analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
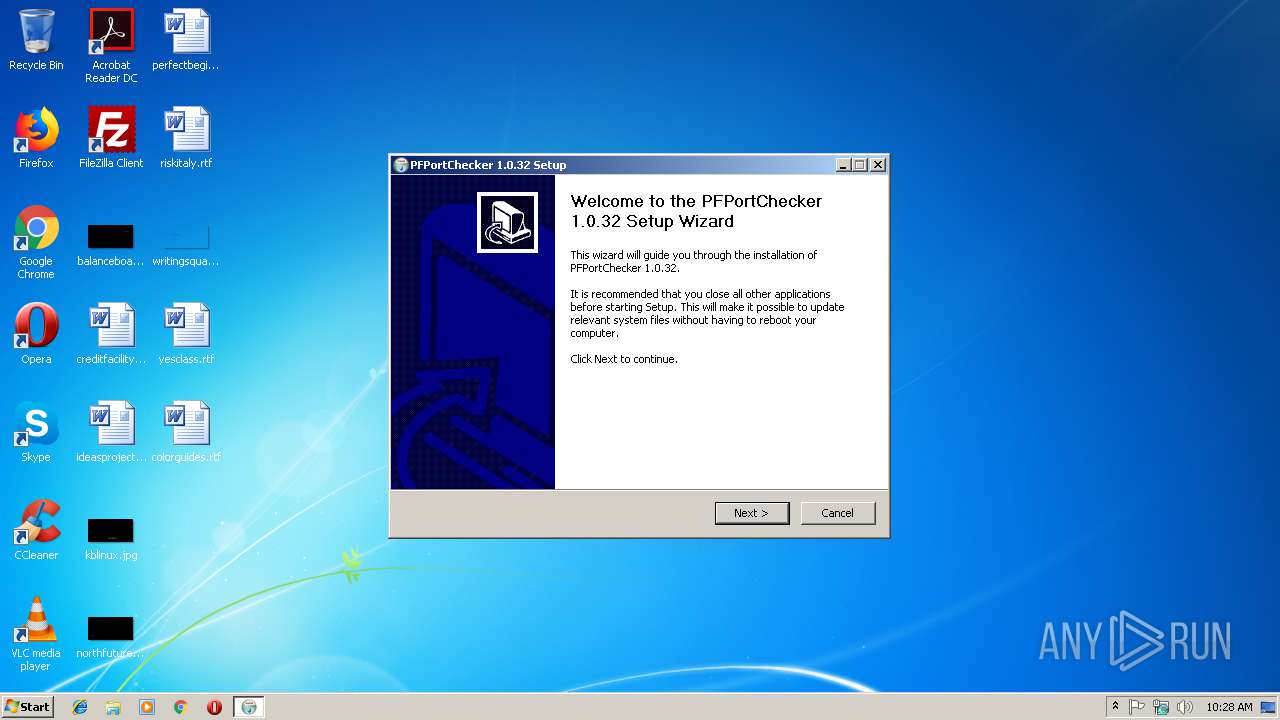
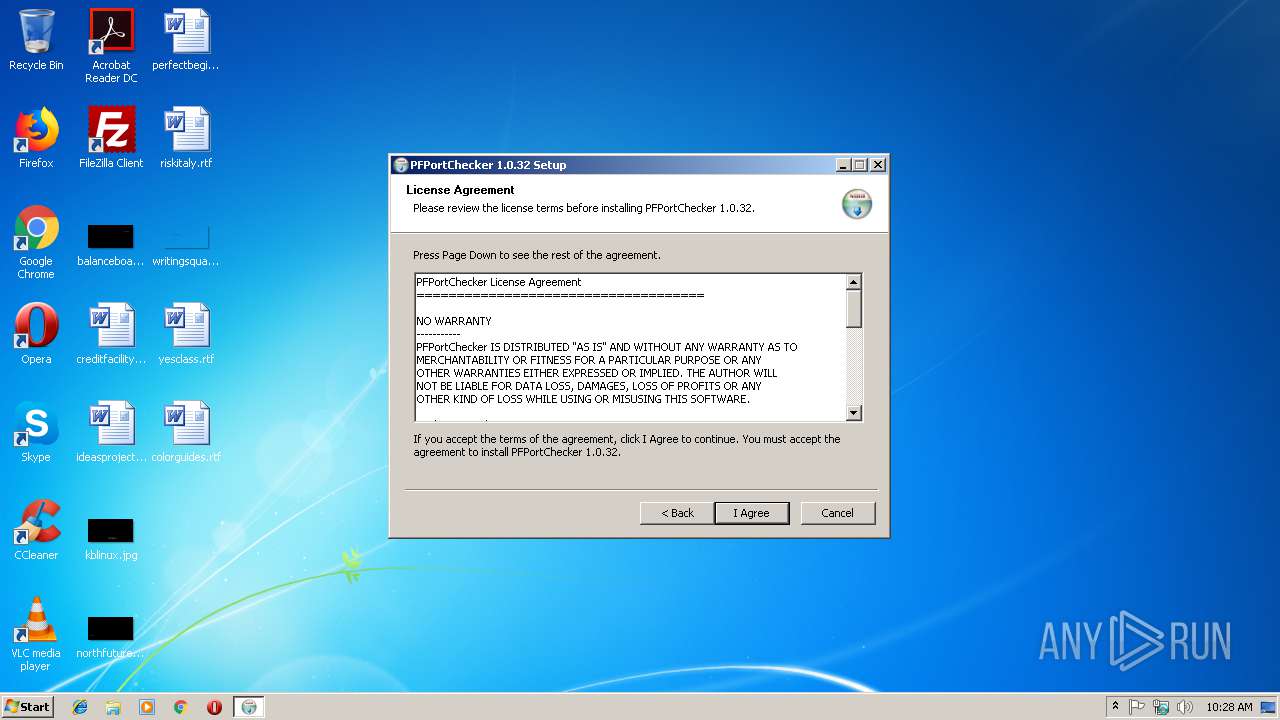
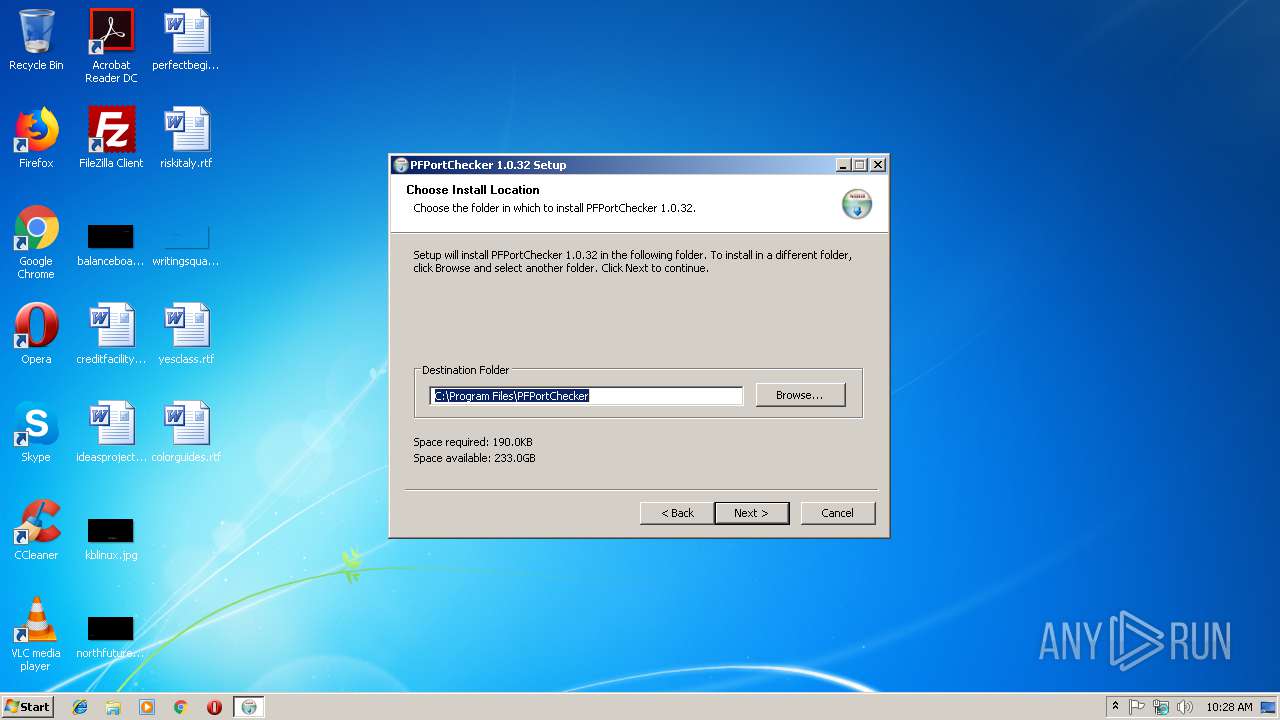
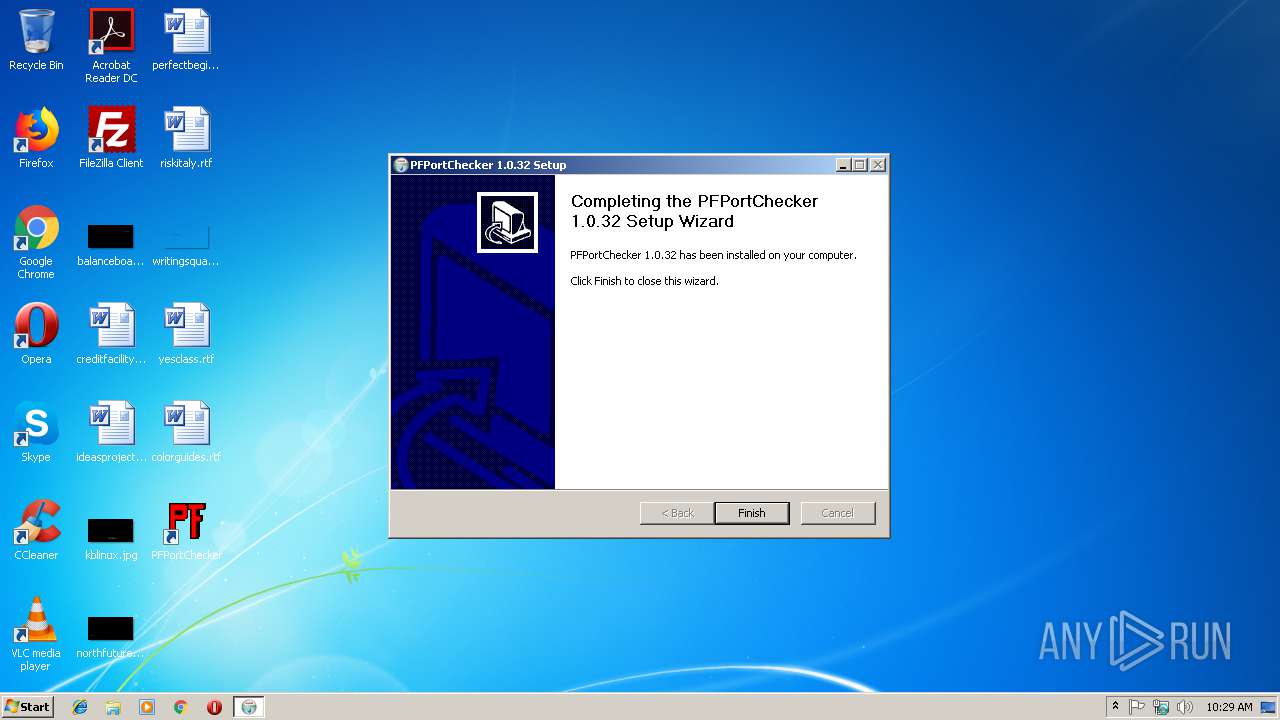
| File name: | PFPortChecker.exe |
| Full analysis: | https://app.any.run/tasks/780c4d0b-d21c-42b4-927c-03380a5241c1 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 10:28:23 |
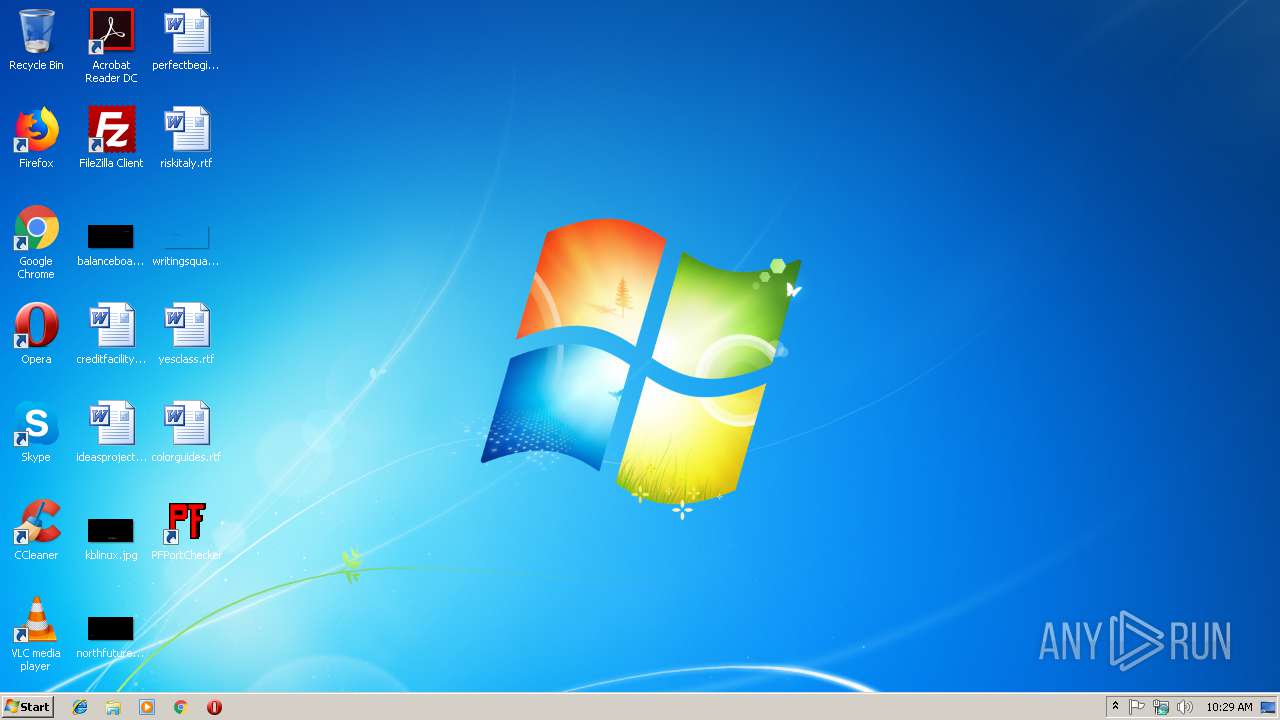
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 20C85C4D158097634816C0EC342139A2 |
| SHA1: | 491E2B79072890B6E193585D21DB40588787A480 |
| SHA256: | 3FE77A676479A75DD2EF25705CEC70FD06F62C9CCC29E16B3180DCB63E330BB4 |
| SSDEEP: | 49152:8SsXGVQDCv9f63SXV02Xb4tx6oi1Kdfvi/knzeiN:IG+uR63S8x6vodfvpzRN |
MALICIOUS
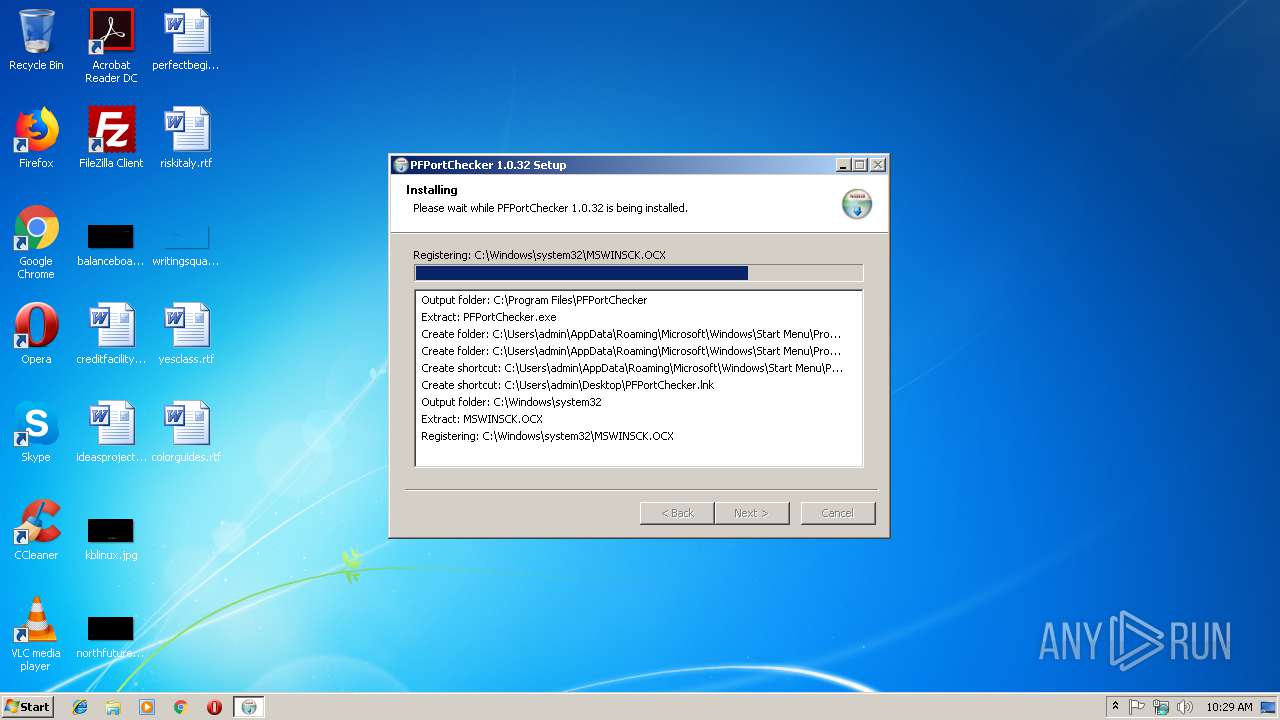
Loads dropped or rewritten executable
- PFPortChecker.exe (PID: 4080)
Application was dropped or rewritten from another process
- AskInstallChecker-1.1.0.0.exe (PID: 2444)
- askToolbarInstaller-1.5.0.0.exe (PID: 2796)
- NEW8EFE.tmp.exe (PID: 2248)
- JSXPCOMInstaller.exe (PID: 2916)
- askHomePage.exe (PID: 2748)
- Processor64Bit.exe (PID: 2832)
- AskPartnerCobrandingTool.exe (PID: 4052)
- TaskScheduler.exe (PID: 3656)
Loads the Task Scheduler COM API
- TaskScheduler.exe (PID: 3656)
SUSPICIOUS
Executable content was dropped or overwritten
- PFPortChecker.exe (PID: 4080)
- askToolbarInstaller-1.5.0.0.exe (PID: 2796)
- NEW8EFE.tmp.exe (PID: 2248)
- MsiExec.exe (PID: 3476)
- msiexec.exe (PID: 2460)
Starts Microsoft Installer
- NEW8EFE.tmp.exe (PID: 2248)
Creates files in the Windows directory
- PFPortChecker.exe (PID: 4080)
Creates a software uninstall entry
- PFPortChecker.exe (PID: 4080)
Creates files in the user directory
- PFPortChecker.exe (PID: 4080)
Changes the started page of IE
- askHomePage.exe (PID: 2748)
Creates files in the program directory
- PFPortChecker.exe (PID: 4080)
Creates COM task schedule object
- MsiExec.exe (PID: 3000)
INFO
Application launched itself
- msiexec.exe (PID: 2460)
Starts application with an unusual extension
- msiexec.exe (PID: 2460)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3000)
Application was dropped or rewritten from another process
- MSI97CA.tmp (PID: 2328)
Creates files in the program directory
- msiexec.exe (PID: 2460)
Creates a software uninstall entry
- msiexec.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6.1 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:06:06 23:41:54+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2009 21:41:54 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2009 21:41:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00017000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x000042D8 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.90403 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21446 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
51
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3636 | "C:\Users\admin\AppData\Local\Temp\PFPortChecker.exe" | C:\Users\admin\AppData\Local\Temp\PFPortChecker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\PFPortChecker.exe" | C:\Users\admin\AppData\Local\Temp\PFPortChecker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2444 | "C:\Users\admin\AppData\Local\Temp\nsgE40A.tmp\AskInstallChecker-1.1.0.0.exe" PF | C:\Users\admin\AppData\Local\Temp\nsgE40A.tmp\AskInstallChecker-1.1.0.0.exe | PFPortChecker.exe | ||||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: Ask Install Checker Exit code: 0 Version: 1,1,0,0 Modules
| |||||||||||||||
| 2796 | "C:\Users\admin\AppData\Local\Temp\nsgE40A.tmp\askToolbarInstaller-1.5.0.0.exe" /tbr /sa /hpr /verysilent toolbar=PF | C:\Users\admin\AppData\Local\Temp\nsgE40A.tmp\askToolbarInstaller-1.5.0.0.exe | PFPortChecker.exe | ||||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: wrapper Application Exit code: 0 Version: 15, 0, 0, 498 Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\AppData\Local\Temp\NEW8EFE.tmp.exe" /s /v"PARTNER=PF /qn" | C:\Users\admin\AppData\Local\Temp\NEW8EFE.tmp.exe | askToolbarInstaller-1.5.0.0.exe | ||||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: Setup Launcher Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 596 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\{2B666535-06D6-4BCA-A9FC-4195BB54EB3C}\Ask Toolbar.msi" /L*vx C:\Users\admin\AppData\Local\Temp\ASKSUTBLOG PARTNER=PF /qn TRANSFORMS="C:\Users\admin\AppData\Local\Temp\{2B666535-06D6-4BCA-A9FC-4195BB54EB3C}\1033.MST" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp" SETUPEXENAME="NEW8EFE.tmp.exe" | C:\Windows\system32\MSIEXEC.EXE | — | NEW8EFE.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | C:\Windows\system32\MsiExec.exe -Embedding 43A03885179FD9DF7D96E1DFBB2976F8 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\Processor64Bit.exe" | C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\Processor64Bit.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: Check Processor Architecture is 64 bit Exit code: 4294967295 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\askHomePage.exe" PF | C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\askHomePage.exe | MsiExec.exe | ||||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: Ask Home Page Reset for Internet Explorer Exit code: 0 Version: 1,0,0,4 Modules
| |||||||||||||||
Total events
1 615
Read events
1 279
Write events
320
Delete events
16
Modification events
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2444) AskInstallChecker-1.1.0.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AskInstallChecker-1_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
25
Suspicious files
3
Text files
141
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90A4.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90A5.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90B5.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90B6.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90B8.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90C9.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90CA.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90CB.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | NEW8EFE.tmp.exe | C:\Users\admin\AppData\Local\Temp\_is90CC.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2444 | AskInstallChecker-1.1.0.0.exe | GET | — | 199.36.100.107:80 | http://toolbar.ask.com/askbardis/util/askInstallChecker.jsp?p=PF&o=&ai=51386 | US | — | — | suspicious |
4052 | AskPartnerCobrandingTool.exe | GET | 200 | 199.36.102.106:80 | http://supertoolbar.ask.com/interim/askbardis/getTbProperties.jsp?tbr=PF | US | text | 410 b | suspicious |
2748 | askHomePage.exe | GET | 200 | 199.36.102.106:80 | http://supertoolbar.ask.com/homepage?tb=PF | US | text | 40 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | askHomePage.exe | 199.36.102.106:80 | supertoolbar.ask.com | Mindspark Interactive Network, Inc. | US | suspicious |
4052 | AskPartnerCobrandingTool.exe | 199.36.102.106:80 | supertoolbar.ask.com | Mindspark Interactive Network, Inc. | US | suspicious |
2444 | AskInstallChecker-1.1.0.0.exe | 199.36.100.107:80 | toolbar.ask.com | Mindspark Interactive Network, Inc. | US | suspicious |
4080 | PFPortChecker.exe | 65.112.29.35:443 | secure.portforward.com | Computer Country | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
toolbar.ask.com |
| suspicious |
secure.portforward.com |
| unknown |
supertoolbar.ask.com |
| suspicious |
wzpo1.ask.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2444 | AskInstallChecker-1.1.0.0.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious User Agent (AskInstallChecker) |
4052 | AskPartnerCobrandingTool.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent String (AskPartnerCobranding) |
Process | Message |
|---|---|
TaskScheduler.exe | SetChrome.. |
TaskScheduler.exe | success! |