| File name: | MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/d4499e8b-1b7a-4e11-84ec-54716f373698 |
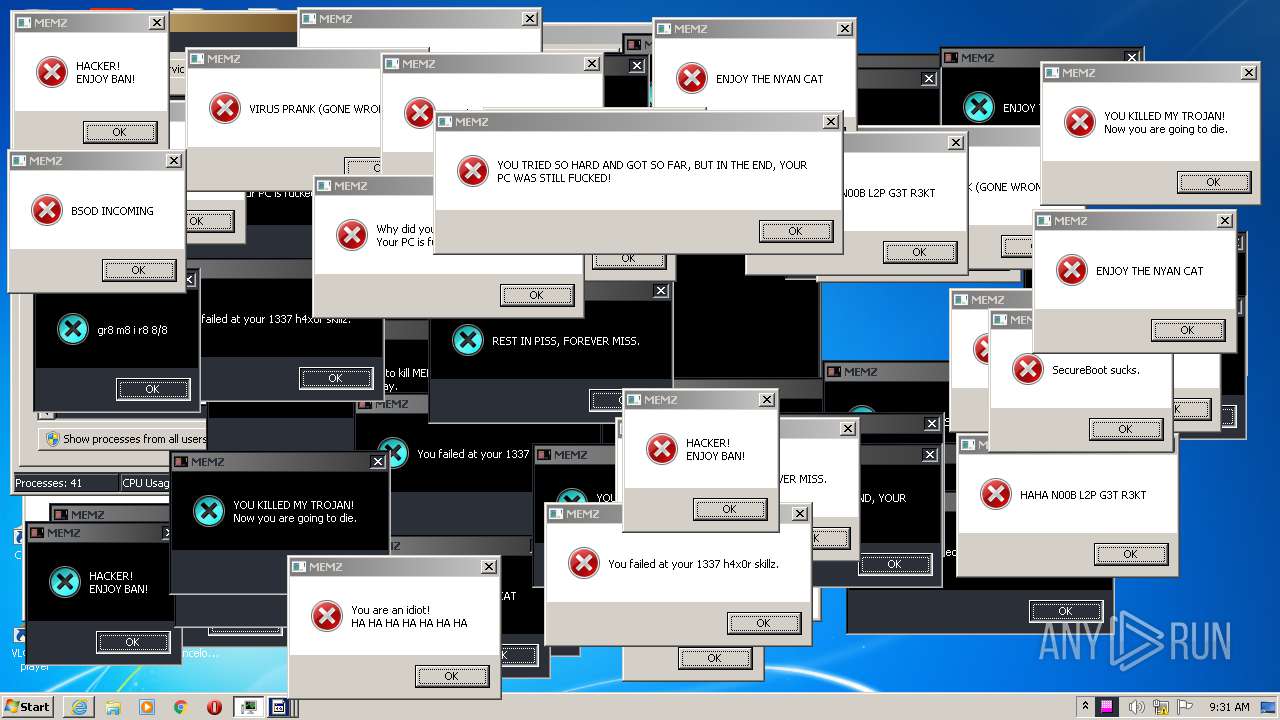
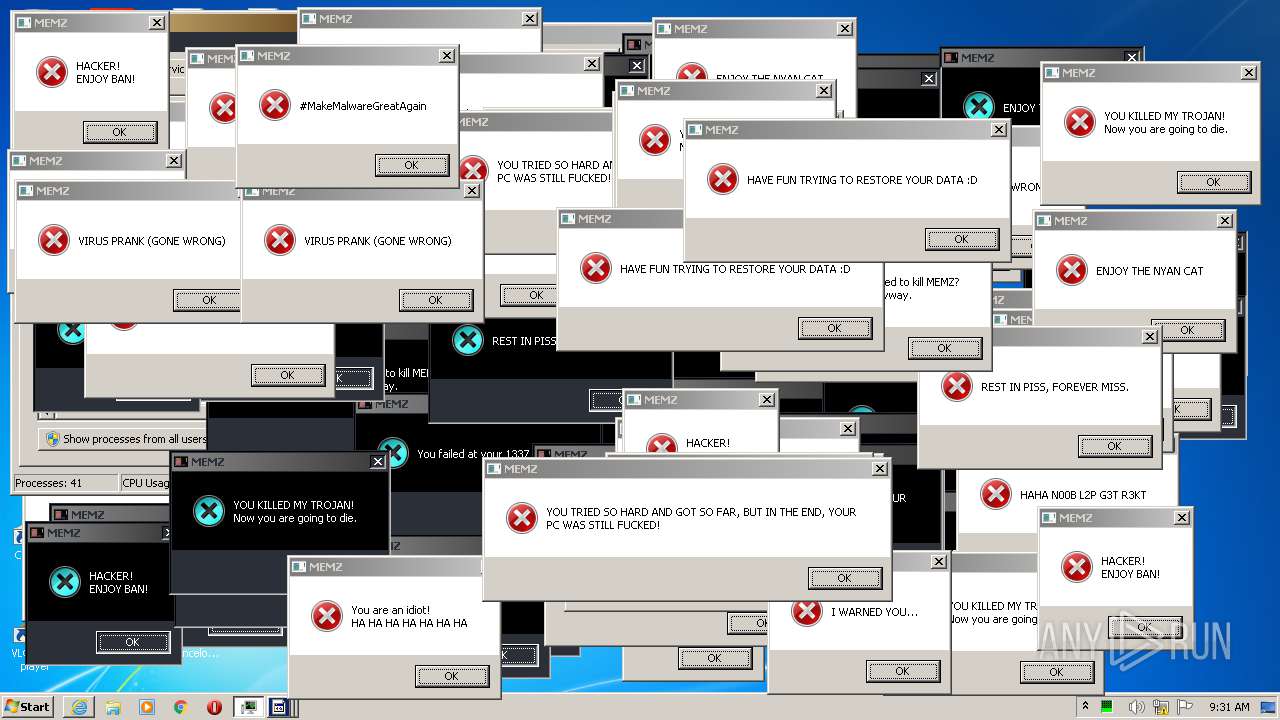
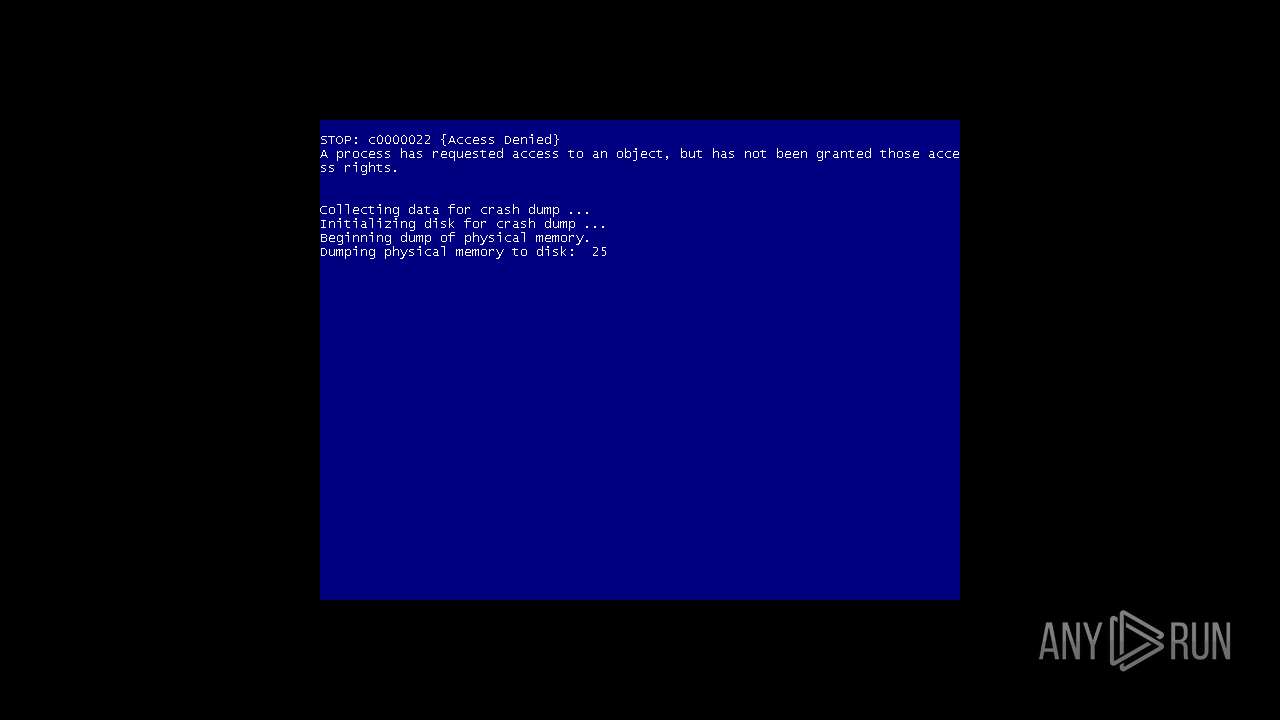
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 08:29:00 |
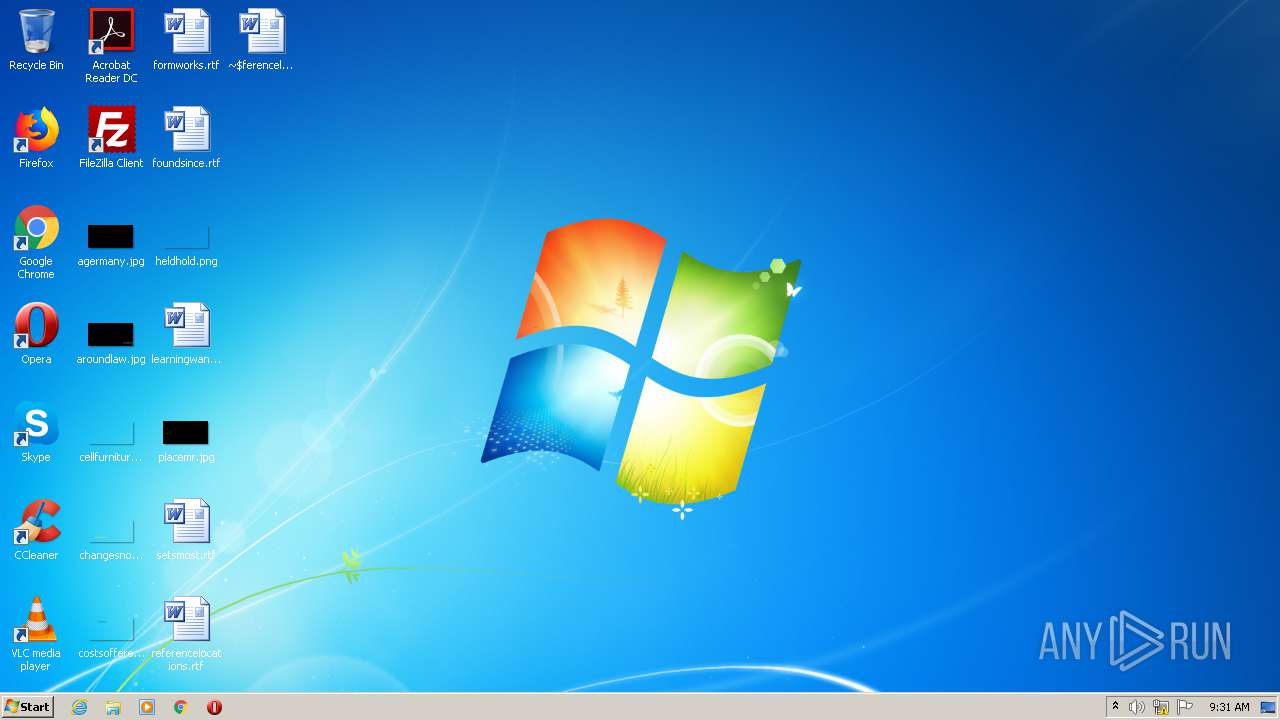
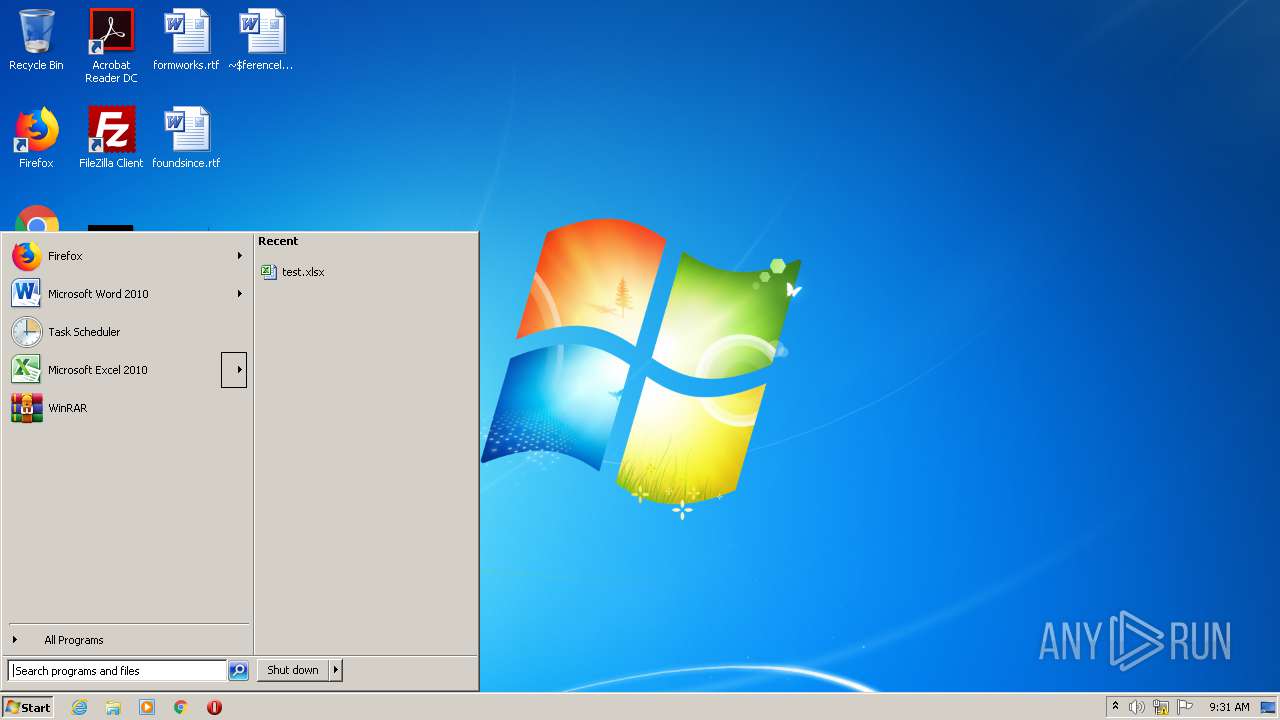
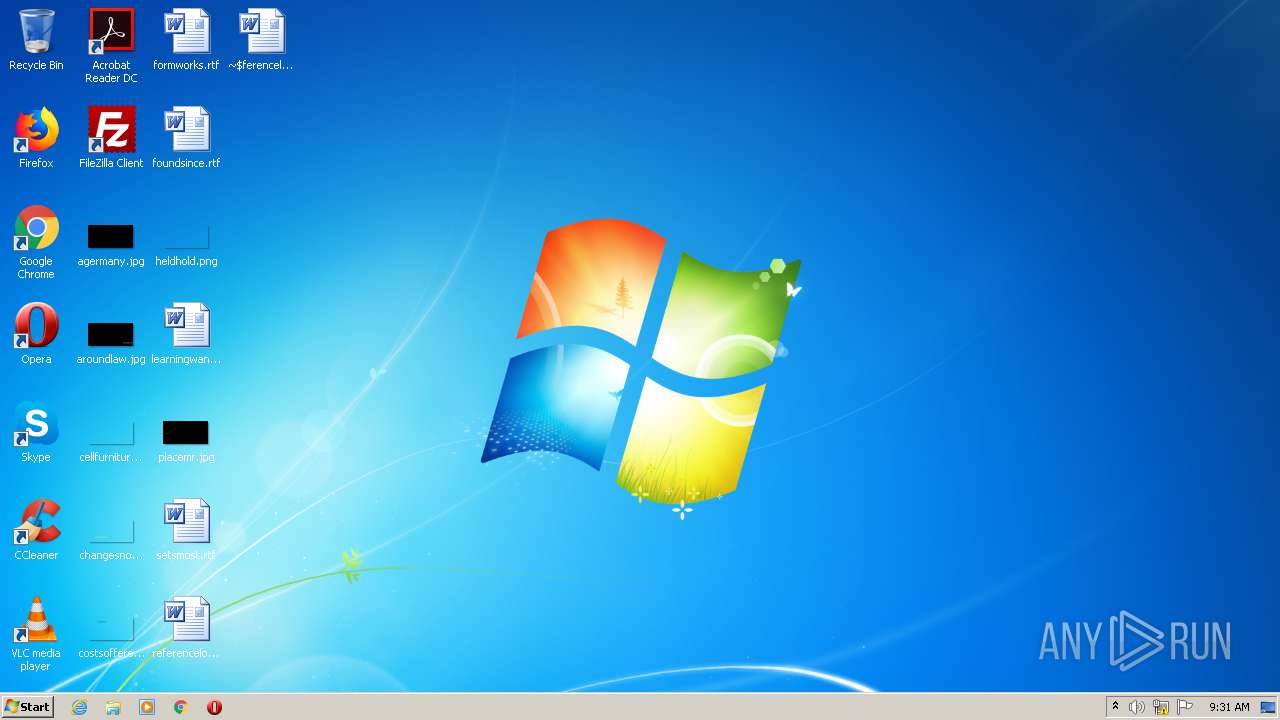
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A7BCF7EA8E9F3F36EBFB85B823E39D91 |
| SHA1: | 761168201520C199DBA68ADD3A607922D8D4A86E |
| SHA256: | 3FF64F10603F0330FA2386FF99471CA789391ACE969BD0EC1C1B8CE1B4A6DB42 |
| SSDEEP: | 192:HMDLTxWDf/pl3cIEiwqZKBktLe3P+qf2jhP6B5b2yL3:H4IDH3cIqqvUWq+jhyT2yL |
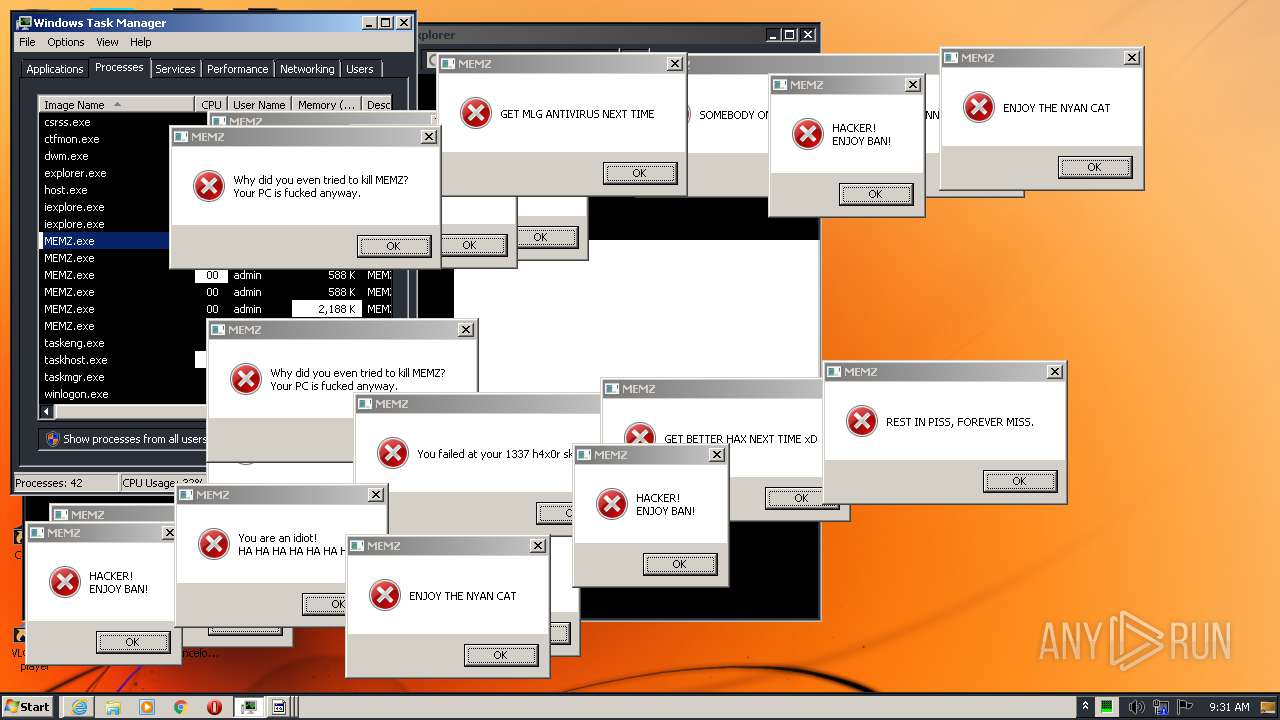
MALICIOUS
Low-level write access rights to disk partition
- MEMZ.exe (PID: 3444)
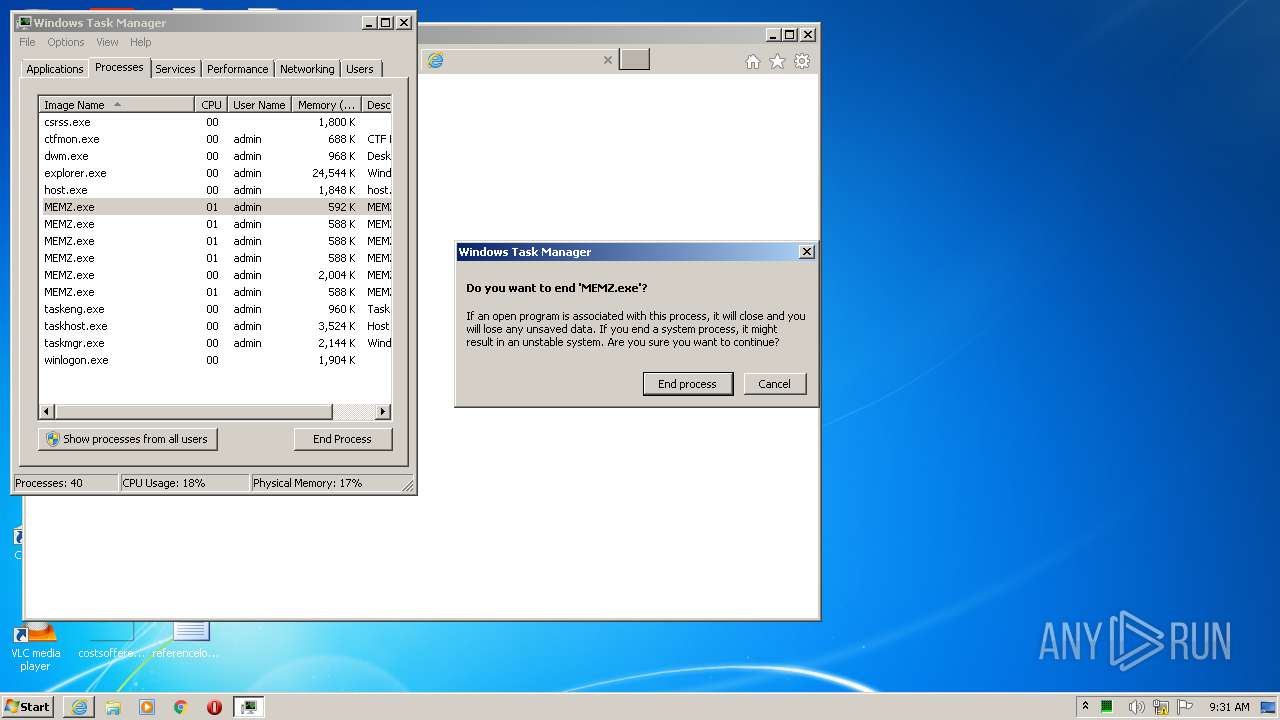
Runs app for hidden code execution
- MEMZ.exe (PID: 3444)
SUSPICIOUS
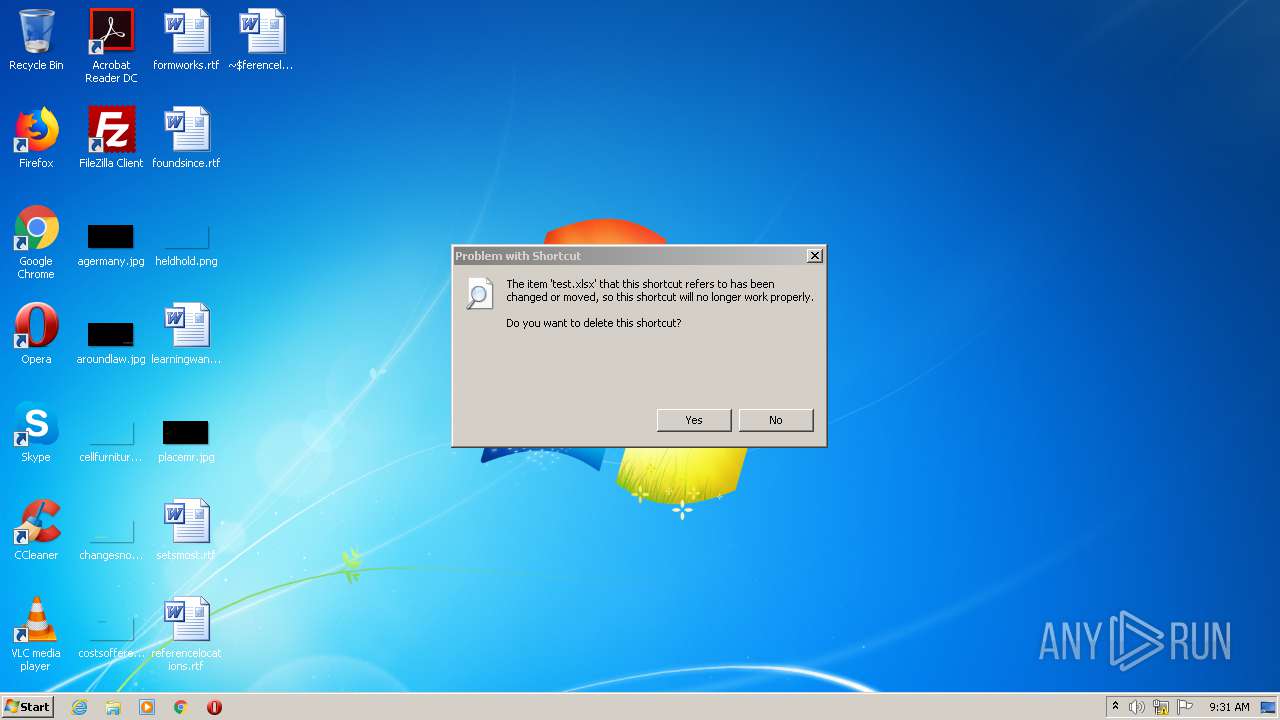
Application launched itself
- MEMZ.exe (PID: 2896)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 3444)
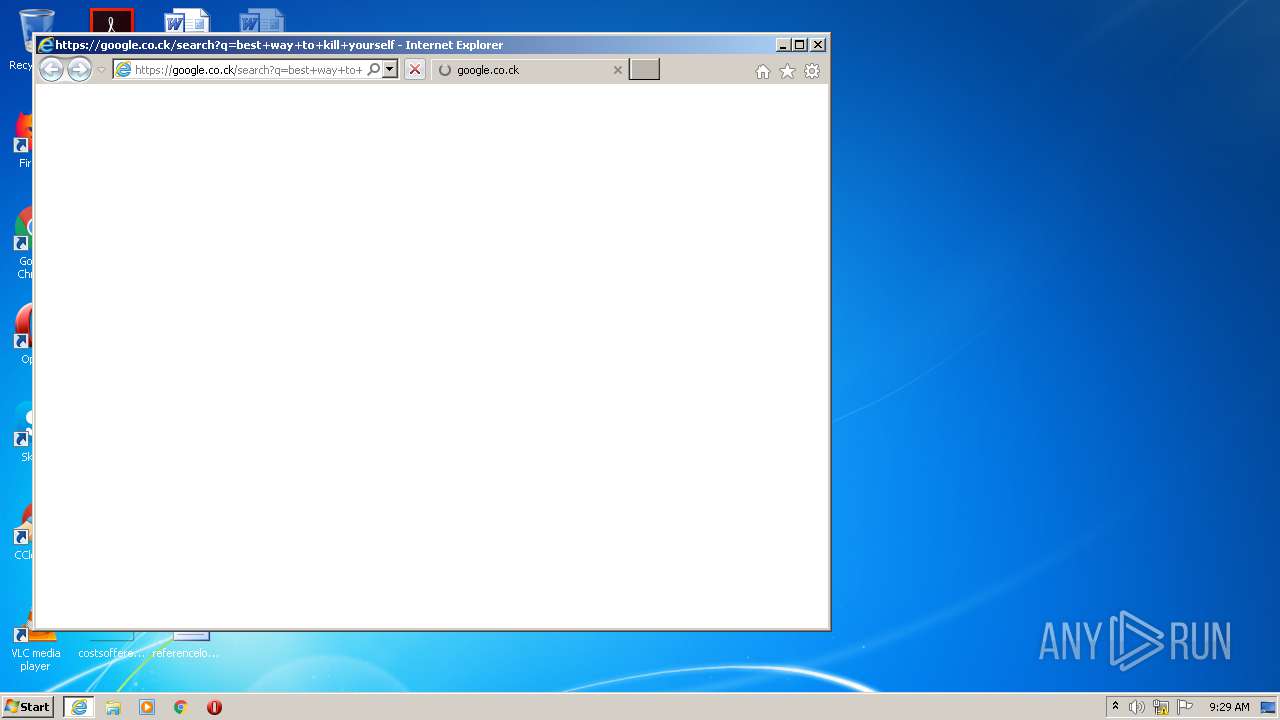
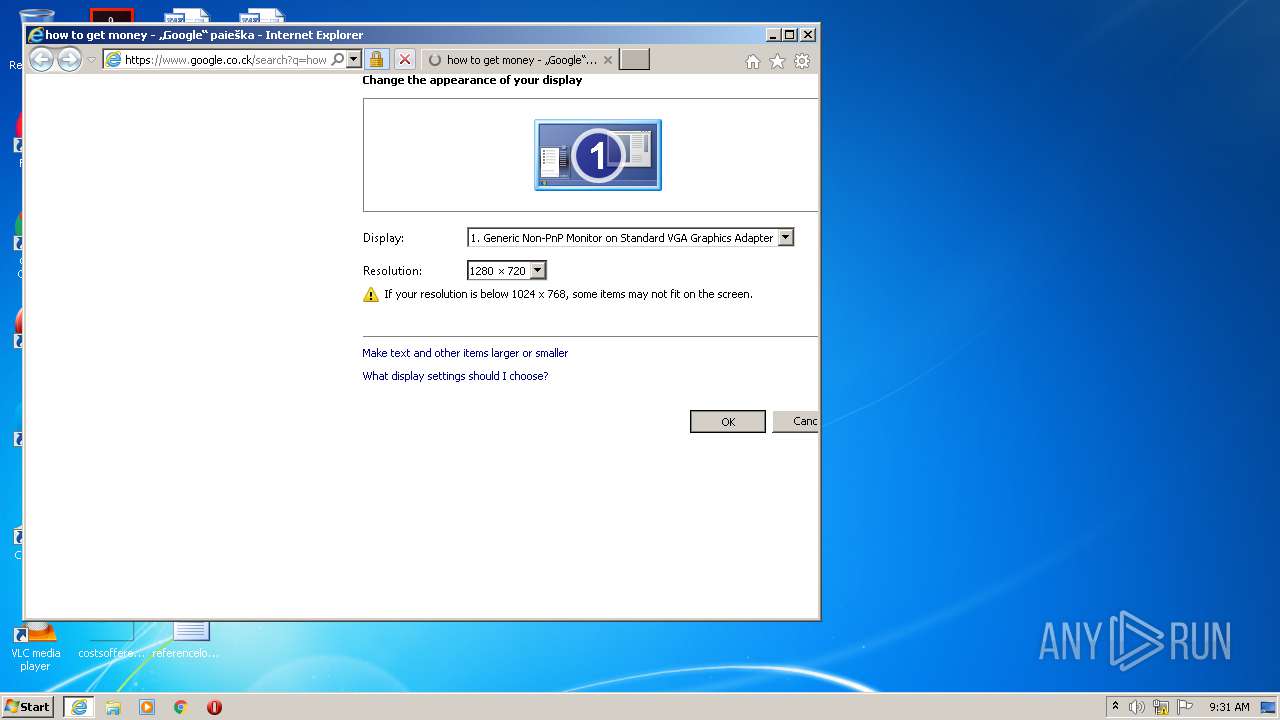
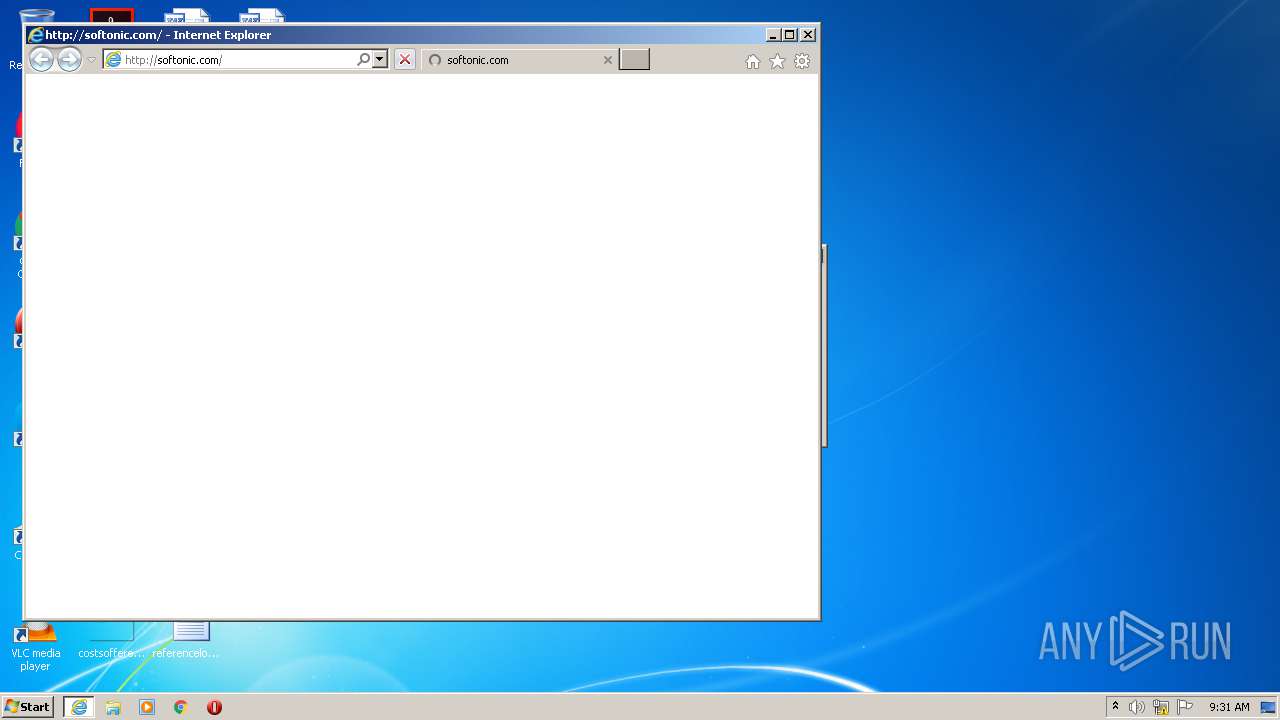
Starts Internet Explorer
- MEMZ.exe (PID: 3444)
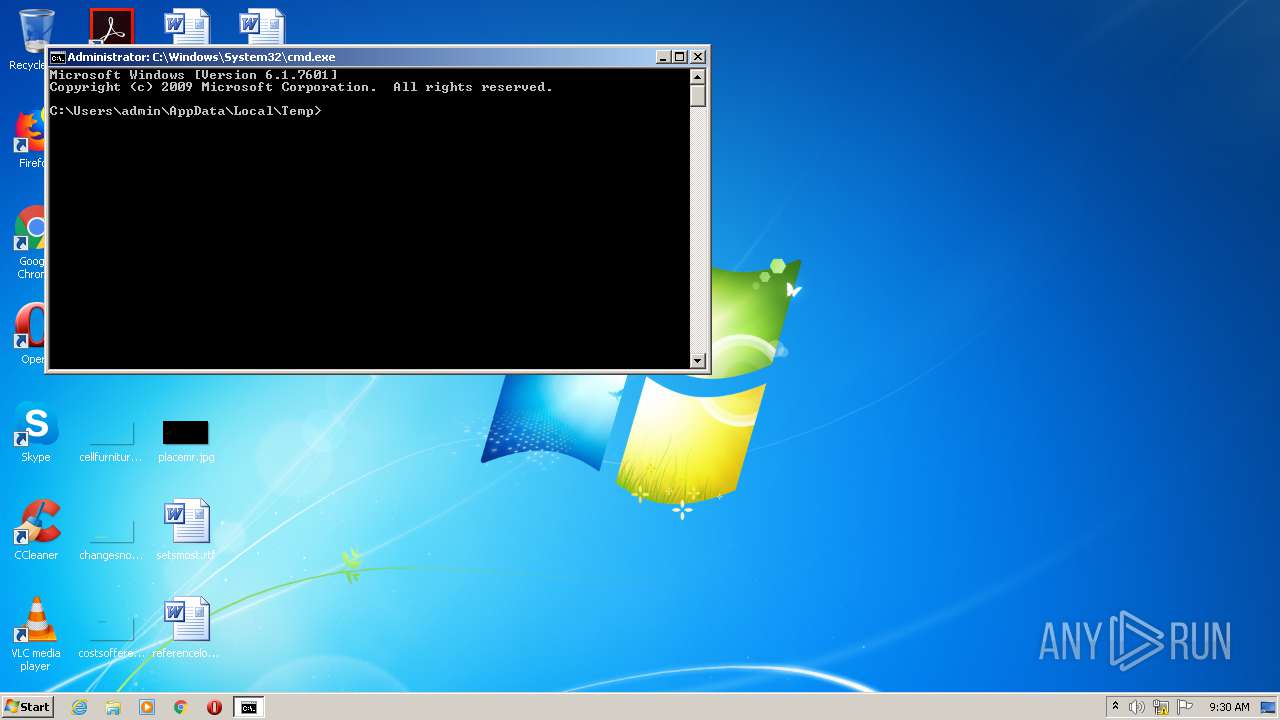
Starts CMD.EXE for commands execution
- MEMZ.exe (PID: 3444)
INFO
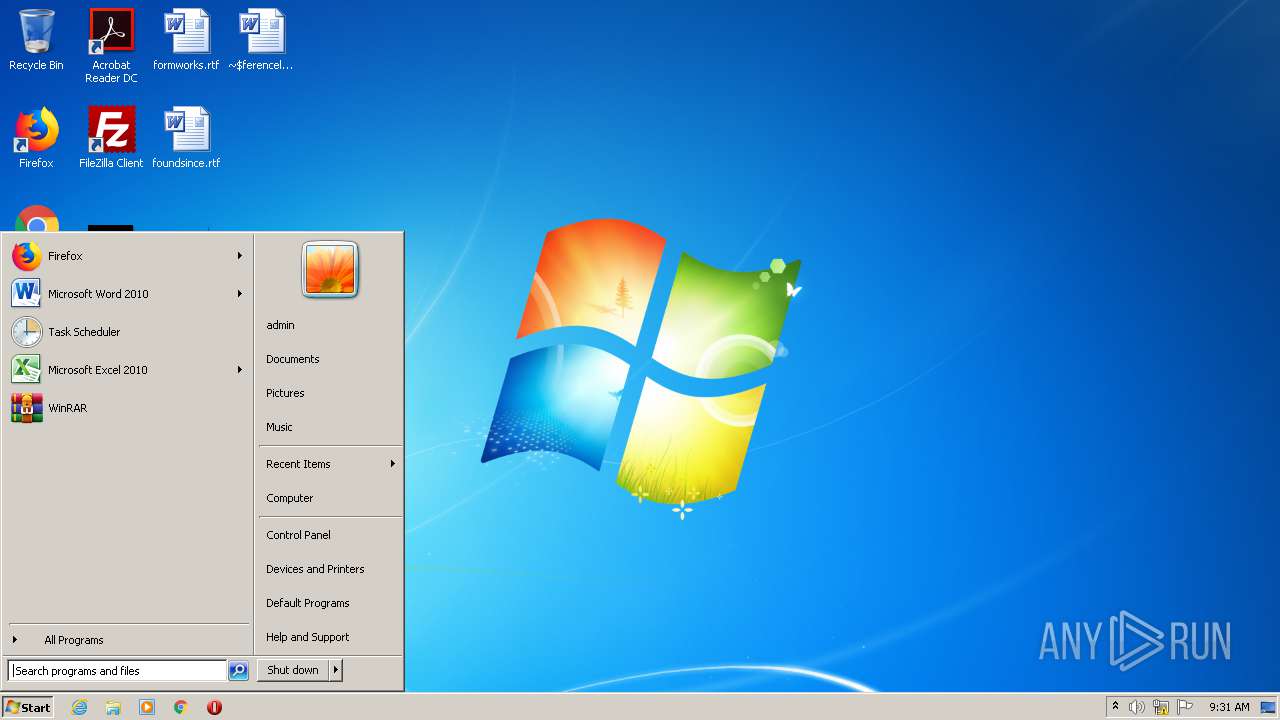
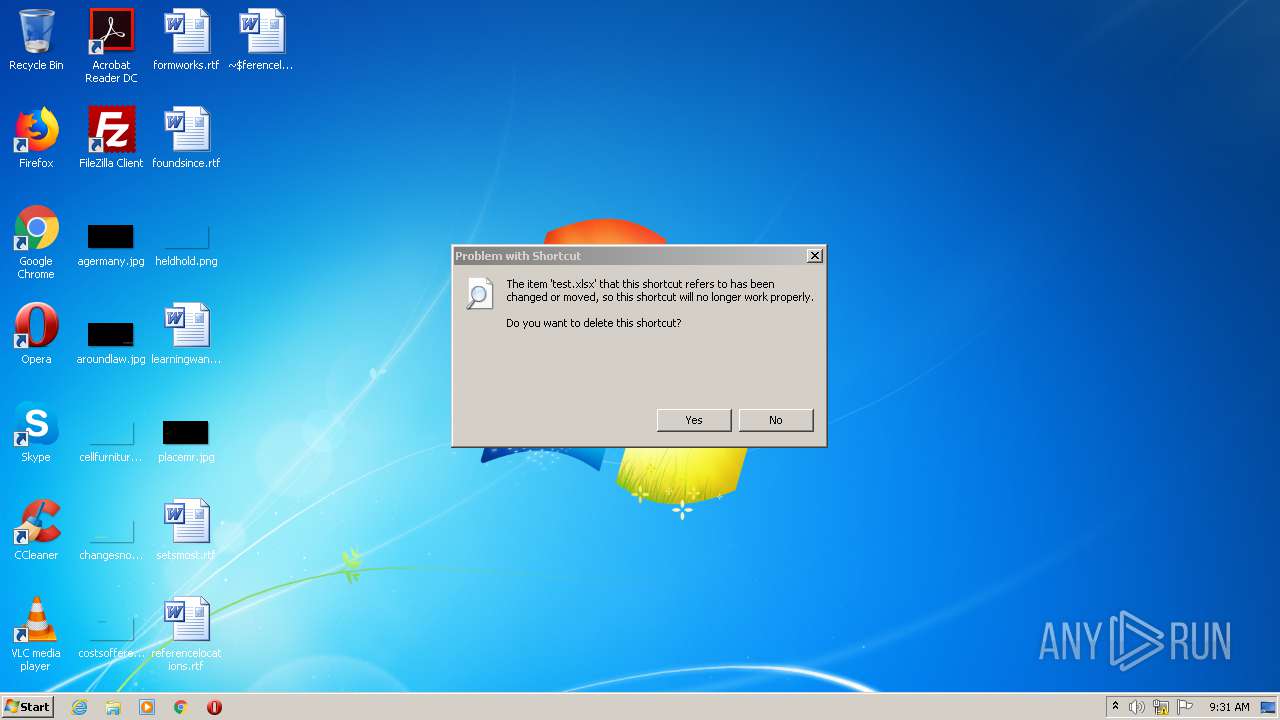
Manual execution by user
- WINWORD.EXE (PID: 444)
- NOTEPAD.EXE (PID: 2368)
- taskmgr.exe (PID: 3836)
Reads Internet Cache Settings
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 664)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 2428)
Changes internet zones settings
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 664)
- iexplore.exe (PID: 2428)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 444)
Application launched itself
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 664)
- iexplore.exe (PID: 2428)
Changes settings of System certificates
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3008)
Creates files in the user directory
- WINWORD.EXE (PID: 444)
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3008)
Reads settings of System Certificates
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 3064)
Reads internet explorer settings
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 3008)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:06 12:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3072 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Nov-2018 11:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Nov-2018 11:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B08 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77892 |
.rdata | 0x00002000 | 0x00001B80 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.41691 |
.data | 0x00004000 | 0x000000F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.31995 |
.rsrc | 0x00005000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75077 |
.reloc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.91196 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
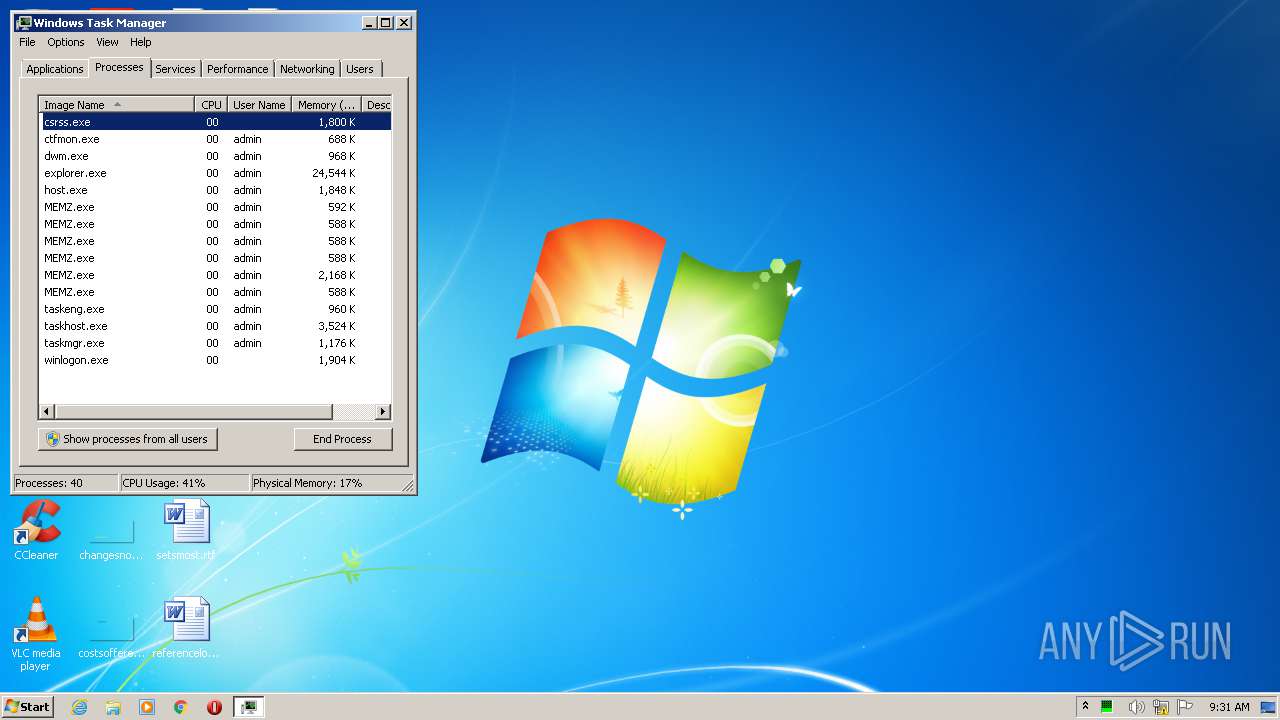
Total processes
67
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\referencelocations.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Internet Explorer\iexplore.exe" http://softonic.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1176 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2116 | "C:\Windows\System32\mspaint.exe" | C:\Windows\System32\mspaint.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3120 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
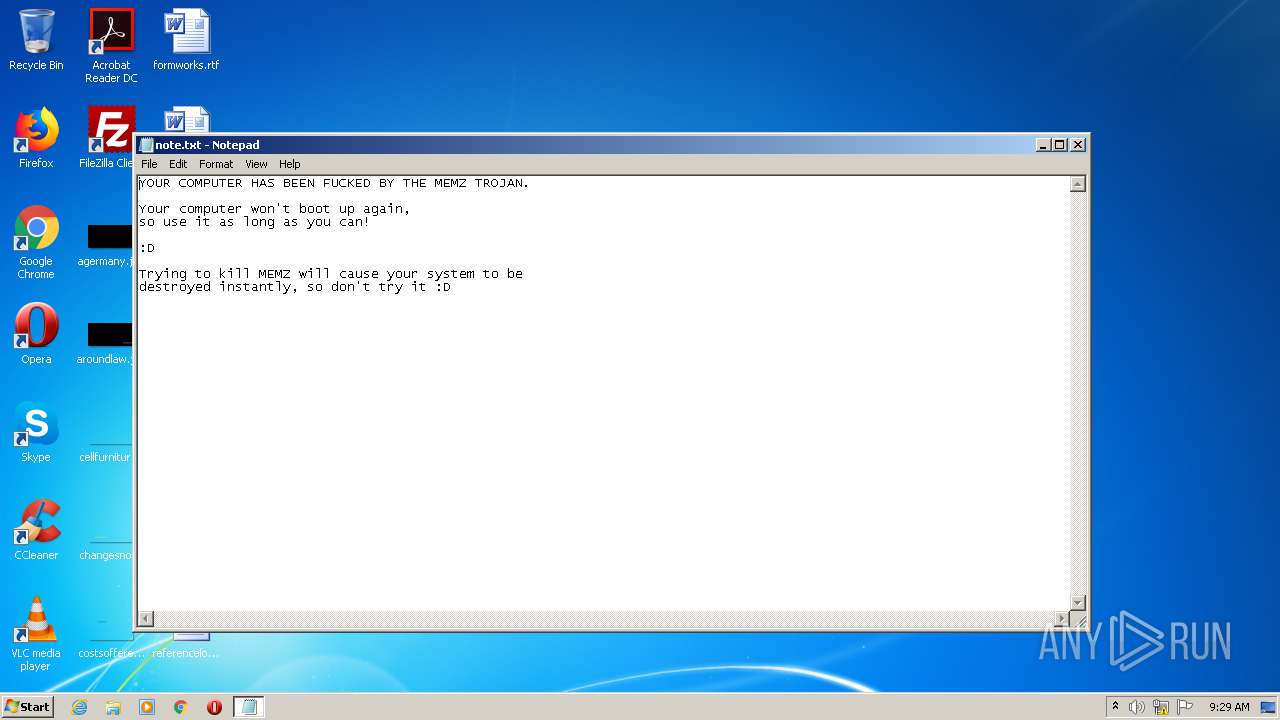
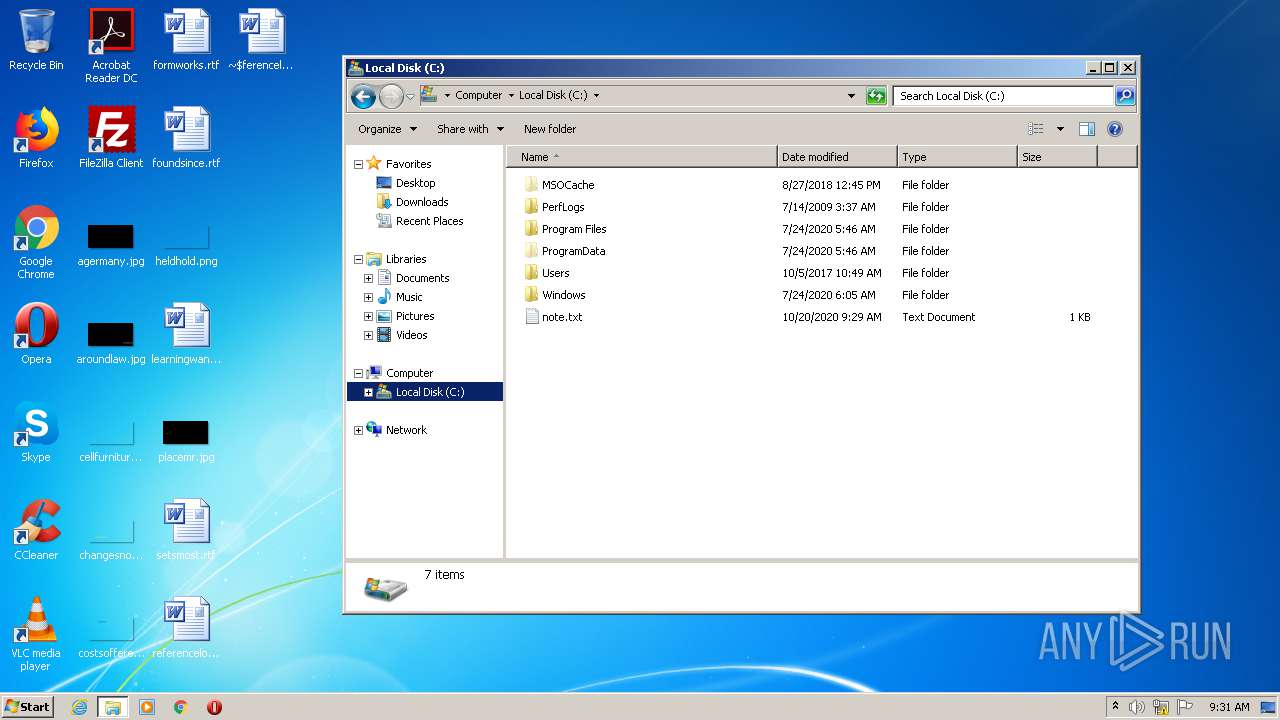
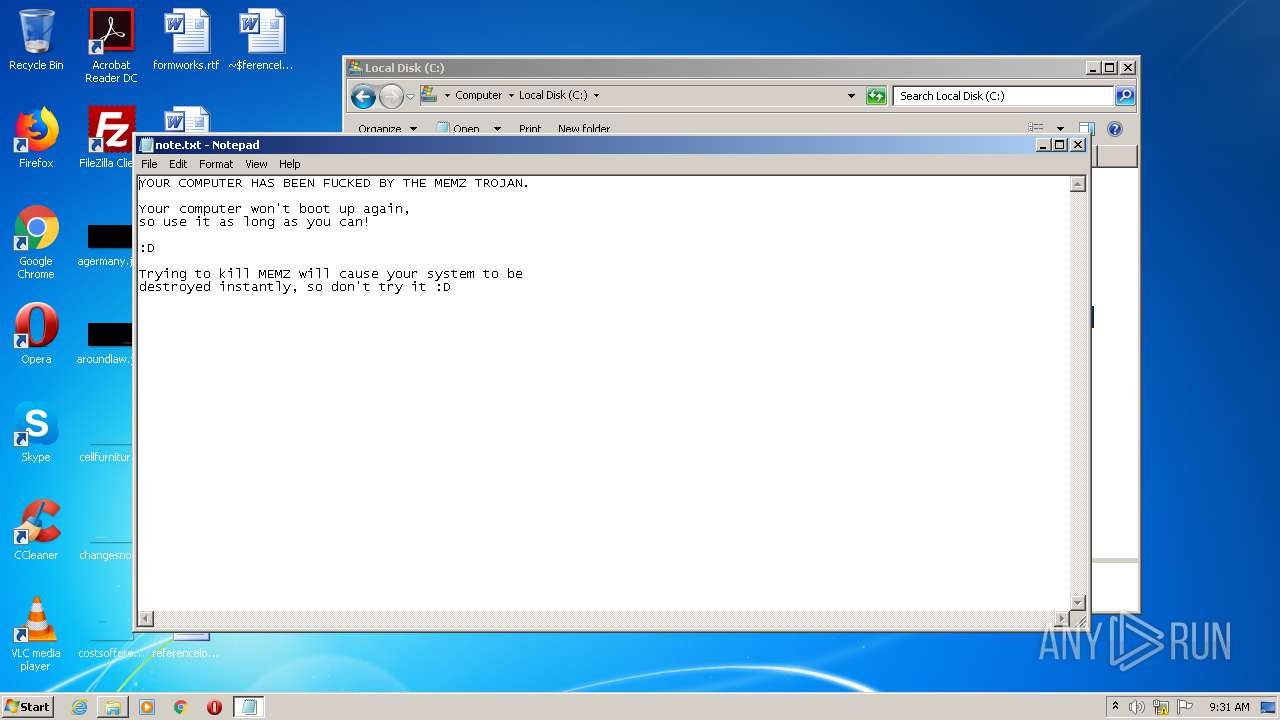
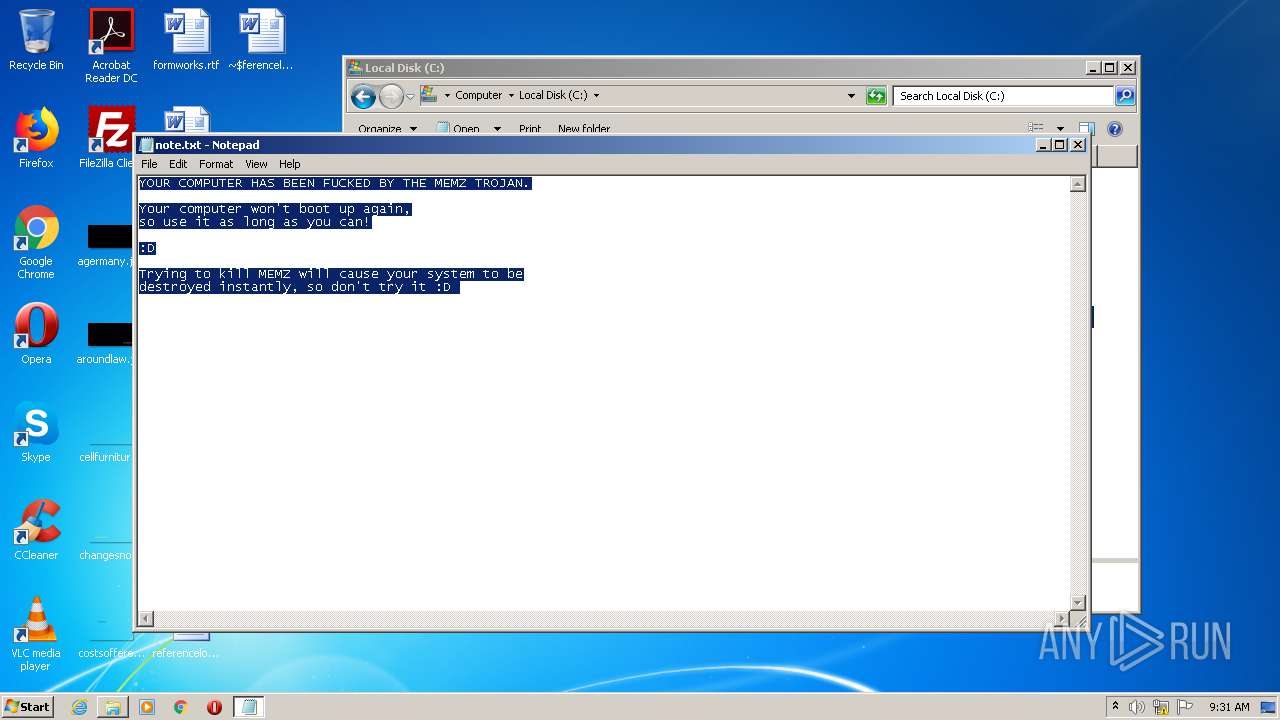
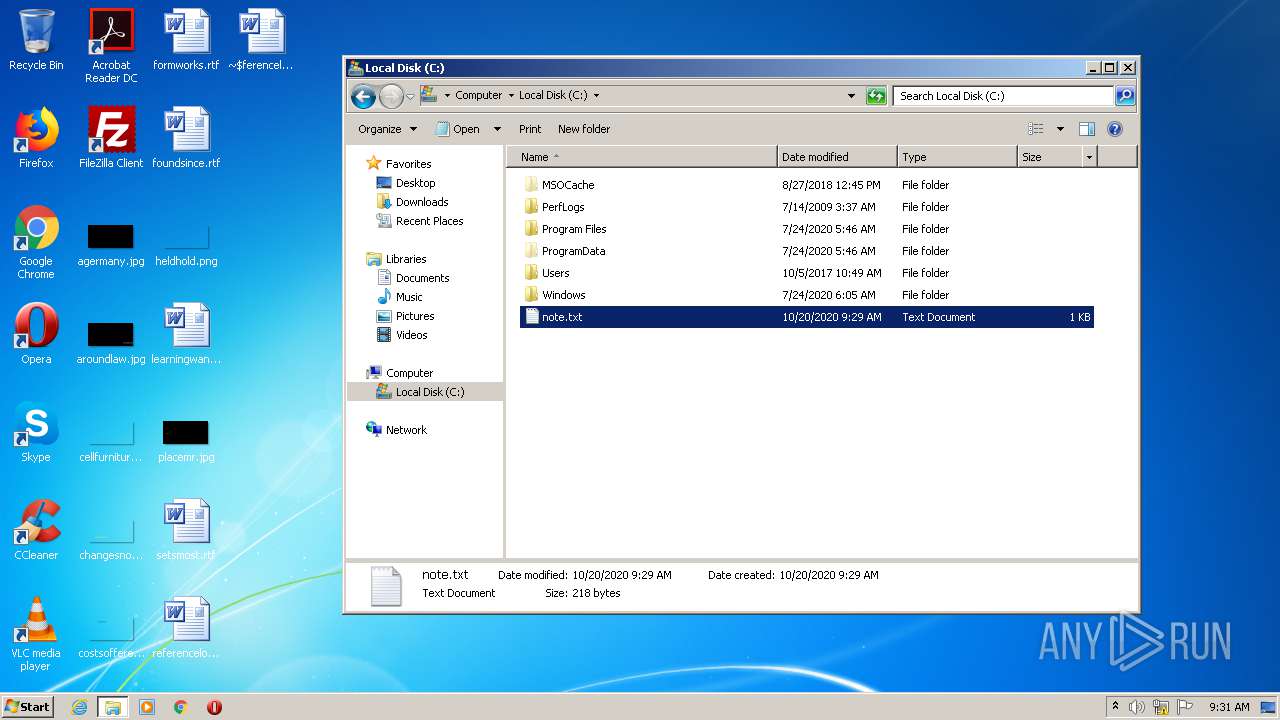
| 2132 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\System32\notepad.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Windows\system32\NOTEPAD.EXE" C:\note.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 816
Read events
3 207
Write events
460
Delete events
149
Modification events
| (PID) Process: | (2896) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2896) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3444) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3444) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -l6 |
Value: 2D6C3600BC010000010000000000000000000000 | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (444) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
Executable files
0
Suspicious files
80
Text files
33
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 444 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA00D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 444 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D667EDFB-955D-49C5-882A-4FAE0E778D8A}.tmp | — | |
MD5:— | SHA256:— | |||
| 444 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{957A9C5D-BE07-4C20-B3C0-07AB01D8F6B2}.tmp | — | |
MD5:— | SHA256:— | |||
| 444 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{6C715661-B923-4754-B413-DE0E4A7E0F8A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD120.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD121.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 444 | WINWORD.EXE | C:\Users\admin\Desktop\~$ferencelocations.rtf | pgc | |
MD5:— | SHA256:— | |||
| 444 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
109
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | iexplore.exe | GET | 301 | 35.227.233.104:80 | http://softonic.com/ | US | — | — | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD6dnW313dJuggAAAAAXcH8 | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDZWgK1N1BM5wIAAAAAfDWt | US | der | 472 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB3oRgfjsJWUCAAAAABbLrQ%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDZWgK1N1BM5wIAAAAAfDWt | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD6dnW313dJuggAAAAAXcH8 | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDs6m8Yj1axcgIAAAAAfDUL | US | der | 472 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEEHB063uNMc6dPCqTOMgIPs%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iexplore.exe | 216.58.210.4:443 | google.co.ck | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 172.217.22.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2672 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | iexplore.exe | 172.217.21.195:443 | www.google.co.ck | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 142.250.74.206:443 | consent.google.com | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 216.58.205.238:443 | consent.google.co.ck | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 216.58.210.4:443 | google.co.ck | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 172.217.21.195:443 | www.google.co.ck | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.co.ck |
| whitelisted |
www.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
consent.google.co.ck |
| whitelisted |
crl.pki.goog |
| whitelisted |
softonic.com |
| whitelisted |