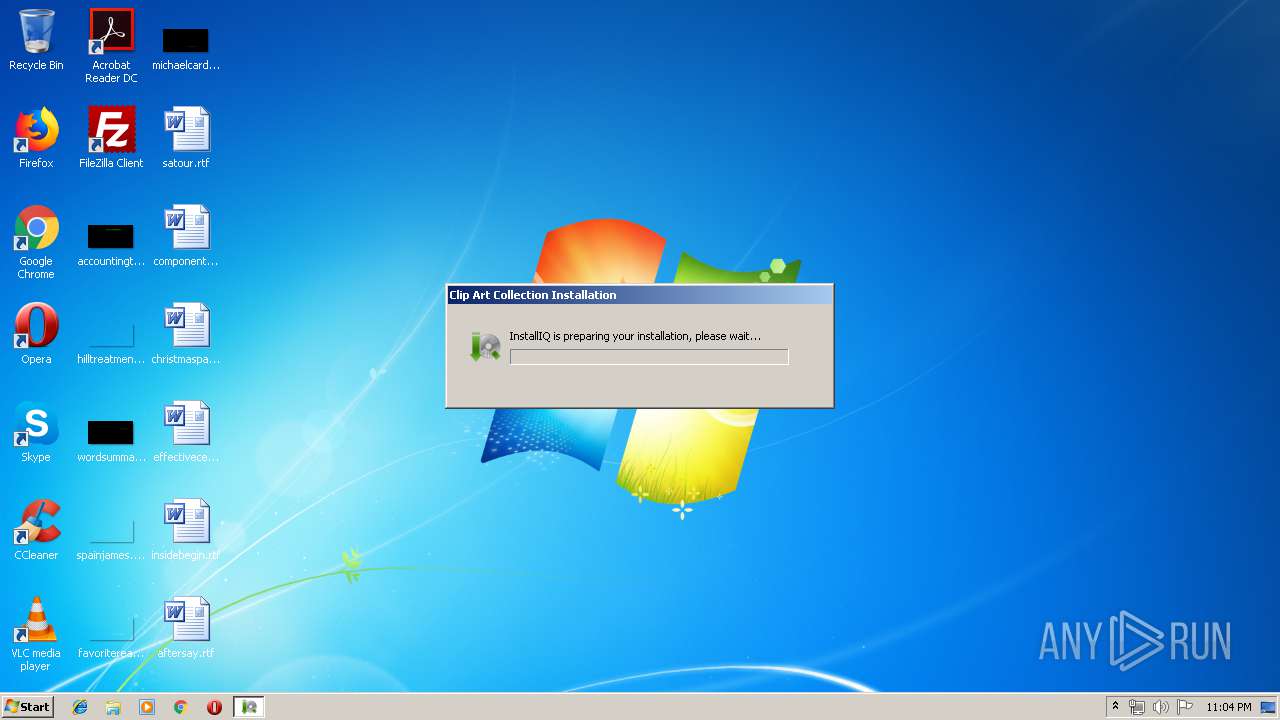
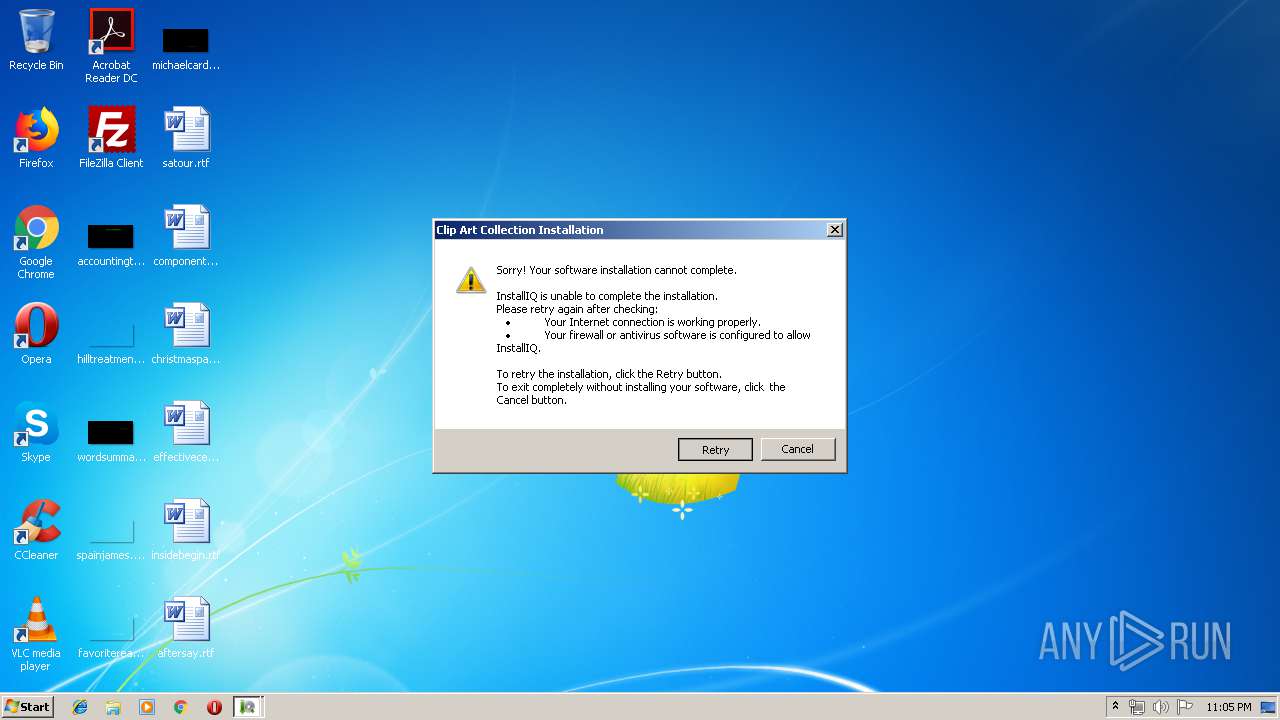
| File name: | clipart.exe |
| Full analysis: | https://app.any.run/tasks/6ca5fcac-91cf-4033-9d7c-5e368930a0e3 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2019, 22:04:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 889ED34850B726F7D6661ADCDBA92C86 |
| SHA1: | ECCE6A14589D1D248679696452C2286330174A74 |
| SHA256: | 3FC47E0EDA2928794D41B717DAEEB5892F109BAD1CDE58534849D8B8B55DC548 |
| SSDEEP: | 12288:3RLAj8bPtnIfqJ1lWgb3ixnxLANr1SlTzmfSS:3RLAy2fsL3ixndANr1Gu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- clipart.exe (PID: 3412)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (43.5) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (27.9) |
| .scr | | | Windows screen saver (13.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.6) |
| .exe | | | Win32 Executable (generic) (4.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:05:29 15:42:58+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 428032 |
| InitializedDataSize: | 196608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b633 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.107.0.0 |
| ProductVersionNumber: | 1.107.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | W3i, LLC |
| FileDescription: | InstallIQ Installation Utility |
| FileVersion: | 1.107.0.0 |
| InternalName: | InstallIQStub.exe |
| LegalCopyright: | Copyright ©2010 W3i Holdings, LLC. All rights reserved. |
| OriginalFileName: | InstallIQStub.exe |
| ProductName: | InstallIQ |
| ProductVersion: | 1.107.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-May-2012 13:42:58 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | W3i, LLC |
| FileDescription: | InstallIQ Installation Utility |
| FileVersion: | 1.107.0.0 |
| InternalName: | InstallIQStub.exe |
| LegalCopyright: | Copyright ©2010 W3i Holdings, LLC. All rights reserved. |
| OriginalFilename: | InstallIQStub.exe |
| ProductName: | InstallIQ |
| ProductVersion: | 1.107.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 18 |
| Time date stamp: | 29-May-2012 13:42:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00033B6A | 0x00033C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60483 |
.text-co\xcdf\x01 | 0x00035000 | 0x000166CD | 0x00016800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42591 |
.text-cotg | 0x0004C000 | 0x00006774 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.3884 |
.text-co\xa3k | 0x00053000 | 0x00006BA3 | 0x00006C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34898 |
.text-co\x0c\x04 | 0x0005A000 | 0x0000040C | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.86017 |
.text-co?A | 0x0005B000 | 0x0000413F | 0x00004200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.33637 |
.text-ti$\xa3 | 0x00060000 | 0x0000A324 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60307 |
.text-co\x12" | 0x0006B000 | 0x00002212 | 0x00002400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.23344 |
.rdata | 0x0006E000 | 0x000211F0 | 0x00021200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97763 |
.data | 0x00090000 | 0x00006A5C | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.157 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.41351 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.62084 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.7081 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.14122 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.34185 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.2788 | 2336 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 5.9991 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Users\admin\Downloads\clipart.exe" /pproc="explorer.exe" | C:\Users\admin\Downloads\clipart.exe | clipart.exe | ||||||||||||
User: admin Company: W3i, LLC Integrity Level: HIGH Description: InstallIQ Installation Utility Exit code: 0 Version: 1.107.0.0 Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\Downloads\clipart.exe" | C:\Users\admin\Downloads\clipart.exe | — | explorer.exe | |||||||||||
User: admin Company: W3i, LLC Integrity Level: MEDIUM Description: InstallIQ Installation Utility Exit code: 0 Version: 1.107.0.0 Modules
| |||||||||||||||
Total events
377
Read events
355
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3412) clipart.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3412) clipart.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2568) clipart.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\clipart_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | clipart.exe | C:\Users\admin\AppData\Local\Temp\pkg_1643070\stubconfig.ini | text | |
MD5:— | SHA256:— | |||
| 2568 | clipart.exe | C:\Users\admin\AppData\Local\Temp\pkg_1643070\pingstub.dat | html | |
MD5:— | SHA256:— | |||
| 3412 | clipart.exe | C:\Users\admin\AppData\Local\Temp\pkg_1642f17e0\stubconfig.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
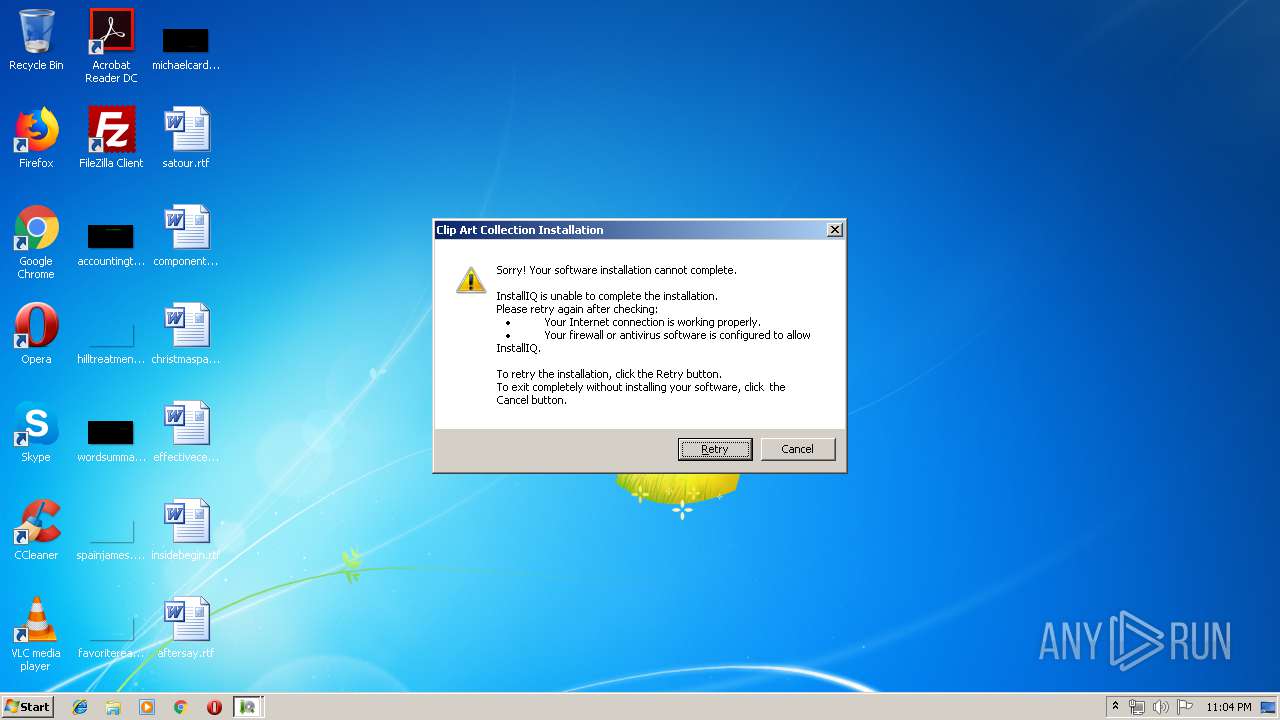
2568 | clipart.exe | GET | 200 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | html | 529 b | malicious |
2568 | clipart.exe | GET | 200 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | html | 529 b | malicious |
2568 | clipart.exe | GET | 200 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | html | 529 b | malicious |
2568 | clipart.exe | GET | 200 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | html | 529 b | malicious |
2568 | clipart.exe | GET | 200 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | html | 529 b | malicious |
2568 | clipart.exe | GET | 302 | 37.48.65.136:80 | http://dl.installiq.com/api/stub/ping.aspx?shortname=clipartcollection&a=13029&f=clipartsf | NL | text | 11 b | malicious |
2568 | clipart.exe | GET | 200 | 208.91.196.145:80 | http://ww1.installiq.com/ | VG | html | 1.88 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | clipart.exe | 37.48.65.136:80 | dl.installiq.com | LeaseWeb Netherlands B.V. | NL | malicious |
— | — | 37.48.65.136:80 | dl.installiq.com | LeaseWeb Netherlands B.V. | NL | malicious |
2568 | clipart.exe | 208.91.196.145:80 | ww1.installiq.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.installiq.com |
| malicious |
ww1.installiq.com |
| malicious |