| File name: | Yandex.exe |
| Full analysis: | https://app.any.run/tasks/f89376a7-3207-436a-800d-2bcc42fd1354 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2018, 06:24:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 22F58C0F305F510962CC8515373F3238 |
| SHA1: | 8534D7BD7C5D8FFAAF97FC421E54F9B55F79A11A |
| SHA256: | 40ED9098C52D60F4C258745CCCB9E7BDE0A4C7F96329B3669A26FBD0B9B88518 |
| SSDEEP: | 24576:5RiYYaOYRK4yfPndVKVTb+0dMfofzGPnVaN/0aiG0:5RTN1KdfPiVP+0iqGtUre |
MALICIOUS
Loads the Task Scheduler COM API
- service_update.exe (PID: 2632)
- searchbandapp.exe (PID: 3788)
- browser.exe (PID: 1320)
- explorer.exe (PID: 1604)
Loads the Task Scheduler DLL interface
- service_update.exe (PID: 3212)
- service_update.exe (PID: 1460)
- browser.exe (PID: 1320)
Application was dropped or rewritten from another process
- service_update.exe (PID: 3604)
- service_update.exe (PID: 2364)
- service_update.exe (PID: 2632)
- service_update.exe (PID: 3180)
- service_update.exe (PID: 3596)
- service_update.exe (PID: 3212)
- setup.exe (PID: 676)
- setup.exe (PID: 2668)
- setup.exe (PID: 3924)
- clidmgr.exe (PID: 3196)
- clidmgr.exe (PID: 3824)
- clidmgr.exe (PID: 2372)
- service_update.exe (PID: 1460)
- Yandex.exe (PID: 3444)
- Yandex__.exe (PID: 2652)
- clidmgr.exe (PID: 3136)
- SEARCHBAND.EXE (PID: 2620)
- crashreporter.exe (PID: 1708)
- searchbandapp.exe (PID: 2820)
- searchbandapp.exe (PID: 3788)
- browser.exe (PID: 1320)
- browser.exe (PID: 3808)
- searchbandcf.exe (PID: 2412)
- browser.exe (PID: 2728)
- browser.exe (PID: 3536)
- browser.exe (PID: 3552)
- SearchbandApp.exe (PID: 3128)
- browser.exe (PID: 3032)
- browser.exe (PID: 1180)
- browser.exe (PID: 2860)
- browser.exe (PID: 624)
- browser.exe (PID: 3492)
- browser.exe (PID: 3320)
- browser.exe (PID: 2952)
- browser.exe (PID: 3452)
- browser.exe (PID: 3352)
- browser.exe (PID: 600)
- browser.exe (PID: 2544)
- searchbandapp.exe (PID: 2704)
Changes the autorun value in the registry
- searchbandapp.exe (PID: 3788)
- browser.exe (PID: 1320)
Loads dropped or rewritten executable
- searchbandapp.exe (PID: 3788)
- explorer.exe (PID: 1604)
- browser.exe (PID: 1320)
- browser.exe (PID: 2728)
- browser.exe (PID: 3808)
- searchbandcf.exe (PID: 2412)
- browser.exe (PID: 3552)
- browser.exe (PID: 3536)
- browser.exe (PID: 3032)
- browser.exe (PID: 1180)
- browser.exe (PID: 624)
- browser.exe (PID: 3492)
- browser.exe (PID: 2860)
- browser.exe (PID: 3320)
- browser.exe (PID: 2952)
- browser.exe (PID: 3452)
- browser.exe (PID: 3352)
- browser.exe (PID: 600)
- browser.exe (PID: 2544)
Changes settings of System certificates
- setup.exe (PID: 2668)
- service_update.exe (PID: 3180)
SUSPICIOUS
Starts itself from another location
- Yandex.exe (PID: 3440)
- searchbandapp.exe (PID: 2820)
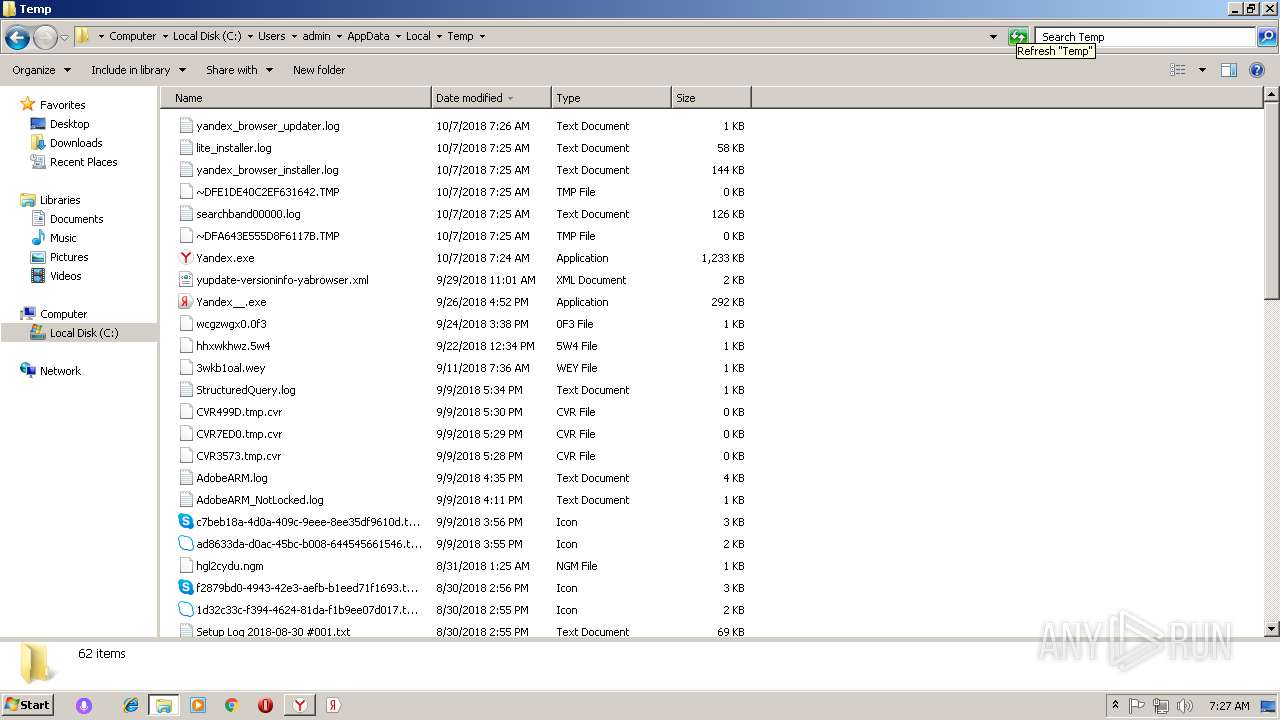
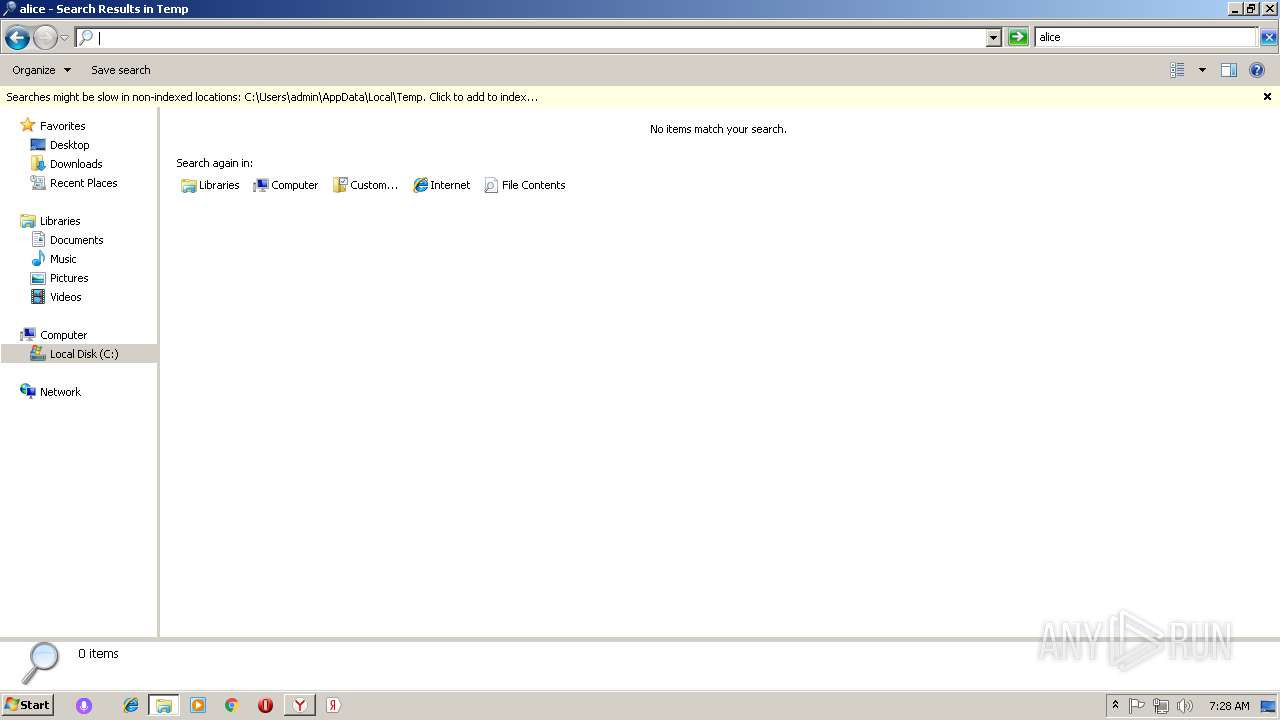
Executable content was dropped or overwritten
- Yandex.exe (PID: 3440)
- service_update.exe (PID: 3604)
- service_update.exe (PID: 2364)
- yb1D7B.tmp (PID: 3900)
- Yandex.exe (PID: 3444)
- msiexec.exe (PID: 1192)
- searchbandapp.exe (PID: 2820)
- Yandex__.exe (PID: 2652)
- explorer.exe (PID: 1604)
- setup.exe (PID: 2668)
Creates files in the program directory
- service_update.exe (PID: 2364)
- service_update.exe (PID: 3212)
Creates files in the Windows directory
- service_update.exe (PID: 3596)
- service_update.exe (PID: 3180)
- service_update.exe (PID: 3212)
- service_update.exe (PID: 1460)
- browser.exe (PID: 1320)
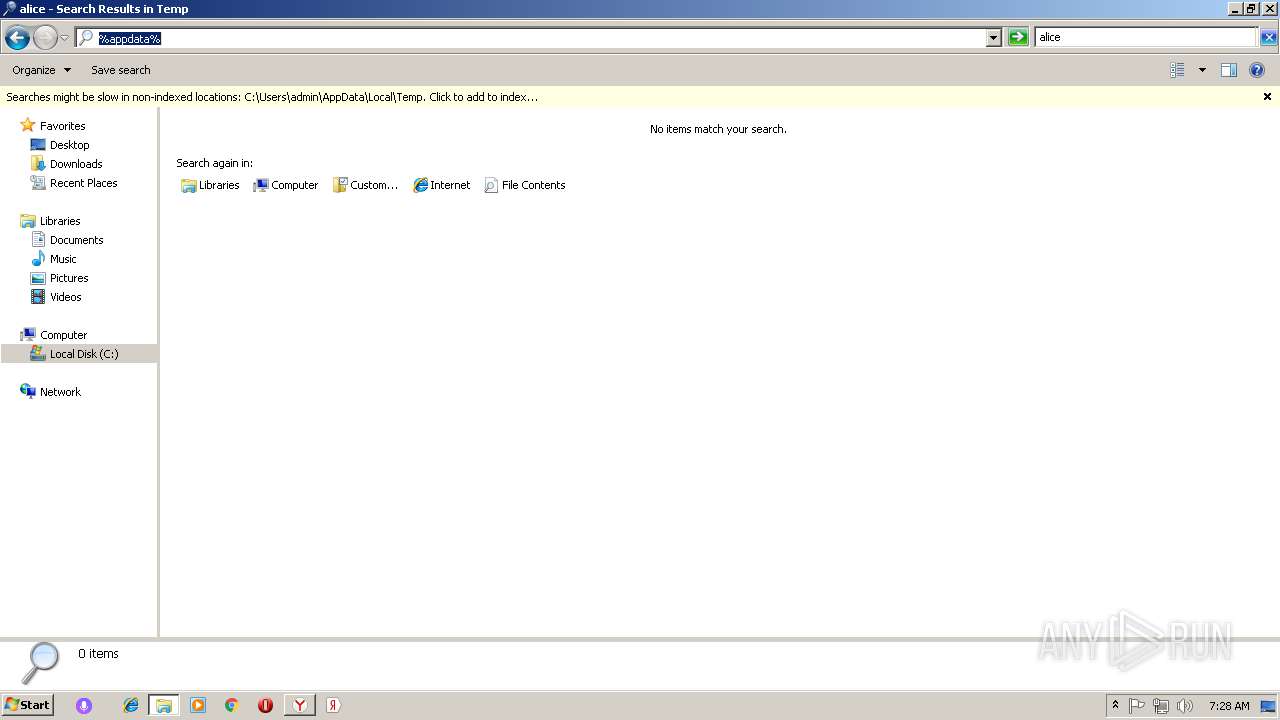
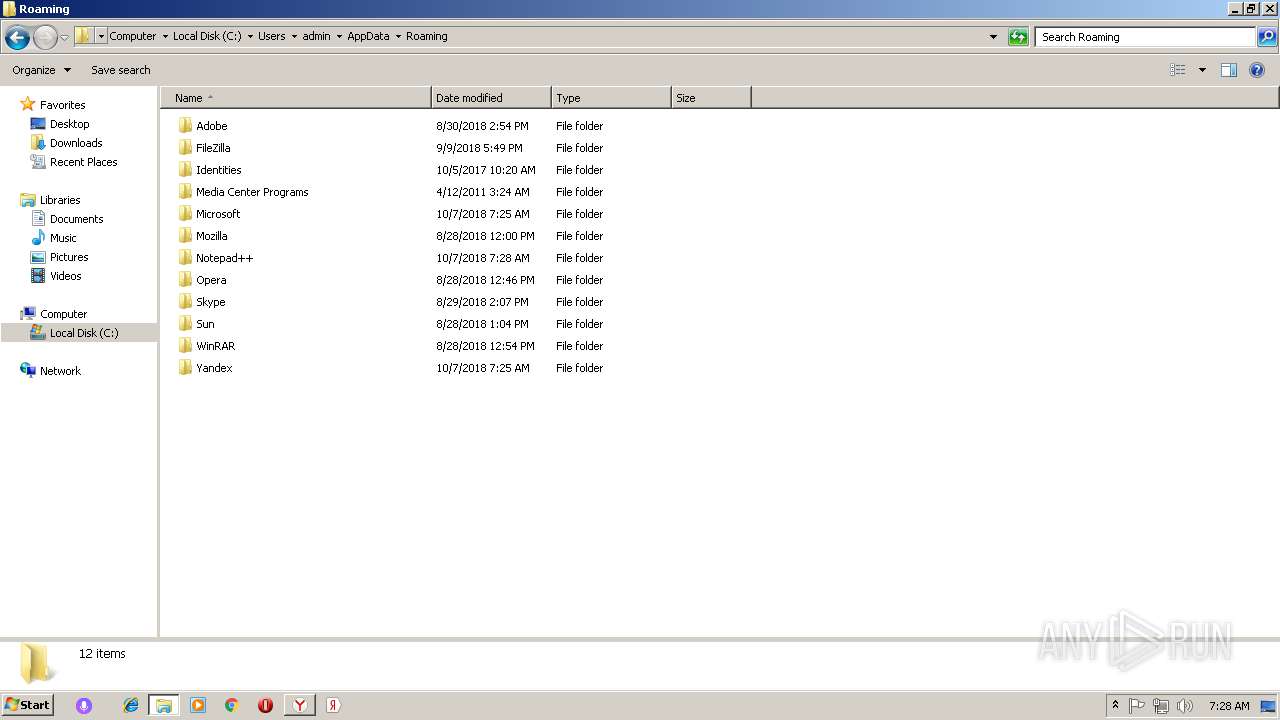
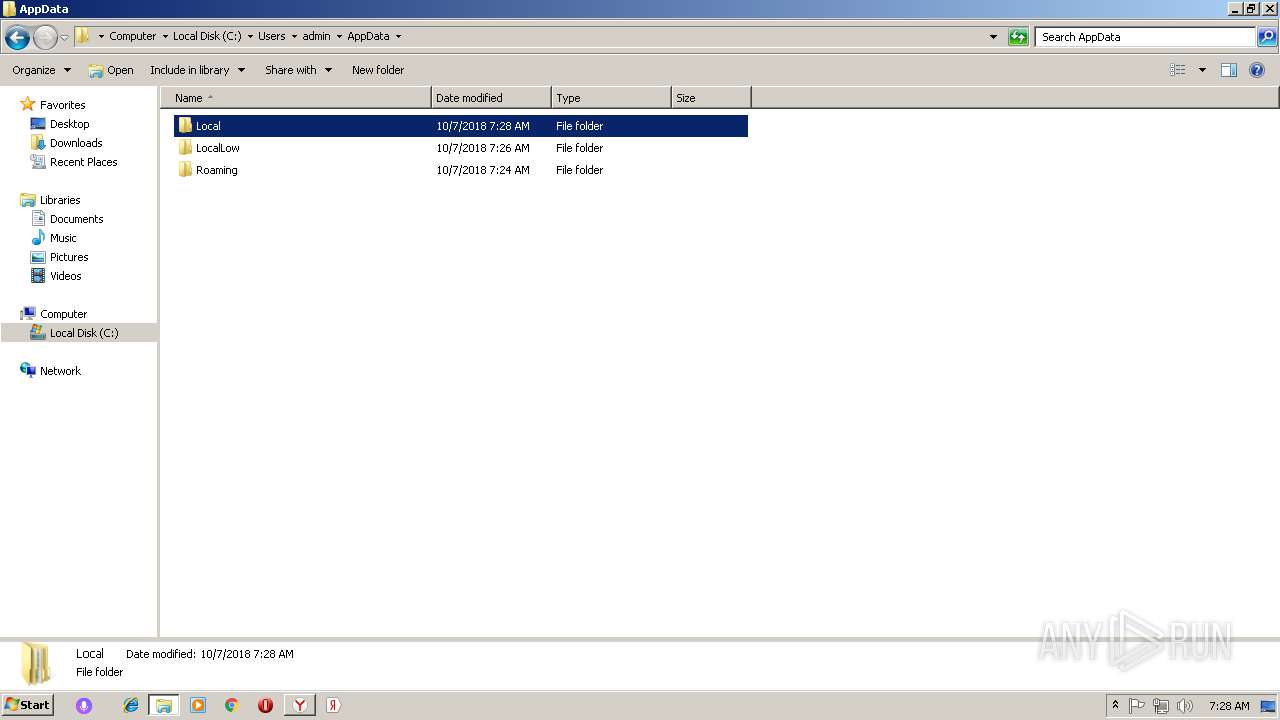
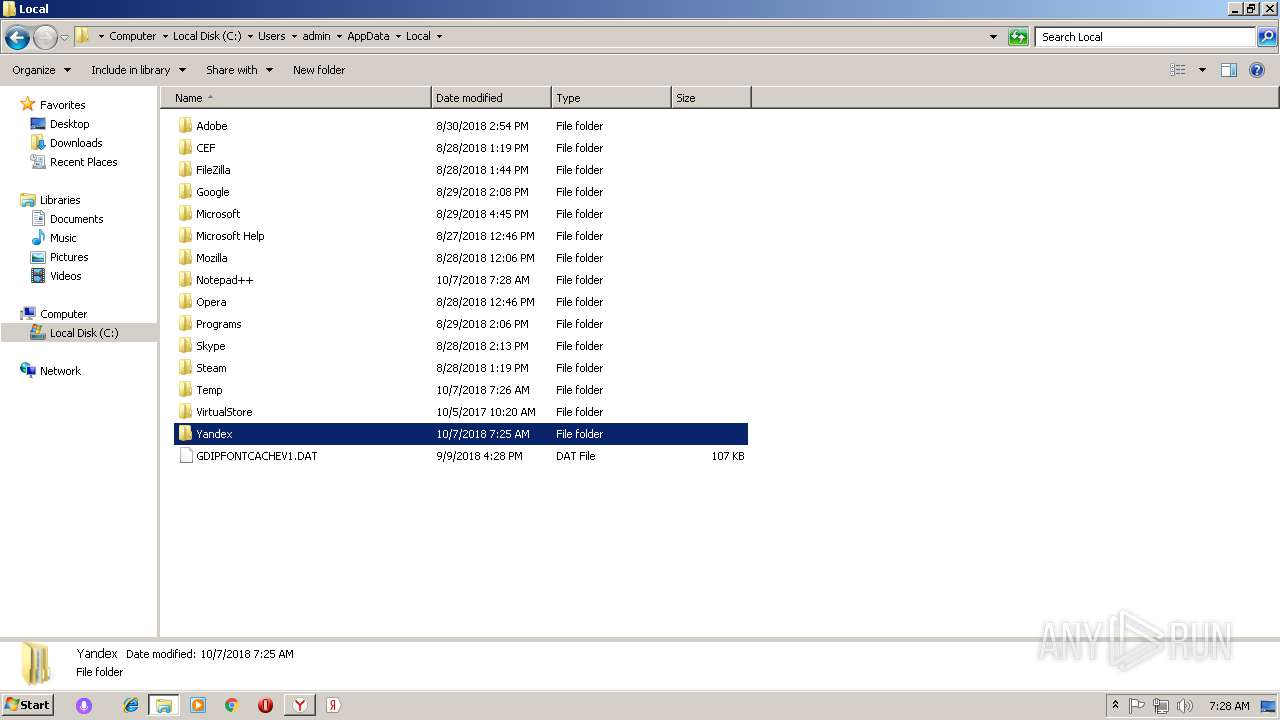
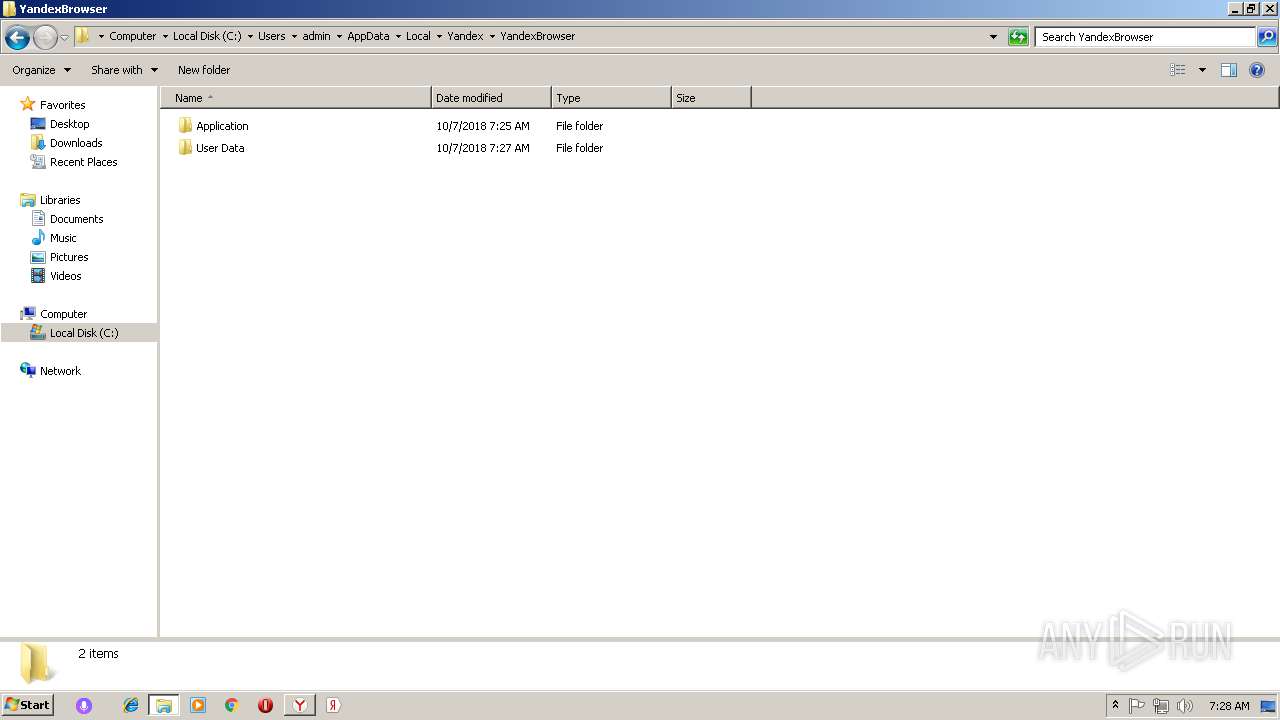
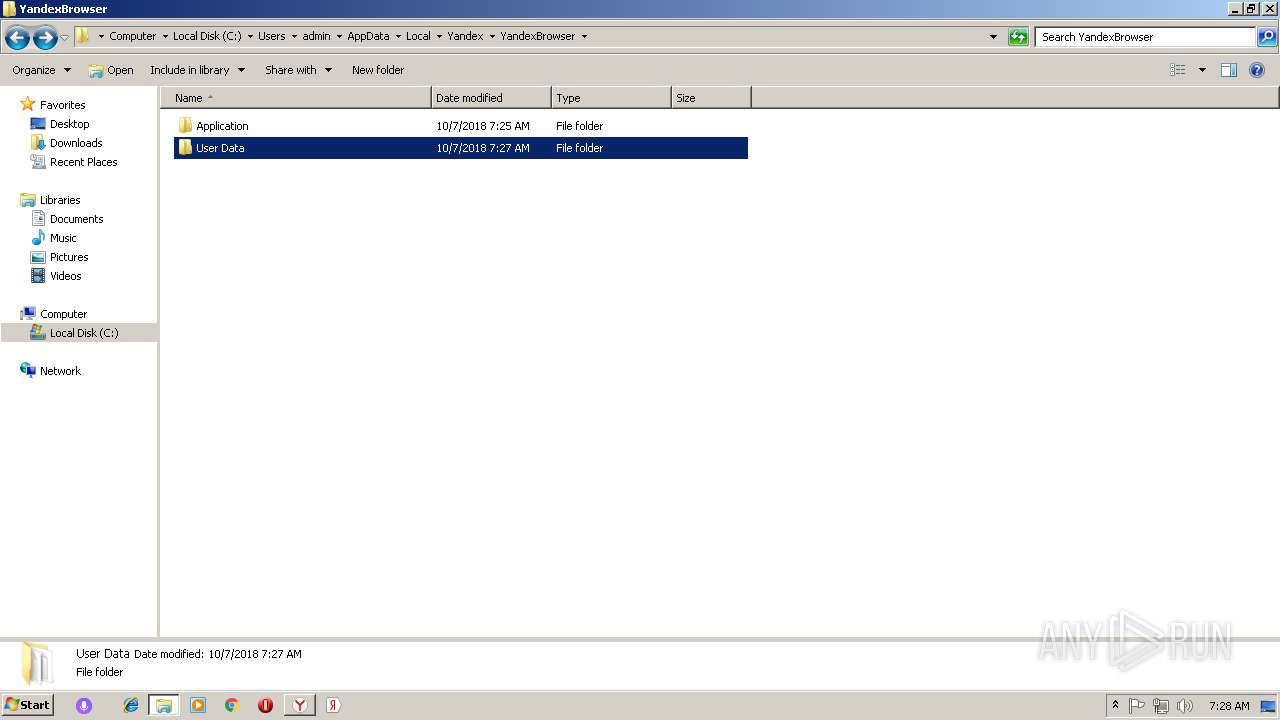
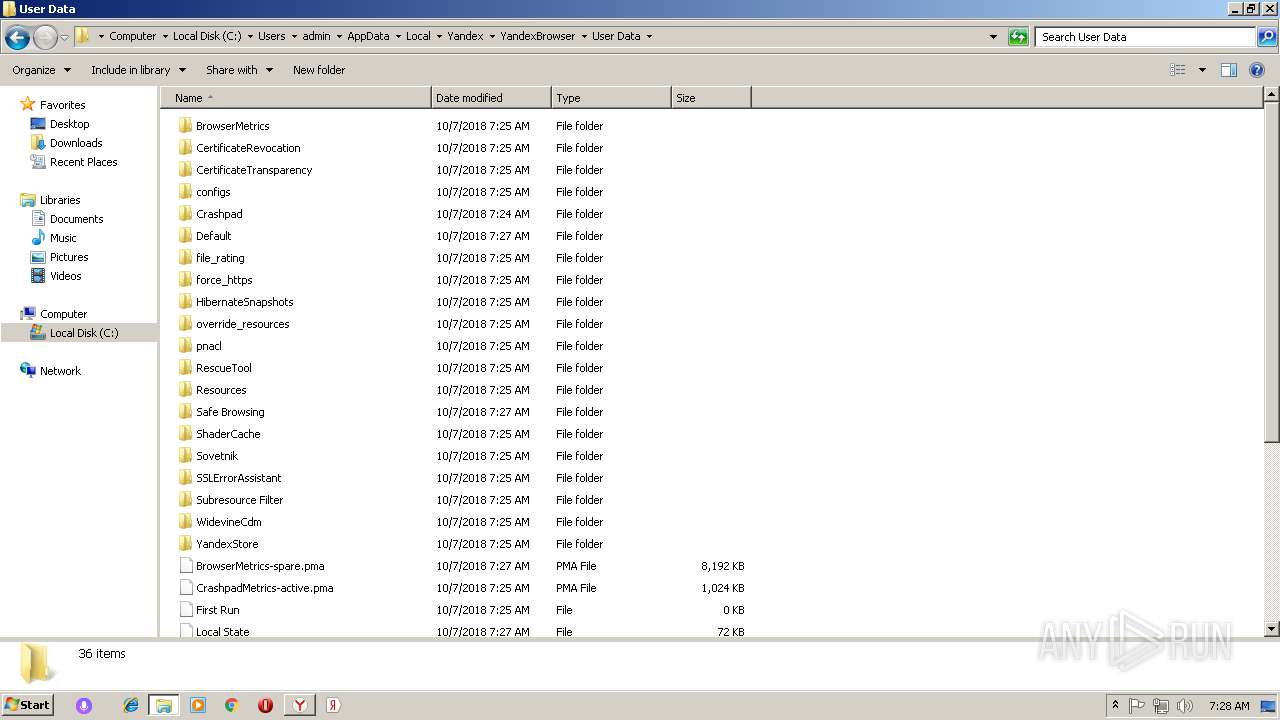
Creates files in the user directory
- Yandex.exe (PID: 3028)
- setup.exe (PID: 2668)
- clidmgr.exe (PID: 3196)
- Yandex__.exe (PID: 2652)
- MsiExec.exe (PID: 1820)
- msiexec.exe (PID: 1192)
- notepad++.exe (PID: 2196)
Starts application with an unusual extension
- Yandex.exe (PID: 3428)
Application launched itself
- setup.exe (PID: 676)
- Yandex.exe (PID: 3028)
- service_update.exe (PID: 3212)
- browser.exe (PID: 1320)
- searchbandapp.exe (PID: 3788)
Creates a software uninstall entry
- setup.exe (PID: 2668)
- Yandex__.exe (PID: 2652)
Reads Internet Cache Settings
- searchbandapp.exe (PID: 2820)
- Yandex.exe (PID: 3028)
- explorer.exe (PID: 1604)
- setup.exe (PID: 2668)
Changes IE settings (feature browser emulation)
- searchbandapp.exe (PID: 3788)
Removes files from Windows directory
- service_update.exe (PID: 3180)
Adds / modifies Windows certificates
- setup.exe (PID: 2668)
- service_update.exe (PID: 3180)
Modifies the open verb of a shell class
- setup.exe (PID: 2668)
INFO
Application launched itself
- msiexec.exe (PID: 1192)
Dropped object may contain Bitcoin addresses
- searchbandapp.exe (PID: 2820)
- explorer.exe (PID: 1604)
- setup.exe (PID: 2668)
Creates a software uninstall entry
- msiexec.exe (PID: 1192)
Reads settings of System Certificates
- explorer.exe (PID: 1604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:26 20:08:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 335872 |
| InitializedDataSize: | 910336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32eb4 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
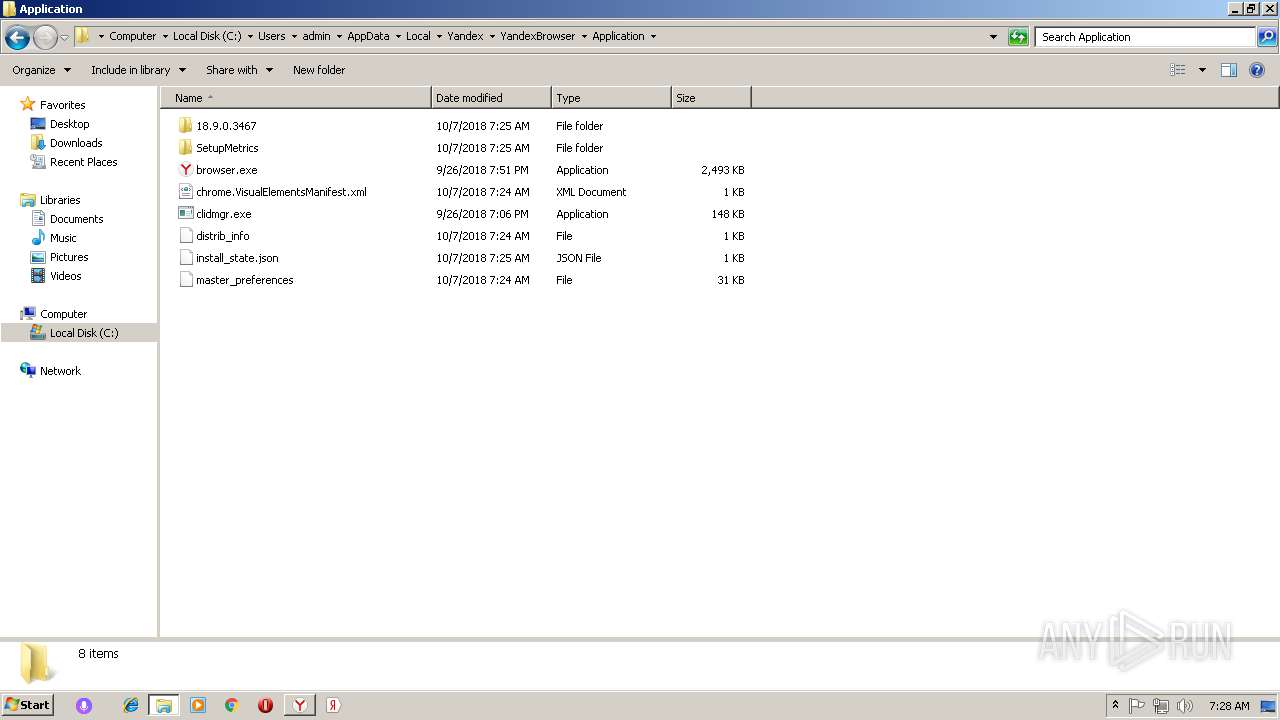
| FileVersionNumber: | 18.9.0.3467 |
| ProductVersionNumber: | 18.9.0.3467 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | YANDEX LLC |
| FileDescription: | Yandex |
| FileVersion: | 18.9.0.3467 |
| InternalName: | lite_installer |
| LegalCopyright: | Copyright (c) 2012-2018 YANDEX LLC. All Rights Reserved. |
| ProductName: | Yandex |
| ProductVersion: | 18.9.0.3467 |
| ProductChromiumVersion: | 68.0.3440.106 |
| ProductYandexVersion: | 18.9.0.3467 |
| CompanyShortName: | YANDEX LLC |
| ProductShortName: | Yandex Installer |
| LastChange: | 0c6b3ad6e5f976cfa306f8c13f2ae966cef49245 |
| OfficialBuild: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Sep-2018 18:08:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | YANDEX LLC |
| FileDescription: | Yandex |
| FileVersion: | 18.9.0.3467 |
| InternalName: | lite_installer |
| LegalCopyright: | Copyright (c) 2012-2018 YANDEX LLC. All Rights Reserved. |
| ProductName: | Yandex |
| ProductVersion: | 18.9.0.3467 |
| ProductChromiumVersion: | 68.0.3440.106 |
| ProductYandexVersion: | 18.9.0.3467 |
| CompanyShortName: | YANDEX LLC |
| ProductShortName: | Yandex Installer |
| LastChange: | 0c6b3ad6e5f976cfa306f8c13f2ae966cef49245 |
| Official Build: | 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 26-Sep-2018 18:08:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00051E27 | 0x00052000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64554 |
.rdata | 0x00053000 | 0x000156E4 | 0x00015800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87367 |
.data | 0x00069000 | 0x00002174 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.52446 |
.00cfg | 0x0006C000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
SHARED | 0x0006E000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
Shared | 0x0006F000 | 0x00000E48 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00070000 | 0x000C2748 | 0x000C2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.91527 |
.reloc | 0x00133000 | 0x00003BB8 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6936 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1744 | 2002 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.44702 | 9832 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.58339 | 4392 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.56164 | 2488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.80269 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
26 | 3.34409 | 1120 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
27 | 3.2916 | 1356 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
28 | 3.17352 | 580 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
128 | 2.68263 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
129 | 2.07664 | 406 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
Imports
GDI32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
99
Monitored processes
50
Malicious processes
16
Suspicious processes
15
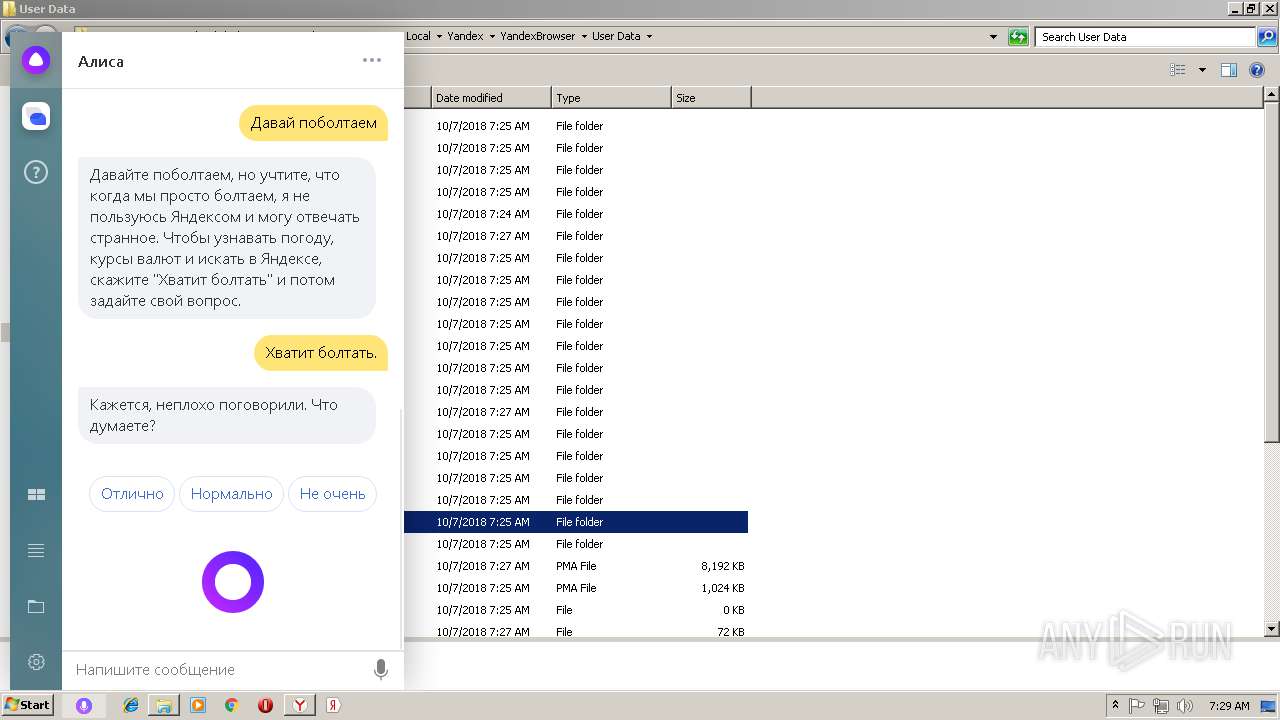
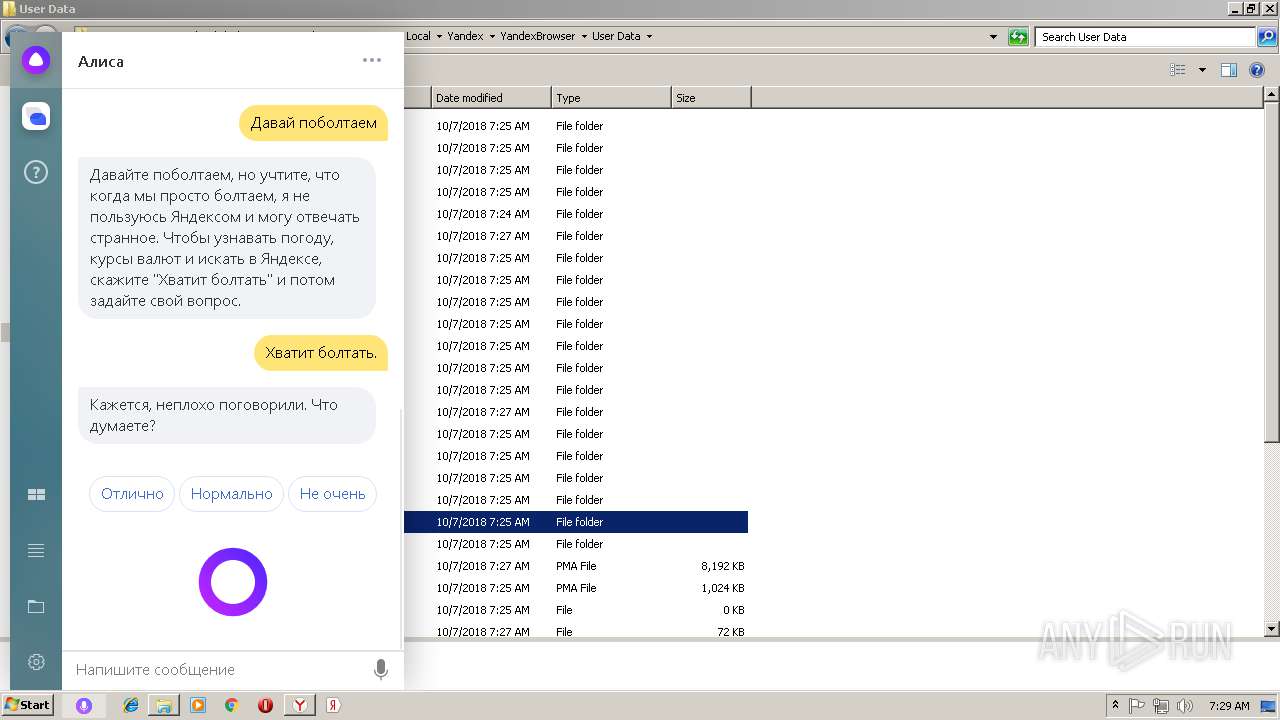
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=utility --field-trial-handle=908,3547791434410764324,8194390457306819597,131072 --lang=ru --no-sandbox --user-id=95027FBC-05EA-40EC-8111-84676100FE2E --brand-id=yandex --partner-id=portal-switch --service-request-channel-token=7CD39624B2086596FAF0537B05B4A173 --process-name="Импорт профилей" --mojo-platform-channel-handle=3184 /prefetch:8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 18.9.0.3467 Modules
| |||||||||||||||
| 624 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=renderer --enable-in-process-wmf-demuxer --field-trial-handle=908,3547791434410764324,8194390457306819597,131072 --js-flags="--no-enable-liveedit --stack-trace-limit=1" --service-pipe-token=BD634A8551E9B5B38BB210DB8FE11CB8 --lang=ru --user-id=95027FBC-05EA-40EC-8111-84676100FE2E --brand-id=yandex --partner-id=portal-switch --help-url=https://api.browser.yandex.ru/redirect/help/ --user-agent-info --translate-security-origin=https://translate.yandex.net --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-instaserp --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BD634A8551E9B5B38BB210DB8FE11CB8 --renderer-client-id=7 --mojo-platform-channel-handle=2968 /prefetch:1 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 18.9.0.3467 Modules
| |||||||||||||||
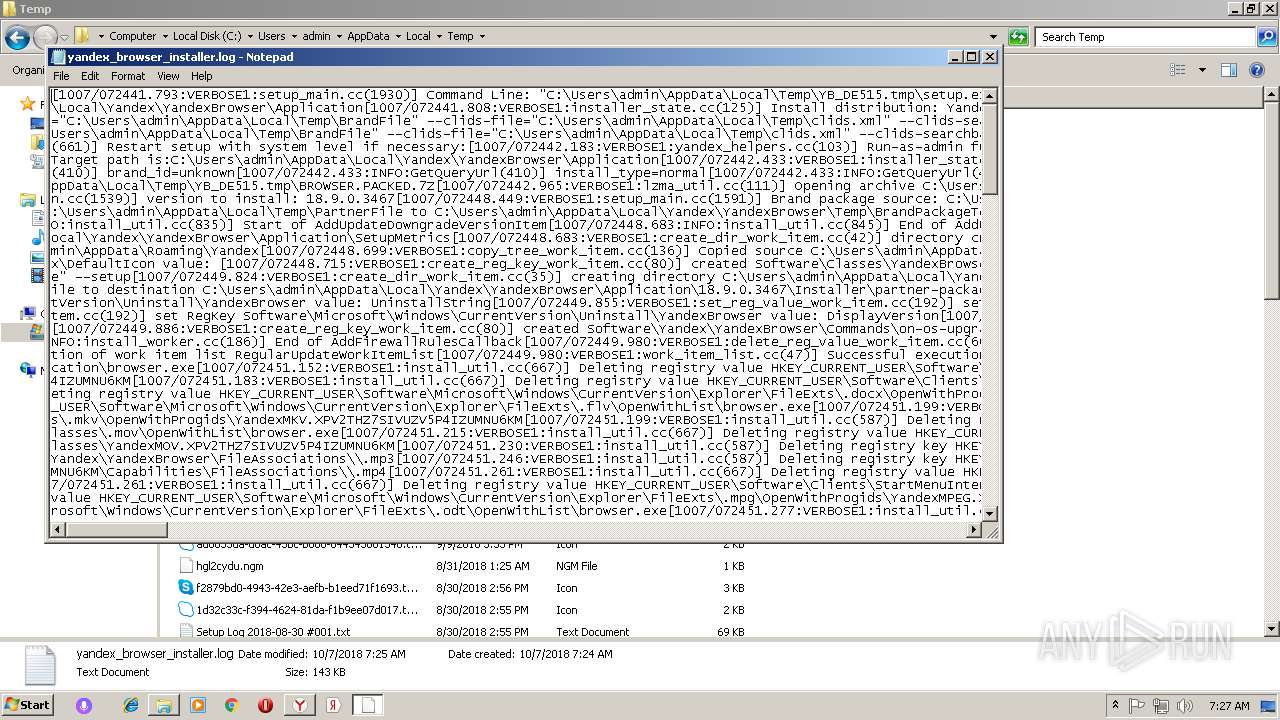
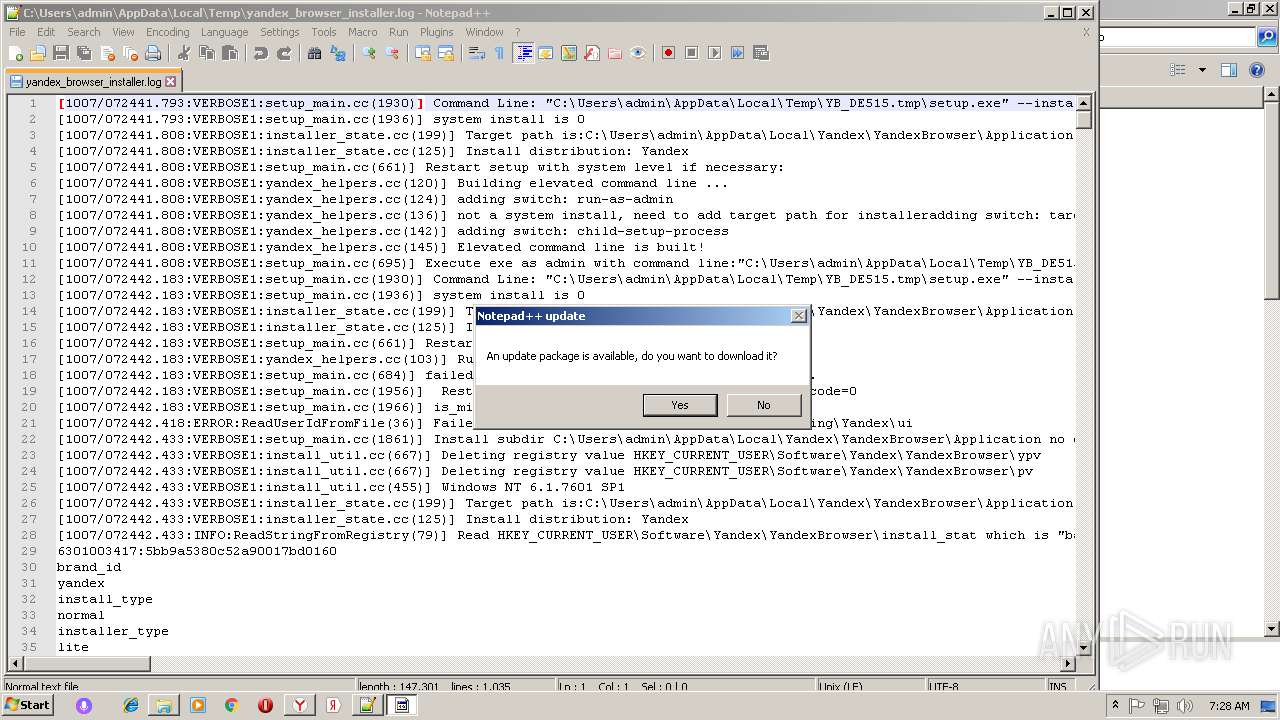
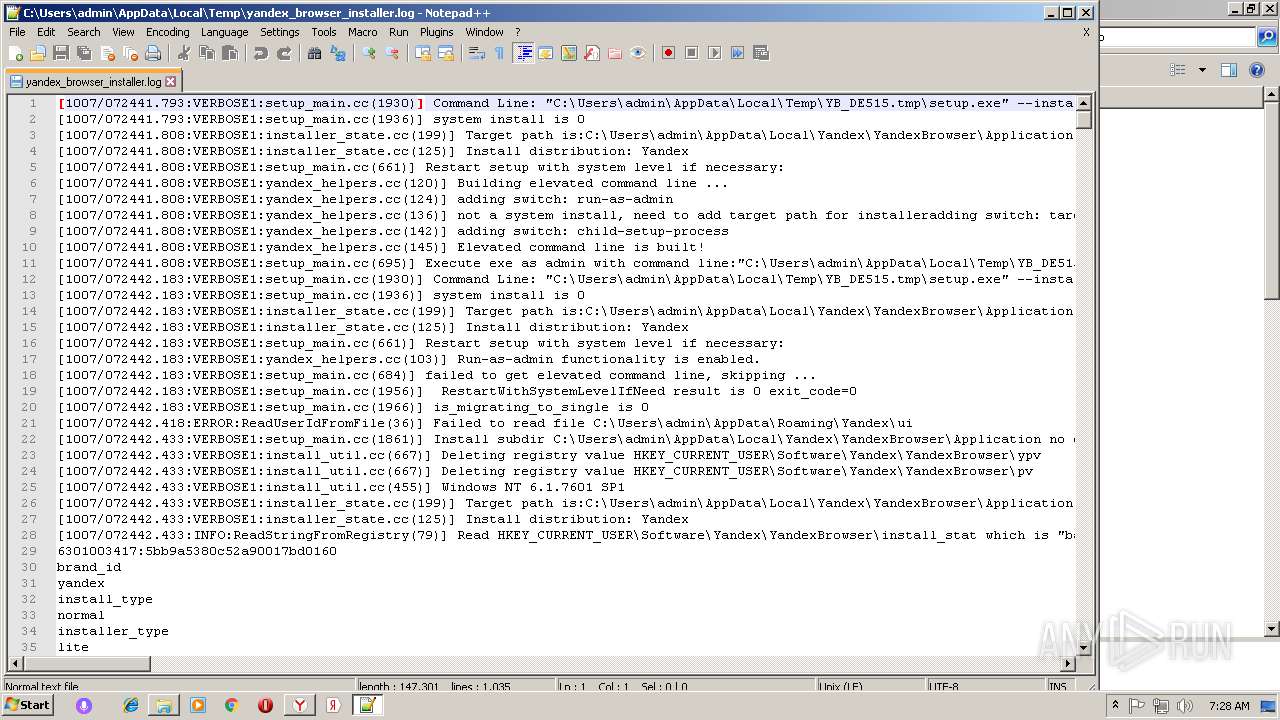
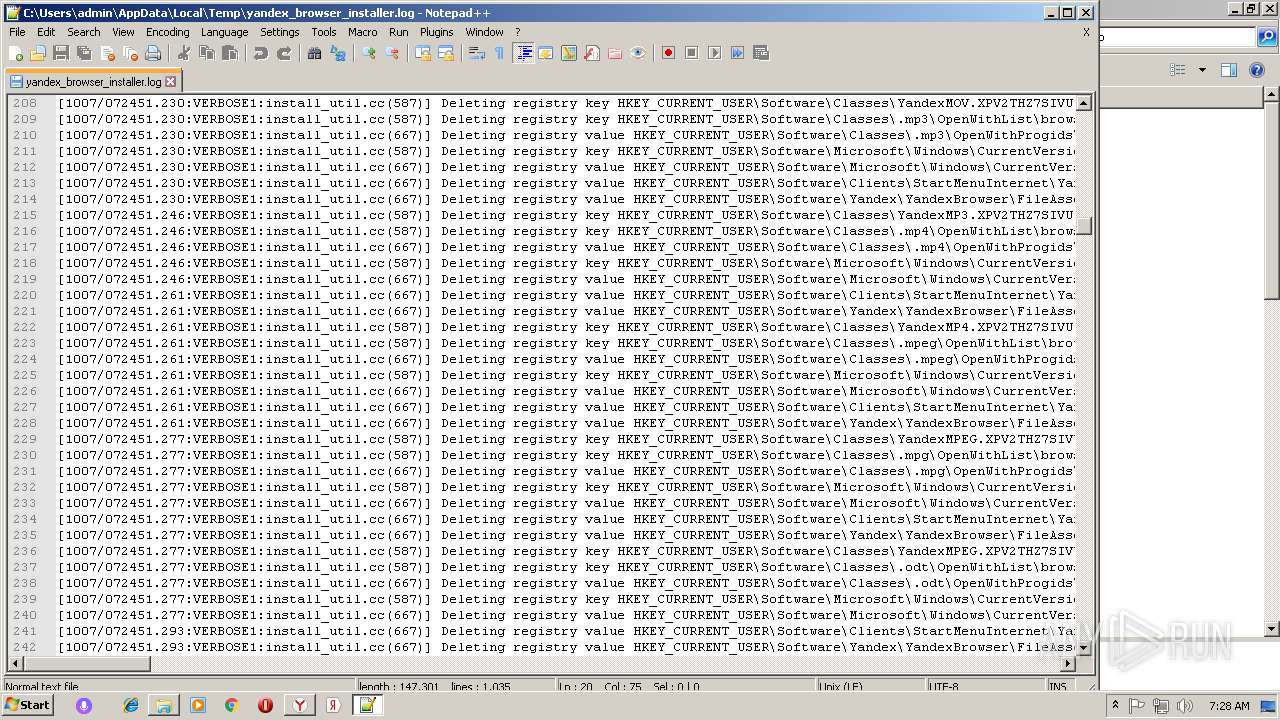
| 676 | "C:\Users\admin\AppData\Local\Temp\YB_DE515.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\YB_DE515.tmp\BROWSER.PACKED.7Z" --searchband-file="C:\Users\admin\AppData\Local\Temp\YB_DE515.tmp\SEARCHBAND.EXE" --brand-name=yandex --brand-package="C:\Users\admin\AppData\Local\Temp\BrandFile" --clids-file="C:\Users\admin\AppData\Local\Temp\clids.xml" --clids-searchband-file="C:\Users\admin\AppData\Local\Temp\clids_searchband.xml" --distr-info-file="C:\Users\admin\AppData\Local\Temp\distrib_info" --installerdata="C:\Users\admin\AppData\Local\Temp\master_preferences" --ok-button-pressed-time=6041637695 --partner-package="C:\Users\admin\AppData\Local\Temp\PartnerFile" --progress-window=525648 --send-statistics --source=lite --spawned_in_protected_dir --verbose-logging | C:\Users\admin\AppData\Local\Temp\YB_DE515.tmp\setup.exe | — | yb1D7B.tmp | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: HIGH Description: Yandex Exit code: 1 Version: 18.9.0.3467 Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=renderer --enable-in-process-wmf-demuxer --field-trial-handle=908,3547791434410764324,8194390457306819597,131072 --js-flags="--no-enable-liveedit --stack-trace-limit=1" --service-pipe-token=4DC9DF35141F5B35B1C43DFD52044FCA --lang=ru --user-id=95027FBC-05EA-40EC-8111-84676100FE2E --brand-id=yandex --partner-id=portal-switch --help-url=https://api.browser.yandex.ru/redirect/help/ --user-agent-info --translate-security-origin=https://translate.yandex.net --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-instaserp --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4DC9DF35141F5B35B1C43DFD52044FCA --renderer-client-id=9 --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 18.9.0.3467 Modules
| |||||||||||||||
| 1192 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1320 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --progress-window=525648 --ok-button-pressed-time=6041637695 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | explorer.exe | ||||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 18.9.0.3467 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Yandex\YandexBrowser\18.9.0.3467\service_update.exe" --update-background-scheduler | C:\Program Files\Yandex\YandexBrowser\18.9.0.3467\service_update.exe | — | service_update.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 18.9.0.3467 Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | C:\Users\admin\AppData\Local\Yandex\SearchBand\Application\4.6.0.1790\crashreporter.exe | C:\Users\admin\AppData\Local\Yandex\SearchBand\Application\4.6.0.1790\crashreporter.exe | — | searchbandapp.exe | |||||||||||
User: admin Company: Yandex LLC Integrity Level: MEDIUM Description: Voice assistant Exit code: 0 Version: 4.6.0.1790 Modules
| |||||||||||||||
| 1820 | C:\Windows\system32\MsiExec.exe -Embedding D9A0A4F1E97E320033C1290F41B17DA7 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 885
Read events
9 438
Write events
4 394
Delete events
53
Modification events
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | DistribInfoParams |
Value: win10pin=1&browser=Firefox/64/62.0&banerid=6301003417:5bb9a5380c52a90017bd0160&exp_yapin2=1&pps=installID%3D6126647871500139013_1538893124596&yandexuid=6126647871500139013&download_date=1538893124 | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | lang |
Value: ru | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | InstallerData |
Value: C:\Users\admin\AppData\Local\Temp\master_preferences | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | ClidsFile |
Value: C:\Users\admin\AppData\Local\Temp\clids.xml | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | ClidsSearchbandFile |
Value: C:\Users\admin\AppData\Local\Temp\clids_searchband.xml | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | brand |
Value: yandex | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | BrandFile |
Value: C:\Users\admin\AppData\Local\Temp\BrandFile | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | PartnerFile |
Value: C:\Users\admin\AppData\Local\Temp\PartnerFile | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Yandex_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3028) Yandex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Yandex_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
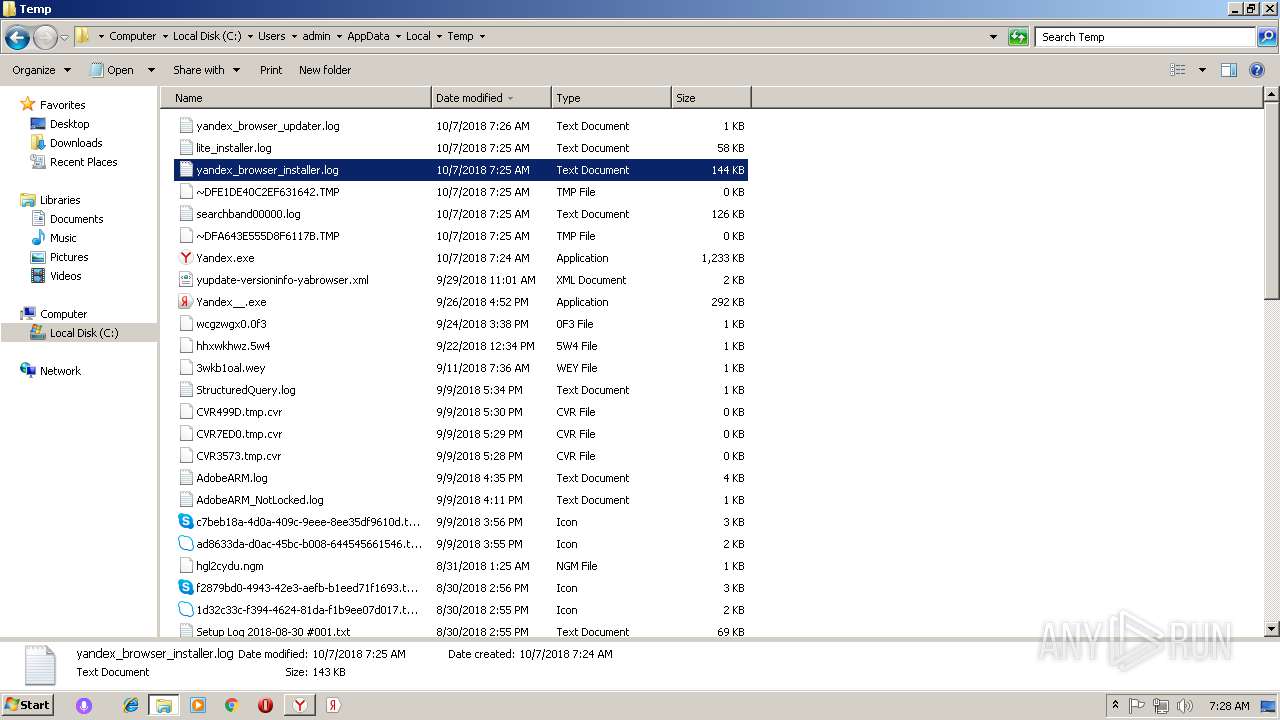
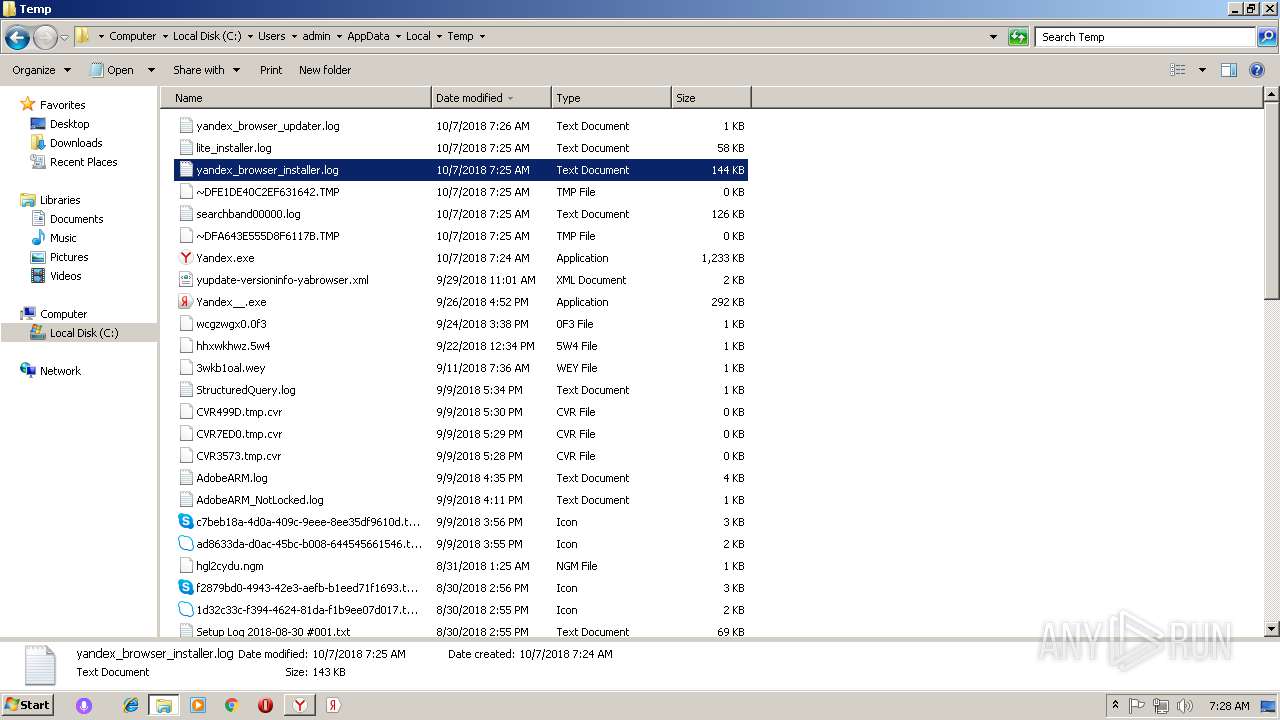
Executable files
38
Suspicious files
118
Text files
714
Unknown types
85
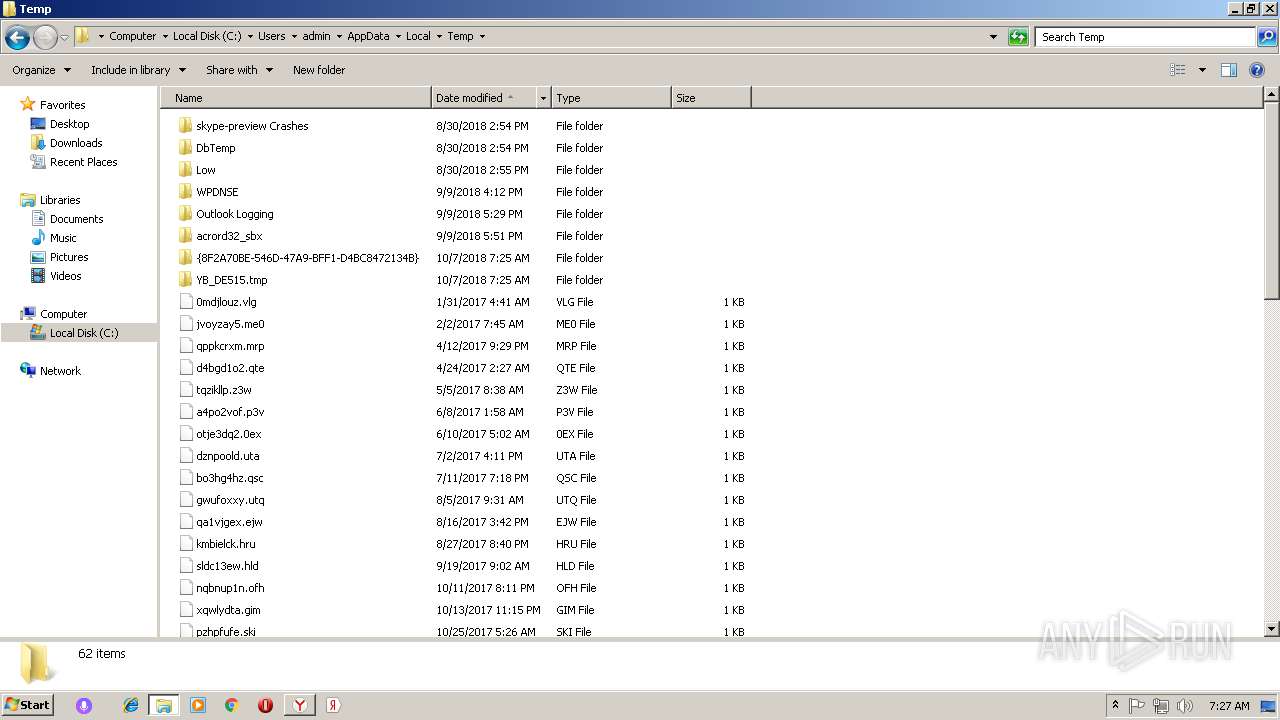
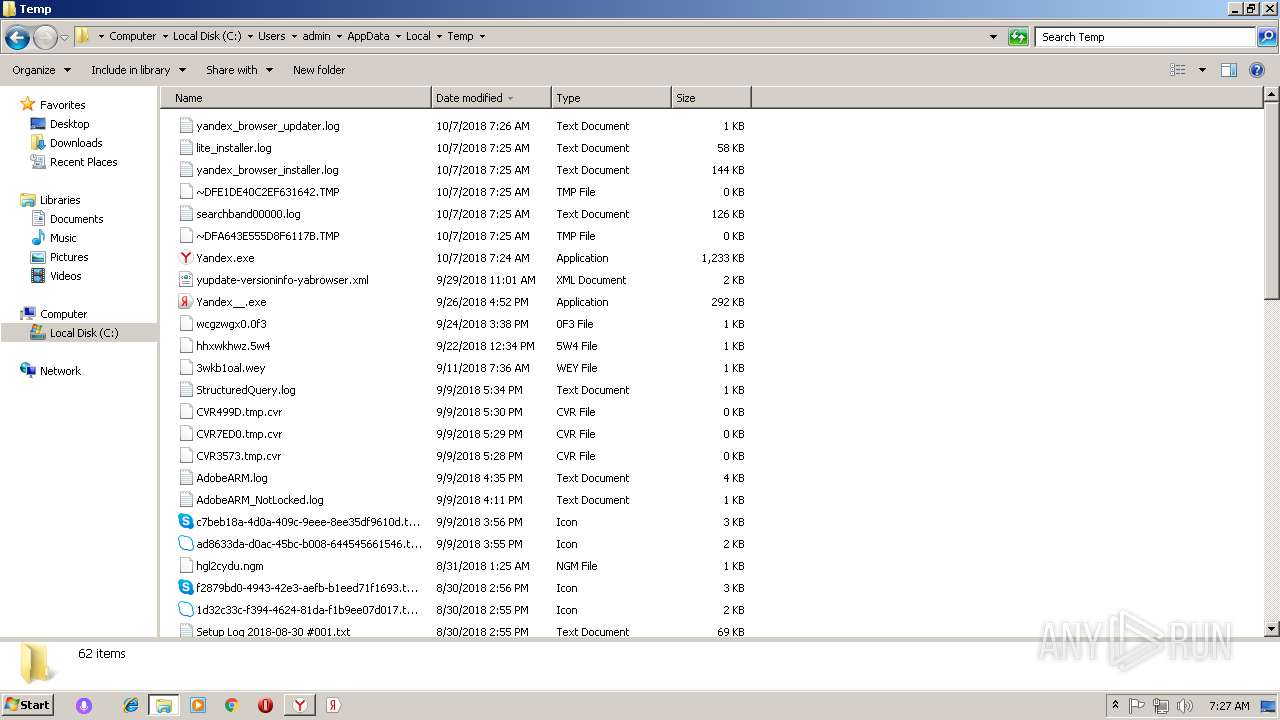
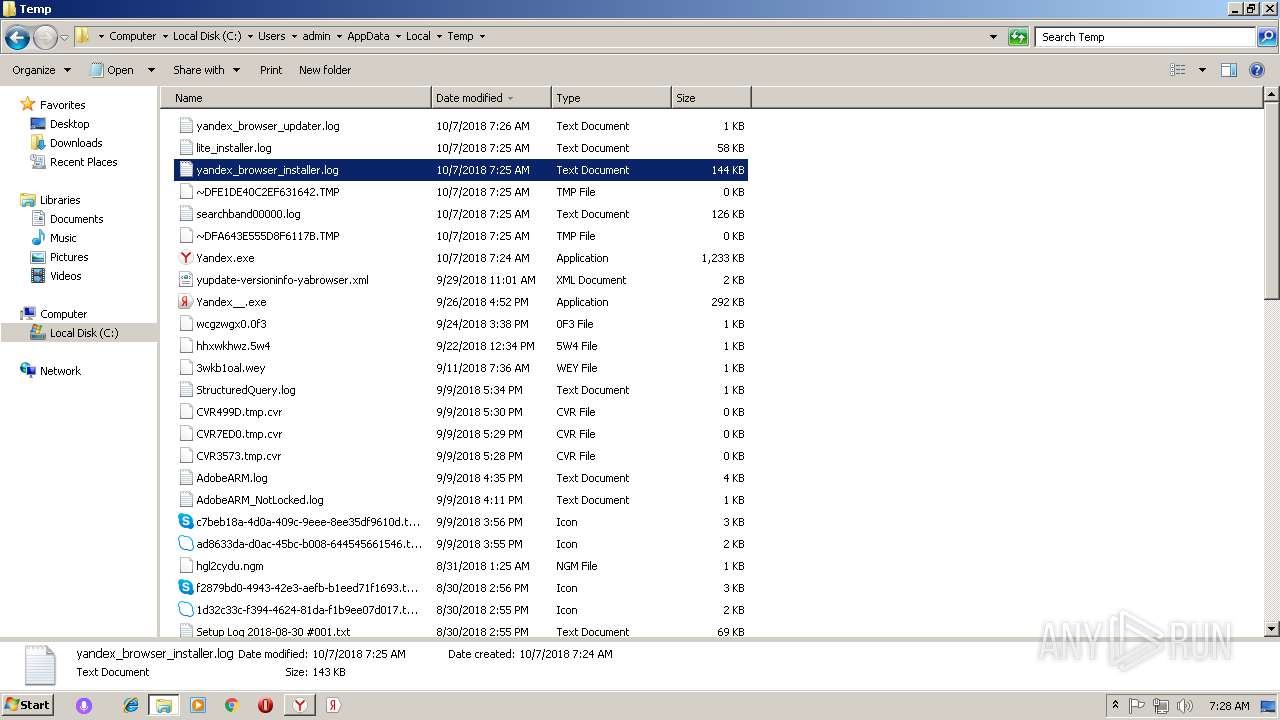
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\PartnerFile | compressed | |
MD5:— | SHA256:— | |||
| 3440 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\3440_3830\Yandex.exe | executable | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\BrandFile | compressed | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\distrib_info | text | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@yandex[1].txt | text | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\clids_searchband.xml | xml | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\04[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\master_preferences | text | |
MD5:— | SHA256:— | |||
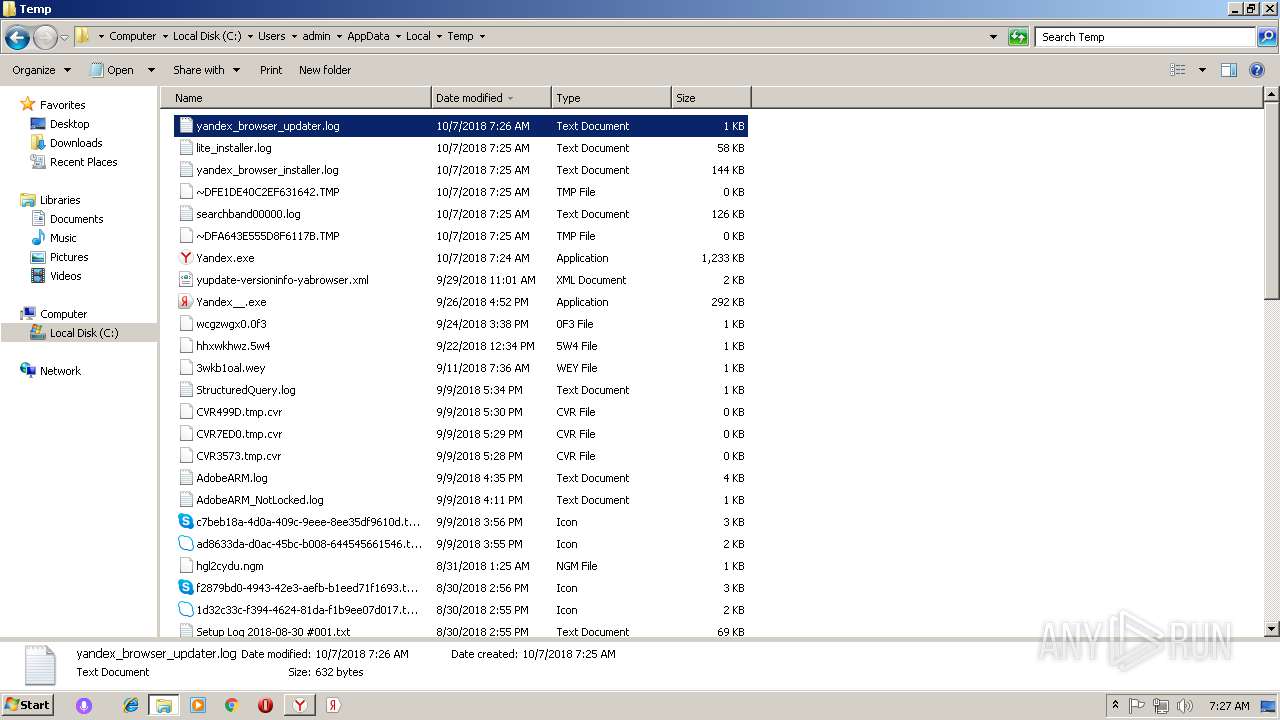
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\lite_installer.log | text | |
MD5:— | SHA256:— | |||
| 3028 | Yandex.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\02[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
9
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | Yandex.exe | GET | 302 | 5.45.205.235:80 | http://download.cdn.yandex.net/browser/portal-switch/browser-setup.arc | RU | — | — | whitelisted |
3028 | Yandex.exe | GET | — | 5.45.205.221:80 | http://cache-man01i.cdn.yandex.net/download.cdn.yandex.net/browser/portal-switch/browser-setup.arc | RU | — | — | whitelisted |
3028 | Yandex.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/gscodesigng3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTHTu2Y6Nr%2FMkfa3PrlxnwonnIpxQQUs9Pm1XFWfTlYs3jSK7j3oR%2F9S5sCDGUxOJI7m%2BYpSWV%2FXQ%3D%3D | US | der | 1.49 Kb | whitelisted |
3028 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.net/root.crl | US | der | 782 b | whitelisted |
3028 | Yandex.exe | GET | 200 | 151.101.2.133:80 | http://crl.globalsign.com/gs/gstimestampingg2.crl | US | der | 905 b | whitelisted |
3028 | Yandex.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkfDD%2F78IrsoD5b%2Bp1JR | US | der | 1.48 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | Yandex.exe | 87.250.251.82:443 | api.browser.yandex.ru | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 5.45.205.235:80 | download.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 5.45.205.221:80 | cache-man01i.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 87.250.250.14:443 | clck.yandex.ru | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 5.45.205.235:443 | download.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 5.45.205.221:443 | cache-man01i.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 151.101.2.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
3028 | Yandex.exe | 87.250.250.55:443 | storage.ape.yandex.net | YANDEX LLC | RU | whitelisted |
3028 | Yandex.exe | 104.18.21.226:80 | crl.globalsign.net | Cloudflare Inc | US | shared |
2668 | setup.exe | 87.250.251.82:443 | api.browser.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.browser.yandex.ru |
| whitelisted |
download.cdn.yandex.net |
| whitelisted |
cache-man01i.cdn.yandex.net |
| whitelisted |
clck.yandex.ru |
| whitelisted |
storage.ape.yandex.net |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
crl.globalsign.net |
| whitelisted |
crl.globalsign.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3028 | Yandex.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1604 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
1604 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
1604 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
Process | Message |
|---|---|
Yandex__.exe | GetLoggedUserSid(): szUserName = admin, szDomain = PC, dwSessionId = 1
|
Yandex__.exe | GetLoggedUserSid(): user sid is found: S-1-5-21-1302019708-1500728564-335382590-1000
|
Yandex__.exe | GetRunData() : run as user SID = S-1-5-21-1302019708-1500728564-335382590-1000
|
Yandex__.exe | Process runs normally, i.e. under a logged user
|
Yandex__.exe | SwitchRegistry() In |
Yandex__.exe | SwitchRegistry() Out |
Yandex__.exe | GetTaskBarDirPath() : Call GetUserSpecDirPath() |
Yandex__.exe | GetUserSpecDirPath(1, bTakeAsIs = 0) res = C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar.
|
Yandex__.exe | GetPinnedSiteFiles(): cand. szFilePath = C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\yandex.website, szURL = https://www.yandex.ru/?clid=2175661 |
Yandex__.exe | is selected as ours.
|