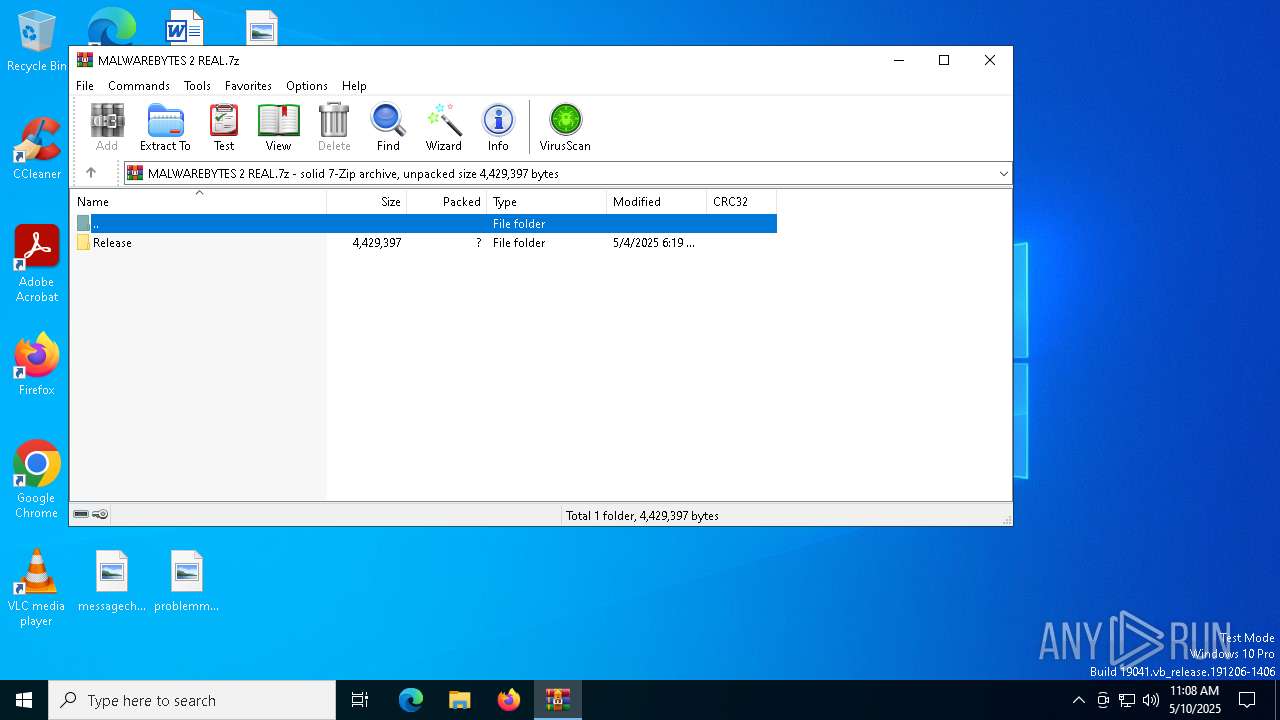
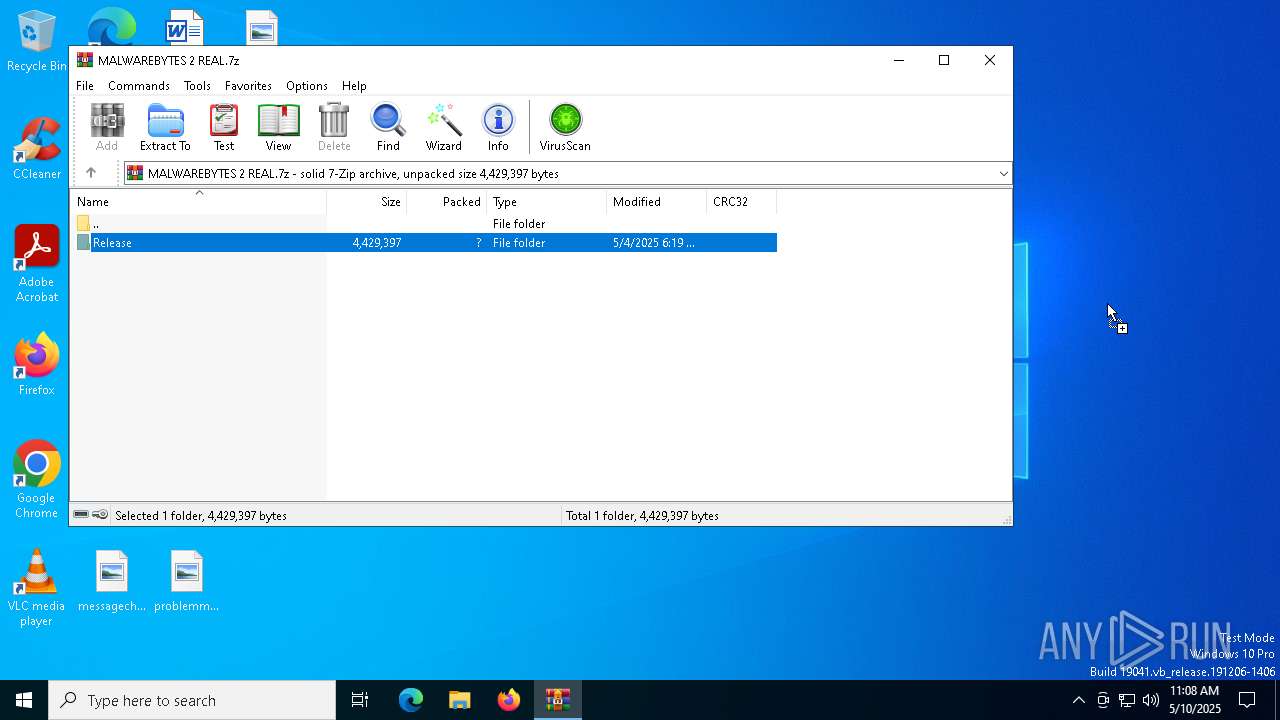
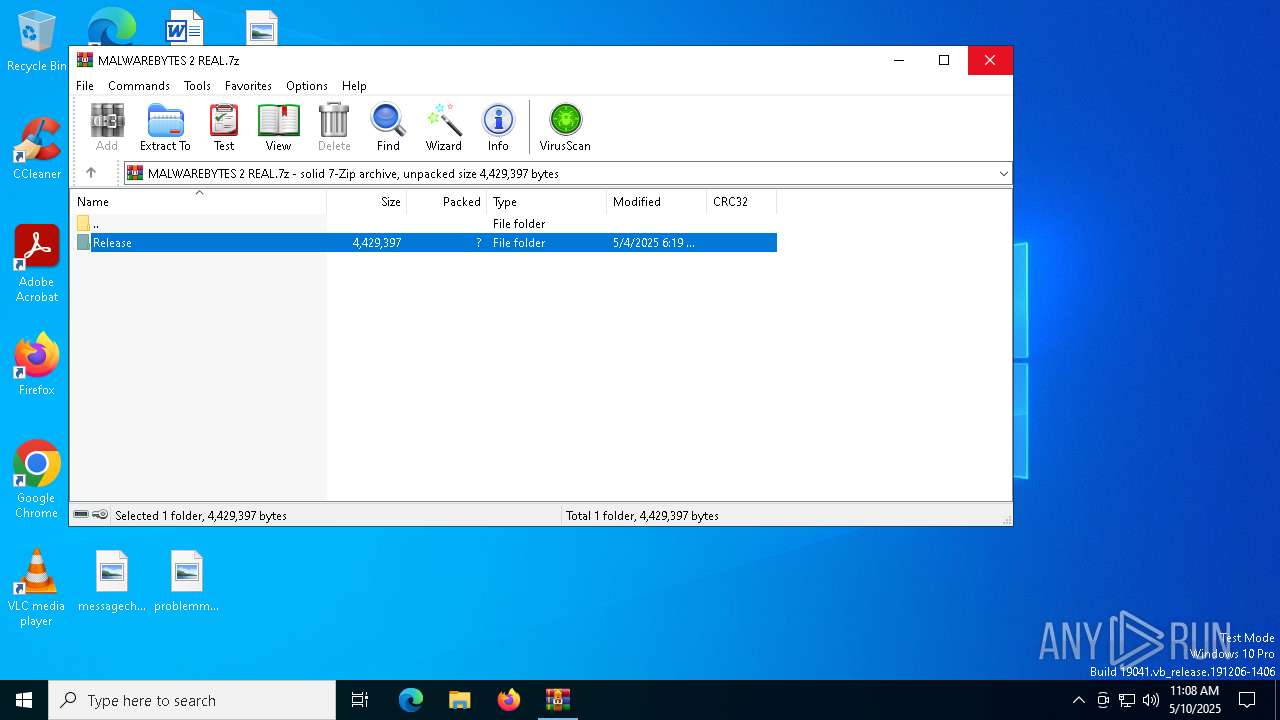
| File name: | MALWAREBYTES 2 REAL.7z |
| Full analysis: | https://app.any.run/tasks/734d1ba2-1407-4007-b093-64448593f6de |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 11:08:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | C863BDBE35966D070FEFE57EFA4A4432 |
| SHA1: | 3E72B91365815F966B25B1E759EA3F86127DAD84 |
| SHA256: | 40D6C9477FDEE105BBC2046D8160FDD8819F19876EE1A2C12A02CB683E001490 |
| SSDEEP: | 98304:YJrgQcnep6GIA0SbM8sU+PFeZdg3INfcsW26ESdRr+gnmfhVDkI+yAEdquBz8n77:KPnUvzkO |
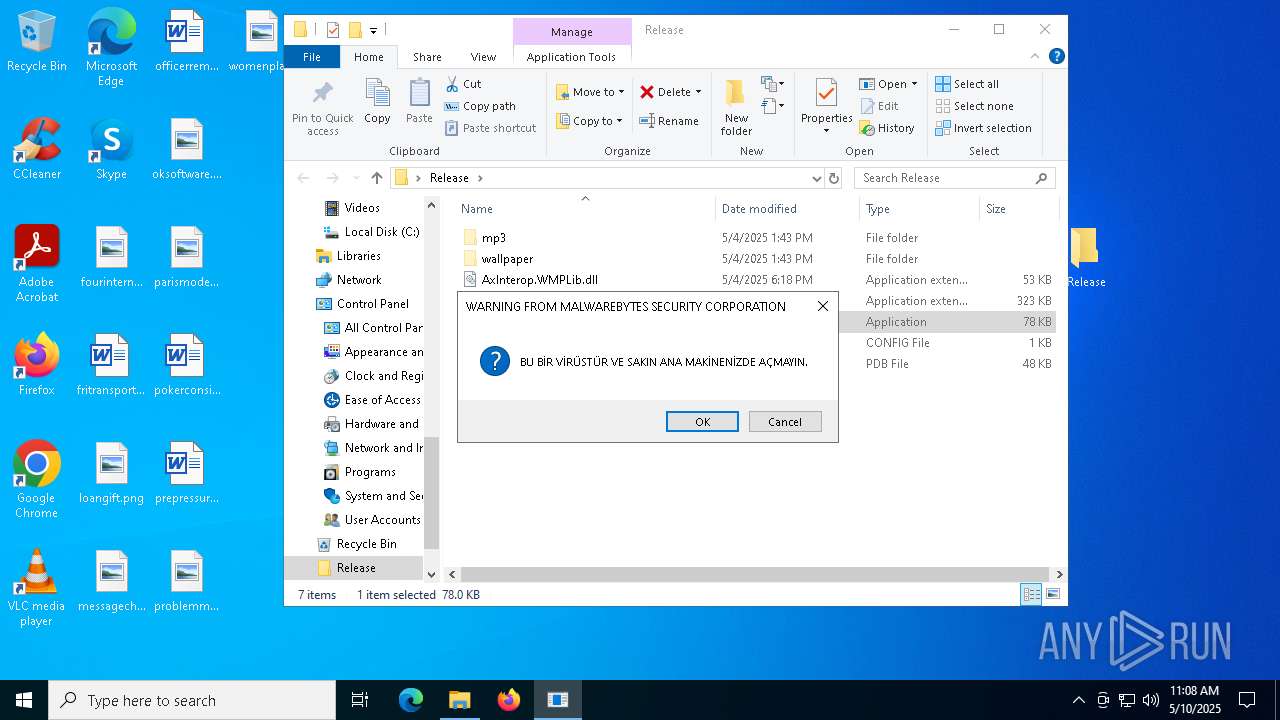
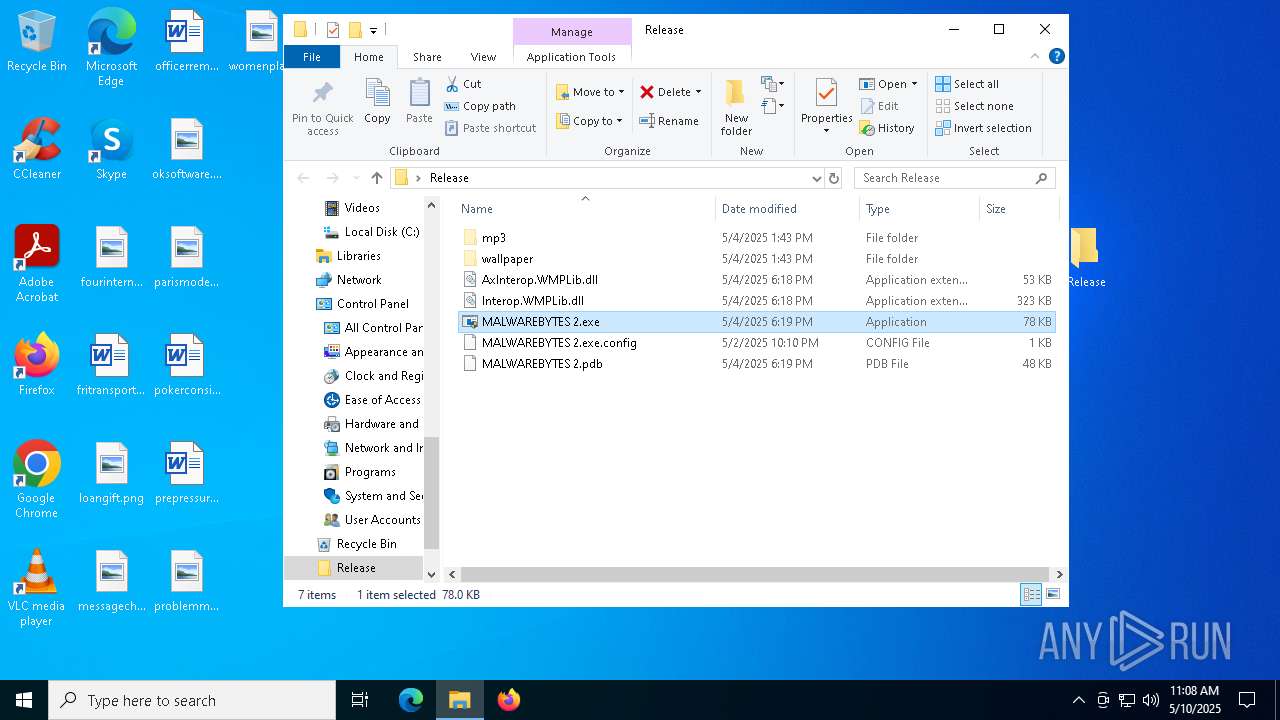
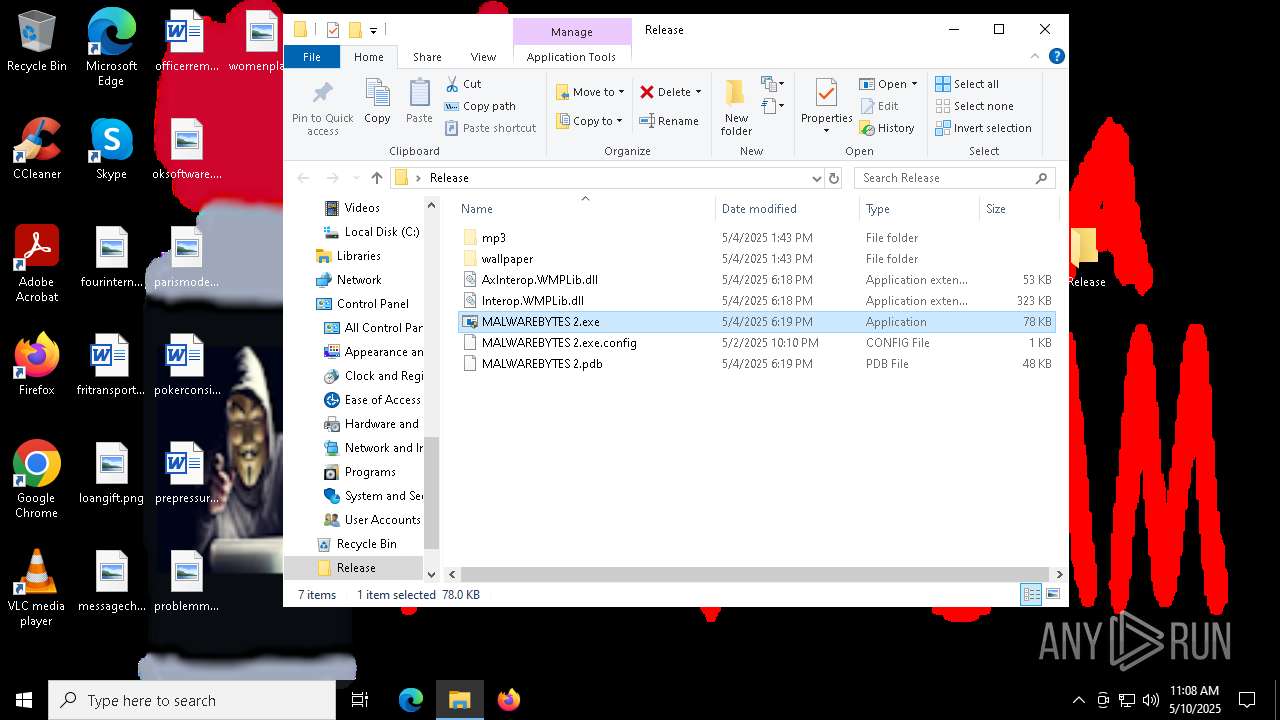
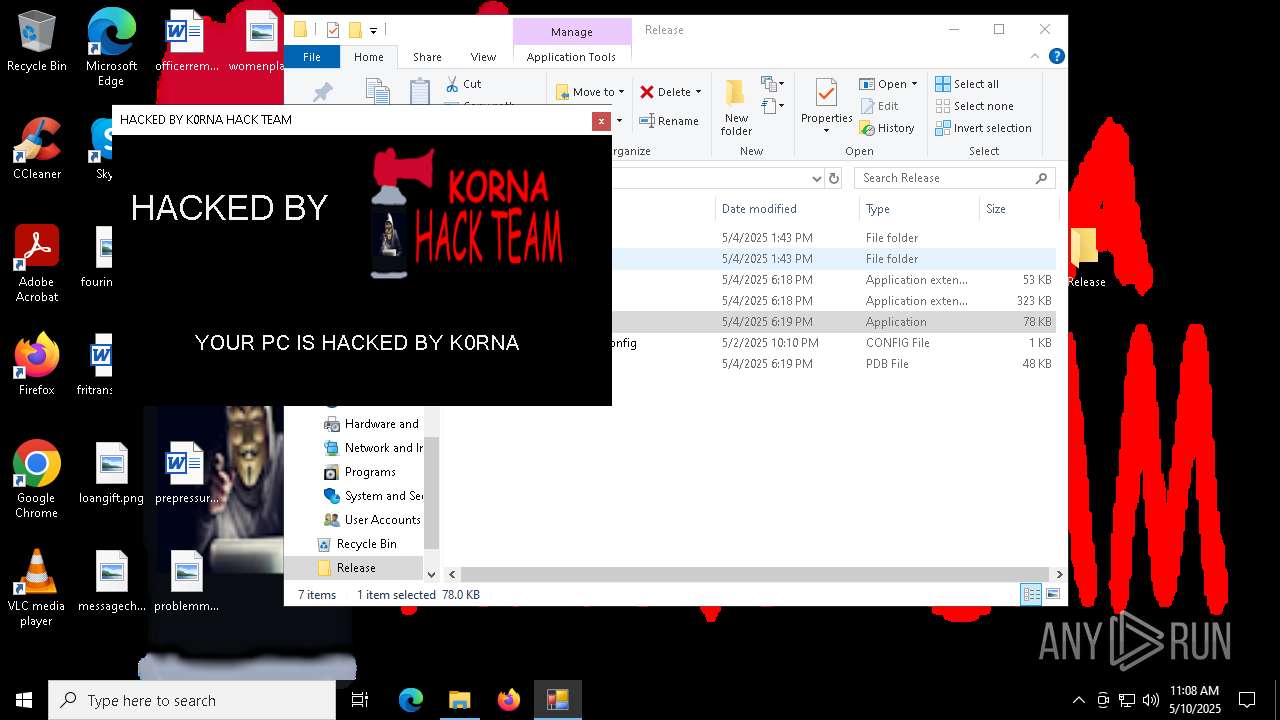
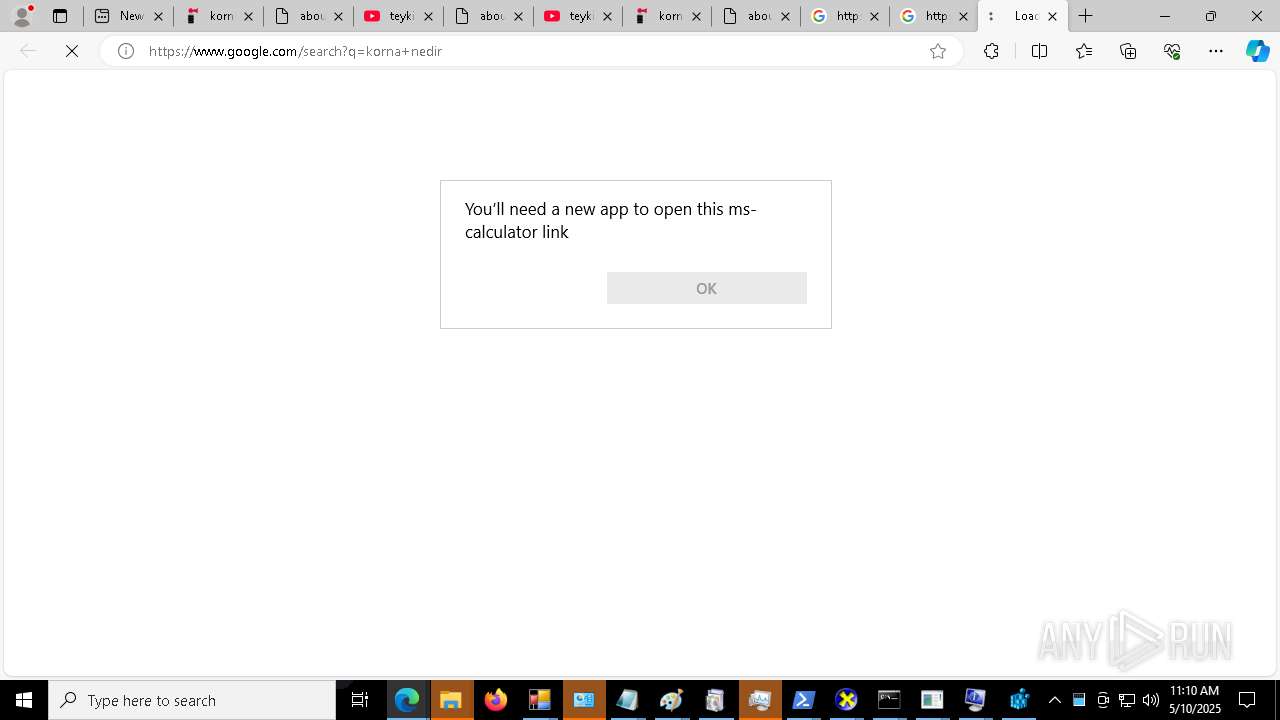
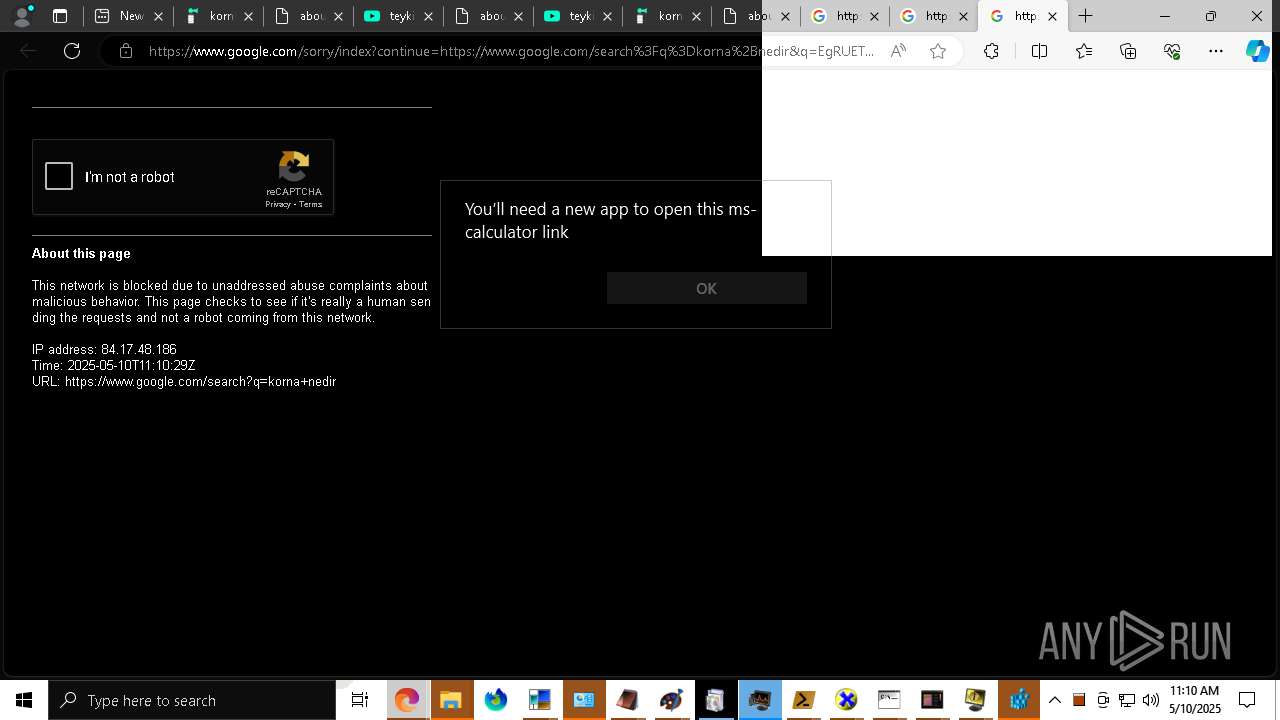
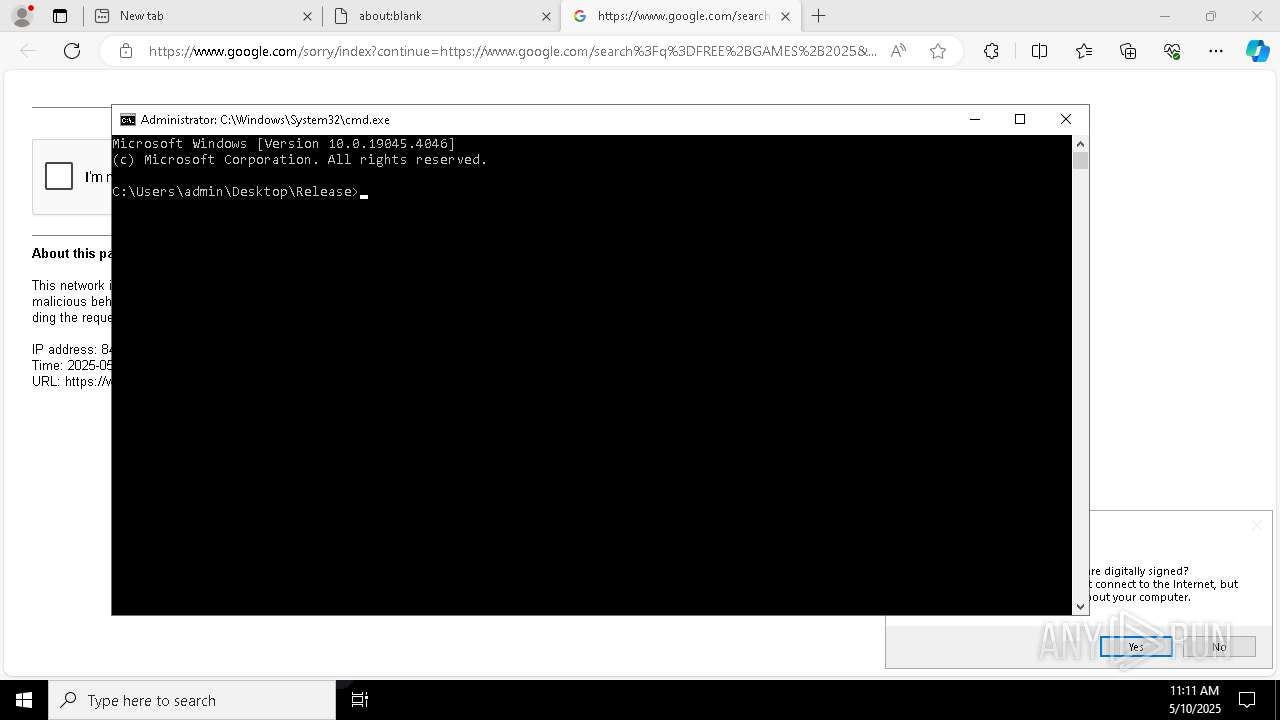
MALICIOUS
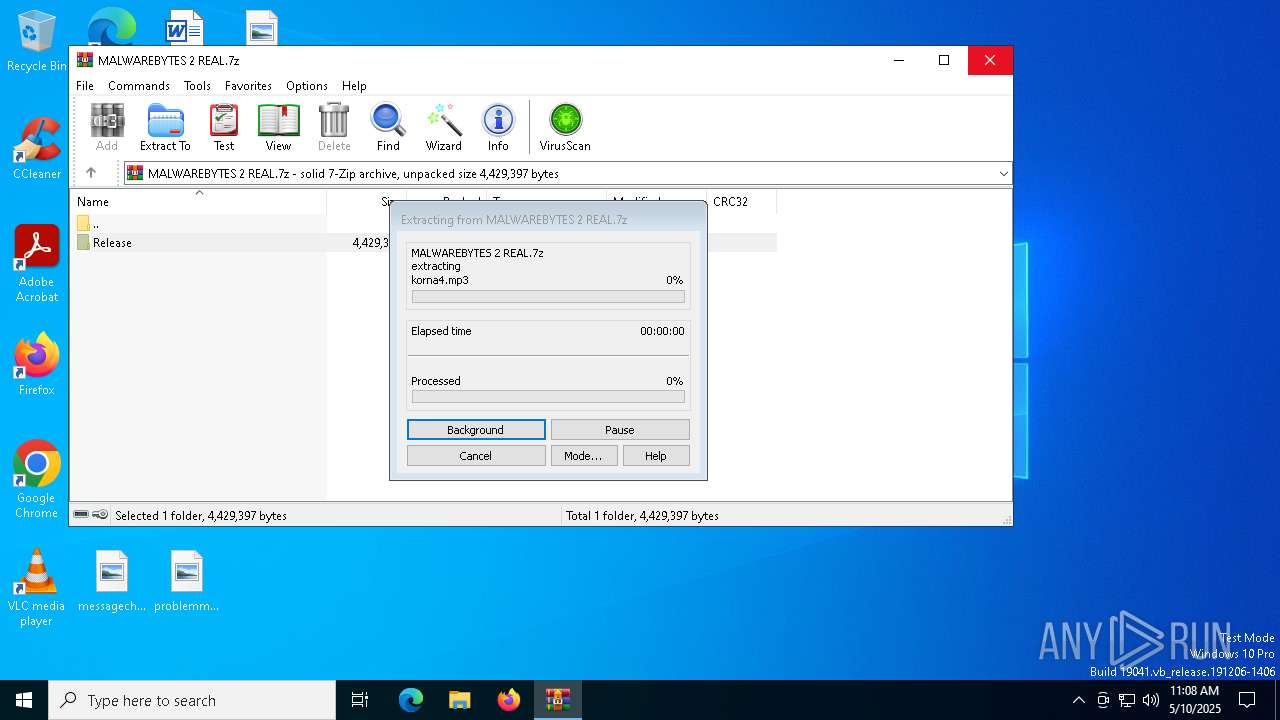
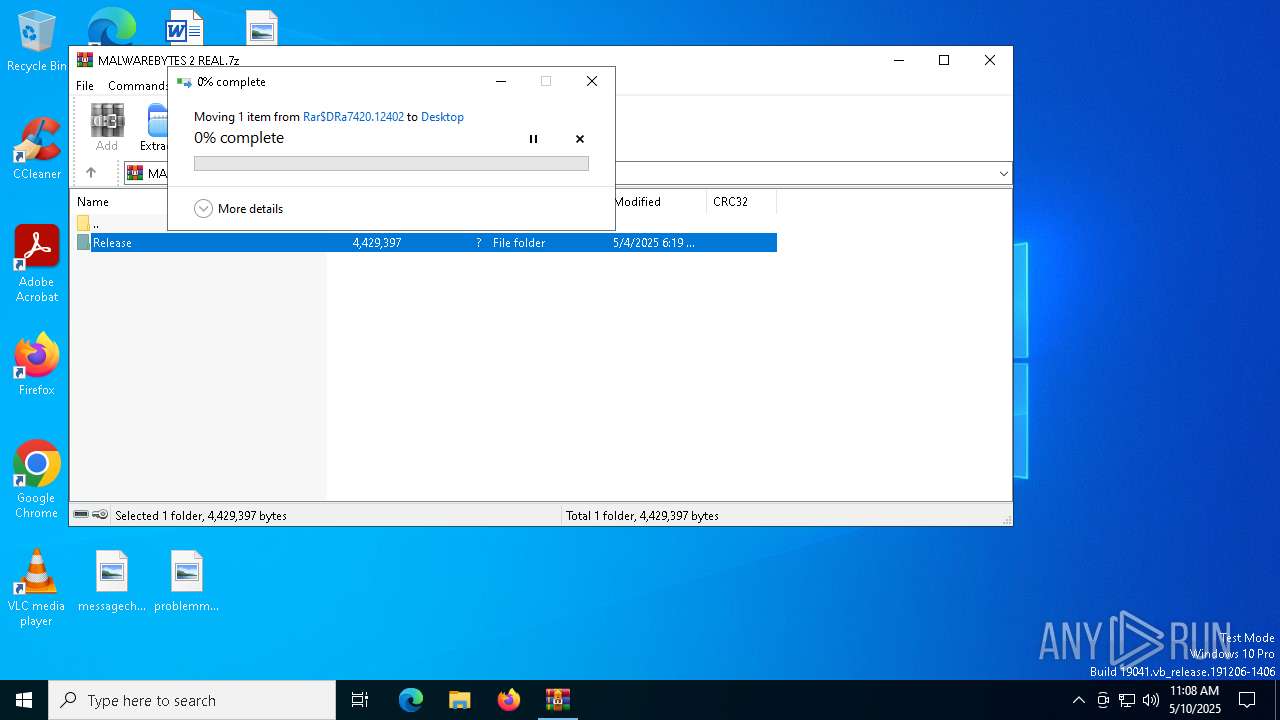
Generic archive extractor
- WinRAR.exe (PID: 7420)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 8180)
- net.exe (PID: 7324)
- net.exe (PID: 7740)
- net.exe (PID: 6620)
- net.exe (PID: 4608)
- net.exe (PID: 7052)
- MALWAREBYTES 2.exe (PID: 8112)
- net.exe (PID: 5436)
- net.exe (PID: 7204)
- net.exe (PID: 496)
- net.exe (PID: 7640)
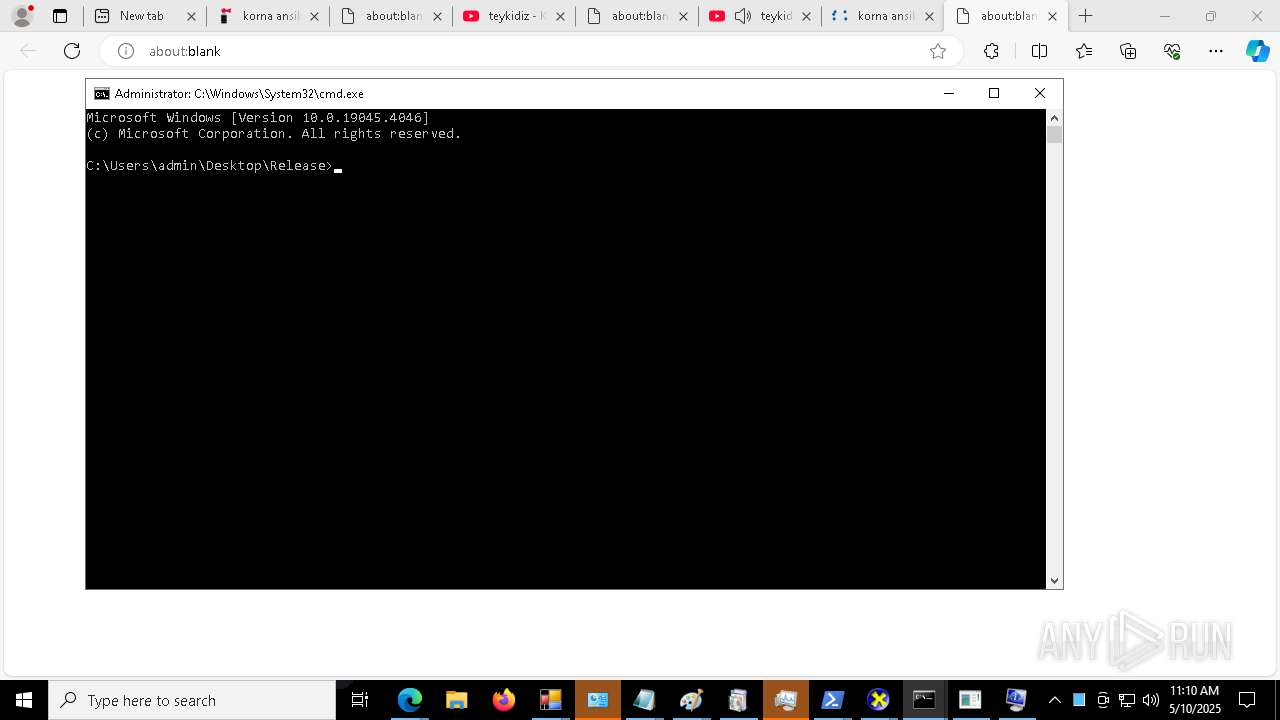
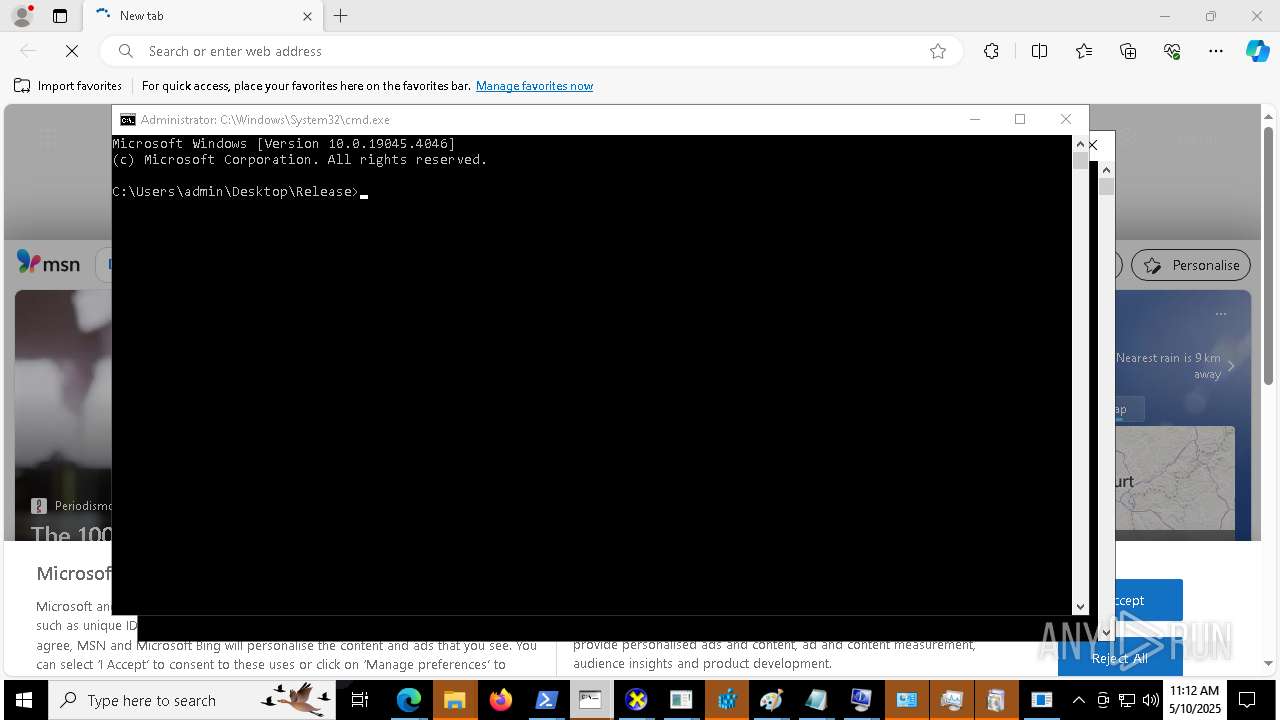
- cmd.exe (PID: 8588)
- net.exe (PID: 8648)
- net.exe (PID: 13704)
- cmd.exe (PID: 14928)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 7848)
- MALWAREBYTES 2.exe (PID: 8112)
- net.exe (PID: 1272)
- net.exe (PID: 6244)
- net.exe (PID: 7252)
- net.exe (PID: 2600)
- net.exe (PID: 8100)
- net.exe (PID: 7256)
- net.exe (PID: 6036)
- net.exe (PID: 6268)
- net.exe (PID: 632)
SUSPICIOUS
Reads security settings of Internet Explorer
- MALWAREBYTES 2.exe (PID: 8112)
Reads the date of Windows installation
- MALWAREBYTES 2.exe (PID: 8112)
There is functionality for taking screenshot (YARA)
- MALWAREBYTES 2.exe (PID: 8112)
SQL CE related mutex has been found
- MALWAREBYTES 2.exe (PID: 8112)
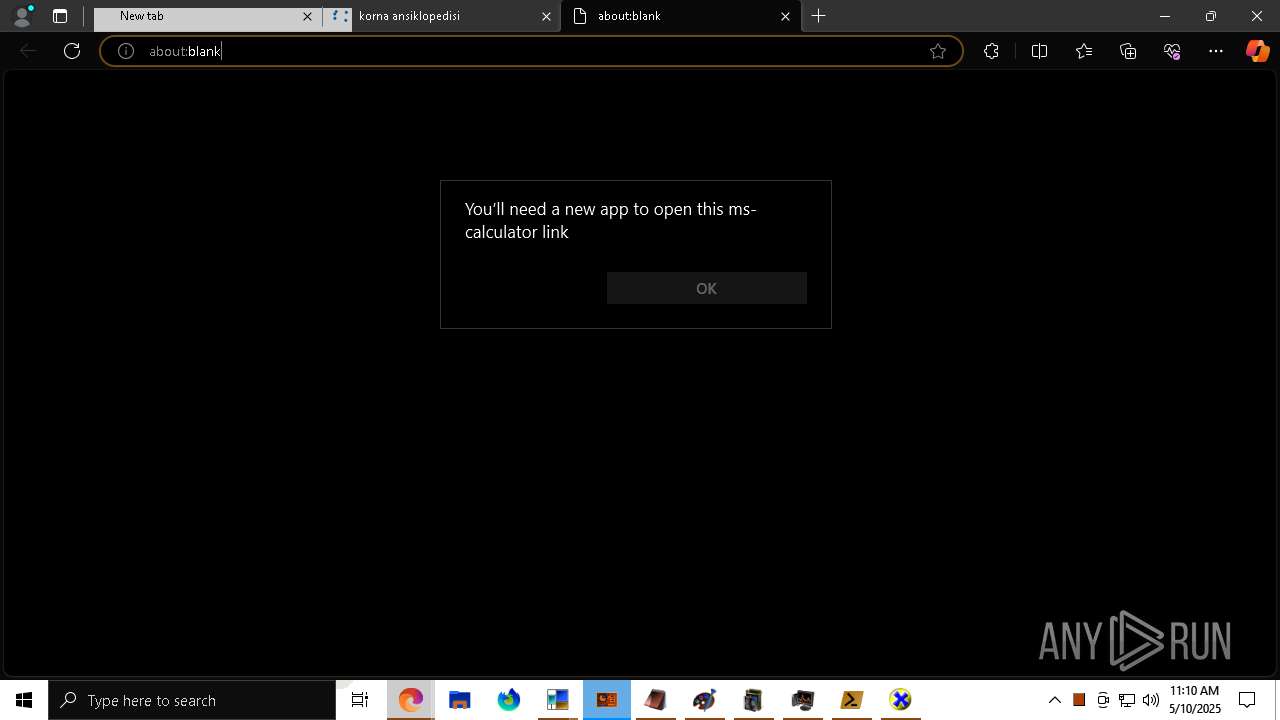
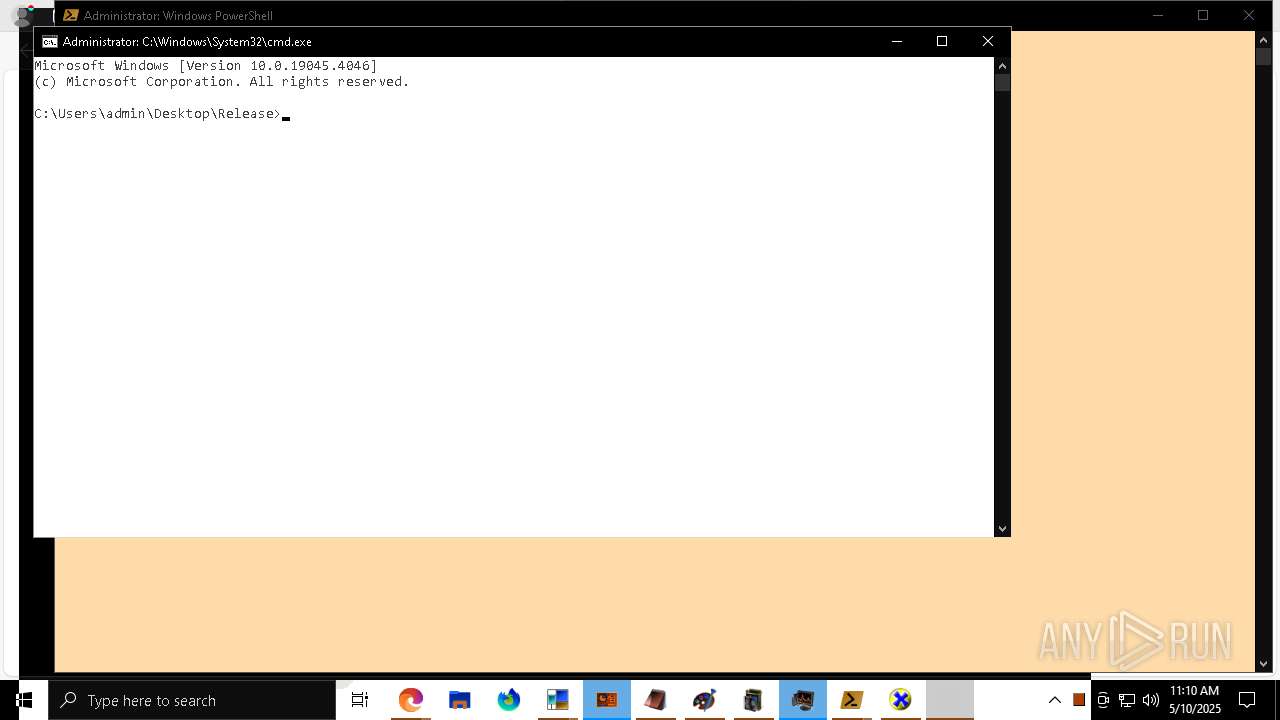
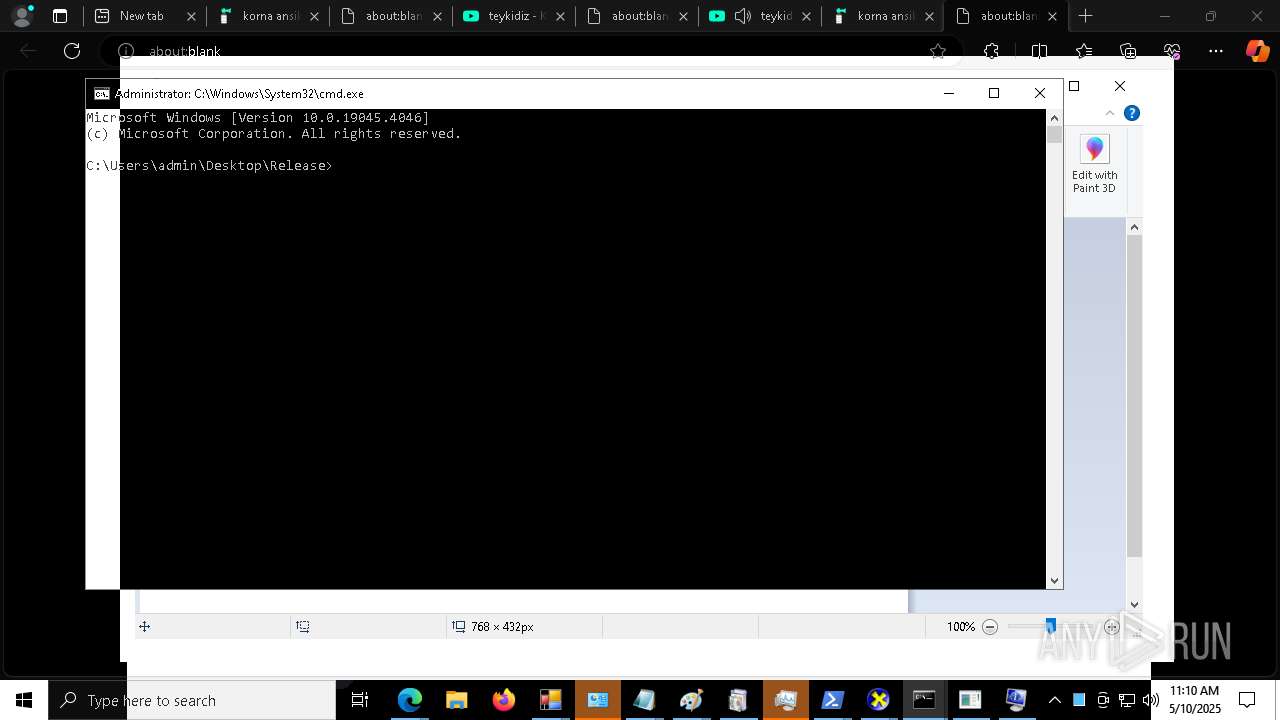
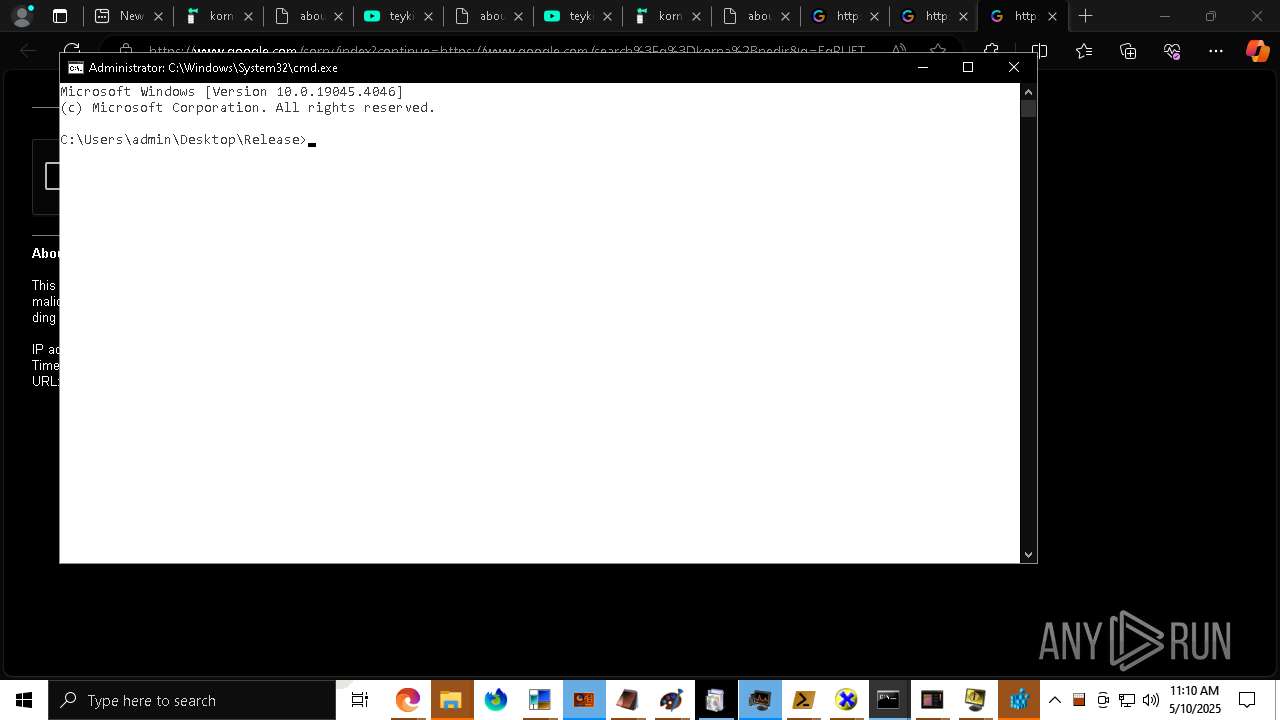
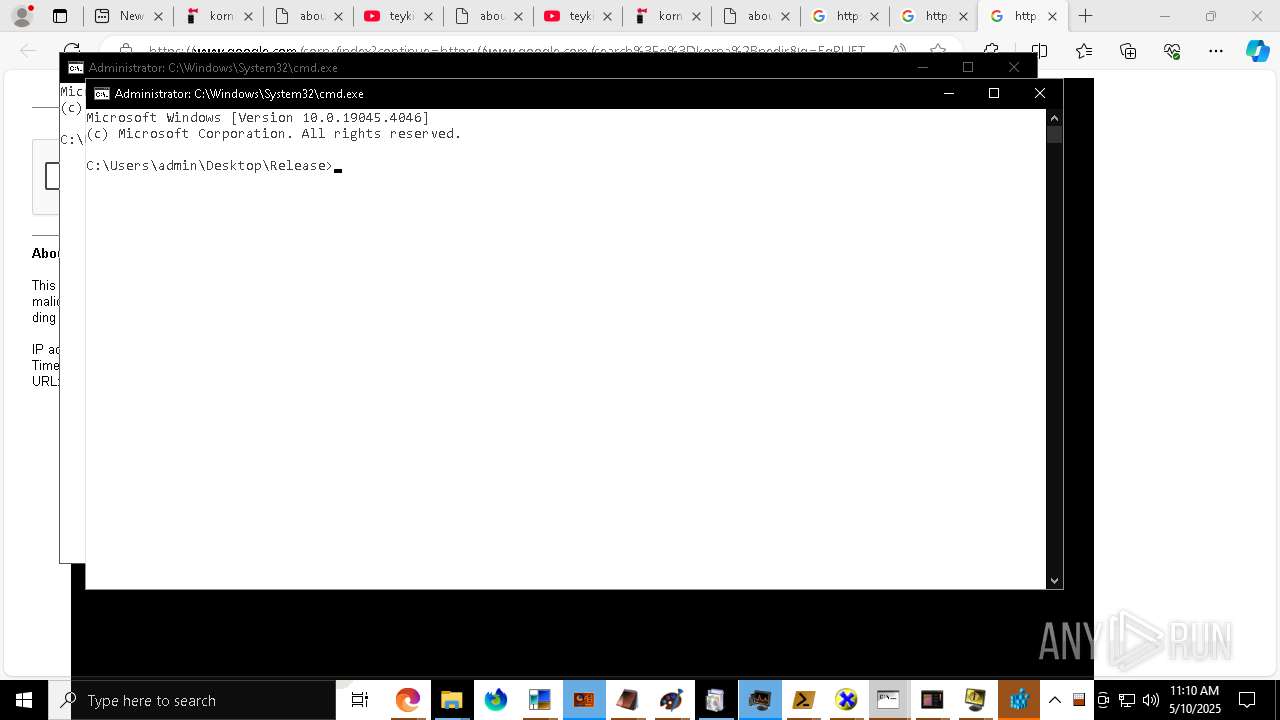
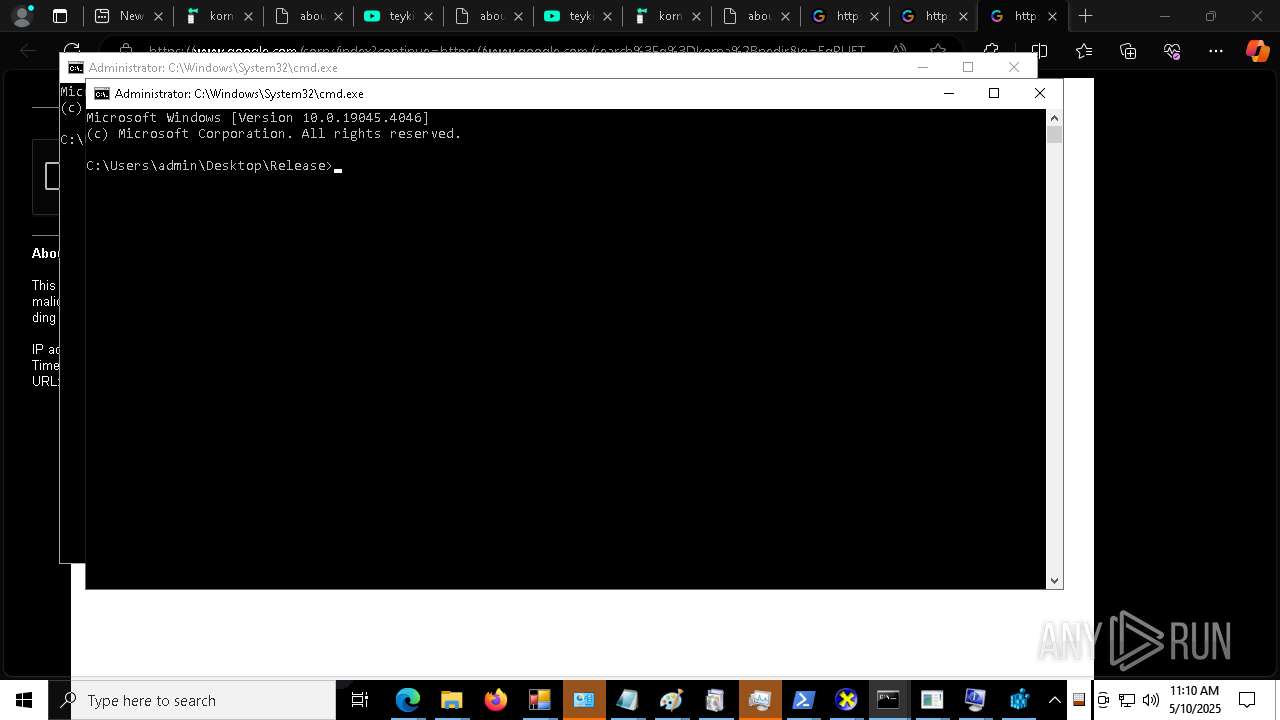
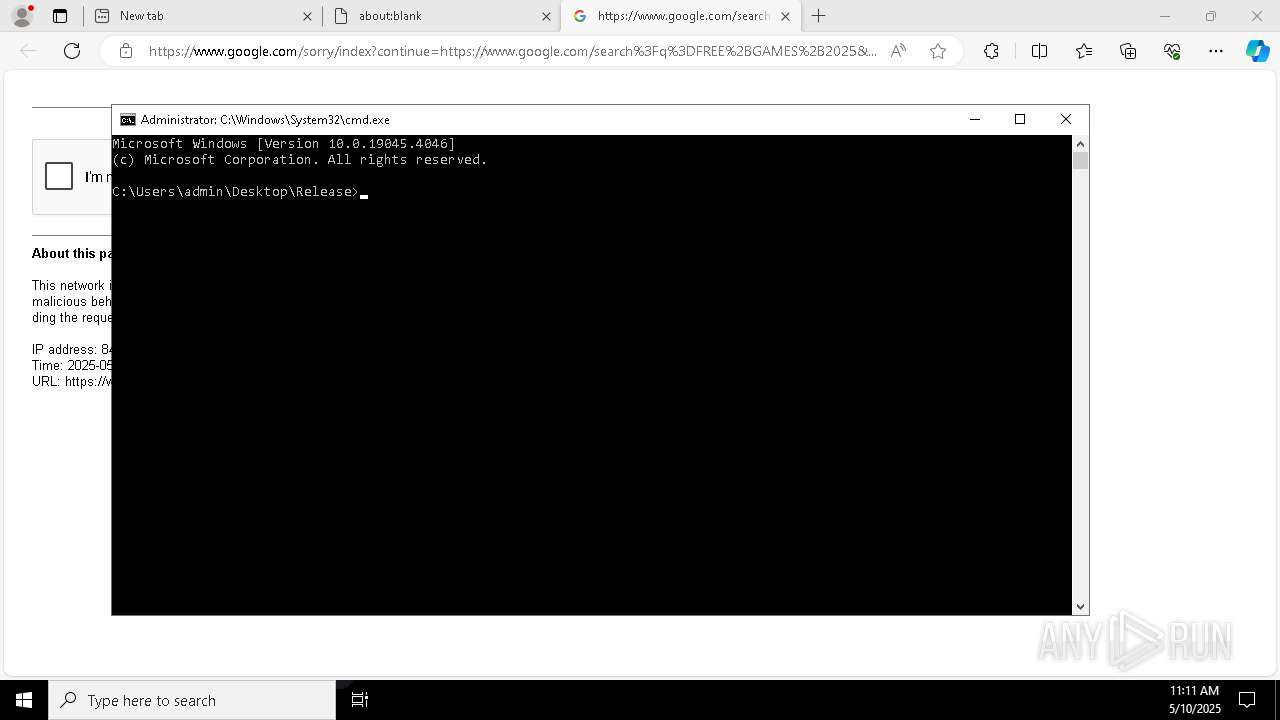
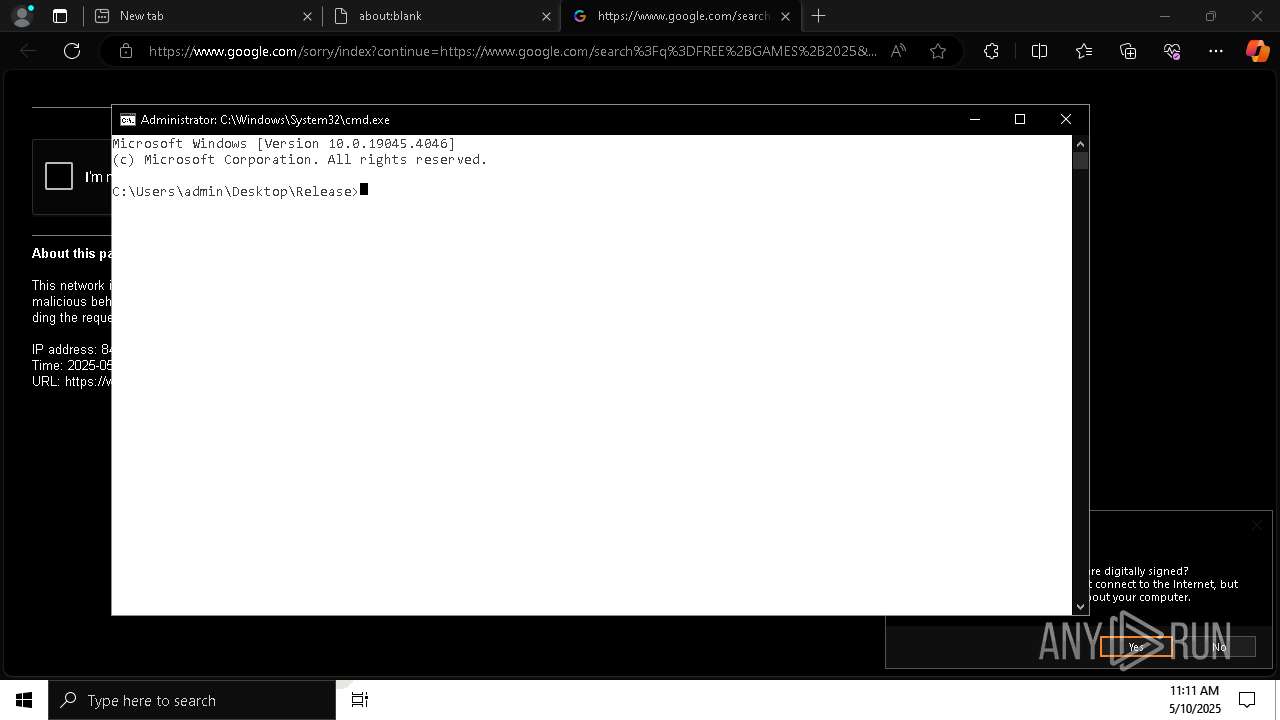
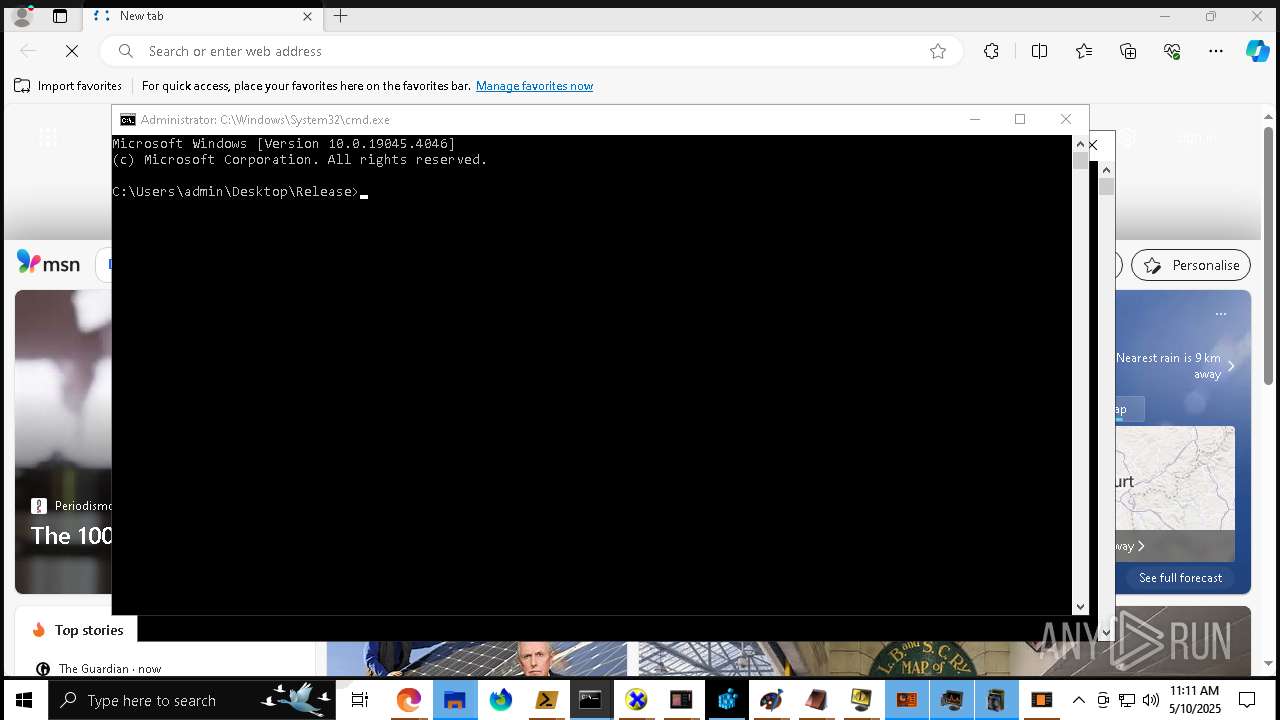
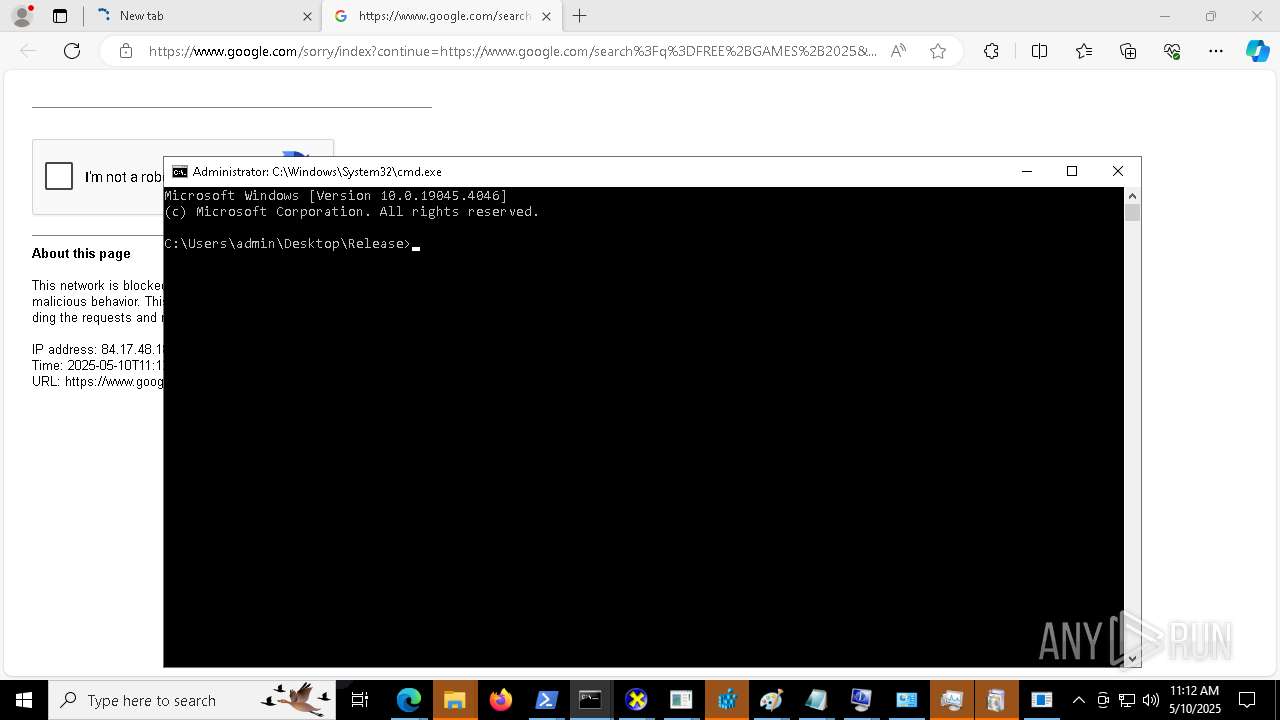
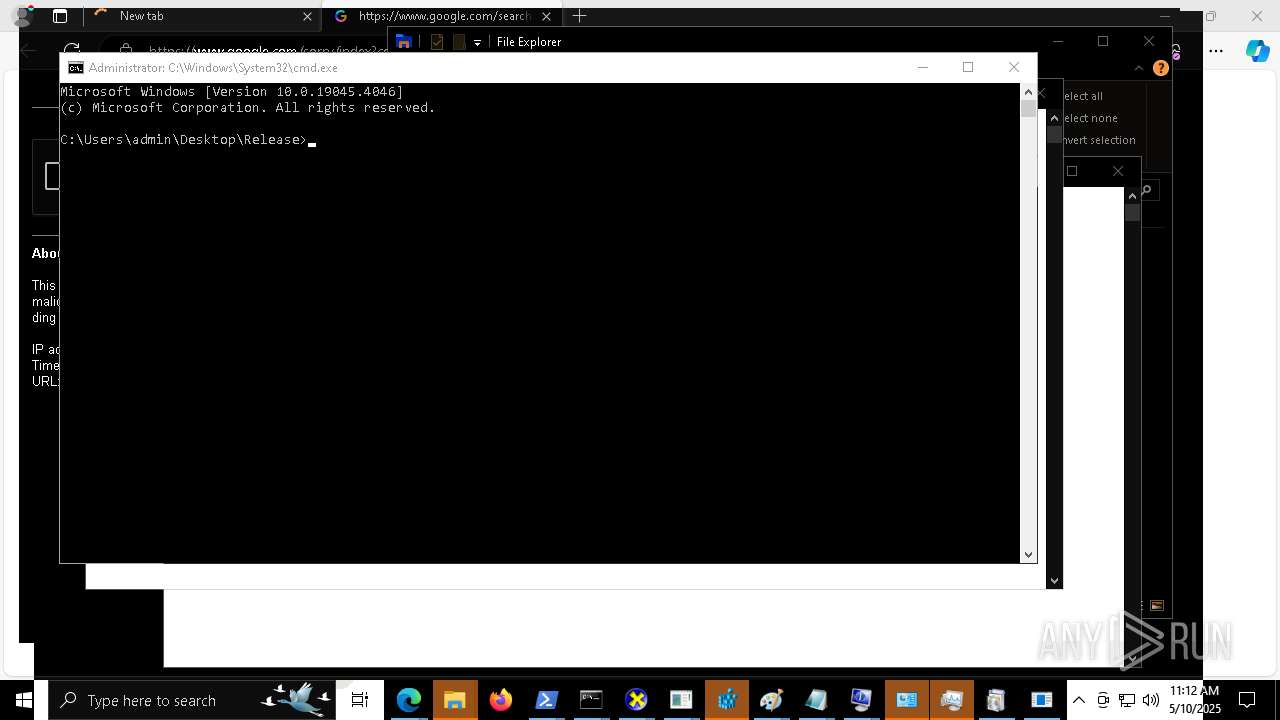
Starts CMD.EXE for commands execution
- MALWAREBYTES 2.exe (PID: 8112)
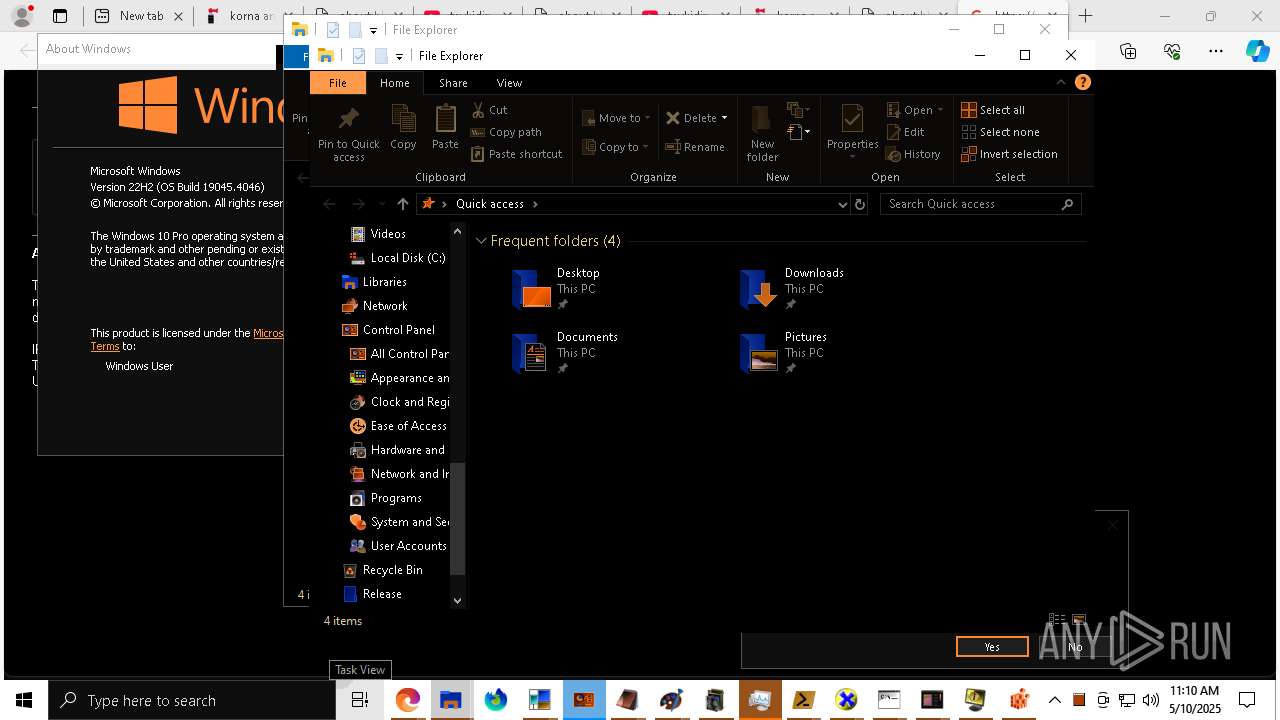
Start notepad (likely ransomware note)
- MALWAREBYTES 2.exe (PID: 8112)
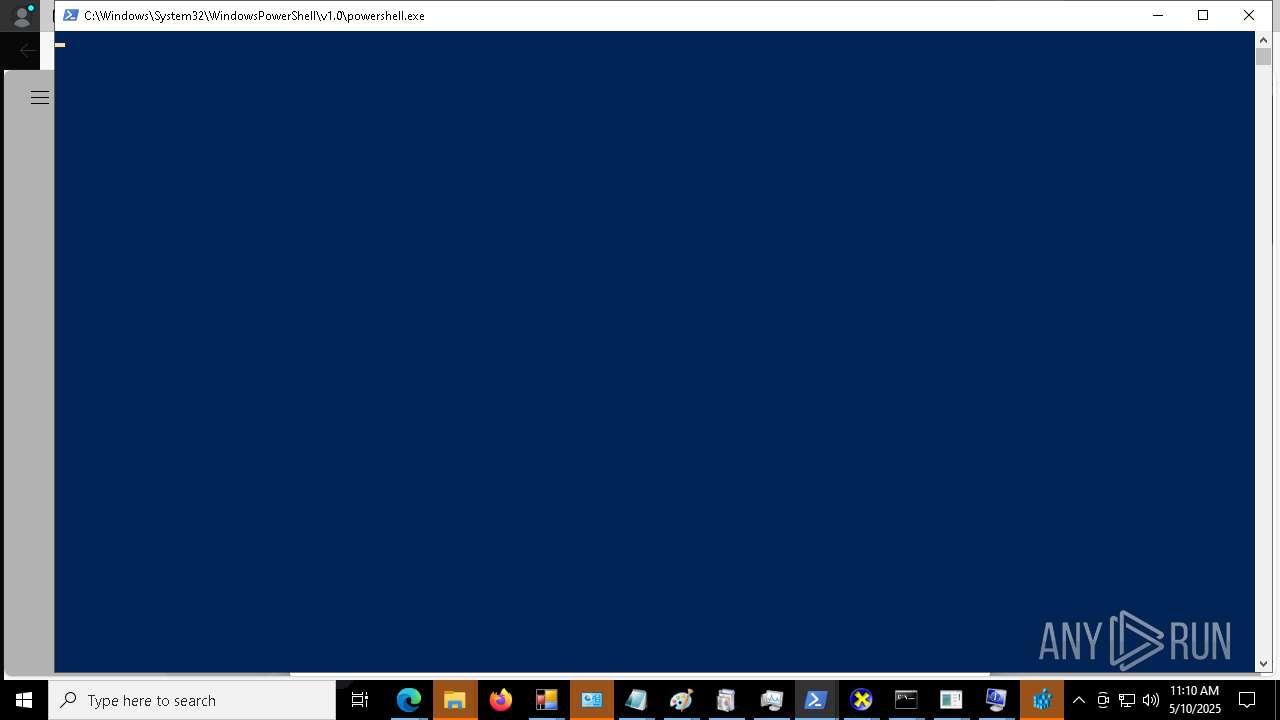
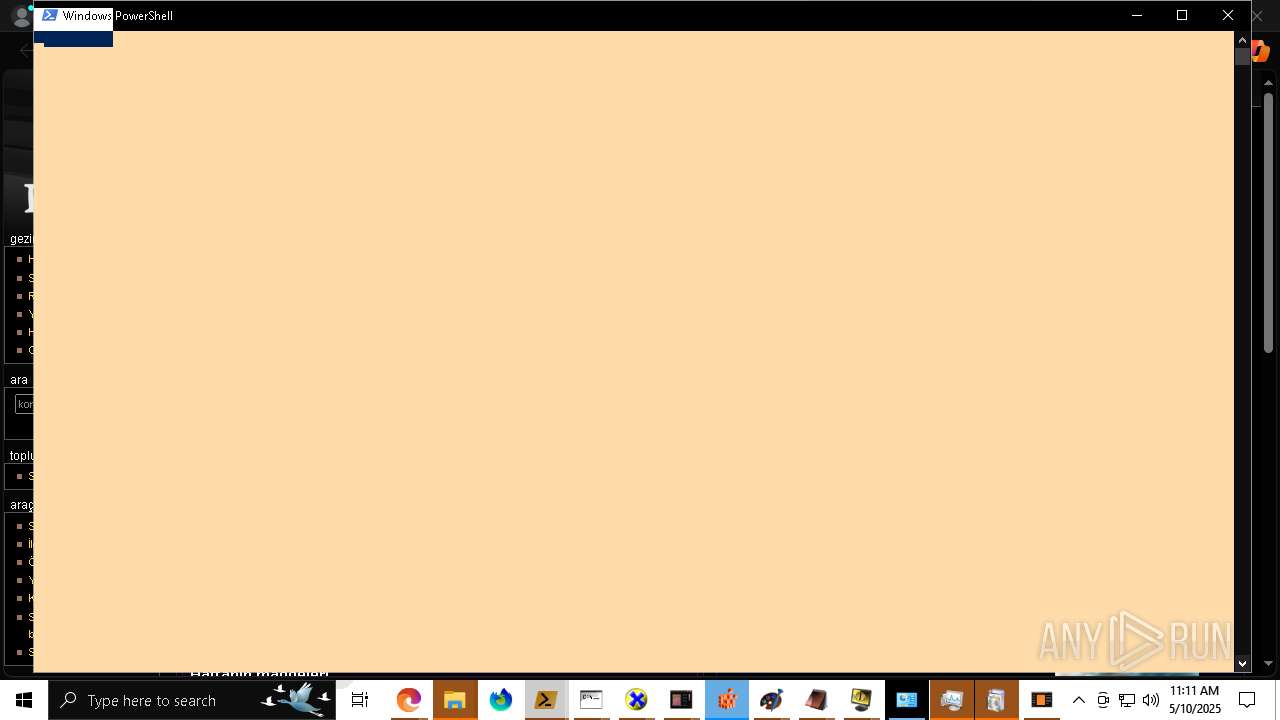
Starts POWERSHELL.EXE for commands execution
- MALWAREBYTES 2.exe (PID: 8112)
The process executes via Task Scheduler
- explorer.exe (PID: 12752)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 12224)
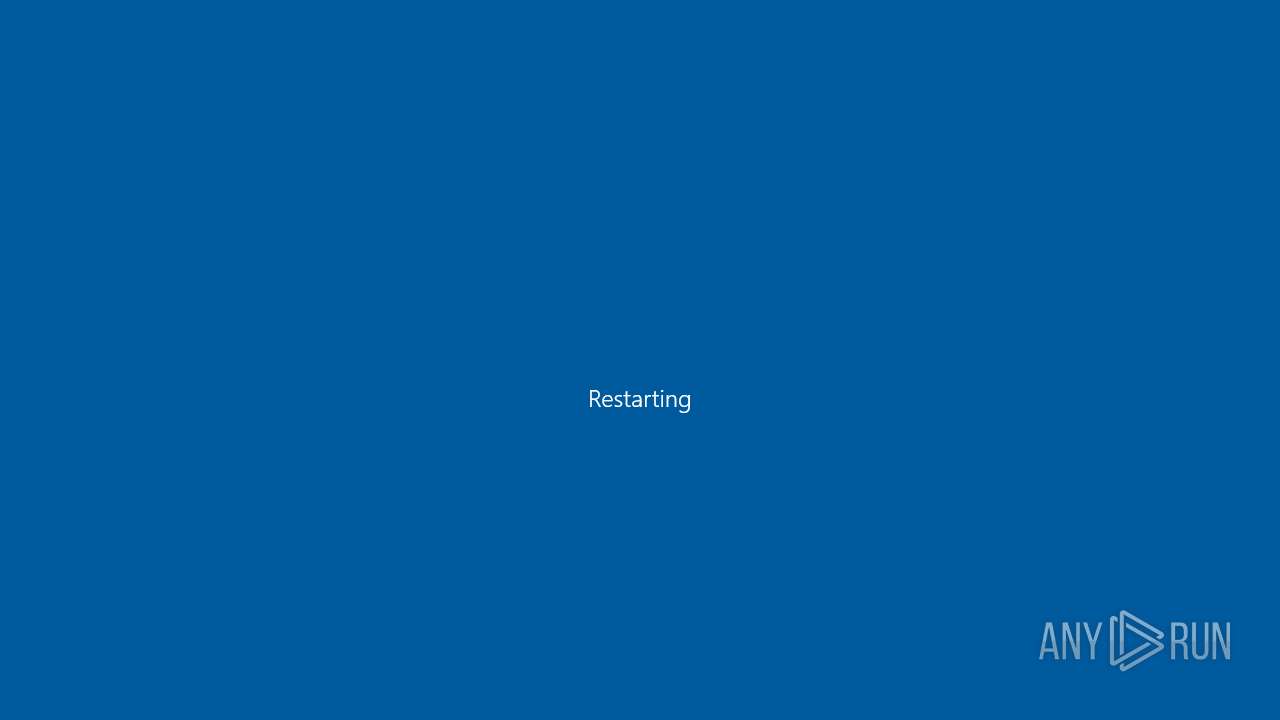
The system shut down or reboot
- MALWAREBYTES 2.exe (PID: 8112)
INFO
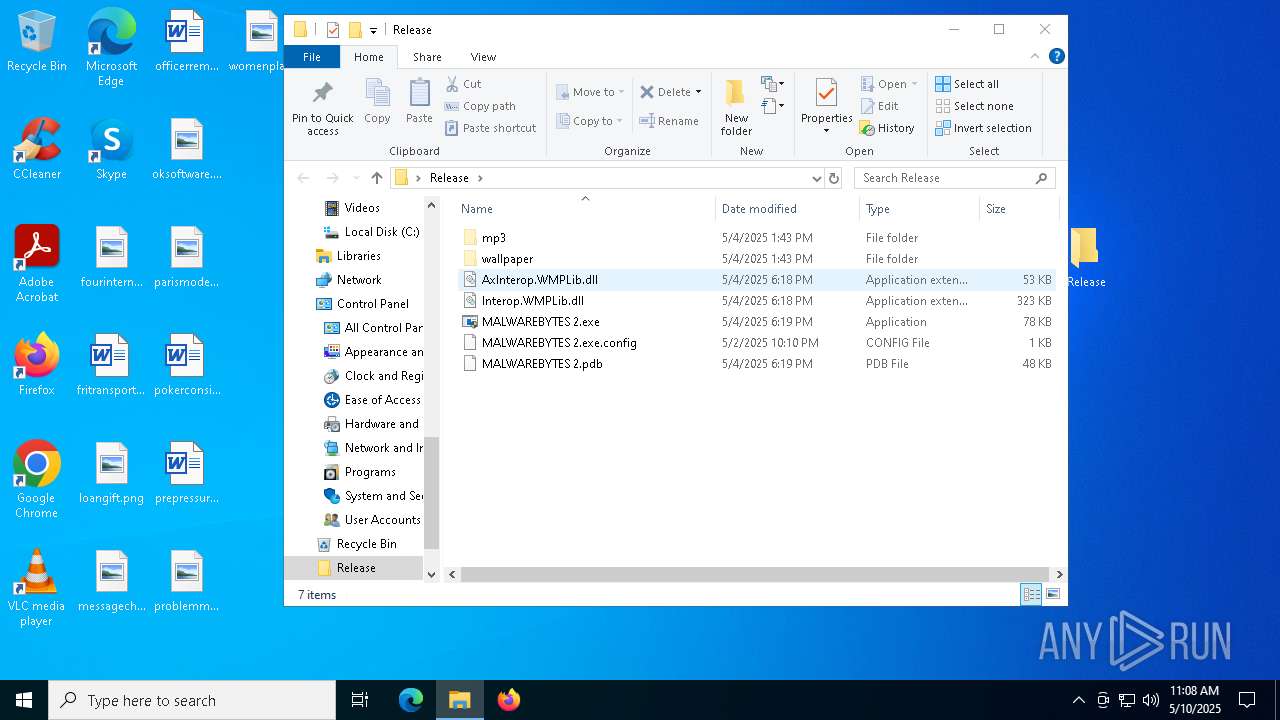
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7420)
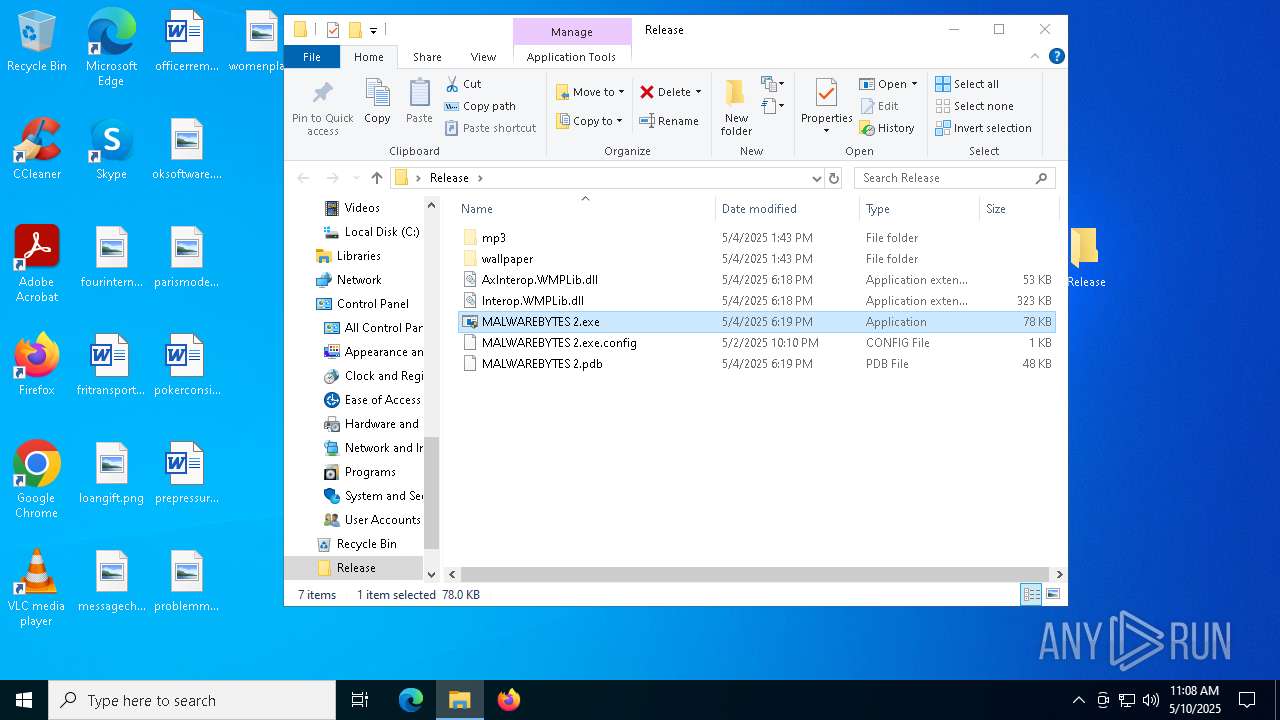
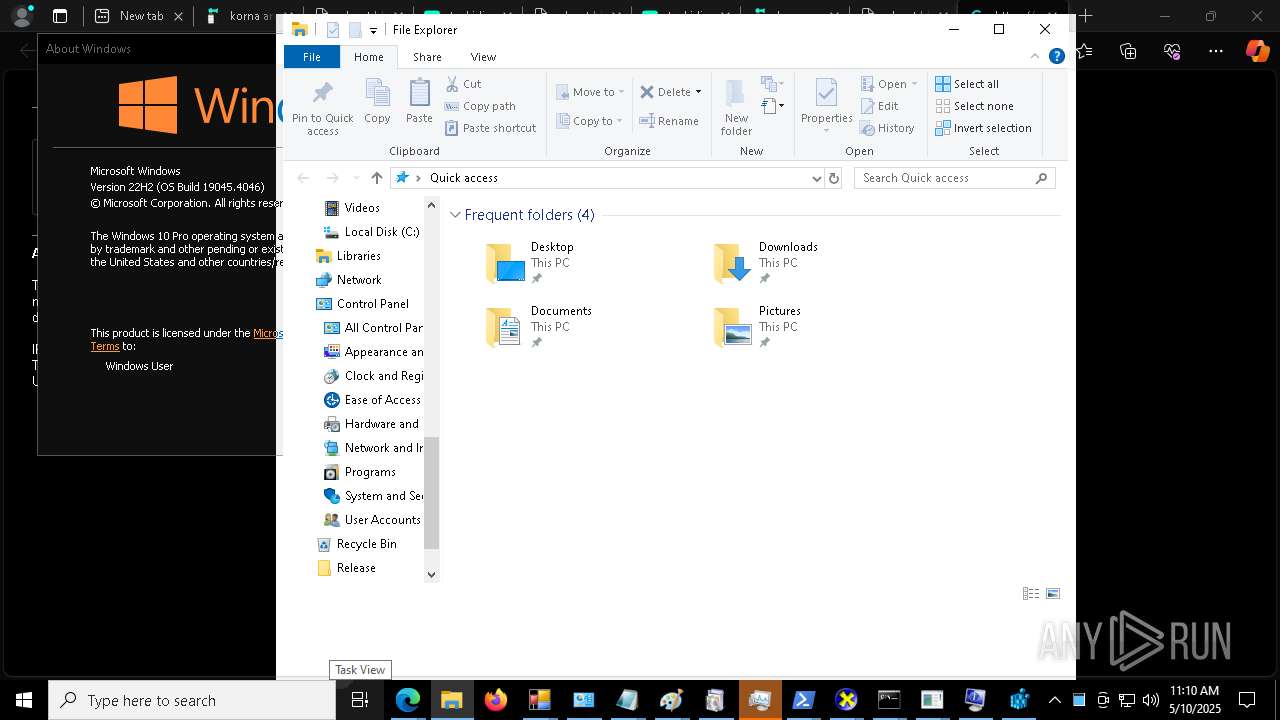
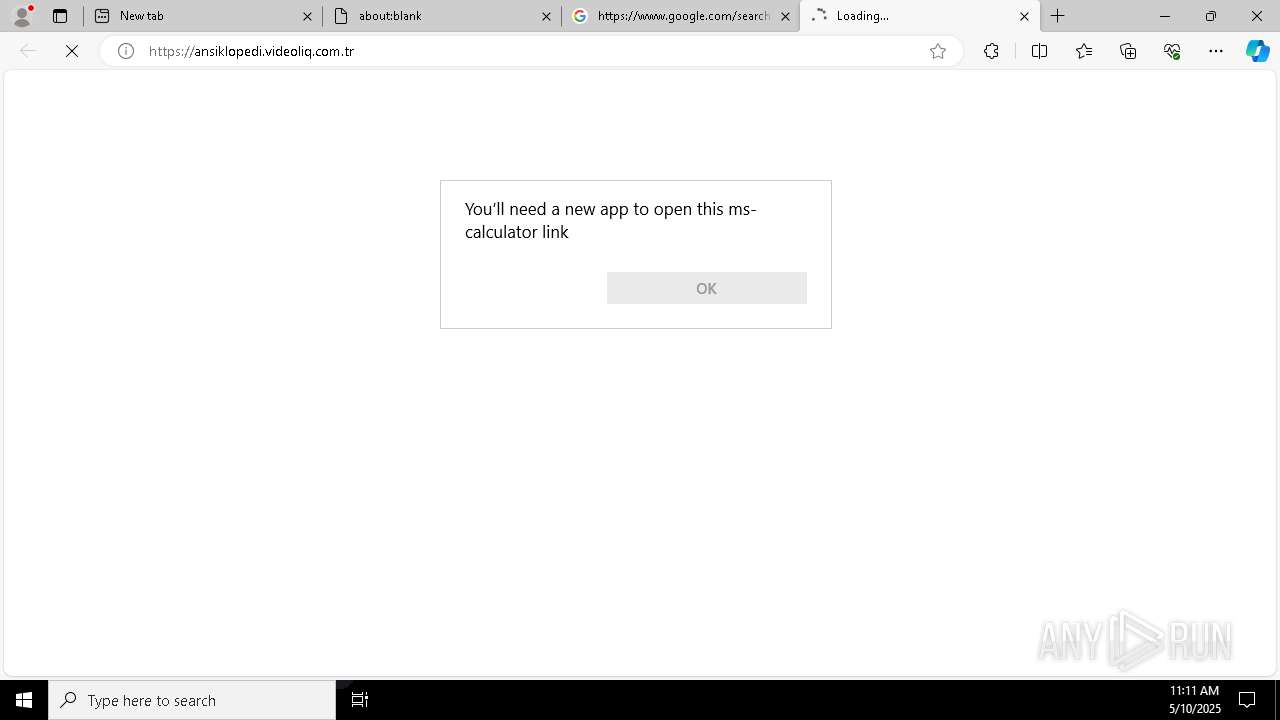
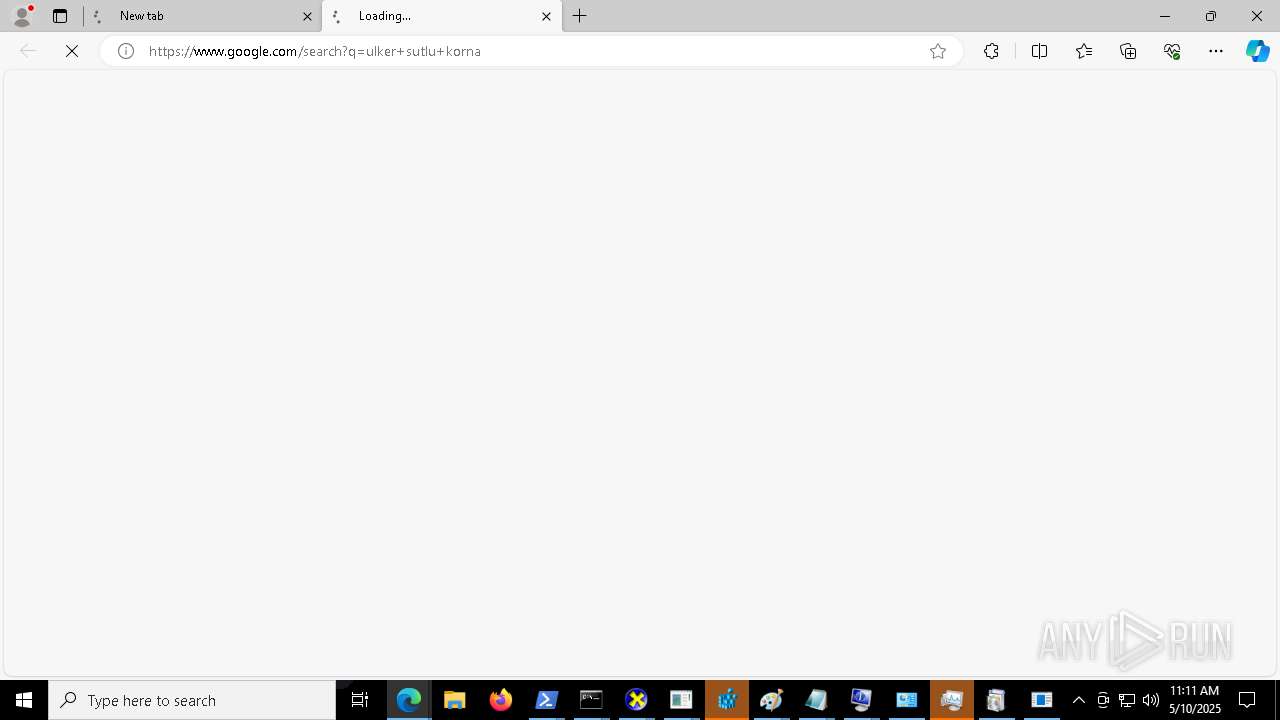
Manual execution by a user
- MALWAREBYTES 2.exe (PID: 8112)
- MALWAREBYTES 2.exe (PID: 8064)
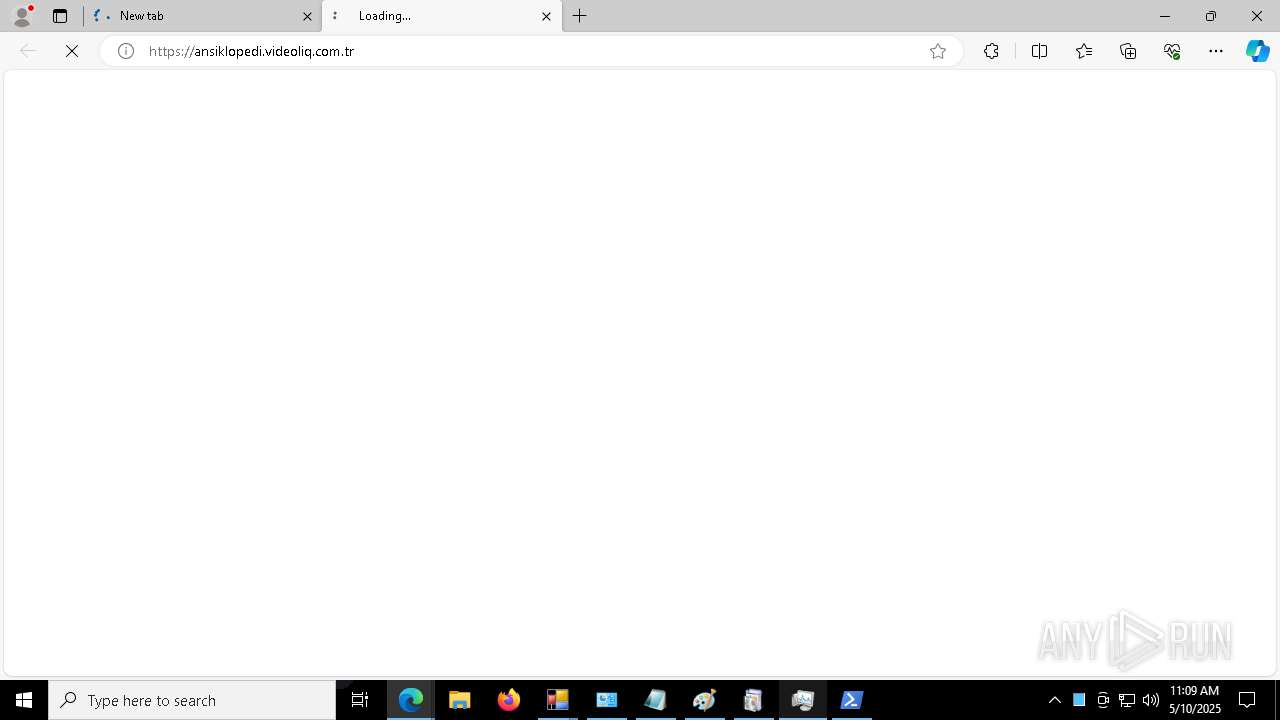
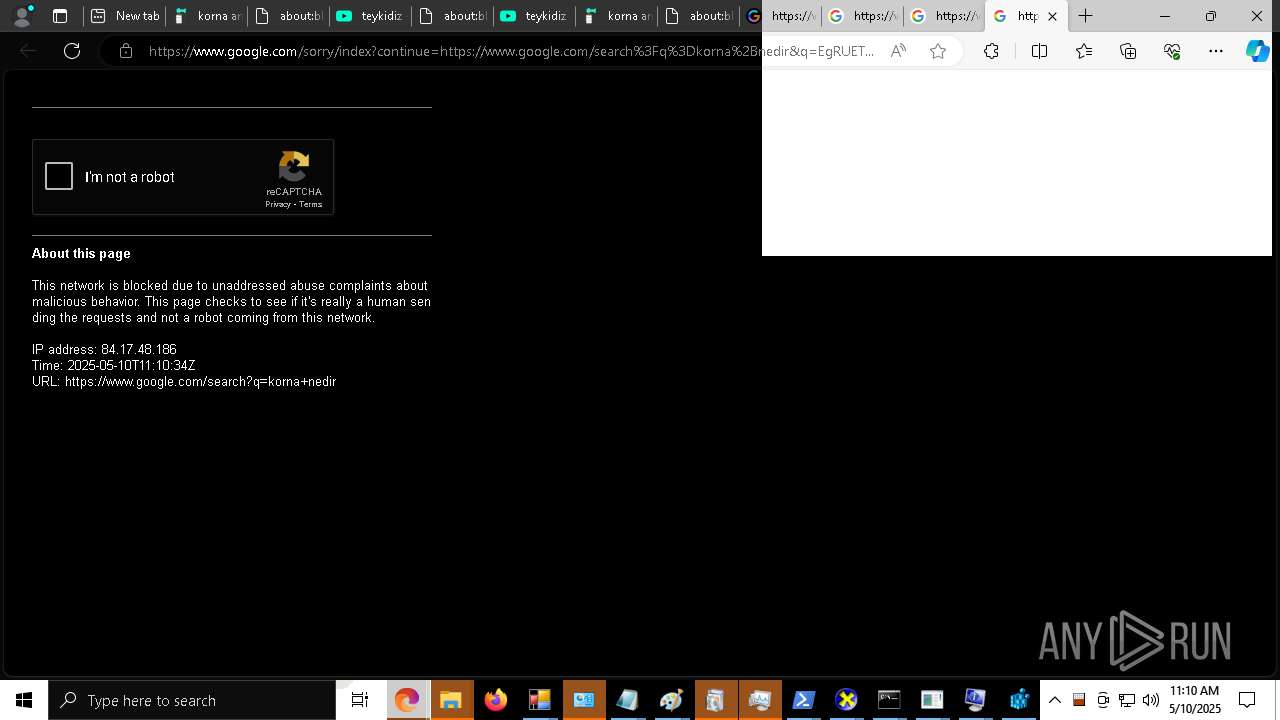
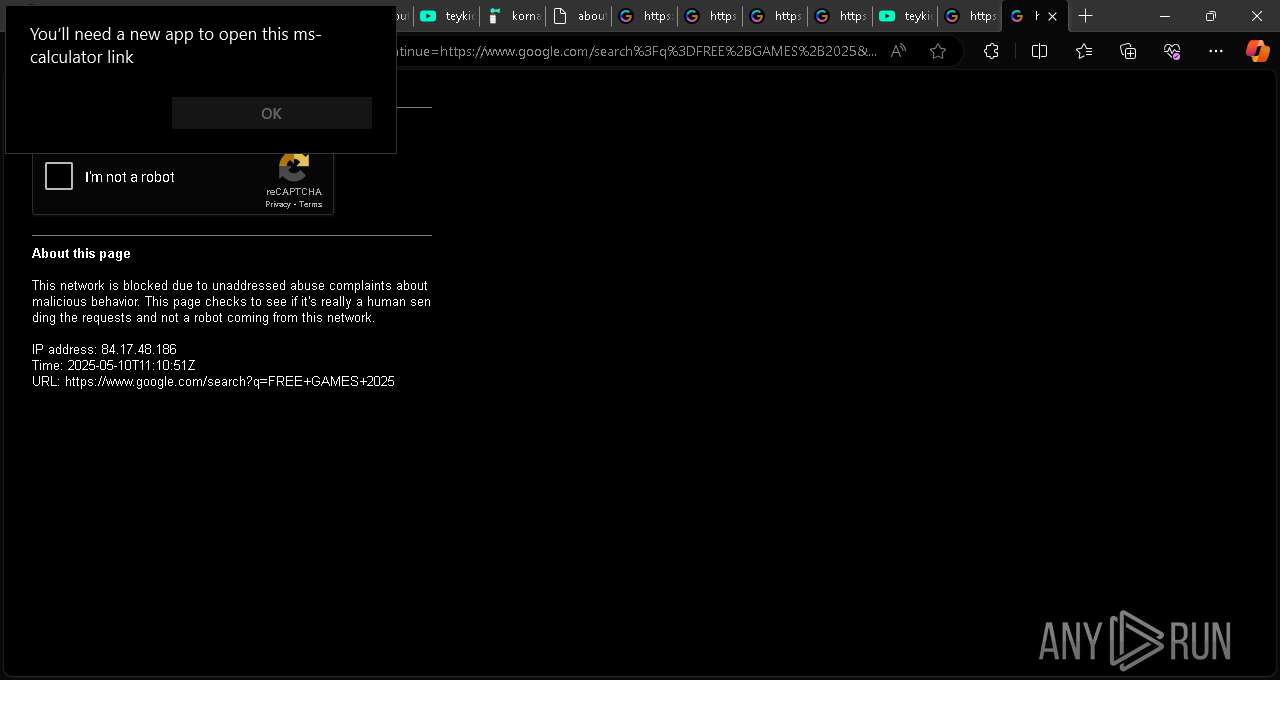
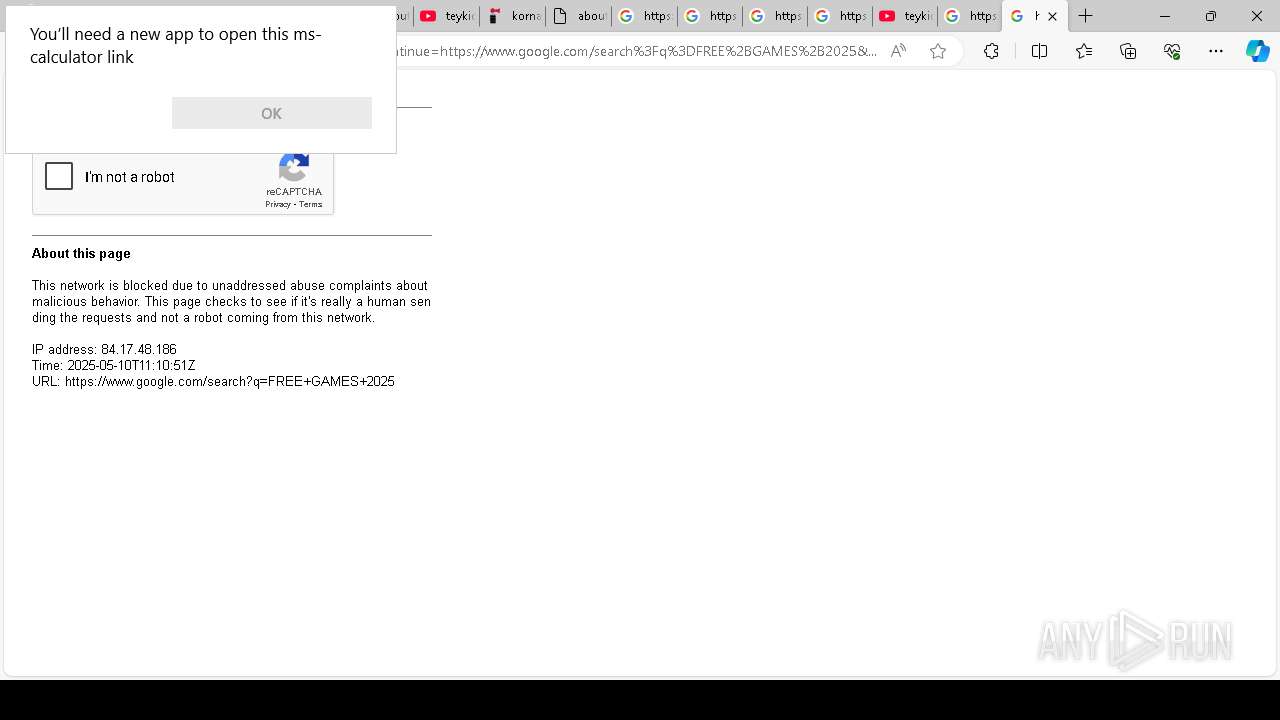
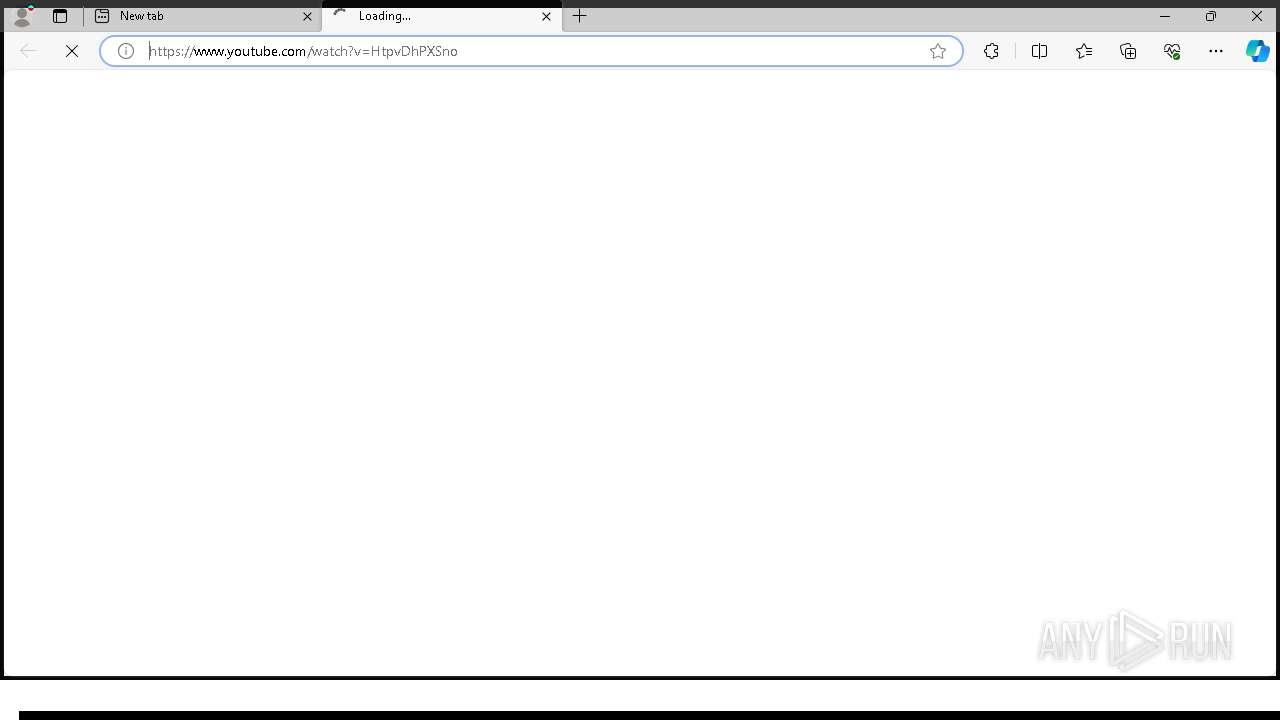
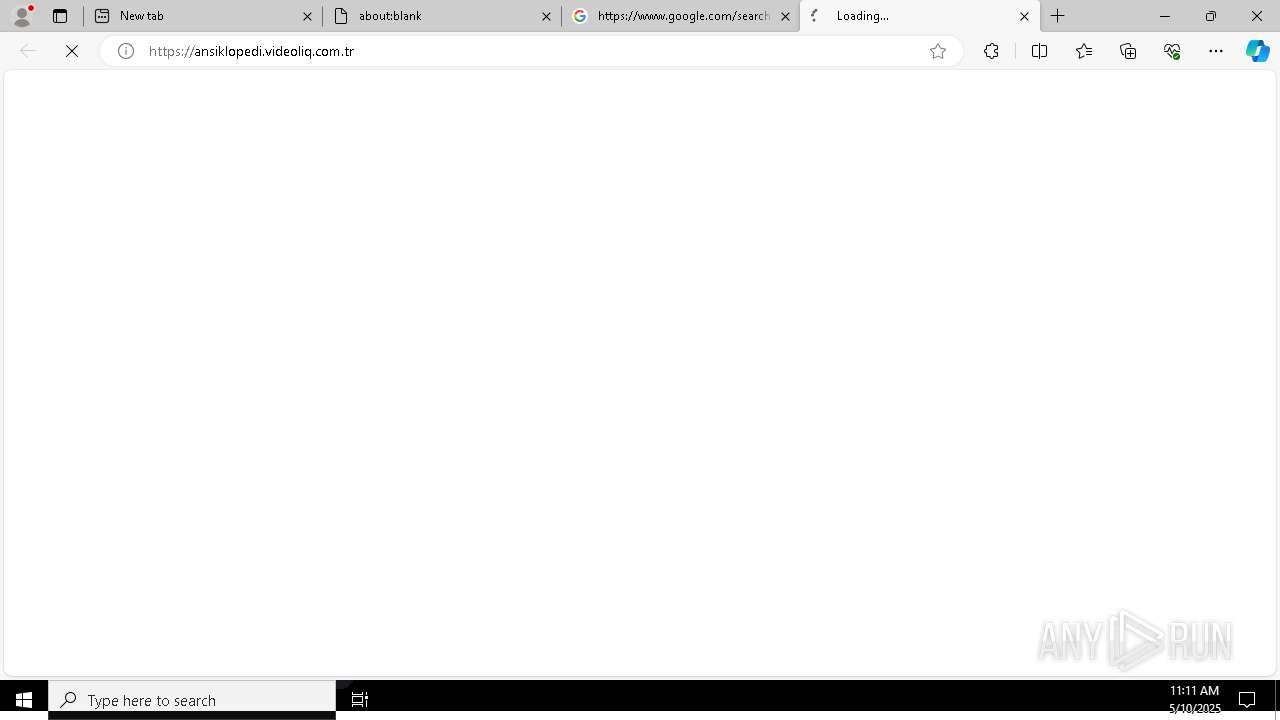
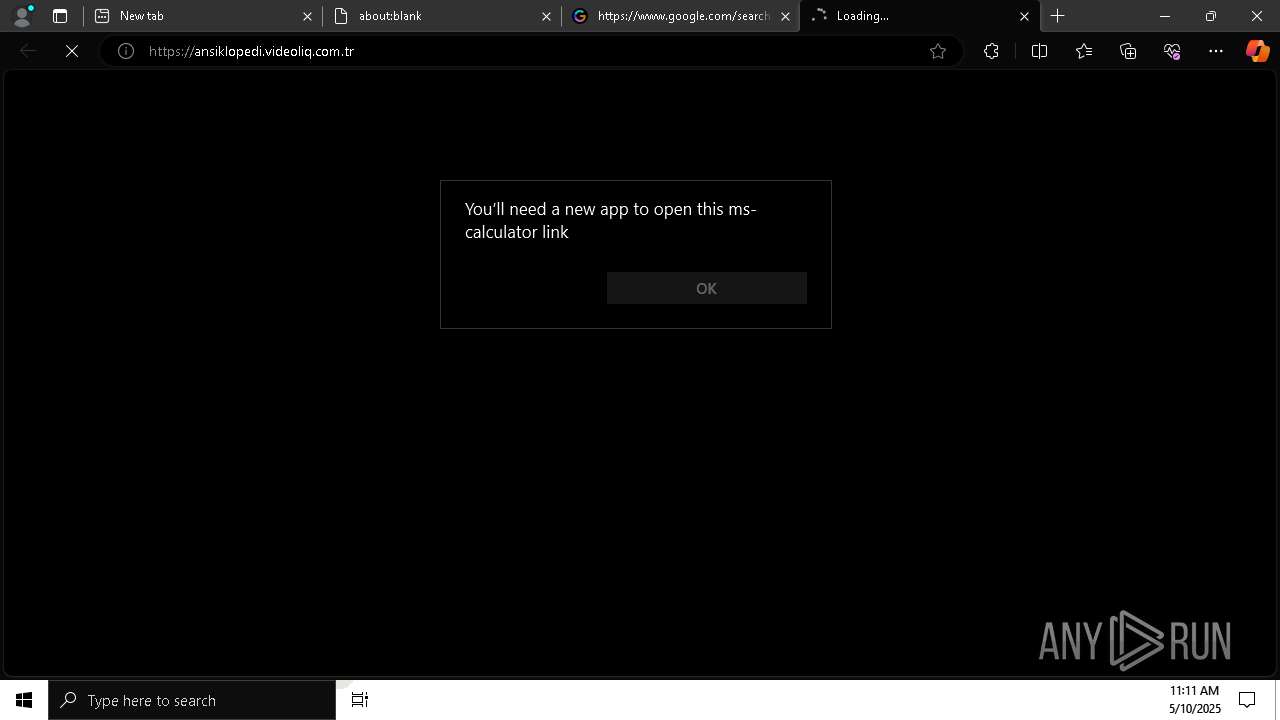
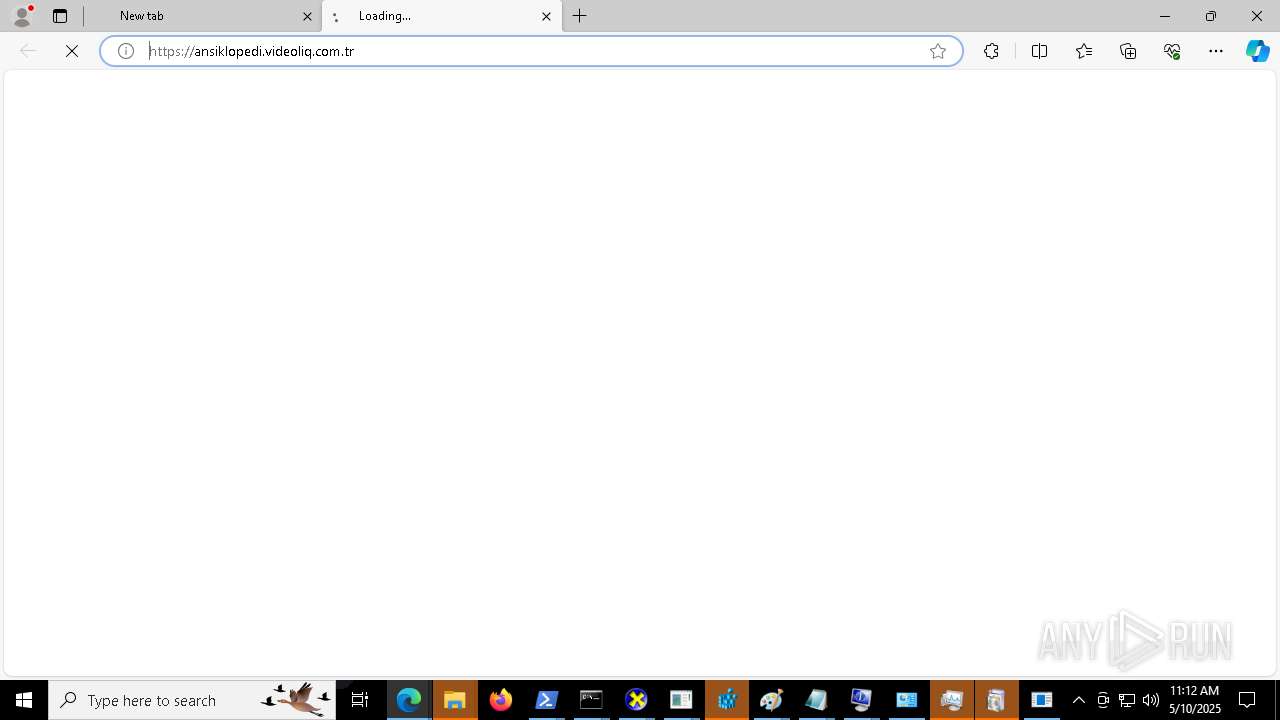
- msedge.exe (PID: 1912)
Reads the machine GUID from the registry
- MALWAREBYTES 2.exe (PID: 8112)
Checks supported languages
- MALWAREBYTES 2.exe (PID: 8112)
- identity_helper.exe (PID: 7764)
Reads the computer name
- MALWAREBYTES 2.exe (PID: 8112)
- identity_helper.exe (PID: 7764)
Process checks computer location settings
- MALWAREBYTES 2.exe (PID: 8112)
Creates files or folders in the user directory
- MALWAREBYTES 2.exe (PID: 8112)
Checks proxy server information
- MALWAREBYTES 2.exe (PID: 8112)
Application launched itself
- msedge.exe (PID: 1912)
- msedge.exe (PID: 7760)
Creates files in the program directory
- MALWAREBYTES 2.exe (PID: 8112)
Reads Environment values
- identity_helper.exe (PID: 7764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:05:04 18:19:39+00:00 |
| ArchivedFileName: | Release |
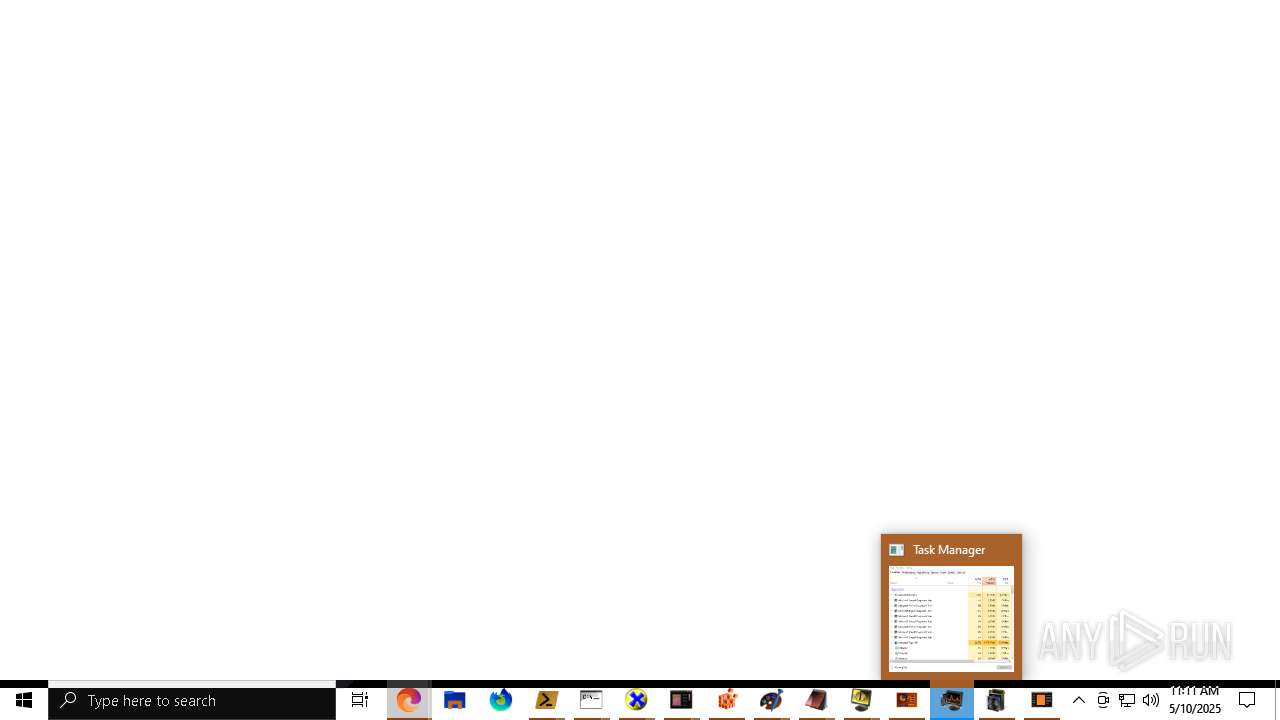
Total processes
527
Monitored processes
382
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\net1 user KORNA8 korna /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Windows\System32\net.exe" user KORNA10 korna /add | C:\Windows\System32\net.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 552 | "C:\Windows\System32\Taskmgr.exe" | C:\Windows\System32\Taskmgr.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Windows\System32\net.exe" localgroup Administrators KORNA7 /add | C:\Windows\System32\net.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5172 --field-trial-handle=2424,i,13638713902643717457,16246164568272538562,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 824 | "C:\Windows\System32\mspaint.exe" | C:\Windows\System32\mspaint.exe | — | MALWAREBYTES 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
176 088
Read events
175 115
Write events
945
Delete events
28
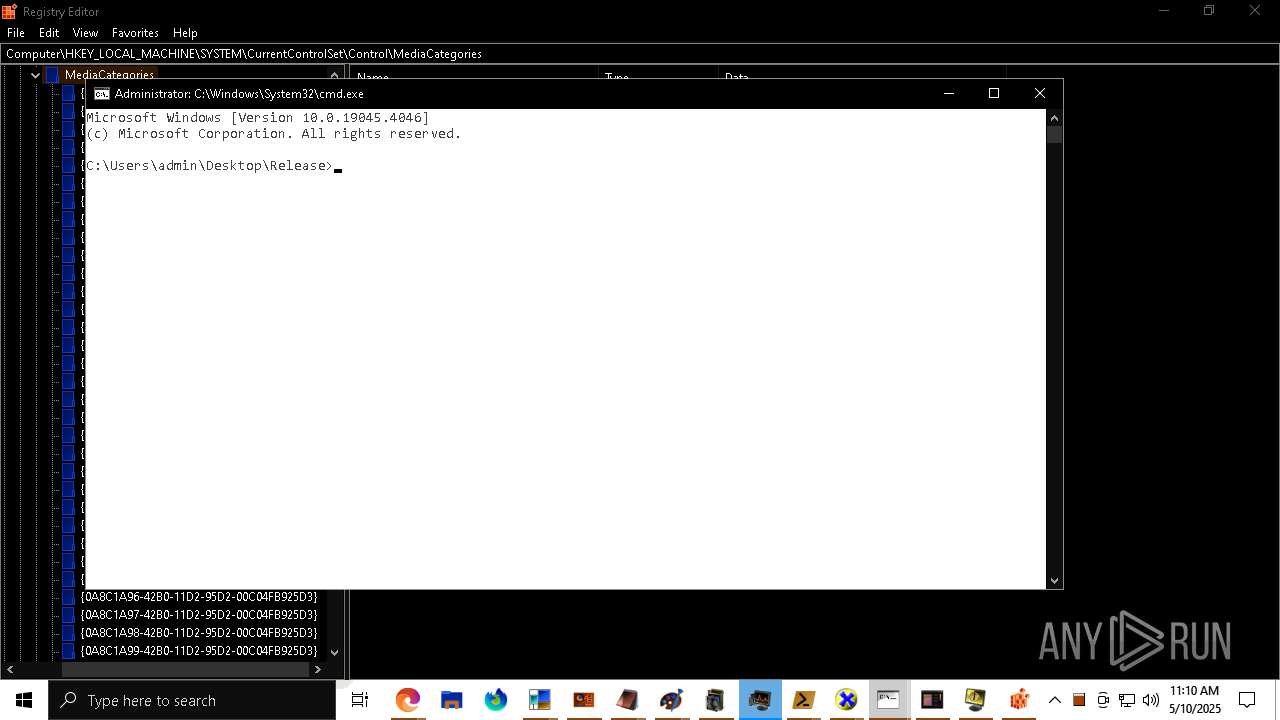
Modification events
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MALWAREBYTES 2 REAL.7z | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
37
Suspicious files
1 245
Text files
308
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7420.12402\Release\MALWAREBYTES 2.exe.config | xml | |
MD5:4D237C02B93B82EBD77993352F461C96 | SHA256:4C0F574147878CD84C300CE2036F968384B88098576AD97FD561CE0963AE7254 | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7420.12402\Release\Interop.WMPLib.dll | executable | |
MD5:7C7B3B60866D8C243A2F3388605F93CB | SHA256:CED36687C7558FF49AF9AC2F4D5A3C26F58F0F5ECD95F4800AE3E87CC92EDF61 | |||
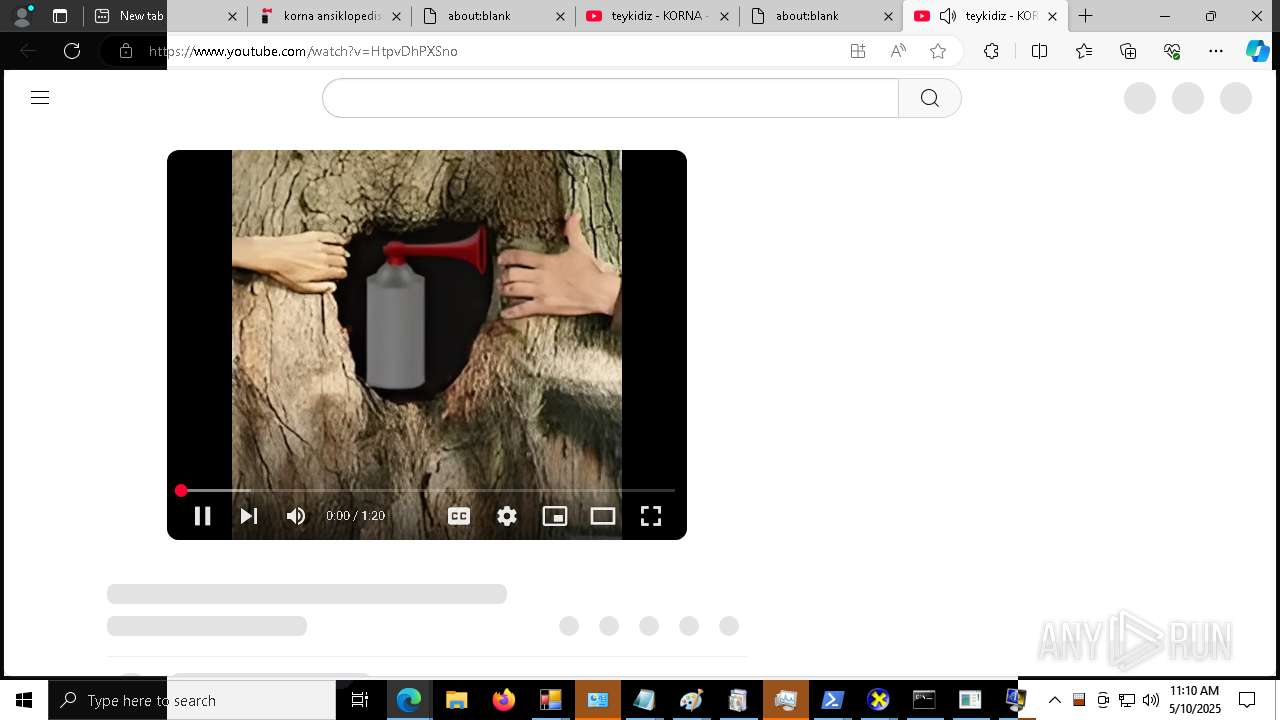
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7420.12402\Release\wallpaper\korna.jpg | image | |
MD5:4C0F5511E066D3FFABEE171CD1C4B7BB | SHA256:D8AF0A03DEE42F68BB730F4A67CA1F148384E6F6246F0A98C53E76F18ED86FFD | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF111049.TMP | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF111049.TMP | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF111049.TMP | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF111049.TMP | — | |
MD5:— | SHA256:— | |||
| 1912 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
293
DNS requests
243
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.48.23.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4692 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
9404 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | — | — | whitelisted |
9404 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | binary | 1.09 Kb | whitelisted |
9404 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | binary | 272 b | whitelisted |
9404 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | binary | 7.73 Kb | whitelisted |
9404 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | binary | 1.16 Kb | whitelisted |
9404 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747344196&P2=404&P3=2&P4=hI1kVlNNWLnjVwHP1pjKoWWvtq2tkR6cezOA8c2cC7s%2b%2fAQT%2biHH5gNlxtOluWm0LUcMTN5E9YydDGUCV%2bM4EA%3d%3d | US | compressed | 12.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1912 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
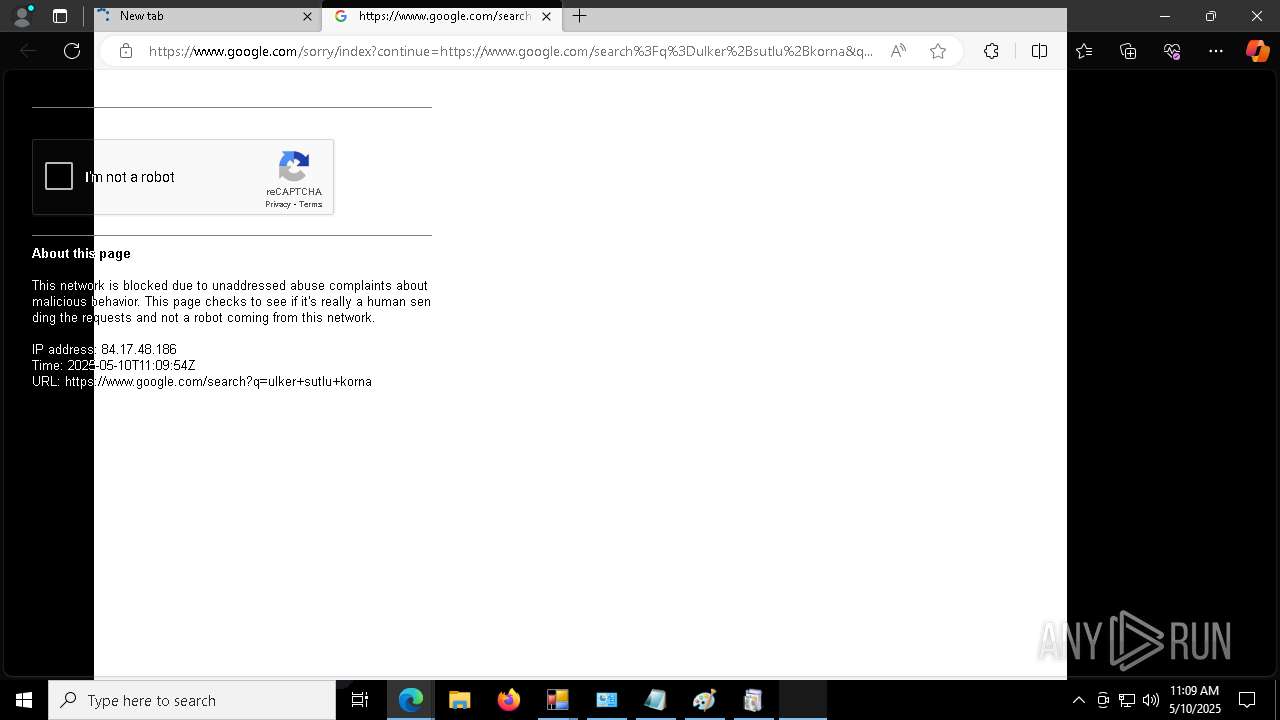
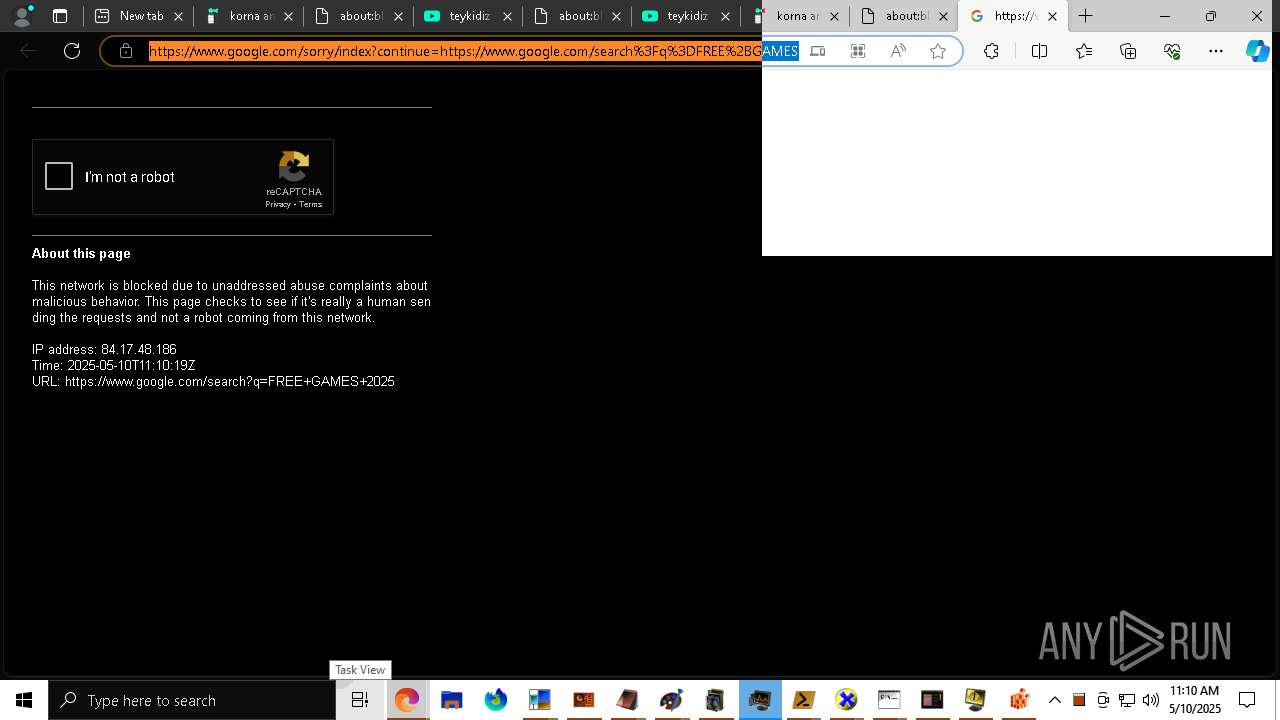
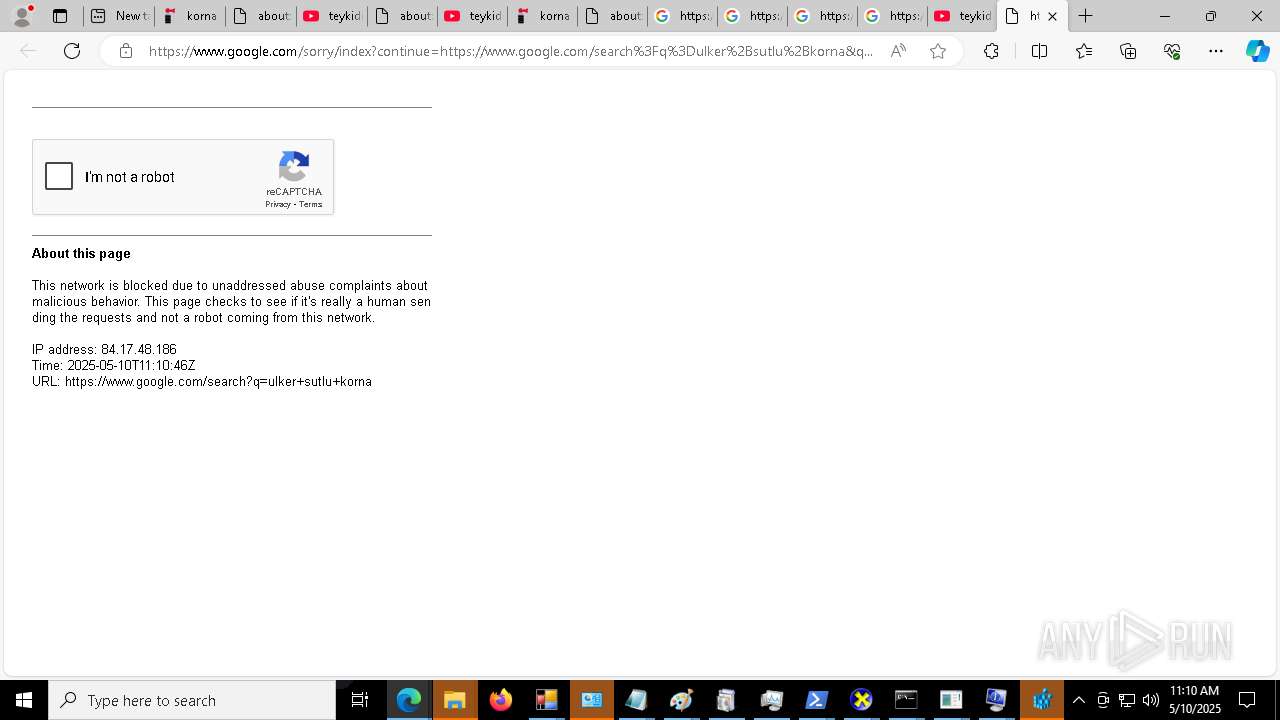
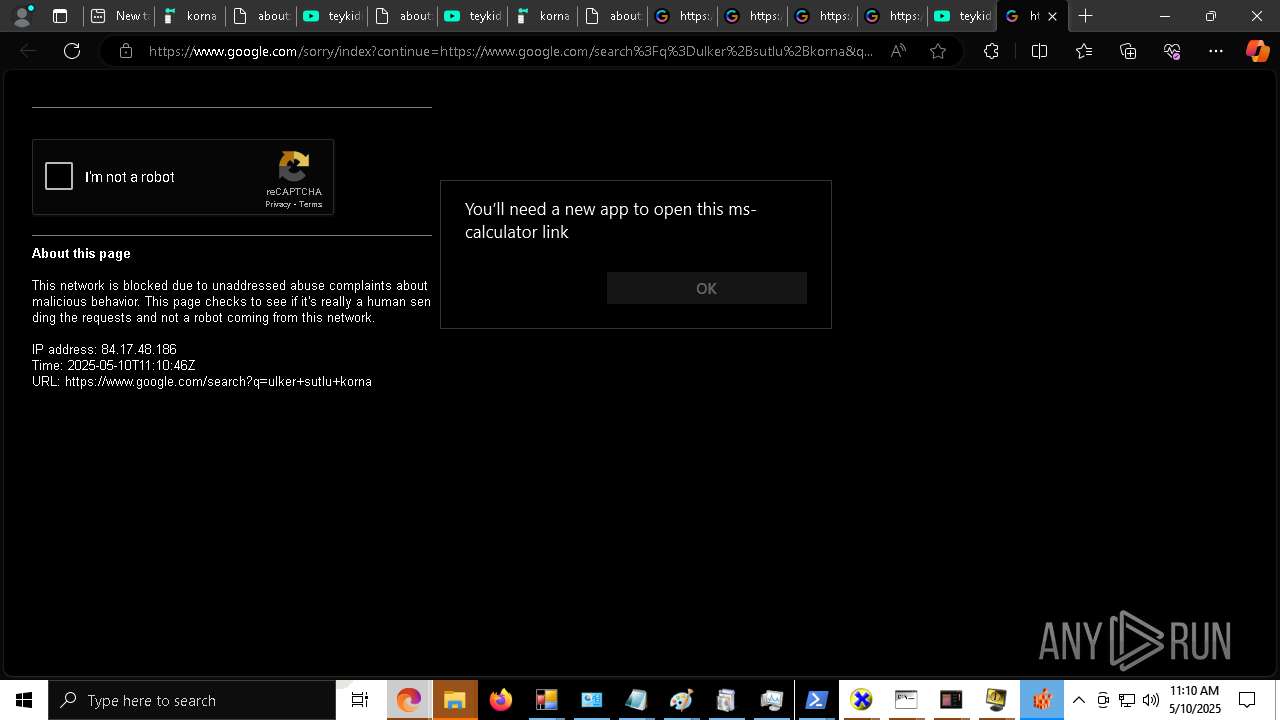
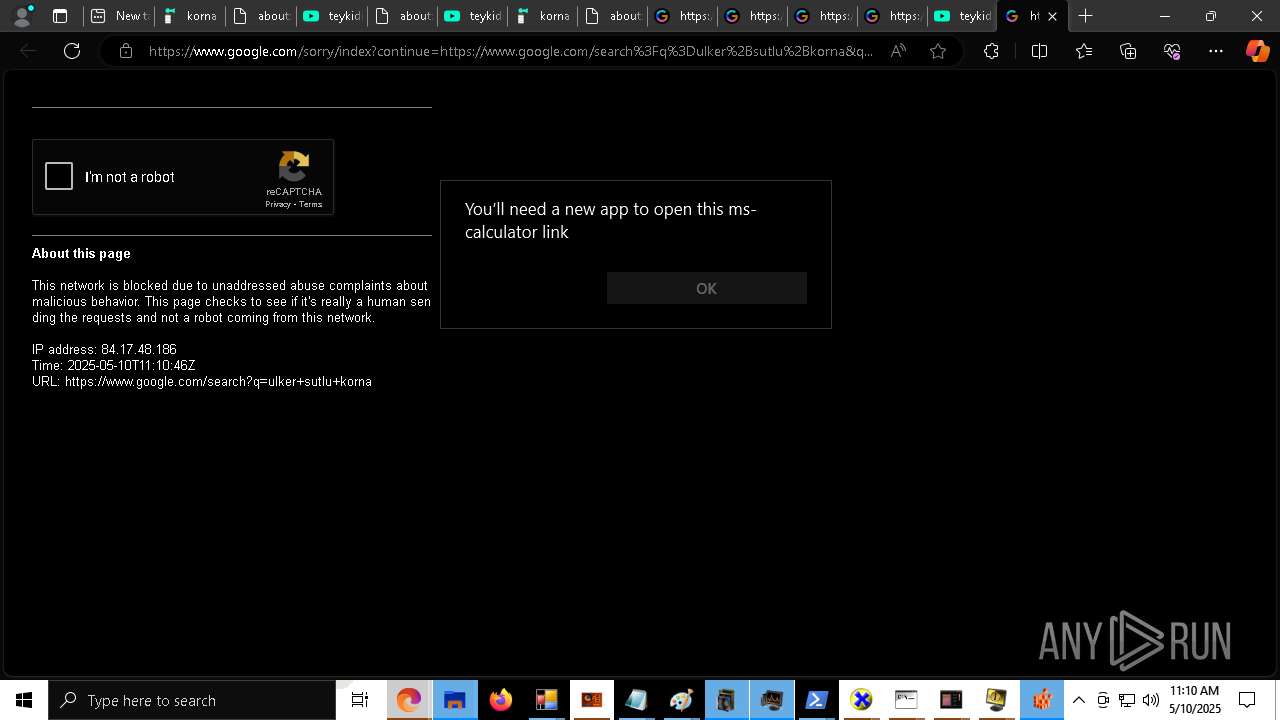
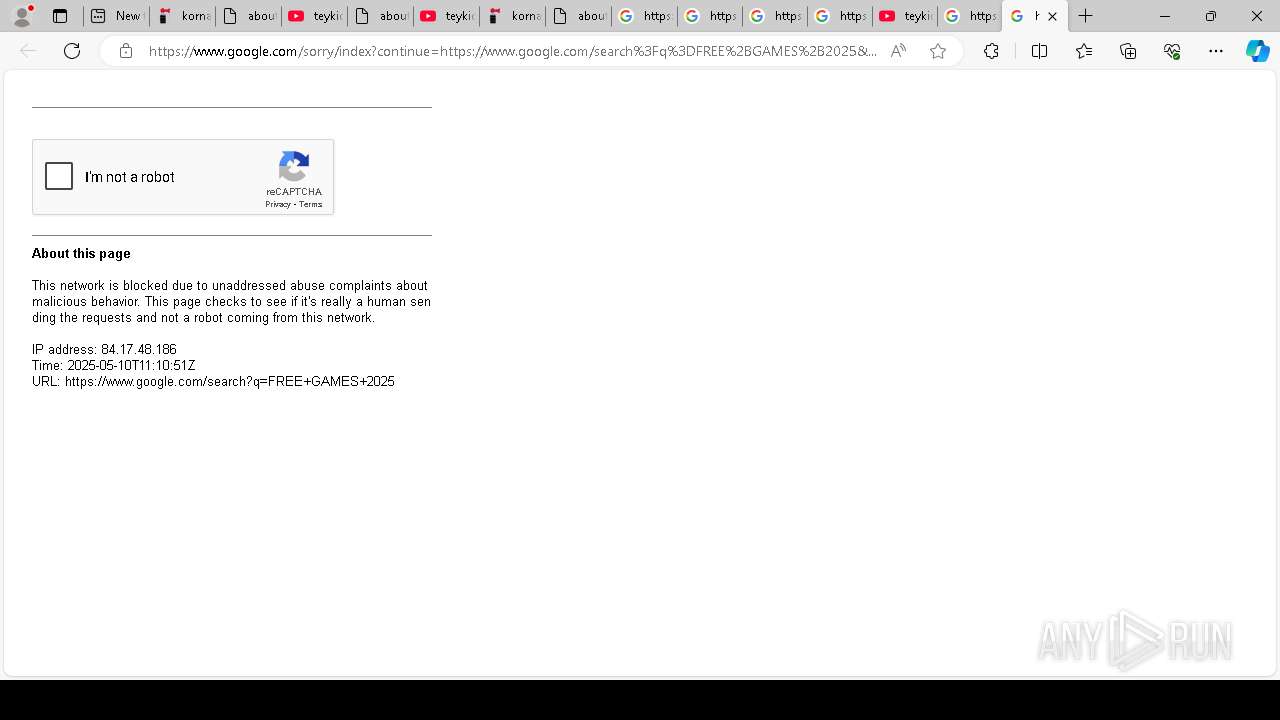
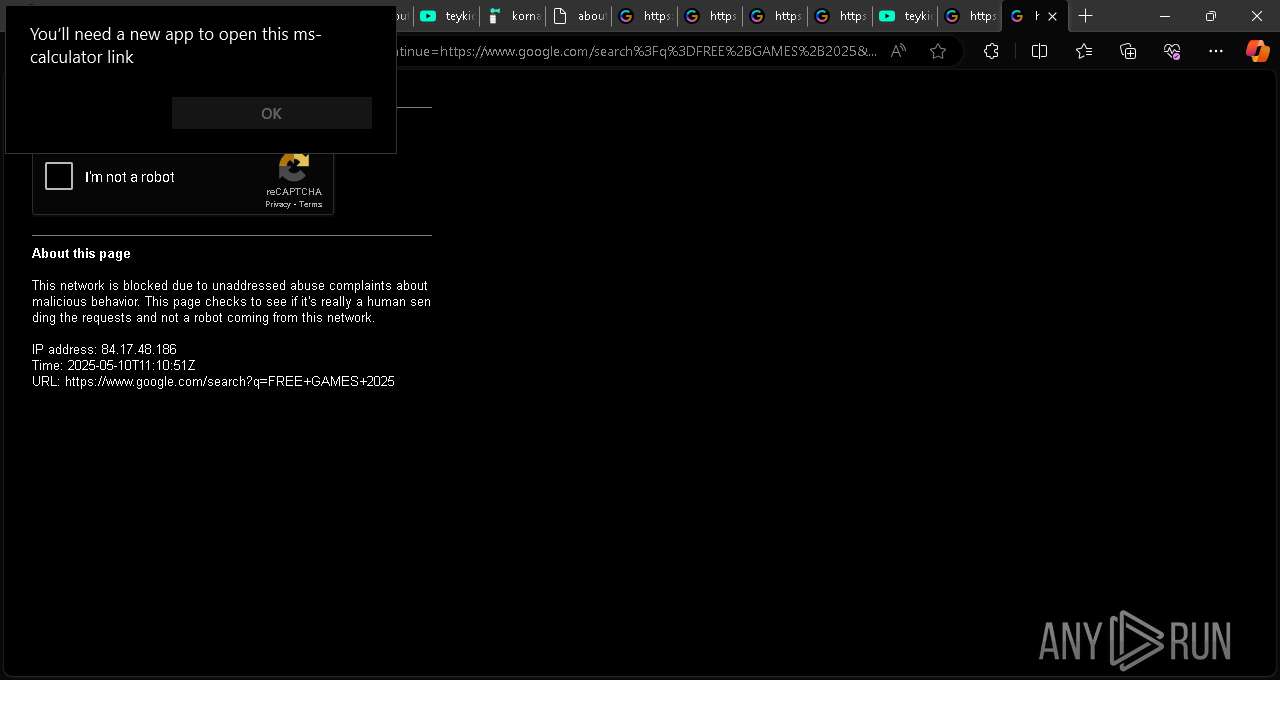
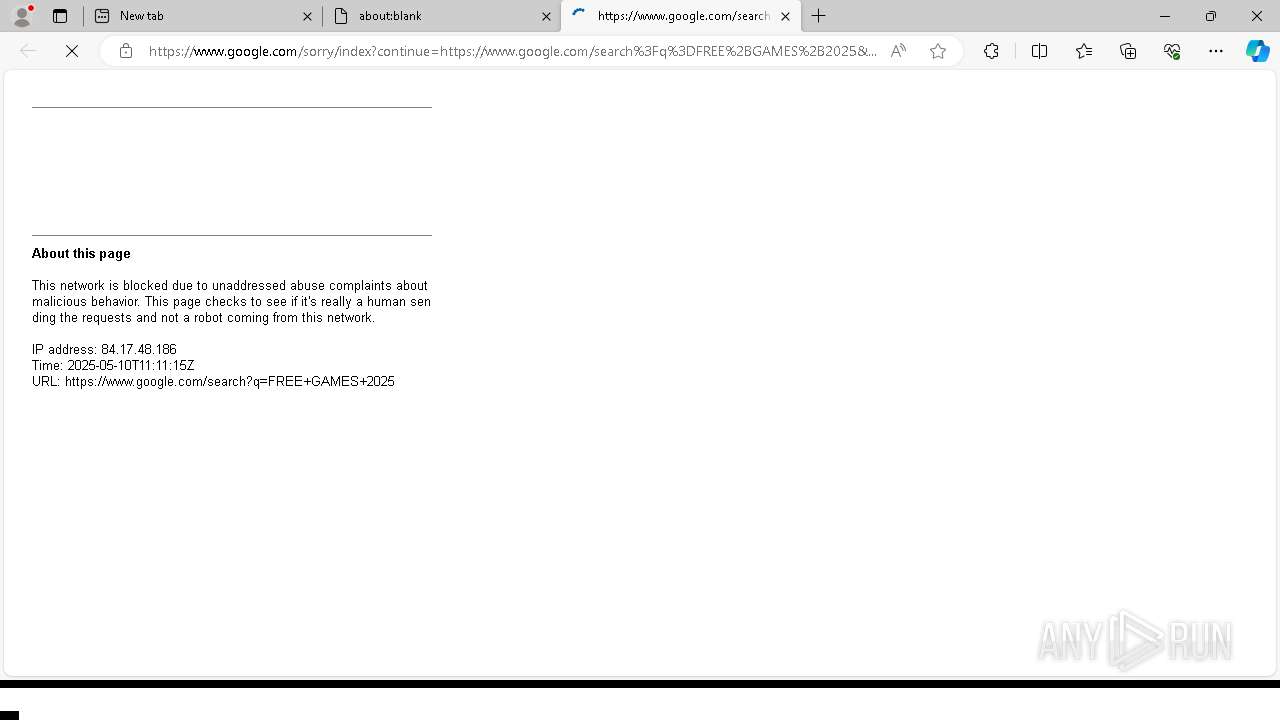
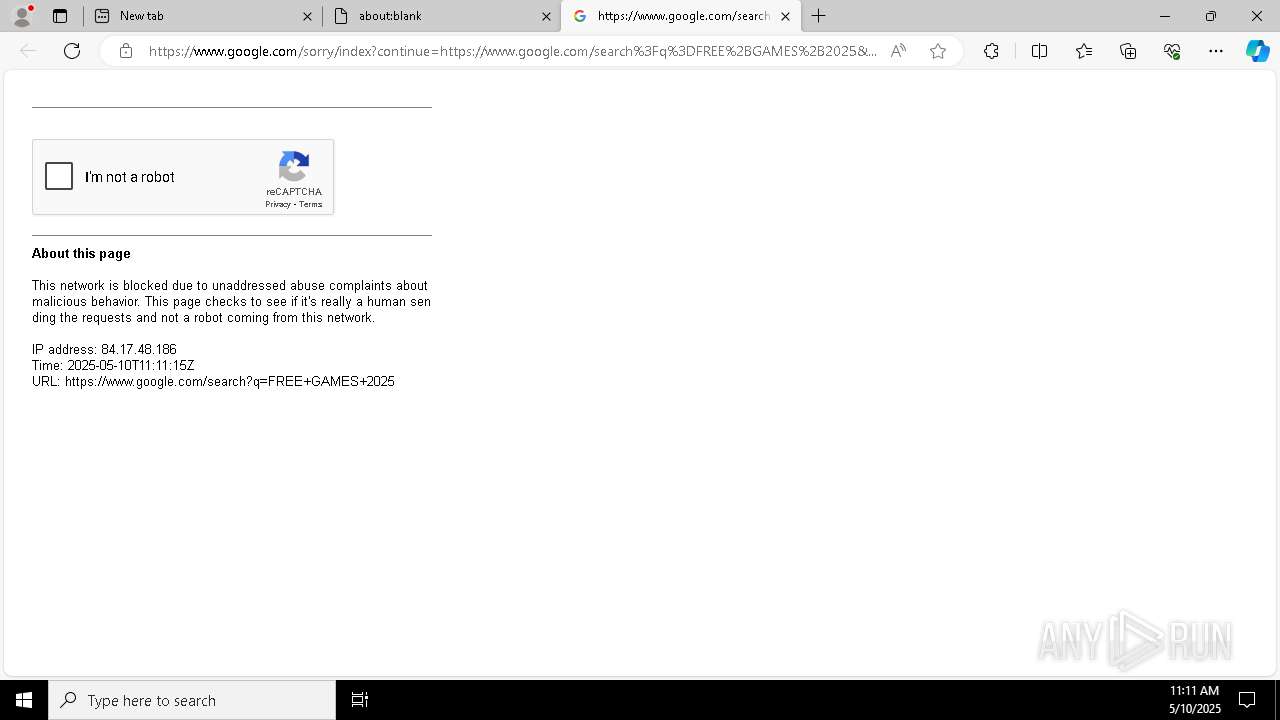
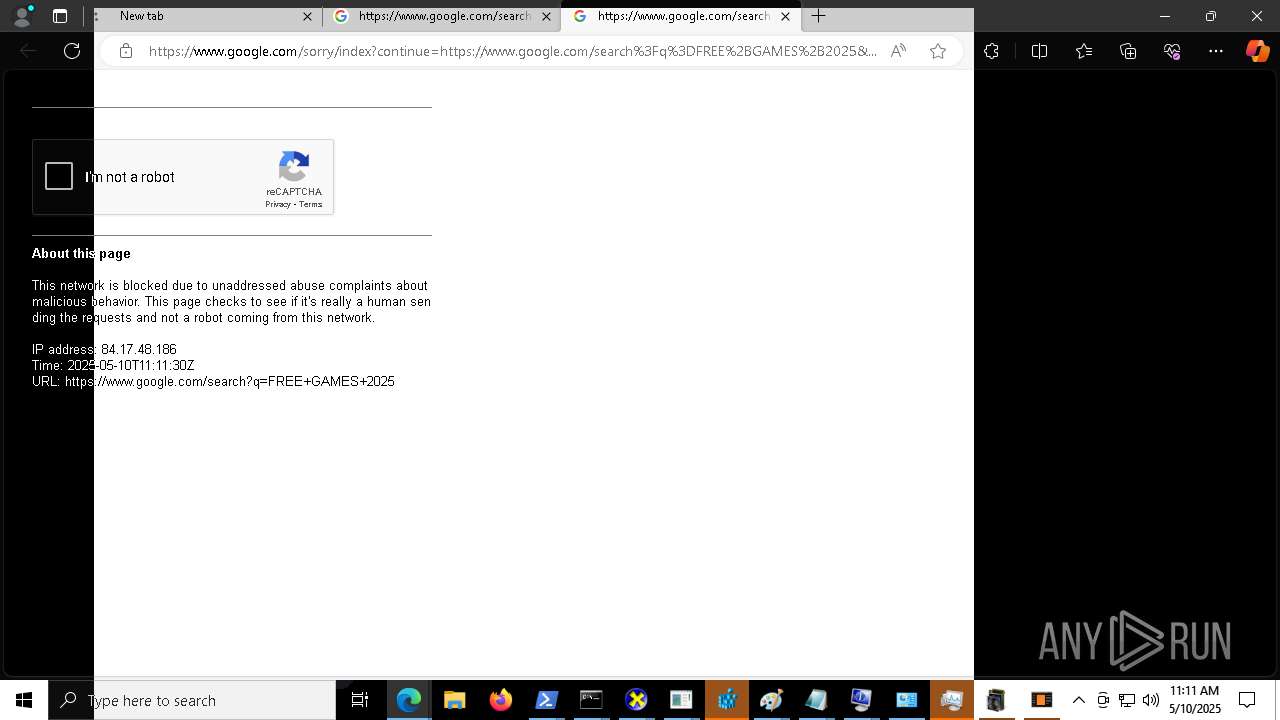
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |