| File name: | GoodCheck_v1.3.02_by_Ori.zip |
| Full analysis: | https://app.any.run/tasks/ad165205-f1ab-49fc-a65f-ecd3647249e1 |
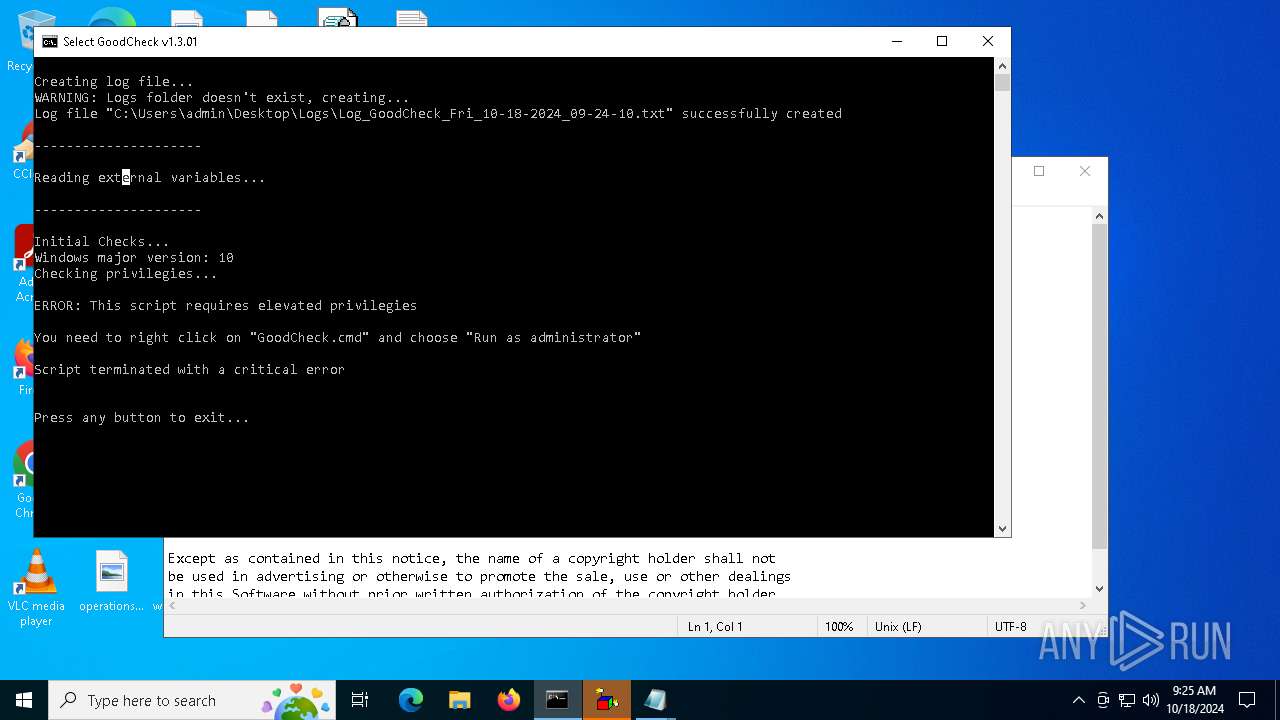
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2024, 09:23:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | FA8BC0DAE14A67C2E599ECCCD3C670D5 |
| SHA1: | 5E16BFF7B061C10B5944AFE2CD64306696F2935B |
| SHA256: | 3FE09876AF783A66168E0E1619396F7AA665ABB698B0B20649ADE648EBEFED83 |
| SSDEEP: | 98304:rgL+Yw/vLkBqrMjeQK2LIWMjSdY67Dh24zbn4H+xrDVkXHsTCkBxIhatGSjcSDJH:wJLNGcm+P2y3M0qo |
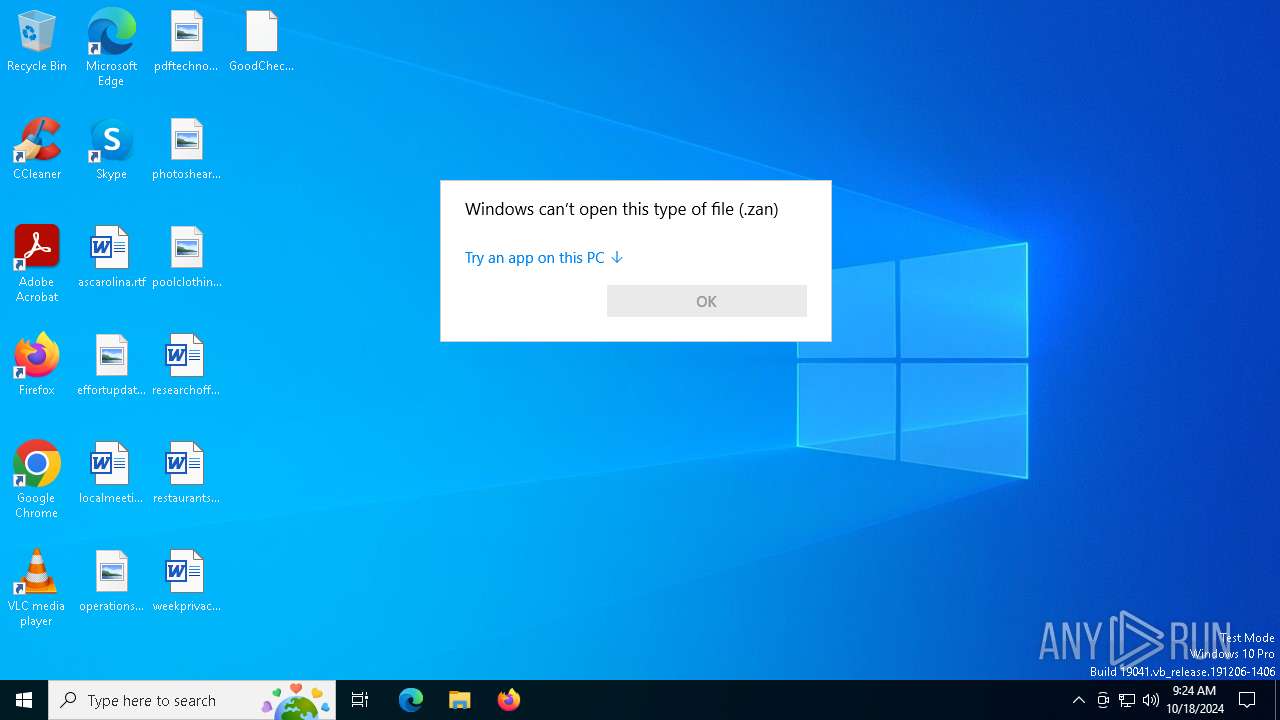
MALICIOUS
Generic archive extractor
- OpenWith.exe (PID: 6688)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 5940)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6408)
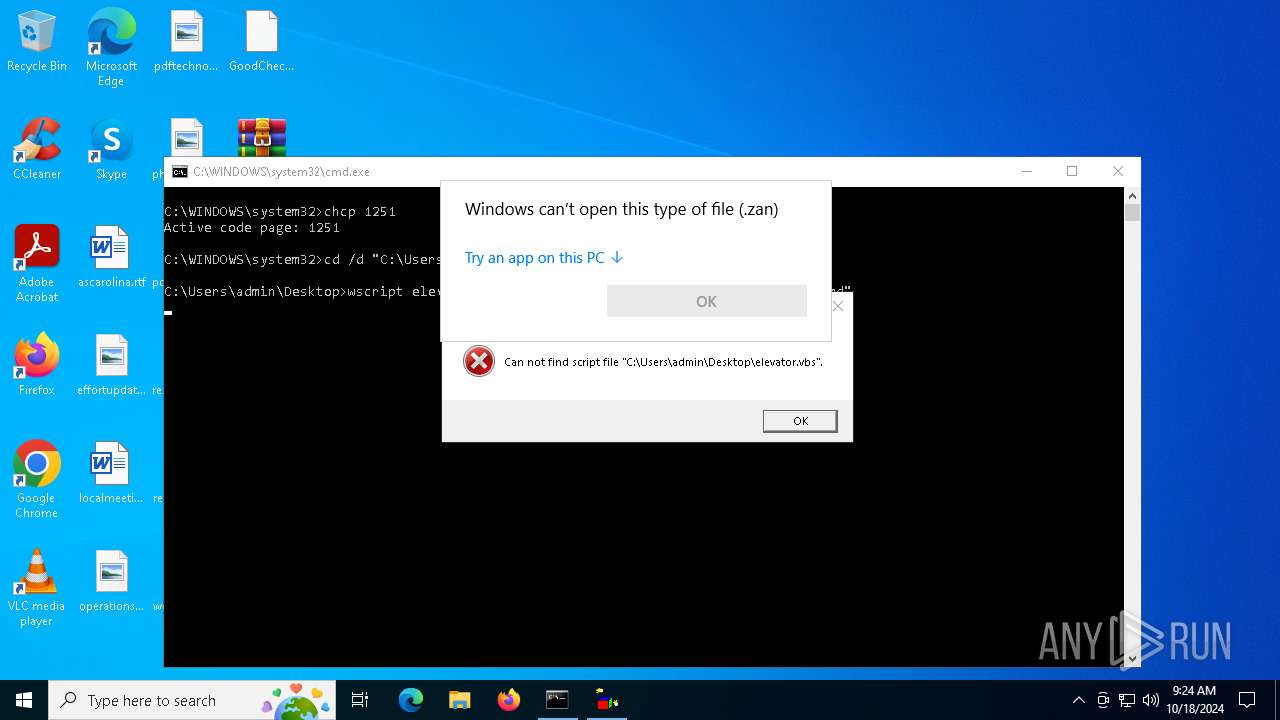
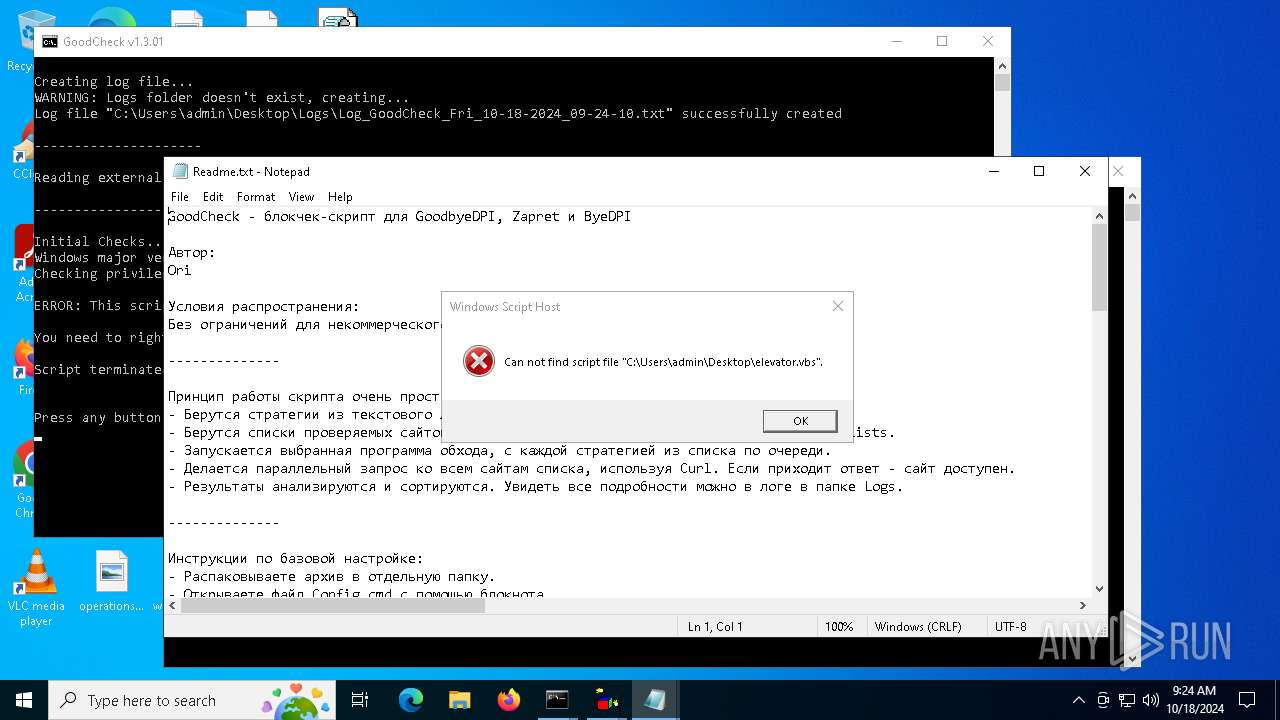
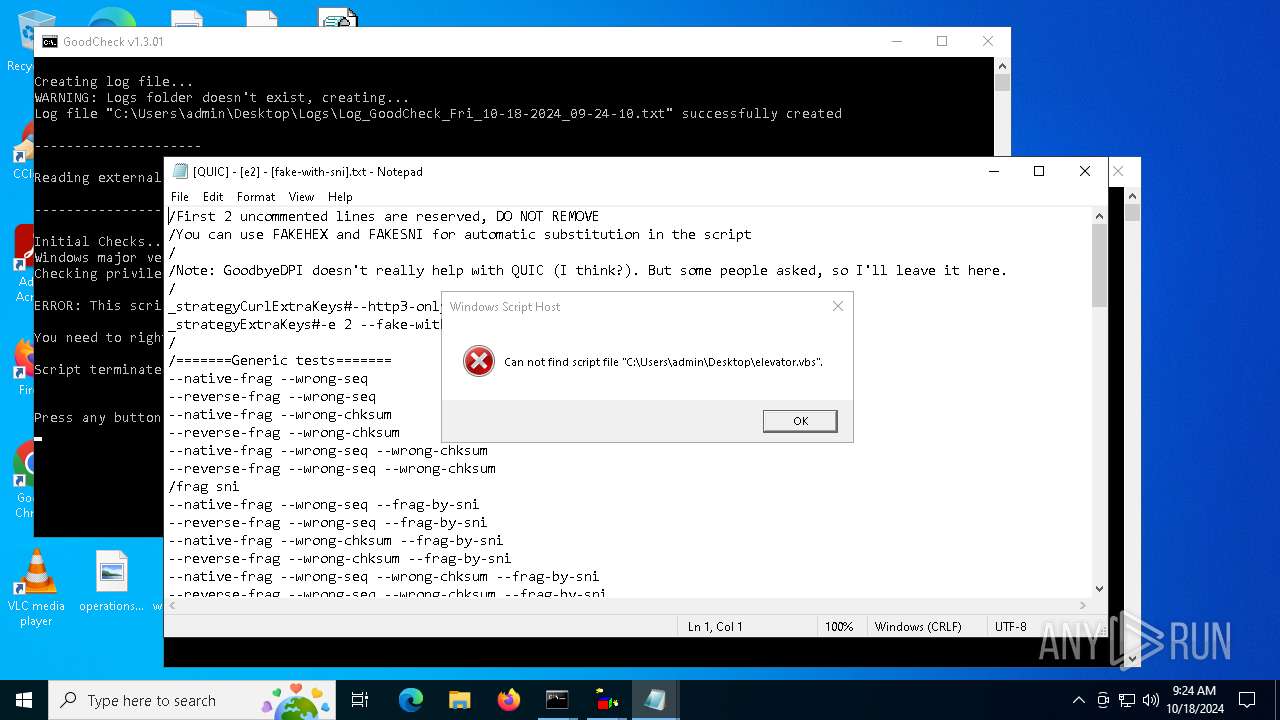
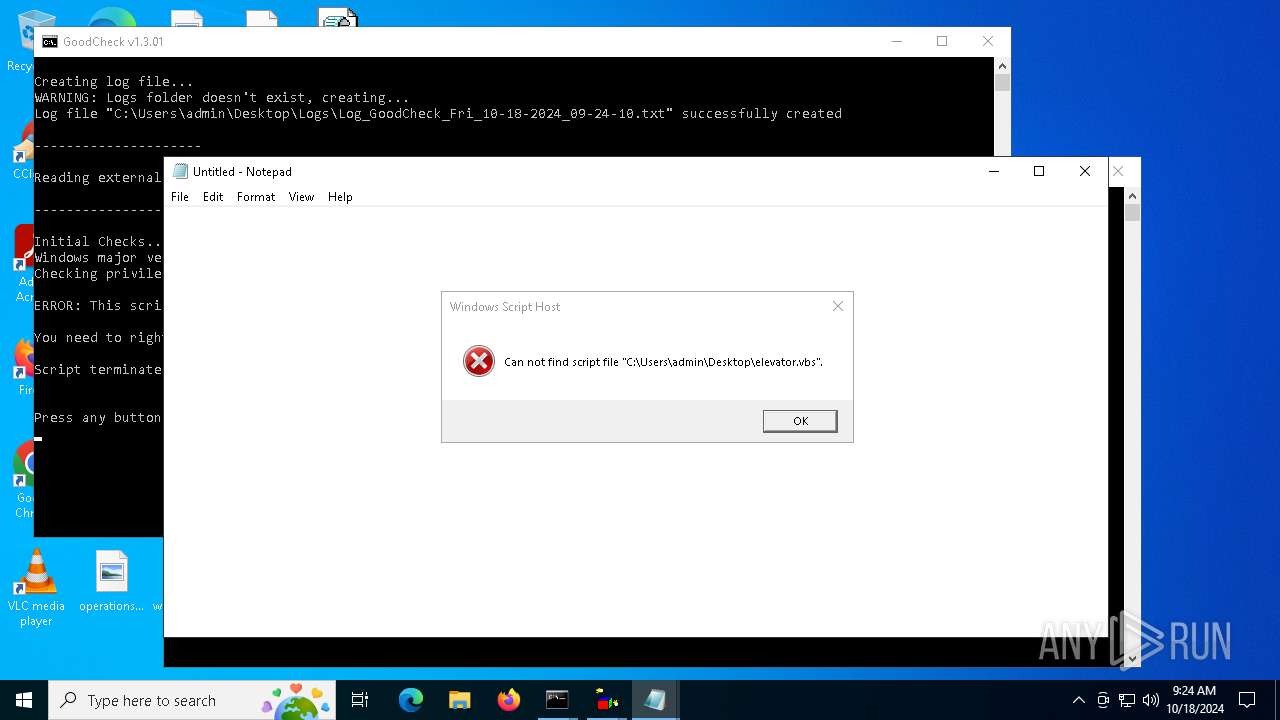
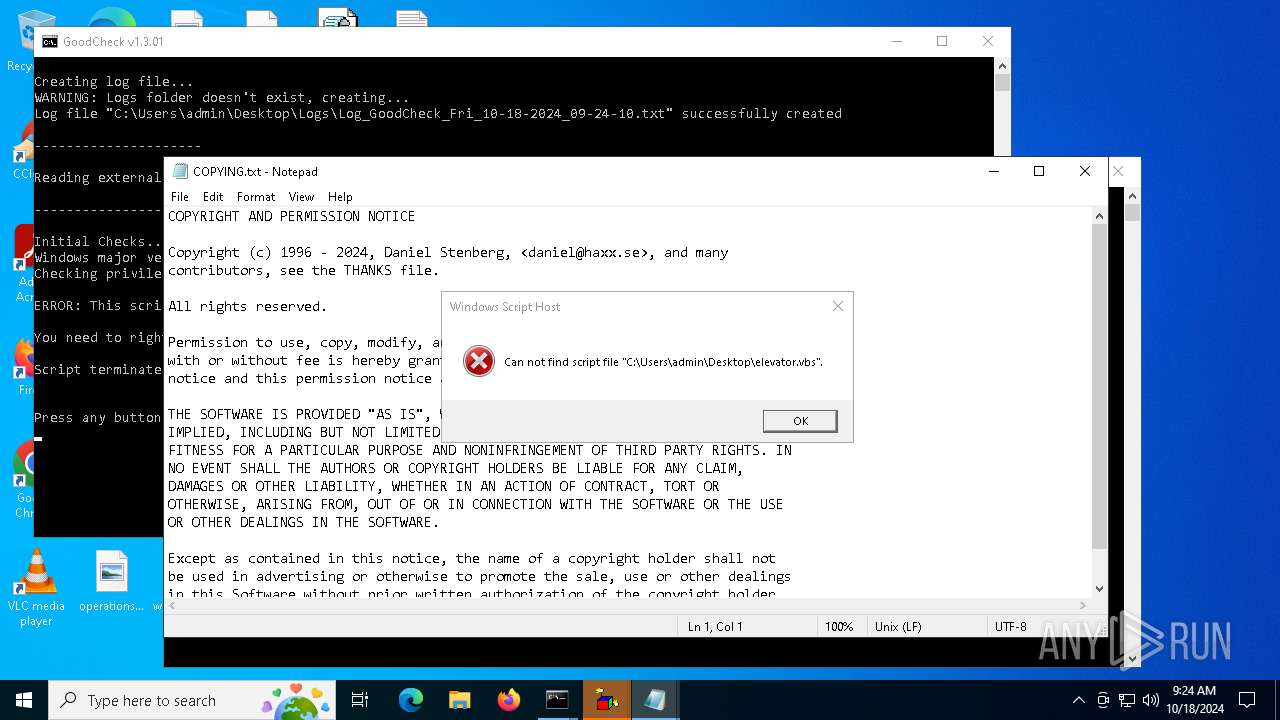
The process executes VB scripts
- cmd.exe (PID: 6384)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6408)
Application launched itself
- cmd.exe (PID: 6408)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6688)
Changes the display of characters in the console
- cmd.exe (PID: 5940)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6408)
Manual execution by a user
- cmd.exe (PID: 6384)
- cmd.exe (PID: 5940)
- cmd.exe (PID: 6408)
- wscript.exe (PID: 2652)
- notepad.exe (PID: 1792)
- notepad.exe (PID: 3832)
- notepad.exe (PID: 6684)
- notepad.exe (PID: 6820)
- notepad.exe (PID: 5196)
- notepad.exe (PID: 3732)
Checks supported languages
- chcp.com (PID: 4556)
Checks operating system version
- cmd.exe (PID: 6408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zan | | | BlueEyes Animation (55.1) |
|---|---|---|
| .zip | | | ZIP compressed archive (16.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:16 10:04:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | GoodCheck_v1.3.02_by_Ori/ |
Total processes
141
Monitored processes
20
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
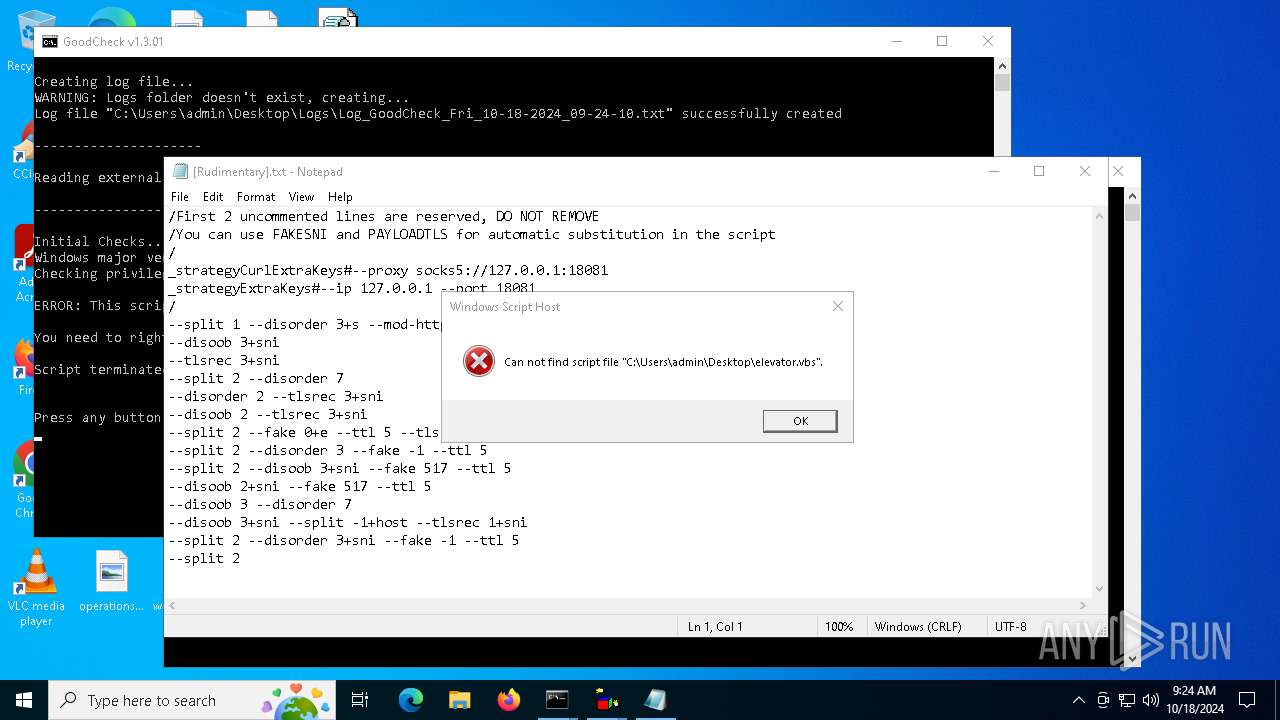
| 1792 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\[Rudimentary].txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | wscript elevator.vbs cmd /c "C:\Users\admin\Desktop\Config.cmd" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2652 | "C:\WINDOWS\System32\WScript.exe" C:\Users\admin\Desktop\elevator.vbs | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3732 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\COPYING.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Readme.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | C:\WINDOWS\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4556 | chcp 1251 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5196 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\[QUIC] - [e2] - [fake-with-sni].txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 946
Read events
1 946
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
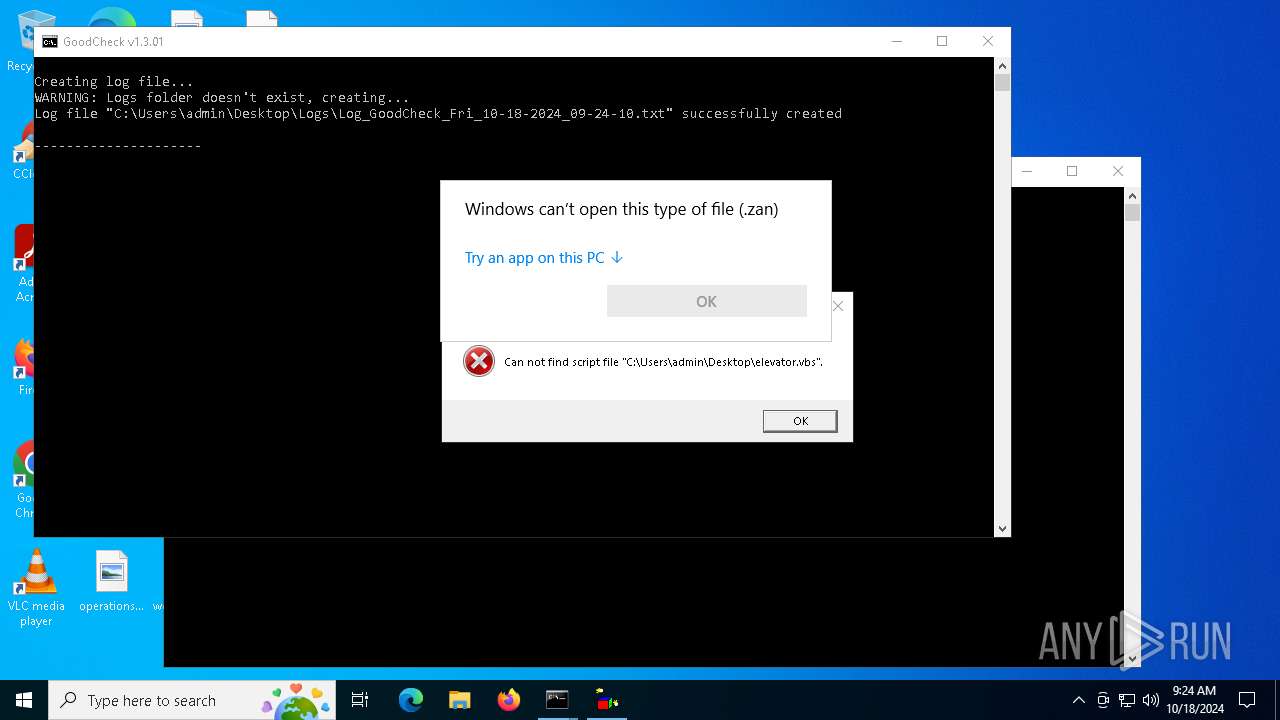
| 6408 | cmd.exe | C:\Users\admin\Desktop\Logs\Log_GoodCheck_Fri_10-18-2024_09-24-10.txt | text | |
MD5:4E8737F6A58F145424FA0047B625F530 | SHA256:CA93CFCACA98A2BAF7424DD66FE247A8FAED2BE9B30A9BC268031766EE9EACED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5700 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5700 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5700 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.29:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5700 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5700 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |