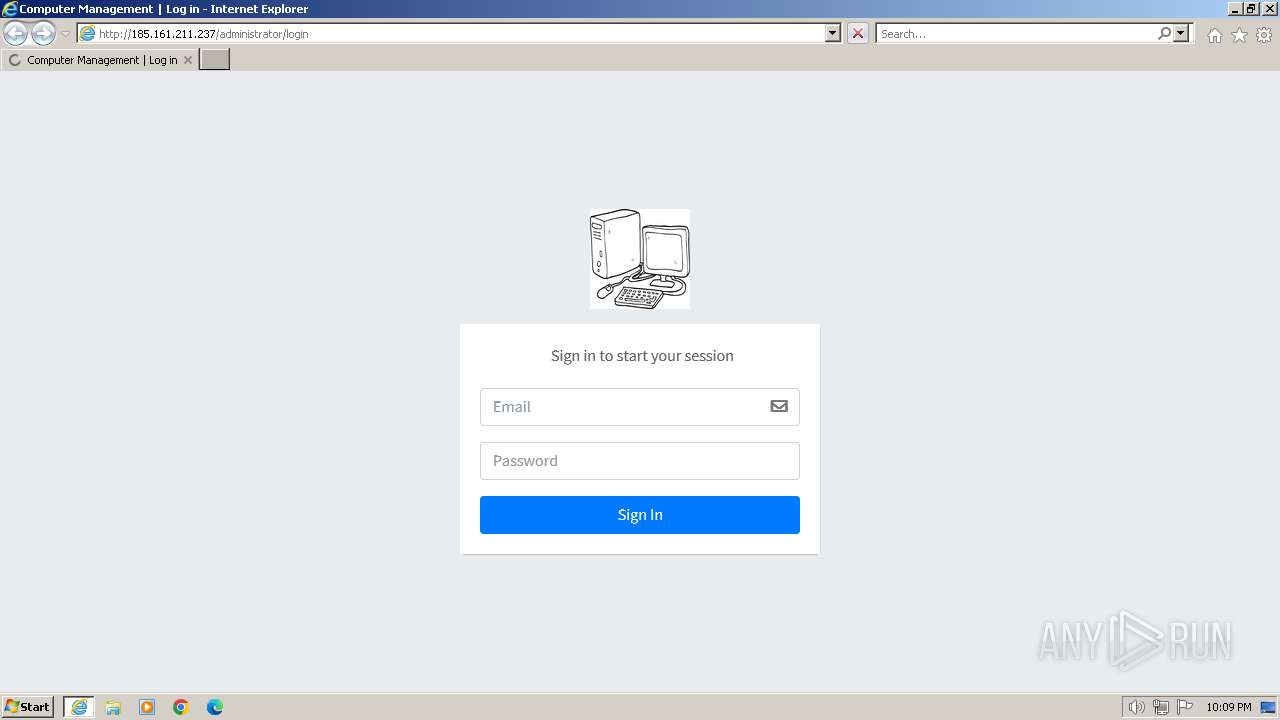
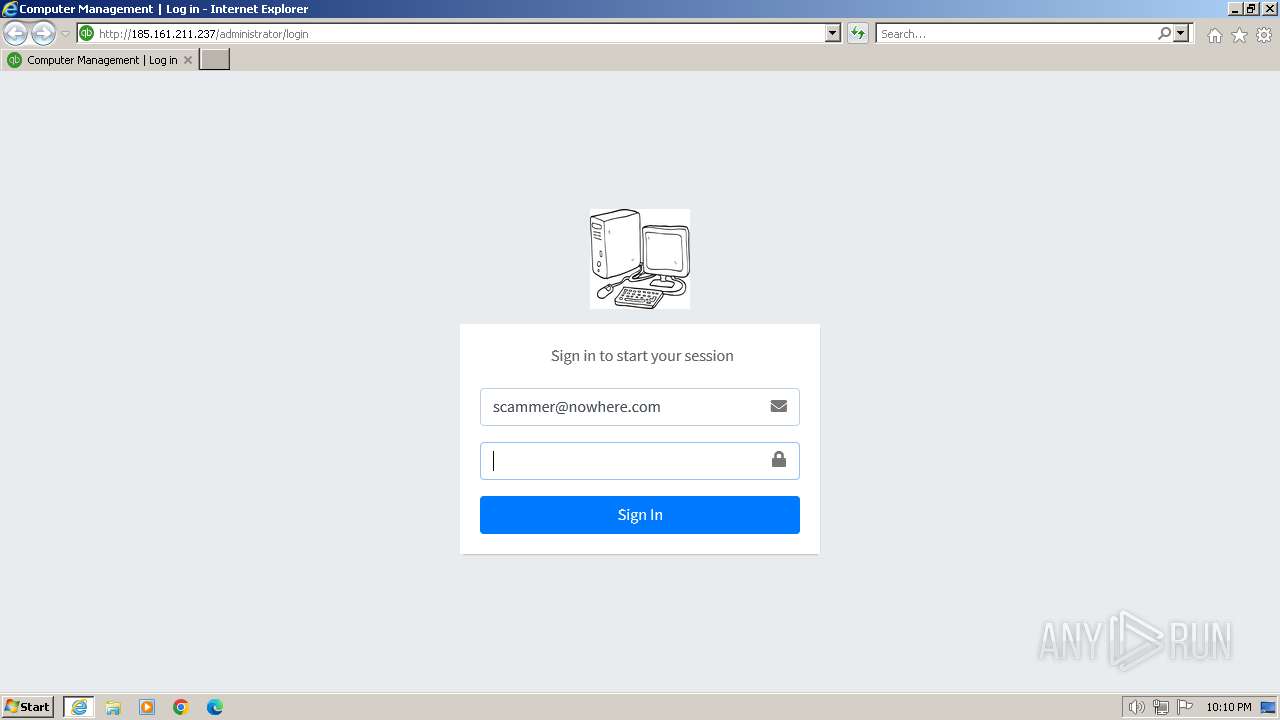
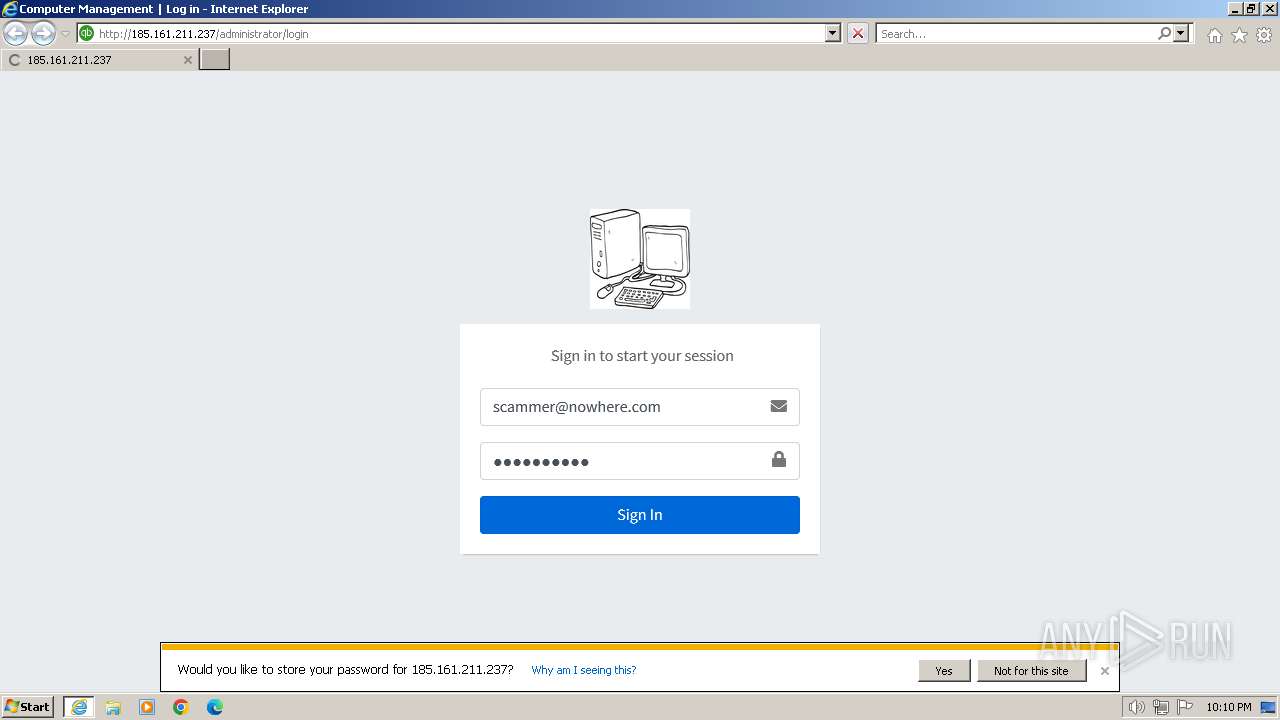
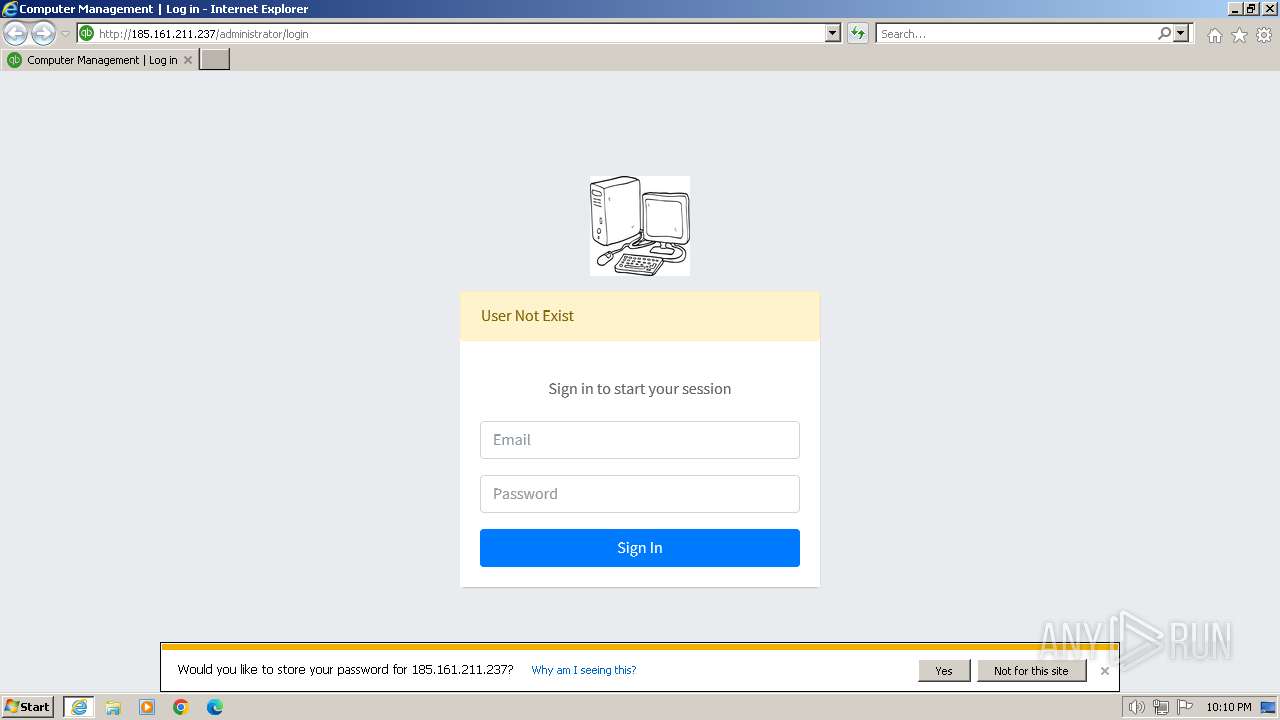
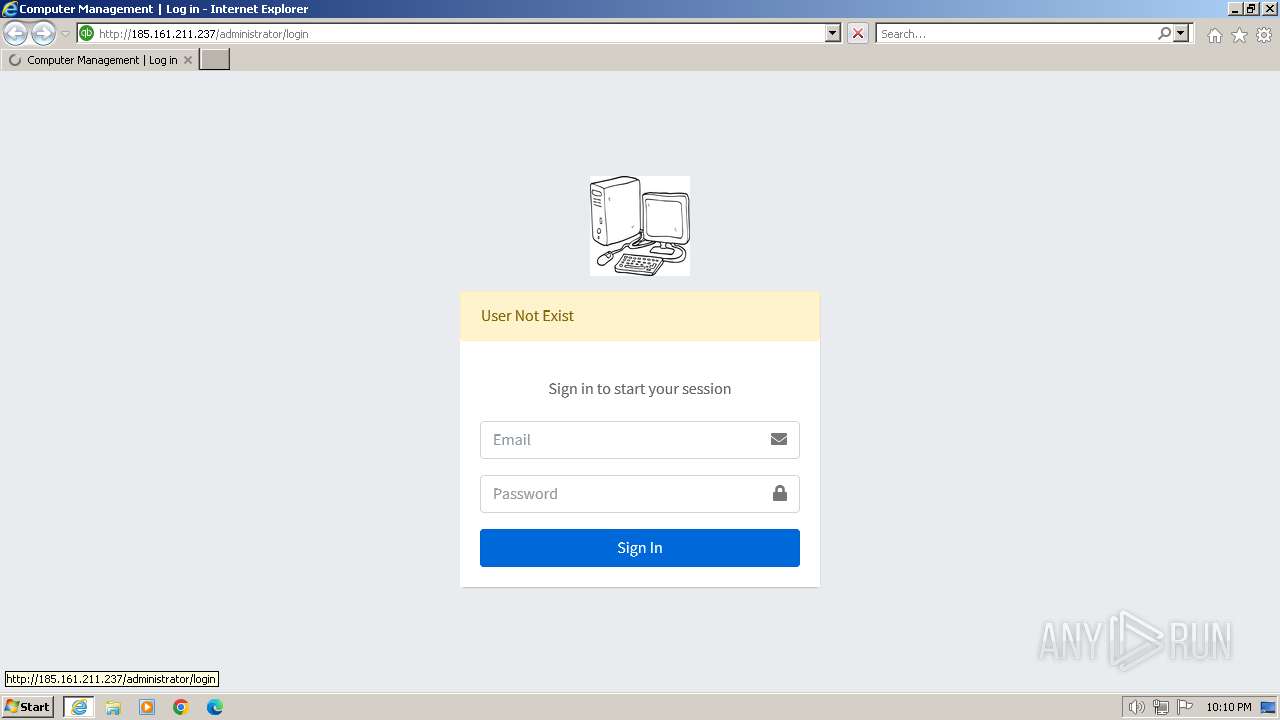
| URL: | 185.161.211.237 |
| Full analysis: | https://app.any.run/tasks/5607c46d-88d2-4ad2-a162-b0380d868583 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2024, 22:09:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BF9E514964936620B8A096CCF0C0D783 |
| SHA1: | 1D9CE939771E2A54B9D85172090B2A6693BAF734 |
| SHA256: | 404328D82E3B1A274B004AE462B2BB3530320534F7240C126CF1DC768CAEB8D2 |
| SSDEEP: | 3:EQgmpF:EQgmv |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" "185.161.211.237" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 715
Read events
17 584
Write events
95
Delete events
36
Modification events
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 826398112 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088128 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088128 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
18
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C6E99A82A2535BA8EEA3F824774C61DA | SHA256:D4393C8706AD393526E246422282C155ABB741EE8A166334F64579C072C18841 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\265C0DEB29181DD1891051371C5F863A_8CFD0F060456F65ABC9E95E41A1F781C | binary | |
MD5:B205BF7AD53872ADD203E76B16C67F93 | SHA256:4F002B6C3FB14C6302EBC126EC9081EC44A3E34FF798288E1B27186A5C4BF276 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:2CAA6303DF5F48DEF48955036F3D65B0 | SHA256:B661798218EF2564A5D13131B742AF5A168478FD8C3ADD589B8CDA7F49274A0A | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\login[1].htm | html | |
MD5:DD2C823094AF61661F476EA2ADD9F074 | SHA256:9C3407B5CCB5030CD9EBEAB7D90262D08DB8F663BF76962F3850B0FB047BE4AF | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:533DDD66883246226B08E2EB924D2FE0 | SHA256:28B97400E4B8DA0D57399433DEB9051DA0853A7FDD5BF2FB0AFE3E2DE1E0B224 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\adminlte.min[1].css | text | |
MD5:3761431942D1ADAD52B80E4E4D174449 | SHA256:150FA4D262057D65D54DA5B56AB877A8AC7C2175F9066E5FE901BED299148DA1 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\all.min[1].css | text | |
MD5:74BAB4578692993514E7F882CC15C218 | SHA256:D87DDF917B7A1449AB45E2B8E3C98354629BDD65B6659C37E6023BBEA1CE1386 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\060EYAQY.txt | text | |
MD5:832438DF43AAE917D234C38019A9FA72 | SHA256:B5EF74D3B07E7B68029BDAF0B10DD45F46ABE1A3CBCD263F0101B277F06B99D4 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\7JONOM7H.txt | text | |
MD5:3C0F62620BE4DCAADDDF4015ADADEA15 | SHA256:0A47B0292371BAA0D7CBA4E6988011D53EBB2CF493B620FD051FD78C5A4743DA | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C8DA72232F364865C763B8C3A997269B | SHA256:0636B734DC8DFF53AEFDCFF36F092072FF1A7C5A35C0E3984890C6CAC849B0C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
27
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | iexplore.exe | GET | 302 | 185.161.211.237:80 | http://185.161.211.237/ | unknown | text | 567 b | unknown |
2044 | iexplore.exe | GET | 200 | 185.161.211.237:80 | http://185.161.211.237/administrator/login | unknown | html | 873 b | unknown |
2044 | iexplore.exe | GET | 200 | 185.161.211.237:80 | http://185.161.211.237/public/plugins/fontawesome-free/css/all.min.css | unknown | text | 14.3 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 185.161.211.237:80 | http://185.161.211.237/public/images/logo-new.png | unknown | image | 3.81 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 185.161.211.237:80 | http://185.161.211.237/resources/assets/backend/css/adminlte.min.css | unknown | text | 146 Kb | unknown |
2044 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?46a3771404230298 | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?86b4b67e50f1d6bf | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2044 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGbSiPAo8Qj1CbnbR%2FpRjKM%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | iexplore.exe | 185.161.211.237:80 | — | Zemlyaniy Dmitro Leonidovich | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2044 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2044 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2044 | iexplore.exe | 142.250.186.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2044 | iexplore.exe | 142.250.186.163:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
4052 | iexplore.exe | 185.161.211.237:80 | — | Zemlyaniy Dmitro Leonidovich | NL | unknown |
4052 | iexplore.exe | 92.123.104.28:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report