| File name: | download91511.apk |
| Full analysis: | https://app.any.run/tasks/a2a3e55e-6c56-4777-bd4c-340ad92d3de1 |
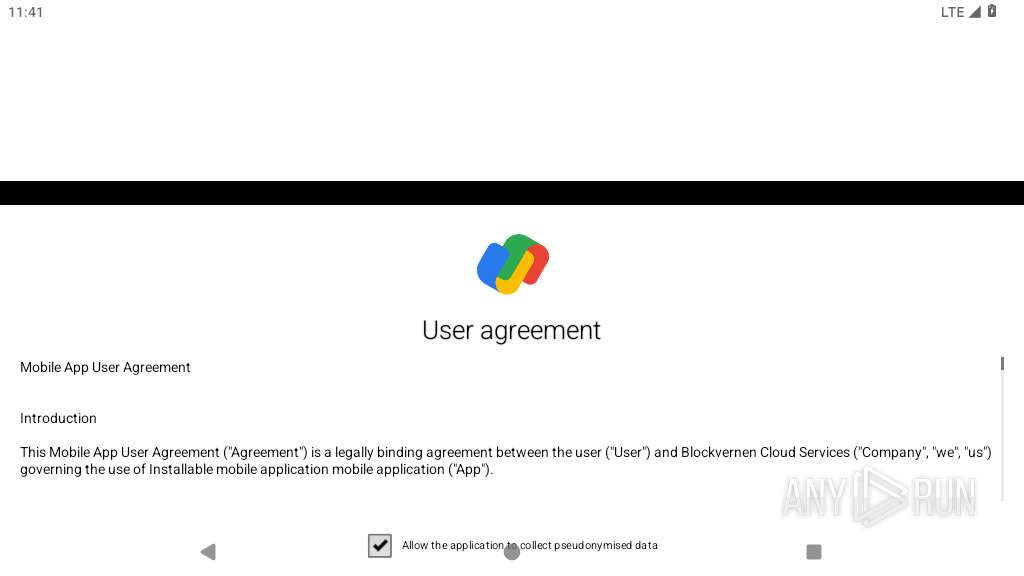
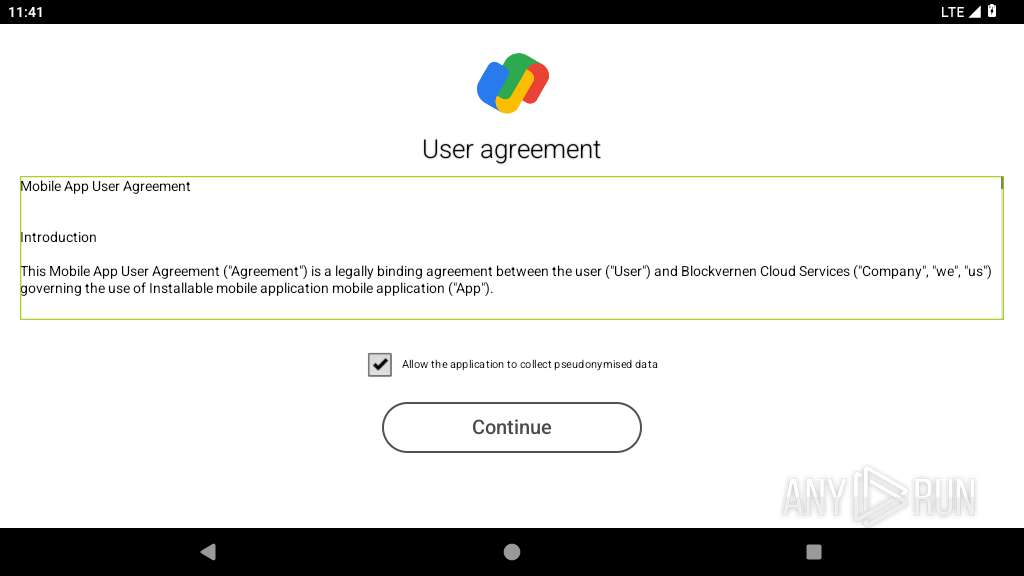
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 23:41:08 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties, with APK Signing Block |
| MD5: | C5A732C60031DBEFF37B5736948D2CCB |
| SHA1: | 5D313EBE4B03095EB26C9408357FDB5AA3F18C20 |
| SHA256: | 409A52081F9BEBD2BC01D54A39221867F8D343584C9F61AB29E10878799A0C04 |
| SSDEEP: | 98304:eKoGeVW13IJQUC/M5gQVXS9J2E1I/XeIUXqaKhe5TURp4udlN7OdOKqpga7eIxbX:o5Se7fCRH7Mf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Abuses foreground service for persistence
- app_process64 (PID: 2230)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2230)
Retrieves the ISO country code of the current network
- app_process64 (PID: 2230)
Establishing a connection
- app_process64 (PID: 2230)
Retrieves the ISO country code of the current SIM card
- app_process64 (PID: 2230)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 2230)
Launches a new activity
- app_process64 (PID: 2230)
Activates a regular task at set intervals
- app_process64 (PID: 2230)
Returns the name of the current network operator
- app_process64 (PID: 2230)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2230)
Retrieves the value of a secure system setting
- app_process64 (PID: 2230)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2230)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2230)
Returns elapsed time since boot
- app_process64 (PID: 2230)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2230)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
131
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2230 | science.ncert.science | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2276 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2292 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2325 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2396 | org.chromium.webview_shell | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2440 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
26
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2230 | app_process64 | /data/data/science.ncert.science/files/08eafdd1.dex | compressed | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTo1NTQ5OTAzNDc4OTY6YW5kcm9pZDo3N2QwZDU5ZDhjYjJkZDcyNmQyZjhk.xml | xml | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/app_webview/Default/Local Storage/leveldb/CURRENT | text | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/app_webview/Default/Local Storage/leveldb/000001.dbtmp | text | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/cache/oat_primary/arm64/base.2230.tmp | binary | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2230 | app_process64 | /data/data/science.ncert.science/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
49
DNS requests
40
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2230 | app_process64 | GET | 200 | 94.130.169.32:80 | http://g2.feradolongricoka.com//client.config/?app=pndr2&format=json&advert_key=ZWMwMDBhMDg4ZTAwNDBjNjAwMDA0MGQ3MDA0MGQ3MDA0MGQ3Y2I5ZjNhMDRkNQ==&uid=F58744BC1459BCD7A26FF03D1197ED08-D7F0CD3E1C3AD3AF4B4F4398ED7699042CACA2F8&version=64.9&pckg=science.ncert.science&em=false&ia=14&im=lg&id=G8_ThinQ&utm_source=3azaPa36WATLViN5epVAcBHWafsq313dv6tvDrKHhDrehnidZnpnoqubGTEYKaZEfRuVo5cyb7MipXQMGqCVDnFm4QvUn4M84DVmfkKAnLD7q1JF8Az2zTRQ7gyT9DTHiePU5bXBPt6DsepRD2kTL3nZHtRy4vagcqxmkRY83hUz9fmoiQPX3q849s4tXkVo9Ce7krRmpd8MhoDpRHfoy88AeBYfnA7p7xcz94mwPhNe5AD3YJyPZbUJGeE2Yb9Jq6d8&sp_time=6&ne=1&network_operator=Verizon&phone_type=gsm&sim_operator=Verizon&network_vpn=&sim_iso=us&networks=dummy0;lo;buried_eth0&network_type=MOBILE&network_iso=us&gaid=none&pndr_install=1 | DE | binary | 186 b | unknown |
— | — | GET | 204 | 142.250.186.99:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
2396 | app_process64 | GET | 302 | 57.129.64.230:80 | http://push.razkondronging.com/register?uid=F58744BC1459BCD7A26FF03D1197ED08-D7F0CD3E1C3AD3AF4B4F4398ED7699042CACA2F8 | FR | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
449 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.186.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
— | — | 64.233.167.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2276 | app_process32 | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2230 | app_process64 | 142.250.186.42:443 | firebaseinstallations.googleapis.com | GOOGLE | US | whitelisted |
2325 | app_process32 | 142.250.186.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2325 | app_process32 | 142.250.186.78:443 | dl.google.com | GOOGLE | US | whitelisted |
2396 | app_process64 | 57.129.64.230:80 | push.razkondronging.com | — | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
time.android.com |
| whitelisted |
google.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
firebaseinstallations.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
push.razkondronging.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2396 | app_process64 | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
2396 | app_process64 | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |