| File name: | IDM 6.xx Patcher v2.2.exe_ |
| Full analysis: | https://app.any.run/tasks/d0001bb0-c69d-4aa8-848b-a11a9e4d23b1 |
| Verdict: | Malicious activity |
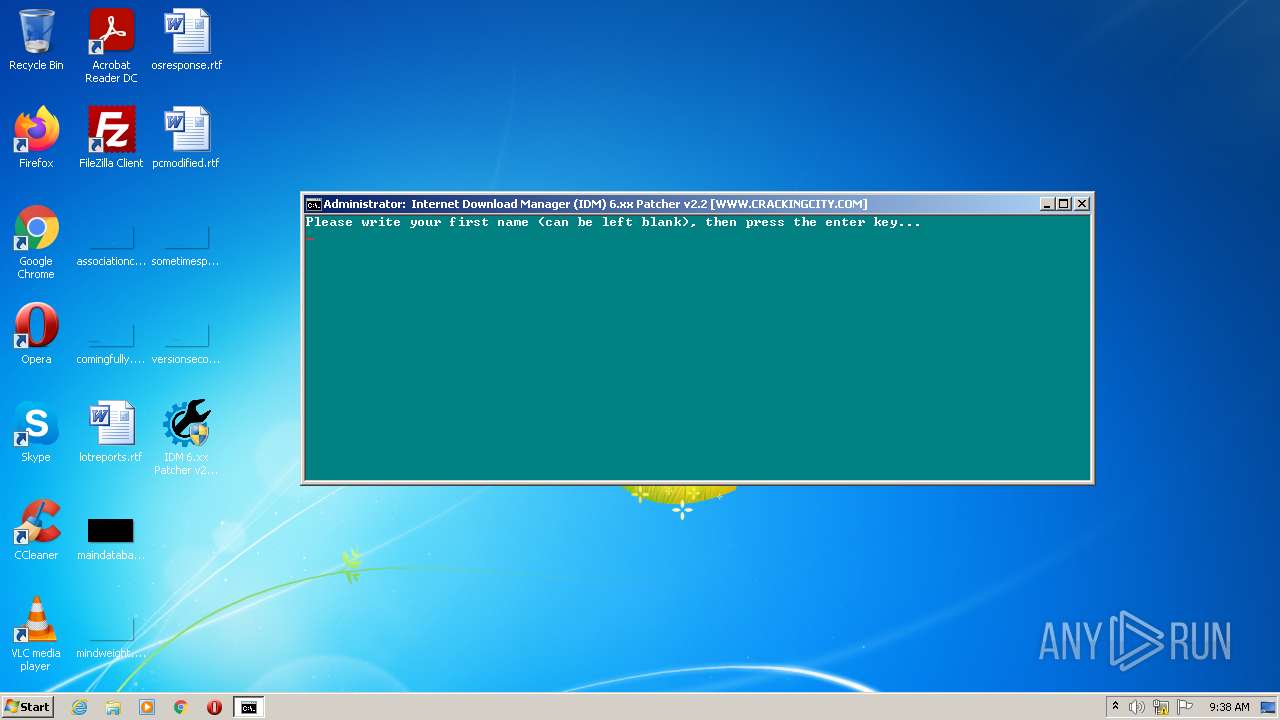
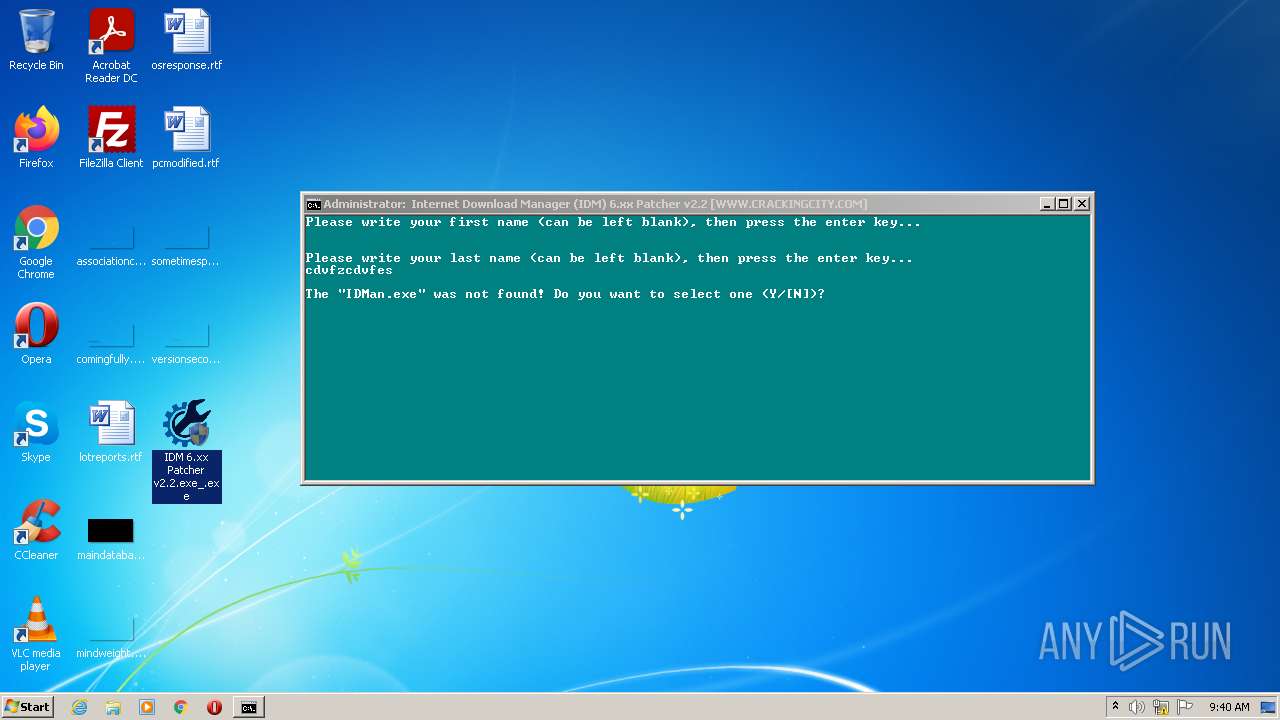
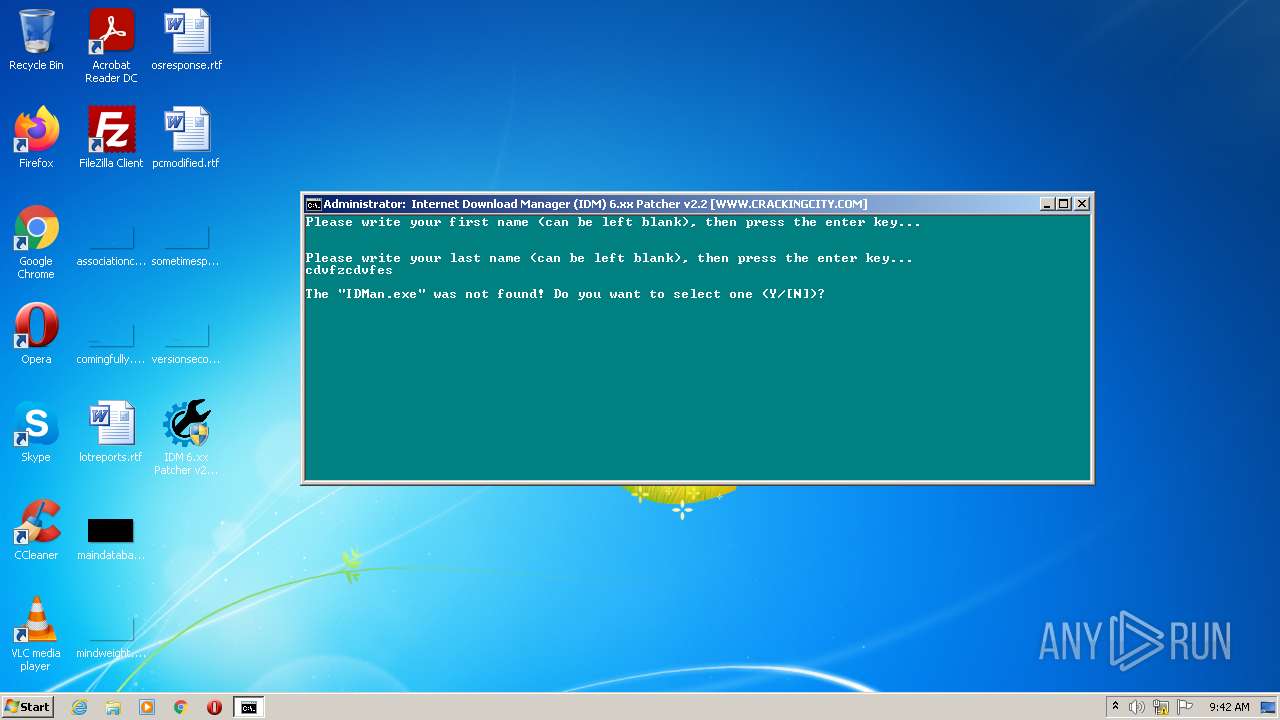
| Analysis date: | January 18, 2022, 09:38:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4B81C4AAAA0F18F4FAE2781F150D6F1A |
| SHA1: | 29F763DA3210ADA233CF44A869EB9BF9A5DD5514 |
| SHA256: | 405F1B3DE58297D747ABE54D26F71603EF2DA31D3B9525DC14C4D62EB63DF5BF |
| SSDEEP: | 24576:Z2yQPaYJJLDfbalTg//hsPS7ybubjKj+NsRv:Zp5m3+Zg/SyWmC |
MALICIOUS
Drops executable file immediately after starts
- IDM 6.xx Patcher v2.2.exe_.exe (PID: 2948)
- 7za.exe (PID: 3564)
- 7za.exe (PID: 508)
Application was dropped or rewritten from another process
- 7za.exe (PID: 3440)
- 7za.exe (PID: 2616)
- AB2EF.exe (PID: 3992)
- AB2EF.exe (PID: 3364)
- AB2EF.exe (PID: 2068)
- AB2EF.exe (PID: 3968)
- 7za.exe (PID: 508)
- 7za.exe (PID: 3564)
- AB2EF.exe (PID: 2000)
- AB2EF.exe (PID: 3196)
- AB2EF.exe (PID: 2984)
- AB2EF.exe (PID: 3712)
SUSPICIOUS
Reads the computer name
- IDM 6.xx Patcher v2.2.exe_.exe (PID: 2948)
- 7za.exe (PID: 3440)
- 7za.exe (PID: 2616)
- 7za.exe (PID: 3564)
- 7za.exe (PID: 508)
Checks supported languages
- IDM 6.xx Patcher v2.2.exe_.exe (PID: 2948)
- cmd.exe (PID: 852)
- 7za.exe (PID: 3440)
- 7za.exe (PID: 2616)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1512)
- AB2EF.exe (PID: 2984)
- 7za.exe (PID: 3564)
- AB2EF.exe (PID: 2000)
- AB2EF.exe (PID: 3196)
- AB2EF.exe (PID: 3992)
- mode.com (PID: 1888)
- AB2EF.exe (PID: 2068)
- AB2EF.exe (PID: 3968)
- cmd.exe (PID: 3148)
- 7za.exe (PID: 508)
- AB2EF.exe (PID: 3364)
- AB2EF.exe (PID: 3712)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 852)
Executable content was dropped or overwritten
- IDM 6.xx Patcher v2.2.exe_.exe (PID: 2948)
- 7za.exe (PID: 3564)
- 7za.exe (PID: 508)
Starts CMD.EXE for commands execution
- IDM 6.xx Patcher v2.2.exe_.exe (PID: 2948)
- cmd.exe (PID: 1512)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2476)
- cmd.exe (PID: 3148)
Application launched itself
- cmd.exe (PID: 1512)
INFO
Checks supported languages
- attrib.exe (PID: 956)
- reg.exe (PID: 2144)
- reg.exe (PID: 1404)
- reg.exe (PID: 1068)
- find.exe (PID: 1612)
- find.exe (PID: 3932)
- find.exe (PID: 2884)
- reg.exe (PID: 2532)
Reads CPU info
- reg.exe (PID: 1068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| ProductVersion: | 2.2.0.0 |
|---|---|
| ProductName: | IDM 6.xx Patcher |
| OriginalFileName: | IDM 6.xx Patcher.exe |
| LegalCopyright: | CrackingCity.com, Copyright © 2020 - 2021 |
| InternalName: | IDM 6.xx Patcher.exe |
| FileVersion: | 2.2.0.0 |
| FileDescription: | IDM 6.xx Patcher |
| CompanyName: | CrackingCity.com |
| Comments: | IDM 6.xx Patcher - CrackingCity.com |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.2.0.0 |
| FileVersionNumber: | 2.2.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x11def |
| UninitializedDataSize: | - |
| InitializedDataSize: | 110080 |
| CodeSize: | 70656 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2010:06:27 09:06:38+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jun-2010 07:06:38 |
| Detected languages: |
|
| Comments: | IDM 6.xx Patcher - CrackingCity.com |
| CompanyName: | CrackingCity.com |
| FileDescription: | IDM 6.xx Patcher |
| FileVersion: | 2.2.0.0 |
| InternalName: | IDM 6.xx Patcher.exe |
| LegalCopyright: | CrackingCity.com, Copyright © 2020 - 2021 |
| OriginalFilename: | IDM 6.xx Patcher.exe |
| ProductName: | IDM 6.xx Patcher |
| ProductVersion: | 2.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 27-Jun-2010 07:06:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011317 | 0x00011400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57699 |
.rdata | 0x00013000 | 0x000030EA | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.54943 |
.data | 0x00017000 | 0x0000292C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.65832 |
.rsrc | 0x0001A000 | 0x000172BB | 0x00017400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.74869 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04909 | 635 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 1.98048 | 20 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
67
Monitored processes
27
Malicious processes
1
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | 7za e files.tmp -pidm@idm420 -aoa "AB2EF.exe" | C:\Users\admin\AppData\Local\Temp\ytmp\7za.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ytmp\main.bat" " | C:\Windows\system32\cmd.exe | — | IDM 6.xx Patcher v2.2.exe_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | ATTRIB -S +H . | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1068 | REG QUERY "HKLM\Hardware\Description\System\CentralProcessor\0" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\Desktop\IDM 6.xx Patcher v2.2.exe_.exe" | C:\Users\admin\Desktop\IDM 6.xx Patcher v2.2.exe_.exe | — | Explorer.EXE | |||||||||||
User: admin Company: CrackingCity.com Integrity Level: MEDIUM Description: IDM 6.xx Patcher Exit code: 3221226540 Version: 2.2.0.0 Modules
| |||||||||||||||
| 1404 | REG QUERY "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced" /v "ShowSuperHidden" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ytmp\IDM.bat" " | C:\Windows\system32\cmd.exe | — | IDM 6.xx Patcher v2.2.exe_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1612 | FIND /I "ppd" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | MODE CON: COLS=98 LINES=22 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | AB2EF j6NM4Cxfv3 | C:\Users\admin\AppData\Local\Temp\ytmp\AB2EF.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 026
Read events
1 018
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2948) IDM 6.xx Patcher v2.2.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2948) IDM 6.xx Patcher v2.2.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2948) IDM 6.xx Patcher v2.2.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2948) IDM 6.xx Patcher v2.2.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | IDM 6.xx Patcher v2.2.exe_.exe | C:\Users\admin\AppData\Local\Temp\ytmp\files.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2616 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\IDM.bat | text | |
MD5:— | SHA256:— | |||
| 2948 | IDM 6.xx Patcher v2.2.exe_.exe | C:\Users\admin\AppData\Local\Temp\ytmp\main.bat | text | |
MD5:320CD6EE614494CAE88E658960B2EA1F | SHA256:B36A223C84CF73FF7C9BE4674B2CED71A1EE5E2724218BAF00D4611A184F221F | |||
| 2948 | IDM 6.xx Patcher v2.2.exe_.exe | C:\Users\admin\AppData\Local\Temp\ytmp\7za.exe | executable | |
MD5:E3C061FA0450056E30285FD44A74CD2A | SHA256:E0E2C7D0F740FE2A4E8658CE54DFB6EB3C47C37FE90A44A839E560C685F1F1FA | |||
| 3440 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\IDM0.bat | text | |
MD5:69C3EDFE8C7003F905F19969922D2626 | SHA256:D90A40FCEF70925252CAF6722C29E95C4B904A19771E6E60AB39F00B161B8464 | |||
| 3564 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\AB2EF.exe | executable | |
MD5:8CF23FA804804EB416F7F395D5F0647F | SHA256:C69B39AD2739DAB03DBEE316BB9B921883AA8880A4E4E9BDDE7723E75A178B21 | |||
| 508 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\AB2EF.exe | executable | |
MD5:8CF23FA804804EB416F7F395D5F0647F | SHA256:C69B39AD2739DAB03DBEE316BB9B921883AA8880A4E4E9BDDE7723E75A178B21 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report