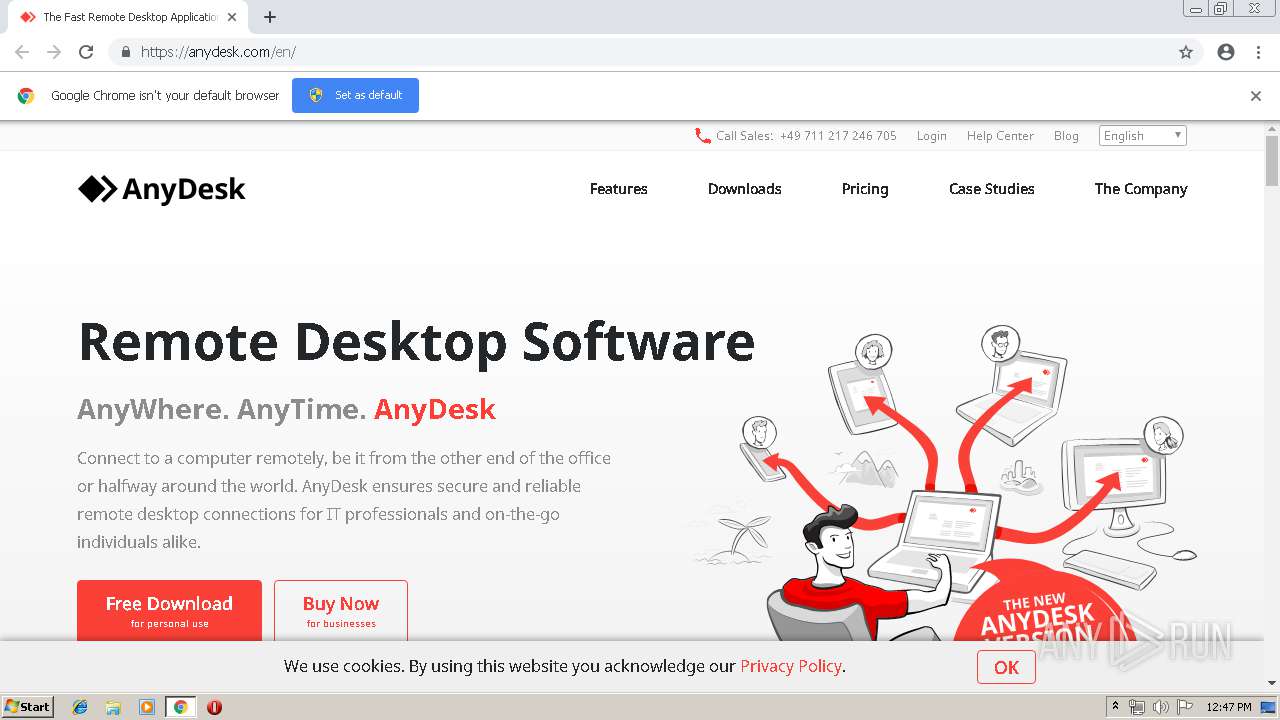
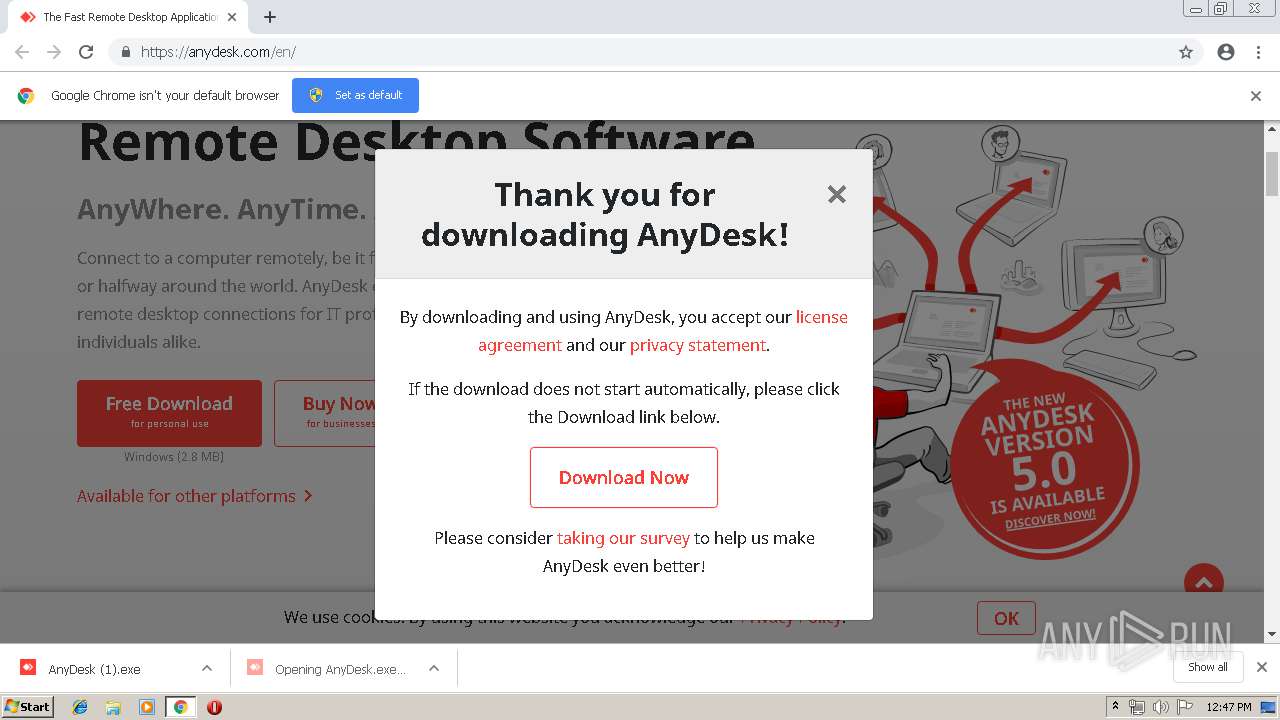
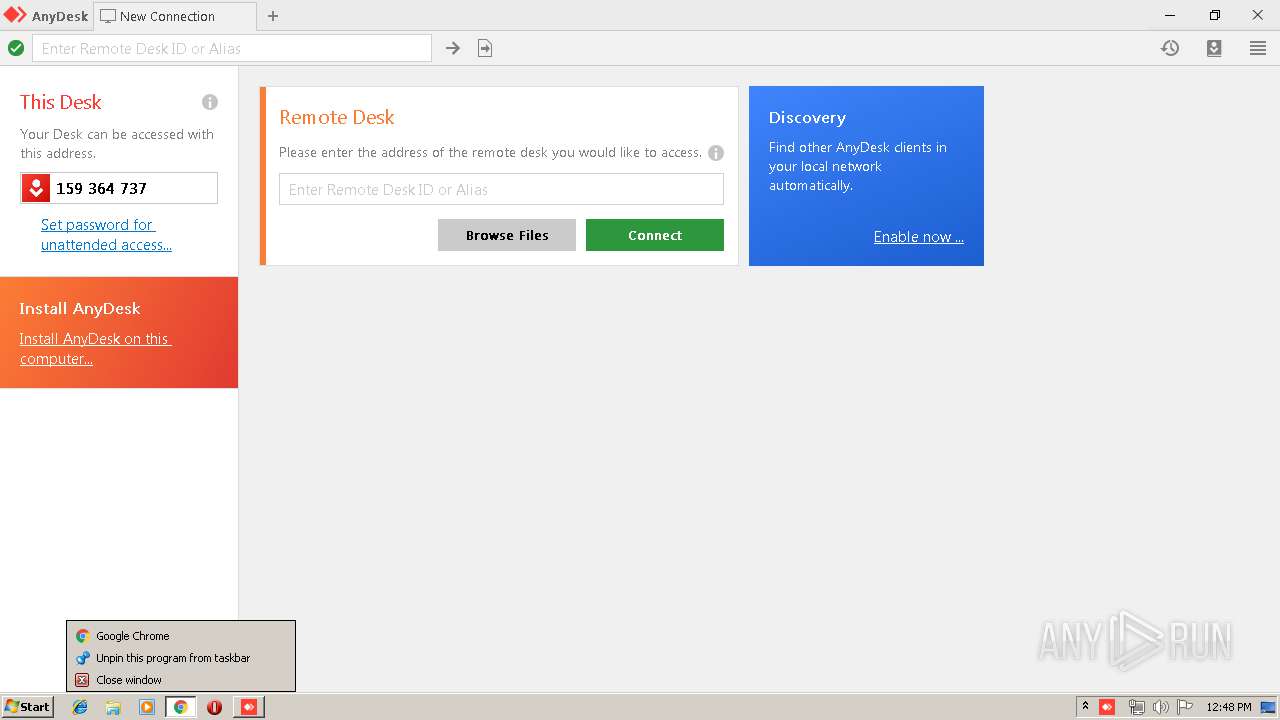
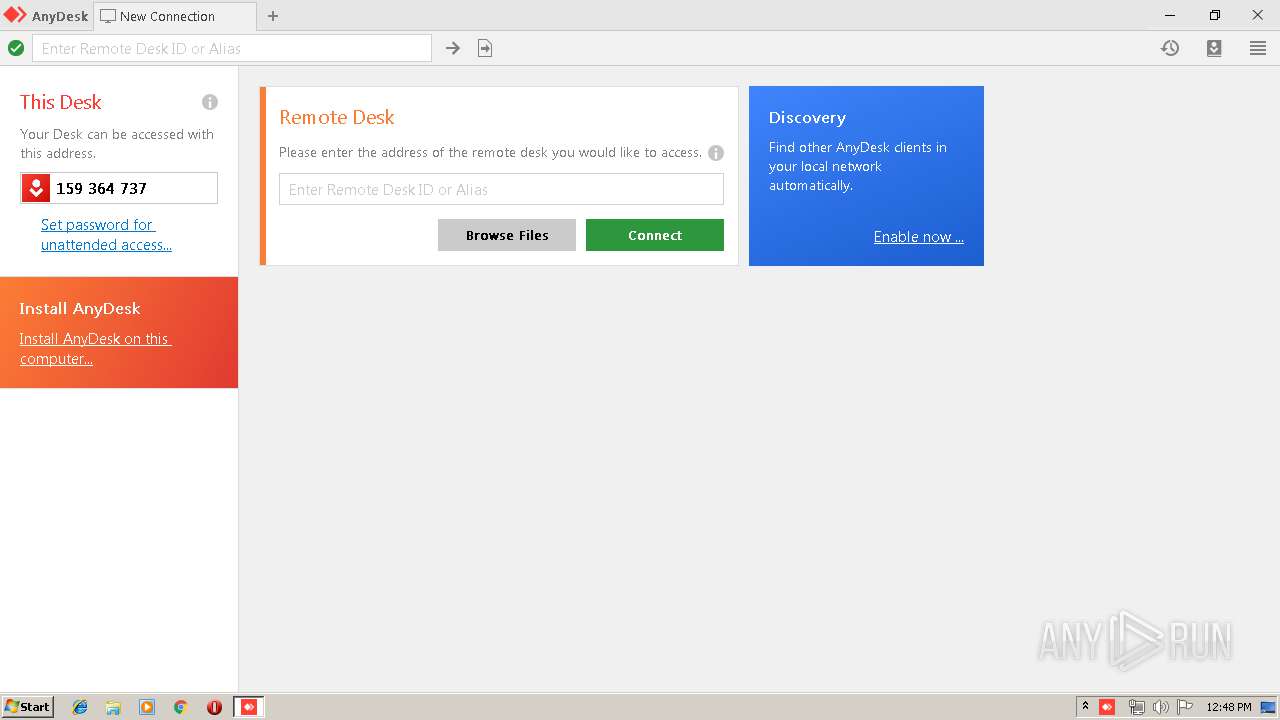
| URL: | http://boot-02.net.anydesk.com |
| Full analysis: | https://app.any.run/tasks/c7f53910-ba8d-43c6-b8ea-ab38c082281e |
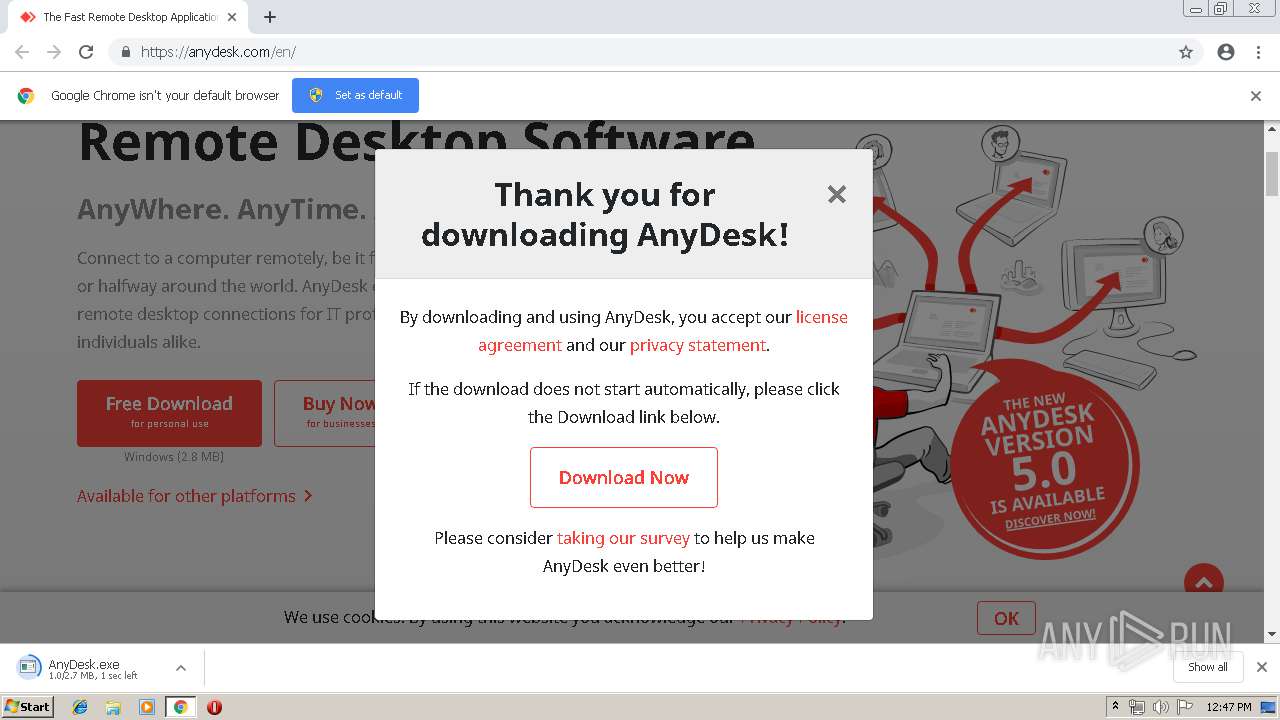
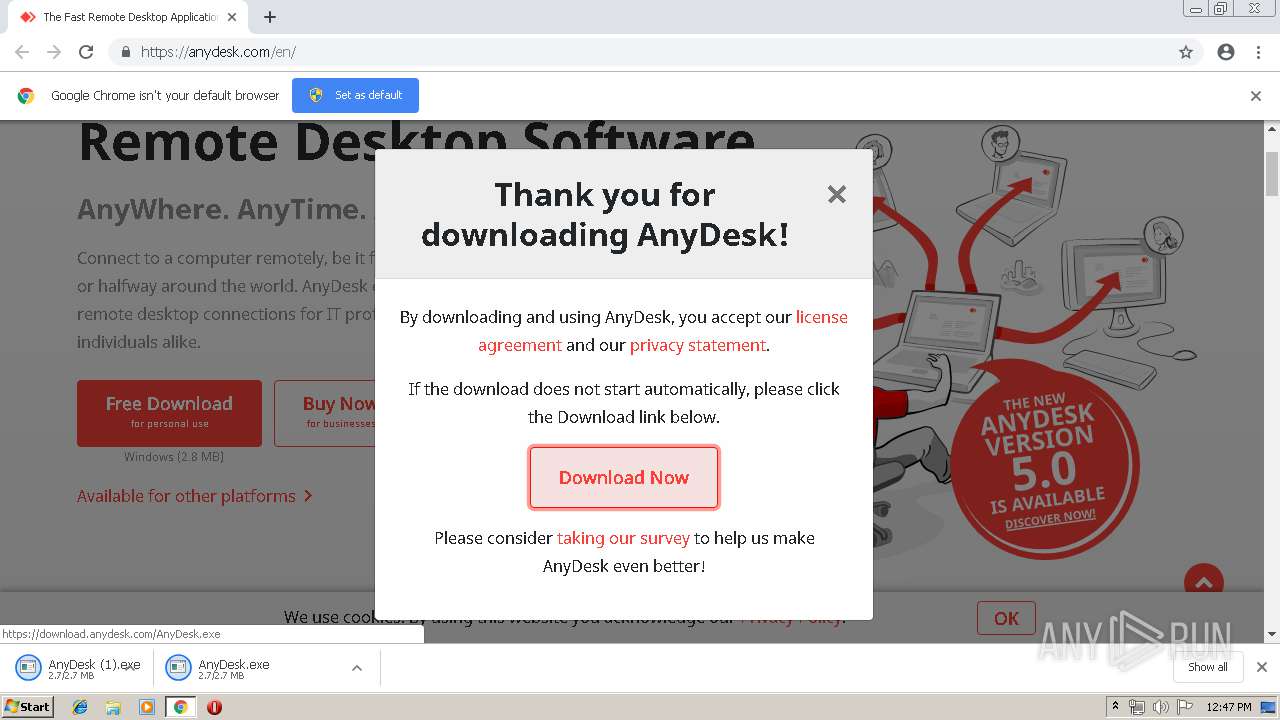
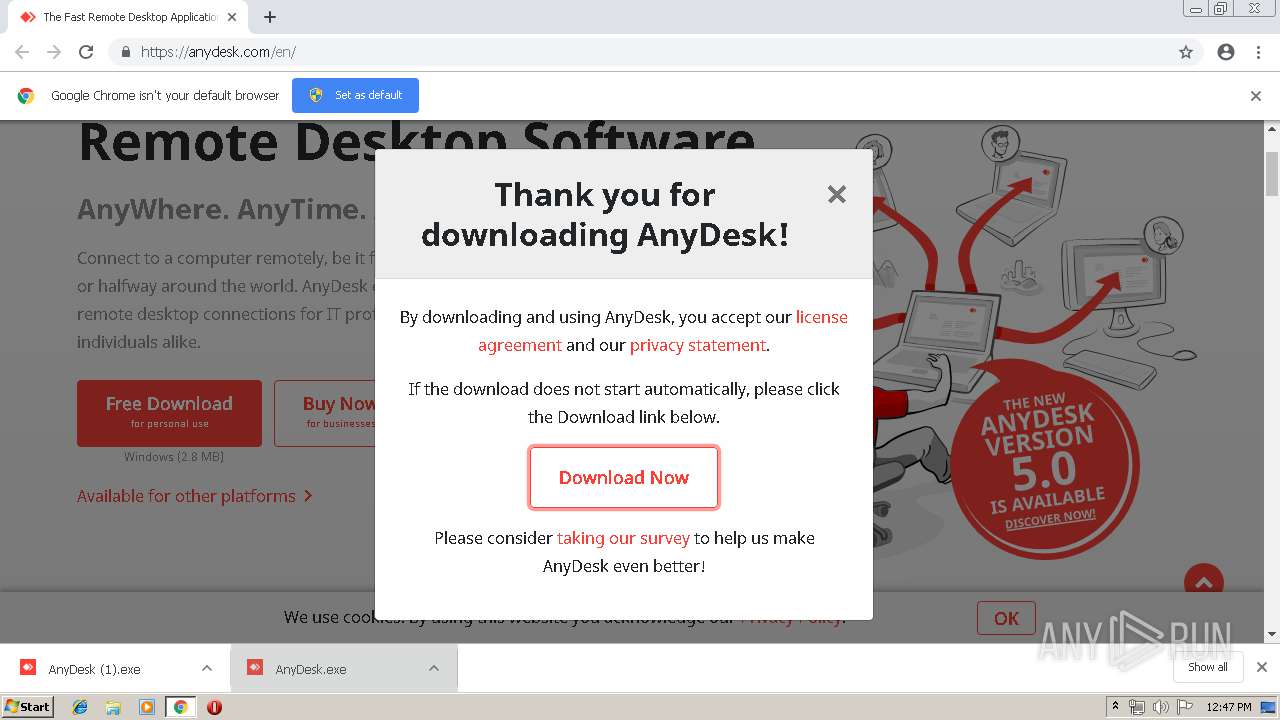
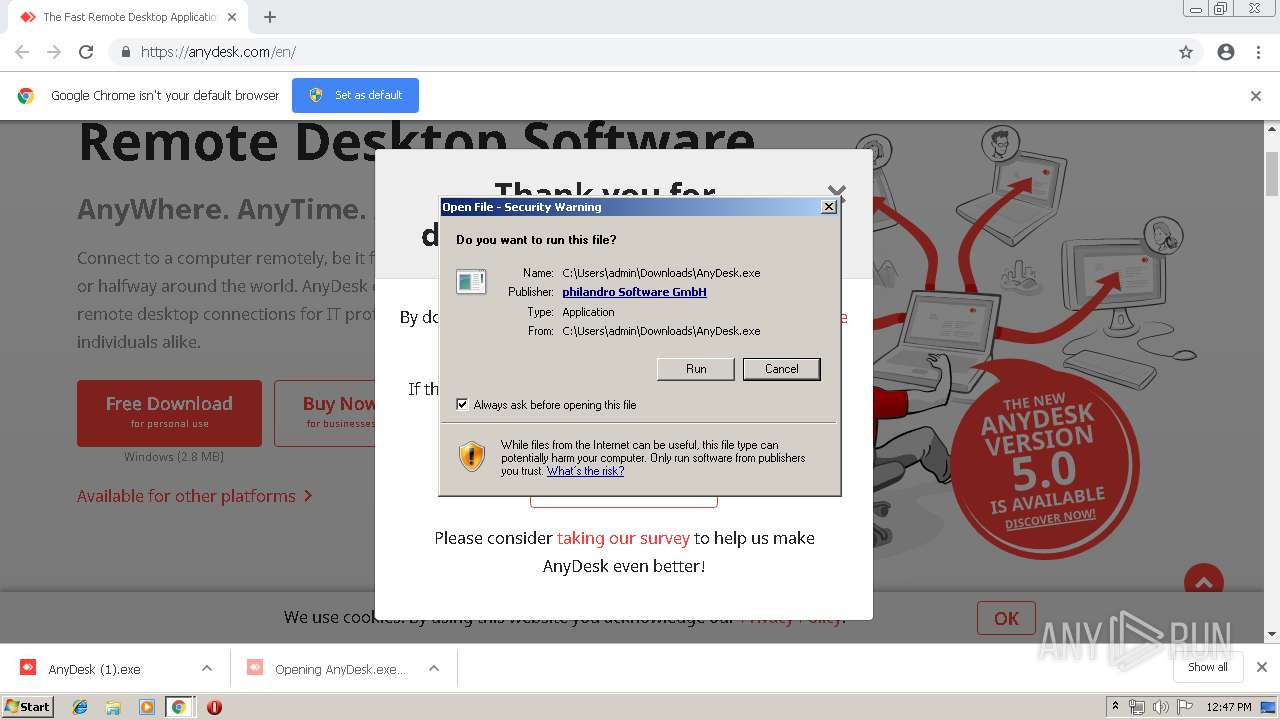
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2019, 11:47:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 53EC36BD24FC40E75D0D1DC7B7307024 |
| SHA1: | 5294DE0417A4CB1E5CAEF9523BC3161033429CF4 |
| SHA256: | 4072AC838C103F35B353978C152FAAAE65FBD75660EC977DC4156ADE3008C9B3 |
| SSDEEP: | 3:N1Kc3K/0LicBuI:Cc6s++ |
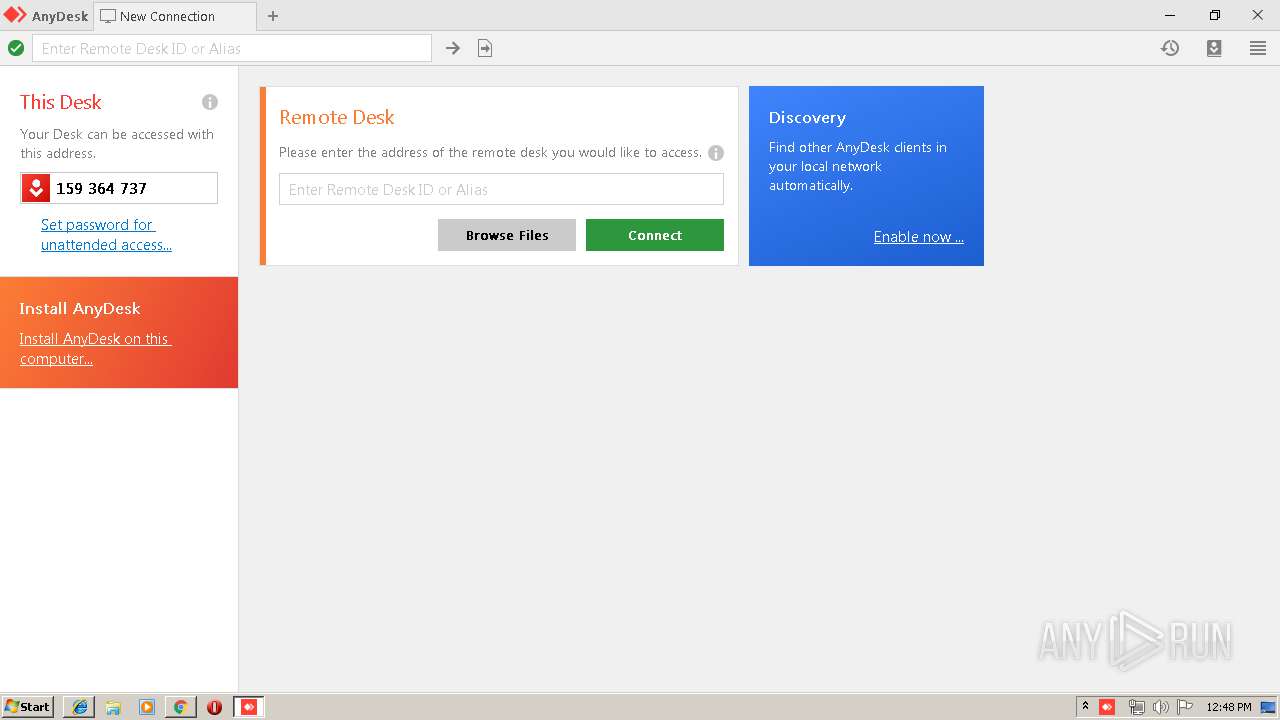
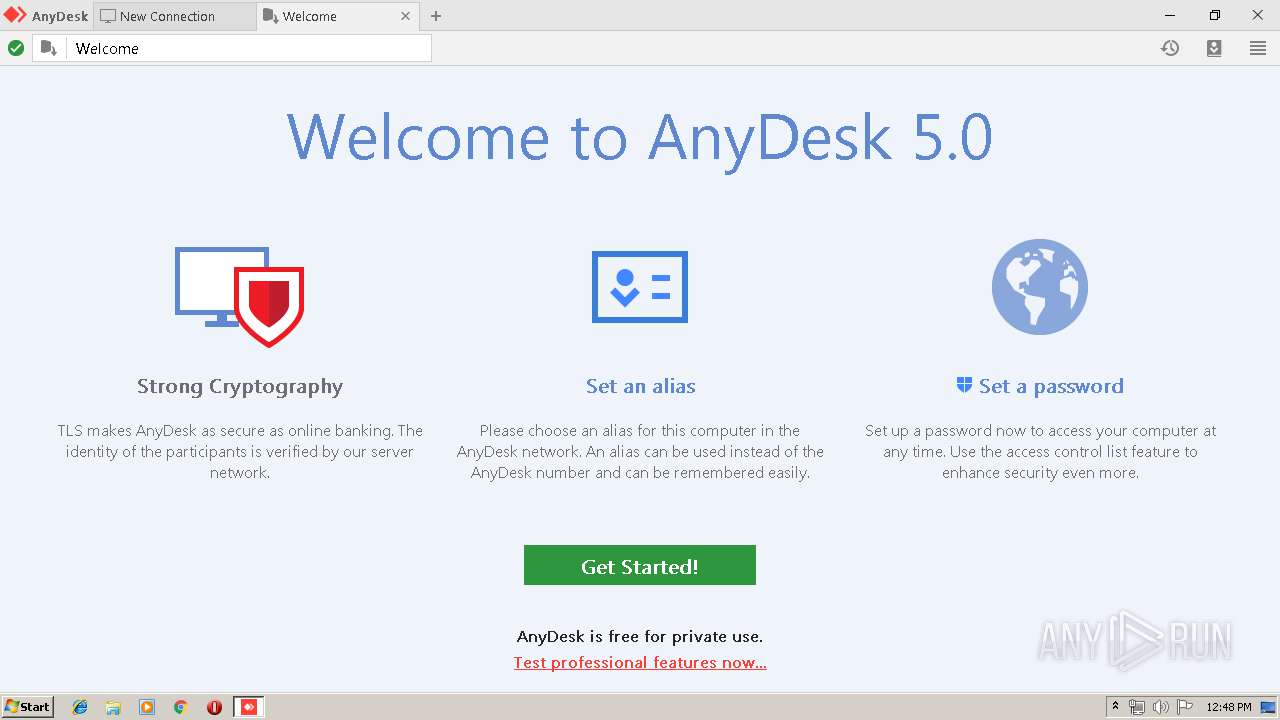
MALICIOUS
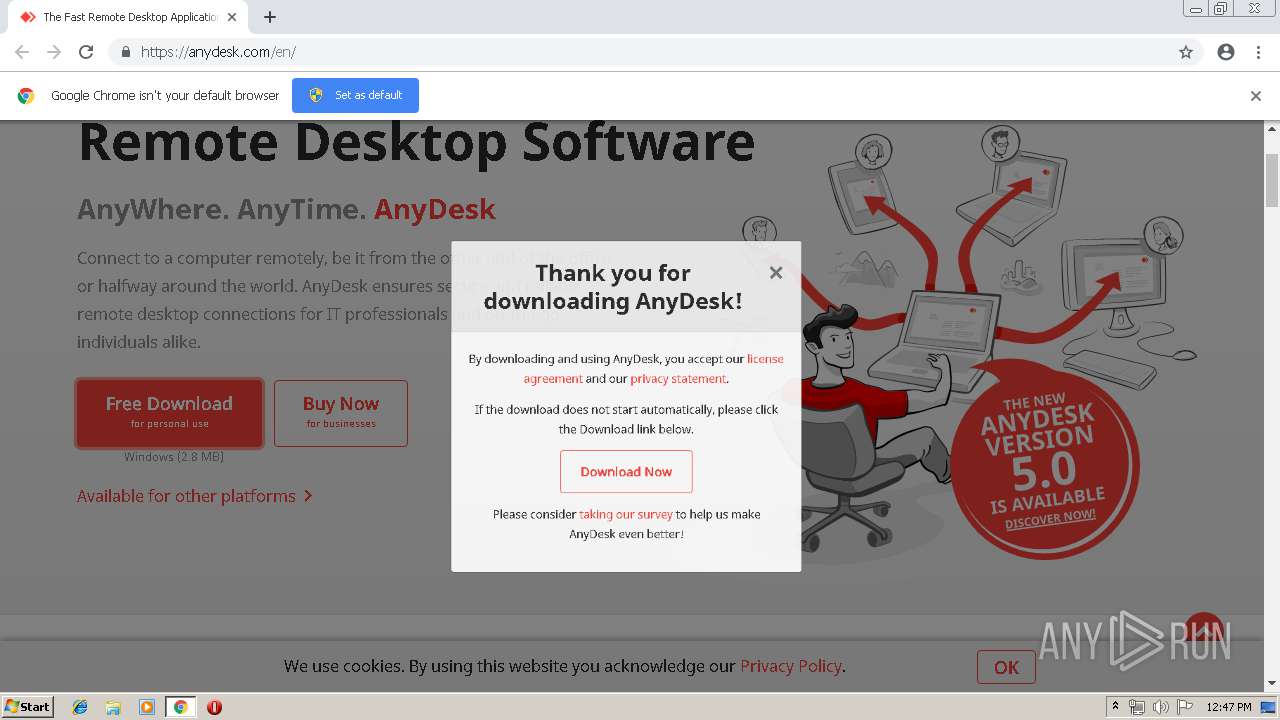
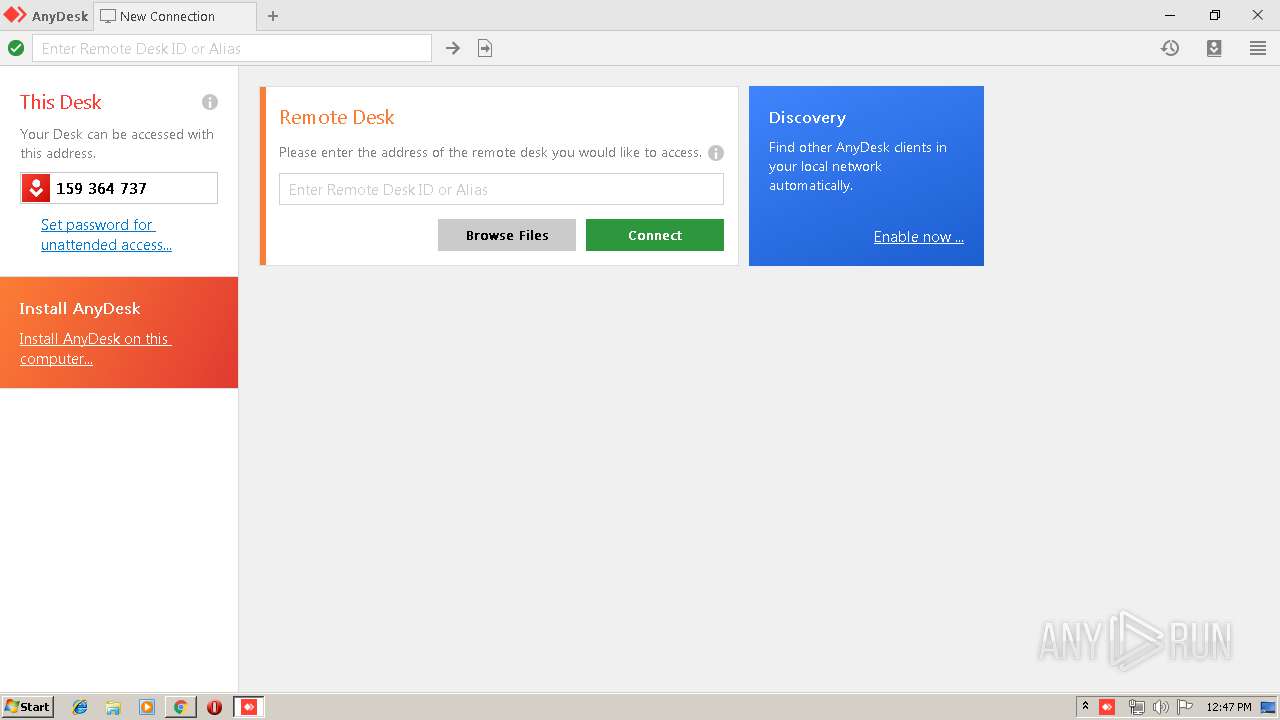
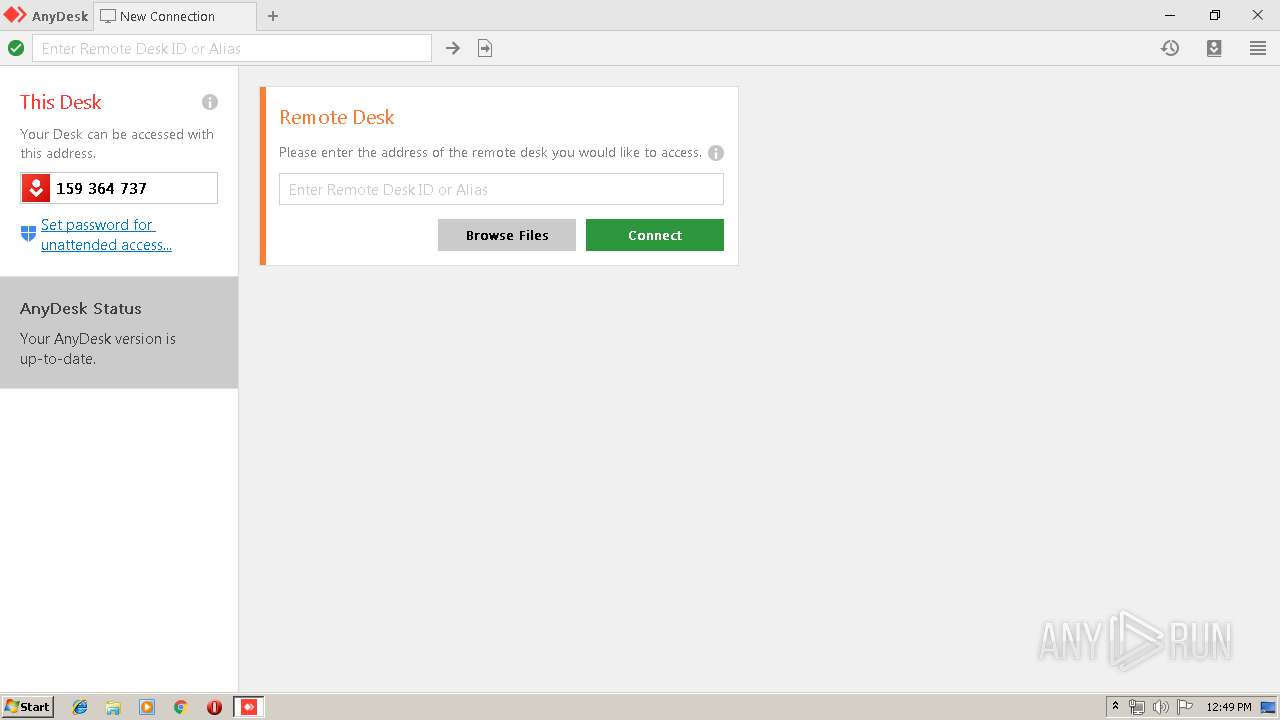
Application was dropped or rewritten from another process
- AnyDesk.exe (PID: 3804)
- AnyDesk.exe (PID: 2268)
- AnyDesk.exe (PID: 2592)
- AnyDesk.exe (PID: 2840)
- AnyDesk.exe (PID: 4028)
- AnyDesk.exe (PID: 2208)
- AnyDesk.exe (PID: 2564)
Writes to a start menu file
- AnyDesk.exe (PID: 3804)
SUSPICIOUS
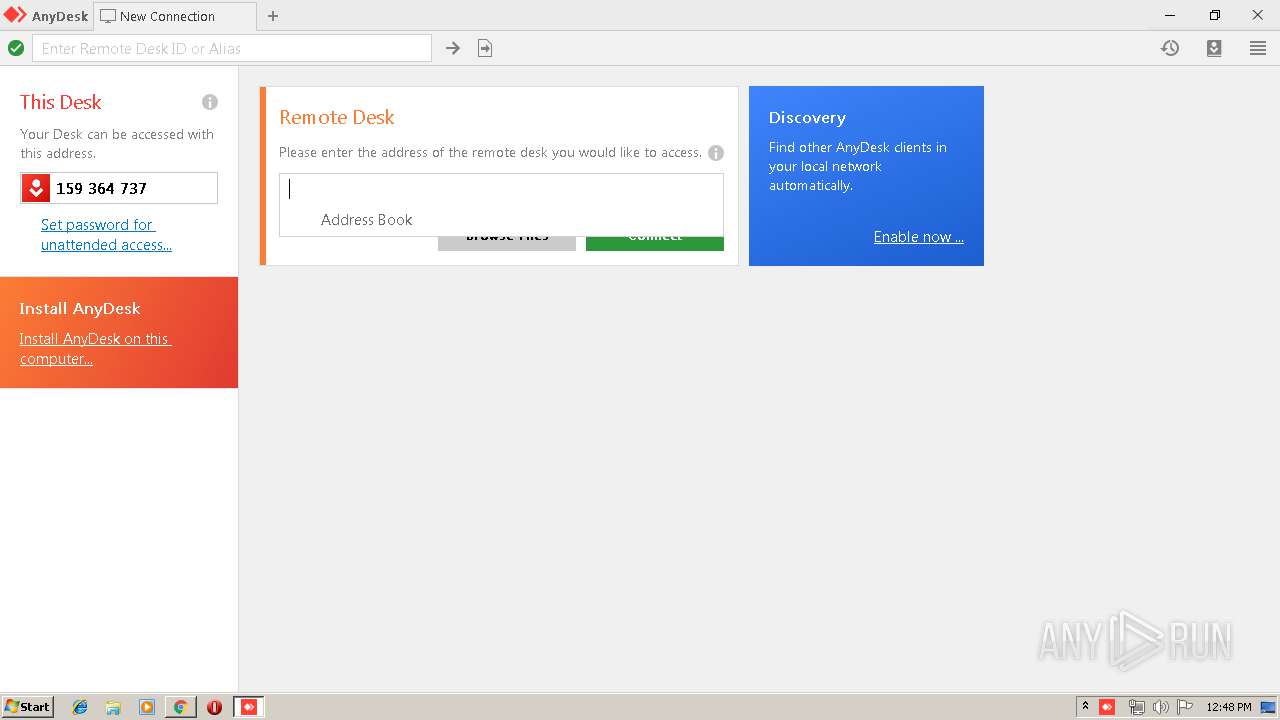
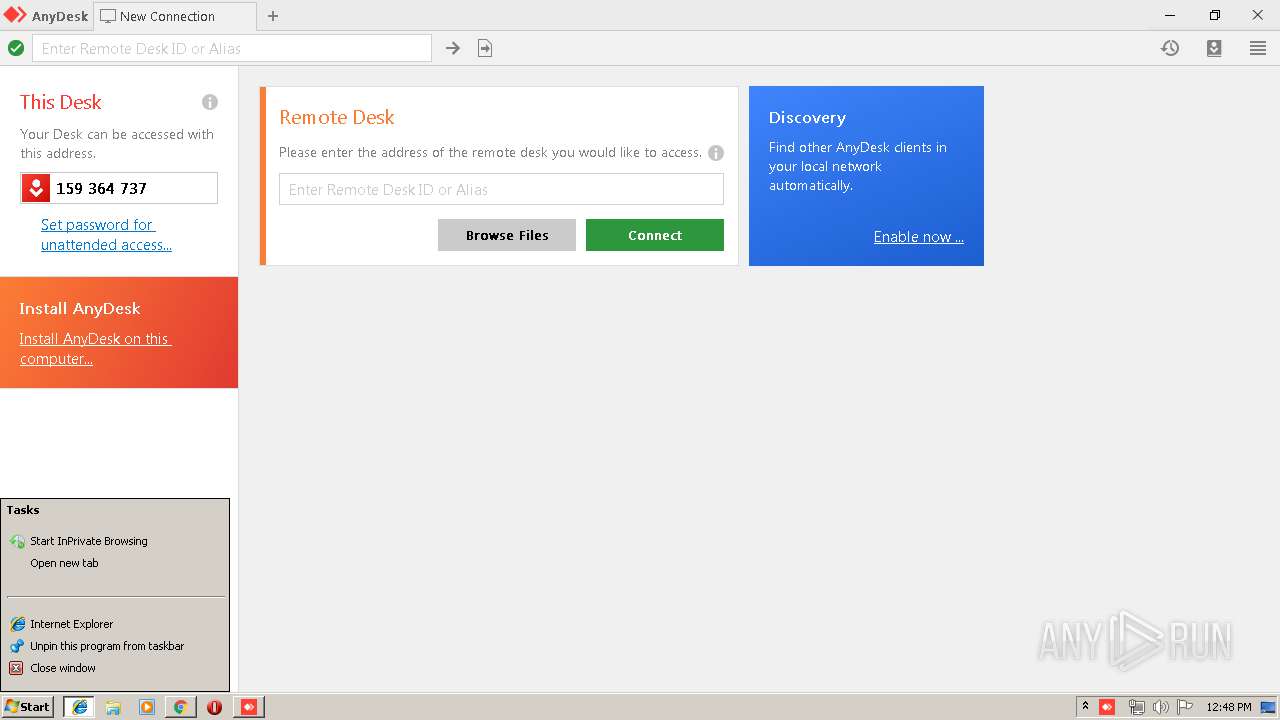
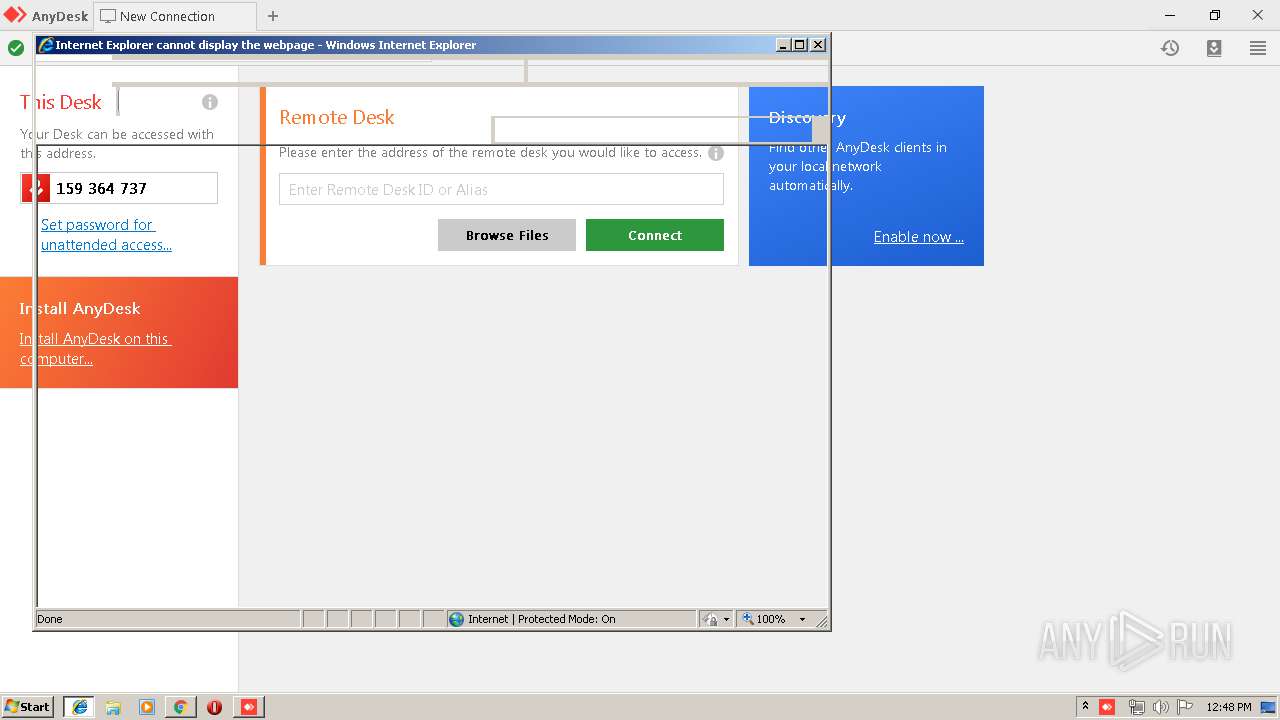
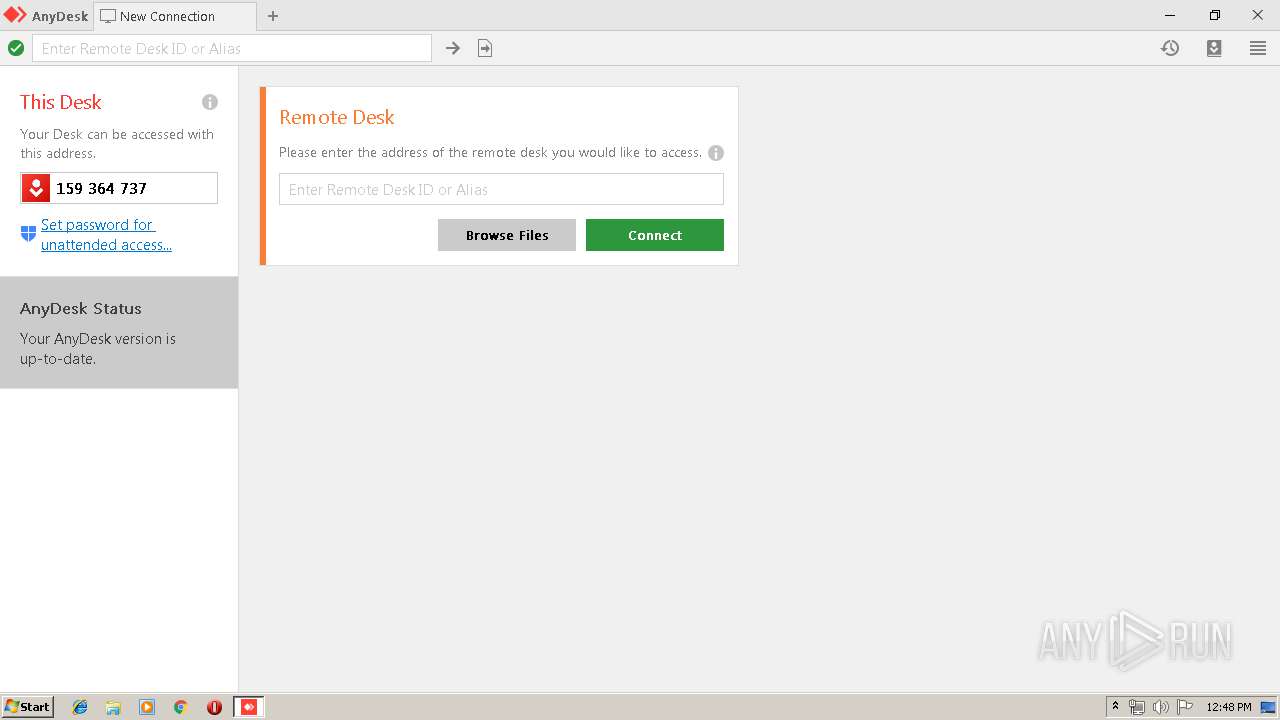
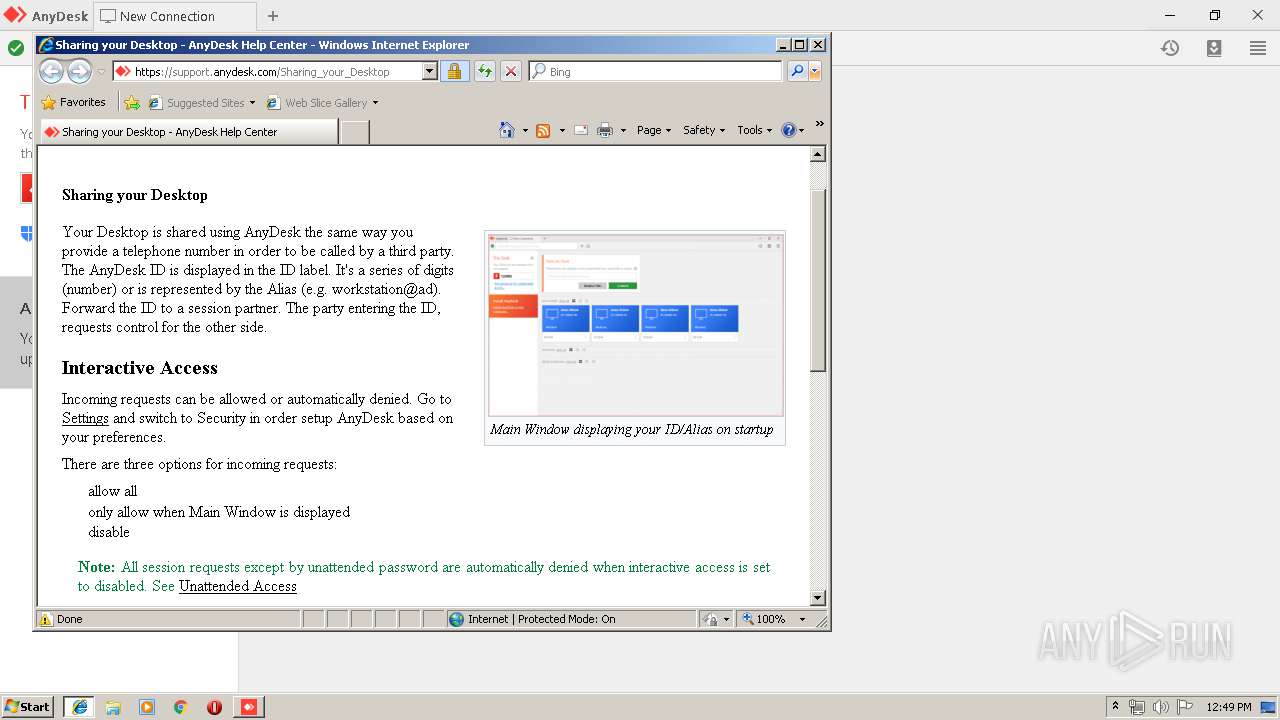
Starts Internet Explorer
- AnyDesk.exe (PID: 2268)
- AnyDesk.exe (PID: 2564)
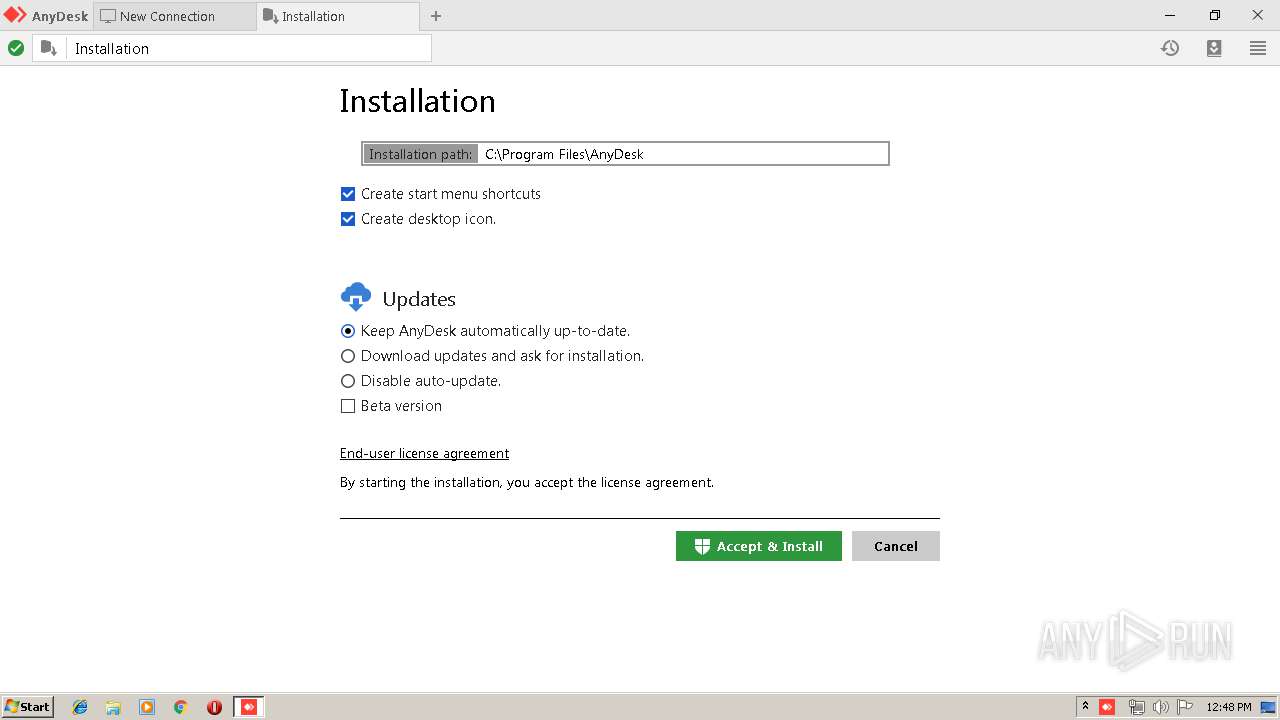
Executable content was dropped or overwritten
- AnyDesk.exe (PID: 3804)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3616)
Creates files in the user directory
- AnyDesk.exe (PID: 2268)
- AnyDesk.exe (PID: 2840)
- AnyDesk.exe (PID: 2564)
Application launched itself
- AnyDesk.exe (PID: 2268)
Cleans NTFS data-stream (Zone Identifier)
- AnyDesk.exe (PID: 2268)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2664)
Creates files in the program directory
- AnyDesk.exe (PID: 3804)
- AnyDesk.exe (PID: 4028)
Modifies the open verb of a shell class
- AnyDesk.exe (PID: 3804)
Creates a software uninstall entry
- AnyDesk.exe (PID: 3804)
- AnyDesk.exe (PID: 4028)
Searches for installed software
- AnyDesk.exe (PID: 2564)
- AnyDesk.exe (PID: 2592)
- AnyDesk.exe (PID: 4028)
INFO
Application launched itself
- chrome.exe (PID: 2664)
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 2336)
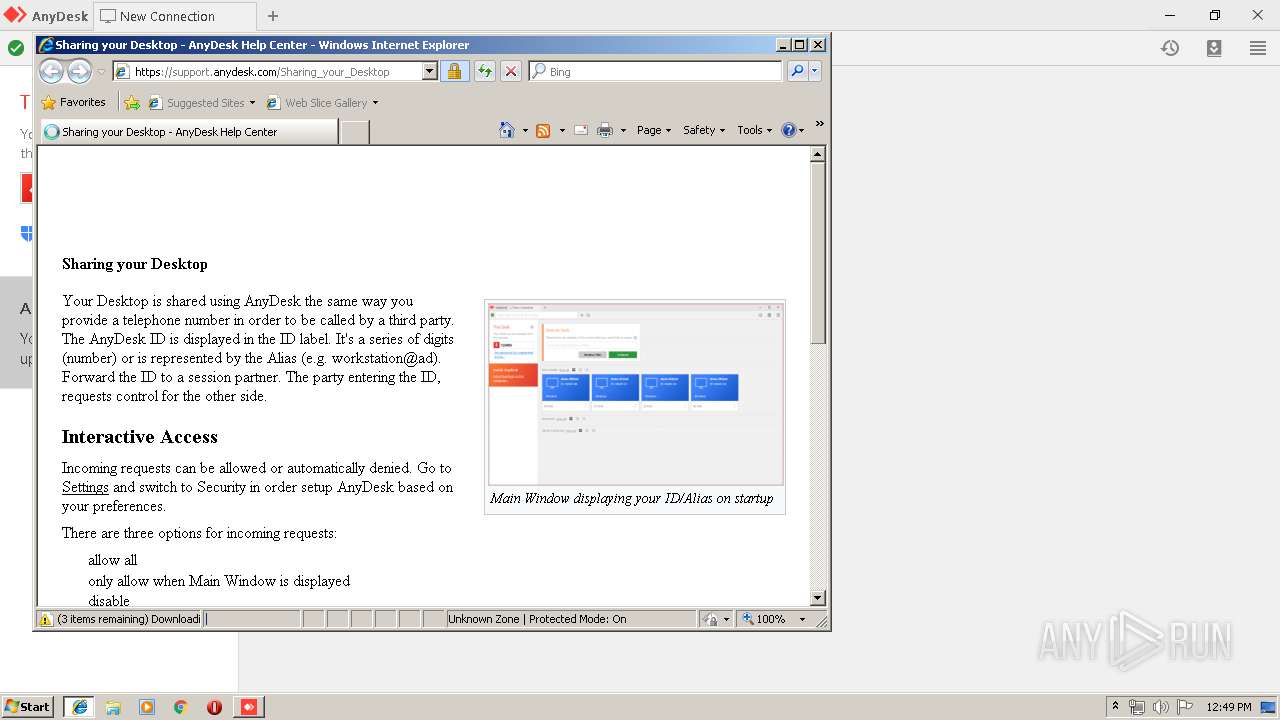
Reads internet explorer settings
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2812)
Creates files in the user directory
- iexplore.exe (PID: 2784)
Reads Internet Cache Settings
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2812)
Reads settings of System Certificates
- chrome.exe (PID: 2664)
- iexplore.exe (PID: 2336)
Changes internet zones settings
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 2336)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2336)
Changes settings of System certificates
- iexplore.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
28
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fae0f18,0x6fae0f28,0x6fae0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1592249978777797949 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\AnyDesk\AnyDesk.exe" --control | C:\Program Files\AnyDesk\AnyDesk.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\Downloads\AnyDesk.exe" | C:\Users\admin\Downloads\AnyDesk.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5355940544960453712 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AnyDesk.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --service-pipe-token=17744979654931415531 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17744979654931415531 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1666989524334067264 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1666989524334067264 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17318126125650744327 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,2091645225952162632,5100537583368141641,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8904799638623136323 --mojo-platform-channel-handle=3200 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 464
Read events
2 231
Write events
223
Delete events
10
Modification events
| (PID) Process: | (3304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2664-13199370448148125 |
Value: 259 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
7
Suspicious files
54
Text files
237
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\32eea809-c62d-43fe-bb9d-b87356e5896e.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
52
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3616 | chrome.exe | GET | — | 176.9.65.111:80 | http://boot-02.net.anydesk.com/ | DE | — | — | suspicious |
3616 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3616 | chrome.exe | GET | 200 | 176.126.58.208:80 | http://r5---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=31.204.150.72&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1554896789&mv=m&pcm2cms=yes&pl=22&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
2336 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2784 | iexplore.exe | GET | 301 | 13.35.253.101:80 | http://anydesk.com/order | US | html | 183 b | whitelisted |
2812 | iexplore.exe | GET | 301 | 188.40.104.135:80 | http://help.anydesk.com/share | DE | html | 178 b | suspicious |
2800 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3616 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 176.9.65.111:80 | boot-02.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3616 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 13.35.253.70:443 | anydesk.com | — | US | suspicious |
3616 | chrome.exe | 209.197.3.15:443 | stackpath.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3616 | chrome.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3616 | chrome.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3616 | chrome.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3616 | chrome.exe | 172.217.16.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
boot-02.net.anydesk.com |
| suspicious |
accounts.google.com |
| shared |
anydesk.com |
| whitelisted |
code.jquery.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2812 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |