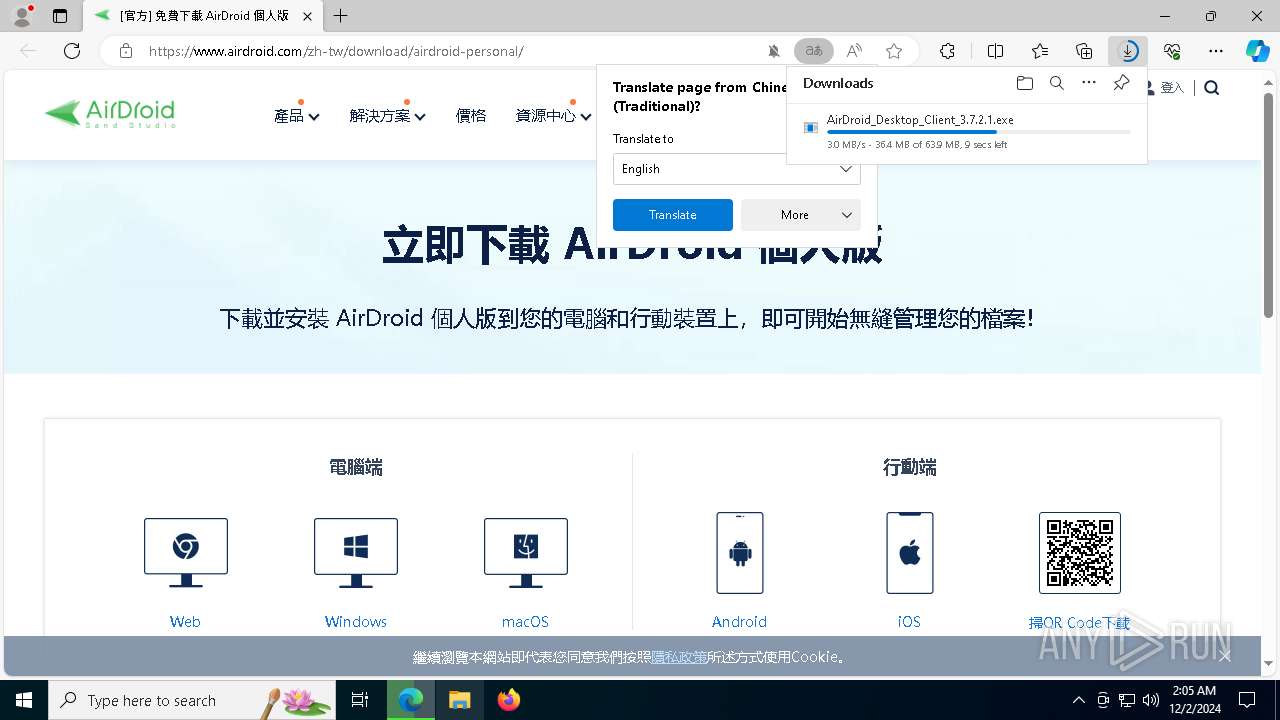
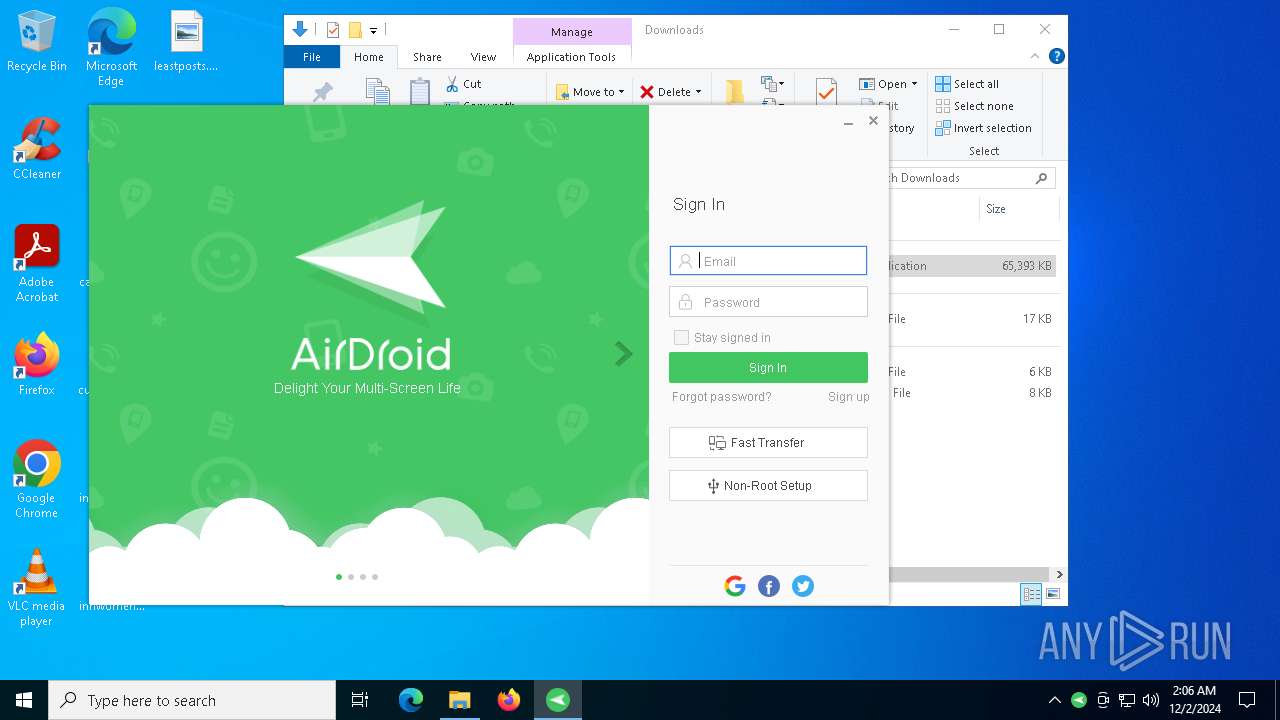
| URL: | https://www.airdroid.com/zh-tw/download/airdroid-personal/ |
| Full analysis: | https://app.any.run/tasks/320813c7-cb20-4c99-8191-a8f6250164a6 |
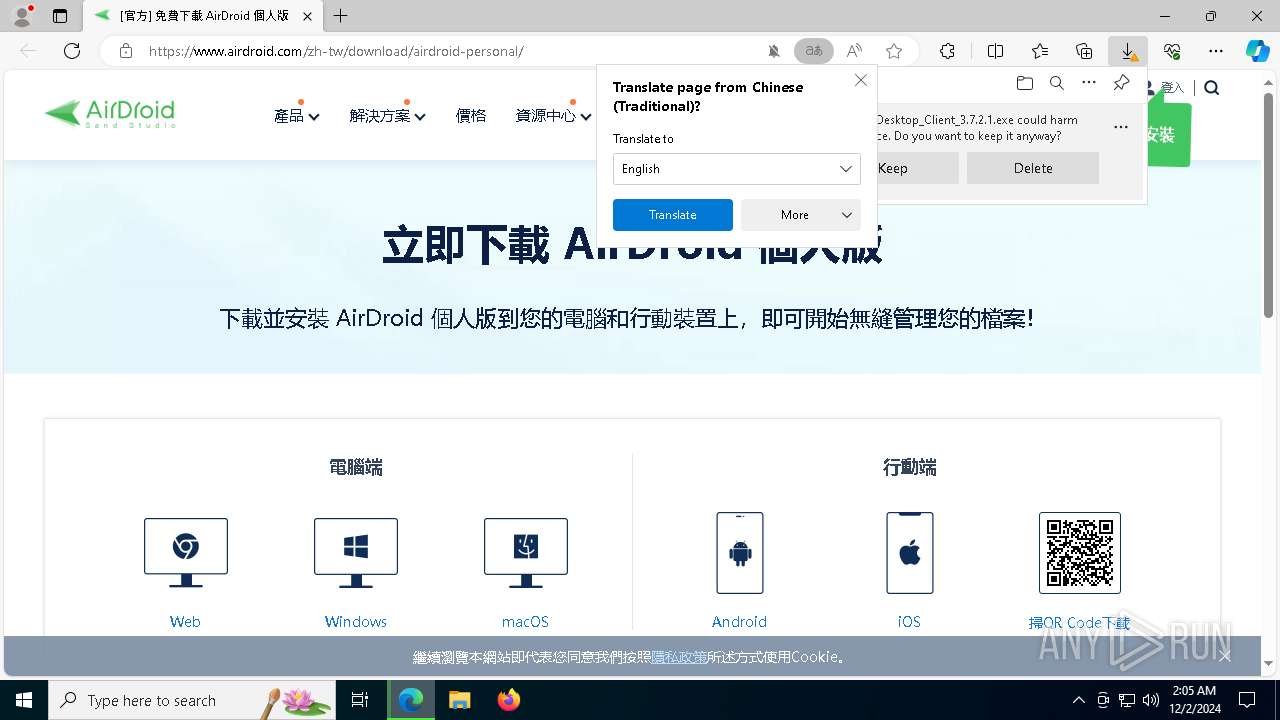
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2024, 02:05:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 85D618D9D57C02B4D7FAF224510A6638 |
| SHA1: | D2C42C5DCB6703B38BA6938BEBA87D0CEBE5E1BF |
| SHA256: | 3FD53579F945790DCEADAA0D72B2515C8360E0626D28C69AA77B1493C5A16BAB |
| SSDEEP: | 3:N8DSLuMBrk9klNBo+Pn:2OLDB4sNBvP |
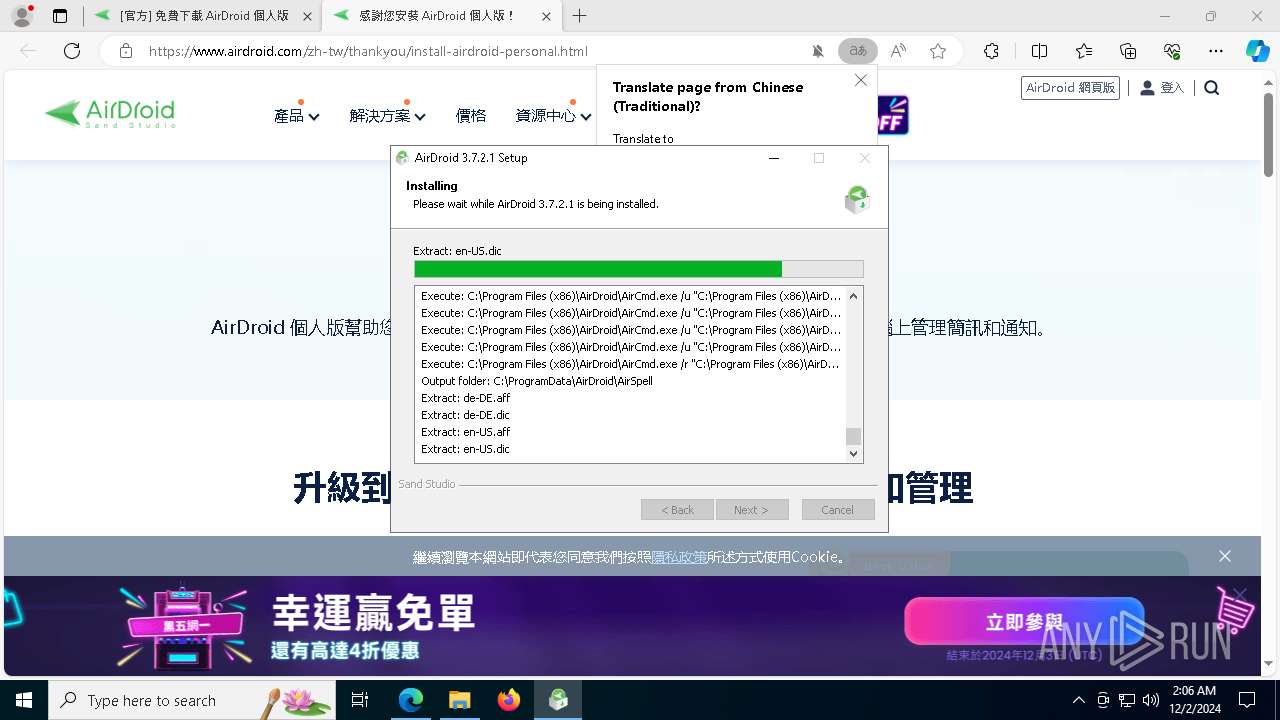
MALICIOUS
Executing a file with an untrusted certificate
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 8040)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Actions looks like stealing of personal data
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
SUSPICIOUS
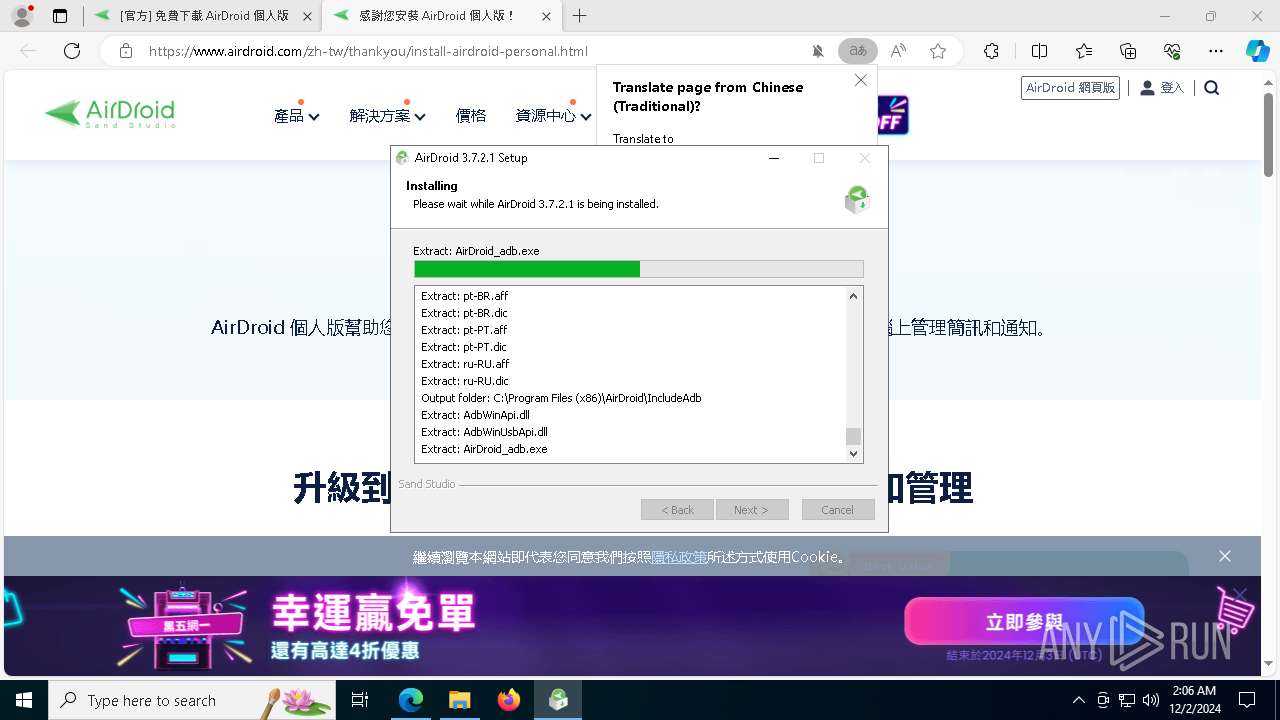
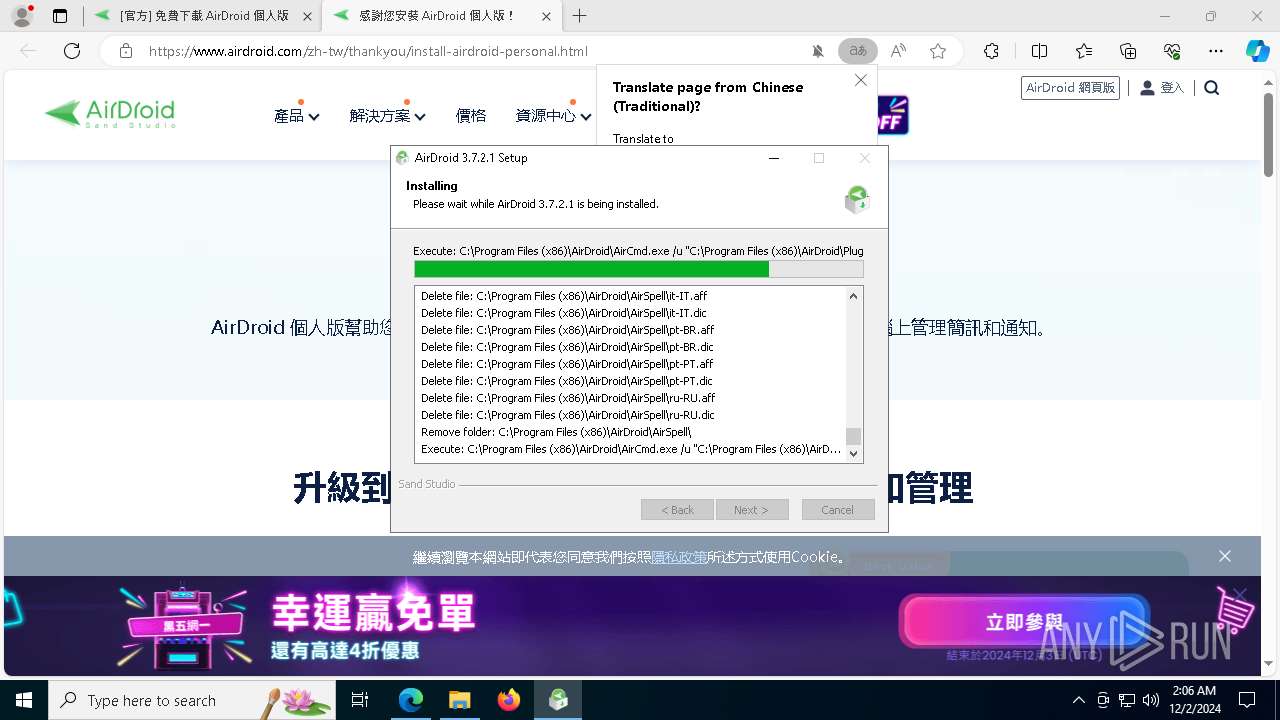
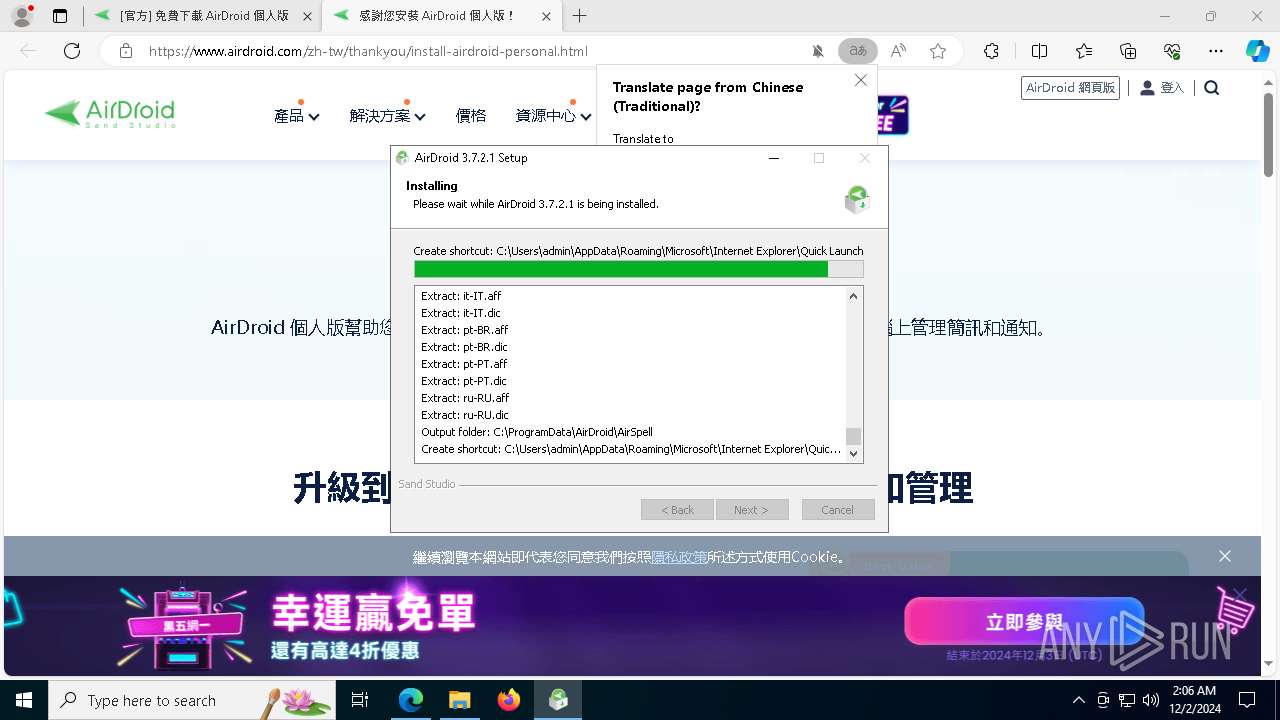
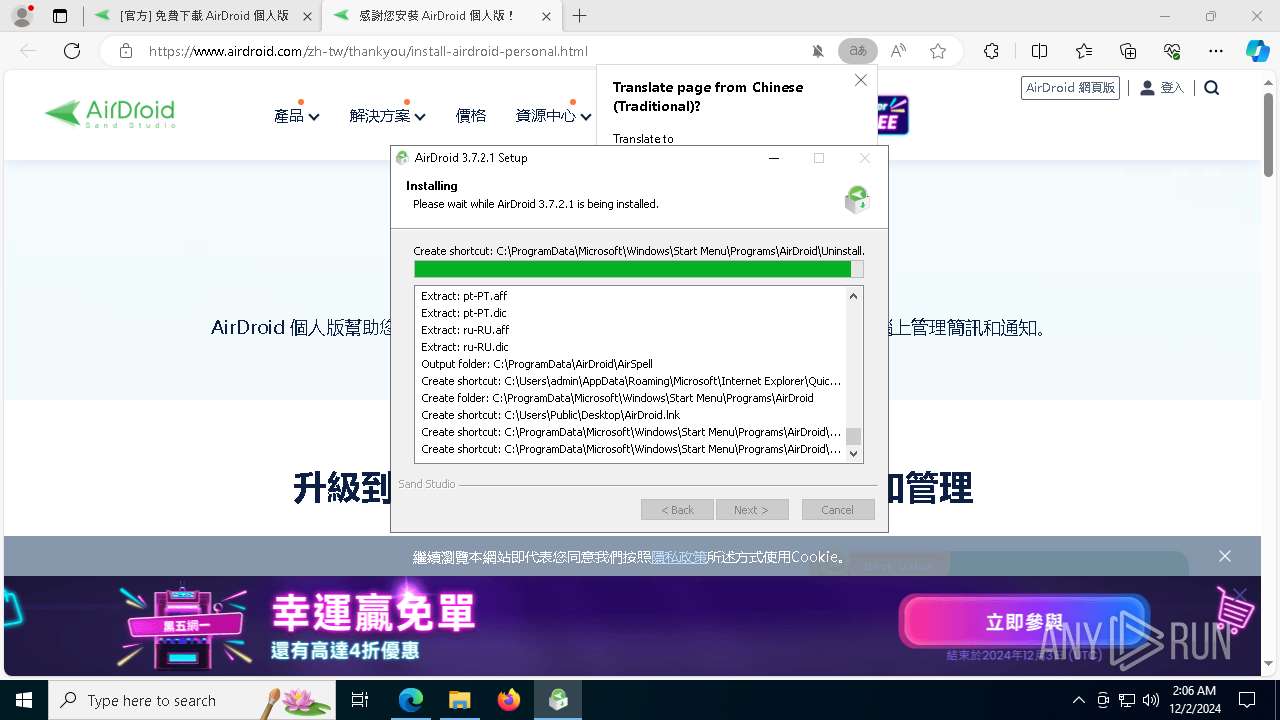
Executable content was dropped or overwritten
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Malware-specific behavior (creating "System.dll" in Temp)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
The process creates files with name similar to system file names
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads the BIOS version
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads security settings of Internet Explorer
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- AirCmd.exe (PID: 2680)
- AirCmd.exe (PID: 1556)
- AirCmd.exe (PID: 1412)
- AirCmd.exe (PID: 7036)
- AirCmd.exe (PID: 7172)
- AirDroid.exe (PID: 6892)
The process drops C-runtime libraries
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads Microsoft Outlook installation path
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads Internet Explorer settings
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Process drops legitimate windows executable
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Creates/Modifies COM task schedule object
- AirCmd.exe (PID: 7172)
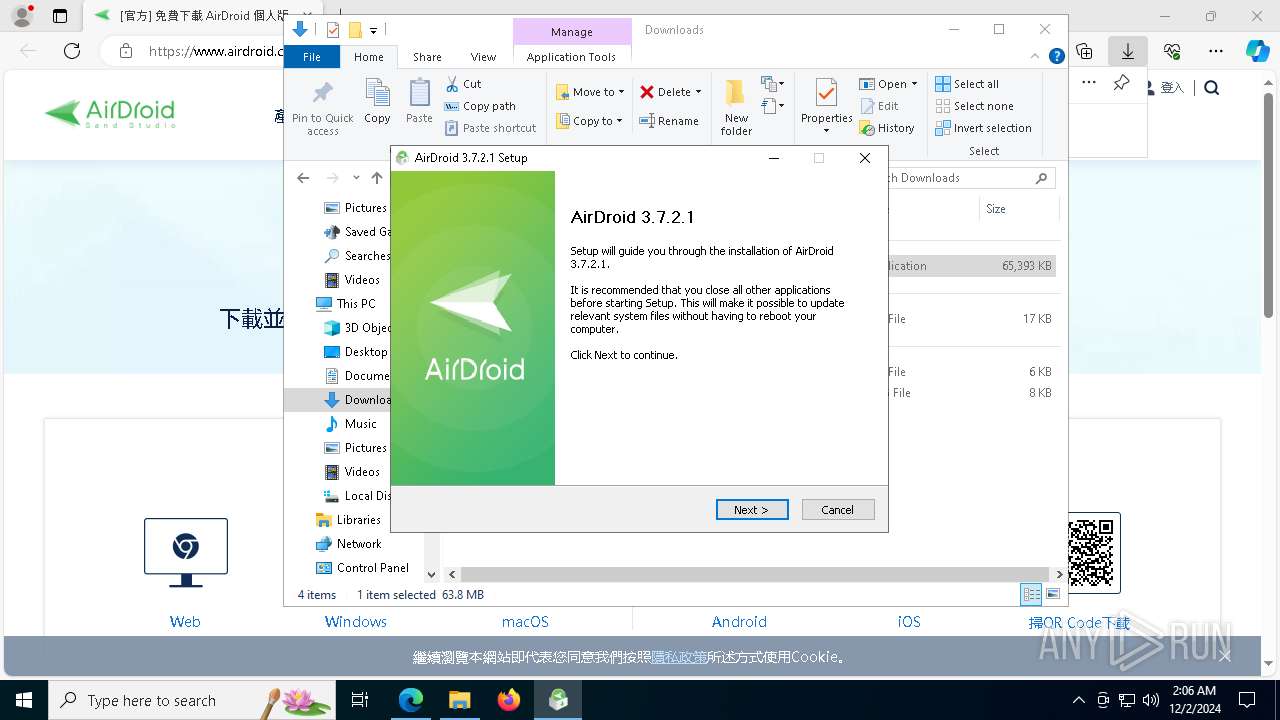
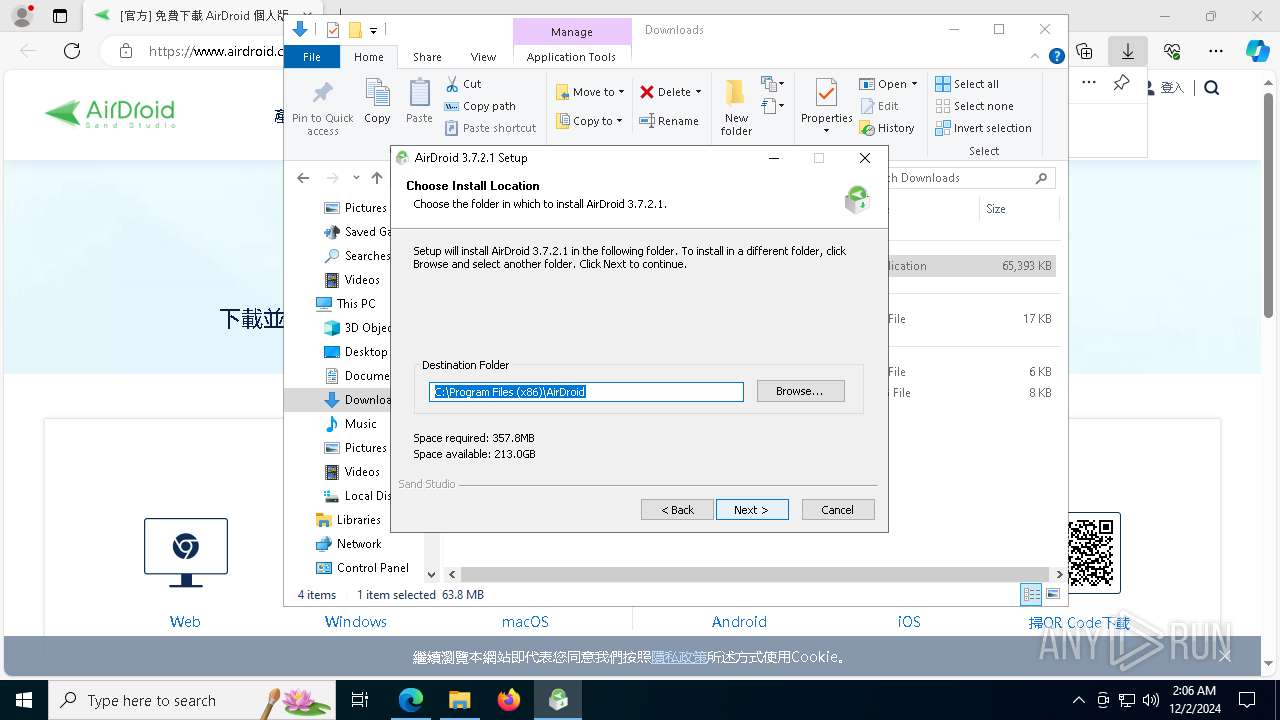
Creates a software uninstall entry
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
INFO
Application launched itself
- msedge.exe (PID: 3608)
- msedge.exe (PID: 7532)
Executable content was dropped or overwritten
- msedge.exe (PID: 3608)
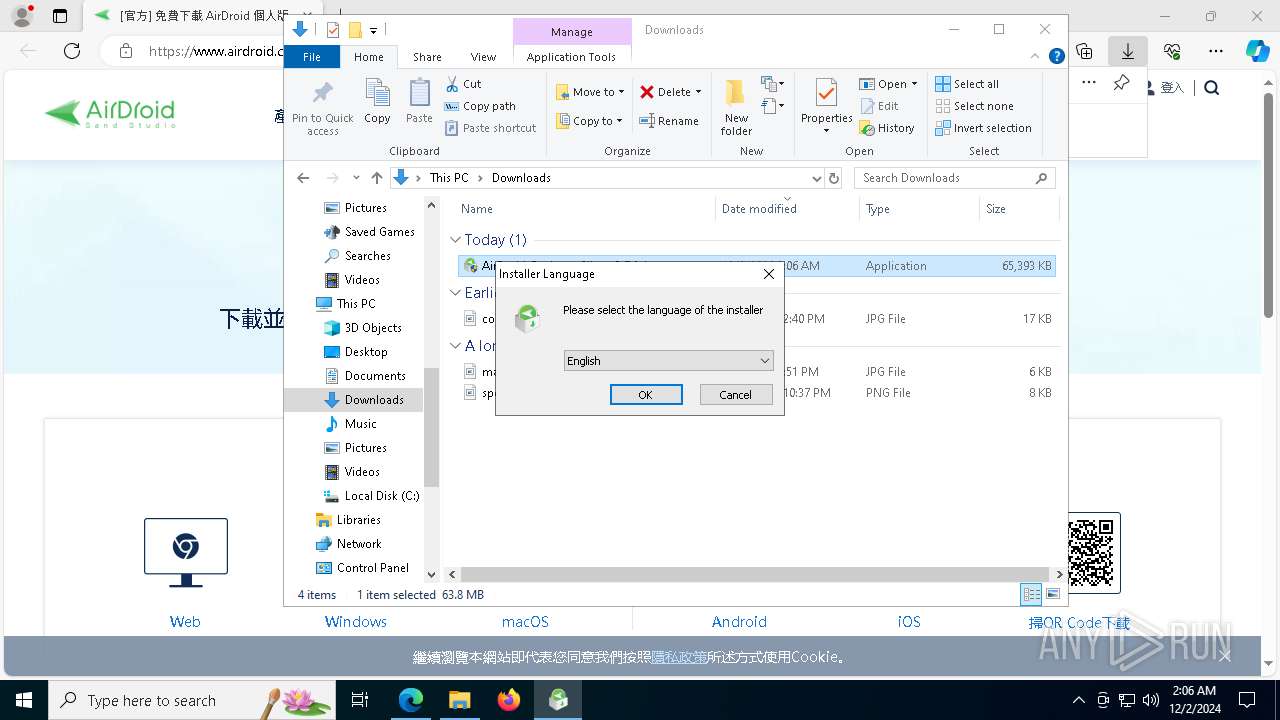
Checks supported languages
- identity_helper.exe (PID: 7392)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- AirCmd.exe (PID: 3928)
- AirCmd.exe (PID: 2680)
- AirCmd.exe (PID: 1556)
- AirCmd.exe (PID: 1412)
- AirCmd.exe (PID: 7036)
- AirCmd.exe (PID: 7172)
- Launcher.exe (PID: 1684)
- Helper.exe (PID: 8172)
- Helper.exe (PID: 5780)
- Launcher_UAC.exe (PID: 1572)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 2152)
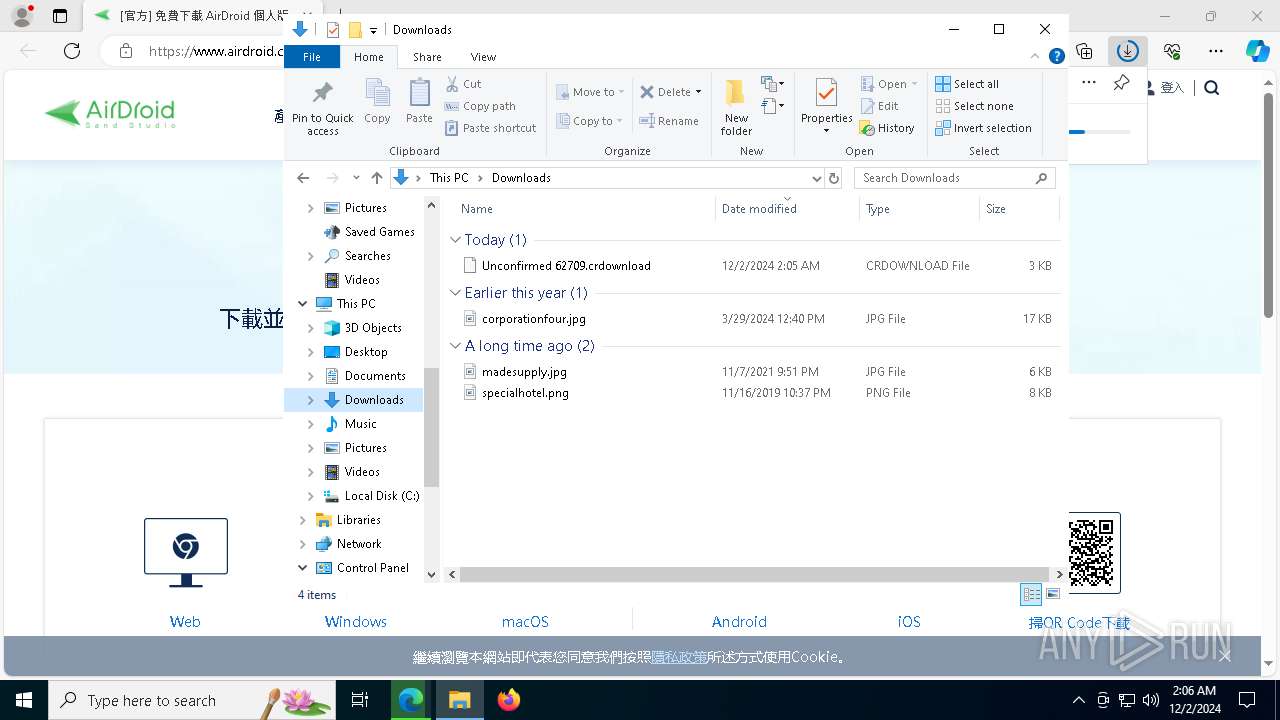
The process uses the downloaded file
- msedge.exe (PID: 5036)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- AirCmd.exe (PID: 2680)
- AirCmd.exe (PID: 1556)
- AirCmd.exe (PID: 1412)
- AirCmd.exe (PID: 7036)
- AirCmd.exe (PID: 7172)
- AirDroid.exe (PID: 6892)
Reads Environment values
- identity_helper.exe (PID: 7392)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads the computer name
- identity_helper.exe (PID: 7392)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- AirCmd.exe (PID: 3928)
- AirCmd.exe (PID: 2680)
- AirCmd.exe (PID: 1556)
- AirCmd.exe (PID: 1412)
- AirCmd.exe (PID: 7036)
- AirCmd.exe (PID: 7172)
- Launcher.exe (PID: 1684)
- Helper.exe (PID: 8172)
- Helper.exe (PID: 5780)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 2152)
- Launcher_UAC.exe (PID: 1572)
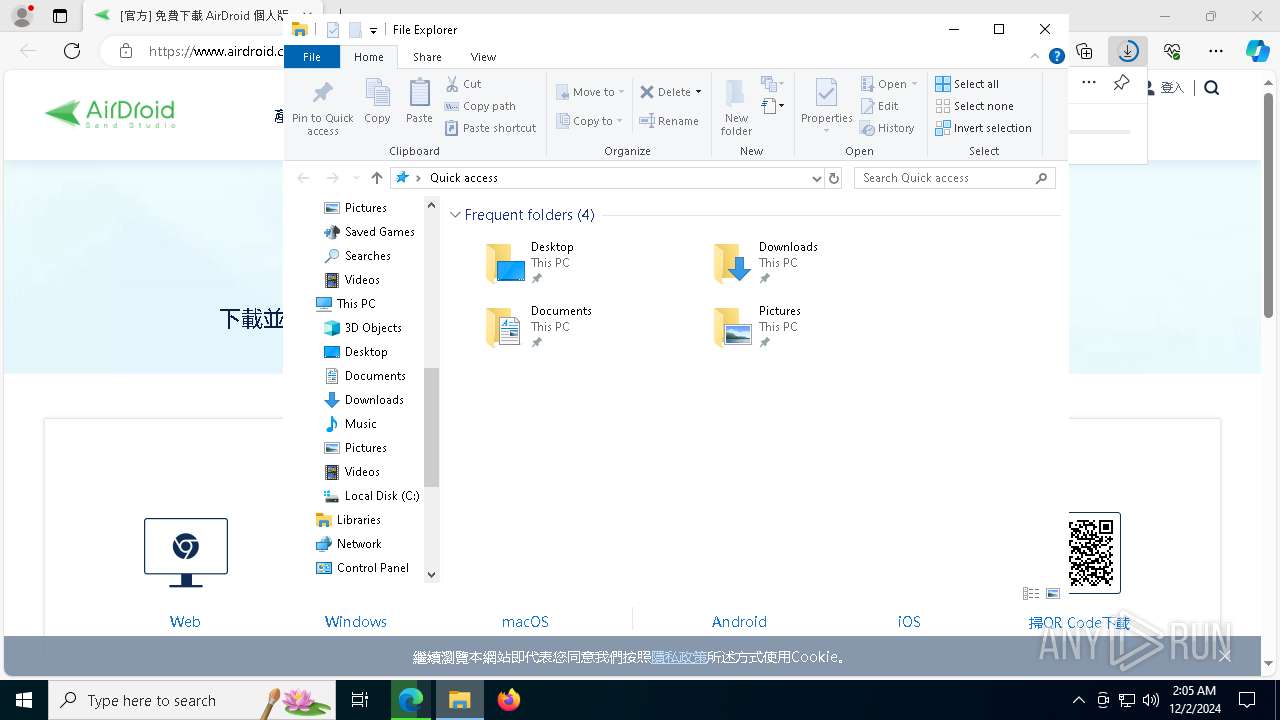
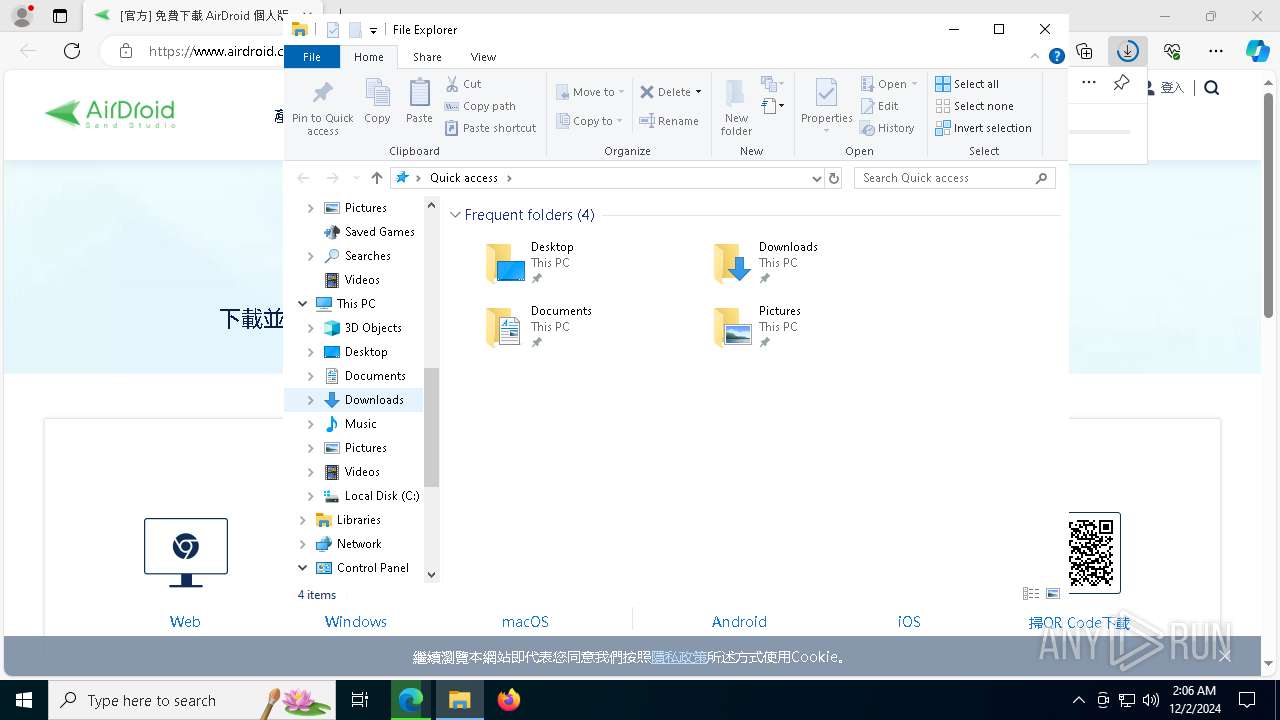
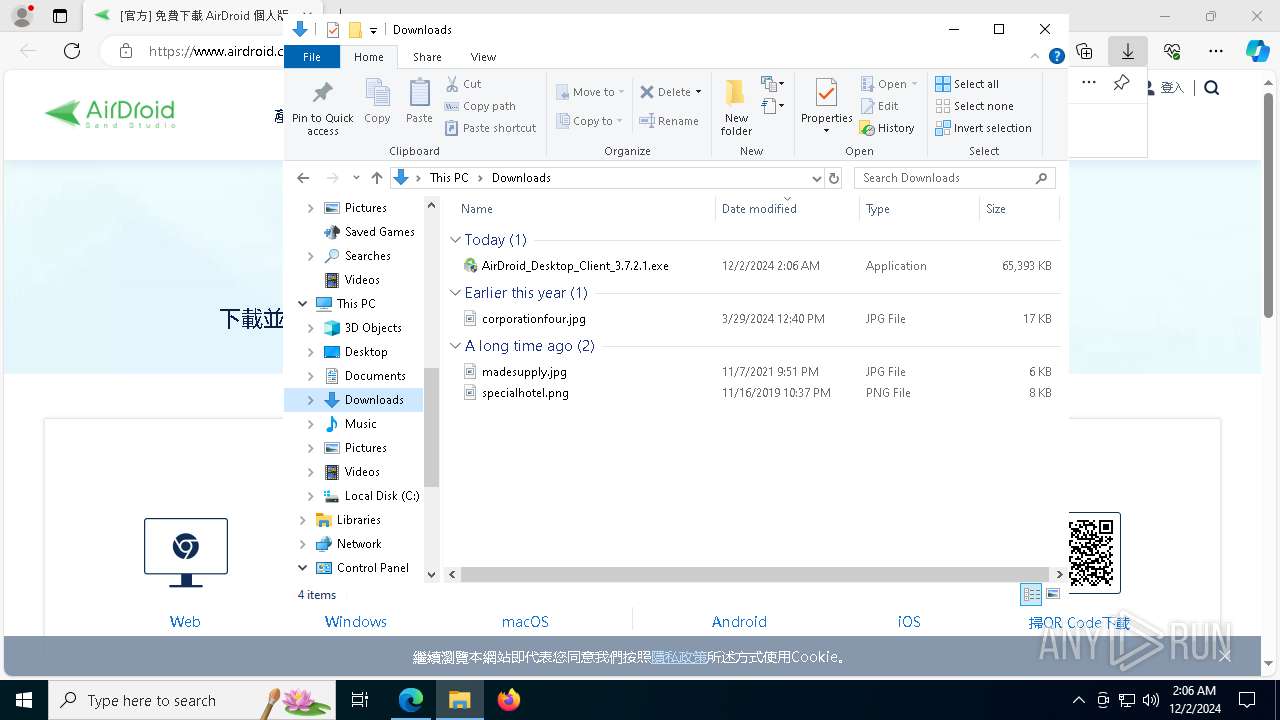
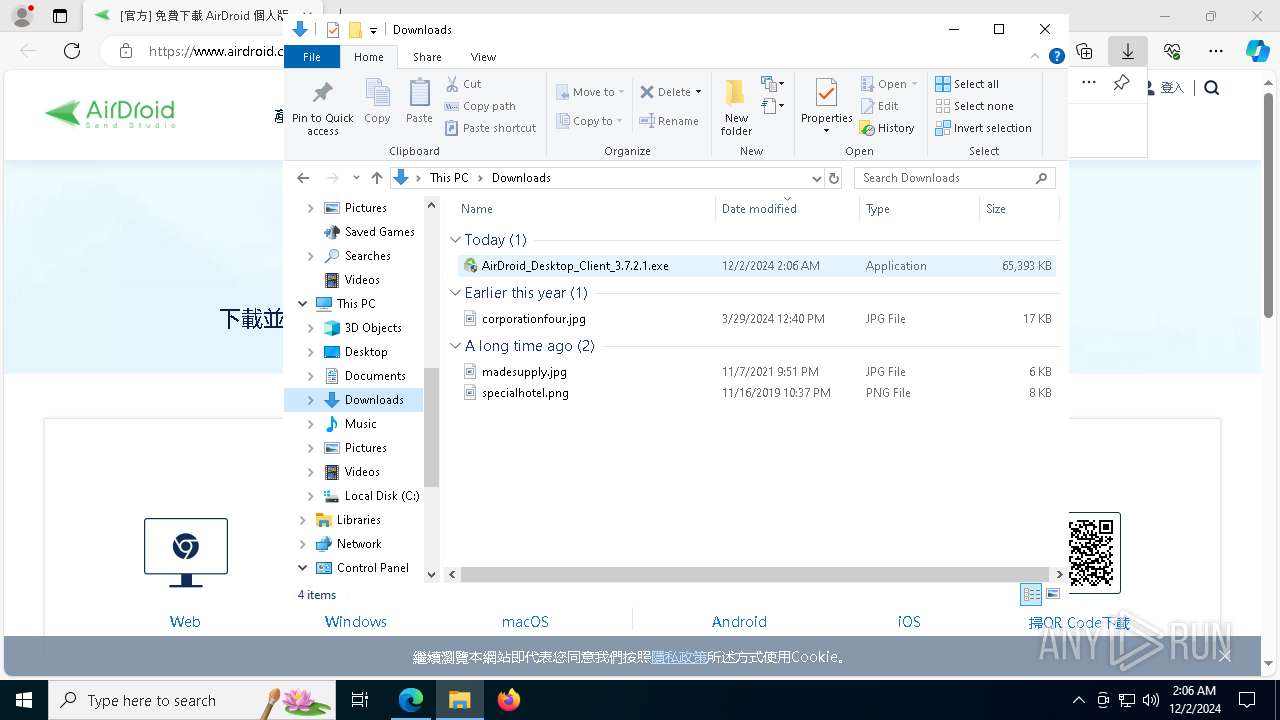
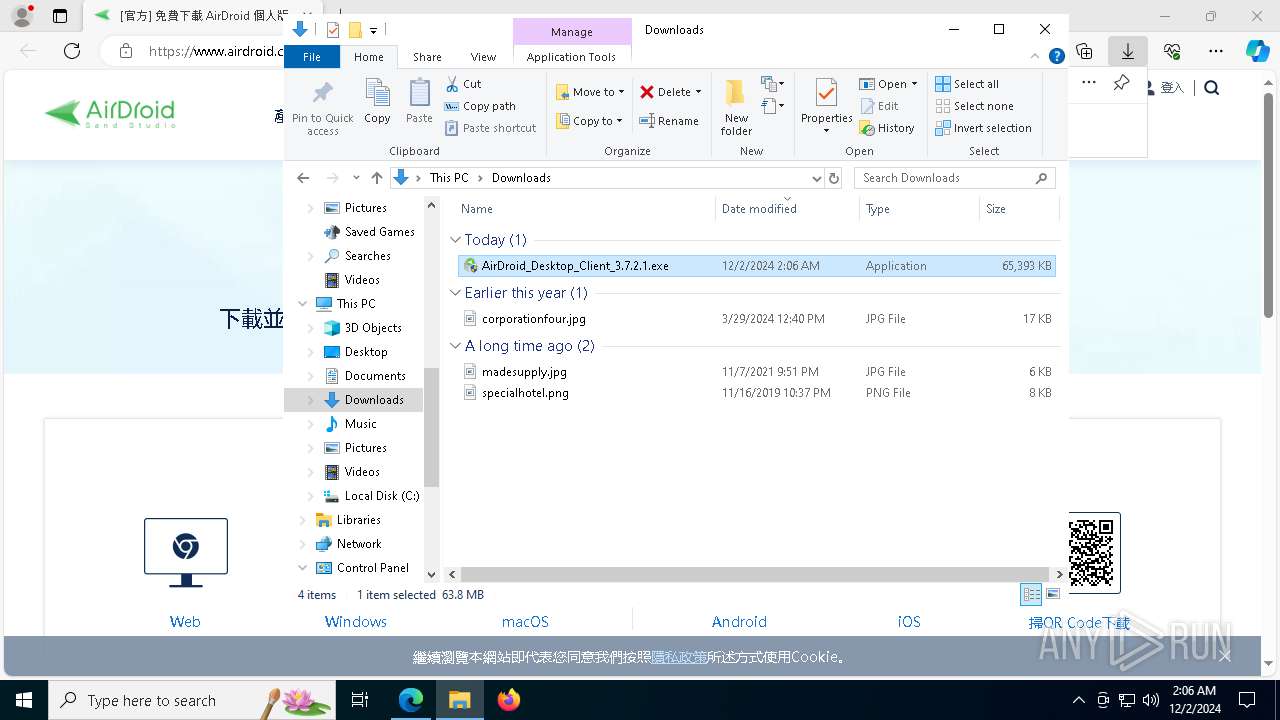
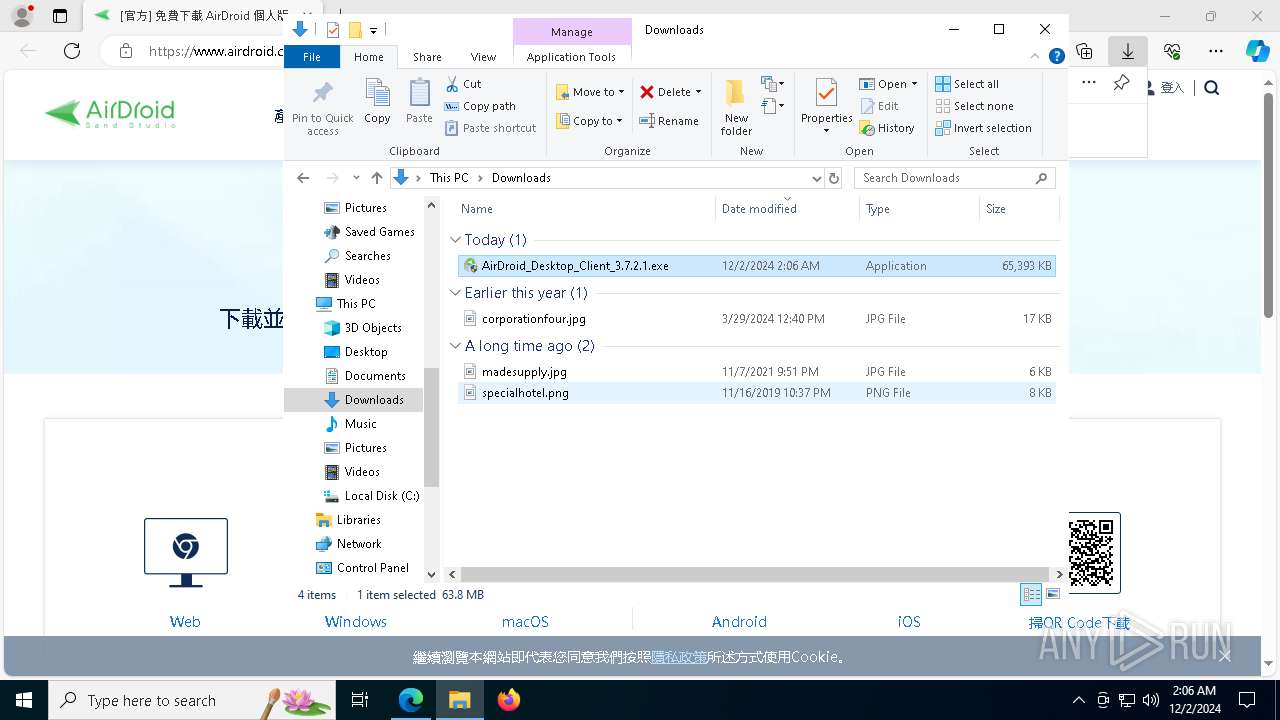
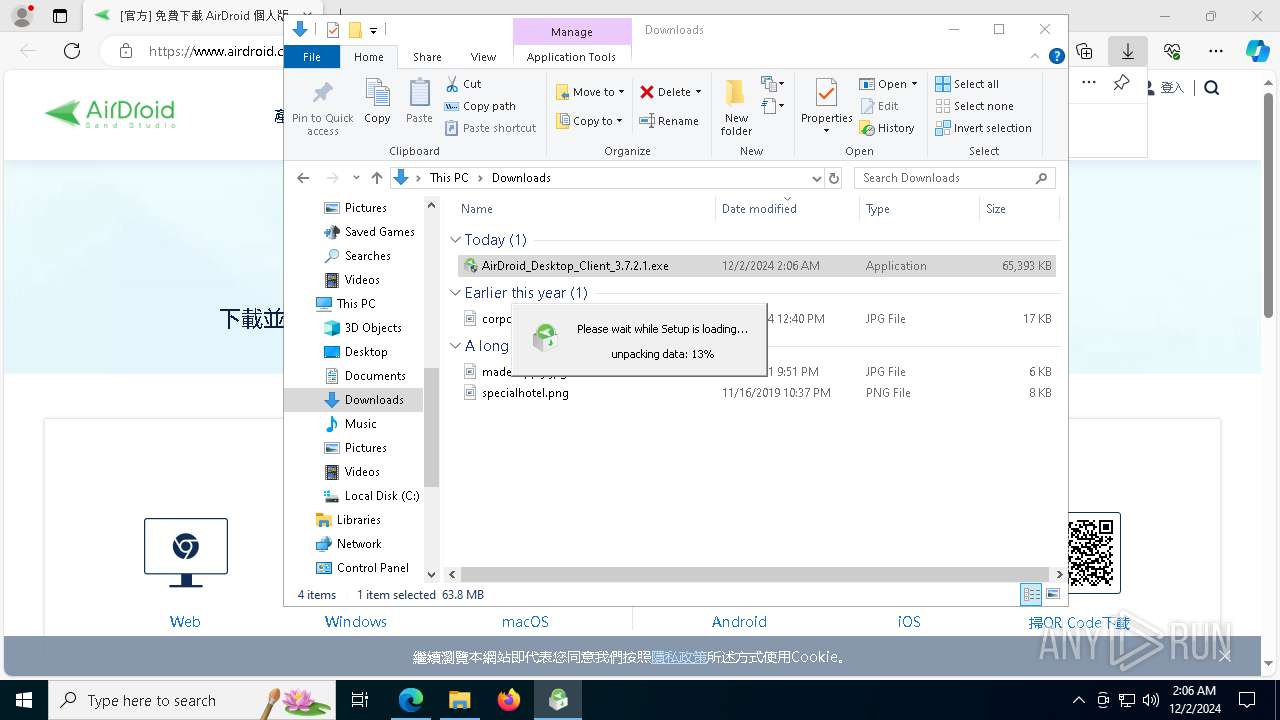
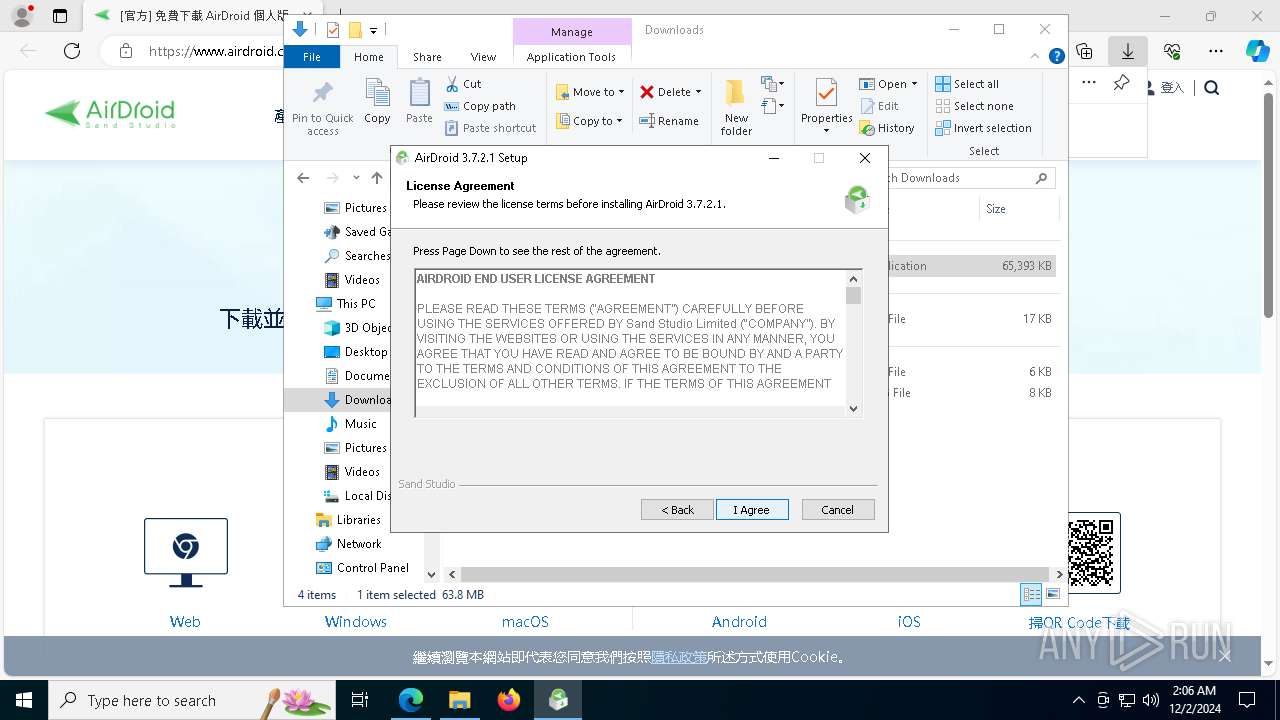
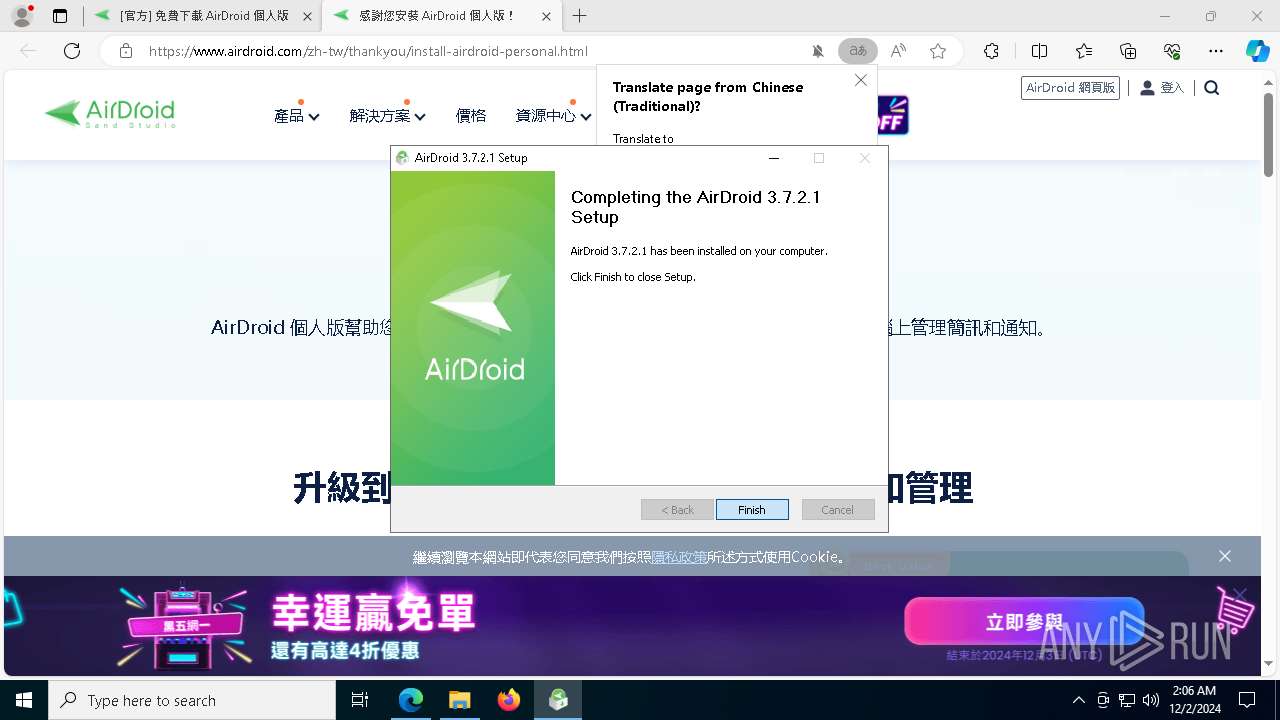
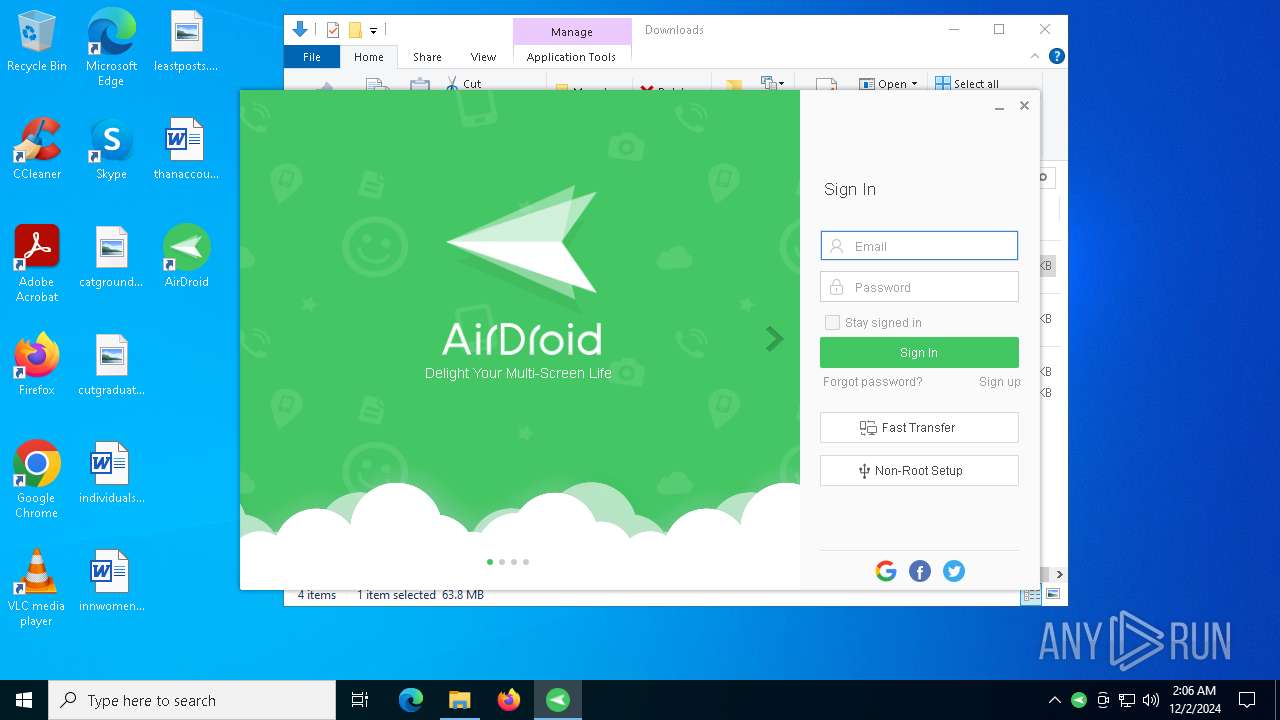
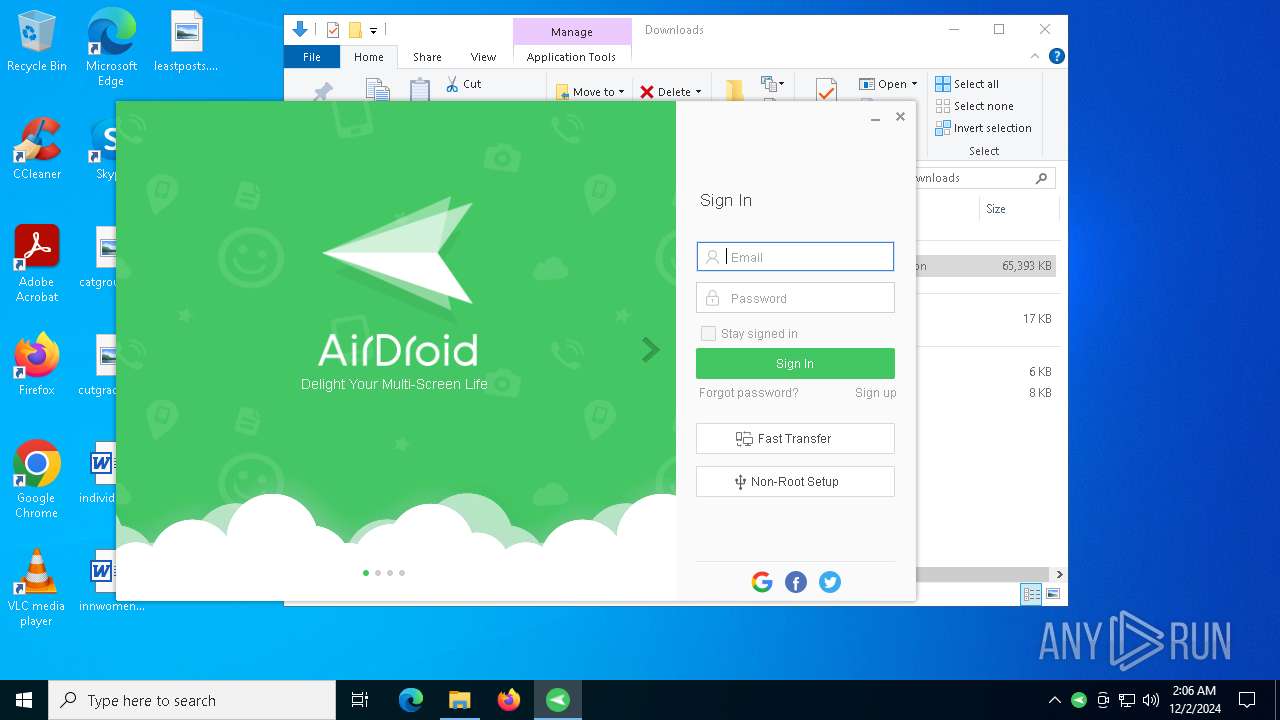
Manual execution by a user
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 8040)
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Process checks whether UAC notifications are on
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads the machine GUID from the registry
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- AirCmd.exe (PID: 3928)
- AirCmd.exe (PID: 2680)
- AirCmd.exe (PID: 1556)
- AirCmd.exe (PID: 1412)
- AirCmd.exe (PID: 7036)
- AirCmd.exe (PID: 7172)
- Helper.exe (PID: 8172)
- Helper.exe (PID: 5780)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 2152)
Create files in a temporary directory
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads CPU info
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Reads Windows Product ID
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Checks proxy server information
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- Helper.exe (PID: 5780)
- Helper.exe (PID: 8172)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 2152)
Creates files in the program directory
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
Disables trace logs
- Helper.exe (PID: 5780)
- Helper.exe (PID: 8172)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 2152)
Creates files or folders in the user directory
- AirDroid_Desktop_Client_3.7.2.1.exe (PID: 440)
- Helper.exe (PID: 5780)
- AirDroid.exe (PID: 6892)
- Helper.exe (PID: 8172)
Process checks computer location settings
- Helper.exe (PID: 5780)
- Helper.exe (PID: 8172)
- Helper.exe (PID: 2152)
- AirDroid.exe (PID: 6892)
Reads the software policy settings
- AirDroid.exe (PID: 6892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
69
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Users\admin\Downloads\AirDroid_Desktop_Client_3.7.2.1.exe" | C:\Users\admin\Downloads\AirDroid_Desktop_Client_3.7.2.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2568 --field-trial-handle=2348,i,468307172153203695,10331943981904562903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5196 --field-trial-handle=2348,i,468307172153203695,10331943981904562903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4152 --field-trial-handle=2348,i,468307172153203695,10331943981904562903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1412 | "C:\Program Files (x86)\AirDroid\AirCmd.exe" /u "C:\Program Files (x86)\AirDroid\Plugins\AirContextMenu_3_4_1.dll" | C:\Program Files (x86)\AirDroid\AirCmd.exe | — | AirDroid_Desktop_Client_3.7.2.1.exe | |||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirCmd Exit code: 0 Version: 3.7.2.1 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\AirDroid\AirCmd.exe" /u "C:\Program Files (x86)\AirDroid\Plugins\AirContextMenu_3_3_5.dll" | C:\Program Files (x86)\AirDroid\AirCmd.exe | — | AirDroid_Desktop_Client_3.7.2.1.exe | |||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirCmd Exit code: 0 Version: 3.7.2.1 Modules
| |||||||||||||||
| 1572 | "C:\Program Files (x86)\AirDroid\launcher_uac.exe" "/fromlauncher" | C:\Program Files (x86)\AirDroid\Launcher_UAC.exe | — | Launcher.exe | |||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirDroid 3 Launcher Exit code: 0 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 1684 | "C:\Program Files (x86)\AirDroid\Launcher.exe" /fromlauncher | C:\Program Files (x86)\AirDroid\Launcher.exe | — | AirDroid_Desktop_Client_3.7.2.1.exe | |||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirDroid 3 Launcher Exit code: 0 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 1796 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2432 --field-trial-handle=2348,i,468307172153203695,10331943981904562903,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 2152 | "C:\Program Files (x86)\AirDroid\Helper.exe" /killlauncher | C:\Program Files (x86)\AirDroid\Helper.exe | AirDroid.exe | ||||||||||||
User: admin Company: Sand Studio Integrity Level: MEDIUM Description: AirDroid 3 Helper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
12 698
Read events
12 610
Write events
86
Delete events
2
Modification events
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D785D244D6862F00 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E324DE44D6862F00 | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9776F17B-C607-41E3-B49F-EB6F778C6CD6} | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CC57FEB0-7DA7-4ABE-B0AB-CB4DE51726B4} | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {35571D69-2D37-4321-A5DE-446F2F8E022E} | |||
| (PID) Process: | (3608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DCB22FA4-D32D-4BF4-878E-C9BA71DFC30E} | |||
Executable files
106
Suspicious files
251
Text files
665
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
204
DNS requests
172
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1412 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7544 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1733659204&P2=404&P3=2&P4=MfW5BXg%2bwfZQ2AF7s0HrkcK4YveXpVdpMhaVpj8lvcYRpIZBXVorBYijmLRHoT%2fhoOvDlW1%2fv1IdXWZFbCAoow%3d%3d | unknown | — | — | whitelisted |
1412 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6372 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
440 | AirDroid_Desktop_Client_3.7.2.1.exe | GET | 200 | 49.51.35.72:80 | http://stat3.airdroid.com/pc/installstat?mac=525400204043&os_ver=10%2E0&os_lang=1033&ui_lang=1033&air_ver=3.7.2.1&os=windows&step=1 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6492 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.airdroid.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |