| File name: | PSO2_Tweaker_Installerv6b.exe |
| Full analysis: | https://app.any.run/tasks/d6ecdc58-6b93-4ff9-97ad-ae88bb89b3f4 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 14:15:12 |
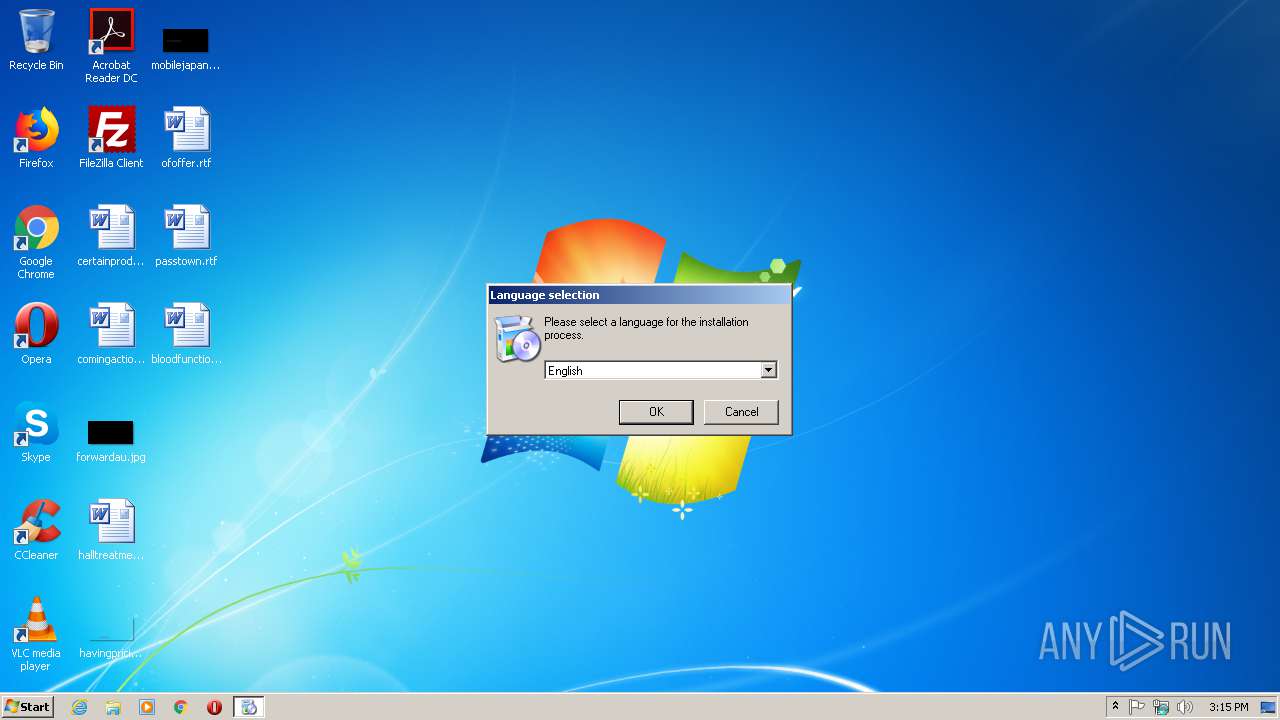
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 1A17FD77EAEB41FD8120A266DFCE2861 |
| SHA1: | 9A58B6E0B9C0658D0C472068F93F30B48412A0D8 |
| SHA256: | 40485D5D70D43432835570A37AE8934073470285870175765E0BF48813557279 |
| SSDEEP: | 98304:va4qzo4DByjl4sTqb9dgBgtC7UEVskv4HhlFUPHV9uRYEUdyjQx/G3:S31yjCsub9PteiXXUPHO+fxe3 |
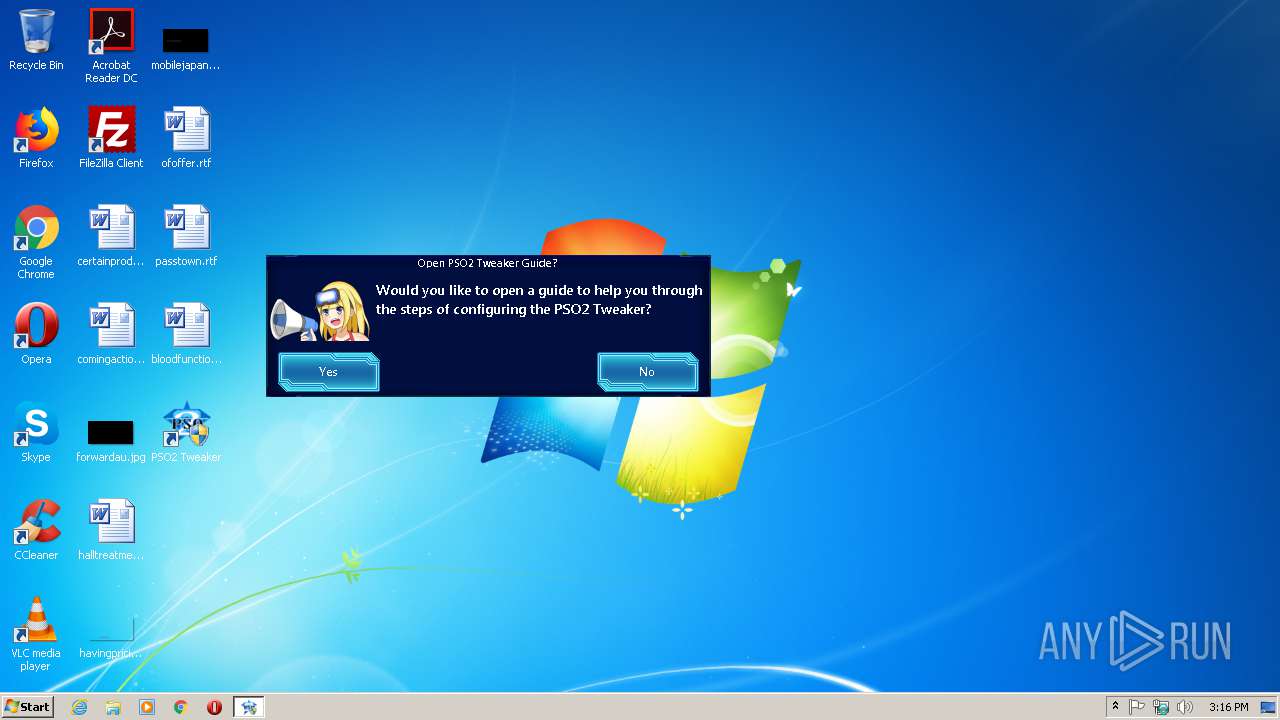
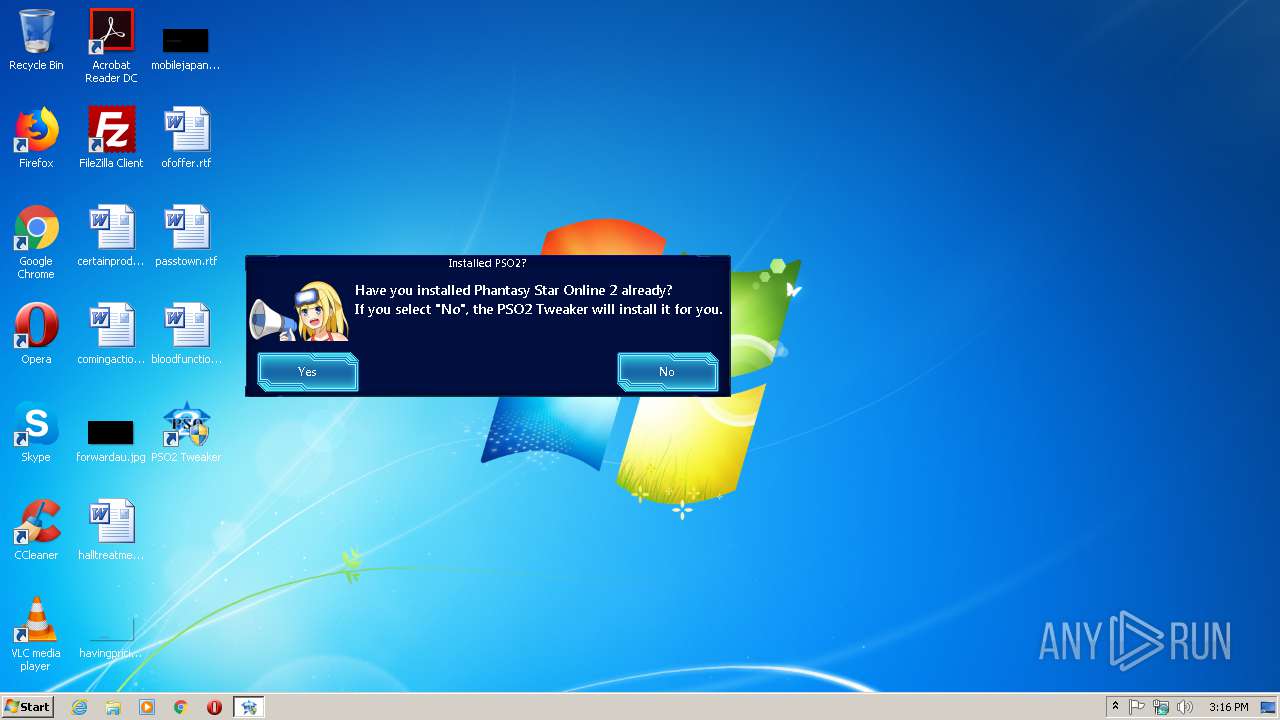
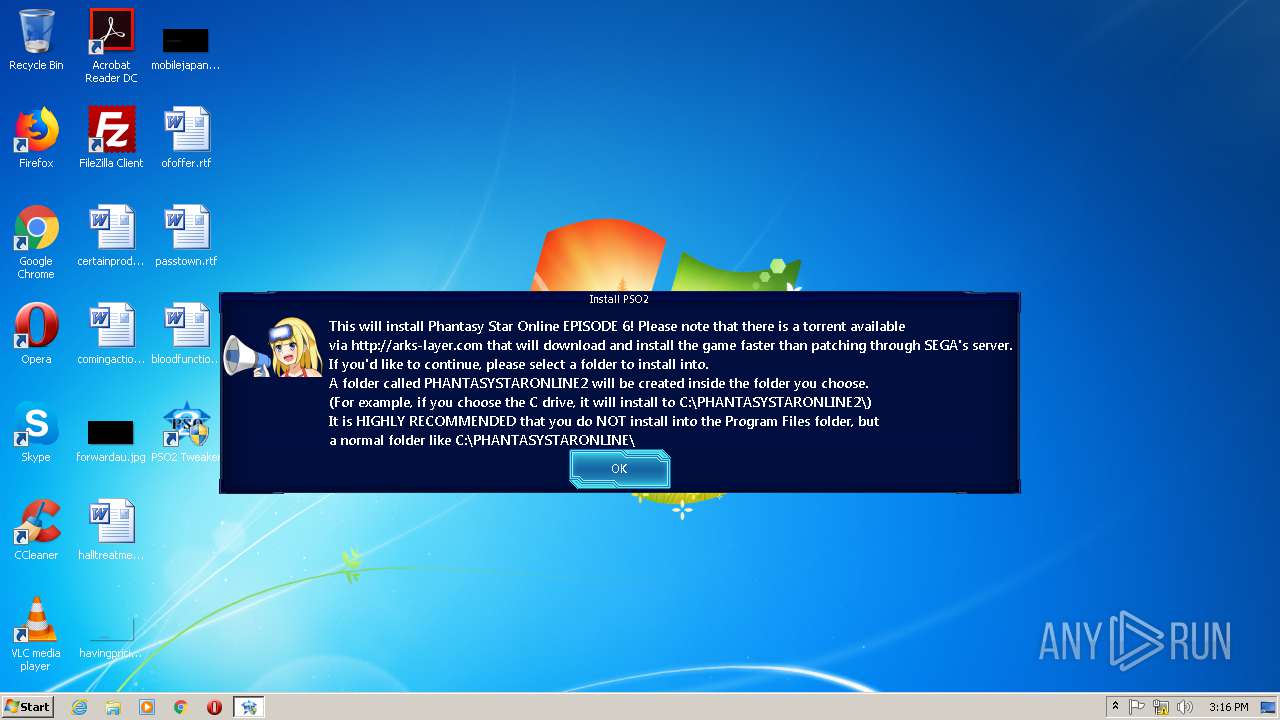
MALICIOUS
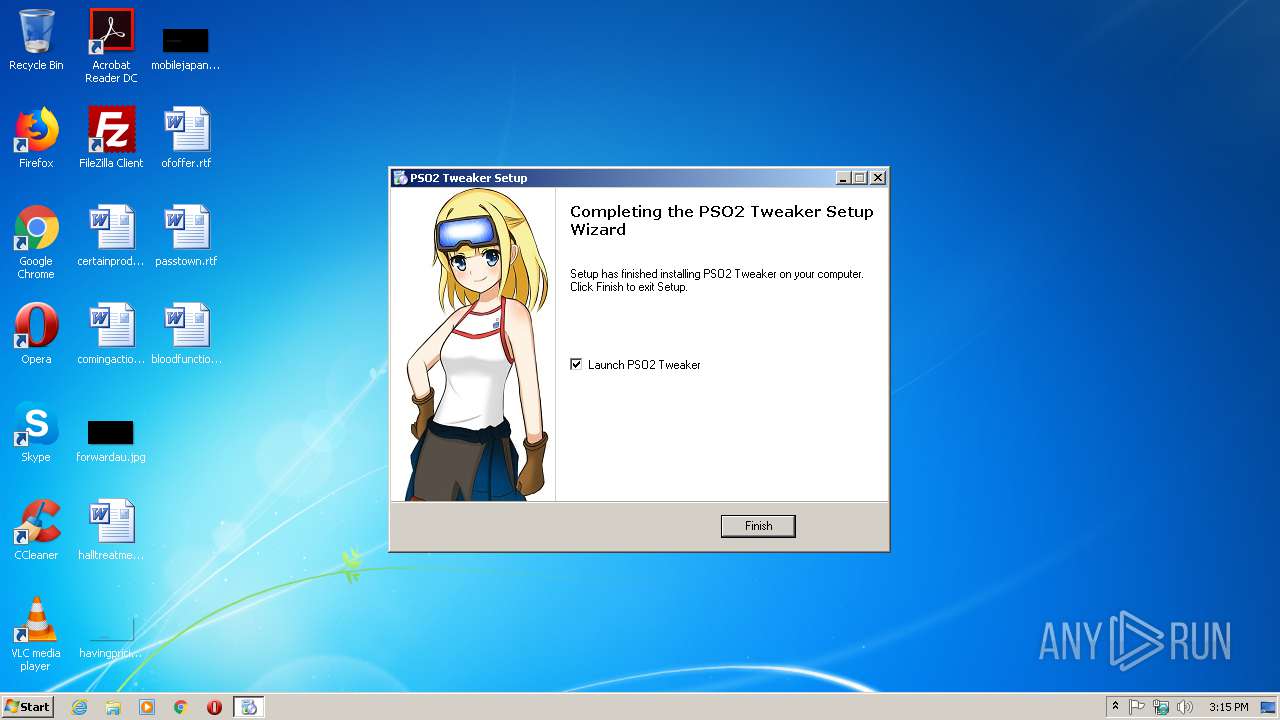
Application was dropped or rewritten from another process
- PSO2 Tweaker.exe (PID: 3924)
- PSO2 Tweaker.exe (PID: 1620)
SUSPICIOUS
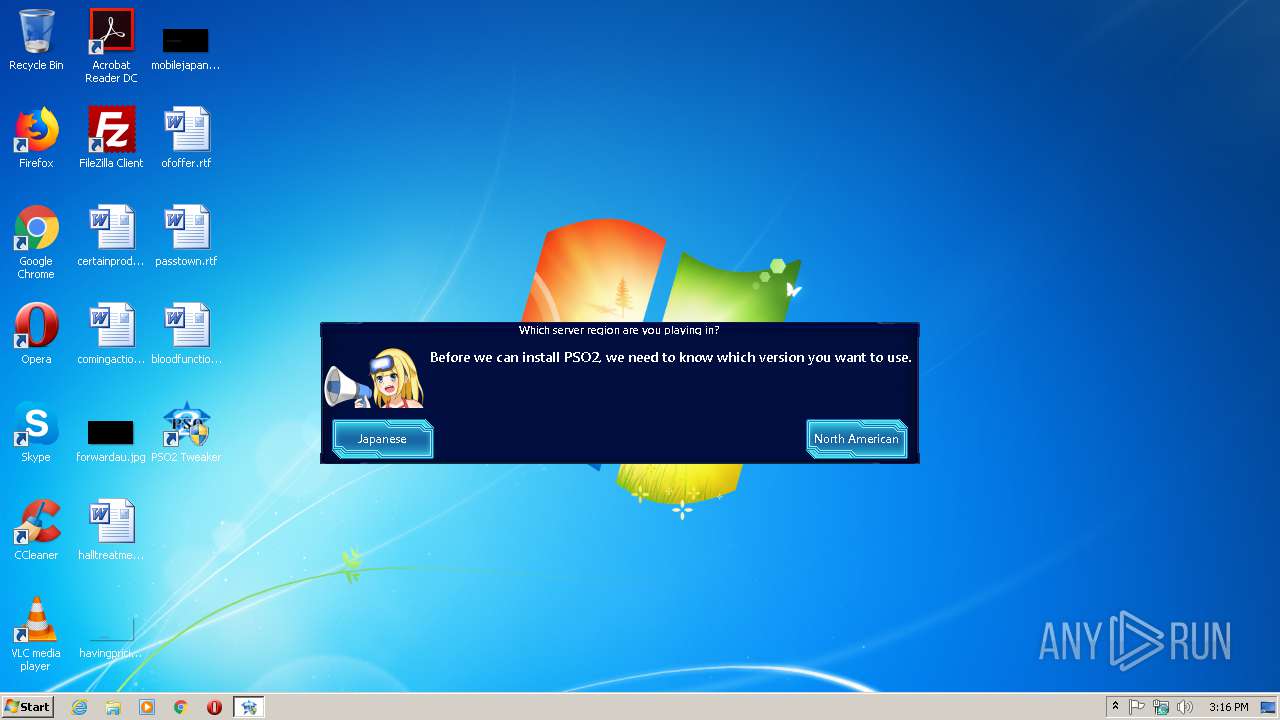
Executable content was dropped or overwritten
- PSO2_Tweaker_Installerv6b.exe (PID: 2776)
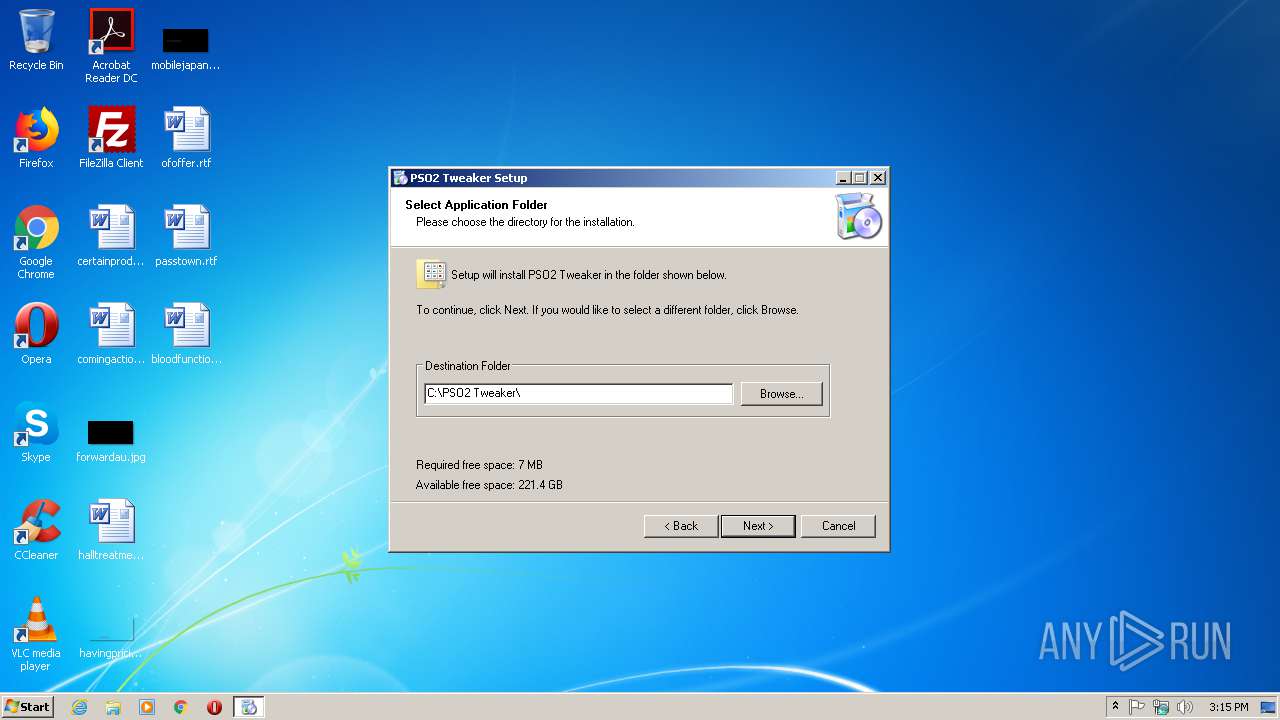
Creates files in the program directory
- PSO2_Tweaker_Installerv6b.exe (PID: 2776)
Application launched itself
- PSO2 Tweaker.exe (PID: 3924)
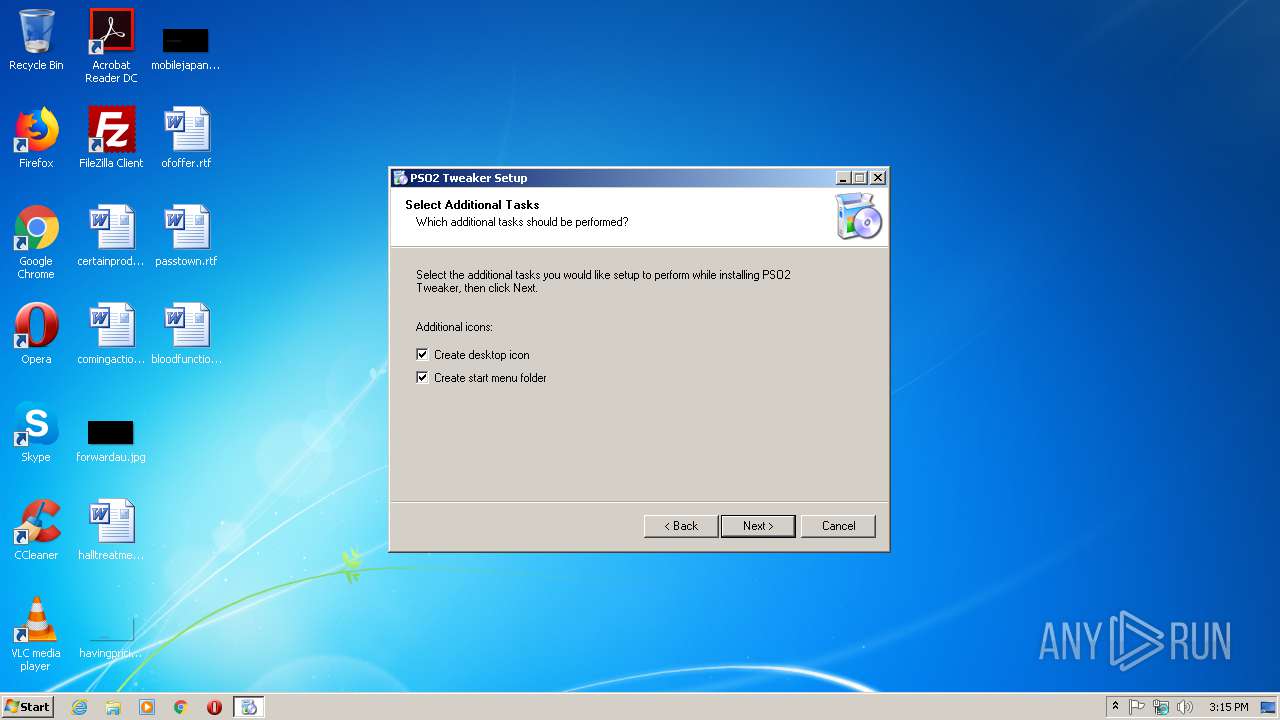
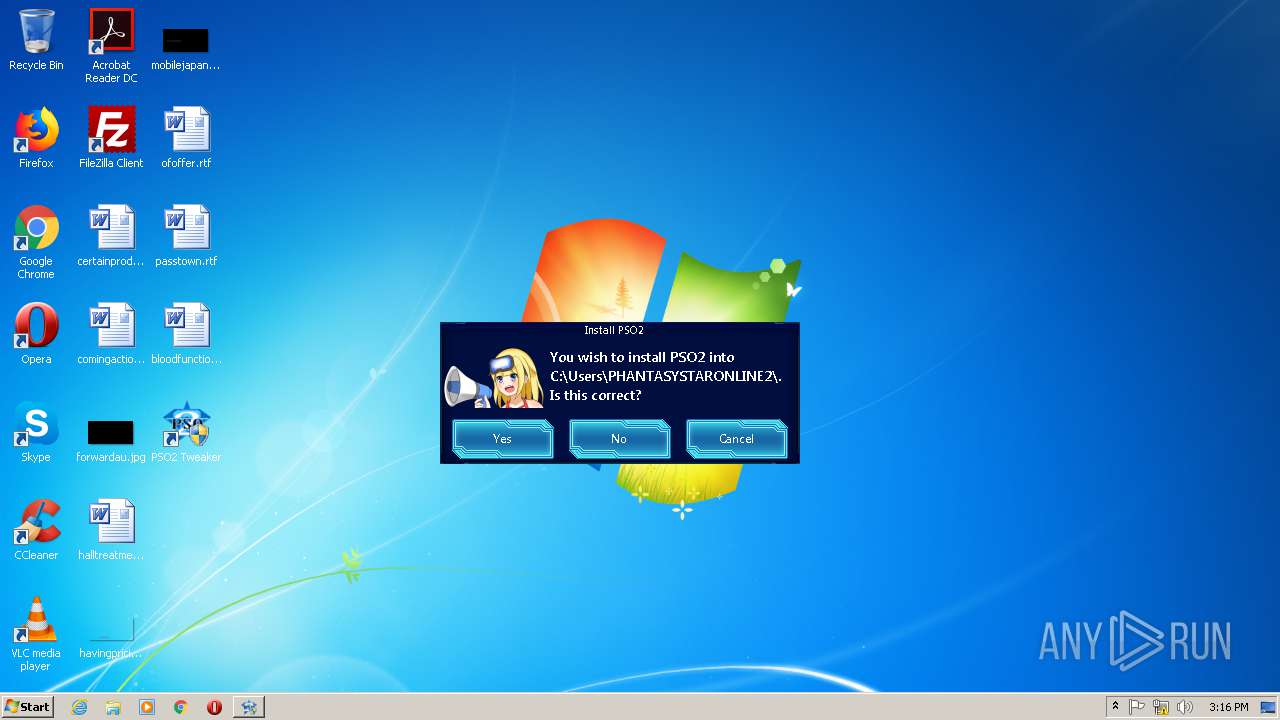
Creates a software uninstall entry
- PSO2_Tweaker_Installerv6b.exe (PID: 2776)
Reads Environment values
- PSO2 Tweaker.exe (PID: 1620)
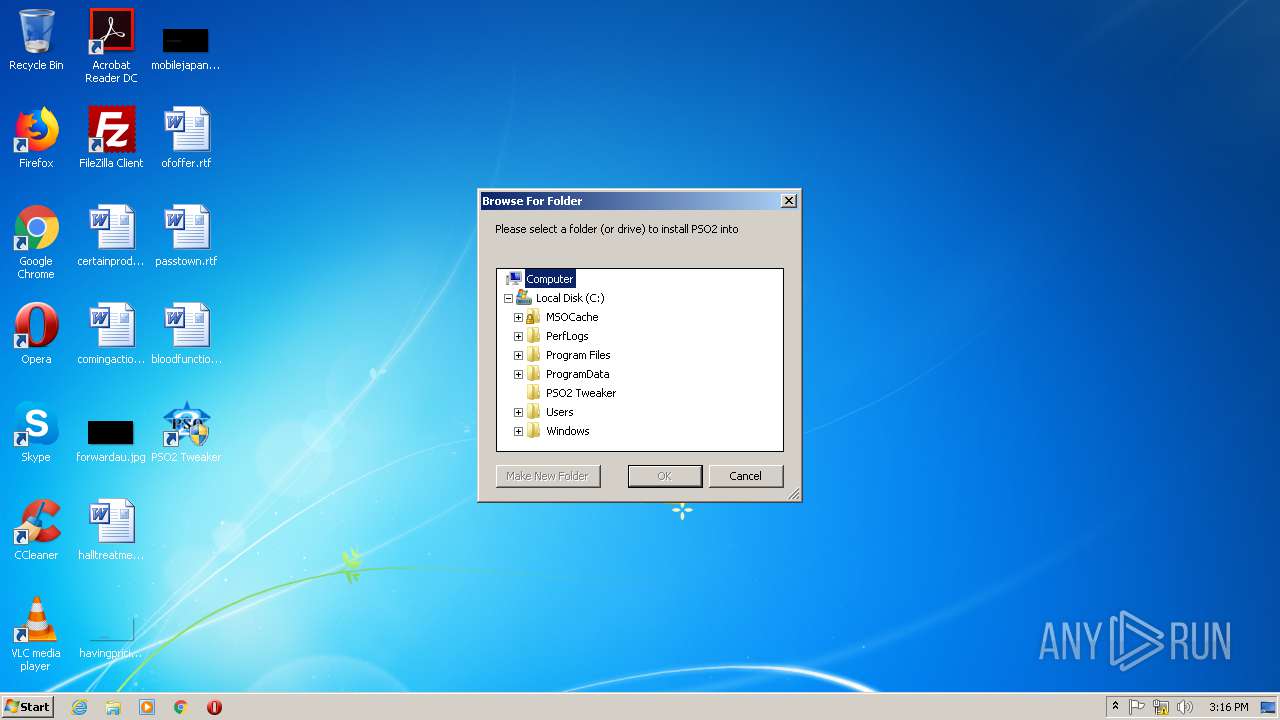
Creates files in the user directory
- PSO2 Tweaker.exe (PID: 1620)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:04 00:28:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 201728 |
| InitializedDataSize: | 259072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Sep-2016 22:28:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Sep-2016 22:28:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00008C0B | 0x00008E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.48422 |
.text | 0x0000A000 | 0x0002842C | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55935 |
.rdata | 0x00033000 | 0x000054AC | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.67857 |
.data | 0x00039000 | 0x00033384 | 0x00032000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.97815 |
.rsrc | 0x0006D000 | 0x00006840 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.84101 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8674 | 874 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.30941 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 4.03304 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 6.4265 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.64193 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.61672 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.11499 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.62416 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 6.05238 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
IMAGEHLP.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SETUPAPI.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
42
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Users\admin\AppData\Local\Temp\PSO2_Tweaker_Installerv6b.exe" | C:\Users\admin\AppData\Local\Temp\PSO2_Tweaker_Installerv6b.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
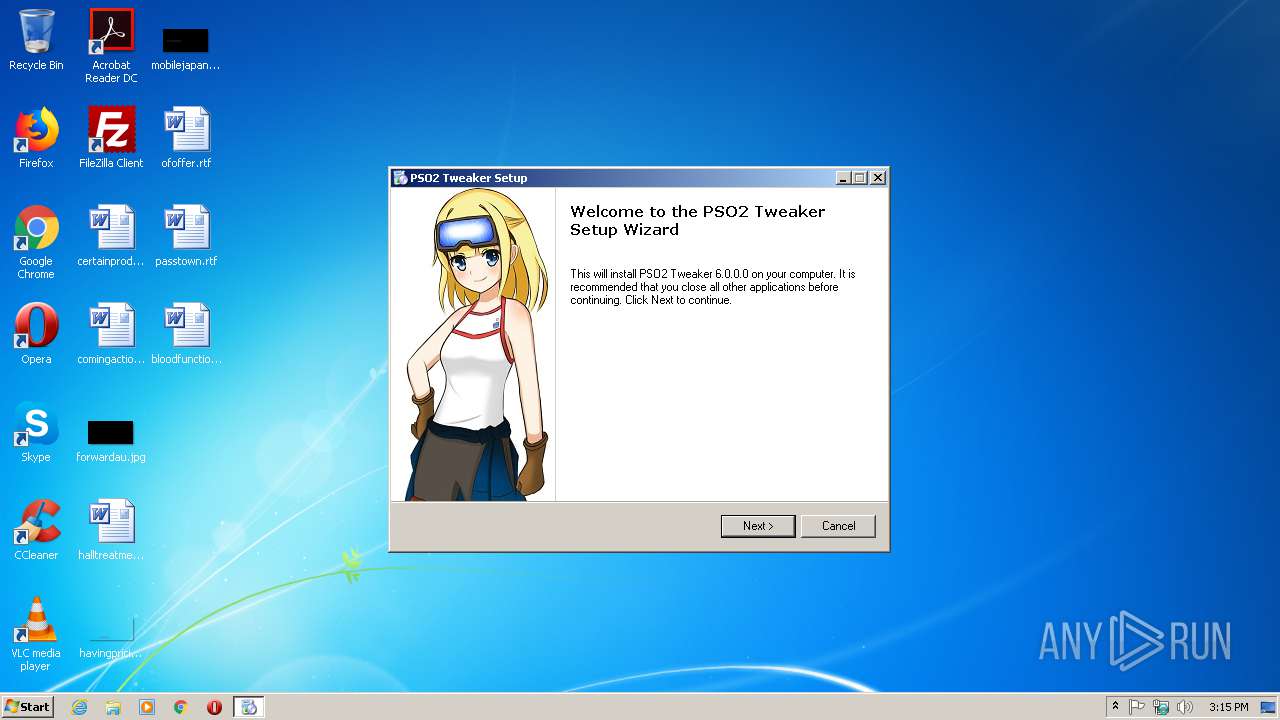
| 1620 | "C:\PSO2 Tweaker\PSO2 Tweaker.exe" | C:\PSO2 Tweaker\PSO2 Tweaker.exe | — | PSO2 Tweaker.exe | |||||||||||
User: admin Company: Arks-Layer Integrity Level: HIGH Description: PSO2 Tweaker Exit code: 0 Version: 6.0.0.0 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\PSO2_Tweaker_Installerv6b.exe" | C:\Users\admin\AppData\Local\Temp\PSO2_Tweaker_Installerv6b.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3924 | "C:\PSO2 Tweaker\PSO2 Tweaker.exe" | C:\PSO2 Tweaker\PSO2 Tweaker.exe | — | PSO2_Tweaker_Installerv6b.exe | |||||||||||
User: admin Company: Arks-Layer Integrity Level: HIGH Description: PSO2 Tweaker Exit code: 3221225547 Version: 6.0.0.0 Modules
| |||||||||||||||
Total events
702
Read events
683
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | DisplayName |
Value: PSO2 Tweaker | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | DisplayVersion |
Value: 6.0.0.0 | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | HelpLink |
Value: http://arks-layer.com | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | Publisher |
Value: Arks-Layer | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | UninstallString |
Value: C:\PSO2 Tweaker\Uninstall.exe | |||
| (PID) Process: | (2776) PSO2_Tweaker_Installerv6b.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PSO2 Tweaker |
| Operation: | write | Name: | DisplayIcon |
Value: C:\PSO2 Tweaker\Uninstall.exe | |||
| (PID) Process: | (3924) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\PSO2Tweaker |
| Operation: | write | Name: | MaxSize |
Value: 524288 | |||
| (PID) Process: | (3924) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\PSO2Tweaker |
| Operation: | write | Name: | AutoBackupLogFiles |
Value: 0 | |||
| (PID) Process: | (3924) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\PSO2Tweaker\PSO2Tweaker |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework\v4.0.30319\EventLogMessages.dll | |||
Executable files
2
Suspicious files
1
Text files
17
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\Setup.cab | compressed | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\SC.dat | text | |
MD5:— | SHA256:— | |||
| 3924 | PSO2 Tweaker.exe | C:\PSO2 Tweaker\logfile.txt | — | |
MD5:— | SHA256:— | |||
| 1620 | PSO2 Tweaker.exe | C:\PSO2 Tweaker\logfile.txt | — | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\Desktop.dat | text | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\OS.dat | text | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\Startmenu.dat | text | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\languages.dat | text | |
MD5:— | SHA256:— | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\English.ifl | text | |
MD5:DC51022CF78C9B519F2058983A773119 | SHA256:93E28A5125B4864773F53D1C5F87C1756EFA0C2D60D5C3FD6B34AA920080F568 | |||
| 2776 | PSO2_Tweaker_Installerv6b.exe | C:\Users\admin\AppData\Local\Temp\IF{FAA17EFA-F1F9-418B-8421-9FB7CC890CD3}\Español.ifl | text | |
MD5:EE85CDA83E5AB141B738B702FCBB9198 | SHA256:0725FE459E577294BDB3CED7E4C6C5847A6E996488C09F75122B508C39F2A4E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report