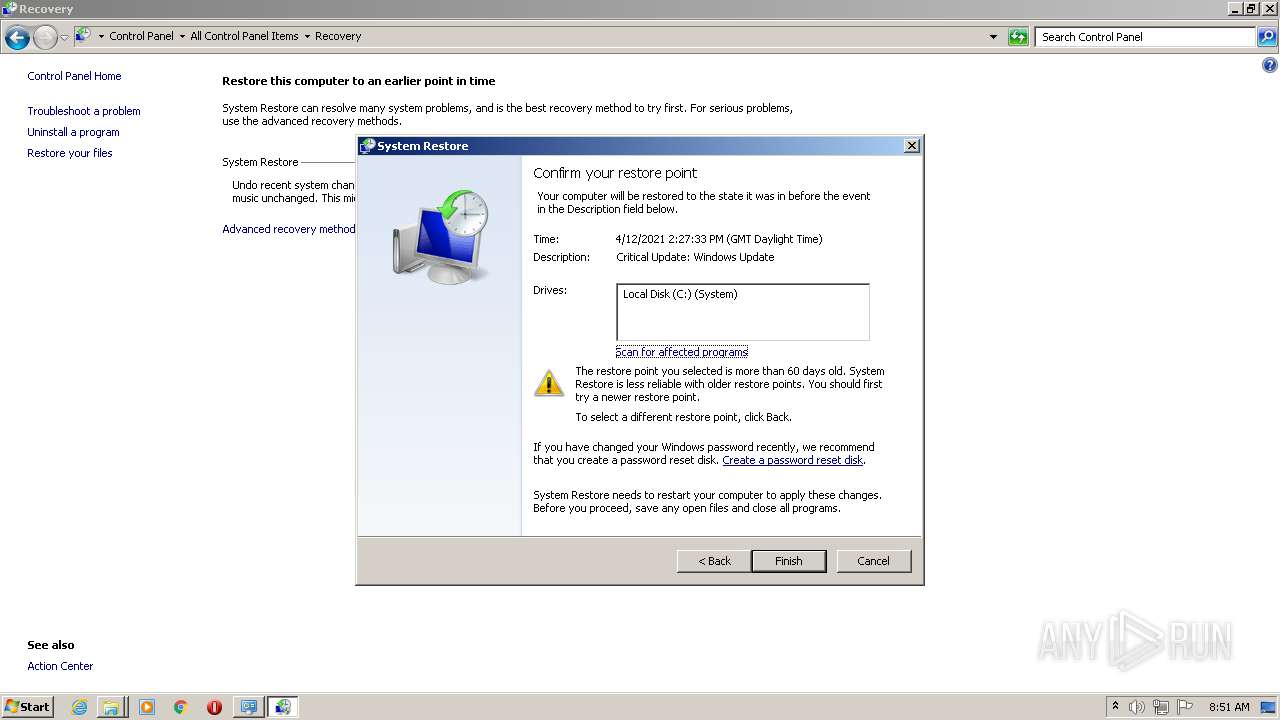
Manual execution by user
- rundll32.exe (PID: 3508)
- rstrui.exe (PID: 2308)
- rundll32.exe (PID: 4048)
- rundll32.exe (PID: 2208)
- WINWORD.EXE (PID: 3944)
- WINWORD.EXE (PID: 2076)
- WINWORD.EXE (PID: 3652)
Checks supported languages
- NOTEPAD.EXE (PID: 3472)
- msdt.exe (PID: 3740)
- rundll32.exe (PID: 3508)
- sdiagnhost.exe (PID: 3488)
- control.exe (PID: 3292)
- rundll32.exe (PID: 4048)
- wbengine.exe (PID: 3624)
- rstrui.exe (PID: 2308)
- vds.exe (PID: 4040)
- vdsldr.exe (PID: 408)
- vssvc.exe (PID: 2468)
- rundll32.exe (PID: 2208)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 596)
- WINWORD.EXE (PID: 3944)
- WINWORD.EXE (PID: 2076)
- WINWORD.EXE (PID: 3652)
Checks Windows Trust Settings
- msdt.exe (PID: 3740)
- sdiagnhost.exe (PID: 3488)
- iexplore.exe (PID: 596)
- iexplore.exe (PID: 2300)
Reads the computer name
- msdt.exe (PID: 3740)
- control.exe (PID: 3292)
- sdiagnhost.exe (PID: 3488)
- rundll32.exe (PID: 4048)
- rstrui.exe (PID: 2308)
- wbengine.exe (PID: 3624)
- vssvc.exe (PID: 2468)
- vdsldr.exe (PID: 408)
- vds.exe (PID: 4040)
- rundll32.exe (PID: 2208)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 596)
- WINWORD.EXE (PID: 3652)
- WINWORD.EXE (PID: 3944)
- WINWORD.EXE (PID: 2076)
Reads settings of System Certificates
- msdt.exe (PID: 3740)
- svchost.exe (PID: 360)
- iexplore.exe (PID: 596)
- iexplore.exe (PID: 2300)
Application launched itself
- iexplore.exe (PID: 2300)
Changes internet zones settings
- iexplore.exe (PID: 2300)
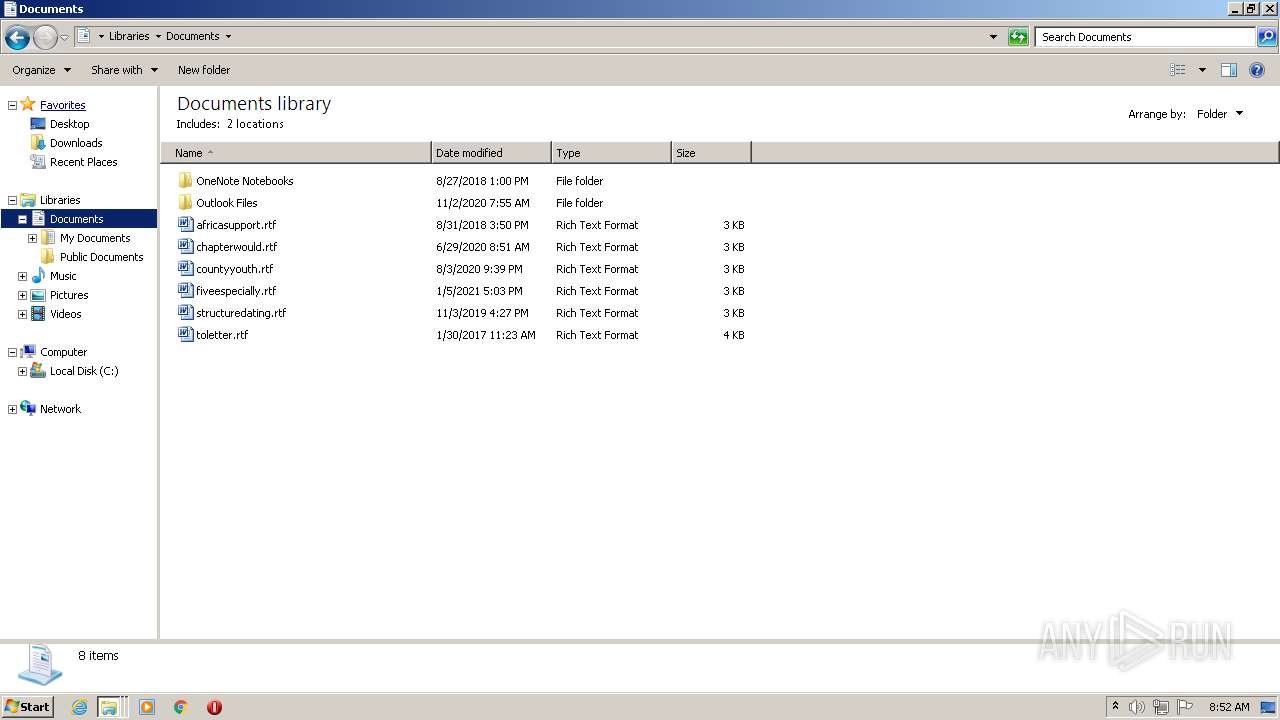
Creates files in the user directory
- iexplore.exe (PID: 596)
- WINWORD.EXE (PID: 3652)
- WINWORD.EXE (PID: 3944)
- WINWORD.EXE (PID: 2076)
Reads internet explorer settings
- iexplore.exe (PID: 596)
Reads the date of Windows installation
- iexplore.exe (PID: 2300)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2076)
- WINWORD.EXE (PID: 3652)
- WINWORD.EXE (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
20
Malicious processes
2
Suspicious processes
1
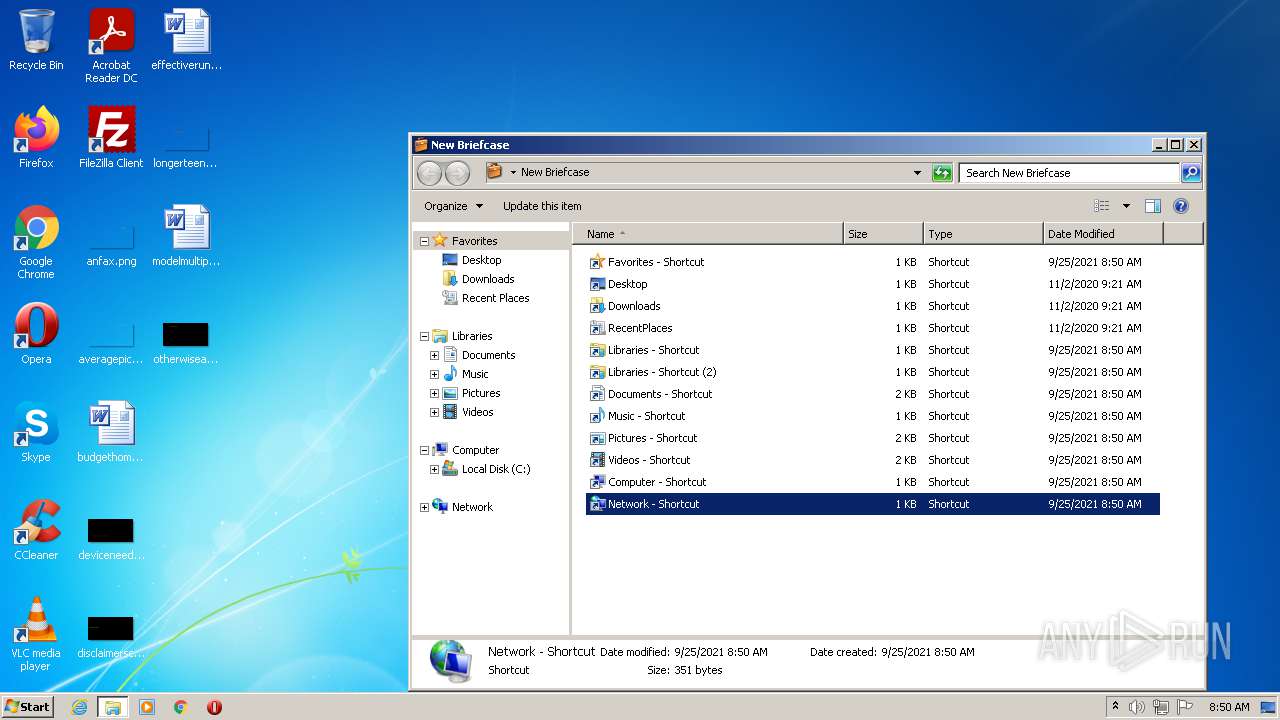
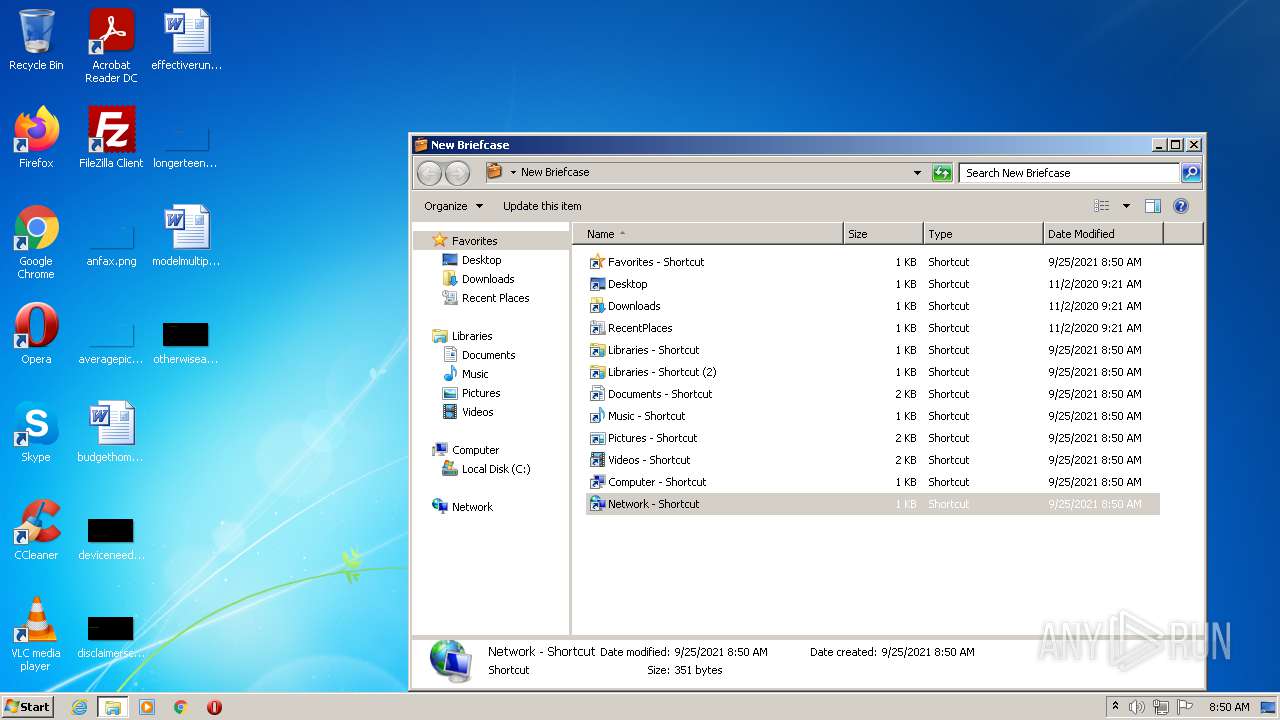
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 408 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
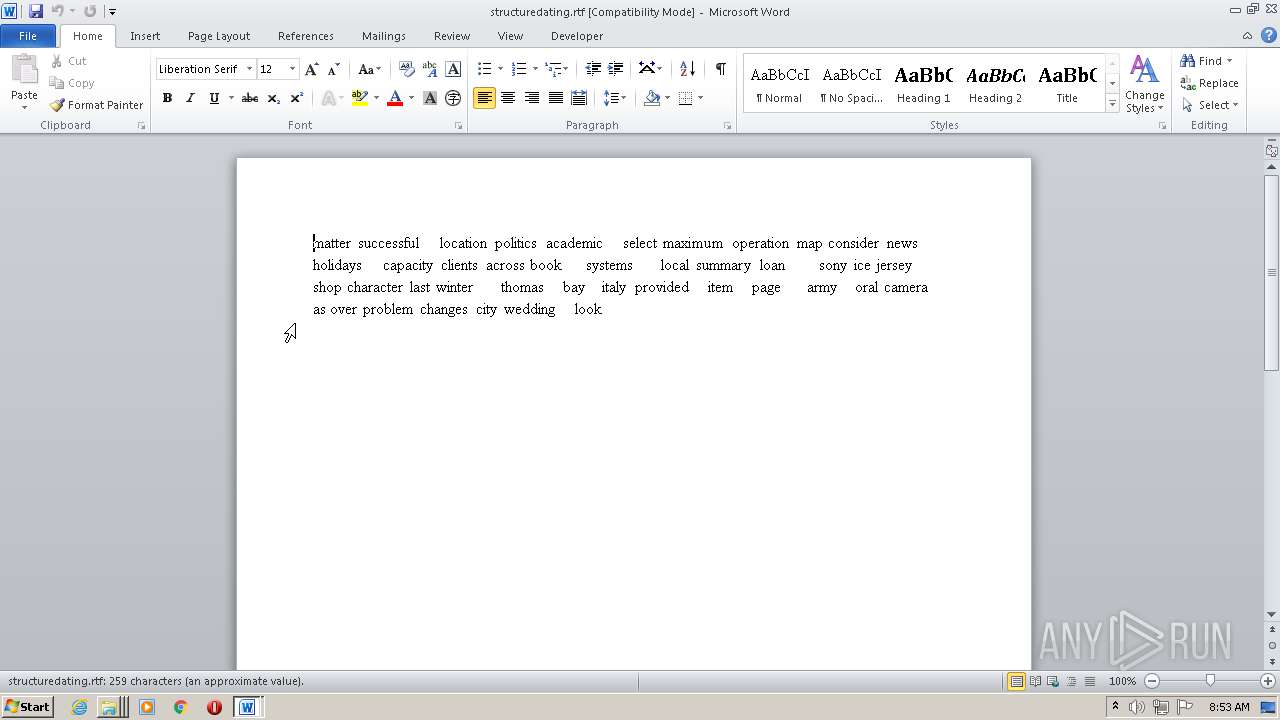
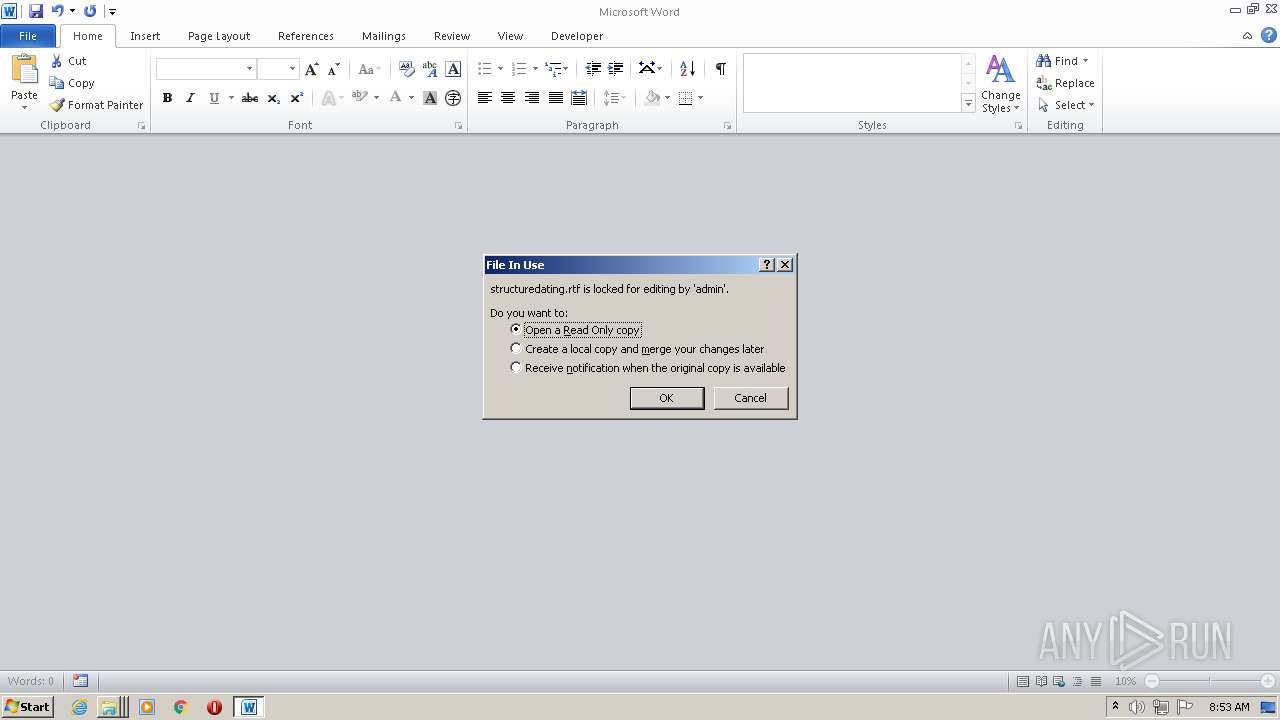
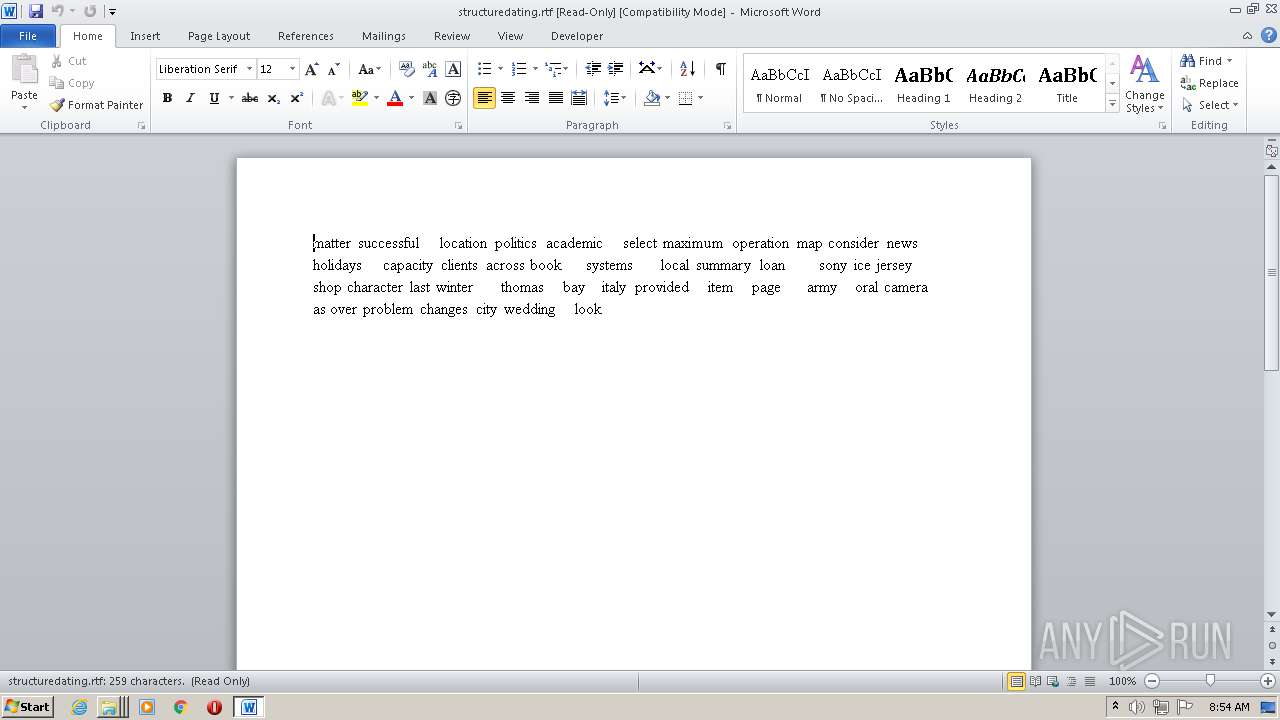
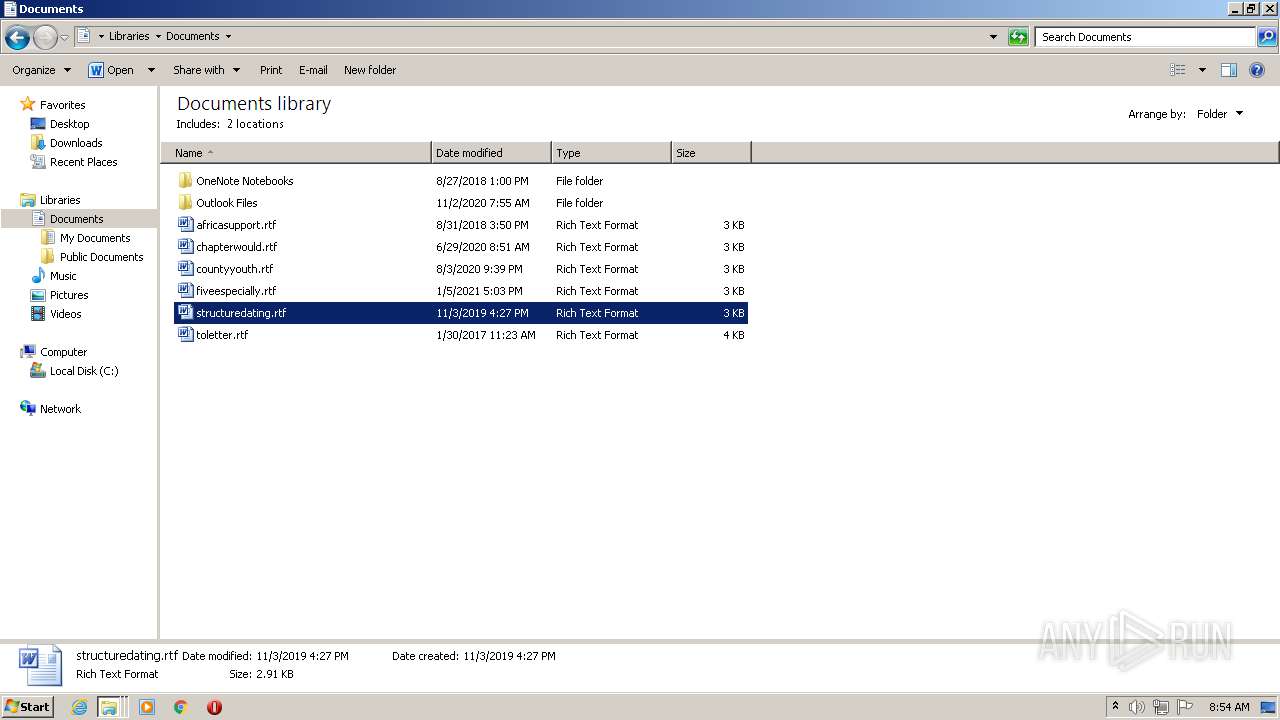
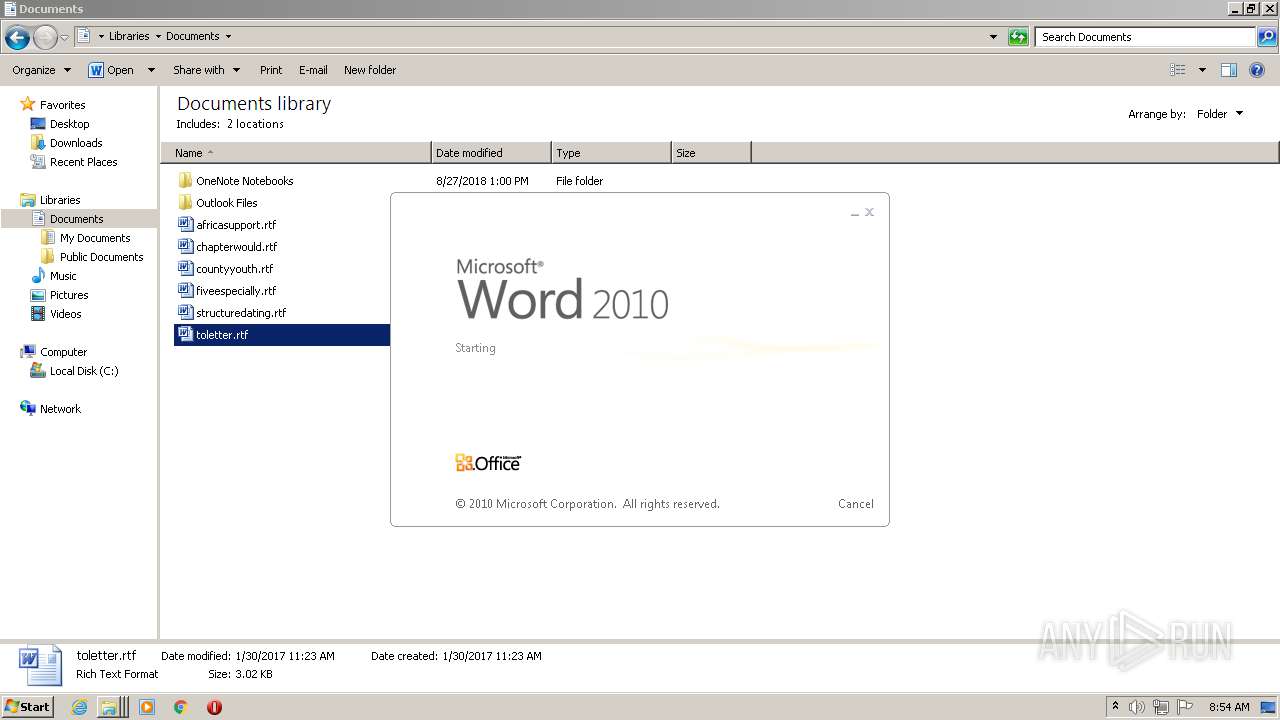
| 2076 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\toletter.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
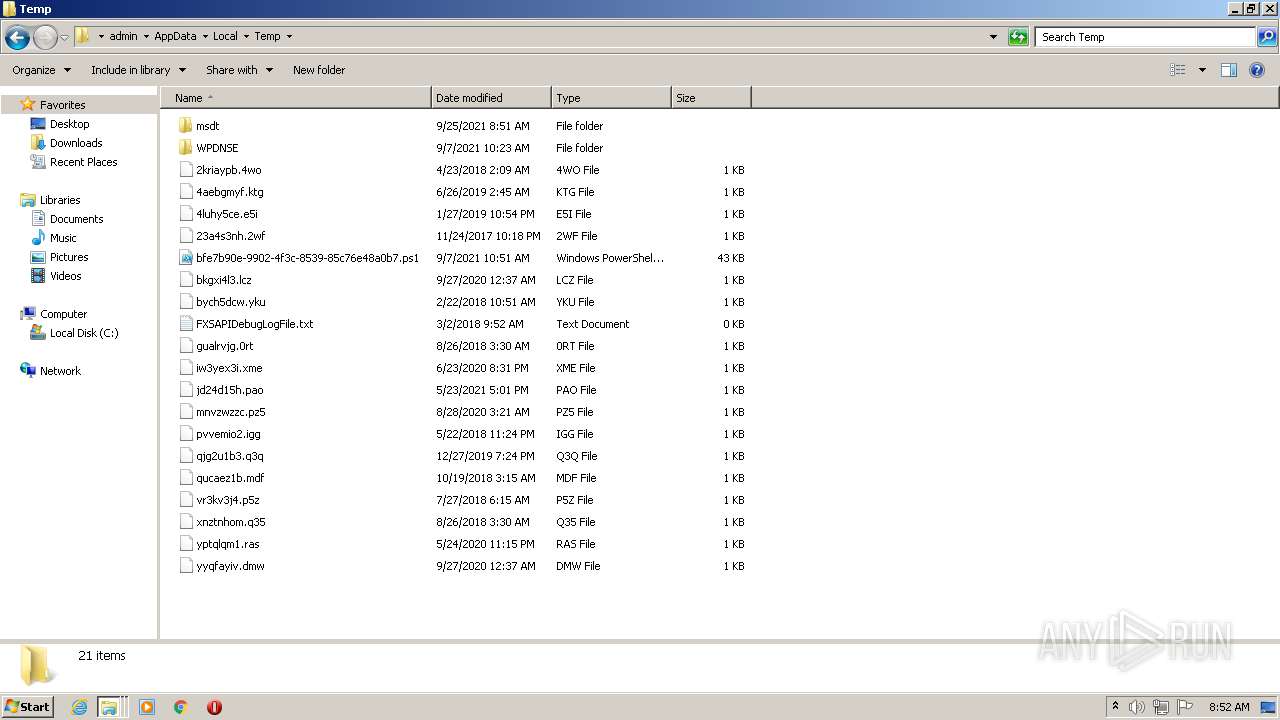
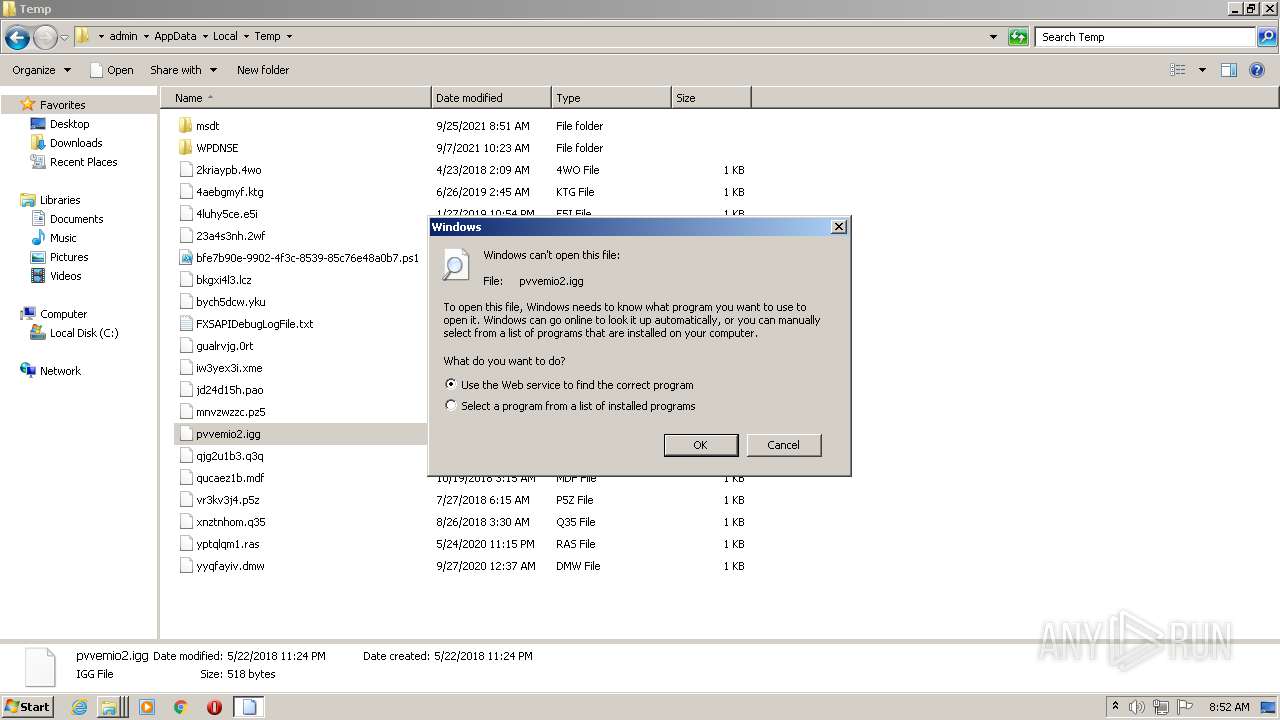
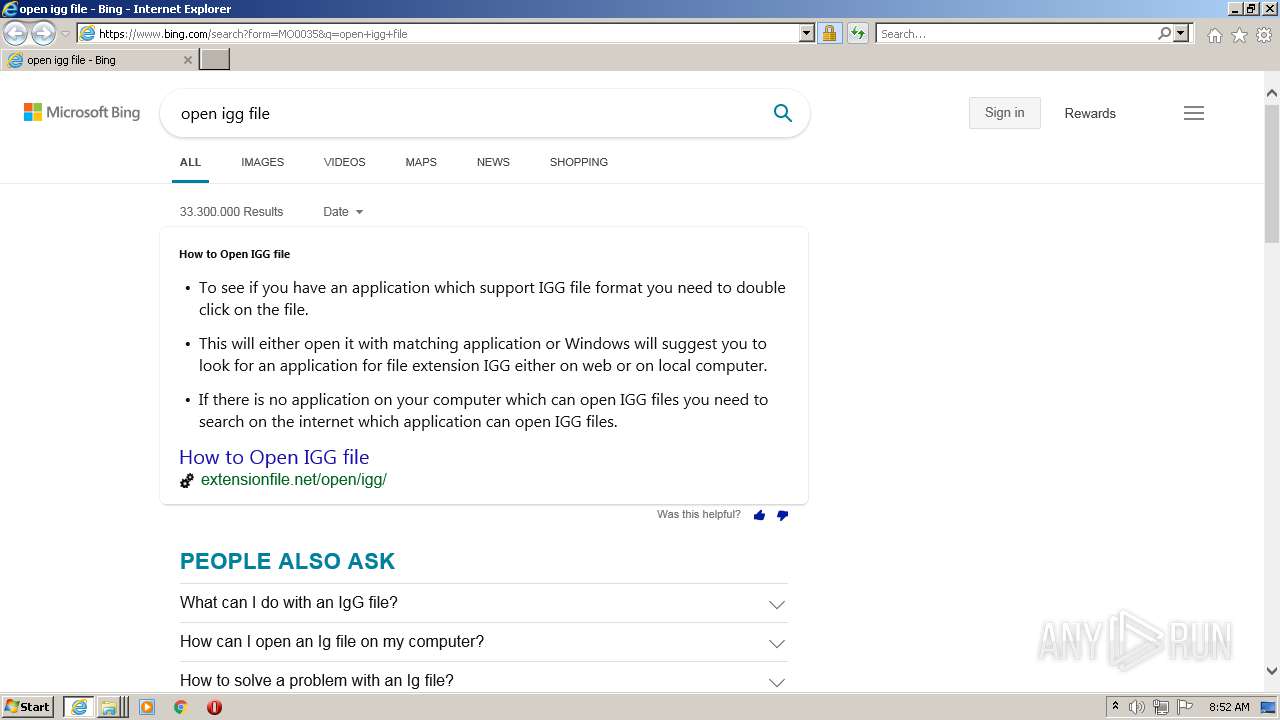
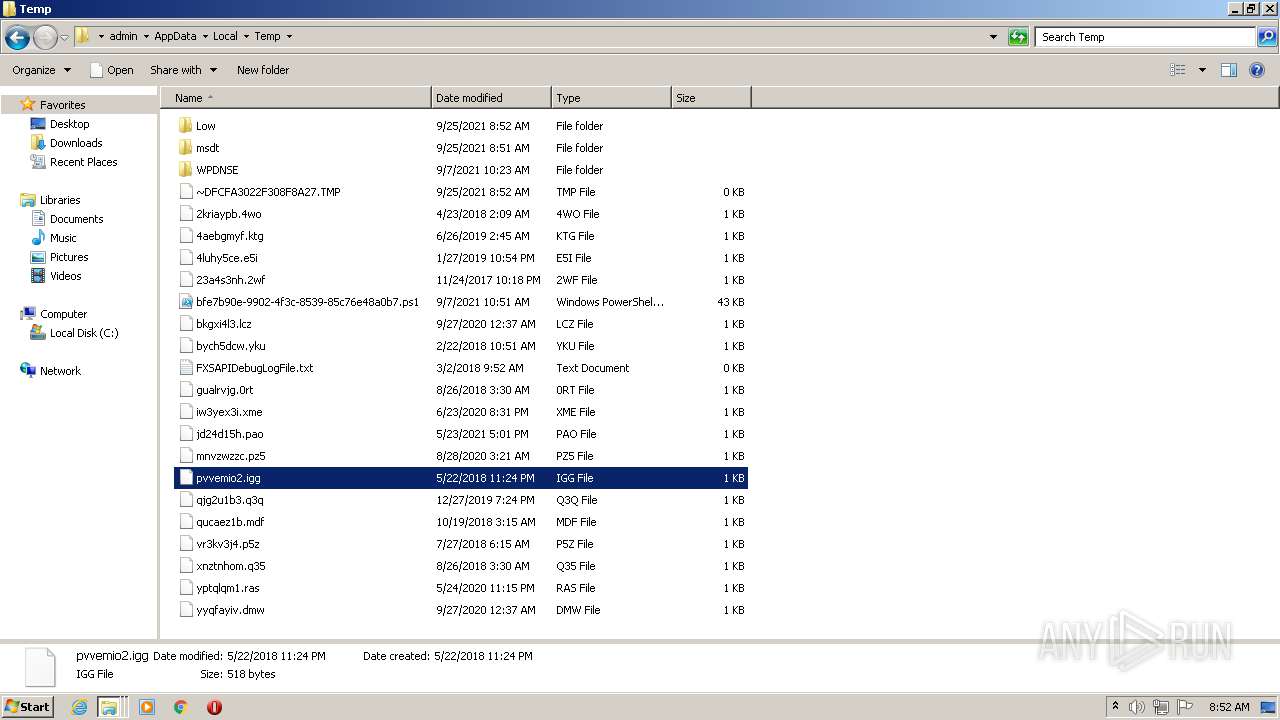
| 2208 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\pvvemio2.igg | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=igg | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2308 | "C:\Windows\system32\rstrui.exe" | C:\Windows\system32\rstrui.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Windows System Restore Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 453
Read events
29 036
Write events
1 038
Delete events
379
Modification events
| (PID) Process: | (3740) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3488) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3488) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3488) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3488) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3740) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3740) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3740) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3740) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3292) control.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
44
Text files
104
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\result\DebugReport.xml | xml | |
MD5:— | SHA256:— | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\DiagPackage.dll | executable | |
MD5:2433E09C08C21455000F7E36D7653759 | SHA256:EA9400E719FB15CD82D5DAB4B7D8E3870BB375BBE11BB95B0D957A84FEE2891C | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\result\ResultReport.xml | xml | |
MD5:— | SHA256:— | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Diagnostics\460911090\2021092507.000\DebugReport.xml | xml | |
MD5:— | SHA256:— | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Diagnostics\460911090\2021092507.000\ResultReport.xml | xml | |
MD5:— | SHA256:— | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\HTInteractiveRes.ps1 | text | |
MD5:C25ED2111C6EE9299E6D9BF51012F2F5 | SHA256:8E326EE0475208D4C943D885035058FAD7146BBA02B66305F7C9F31F6A57E81B | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\NetworkDiagnosticsResolve.ps1 | text | |
MD5:A7B957F221C643580184665BE57E6AC8 | SHA256:8582EF50174CB74233F196F193E04C0CCBBEE2AED5CE50964CBB95822C218E7F | |||
| 3740 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_5214c6d8-082b-4362-b5d4-a9da7027ceb3\NetworkDiagnosticsTroubleshoot.ps1 | text | |
MD5:1D192CE36953DBB7DC7EE0D04C57AD8D | SHA256:935A231924AE5D4A017B0C99D4A5F3904EF280CEA4B3F727D365283E26E8A756 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
596 | iexplore.exe | GET | 301 | 23.39.160.50:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=igg | NL | — | — | whitelisted |
2300 | iexplore.exe | GET | 304 | 2.23.158.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5dafd3d871276439 | unknown | — | — | whitelisted |
596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
596 | iexplore.exe | GET | 200 | 2.23.158.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?232a02d6c36fc7ef | unknown | compressed | 4.70 Kb | whitelisted |
2300 | iexplore.exe | GET | 304 | 2.23.158.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?77a7e12f83a6f553 | unknown | — | — | whitelisted |
596 | iexplore.exe | GET | 200 | 2.23.158.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3be1e857d7a0ab68 | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
596 | iexplore.exe | 20.190.160.132:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
596 | iexplore.exe | 2.18.105.186:443 | go.microsoft.com | Deutsche Telekom AG | — | suspicious |
596 | iexplore.exe | 2.23.158.8:80 | ctldl.windowsupdate.com | Telia Company AB | — | unknown |
596 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
596 | iexplore.exe | 23.39.160.50:80 | shell.windows.com | TELECOM ITALIA SPARKLE S.p.A. | NL | suspicious |
596 | iexplore.exe | 40.126.31.135:443 | login.live.com | Microsoft Corporation | US | suspicious |
2300 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
596 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2300 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2300 | iexplore.exe | 2.23.158.8:80 | ctldl.windowsupdate.com | Telia Company AB | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |