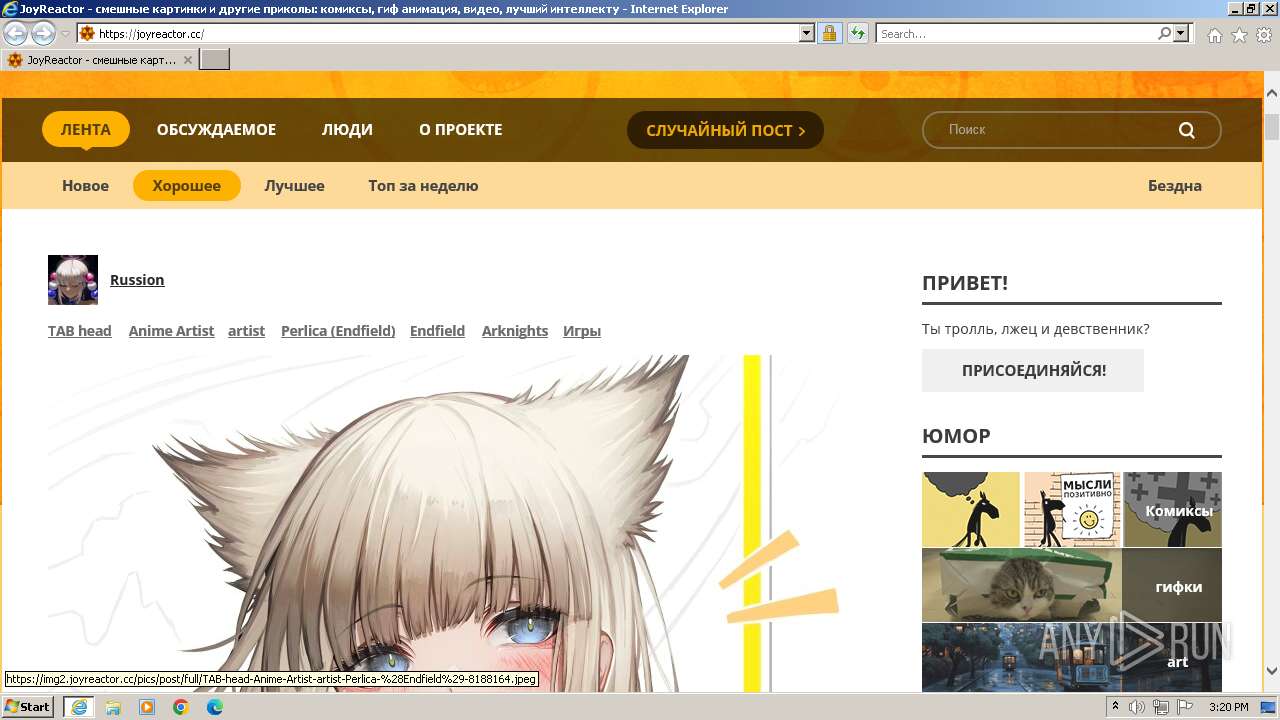
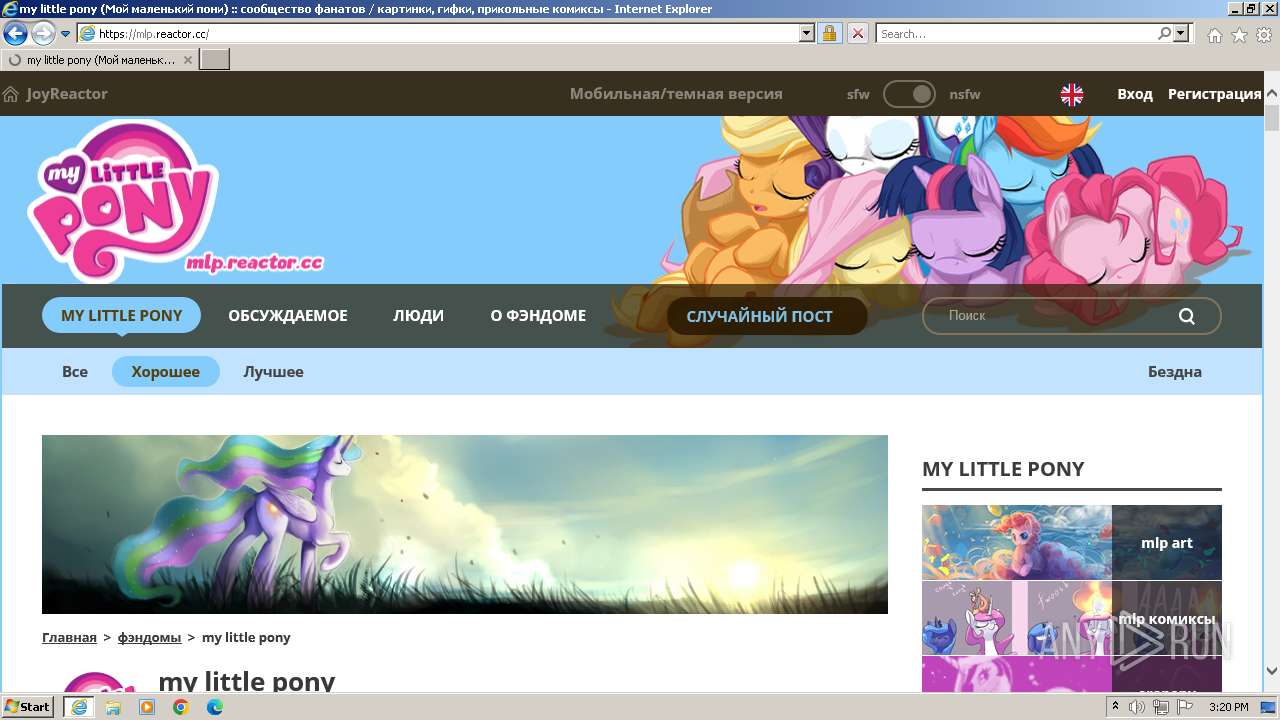
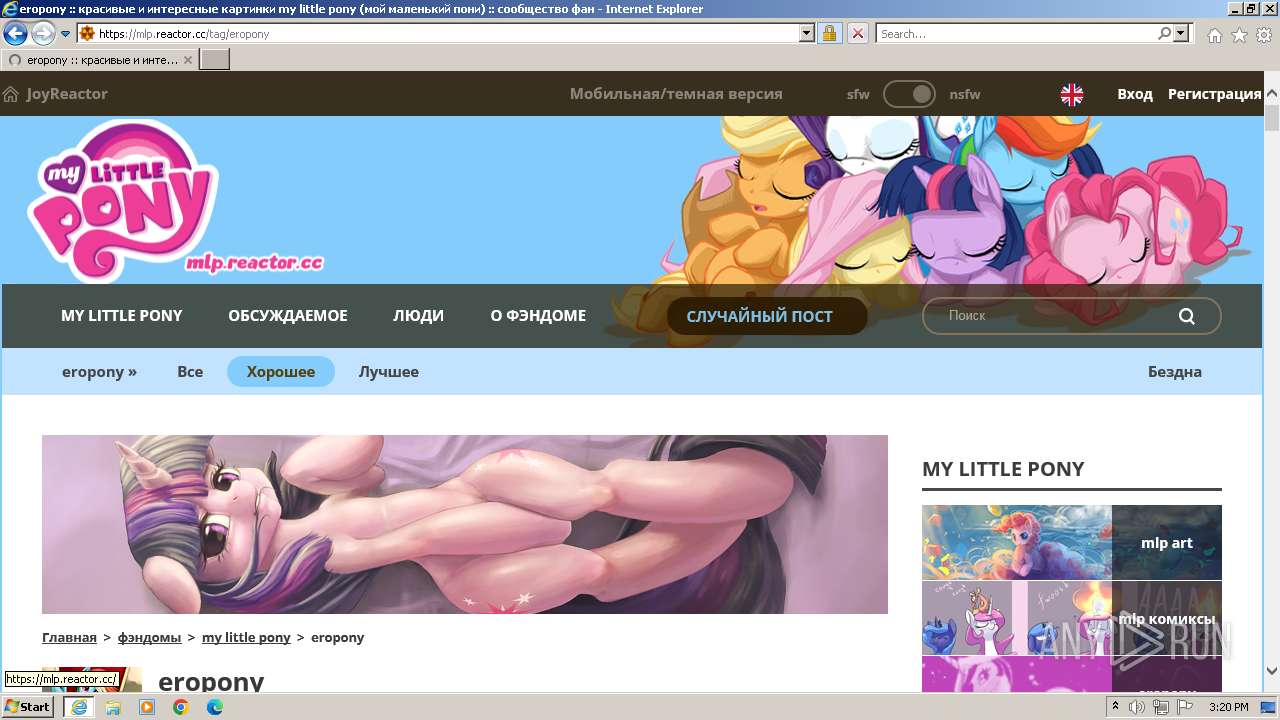
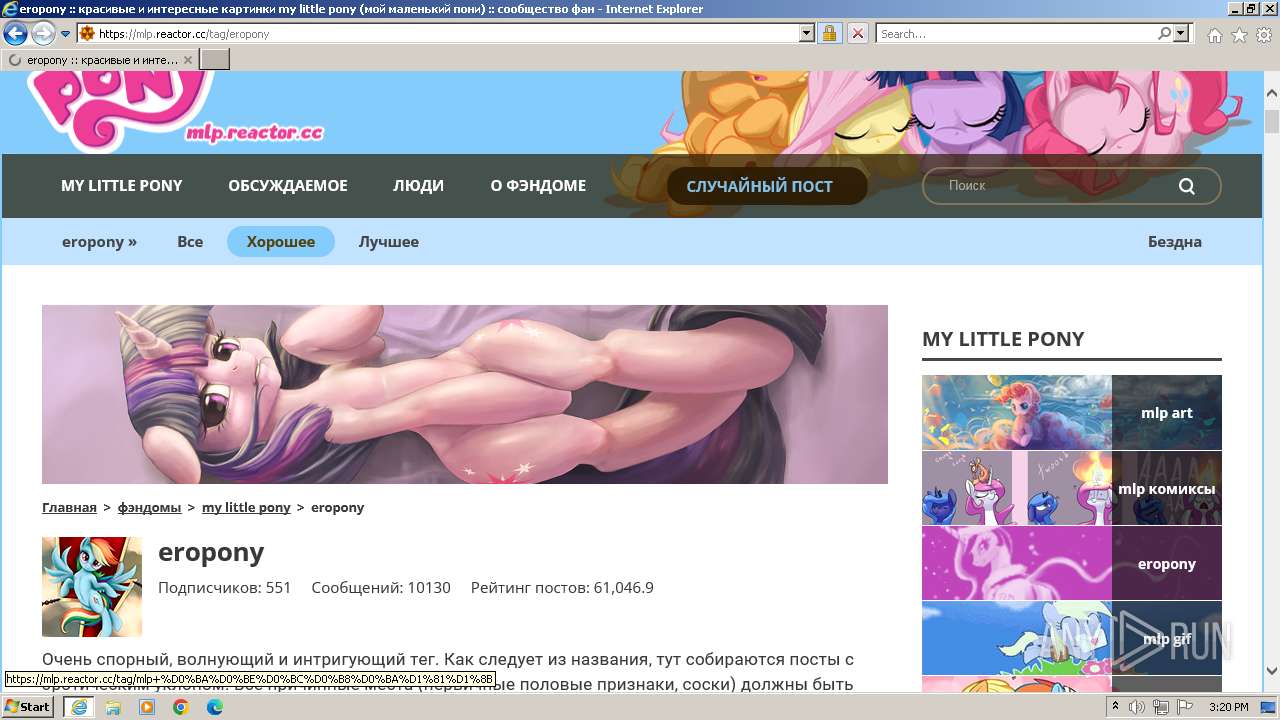
| URL: | joyreactor.cc |
| Full analysis: | https://app.any.run/tasks/881078b6-5833-49a5-b4d2-884bc43ade8a |
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2023, 15:19:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | AAE09A647DD434AA9D22546A0CE494797C027880 |
| SHA256: | 3FC7412221EDE5175B40ED95B50B5AA1A6730E0729E69D2386B10821E387CAC8 |
| SSDEEP: | 3:h:h |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 3728)
Manual execution by a user
- wmpnscfg.exe (PID: 3728)
Application launched itself
- iexplore.exe (PID: 3448)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3728)
Reads the computer name
- wmpnscfg.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Internet Explorer\iexplore.exe" "joyreactor.cc" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 677
Read events
17 610
Write events
62
Delete events
5
Modification events
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
460
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\P9ELVBE9.htm | html | |
MD5:4F8E702CC244EC5D4DE32740C0ECBD97 | SHA256:9E17CB15DD75BBBD5DBB984EDA674863C3B10AB72613CF8A39A00C3E11A8492A | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7295.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4ABBC4D4EBE27330C00C5A4E6FCA6945 | SHA256:AF74506767C9D4F8BC984E881FCF04336934DF7230F01674B159B5436F38C698 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:9CBA0E8DA7A30FBF11DC997440560CDF | SHA256:E06AE4B513DF4B55AA1BD6EAA0CA1390D78DAD6504DAD199662CF9110FAA2EBC | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:18222214C332D35F6BD1262D9D93C04A | SHA256:DE1D40851CDA42DD94D96215CC4F324A13954C96531EF96138B5F48D2AD75D21 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\313138[1].jpg | image | |
MD5:8D61D1D918B872F2F79CC2822A907AE5 | SHA256:A9AFD9E56287EBA288F55AEA6658DCDF9B5F802F10EBB8B6507030BE5E186571 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\localized.ru[1].js | text | |
MD5:D4E91127A219856B678EC8284116E95C | SHA256:CB7175EEEBF0F0DA7B4DC477E54D90B5DBEC8E4B81E2F4AA72E956EC36559DE1 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\icon_en[1].png | image | |
MD5:1D418BF40697203F7ED77A83824D97D9 | SHA256:BC1C4F0BE4E0FF136B7438A8AF600E27C325C9A4077C8A20E780084571DBB694 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
102
DNS requests
29
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | iexplore.exe | GET | 200 | 95.101.54.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d6bb2ad0af14907d | unknown | compressed | 61.6 Kb | unknown |
3196 | iexplore.exe | GET | 200 | 95.101.54.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?24ee352ddd3d4dea | unknown | compressed | 4.66 Kb | unknown |
3196 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3196 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3196 | iexplore.exe | GET | 200 | 23.60.200.134:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3196 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHUeP1PjGFkz6V8I7O6tApc%3D | unknown | binary | 1.41 Kb | unknown |
3196 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCSbiqNK5280hBN2lVZWzUN | unknown | binary | 472 b | unknown |
3196 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr5/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQiD0S5cIHyfrLTJ1fvAkJWflH%2B2QQUPeYpSJvqB8ohREom3m7e0oPQn1kCDQHuXyKVQkkF%2BQGRqNw%3D | unknown | binary | 1.25 Kb | unknown |
3196 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDCjDk6BcP0YRJkTzSsQwBD | unknown | binary | 472 b | unknown |
3196 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gseccovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSTMjK03nNiYoQYvu4Izyfn9OJNdAQUWHuOdSr%2BYYCqkEABrtboB0ZuP0gCDENqNL2NzdqQCxTmkQ%3D%3D | unknown | binary | 938 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | iexplore.exe | 95.101.54.120:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3196 | iexplore.exe | 23.60.200.134:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3196 | iexplore.exe | 146.59.26.8:443 | js.joyreactor.cc | OVH SAS | FR | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3196 | iexplore.exe | 142.250.185.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3196 | iexplore.exe | 5.255.255.77:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
3196 | iexplore.exe | 88.198.226.179:443 | img2.joyreactor.cc | Hetzner Online GmbH | DE | unknown |
3196 | iexplore.exe | 87.98.145.65:443 | img10.joyreactor.cc | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
js.joyreactor.cc |
| unknown |
yandex.ru |
| whitelisted |
img2.joyreactor.cc |
| unknown |
img10.joyreactor.cc |
| unknown |
ocsp.pki.goog |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |