| URL: | http://daas4uyngl.execute-api.ap-southeast-2.amazonaws.com |
| Full analysis: | https://app.any.run/tasks/1afaacdc-4113-4af6-8489-bc5cd31c9fa6 |
| Verdict: | No threats detected |
| Analysis date: | December 14, 2019, 15:48:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MD5: | 6434A95E14DBE01D82C470EB28DD7C8F |
| SHA1: | AC99AE8B7DA61F84B7457AA82E9BDD8B0B0A0CEC |
| SHA256: | 409EE07E7132688976CD56B2A5025E02F84710EA748EB59C33D0B9BB0A1E4AEF |
| SSDEEP: | 3:N1KaEEXLAqM8EiWQ2N2Q7W2:Cat7AF8Z/e3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the machine GUID from the registry
- rundll32.exe (PID: 3016)
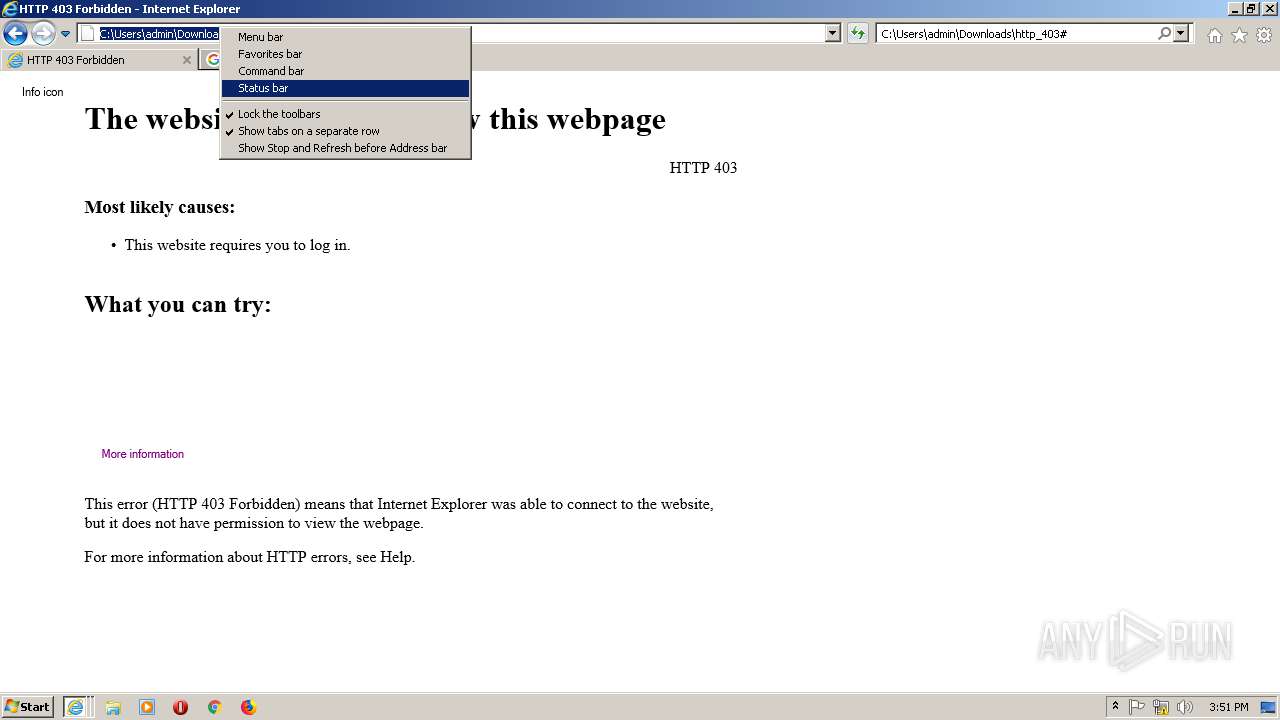
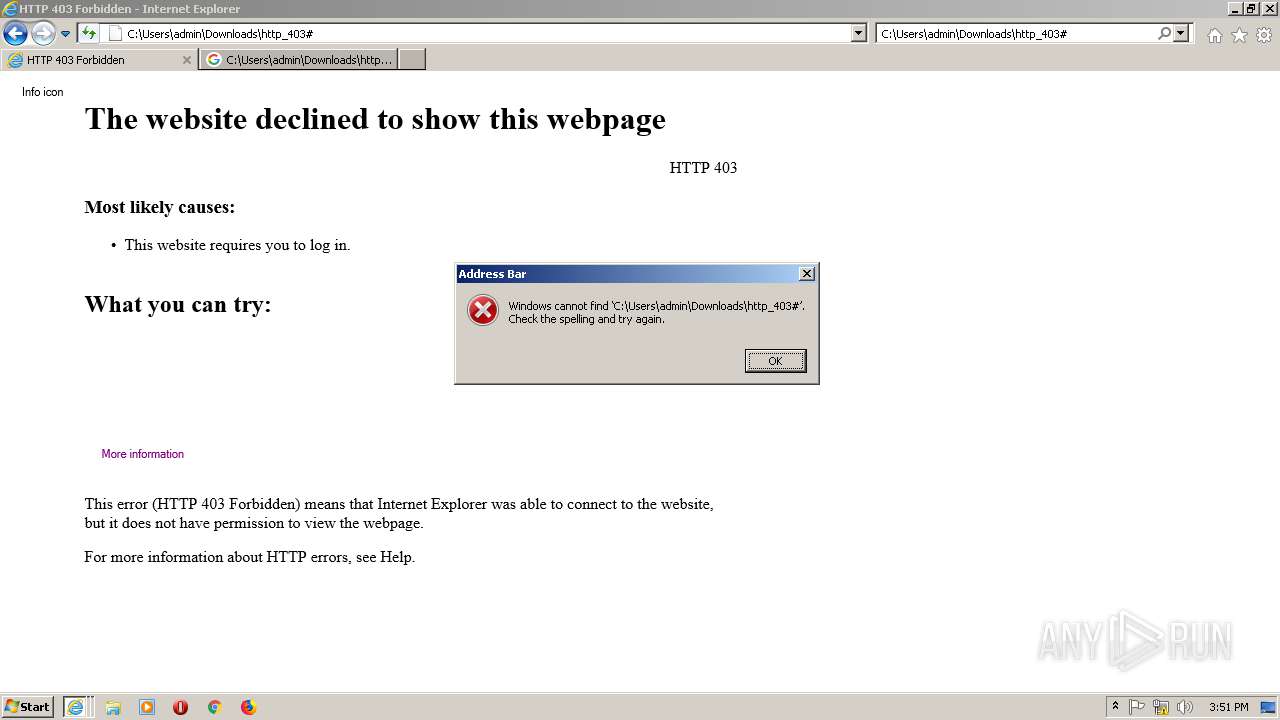
Starts Internet Explorer
- rundll32.exe (PID: 3016)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 2504)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2504)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2440)
- IEXPLORE.EXE (PID: 1404)
Creates files in the user directory
- IEXPLORE.EXE (PID: 1404)
- iexplore.exe (PID: 2504)
- IEXPLORE.EXE (PID: 2440)
Changes internet zones settings
- iexplore.exe (PID: 2504)
Reads the machine GUID from the registry
- iexplore.exe (PID: 2504)
Reads settings of System Certificates
- iexplore.exe (PID: 2504)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2504 CREDAT:3085593 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2440 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2504 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
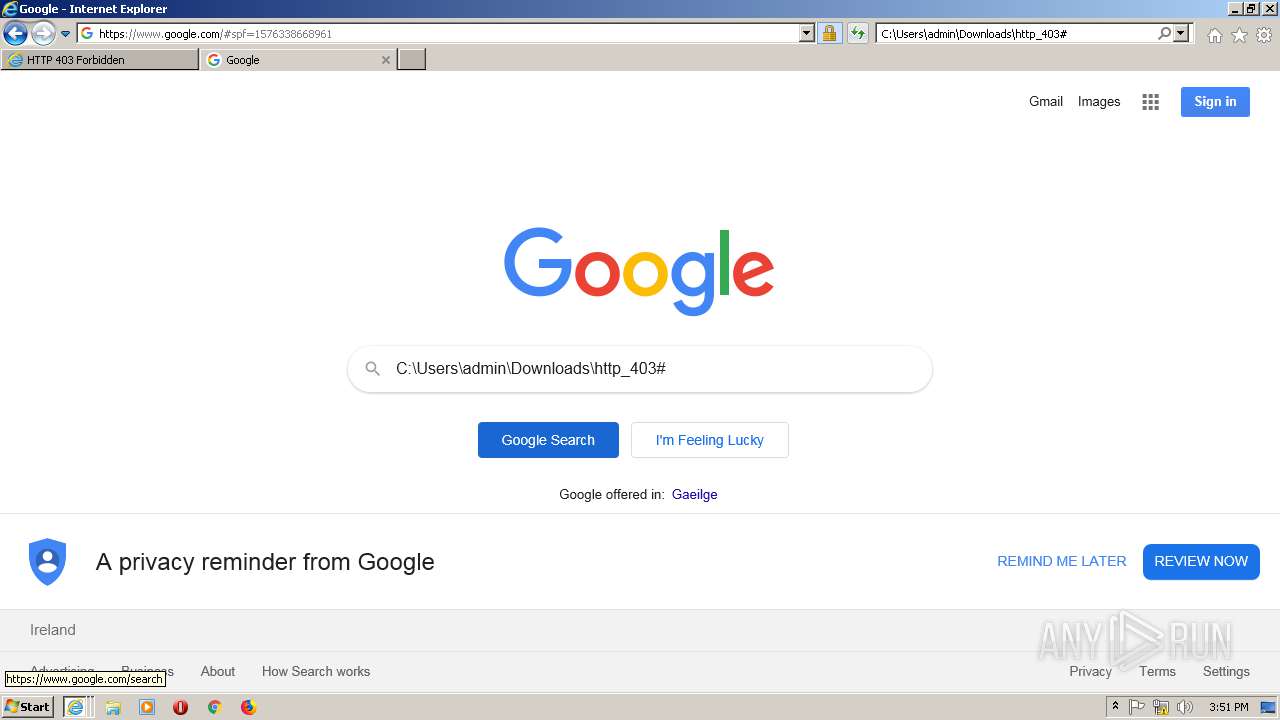
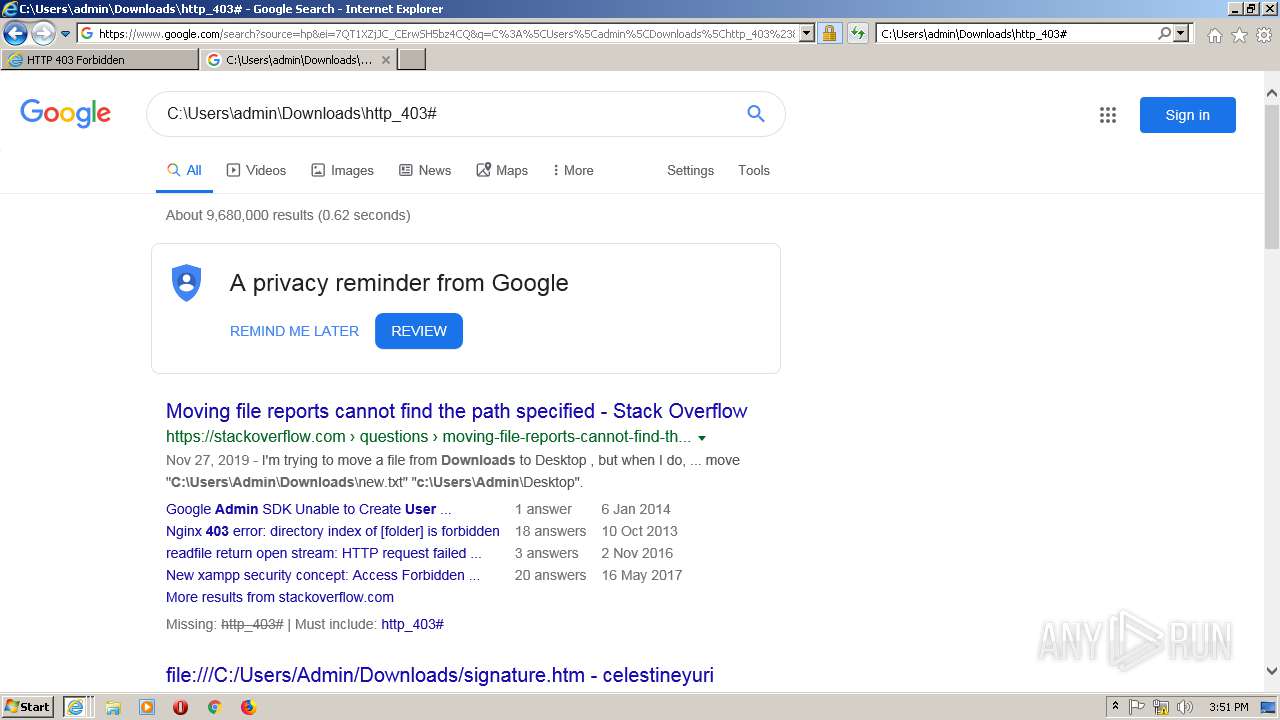
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://daas4uyngl.execute-api.ap-southeast-2.amazonaws.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
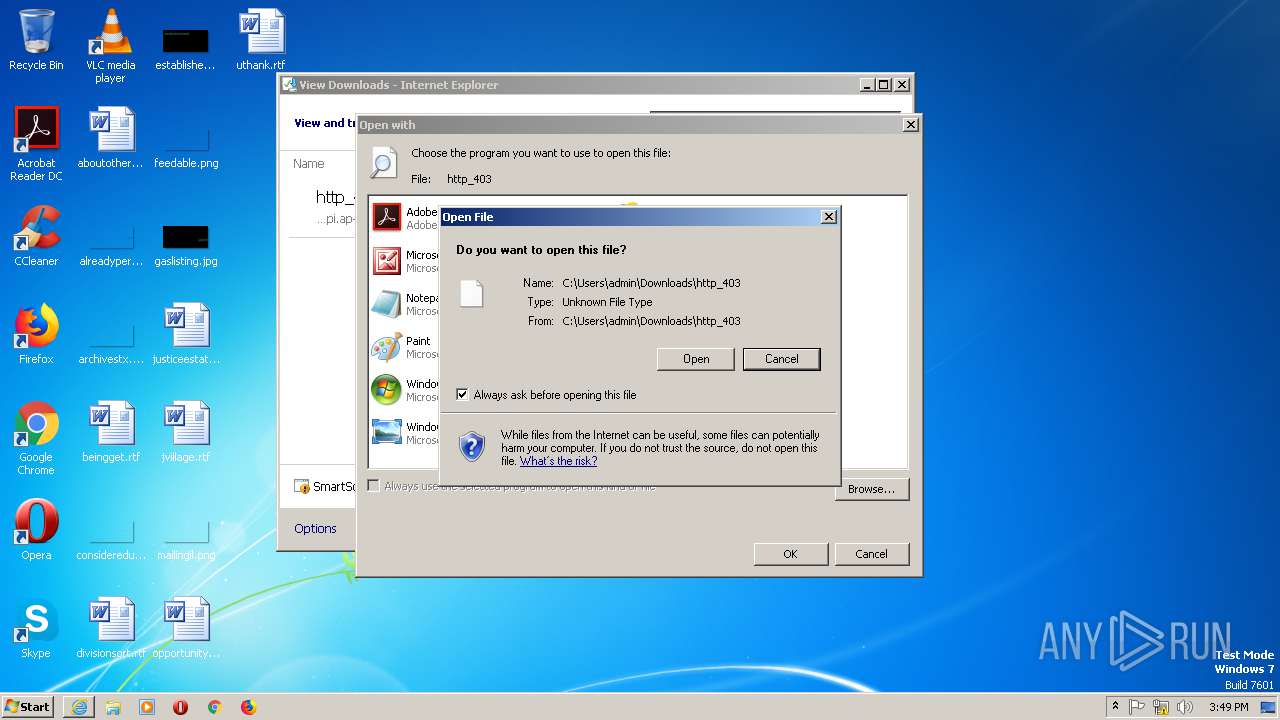
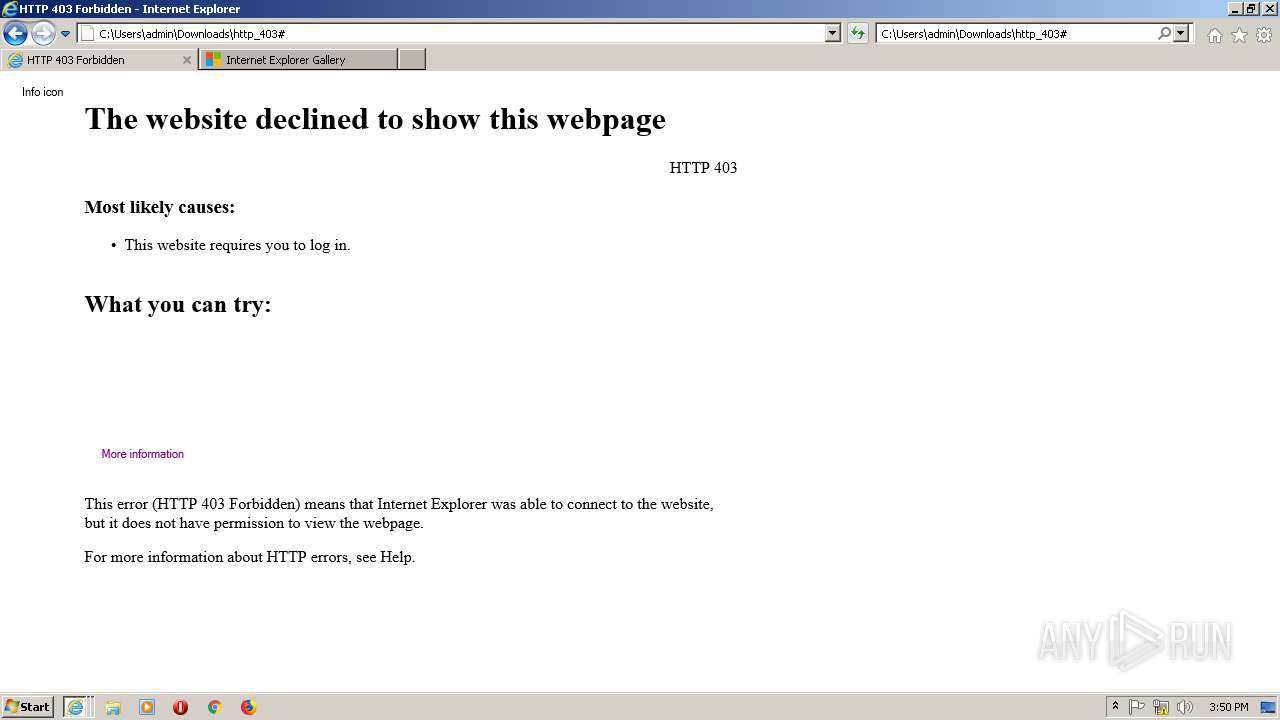
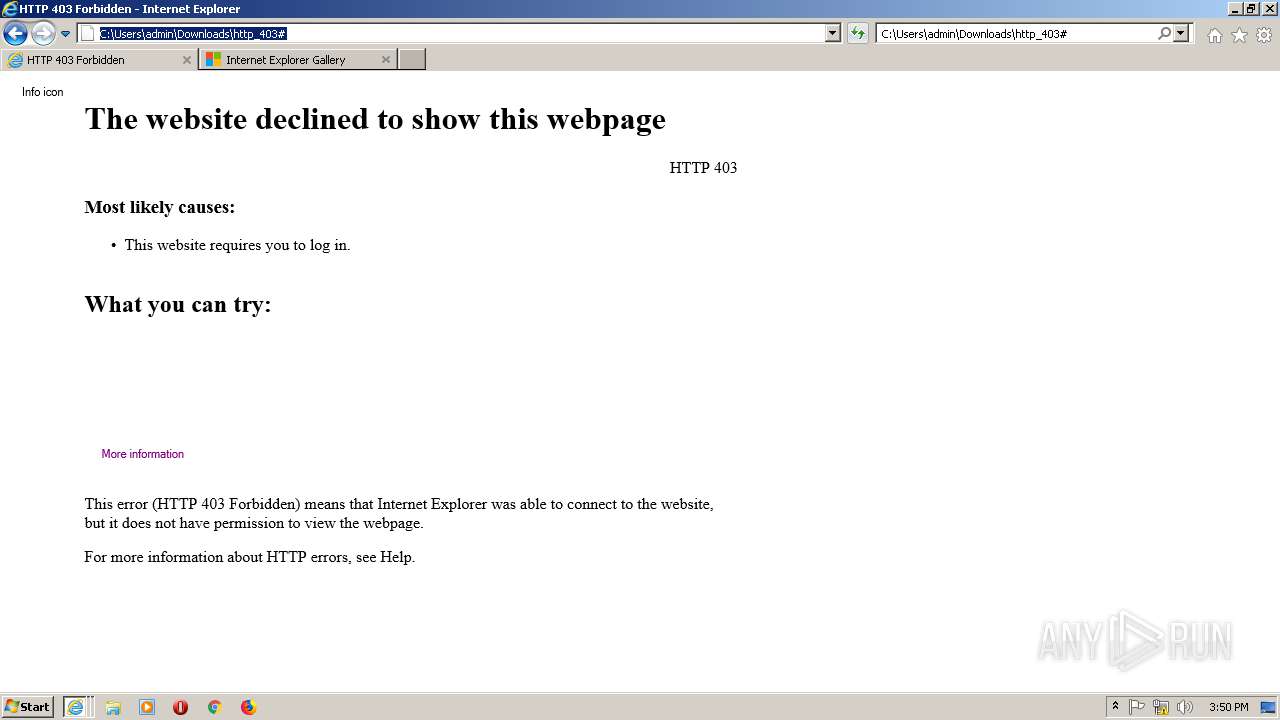
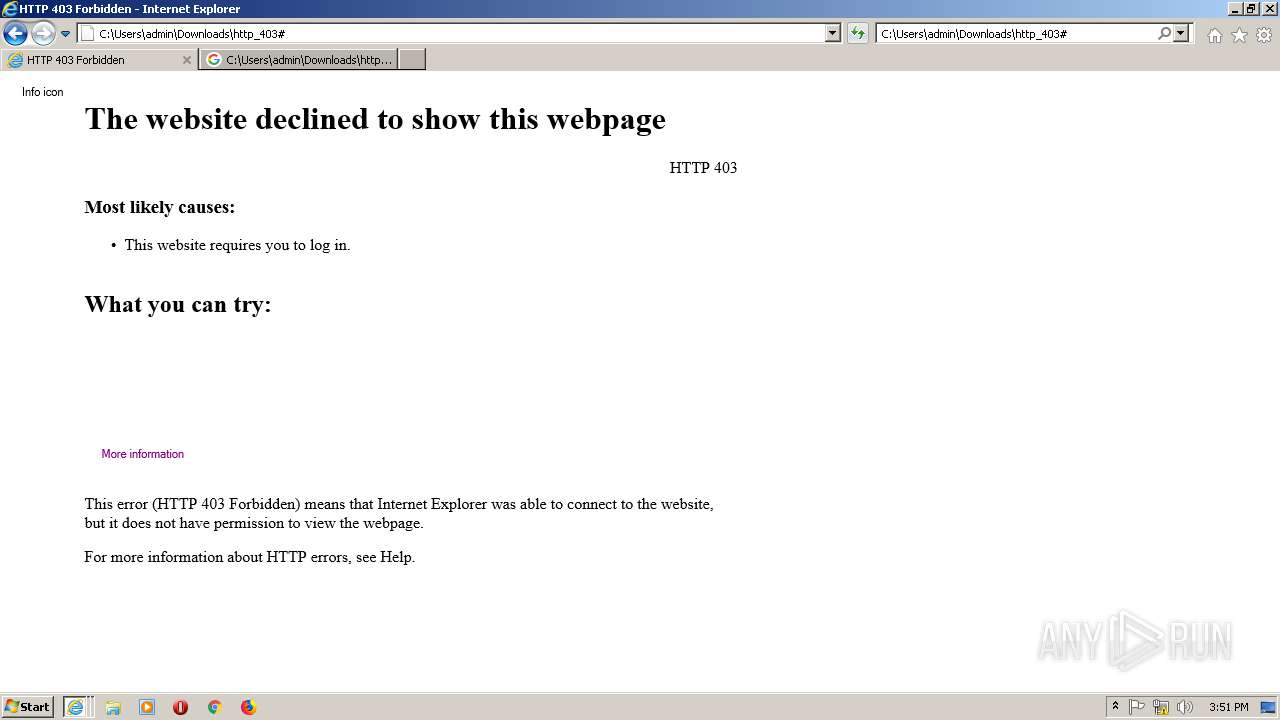
| 2860 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Downloads\http_403 | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
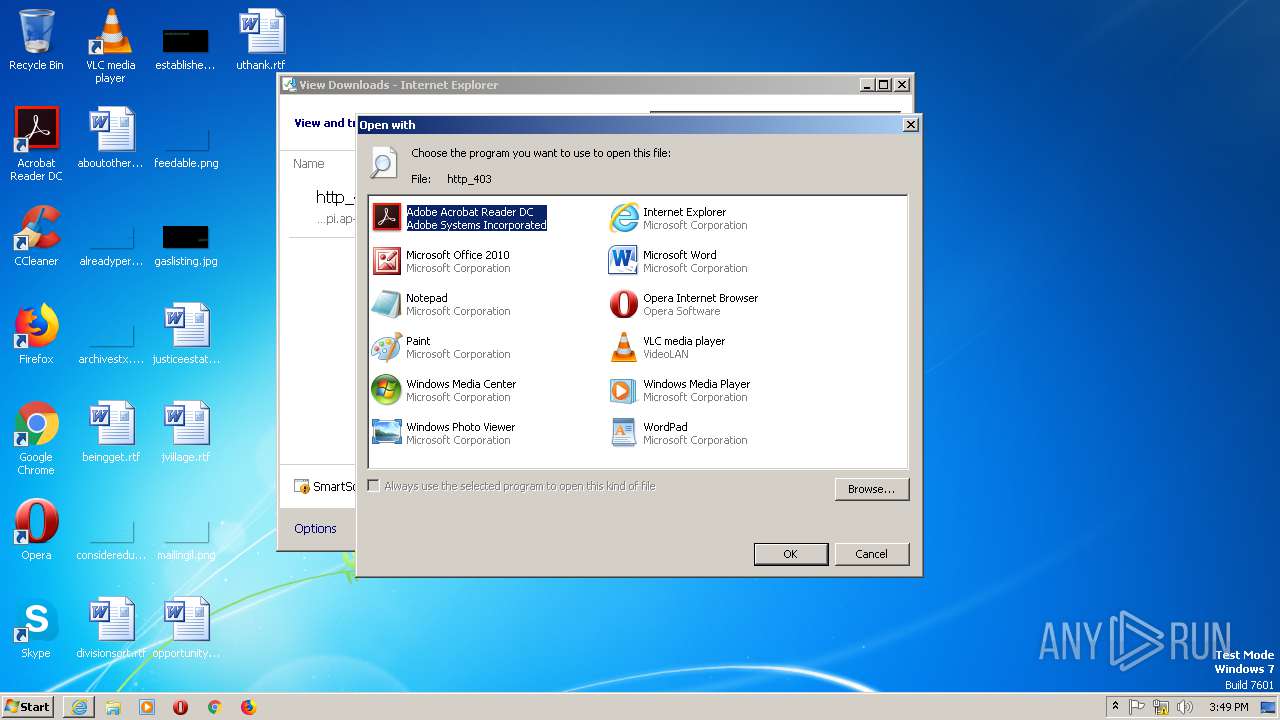
| 3016 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\http_403 | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 310
Read events
1 930
Write events
380
Delete events
0
Modification events
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 3 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 108473808 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30782102 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 408636308 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30782102 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
18
Text files
120
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\favicon[2].ico | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2440 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\Cab56F7.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\Tar56F8.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF928C1D08227B5F8C.TMP | — | |
MD5:— | SHA256:— | |||
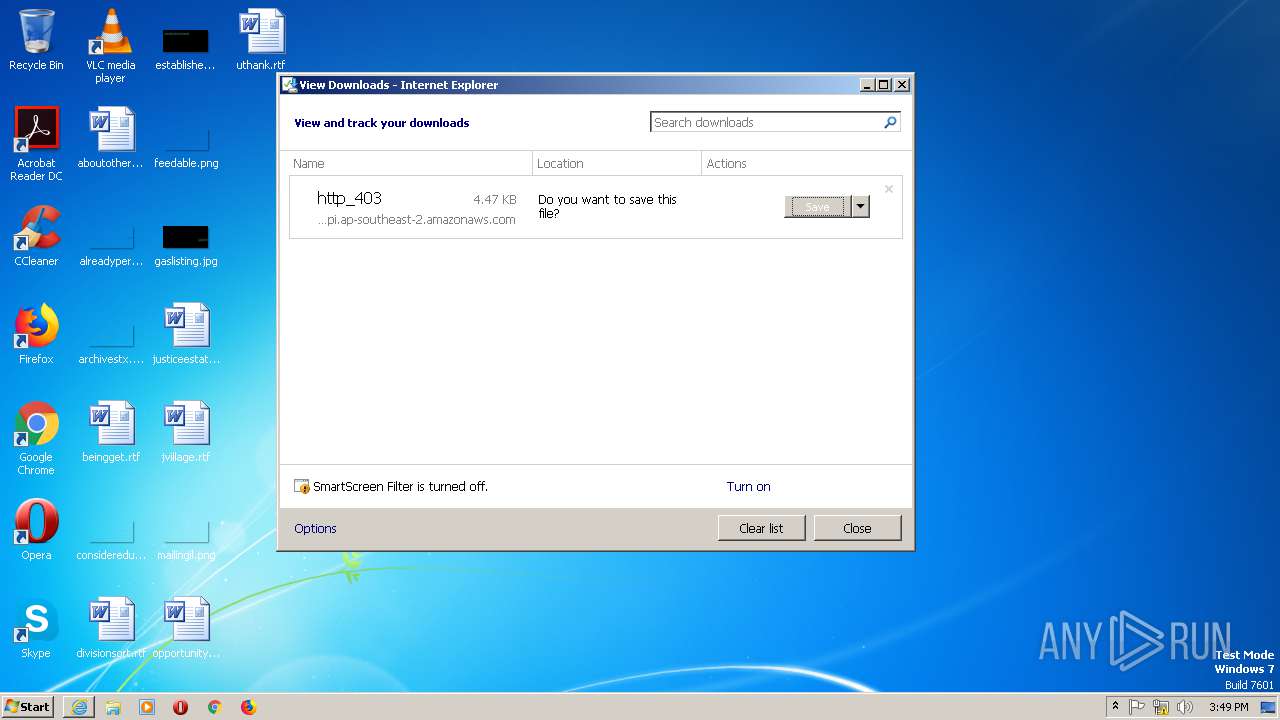
| 2504 | iexplore.exe | C:\Users\admin\Downloads\http_403.q4mvout.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\favicon[1].ico | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{441583FB-1E89-11EA-9C27-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
| 2440 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\070E0202839D9D67350CD2613E78E416 | binary | |
MD5:— | SHA256:— | |||
| 2440 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
76
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
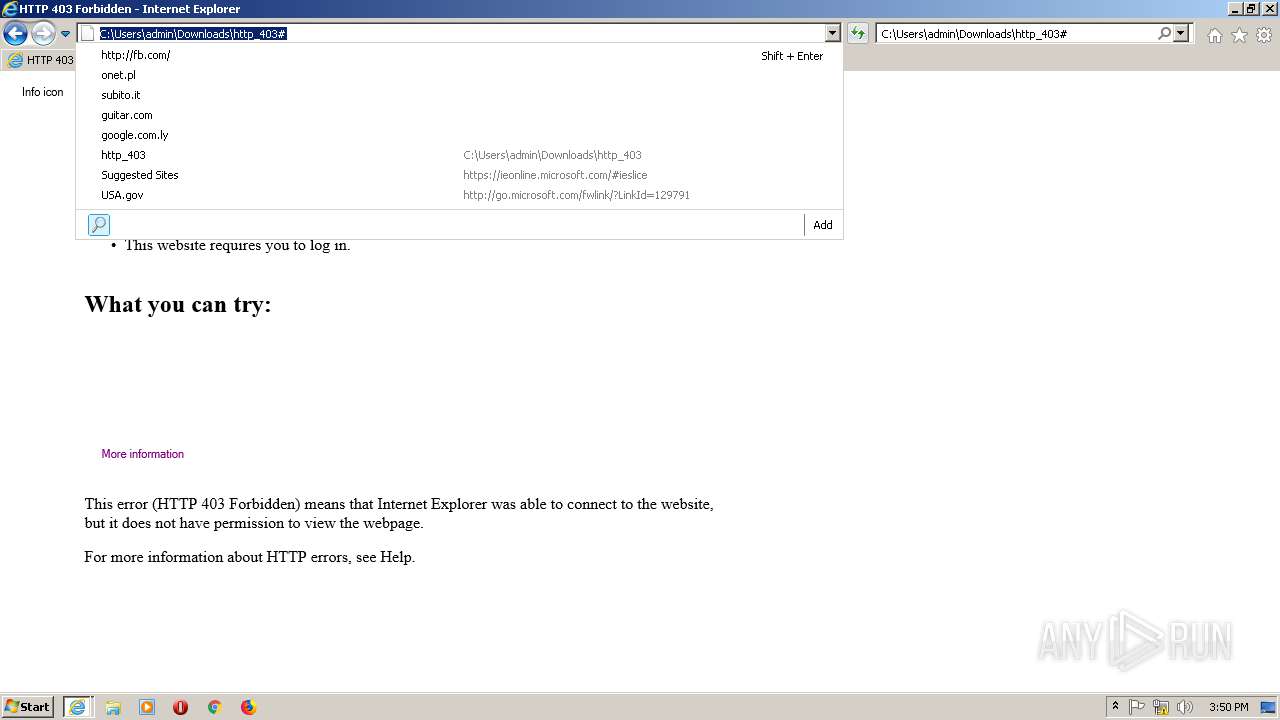
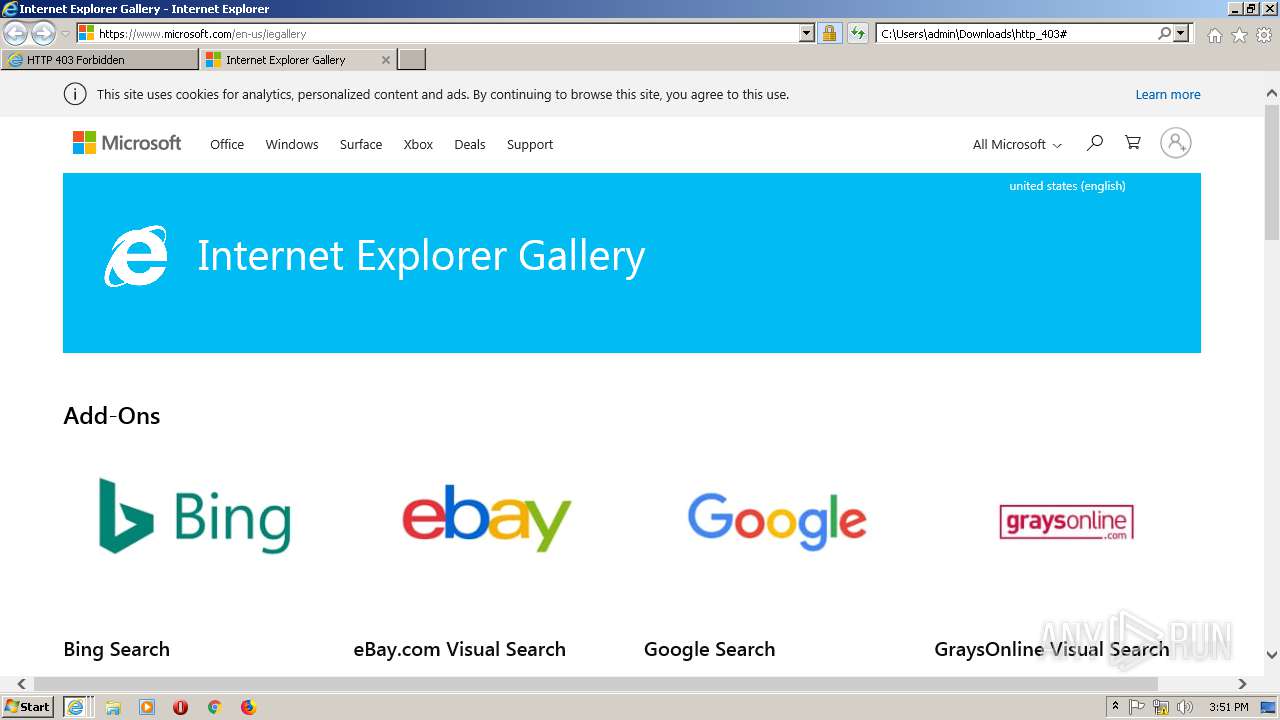
1404 | IEXPLORE.EXE | GET | 302 | 104.108.55.117:80 | http://go.microsoft.com/fwlink/?LinkId=122812 | NL | — | — | whitelisted |
1404 | IEXPLORE.EXE | GET | — | 2.18.233.62:80 | http://www.microsoft.com/en-us/iegallery | unknown | — | — | whitelisted |
2440 | IEXPLORE.EXE | GET | 301 | 13.35.253.118:80 | http://daas4uyngl.execute-api.ap-southeast-2.amazonaws.com/ | US | html | 183 b | shared |
2440 | IEXPLORE.EXE | GET | 200 | 205.185.216.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?08f4f0bc2142acff | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2440 | IEXPLORE.EXE | 13.35.253.118:80 | daas4uyngl.execute-api.ap-southeast-2.amazonaws.com | — | US | shared |
2440 | IEXPLORE.EXE | 13.35.253.118:443 | daas4uyngl.execute-api.ap-southeast-2.amazonaws.com | — | US | shared |
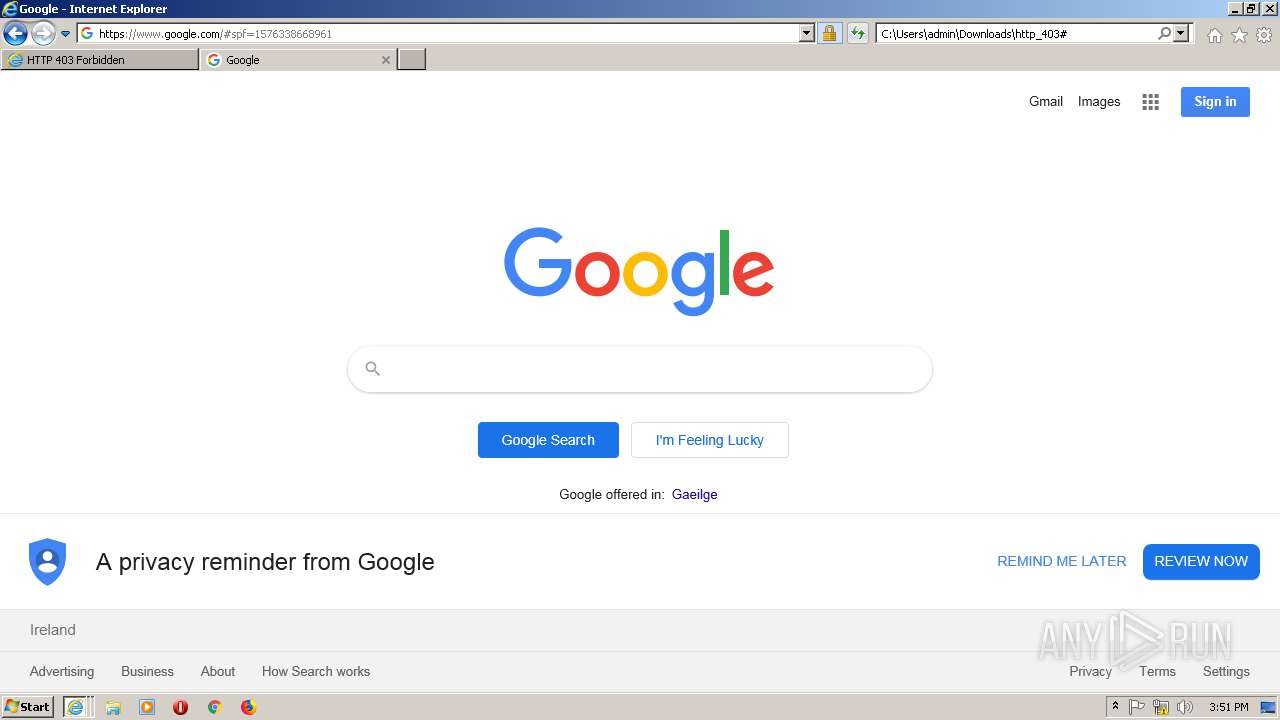
2504 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2440 | IEXPLORE.EXE | 205.185.216.10:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1404 | IEXPLORE.EXE | 2.16.186.40:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
1404 | IEXPLORE.EXE | 23.210.249.93:443 | c.s-microsoft.com | Akamai International B.V. | NL | whitelisted |
1404 | IEXPLORE.EXE | 23.37.51.125:443 | mem.gfx.ms | Akamai Technologies, Inc. | NL | whitelisted |
1404 | IEXPLORE.EXE | 23.210.248.233:443 | uhf.microsoft.com | Akamai International B.V. | NL | whitelisted |
2504 | iexplore.exe | 23.210.249.93:443 | c.s-microsoft.com | Akamai International B.V. | NL | whitelisted |
1404 | IEXPLORE.EXE | 40.90.22.191:443 | login.live.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
daas4uyngl.execute-api.ap-southeast-2.amazonaws.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x.ss2.us |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |