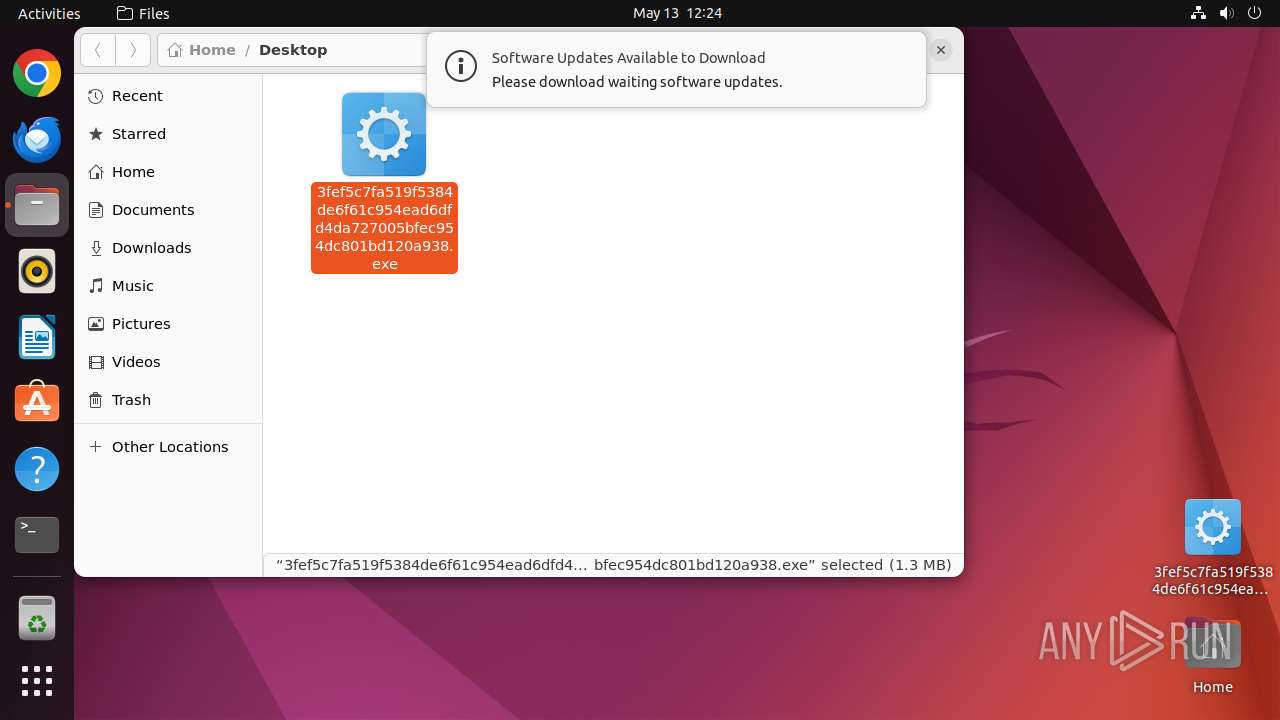
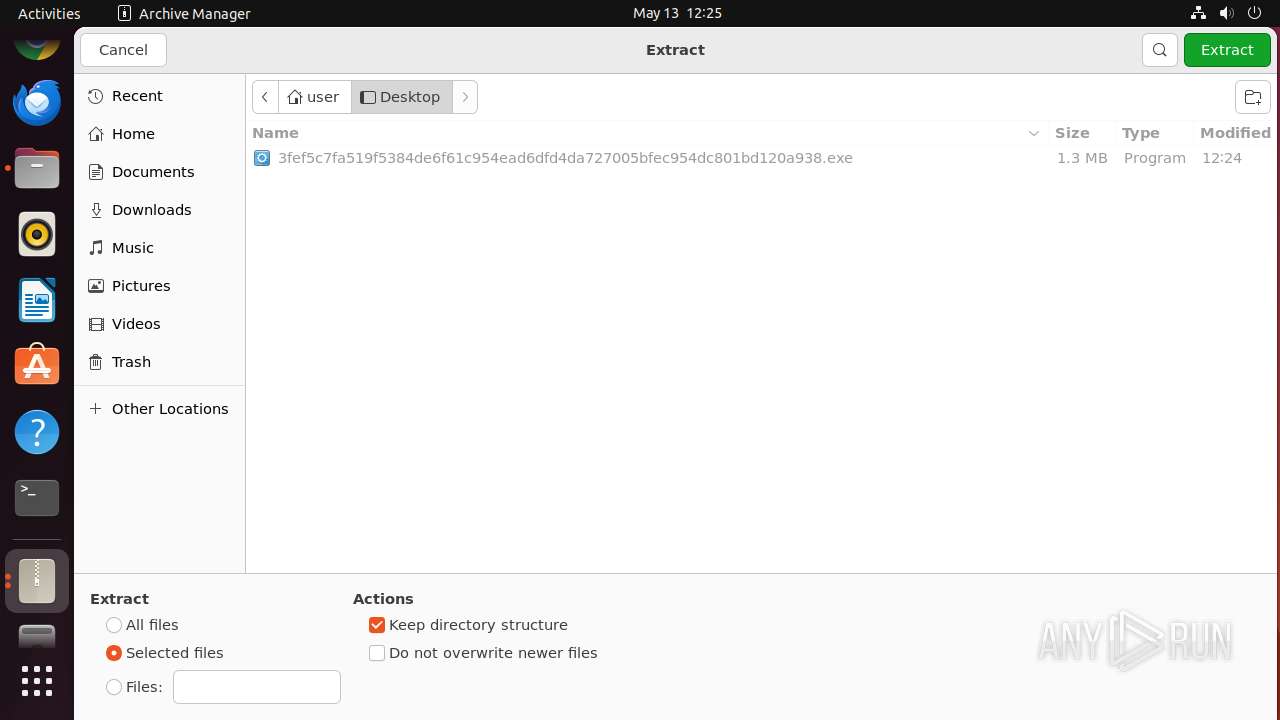
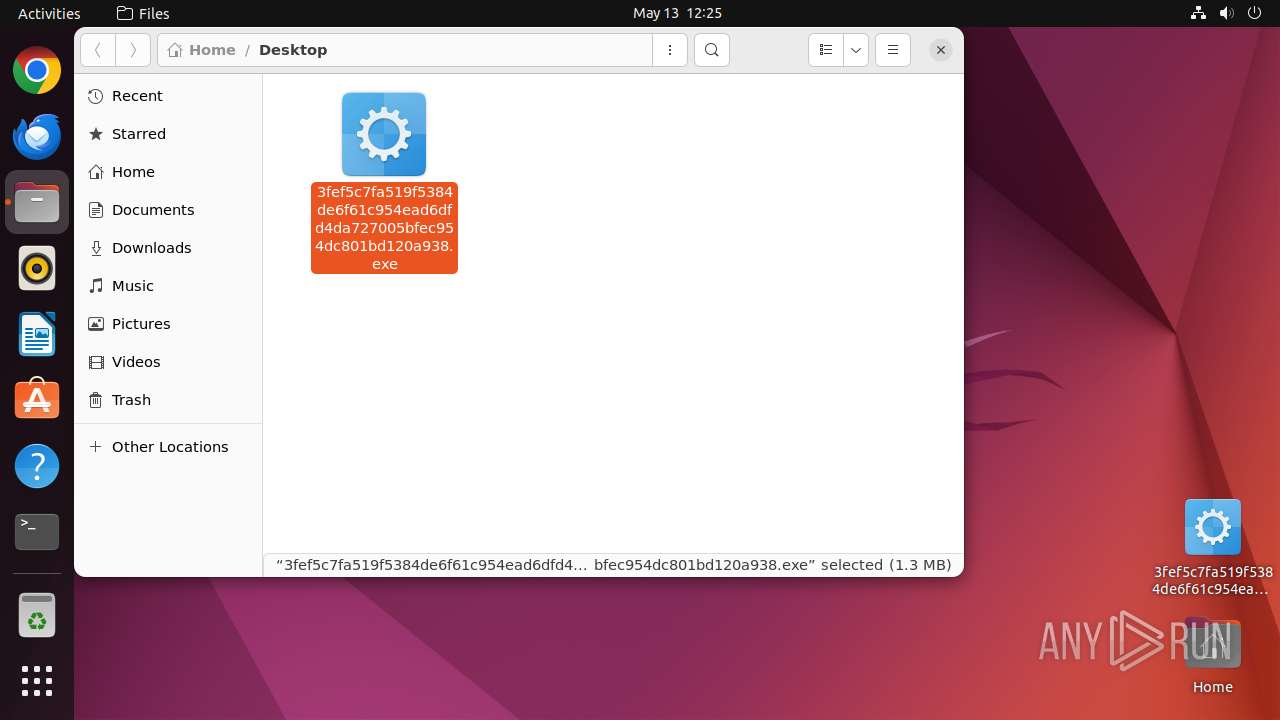
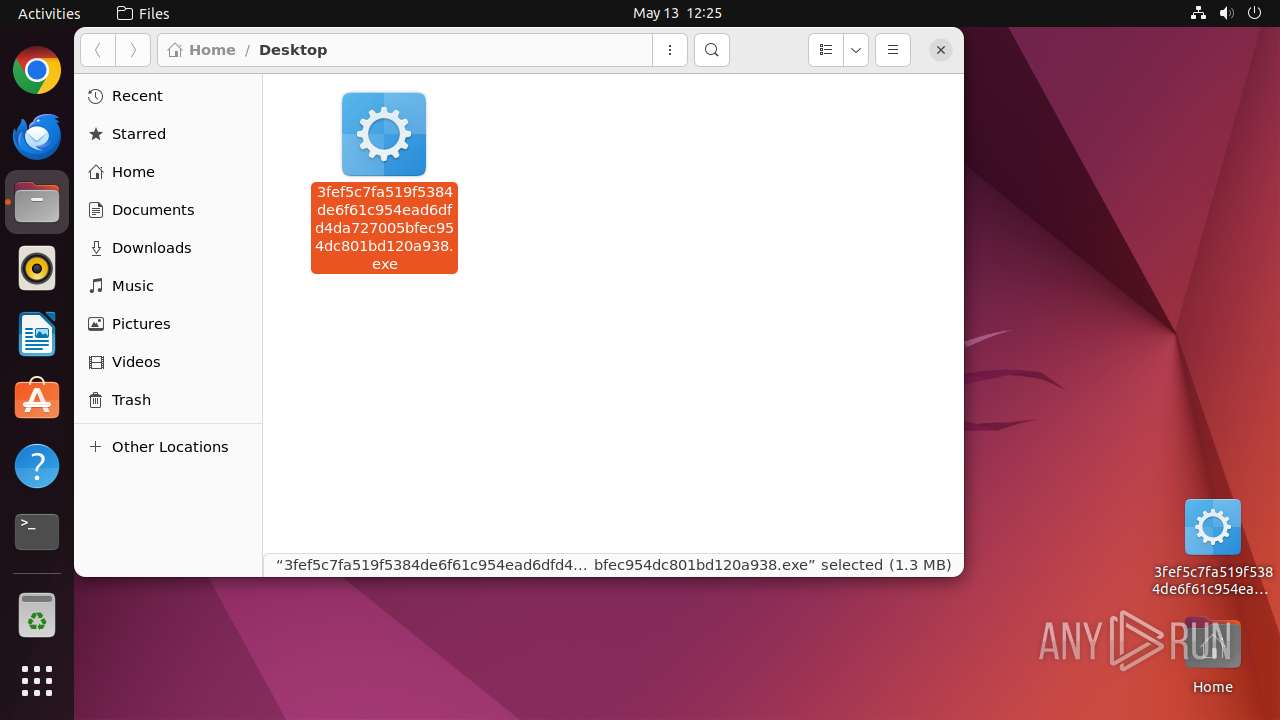
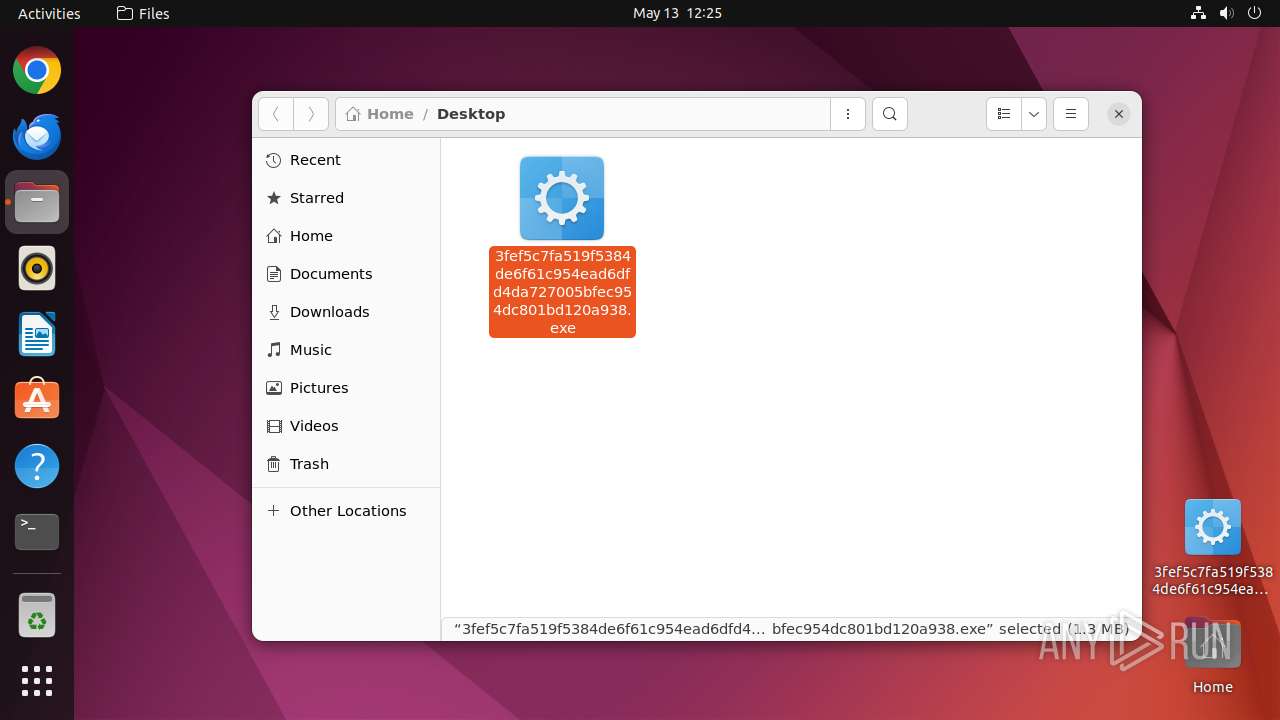
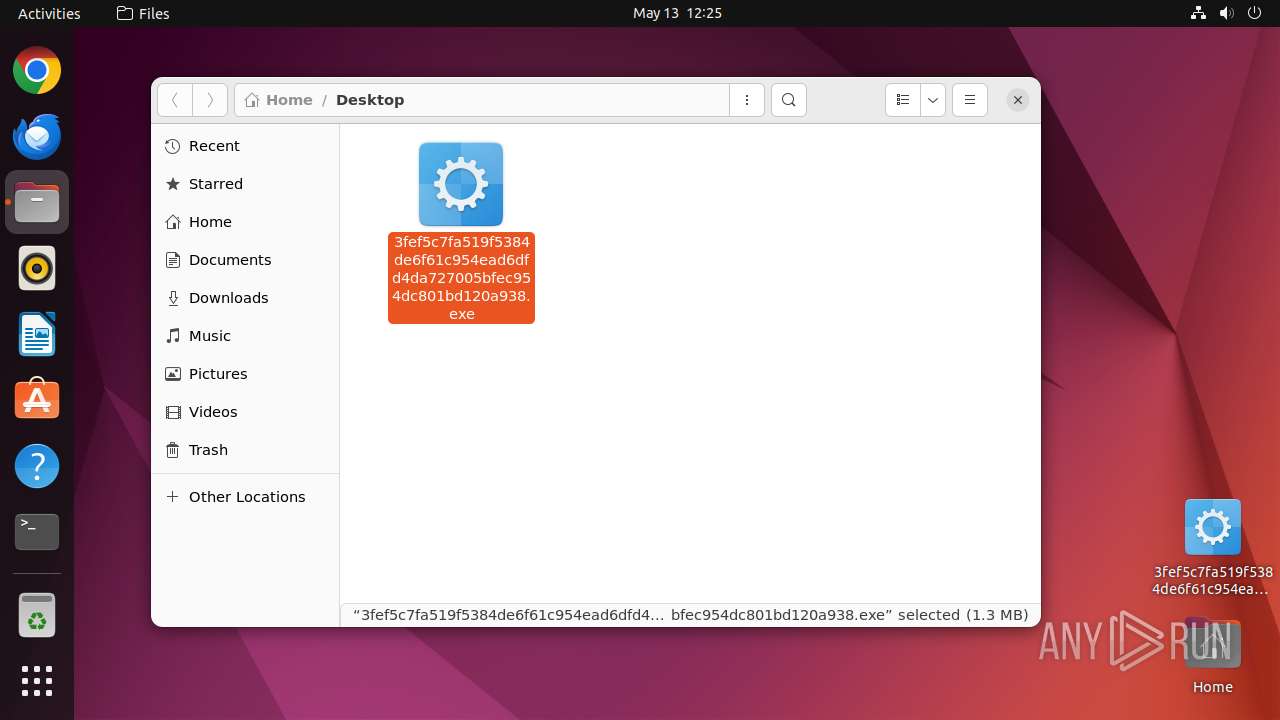
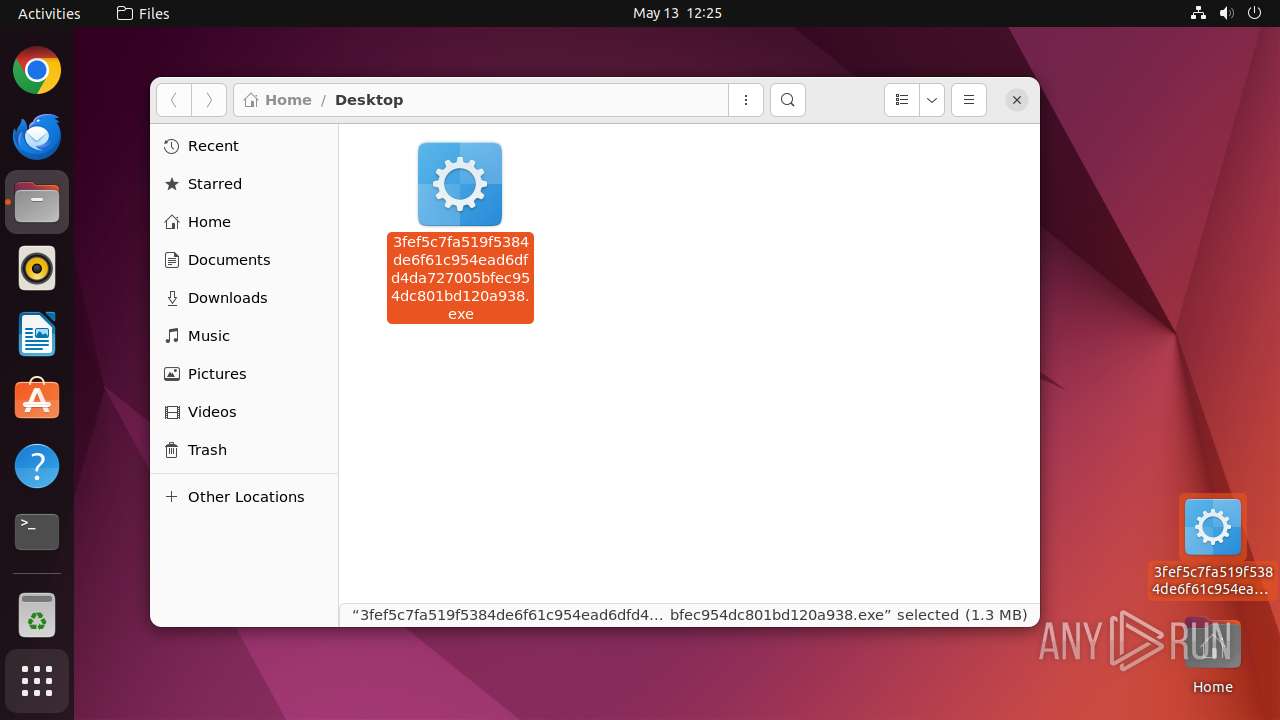
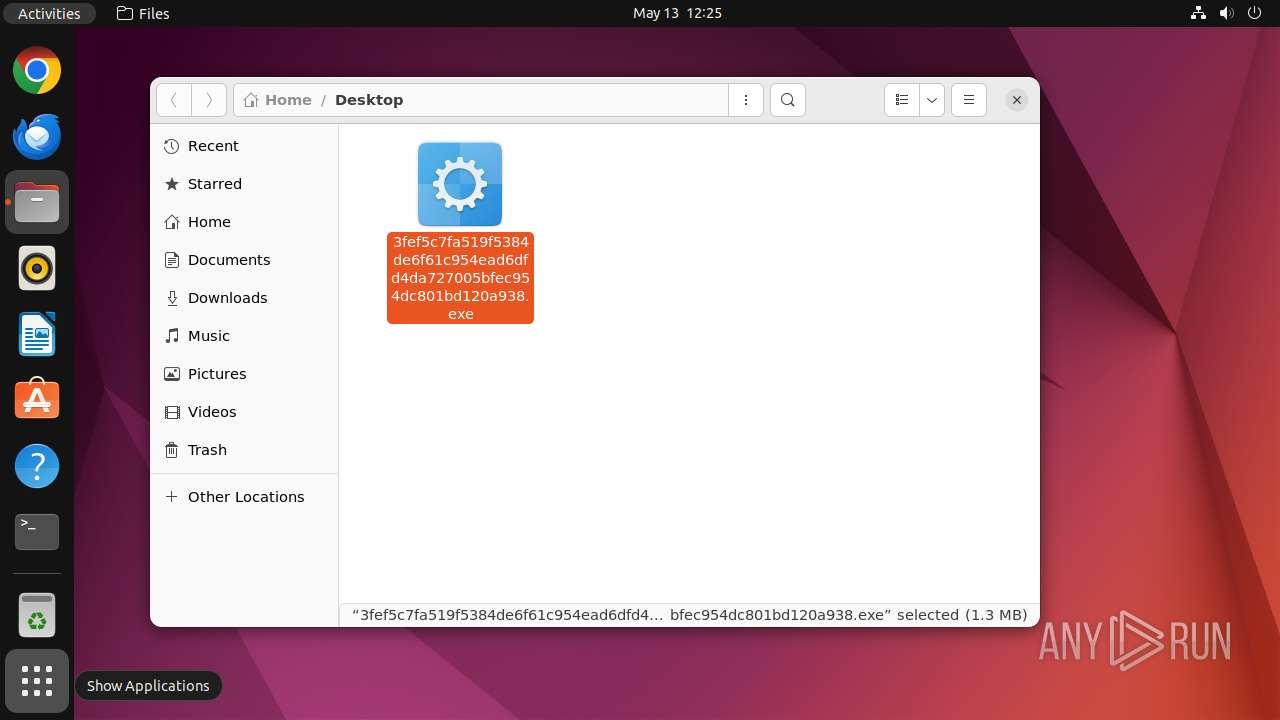
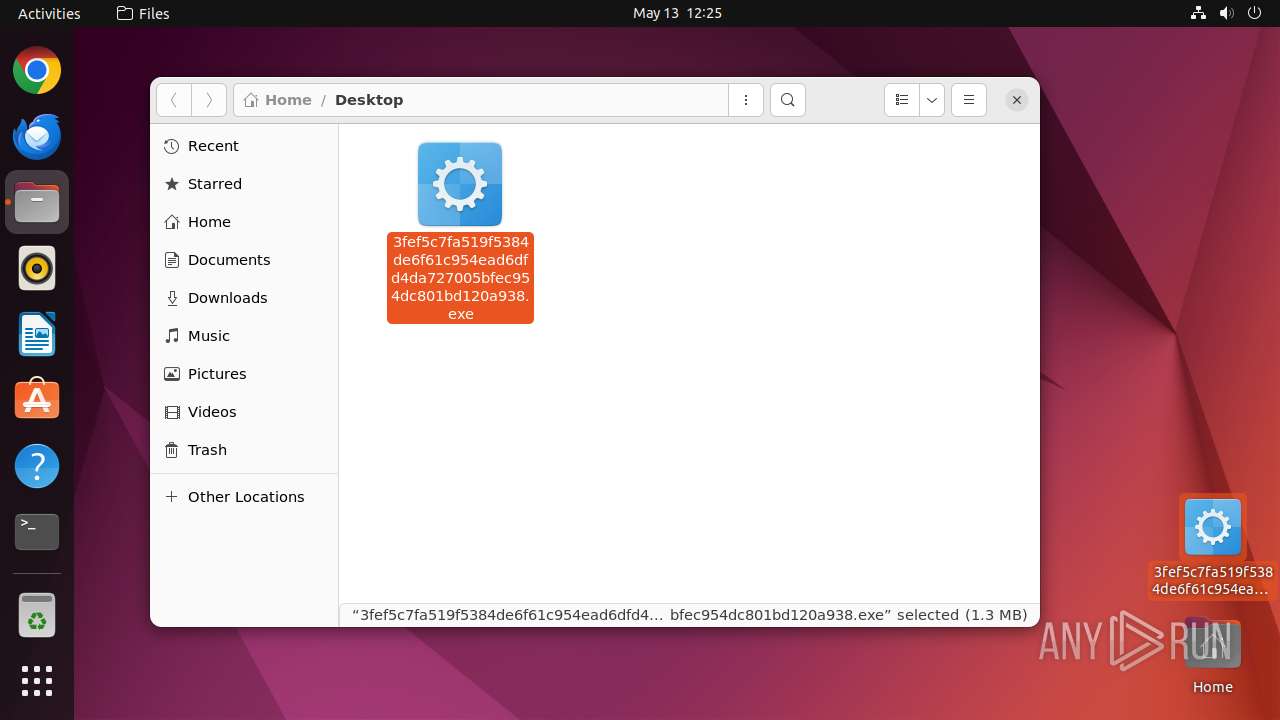
| File name: | 3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938.exe |
| Full analysis: | https://app.any.run/tasks/77bea0e6-3934-4394-81b1-6c759e609933 |
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2025, 11:24:50 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
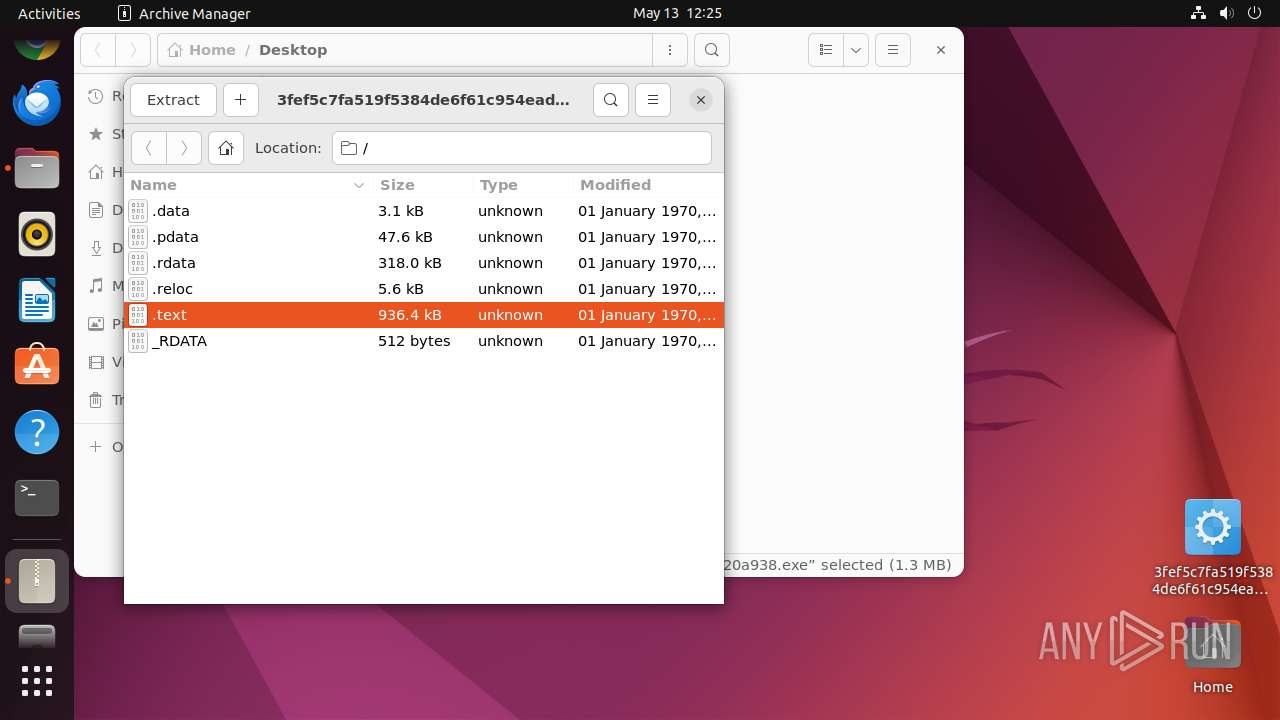
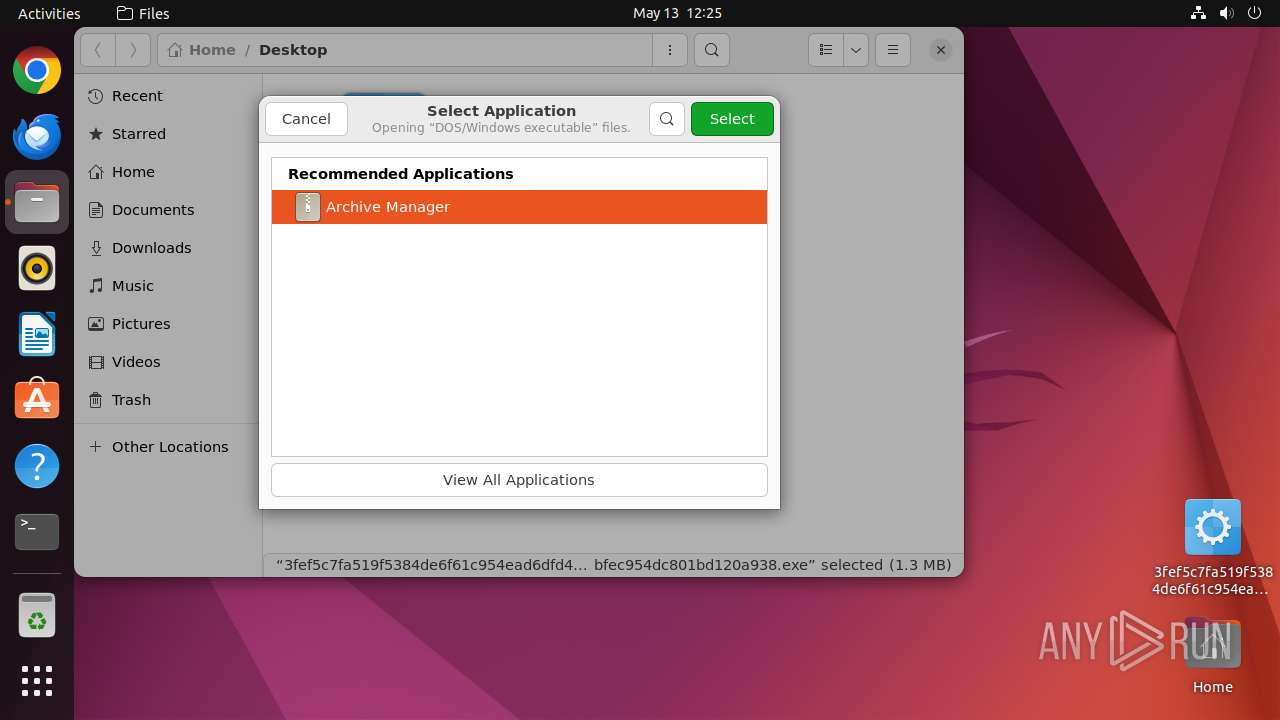
| MIME: | application/vnd.microsoft.portable-executable |
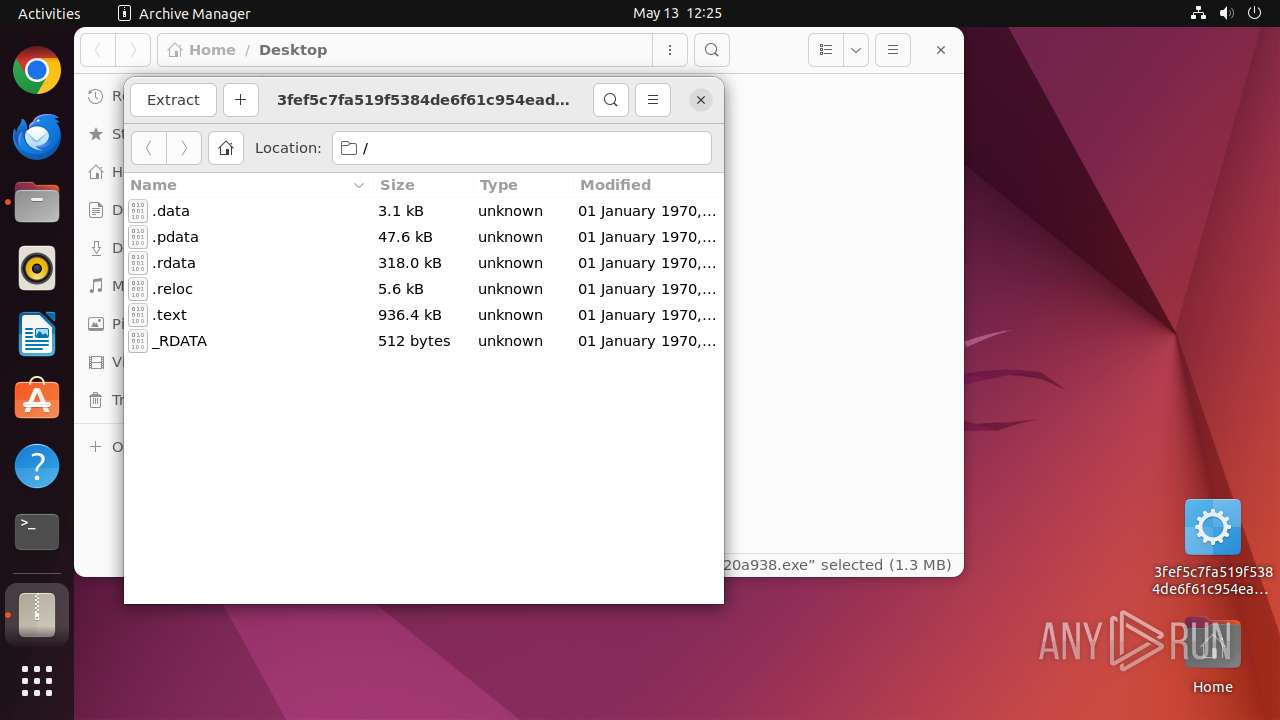
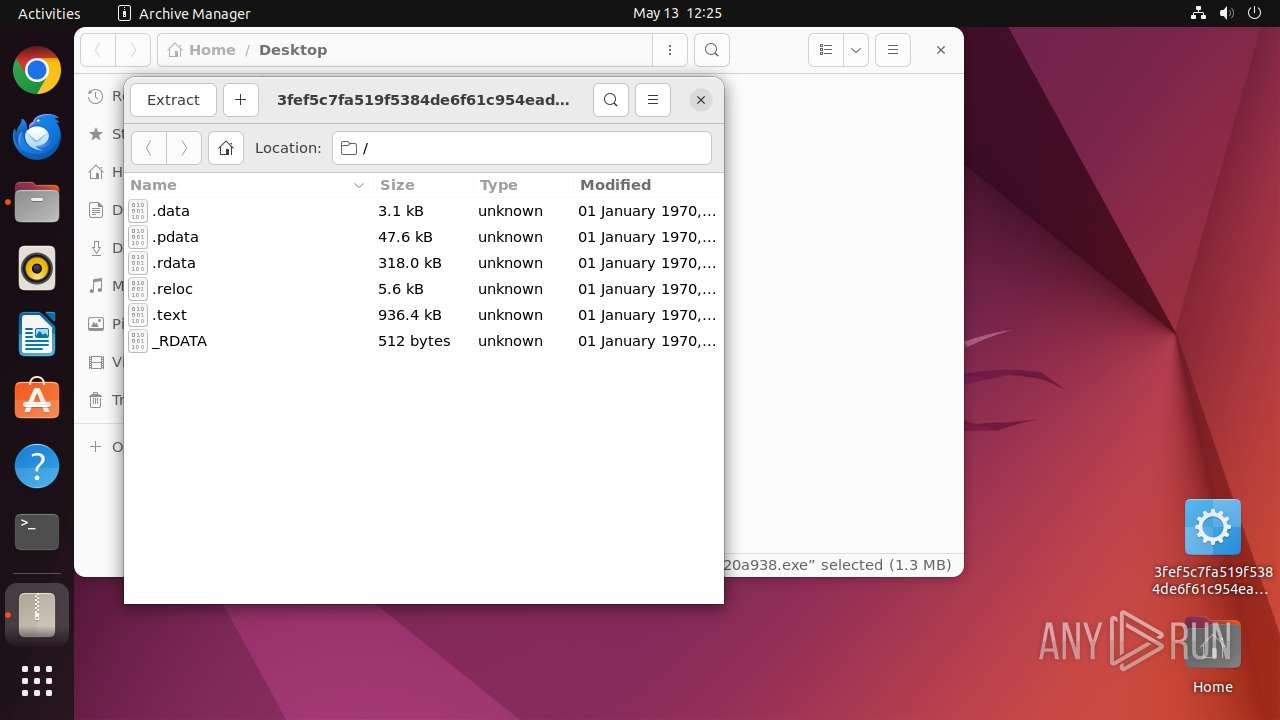
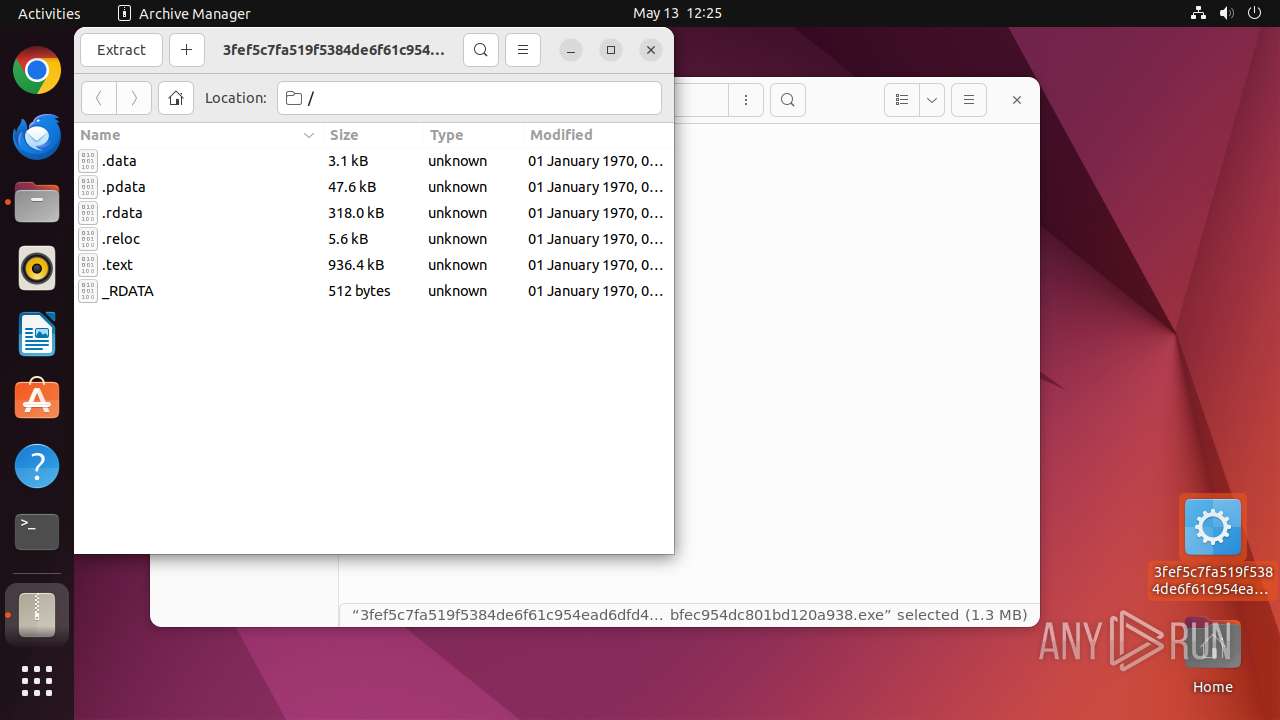
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | D69EBD183B2E0072C396E55503D5EDE7 |
| SHA1: | 901FB343F20CA85CE3A68C7EDB2D4658FFCFEA0A |
| SHA256: | 3FEF5C7FA519F5384DE6F61C954EAD6DFD4DA727005BFEC954DC801BD120A938 |
| SSDEEP: | 49152:MhIrcSO26tw3HSc8/qlvnQqjUD7AxRmCW:m/qdNUV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads profile file
- nautilus (PID: 39508)
Executes commands using command-line interpreter
- sudo (PID: 39507)
Reads passwd file
- whoopsie (PID: 39627)
- whoopsie (PID: 39636)
INFO
Checks timezone
- 7z (PID: 39582)
- file-roller (PID: 39536)
- file-roller (PID: 39567)
- 7z (PID: 39551)
- 7z (PID: 39621)
- python3.10 (PID: 39632)
- whoopsie (PID: 39636)
- python3.10 (PID: 39640)
- file-roller (PID: 39651)
- whoopsie (PID: 39627)
- 7z (PID: 39583)
- 7z (PID: 39684)
- 7z (PID: 39665)
- python3.10 (PID: 39634)
- file-roller (PID: 39671)
- python3.10 (PID: 39642)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
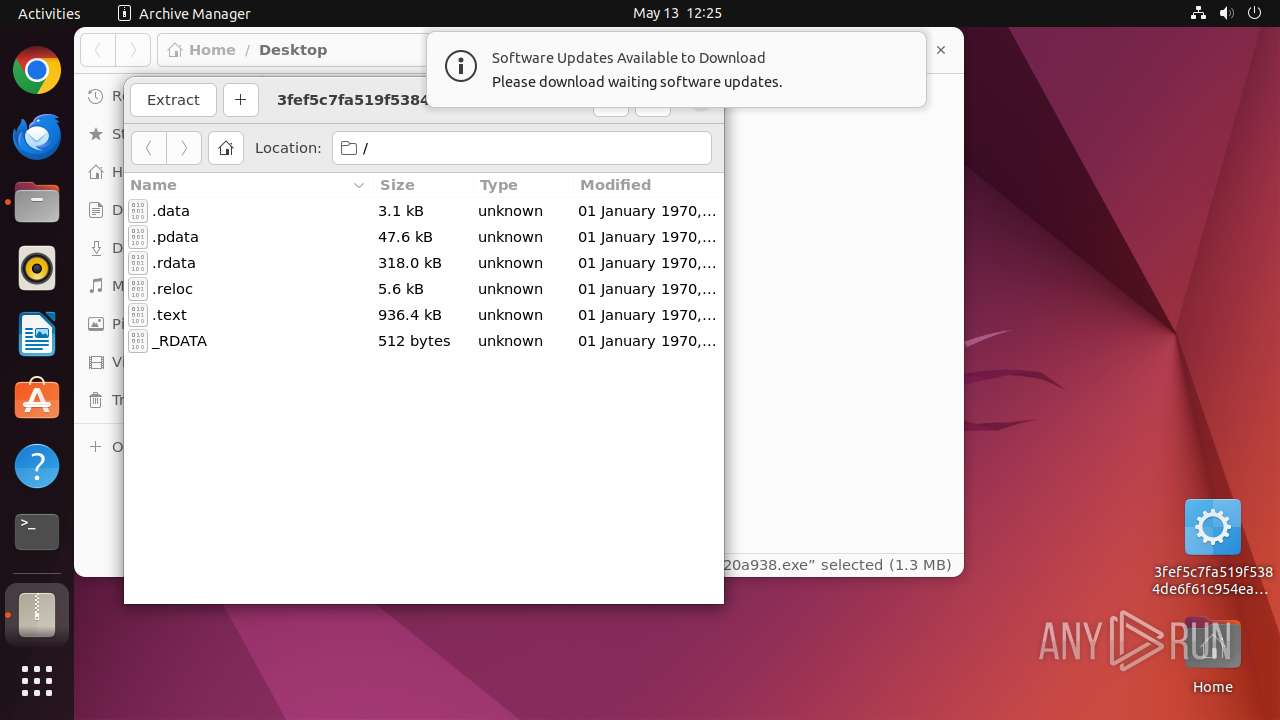
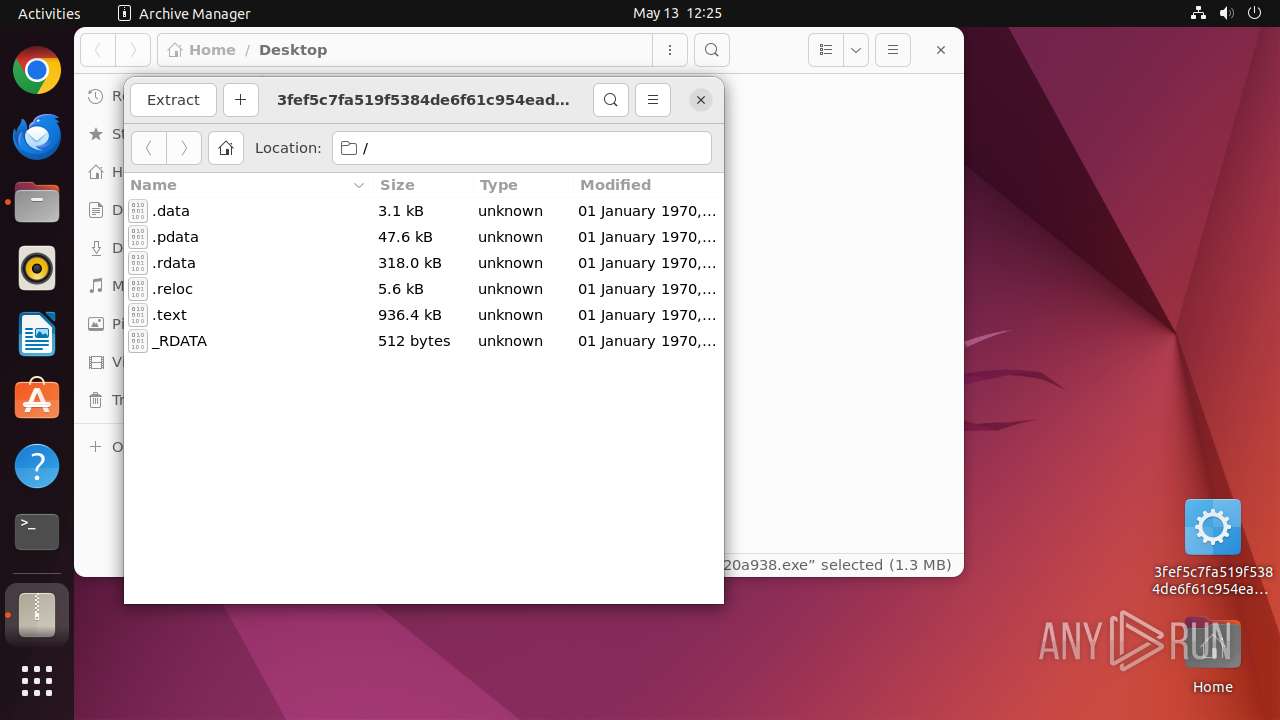
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:03 18:50:17+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 936448 |
| InitializedDataSize: | 388608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd235c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
261
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
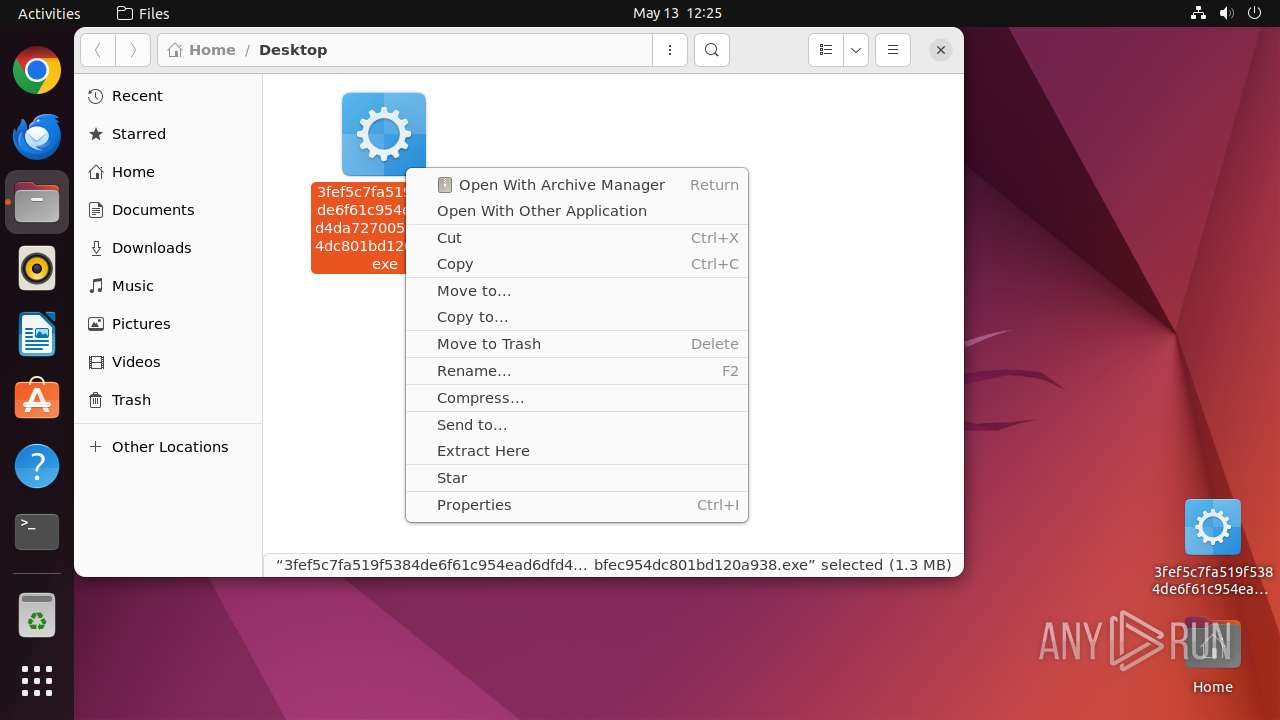
| 39506 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /home/user/Desktop/3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938\.exe " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 39507 | sudo -iu user nautilus /home/user/Desktop/3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938.exe | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39508 | nautilus /home/user/Desktop/3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39509 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39510 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39517 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39518 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39525 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39535 | nautilus /home/user/Desktop/3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938.exe | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
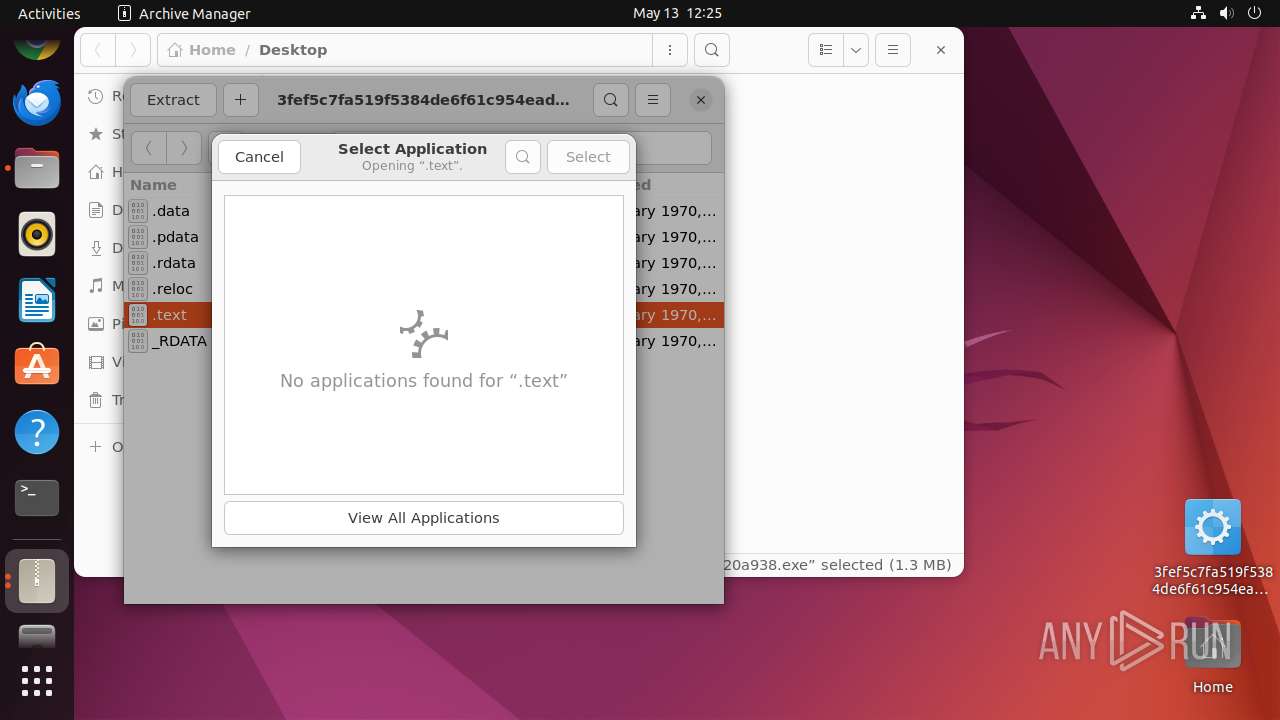
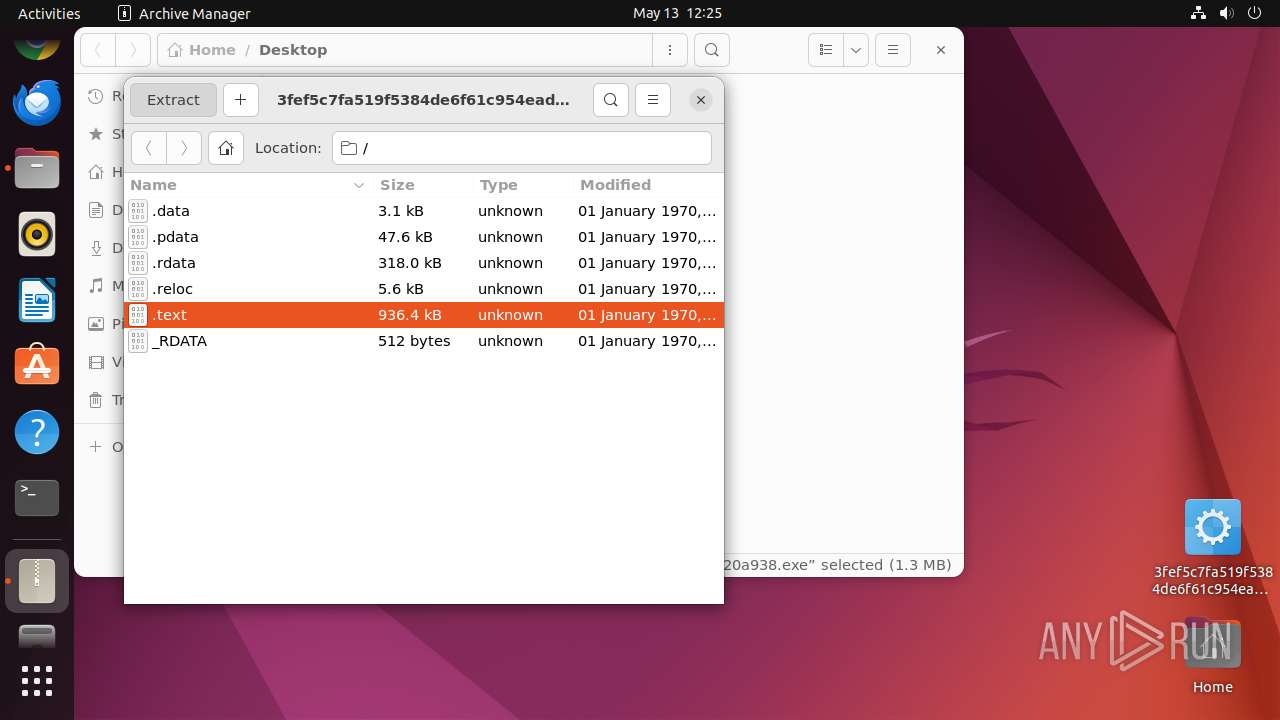
| 39536 | file-roller /home/user/Desktop/3fef5c7fa519f5384de6f61c954ead6dfd4da727005bfec954dc801bd120a938.exe | /usr/bin/file-roller | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
2
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39508 | nautilus | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 39536 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 39536 | file-roller | /home/user/.local/share/recently-used.xbel.41DW62 | xml | |
MD5:— | SHA256:— | |||
| 39508 | nautilus | /home/user/.local/share/recently-used.xbel.IGVN62 | xml | |
MD5:— | SHA256:— | |||
| 39567 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 39583 | 7z | /home/user/.cache/.fr-XTSNFK/.text | binary | |
MD5:— | SHA256:— | |||
| 39621 | 7z | /home/user/Desktop/.text | binary | |
MD5:— | SHA256:— | |||
| 39627 | whoopsie | /var/lib/whoopsie/whoopsie-id.47ZS62 | text | |
MD5:— | SHA256:— | |||
| 39636 | whoopsie | /var/lib/whoopsie/whoopsie-id | text | |
MD5:— | SHA256:— | |||
| 39508 | nautilus | /home/user/.config/mimeapps.list | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.18:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 37.19.194.81:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
39606 | gvfsd-smb-browse | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
8.100.168.192.in-addr.arpa |
| unknown |