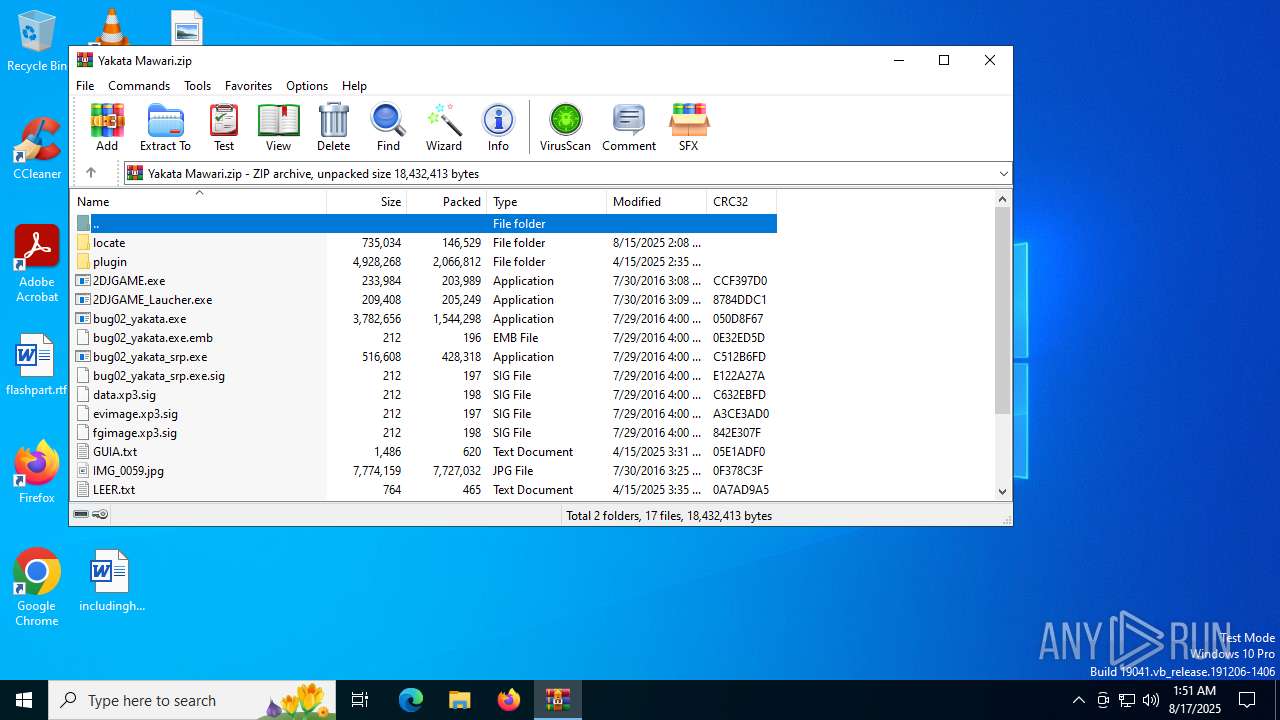
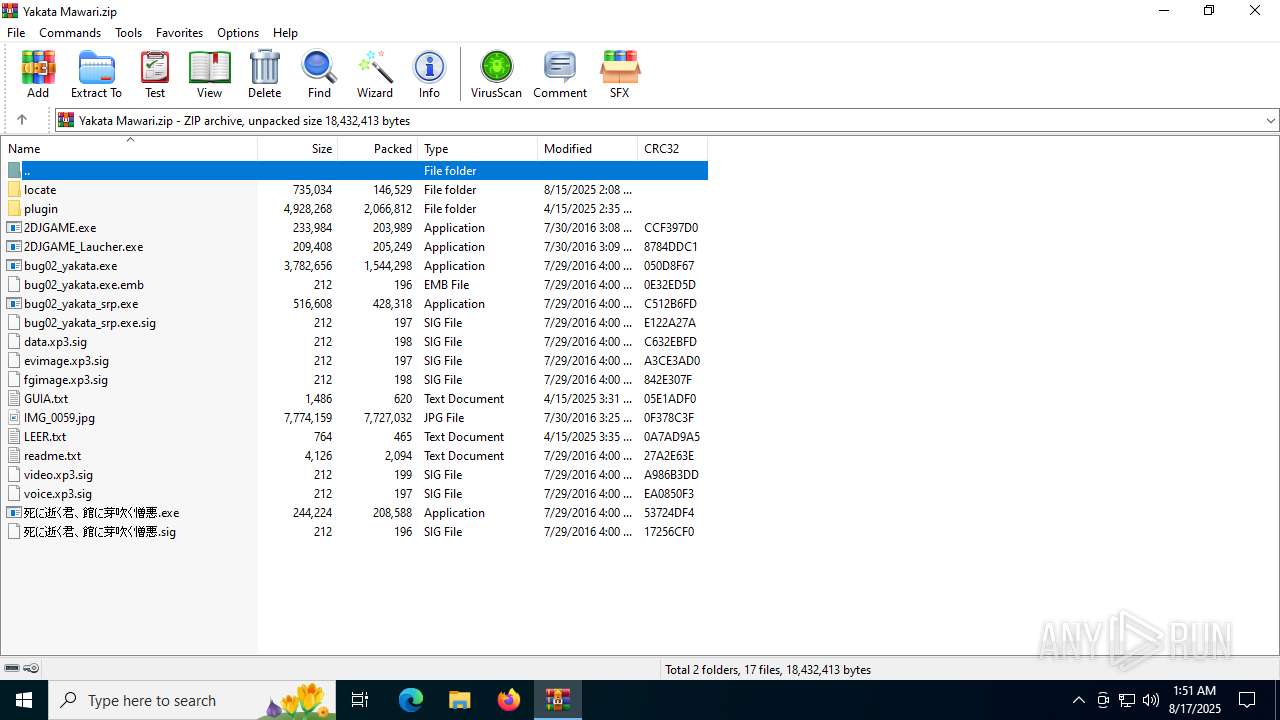
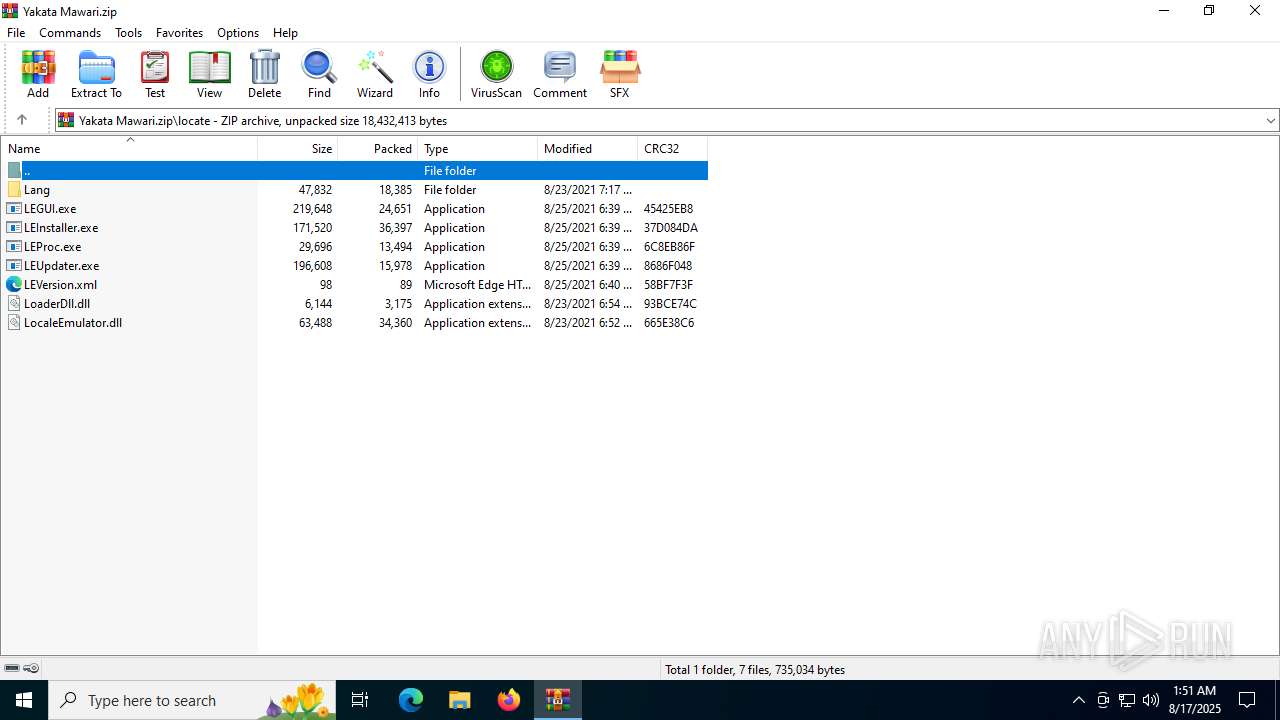
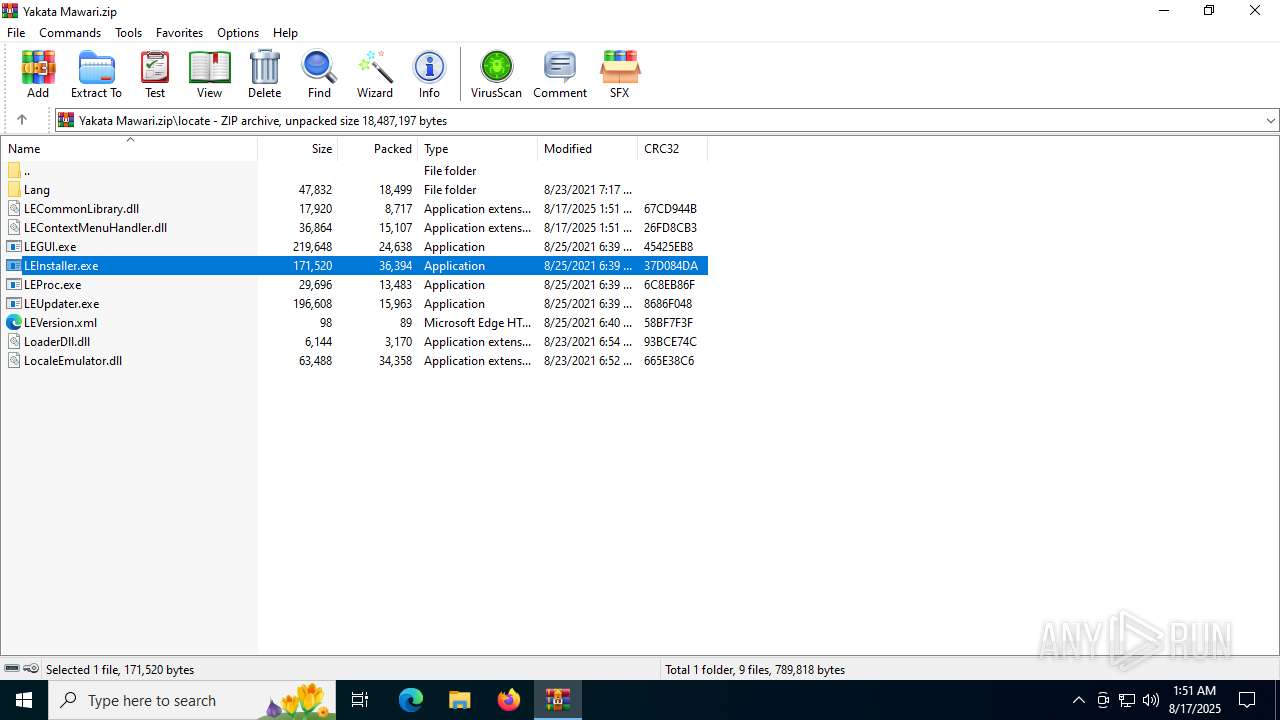
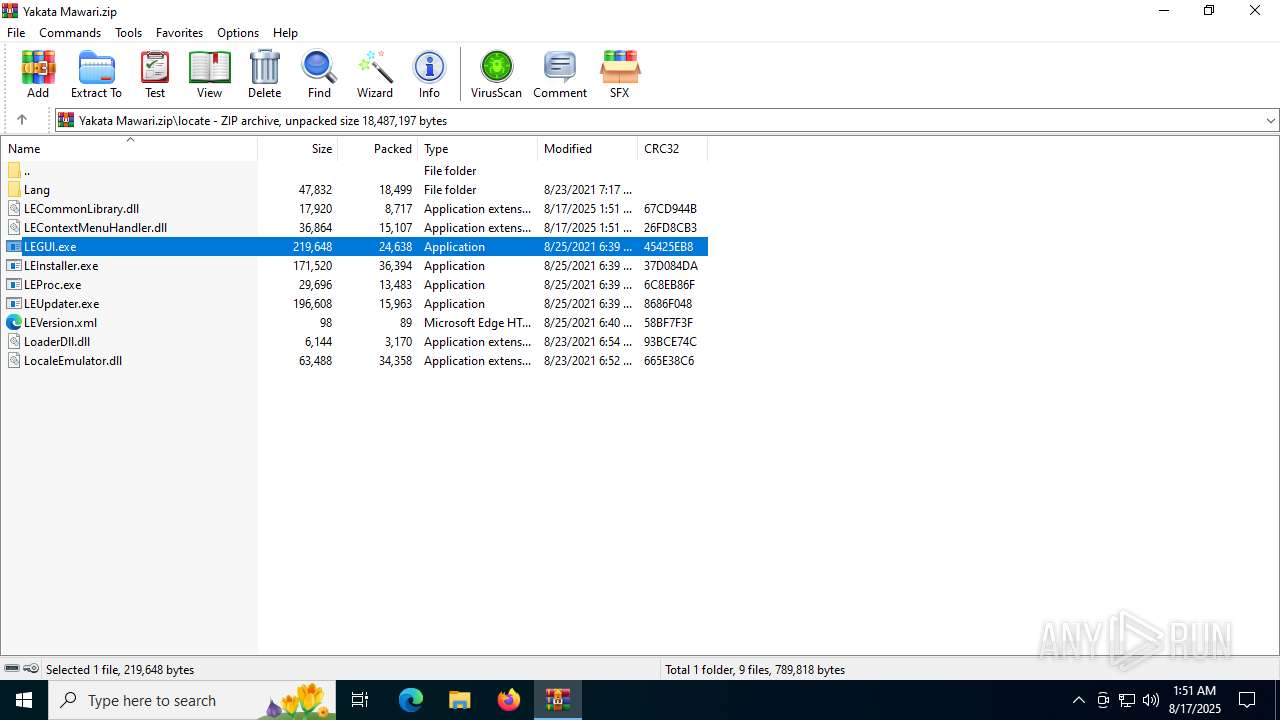
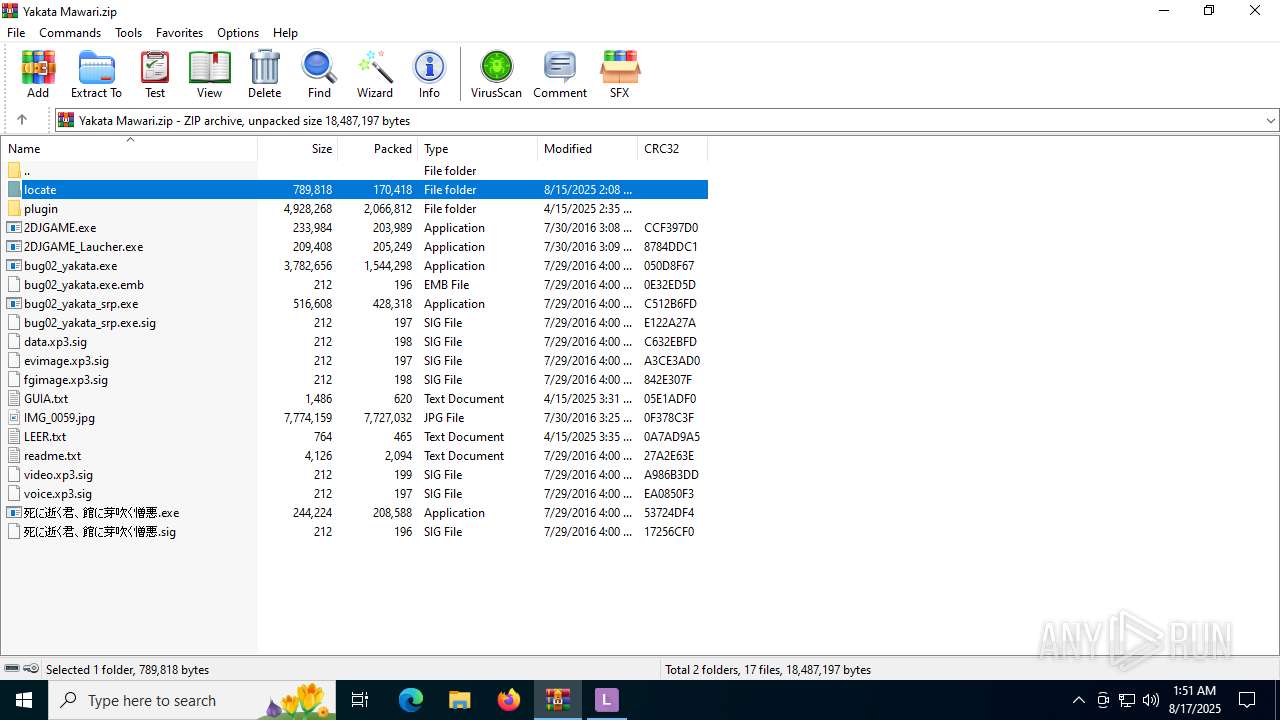
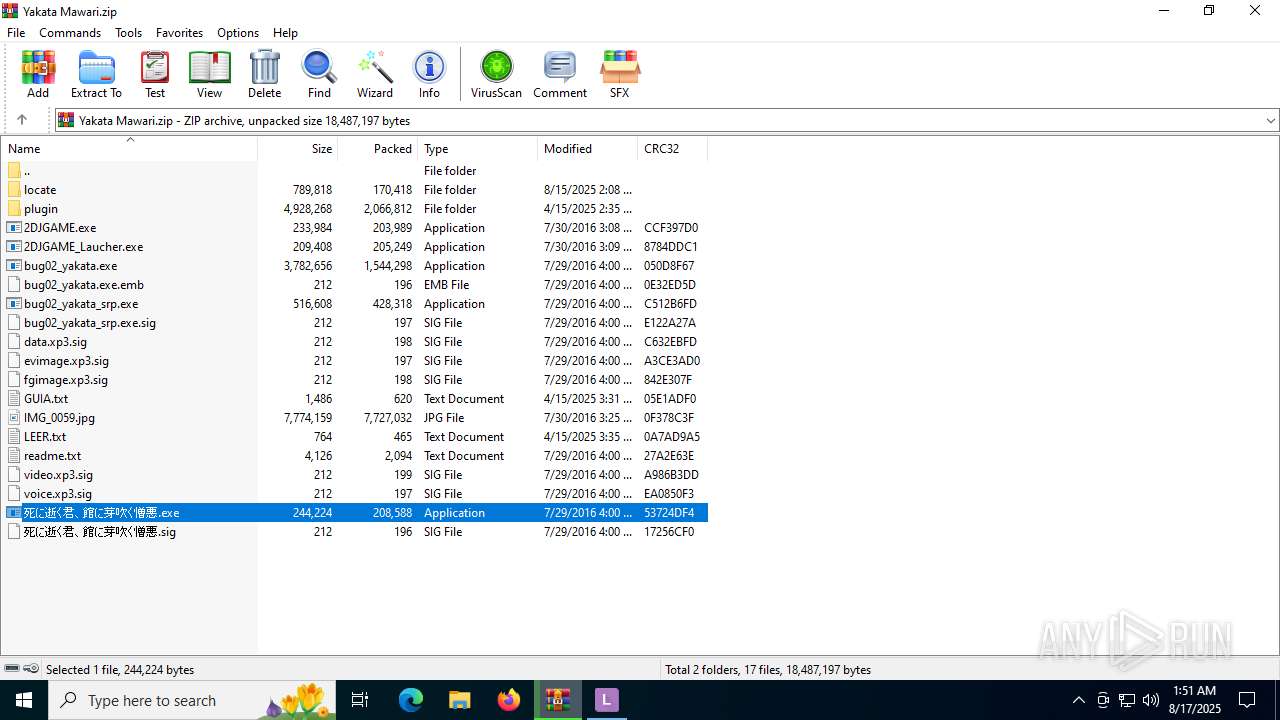
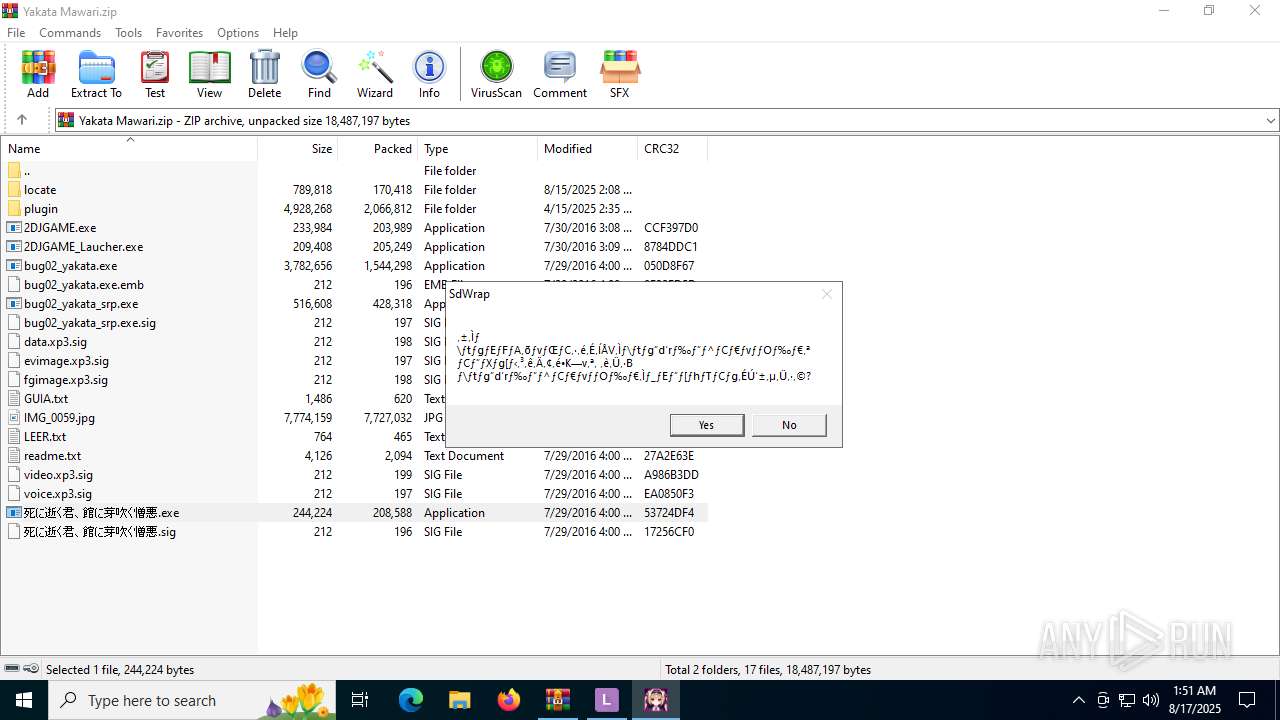
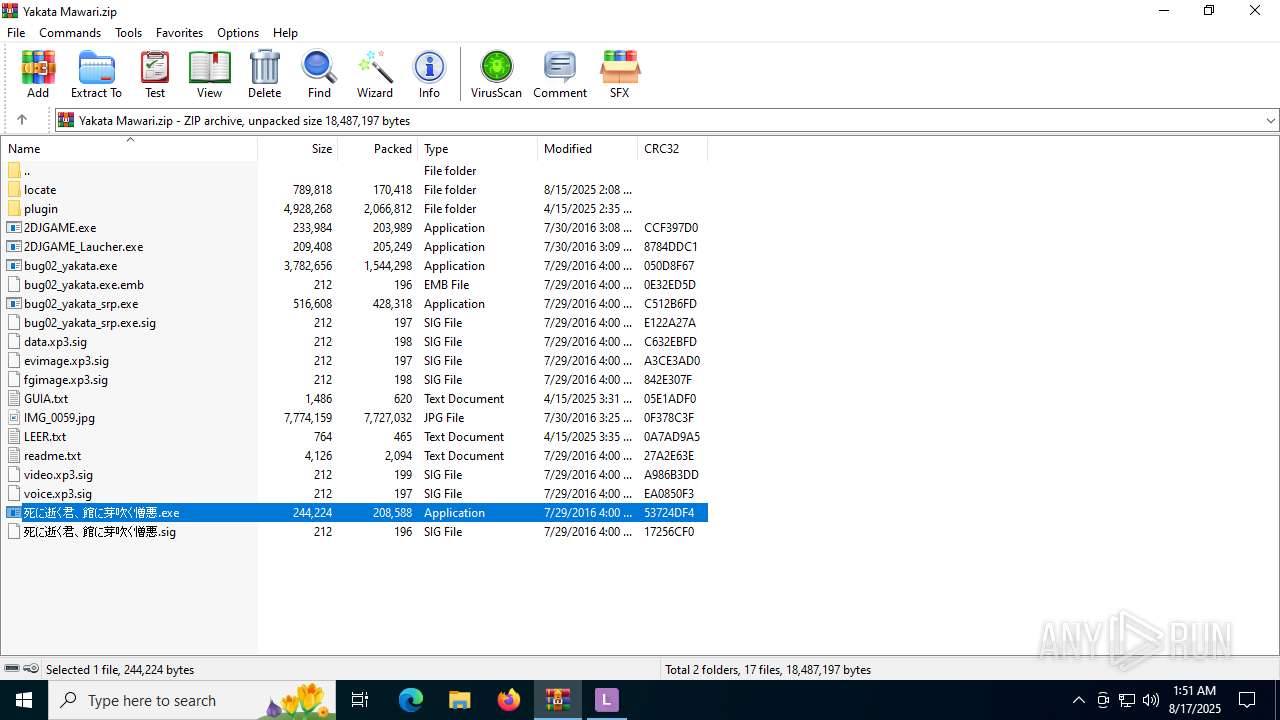
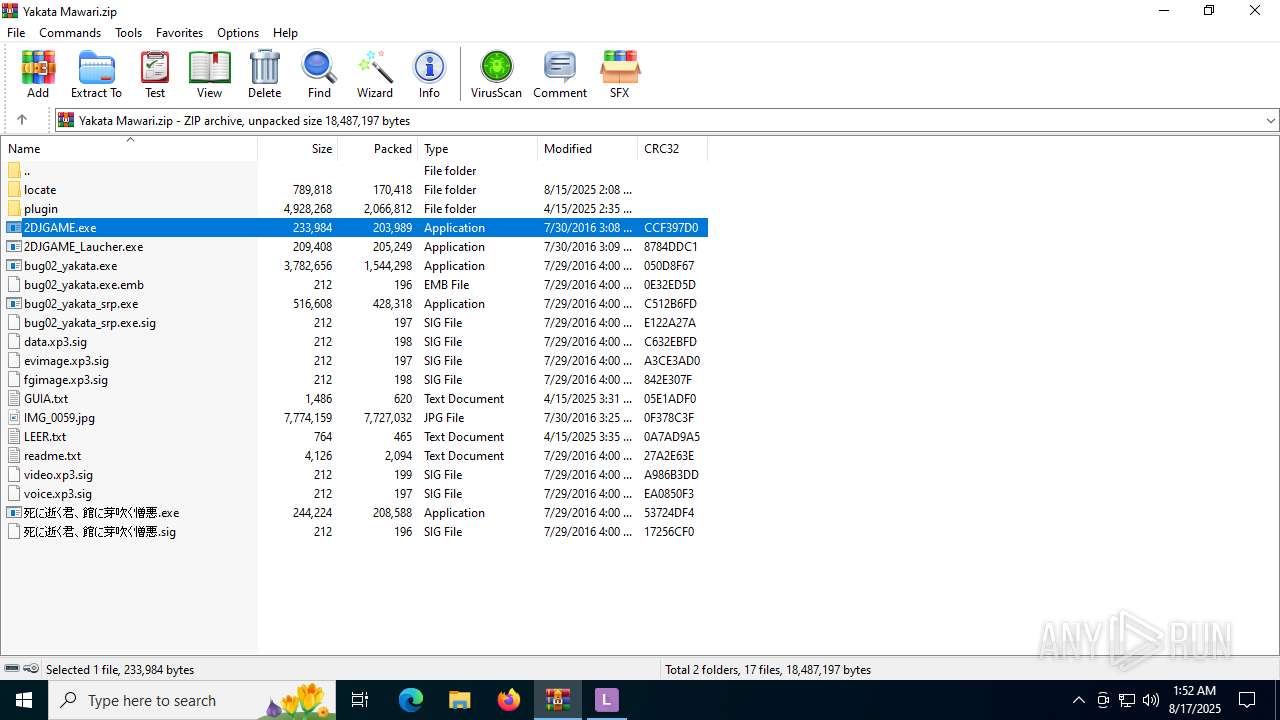
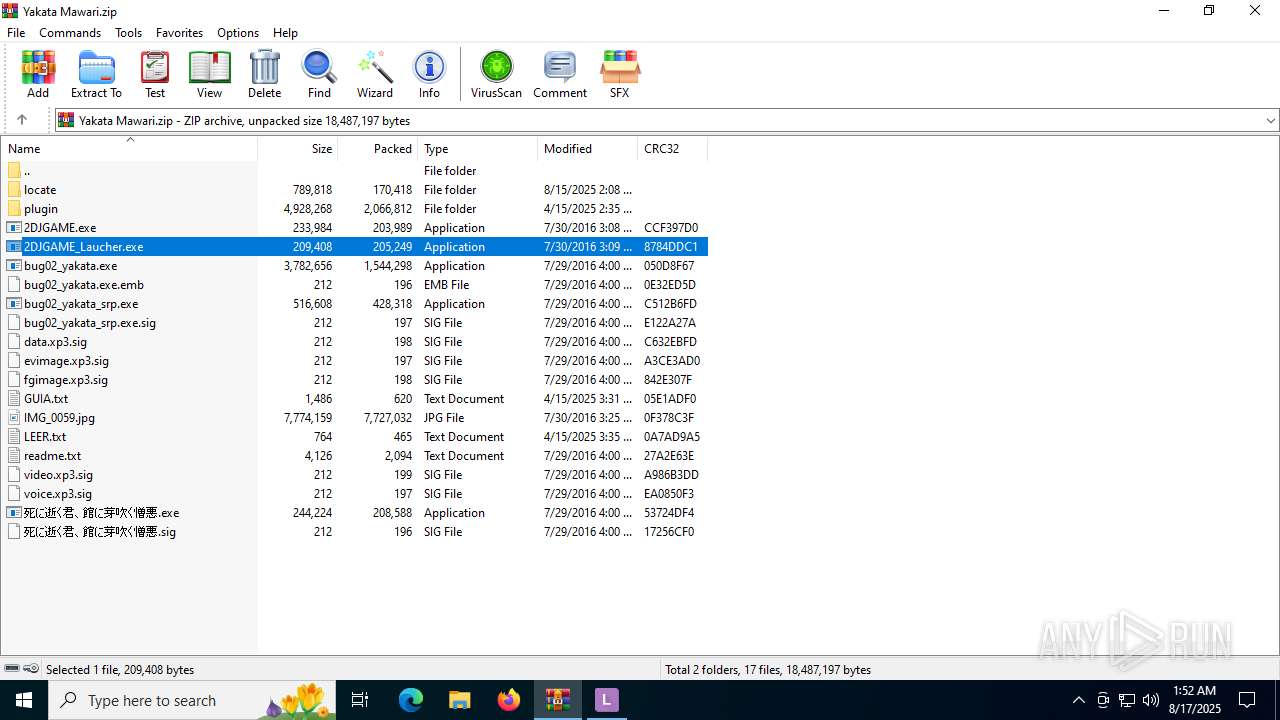
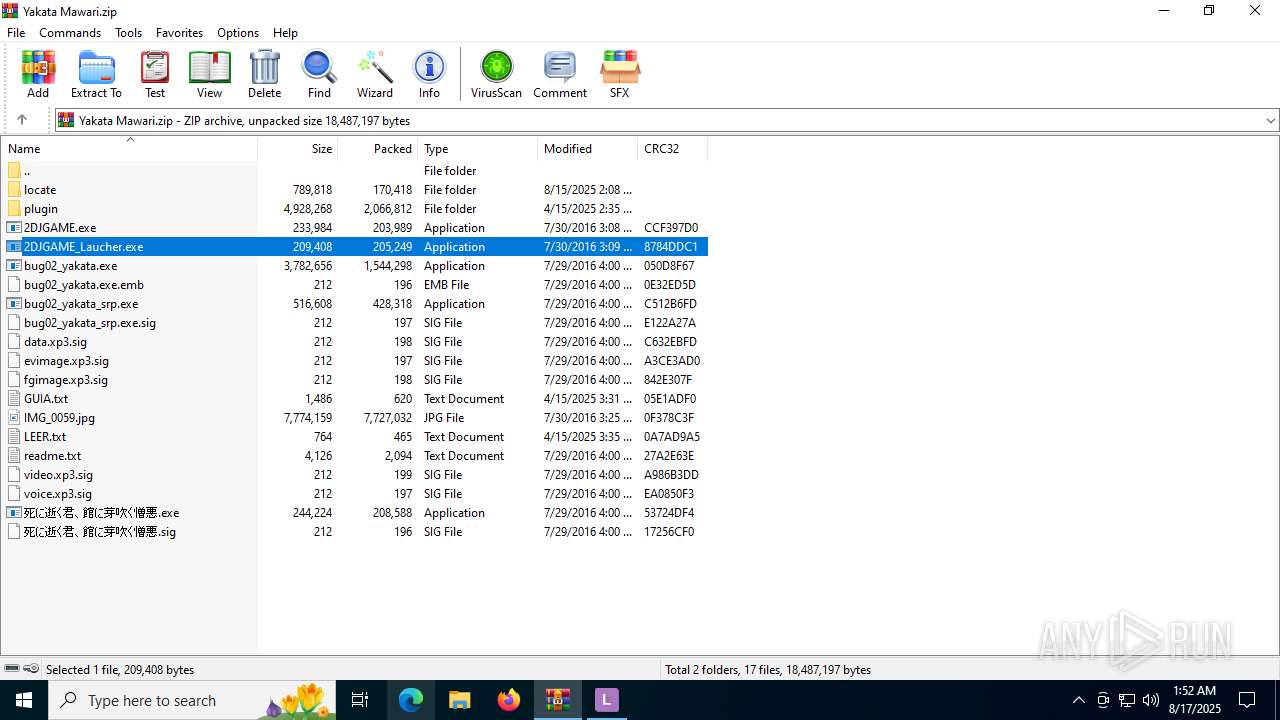
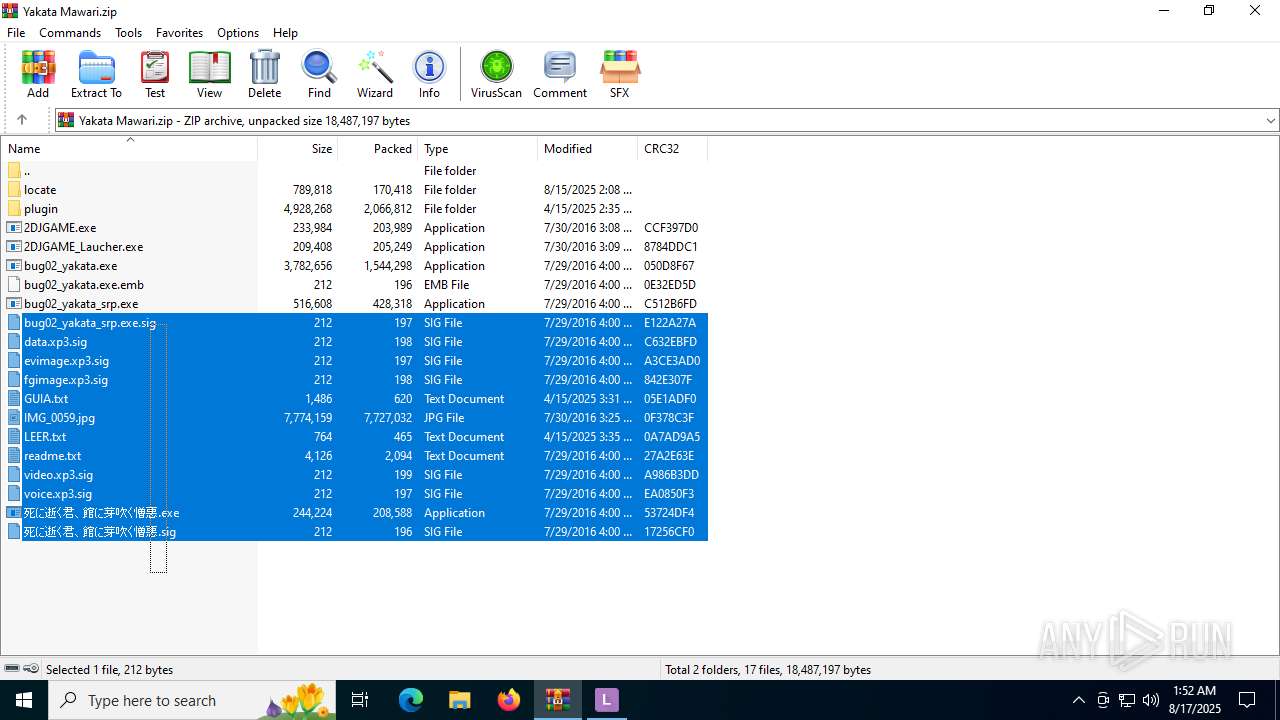
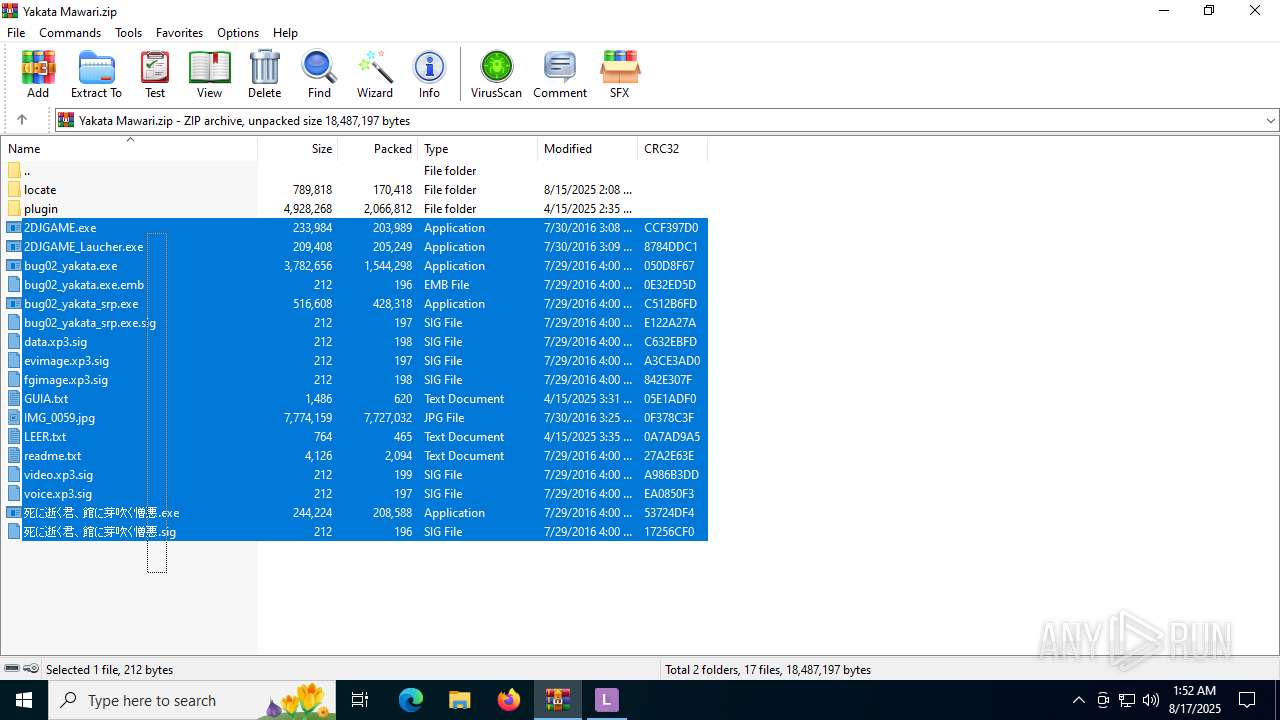
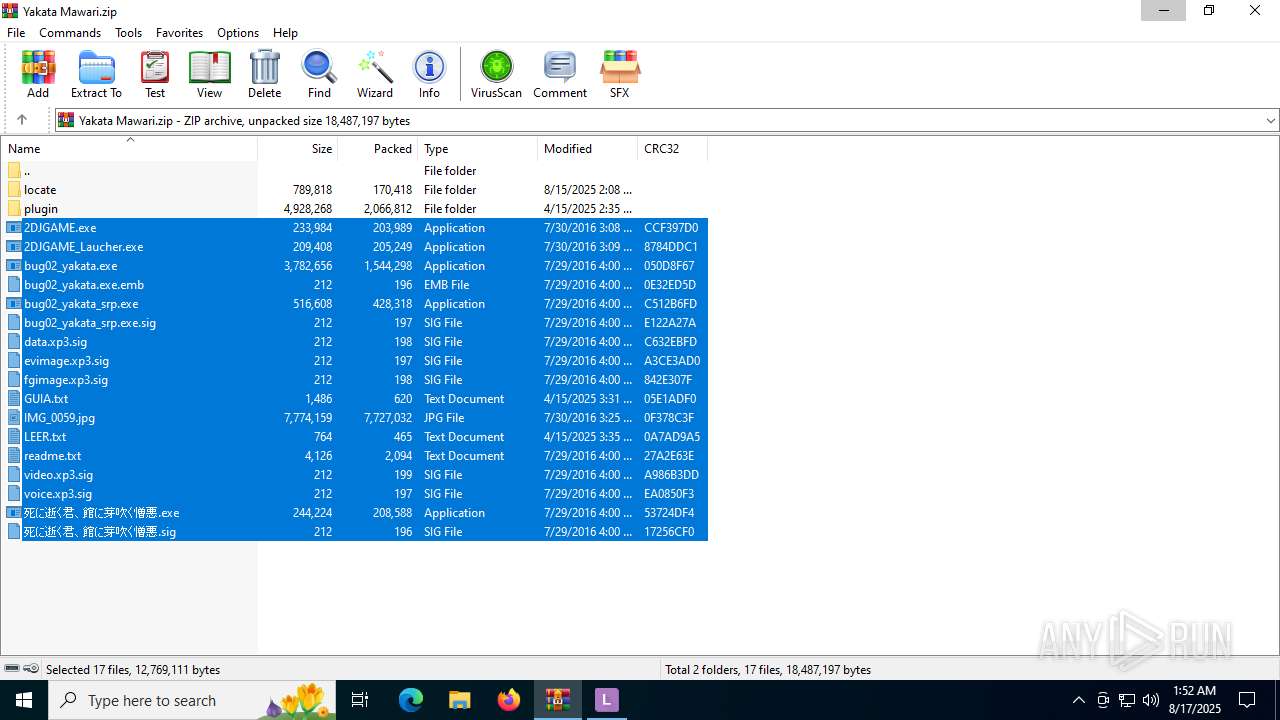
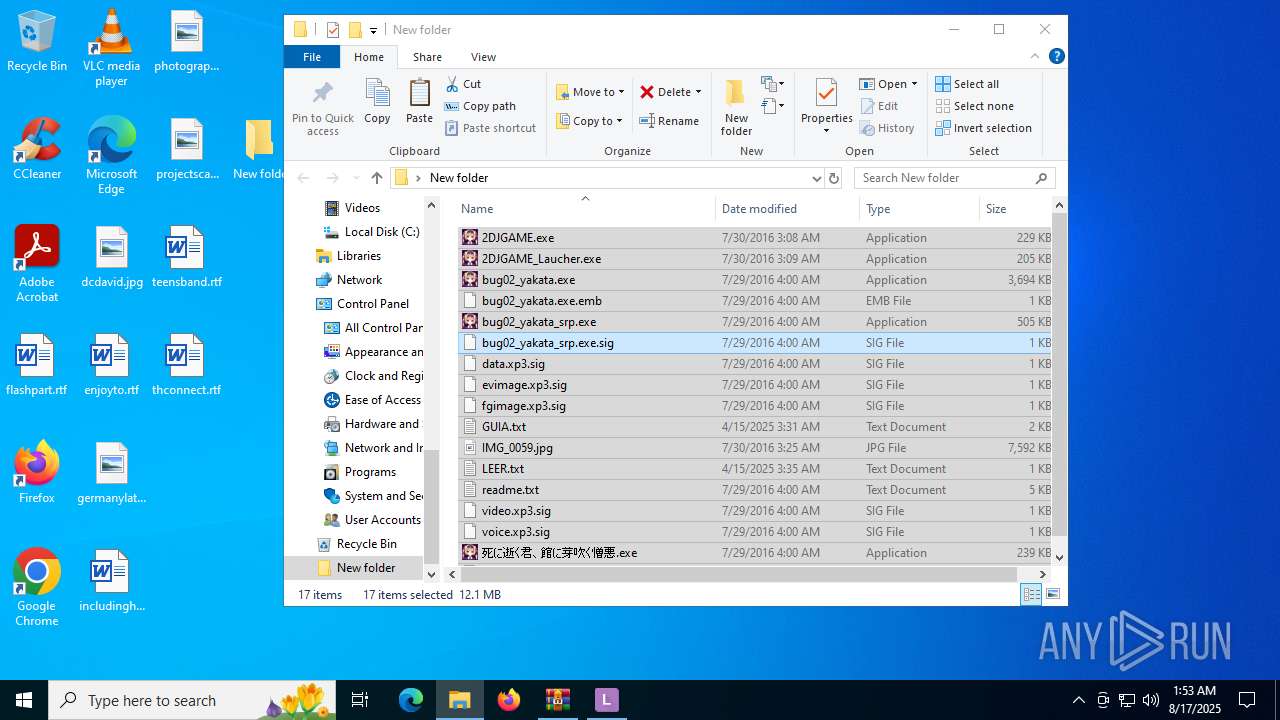
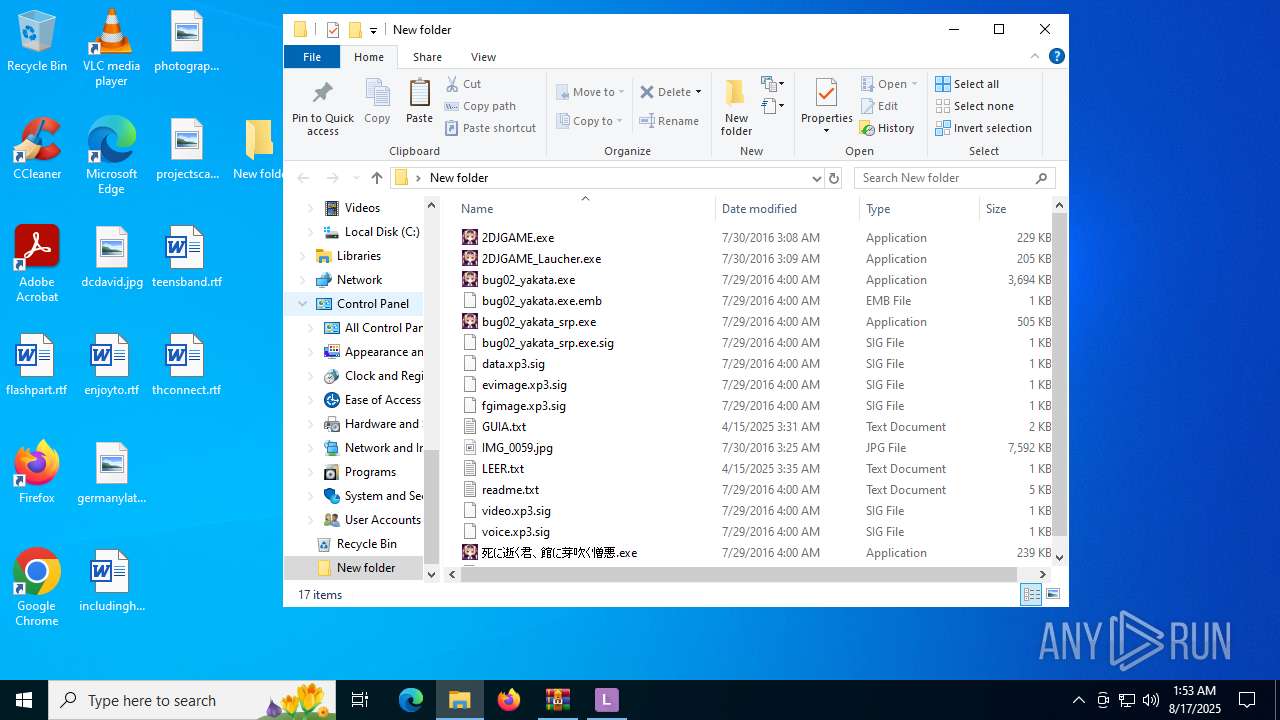
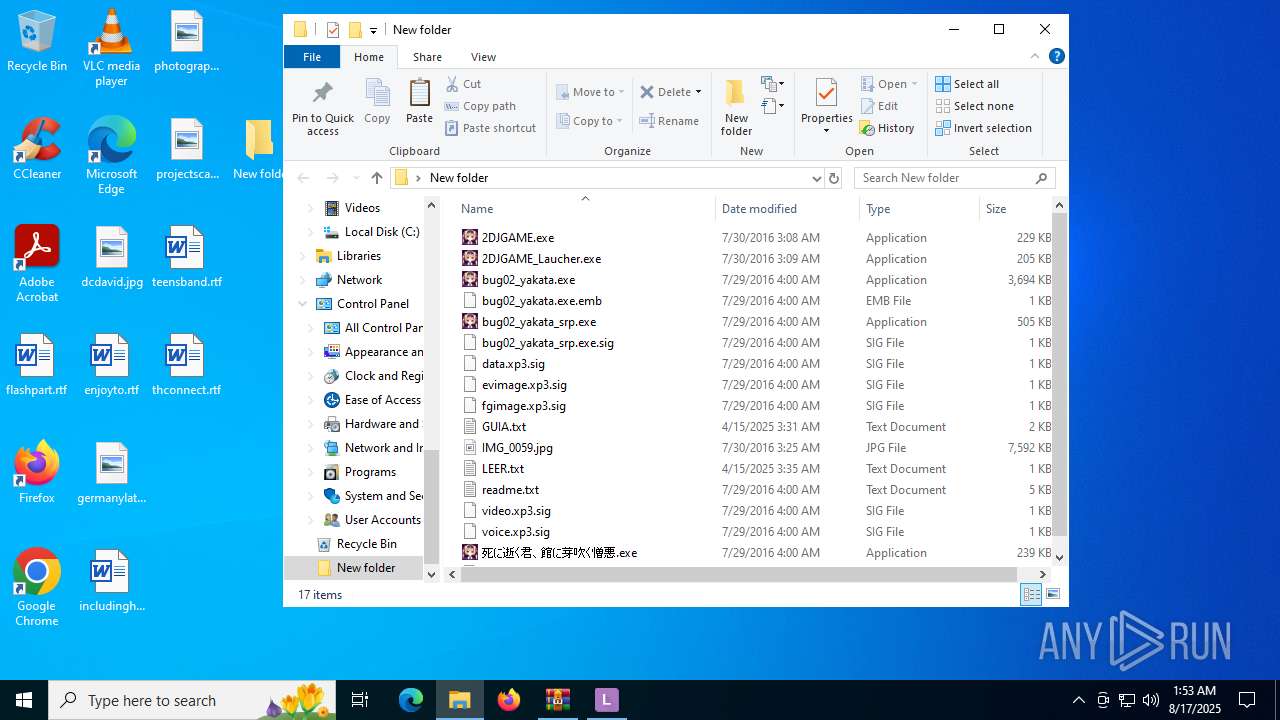
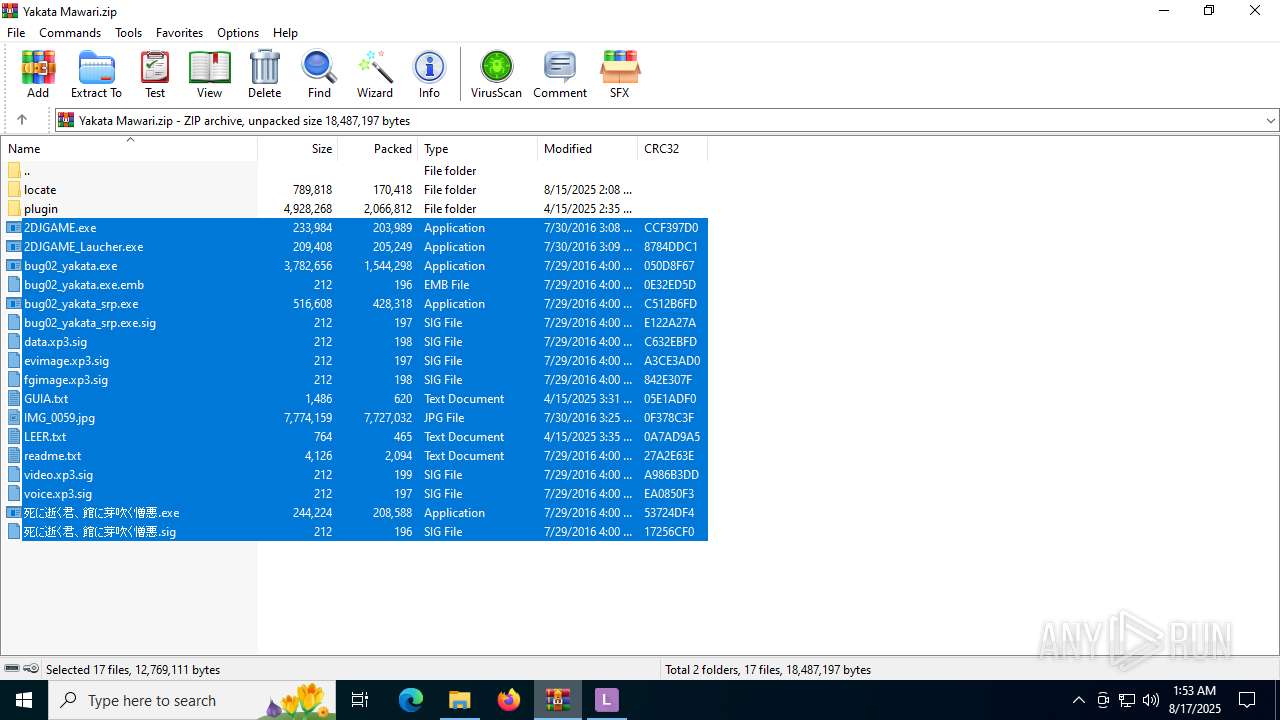
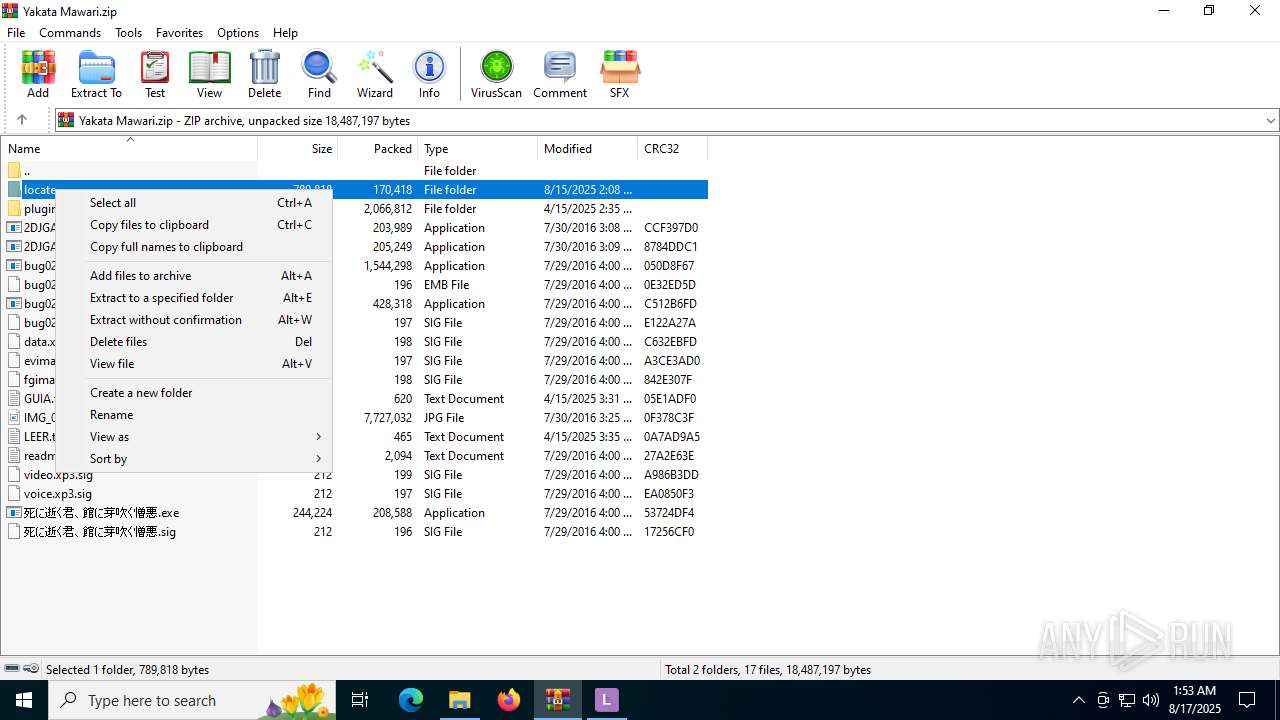
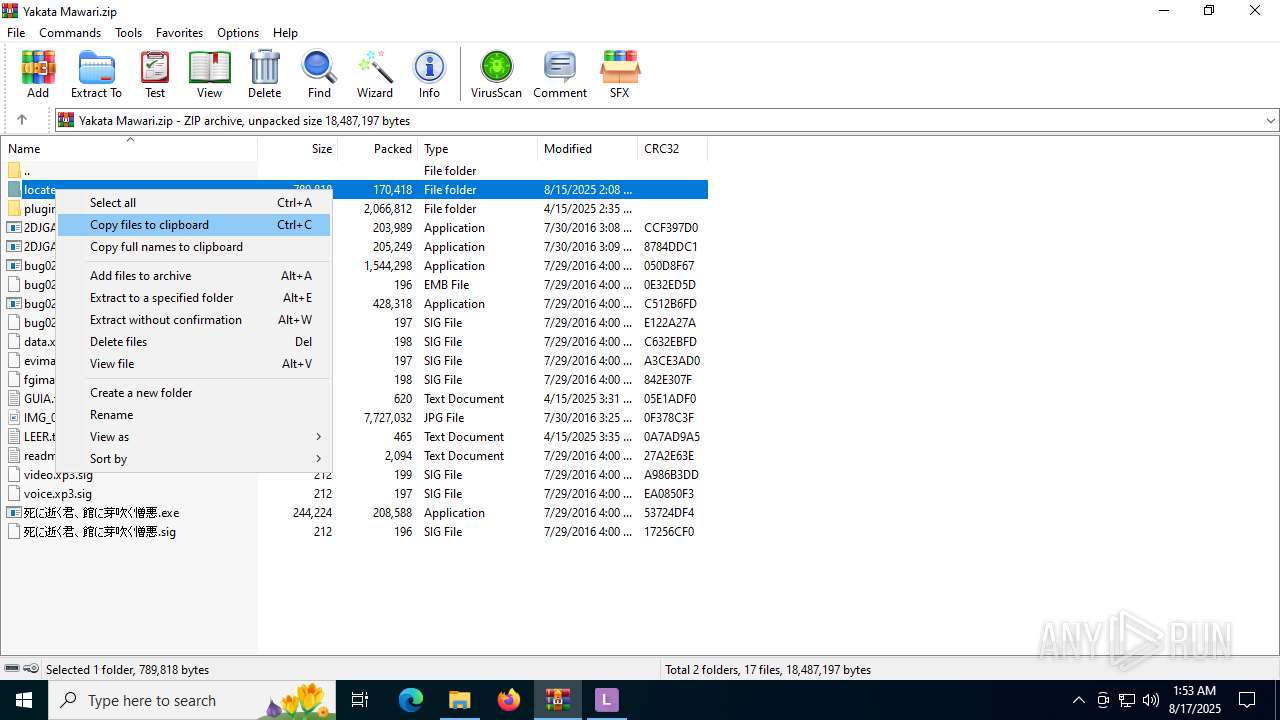
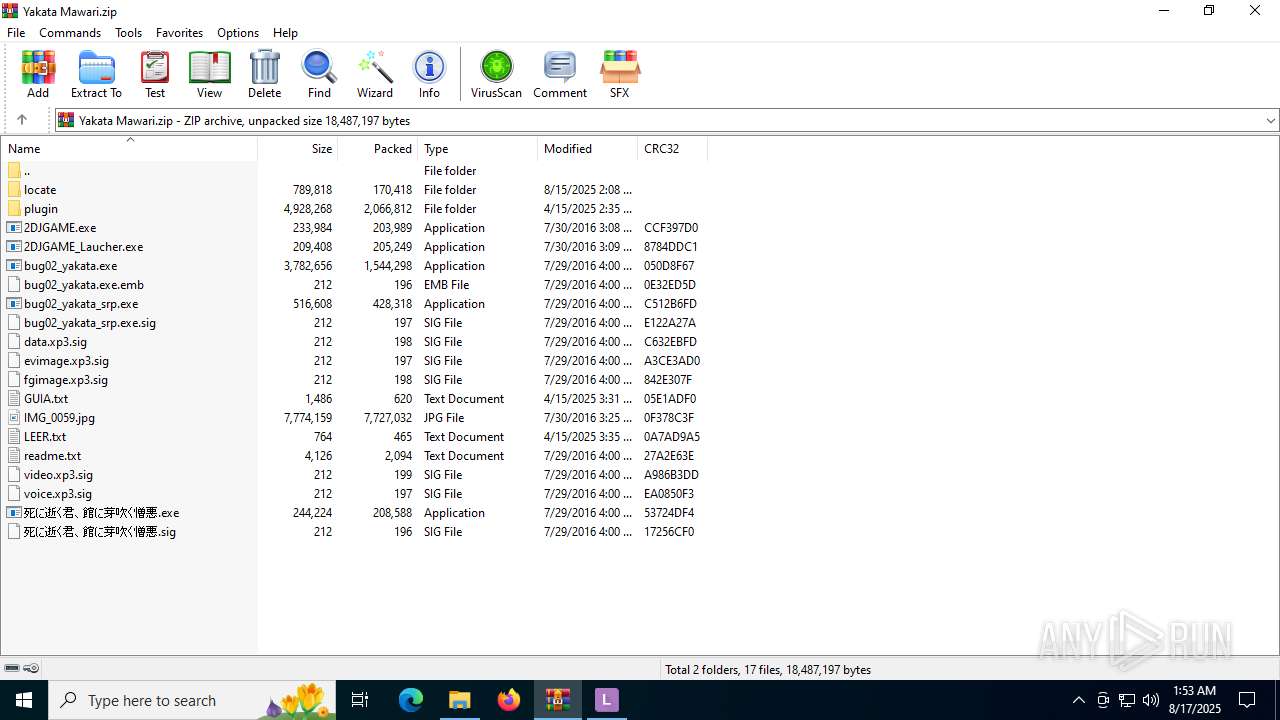
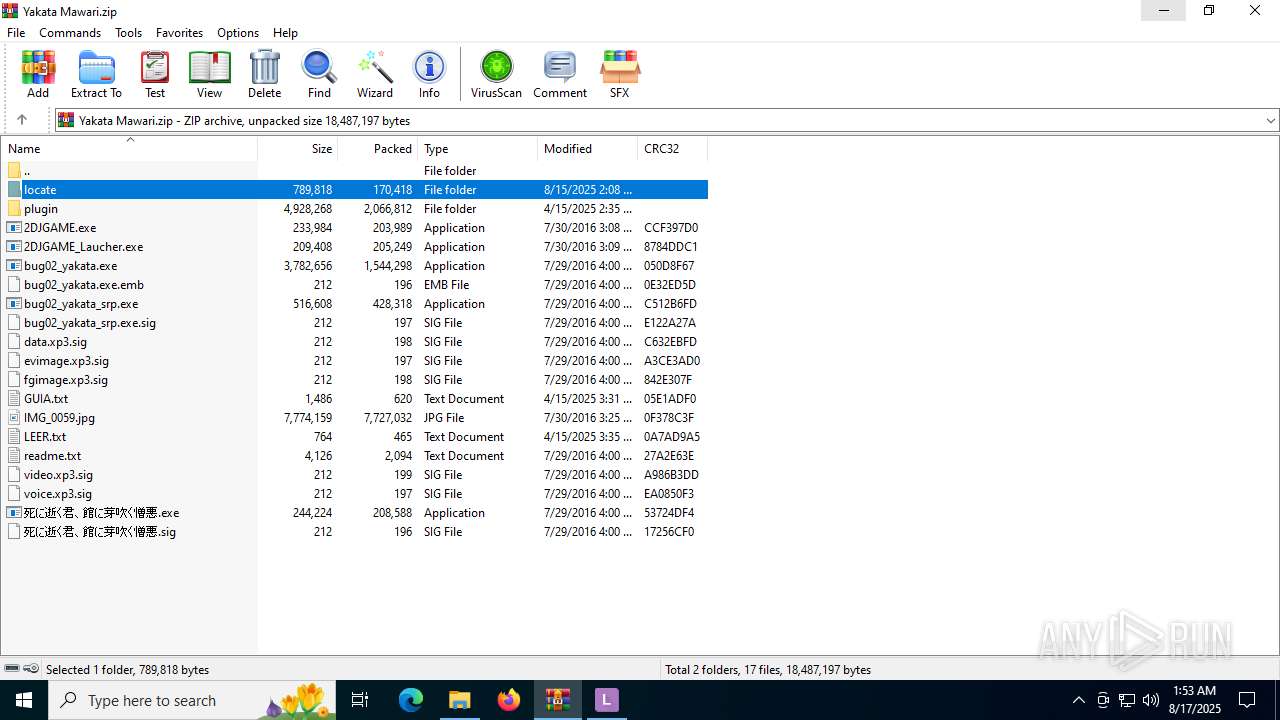
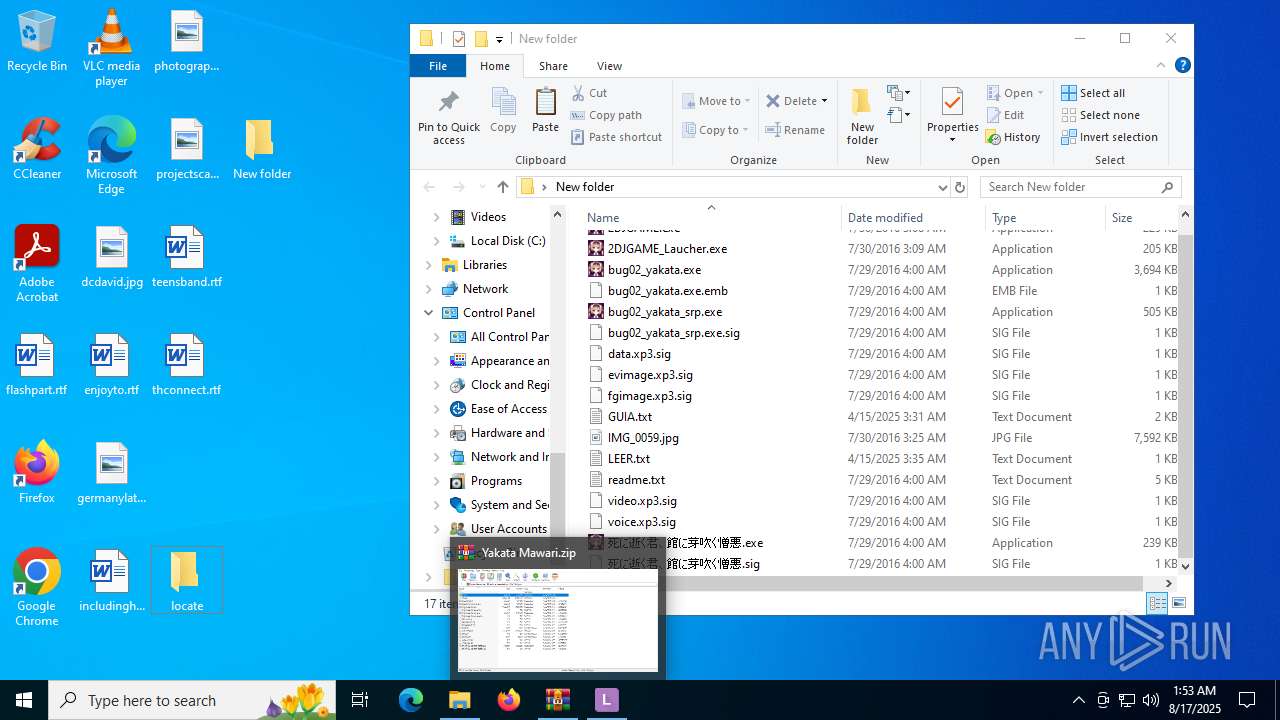
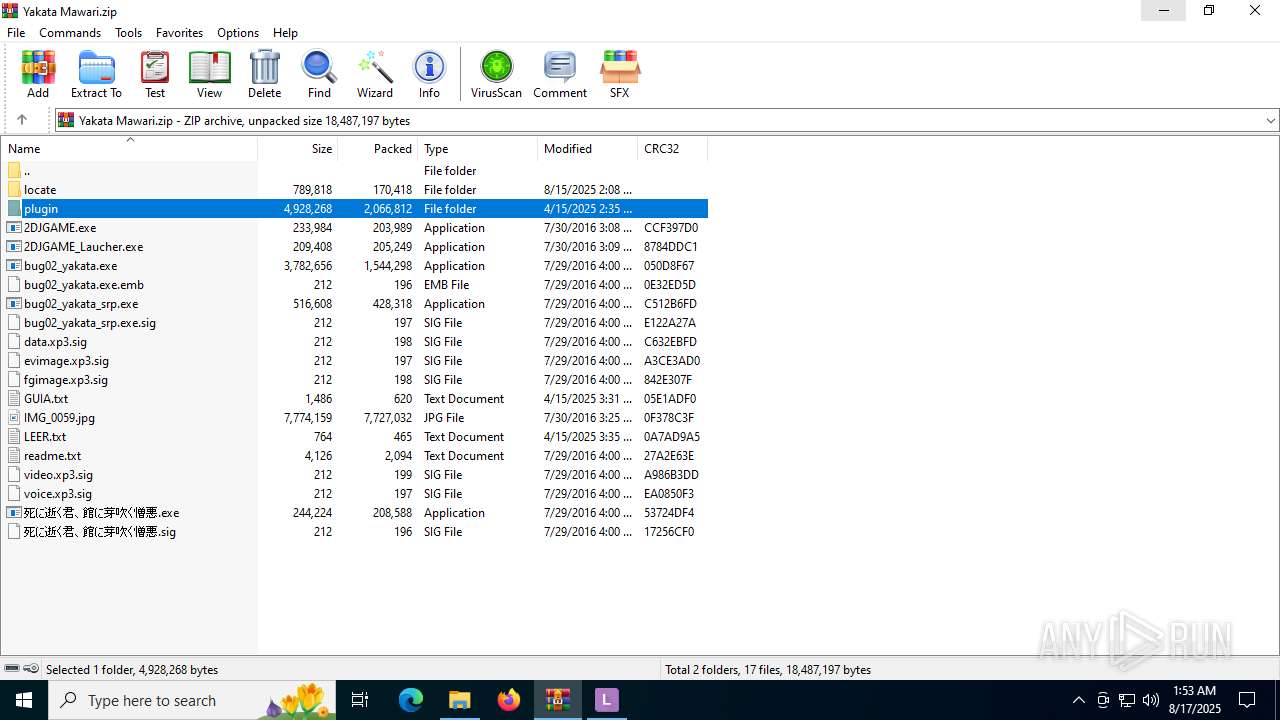
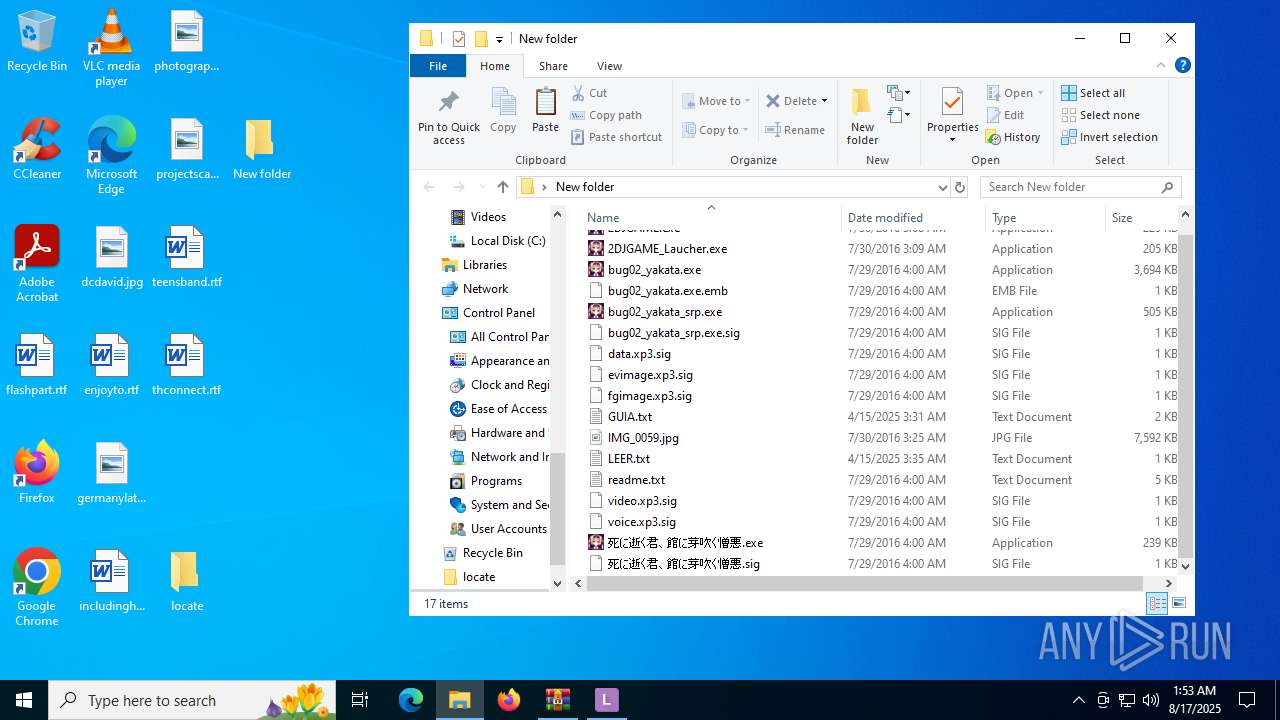
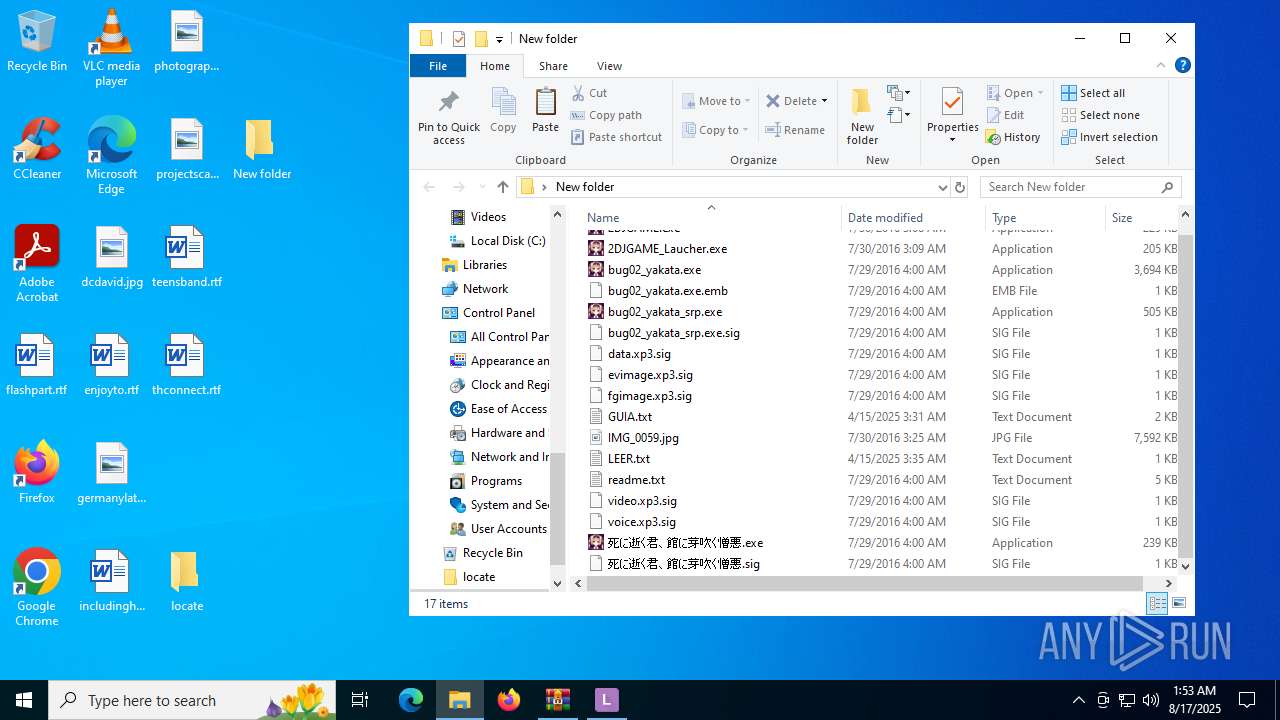
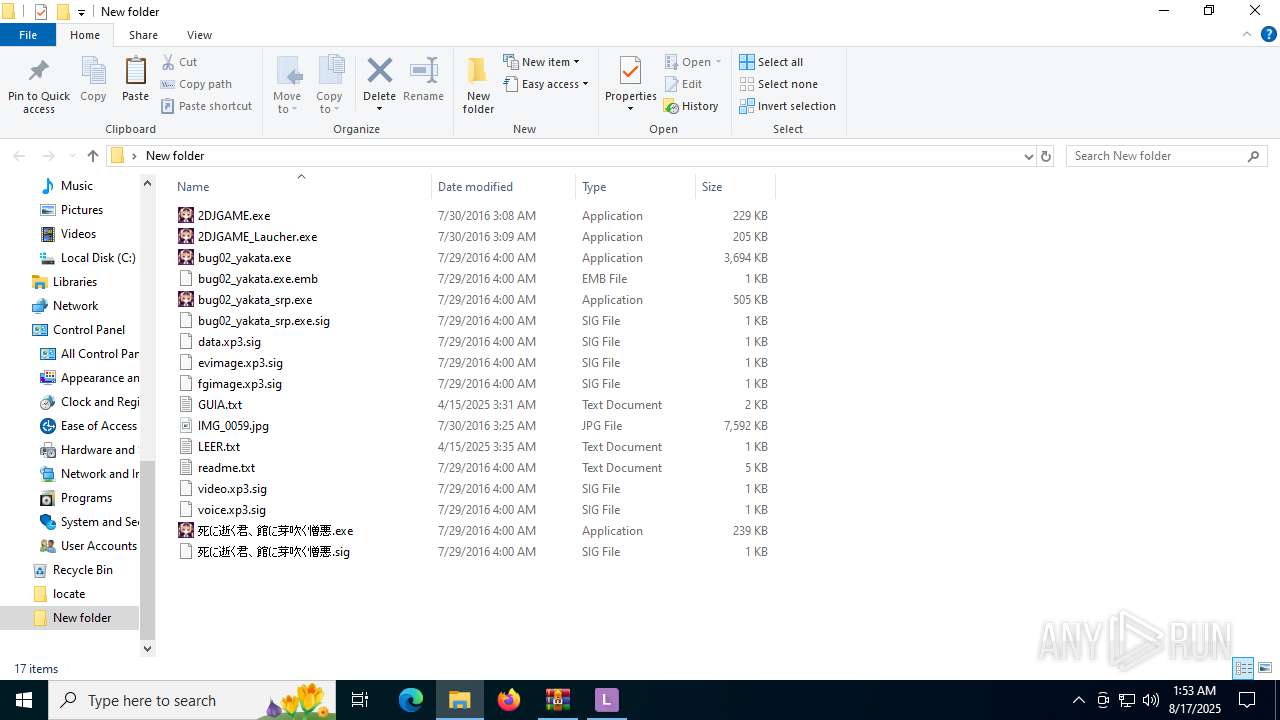
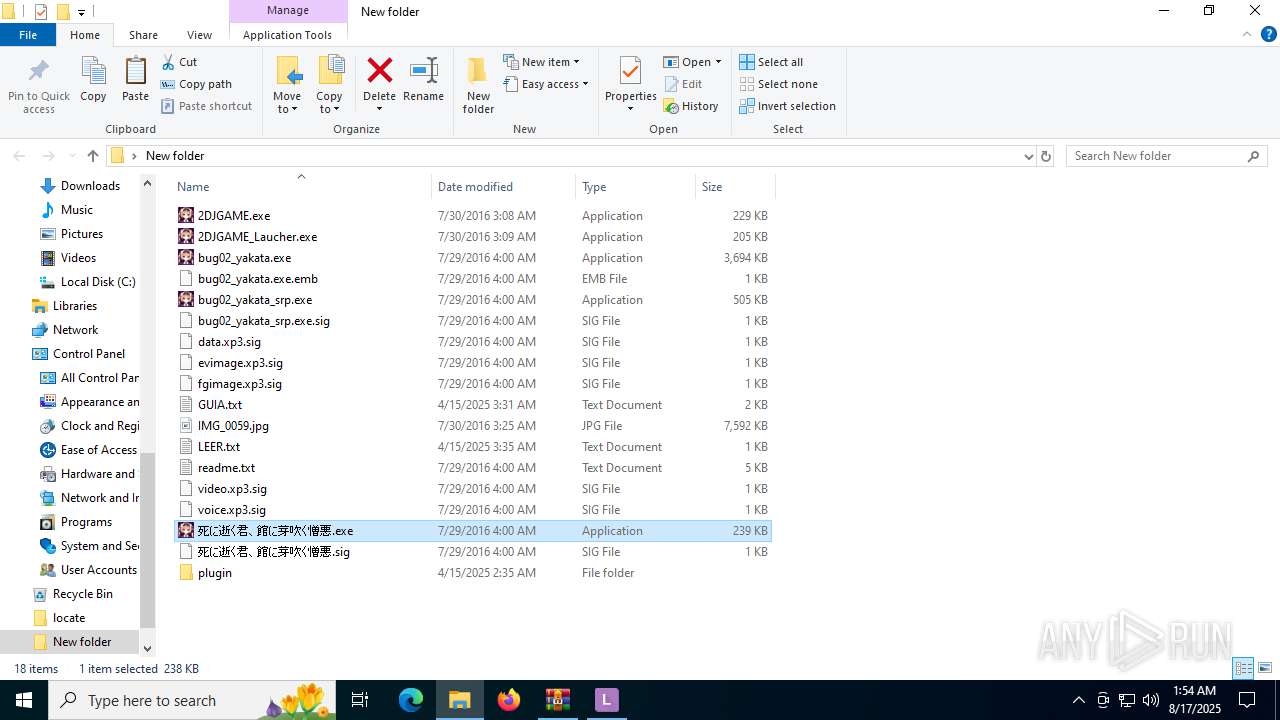
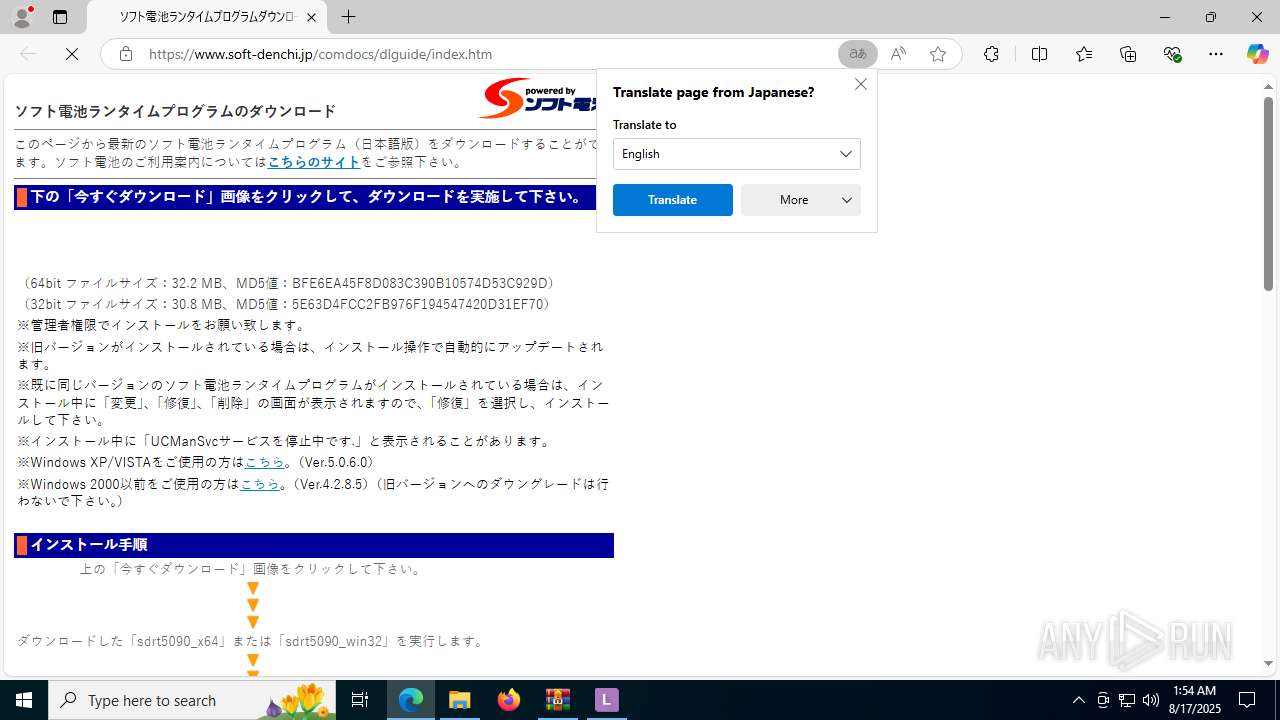
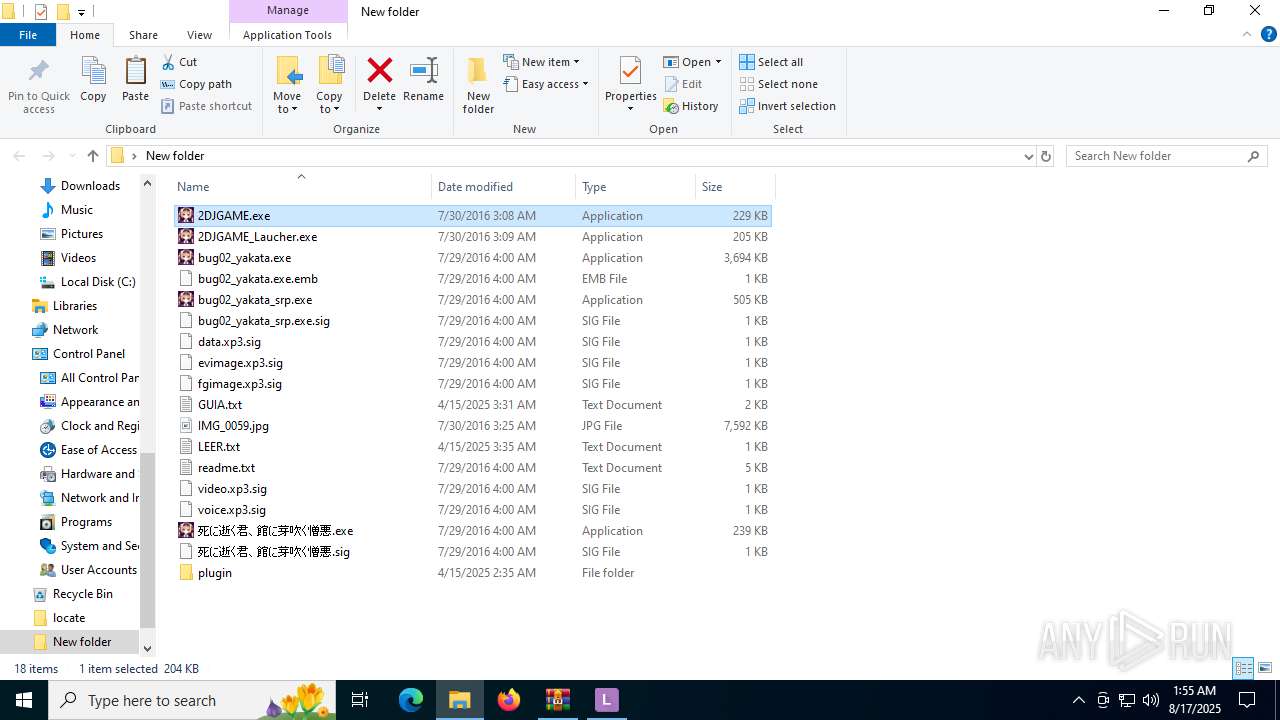
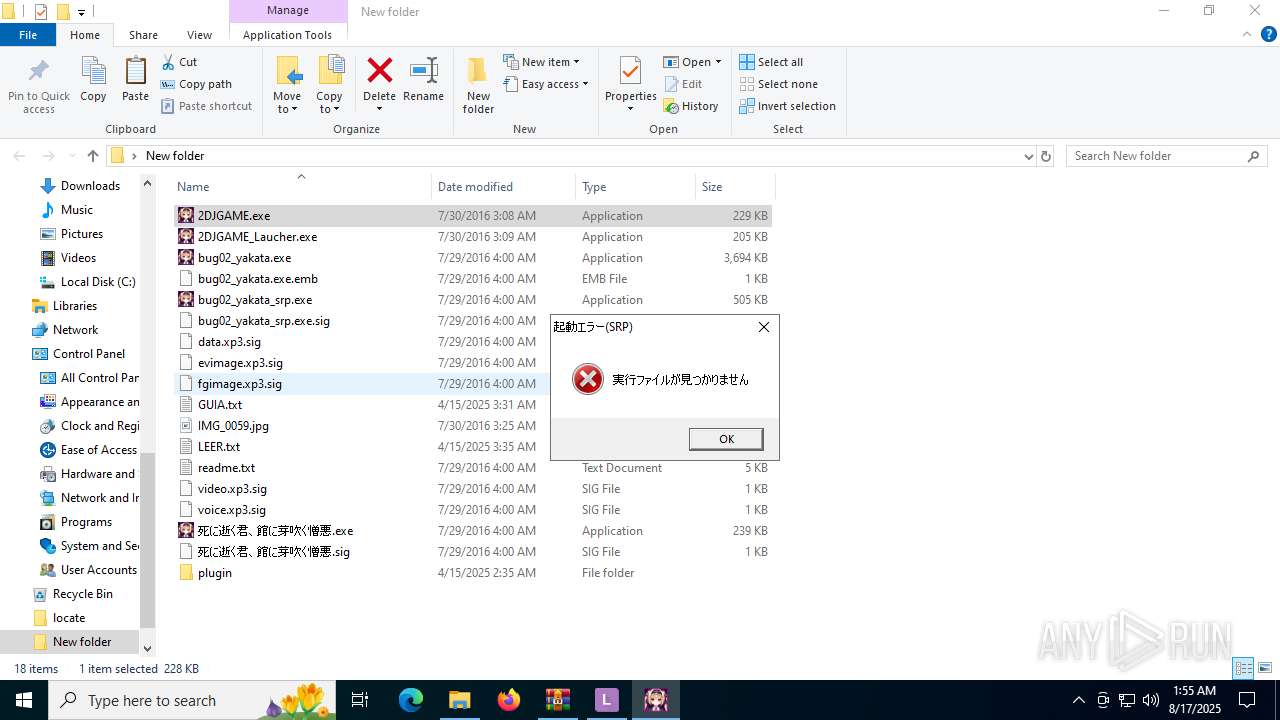
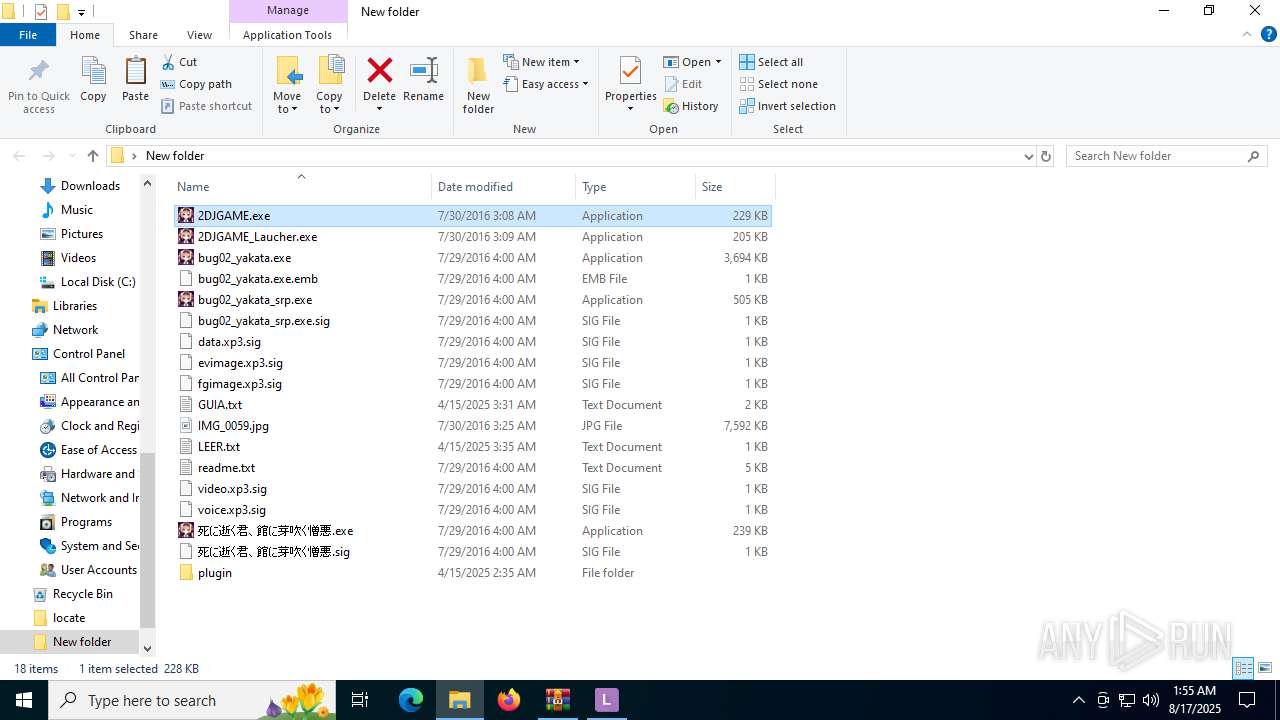
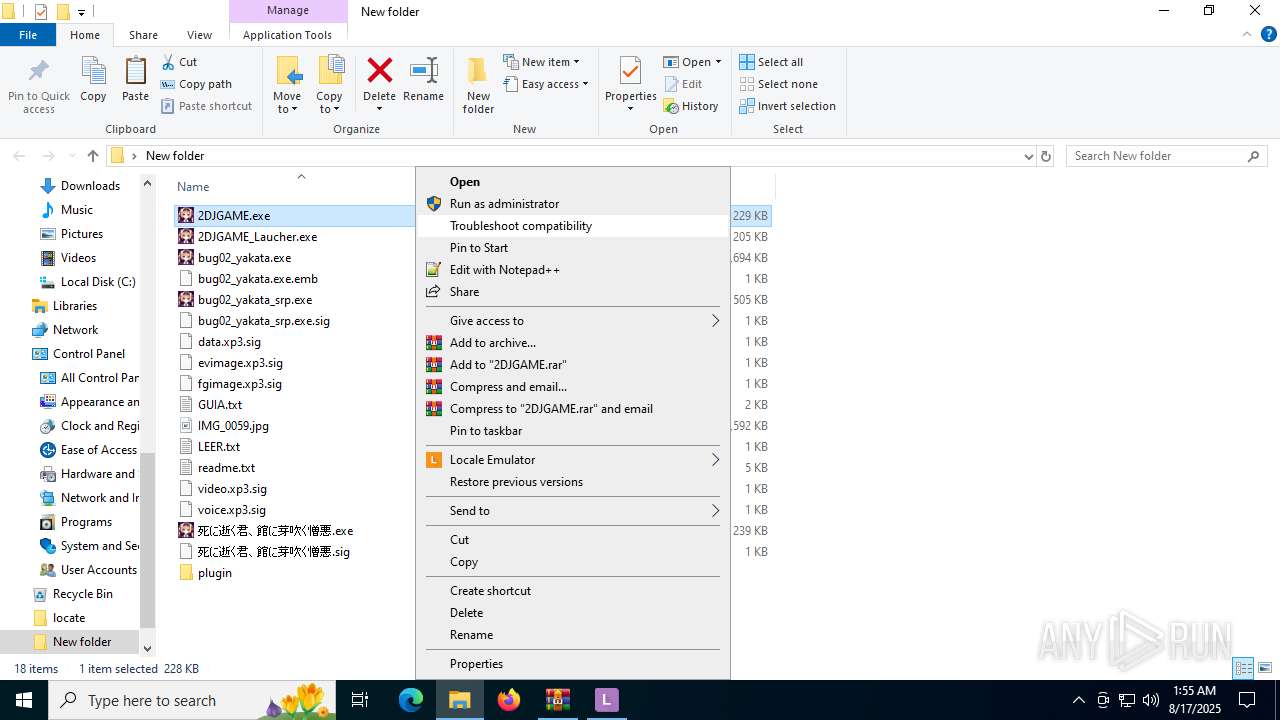
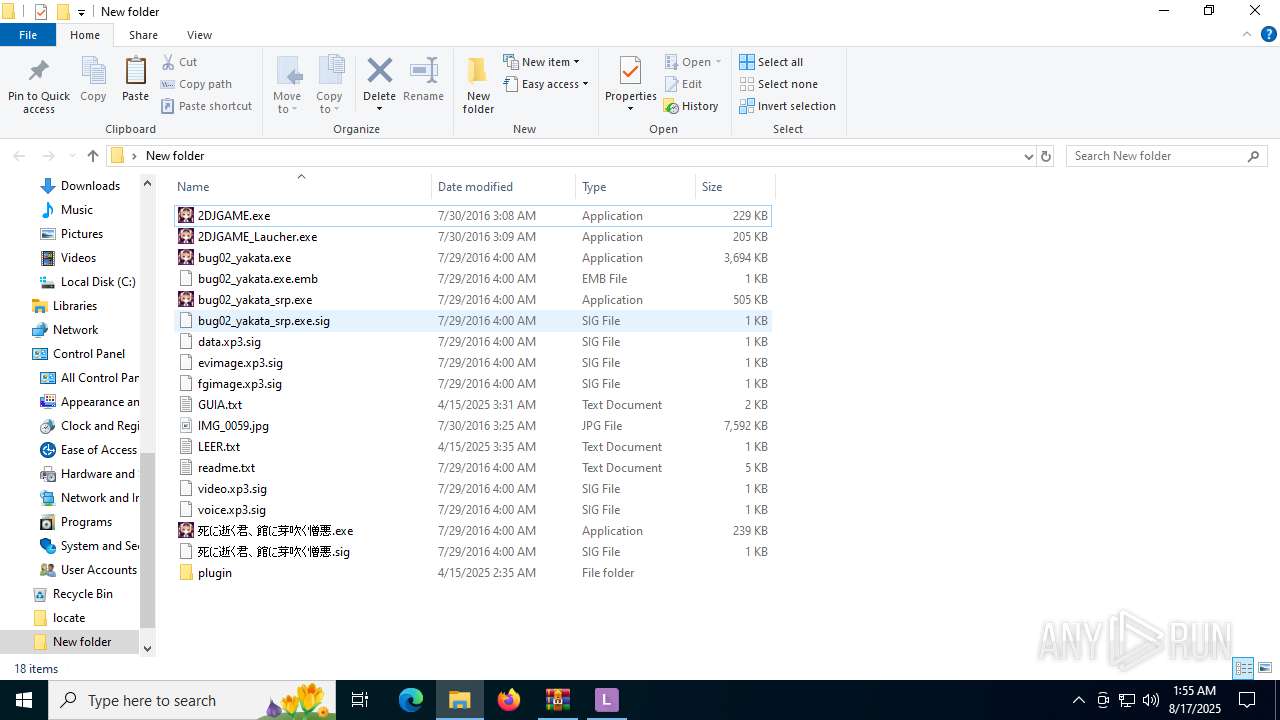
| File name: | Yakata Mawari.zip |
| Full analysis: | https://app.any.run/tasks/9b0617b6-046c-4844-8166-d6326c10cf25 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2025, 01:51:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 32AE20282CA836258CB36F9E0675AA26 |
| SHA1: | 9F6D80751D7DDB9432C6A6F22999FE271719E67E |
| SHA256: | 40B8FBEC20BD1F3DBF0F3D166EF04AAD3734CC5A8451B3D1B9B14389A92B4C55 |
| SSDEEP: | 98304:TvF7HvfJN06Mj7L+ellAmPhIInDWlUgVbspIHQbZQKfUH2y9uPjWqG4FVKVrZMua:/sOOmAXL+VWvvP9JZXRd5KS+MDeco8 |
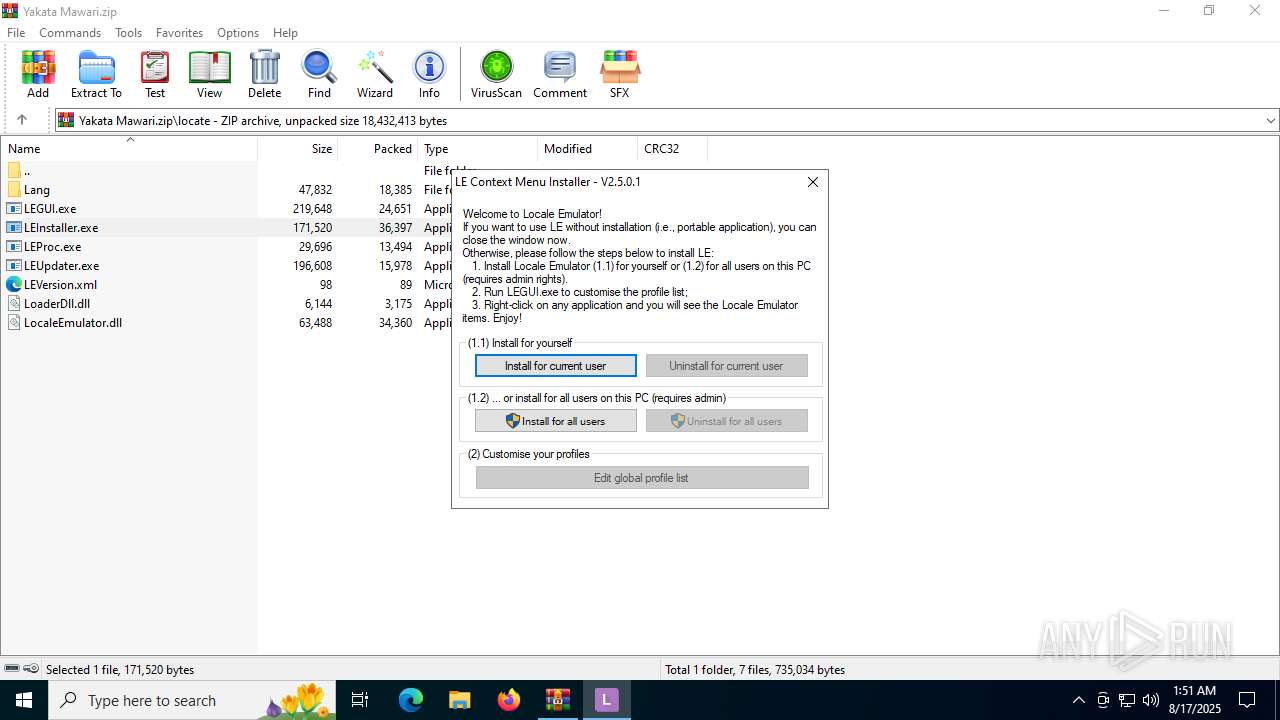
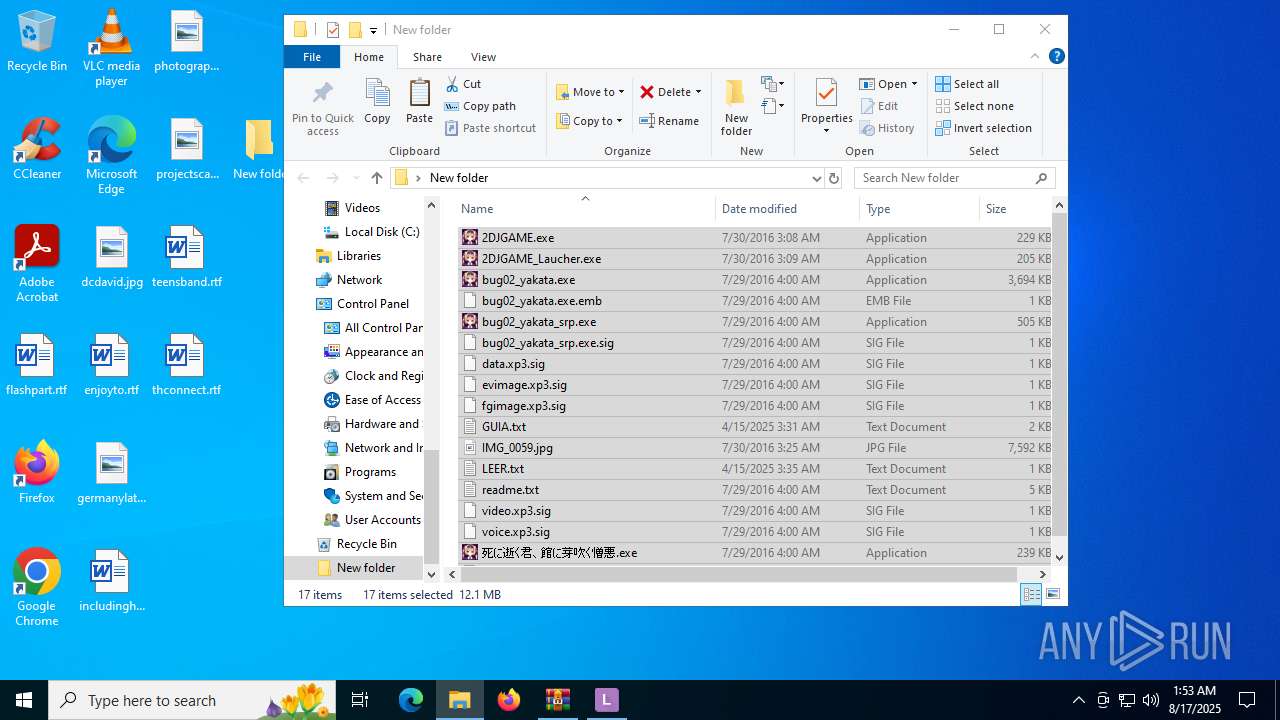
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- LEInstaller.exe (PID: 5476)
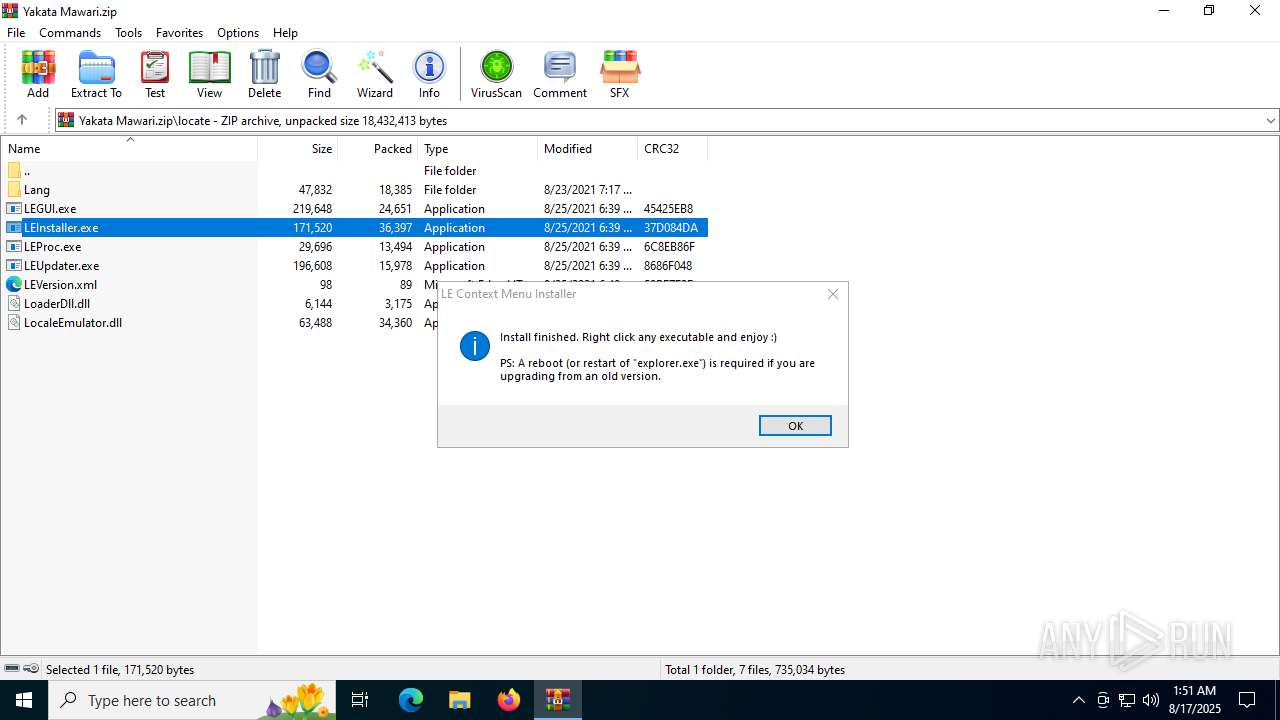
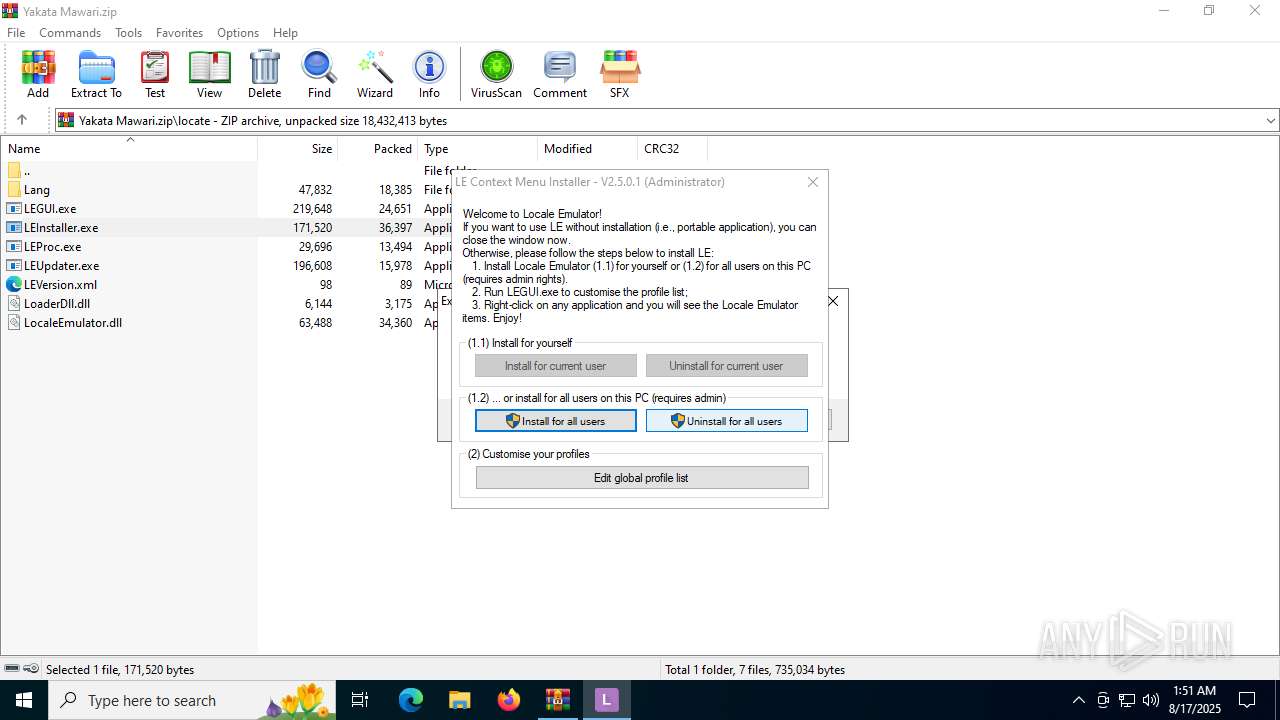
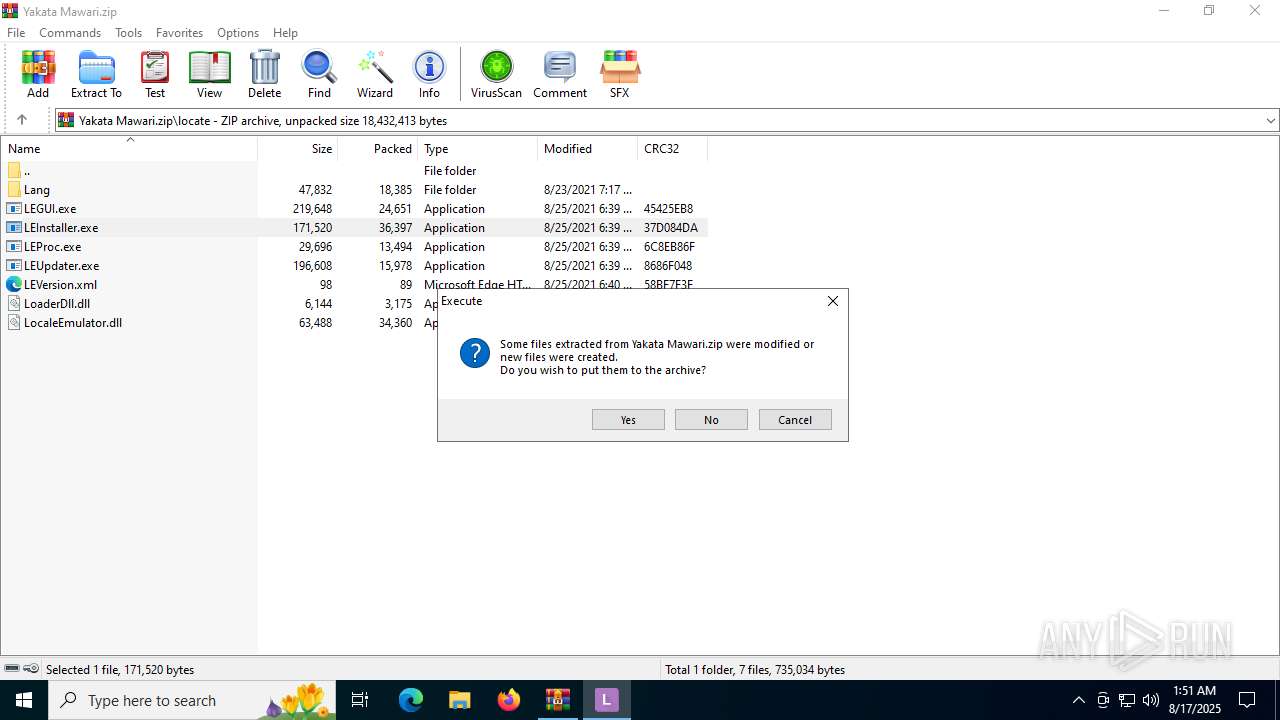
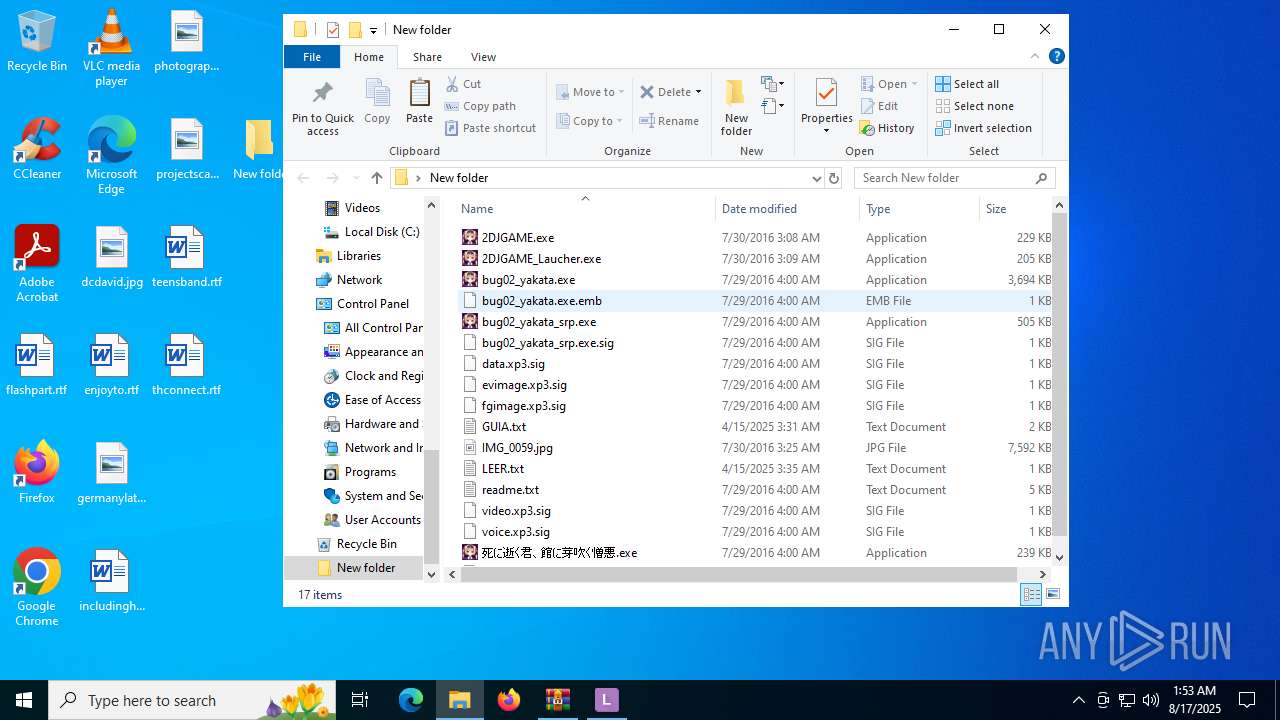
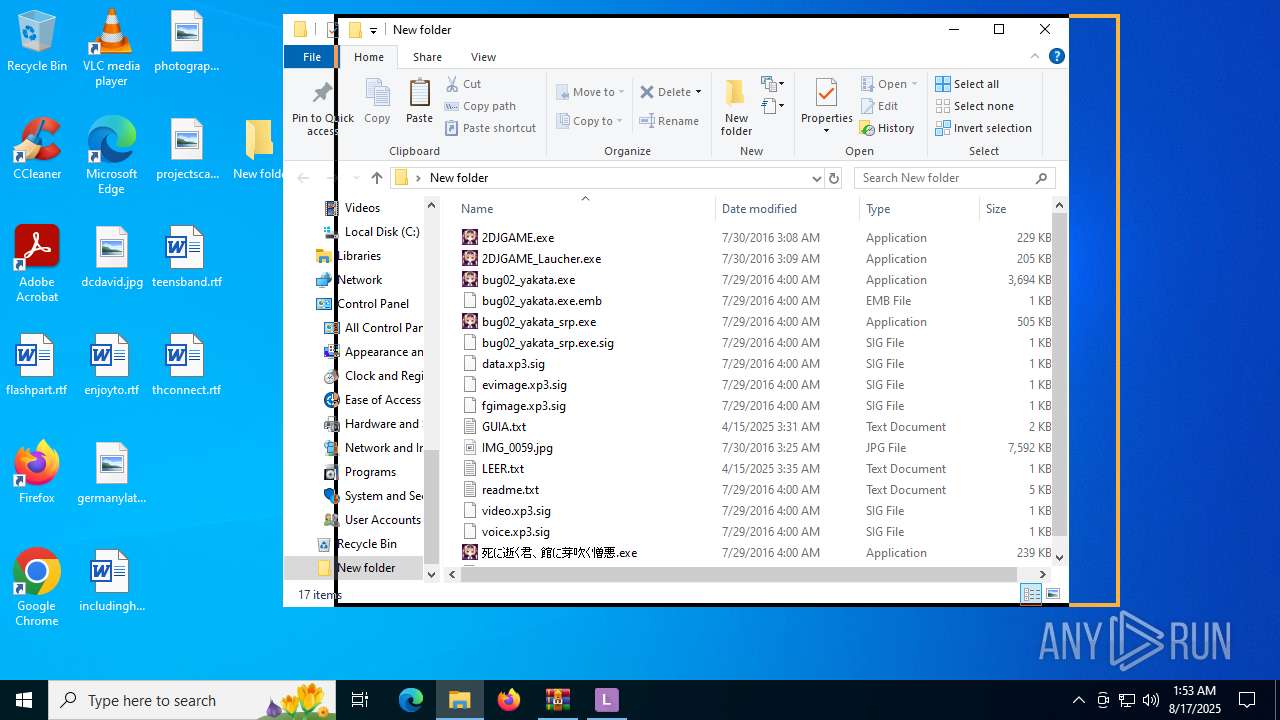
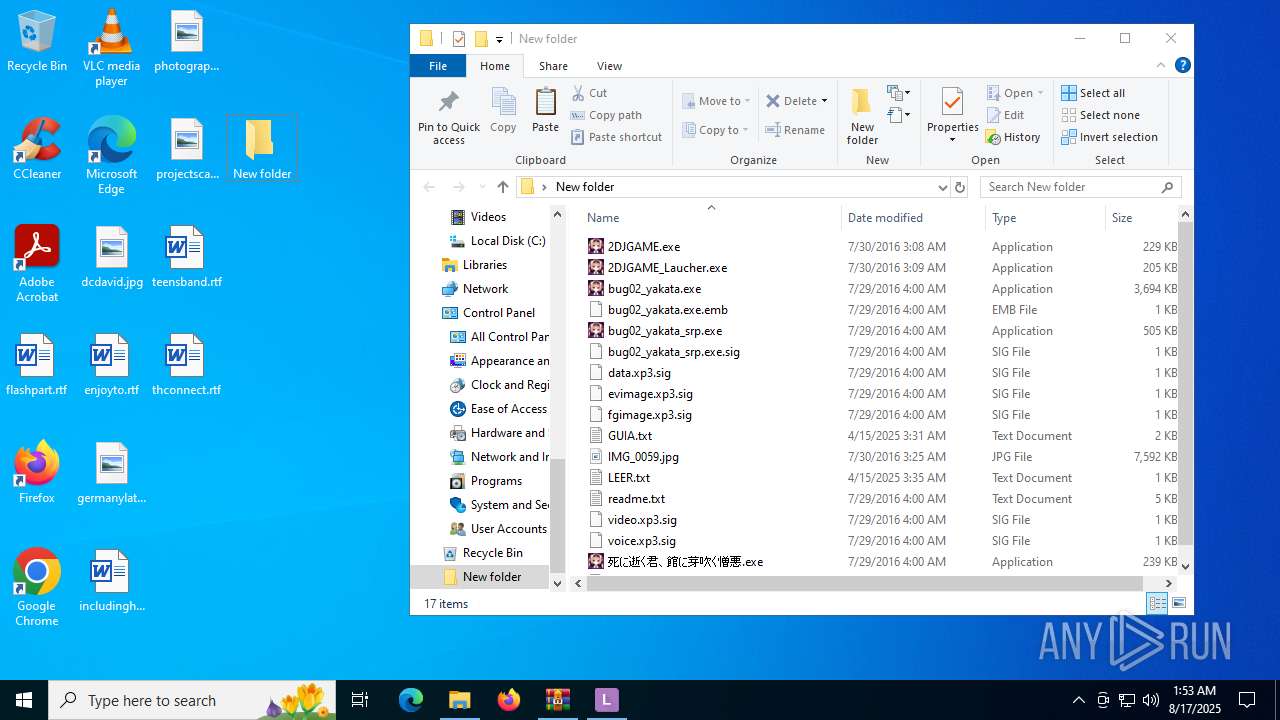
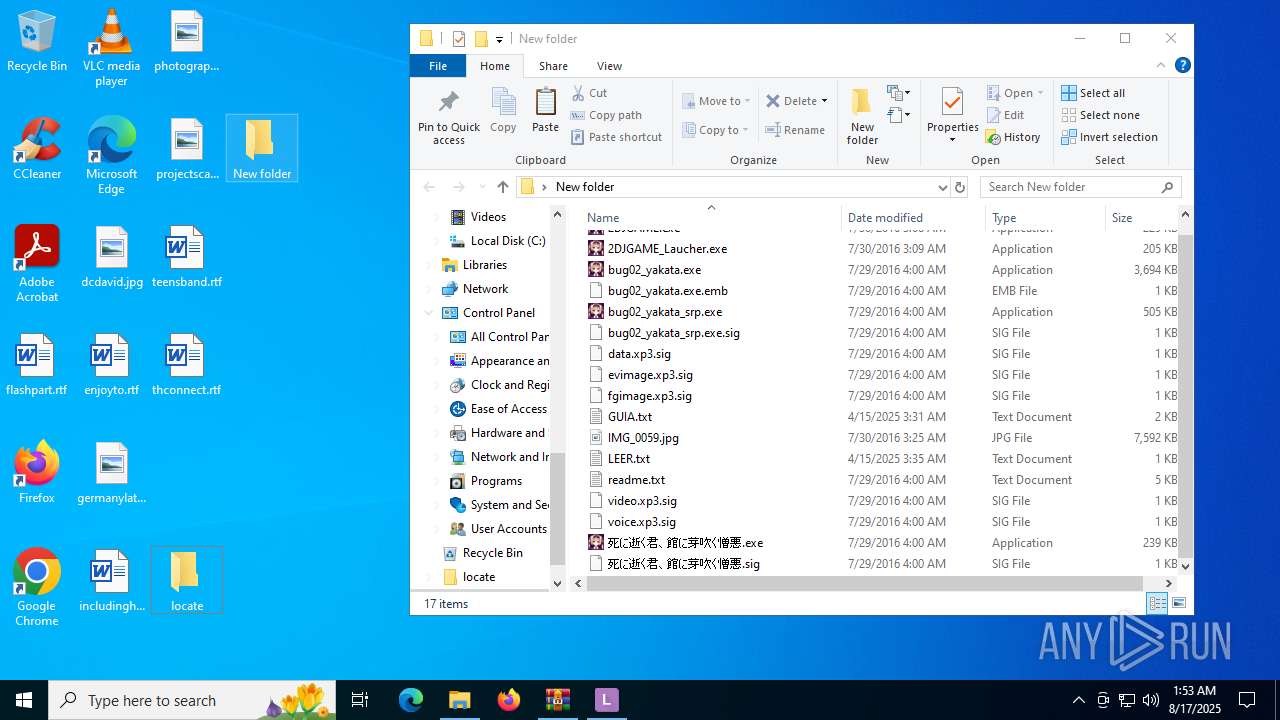
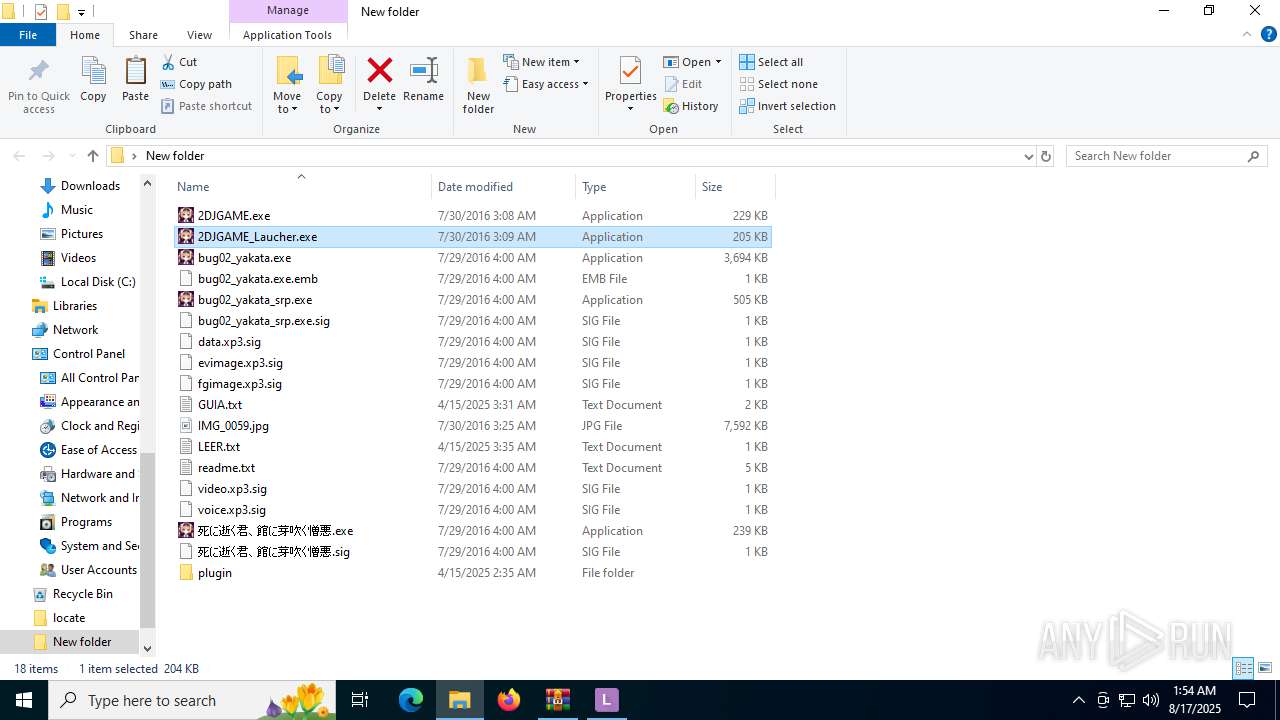
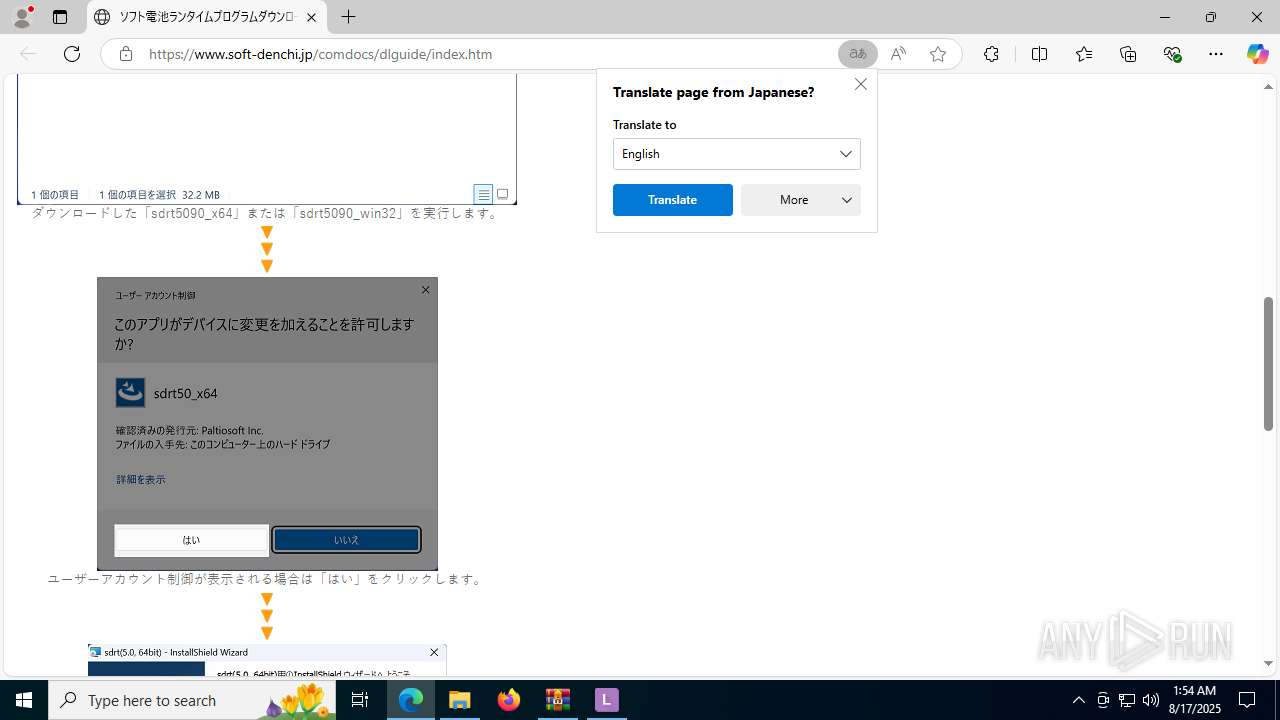
Executable content was dropped or overwritten
- LEInstaller.exe (PID: 5476)
- LEInstaller.exe (PID: 6356)
Reads security settings of Internet Explorer
- LEInstaller.exe (PID: 5476)
- WinRAR.exe (PID: 2228)
- LEInstaller.exe (PID: 6356)
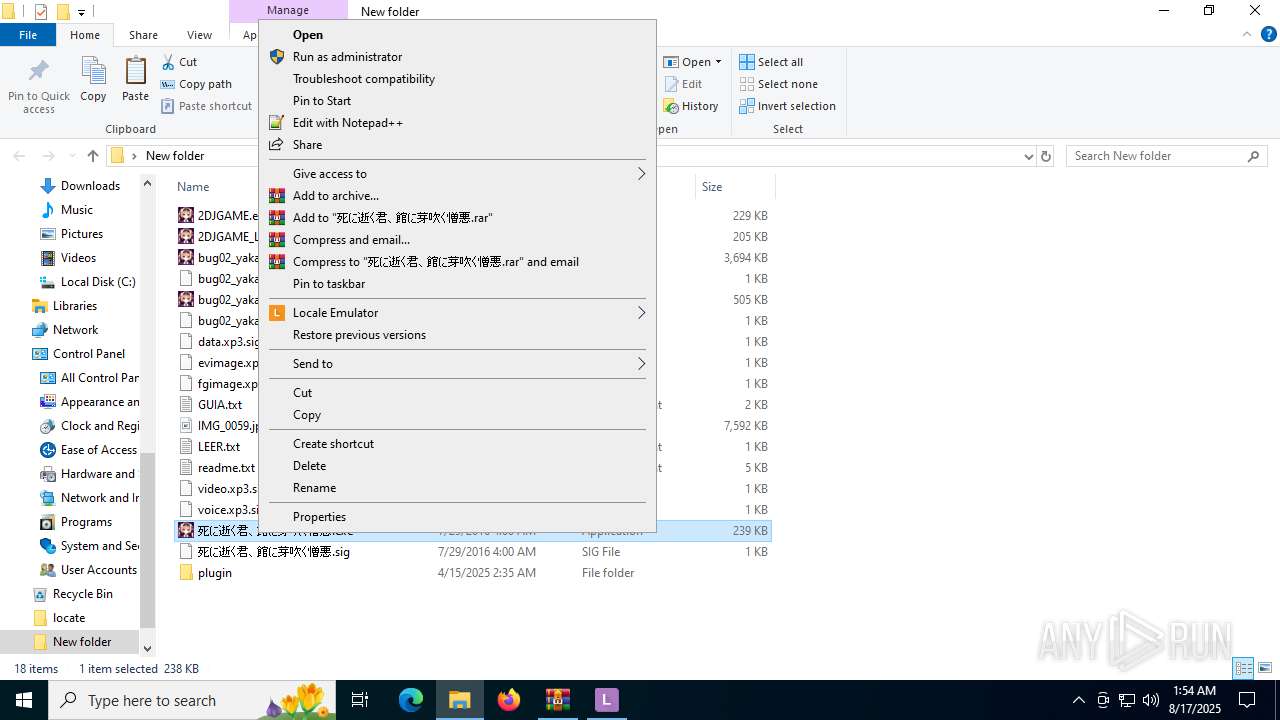
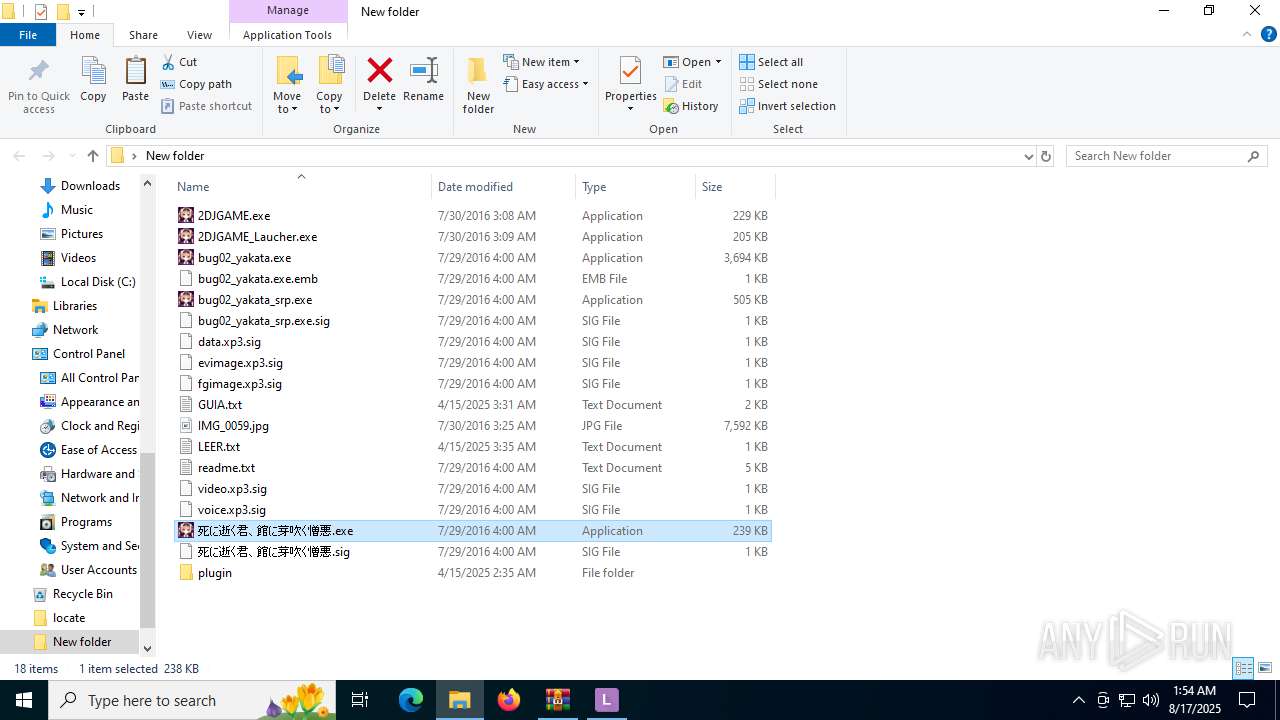
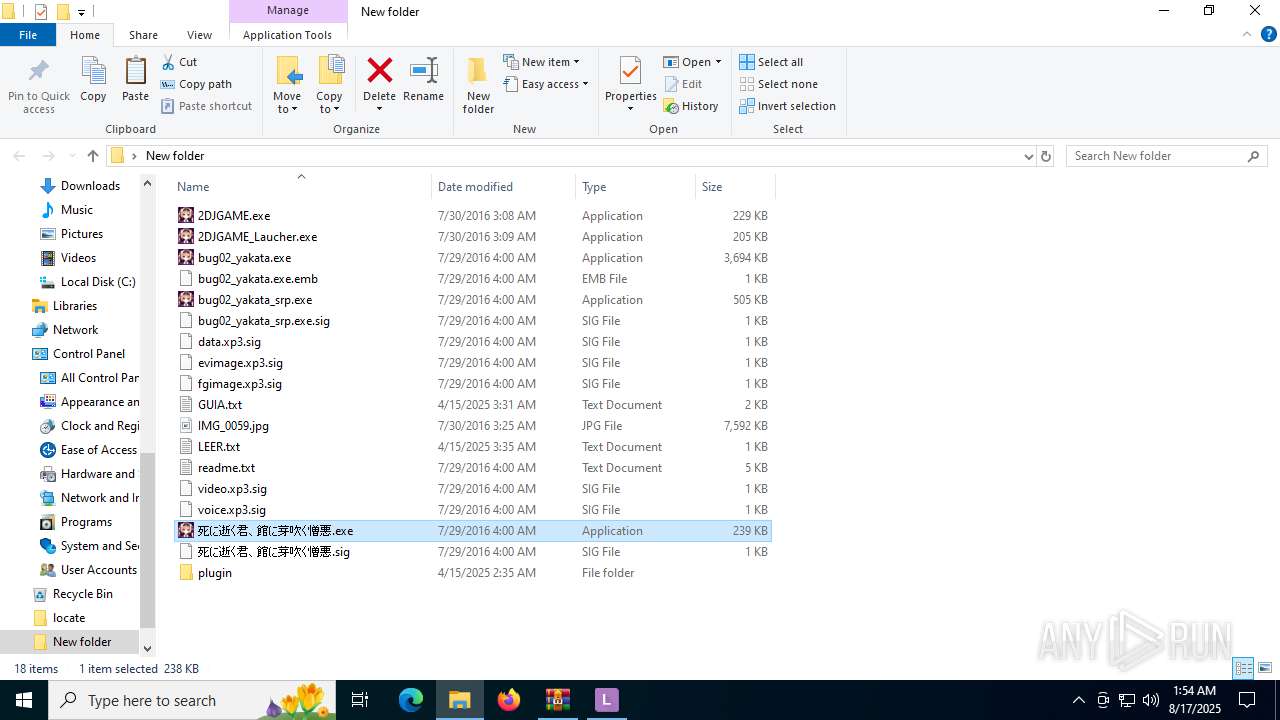
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6936)
- 2DJGAME_Laucher.exe (PID: 6748)
- 2DJGAME_Laucher.exe (PID: 4520)
- LEProc.exe (PID: 4560)
- 2DJGAME_Laucher.exe (PID: 6912)
- LEProc.exe (PID: 6980)
- LEProc.exe (PID: 5824)
- LEProc.exe (PID: 7028)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6304)
- bug02_yakata_srp.exe (PID: 6268)
- 2DJGAME_Laucher.exe (PID: 4232)
- LEProc.exe (PID: 512)
- LEProc.exe (PID: 6488)
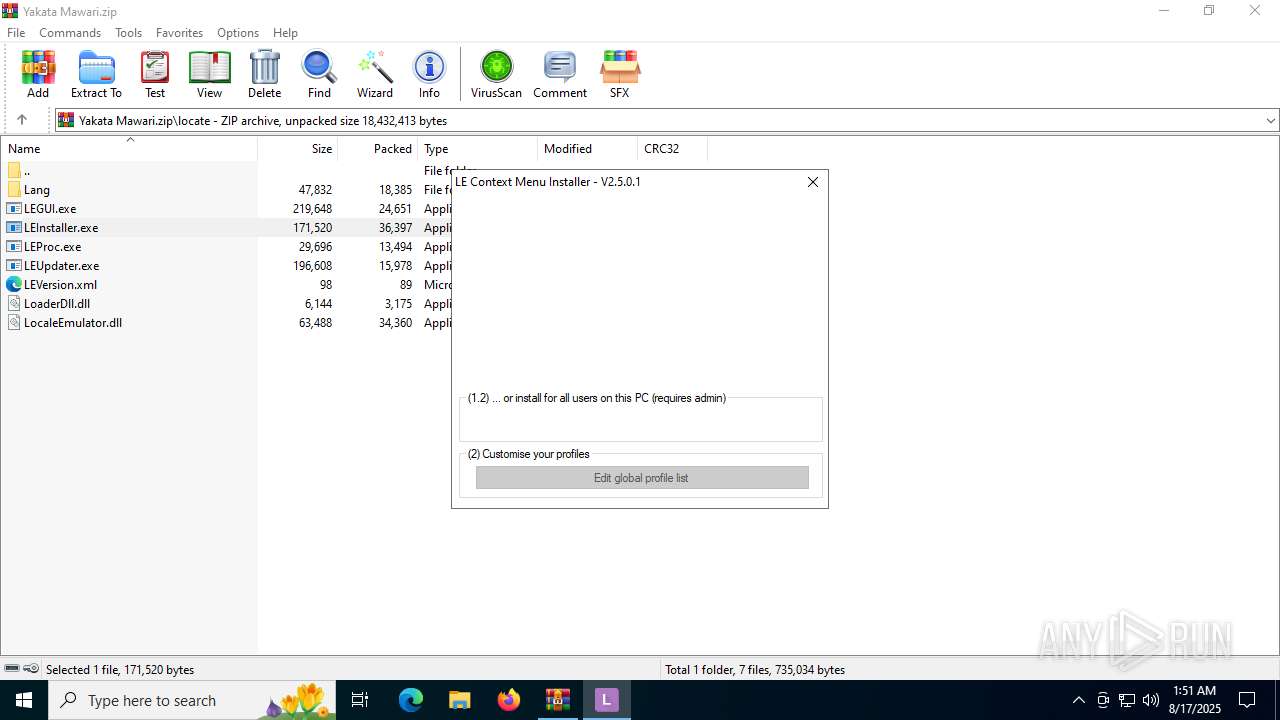
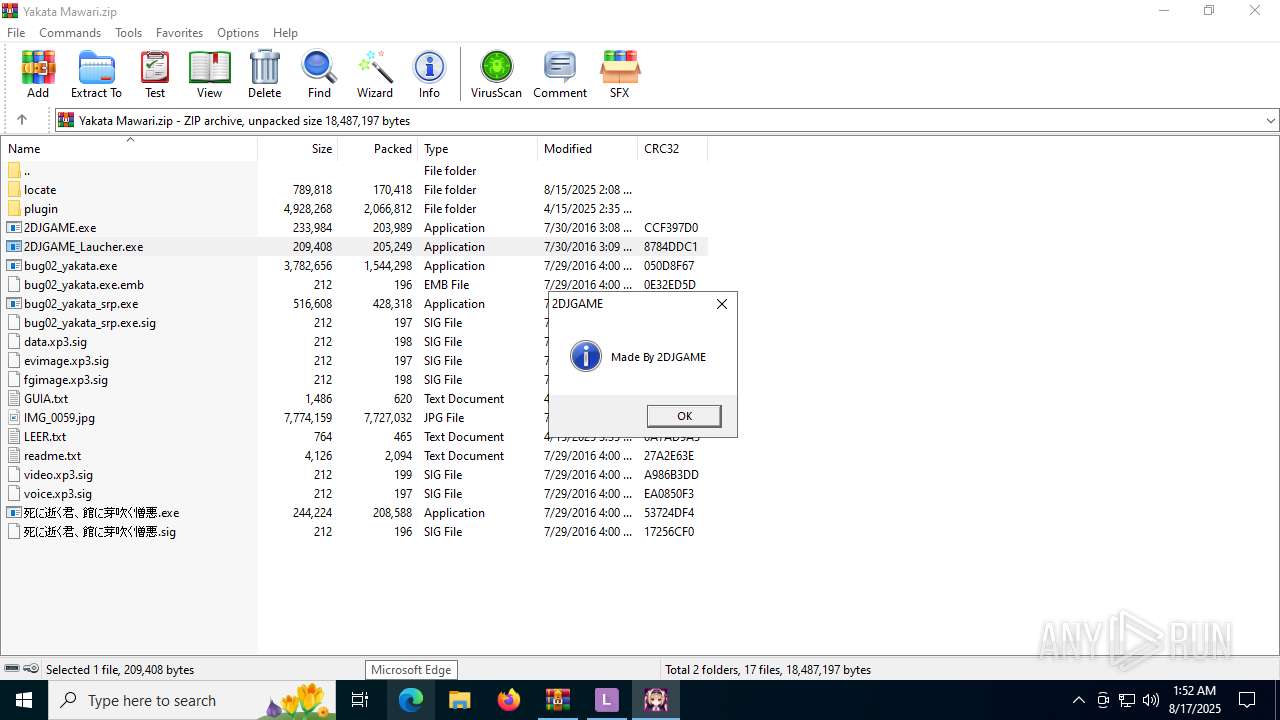
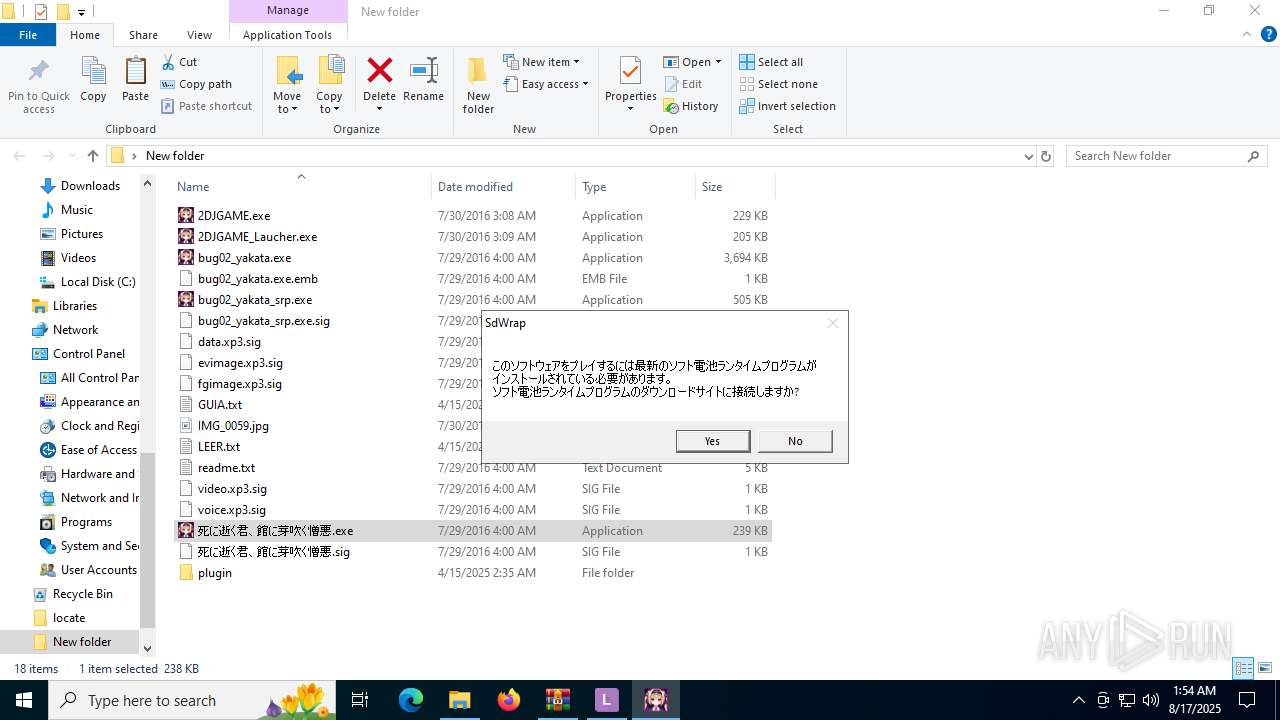
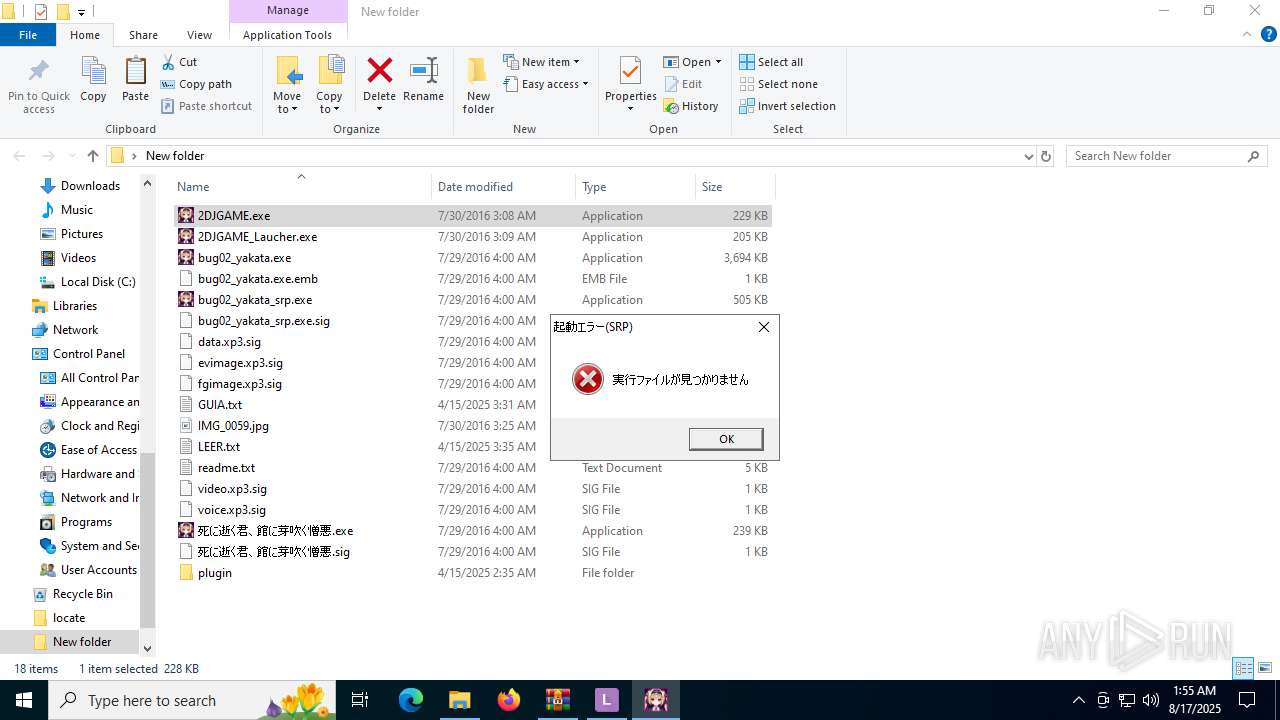
Application launched itself
- LEInstaller.exe (PID: 5476)
- LEProc.exe (PID: 6980)
- LEProc.exe (PID: 5824)
- LEProc.exe (PID: 512)
Creates/Modifies COM task schedule object
- LEInstaller.exe (PID: 6356)
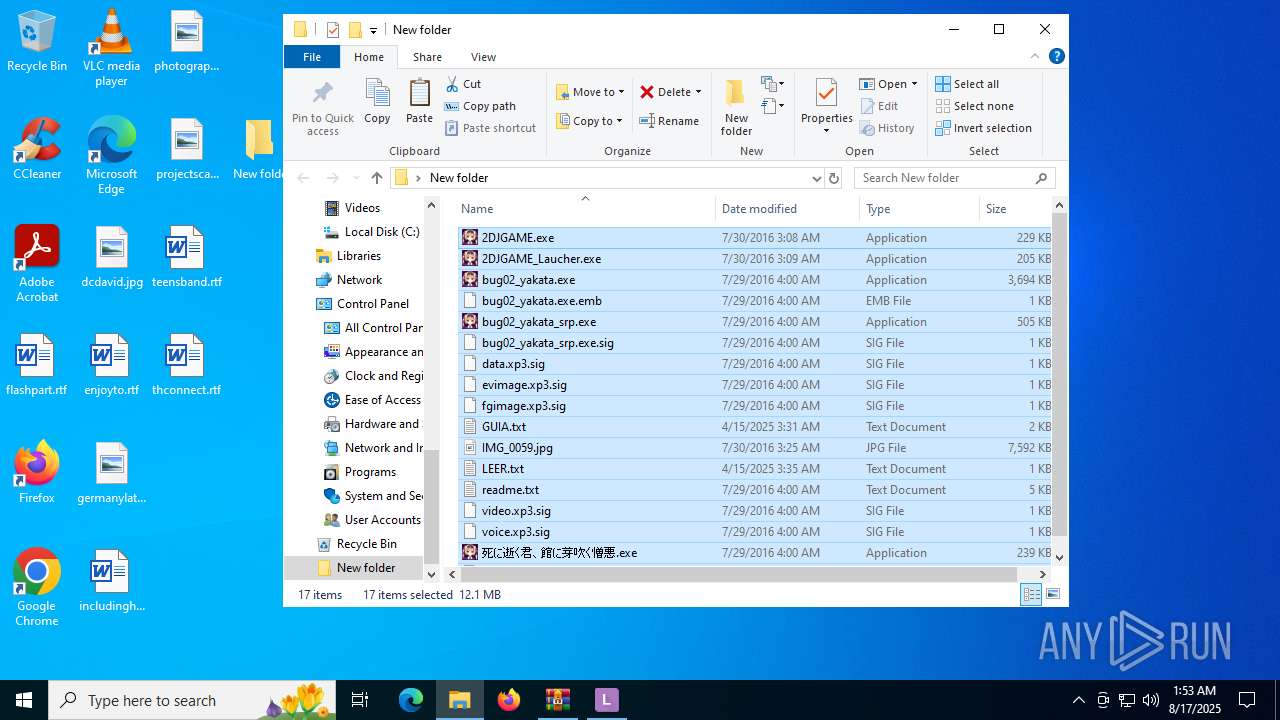
INFO
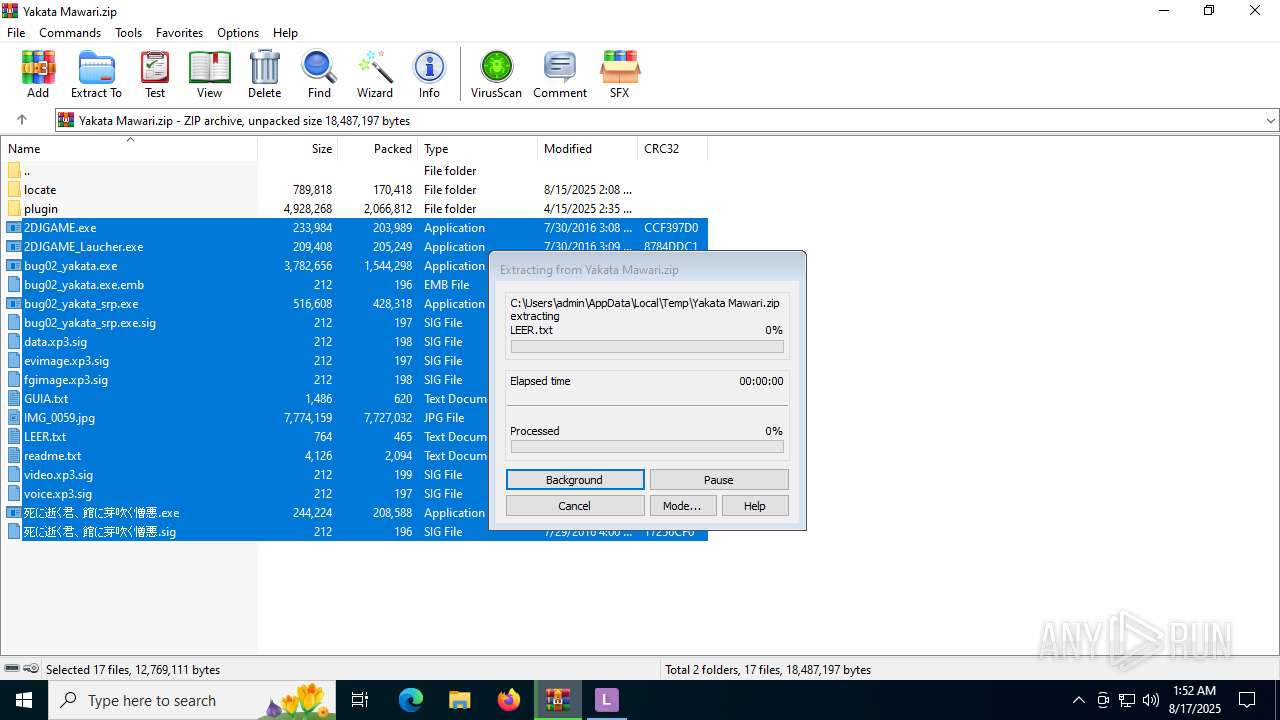
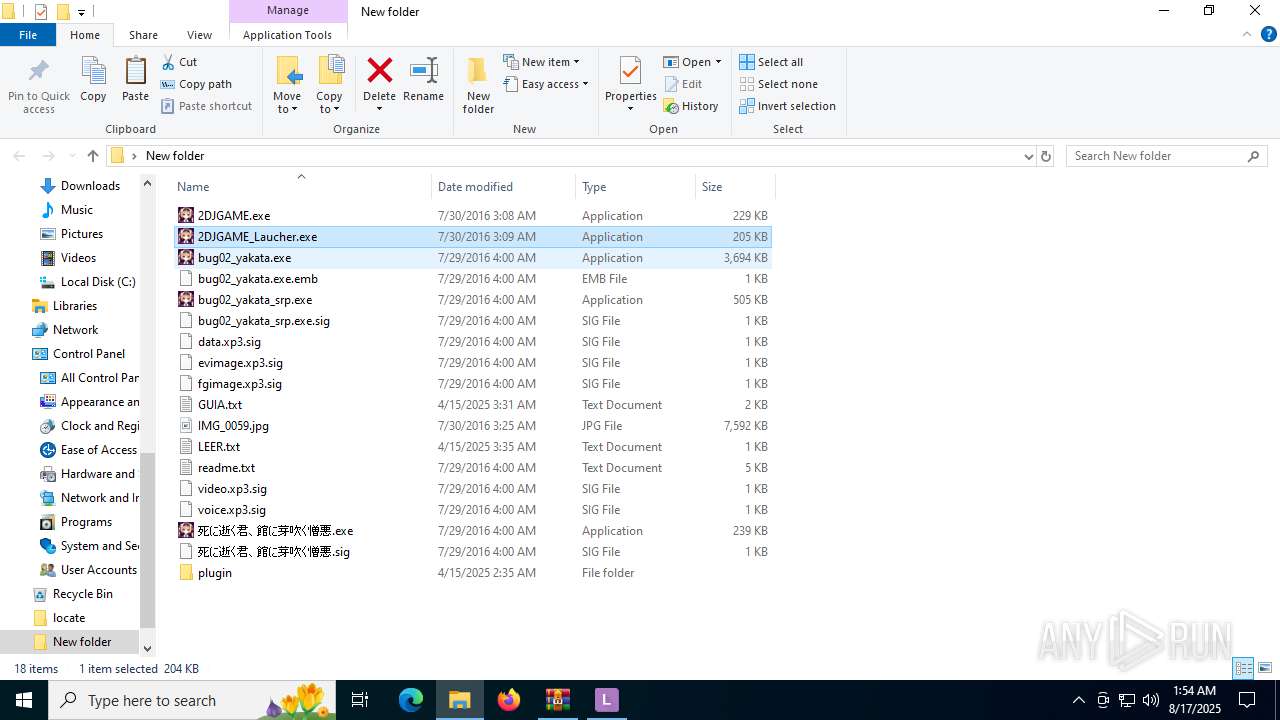
The sample compiled with english language support
- WinRAR.exe (PID: 2228)
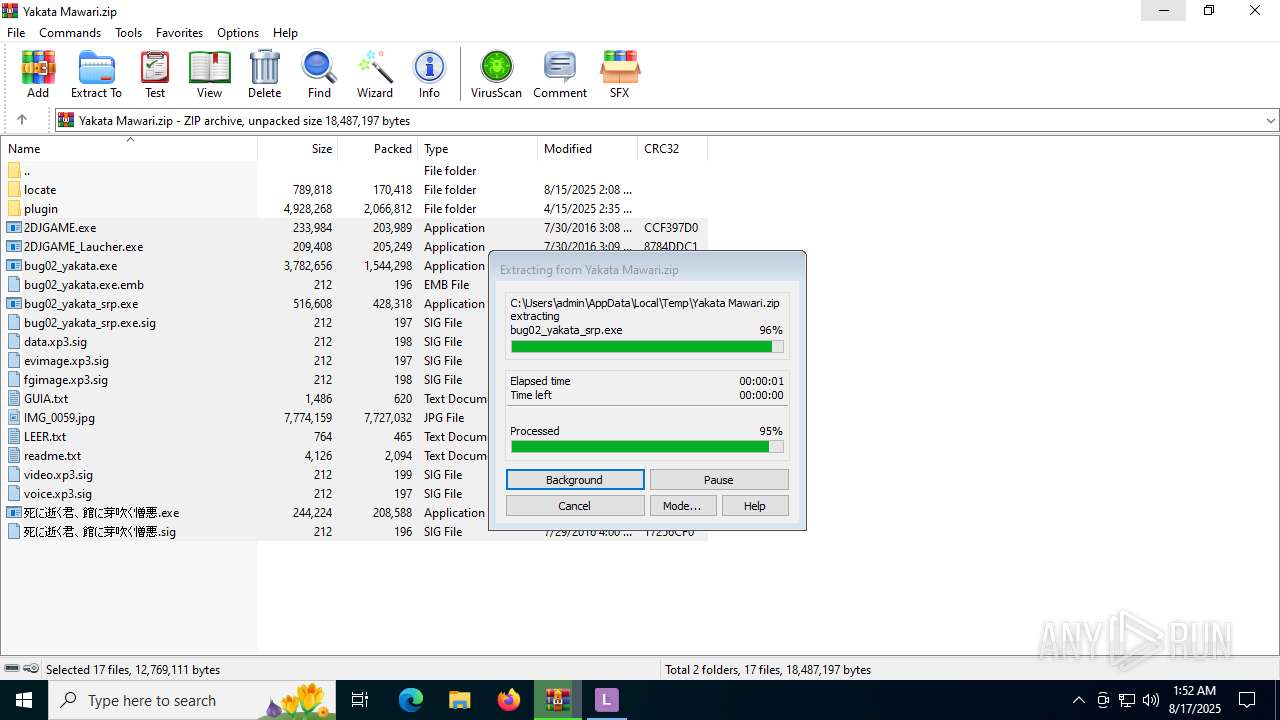
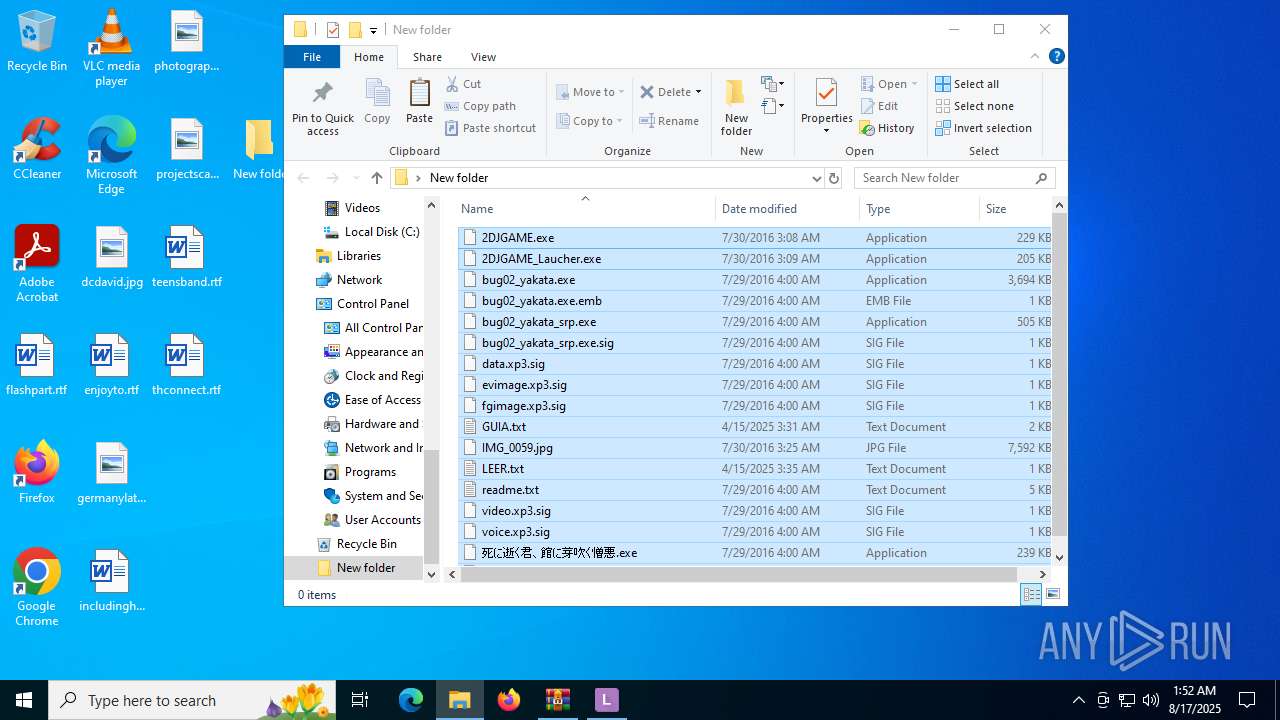
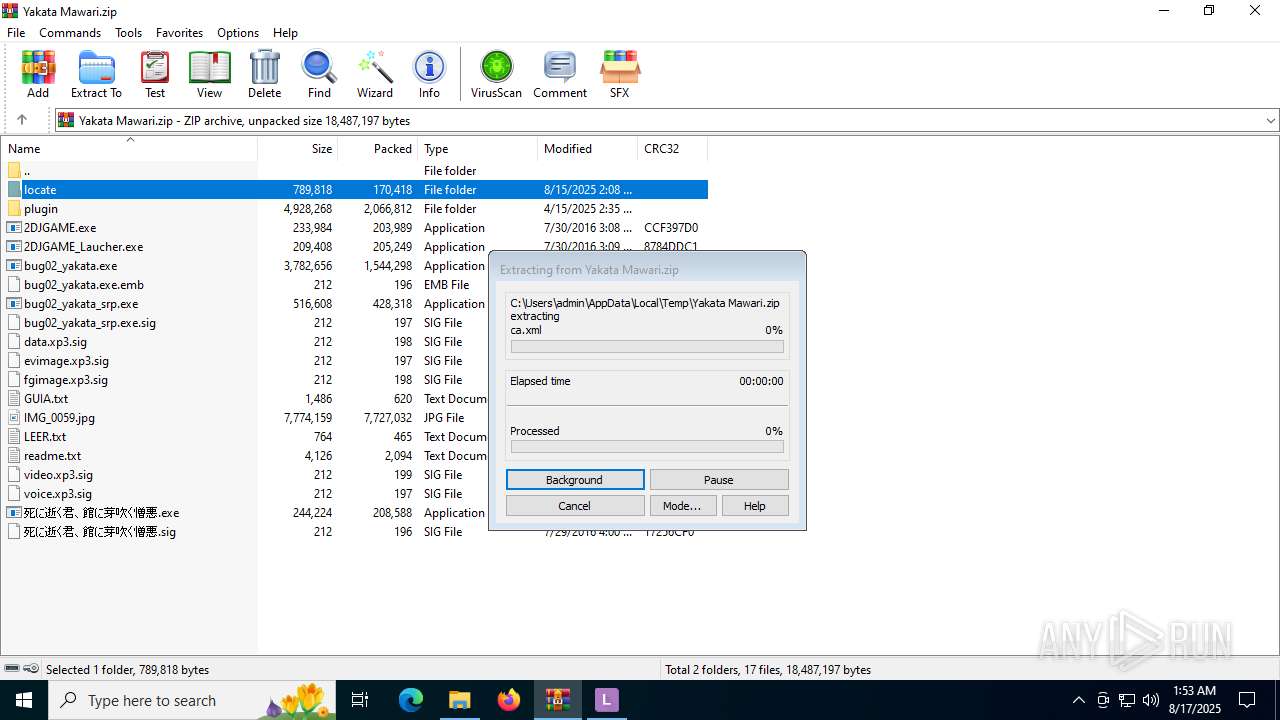
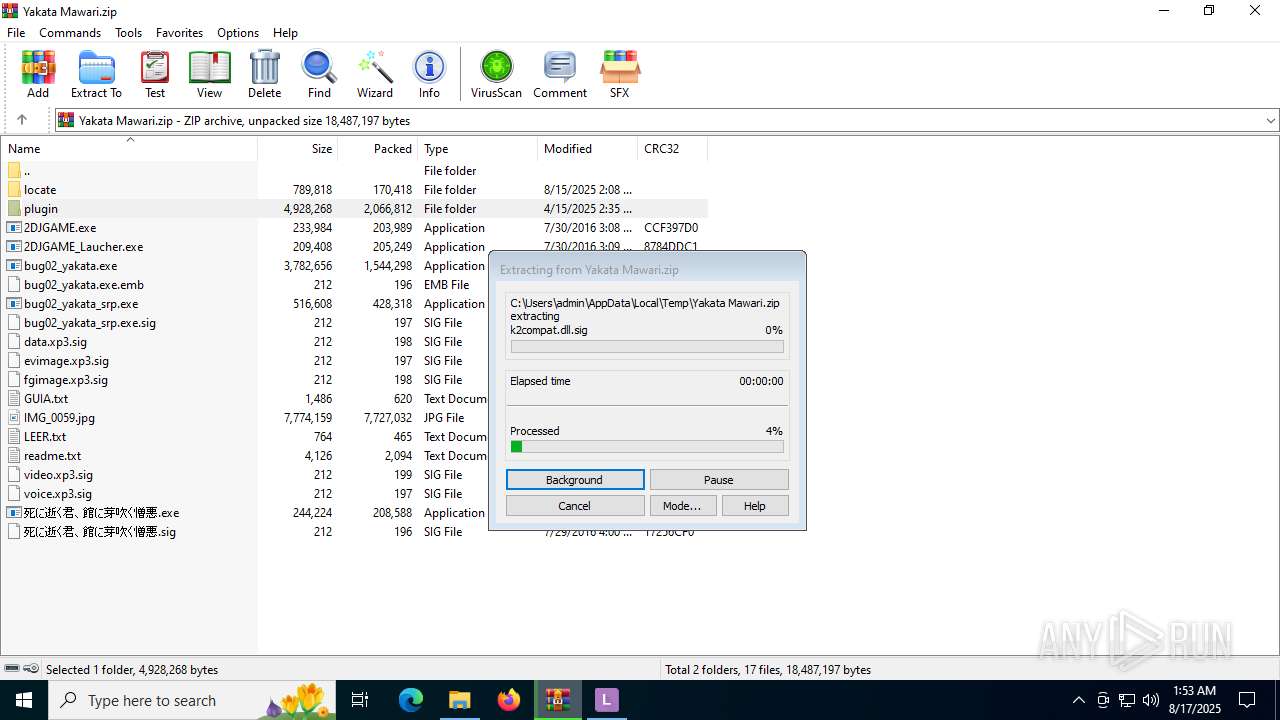
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2228)
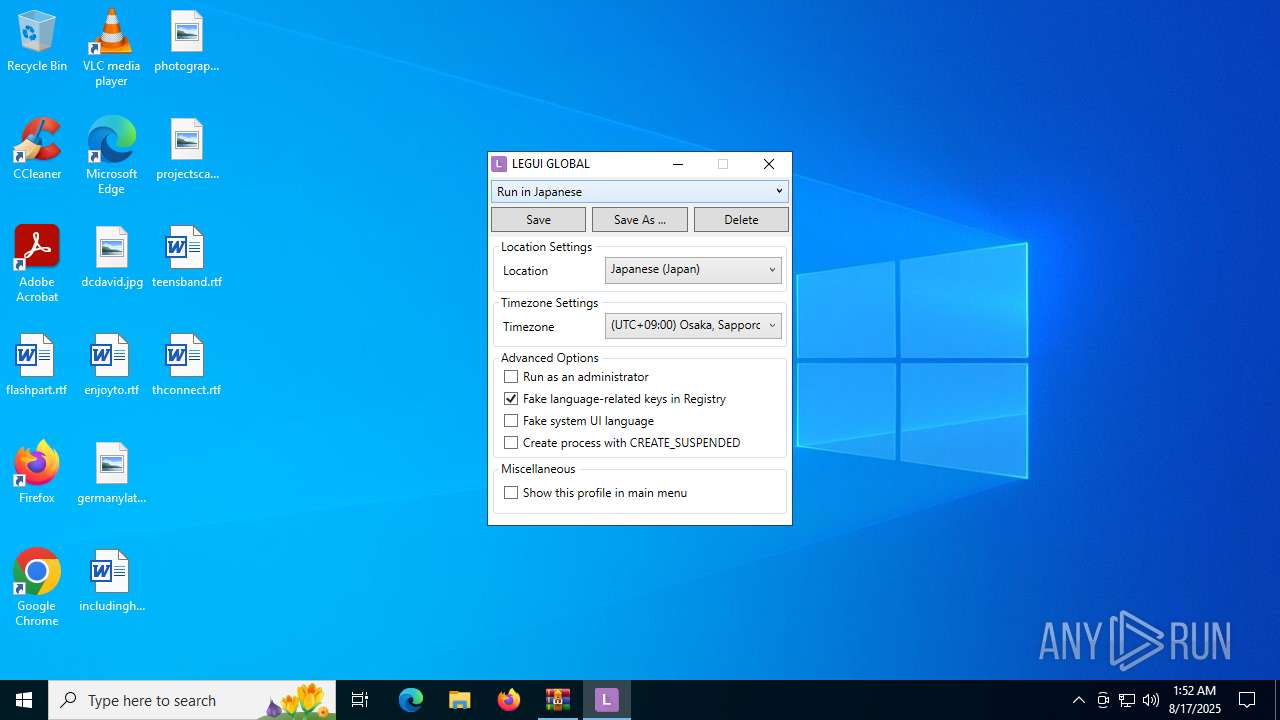
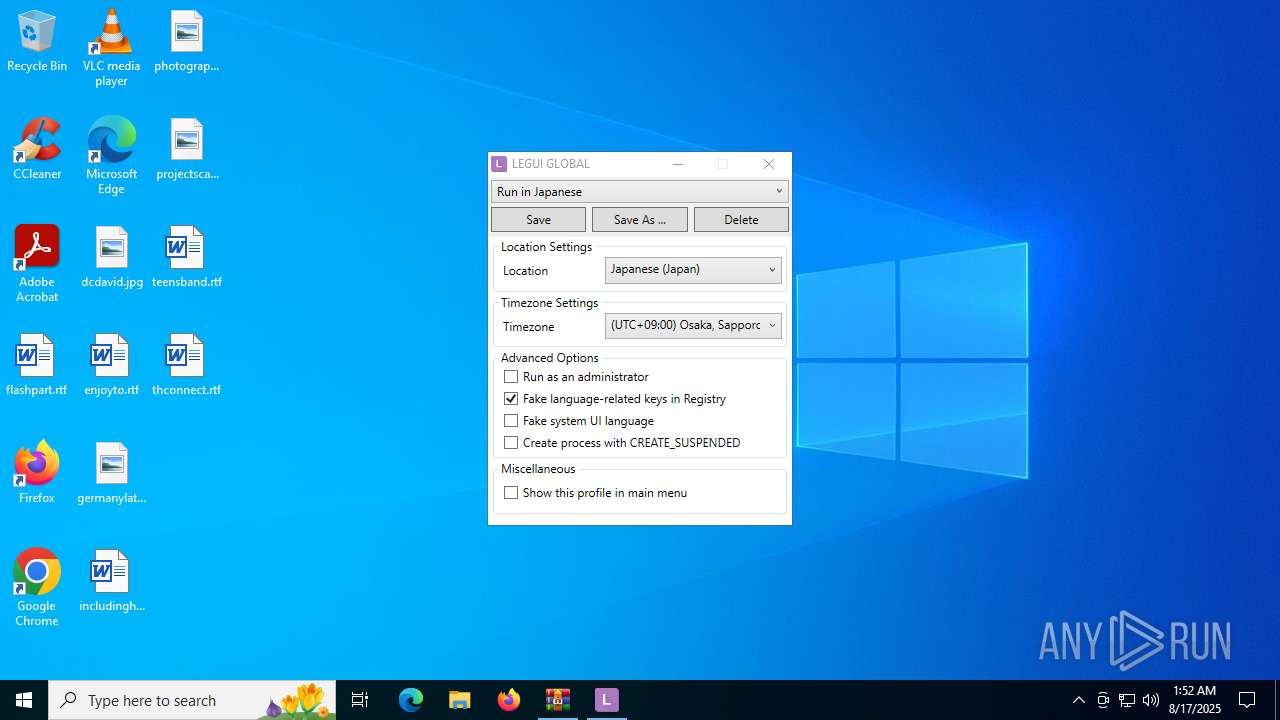
Process checks computer location settings
- LEInstaller.exe (PID: 5476)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6936)
- 2DJGAME_Laucher.exe (PID: 6748)
- 2DJGAME_Laucher.exe (PID: 4520)
- LEProc.exe (PID: 6980)
- LEProc.exe (PID: 4560)
- LEProc.exe (PID: 7028)
- LEProc.exe (PID: 5824)
- 2DJGAME_Laucher.exe (PID: 4232)
- LEProc.exe (PID: 512)
- LEProc.exe (PID: 6488)
Reads the computer name
- LEInstaller.exe (PID: 5476)
- LEInstaller.exe (PID: 6356)
- LEGUI.exe (PID: 2808)
- 2DJGAME.exe (PID: 3840)
- 2DJGAME_Laucher.exe (PID: 6748)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6936)
- bug02_yakata_srp.exe (PID: 6004)
- LEProc.exe (PID: 6980)
- LEUpdater.exe (PID: 6812)
- 2DJGAME_Laucher.exe (PID: 4520)
- 2DJGAME_Laucher.exe (PID: 6912)
- LEProc.exe (PID: 4560)
- LEUpdater.exe (PID: 3480)
- LEProc.exe (PID: 7028)
- LEUpdater.exe (PID: 5340)
- LEProc.exe (PID: 5824)
- LEUpdater.exe (PID: 3540)
- bug02_yakata_srp.exe (PID: 6268)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6304)
- 2DJGAME_Laucher.exe (PID: 4232)
- identity_helper.exe (PID: 1352)
- identity_helper.exe (PID: 4448)
- 2DJGAME.exe (PID: 6348)
- LEProc.exe (PID: 512)
- LEUpdater.exe (PID: 2304)
- LEProc.exe (PID: 6488)
- LEUpdater.exe (PID: 5060)
- 2DJGAME.exe (PID: 4676)
Reads the machine GUID from the registry
- LEInstaller.exe (PID: 5476)
- LEInstaller.exe (PID: 6356)
- LEGUI.exe (PID: 2808)
- LEUpdater.exe (PID: 6812)
- LEProc.exe (PID: 6980)
- LEProc.exe (PID: 4560)
- LEUpdater.exe (PID: 3480)
- LEUpdater.exe (PID: 3540)
- LEProc.exe (PID: 7028)
- LEUpdater.exe (PID: 5340)
- LEProc.exe (PID: 5824)
- LEProc.exe (PID: 512)
- LEUpdater.exe (PID: 2304)
- LEProc.exe (PID: 6488)
- LEUpdater.exe (PID: 5060)
The sample compiled with japanese language support
- WinRAR.exe (PID: 2228)
Checks supported languages
- LEInstaller.exe (PID: 5476)
- LEInstaller.exe (PID: 6356)
- LEGUI.exe (PID: 2808)
- bug02_yakata_srp.exe (PID: 6004)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6936)
- 2DJGAME.exe (PID: 3840)
- 2DJGAME_Laucher.exe (PID: 6748)
- 2DJGAME.exe (PID: 2428)
- bug02_yakata.exe (PID: 3628)
- 2DJGAME_Laucher.exe (PID: 4520)
- LEProc.exe (PID: 6980)
- 2DJGAME.exe (PID: 6732)
- bug02_yakata.exe (PID: 6756)
- LEUpdater.exe (PID: 6812)
- LEProc.exe (PID: 4560)
- LEUpdater.exe (PID: 3480)
- 2DJGAME_Laucher.exe (PID: 6912)
- 2DJGAME.exe (PID: 4884)
- bug02_yakata.exe (PID: 2508)
- LEProc.exe (PID: 7028)
- LEUpdater.exe (PID: 3540)
- LEUpdater.exe (PID: 5340)
- 死に逝く君、館に芽吹く憎悪.exe (PID: 6304)
- LEProc.exe (PID: 5824)
- bug02_yakata_srp.exe (PID: 6268)
- 2DJGAME.exe (PID: 1632)
- identity_helper.exe (PID: 4448)
- identity_helper.exe (PID: 1352)
- 2DJGAME_Laucher.exe (PID: 4232)
- bug02_yakata.exe (PID: 1156)
- 2DJGAME.exe (PID: 6348)
- LEUpdater.exe (PID: 2304)
- LEProc.exe (PID: 6488)
- LEProc.exe (PID: 512)
- LEUpdater.exe (PID: 5060)
- 2DJGAME.exe (PID: 4676)
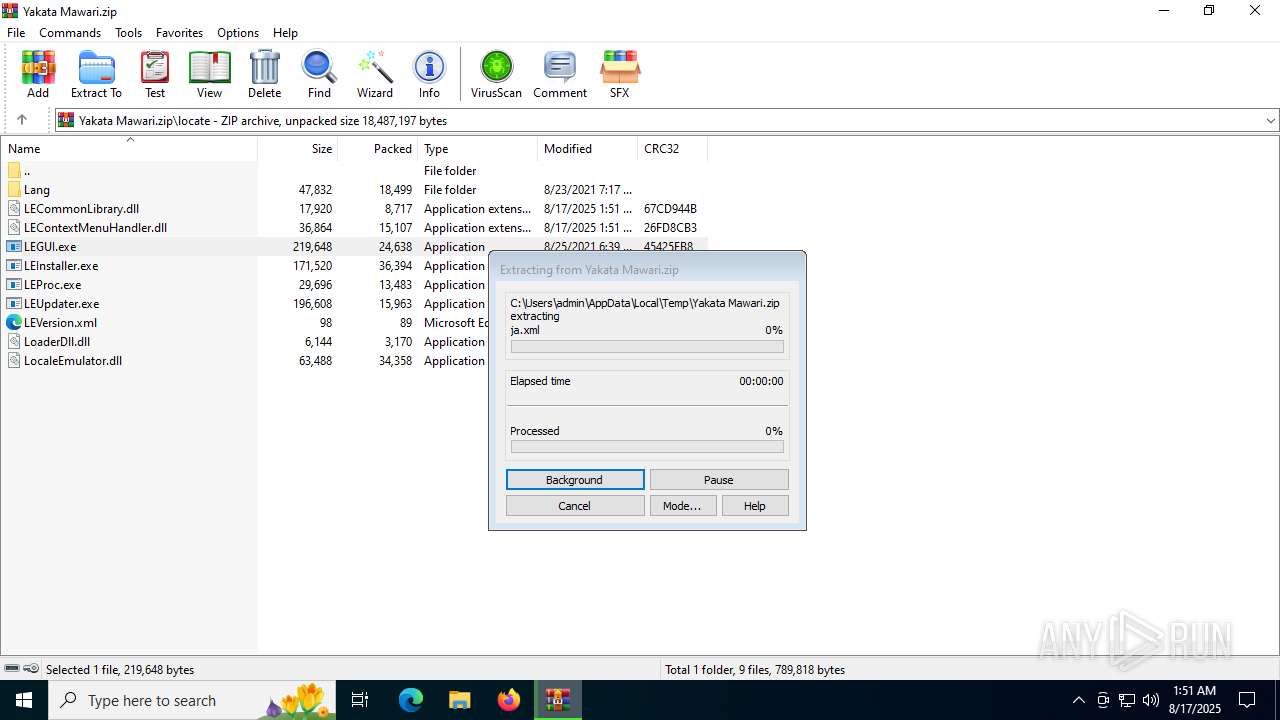
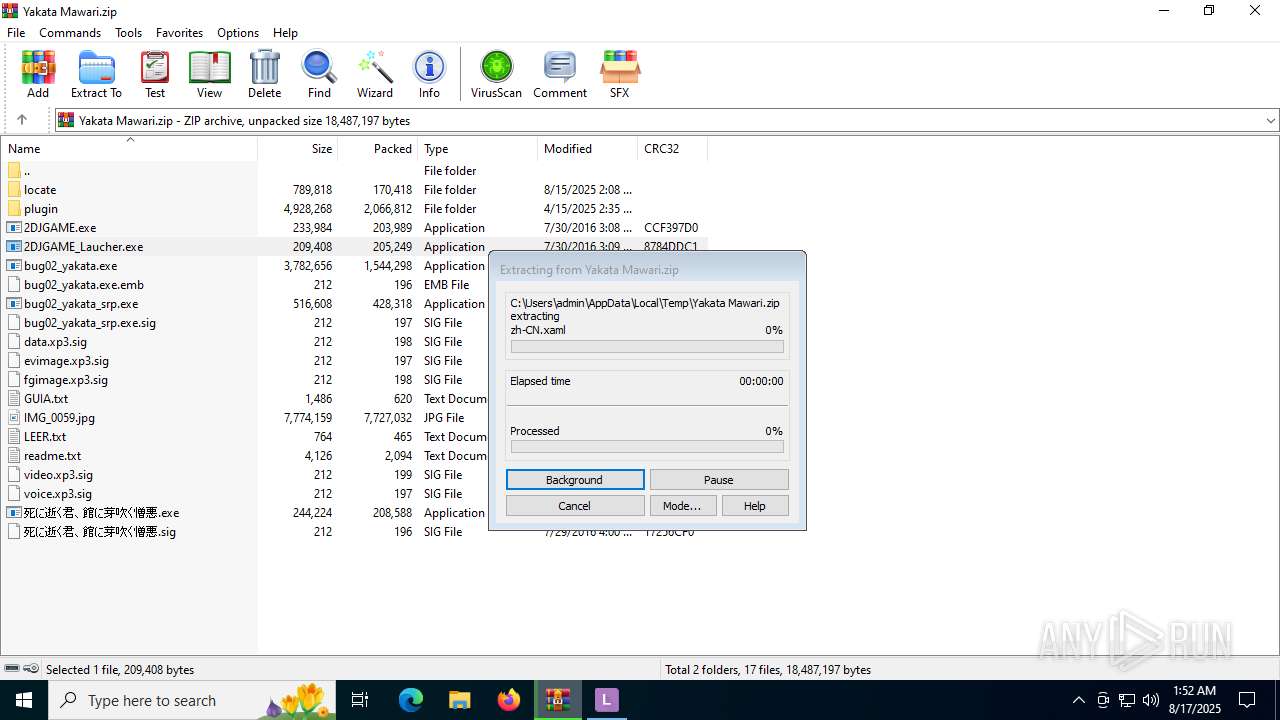
Create files in a temporary directory
- LEInstaller.exe (PID: 5476)
- LEInstaller.exe (PID: 6356)
- LEGUI.exe (PID: 2808)
- LEUpdater.exe (PID: 6812)
Reads the software policy settings
- slui.exe (PID: 4456)
Checks proxy server information
- slui.exe (PID: 4456)
- LEUpdater.exe (PID: 6812)
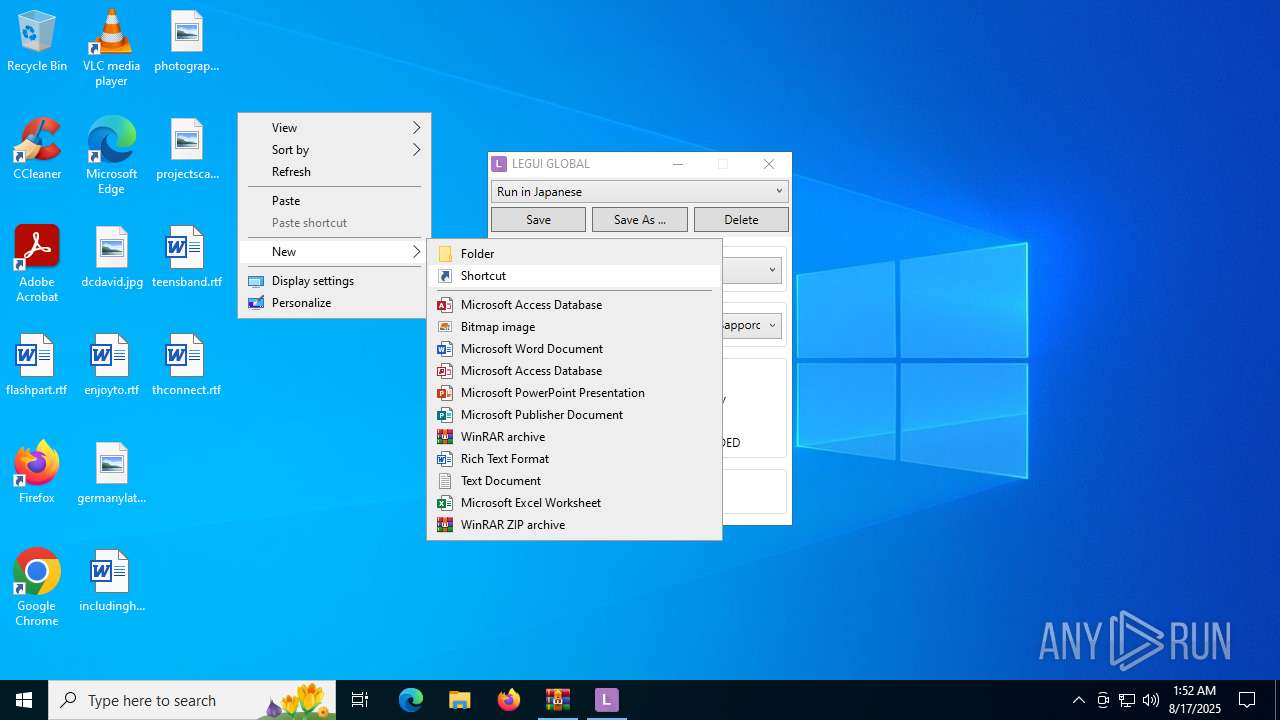
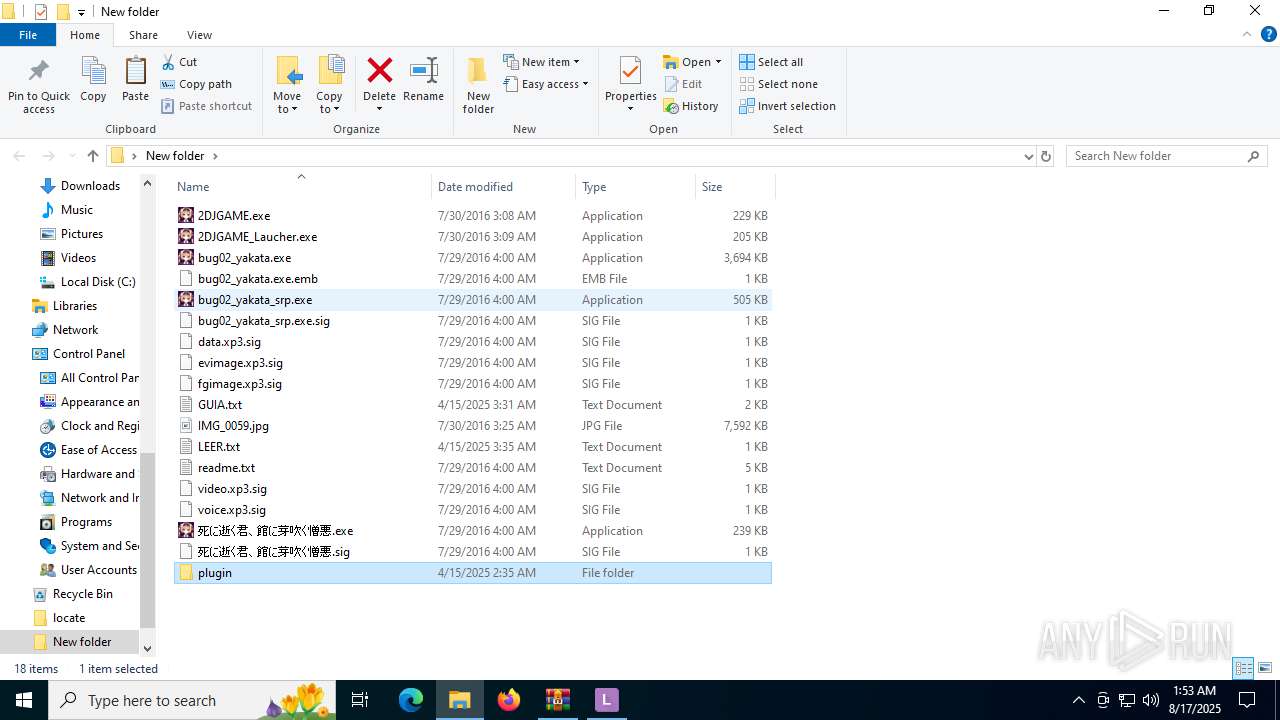
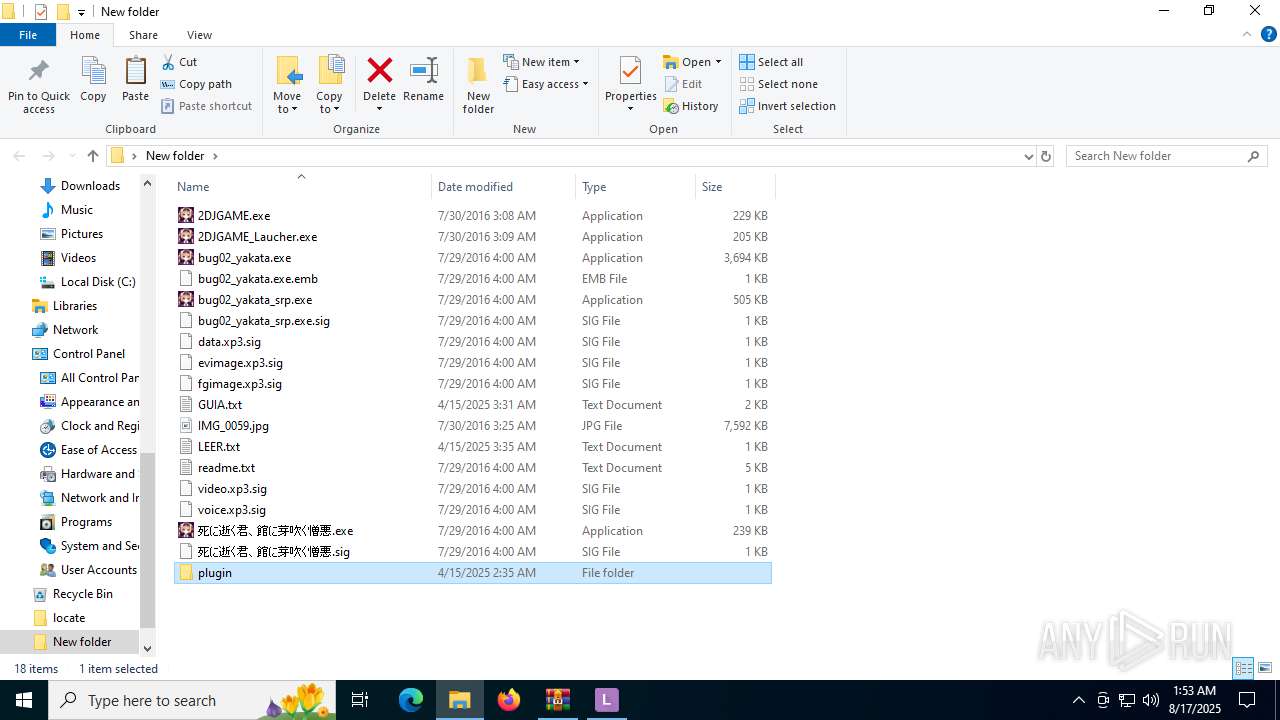
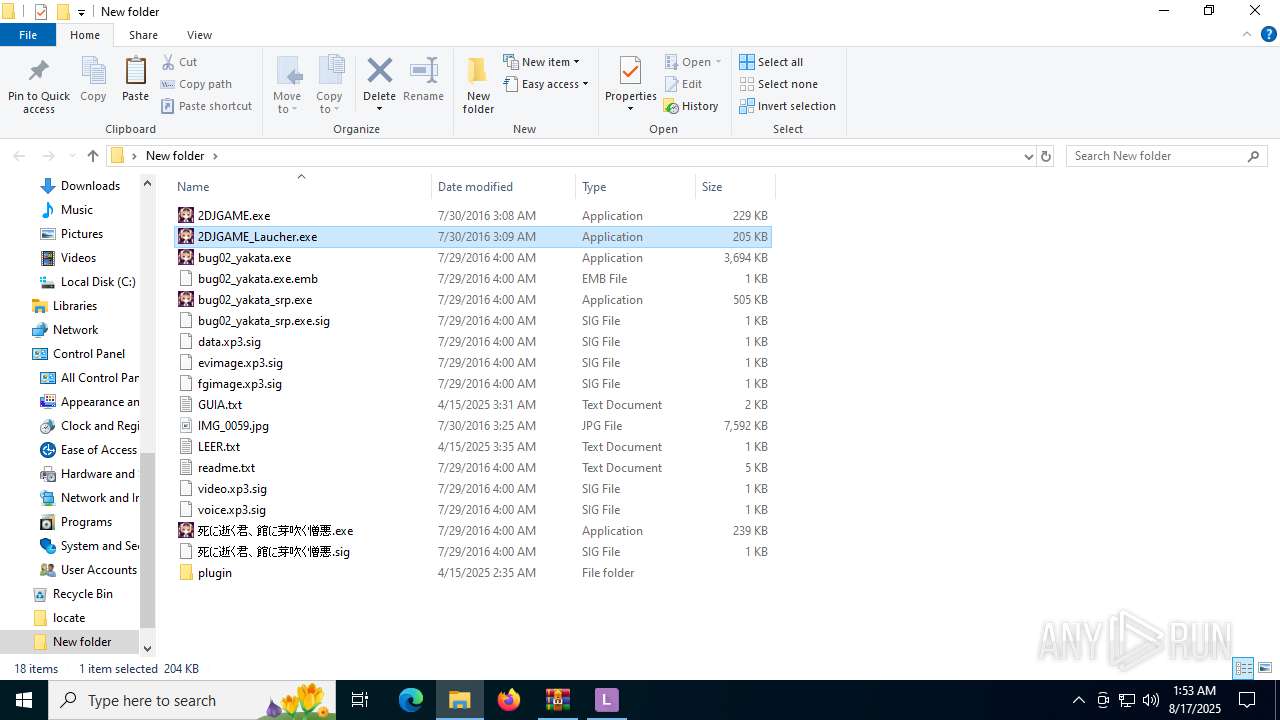
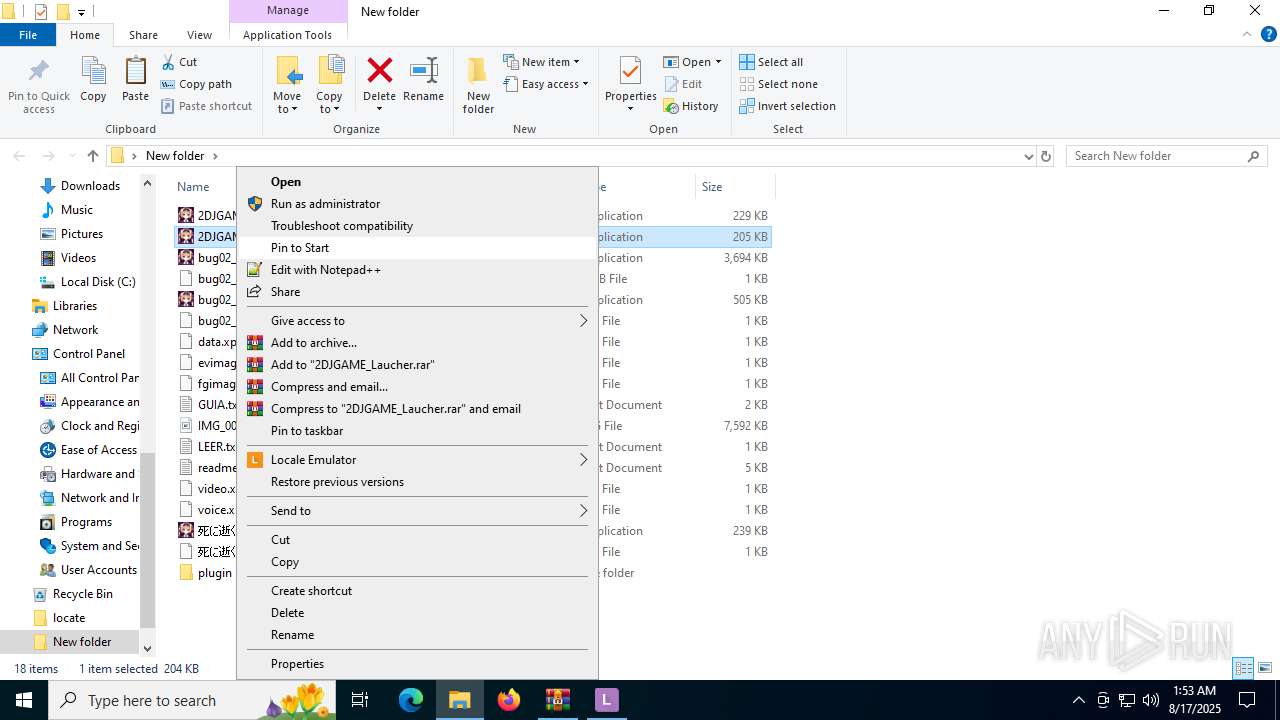
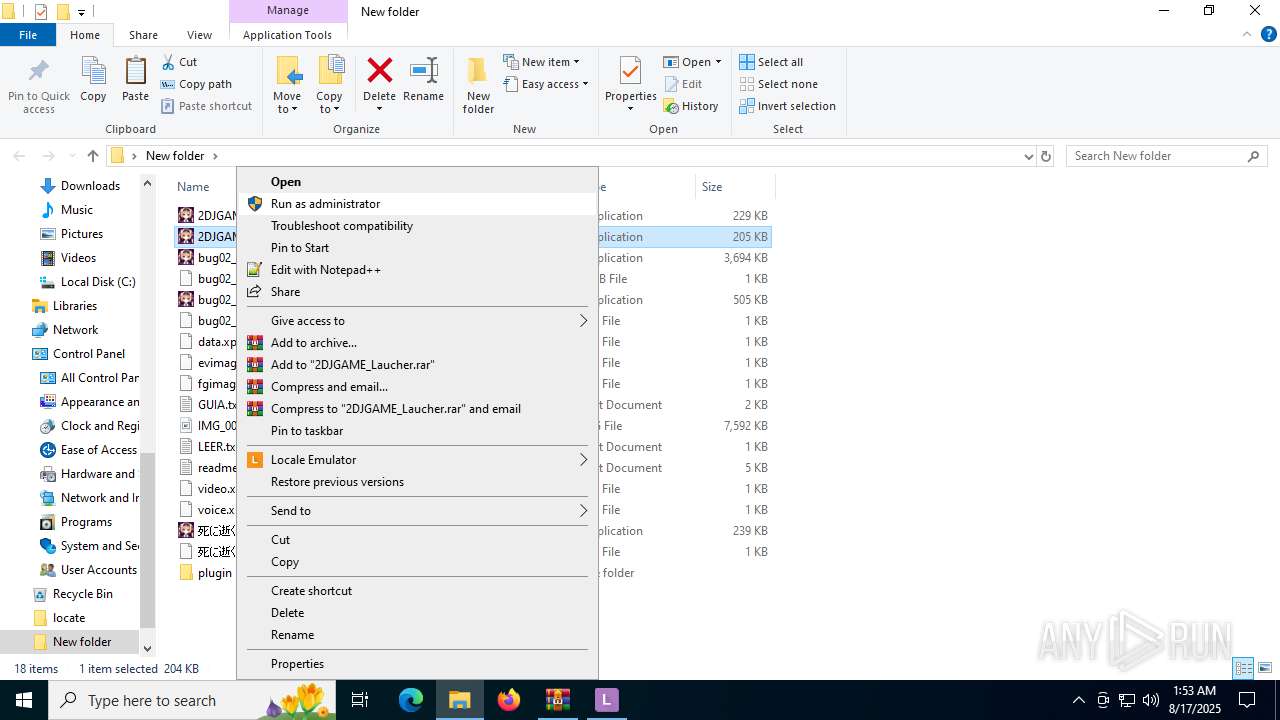
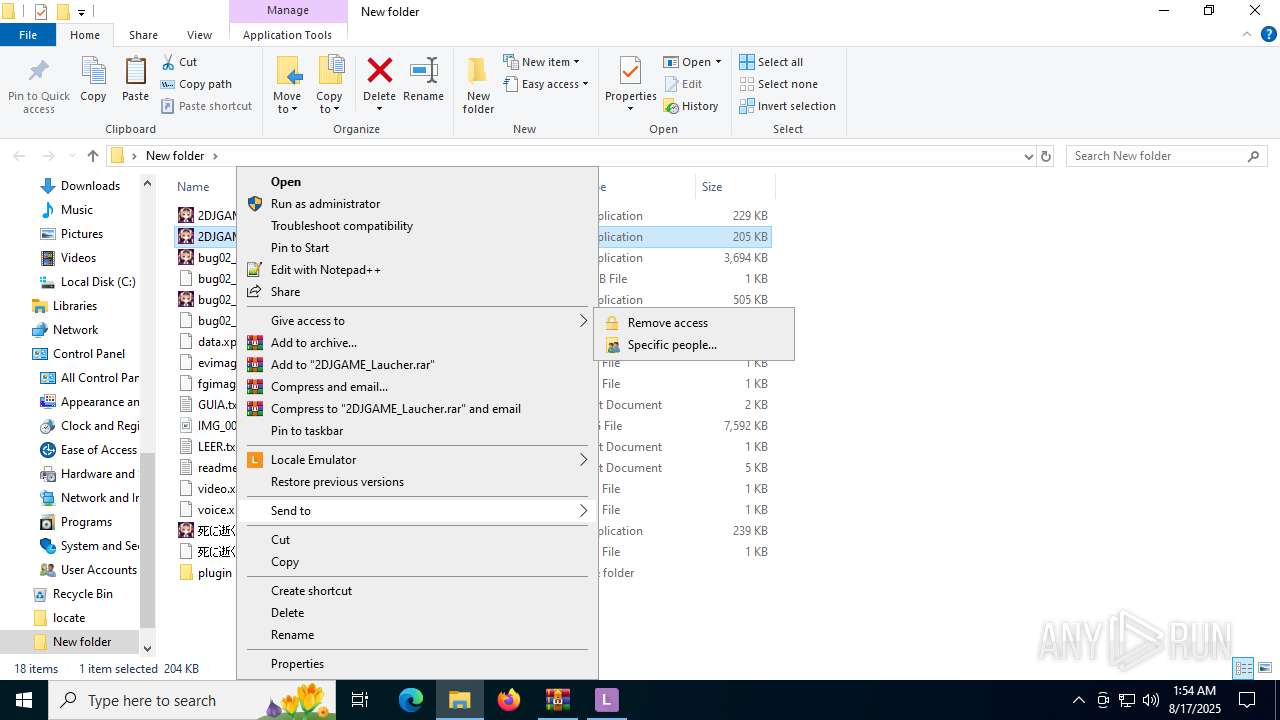
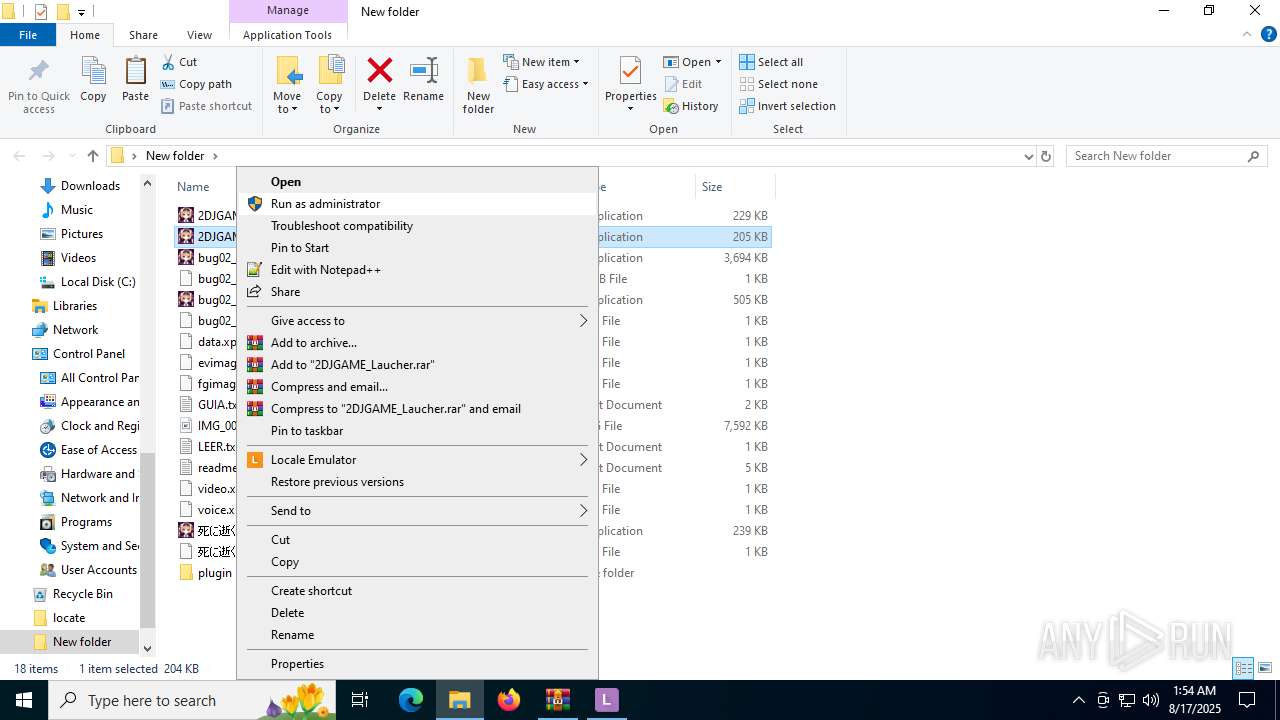
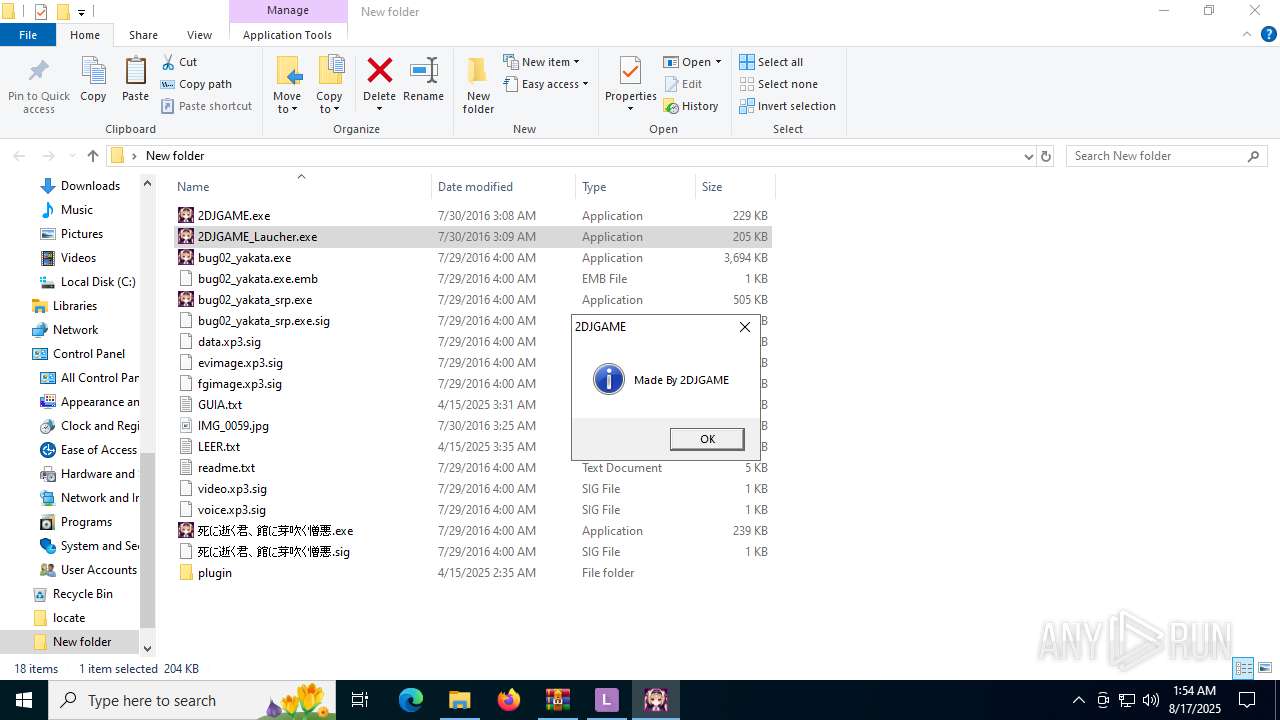
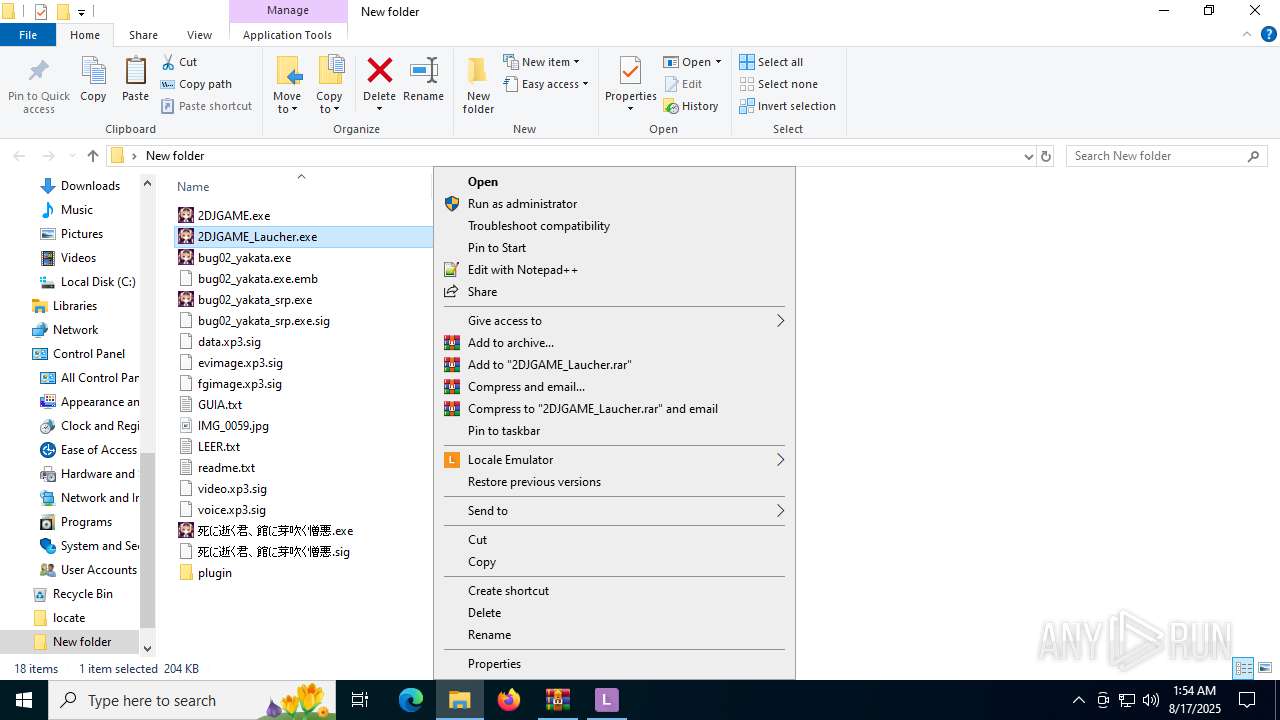
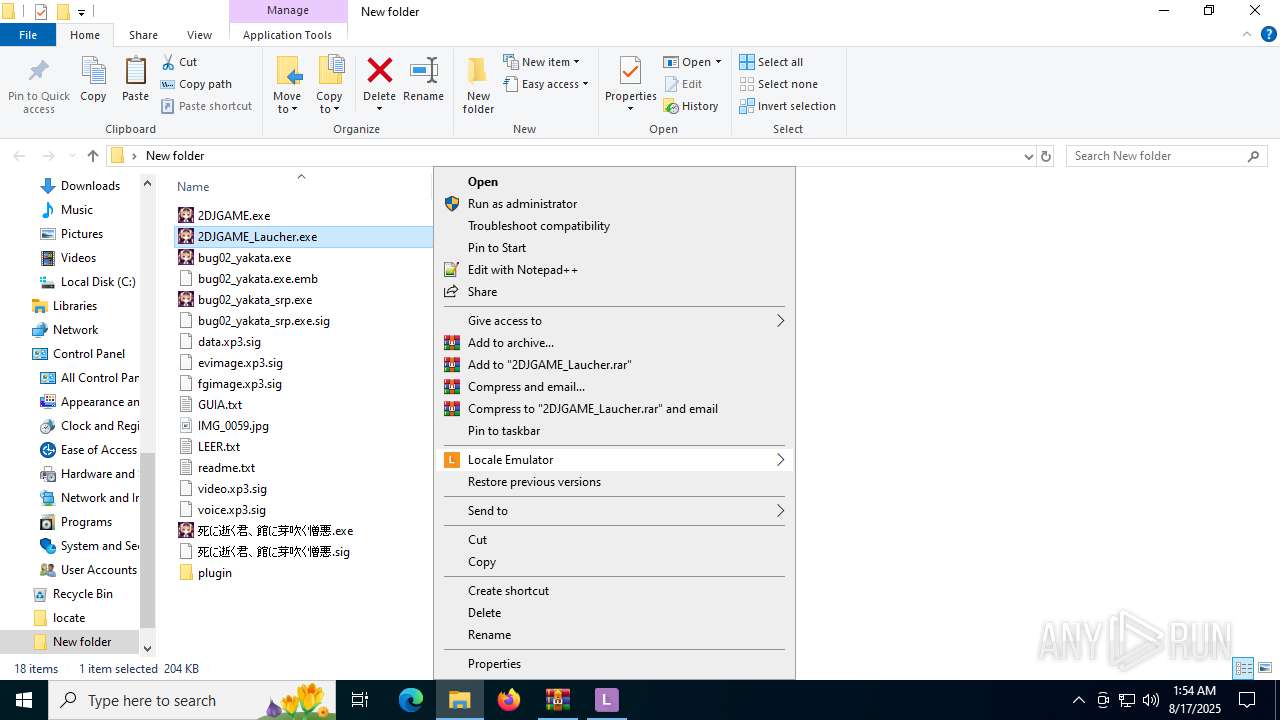
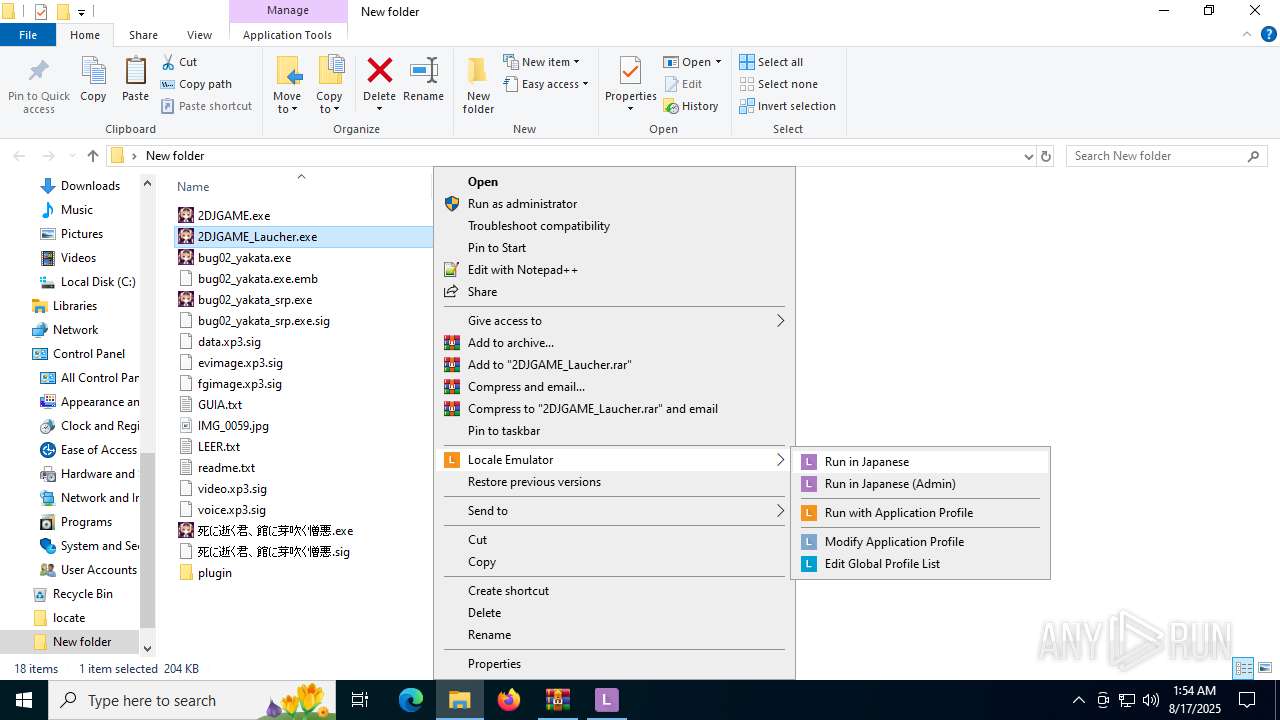
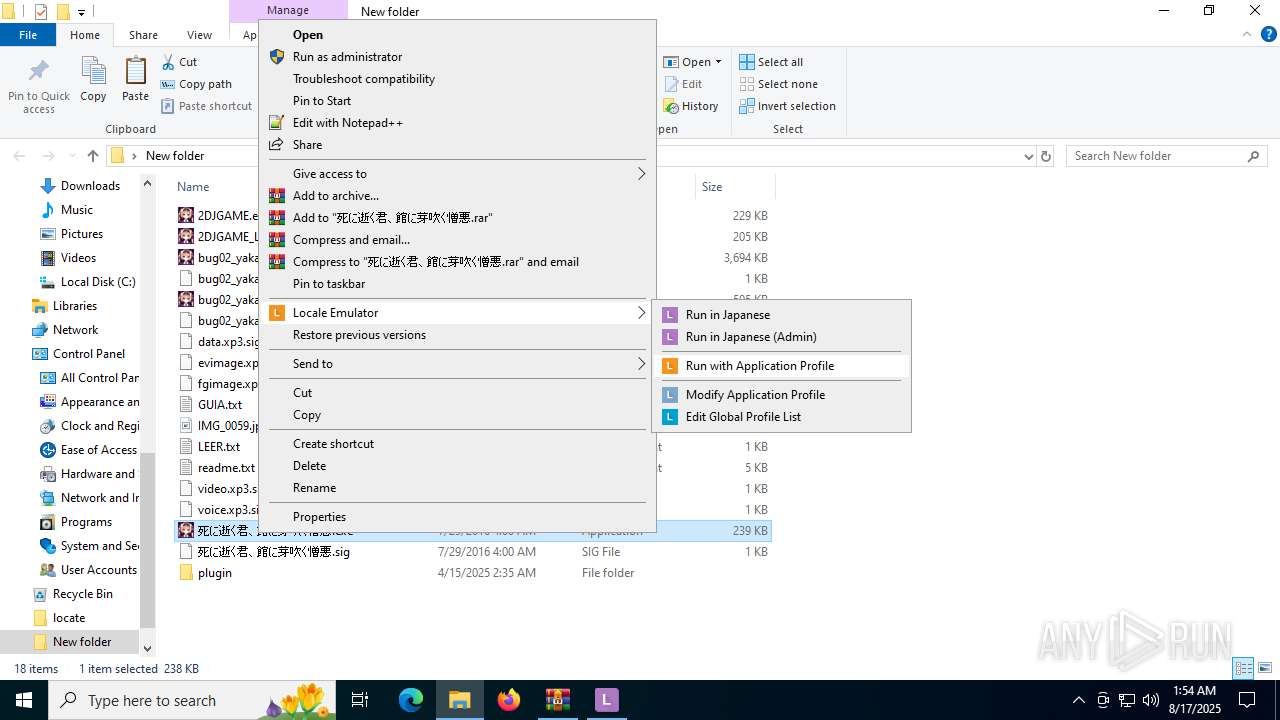
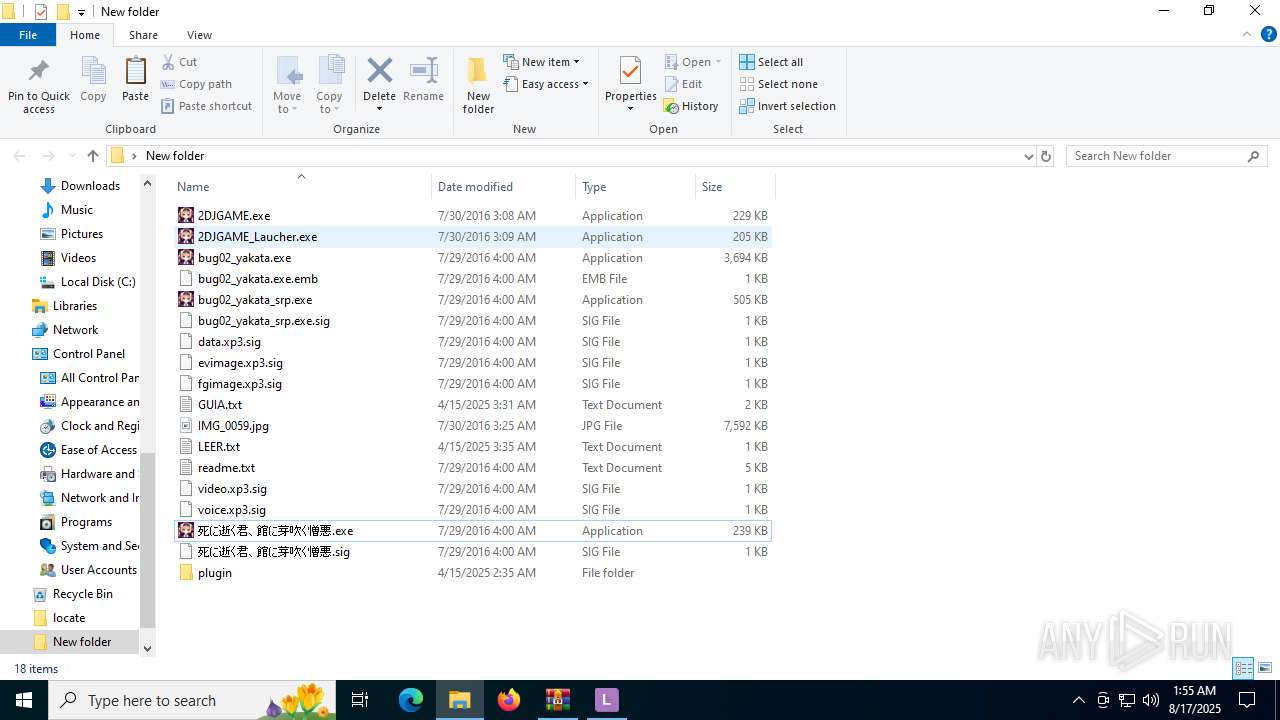
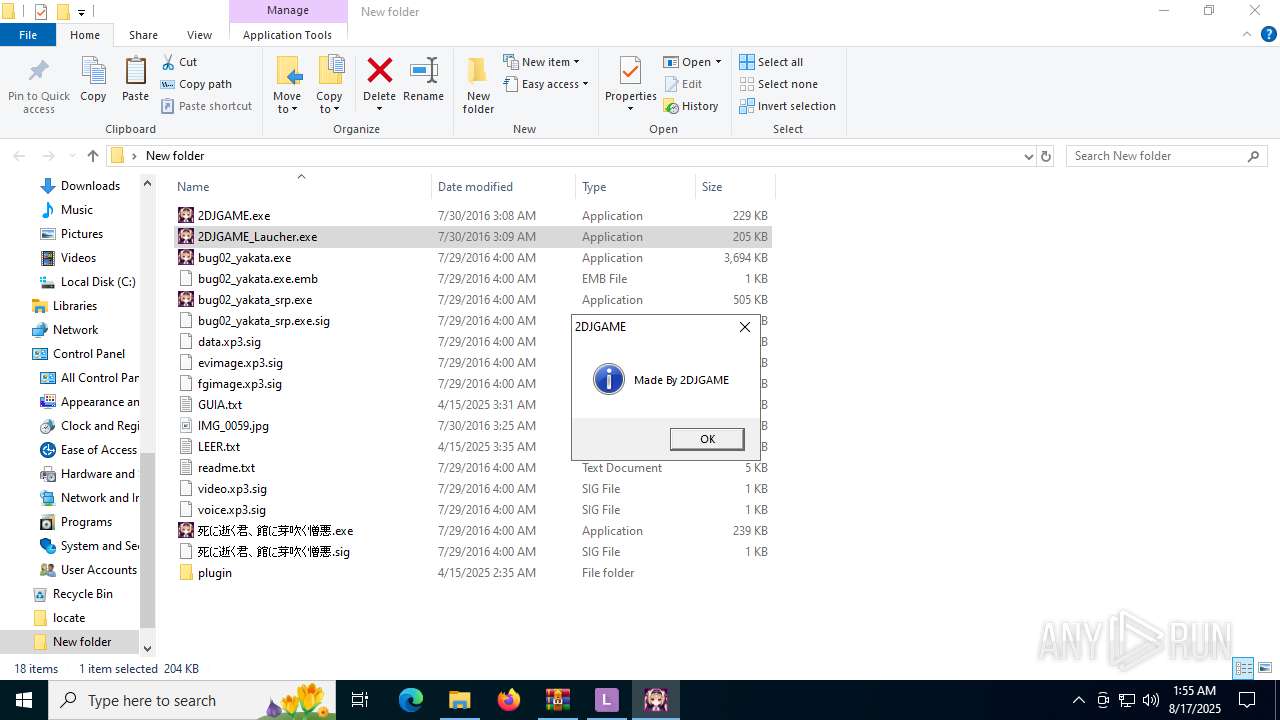
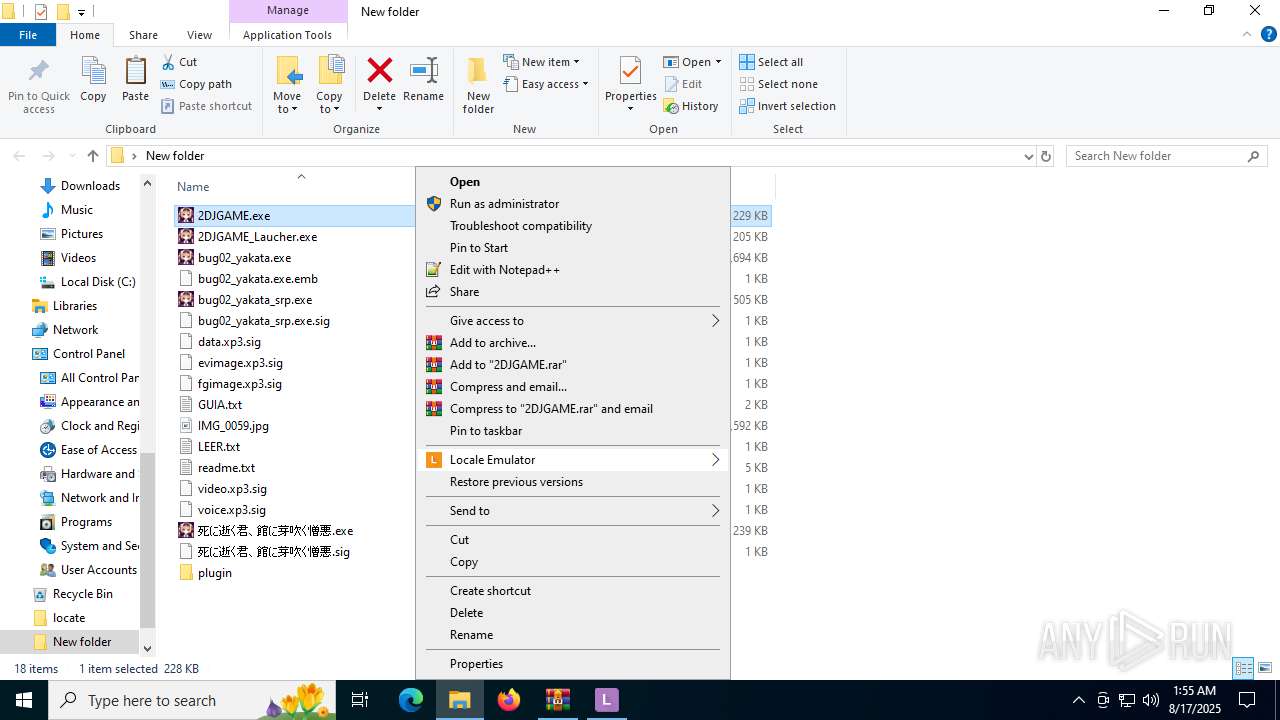
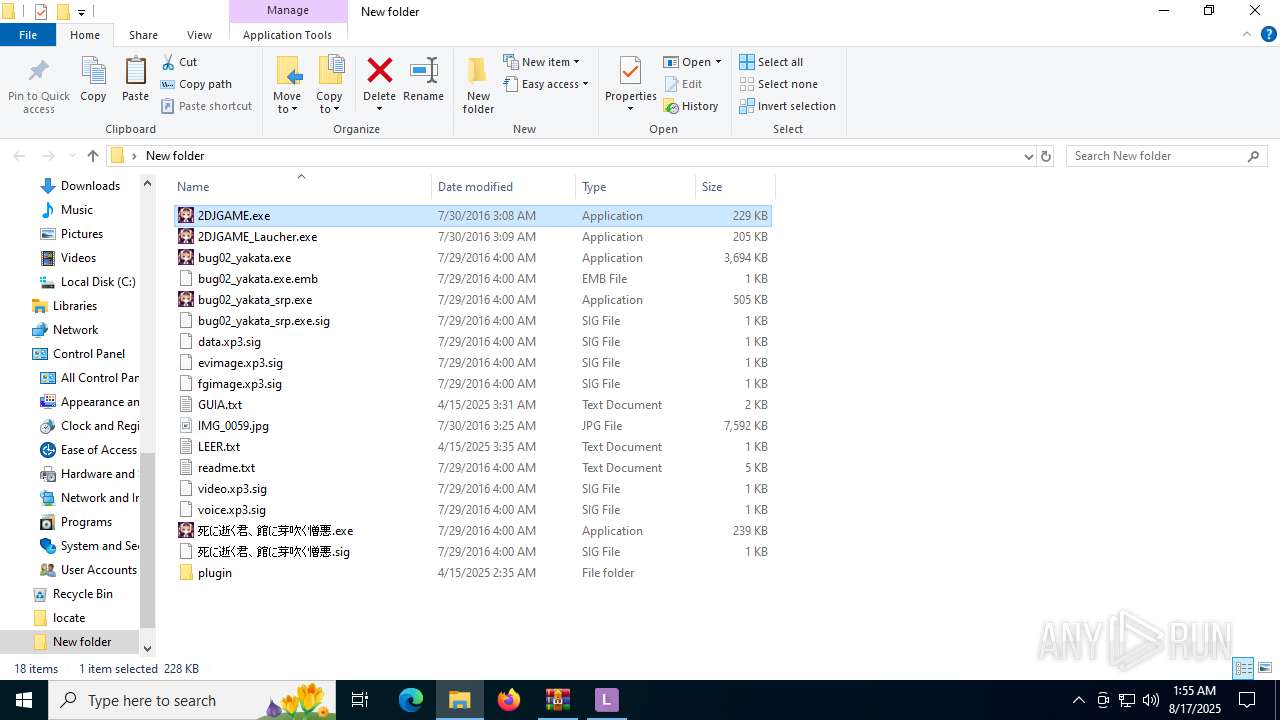
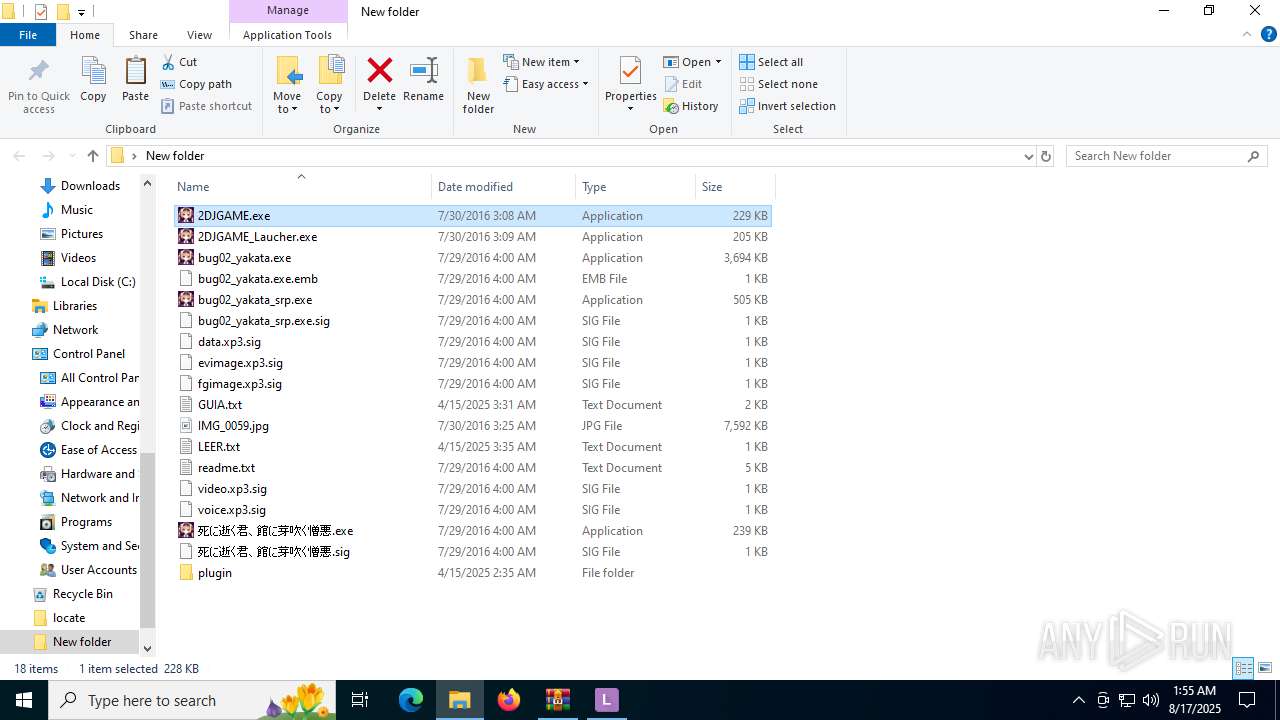
Manual execution by a user
- 2DJGAME_Laucher.exe (PID: 4520)
- LEProc.exe (PID: 6980)
- LEProc.exe (PID: 5824)
- msedge.exe (PID: 3392)
- 2DJGAME_Laucher.exe (PID: 4232)
- 2DJGAME.exe (PID: 6348)
- LEProc.exe (PID: 512)
- notepad.exe (PID: 5220)
- notepad.exe (PID: 3624)
Disables trace logs
- LEUpdater.exe (PID: 6812)
Reads Environment values
- LEUpdater.exe (PID: 6812)
- identity_helper.exe (PID: 1352)
- identity_helper.exe (PID: 4448)
Application launched itself
- msedge.exe (PID: 4080)
- msedge.exe (PID: 2460)
- msedge.exe (PID: 3392)
- msedge.exe (PID: 1948)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5220)
- notepad.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
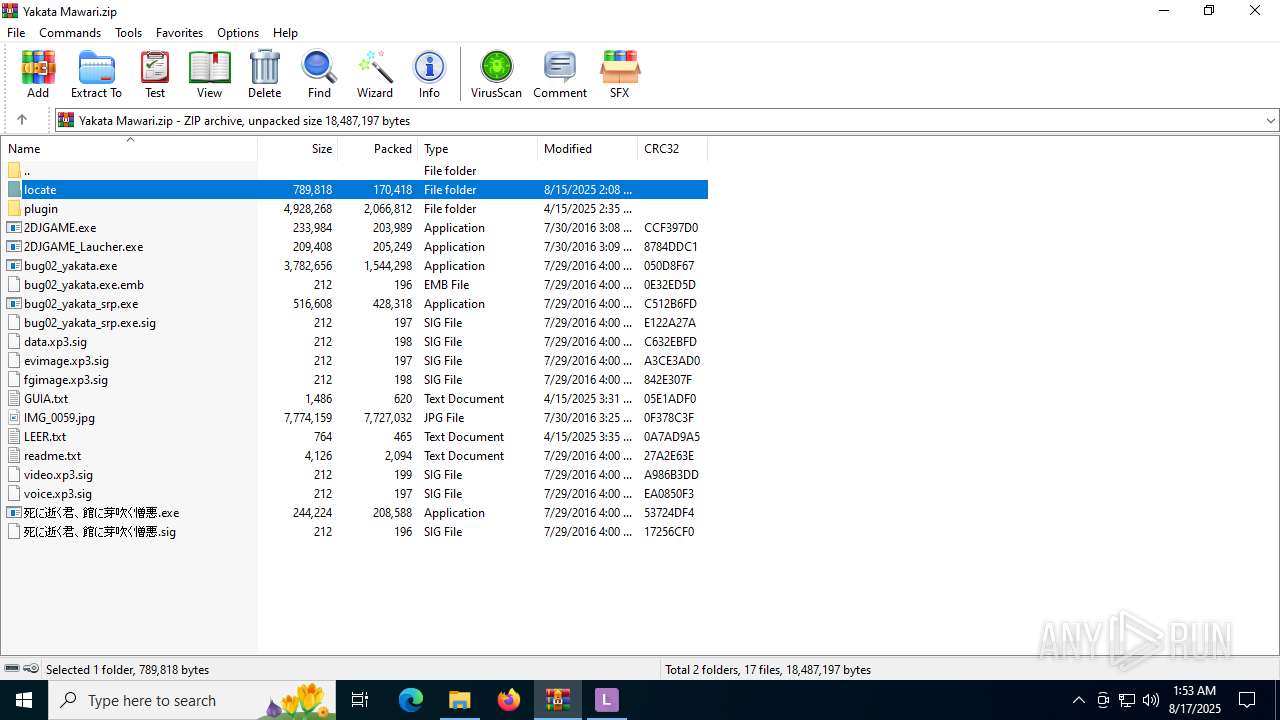
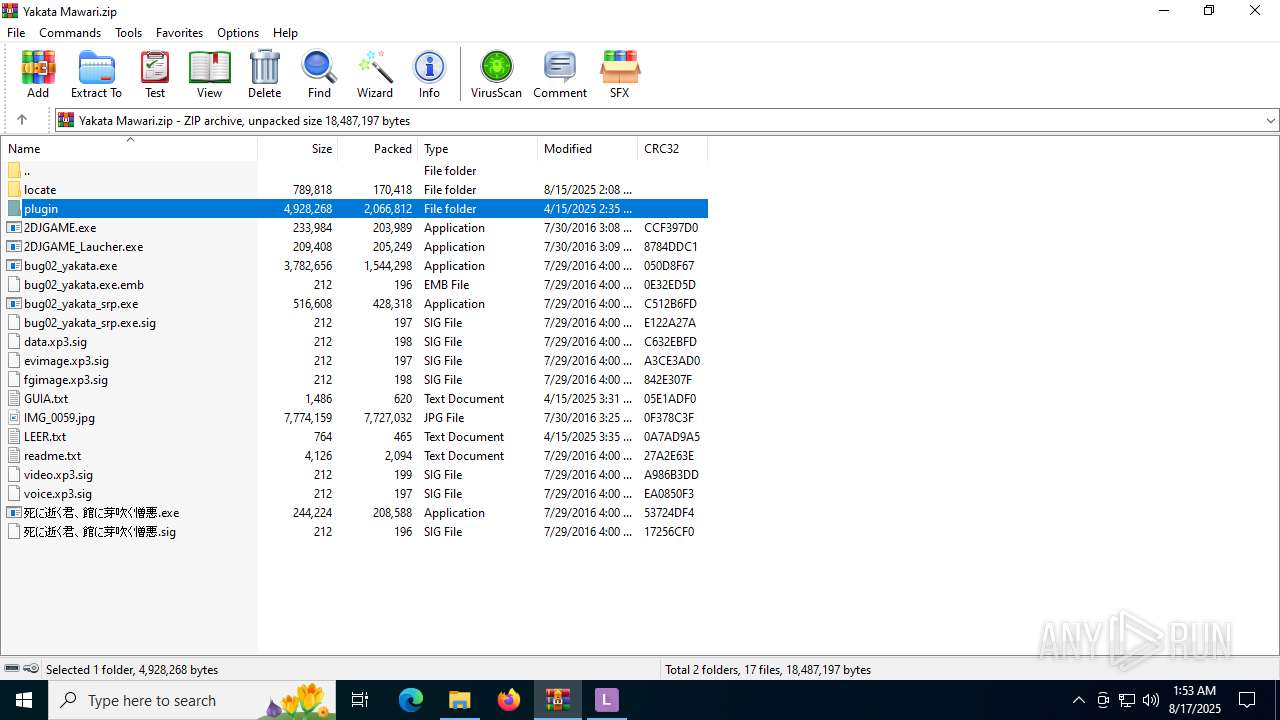
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:07:29 00:00:00 |
| ZipCRC: | 0x27a2e63e |
| ZipCompressedSize: | 2094 |
| ZipUncompressedSize: | 4126 |
| ZipFileName: | readme.txt |
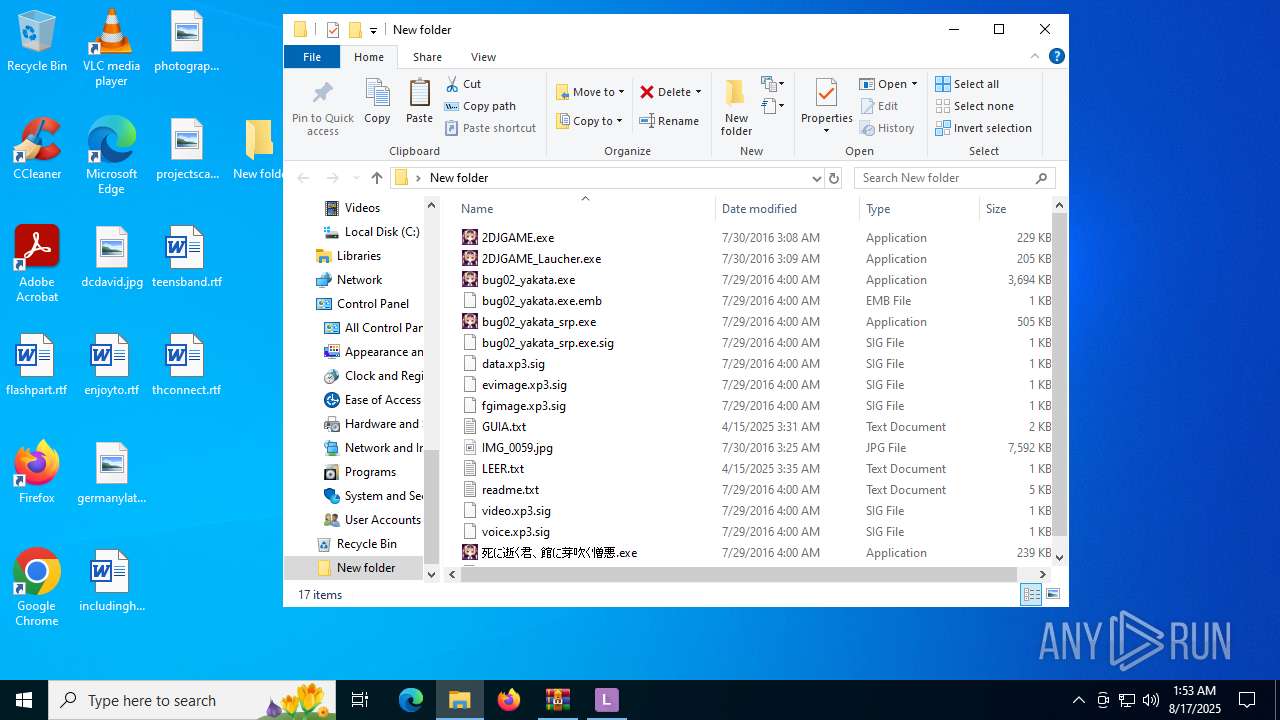
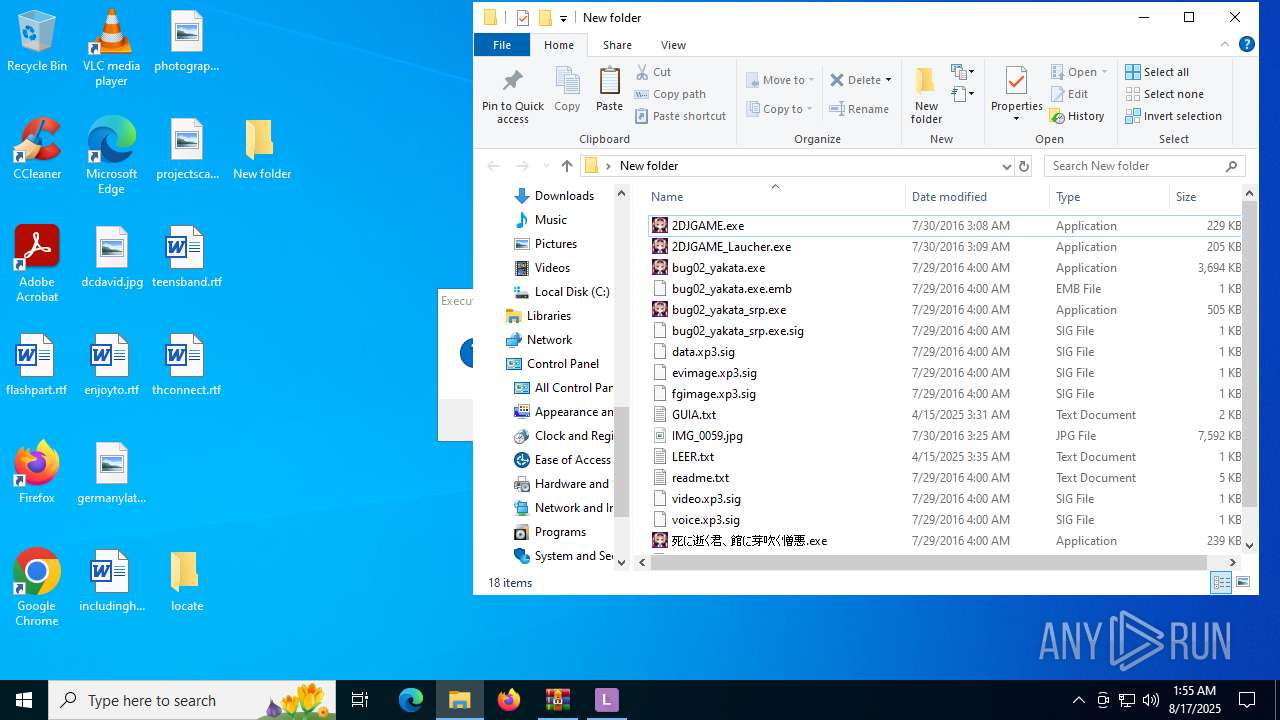
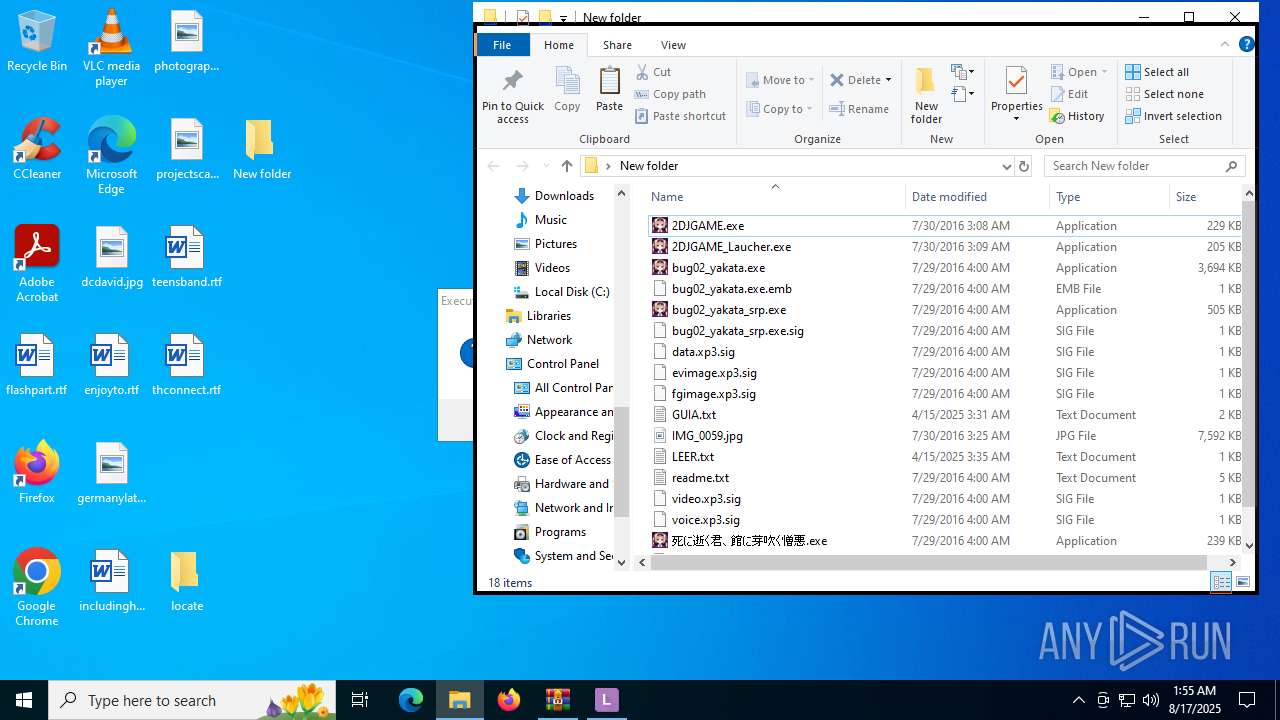
Total processes
226
Monitored processes
76
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5472,i,10234293629343212156,8459170687547123485,262144 --variations-seed-version --mojo-platform-channel-handle=4308 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 512 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\LEProc.exe" -runas "d8d9f3b2-7836-484a-907d-42d97c34ccab" "C:\Users\admin\Desktop\New folder\2DJGAME.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\LEProc.exe | — | explorer.exe | |||||||||||
User: admin Company: Paddy Xu Integrity Level: MEDIUM Description: LEProc Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 700 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5920,i,10234293629343212156,8459170687547123485,262144 --variations-seed-version --mojo-platform-channel-handle=5760 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\Desktop\New folder\bug02_yakata.exe" -launchkey=nkgnaiclimlnebcpjfhmdmpofdlmnmhh | C:\Users\admin\Desktop\New folder\bug02_yakata.exe | — | 2DJGAME_Laucher.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: TVP(KIRIKIRI) 2 core / Scripting Platform for Win32 Exit code: 0 Version: 2.31.2013.330 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5116,i,8012475530129768292,14306691419389643887,262144 --variations-seed-version --mojo-platform-channel-handle=5148 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4760,i,8012475530129768292,14306691419389643887,262144 --variations-seed-version --mojo-platform-channel-handle=4776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2432,i,10234293629343212156,8459170687547123485,262144 --variations-seed-version --mojo-platform-channel-handle=2428 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x8c,0x90,0x94,0x1e4,0x294,0x7ffc3c11f208,0x7ffc3c11f214,0x7ffc3c11f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Users\admin\Desktop\New folder\2DJGAME.exe" | C:\Users\admin\Desktop\New folder\2DJGAME.exe | — | 2DJGAME_Laucher.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
35 252
Read events
35 175
Write events
77
Delete events
0
Modification events
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Yakata Mawari.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
232
Suspicious files
289
Text files
567
Unknown types
0
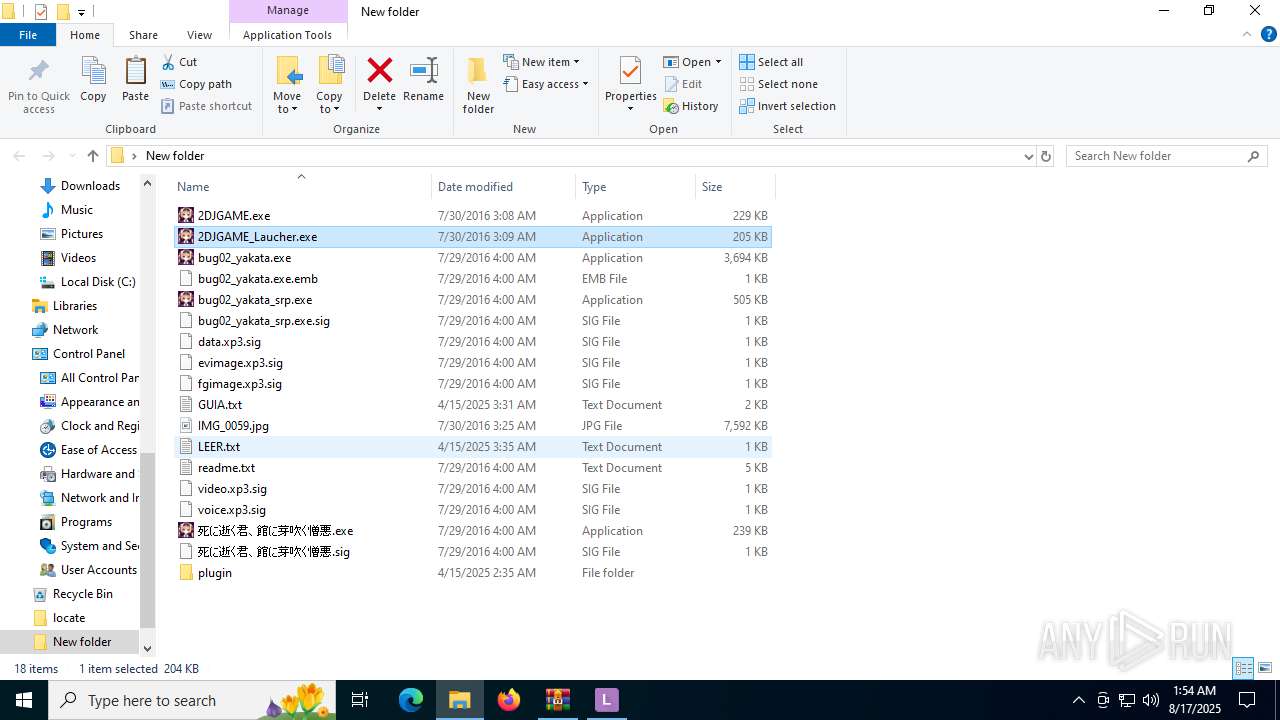
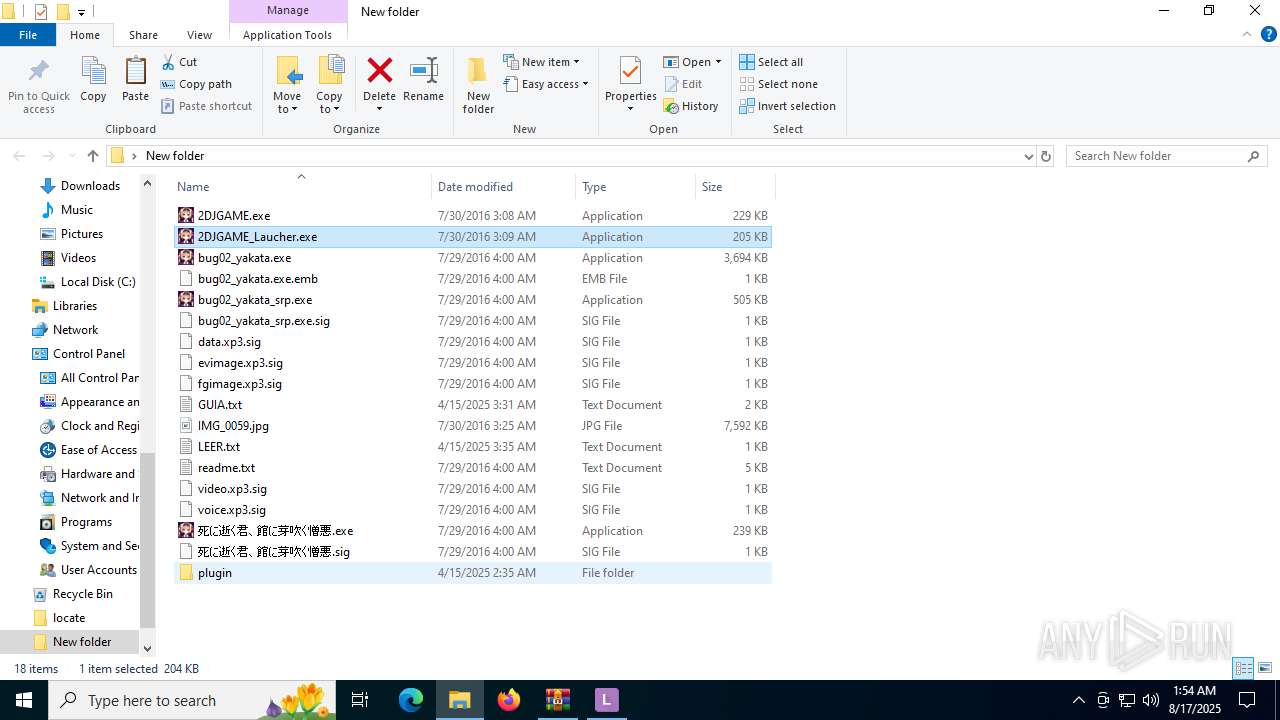
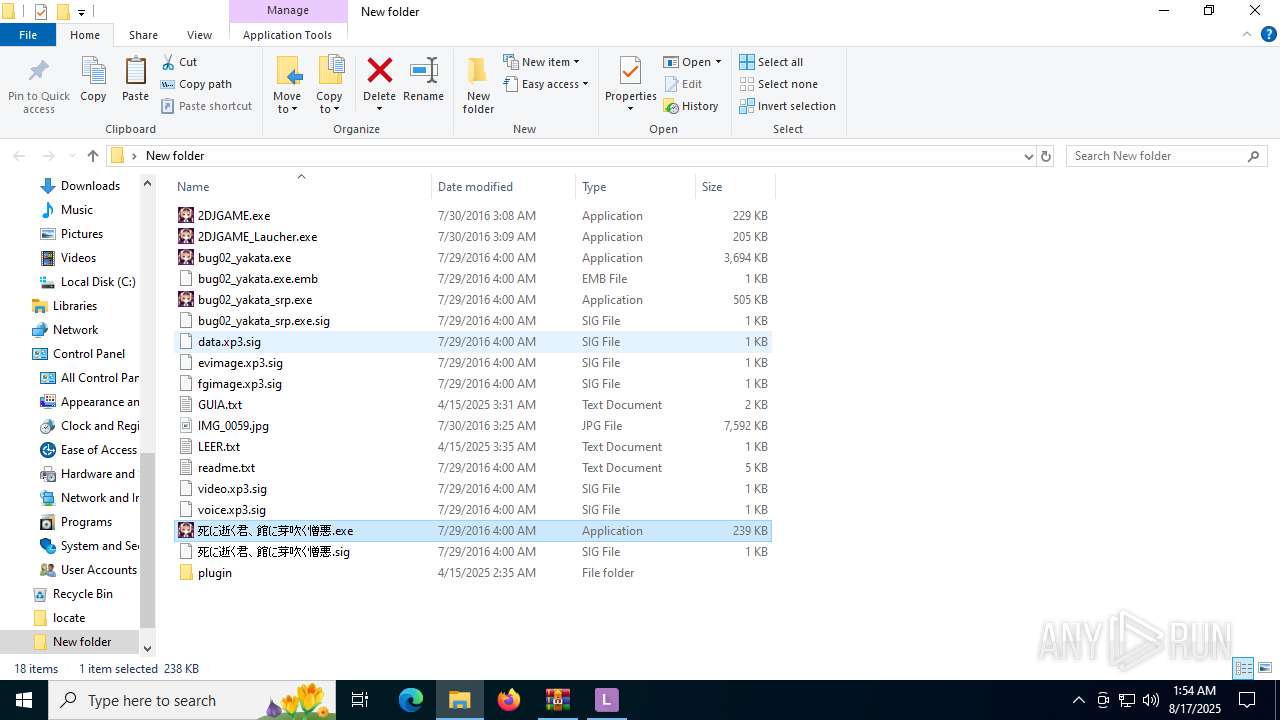
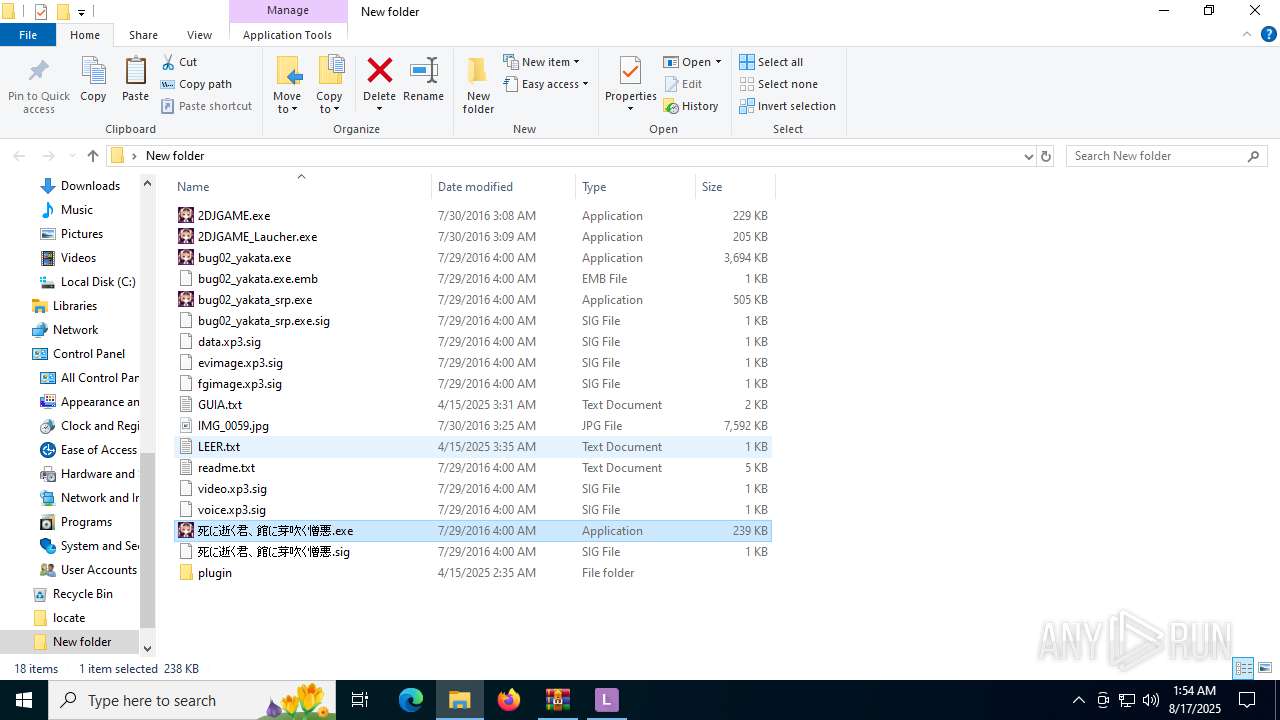
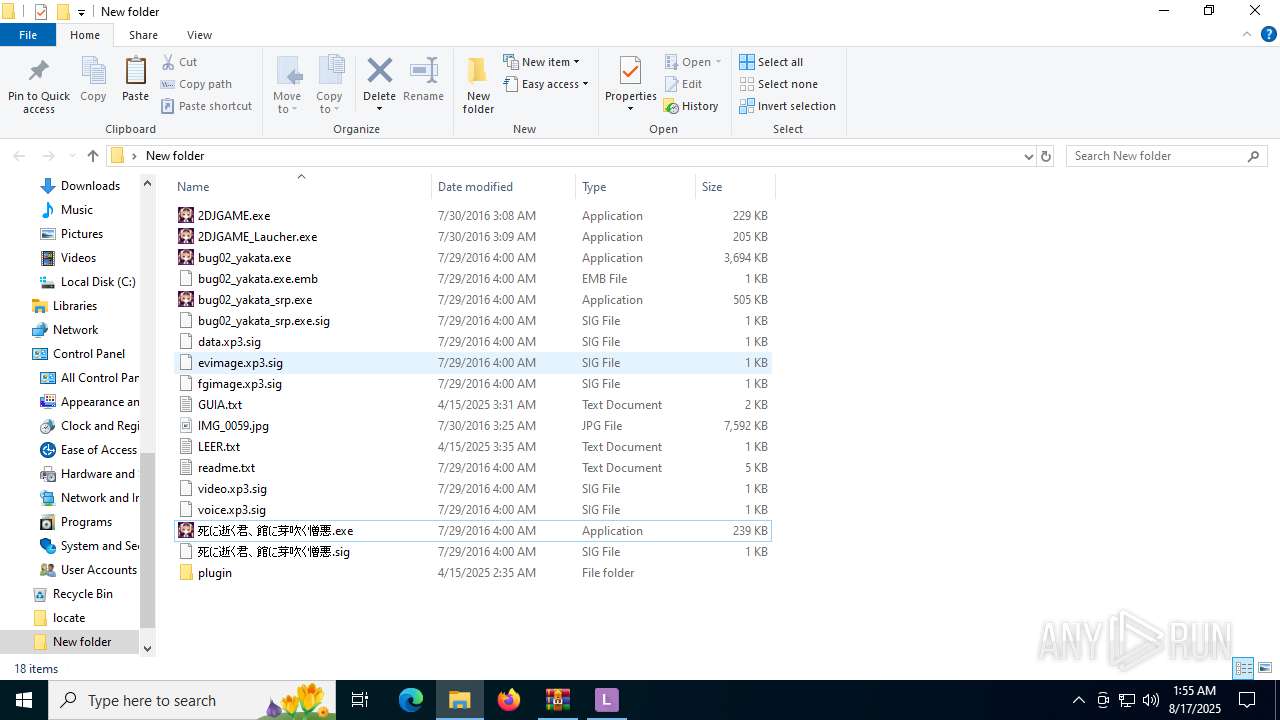
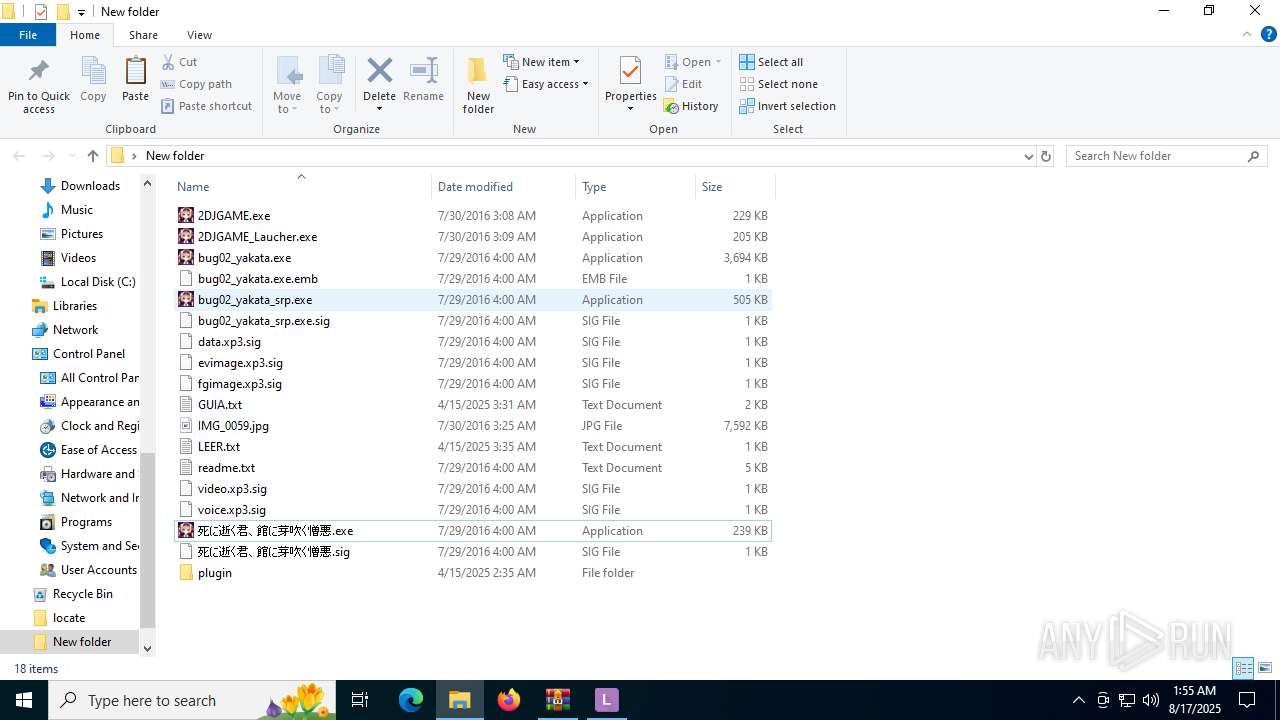
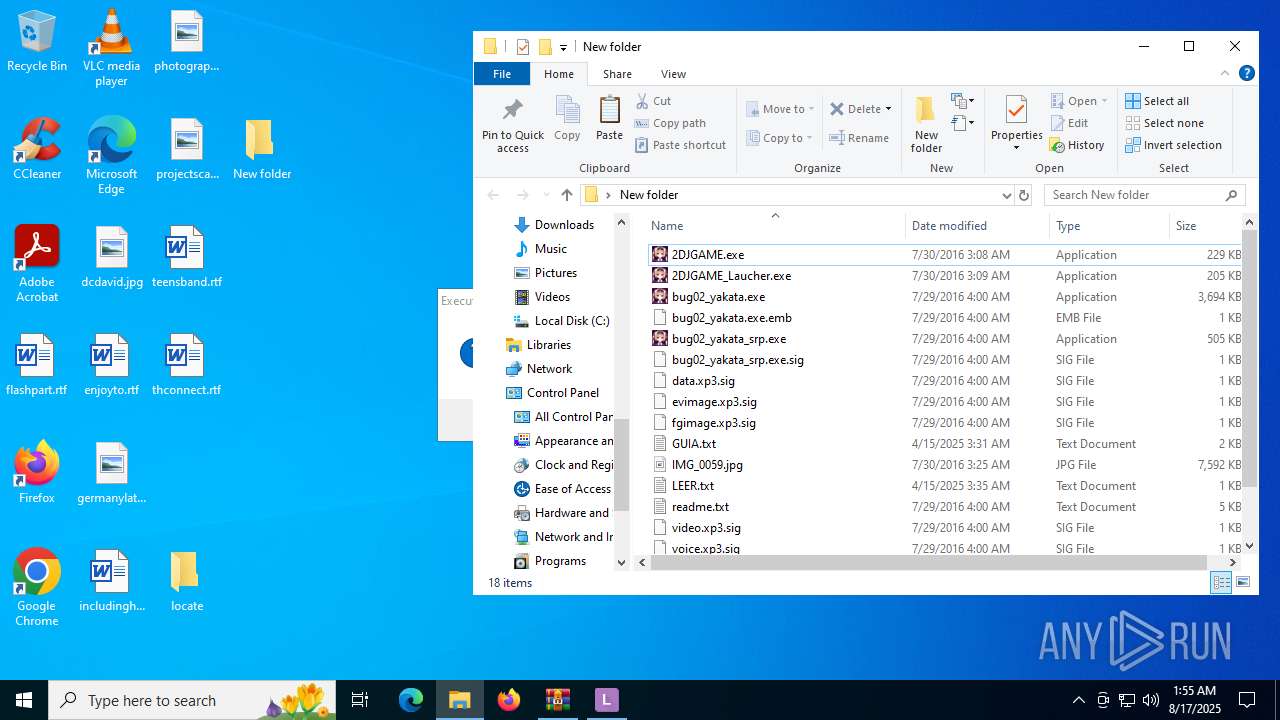
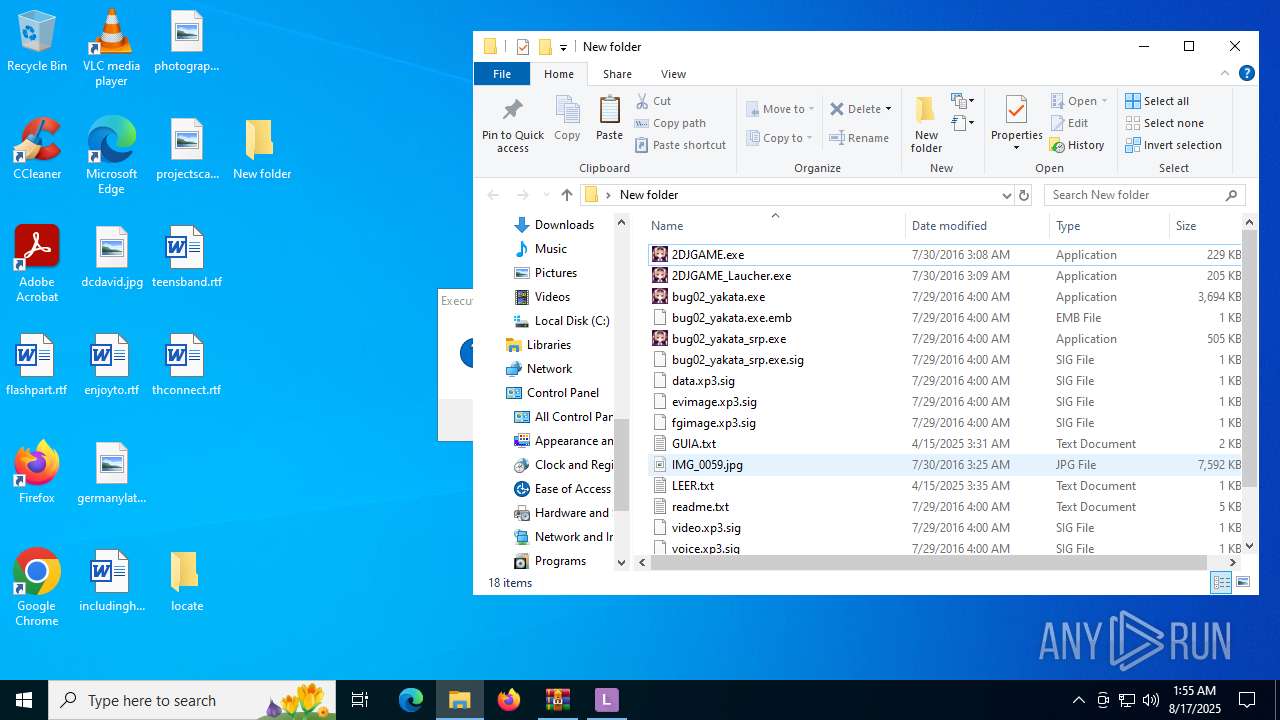
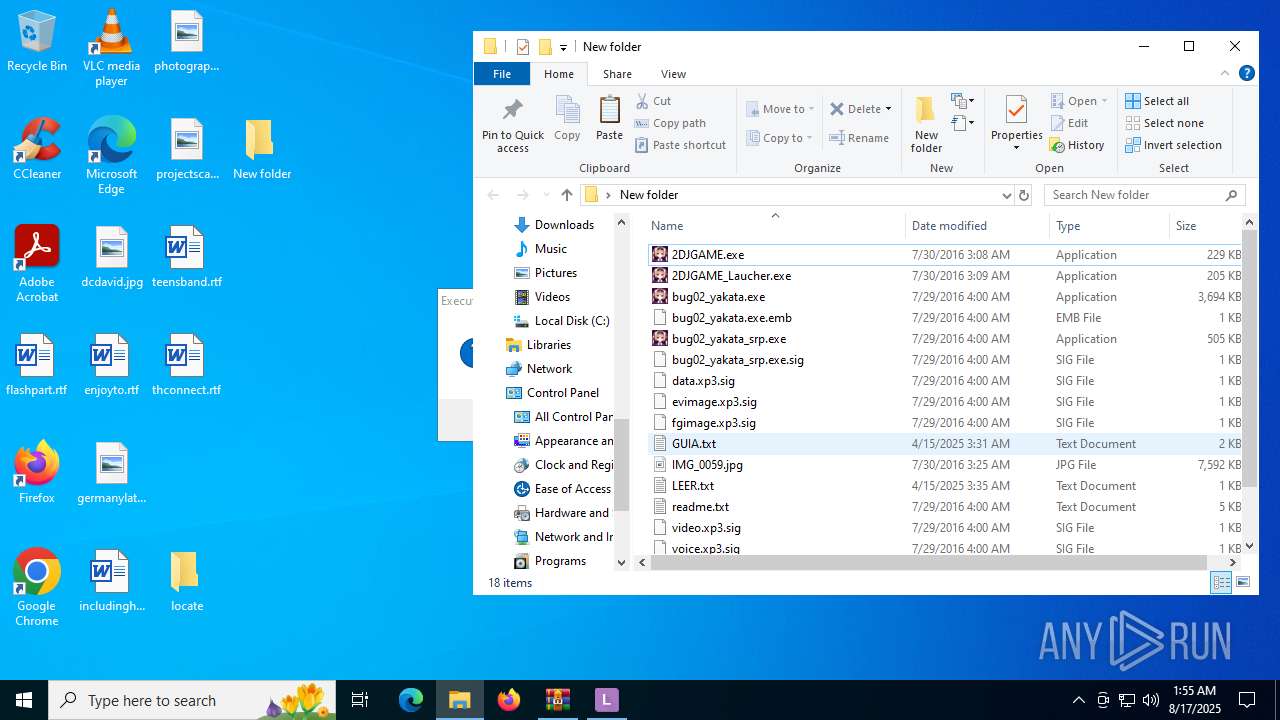
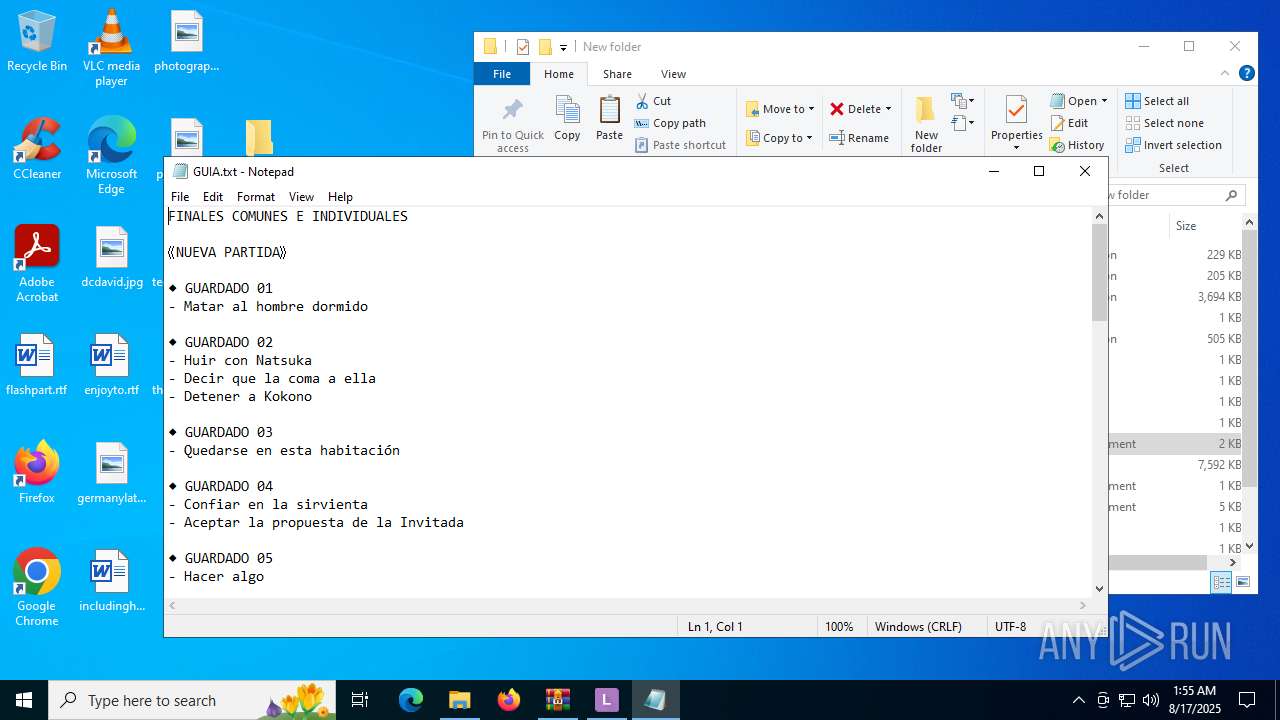
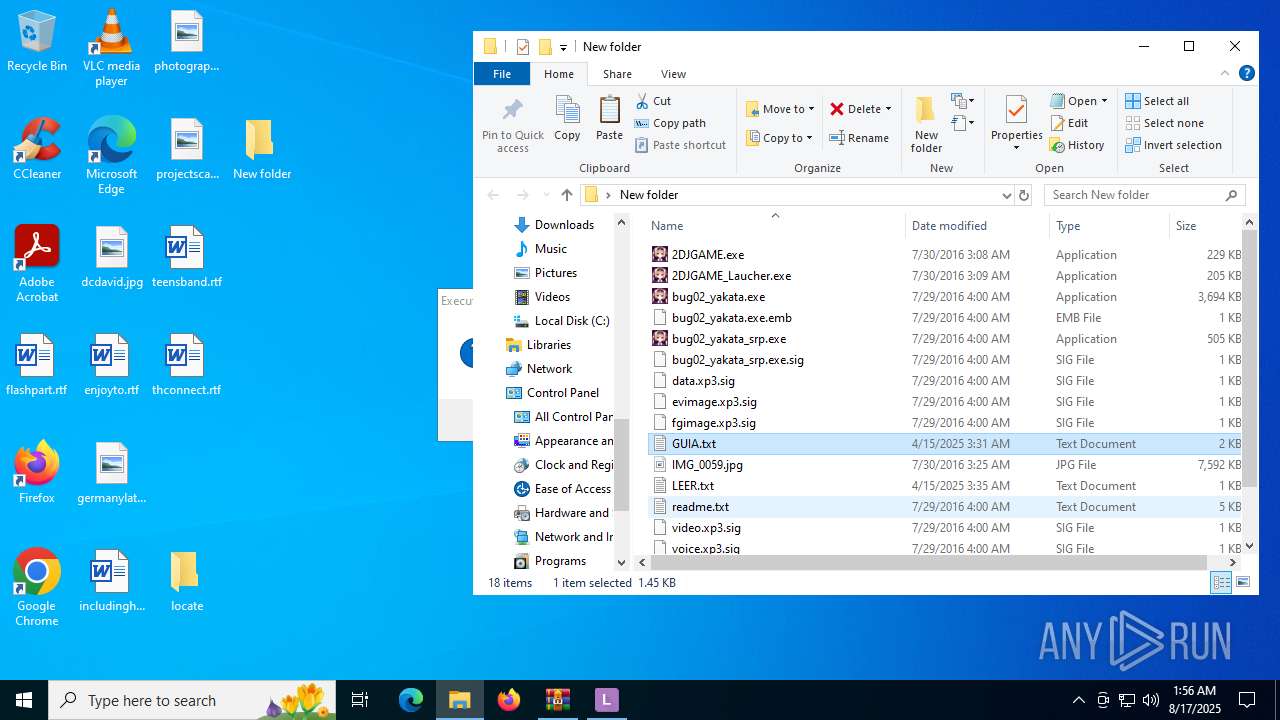
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\bug02_yakata.exe.emb | text | |
MD5:1AF304CBD5E711ED8A481739531298C2 | SHA256:1E0EEAEB42A11ACA10B69875838444D34543DC94ADF8E22D6BAD6166C7E2726B | |||
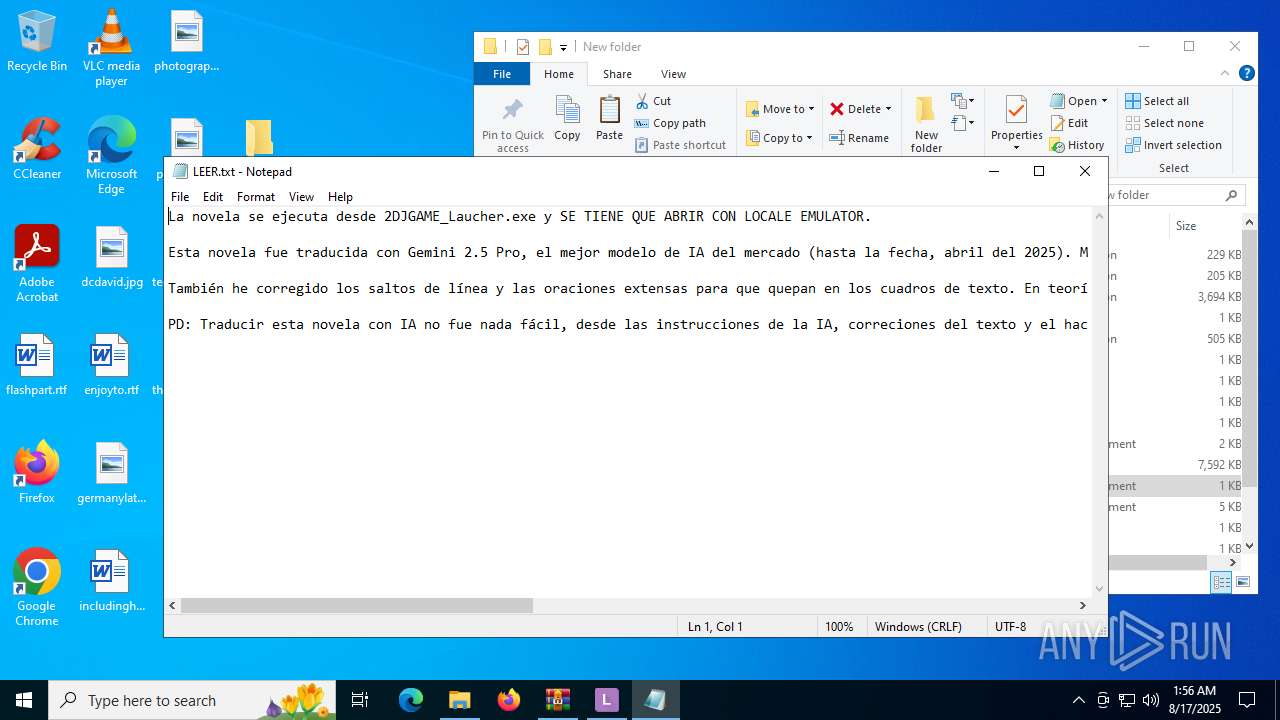
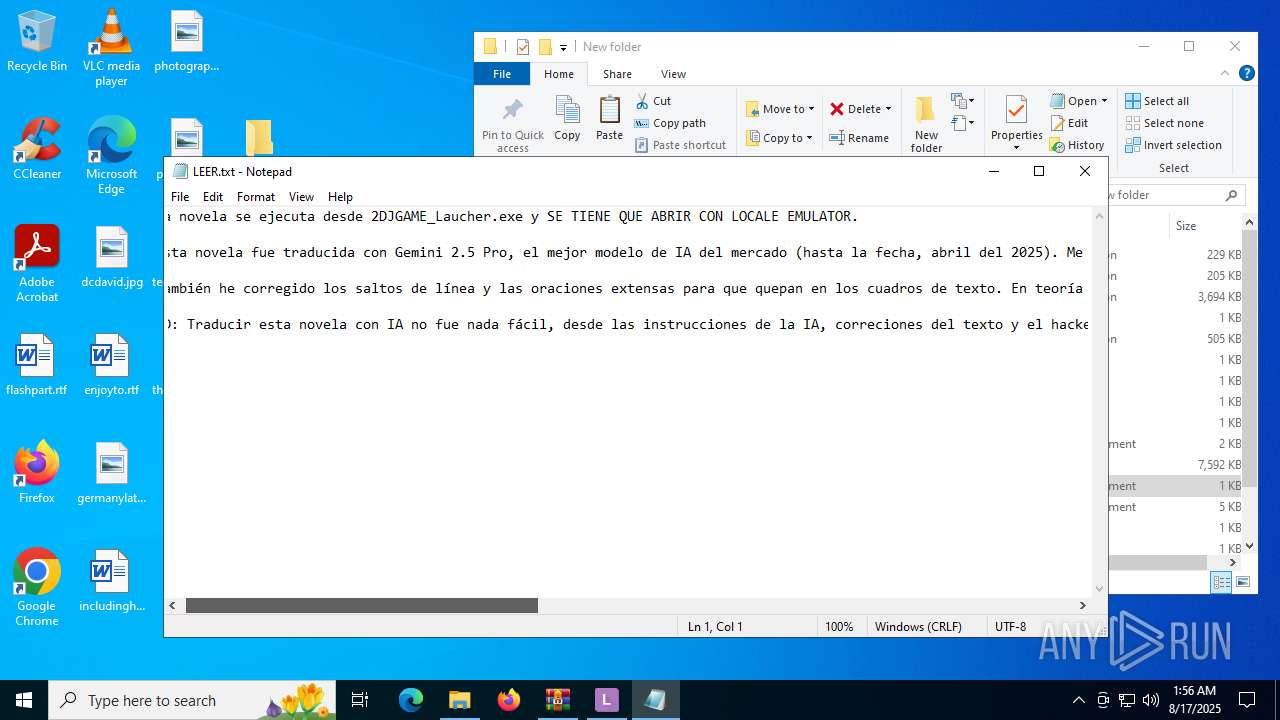
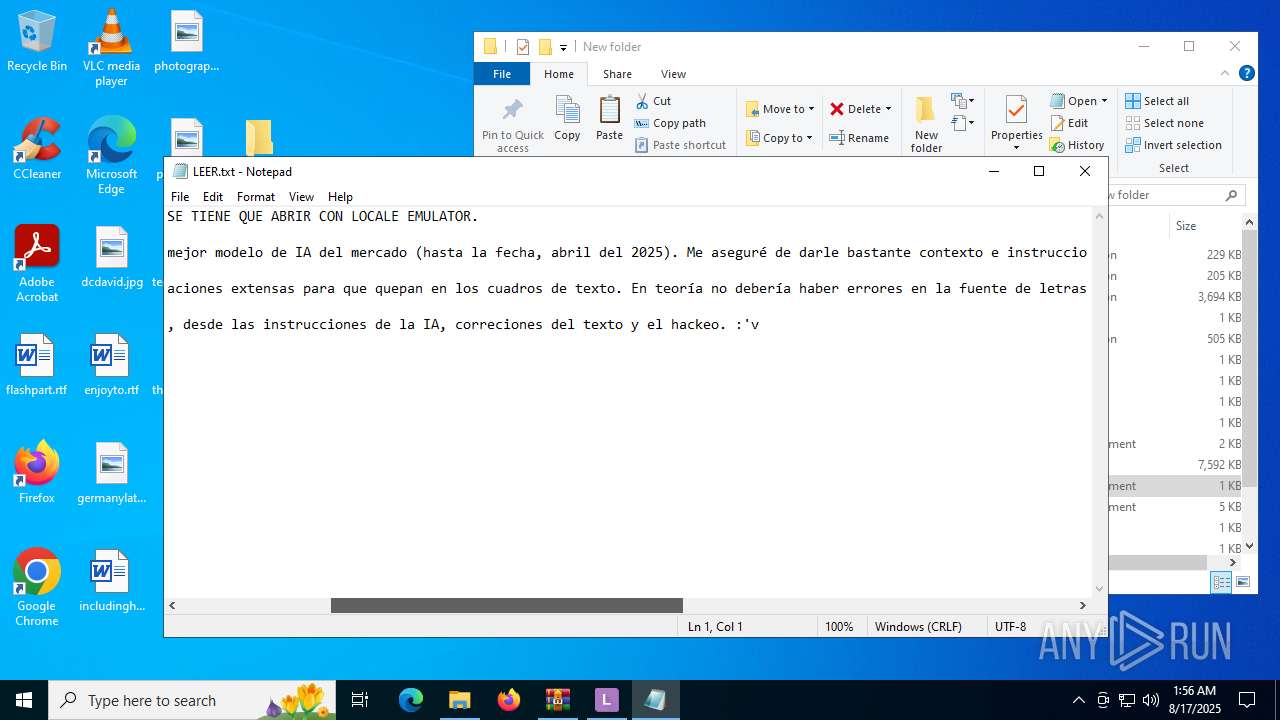
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\LEER.txt | text | |
MD5:1B64FB9C9CB14B77321490055F428090 | SHA256:99C16DA85F7FC5839AC9BD3D0B440FF5CA662F0C6EA3773CF100116DD2921597 | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\bug02_yakata_srp.exe.sig | text | |
MD5:E87E1D6D04938D1DF7E40BF378EC84D3 | SHA256:7A2641AF3005F7315A365EA3A58E400F437CCC31BF162782C44625A9A62784FF | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\data.xp3.sig | text | |
MD5:D9951D93CE383864F67556BE61FD21B5 | SHA256:5896E40D44746B766837509CBDFC50DFE85BCC6AC06412F6A439B4FA861EB69C | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\readme.txt | text | |
MD5:E44A110D65B5A9A80EF84B2CFE602AC6 | SHA256:B2F7715A91734E1606BCF38D19BF10AD9B4B407968B70DEF0389792CA36B2B5C | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\Lang\DefaultLanguage.xaml | text | |
MD5:C27AF0F032D1A4F9FF0DF7AB652711DE | SHA256:D677F5287289C9A6BA13F512D4F1BD21429671790654E8342A2B45F230A12A16 | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\Lang\ca.xml | xml | |
MD5:5349503FECE5ADD350680291E6002C04 | SHA256:415A4AE0CDF2E264D612F86AF4592C2EA31E482643FD43D642867EEB3D9F753B | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\死に逝く君、館に芽吹く憎悪.sig | text | |
MD5:D46D3BC7749339995EF1958150C1350B | SHA256:9F7B5F24DD7DBCCFB333783E45226CA42A9114D617BD5BDC67B2704BFCA6156C | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\Lang\cs.xaml | text | |
MD5:6A3002BE2DA6358E799CF6096CC5CD6E | SHA256:8789C3BD67941654754903A7E51108C91EED7729A25E87D002C023EB332E2ADA | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.29914\locate\Lang\de.xml | xml | |
MD5:A3A3677200FE7B776D15A926B2B87375 | SHA256:F6E48B0B8B398128C2785B9B861DABAFBB502BCB55A48B79A7AACF3714ADEE88 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
81
DNS requests
74
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5724 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2188 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2188 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.3.109.48:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4192 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:0oGNtGPee1iodx6johKm_77WQLC-L2t-vbvrkfNnzC4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6812 | LEUpdater.exe | GET | 200 | 185.199.109.153:80 | http://xupefei.github.io/Locale-Emulator/VersionInfo.xml | unknown | — | — | unknown |
6096 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755803802&P2=404&P3=2&P4=VDqAh4qrs1TjZvc35u5I%2bw00gpNxBucjUxI4k1t8LQapud80nhCJZ7NyybR2ToI7ykBTHsCJzIhHrQ568T7v0g%3d%3d | unknown | — | — | whitelisted |
6096 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755803802&P2=404&P3=2&P4=VDqAh4qrs1TjZvc35u5I%2bw00gpNxBucjUxI4k1t8LQapud80nhCJZ7NyybR2ToI7ykBTHsCJzIhHrQ568T7v0g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6388 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5724 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5724 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |