| File name: | lgs504_x64.exe |
| Full analysis: | https://app.any.run/tasks/a265848e-b907-4fd9-94ea-9d13357075d6 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2020, 07:22:01 |
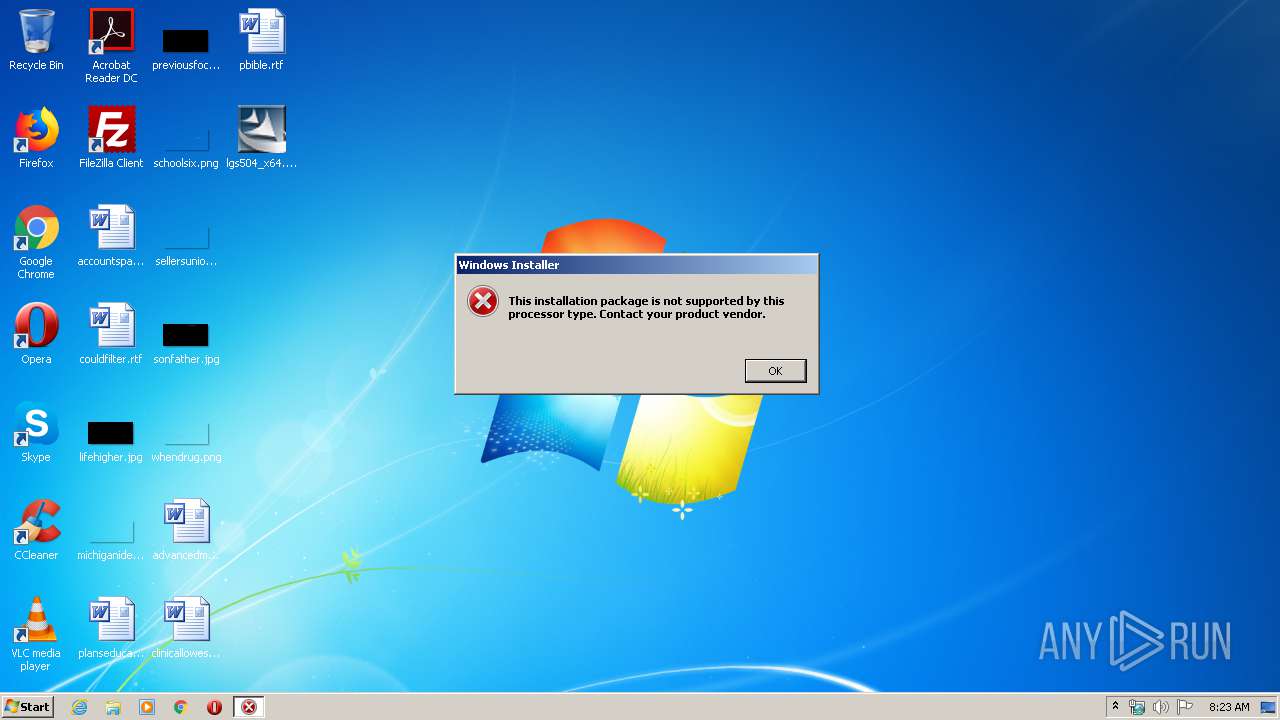
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | EE02A6B03FD2F7E16CA45297FE448EF8 |
| SHA1: | 736062F98A6F196711ADB69F3CC2C7A61B85ADAE |
| SHA256: | 40ED0569165702FBBC3A40A610ECE7C29CD795543461A3029CC32DECD61B78E1 |
| SSDEEP: | 196608:MHxkcVN6ZC155//W161VHKloe6Bz/IZPNkDLAvjLEKjwNH0kqOqyFOO2h4AZpWUj:IksX55+Q1VUoFi1kDLGLNcNsO26AmI |
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 3028)
Actions looks like stealing of personal data
- lgs504_x64.exe (PID: 2052)
SUSPICIOUS
Executable content was dropped or overwritten
- lgs504_x64.exe (PID: 2052)
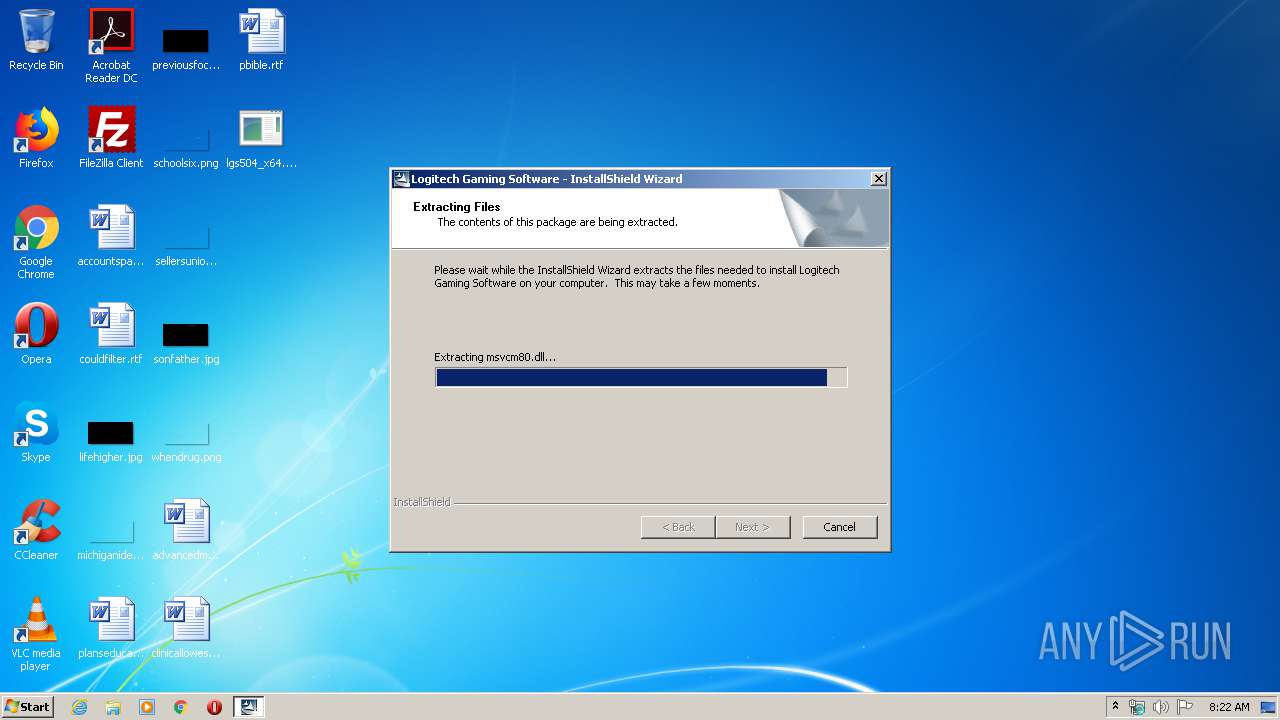
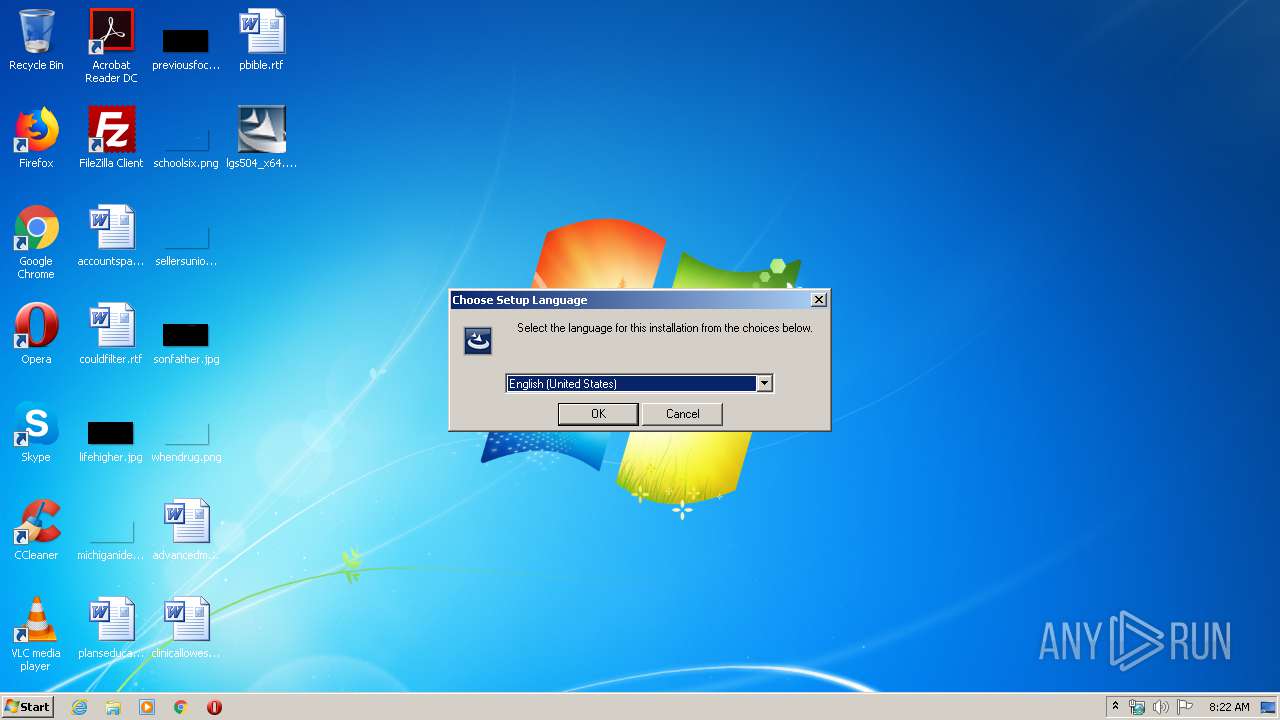
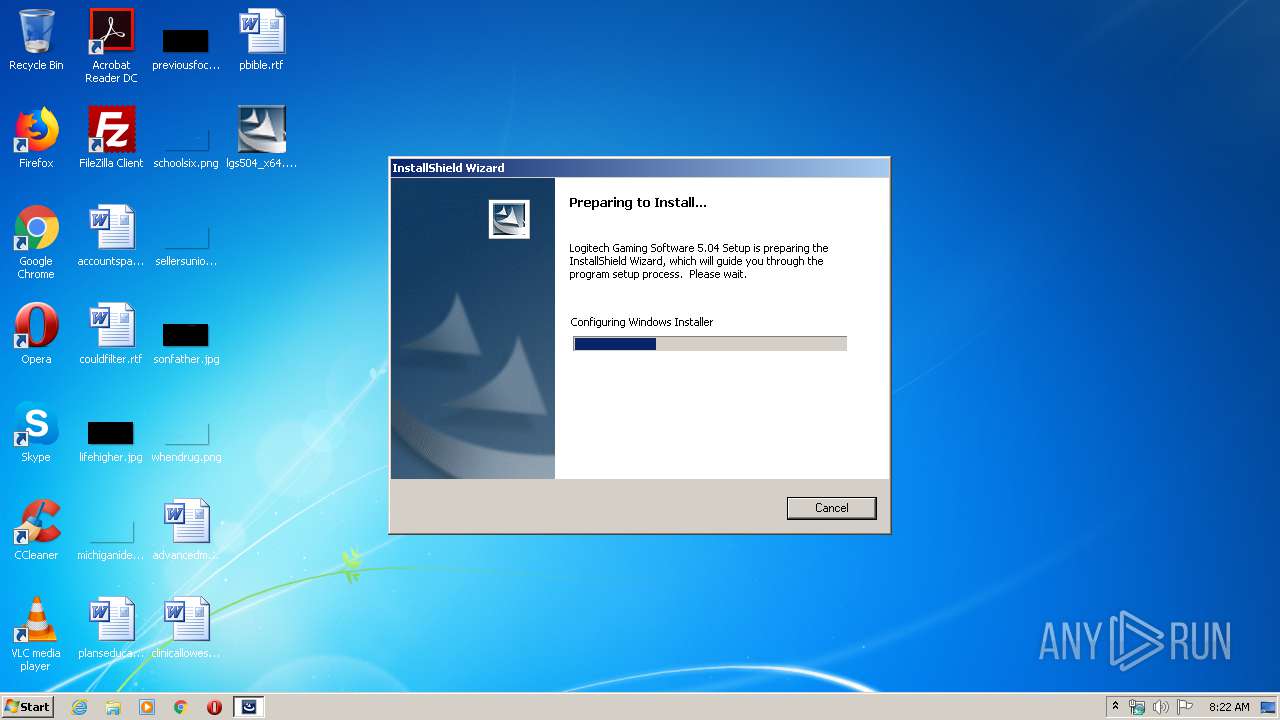
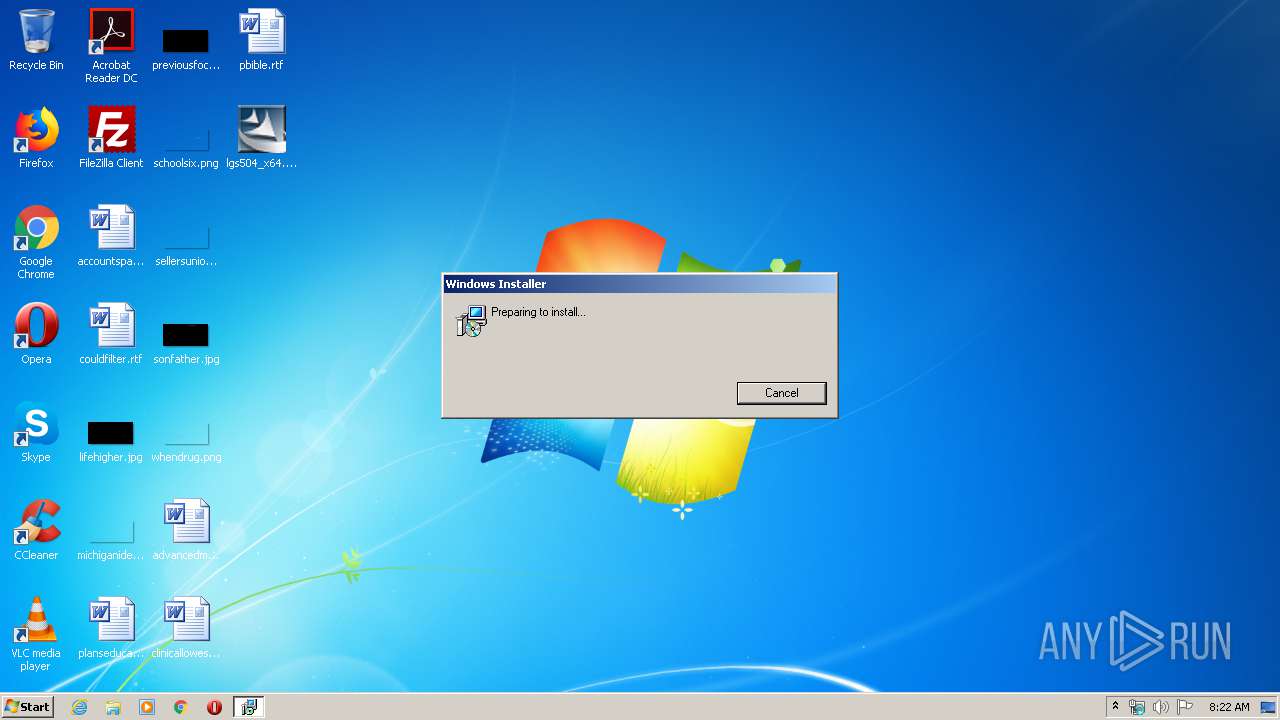
Starts Microsoft Installer
- setup.exe (PID: 3028)
Creates files in the program directory
- lgs504_x64.exe (PID: 2052)
INFO
Dropped object may contain Bitcoin addresses
- lgs504_x64.exe (PID: 2052)
Reads settings of System Certificates
- MSIEXEC.EXE (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:08:02 09:01:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 77824 |
| InitializedDataSize: | 208896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8af7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.100.1332 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | |
| CompanyName: | Logitech |
| FileDescription: | |
| InternalName: | stub32 |
| OriginalFileName: | stub32i.exe |
| FileVersion: | 5.04 |
| LegalCopyright: | |
| ProductName: | Logitech Gaming Software |
| ProductVersion: | 5.04 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2002 07:01:18 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Logitech |
| FileDescription: | - |
| InternalName: | stub32 |
| OriginalFilename: | stub32i.exe |
| FileVersion: | 5.04 |
| LegalCopyright: | - |
| ProductName: | Logitech Gaming Software |
| ProductVersion: | 5.04 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Aug-2002 07:01:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012436 | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53609 |
.rdata | 0x00014000 | 0x000019B2 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8719 |
.data | 0x00016000 | 0x00006E64 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.35003 |
.rsrc | 0x0001D000 | 0x0002CC84 | 0x0002D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.04575 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.75048 | 443 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.39652 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.18406 | 424 | Latin 1 / Western European | English - United States | RT_STRING |
4 | 3.07096 | 282 | Latin 1 / Western European | English - United States | RT_STRING |
19 | 2.86832 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
20 | 3.28952 | 870 | Latin 1 / Western European | English - United States | RT_STRING |
21 | 2.89596 | 152 | Latin 1 / Western European | English - United States | RT_STRING |
103 | 2.64576 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
118 | 7.04133 | 154530 | Latin 1 / Western European | English - United States | RT_BITMAP |
132 | 4.04914 | 14564 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
SHELL32.dll |
USER32.dll |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Users\admin\Desktop\lgs504_x64.exe" | C:\Users\admin\Desktop\lgs504_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Logitech Integrity Level: MEDIUM Description: Exit code: 1633 Version: 5.04 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\pft8696.tmp\setup.exe" | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\setup.exe | — | lgs504_x64.exe | |||||||||||
User: admin Company: Logitech Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 1633 Version: 5.04.110 Modules
| |||||||||||||||
| 3172 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\pft8696.tmp\LGSInst.msi" /L*v C:\Users\admin\AppData\Local\Temp\LGSInst.log TRANSFORMS="1033.MST" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\pft8696.tmp" SETUPEXENAME="setup.exe" | C:\Windows\system32\MSIEXEC.EXE | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1633 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
43
Read events
33
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3172) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
66
Suspicious files
9
Text files
41
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\ext8675.tmp | — | |
MD5:— | SHA256:— | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\plf8674.tmp | text | |
MD5:CFAEC980A3639A6B33704C0DB20CB812 | SHA256:55023B00E2C2401272D0AD7B4B633814869483B6D939C5D4910E4FF18EEEEE6C | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\0x040b.ini | text | |
MD5:895F03FD4511DEA2D2463E415085B8C7 | SHA256:718D63EB79B400E473205754C09EEE02B9777C677805959BF2554E0CA383D89C | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\0x0404.ini | text | |
MD5:CBF701214E39516D60DF48852A4A3577 | SHA256:38FD1AC7CF1D6E8785189663E366EE01D712A95BFC69FE9ADBA8AE5DC9B682D9 | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\0x040c.ini | text | |
MD5:9A7BBBA91779895F36F8A3885E53FC10 | SHA256:B0D0743FCFEFE8D8817468930E7F766368C4384BC16F6D4FBB553F9A592D9320 | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\1032.mst | mst | |
MD5:— | SHA256:— | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\1030.mst | mst | |
MD5:— | SHA256:— | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\1031.mst | mst | |
MD5:— | SHA256:— | |||
| 2052 | lgs504_x64.exe | C:\Users\admin\AppData\Local\Temp\pft8696.tmp\1028.mst | mst | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3172 | MSIEXEC.EXE | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
3172 | MSIEXEC.EXE | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | MSIEXEC.EXE | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |