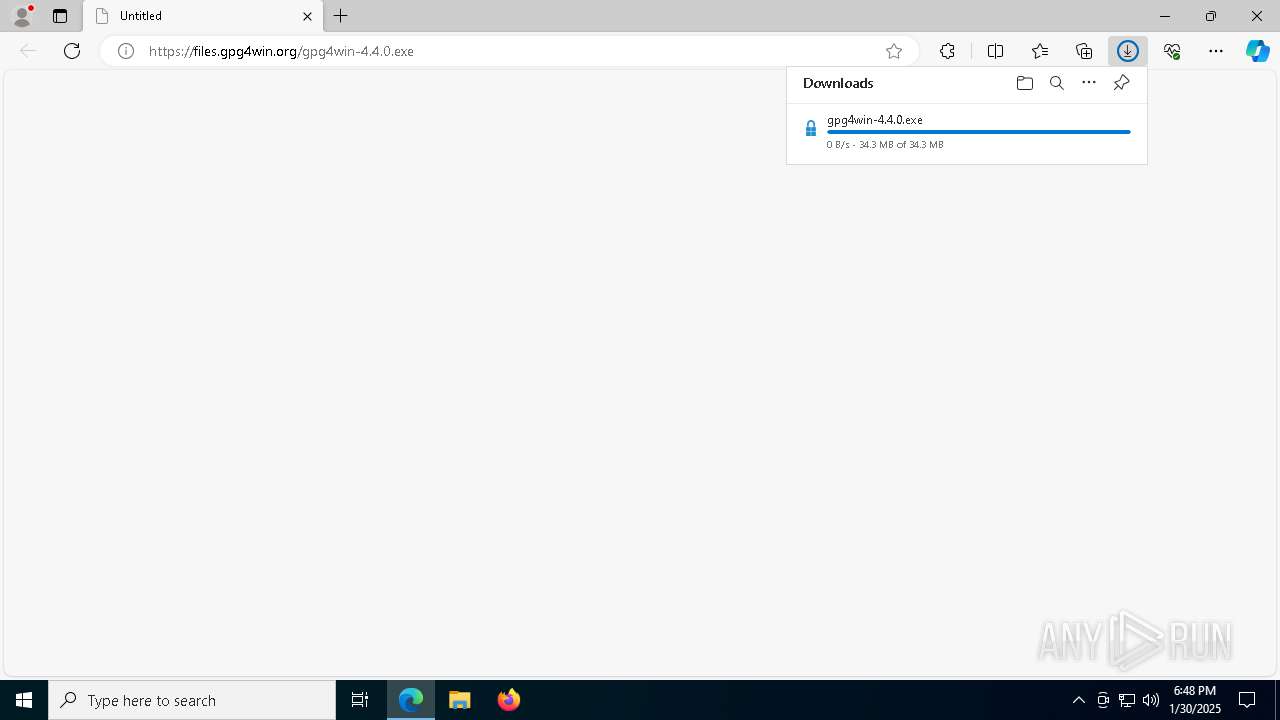
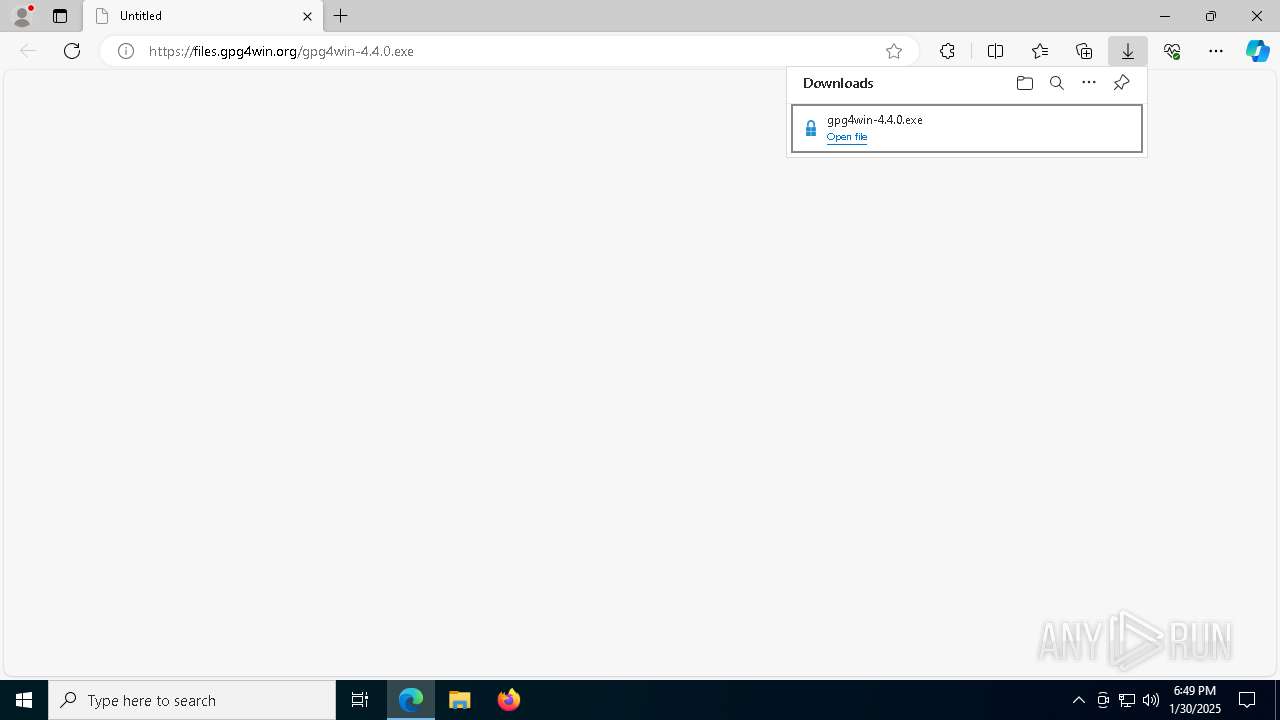
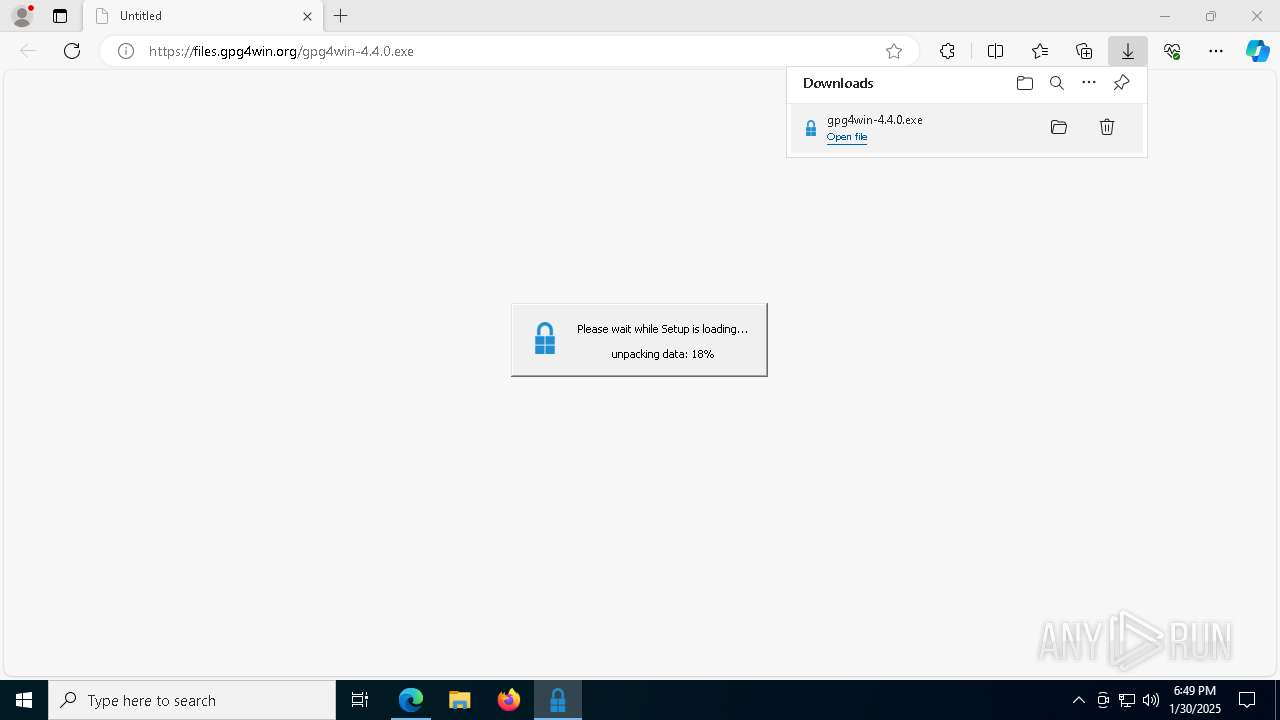
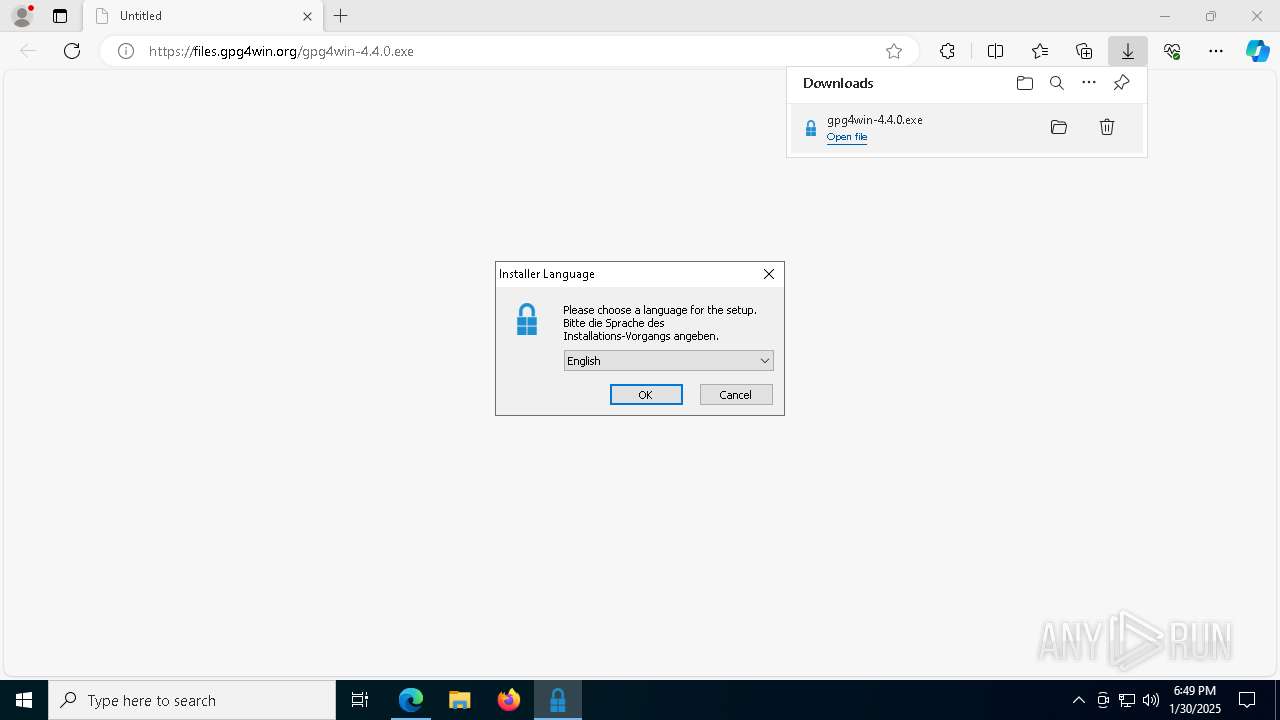
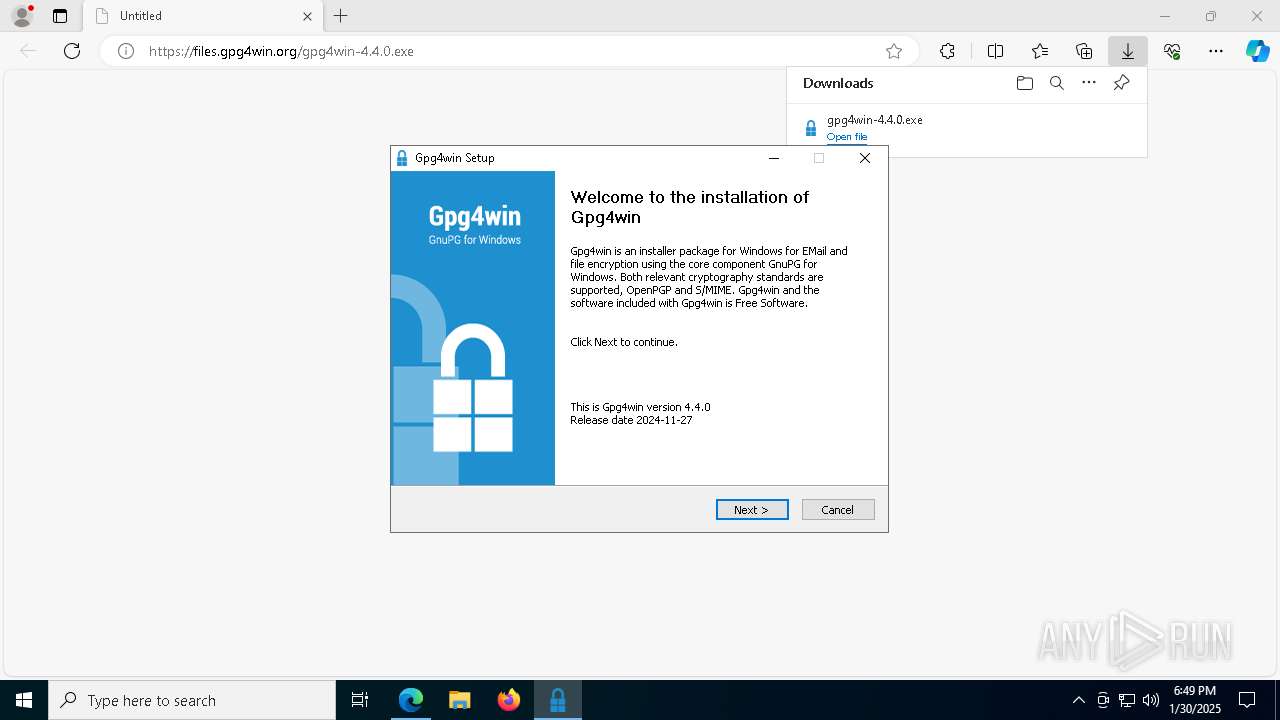
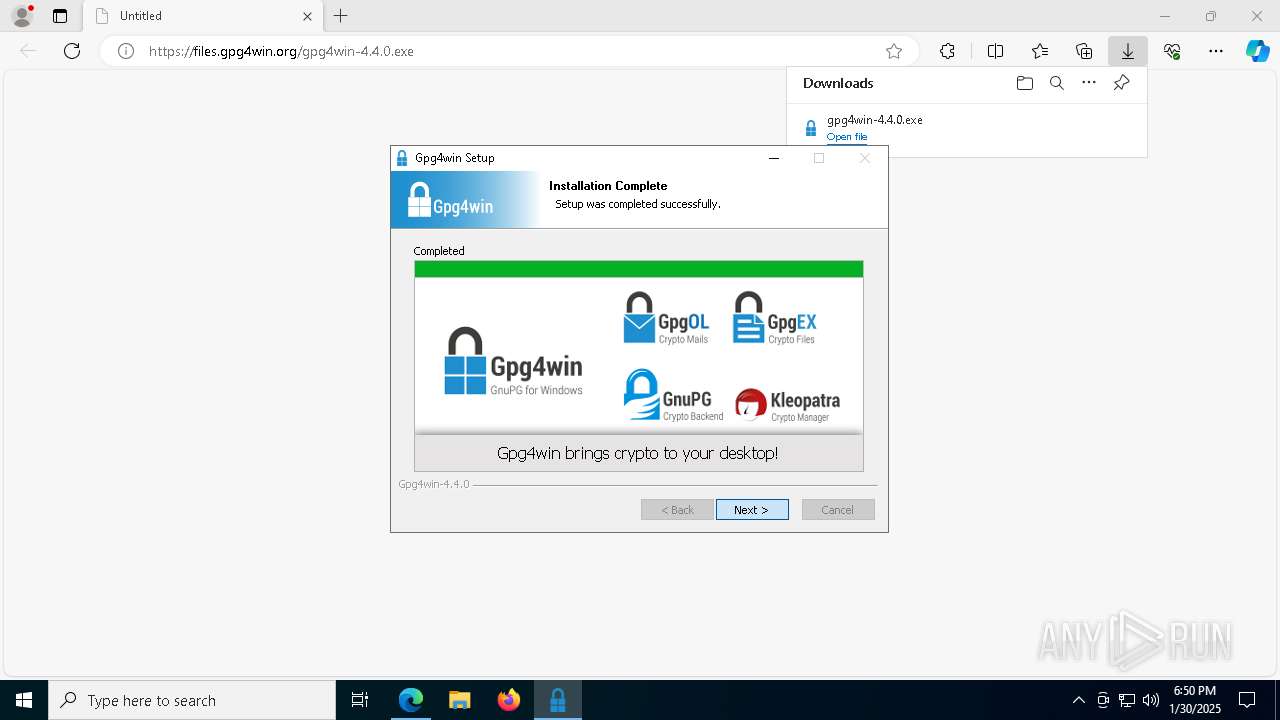
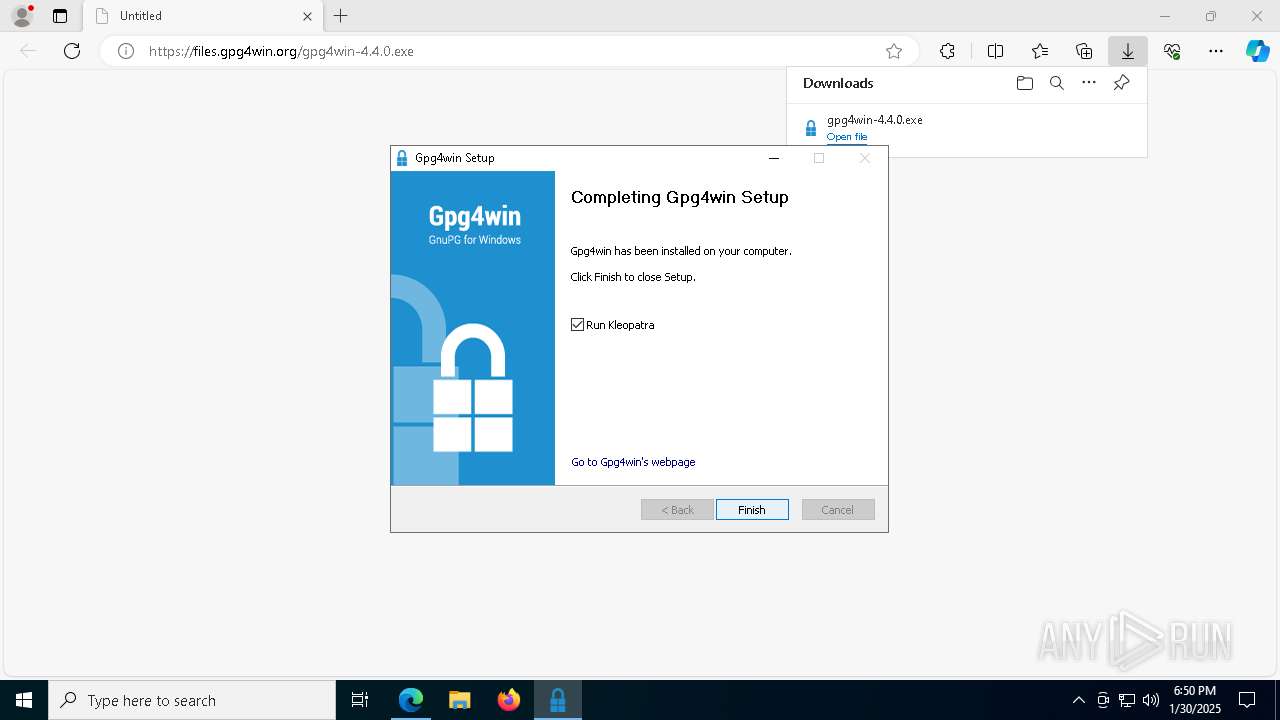
| URL: | https://files.gpg4win.org/gpg4win-4.4.0.exe |
| Full analysis: | https://app.any.run/tasks/6868b516-7380-4826-9109-b647526b1492 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2025, 18:48:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 23F3FACFC0589DB4C77C736702C4932E |
| SHA1: | CF5201E4E72F555ED5404215390992F321E7F386 |
| SHA256: | 407CB9FDAF3B623589308F233743B97AE3472F51F9AAE28807C49D0D1F6F7827 |
| SSDEEP: | 3:N8MGM/K5QRAC:2MGRQmC |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- gpg4win-4.4.0.exe (PID: 1580)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
Executable content was dropped or overwritten
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
Reads Microsoft Outlook installation path
- gpg4win-4.4.0.exe (PID: 1580)
There is functionality for taking screenshot (YARA)
- gpg4win-4.4.0.exe (PID: 1580)
- kleopatra.exe (PID: 5000)
Reads security settings of Internet Explorer
- gpg4win-4.4.0.exe (PID: 1580)
The process creates files with name similar to system file names
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
- gpg4win-4.4.0.exe (PID: 1580)
Creates/Modifies COM task schedule object
- gpg4win-4.4.0.exe (PID: 1580)
- regsvr32.exe (PID: 7780)
- regsvr32.exe (PID: 7704)
Creates a software uninstall entry
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
- gpg4win-4.4.0.exe (PID: 1580)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 6644)
Reads the computer name
- identity_helper.exe (PID: 7824)
- identity_helper.exe (PID: 6236)
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
- kleopatra.exe (PID: 5000)
- scdaemon.exe (PID: 8188)
Reads Environment values
- identity_helper.exe (PID: 7824)
- identity_helper.exe (PID: 6236)
Checks supported languages
- identity_helper.exe (PID: 6236)
- identity_helper.exe (PID: 7824)
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
- gpgme-w32spawn.exe (PID: 7216)
- kleopatra.exe (PID: 5000)
- gpgconf.exe (PID: 6484)
- gpgme-w32spawn.exe (PID: 2144)
- gpgme-w32spawn.exe (PID: 1856)
- gpg-agent.exe (PID: 5200)
- gpgsm.exe (PID: 7252)
- gpgme-w32spawn.exe (PID: 7724)
- gpgconf.exe (PID: 2152)
- dirmngr.exe (PID: 7504)
- gpg-connect-agent.exe (PID: 5572)
- gpg-agent.exe (PID: 6584)
- gpgconf.exe (PID: 6148)
- gpg.exe (PID: 4708)
- gpgconf.exe (PID: 7864)
- gpgme-w32spawn.exe (PID: 5888)
- gpgconf.exe (PID: 3724)
- gpgconf.exe (PID: 6556)
- gpg.exe (PID: 3900)
- gpg.exe (PID: 3996)
- gpgconf.exe (PID: 3824)
- gpgme-w32spawn.exe (PID: 3896)
- gpgme-w32spawn.exe (PID: 6576)
- keyboxd.exe (PID: 308)
- gpgsm.exe (PID: 1296)
- gpgsm.exe (PID: 5456)
- gpgconf.exe (PID: 4164)
- keyboxd.exe (PID: 2632)
- gpgme-w32spawn.exe (PID: 5652)
- gpgme-w32spawn.exe (PID: 5540)
- gpg-agent.exe (PID: 3832)
- gpgconf.exe (PID: 4144)
- gpg-agent.exe (PID: 6476)
- gpgconf.exe (PID: 7280)
- scdaemon.exe (PID: 3936)
- gpgme-w32spawn.exe (PID: 2676)
- dirmngr.exe (PID: 7628)
- scdaemon.exe (PID: 5964)
- dirmngr.exe (PID: 7976)
- gpgconf.exe (PID: 7452)
- gpgme-w32spawn.exe (PID: 7200)
- gpgme-w32spawn.exe (PID: 4244)
- gpgconf.exe (PID: 7924)
- gpgme-w32spawn.exe (PID: 7612)
- gpgme-w32spawn.exe (PID: 7940)
- gpgconf.exe (PID: 7644)
- gpgsm.exe (PID: 7212)
- gpg.exe (PID: 4468)
- scdaemon.exe (PID: 8188)
- keyboxd.exe (PID: 5400)
- gpgme-w32spawn.exe (PID: 1828)
- gpgsm.exe (PID: 6464)
- gpgme-w32spawn.exe (PID: 3052)
- gpg.exe (PID: 6256)
- gpgme-w32spawn.exe (PID: 6076)
- gpgme-w32spawn.exe (PID: 2996)
- gpgconf.exe (PID: 3656)
The sample compiled with english language support
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
Creates files in the program directory
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
Create files in a temporary directory
- gpg4win-4.4.0.exe (PID: 1580)
- gnupg-w32-2.4.7_20241125-bin.exe (PID: 5740)
- kleopatra.exe (PID: 5000)
Application launched itself
- msedge.exe (PID: 6644)
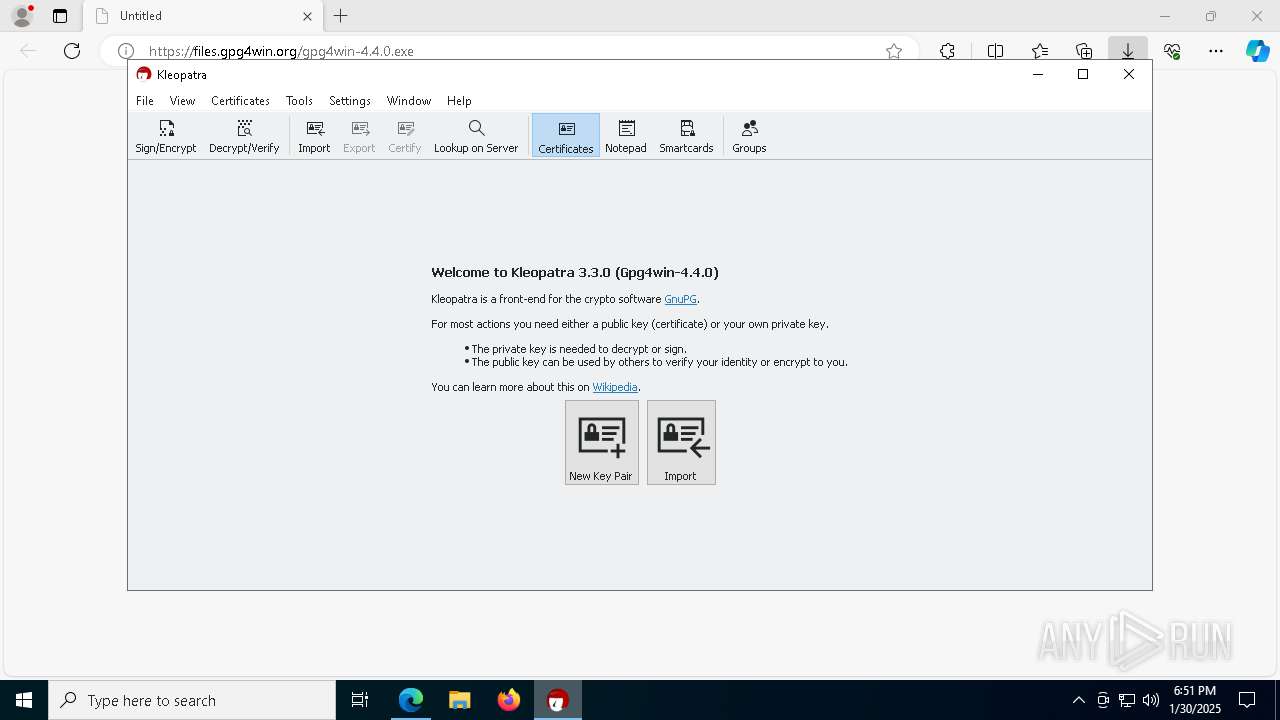
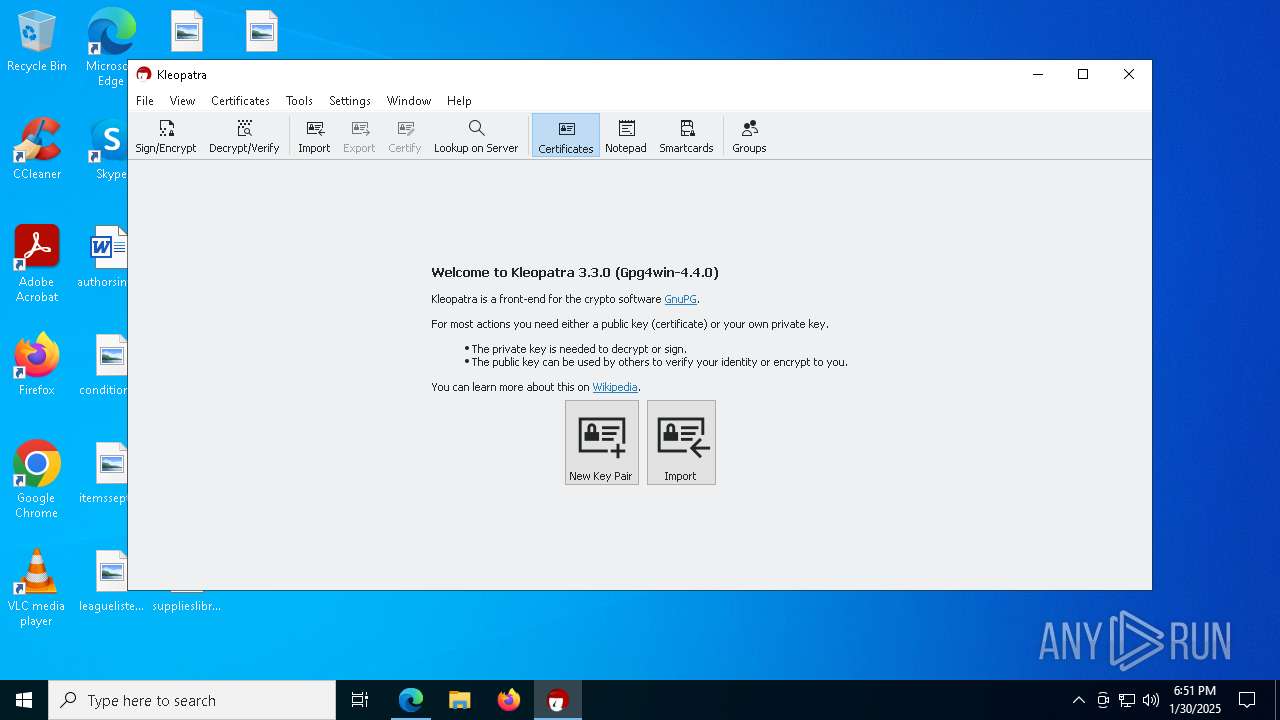
Manual execution by a user
- kleopatra.exe (PID: 5000)
Creates files or folders in the user directory
- kleopatra.exe (PID: 5000)
- gpgconf.exe (PID: 6484)
- gpg-agent.exe (PID: 6584)
- gpg-connect-agent.exe (PID: 5572)
- gpgsm.exe (PID: 7212)
- keyboxd.exe (PID: 5400)
- gpg.exe (PID: 4468)
- scdaemon.exe (PID: 8188)
Reads the machine GUID from the registry
- kleopatra.exe (PID: 5000)
- gpg-agent.exe (PID: 6584)
- keyboxd.exe (PID: 5400)
- scdaemon.exe (PID: 8188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
274
Monitored processes
137
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files (x86)\GnuPG\bin\keyboxd.exe" --dump-option-table | C:\Program Files (x86)\GnuPG\bin\keyboxd.exe | — | gpgconf.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s public key daemon Exit code: 0 Version: 2.4.7 (7bdaf5647) built on <anon> at <none> Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6780 --field-trial-handle=2432,i,17130874488112063143,6135826742247878439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=6836 --field-trial-handle=2432,i,17130874488112063143,6135826742247878439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2432,i,17130874488112063143,6135826742247878439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | gpgconf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\GnuPG\bin\gpgsm.exe" --dump-option-table | C:\Program Files (x86)\GnuPG\bin\gpgsm.exe | — | gpgconf.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s X.509/CMS tool Exit code: 0 Version: 2.4.7 (7bdaf5647) built on <anon> at <none> Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4100 --field-trial-handle=2432,i,17130874488112063143,6135826742247878439,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Downloads\gpg4win-4.4.0.exe" | C:\Users\admin\Downloads\gpg4win-4.4.0.exe | msedge.exe | ||||||||||||
User: admin Company: g10 Code GmbH Integrity Level: HIGH Description: Gpg4win: The GNU Privacy Guard and Tools for Windows Exit code: 0 Version: 4.4.0.22704 Modules
| |||||||||||||||
| 1828 | "C:\\Program Files (x86)\\Gpg4win\\bin\\gpgme-w32spawn.exe" "C:\\Users\\admin\\AppData\\Local\\Temp\\gpgme-0jbdmo" "C:\\Program Files (x86)\\GnuPG\\bin\\gpg.exe" "--disable-dirmngr" "--batch" "--status-fd" "3" "--logger-fd" "7" "--no-tty" "--charset=utf8" "--enable-progress-filter" "--exit-on-status-write-error" "--ttyname=/dev/tty" "--with-colons" "--with-secret" "--with-keygrip" "--with-sig-check" "--list-options" "show-sig-subpackets=\"20,26\"" "--check-sigs" "--" | C:\Program Files (x86)\Gpg4win\bin\gpgme-w32spawn.exe | — | kleopatra.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 1856 | "C:\\Program Files (x86)\\Gpg4win\\bin\\gpgme-w32spawn.exe" "C:\\Users\\admin\\AppData\\Local\\Temp\\gpgme-md7oAl" "C:\\Program Files (x86)\\GnuPG\\bin\\gpgconf.exe" "--version" | C:\Program Files (x86)\Gpg4win\bin\gpgme-w32spawn.exe | — | kleopatra.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
14 681
Read events
14 539
Write events
141
Delete events
1
Modification events
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6280) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E6FADC27878B2F00 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EEDF8F14-96DF-46B8-AA4A-5AB78E66A07A} | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
148
Suspicious files
1 323
Text files
226
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135900.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135900.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
52
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3848 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3848 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6548 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7264 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
7264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
7264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
7264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
7264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
7264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738739530&P2=404&P3=2&P4=e5S2zIo7GbvDNzboyepSPCiiYpgjrmymjWARuuR3tD9tcIqmQi1emOuhkf3sZcE96smvP4%2bkJanDyOFqUtmd3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1864 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6936 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6644 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6936 | msedge.exe | 46.4.134.23:443 | files.gpg4win.org | Hetzner Online GmbH | DE | suspicious |
6936 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6936 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
files.gpg4win.org |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
gpg4win-4.4.0.exe | Created: |
gpg4win-4.4.0.exe | CLSID\{42d30988-1a3a-11da-c687-000d6080e735} |
regsvr32.exe | Created: |
regsvr32.exe | CLSID\{42d30988-1a3a-11da-c687-000d6080e735} |
kleopatra.exe | org.kde.pim.kleopatra: Responder handle: 0x0
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 73 ms: Application created
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 80 ms: Starting version info check
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 76 ms: Service created
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 82 ms: Checking backend versions
|
kleopatra.exe | org.kde.pim.kleopatra: Created responder: "kleopatraResponder" with handle: 0x50318
|