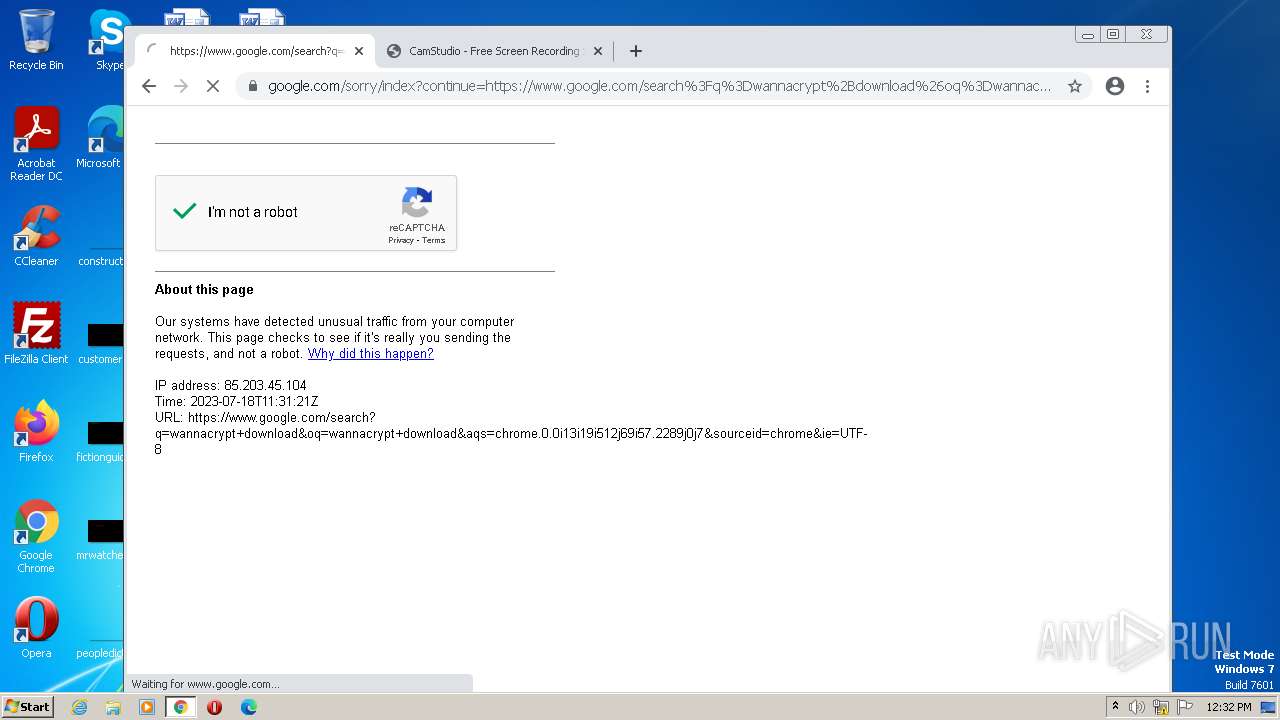
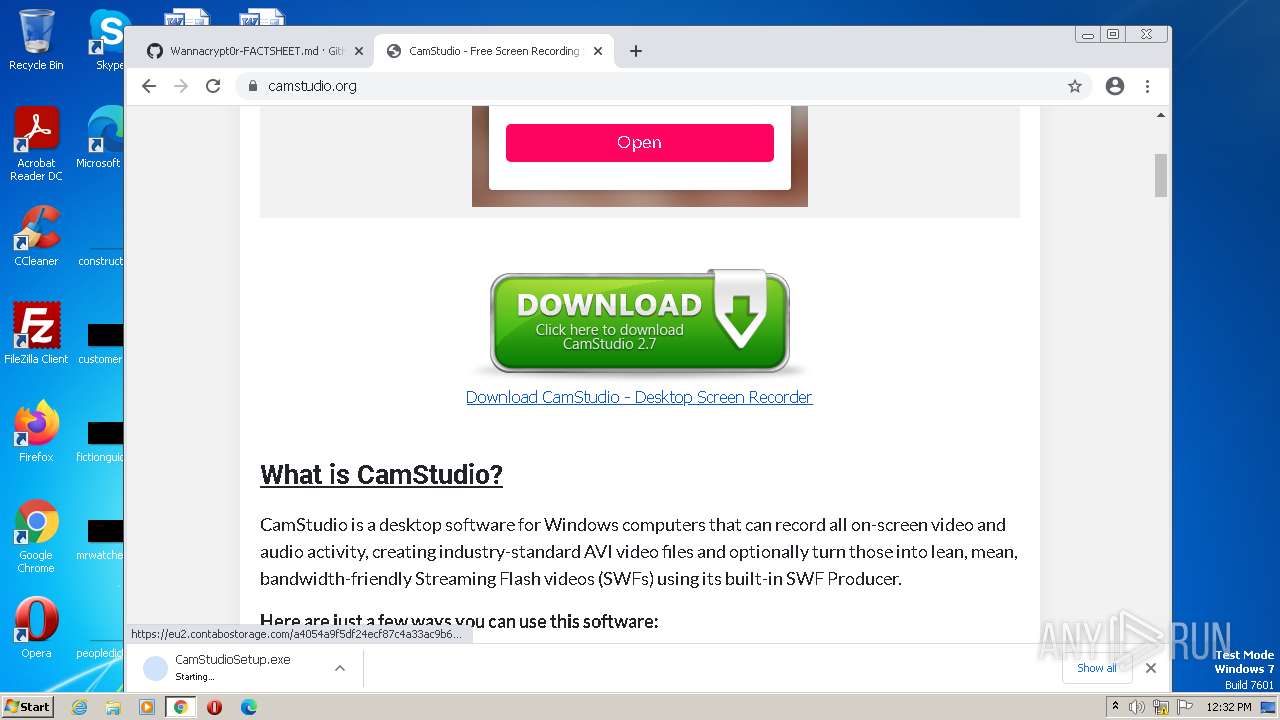
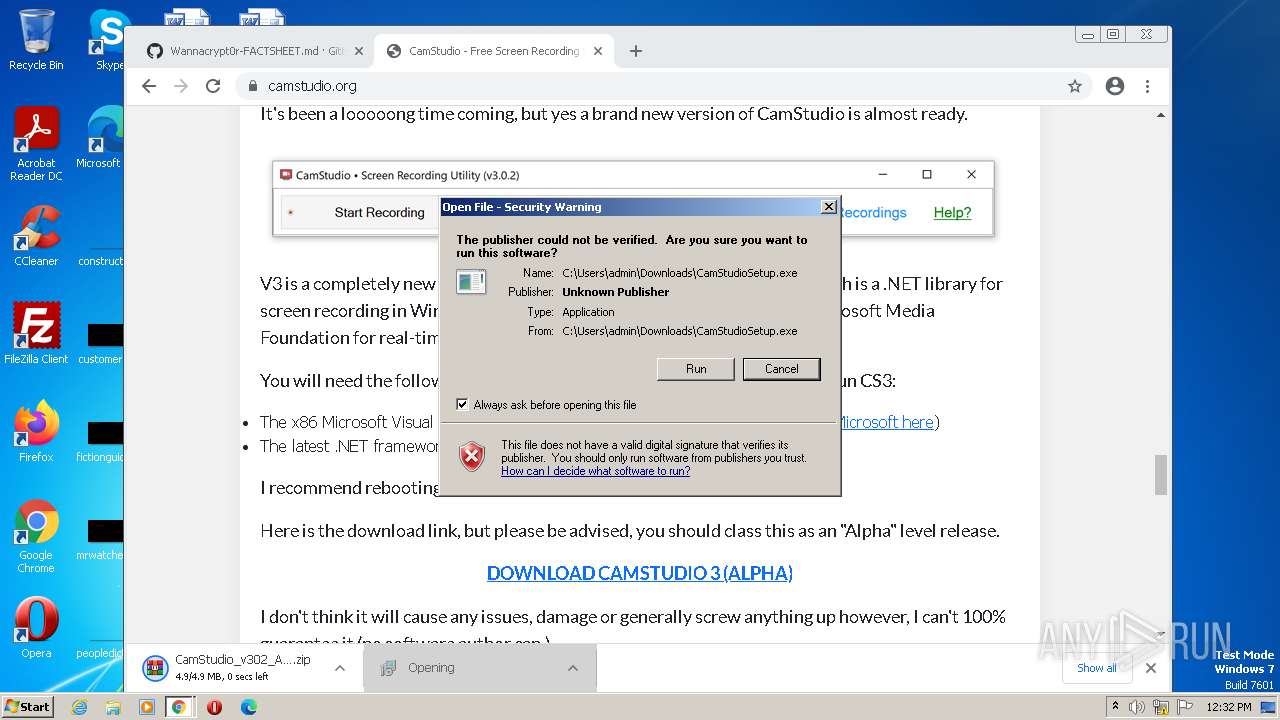
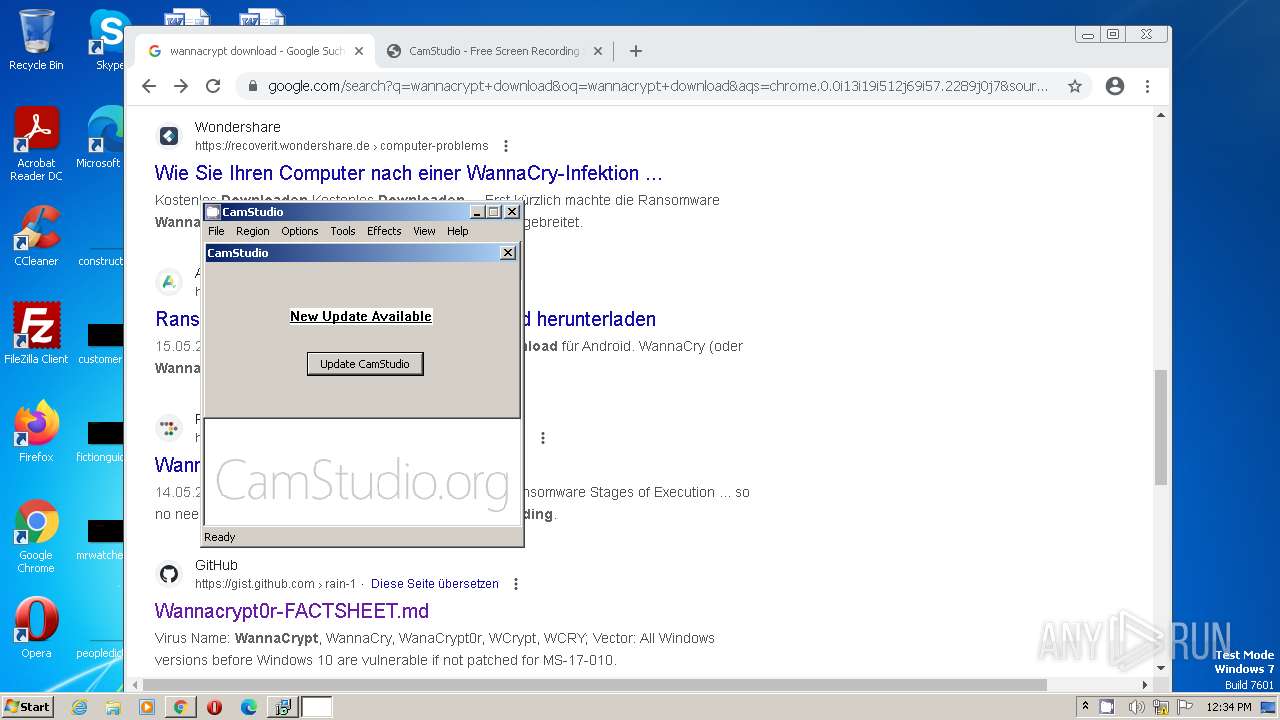
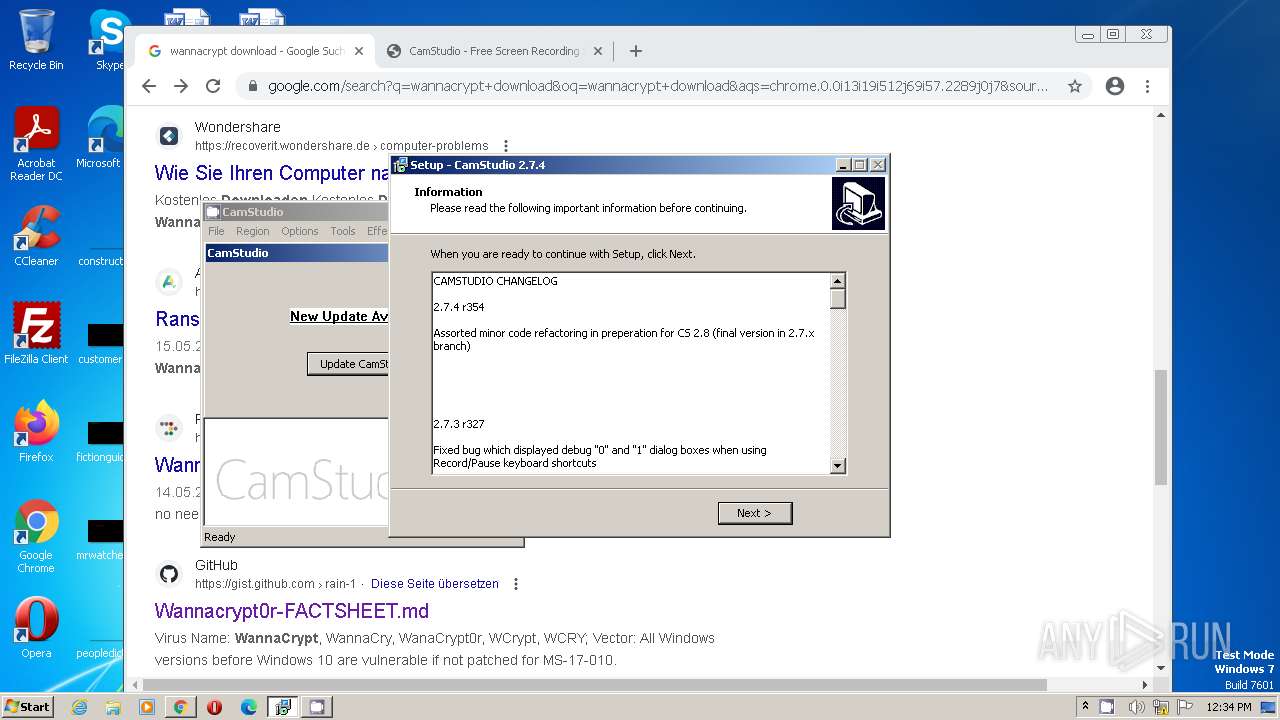
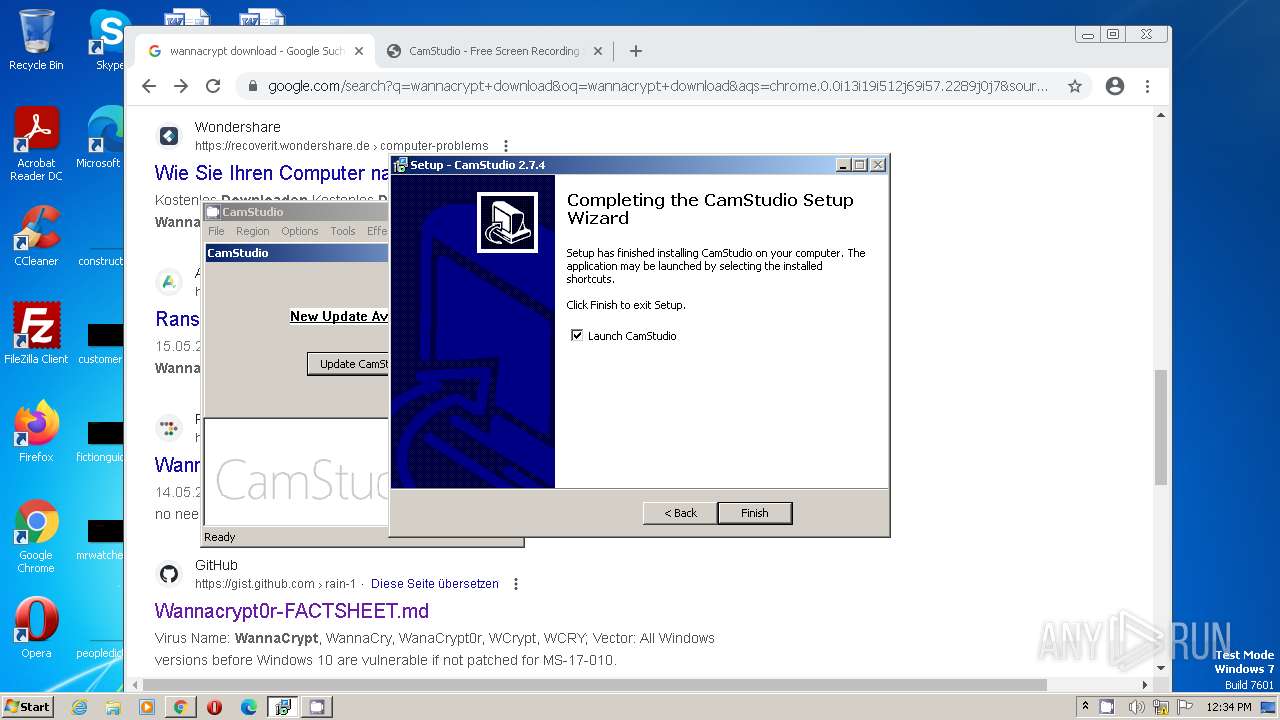
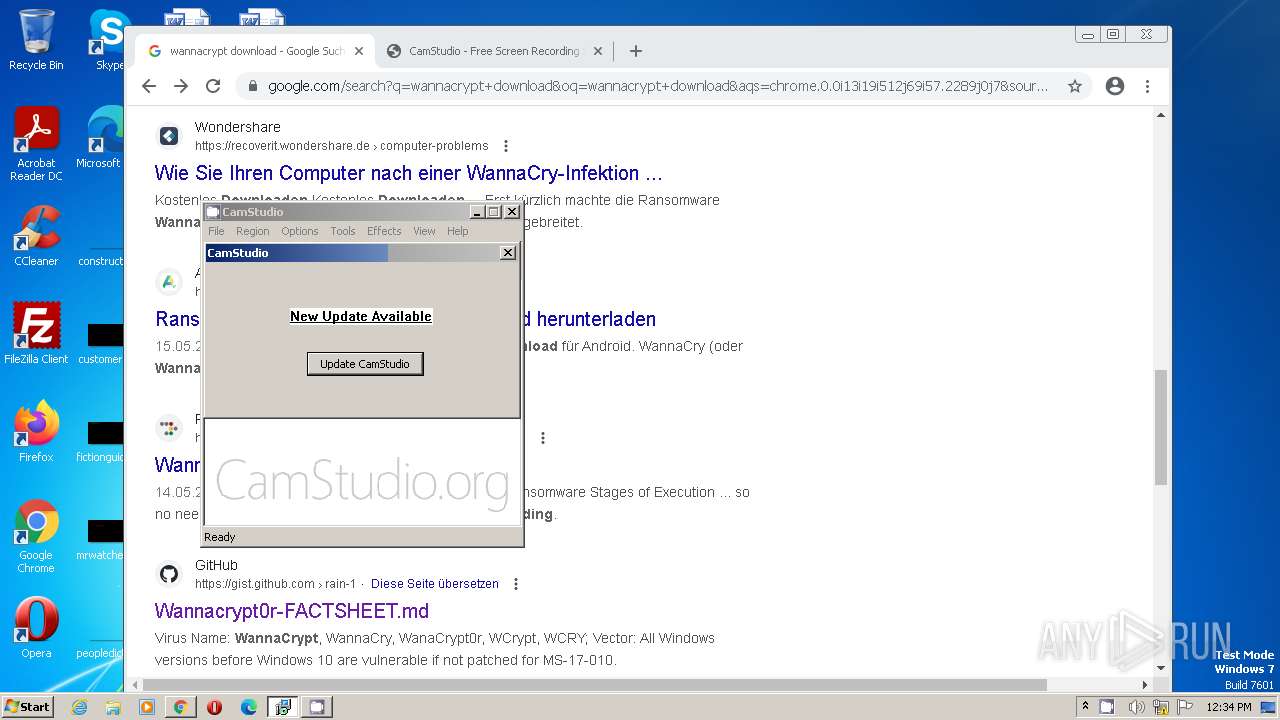
| File name: | dontopen-CamStudioSetup.exe |
| Full analysis: | https://app.any.run/tasks/edc02009-19aa-4588-a497-a1cae44a4788 |
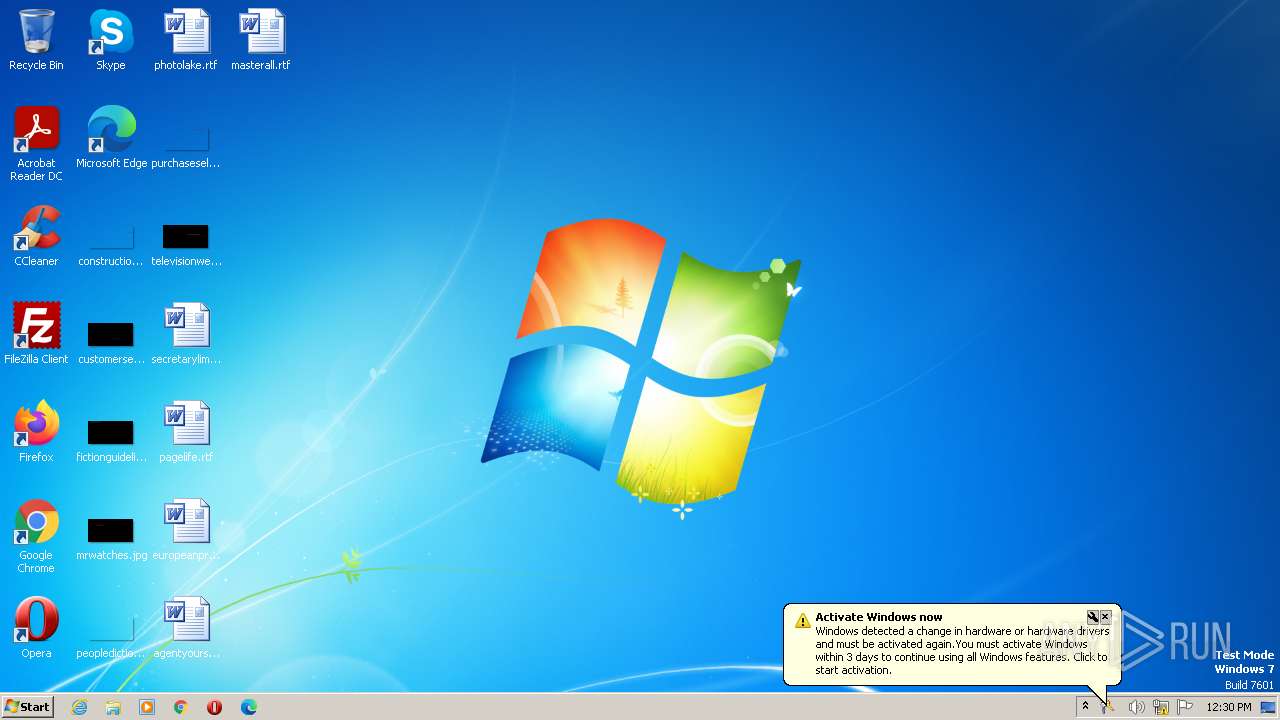
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2023, 11:29:49 |
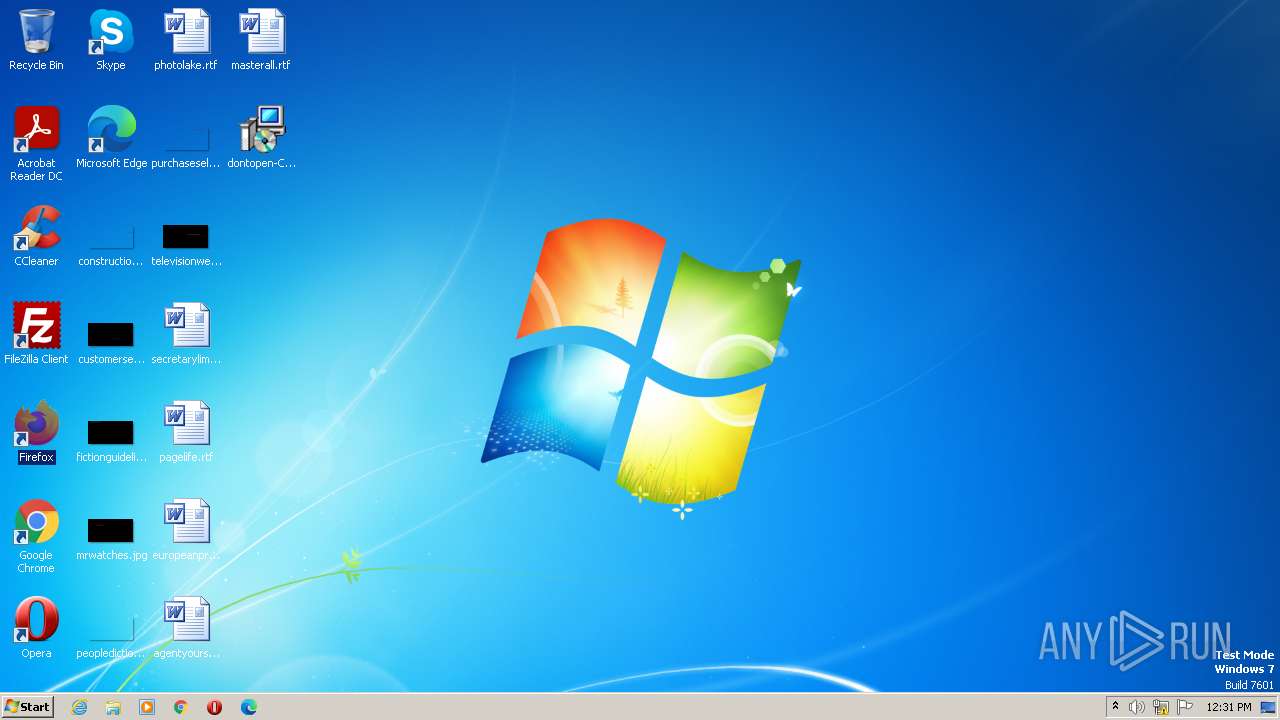
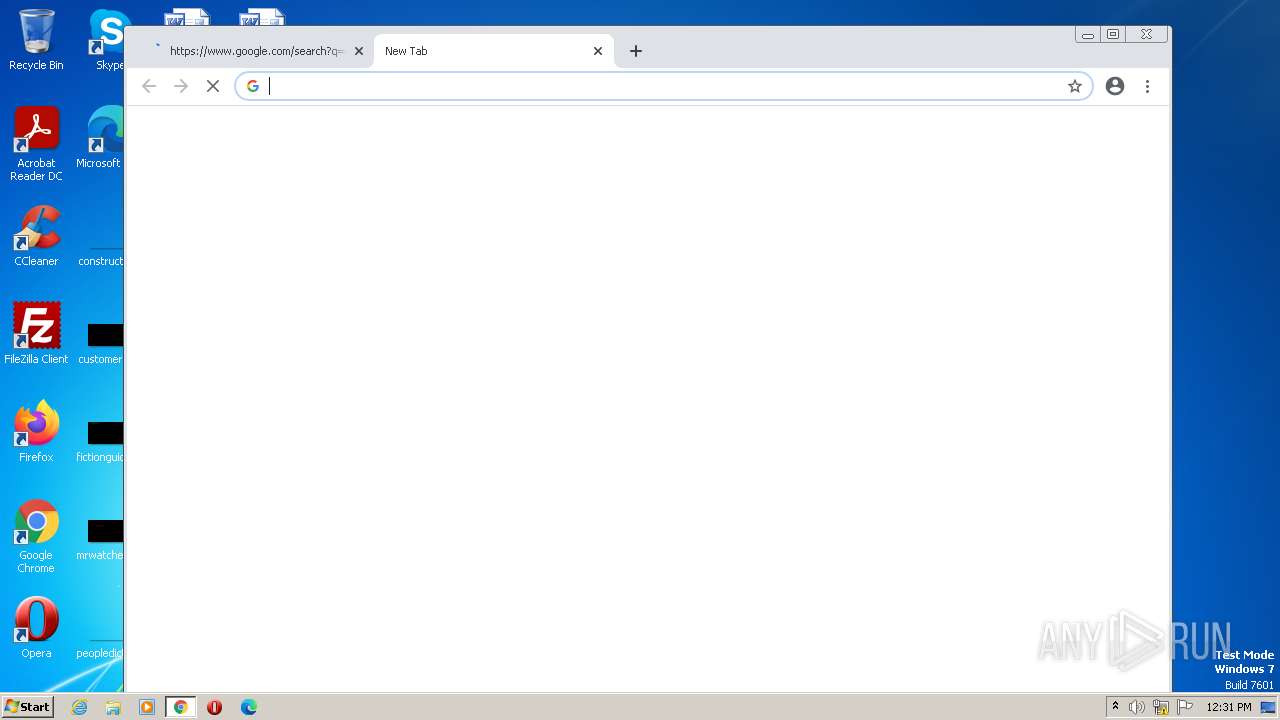
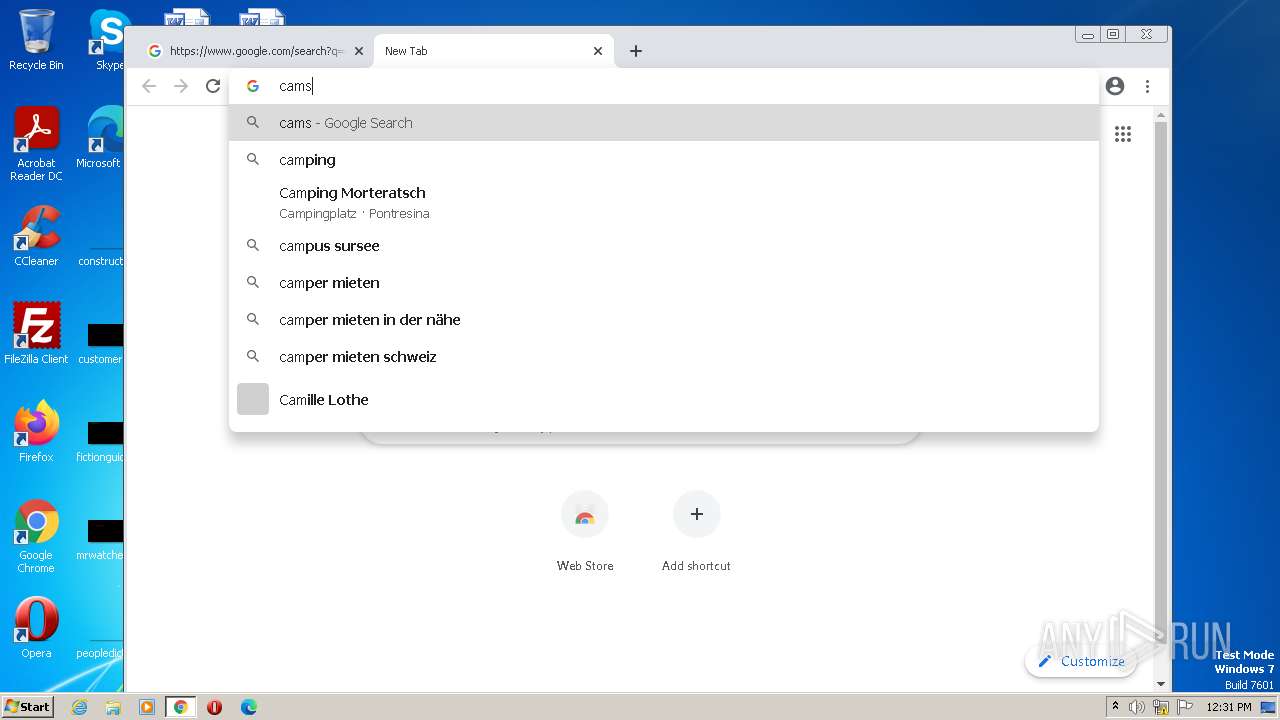
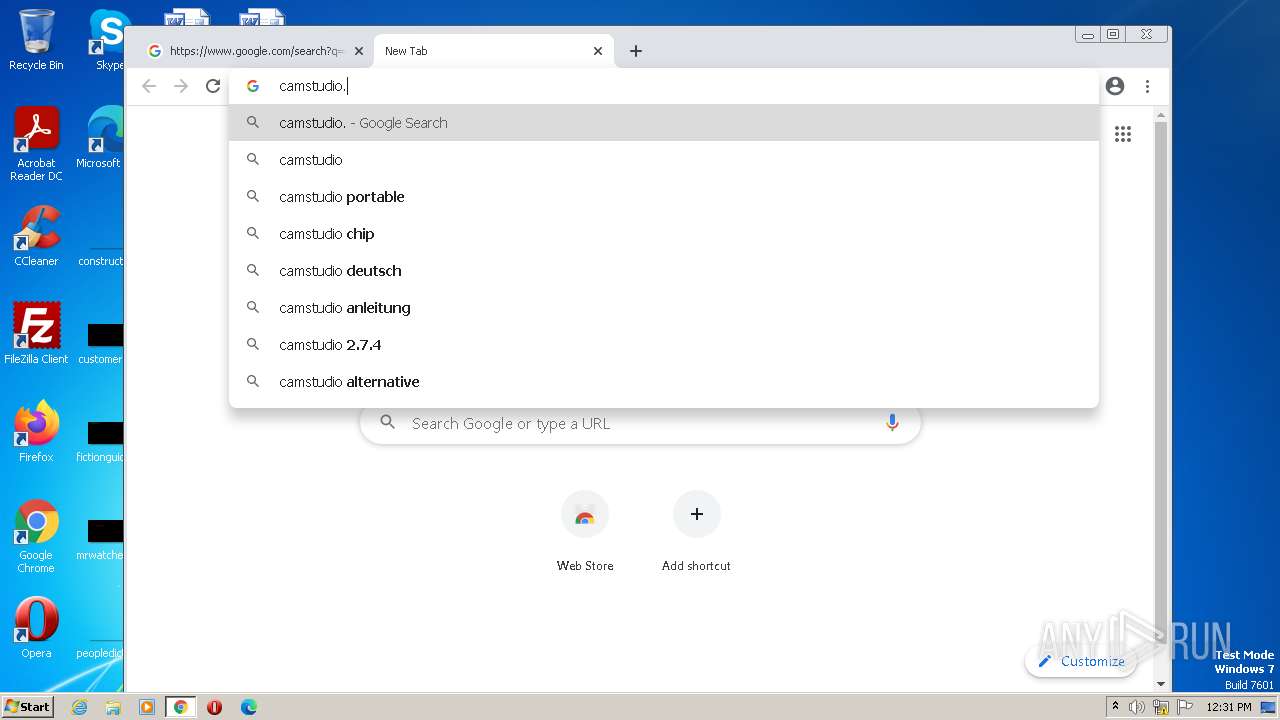
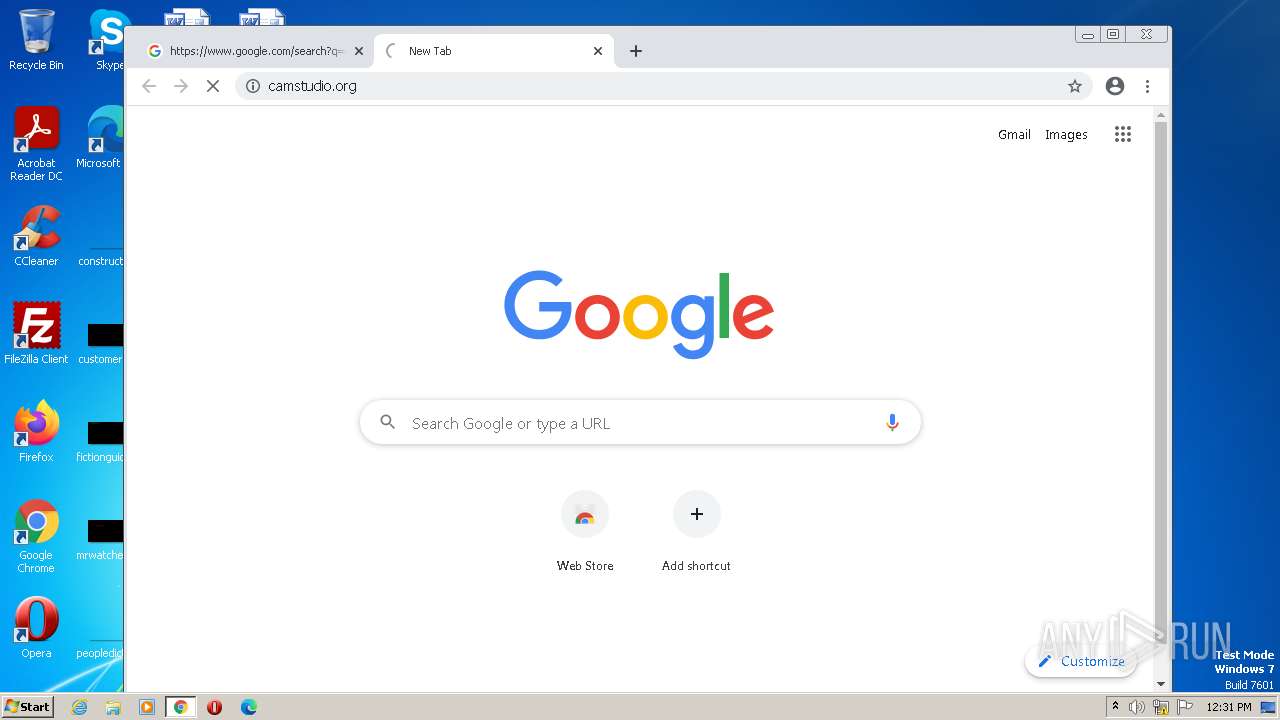
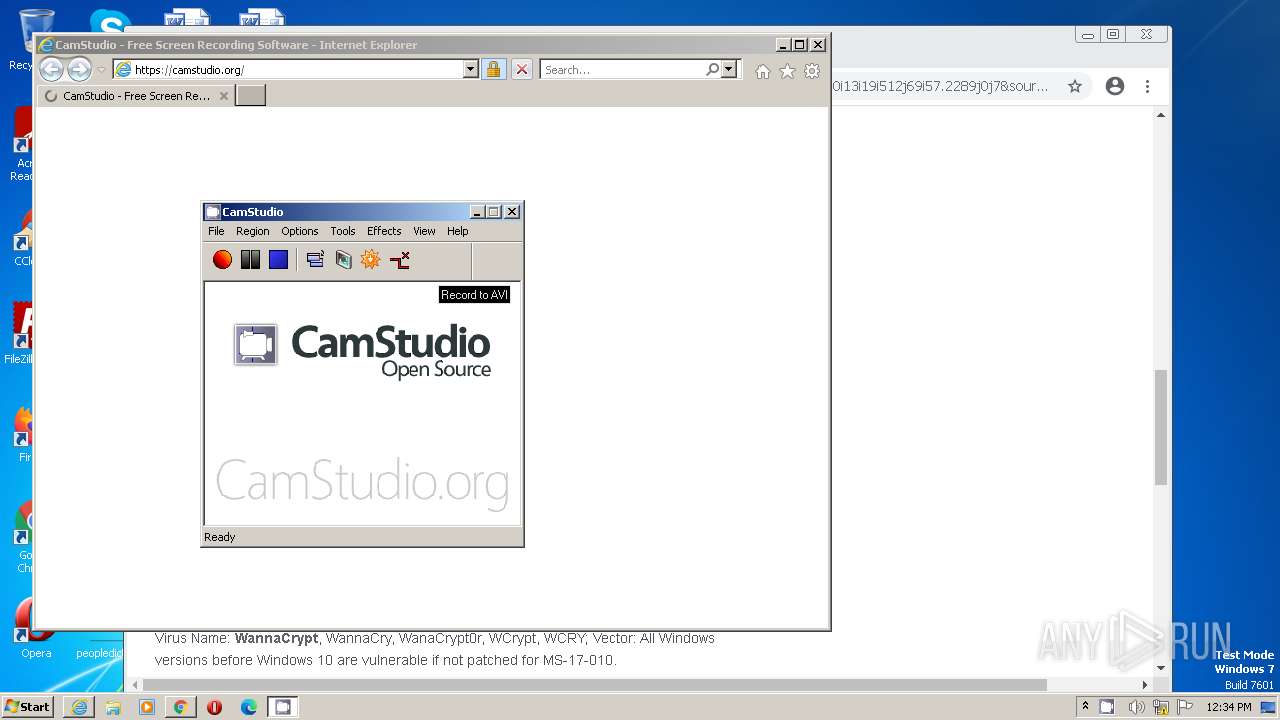
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 13EF0A01C20FB4DC01430810254D056A |
| SHA1: | 252B6C57773FA76C9450BC221EDEFB98D8BC6C4D |
| SHA256: | 3FBE450E3267799F372A775E4C7E7C47C8BBFFEEBB0BD0C9690E63374EBA8BA0 |
| SSDEEP: | 196608:crGkOf57TOjzO72VBbQuvBWc93BXqdL0yGsr8AWBaGb46bC4DkyAr/N7WtmG1bOu:wFU0zQgZD3cZ0yGsAAWBaC4/4gyA74mW |
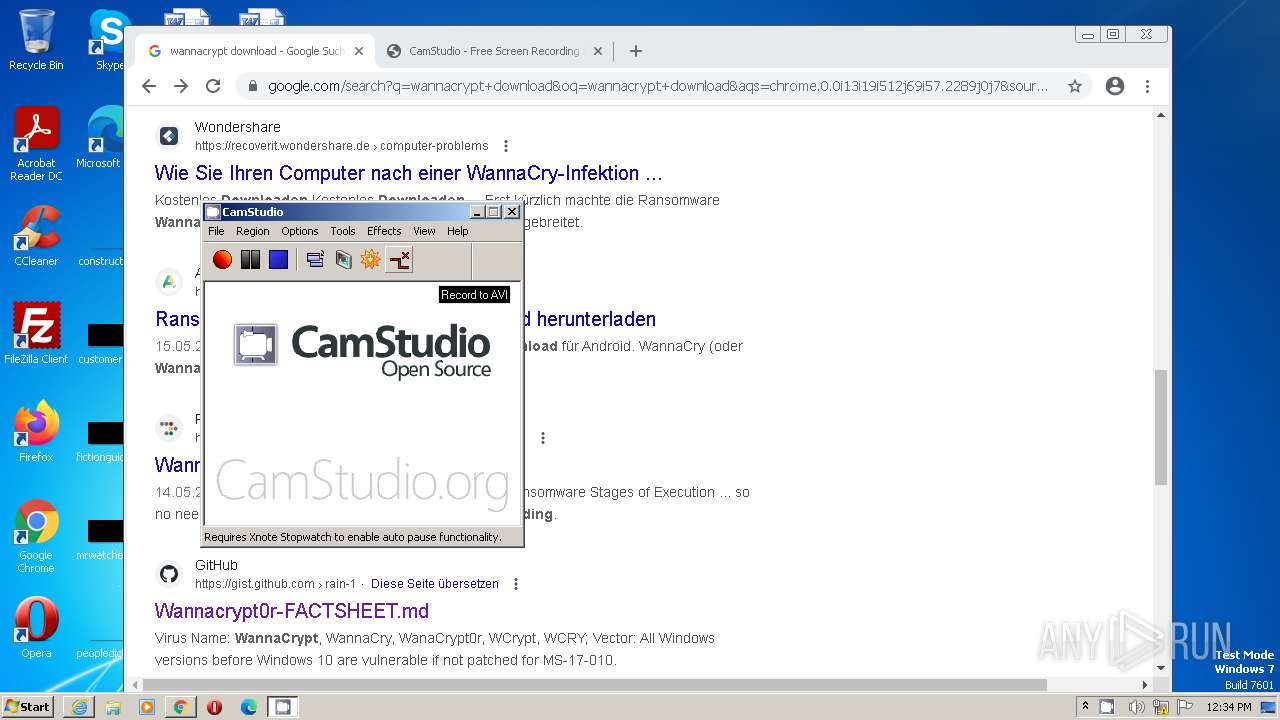
MALICIOUS
Application was dropped or rewritten from another process
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 1232)
- Recorder.exe (PID: 3684)
- Recorder.exe (PID: 3152)
- Recorder.exe (PID: 4020)
Loads dropped or rewritten executable
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 1232)
- Recorder.exe (PID: 3684)
- Recorder.exe (PID: 4020)
- Recorder.exe (PID: 3152)
SUSPICIOUS
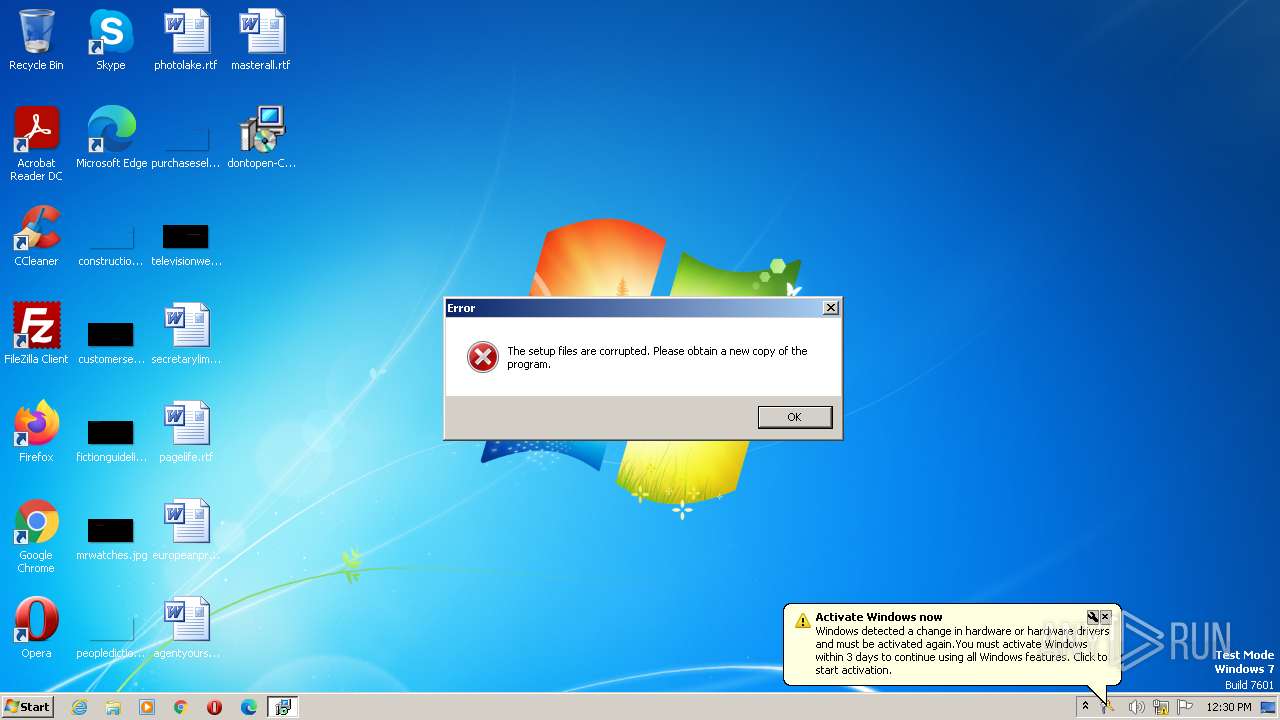
Executable content was dropped or overwritten
- CamStudioSetup.exe (PID: 1816)
- CamStudioSetup.exe (PID: 3780)
- CamStudioSetup.tmp (PID: 3468)
Reads the Windows owner or organization settings
- CamStudioSetup.tmp (PID: 3468)
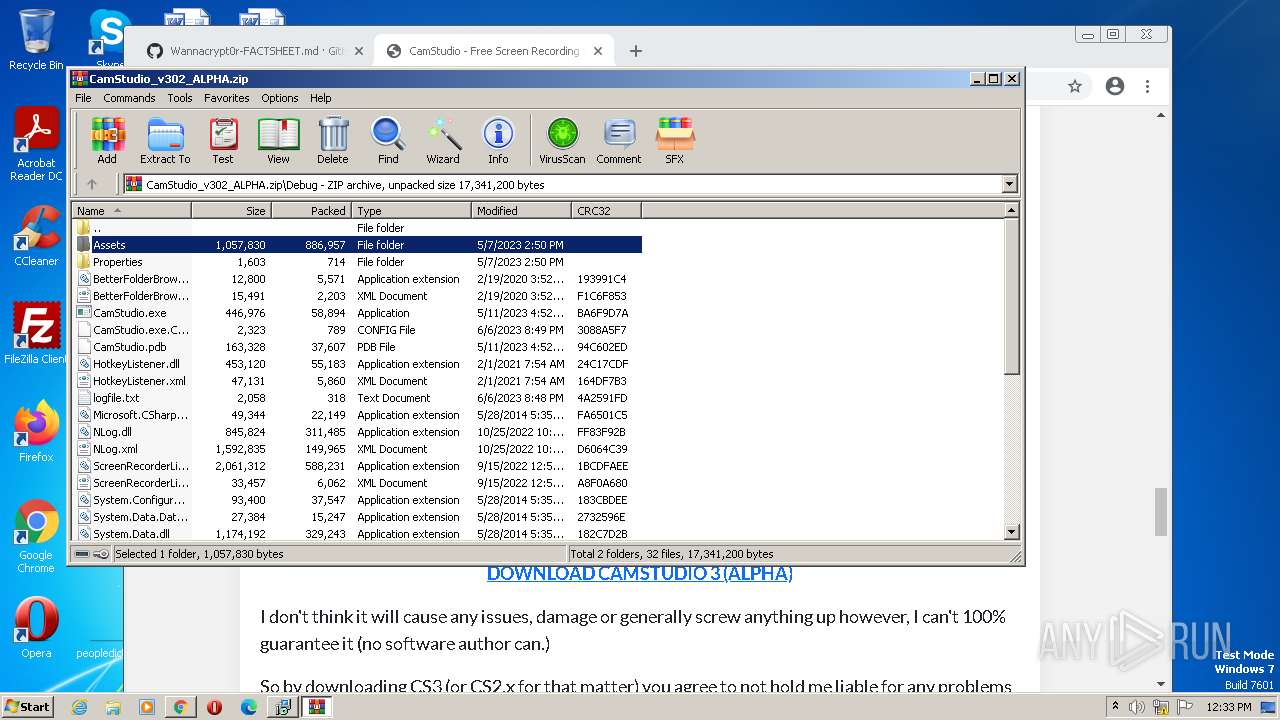
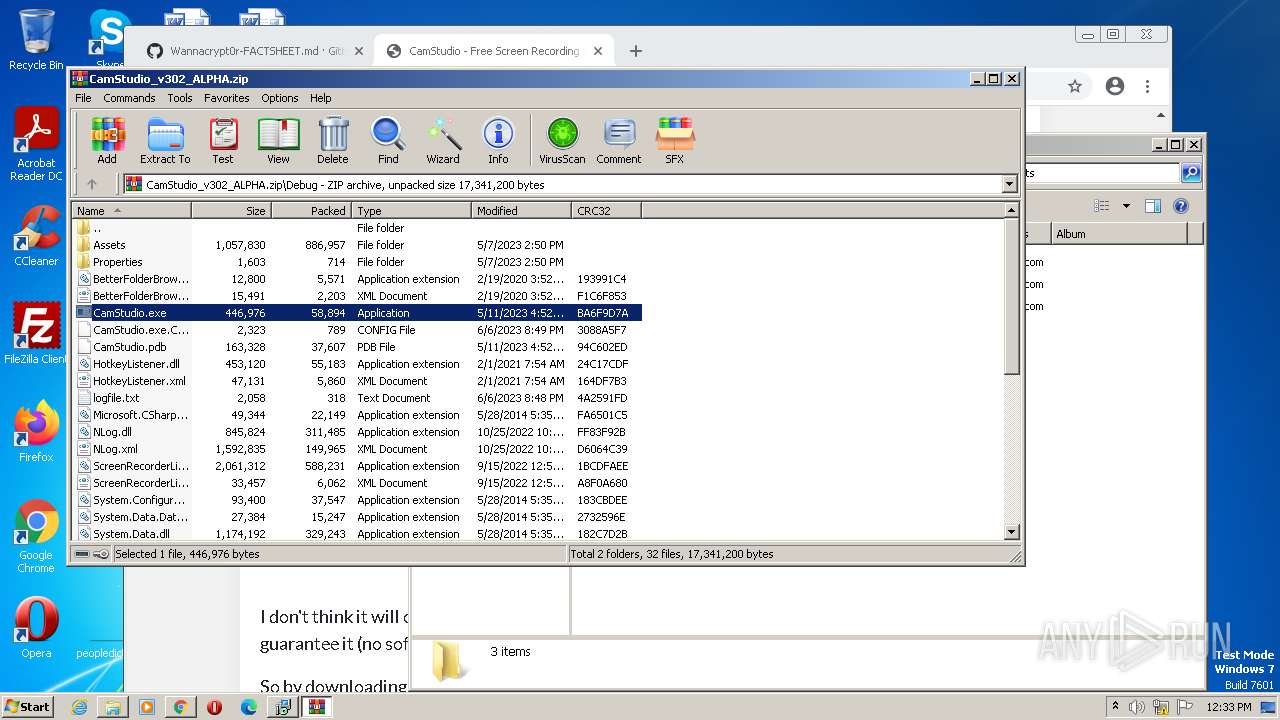
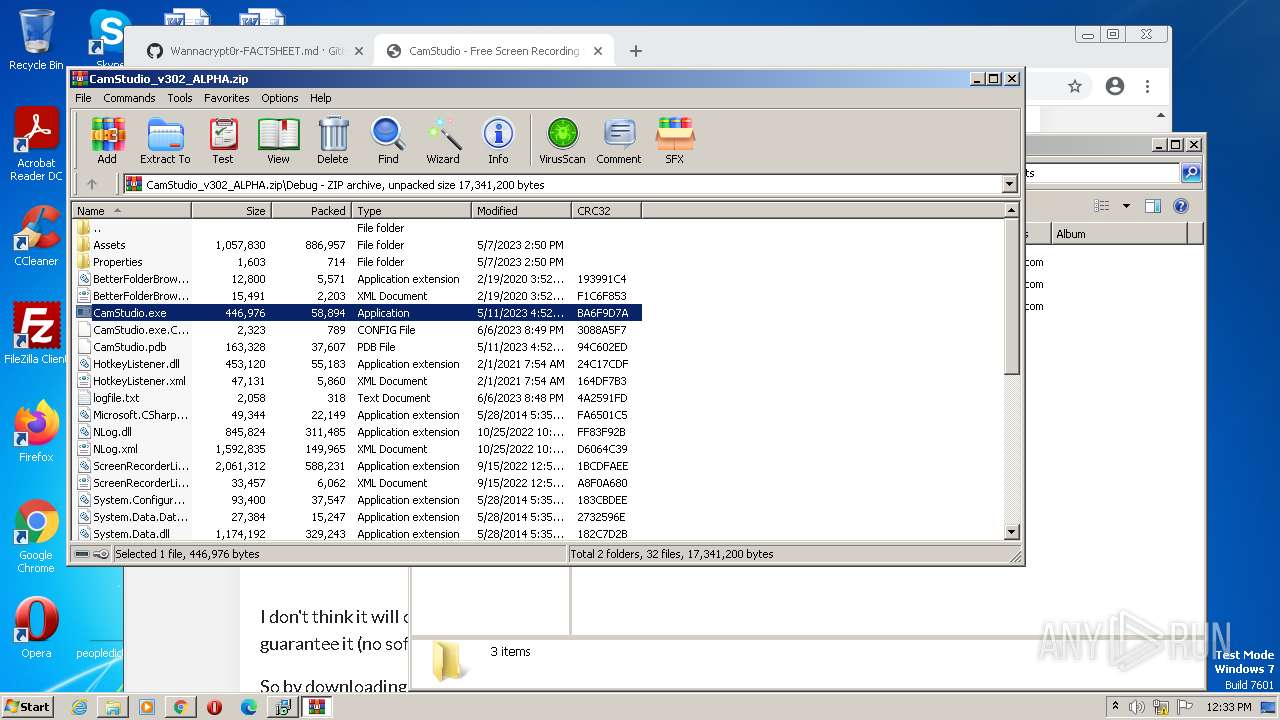
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3032)
Reads the Internet Settings
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
Reads security settings of Internet Explorer
- Recorder.exe (PID: 3304)
Checks Windows Trust Settings
- Recorder.exe (PID: 3304)
Reads settings of System Certificates
- Recorder.exe (PID: 3304)
INFO
Checks supported languages
- dontopen-CamStudioSetup.exe (PID: 3816)
- CamStudioSetup.exe (PID: 3780)
- CamStudioSetup.tmp (PID: 3496)
- CamStudioSetup.exe (PID: 1816)
- CamStudioSetup.tmp (PID: 3468)
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 1232)
- Recorder.exe (PID: 3684)
- Recorder.exe (PID: 3152)
- Recorder.exe (PID: 4020)
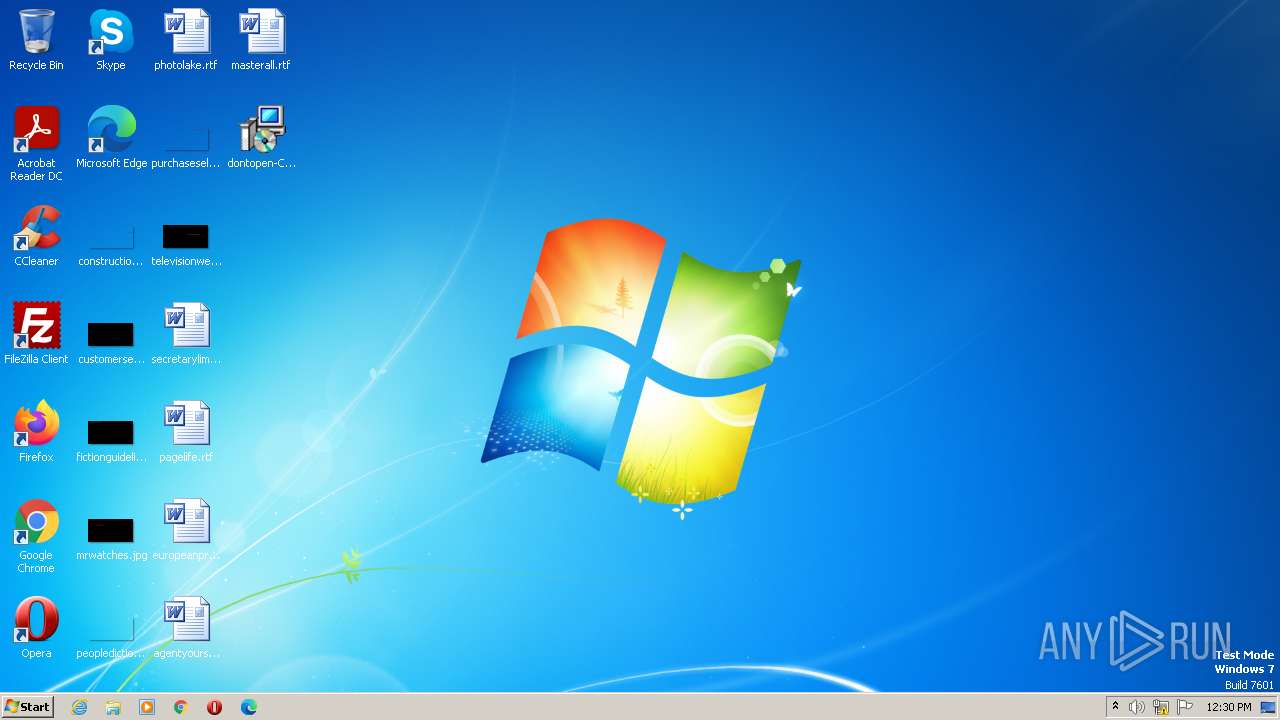
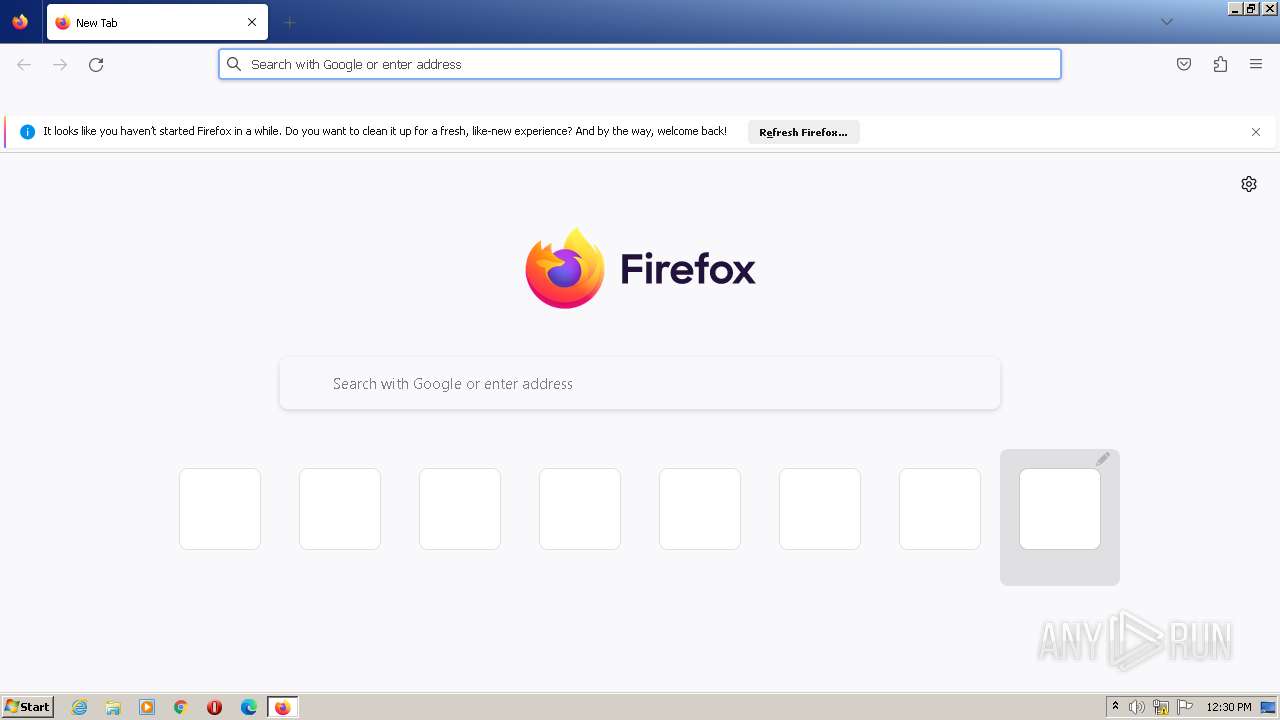
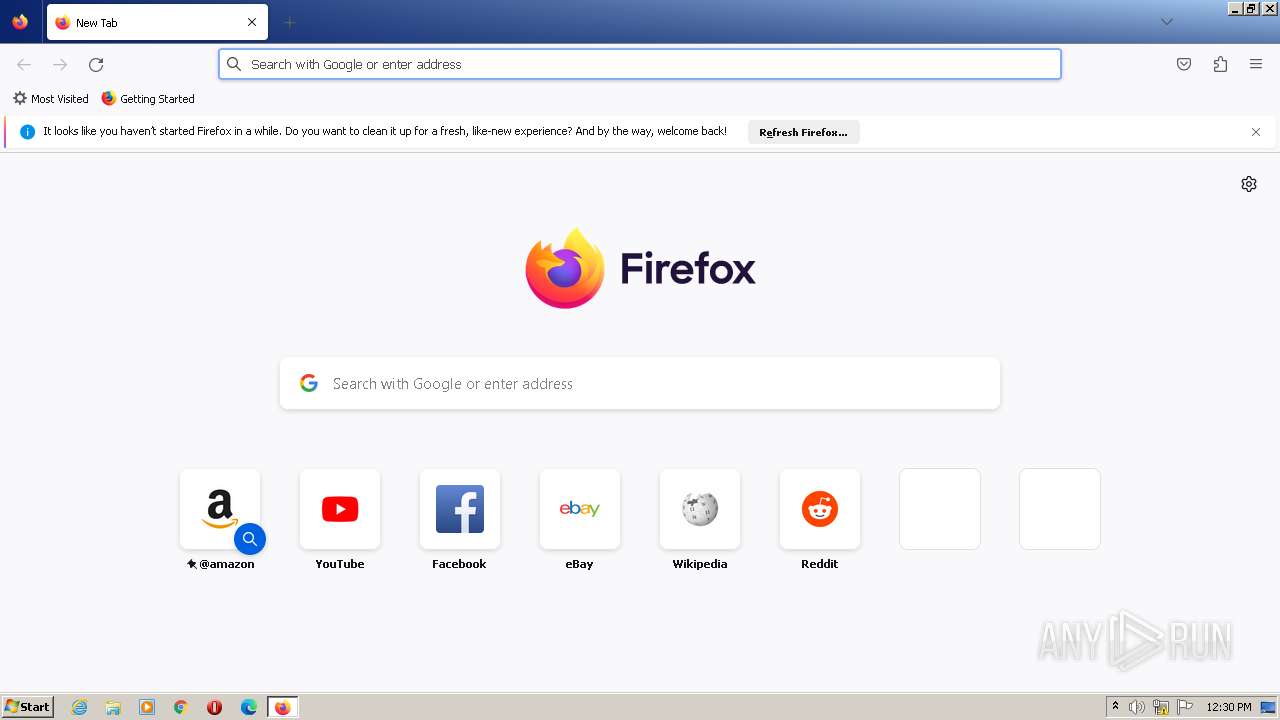
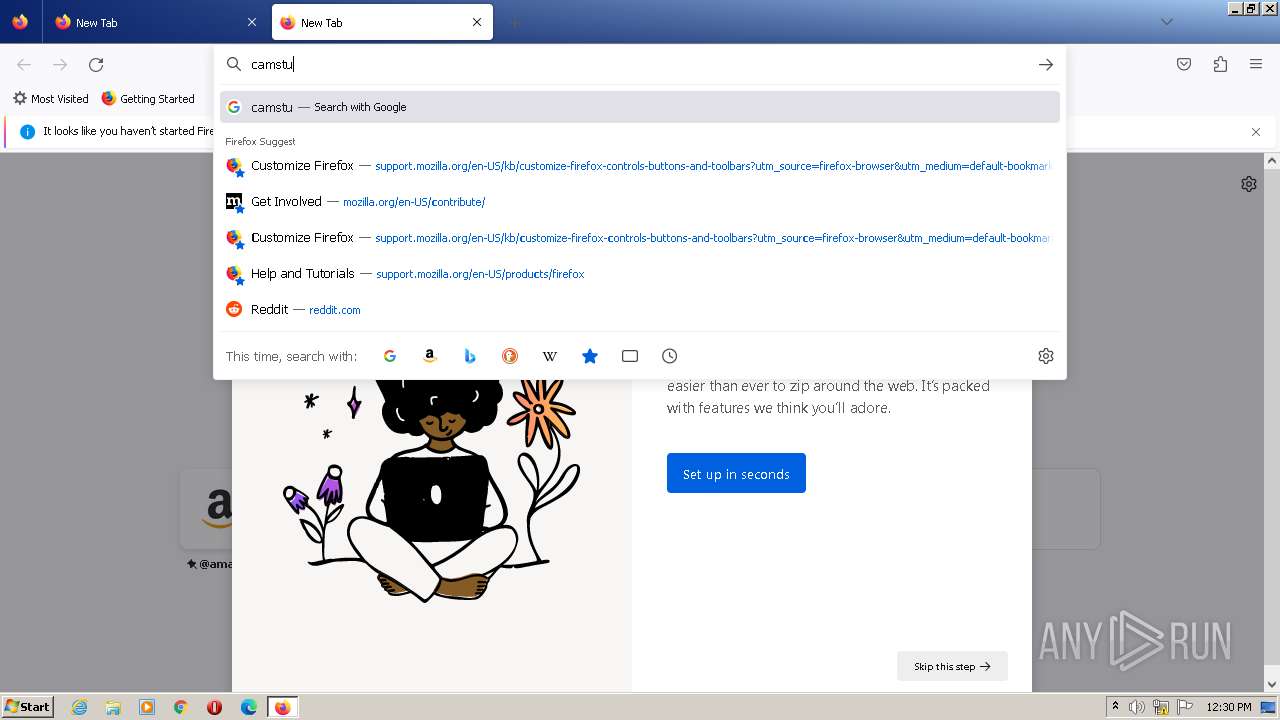
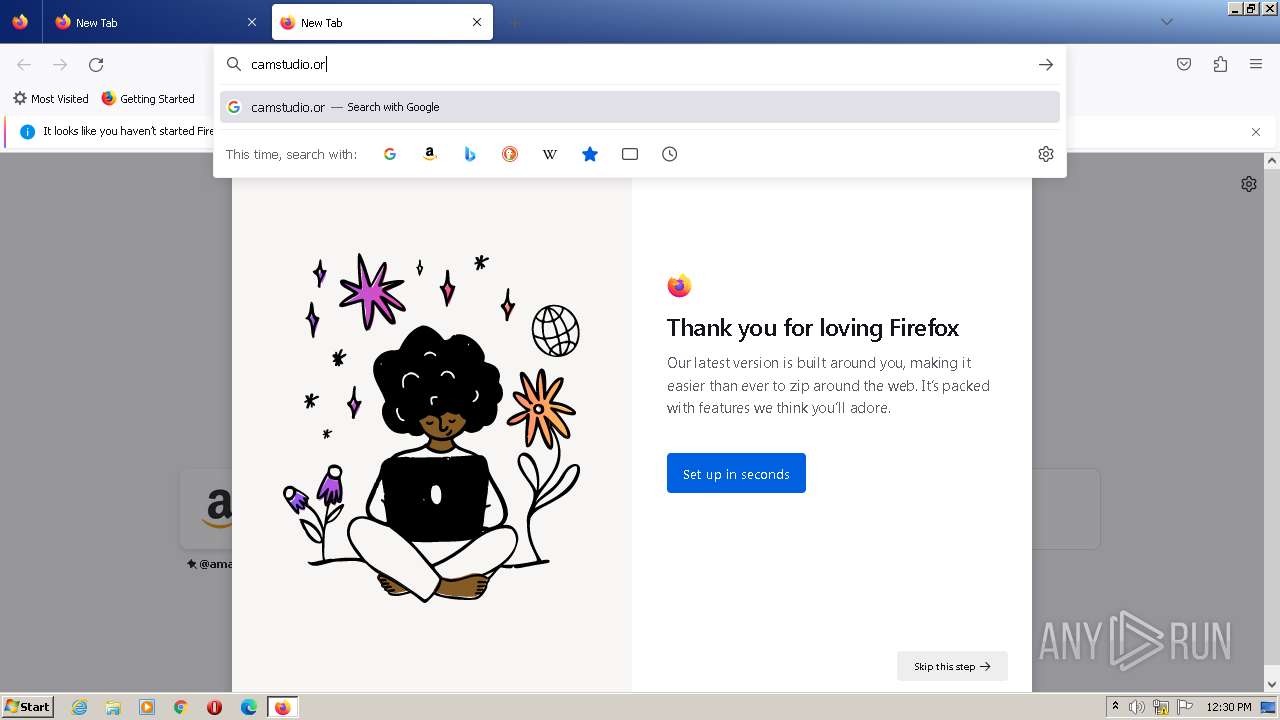
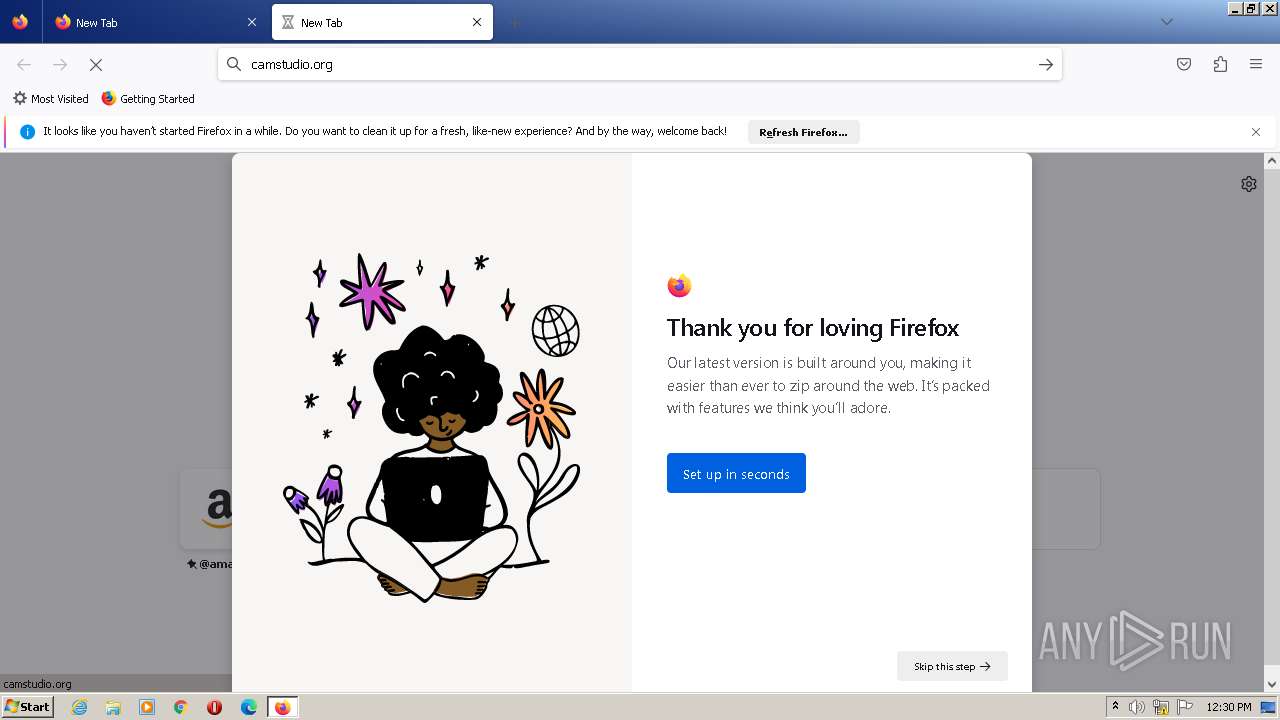
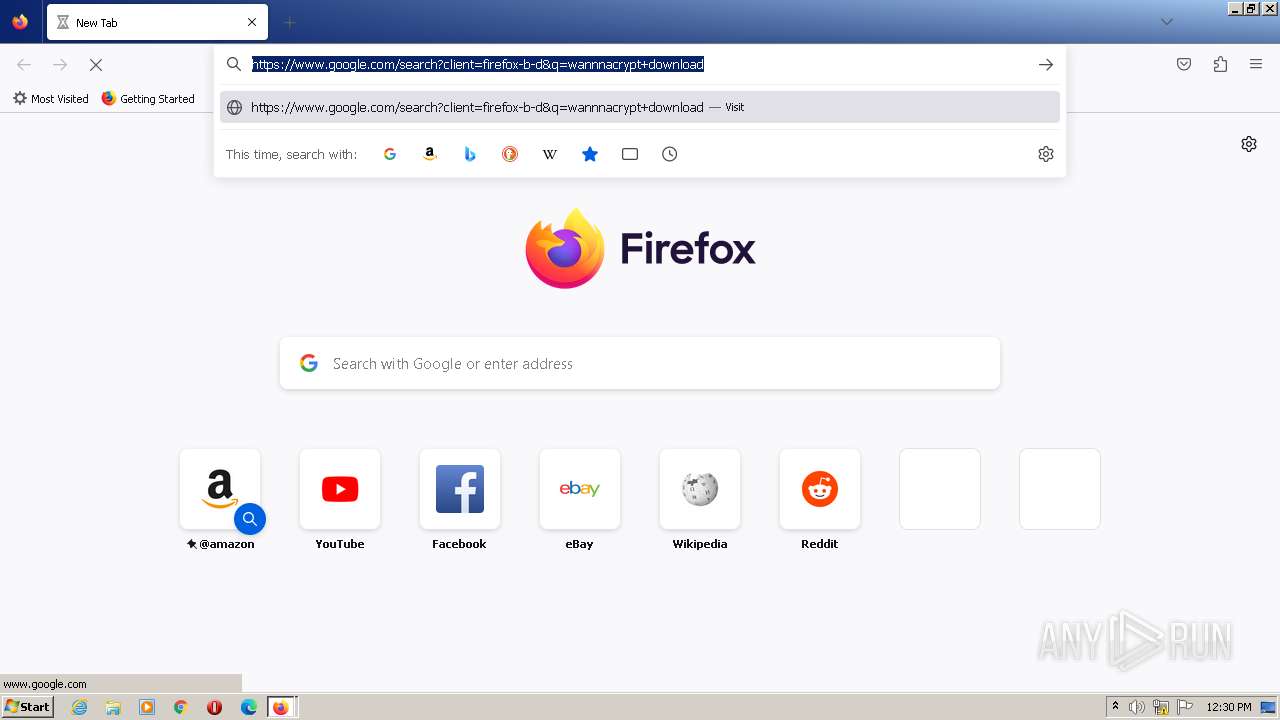
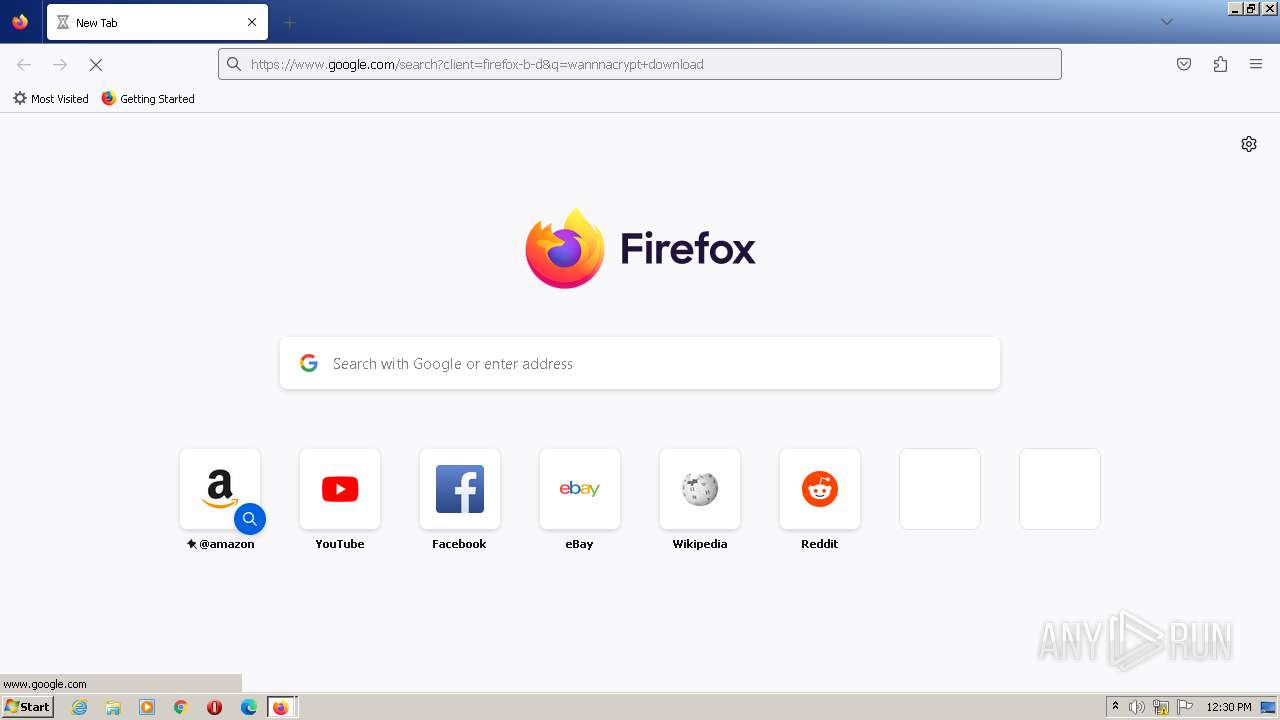
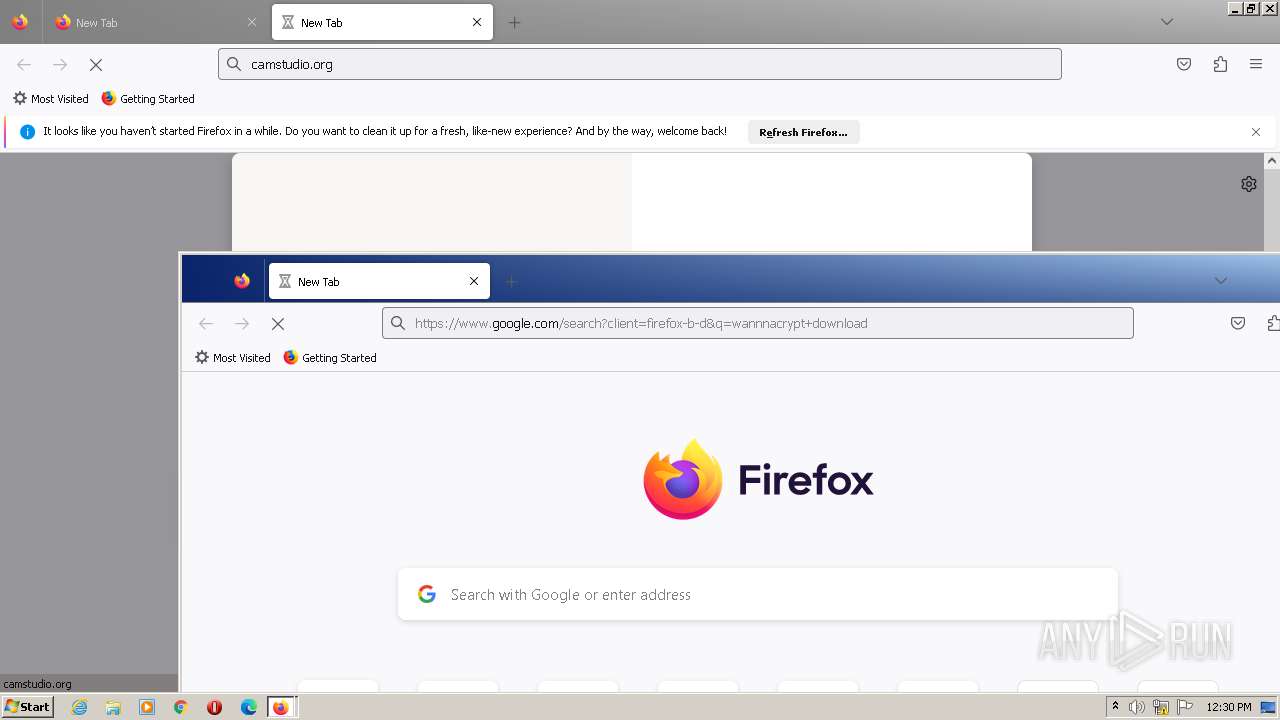
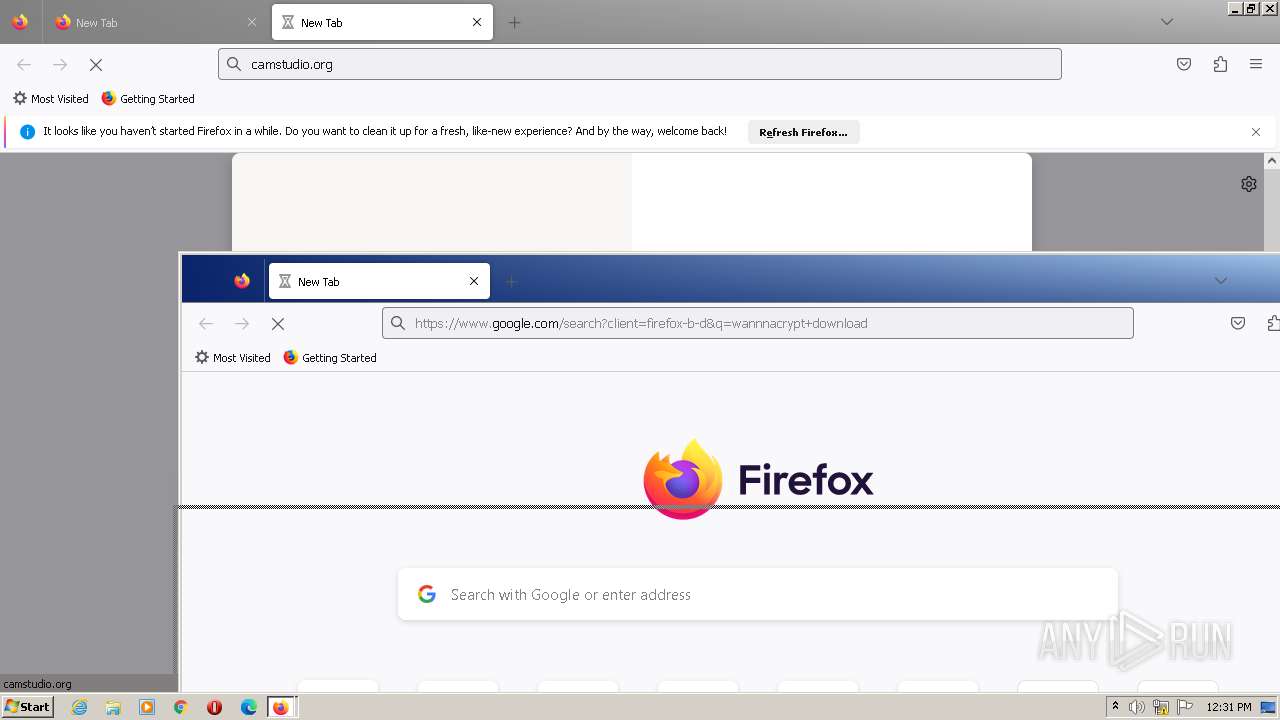
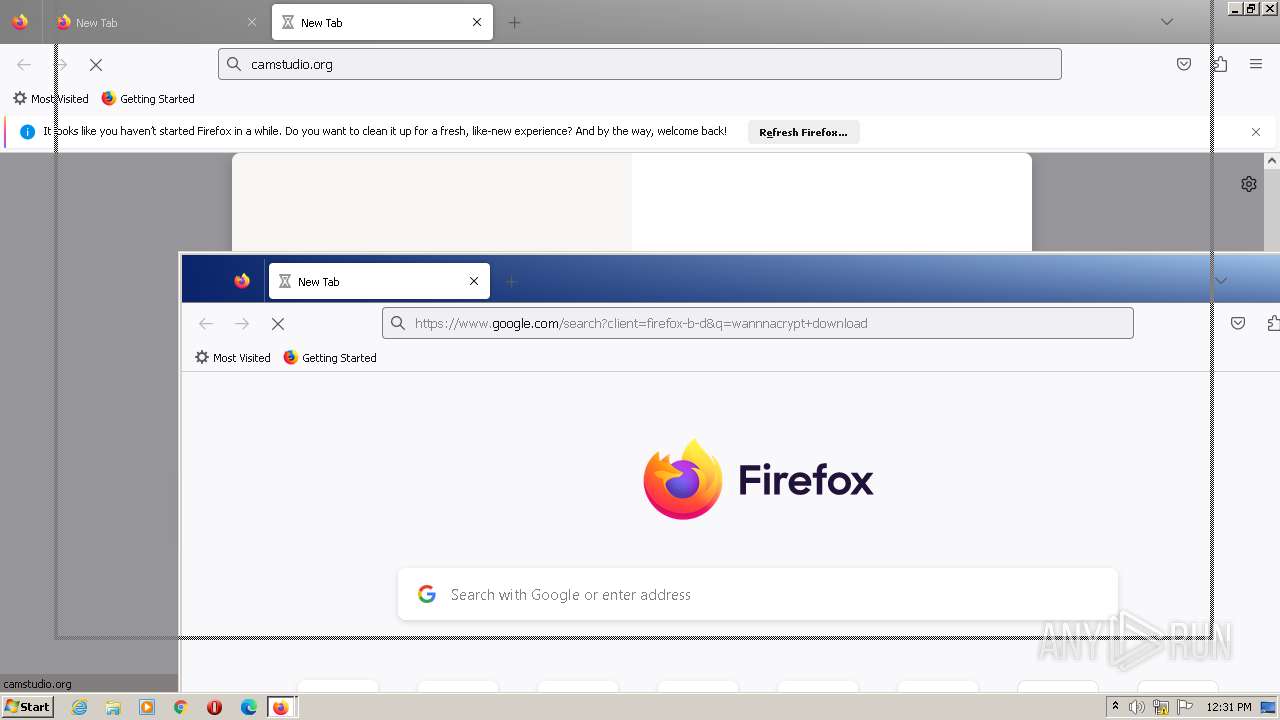
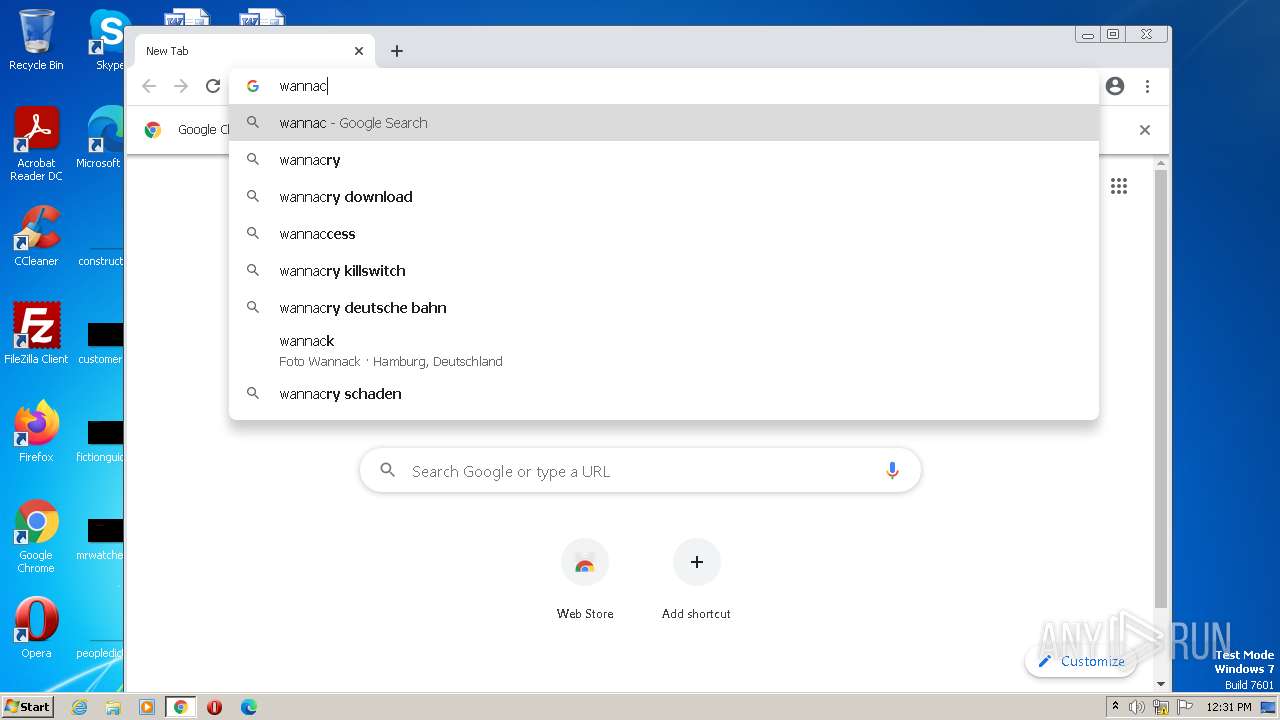
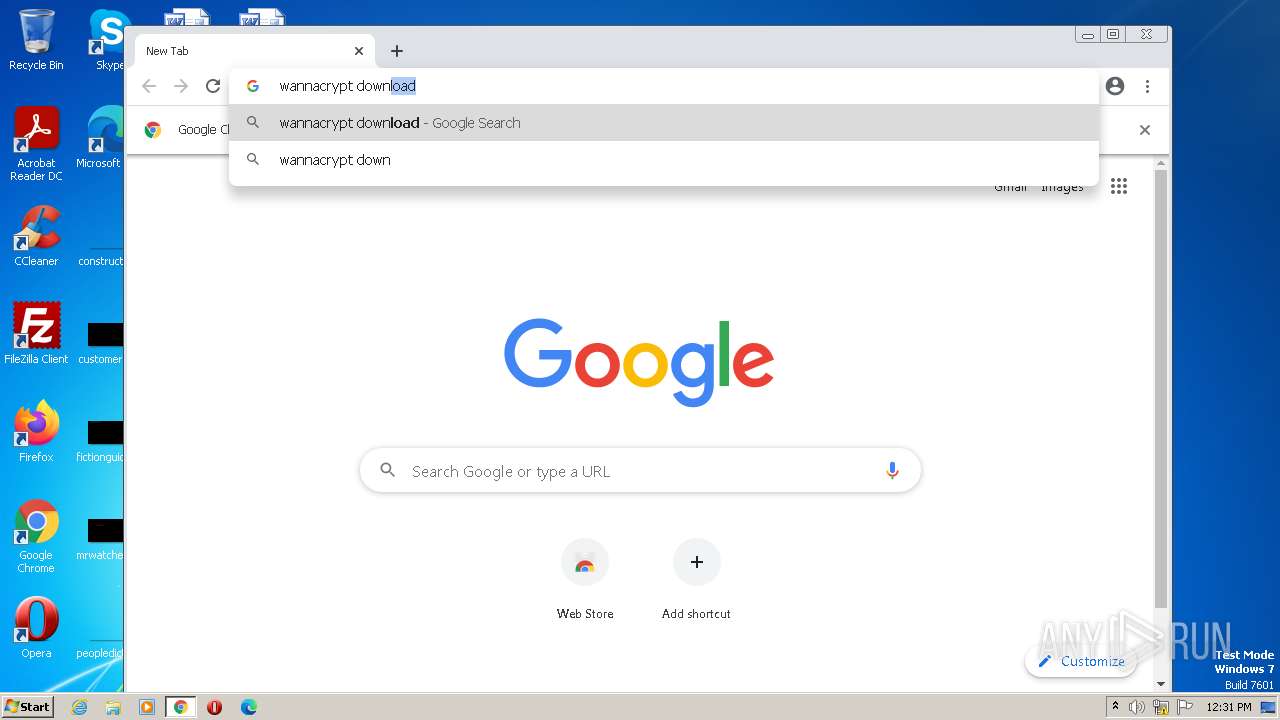
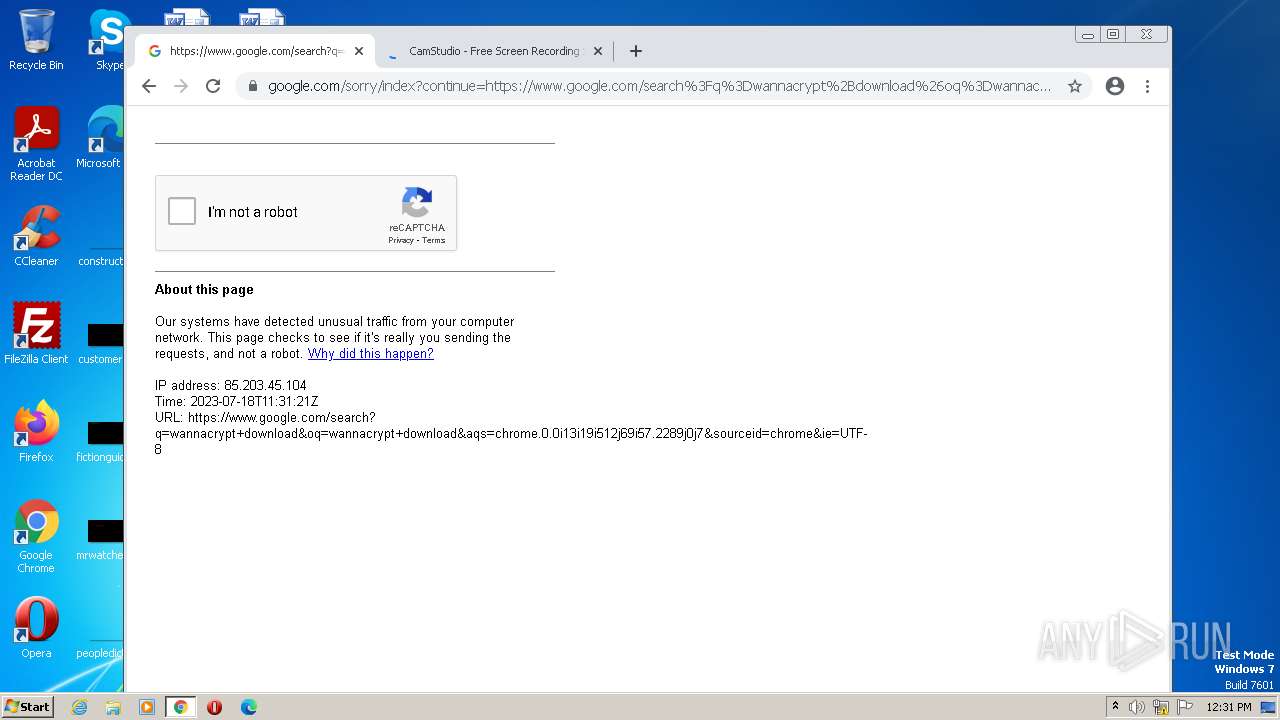
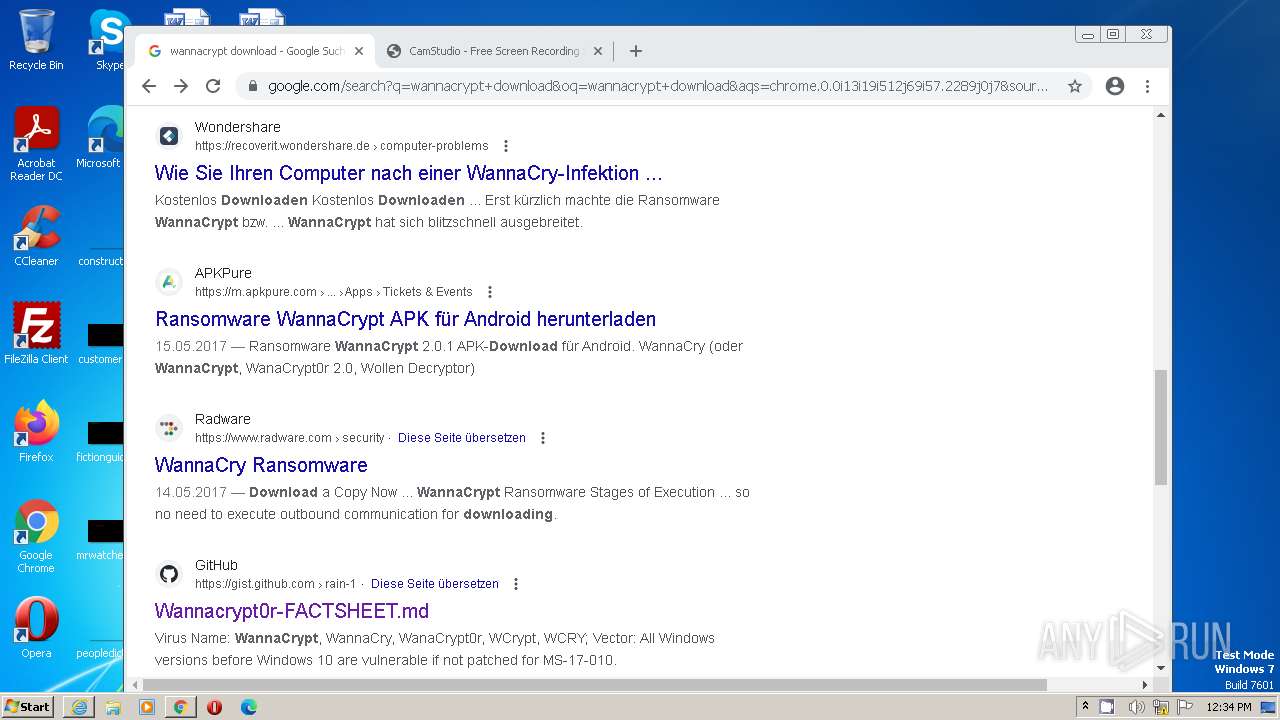
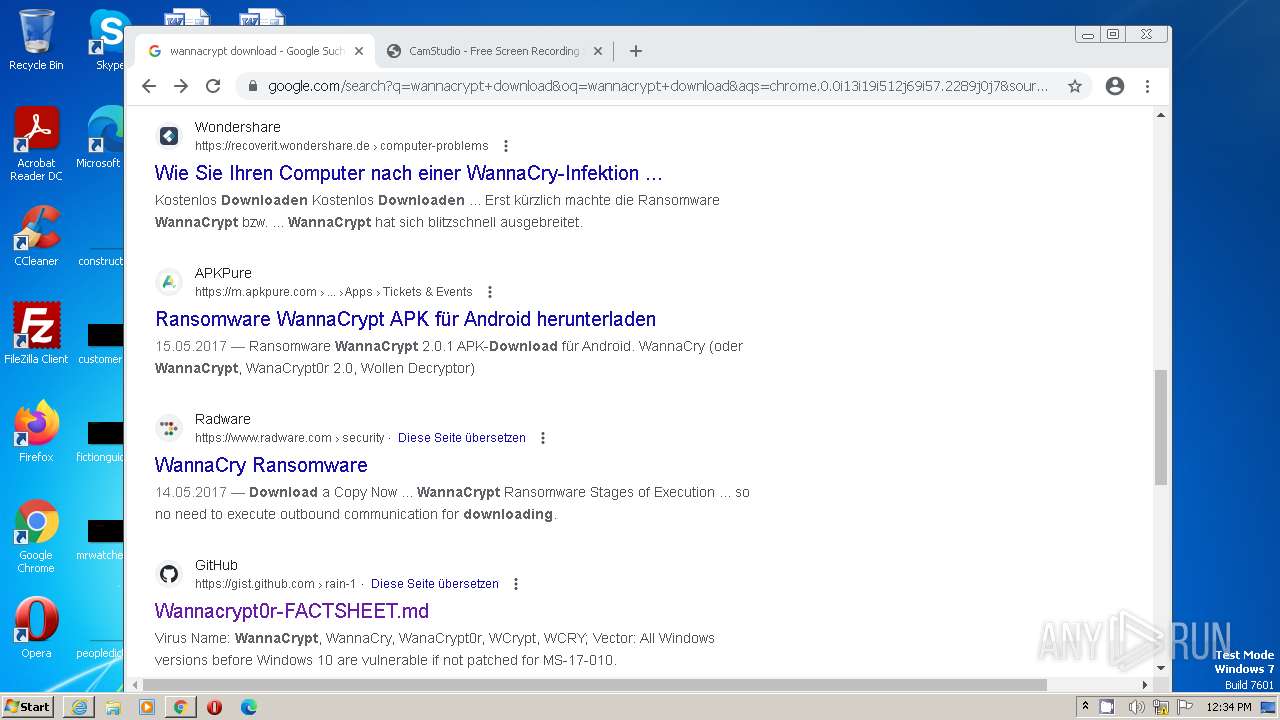
Application launched itself
- firefox.exe (PID: 3608)
- firefox.exe (PID: 1152)
- chrome.exe (PID: 3232)
- msedge.exe (PID: 1984)
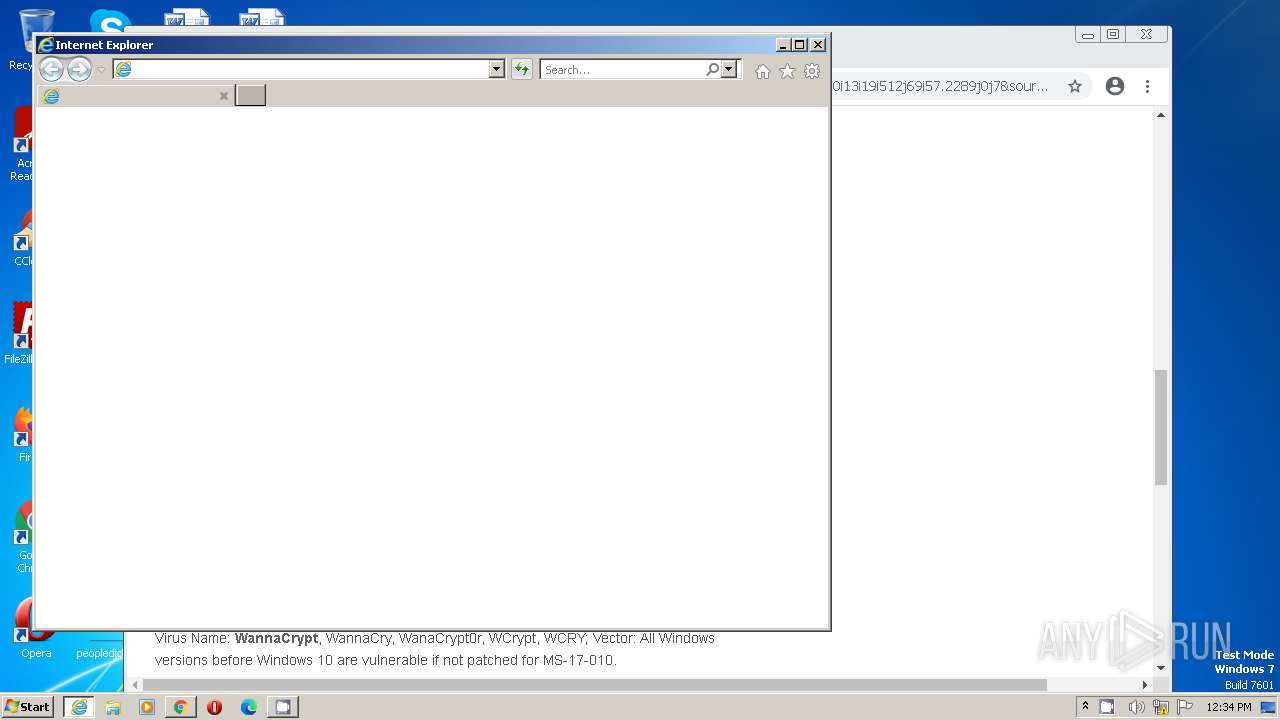
- iexplore.exe (PID: 1420)
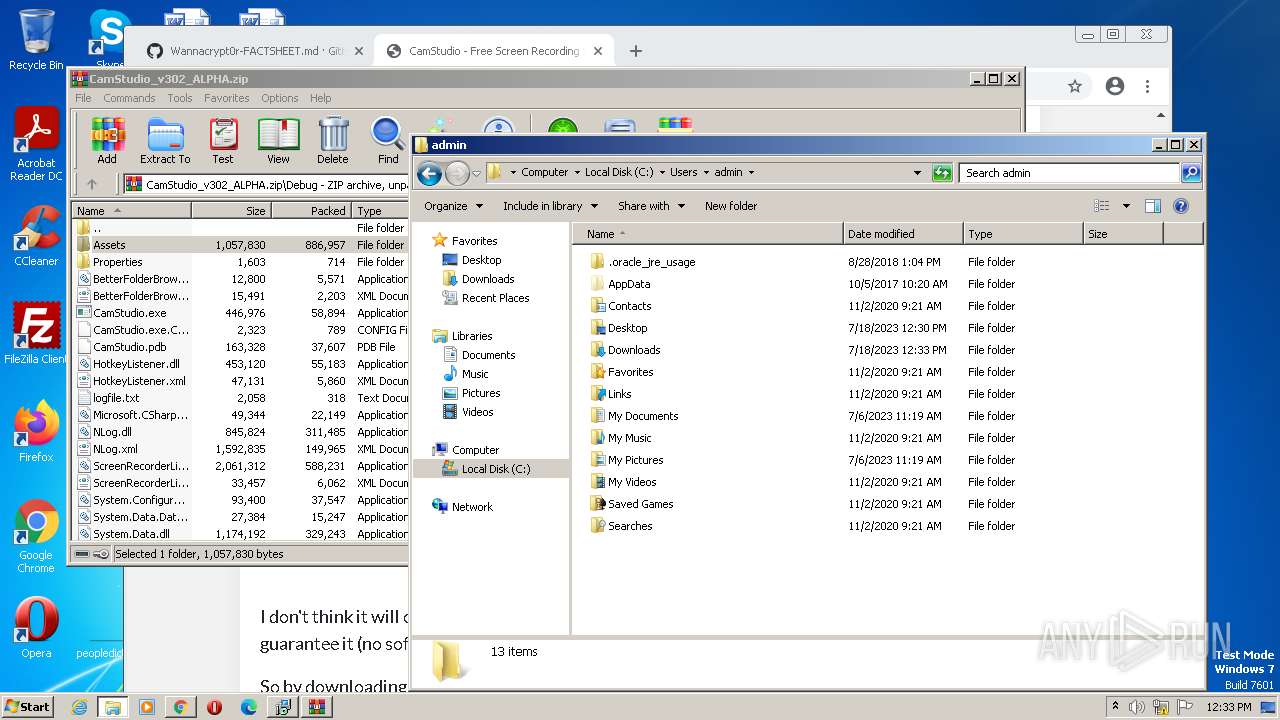
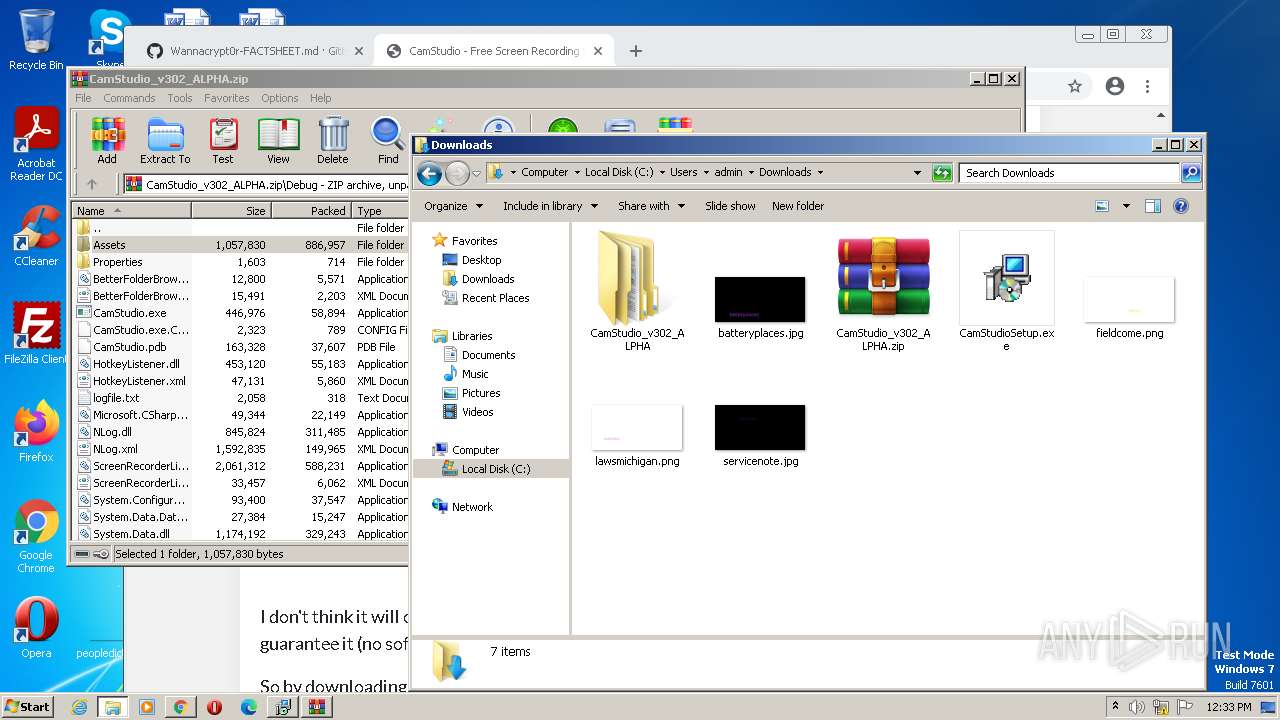
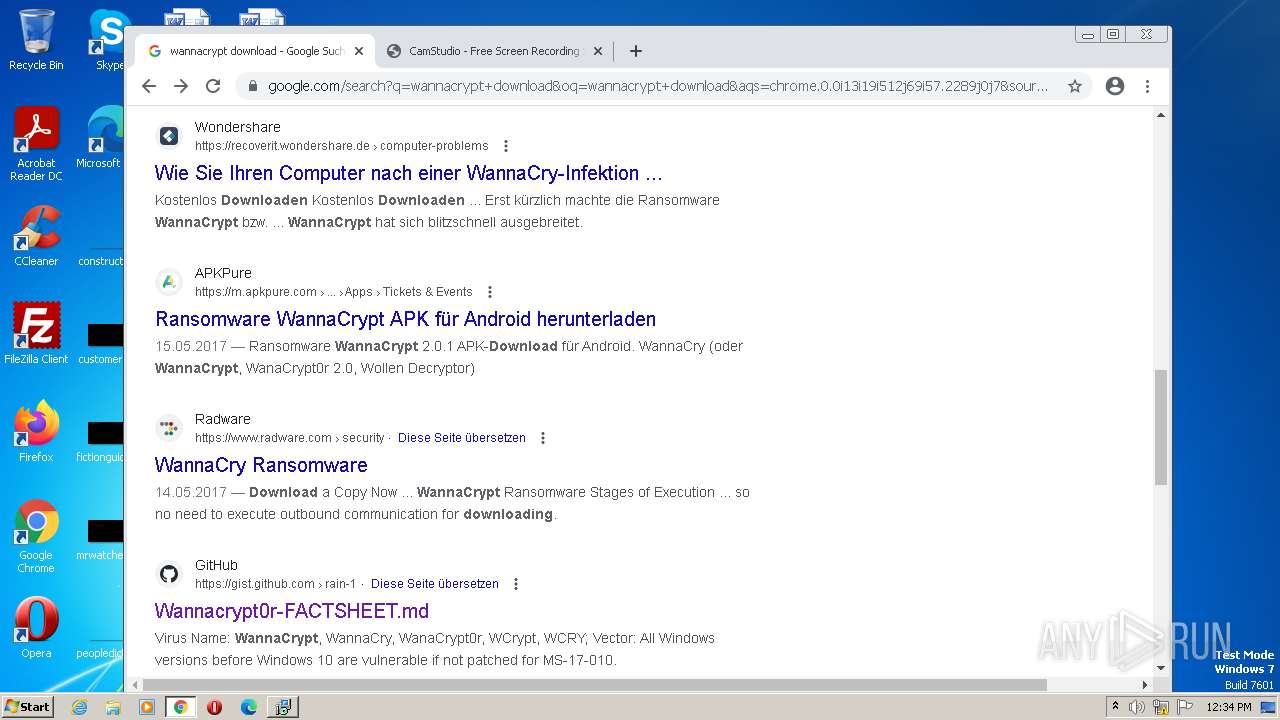
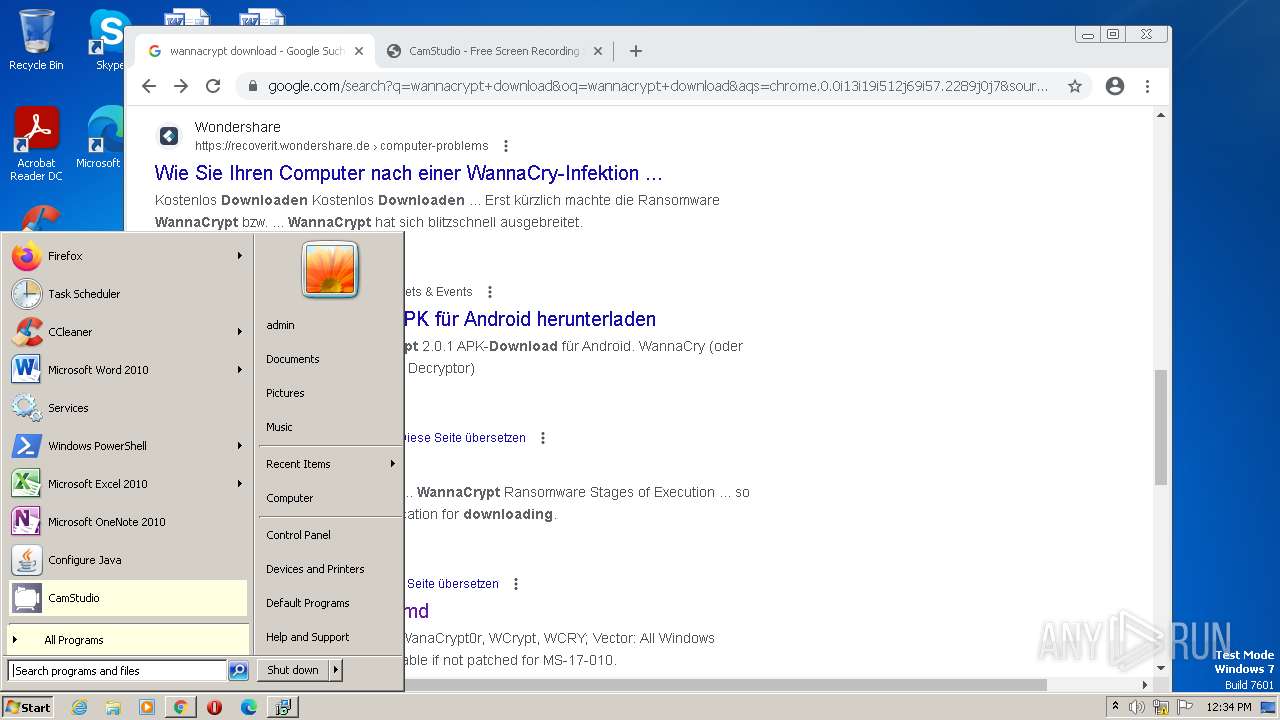
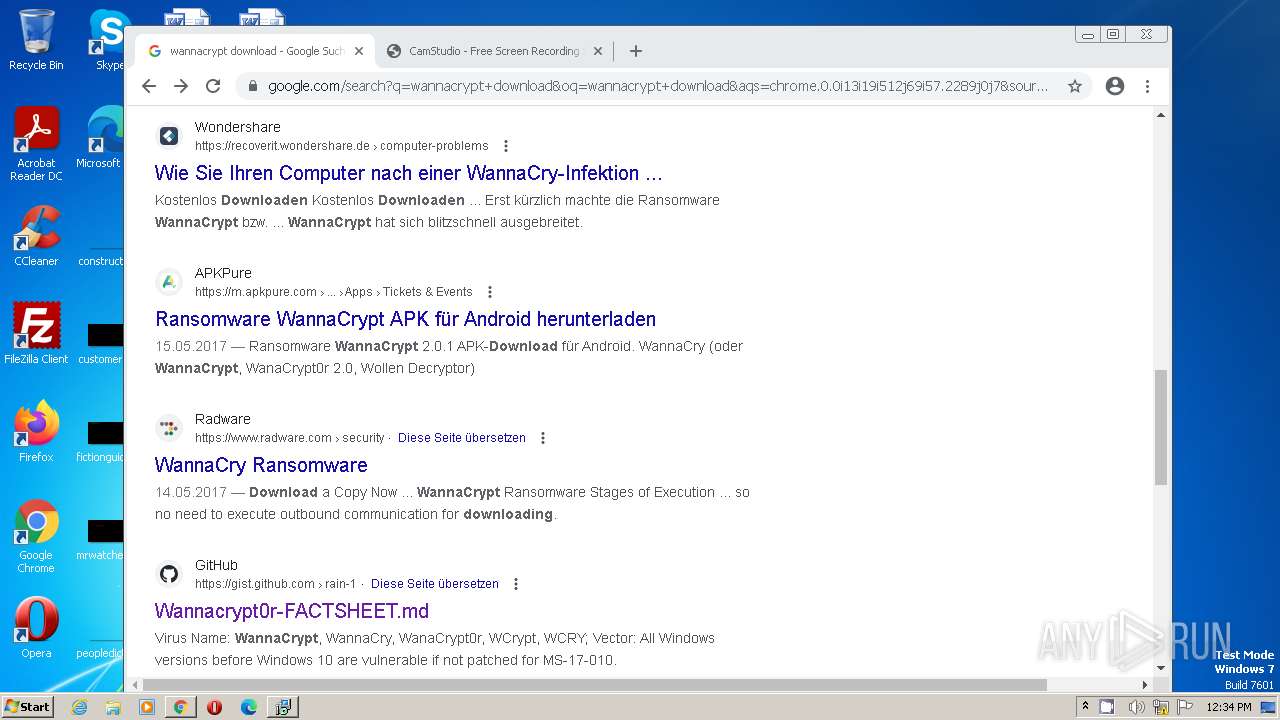
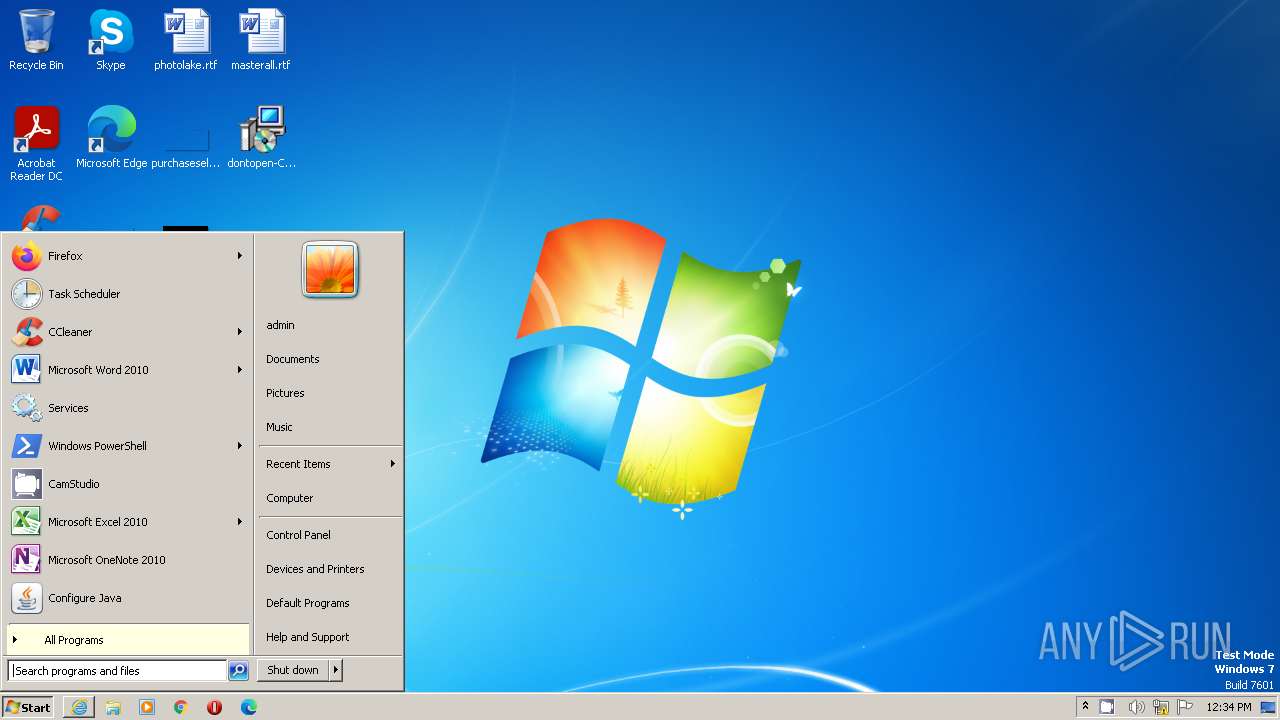
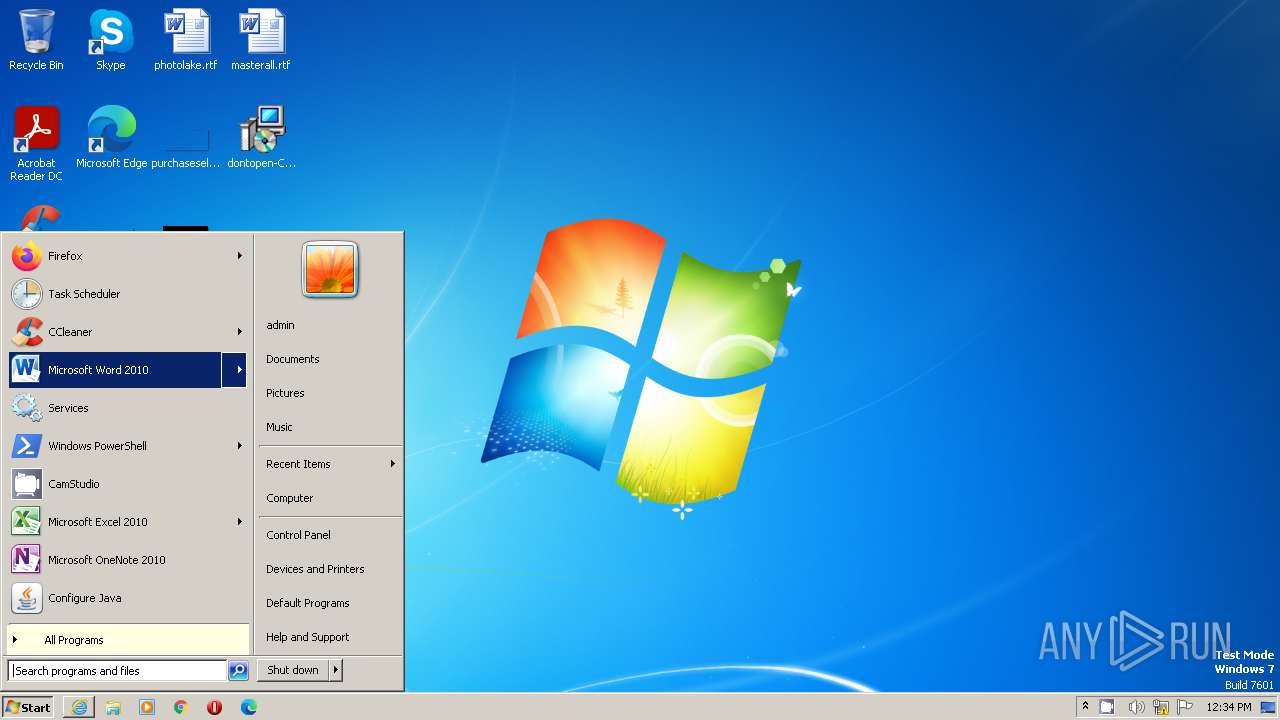
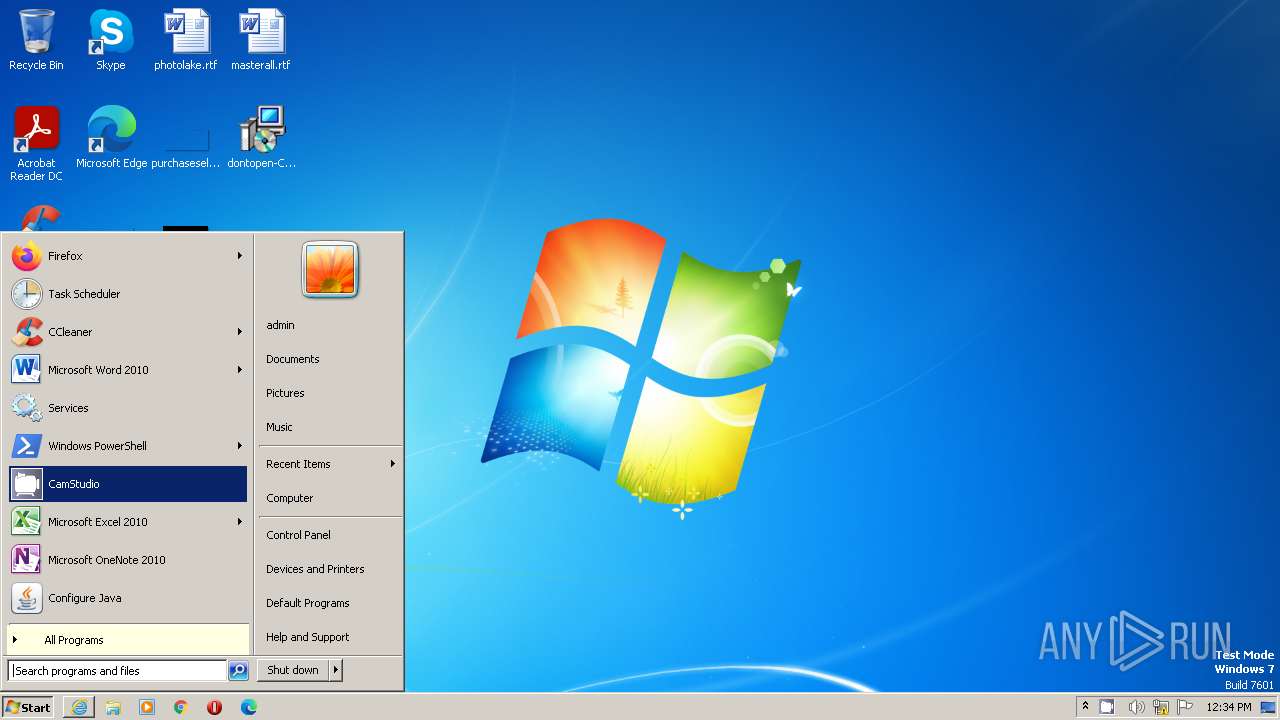
Manual execution by a user
- chrome.exe (PID: 3232)
- firefox.exe (PID: 3608)
- explorer.exe (PID: 2032)
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 3684)
- Recorder.exe (PID: 3152)
- Recorder.exe (PID: 4020)
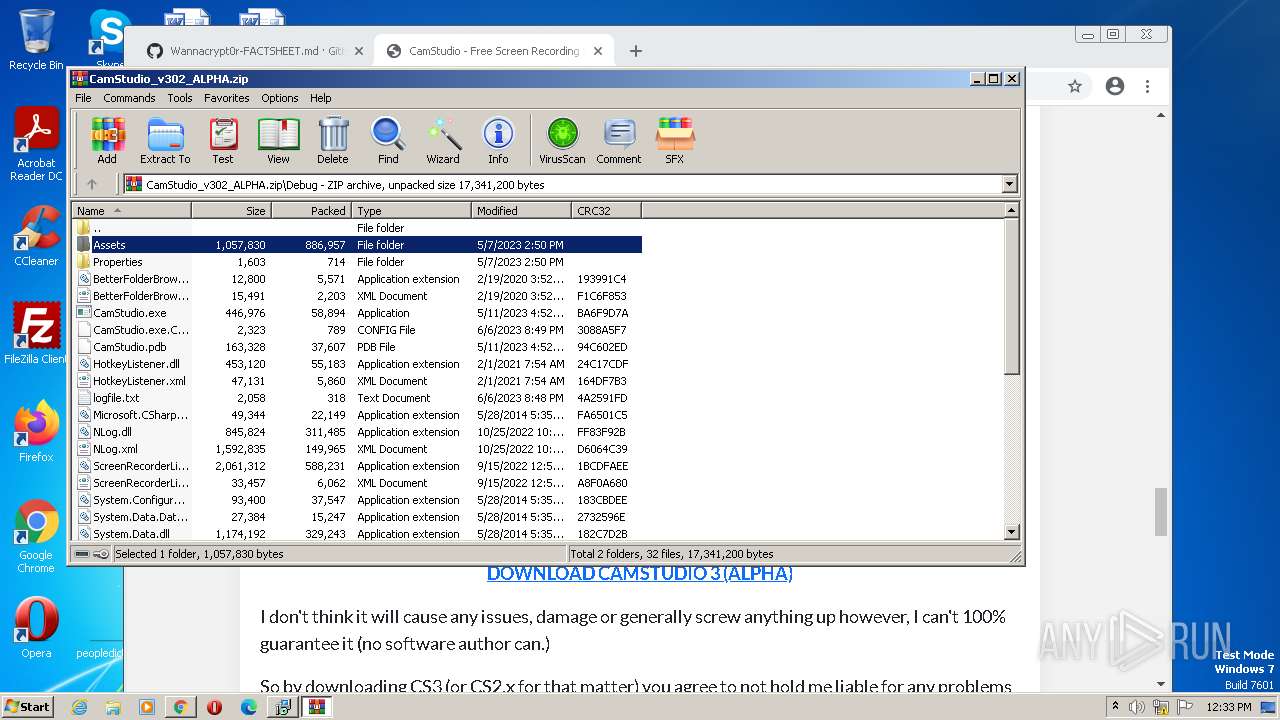
The process uses the downloaded file
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2256)
- WinRAR.exe (PID: 3032)
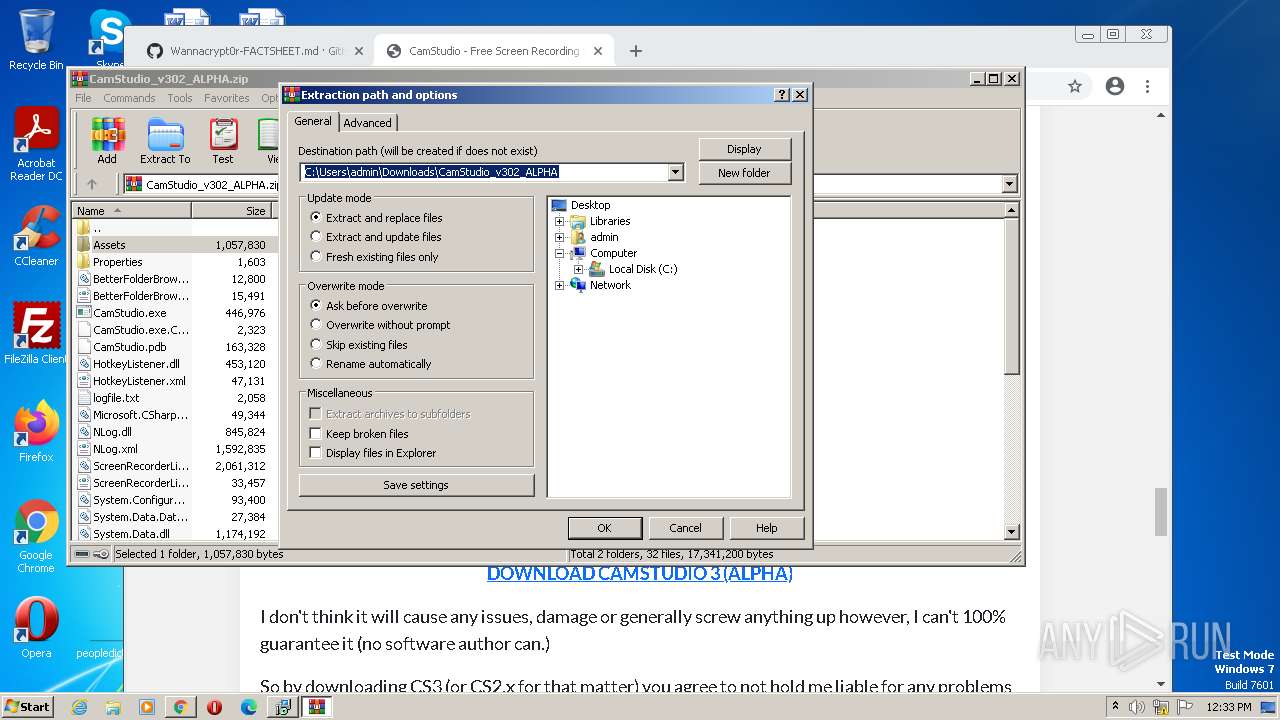
Create files in a temporary directory
- CamStudioSetup.exe (PID: 3780)
- CamStudioSetup.exe (PID: 1816)
- CamStudioSetup.tmp (PID: 3468)
Reads the computer name
- CamStudioSetup.tmp (PID: 3496)
- CamStudioSetup.tmp (PID: 3468)
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 1232)
- Recorder.exe (PID: 3684)
- Recorder.exe (PID: 4020)
- Recorder.exe (PID: 3152)
Executable content was dropped or overwritten
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2300)
- WinRAR.exe (PID: 3032)
The process checks LSA protection
- CamStudioSetup.tmp (PID: 3496)
- CamStudioSetup.tmp (PID: 3468)
- explorer.exe (PID: 2032)
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
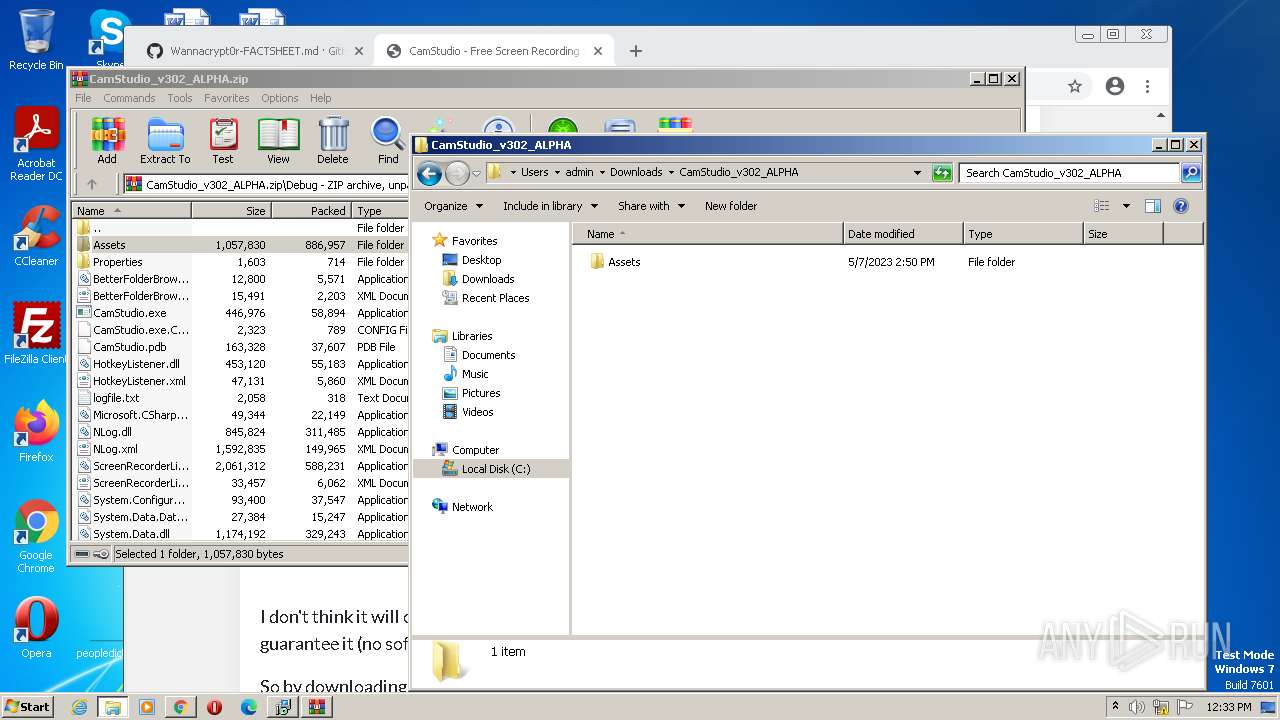
Creates files in the program directory
- CamStudioSetup.tmp (PID: 3468)
Application was dropped or rewritten from another process
- CamStudioSetup.tmp (PID: 3468)
- CamStudioSetup.tmp (PID: 3496)
Reads the machine GUID from the registry
- CamStudio.exe (PID: 3240)
- Recorder.exe (PID: 3304)
Loads dropped or rewritten executable
- CamStudio.exe (PID: 3240)
Checks proxy server information
- Recorder.exe (PID: 3304)
Creates files or folders in the user directory
- Recorder.exe (PID: 3304)
- Recorder.exe (PID: 1232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
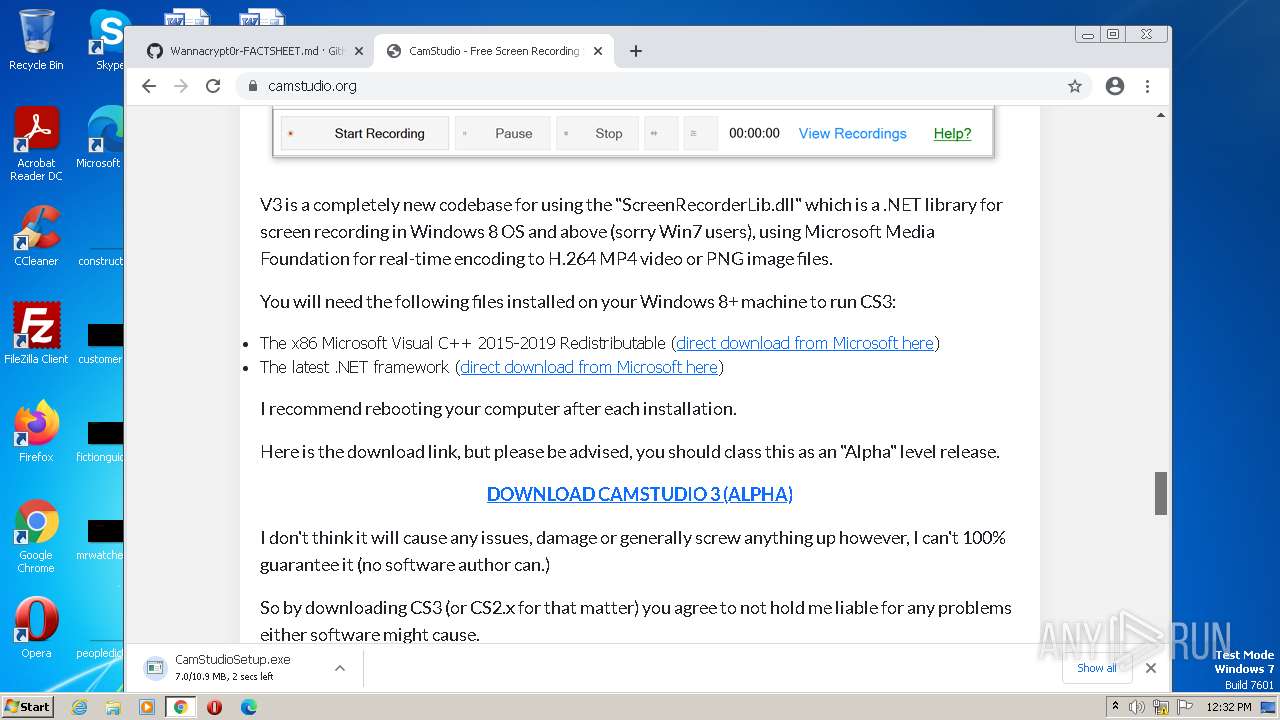
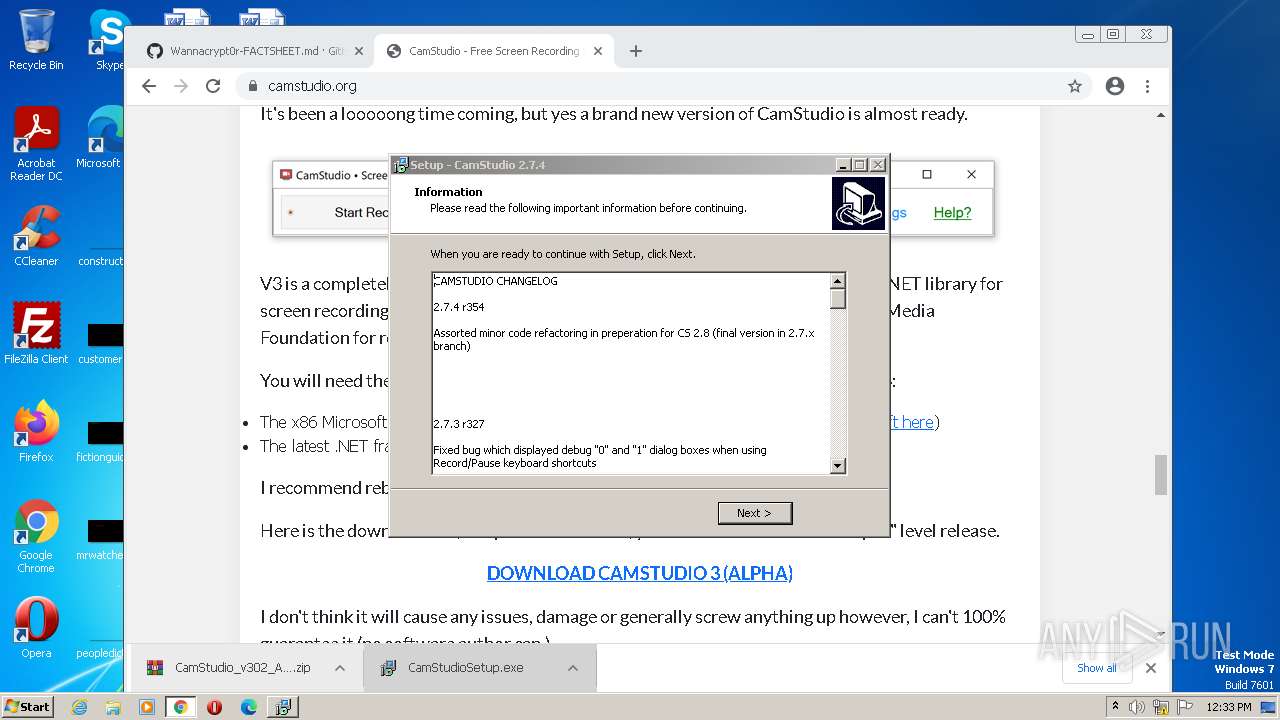
| ProductVersion: | 2.7.4 |
|---|---|
| ProductName: | CamStudio |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | CamStudio Setup |
| CompanyName: | CamStudio Open Source |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0xaad0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 17920 |
| CodeSize: | 41984 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | CamStudio Open Source |
| FileDescription: | CamStudio Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | CamStudio |
| ProductVersion: | 2.7.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A208 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60167 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77135 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x00000920 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.5833 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
146
Monitored processes
95
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3376 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\CamStudio 2.7\Recorder.exe" | C:\Program Files\CamStudio 2.7\Recorder.exe | — | CamStudioSetup.tmp | |||||||||||
User: admin Company: CamStudio Group Integrity Level: MEDIUM Description: CamStudio Recorder Exit code: 3221225547 Version: 3.1.0.0 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,8844535581348292442,7837956099069188402,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1364 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
55 975
Read events
55 508
Write events
448
Delete events
19
Modification events
| (PID) Process: | (3608) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | delete value | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 09611C1E1E000000 | |||
| (PID) Process: | (3608) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | delete value | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: AD681C1E1E000000 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000040010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1152) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|ScreenX |
Value: 0 | |||
Executable files
62
Suspicious files
604
Text files
451
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-wal | — | |
MD5:— | SHA256:— | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\permissions.sqlite-journal | binary | |
MD5:814A6A99F38A23D080301950E3F7896F | SHA256:806E7DFD19F8E4754B17574ACFF892546FD6A89984238AFA3FAA0BEA5673E71C | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | binary | |
MD5:8393B16499255AE2482DDA119159708F | SHA256:00FA5C6C6AE57C86425D1BAA02BE12AE4E4C328742A3DF994878BFED61150143 | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Crash Reports\InstallTime20230710165010 | text | |
MD5:1675186BEF9E7F65C05F9EAD59DB6801 | SHA256:913BD25D5405B3FD82C3B595660EA4F6F757500D8F7C5B80D467146DED48B0C9 | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\compatibility.ini | text | |
MD5:5A14BC3397EA072906B63D69FC704FEA | SHA256:03F45724EA1FE89E753AA76B40DE9078BFC9160AA1065ED9D4D98DA04B7FB3E7 | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:ABB63144DE821246C21B8C8B0855D096 | SHA256:4DA38BE0F4EE3843A8440331FFEBBA0ABF05087E73056C6E151684521BBBA323 | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\extensions.json | text | |
MD5:2C513EB8293B349968163678524E7C53 | SHA256:B2FB2366C66615C773D968806EF8C90A380353382AD08CB8BCB72D88E92345BD | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage.sqlite-journal | binary | |
MD5:8F1F8B92AA14D78294E9AC744C695DF2 | SHA256:6E32C4E33994BA71F3CF5DC46D3CEA56470500DF7B8775D7F0C5515ACC28A3F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
249
DNS requests
218
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1152 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1152 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
2300 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | binary | 242 Kb | whitelisted |
1152 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1152 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
2300 | chrome.exe | GET | 302 | 209.59.174.236:80 | http://camstudio.org/ | US | html | 206 b | unknown |
1152 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
1152 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
1152 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
1152 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1152 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1152 | firefox.exe | 142.250.181.234:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
1152 | firefox.exe | 184.24.77.48:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
1152 | firefox.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
1152 | firefox.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1152 | firefox.exe | 209.59.174.236:80 | camstudio.org | LIQUIDWEB | US | unknown |
1152 | firefox.exe | 209.59.174.236:443 | camstudio.org | LIQUIDWEB | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| shared |
normandy.cdn.mozilla.net |
| whitelisted |
normandy-cdn.services.mozilla.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
r3.o.lencr.org |
| shared |
a1887.dscq.akamai.net |
| whitelisted |