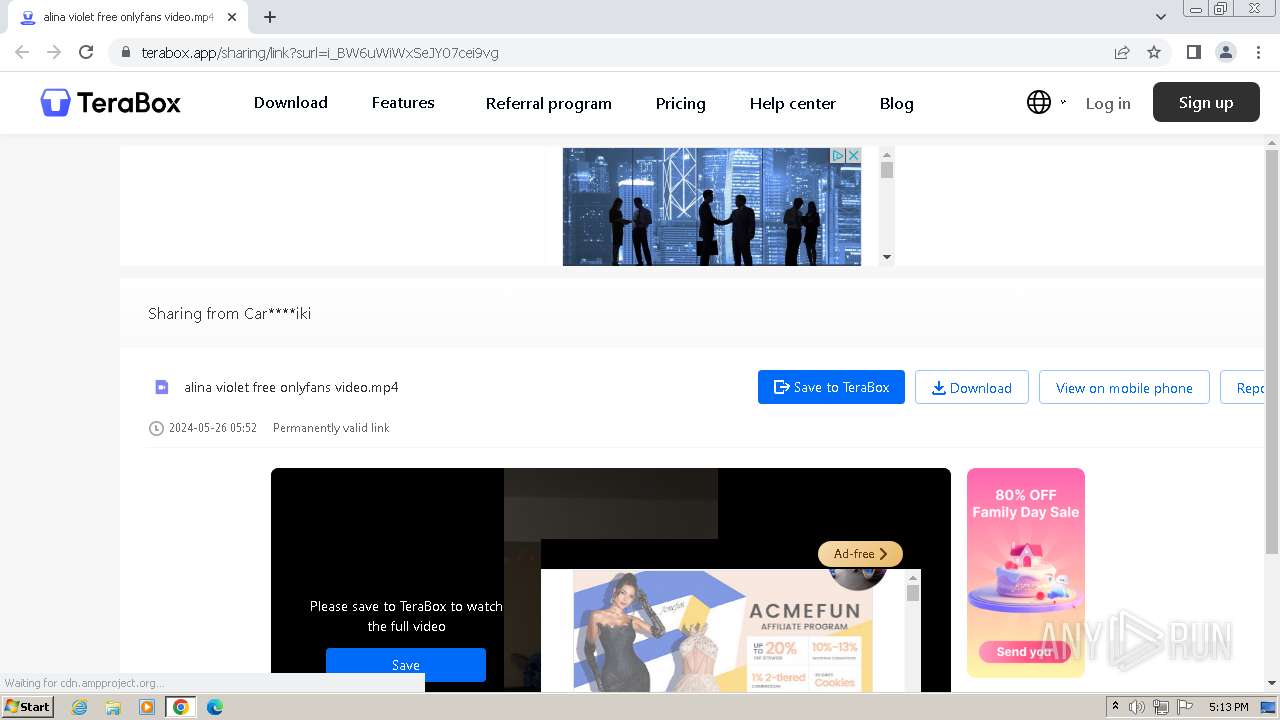
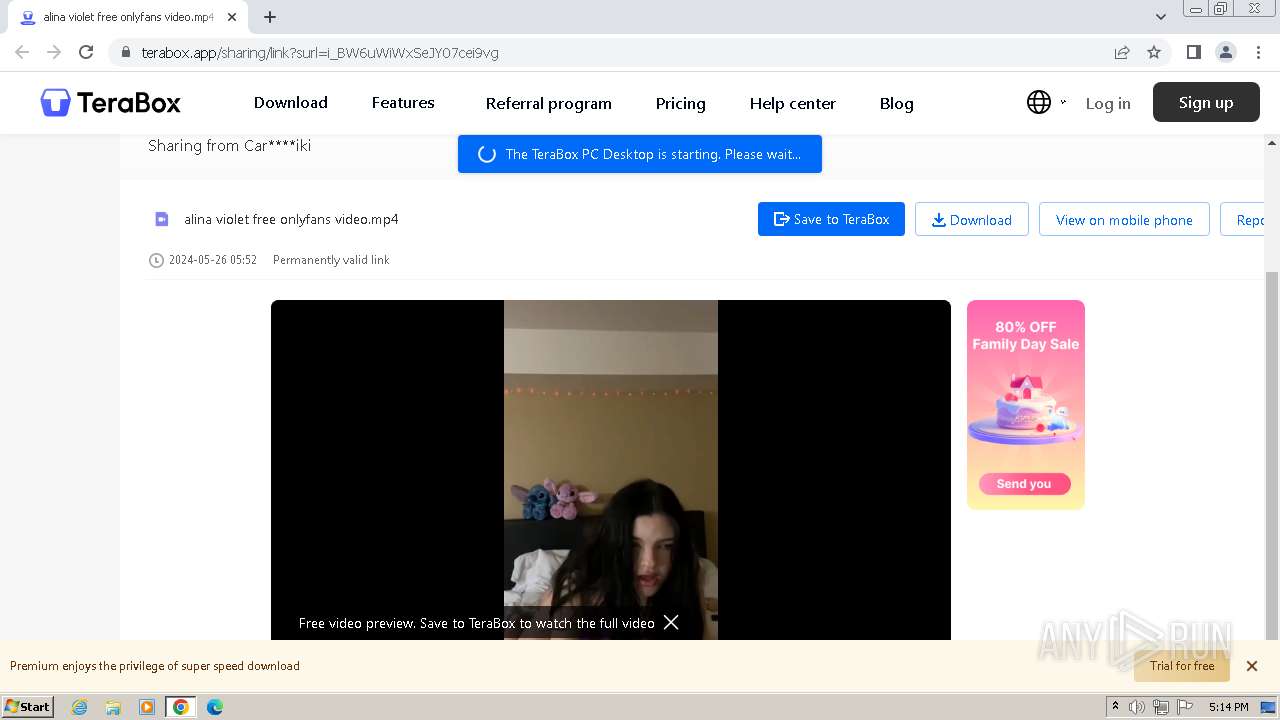
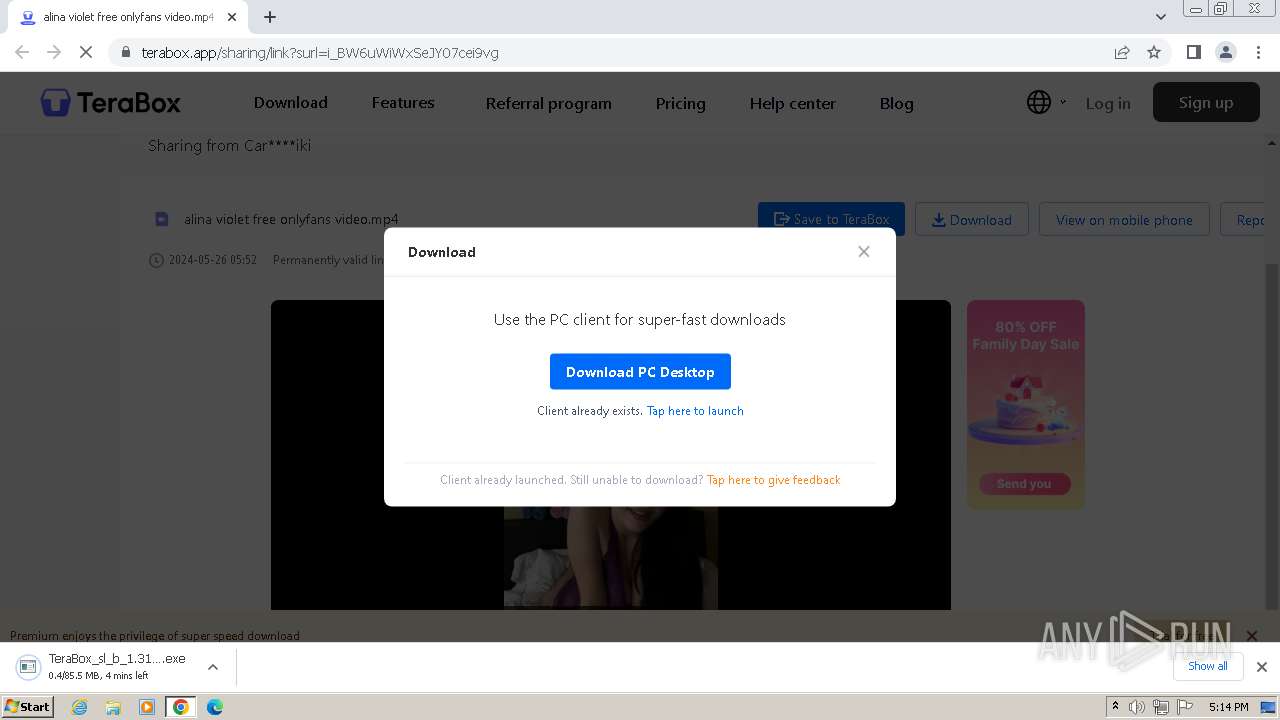
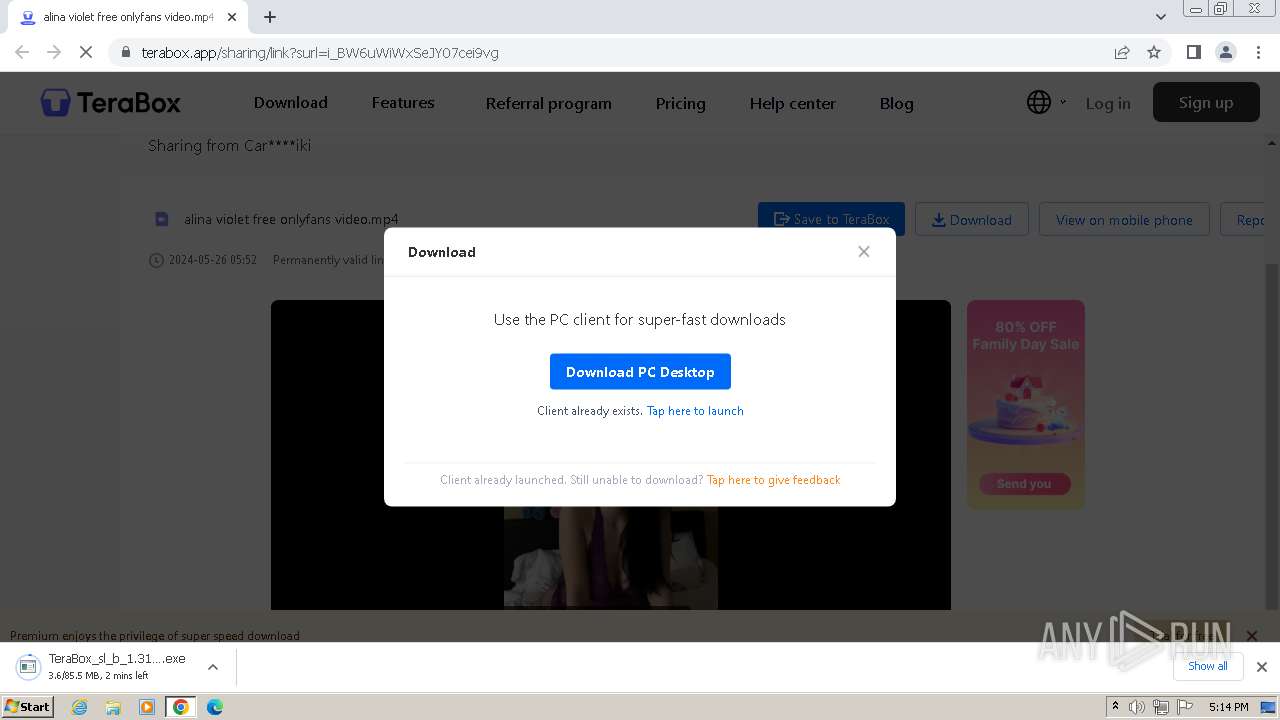
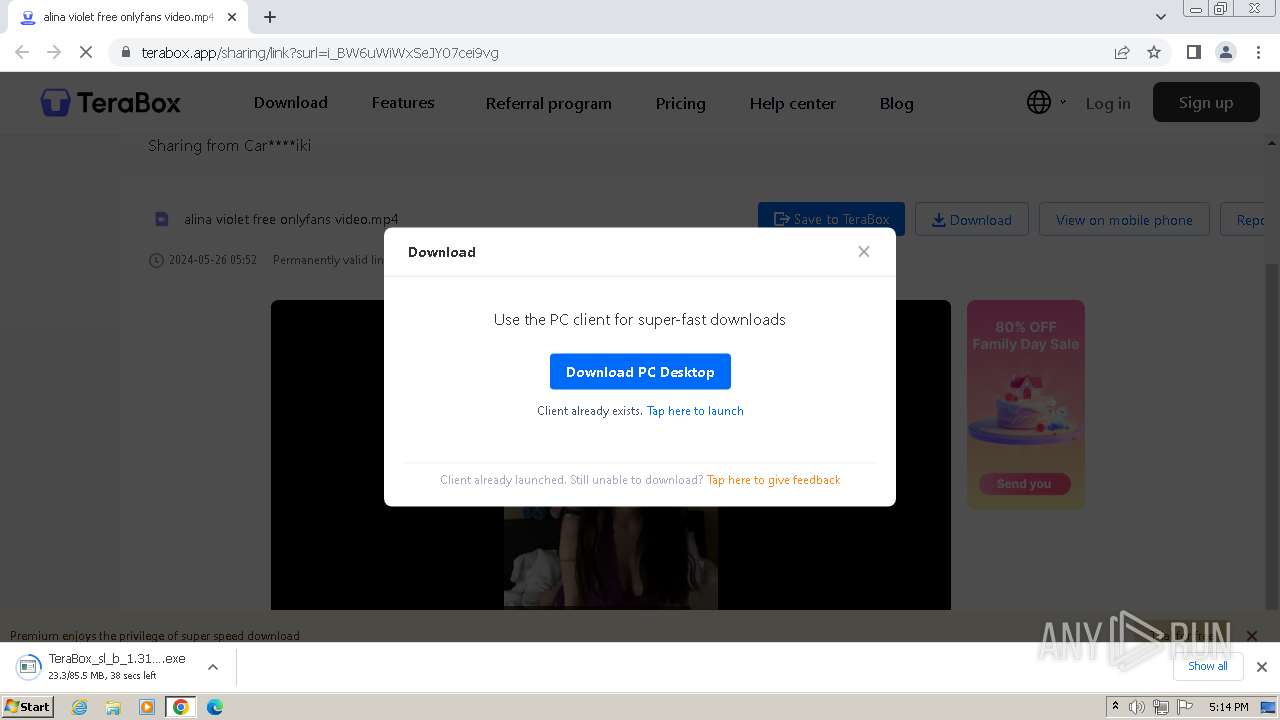
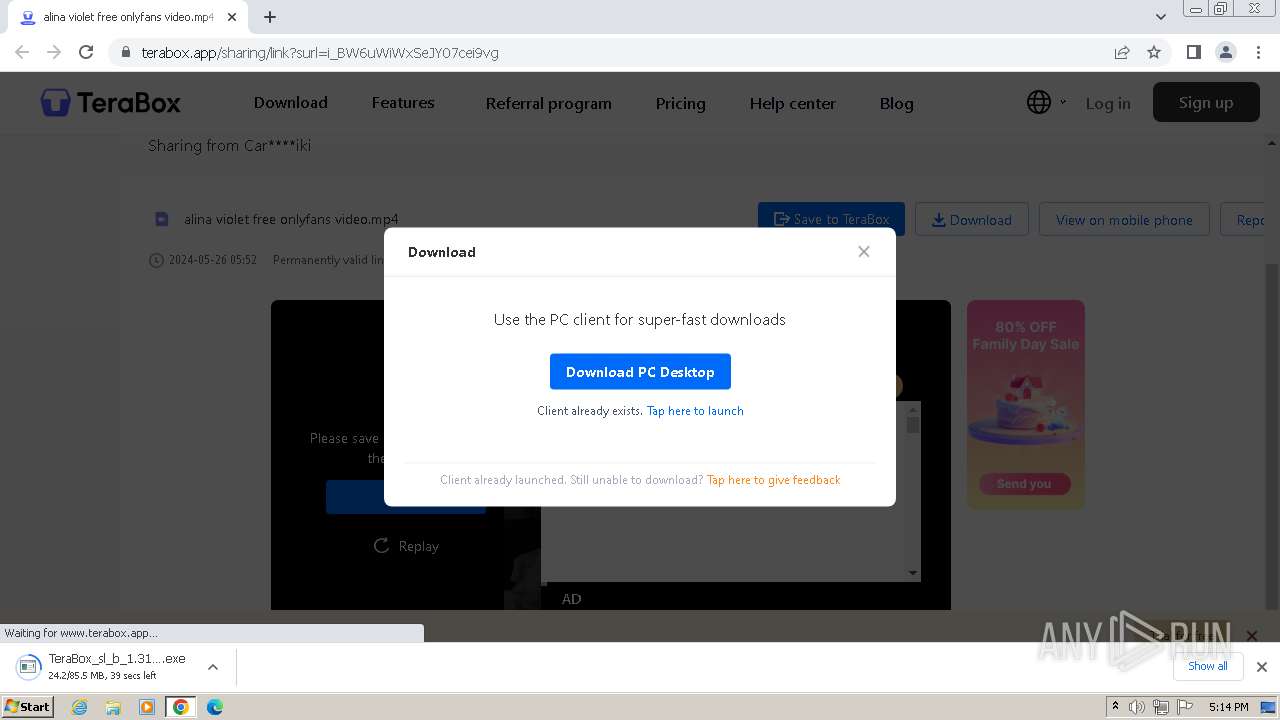
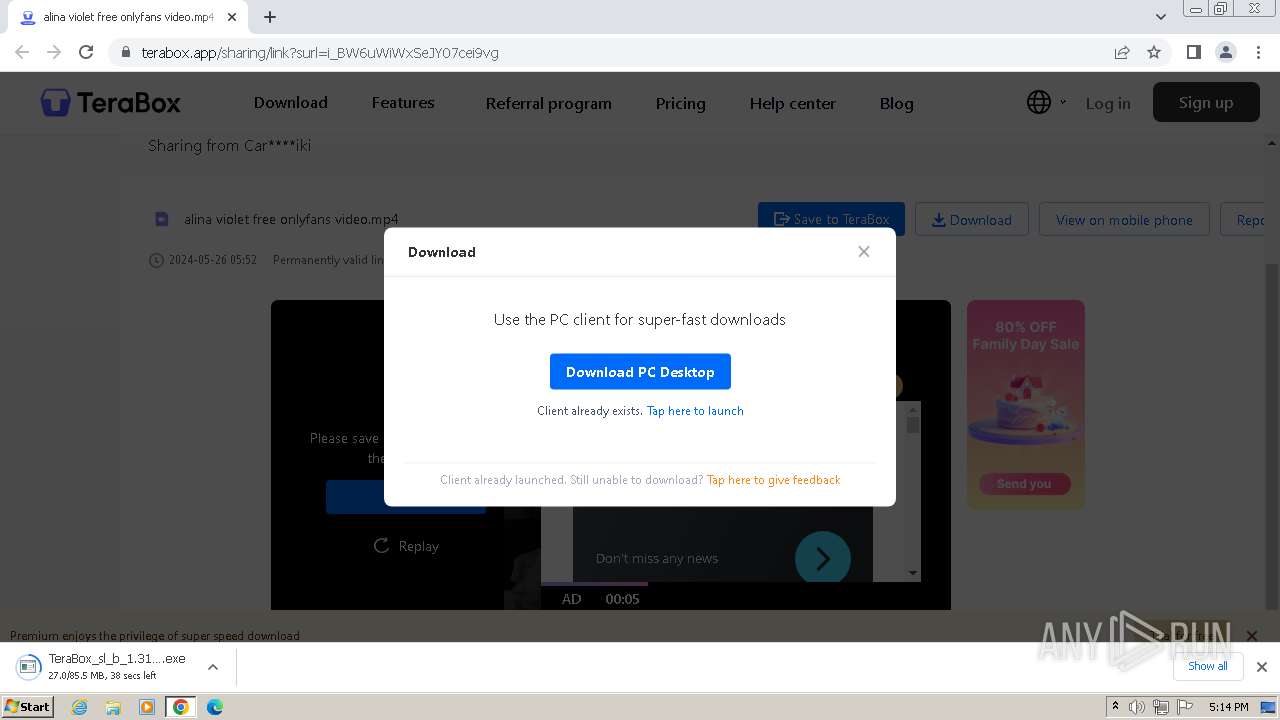
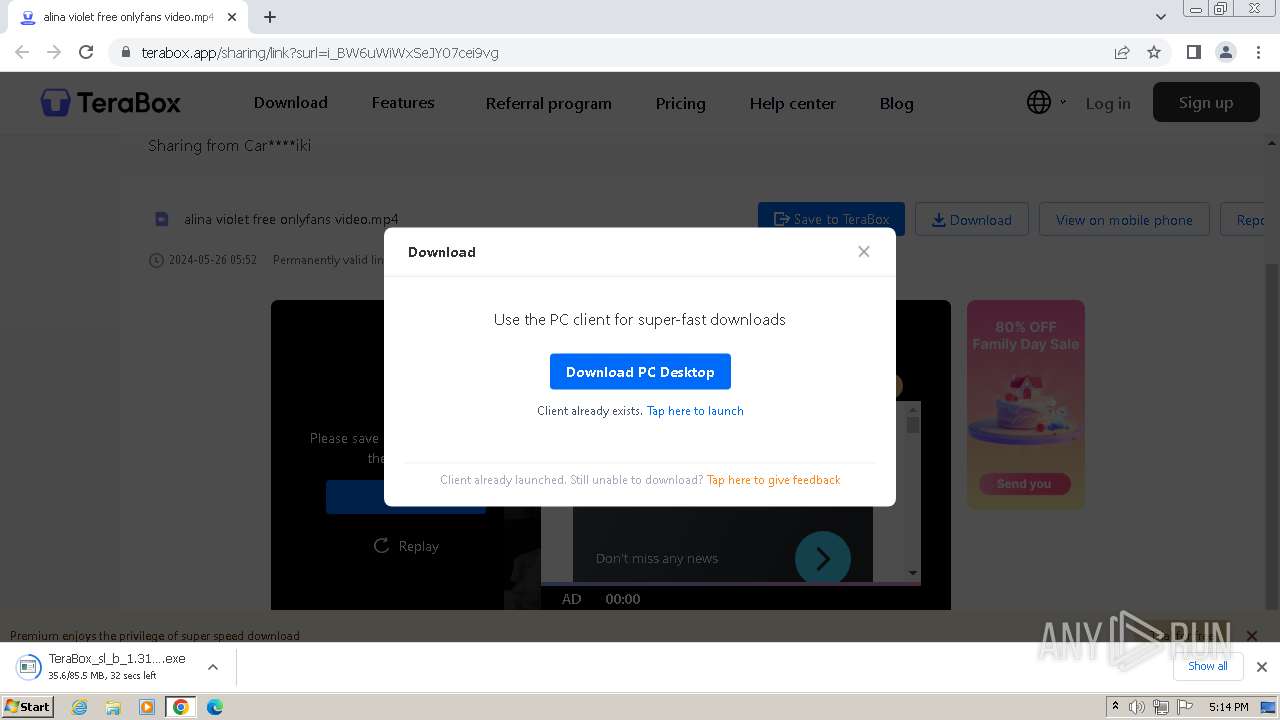
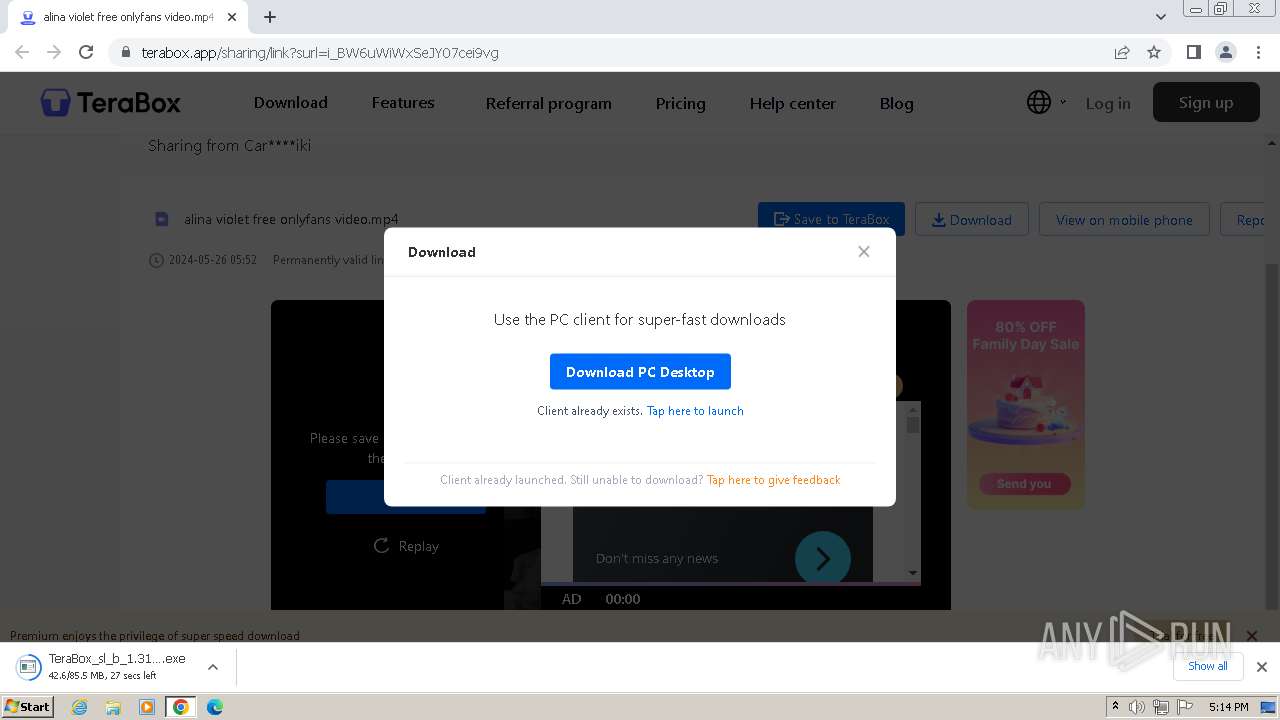
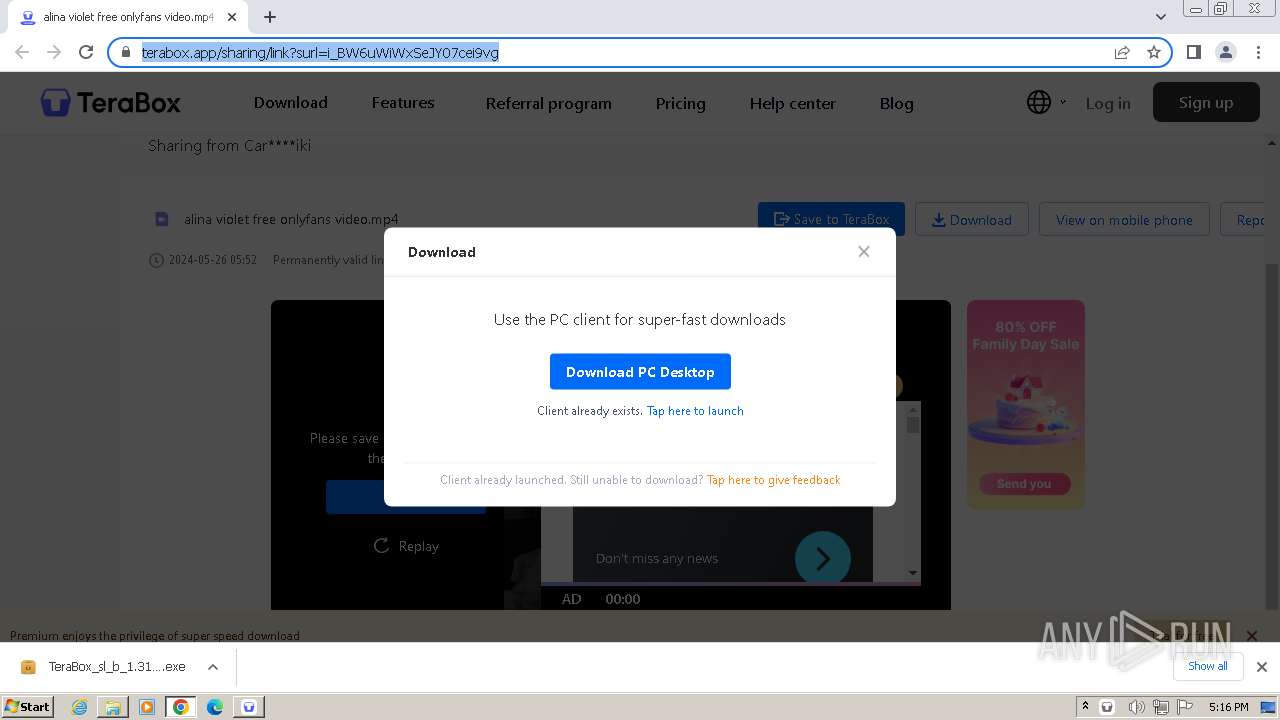
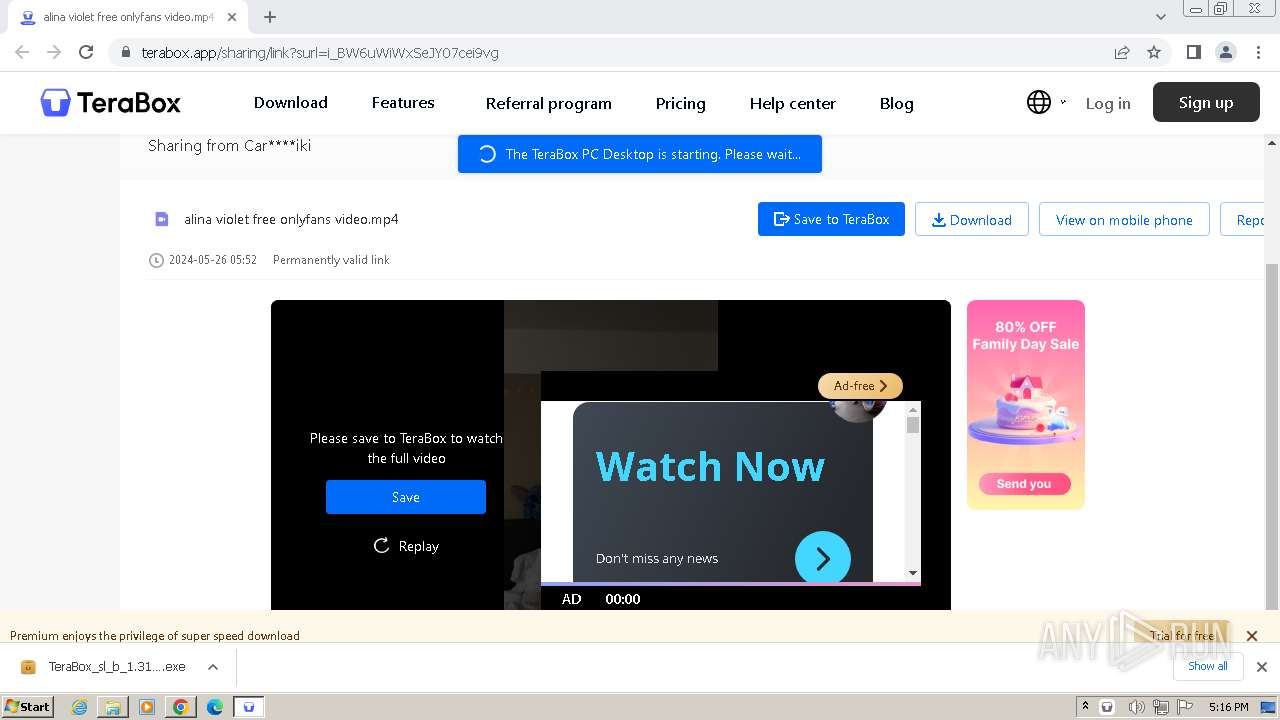
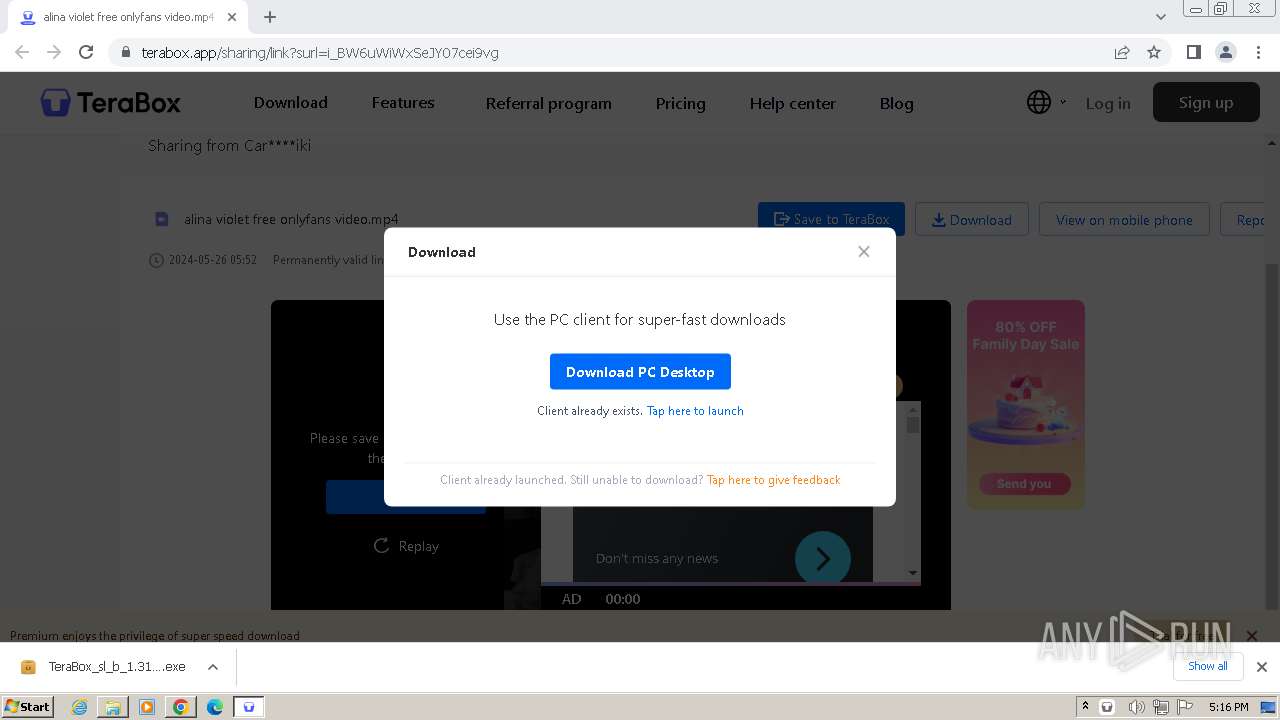
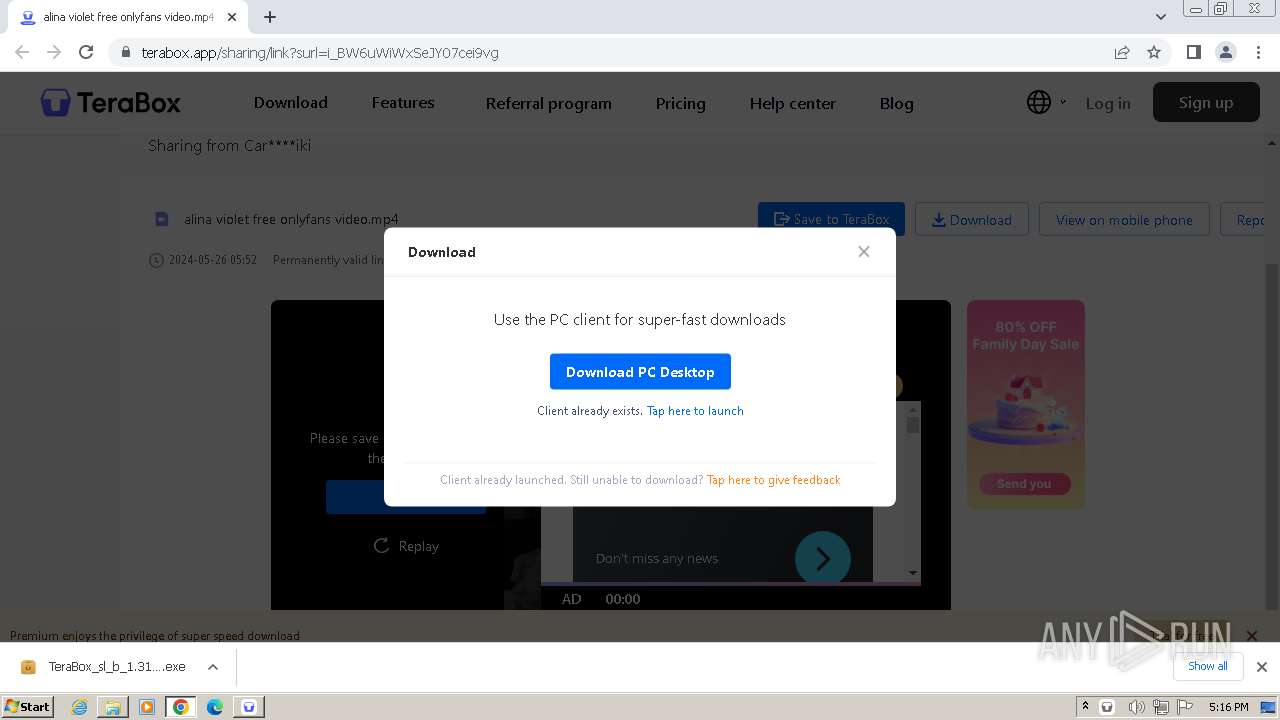
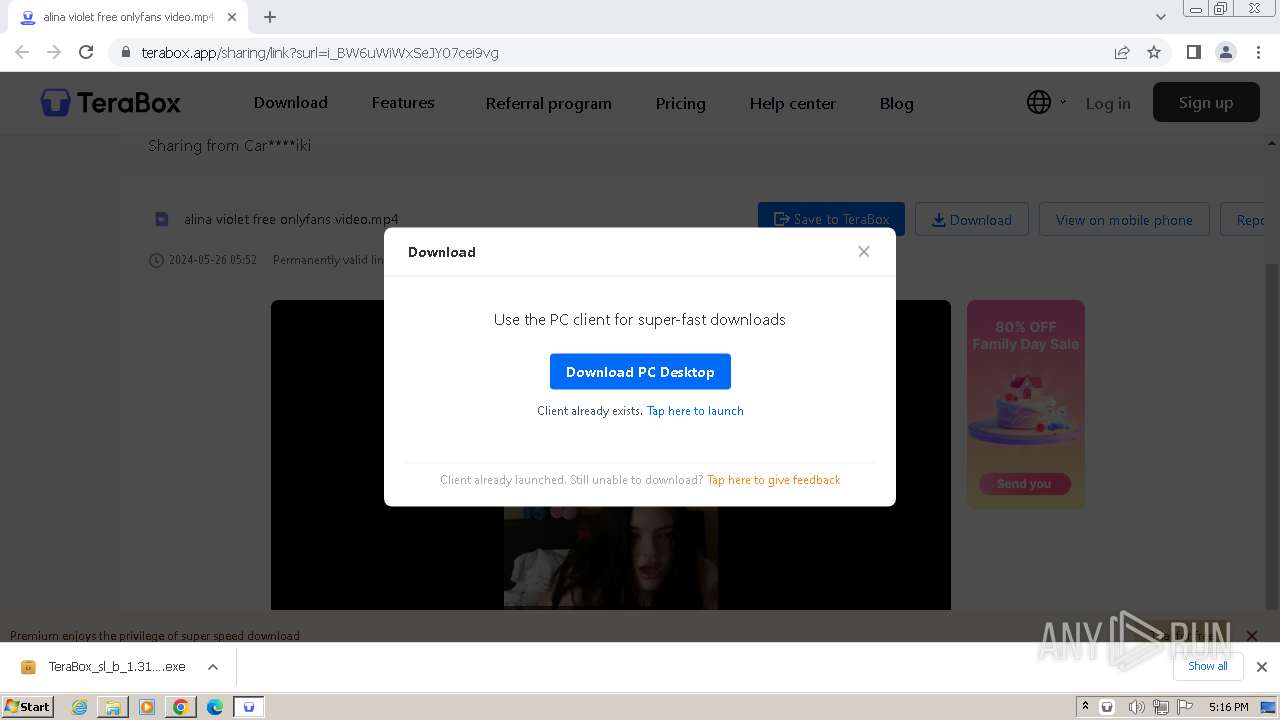
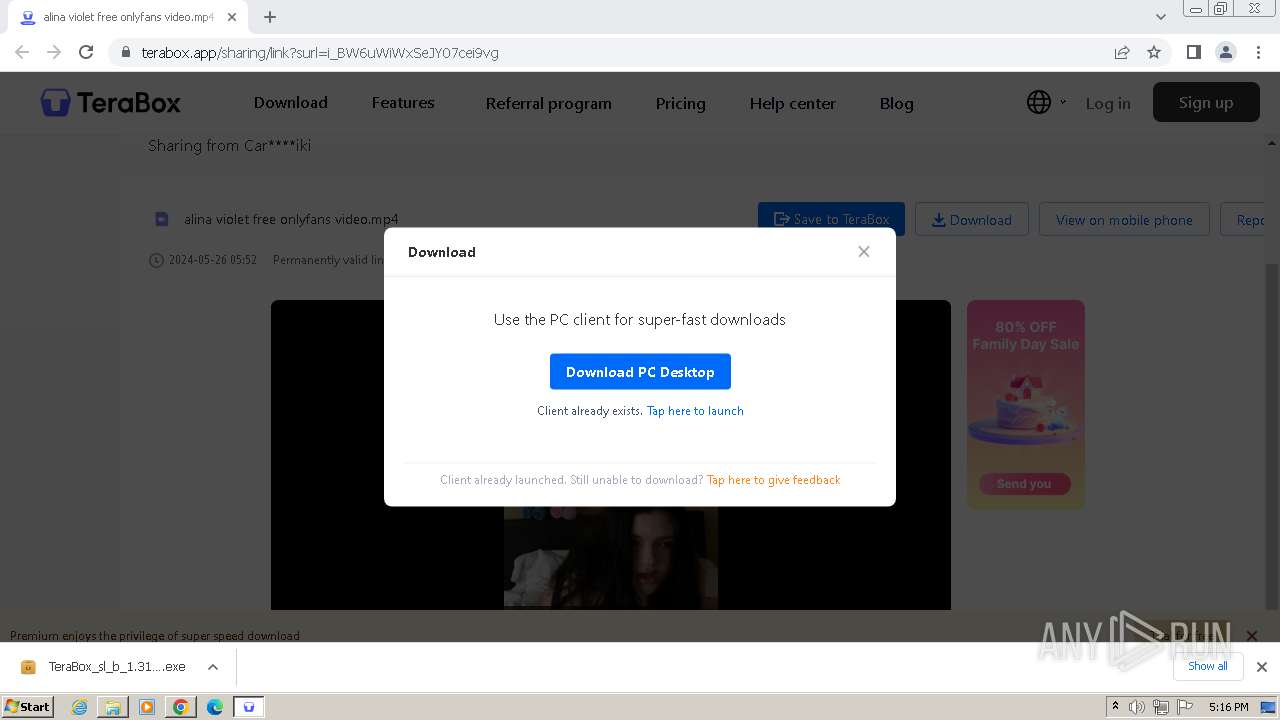
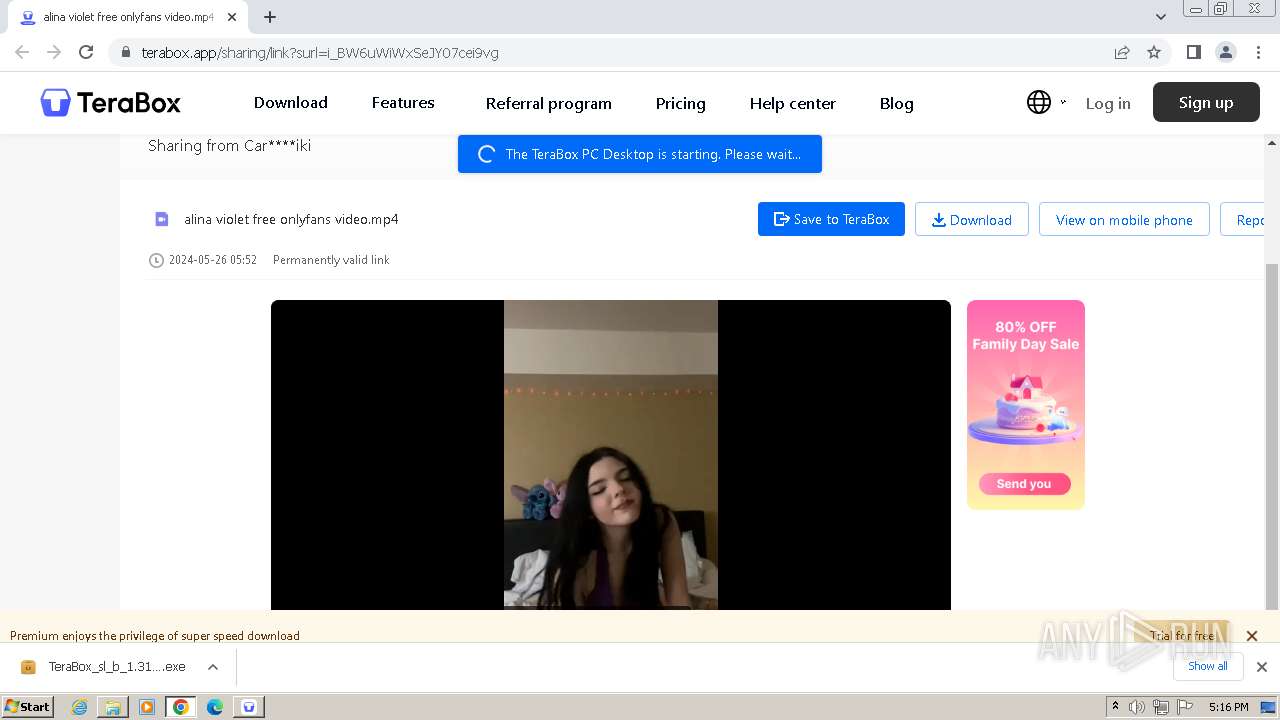
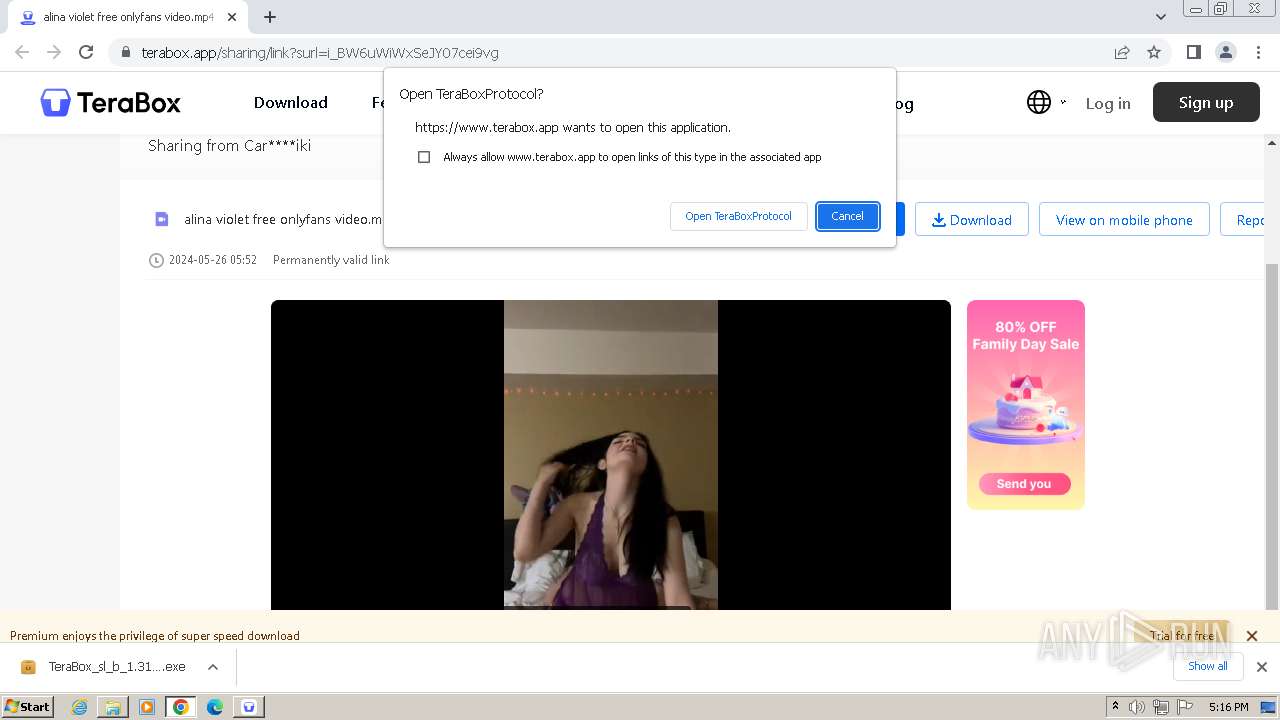
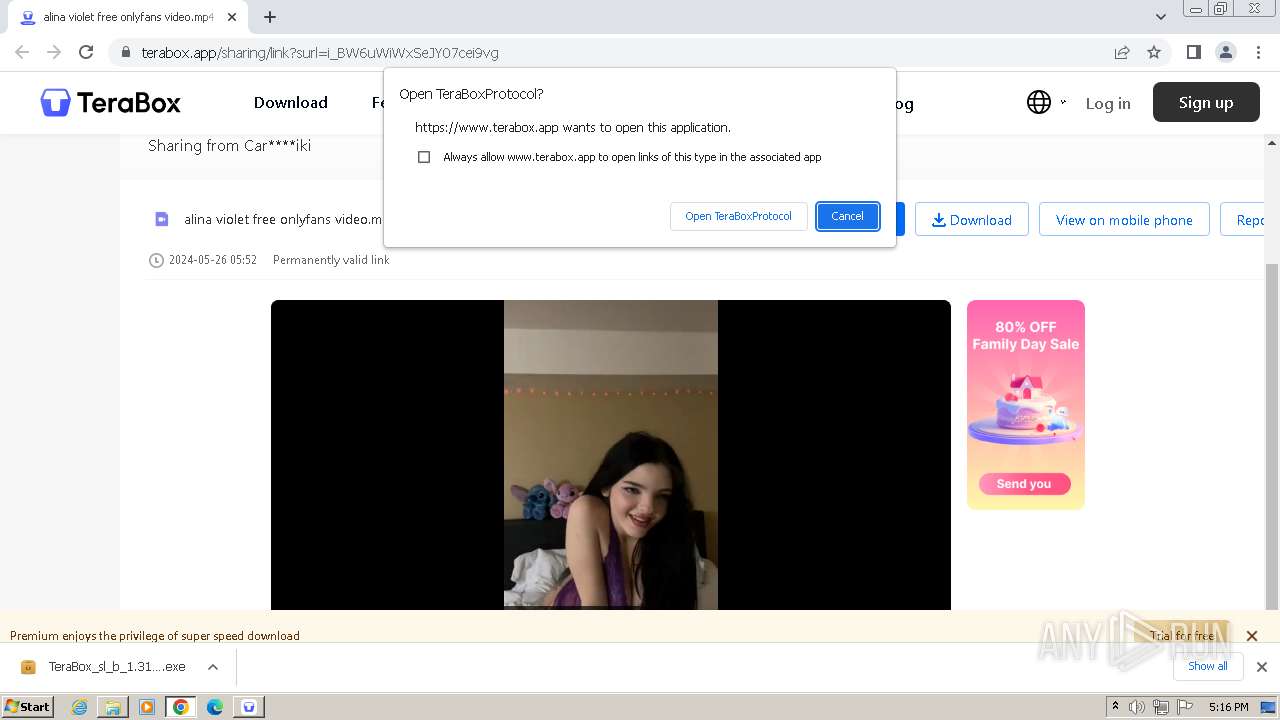
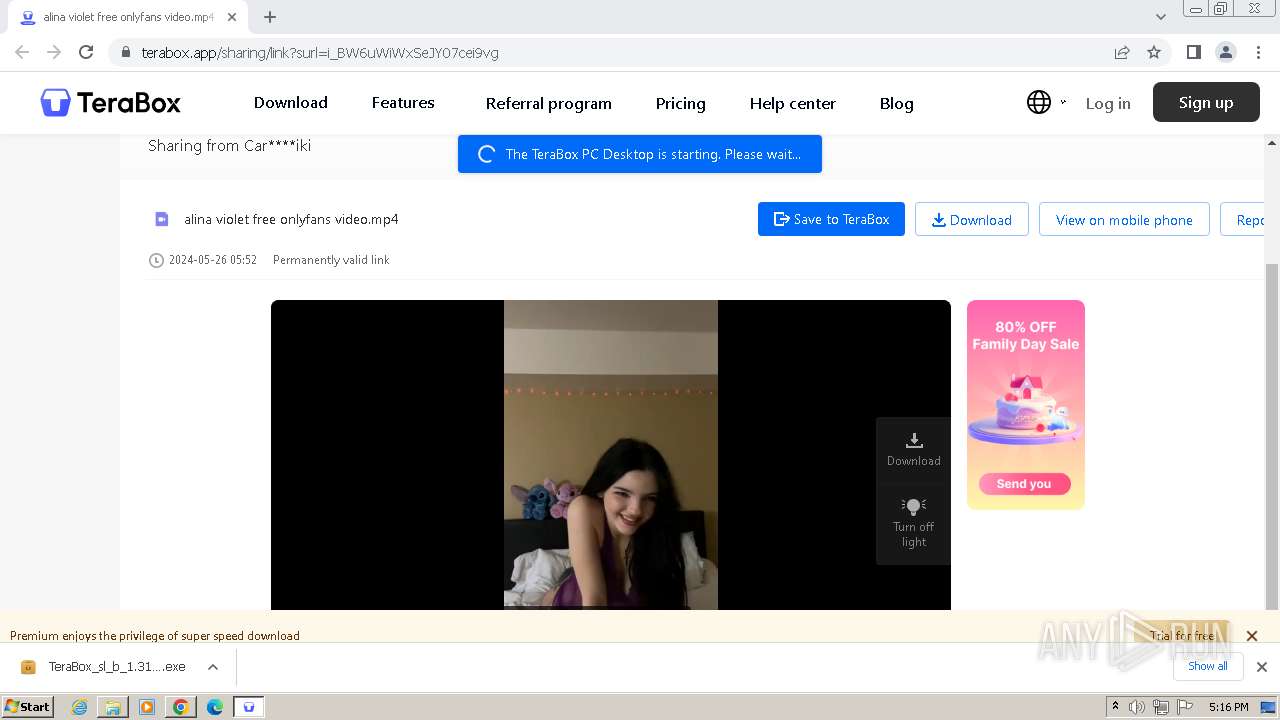
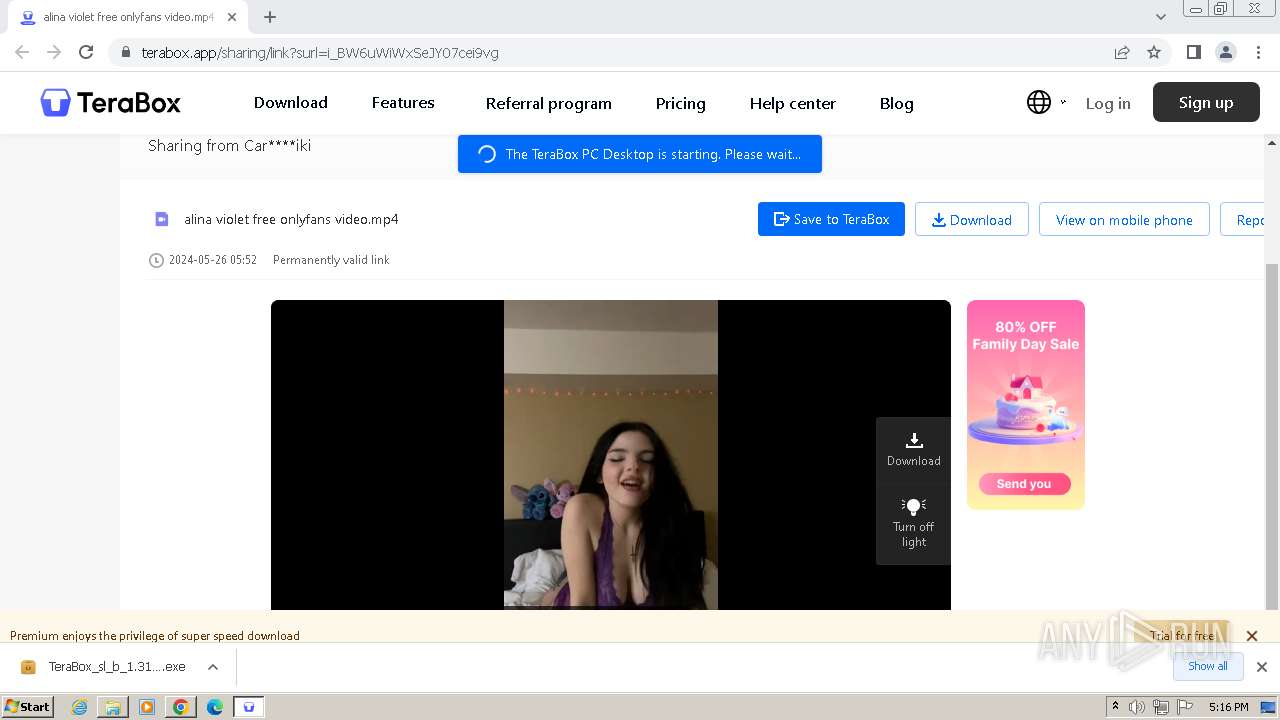
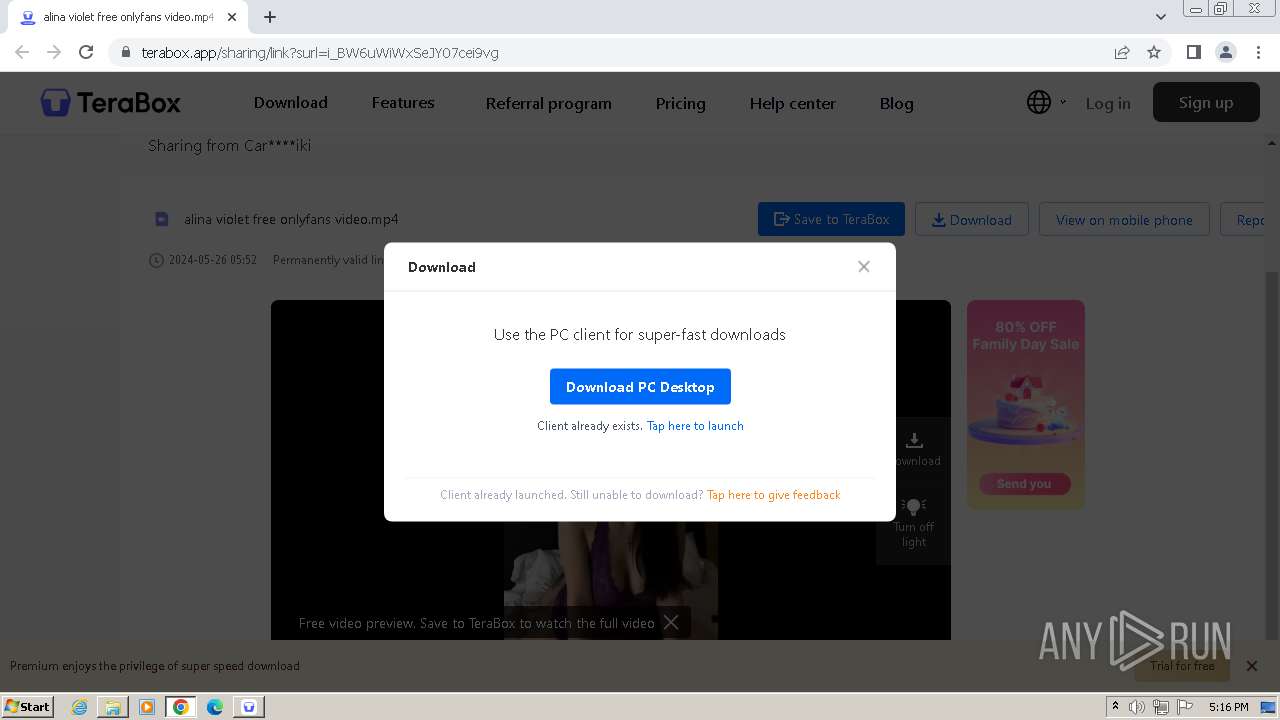
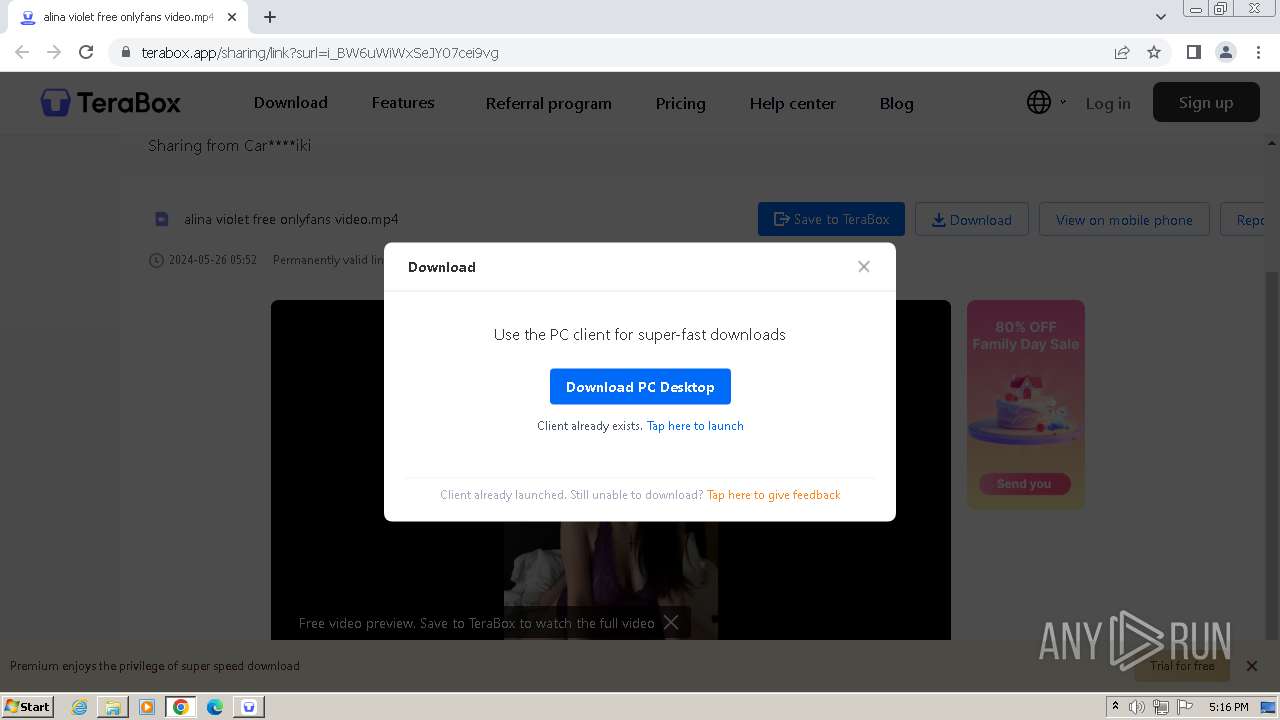
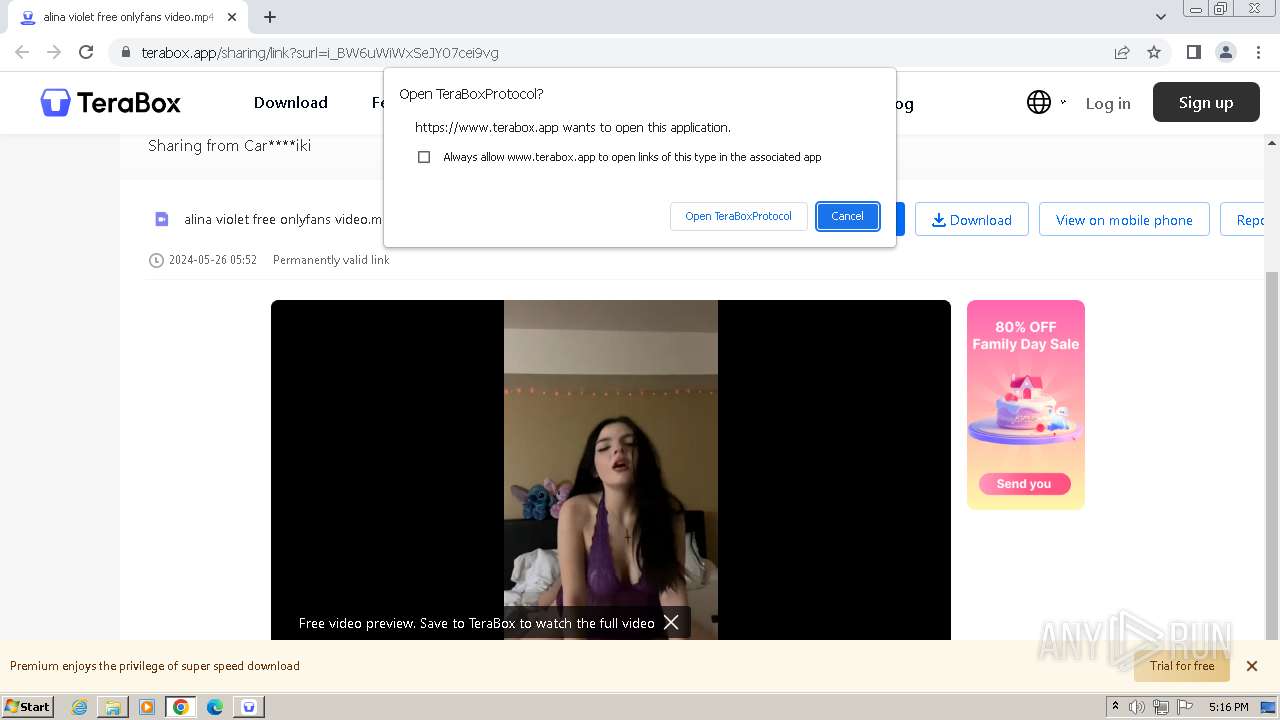
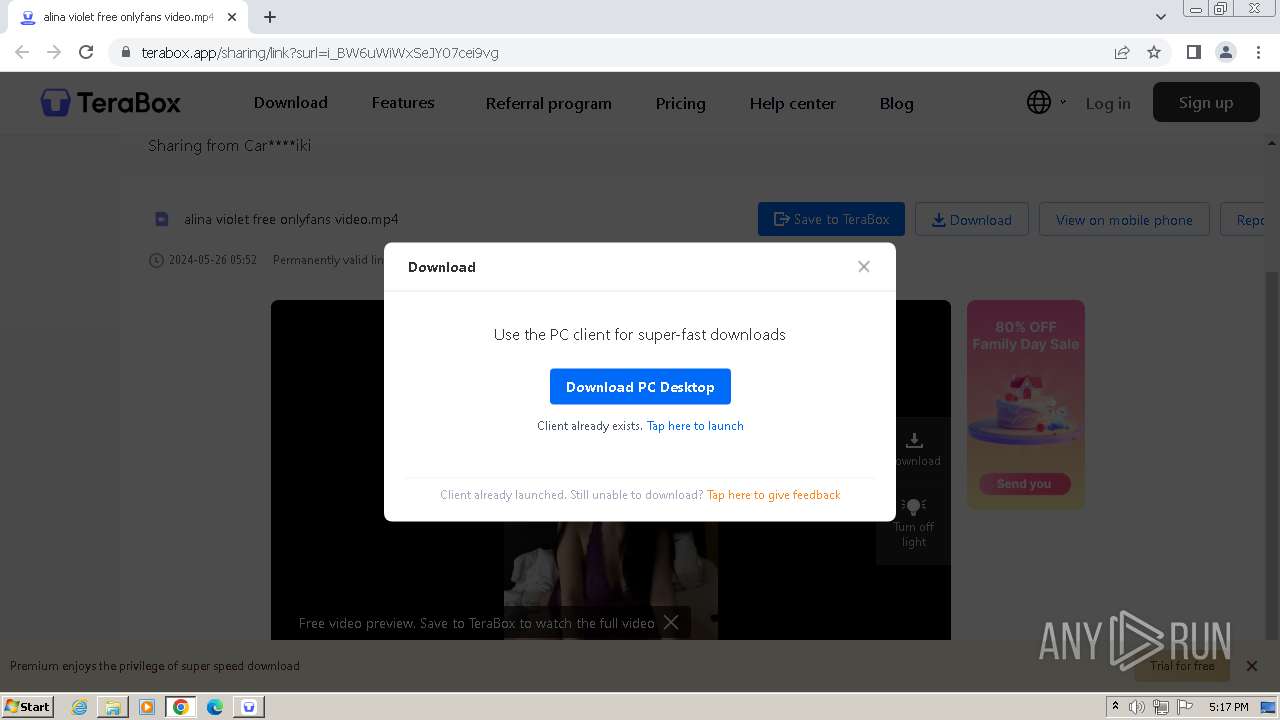
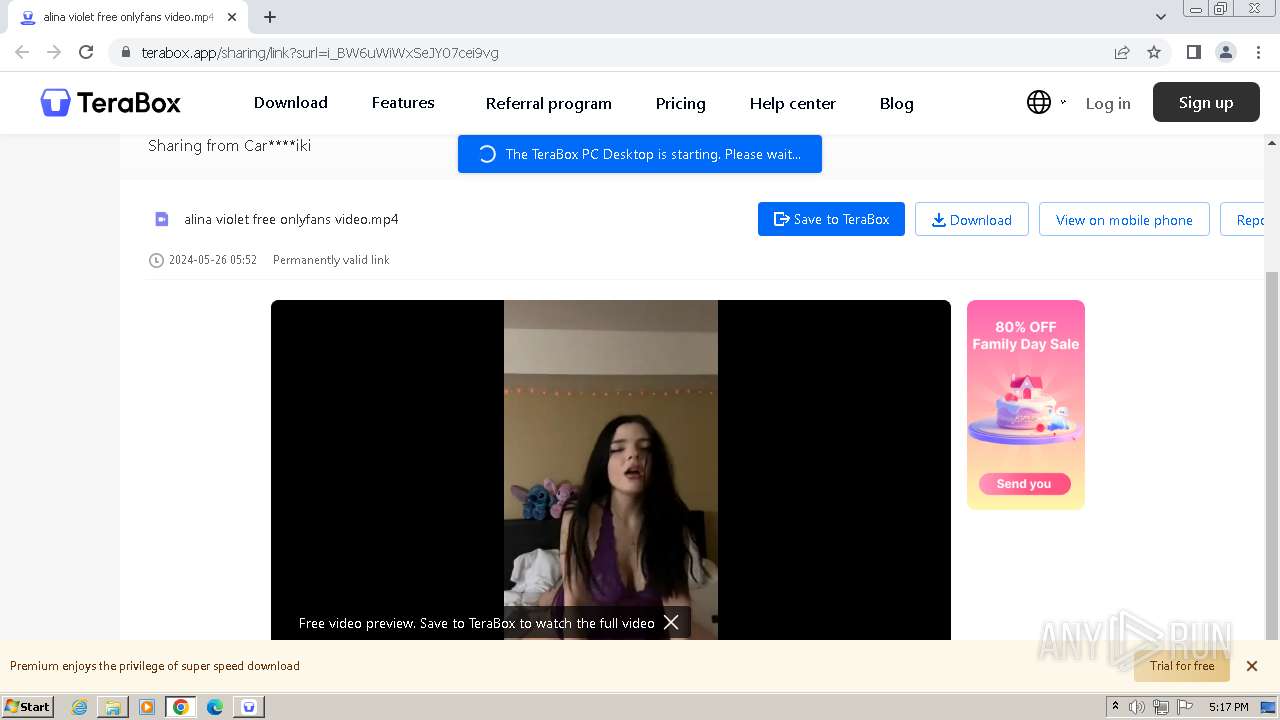
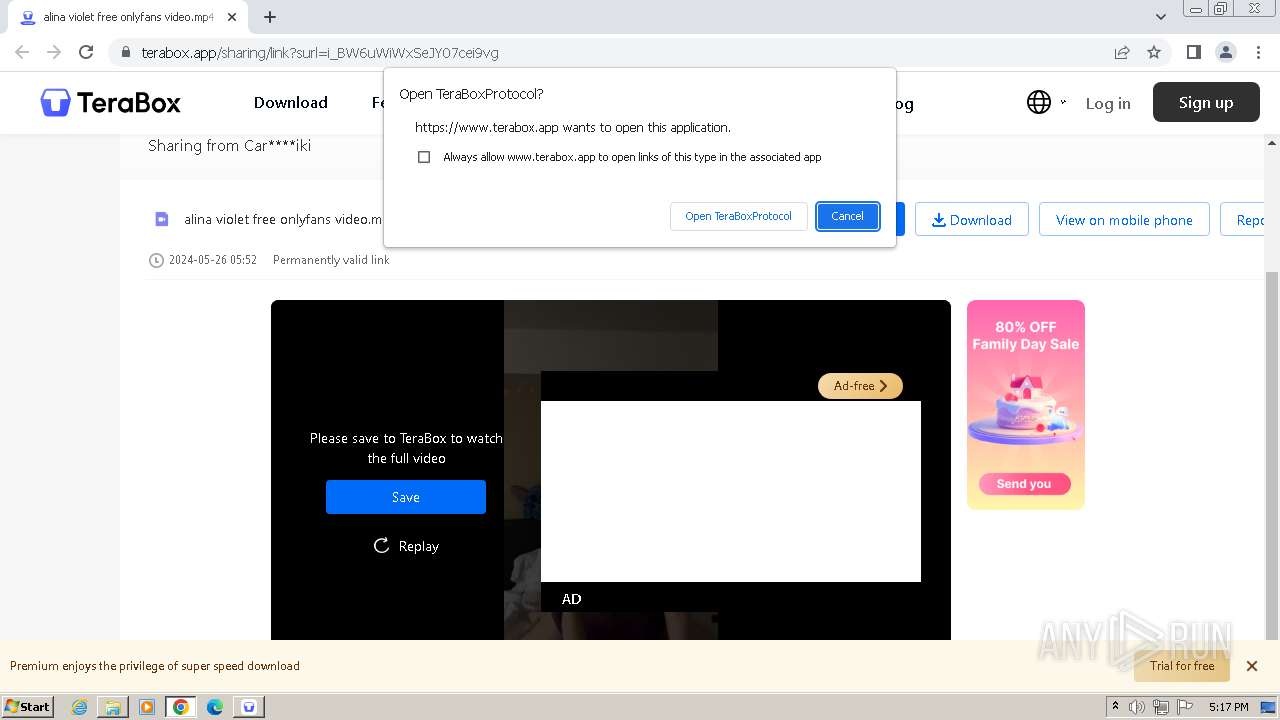
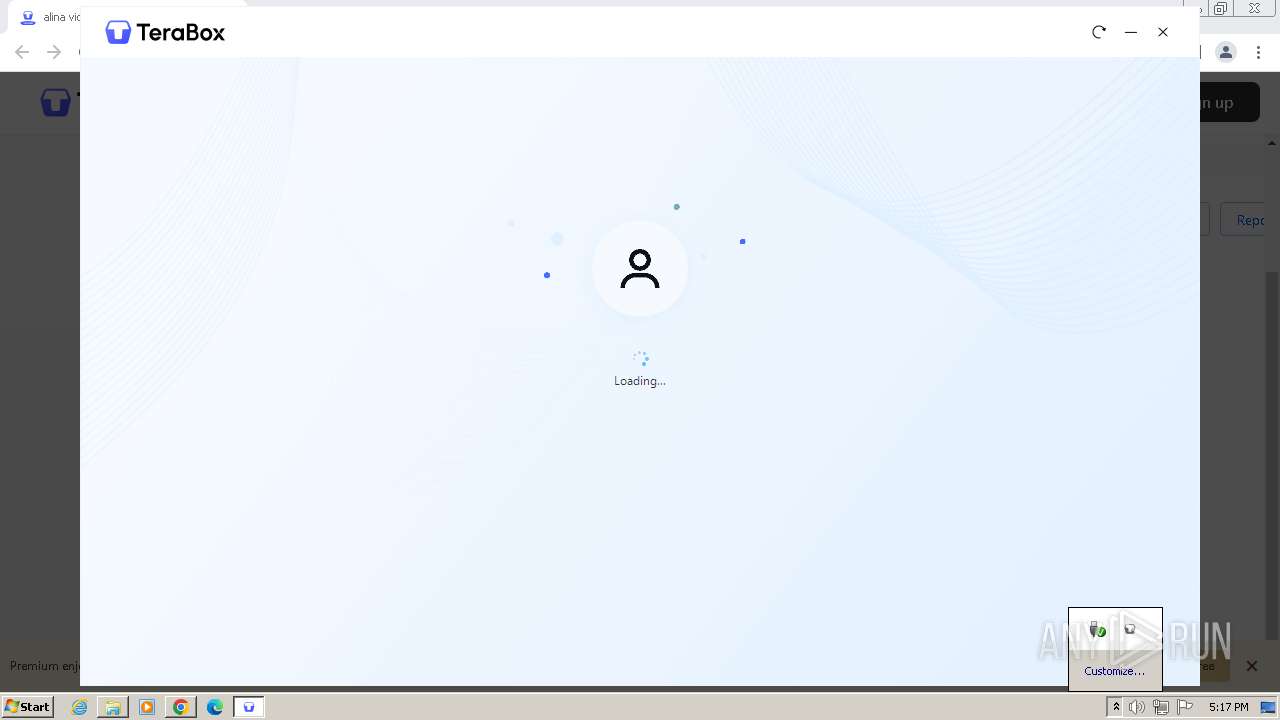
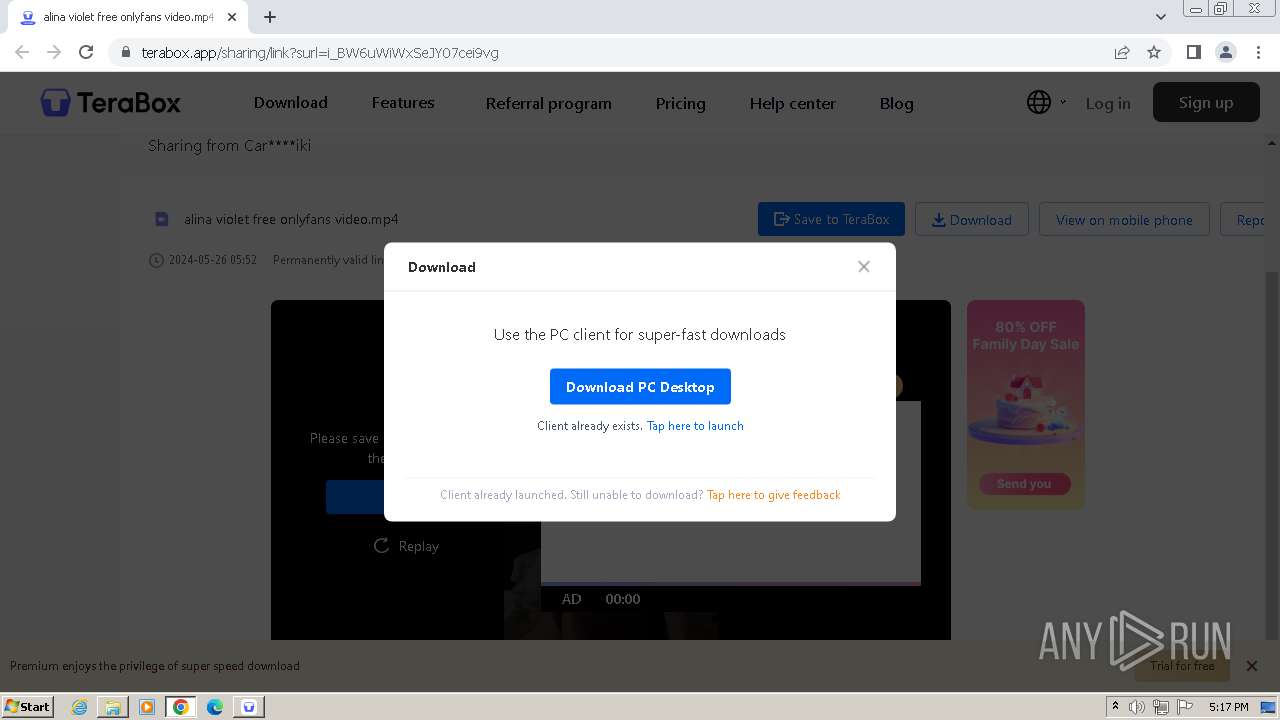
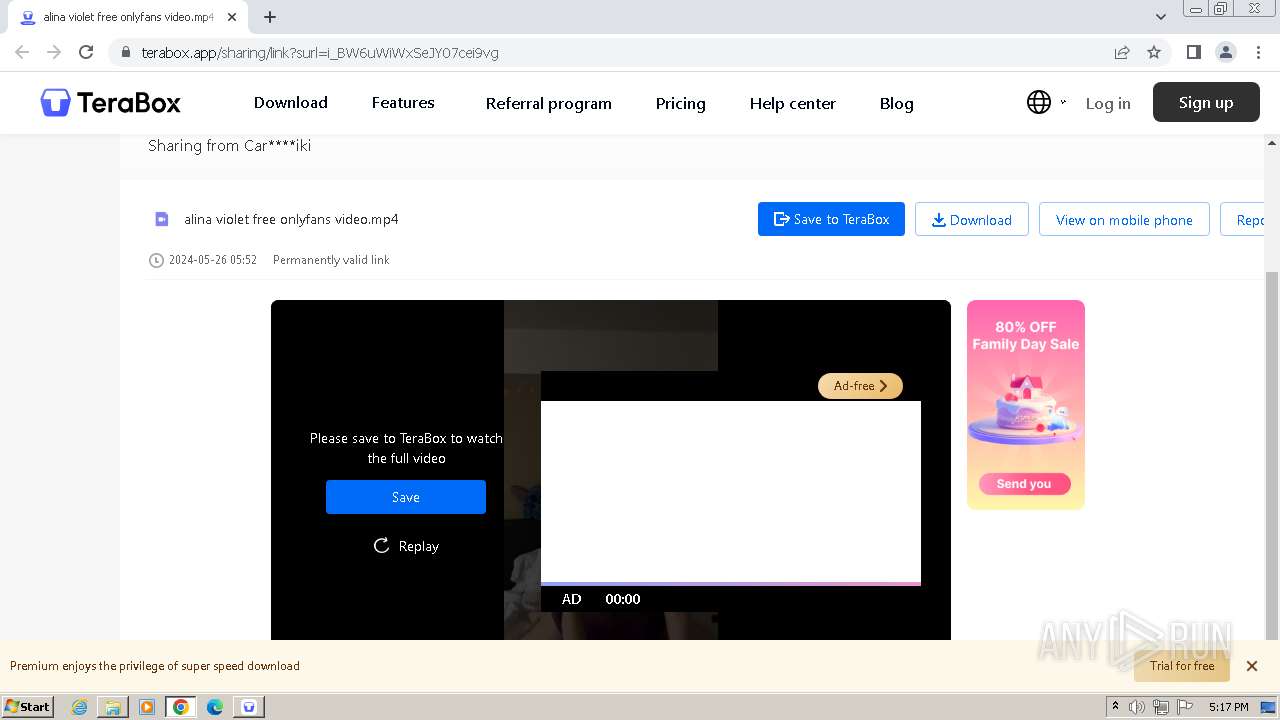
| URL: | https://terabox.app/s/1i_BW6uWiWxSeJY07cei9vg |
| Full analysis: | https://app.any.run/tasks/e5ab2a46-a31f-43c5-a5ae-0d9381dfe4b6 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2024, 16:12:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 127916854CCFA02FF1FEEFDFBE2E656C |
| SHA1: | 6822691882C5C0C03CA2ACD7D764DB21C3A56647 |
| SHA256: | 3FEC34A511EC634C43463C39443125F9A78512BB6F23018319E5403C13816BC1 |
| SSDEEP: | 3:N8IUqOgWKUjyndv7chn:2IVOGUjy2n |
MALICIOUS
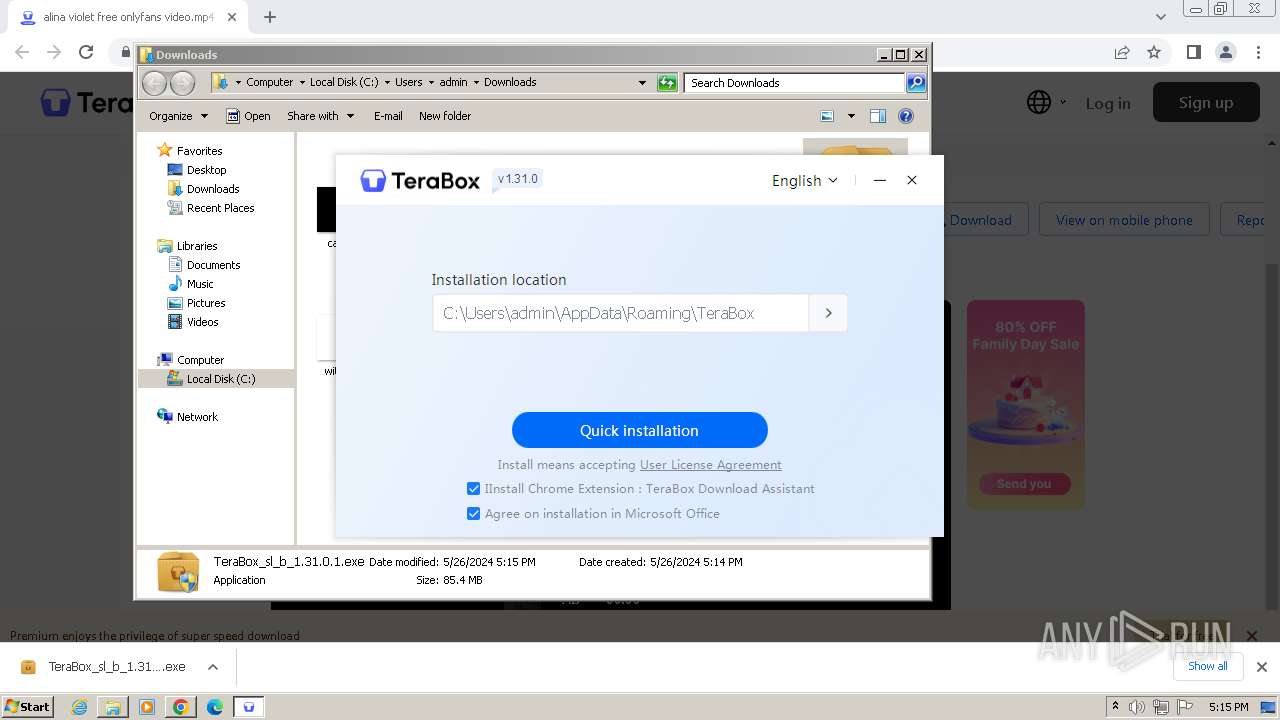
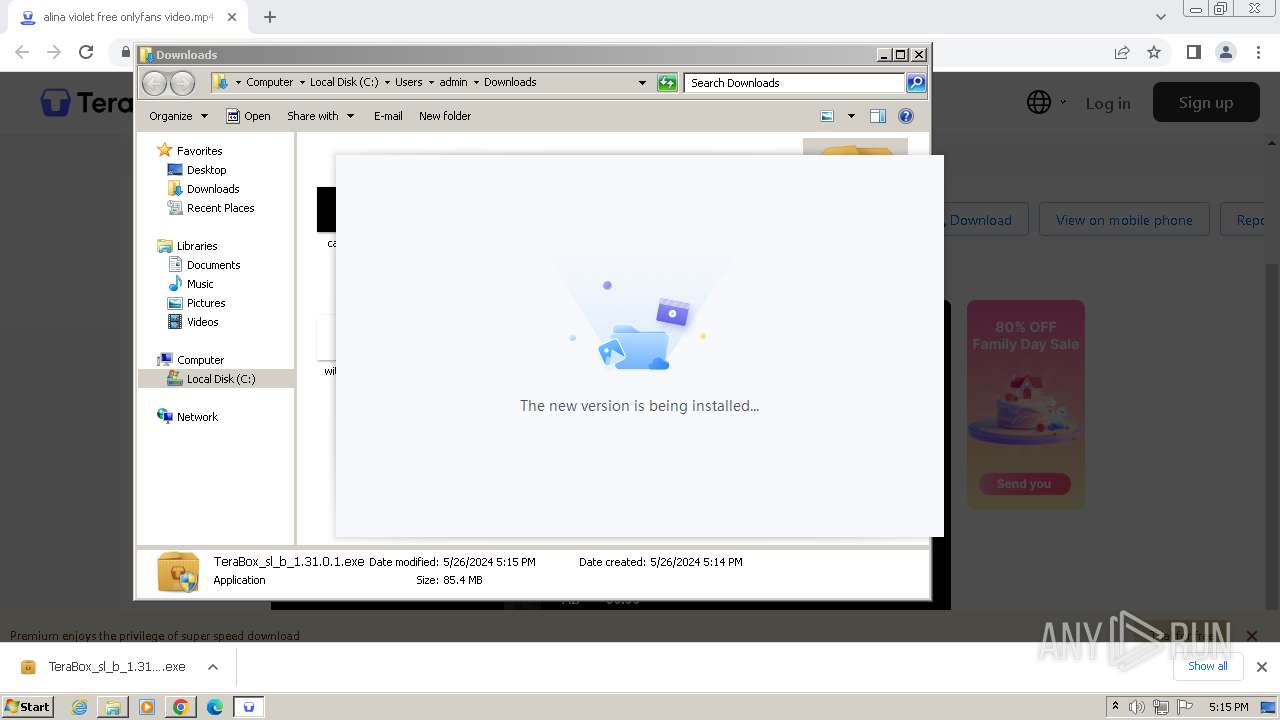
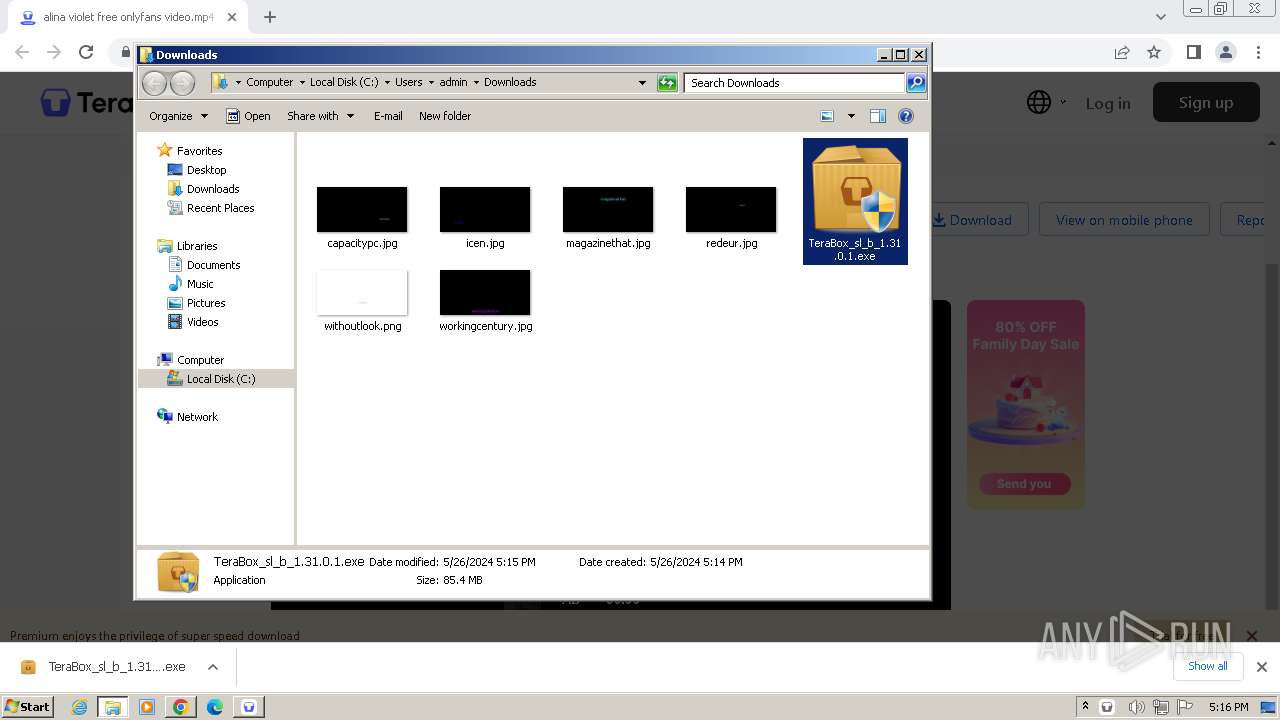
Drops the executable file immediately after the start
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBoxHost.exe (PID: 3668)
Changes the autorun value in the registry
- TeraBox.exe (PID: 1288)
Registers / Runs the DLL via REGSVR32.EXE
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
Creates a writable file in the system directory
- YunUtilityService.exe (PID: 1576)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
Executable content was dropped or overwritten
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
The process creates files with name similar to system file names
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBoxRender.exe (PID: 3248)
Process drops legitimate windows executable
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
The process drops C-runtime libraries
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
Creates a software uninstall entry
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
Reads the date of Windows installation
- TeraBox.exe (PID: 1288)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 552)
- regsvr32.exe (PID: 2380)
Reads the Internet Settings
- TeraBoxWebService.exe (PID: 3344)
- TeraBox.exe (PID: 1468)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
Reads security settings of Internet Explorer
- TeraBoxWebService.exe (PID: 3344)
- TeraBox.exe (PID: 1468)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
Checks Windows Trust Settings
- TeraBox.exe (PID: 1468)
- YunUtilityService.exe (PID: 1576)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- YunUtilityService.exe (PID: 2628)
Reads settings of System Certificates
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3440)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 2624)
Executes as Windows Service
- YunUtilityService.exe (PID: 1576)
- YunUtilityService.exe (PID: 2628)
Adds/modifies Windows certificates
- YunUtilityService.exe (PID: 1576)
INFO
Application launched itself
- chrome.exe (PID: 3964)
Reads the computer name
- wmpnscfg.exe (PID: 2348)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBox.exe (PID: 1288)
- YunUtilityService.exe (PID: 3120)
- TeraBoxWebService.exe (PID: 3344)
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3248)
- TeraBoxRender.exe (PID: 3440)
- YunUtilityService.exe (PID: 1576)
- TeraBoxRender.exe (PID: 3816)
- TeraBoxHost.exe (PID: 3680)
- TeraBoxHost.exe (PID: 3668)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 3292)
- TeraBoxRender.exe (PID: 2624)
- TeraBoxRender.exe (PID: 1660)
- TeraBoxHost.exe (PID: 2516)
- YunUtilityService.exe (PID: 2628)
- TeraBoxHost.exe (PID: 3660)
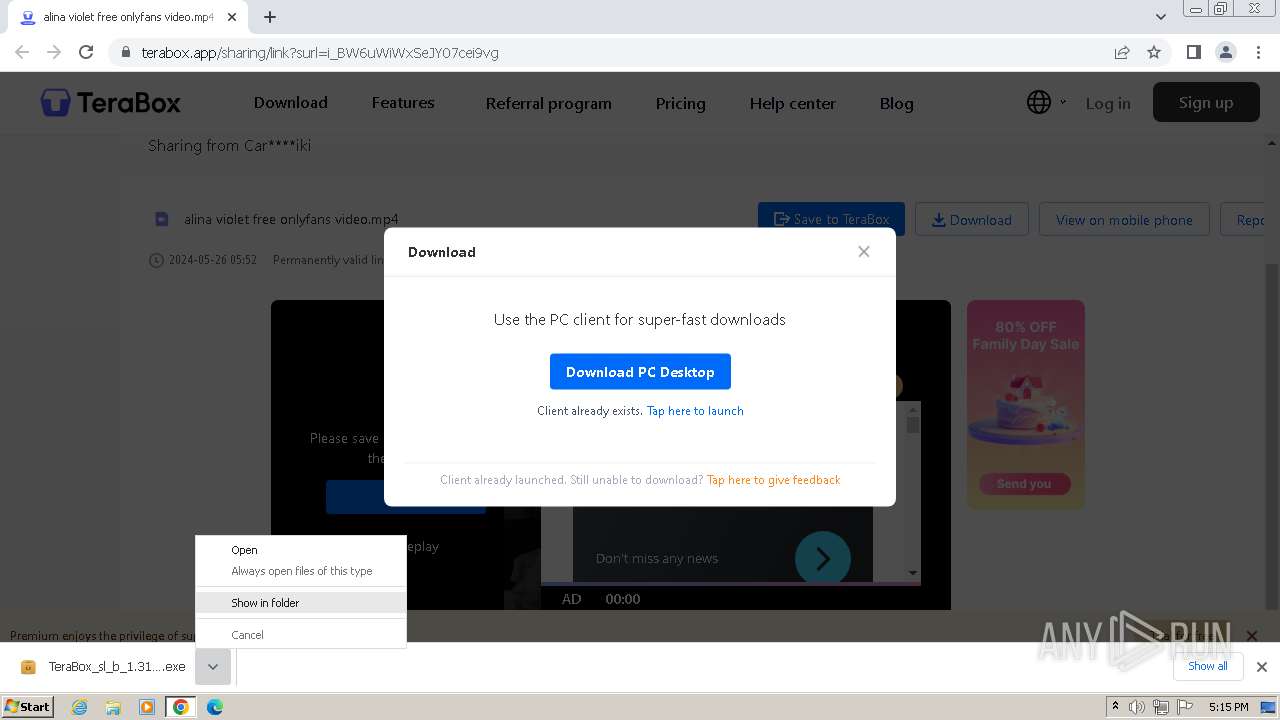
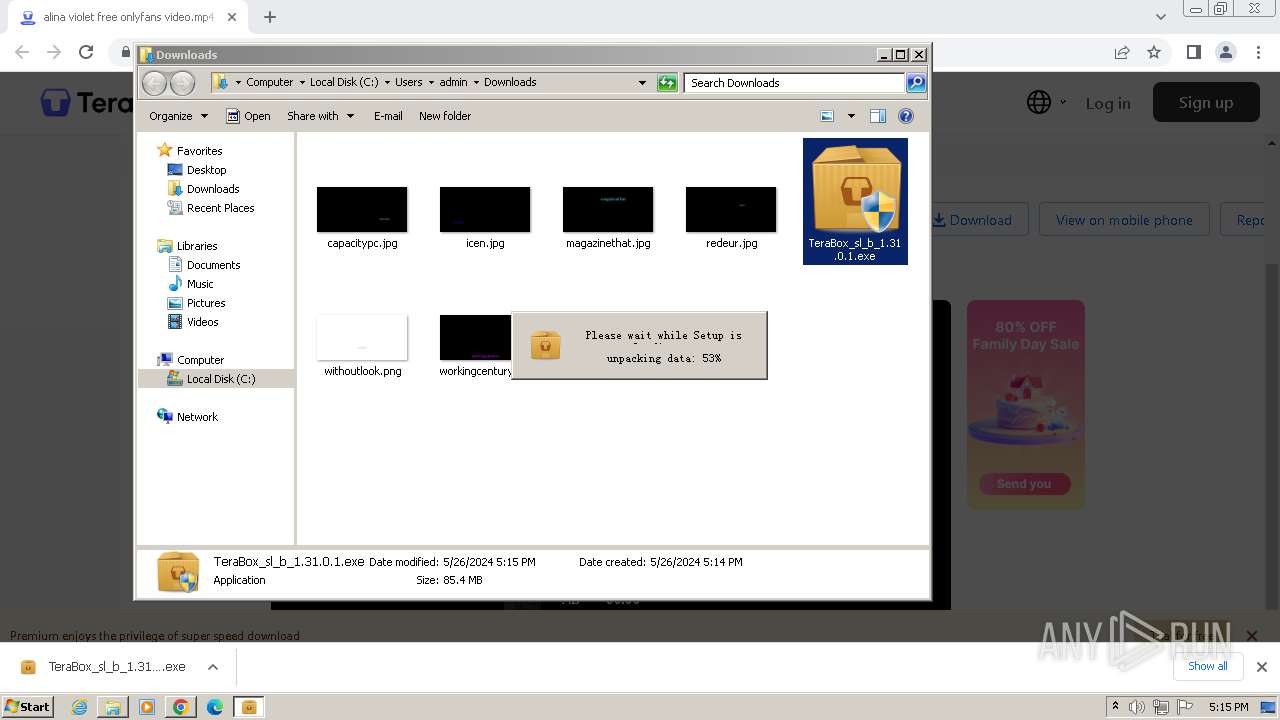
Manual execution by a user
- wmpnscfg.exe (PID: 2348)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBox_sl_b_1.31.0.1.exe (PID: 444)
Checks supported languages
- wmpnscfg.exe (PID: 2348)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBox.exe (PID: 1288)
- YunUtilityService.exe (PID: 3120)
- TeraBoxWebService.exe (PID: 3404)
- TeraBoxWebService.exe (PID: 3344)
- TeraBoxRender.exe (PID: 3248)
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3784)
- TeraBoxRender.exe (PID: 3816)
- YunUtilityService.exe (PID: 1576)
- TeraBoxRender.exe (PID: 3440)
- TeraBoxRender.exe (PID: 3384)
- TeraBoxHost.exe (PID: 3668)
- TeraBoxHost.exe (PID: 3680)
- AutoUpdate.exe (PID: 3120)
- TeraBoxWebService.exe (PID: 2676)
- TeraBoxWebService.exe (PID: 3280)
- TeraBoxWebService.exe (PID: 3228)
- TeraBoxWebService.exe (PID: 3584)
- TeraBoxWebService.exe (PID: 2432)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 3292)
- TeraBoxRender.exe (PID: 2624)
- TeraBoxRender.exe (PID: 3236)
- TeraBoxRender.exe (PID: 2444)
- YunUtilityService.exe (PID: 2628)
- TeraBoxHost.exe (PID: 2516)
- TeraBoxHost.exe (PID: 3660)
- TeraBoxRender.exe (PID: 1660)
Drops the executable file immediately after the start
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3280)
Executable content was dropped or overwritten
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3280)
The process uses the downloaded file
- chrome.exe (PID: 3872)
Create files in a temporary directory
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3440)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 2624)
Reads Environment values
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
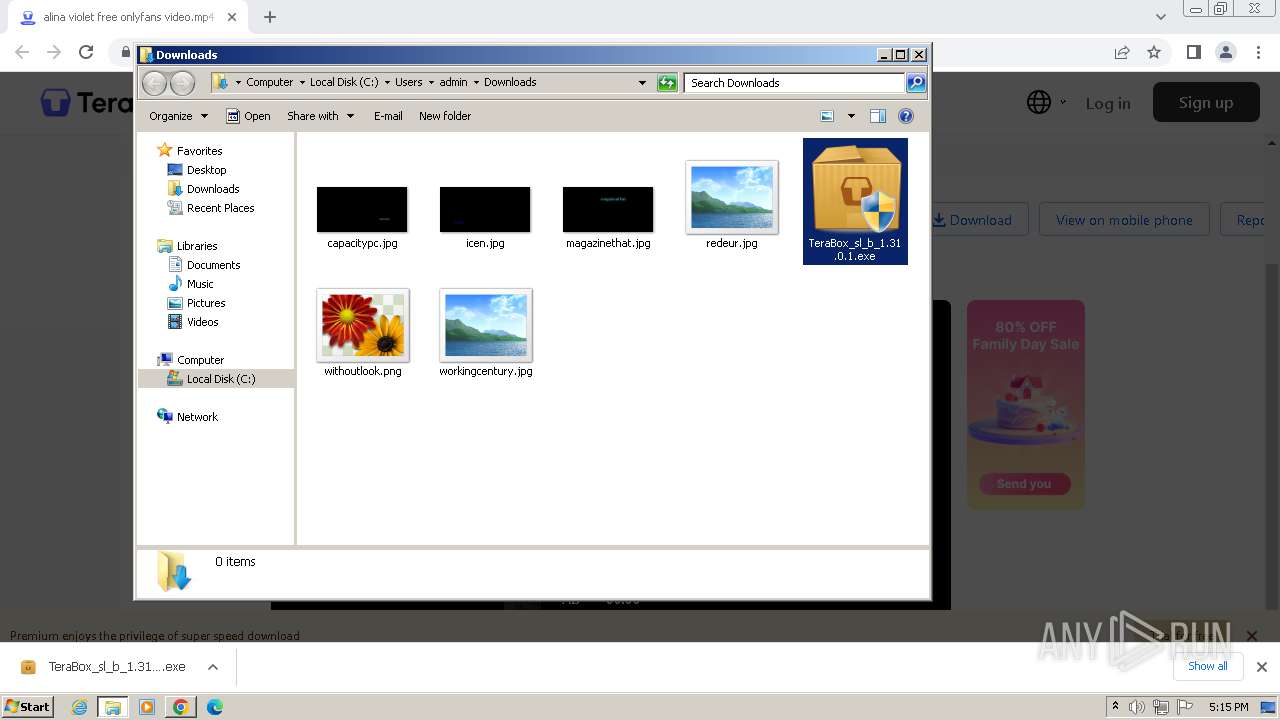
Creates files or folders in the user directory
- TeraBox_sl_b_1.31.0.1.exe (PID: 3712)
- TeraBox.exe (PID: 1288)
- TeraBox.exe (PID: 1468)
- TeraBoxWebService.exe (PID: 3344)
- TeraBoxHost.exe (PID: 3668)
- TeraBoxHost.exe (PID: 3680)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- TeraBoxHost.exe (PID: 2516)
- TeraBoxHost.exe (PID: 3660)
Checks proxy server information
- TeraBoxWebService.exe (PID: 3344)
- TeraBox.exe (PID: 1468)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 1288)
- TeraBoxWebService.exe (PID: 3344)
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3440)
- YunUtilityService.exe (PID: 1576)
- TeraBoxHost.exe (PID: 3668)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 2624)
- YunUtilityService.exe (PID: 2628)
- TeraBoxHost.exe (PID: 2516)
Process checks computer location settings
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3384)
- TeraBoxRender.exe (PID: 3784)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 3236)
- TeraBoxRender.exe (PID: 2444)
Reads the software policy settings
- TeraBox.exe (PID: 1468)
- TeraBoxRender.exe (PID: 3440)
- YunUtilityService.exe (PID: 1576)
- AutoUpdate.exe (PID: 3120)
- TeraBox.exe (PID: 3300)
- TeraBoxRender.exe (PID: 2624)
- YunUtilityService.exe (PID: 2628)
Creates files in the program directory
- TeraBoxHost.exe (PID: 3668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
76
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=1812 --field-trial-handle=1184,i,5209932811835677924,10621656628912531663,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 444 | "C:\Users\admin\Downloads\TeraBox_sl_b_1.31.0.1.exe" | C:\Users\admin\Downloads\TeraBox_sl_b_1.31.0.1.exe | — | explorer.exe | |||||||||||
User: admin Company: Flextech Integrity Level: MEDIUM Description: TeraBox Installer Exit code: 3221226540 Version: 1.31.0.1 Modules
| |||||||||||||||
| 552 | "C:\Windows\system32\regsvr32.exe" "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunOfficeAddin.dll" | C:\Windows\System32\regsvr32.exe | — | TeraBox_sl_b_1.31.0.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1524 --field-trial-handle=1184,i,5209932811835677924,10621656628912531663,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1292 --field-trial-handle=1184,i,5209932811835677924,10621656628912531663,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3544 --field-trial-handle=1184,i,5209932811835677924,10621656628912531663,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1080 --field-trial-handle=1184,i,5209932811835677924,10621656628912531663,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe" -install "createdetectstartup" -install "btassociation" -install "createshortcut" "0" -install "createstartup" | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_sl_b_1.31.0.1.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: HIGH Description: TeraBox Exit code: 1 Version: 1.31.0.1 Modules
| |||||||||||||||
| 1468 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_sl_b_1.31.0.1.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBox Exit code: 0 Version: 1.31.0.1 Modules
| |||||||||||||||
| 1576 | C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe | C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Flextech Inc. Integrity Level: SYSTEM Description: TeraBox Service Used to Quickly Apply For Disk Space Exit code: 0 Version: 1.31.0.1 Modules
| |||||||||||||||
Total events
73 637
Read events
72 953
Write events
639
Delete events
45
Modification events
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
88
Suspicious files
355
Text files
56
Unknown types
201
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF103f9b.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF103f9b.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF104cca.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF10418f.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
210
DNS requests
142
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.13 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.00 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.74 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.52 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 20.5 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 41.7 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 66.8 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 146 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 348 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
820 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | unknown |
3964 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
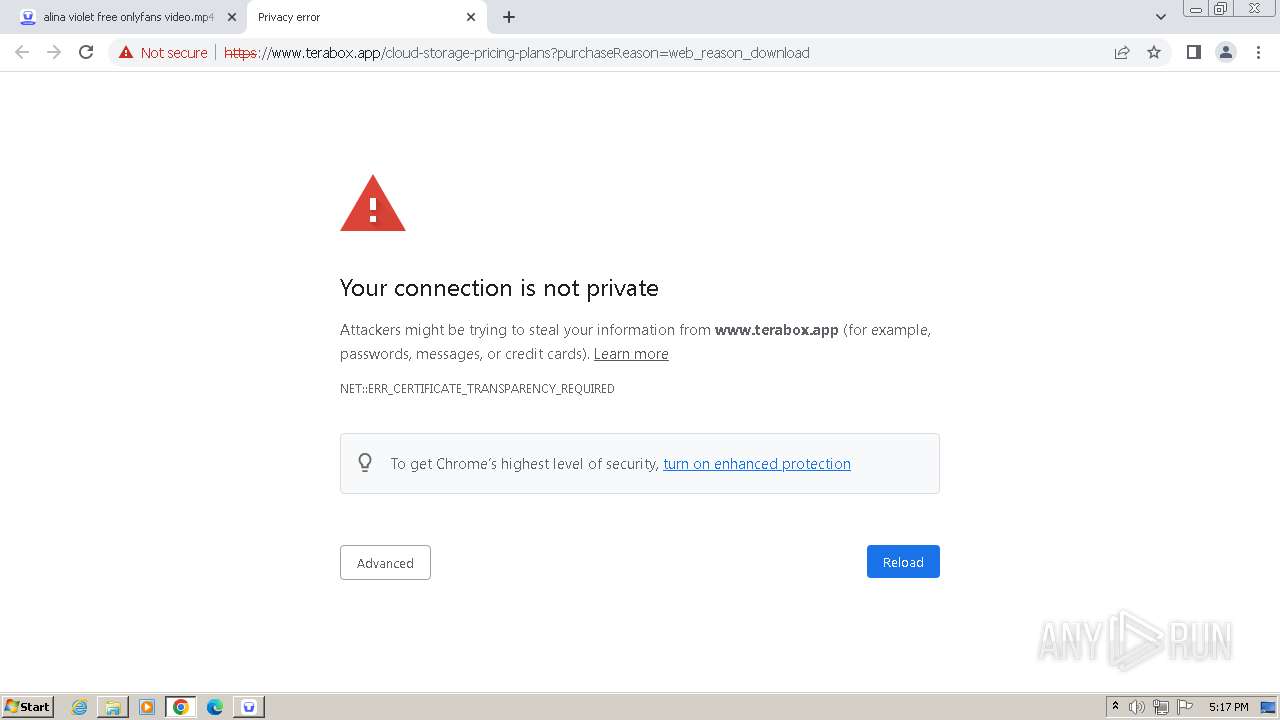
820 | chrome.exe | 210.148.85.14:443 | terabox.app | Internet Initiative Japan Inc. | JP | unknown |
820 | chrome.exe | 128.1.34.162:443 | www.staticcc.com | ZEN-ECN | DE | unknown |
820 | chrome.exe | 142.250.185.170:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
820 | chrome.exe | 18.66.112.74:443 | static.line-scdn.net | AMAZON-02 | US | unknown |
820 | chrome.exe | 142.250.184.234:443 | firebase.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
terabox.app |
| unknown |
accounts.google.com |
| shared |
www.terabox.app |
| unknown |
www.staticcc.com |
| unknown |
blog.terabox.com |
| unknown |
data.terabox.app |
| unknown |
ymg-api.terabox.app |
| unknown |
safebrowsing.googleapis.com |
| whitelisted |
s2.teraboxcdn.com |
| unknown |
sofire.bdstatic.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
— | — | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
820 | chrome.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
— | — | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
820 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
Process | Message |
|---|---|
TeraBoxHost.exe | vast_media--[2024-05-26 17:16:08:237] Initialized sdl_audio_play_driver=directsound
|
TeraBoxHost.exe | vast_media--[2024-05-26 17:16:08:237] Initialized sdl_video_render_driver=software
|
TeraBoxHost.exe | vast_media--[2024-05-26 17:16:08:237] Initialized hardware_type=3001
|
TeraBoxHost.exe | vast_media--[2024-05-26 17:17:24:637] Initialized sdl_video_render_driver=software
|
TeraBoxHost.exe | vast_media--[2024-05-26 17:17:24:637] Initialized hardware_type=3001
|
TeraBoxHost.exe | vast_media--[2024-05-26 17:17:24:637] Initialized sdl_audio_play_driver=directsound
|