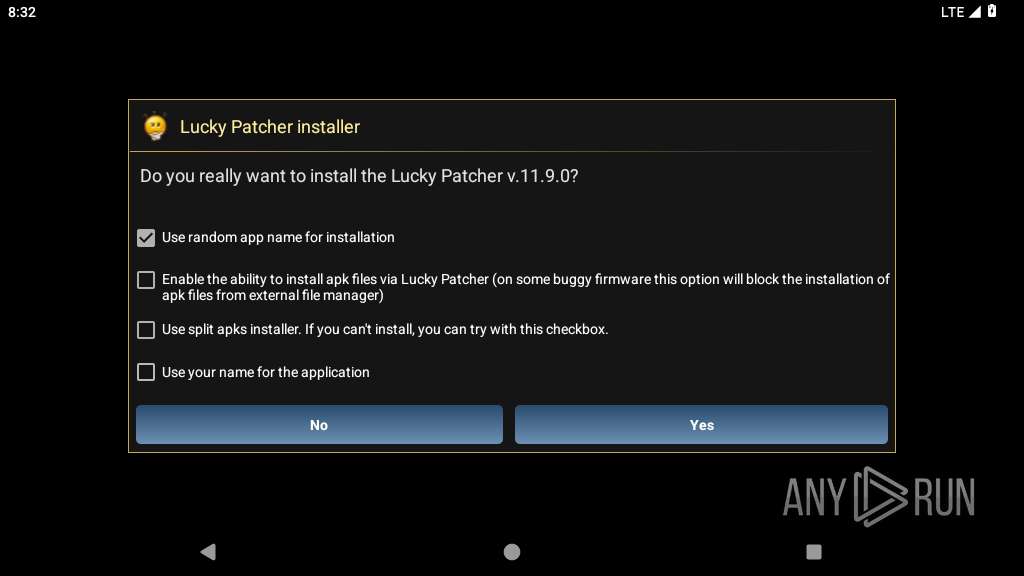
| File name: | LuckyPatchers.com_Official_Installer_11.9.0.apk |
| Full analysis: | https://app.any.run/tasks/e7403123-b22b-4ef2-a884-84c4b50b5cf2 |
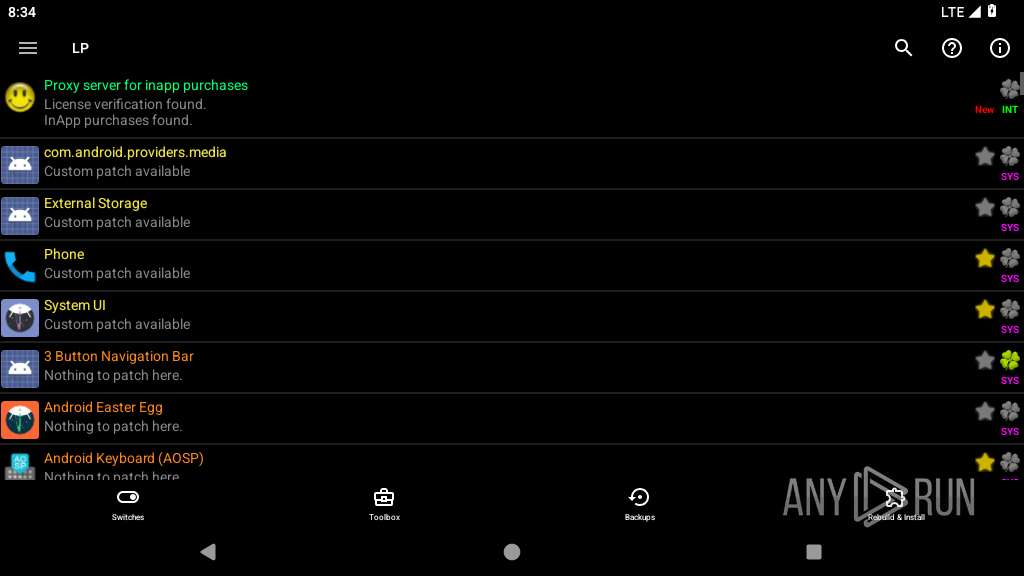
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2025, 20:31:53 |
| OS: | Android 14 |
| Tags: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with zipflinger virtual entry |
| MD5: | A50C46928E8C280F28E239E561171FFE |
| SHA1: | CEFF6EC022A4A76C46A1A7C8860F8C49E9656FDB |
| SHA256: | 4072150D090308F019FFEBFF8A718D631618B4366FF3D928C100A8645608F9A0 |
| SSDEEP: | 98304:azQ2P4gjPJMRvoB6aVTmNS8ffDW894+Szh0MdRQyk0WcEbDEOiyLFlHX9ZiAaNNs:0/GcPbgzsMG+1 |
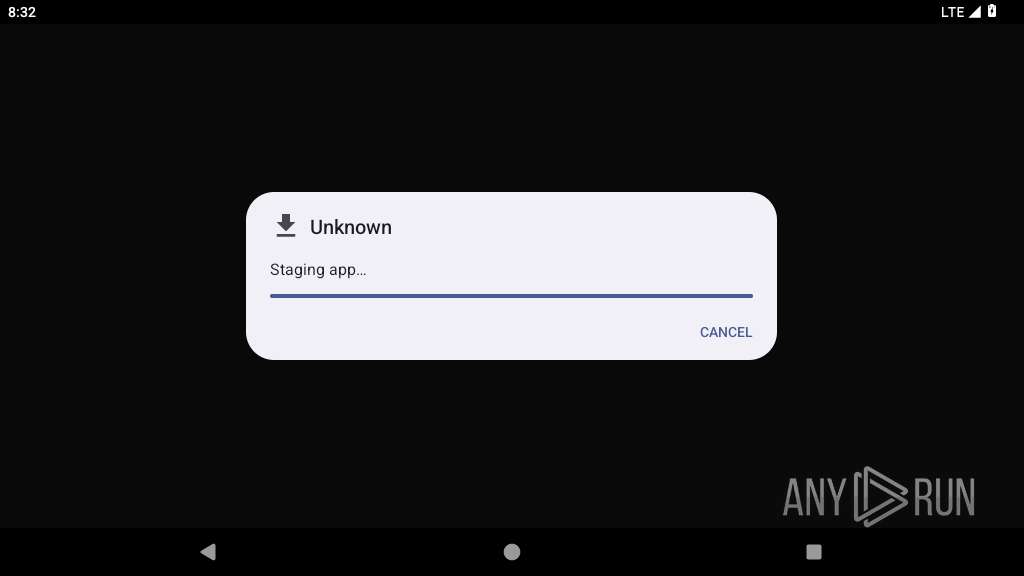
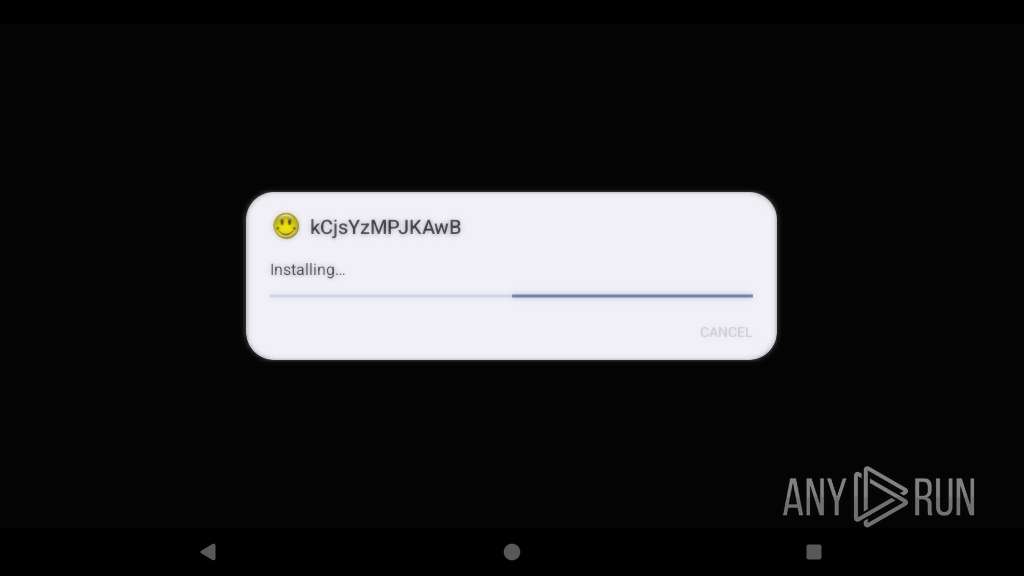
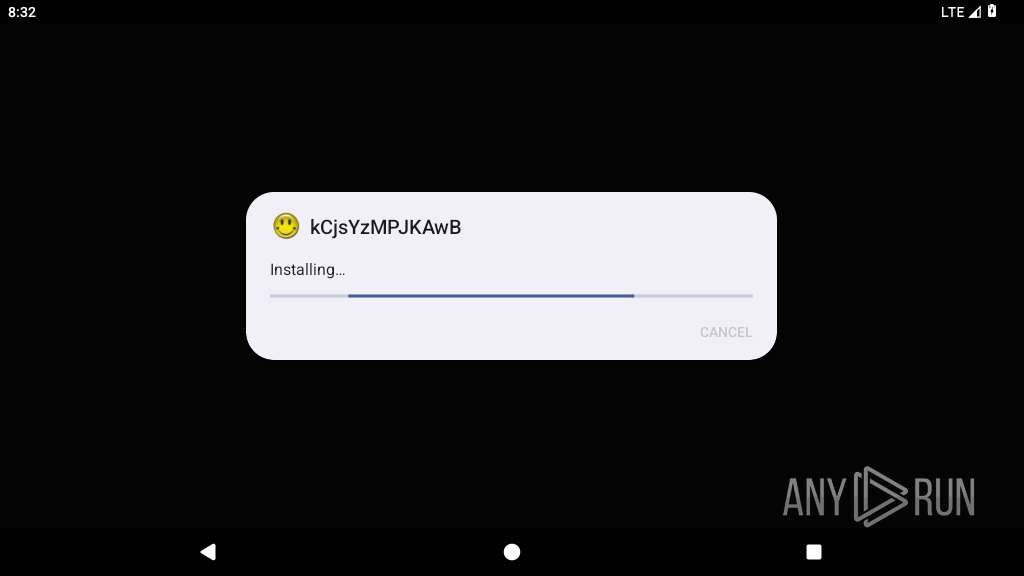
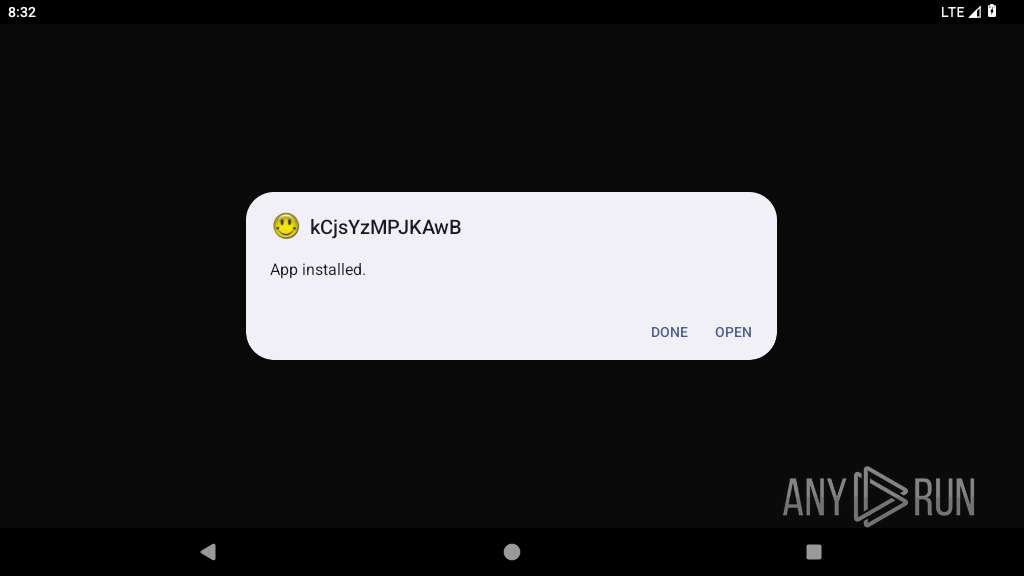
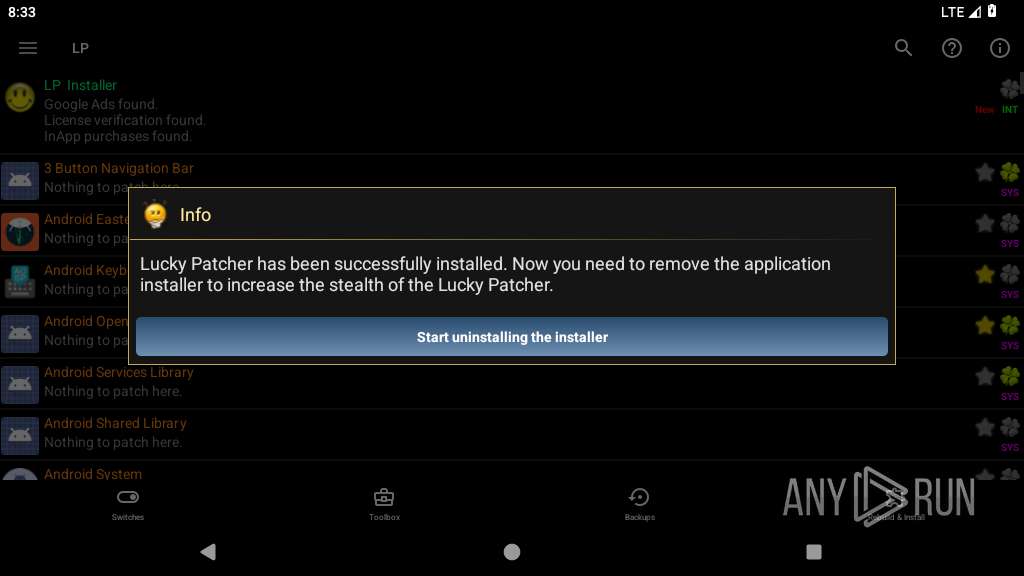
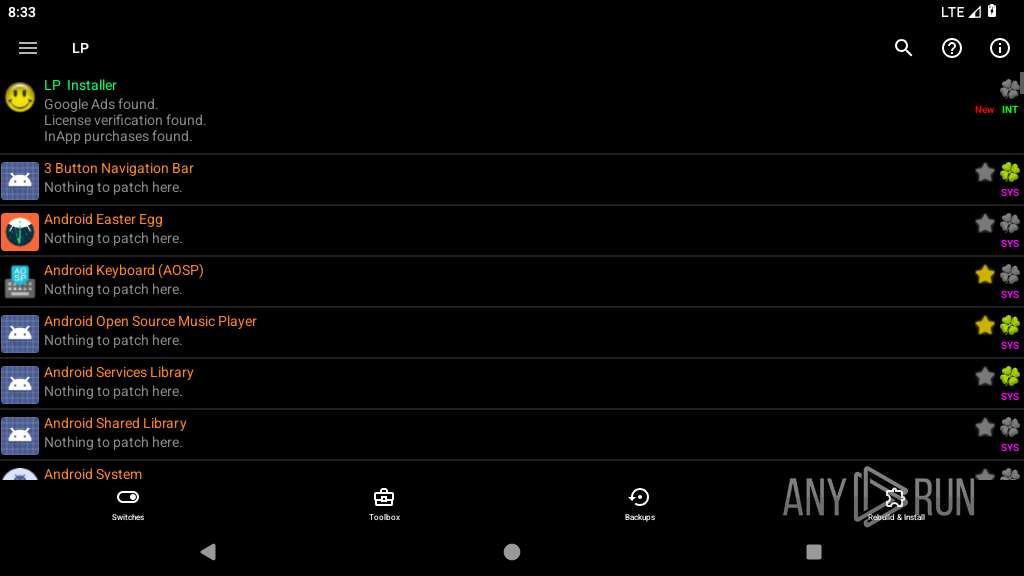
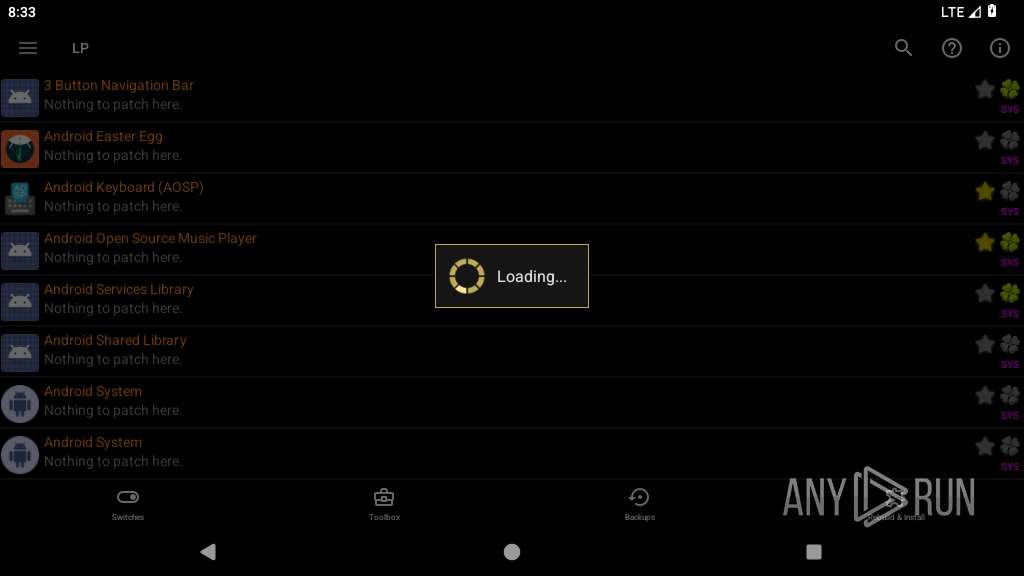
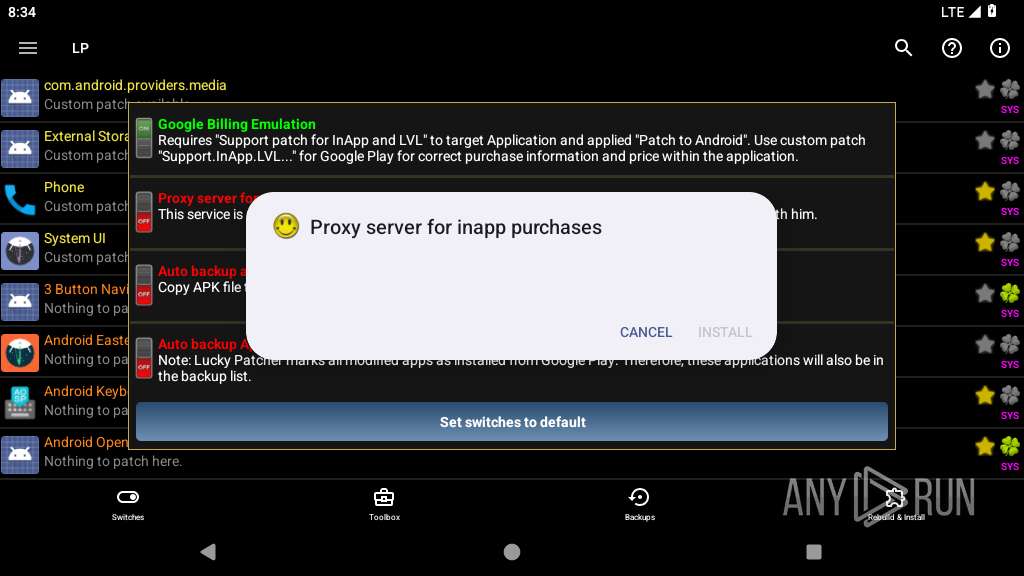
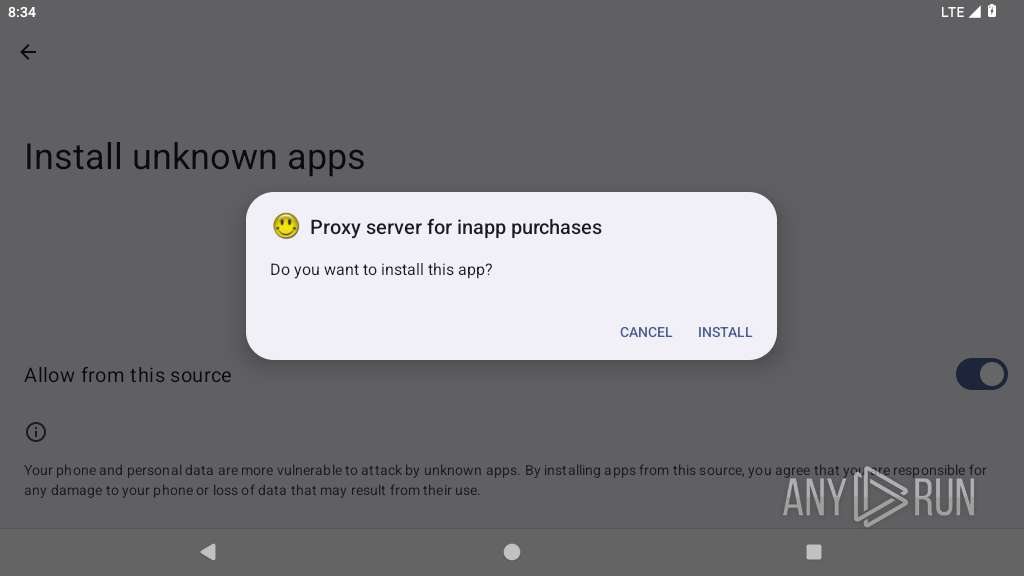
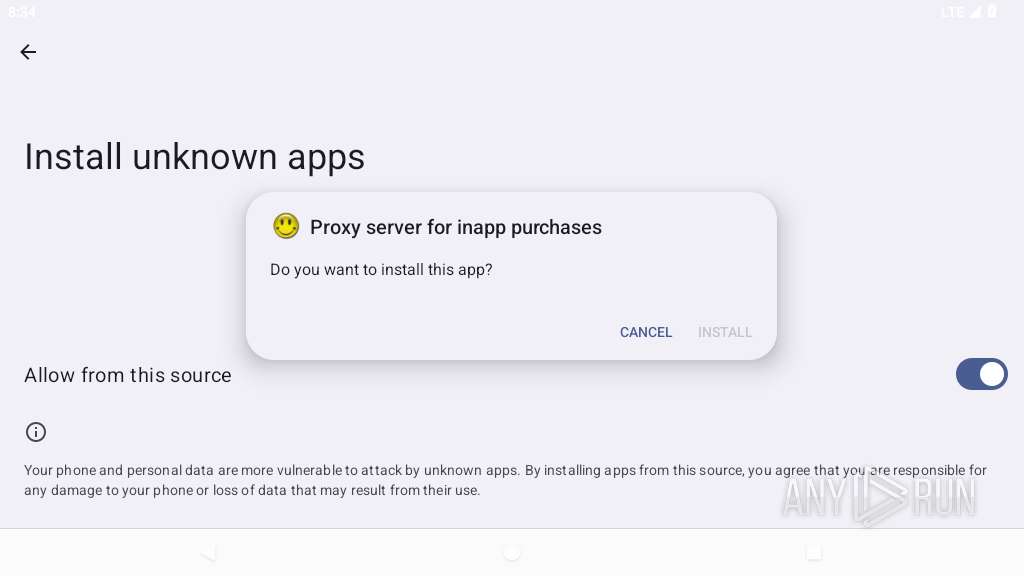
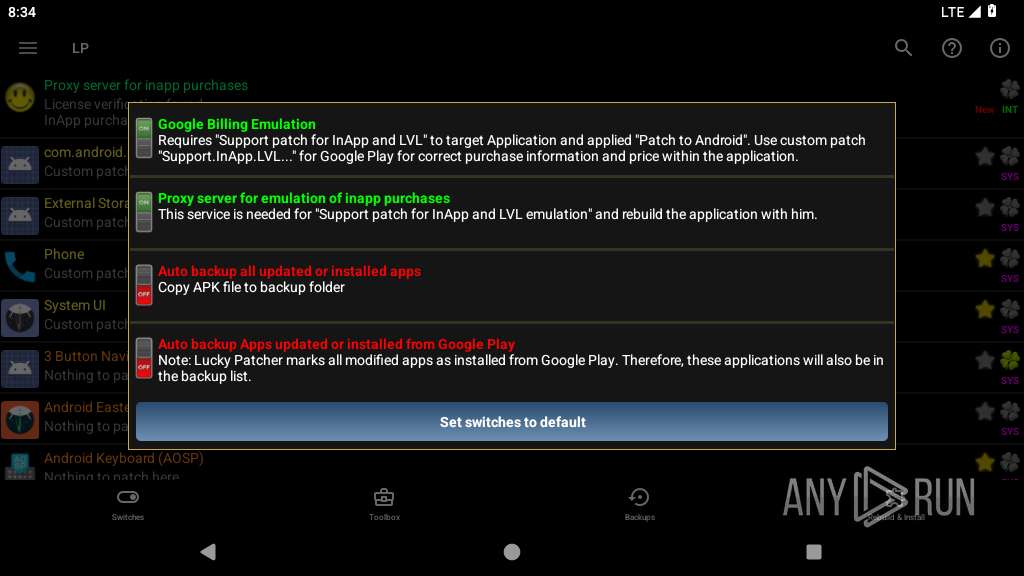
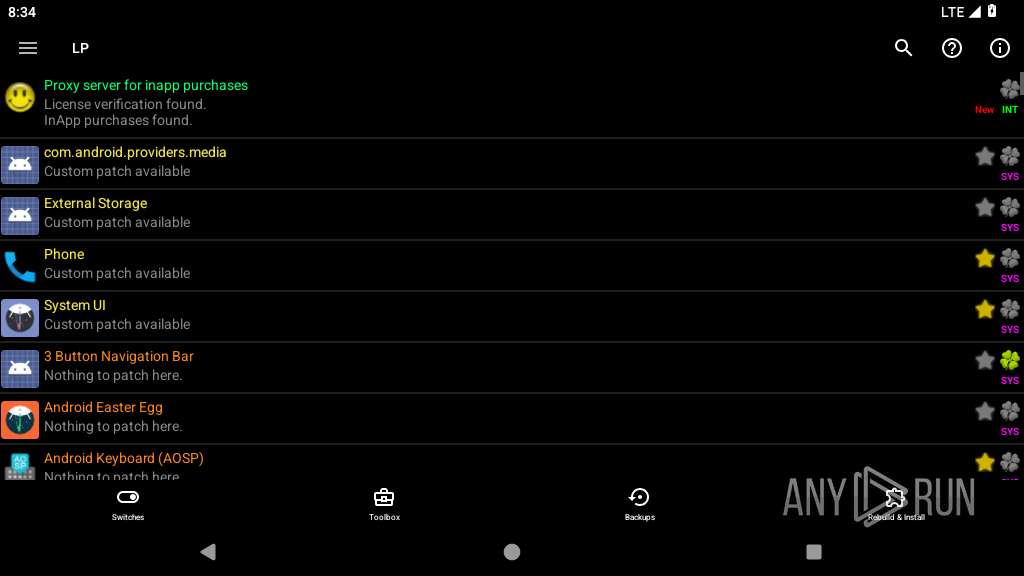
MALICIOUS
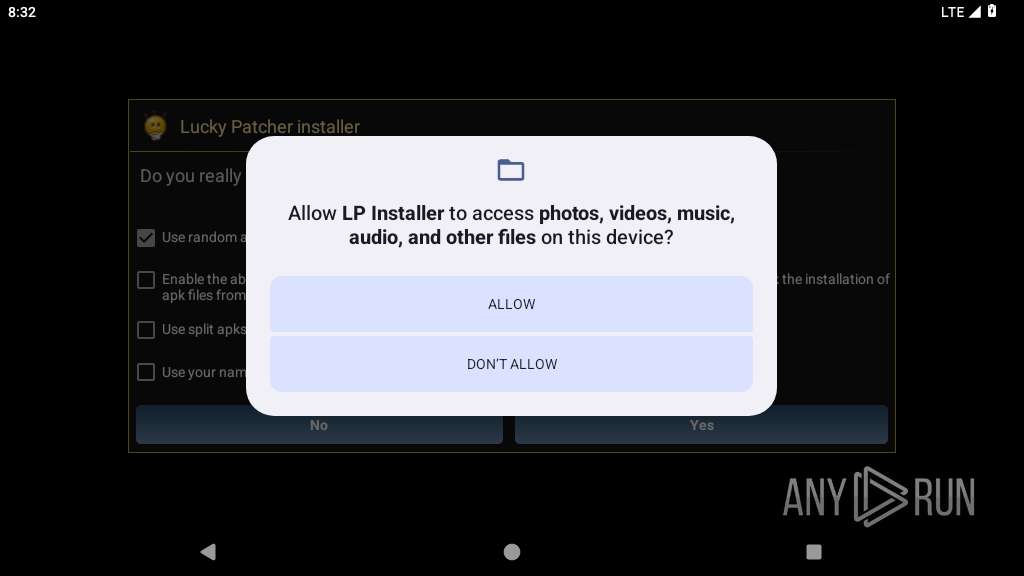
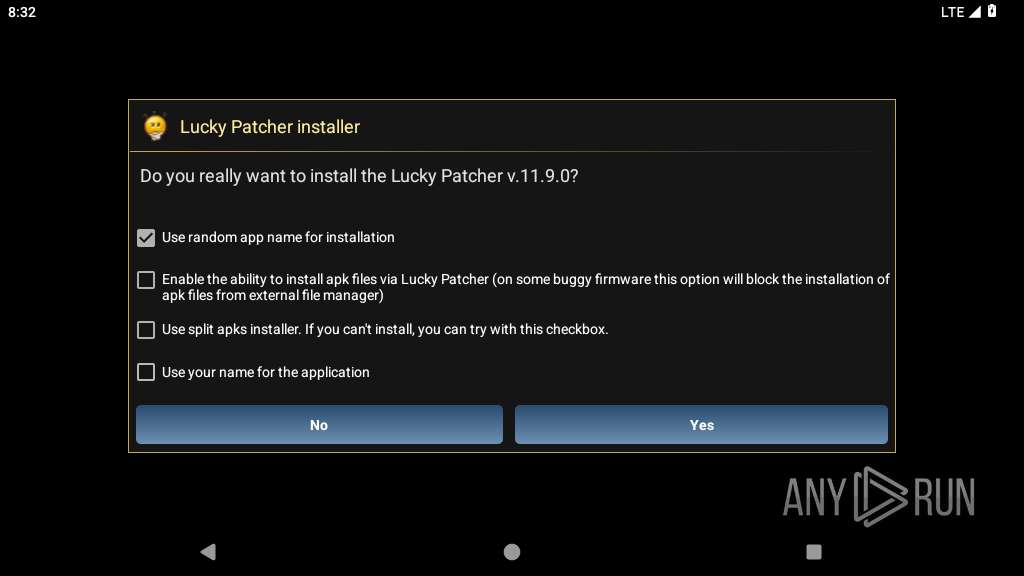
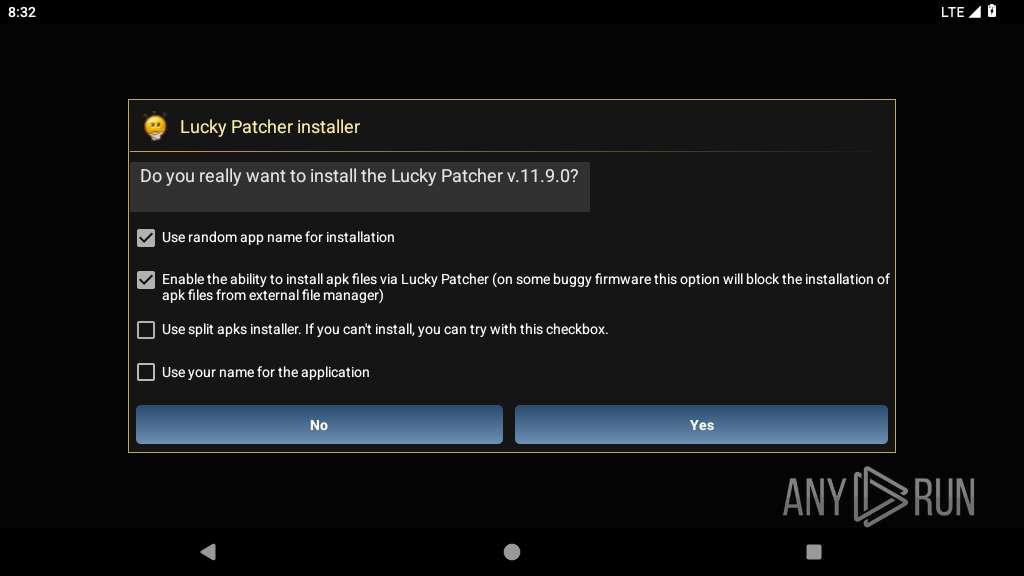
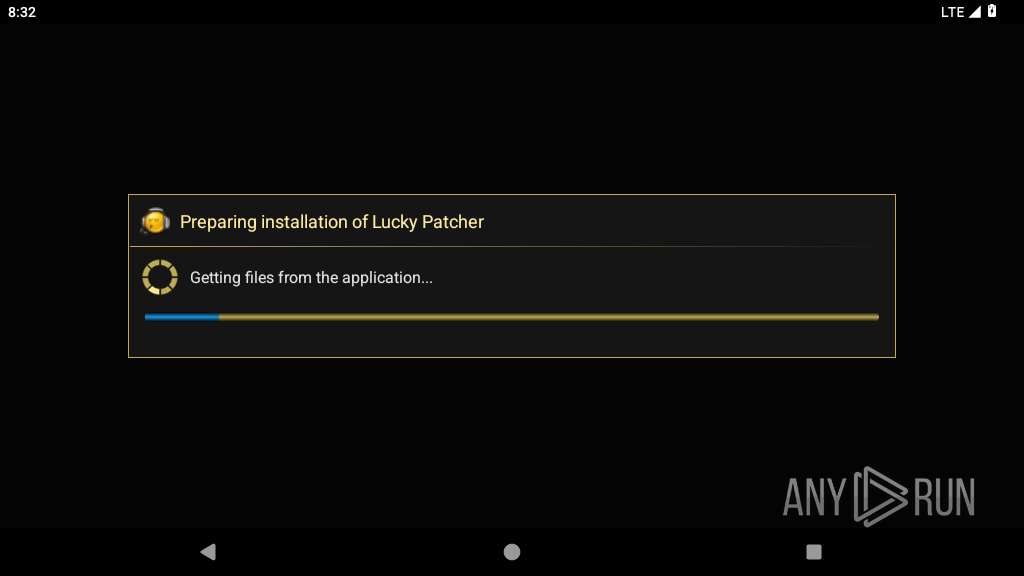
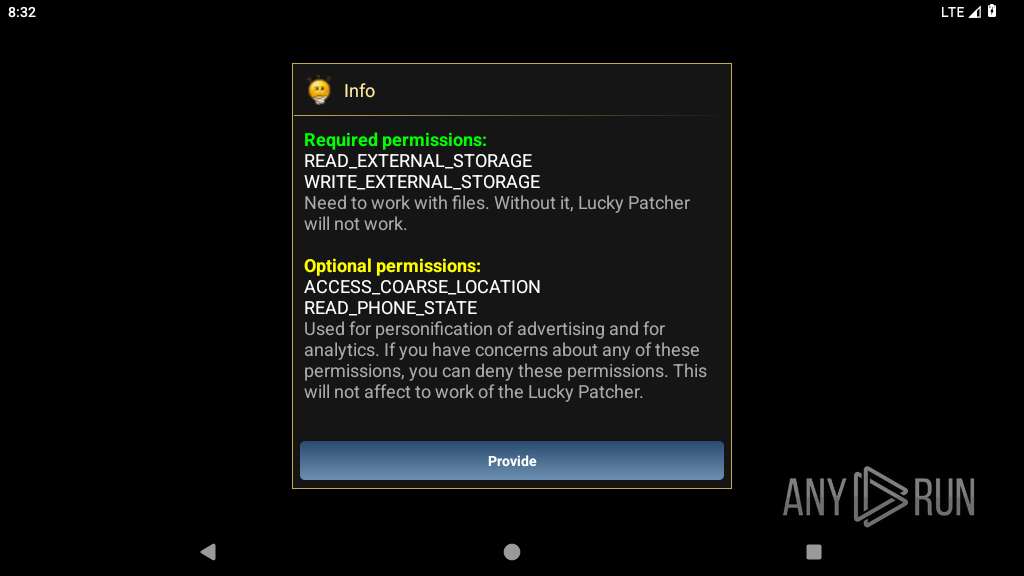
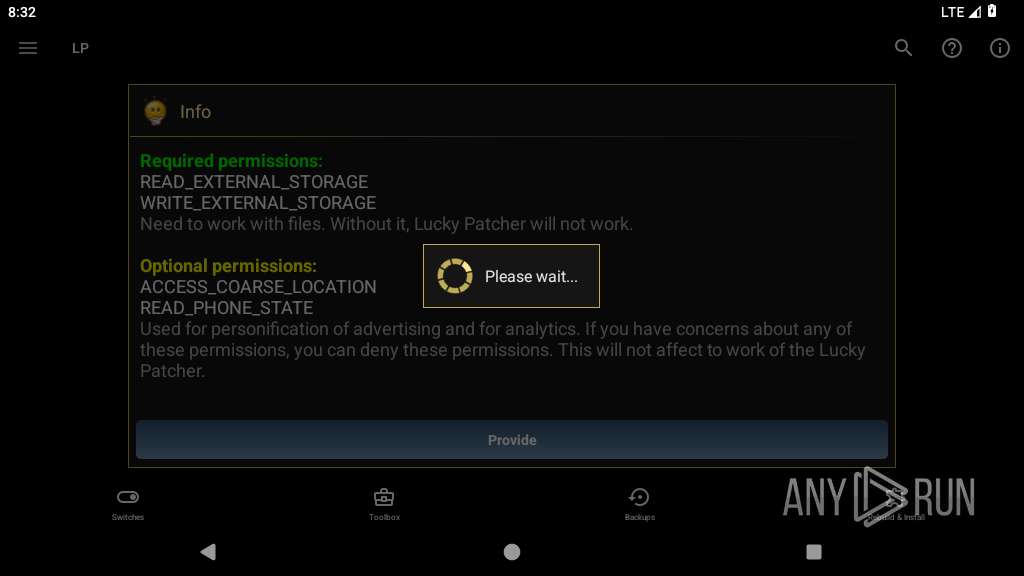
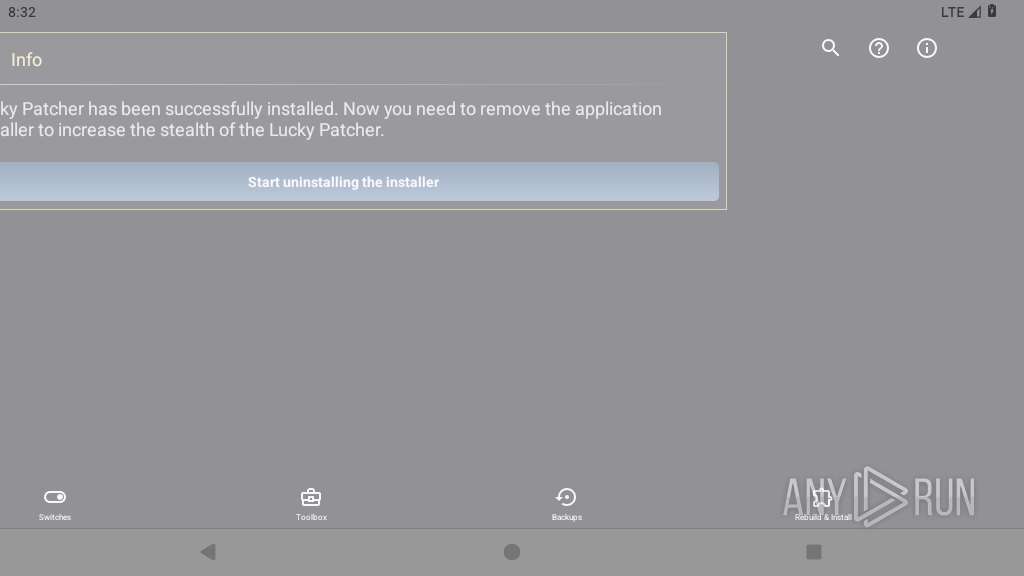
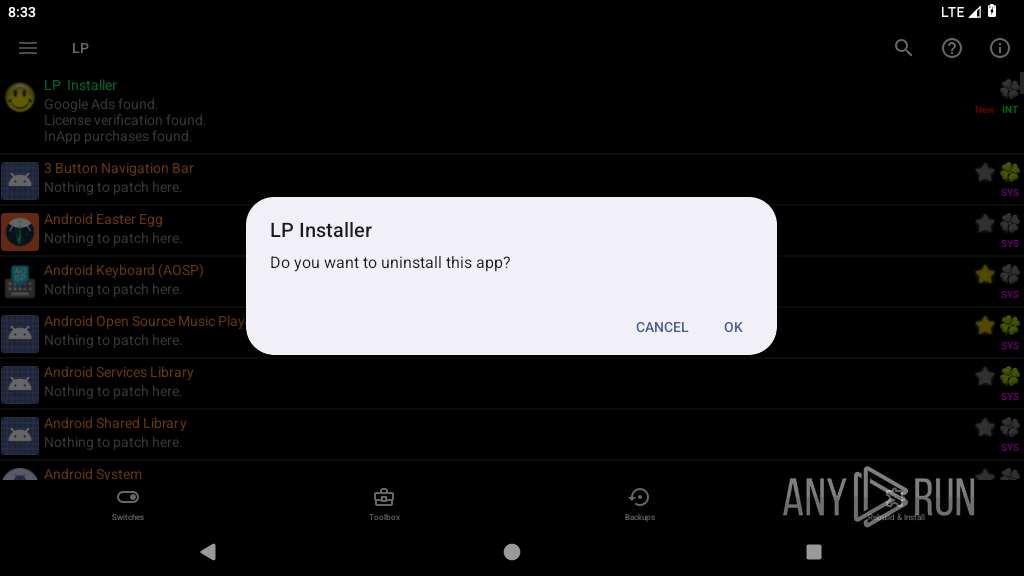
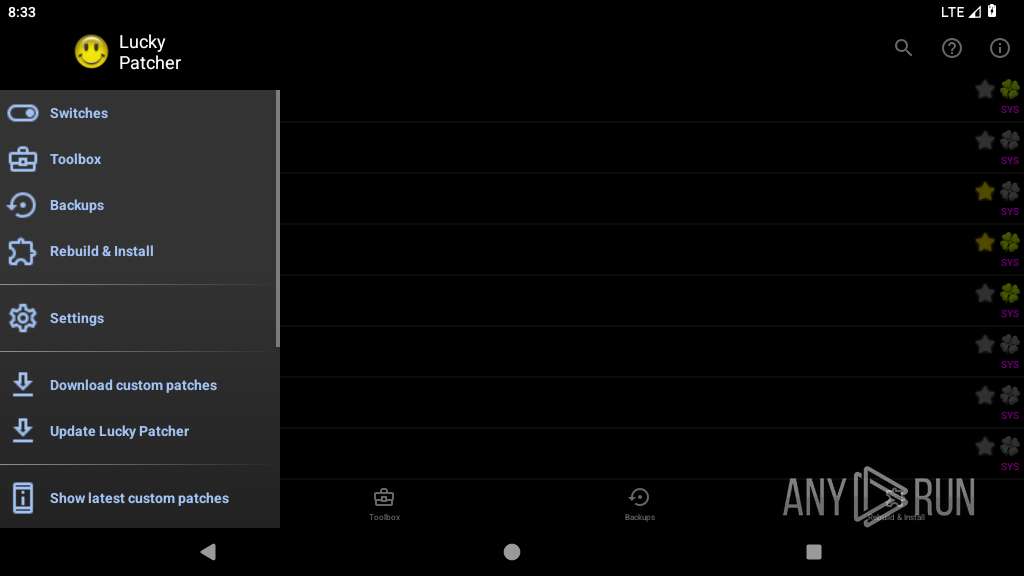
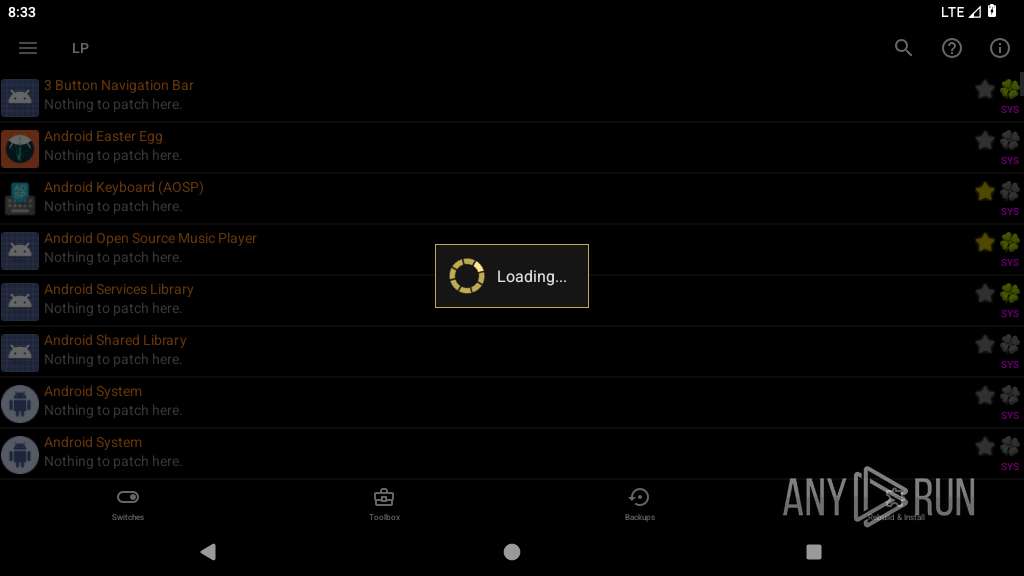
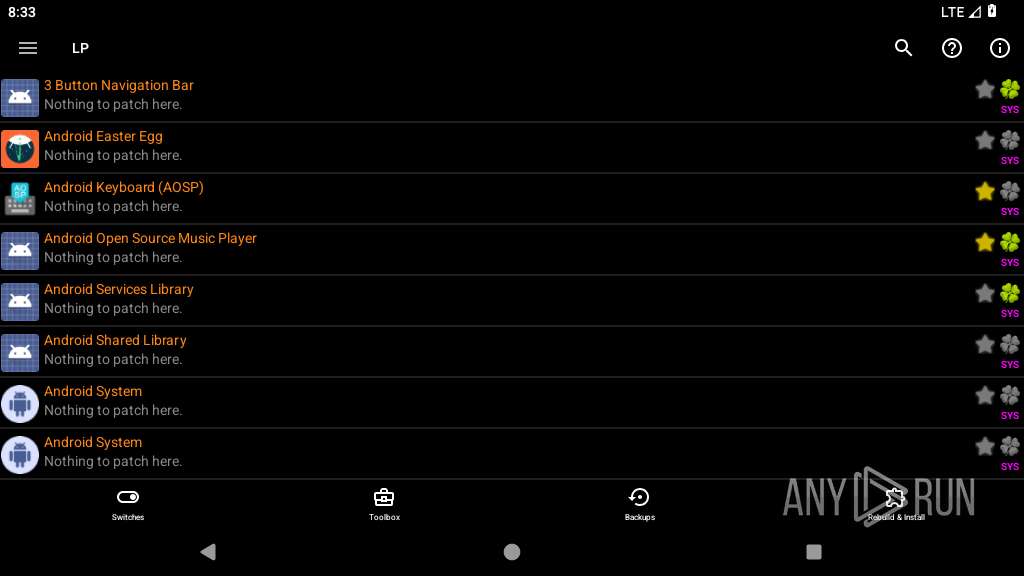
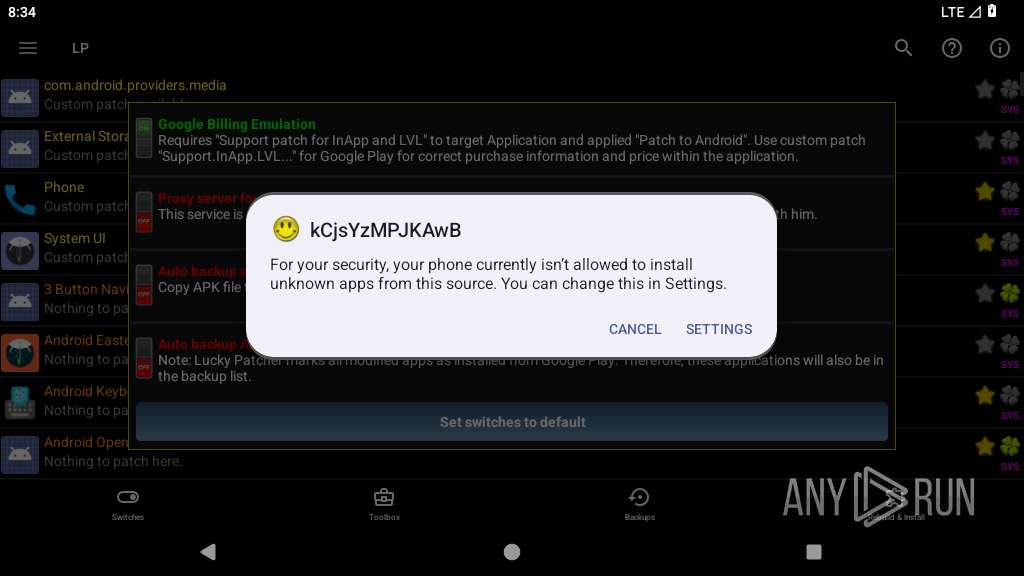
Requests APK Installation via system installer
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Detects root access on device
- app_process64 (PID: 2448)
SUSPICIOUS
Retrieves the file path to the APK
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2258)
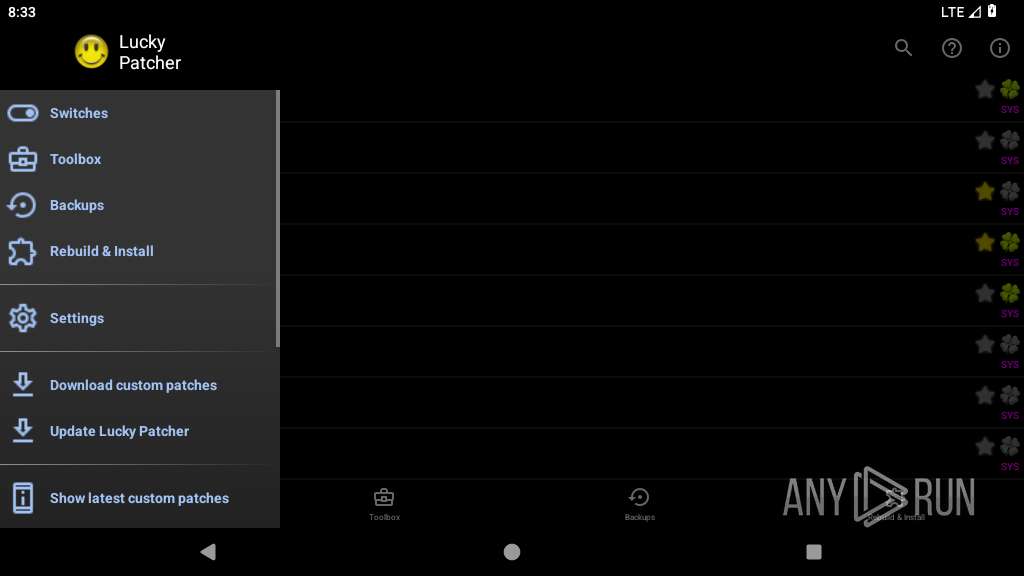
Accesses system-level resources
- app_process64 (PID: 2258)
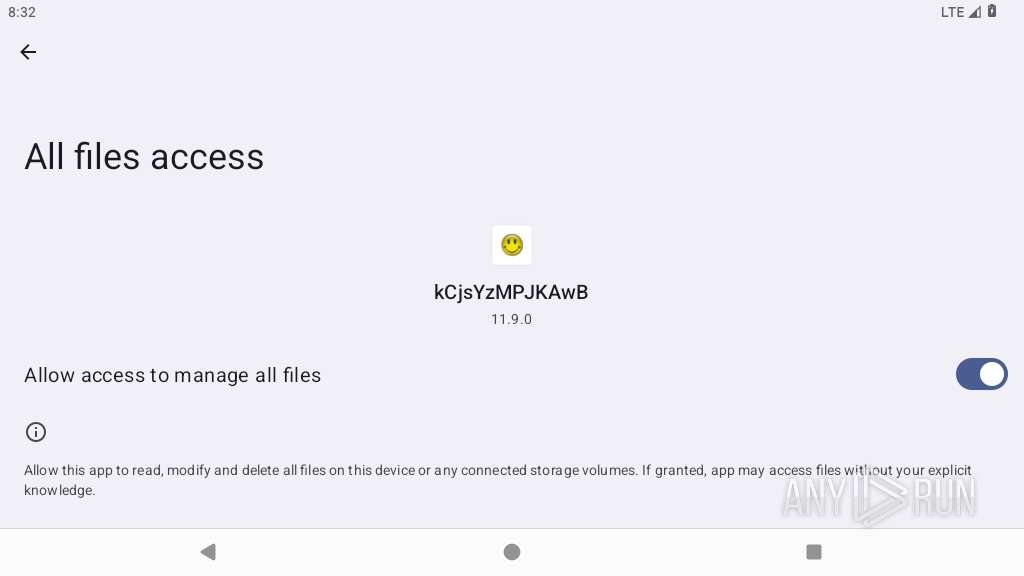
Accesses external device storage files
- app_process64 (PID: 2448)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
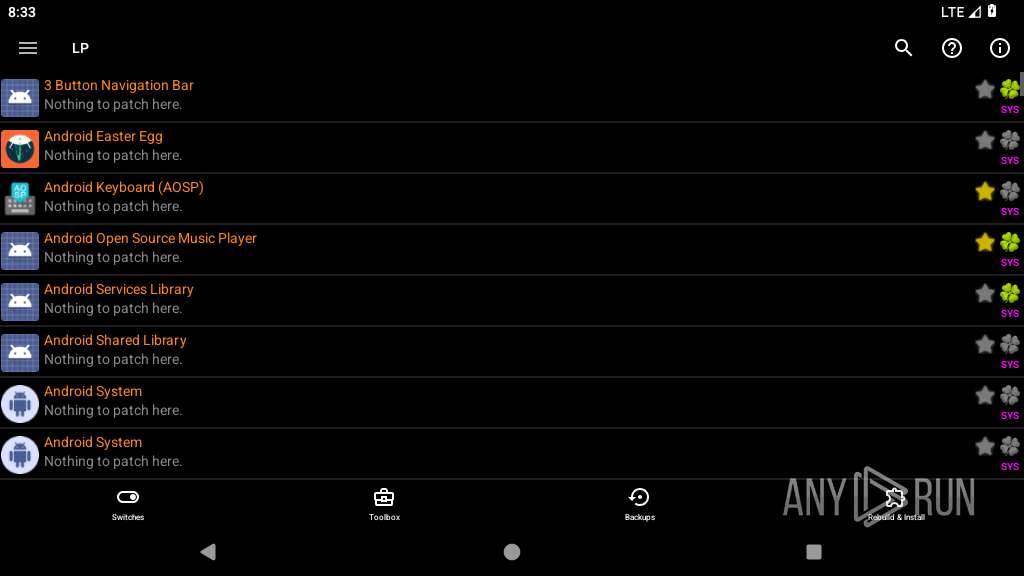
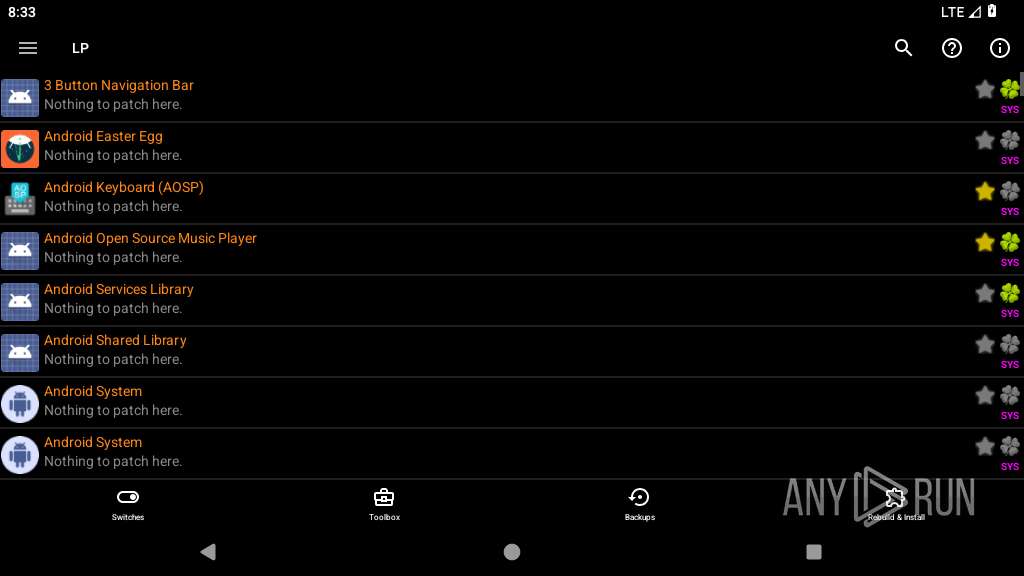
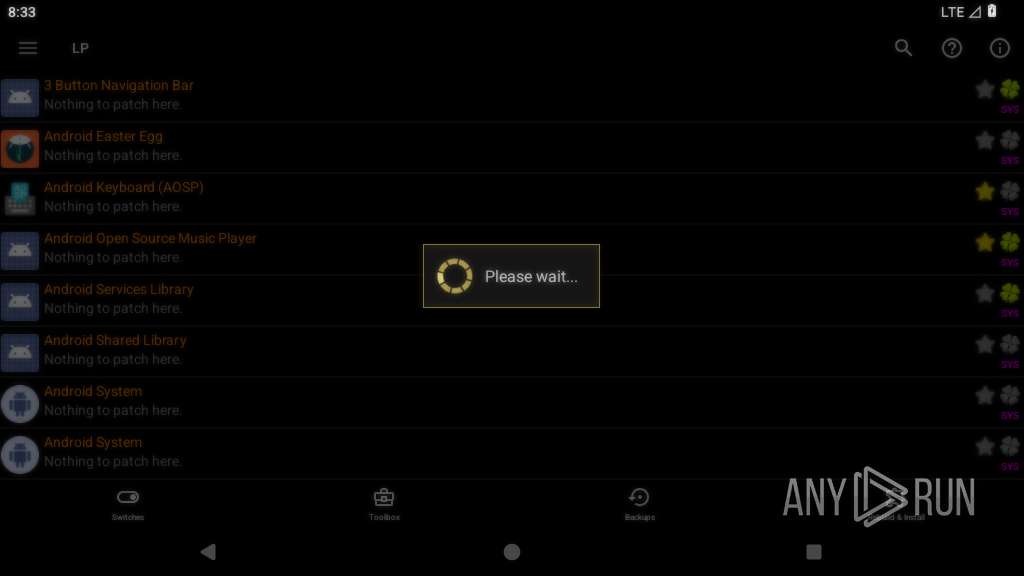
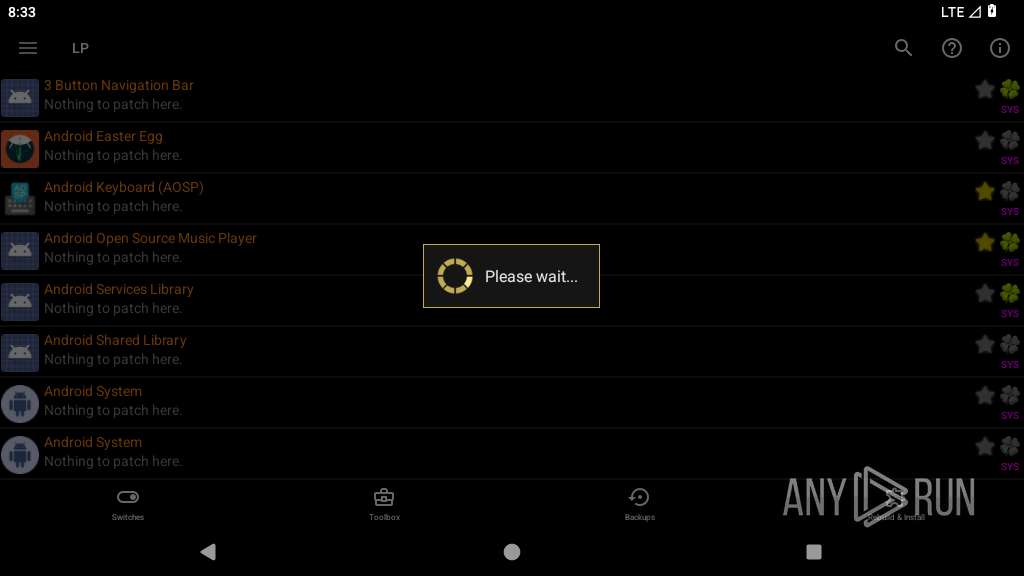
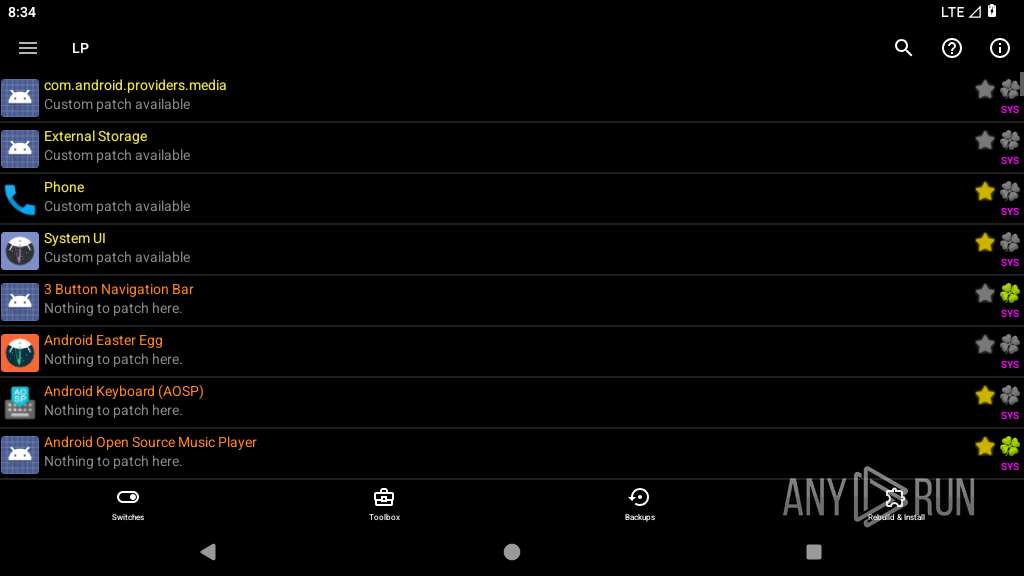
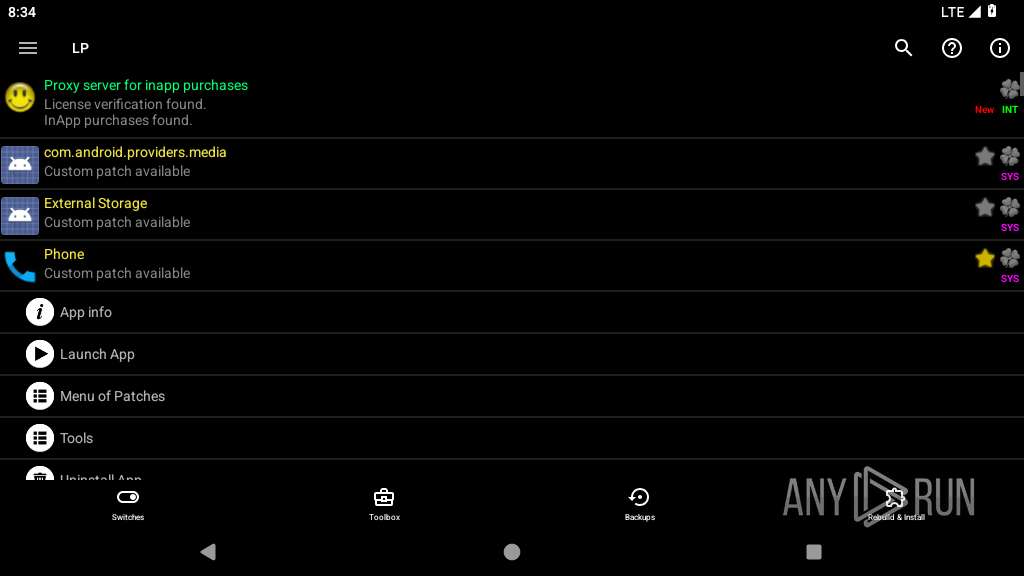
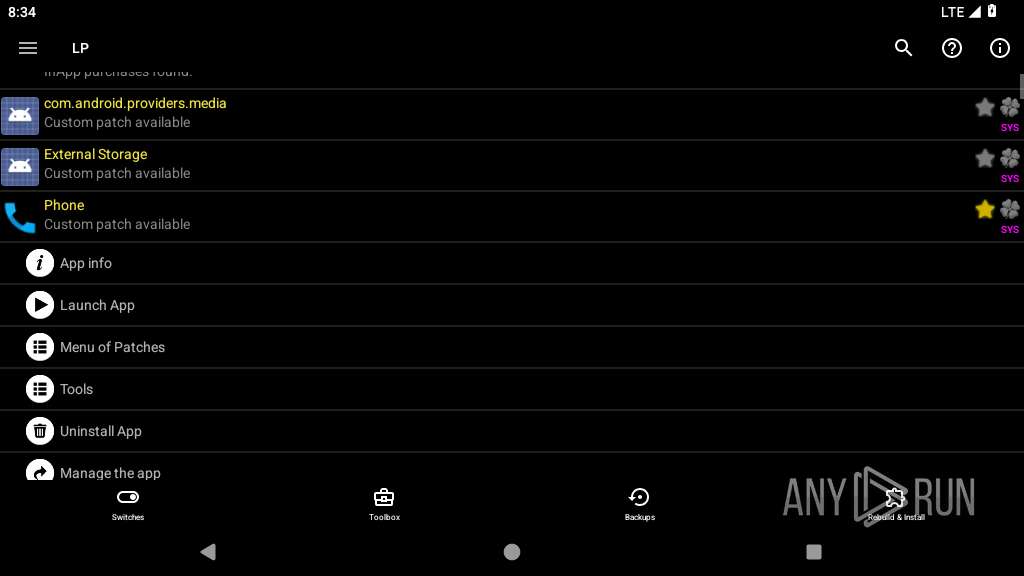
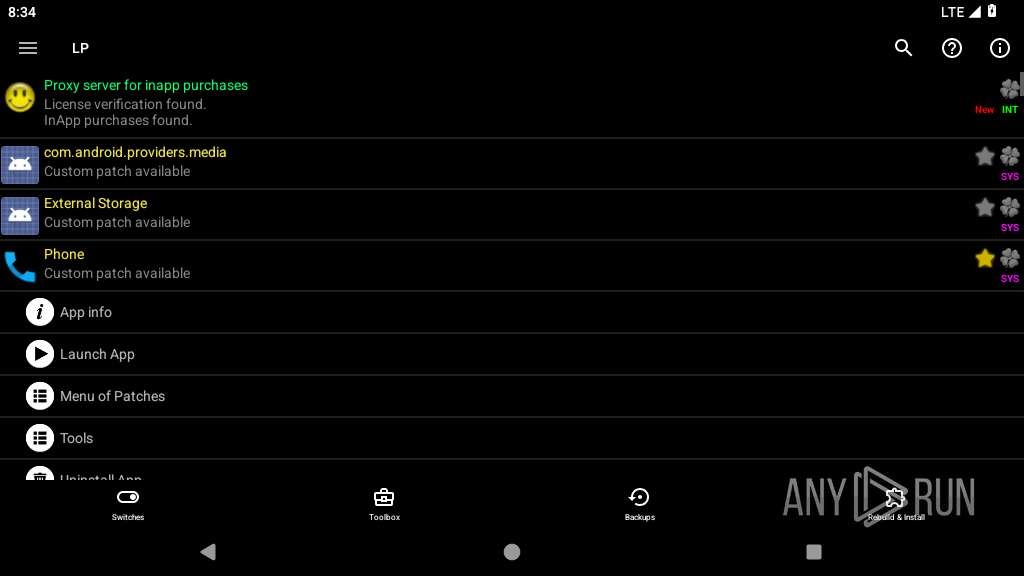
Retrieves installed applications on device
- app_process64 (PID: 2448)
Detects uninstallation of applications
- app_process64 (PID: 2448)
Launches a new activity
- app_process64 (PID: 2448)
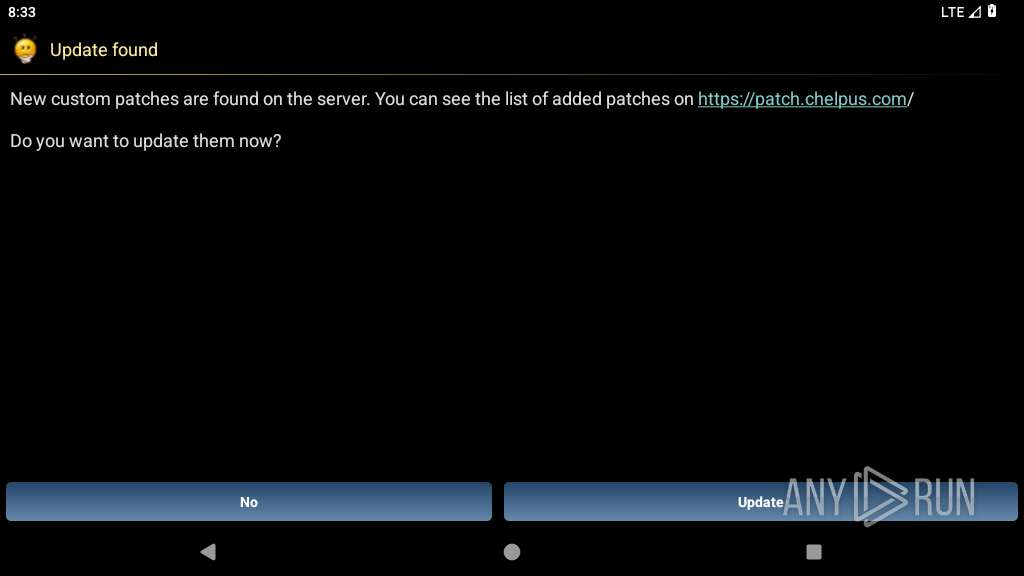
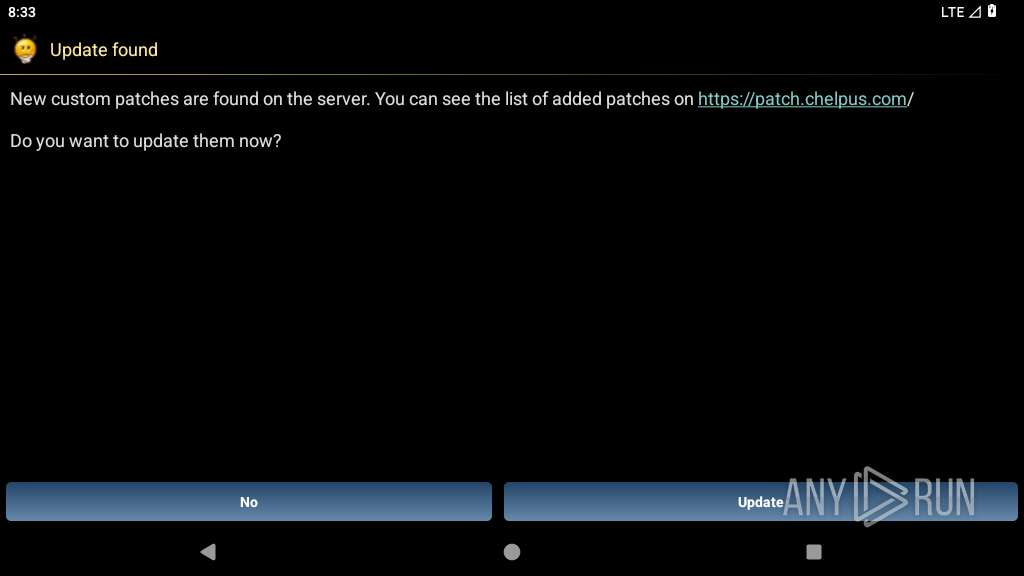
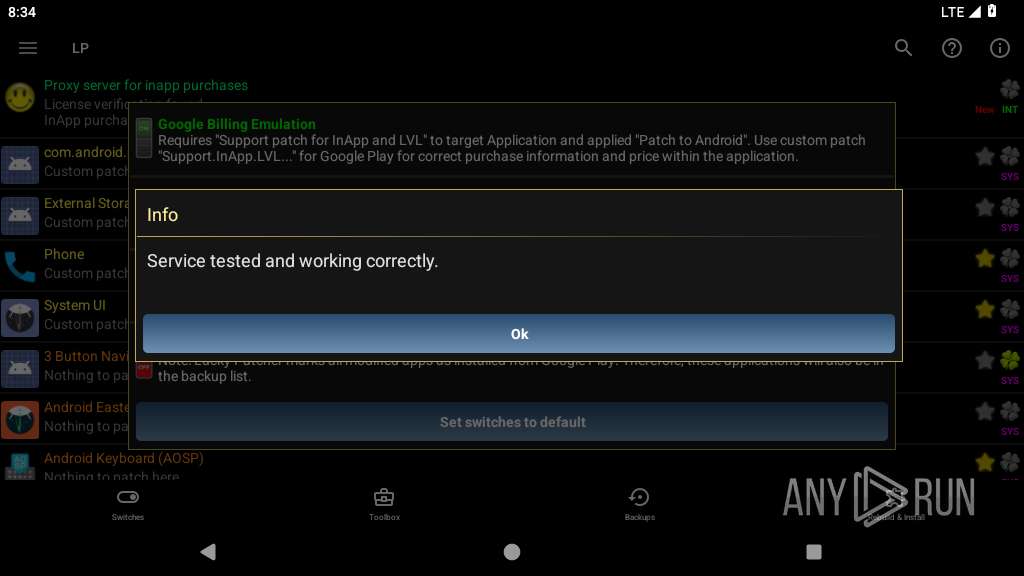
Establishing a connection
- app_process64 (PID: 2448)
Scans for installed antivirus apps
- app_process64 (PID: 2448)
Scans for popular installed apps
- app_process64 (PID: 2448)
INFO
Gets file name without full path
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2448)
- app_process64 (PID: 2258)
Stores data using SQLite database
- app_process64 (PID: 2258)
- app_process64 (PID: 2448)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2448)
Retrieves the value of a global system setting
- app_process64 (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (48.1) |
|---|---|---|
| .spe | | | SPSS Extension (27.5) |
| .jar | | | Java Archive (13.3) |
| .xpi | | | Mozilla Firefox browser extension (7.3) |
| .zip | | | ZIP compressed archive (3.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xd1f06b7f |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
136
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2258 | ru.aaaaaccw.installer | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2429 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2432 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~StshejhmLykhOJP4AYsGug==/ru.ioosqwtl.ztkfdwfni-foiLGsxuYb-AOM5Uml2xDQ==/base.apk --oat-fd=7 --oat-location=/data/app/~~StshejhmLykhOJP4AYsGug==/ru.ioosqwtl.ztkfdwfni-foiLGsxuYb-AOM5Uml2xDQ==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context-fds=10 --class-loader-context=PCL[]{PCL[/system/framework/android.test.base.jar]} --classpath-dir=/data/app/~~StshejhmLykhOJP4AYsGug==/ru.ioosqwtl.ztkfdwfni-foiLGsxuYb-AOM5Uml2xDQ== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:28 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:11.9.0,app-version-code:1950,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2448 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2546 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2557 | com.android.documentsui | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2632 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2634 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2697 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2701 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~M98umtJNY0m67vStod1zrw==/com.android.vending.billing.InAppBillingService.BINN-pCH8Li9hjYhlW9S3tawpYQ==/base.apk --oat-fd=7 --oat-location=/data/app/~~M98umtJNY0m67vStod1zrw==/com.android.vending.billing.InAppBillingService.BINN-pCH8Li9hjYhlW9S3tawpYQ==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context=PCL[] --classpath-dir=/data/app/~~M98umtJNY0m67vStod1zrw==/com.android.vending.billing.InAppBillingService.BINN-pCH8Li9hjYhlW9S3tawpYQ== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:33 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:1.0.6,app-version-code:1536,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
179
Text files
927
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2258 | app_process64 | /data/user/0/ru.aaaaaccw.installer/shared_prefs/config.xml | xml | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/AdsBlockList_user_edit.txt | ini | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/AdsBlockList.txt | ini | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /data/user/0/ru.aaaaaccw.installer/shared_prefs/ru.aaaaaccw.installer_preferences.xml | xml | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /data/user/0/ru.aaaaaccw.installer/cache/oat_primary/arm64/base.2258.tmp | binary | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/Modified/tmp/AndroidManifest.xml | dbf | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/Modified/Keys/testkey.pk8 | der | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/Modified/Keys/testkey.sbt | cat | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/Modified/Keys/testkey.x509.pem | text | |
MD5:— | SHA256:— | |||
| 2258 | app_process64 | /storage/emulated/0/Android/data/ru.aaaaaccw.installer/files/LuckyPatcher/Modified/tmp/install.apk.temp_for_add | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
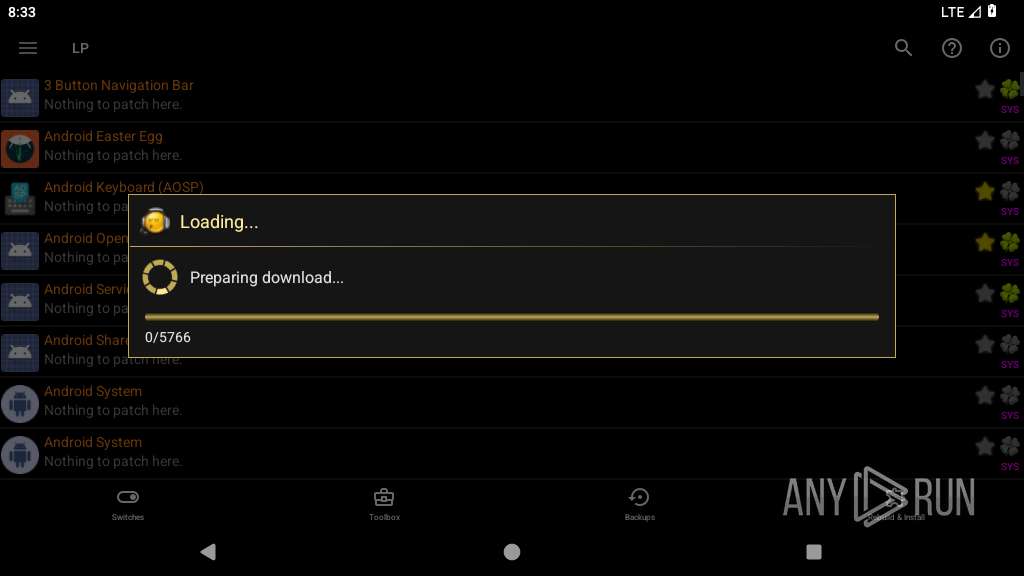
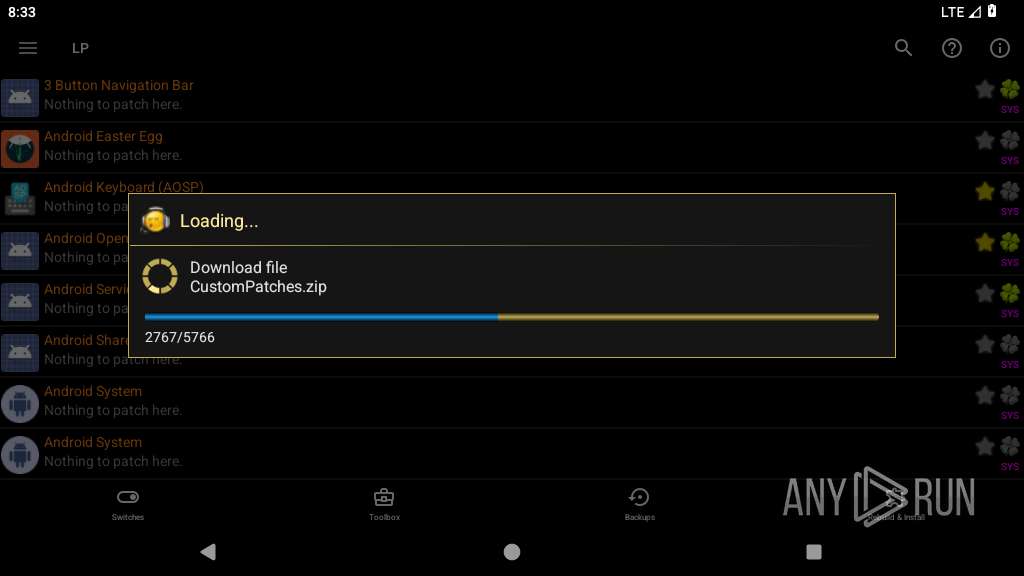
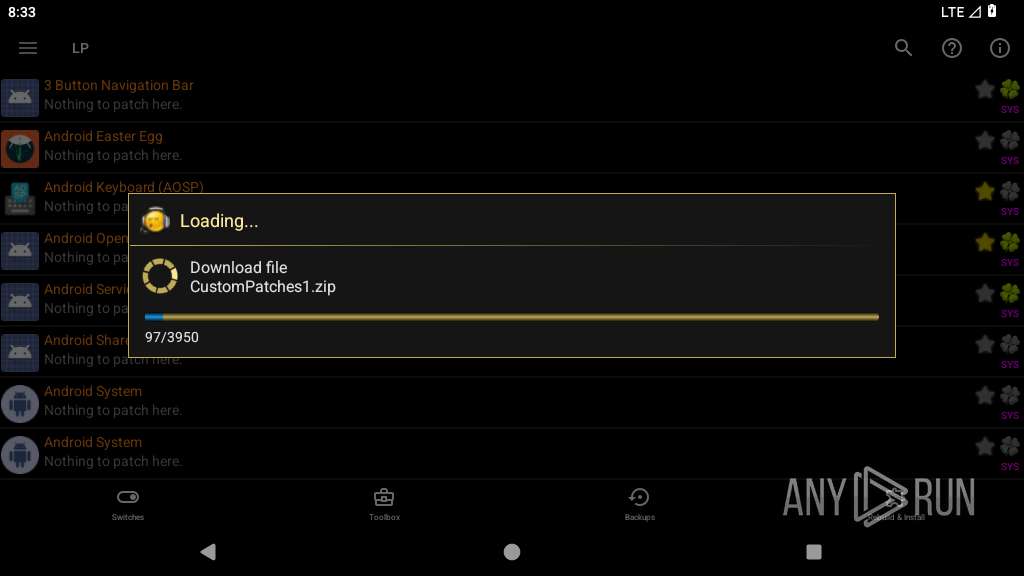
HTTP(S) requests
5
TCP/UDP connections
33
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.208.195:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
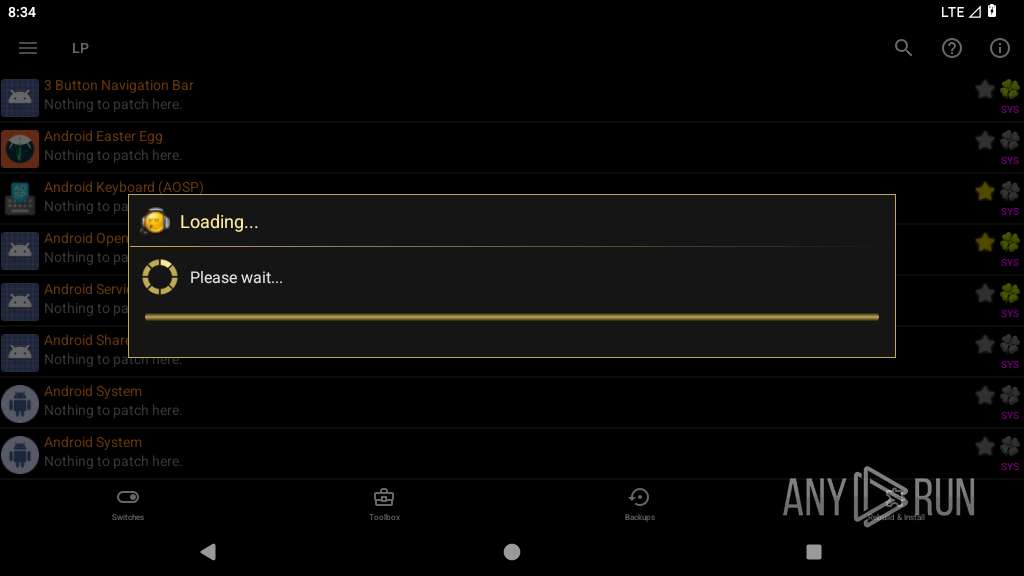
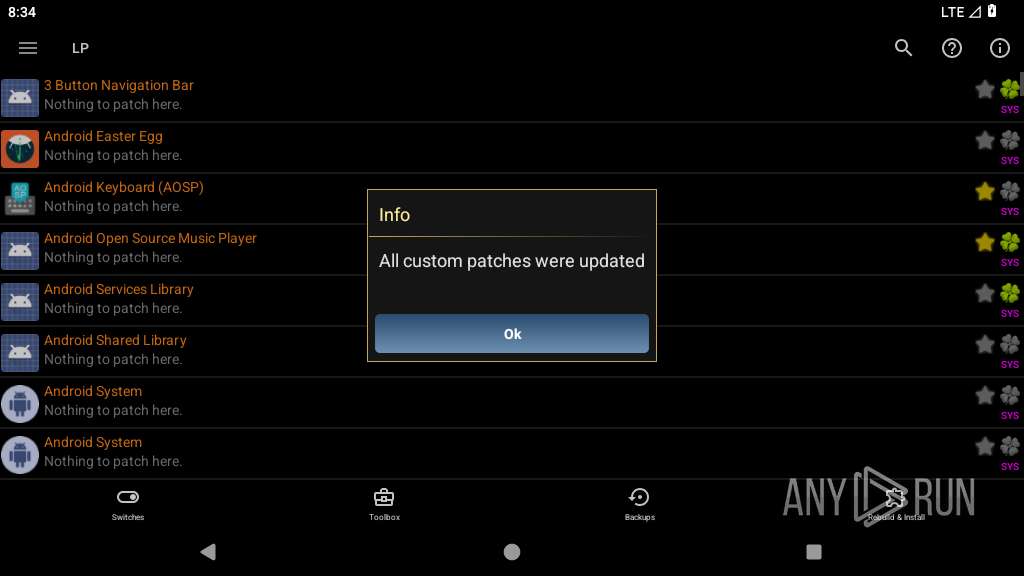
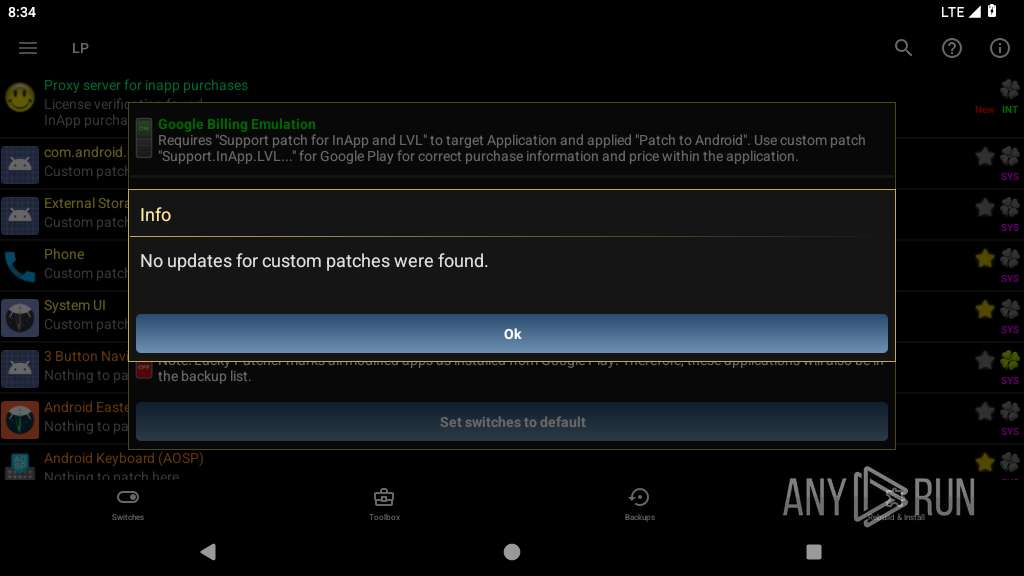
2448 | app_process64 | POST | 404 | 104.21.59.188:80 | http://chelpus.com/luckypatcher/CustomPatches2.zip | unknown | — | — | unknown |
2448 | app_process64 | POST | 404 | 104.21.59.188:80 | http://chelpus.com/luckypatcher/CustomPatches2.zip | unknown | — | — | unknown |
2448 | app_process64 | POST | 404 | 104.21.59.188:80 | http://chelpus.com/luckypatcher/CustomPatches2.zip | unknown | — | — | unknown |
2448 | app_process64 | POST | 404 | 104.21.59.188:80 | http://chelpus.com/luckypatcher/CustomPatches2.zip | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 172.217.16.36:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.208.195:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
— | — | 142.251.9.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
573 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
2448 | app_process64 | 104.21.59.188:443 | chelpus.com | CLOUDFLARENET | — | suspicious |
2448 | app_process64 | 104.21.59.188:80 | chelpus.com | CLOUDFLARENET | — | suspicious |
2448 | app_process64 | 149.56.155.246:443 | — | OVH SAS | CA | unknown |
2448 | app_process64 | 34.110.229.214:443 | config.unityads.unity3d.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
chelpus.com |
| unknown |
config.unityads.unity3d.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |