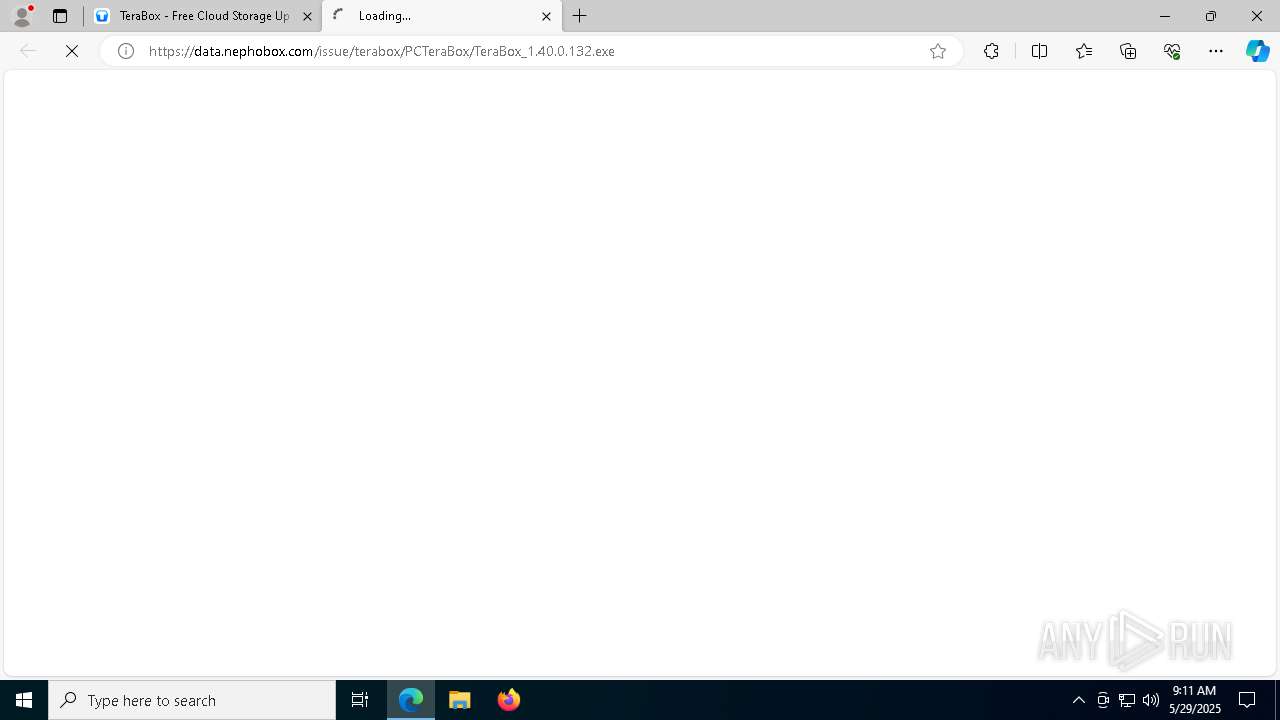
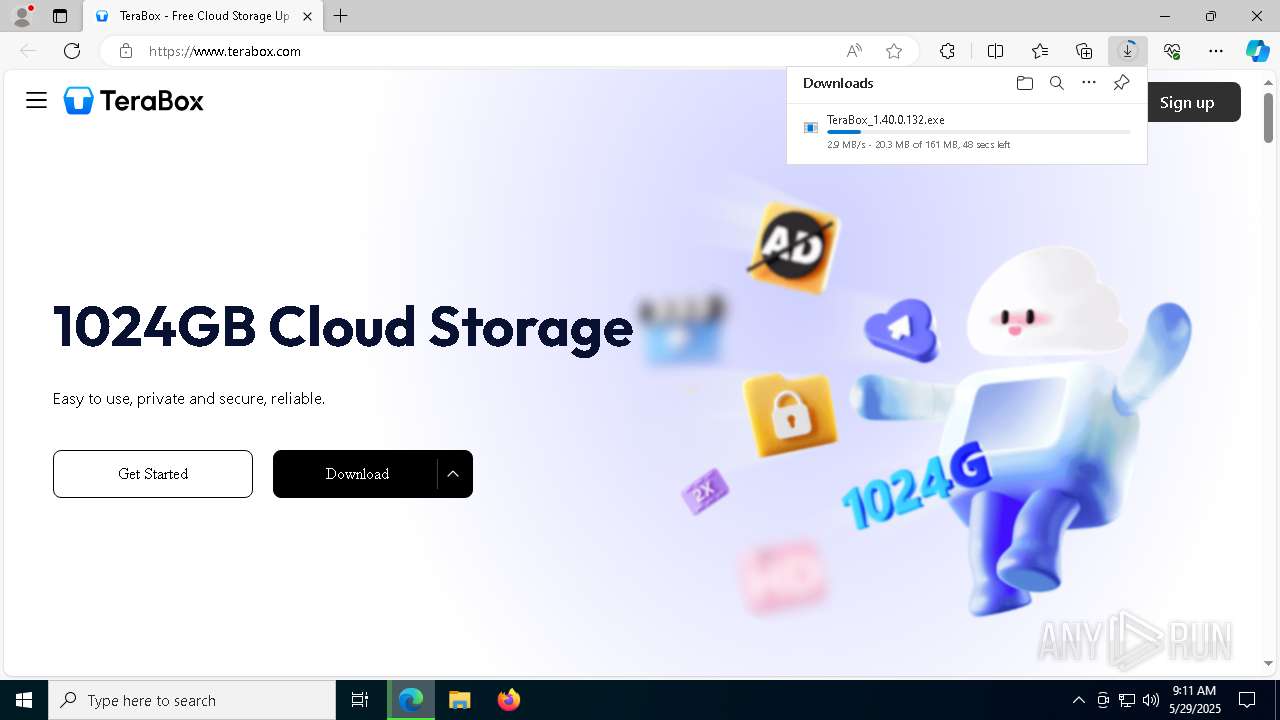
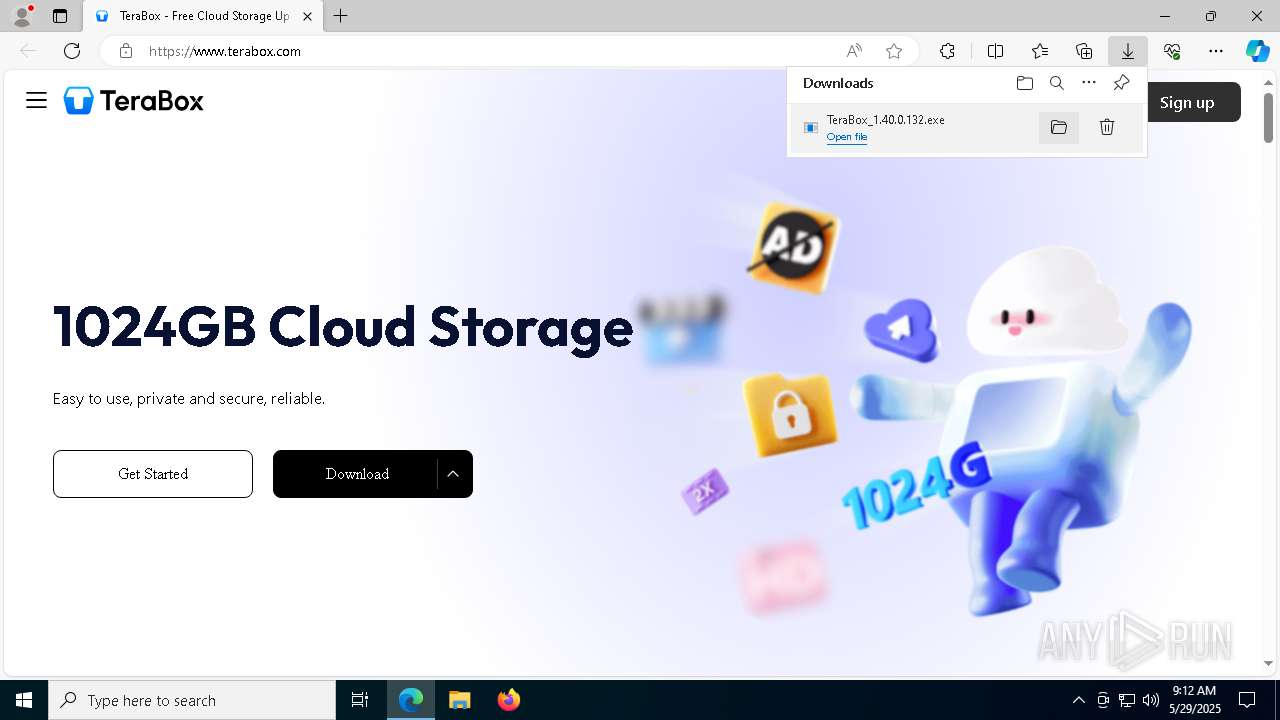
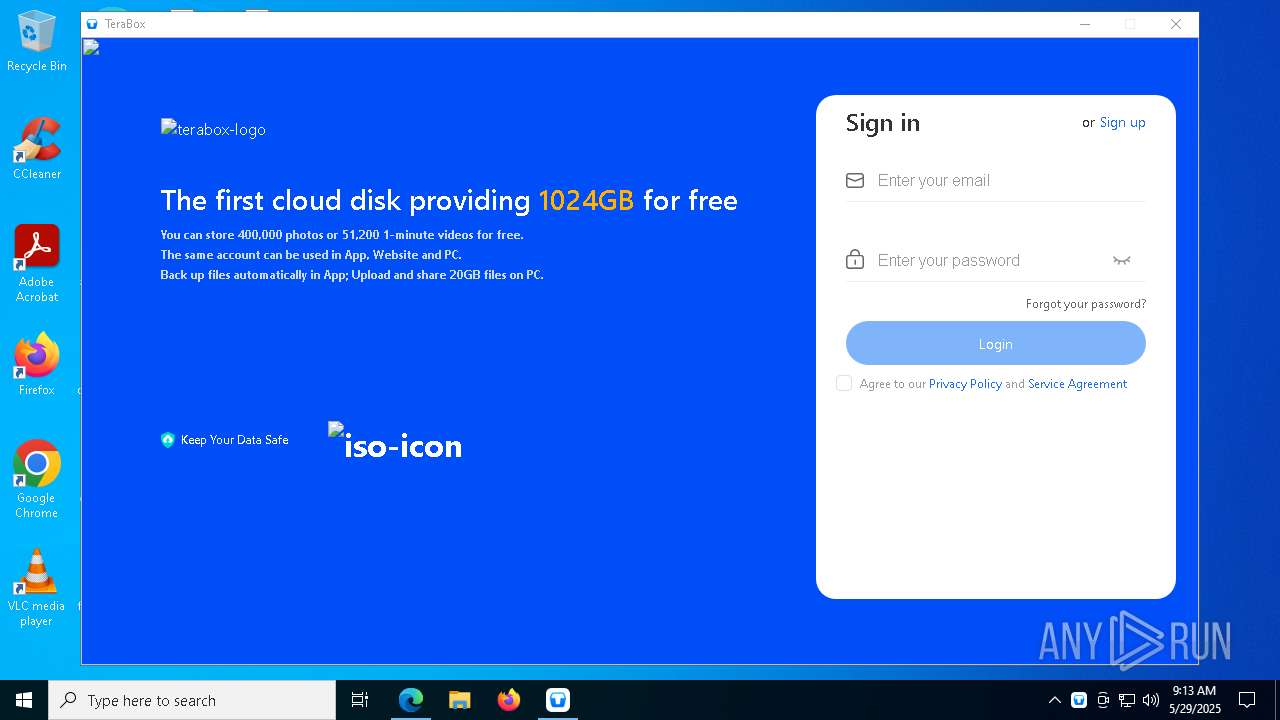
| URL: | https://www.terabox.com/ |
| Full analysis: | https://app.any.run/tasks/92c2ad7a-d266-4950-be24-3ee10ef16a61 |
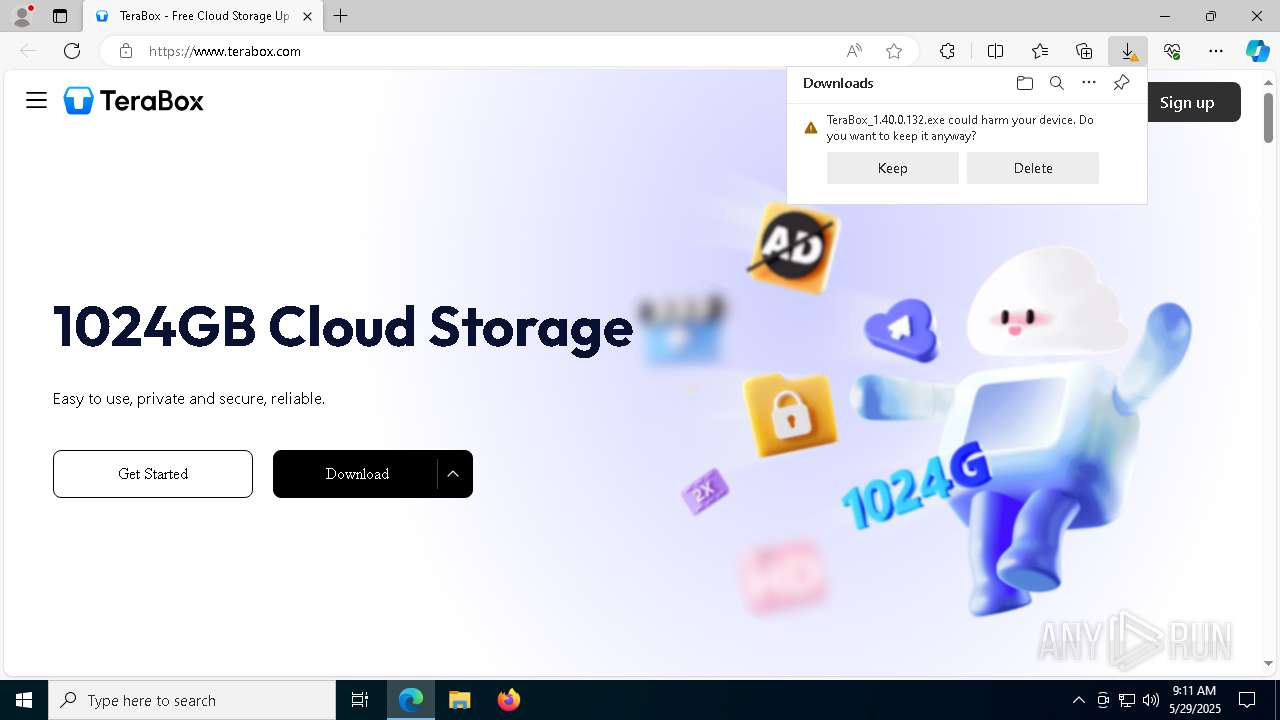
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2025, 09:10:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EEAA3CD5CC2BD738EFF9EC84A81DC302 |
| SHA1: | C326AF84A96873ACB477770F6776F37CB7D904B4 |
| SHA256: | 4085BE154A18CBDBA2056060FC06ED98AE1F7DEF2A89A2BAE99676344954217A |
| SSDEEP: | 3:N8DSLBH2:2OLw |
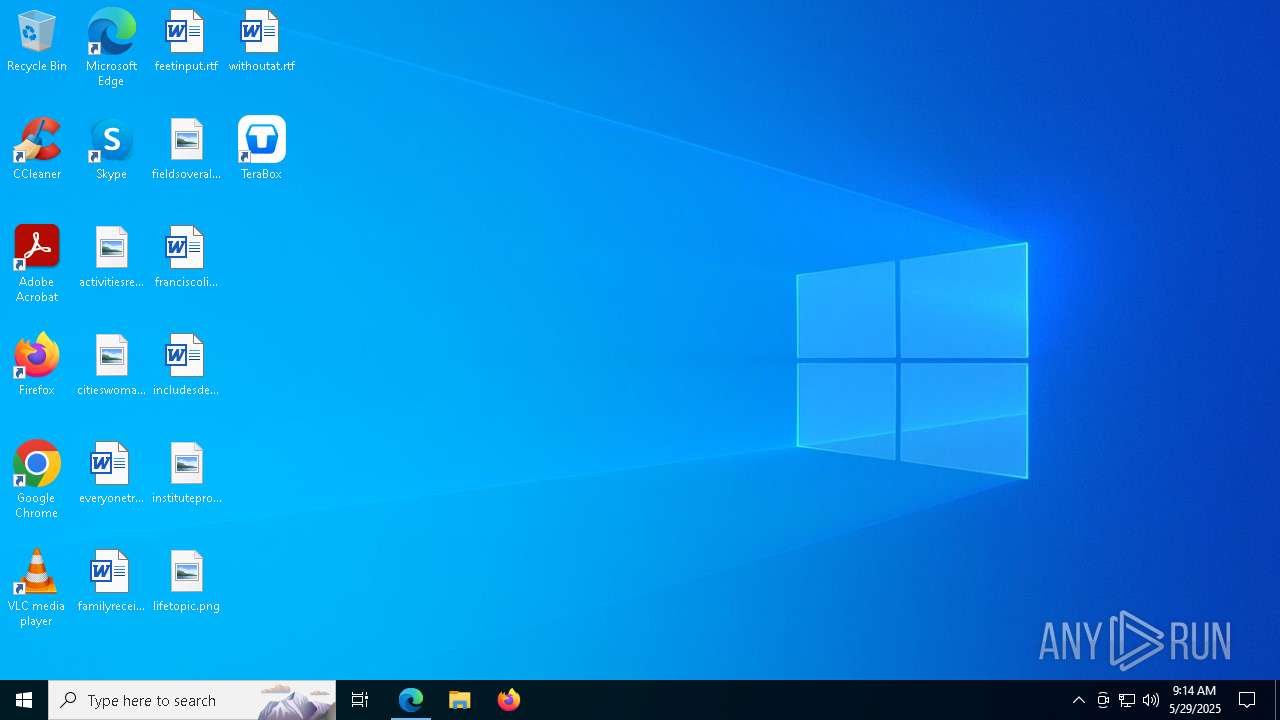
MALICIOUS
Changes the autorun value in the registry
- TeraBox.exe (PID: 7980)
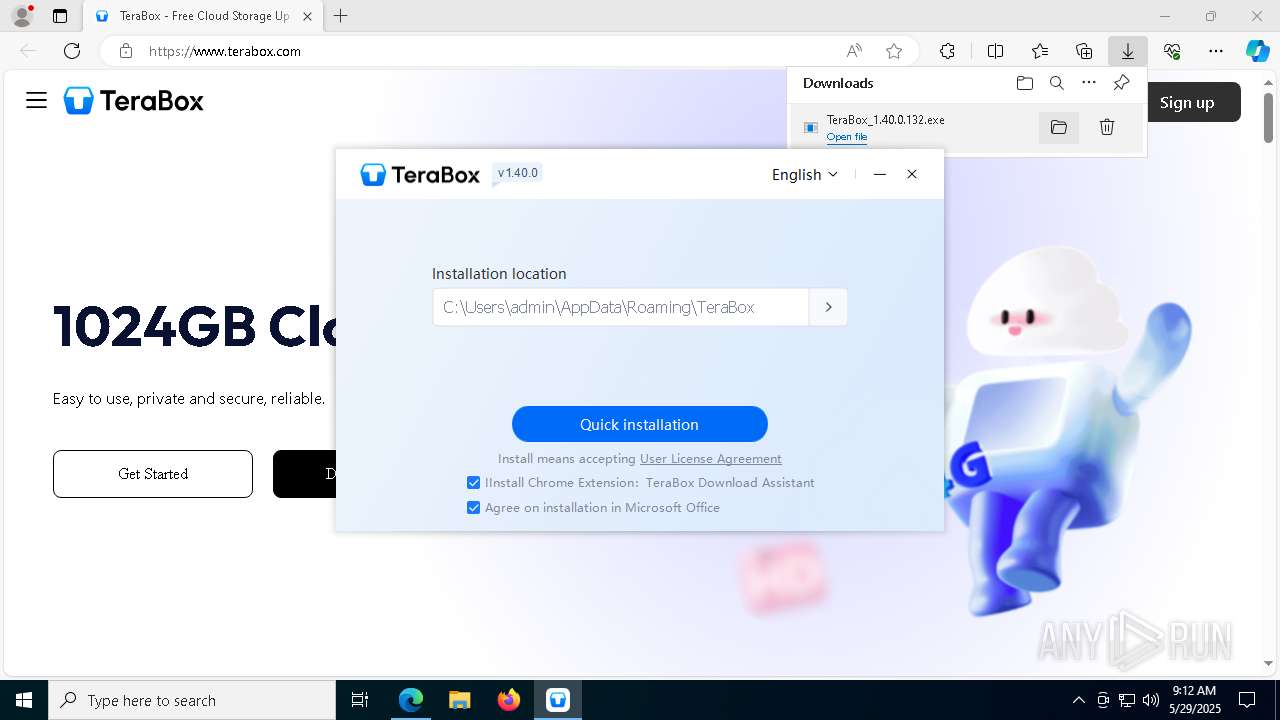
Registers / Runs the DLL via REGSVR32.EXE
- TeraBox_1.40.0.132.exe (PID: 5428)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBox_1.40.0.132.exe (PID: 5428)
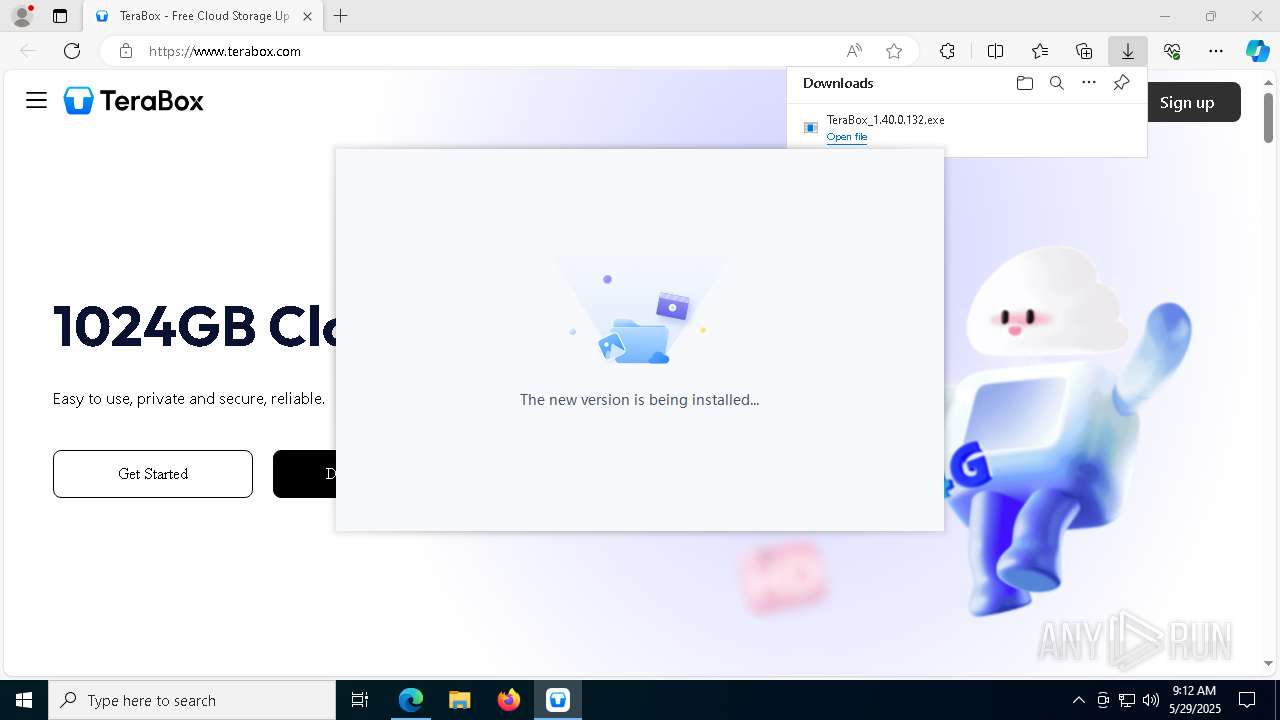
Executable content was dropped or overwritten
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBox_1.40.0.132.exe (PID: 8188)
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBoxUnite.exe (PID: 1812)
Process drops legitimate windows executable
- TeraBox_1.40.0.132.exe (PID: 5428)
The process drops C-runtime libraries
- TeraBox_1.40.0.132.exe (PID: 5428)
The process creates files with name similar to system file names
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBox_1.40.0.132.exe (PID: 8032)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5360)
- regsvr32.exe (PID: 2288)
- regsvr32.exe (PID: 3396)
Creates a software uninstall entry
- TeraBox_1.40.0.132.exe (PID: 5428)
Reads security settings of Internet Explorer
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBoxWebService.exe (PID: 5344)
- TeraBox.exe (PID: 1056)
Application launched itself
- TeraBoxUnite.exe (PID: 1812)
INFO
Reads Environment values
- identity_helper.exe (PID: 7880)
Checks supported languages
- identity_helper.exe (PID: 7880)
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBox_1.40.0.132.exe (PID: 8188)
- TeraBox.exe (PID: 7980)
- YunUtilityService.exe (PID: 5452)
- TeraBox.exe (PID: 1056)
- TeraBoxWebService.exe (PID: 4008)
- TeraBoxWebService.exe (PID: 5344)
- TeraBoxUnite.exe (PID: 1812)
- TeraBoxUnite.exe (PID: 4736)
- TeraBoxUnite.exe (PID: 1452)
Executable content was dropped or overwritten
- msedge.exe (PID: 7276)
Reads the computer name
- identity_helper.exe (PID: 7880)
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBox_1.40.0.132.exe (PID: 8188)
- TeraBox.exe (PID: 7980)
- YunUtilityService.exe (PID: 5452)
- TeraBoxWebService.exe (PID: 5344)
- TeraBox.exe (PID: 1056)
- TeraBoxUnite.exe (PID: 1812)
- TeraBoxUnite.exe (PID: 4736)
- TeraBoxUnite.exe (PID: 1452)
Reads the software policy settings
- slui.exe (PID: 3332)
- slui.exe (PID: 5528)
- TeraBox.exe (PID: 1056)
Application launched itself
- msedge.exe (PID: 7276)
Create files in a temporary directory
- TeraBox_1.40.0.132.exe (PID: 8188)
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBoxUnite.exe (PID: 1812)
Creates files or folders in the user directory
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBox.exe (PID: 7980)
- TeraBox.exe (PID: 1056)
- TeraBoxWebService.exe (PID: 5344)
- TeraBoxUnite.exe (PID: 1812)
Checks proxy server information
- slui.exe (PID: 5528)
- TeraBox_1.40.0.132.exe (PID: 5428)
- TeraBoxWebService.exe (PID: 5344)
- TeraBox.exe (PID: 1056)
- TeraBoxUnite.exe (PID: 1812)
The sample compiled with chinese language support
- TeraBox_1.40.0.132.exe (PID: 8188)
- TeraBox_1.40.0.132.exe (PID: 8032)
- TeraBox_1.40.0.132.exe (PID: 5428)
The sample compiled with english language support
- TeraBox_1.40.0.132.exe (PID: 5428)
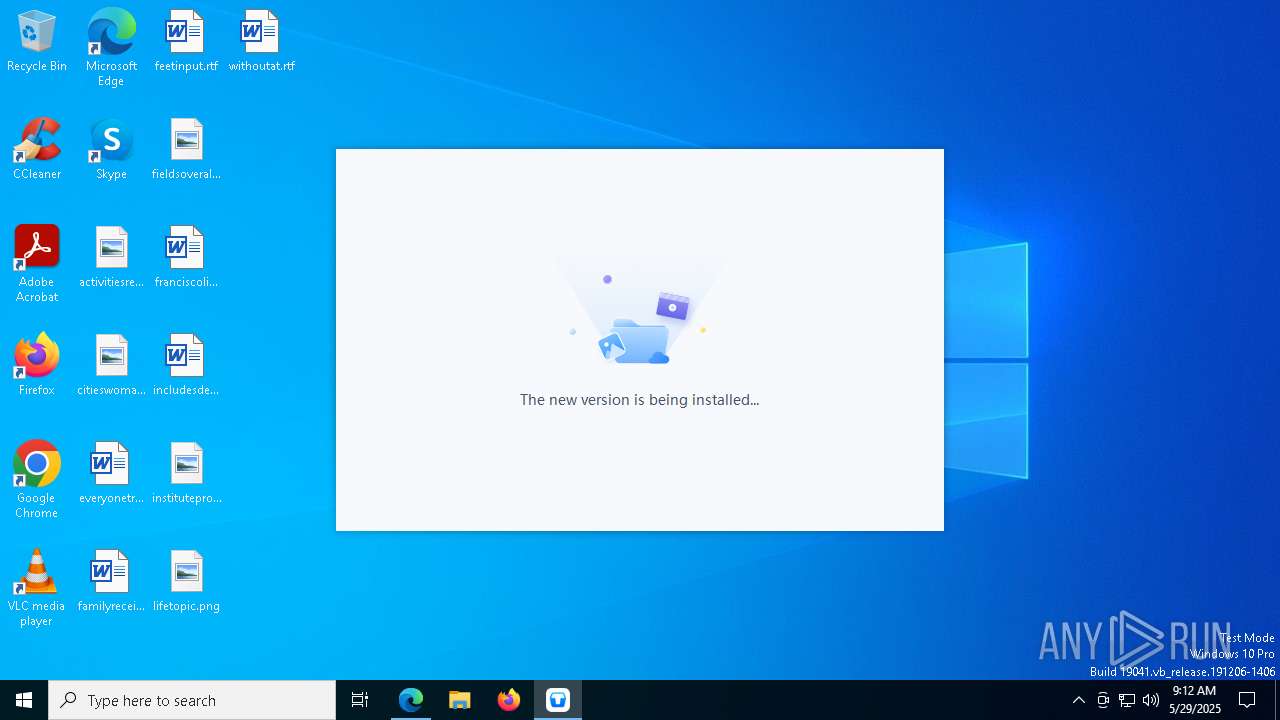
Launch of the file from Registry key
- TeraBox.exe (PID: 7980)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 1056)
Process checks computer location settings
- TeraBoxUnite.exe (PID: 1812)
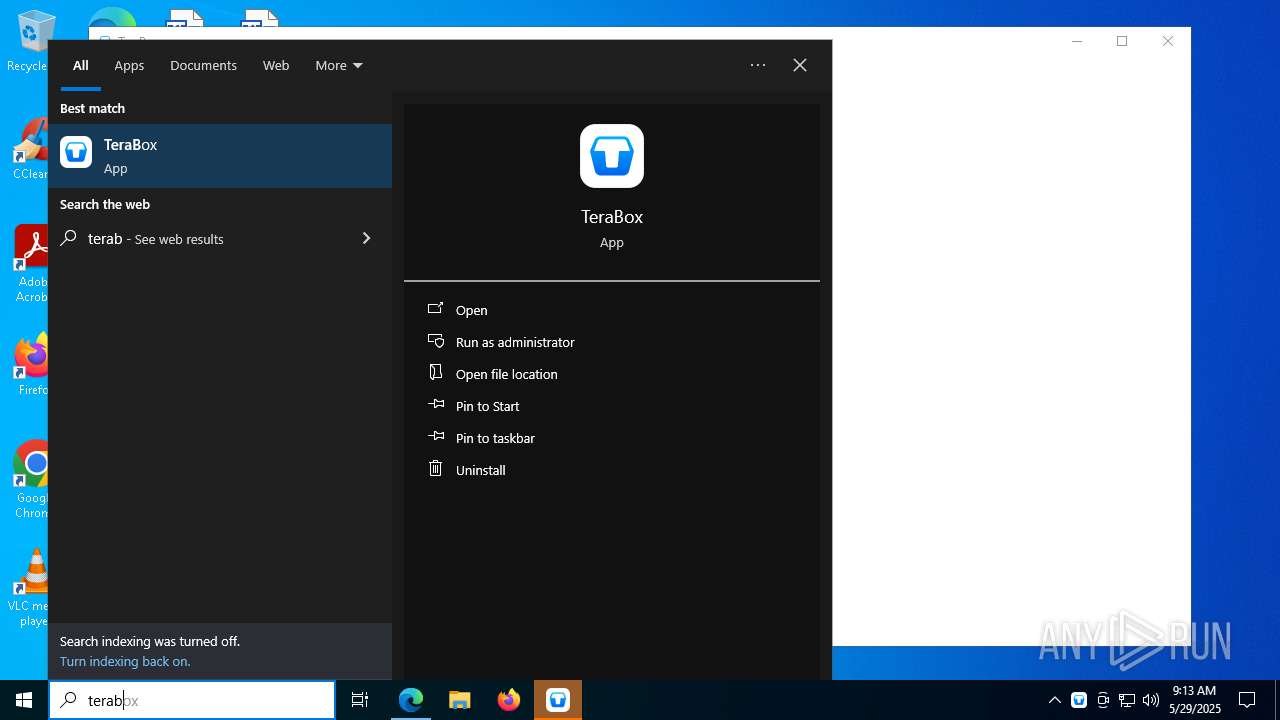
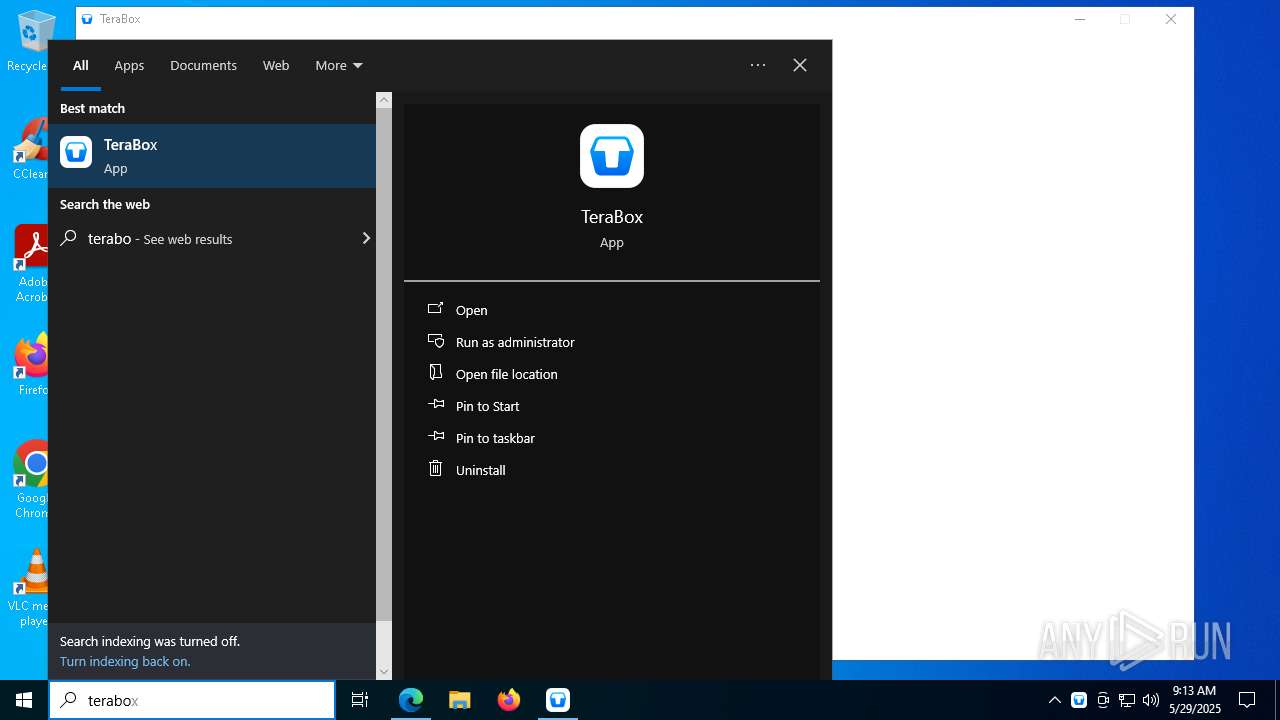
Manual execution by a user
- TeraBox.exe (PID: 6908)
Node.js compiler has been detected
- TeraBoxUnite.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
230
Monitored processes
89
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\WINDOWS\system32\regsvr32.exe" "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunShellExt64.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | TeraBox_1.40.0.132.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4428 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=3668 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6556 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3652 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1316 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_1.40.0.132.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Version: 1.40.0.132 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5928 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6588 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4464 --field-trial-handle=2324,i,7877859352198910376,16861498967941114884,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 329
Read events
20 215
Write events
96
Delete events
18
Modification events
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3CA534F4D8942F00 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 86DA42F4D8942F00 | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {56C5BD46-936C-4308-ABC6-B9C7403FC6B7} | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {905B2785-BA0F-4546-9EDD-EC8480C095B9} | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AD908237-B90A-442C-916C-2260BE438C49} | |||
| (PID) Process: | (7276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B97226B-8E08-42F1-B416-28D24AC8ADC9} | |||
Executable files
103
Suspicious files
663
Text files
384
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
934
DNS requests
141
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748972816&P2=404&P3=2&P4=EtU5JQeqtUJqhEgxdJHY0OxLEMBpVJA8w6TfwVmKjTg2Cpm0umYpA8md4M8062Ysrb%2b1kTw26U69eFlrC57esw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748972816&P2=404&P3=2&P4=EtU5JQeqtUJqhEgxdJHY0OxLEMBpVJA8w6TfwVmKjTg2Cpm0umYpA8md4M8062Ysrb%2b1kTw26U69eFlrC57esw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748972816&P2=404&P3=2&P4=TjGisan9gx%2fw3XqUQYalCd5BGz9z9KVm6M9YOtURMqx22Er%2fSvnC6MNzLnj9WRO0%2biNDzNqN36qDTKR3NLrPQg%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985694&P2=404&P3=2&P4=Ayl2U0JQRchH3udhu6Q9THfrcxYDXa9F%2fEgmOhRHReBqxpWRNN1cXrFBcTmkRmout4bBnSEko6RYy7odla7Jyw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985694&P2=404&P3=2&P4=Ayl2U0JQRchH3udhu6Q9THfrcxYDXa9F%2fEgmOhRHReBqxpWRNN1cXrFBcTmkRmout4bBnSEko6RYy7odla7Jyw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985694&P2=404&P3=2&P4=Ayl2U0JQRchH3udhu6Q9THfrcxYDXa9F%2fEgmOhRHReBqxpWRNN1cXrFBcTmkRmout4bBnSEko6RYy7odla7Jyw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748972816&P2=404&P3=2&P4=TjGisan9gx%2fw3XqUQYalCd5BGz9z9KVm6M9YOtURMqx22Er%2fSvnC6MNzLnj9WRO0%2biNDzNqN36qDTKR3NLrPQg%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985694&P2=404&P3=2&P4=Ayl2U0JQRchH3udhu6Q9THfrcxYDXa9F%2fEgmOhRHReBqxpWRNN1cXrFBcTmkRmout4bBnSEko6RYy7odla7Jyw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985694&P2=404&P3=2&P4=Ayl2U0JQRchH3udhu6Q9THfrcxYDXa9F%2fEgmOhRHReBqxpWRNN1cXrFBcTmkRmout4bBnSEko6RYy7odla7Jyw%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1748972816&P2=404&P3=2&P4=NIbBJOf%2bNXUvjEdwtksvcz74NJu51KuV1TUKjIO40URgI%2bah5xuOoeUG9NBDcdnuUx8afccg%2f8KaLpycZg%2bBYw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7580 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7580 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7580 | msedge.exe | 40.90.65.34:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.terabox.com |
| unknown |
business.bing.com |
| whitelisted |
s3.teraboxcdn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING Observed File Sharing Domain (terabox .com in TLS SNI) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING Observed File Sharing Domain (terabox .com in TLS SNI) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |