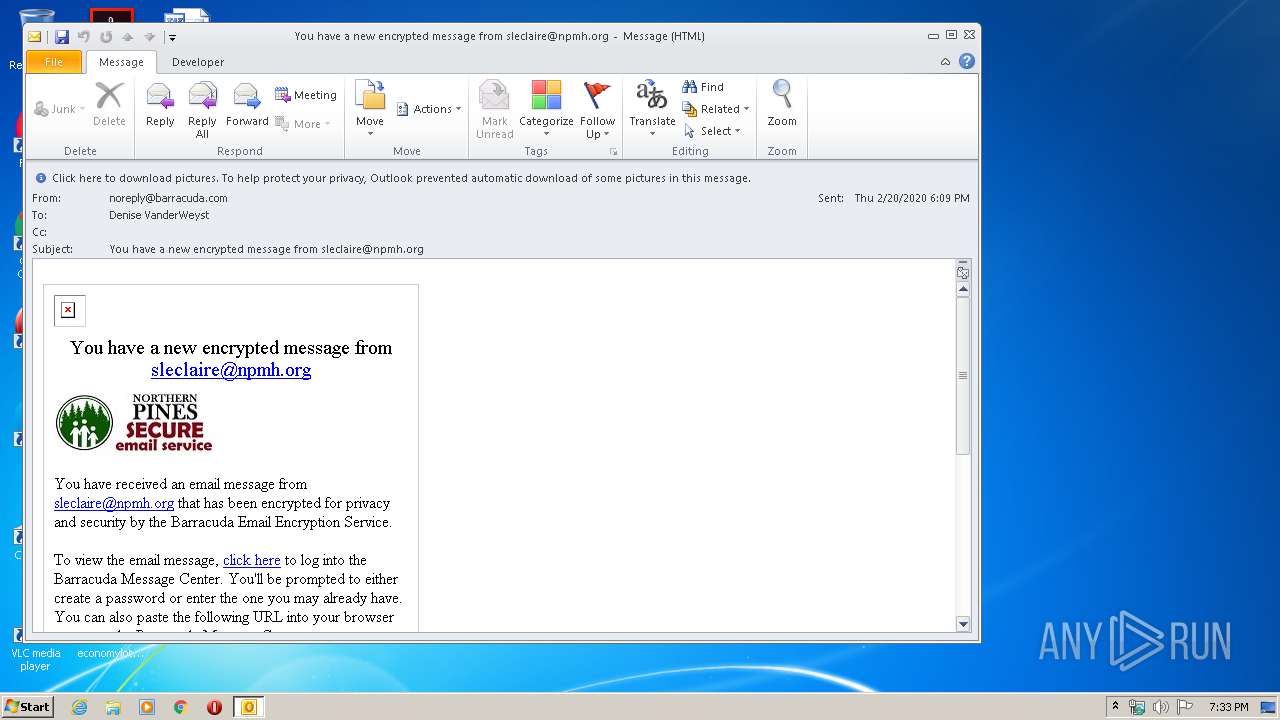
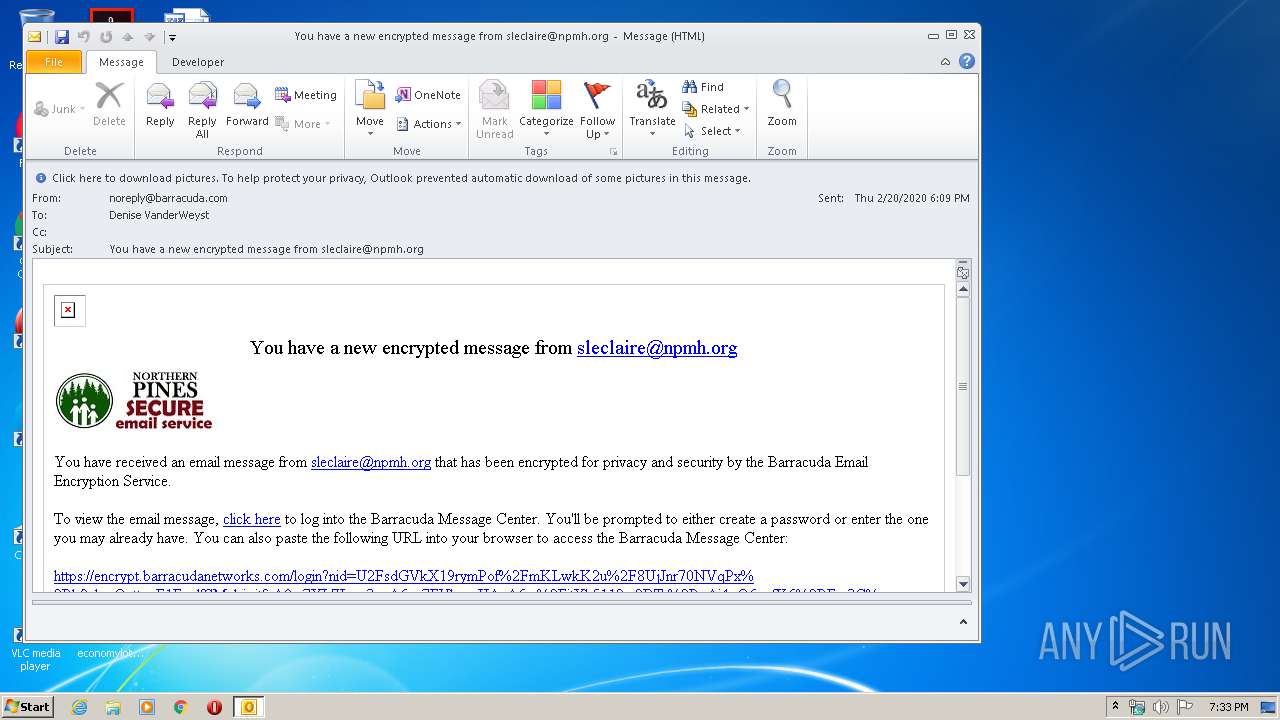
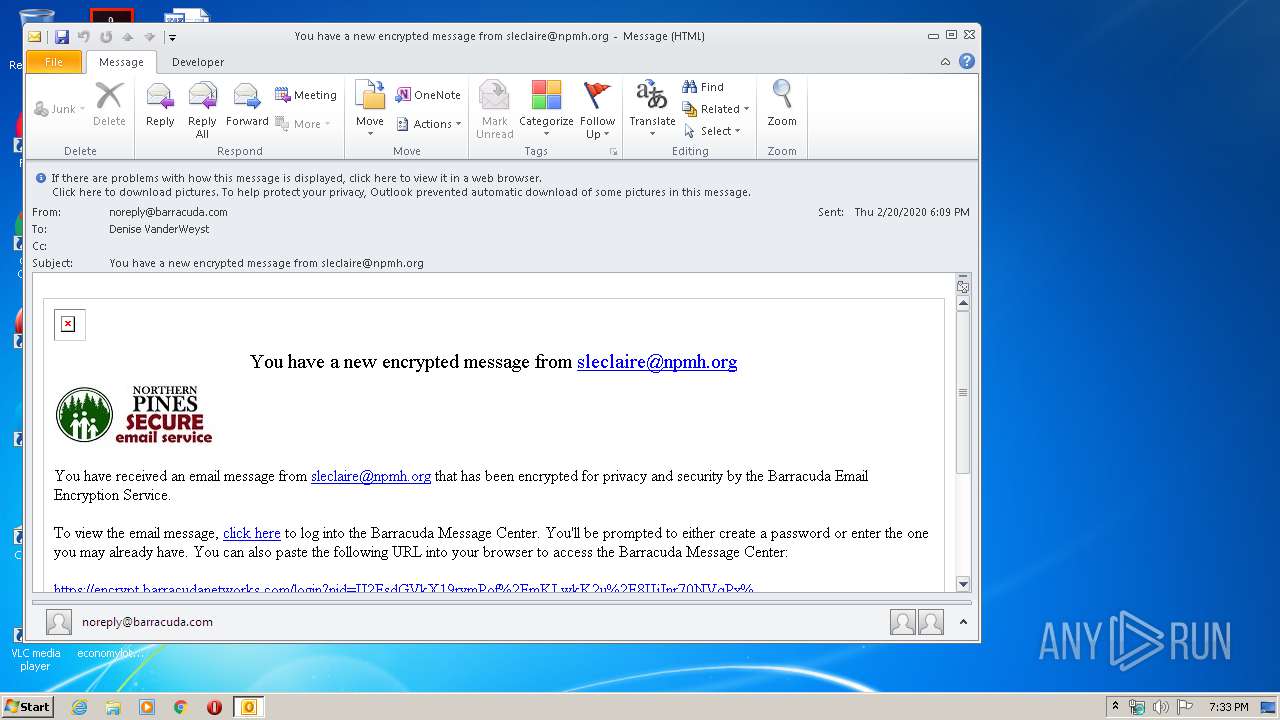
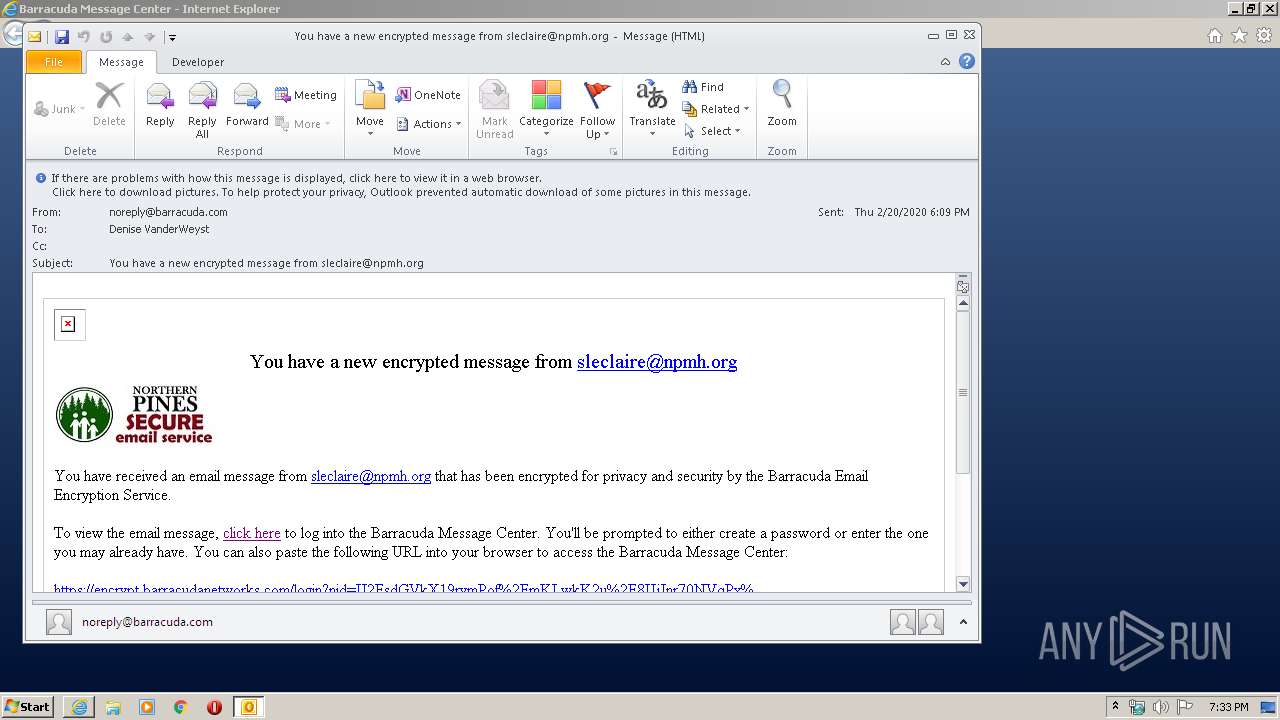
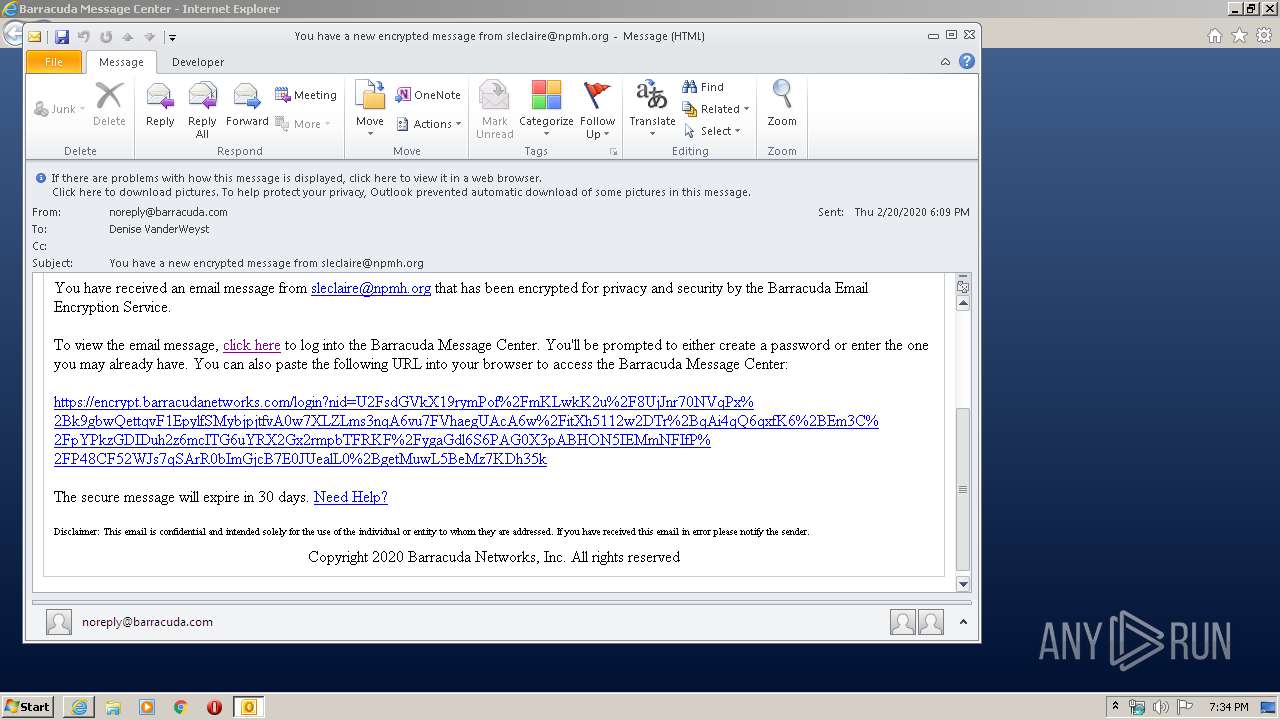
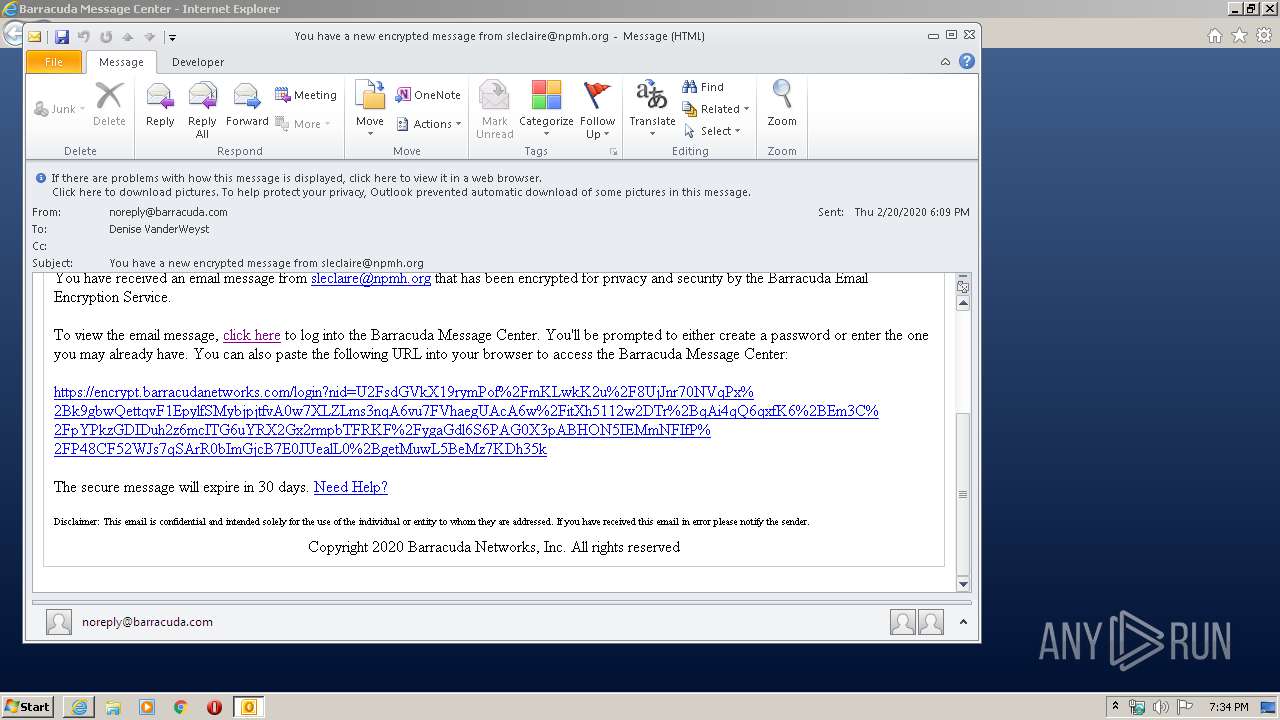
| File name: | You have a new encrypted message from sleclaire@npmh.org.msg |
| Full analysis: | https://app.any.run/tasks/4b26caff-09b4-4315-a619-5467fe827f4b |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 19:32:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 404397A74C21FF15D23614F42B2FE0AE |
| SHA1: | 10346B8D771D4F81F5452A80368D9E764F9747E3 |
| SHA256: | 40836588FF8C750697A86A18D2932912EBC000E145F2F730BF21862FF04BE44A |
| SSDEEP: | 768:SHAV8noXwxWYosK2sKURD0JuvbCsK2sK2sKv+2dqyQh10dM:SgRWdoeqD0BeeOF/h1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3224)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3224)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3224)
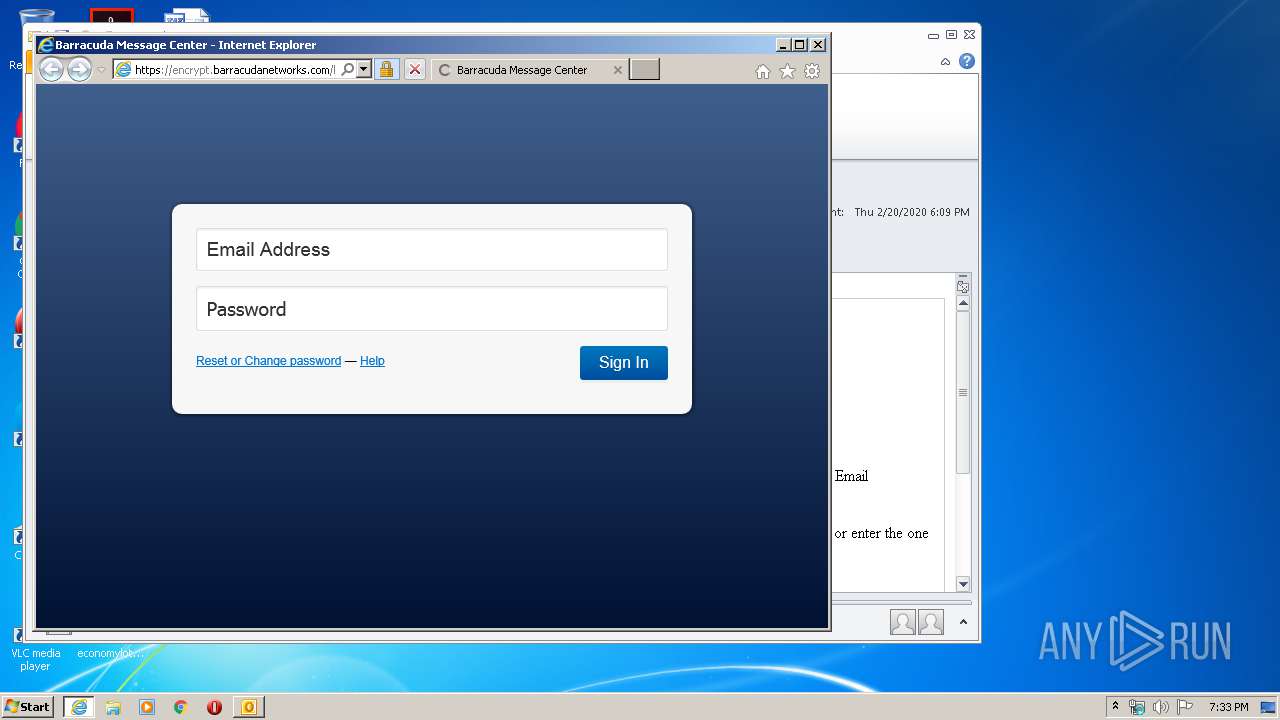
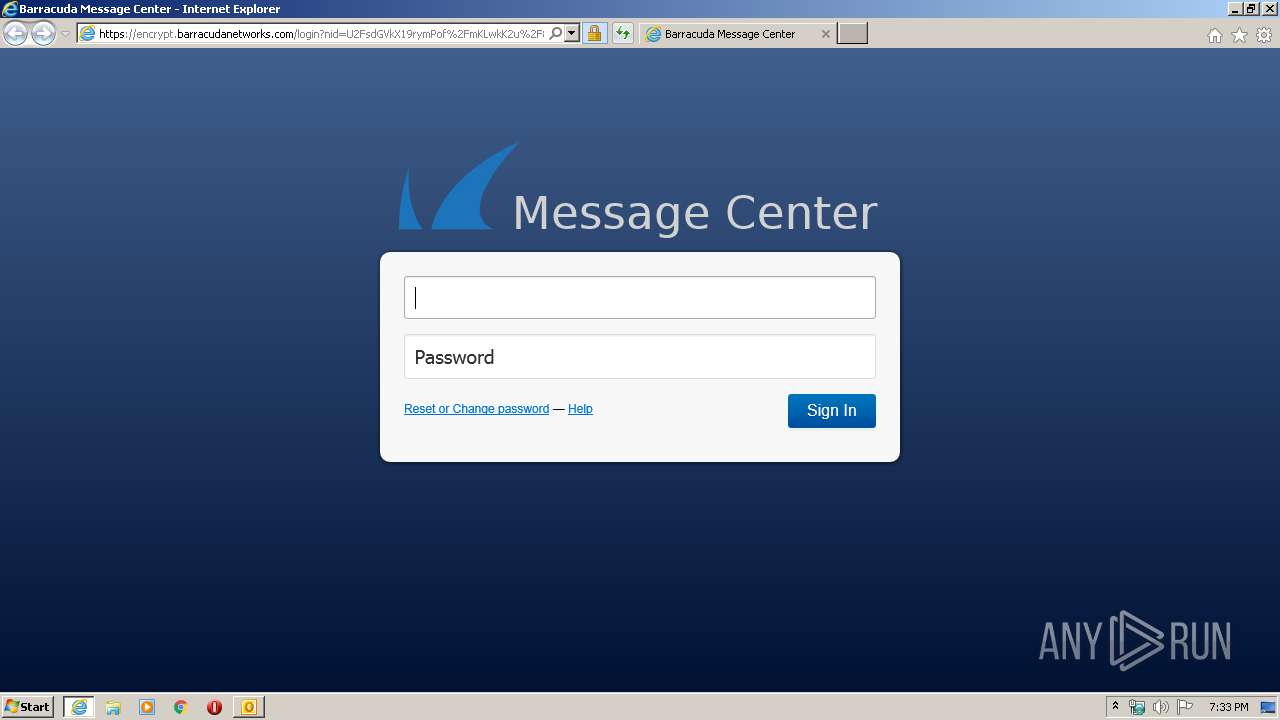
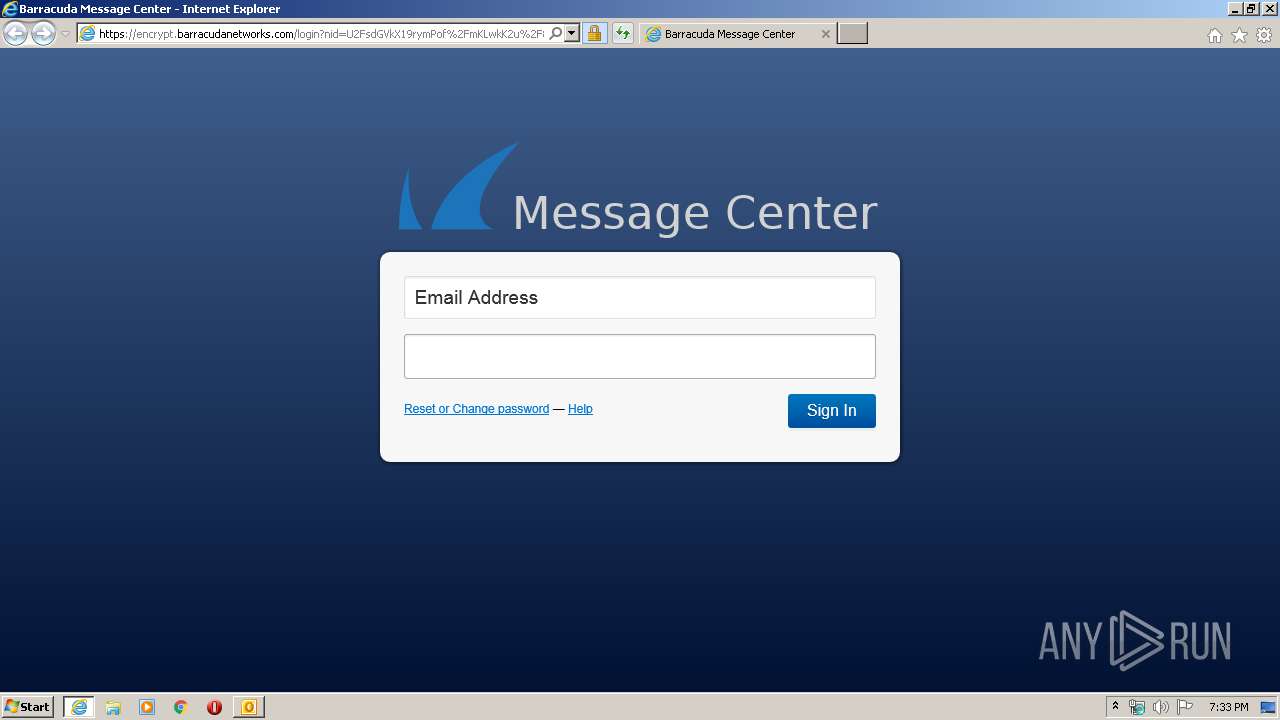
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3224)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 3772)
Changes internet zones settings
- iexplore.exe (PID: 3772)
Application launched itself
- iexplore.exe (PID: 3772)
Reads internet explorer settings
- iexplore.exe (PID: 2896)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3224)
Reads settings of System Certificates
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 2896)
Changes settings of System certificates
- iexplore.exe (PID: 3772)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3772 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\You have a new encrypted message from sleclaire@npmh.org.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
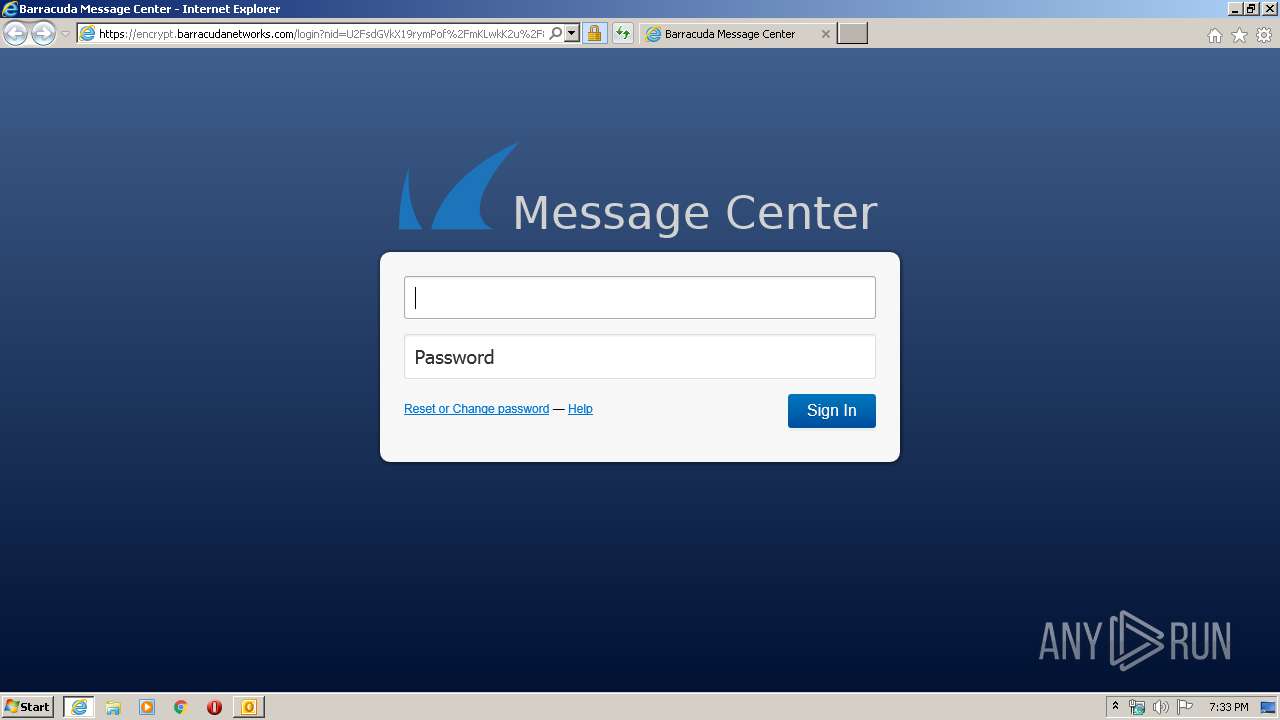
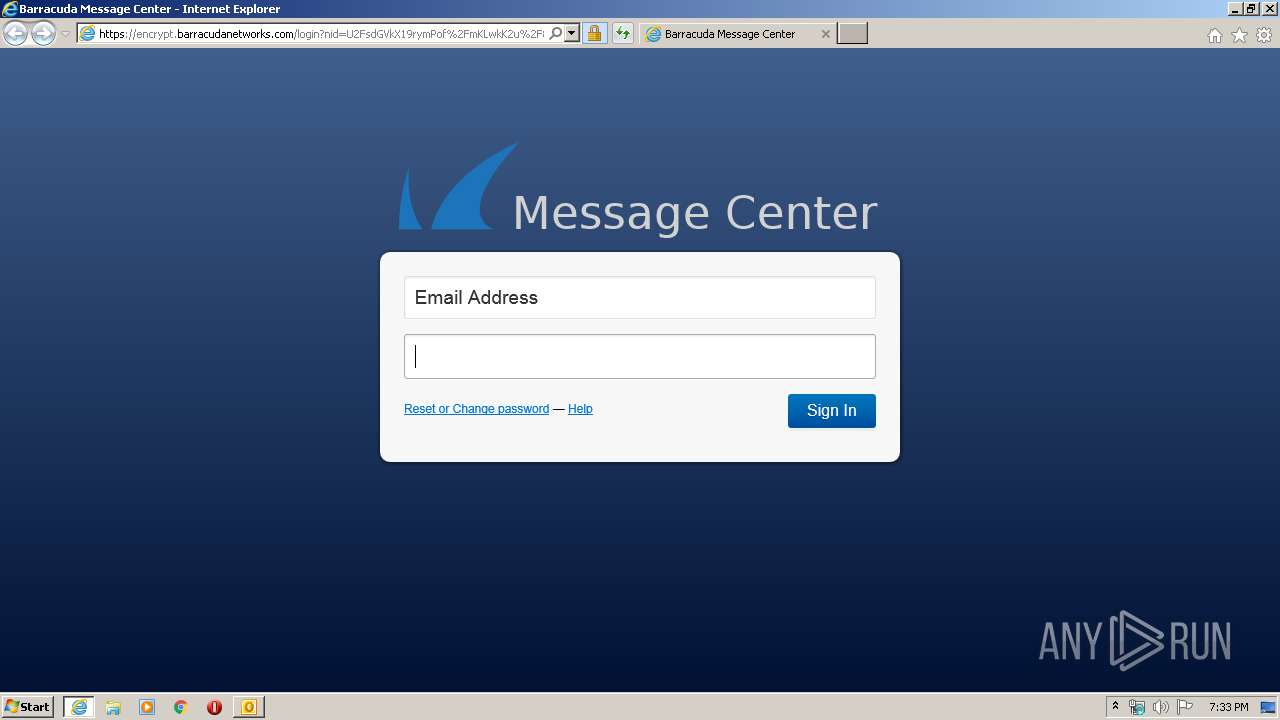
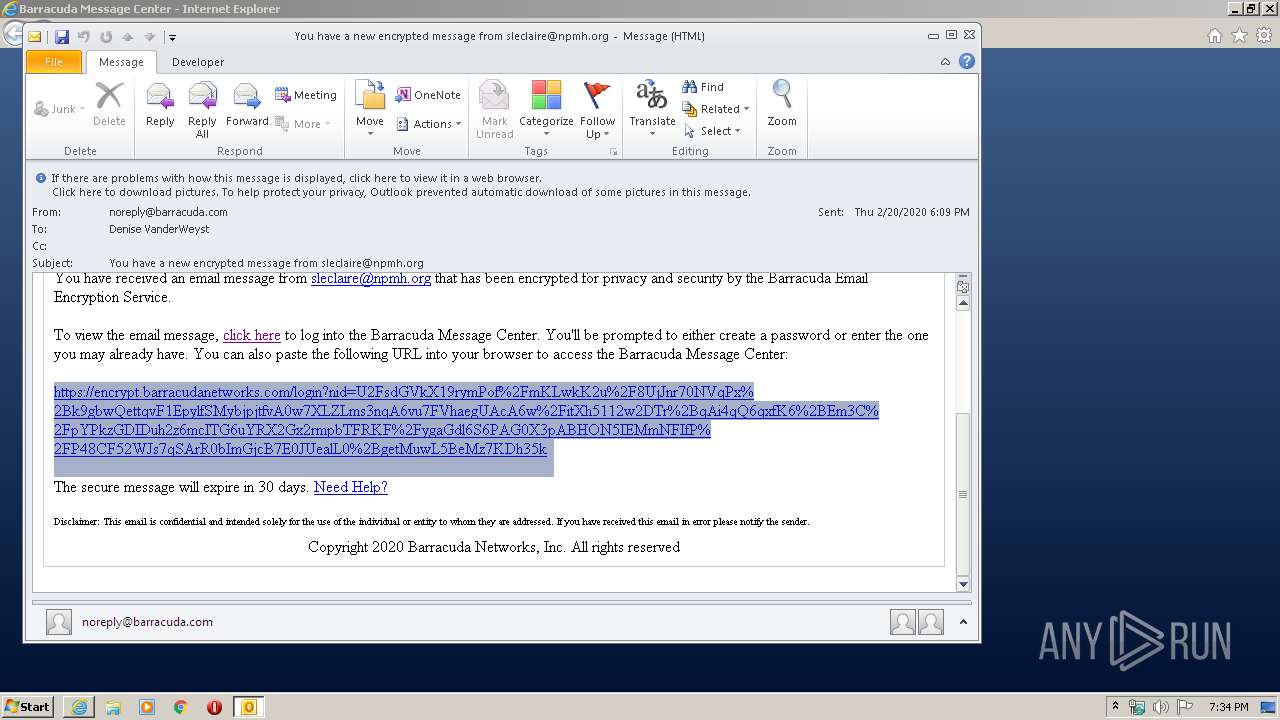
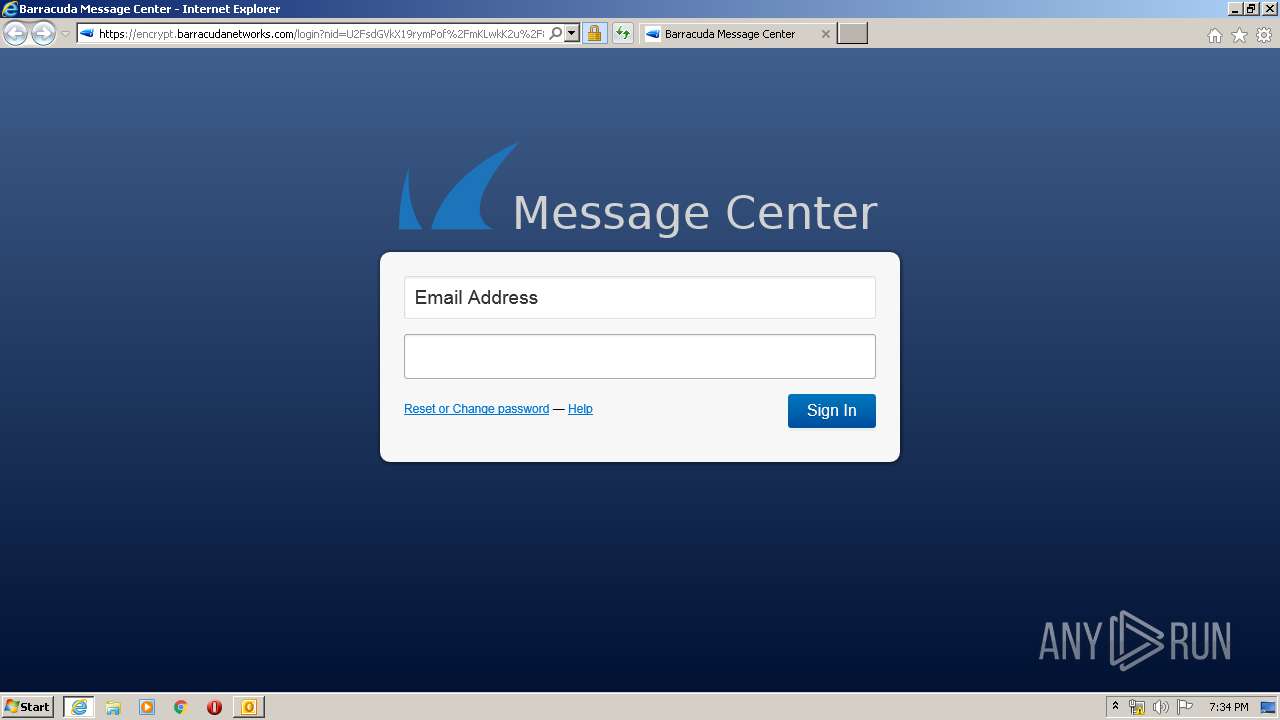
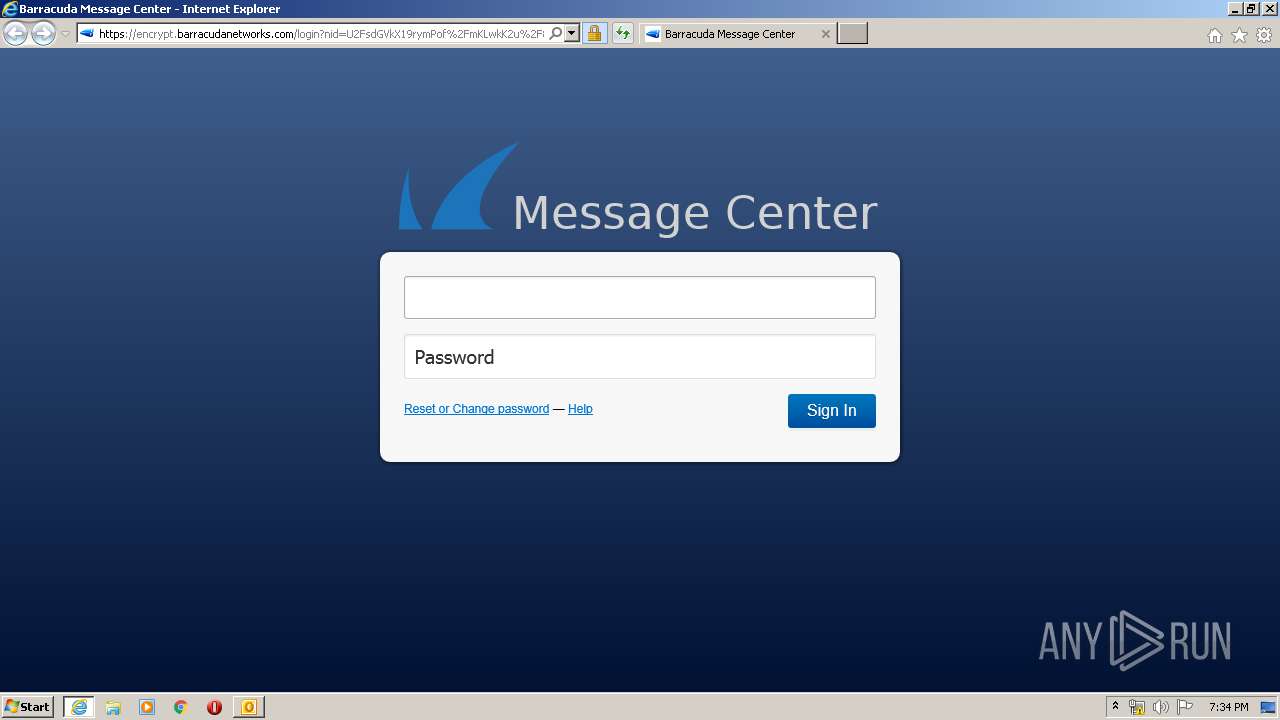
| 3772 | "C:\Program Files\Internet Explorer\iexplore.exe" https://encrypt.barracudanetworks.com/login?nid=U2FsdGVkX19rymPof%2FmKLwkK2u%2F8UjJnr70NVqPx%2Bk9gbwQettqvF1EpylfSMybjpjtfvA0w7XLZLms3nqA6vu7FVhaegUAcA6w%2FitXh5112w2DTr%2BqAi4qQ6qxfK6%2BEm3C%2FpYPkzGDIDuh2z6mcITG6uYRX2Gx2rmpbTFRKF%2FygaGdl6S6PAG0X3pABHON5IEMmNFIfP%2FP48CF52WJs7qSArR0bImGjcB7E0JUealL0%2BgetMuwL5BeMz7KDh35k | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 724
Read events
1 396
Write events
3 748
Delete events
1 580
Modification events
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3224) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
23
Text files
38
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9D61.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9D62.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3224 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3224 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E143CEF1.dat | image | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_C945B4599B2746946B522AC0E32A3309 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2896 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
3772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2896 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
3772 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2896 | iexplore.exe | 13.58.31.72:443 | encrypt.barracudanetworks.com | Amazon.com, Inc. | US | unknown |
3772 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2896 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
2896 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2896 | iexplore.exe | 151.101.2.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
3772 | iexplore.exe | 13.58.31.72:443 | encrypt.barracudanetworks.com | Amazon.com, Inc. | US | unknown |
2896 | iexplore.exe | 162.247.242.20:443 | bam.nr-data.net | New Relic | US | whitelisted |
3772 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3772 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
encrypt.barracudanetworks.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |
crl4.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |