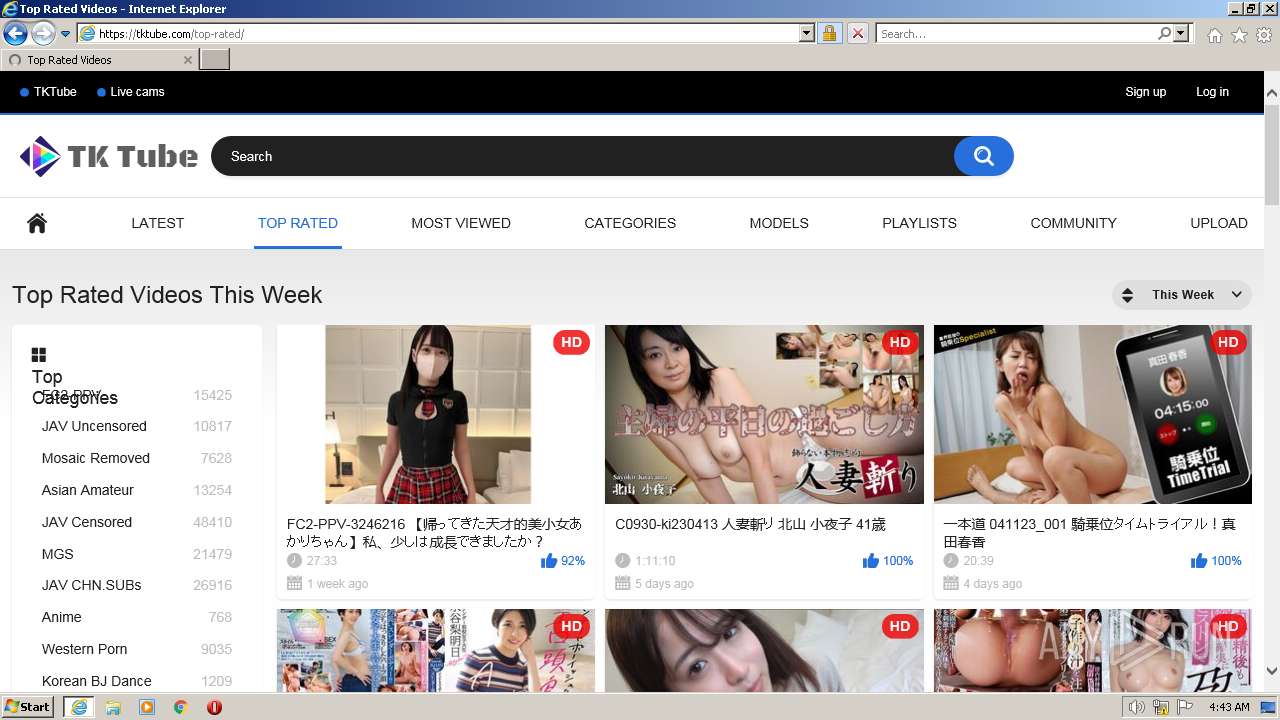
| URL: | https://tktube.com/ |
| Full analysis: | https://app.any.run/tasks/d670f332-380e-423c-9f3b-2e2c882b6438 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2023, 03:43:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9EEEC90050C81B23B3C733072D366865 |
| SHA1: | D0EA52CF3193C34D22F9BE52BA89AD805F08D7A2 |
| SHA256: | 3FC6C17121E8ABF8B828DC6EA12F904BBC2C61A78F0EA275EEF9F5453FF9EC53 |
| SSDEEP: | 3:N8GRnKKn:2GxR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3328)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1428)
Create files in a temporary directory
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://tktube.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3756 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3328 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
41 070
Read events
40 856
Write events
210
Delete events
4
Modification events
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
91
Text files
414
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ORWYPVPV.txt | text | |
MD5:EE6A7925748DEB834267AD3913D2C987 | SHA256:26A324E0E1F0A5A75A56645C3EDAA19EDDF28C1384818E4C35FDD1FECCF91688 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:65881C1F7753B346F02954D46C43BA46 | SHA256:0A6EE9F7B9AC4C7FE3360BA95B06297E2EEA71CE7F8C36A007EDC4256776F512 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\1[2].jpg | image | |
MD5:27D48FFD1A16F625E22BF9EAFF5C1A01 | SHA256:8DDBB484484F29886342A954A4C97E029DA621DCE6BE6B8B725BA3E6870FF93A | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\1[1].jpg | image | |
MD5:87BBC24CEA8AC44EDA2F51EE174E5E5C | SHA256:36AA233BAE0D75DC4479FEF744917C895F46EBA88BF8C1F072DD0B54E17EAC16 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\1[1].jpg | image | |
MD5:95D842E2FF29843D9BD285E24A280FC3 | SHA256:694F54969DB4F4591912380F978D4B802AD3F52CED4CE83131AA9BF51221C518 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:CFBC16E33DCBEF6F773F0F79AF528F45 | SHA256:F0937890FB1053069BAAC97B7992C6D22CB74CAE20317FC05D51070D96950FFA | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\K0XEH3T5.htm | html | |
MD5:133304BD0E98E3491D0CAE0A7A22B8FC | SHA256:76E1A3FA594FEB6186ABA851AA021BA55940C0384E2E75E3E7291C655015E537 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\1[2].jpg | image | |
MD5:5DB8012674C60D89974087BD2B1137F9 | SHA256:20C5F78DFC441470E40843865192F8468E5ED2FB5B5295F1FDB18336DF948566 | |||
| 3756 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:8FFB38D9BAC35D63440B7C4F0884DF0D | SHA256:F0451655C4D809804D2144E53824F7EC2F90CCA1160A29335DDE5D6B0E948F91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
100
DNS requests
36
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3756 | iexplore.exe | GET | — | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAKao9KC3BF8ChRY1uq8%2FwI%3D | US | — | — | whitelisted |
3756 | iexplore.exe | GET | — | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2e0a7ea4d65fd689 | US | — | — | whitelisted |
3756 | iexplore.exe | GET | — | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7707d6fadef9d018 | US | — | — | whitelisted |
3756 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEDGYcFStFHefh%2FzuVFEKHNw%3D | US | der | 471 b | whitelisted |
3756 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3756 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2ee53308fe481ef0 | US | compressed | 4.70 Kb | whitelisted |
3756 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDBv5Zowk3JoRI3XQvkFZx%2F | US | der | 472 b | whitelisted |
3756 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?91ec4e44decb1dbe | US | compressed | 61.1 Kb | whitelisted |
3756 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGRX2%2BD39iCpEttvowkOp0M%3D | US | der | 471 b | whitelisted |
3756 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | iexplore.exe | 172.64.96.12:443 | — | CLOUDFLARENET | US | unknown |
3756 | iexplore.exe | 216.58.212.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3756 | iexplore.exe | 142.250.185.168:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
3756 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
3756 | iexplore.exe | 156.146.33.26:443 | a.realsrv.com | Datacamp Limited | DE | suspicious |
3756 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
3756 | iexplore.exe | 185.94.237.101:443 | poweredby.jads.co | Mojohost B.v. | NL | suspicious |
3756 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3756 | iexplore.exe | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
3756 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
a.realsrv.com |
| whitelisted |
poweredby.jads.co |
| whitelisted |
www.google.com |
| malicious |
sstatic1.histats.com |
| malicious |
creative.live.tktube.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
3756 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |