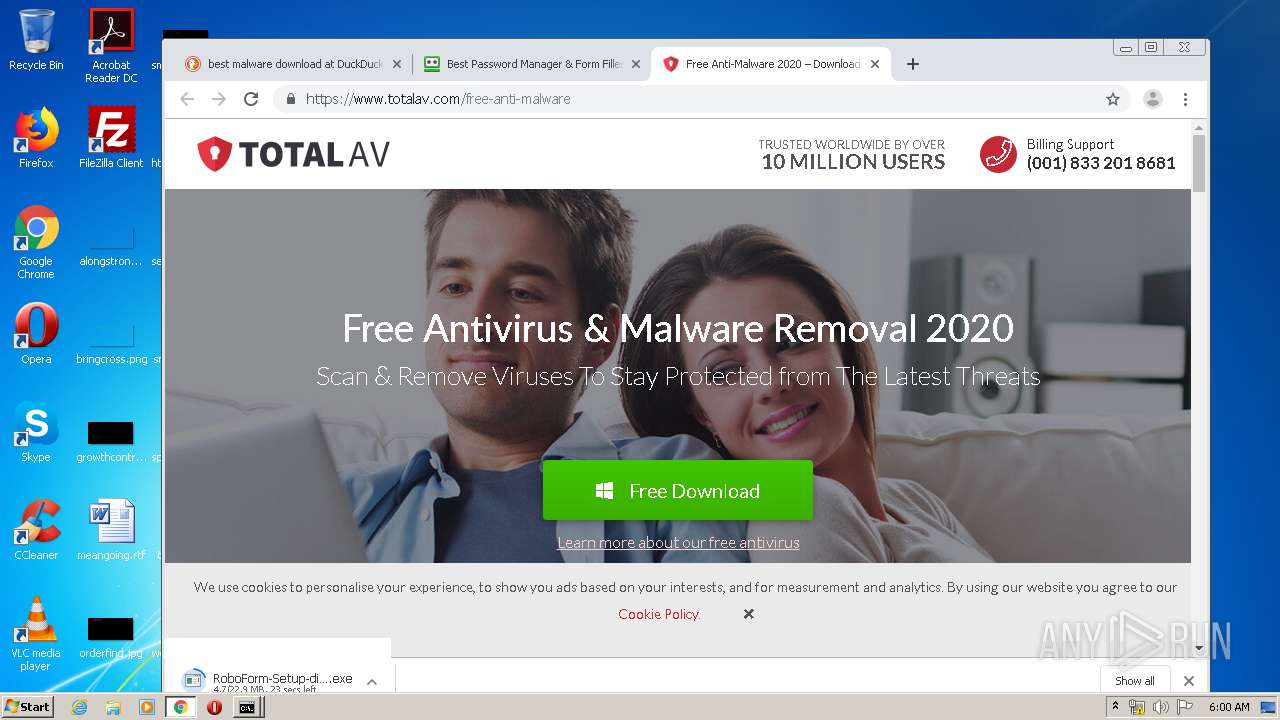
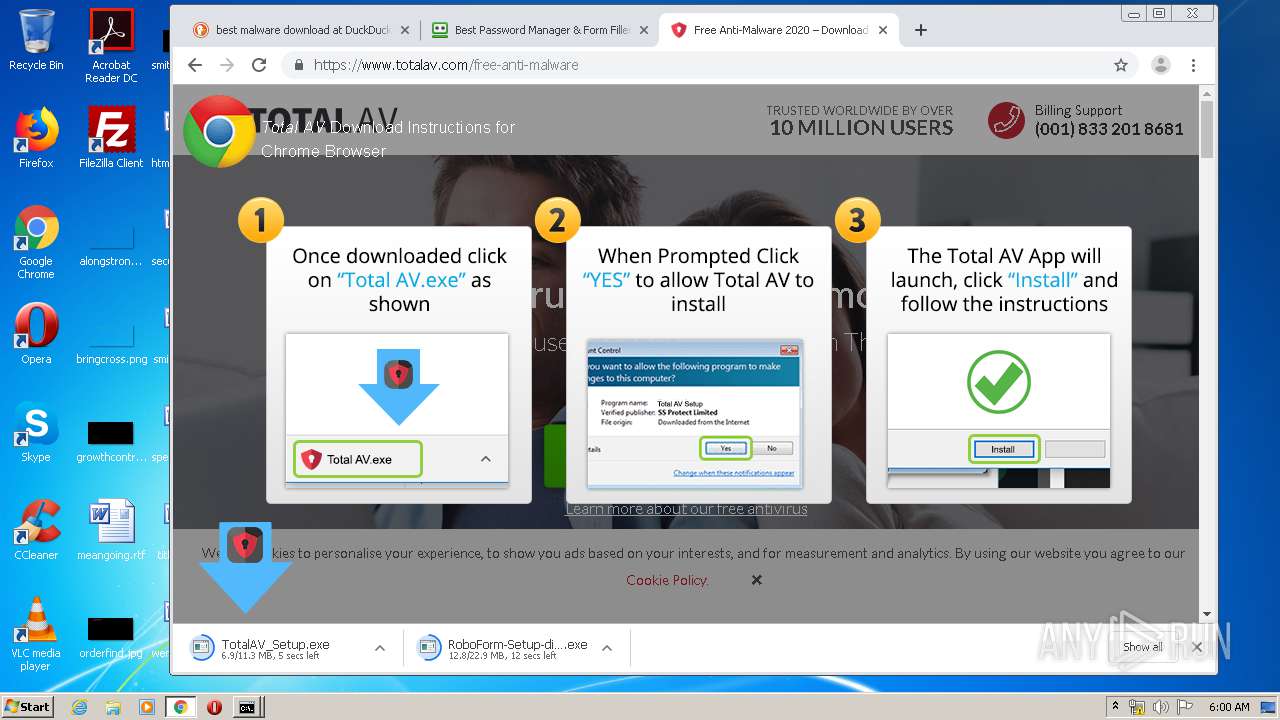
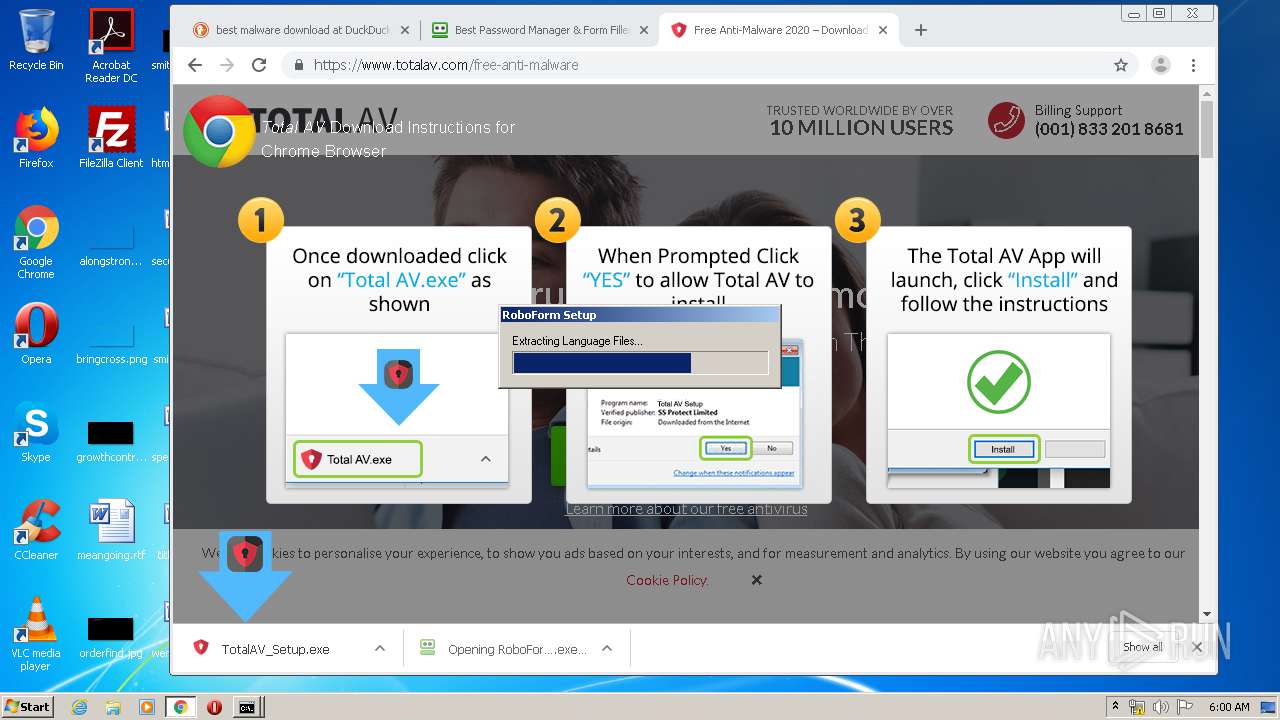
| File name: | http://old.siparerrrnoho.com/ |
| Full analysis: | https://app.any.run/tasks/c29f6657-3f8d-44b7-9959-66a6ea064592 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 04:55:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | C94D2910C0BF7759A0E71455D461E2F3 |
| SHA1: | DD755A5C2F8D85C53AEC3A3C8152B1B88EC70861 |
| SHA256: | 3FB941F65F4B62536B762DC54CD017C2B36649C46626038036F12F31EFBBBCE8 |
| SSDEEP: | 48:GDTFHT/LWrXgotMH3PiH3TR9sB1g0ZdZvfqRTGU3r:8TFHKgoaHUtuZKRTGUb |
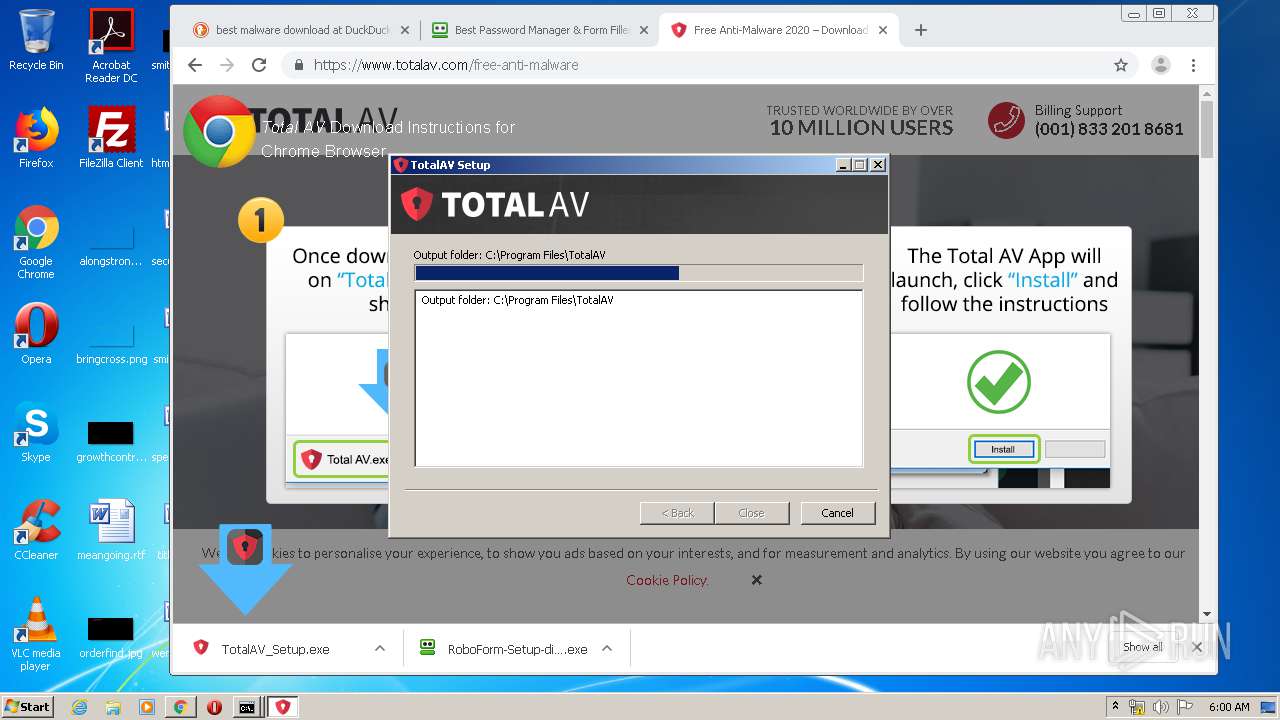
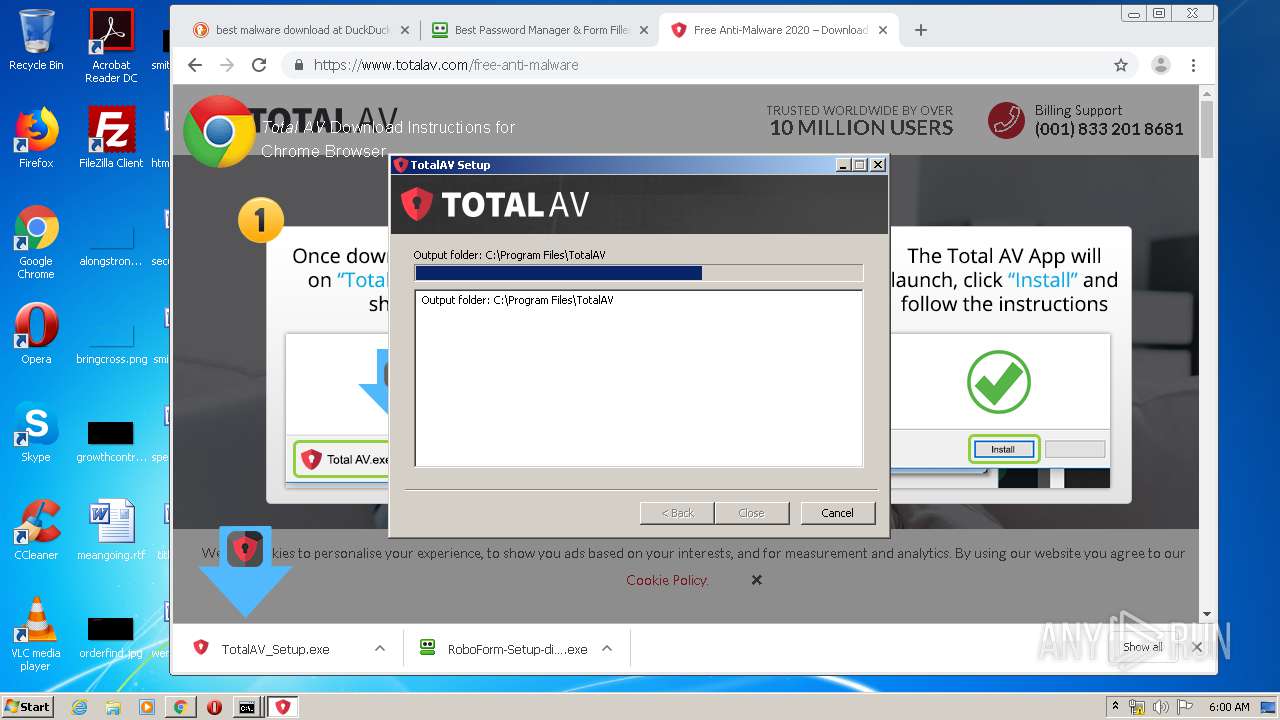
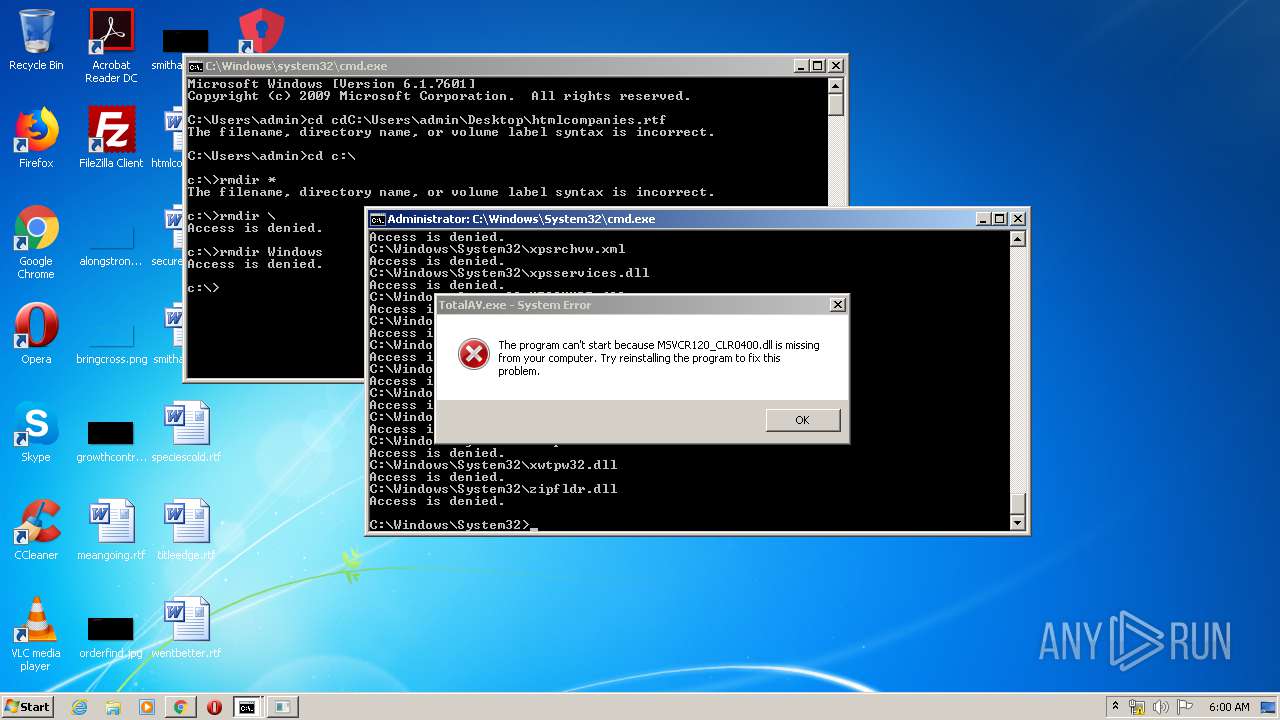
MALICIOUS
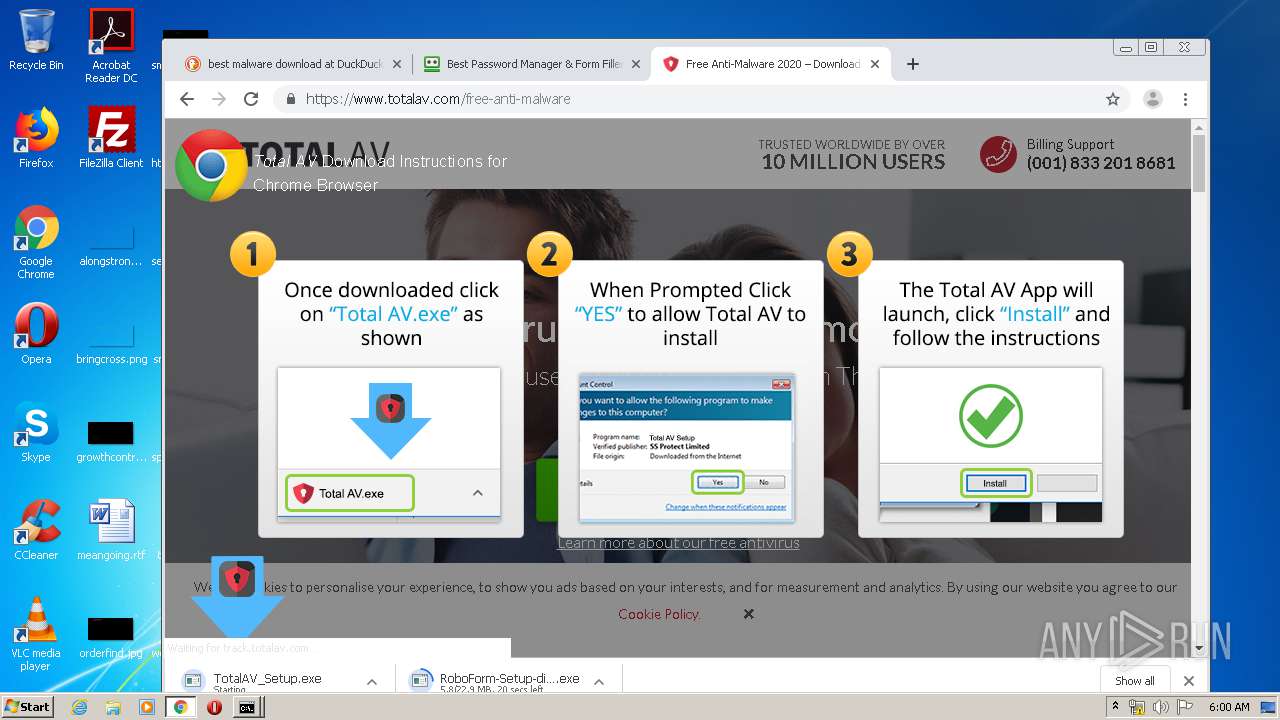
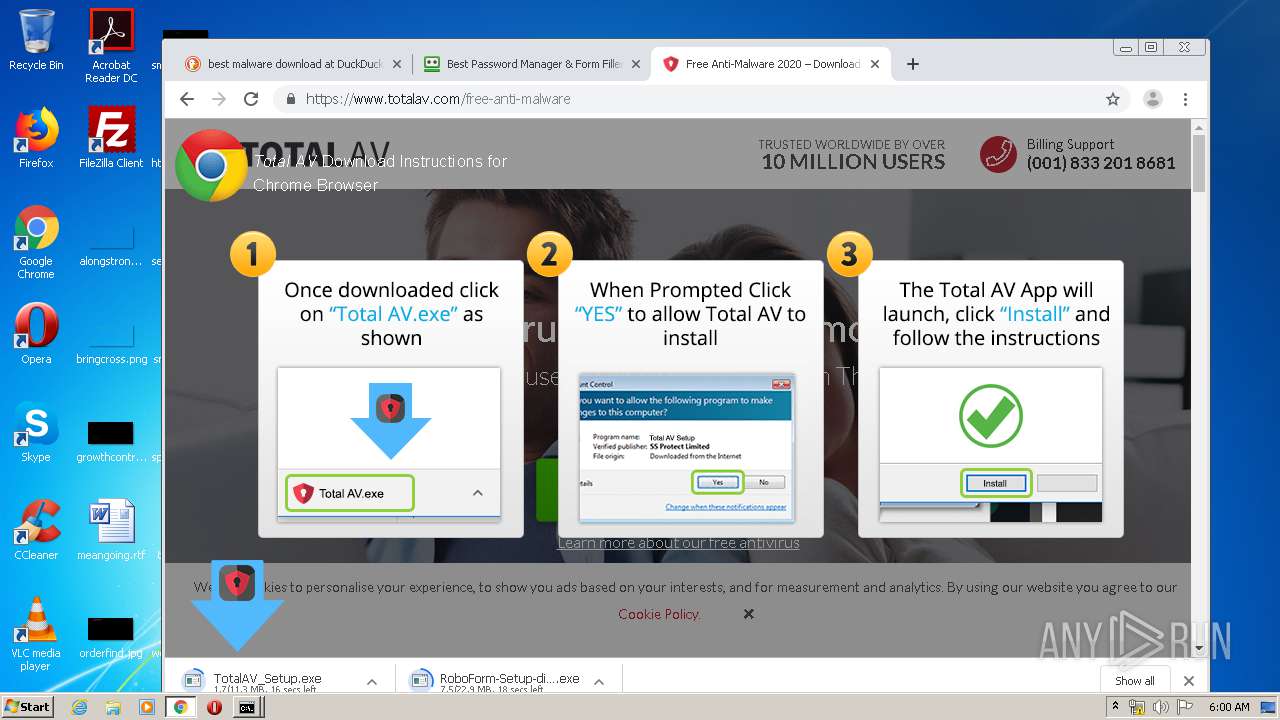
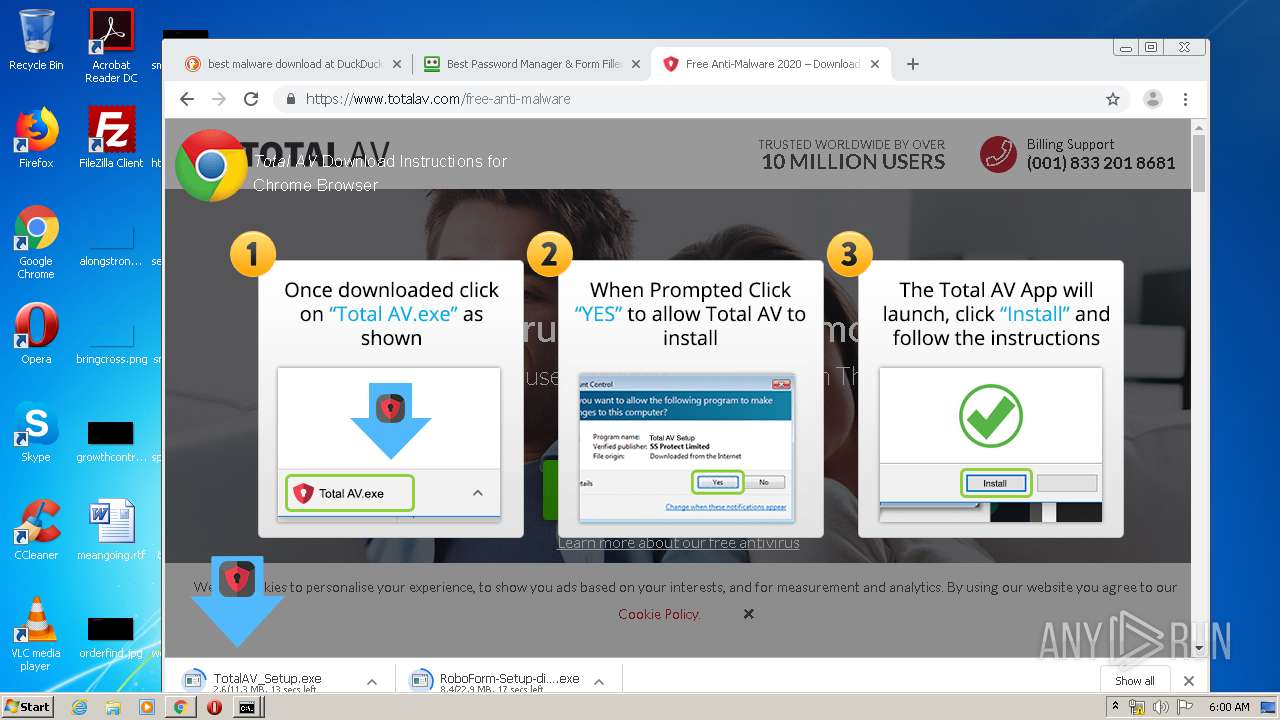
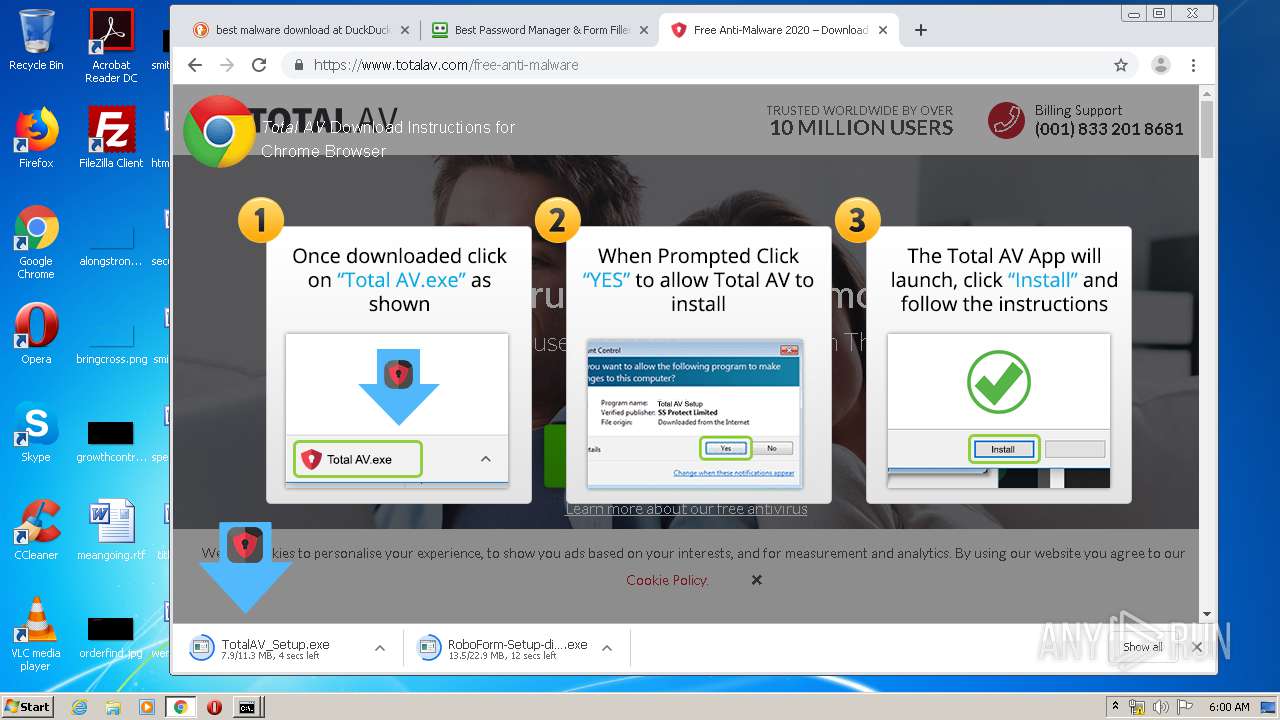
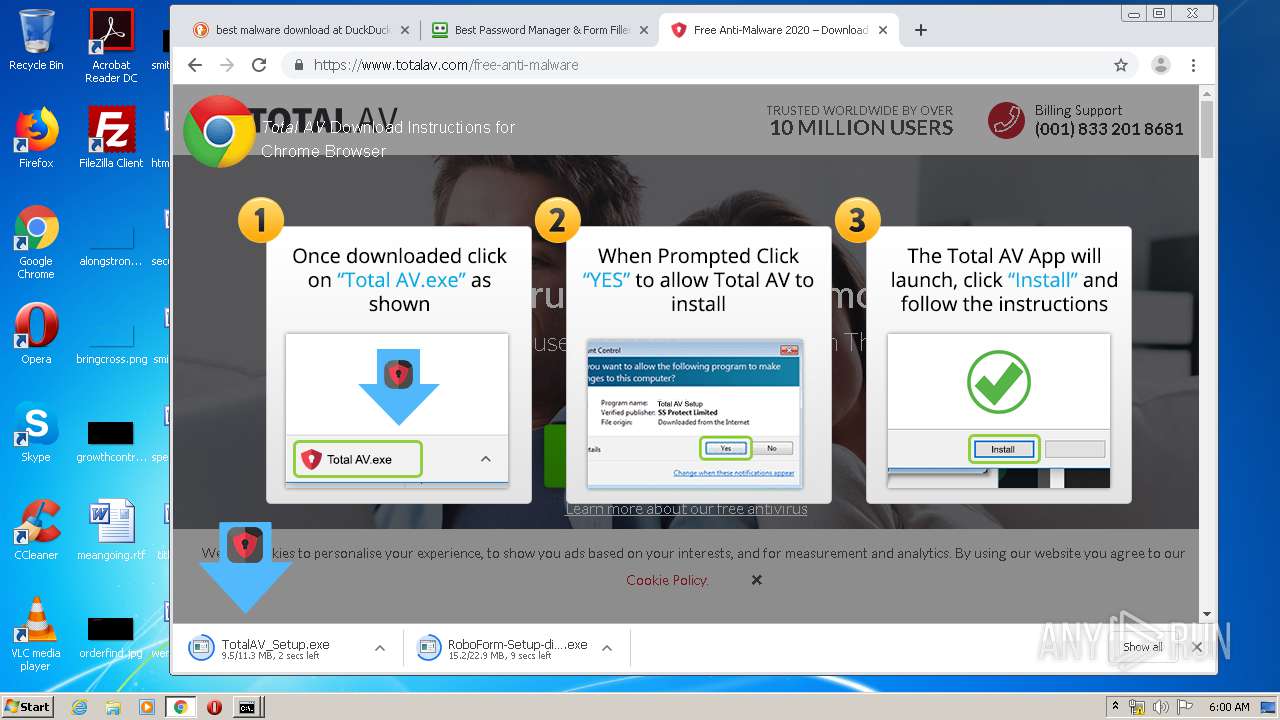
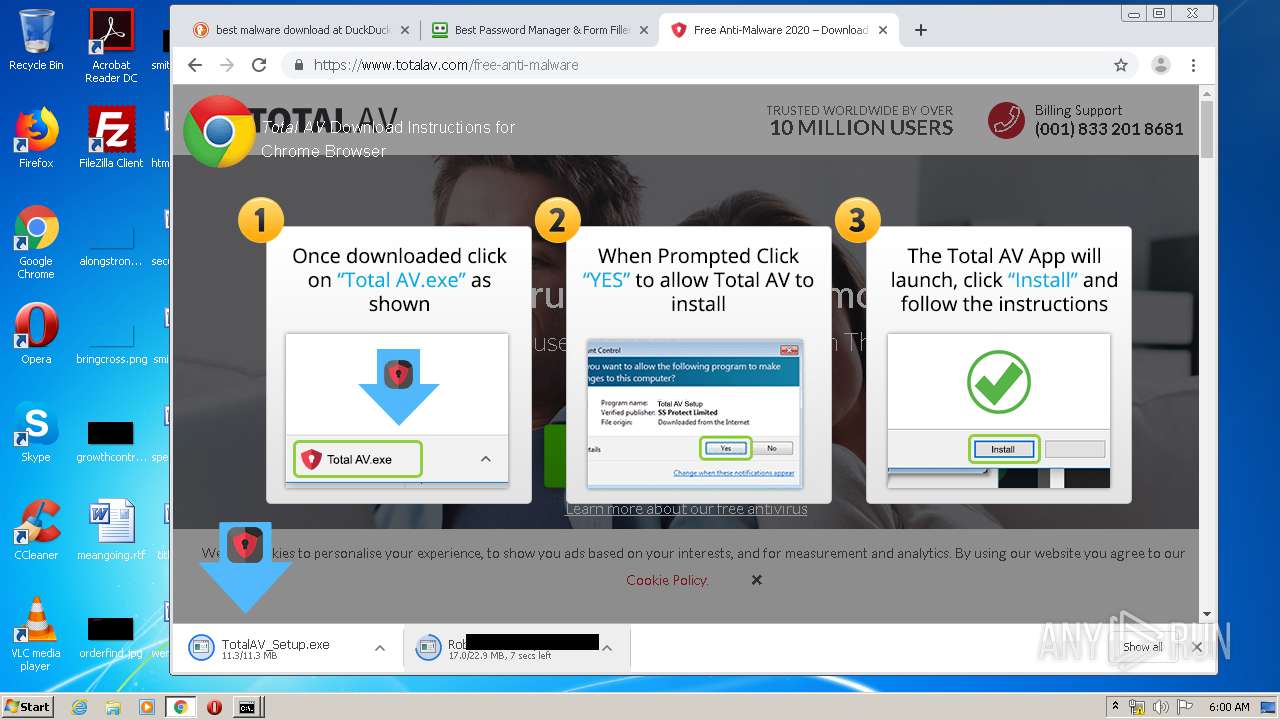
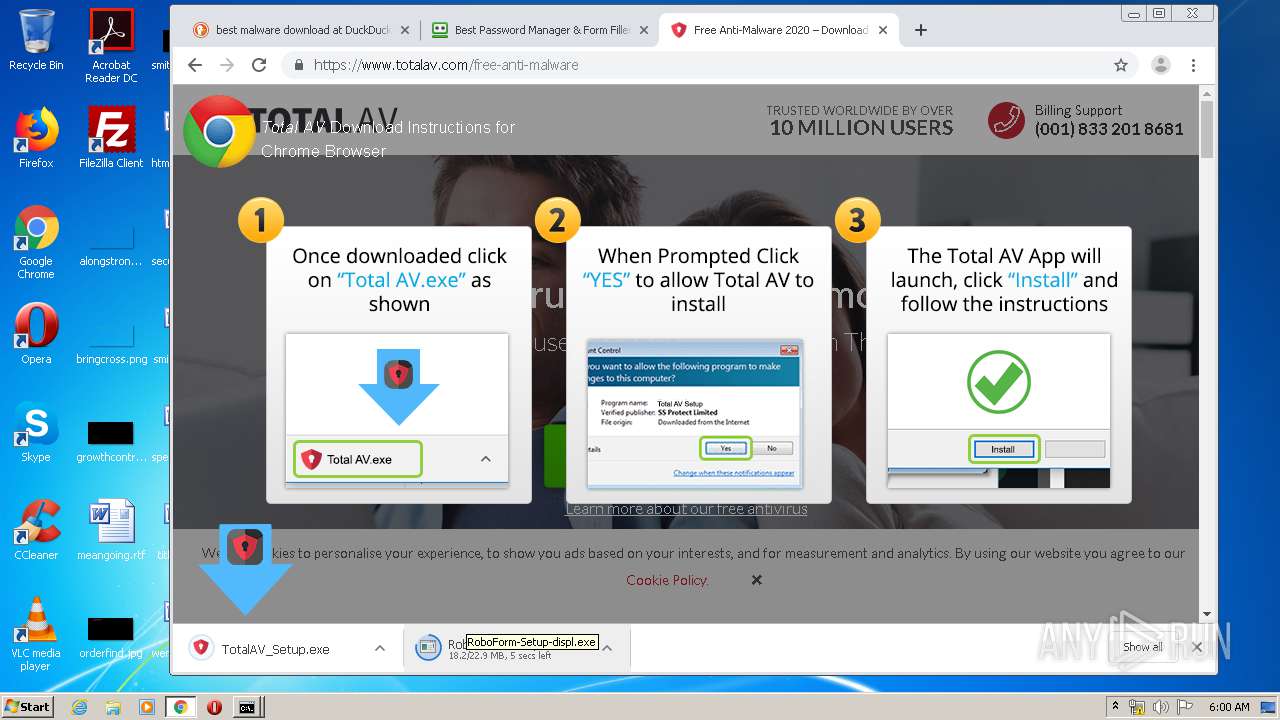
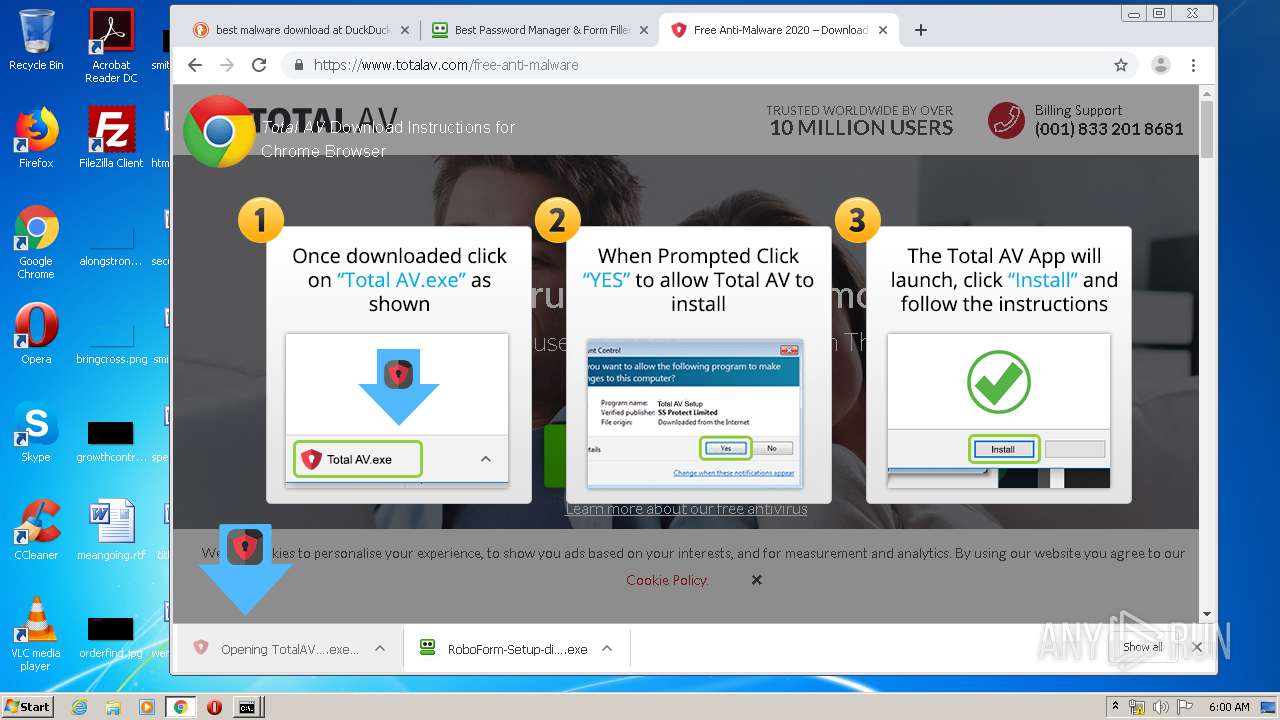
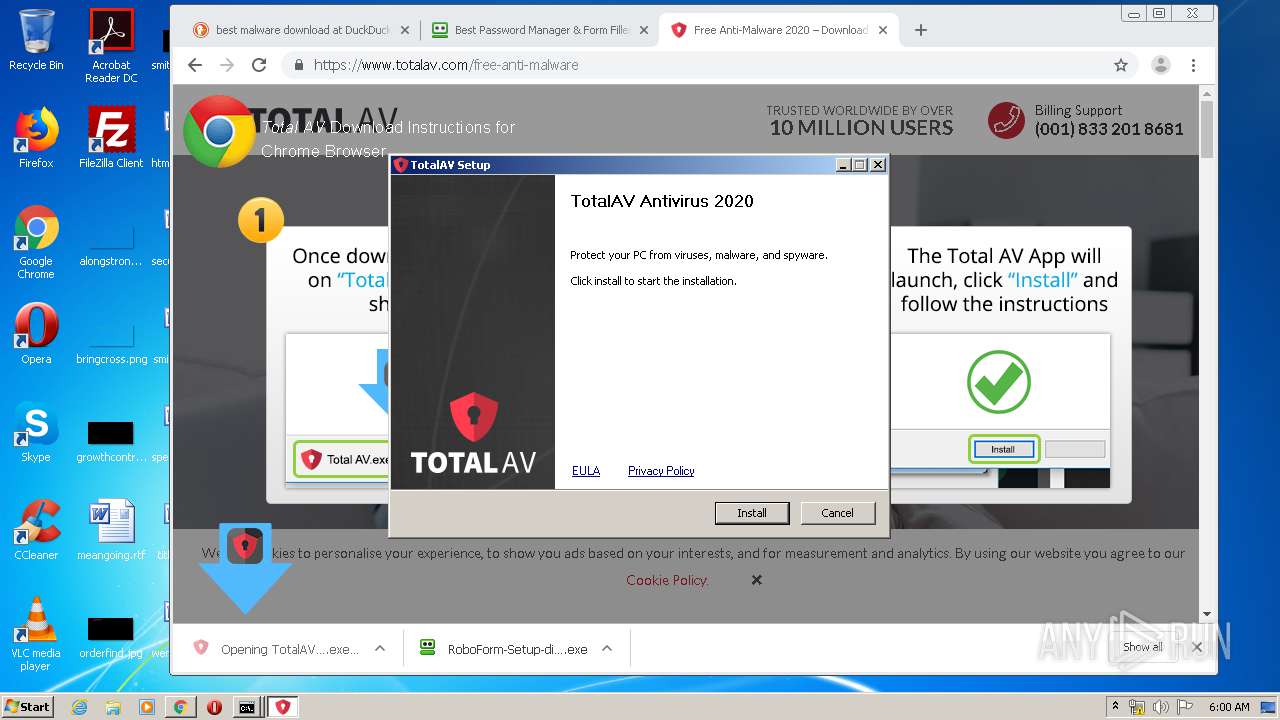
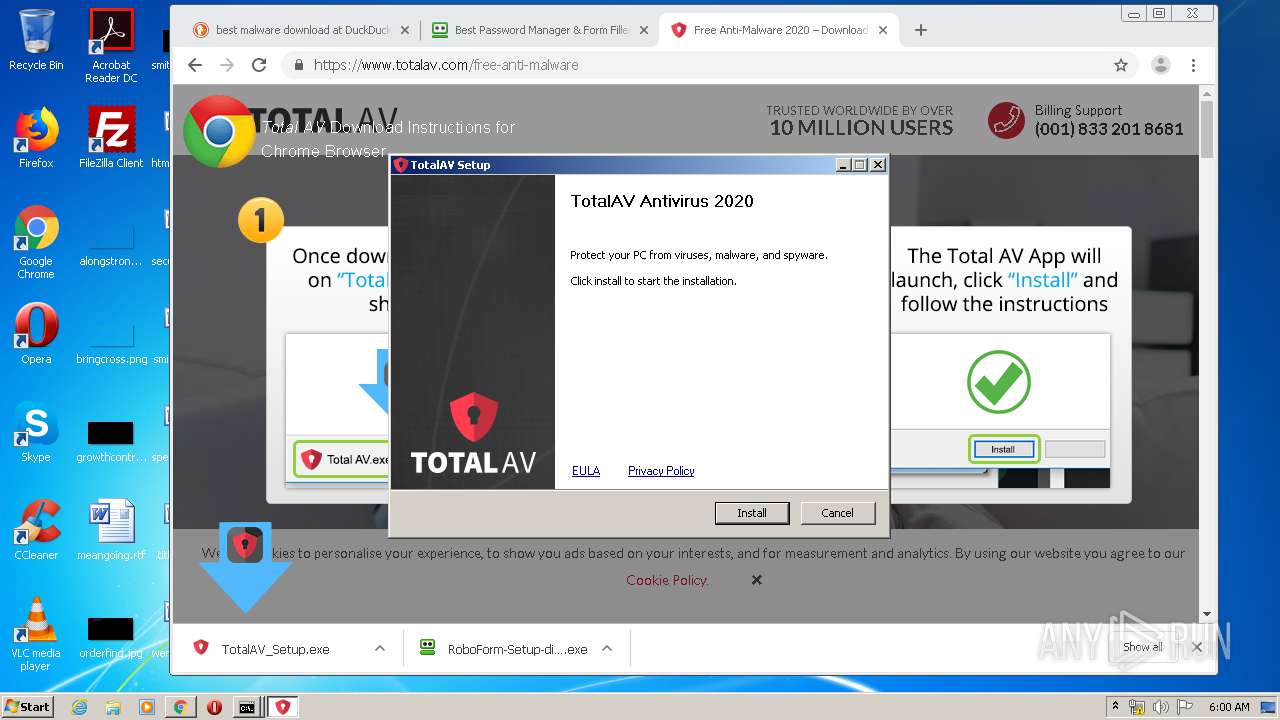
Application was dropped or rewritten from another process
- TotalAV_Setup.exe (PID: 1796)
- TotalAV_Setup.exe (PID: 1432)
- ns2271.tmp (PID: 2460)
- ns24D3.tmp (PID: 3548)
- ns286F.tmp (PID: 3996)
- ns267A.tmp (PID: 3212)
- ns2A16.tmp (PID: 3880)
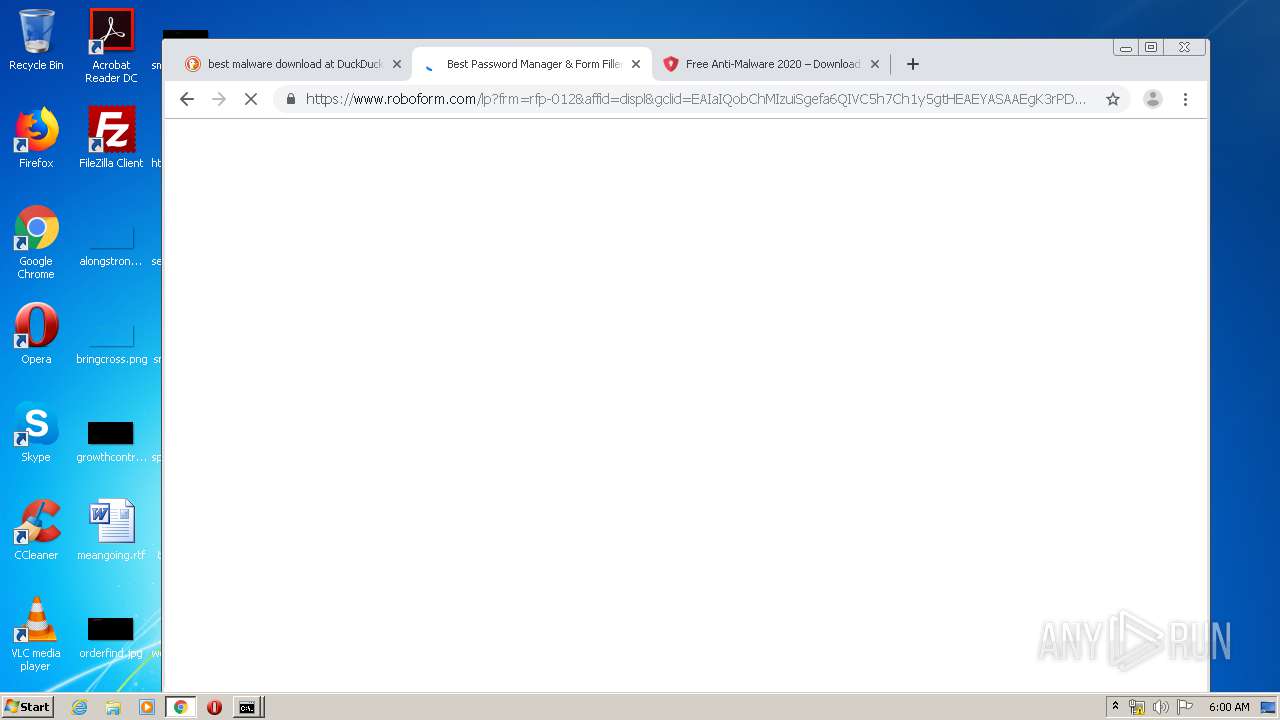
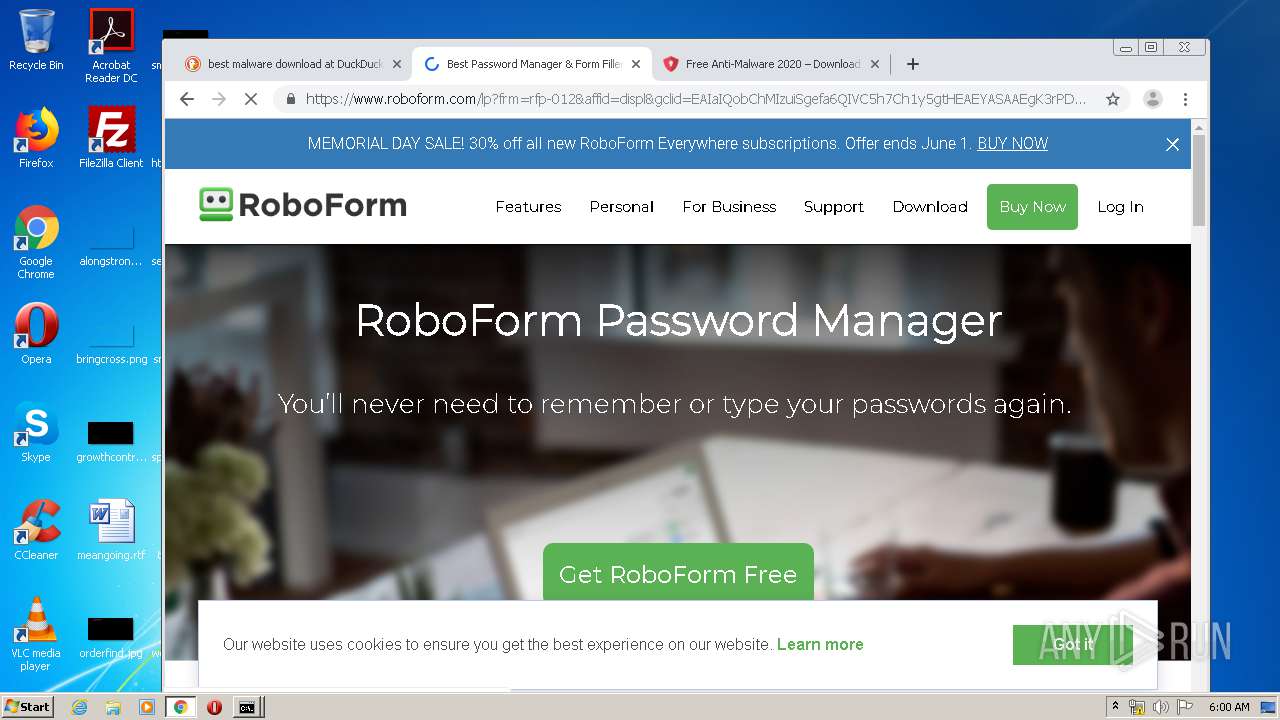
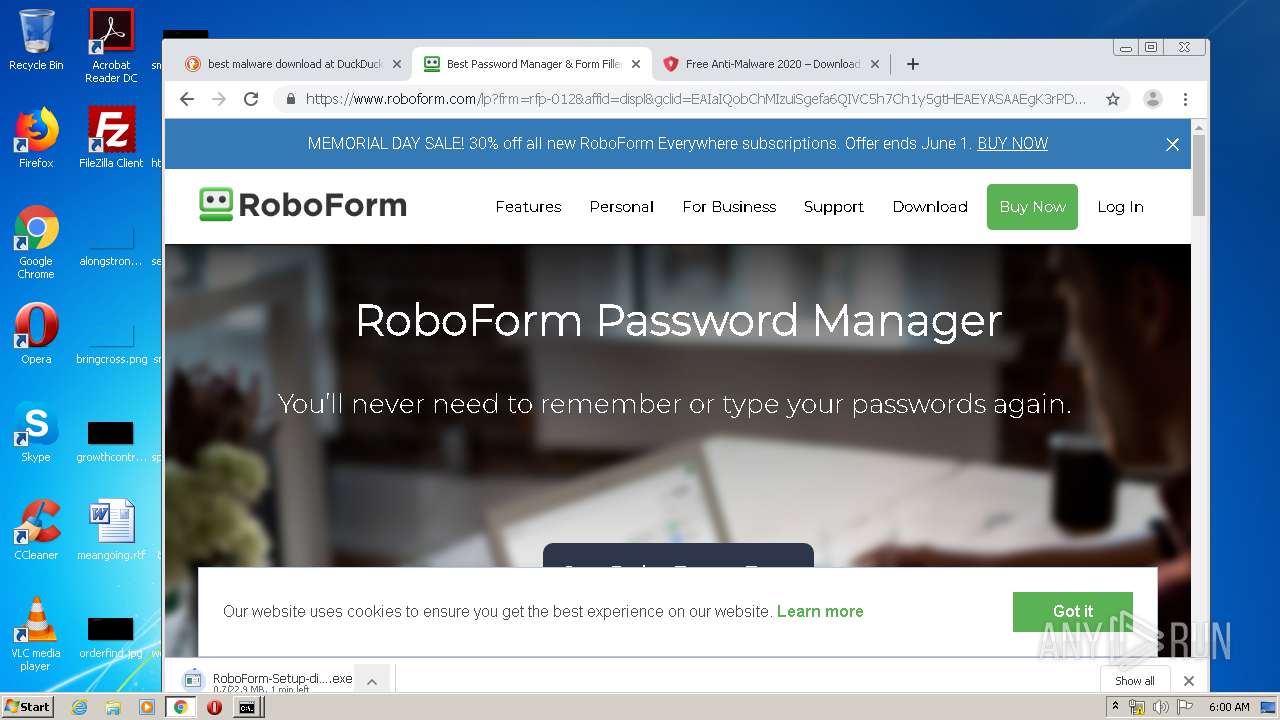
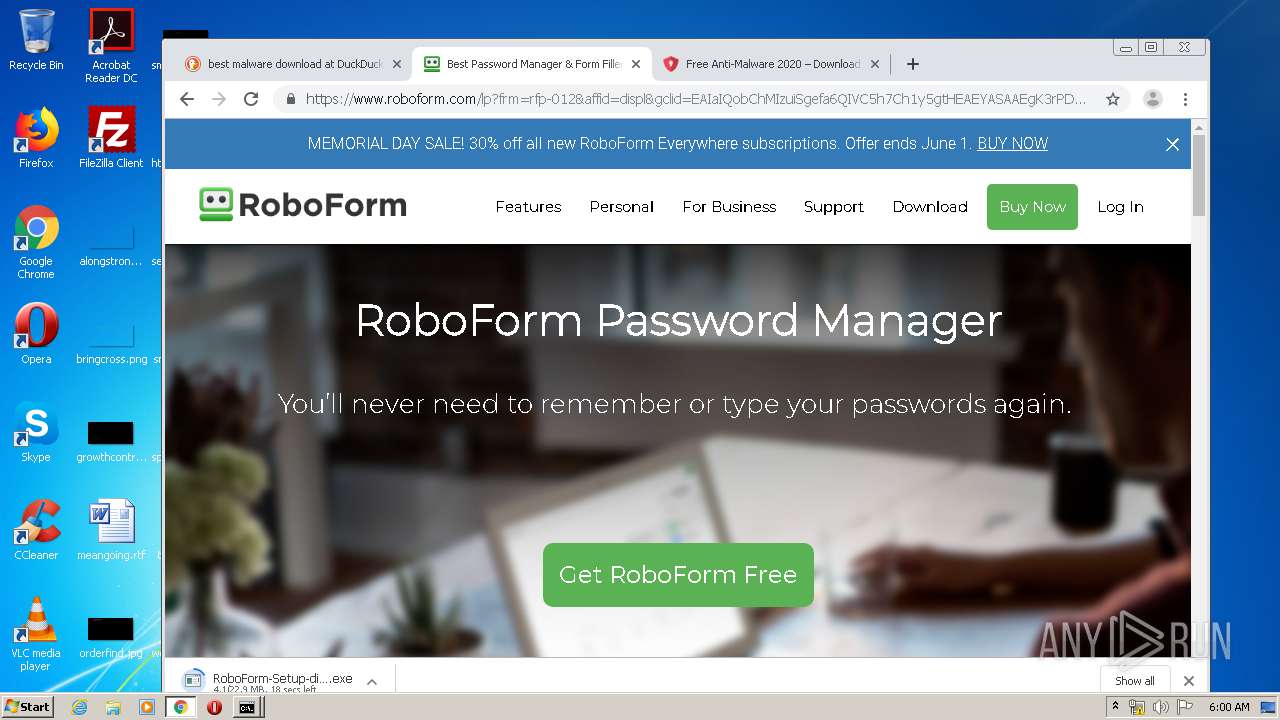
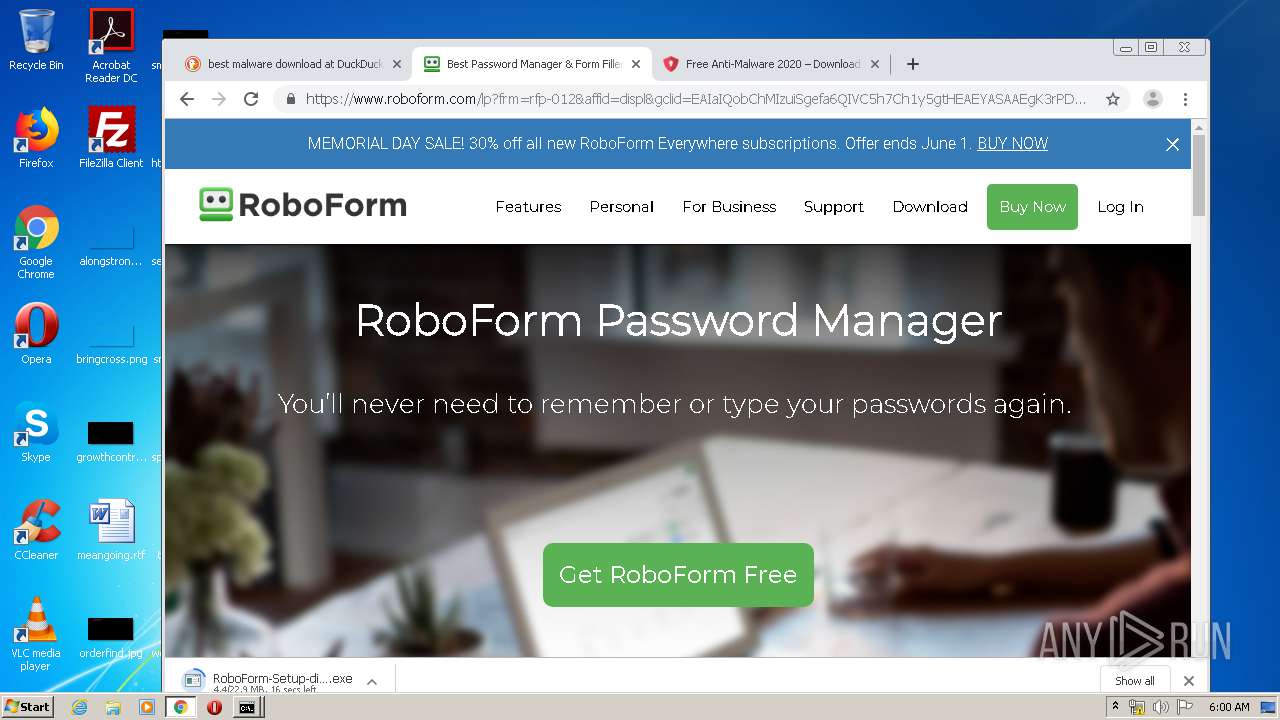
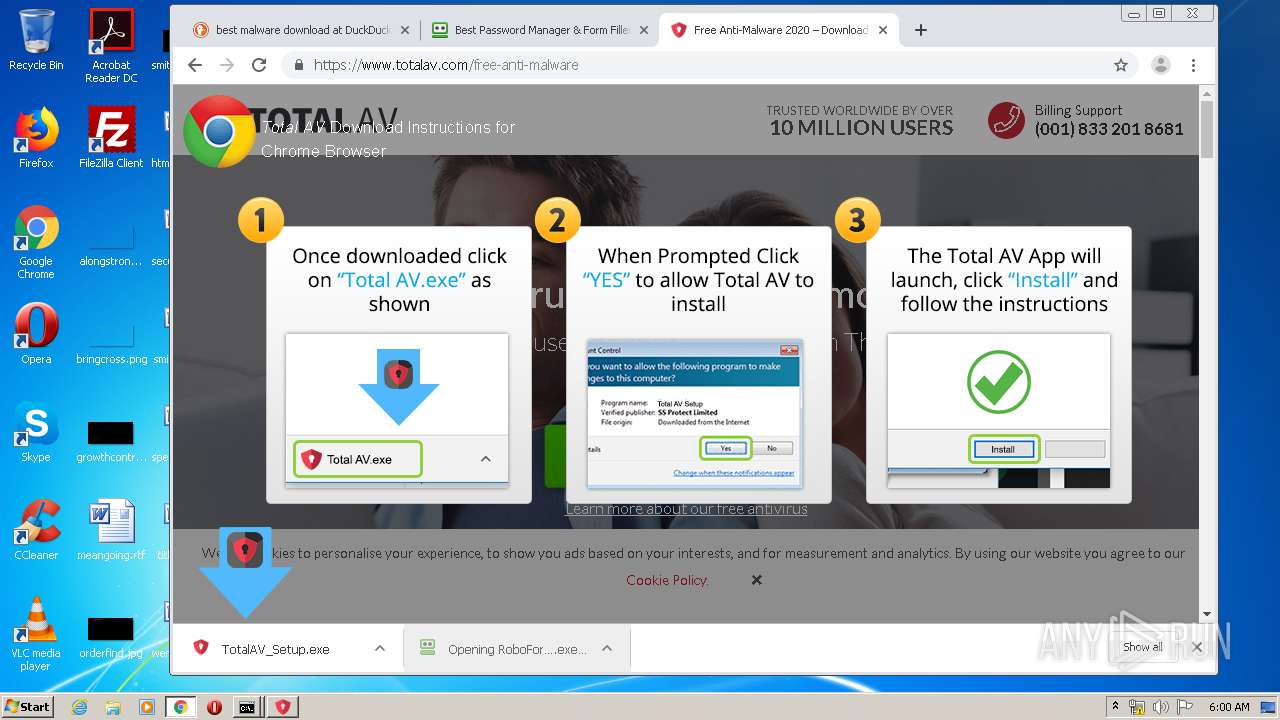
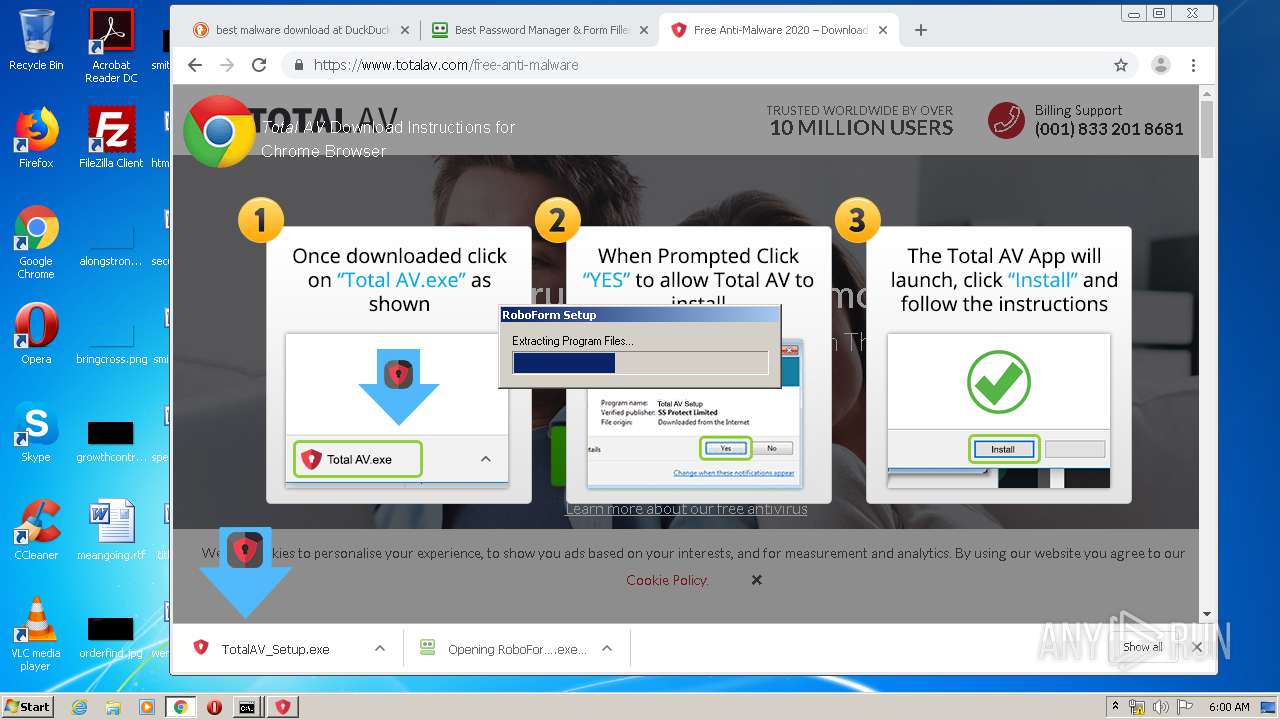
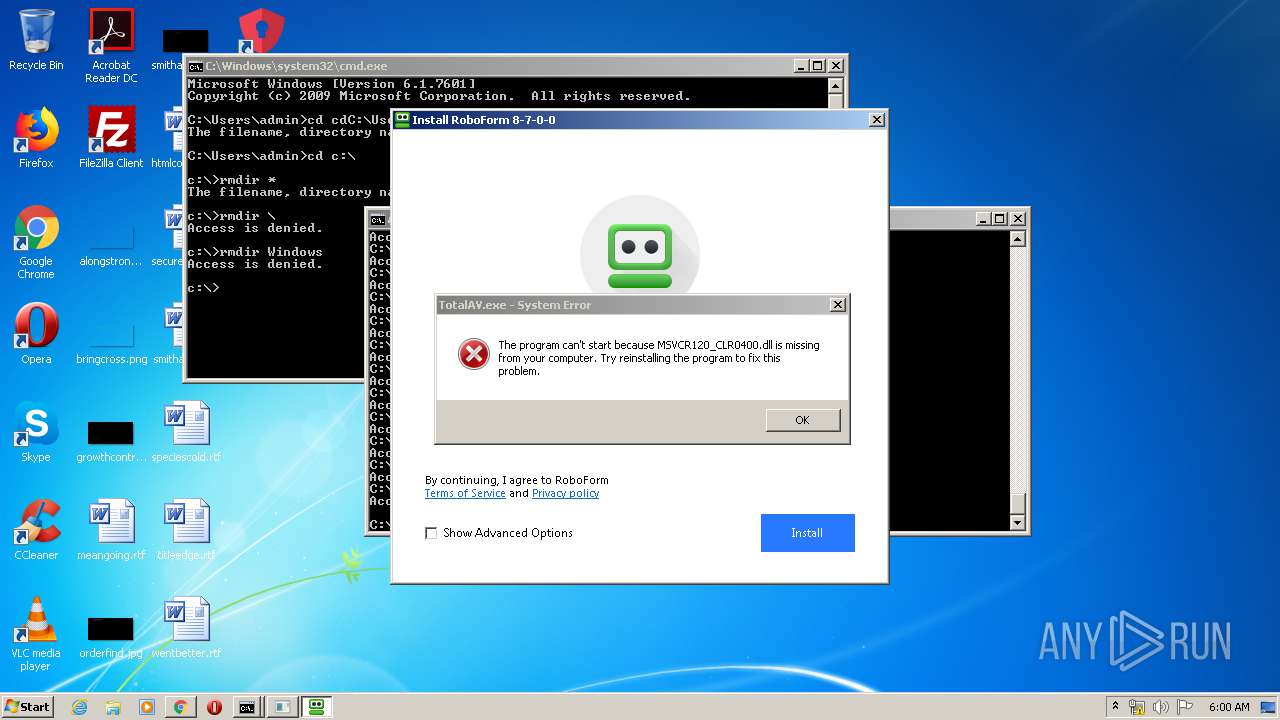
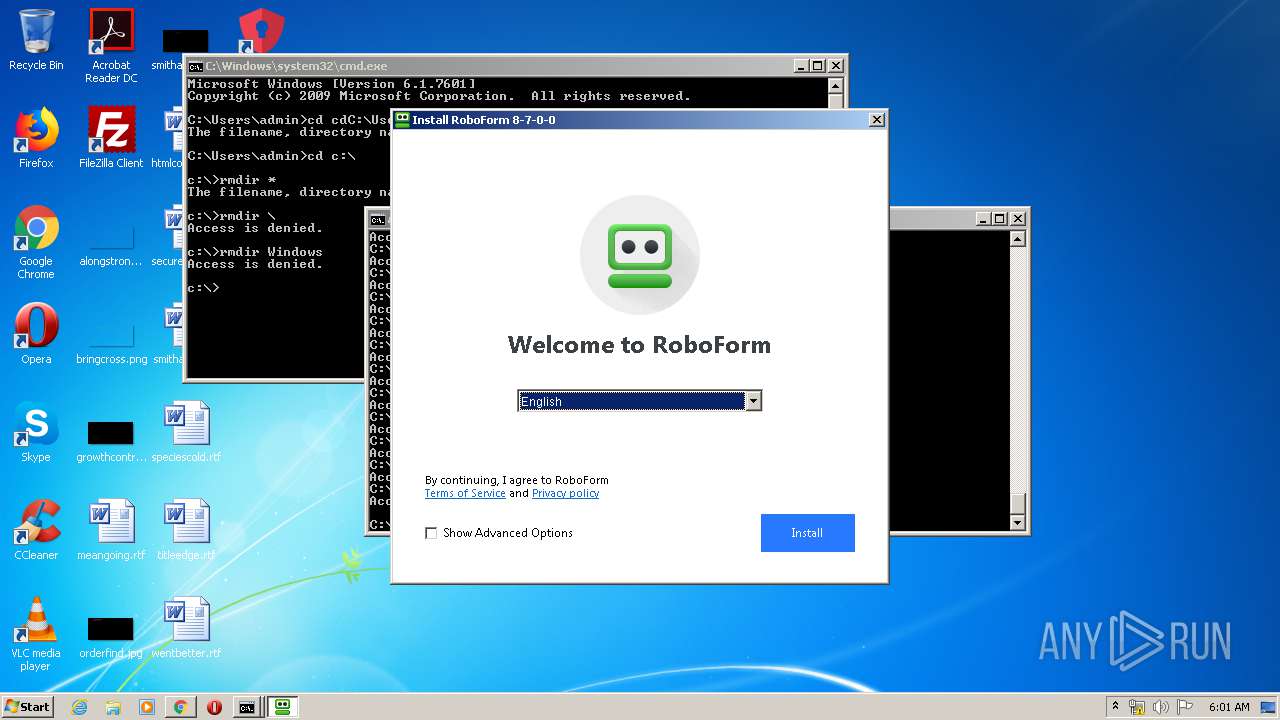
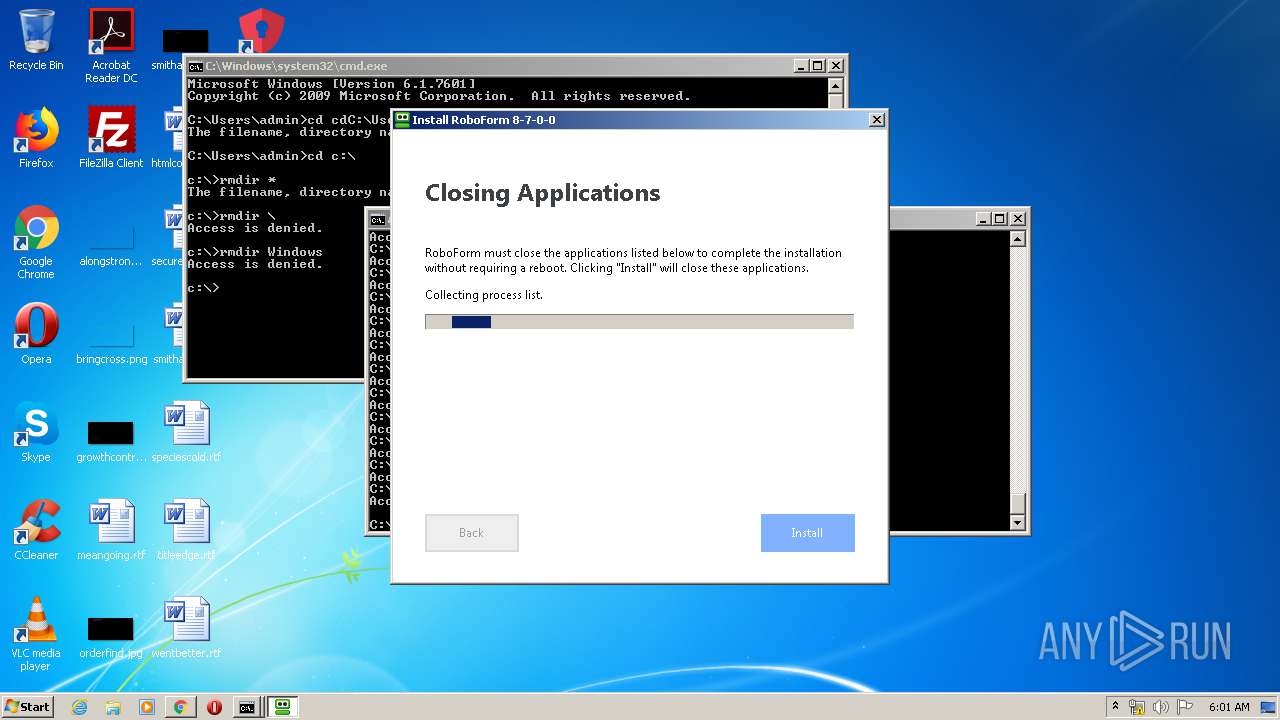
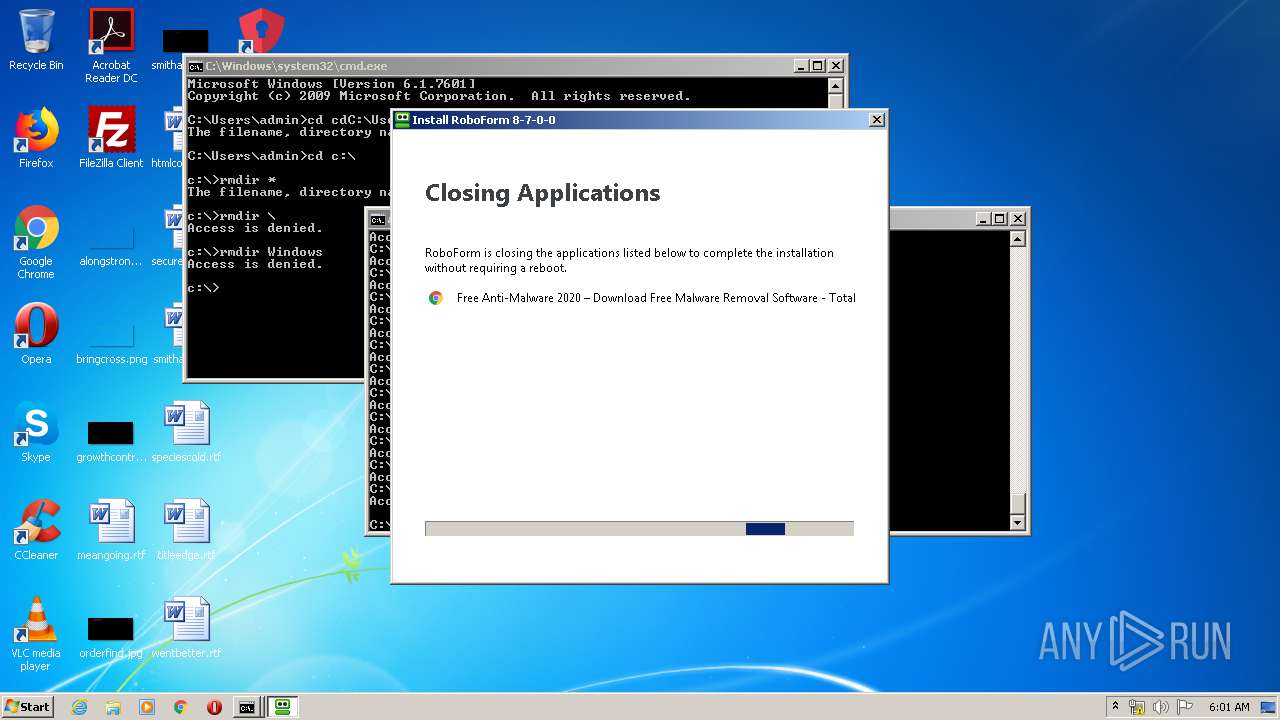
- RoboForm-Setup-displ.exe (PID: 964)
- RoboForm-Setup-displ.exe (PID: 1416)
- ns3726.tmp (PID: 3920)
- SecurityService.exe (PID: 3564)
- rfwipeout.exe (PID: 3412)
- TotalAV.exe (PID: 2304)
Loads dropped or rewritten executable
- TotalAV_Setup.exe (PID: 1796)
SUSPICIOUS
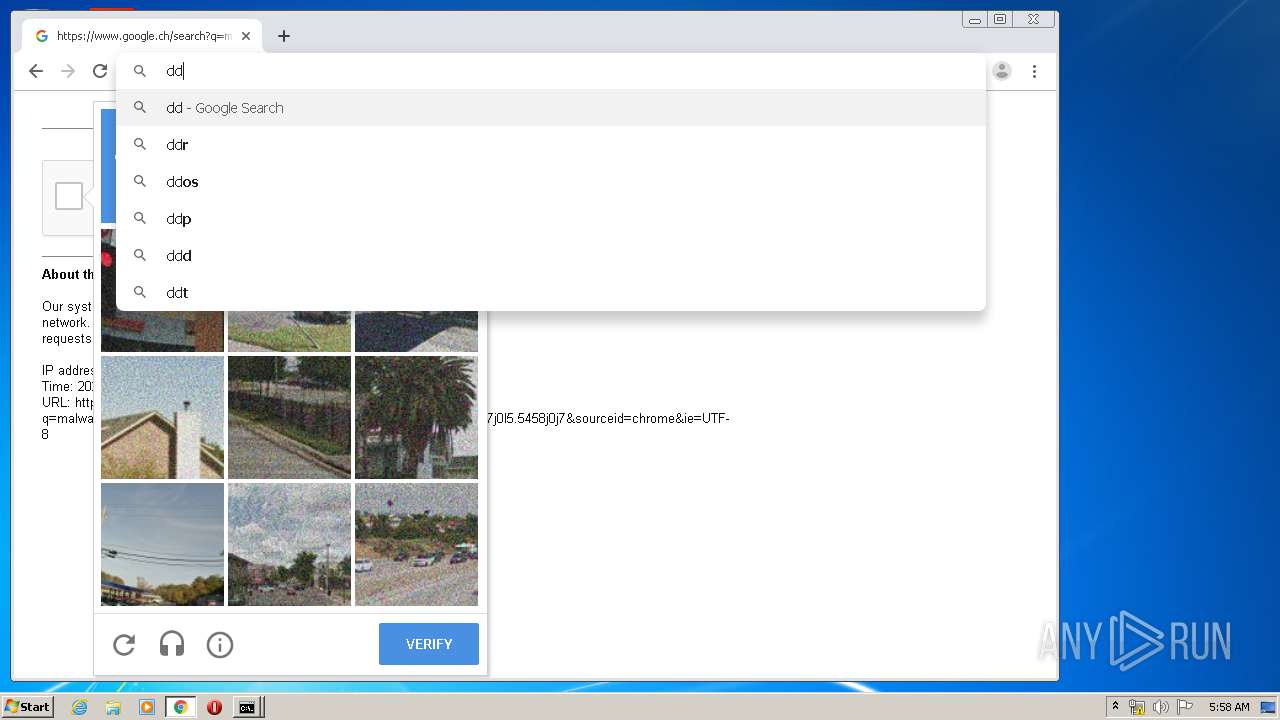
Modifies files in Chrome extension folder
- chrome.exe (PID: 3228)
Executable content was dropped or overwritten
- chrome.exe (PID: 2064)
- TotalAV_Setup.exe (PID: 1796)
- chrome.exe (PID: 3228)
- RoboForm-Setup-displ.exe (PID: 1416)
Starts application with an unusual extension
- TotalAV_Setup.exe (PID: 1796)
Uses TASKKILL.EXE to kill process
- ns286F.tmp (PID: 3996)
- ns24D3.tmp (PID: 3548)
- ns2271.tmp (PID: 2460)
- ns267A.tmp (PID: 3212)
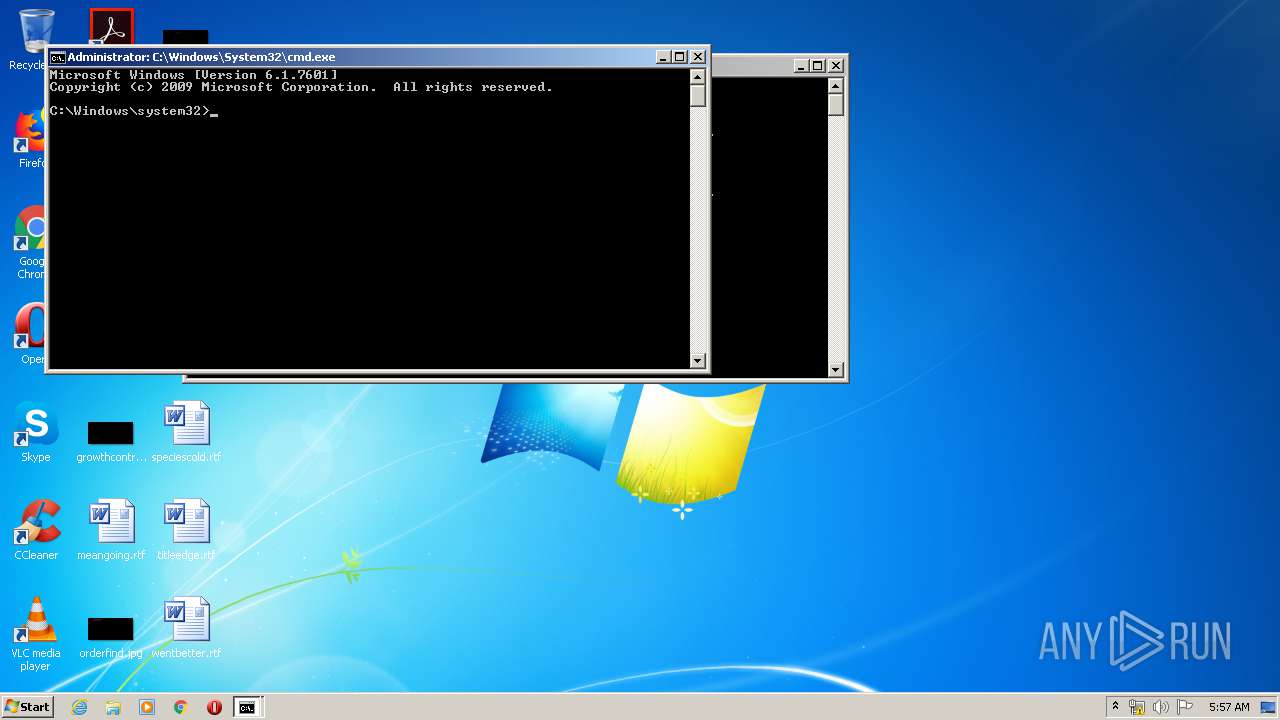
Creates files in the program directory
- TotalAV_Setup.exe (PID: 1796)
- rfwipeout.exe (PID: 3412)
Creates a software uninstall entry
- TotalAV_Setup.exe (PID: 1796)
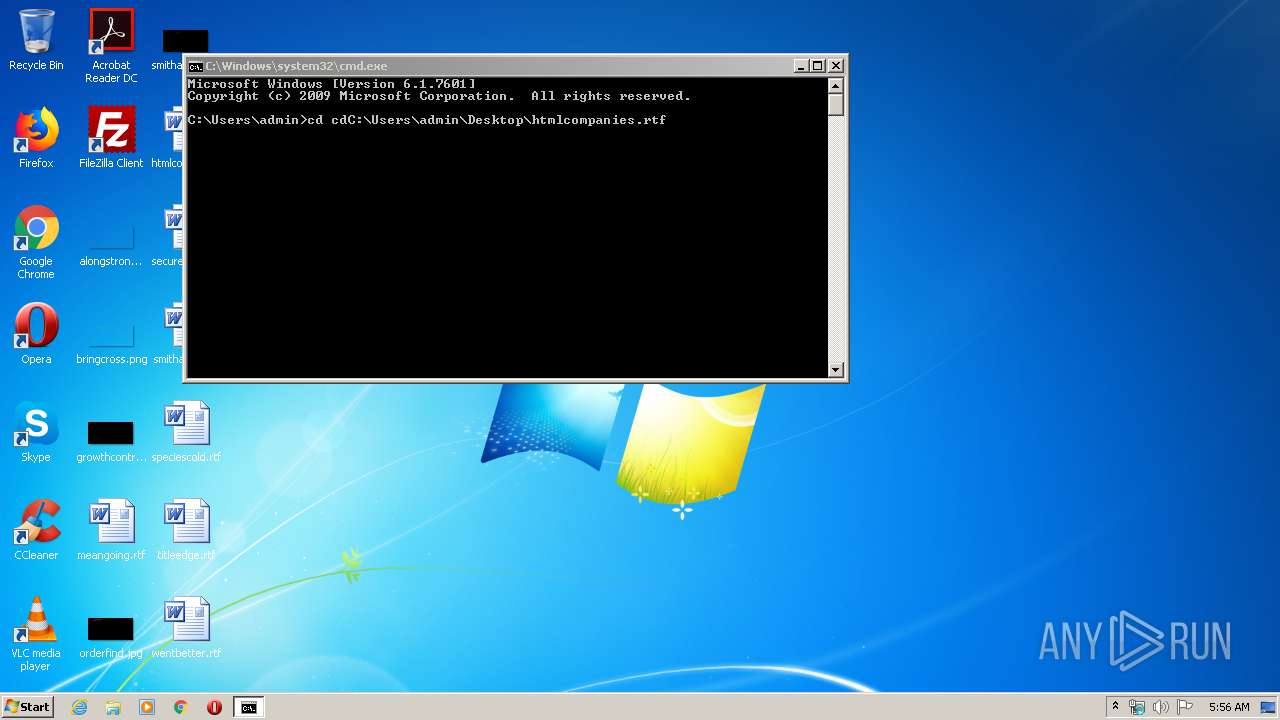
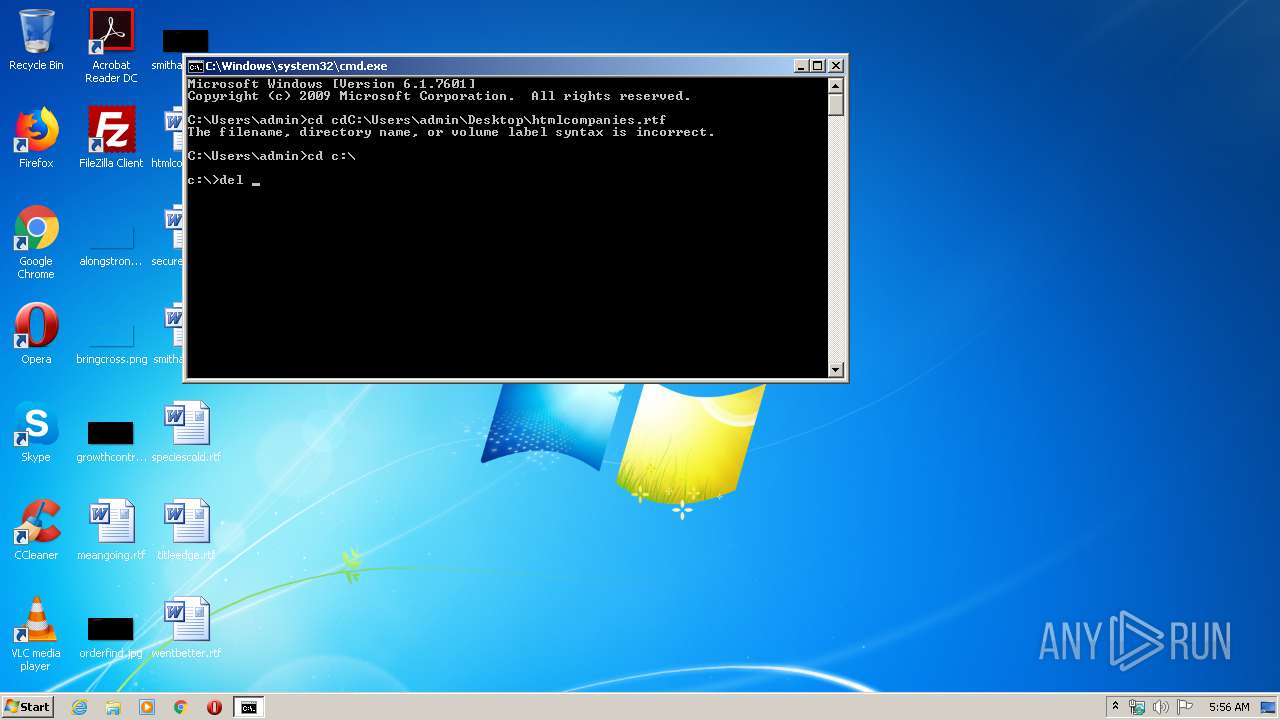
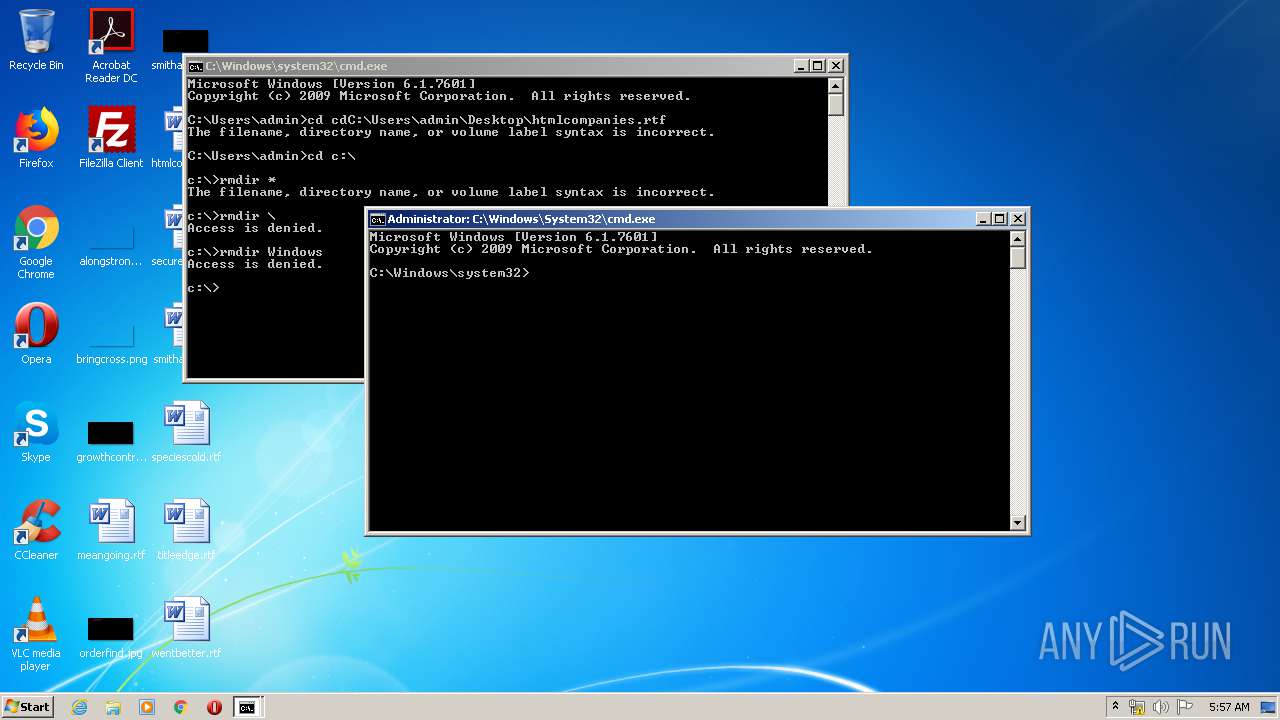
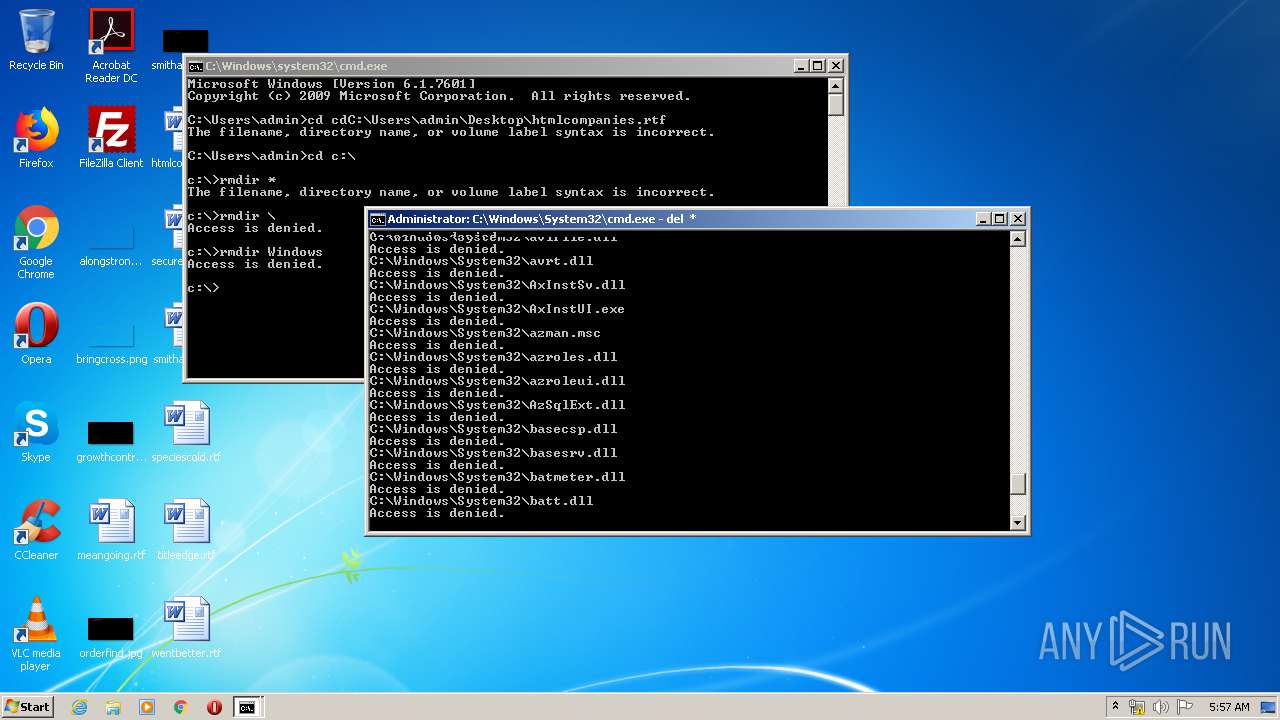
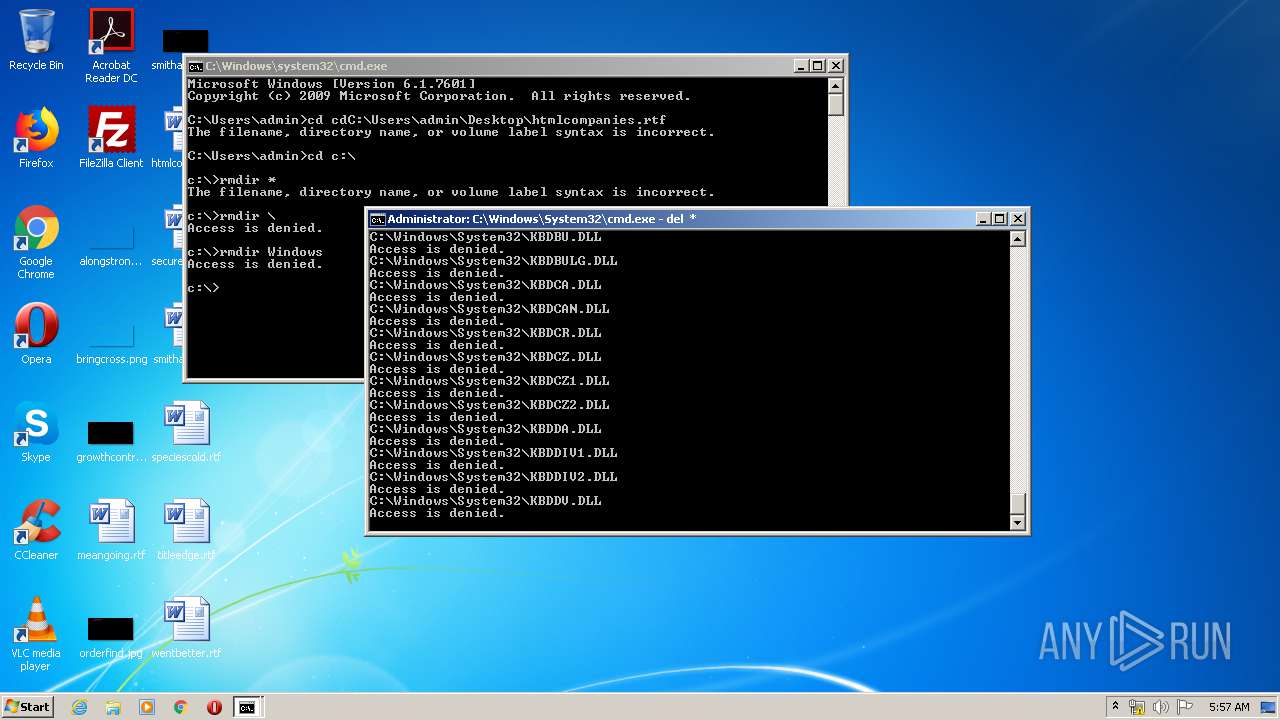
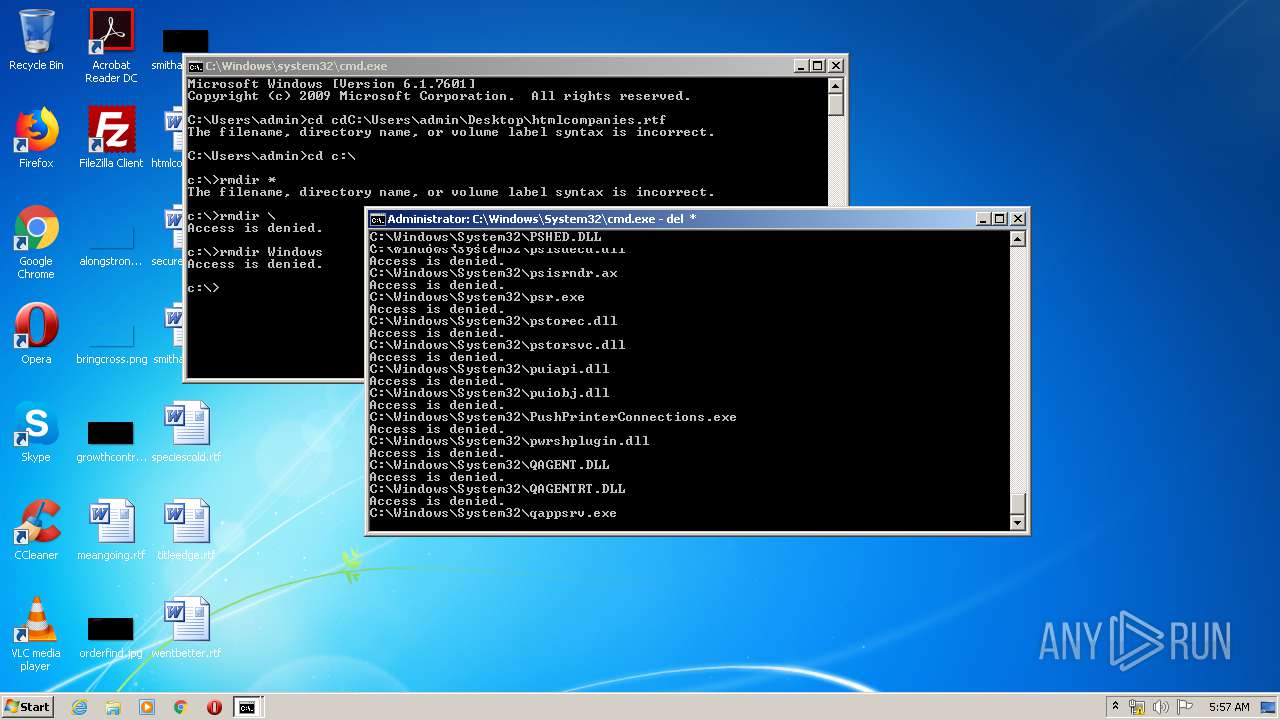
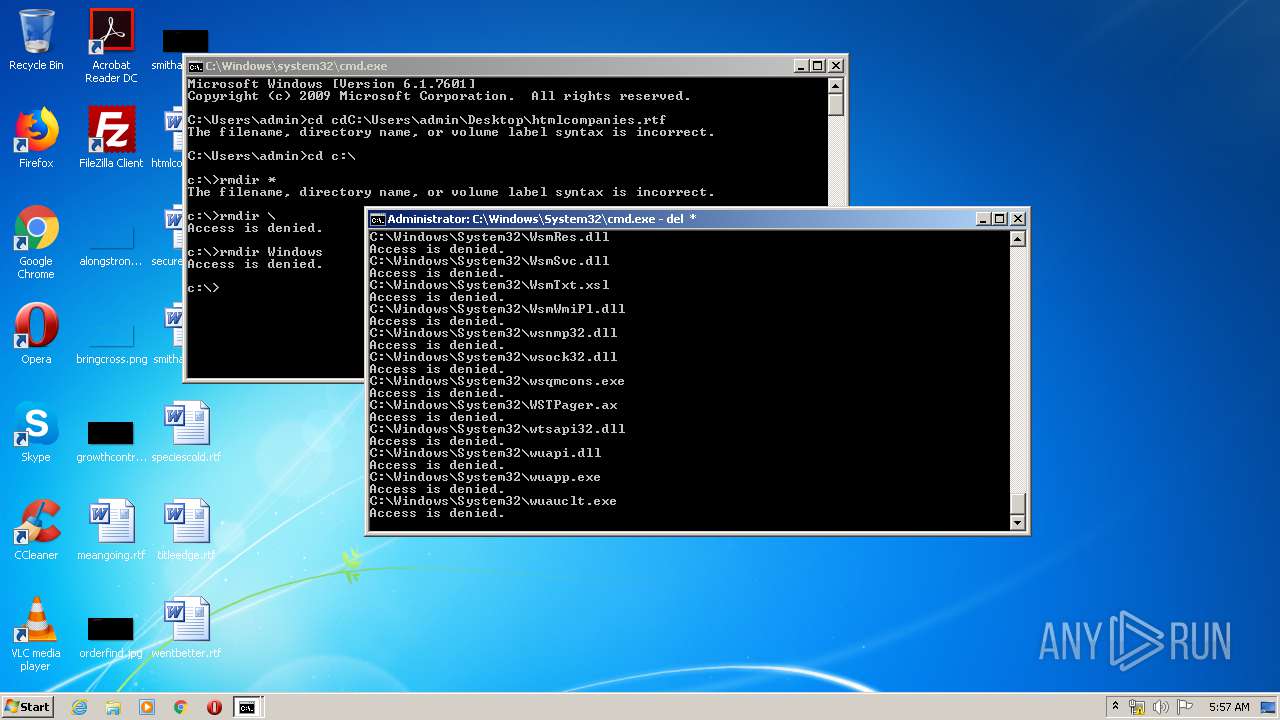
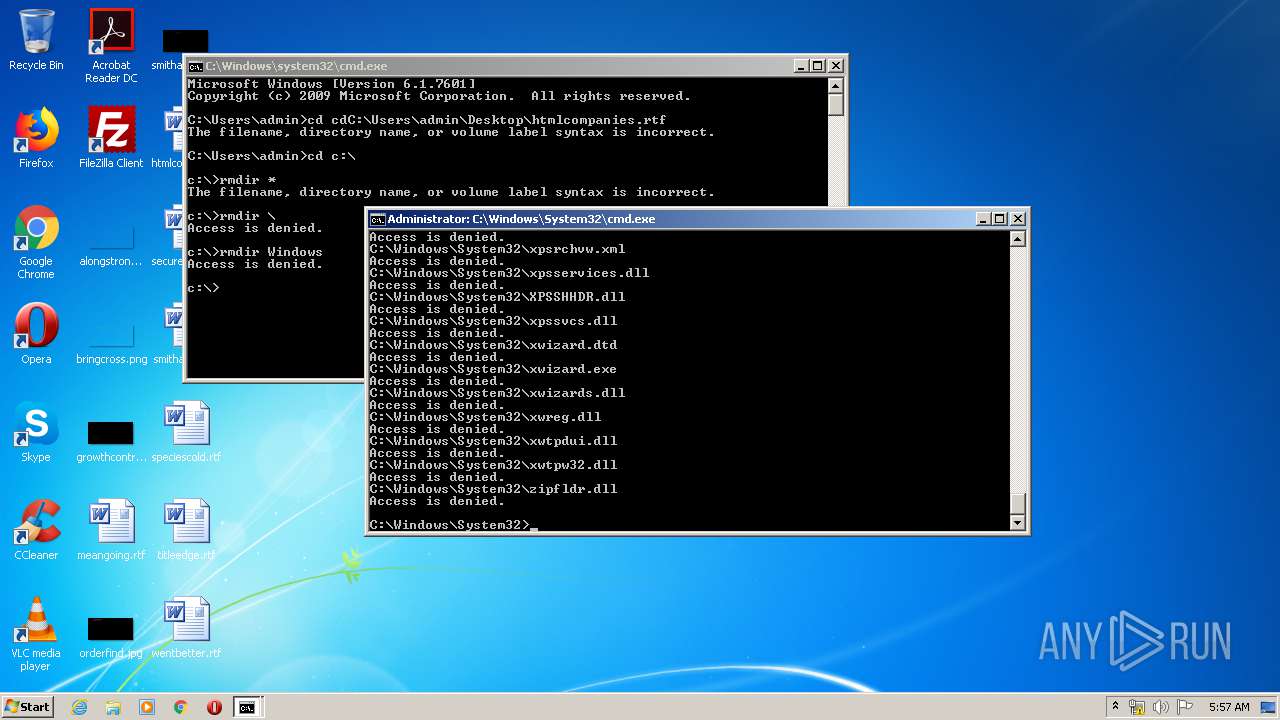
Removes files from Windows directory
- cmd.exe (PID: 3180)
INFO
Reads the hosts file
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2064)
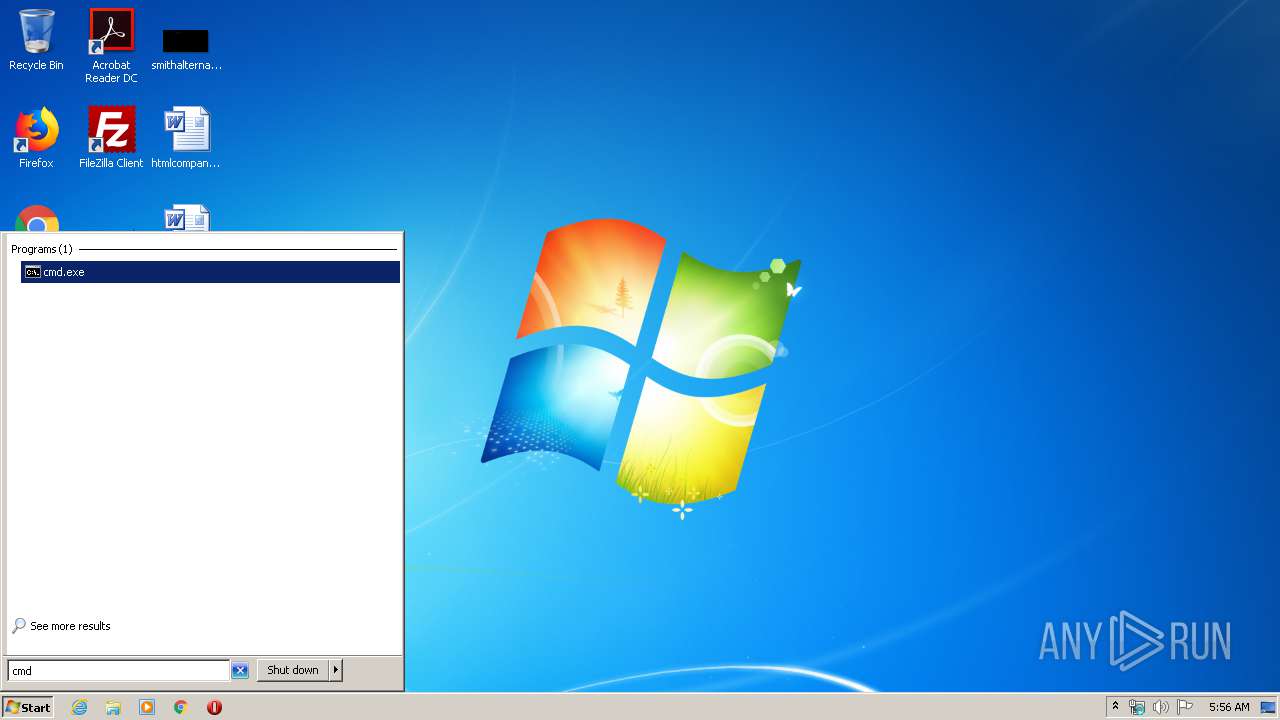
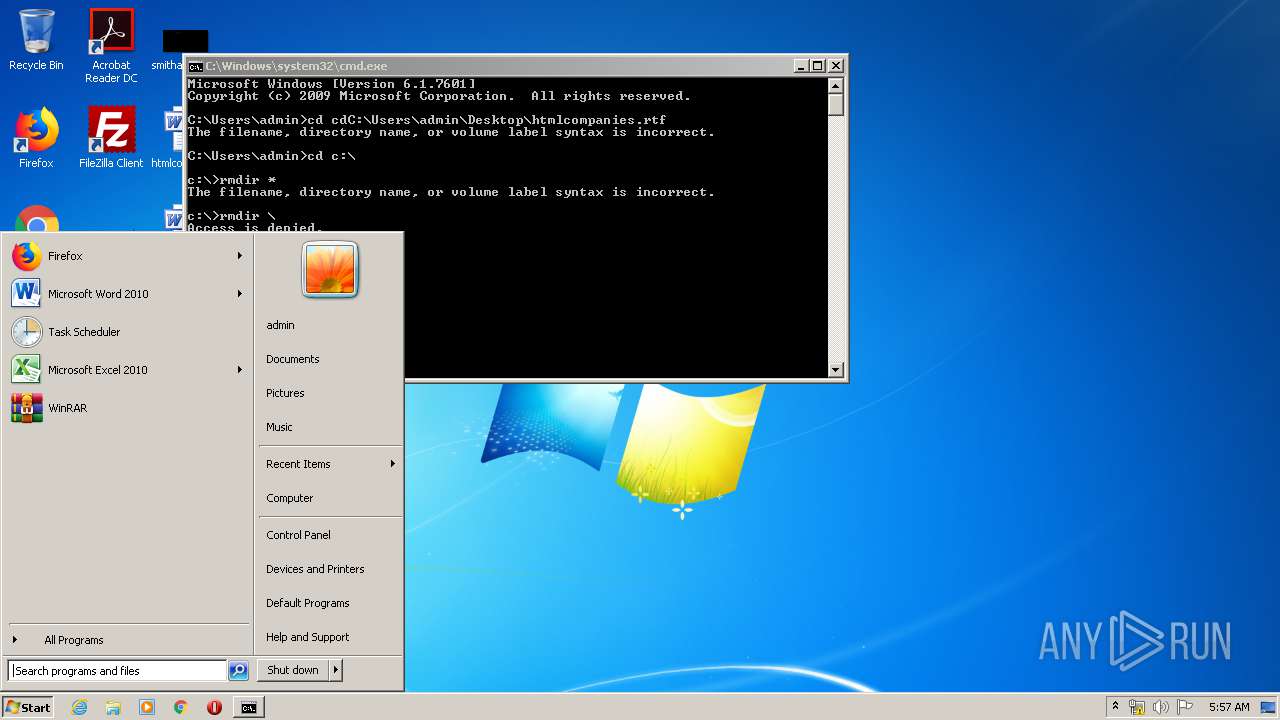
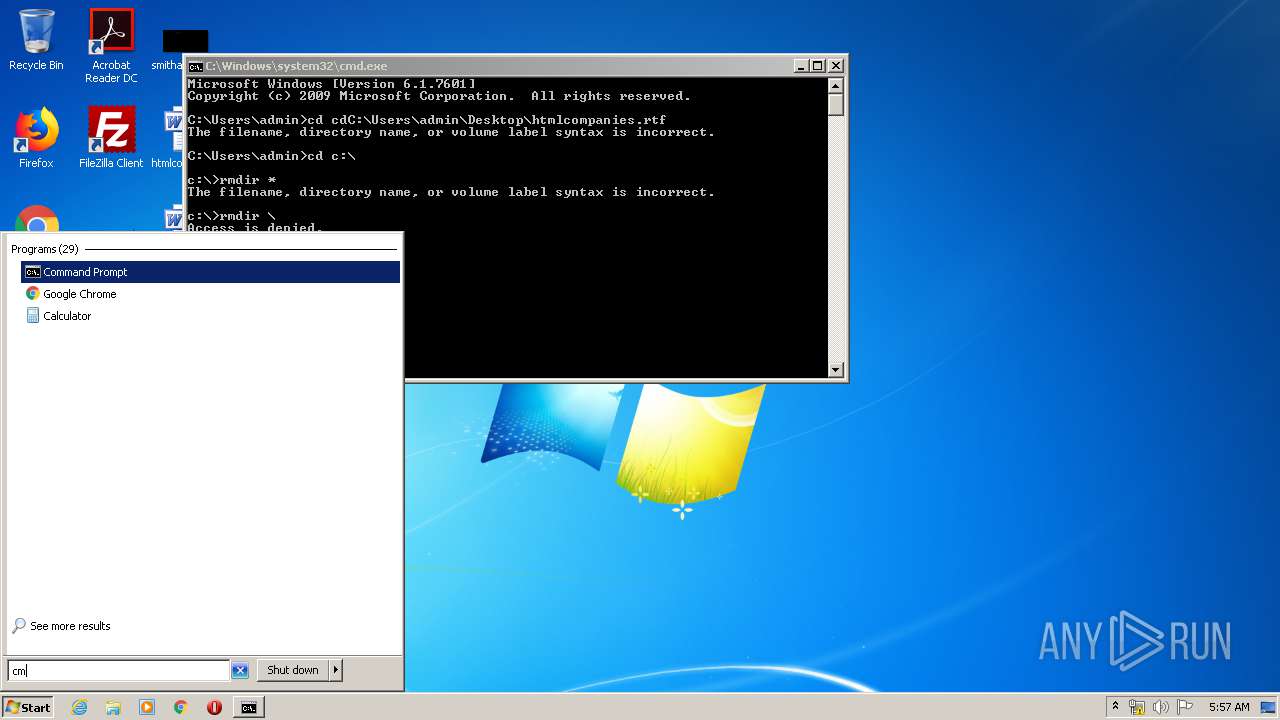
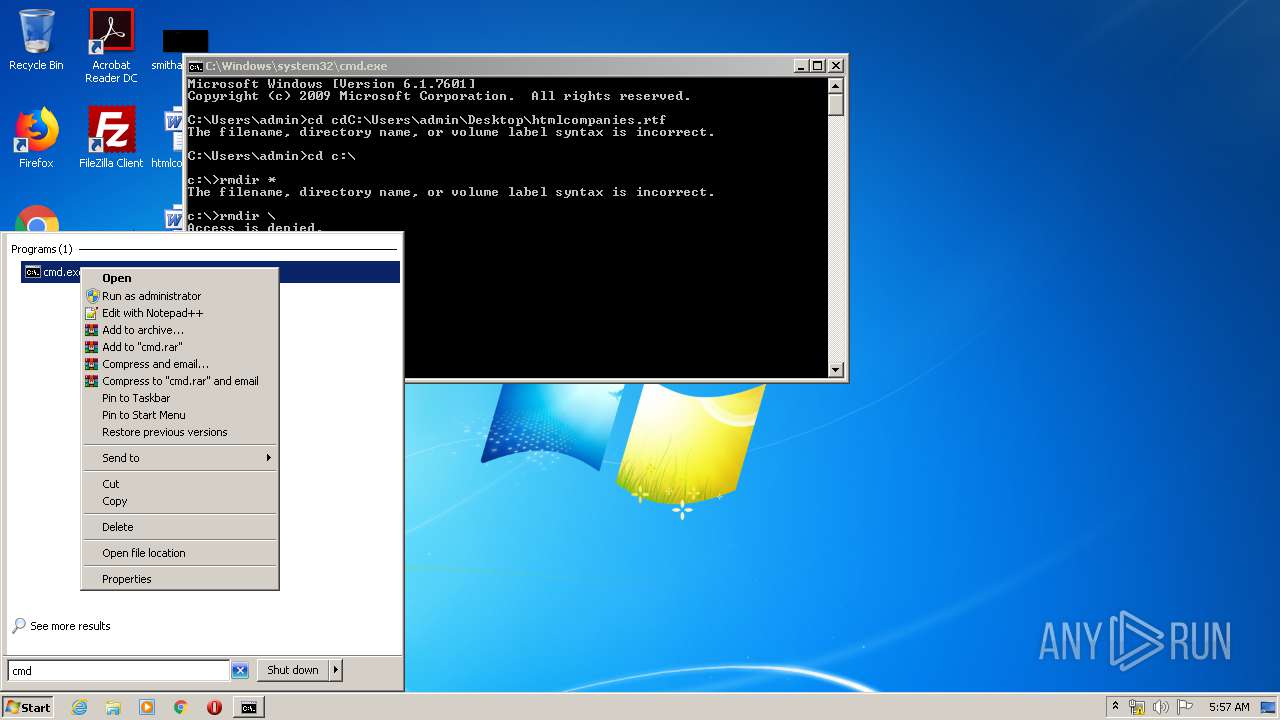
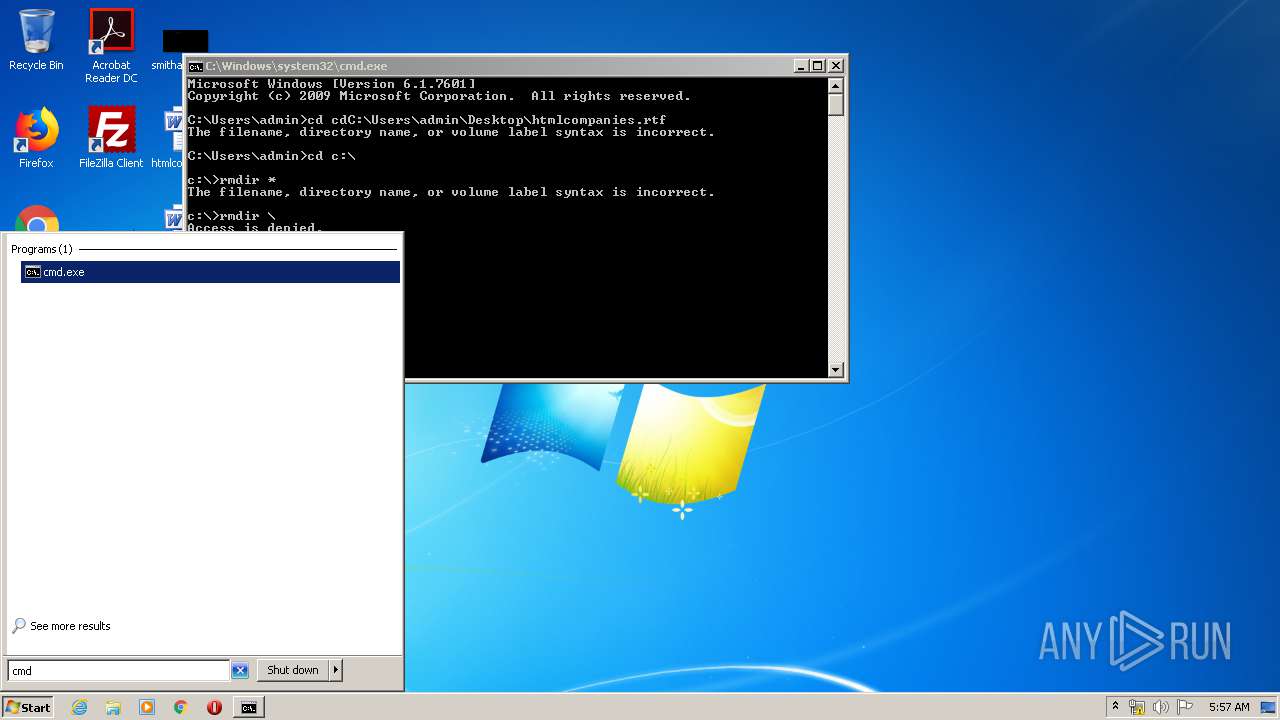
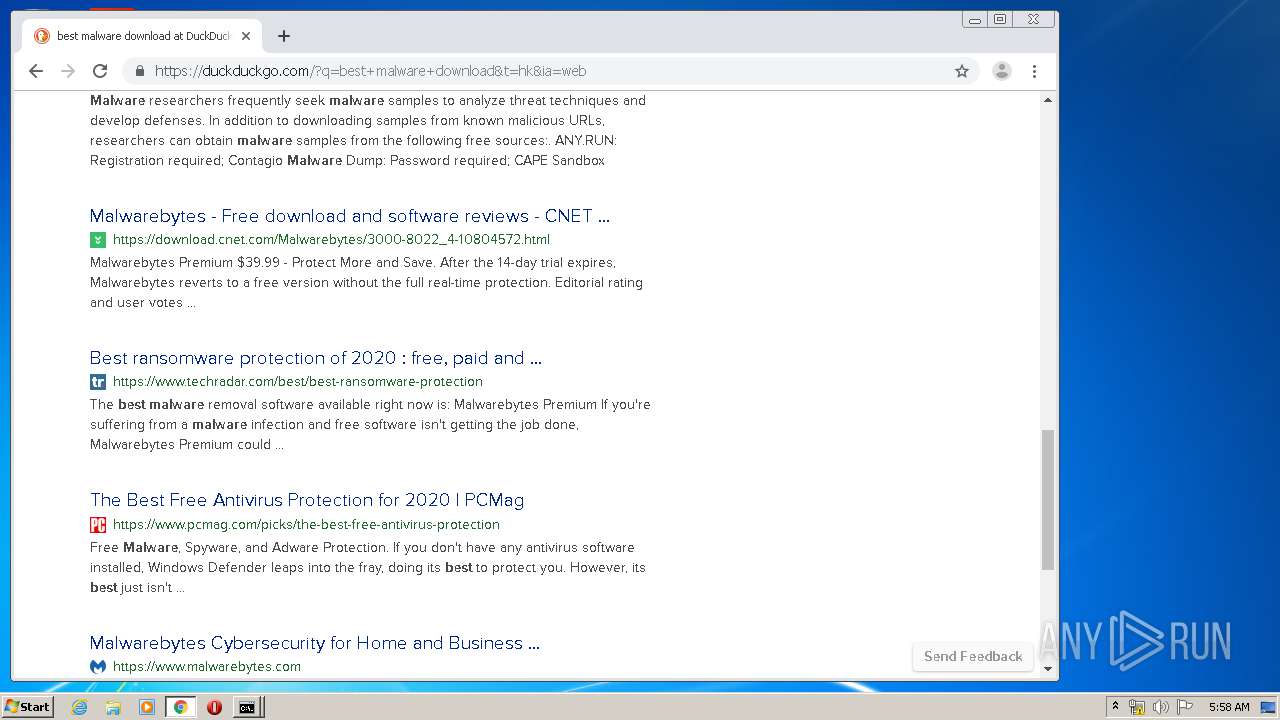
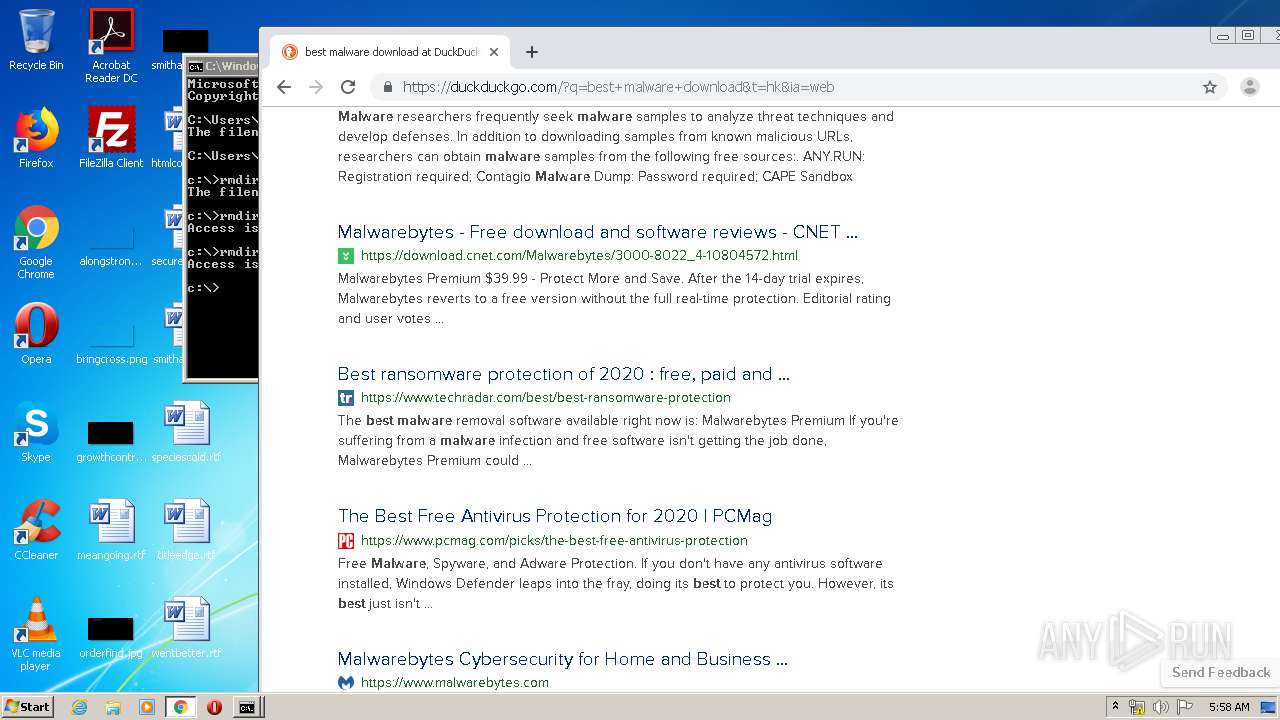
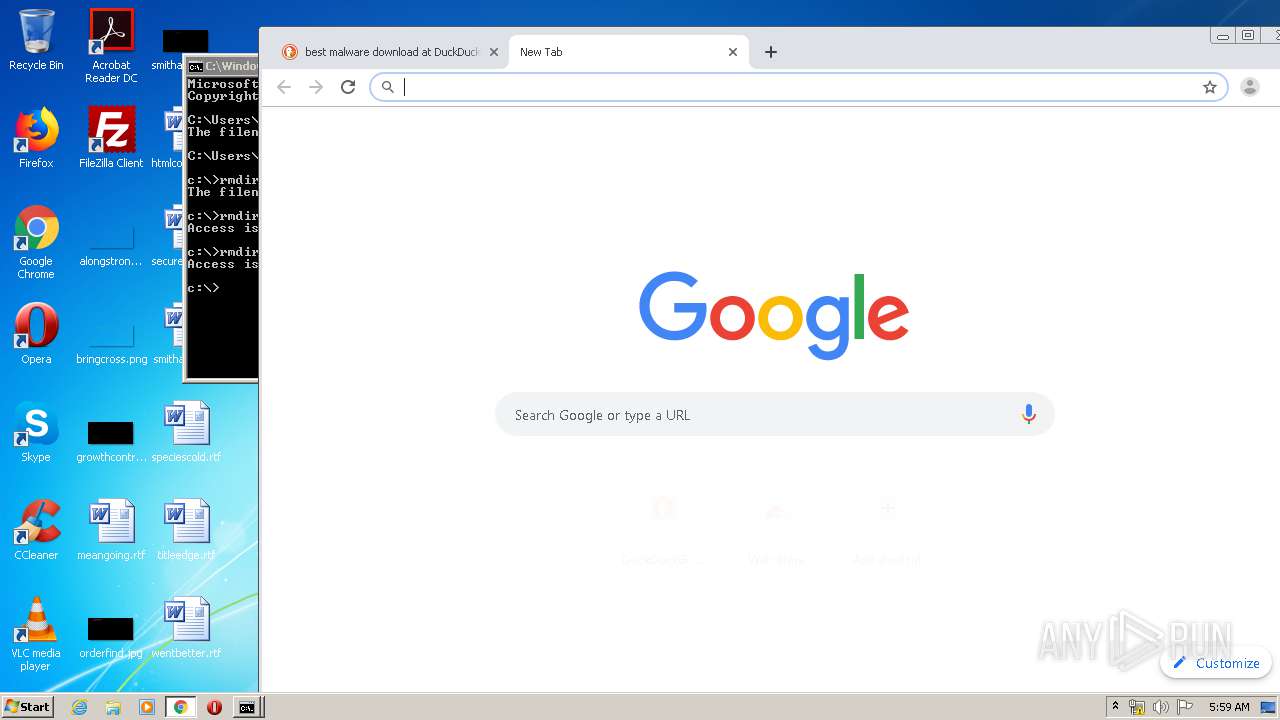
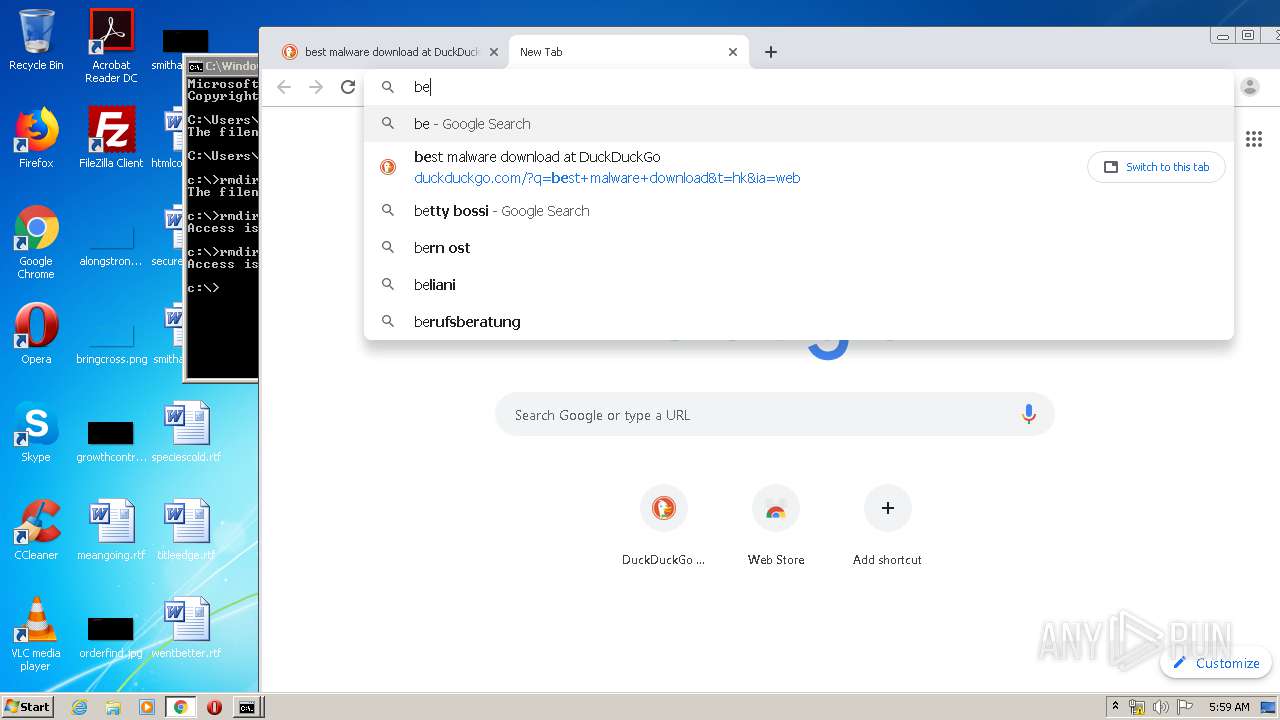
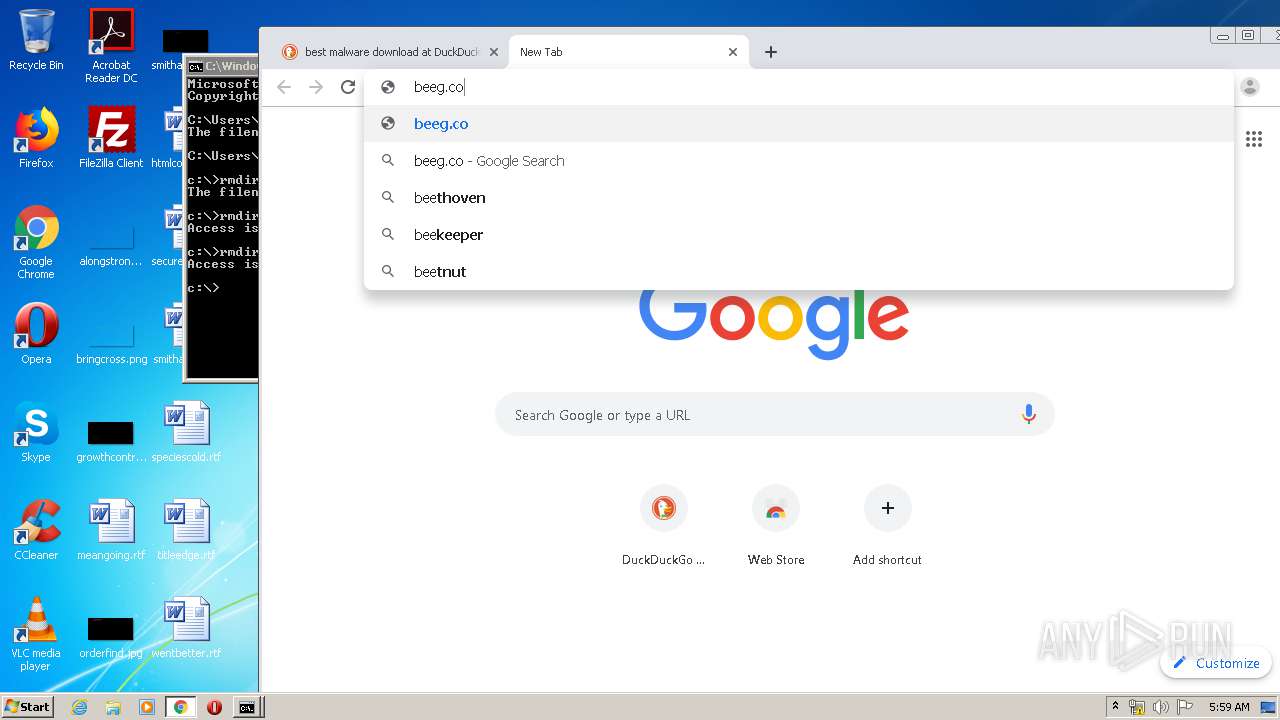
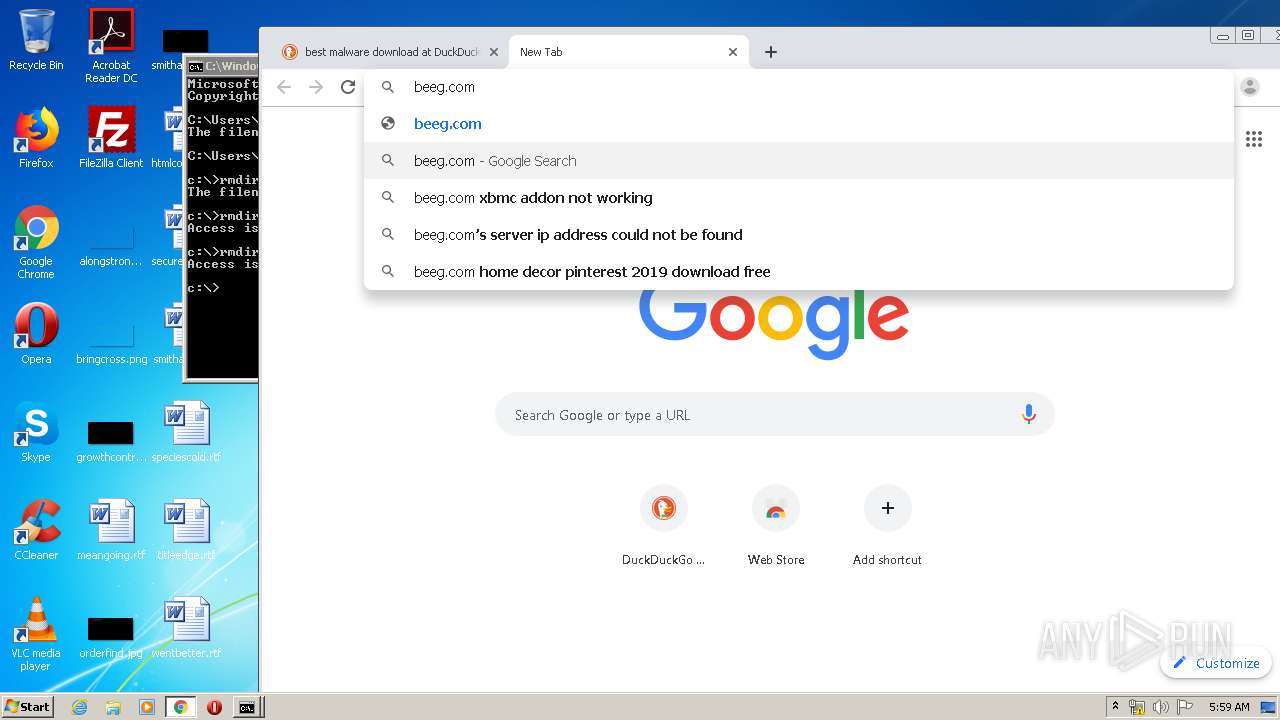
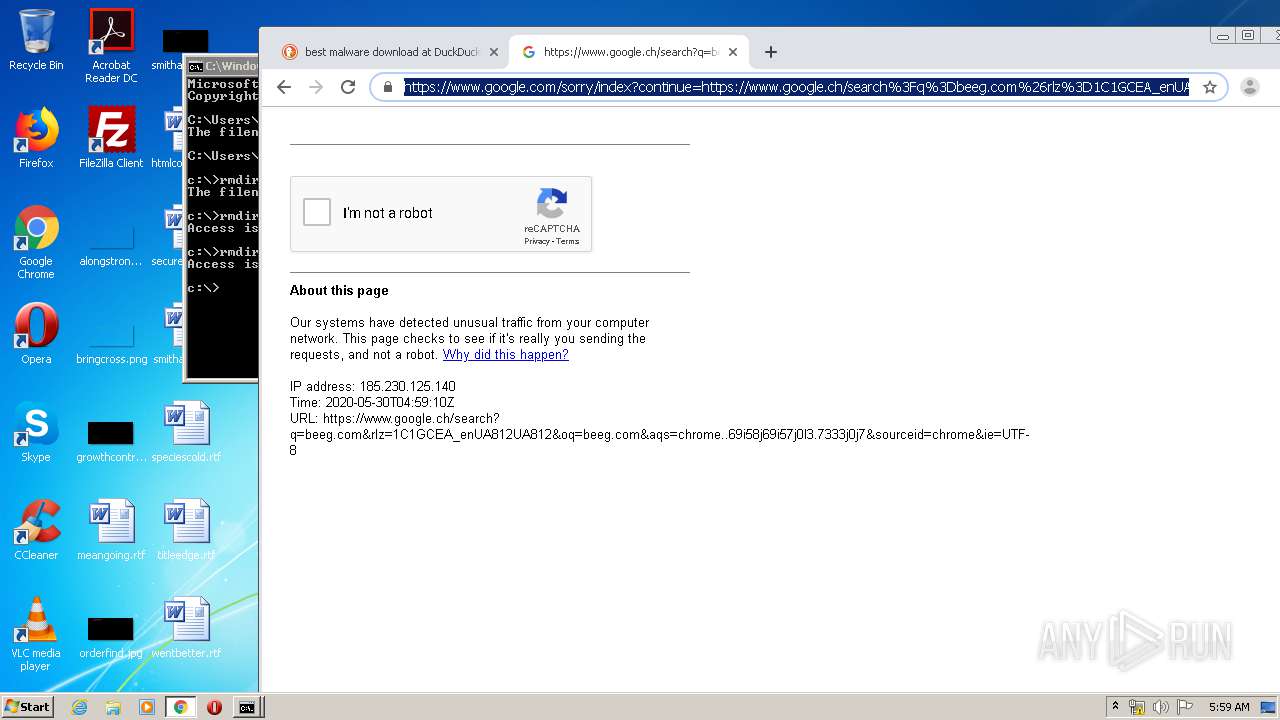
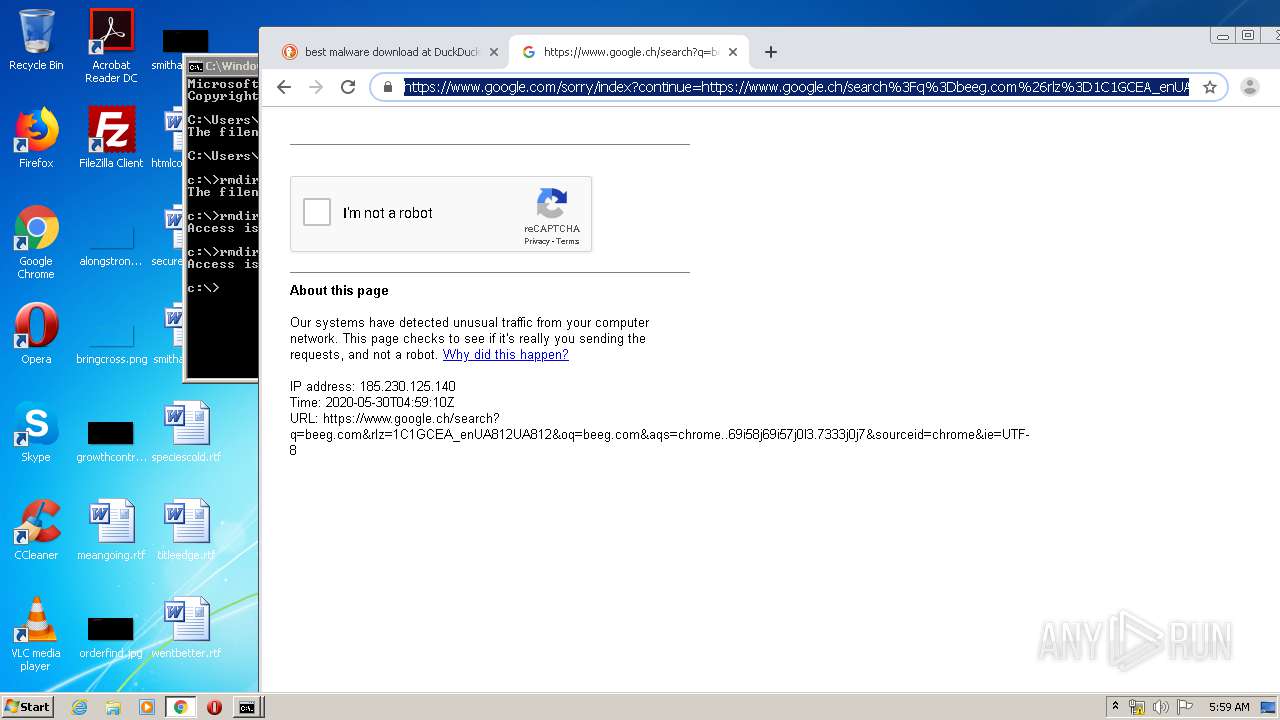
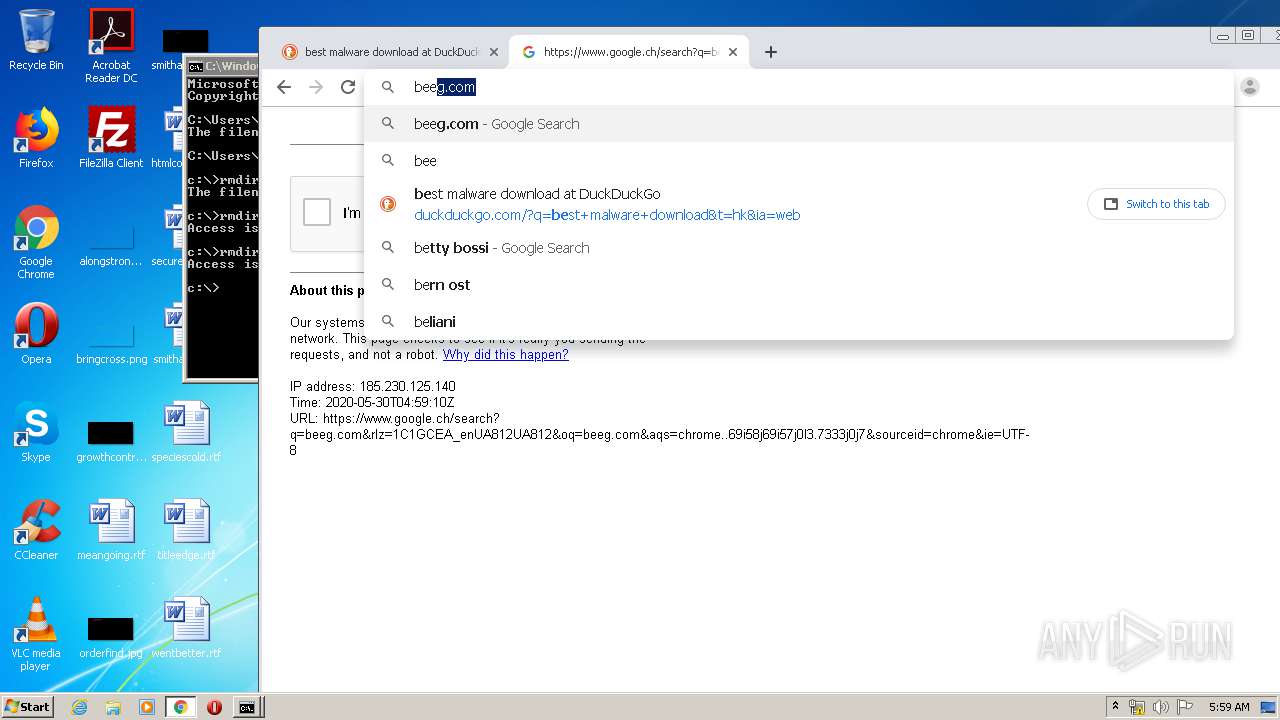
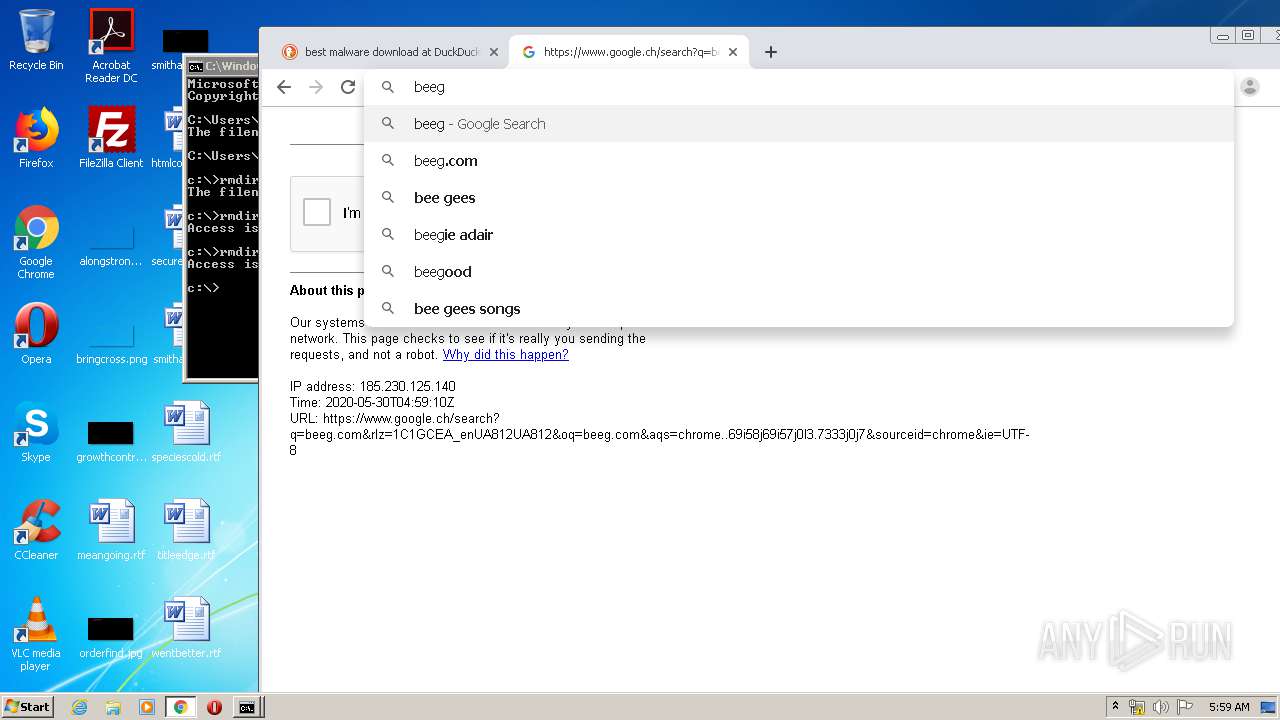
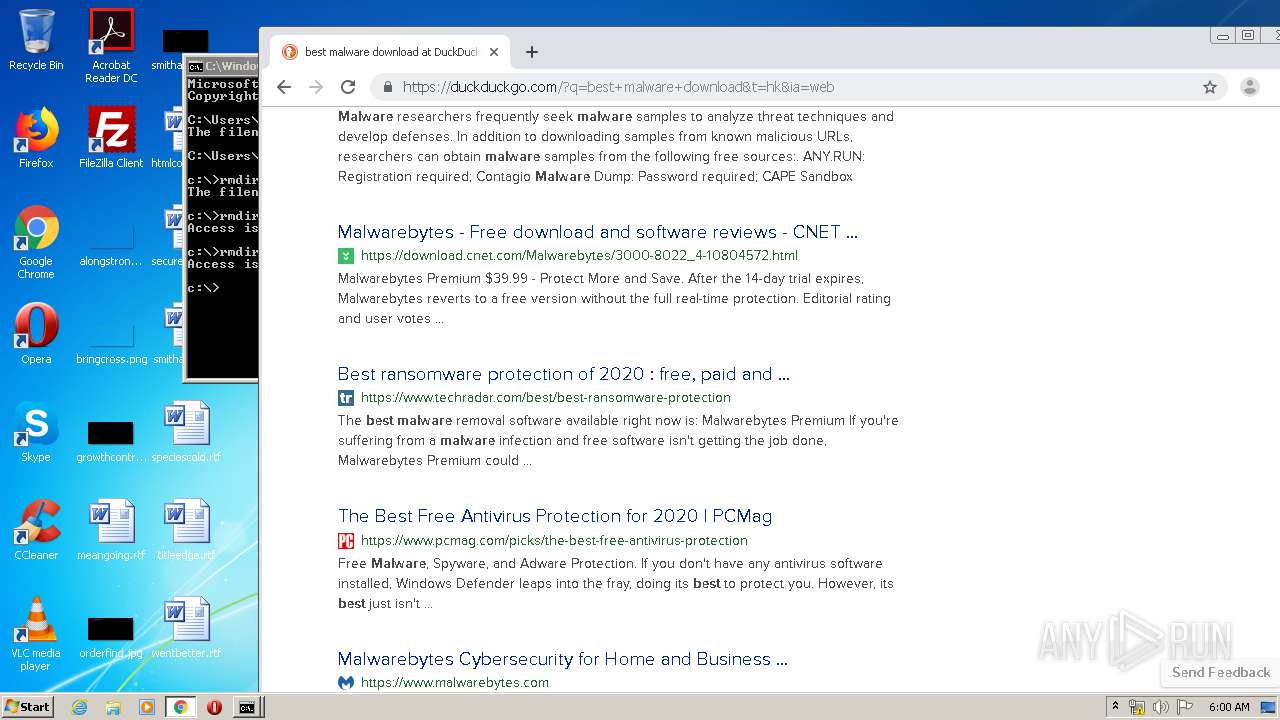
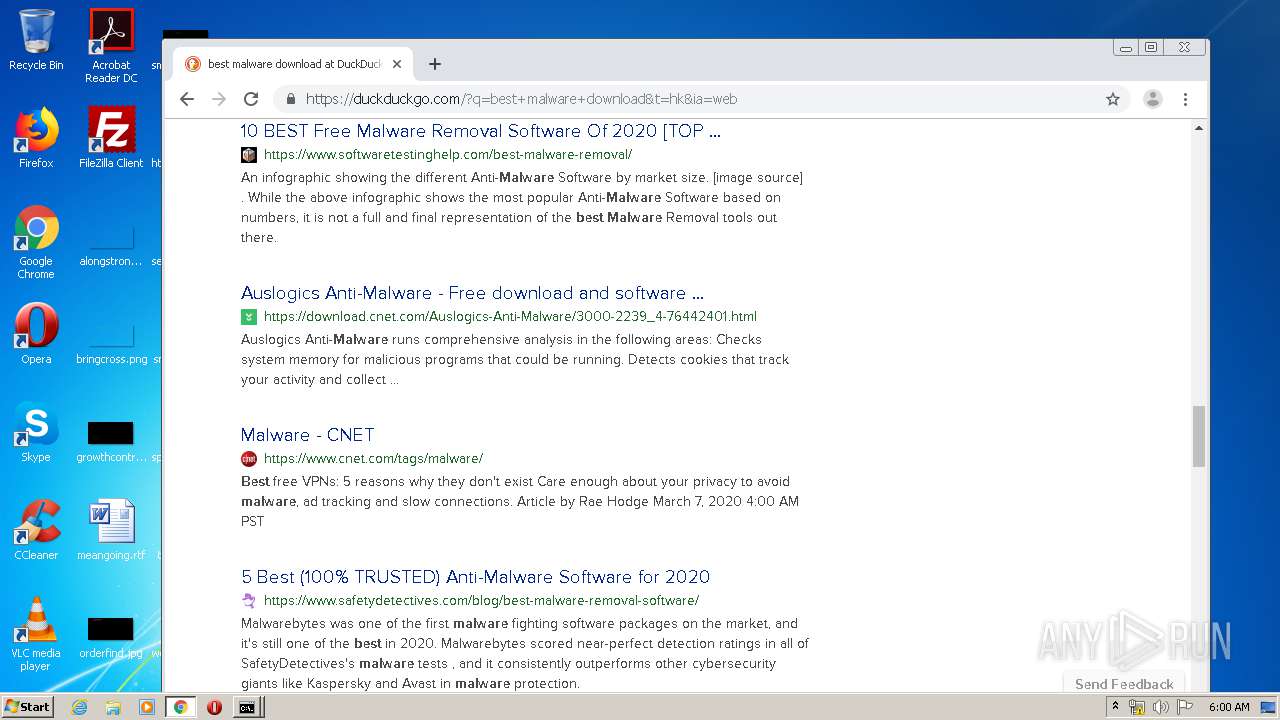
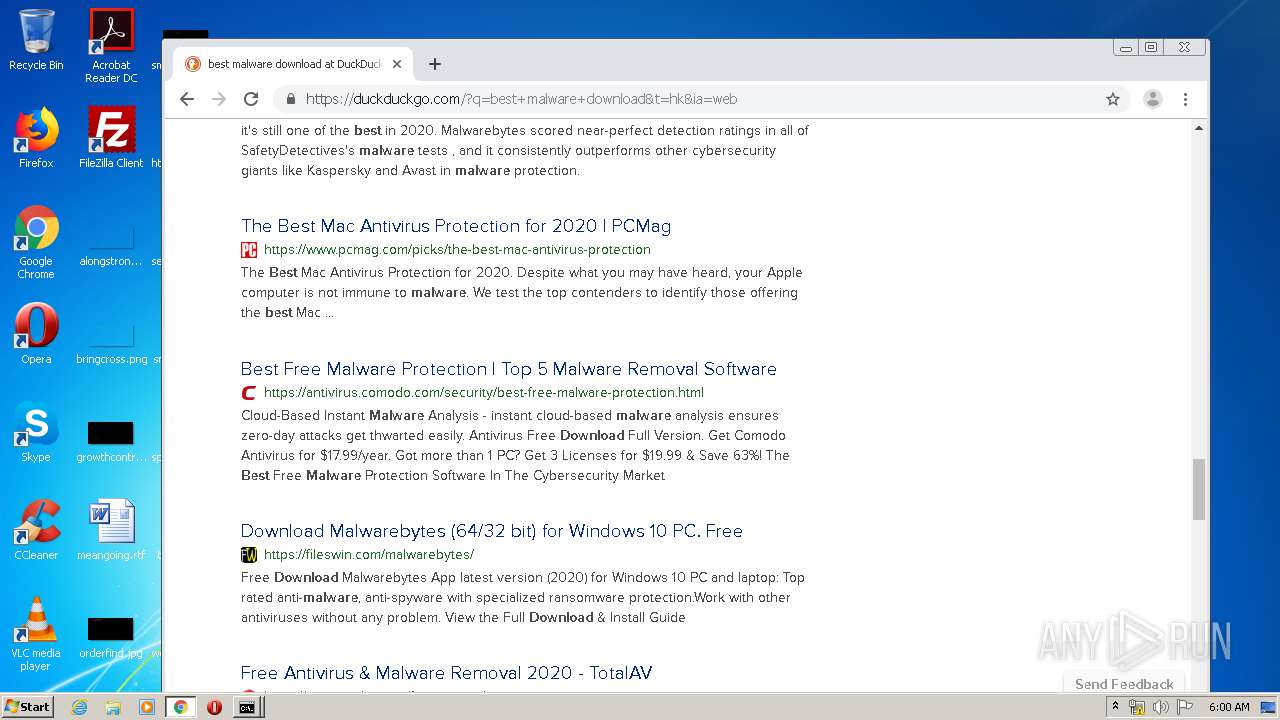
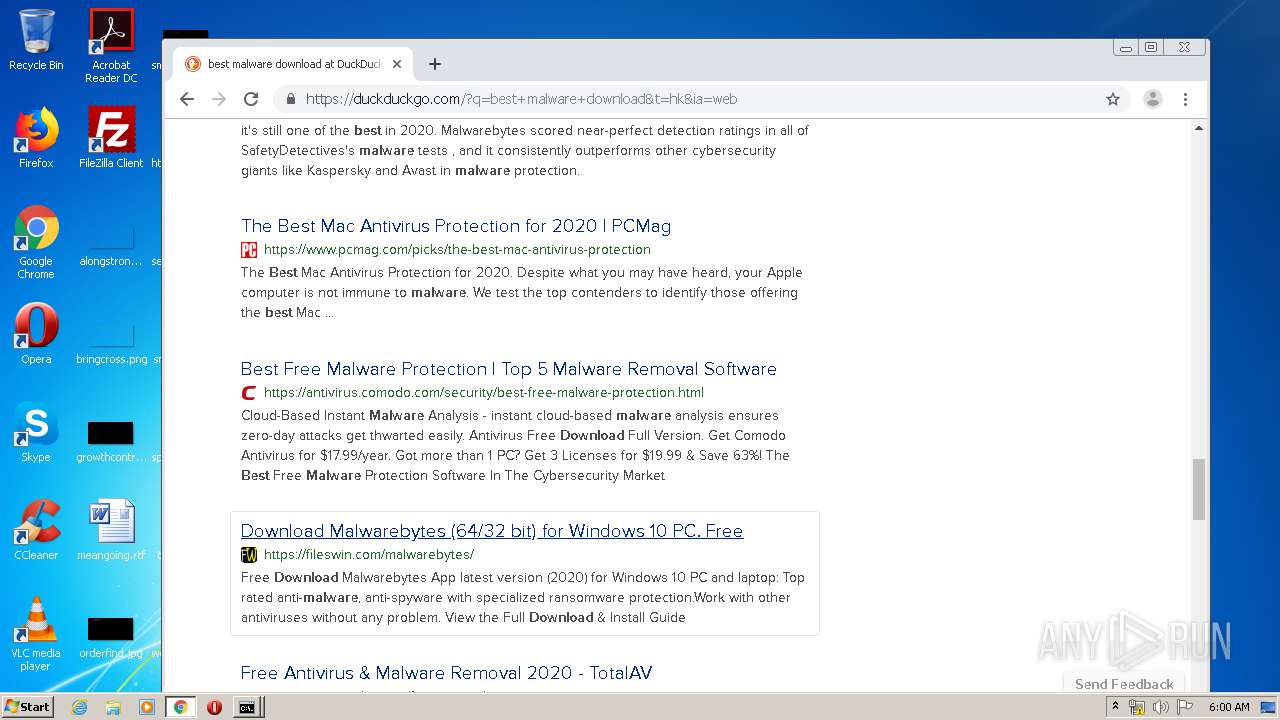
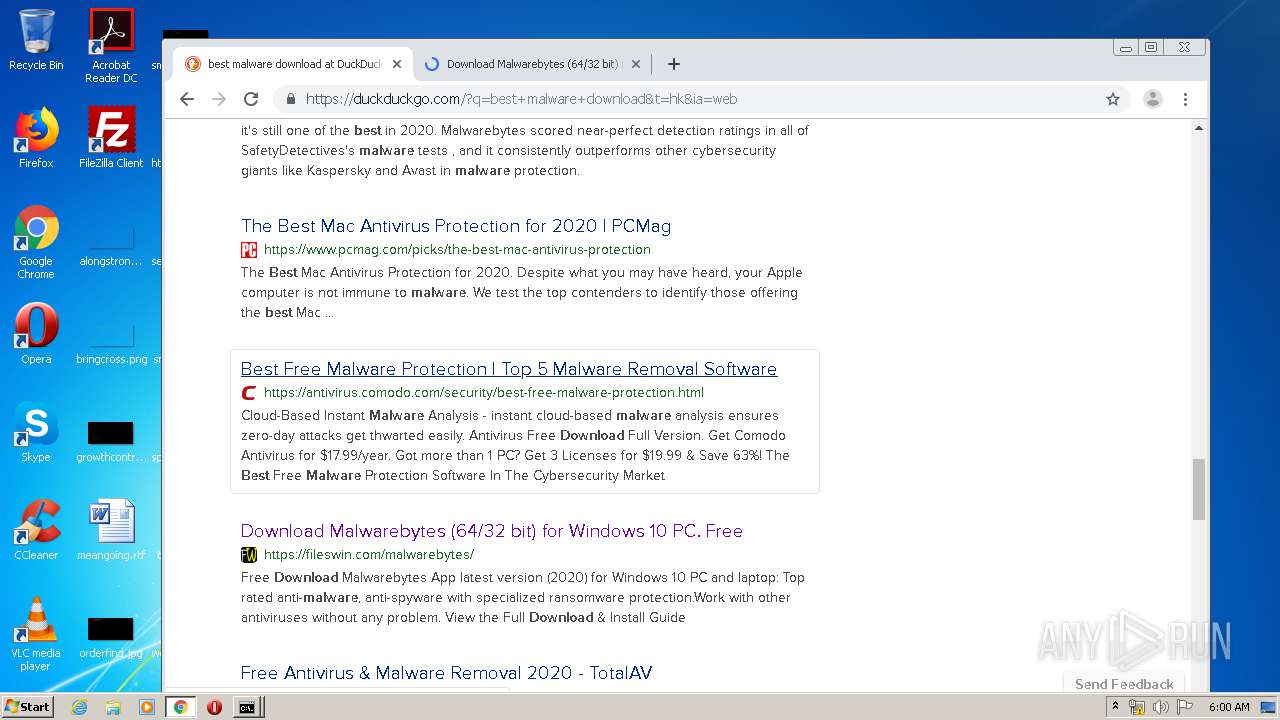
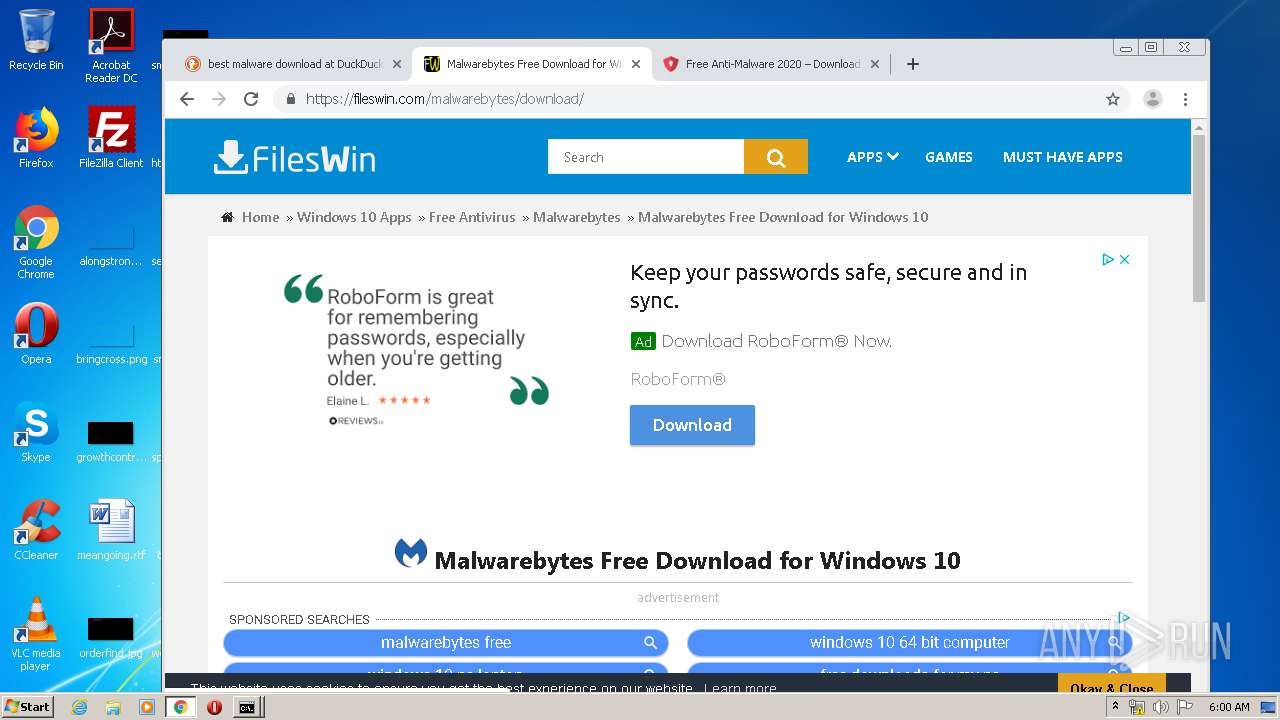
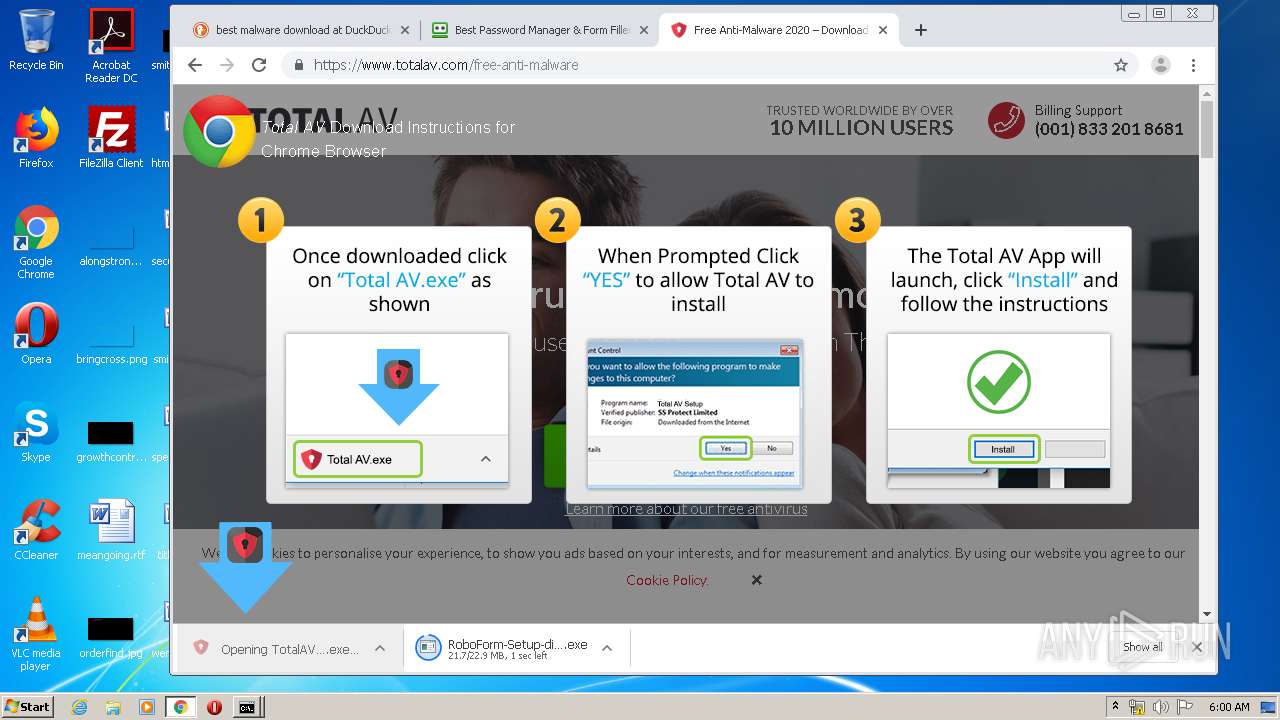
Manual execution by user
- chrome.exe (PID: 3228)
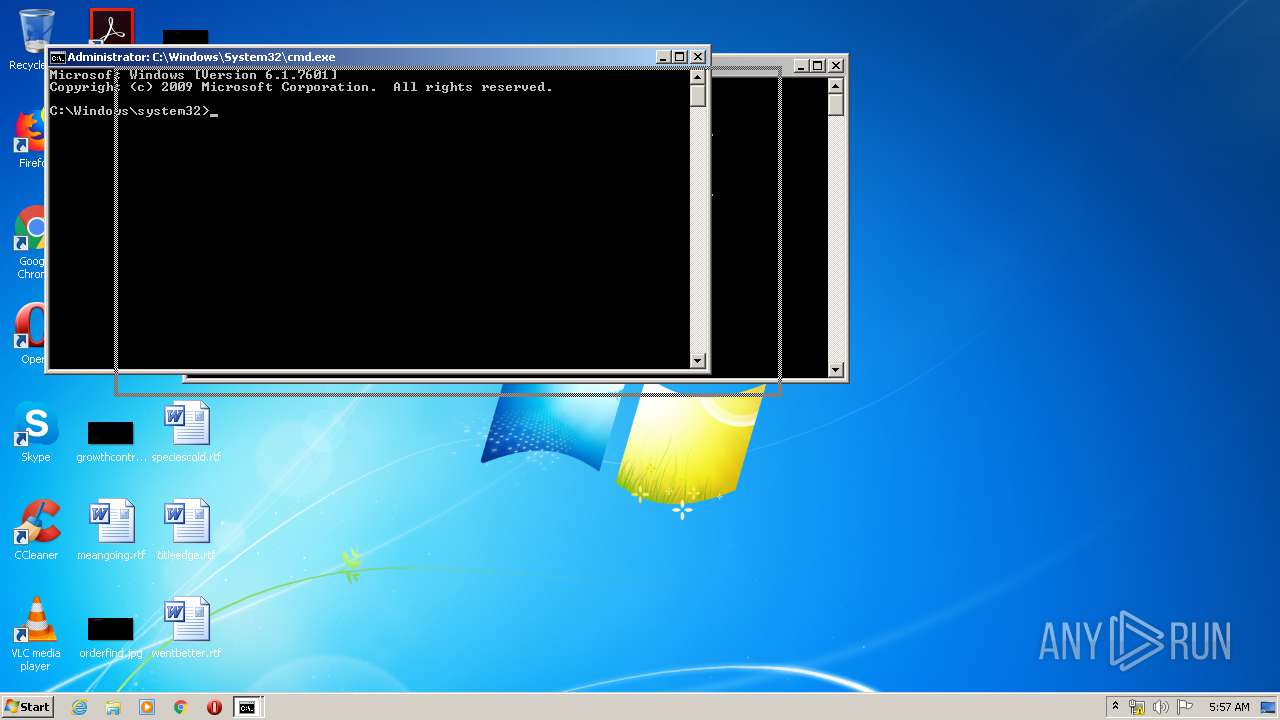
- cmd.exe (PID: 336)
- cmd.exe (PID: 3180)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3228)
Application launched itself
- chrome.exe (PID: 3228)
Reads settings of System Certificates
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2064)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3228)
Reads Internet Cache Settings
- chrome.exe (PID: 3228)
Creates files in the user directory
- chrome.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
135
Monitored processes
74
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17771222295712081936 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 336 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16601596358102864621 --mojo-platform-channel-handle=3404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14068242706674757542 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16059817265536403146 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12030552913278171191 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13913587916576605820 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
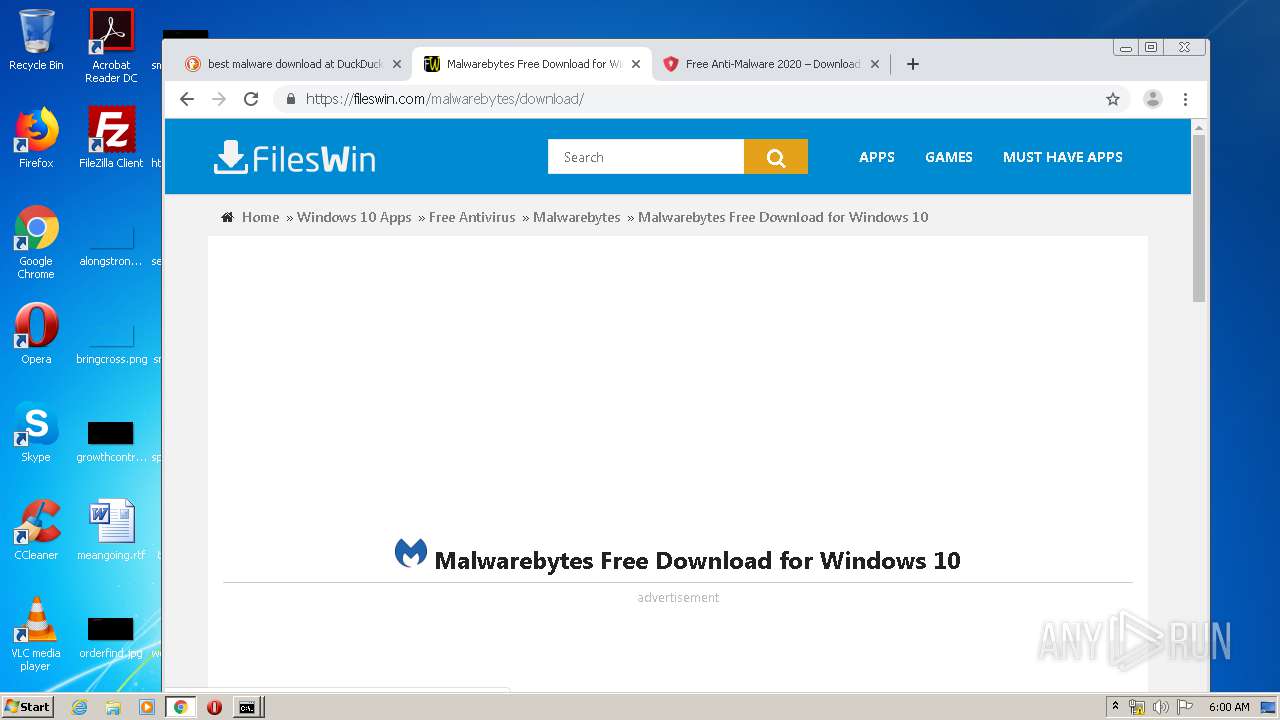
| 964 | "C:\Users\admin\Downloads\RoboForm-Setup-displ.exe" | C:\Users\admin\Downloads\RoboForm-Setup-displ.exe | — | chrome.exe | |||||||||||
User: admin Company: Siber Systems Integrity Level: MEDIUM Description: RoboForm Installer and Uninstaller Exit code: 3221226540 Version: 8-7-0-0 Modules
| |||||||||||||||
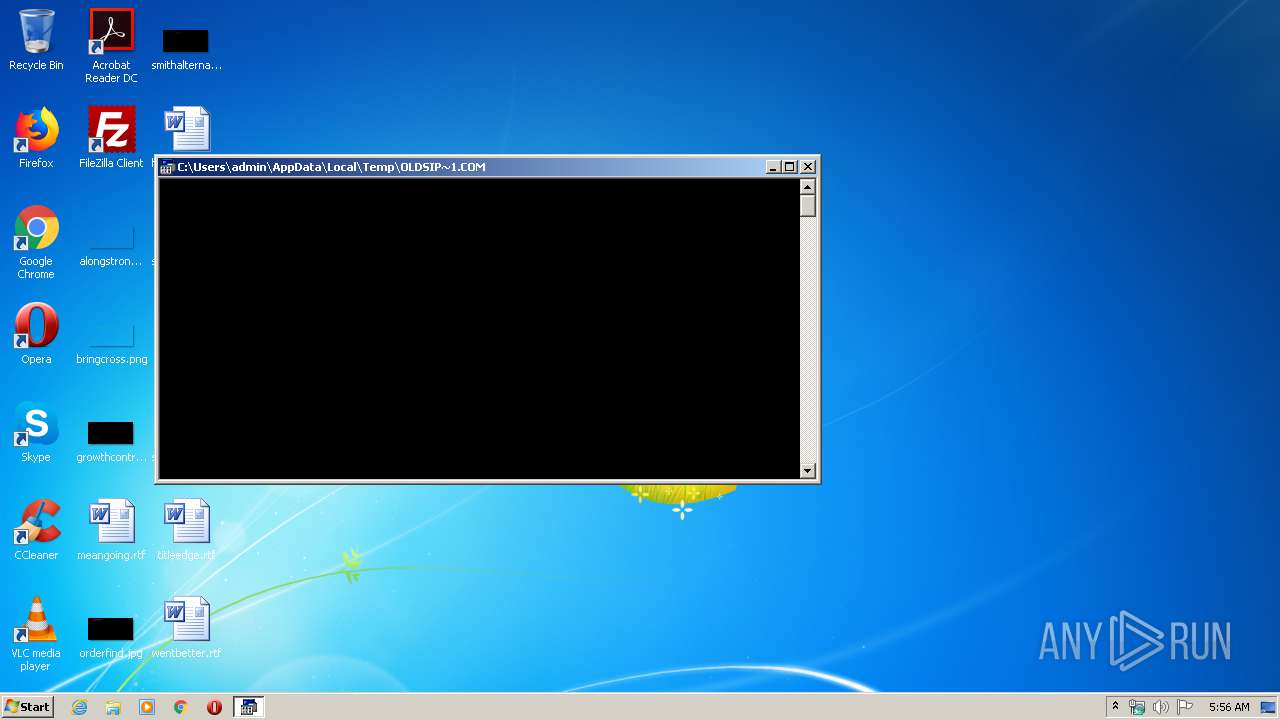
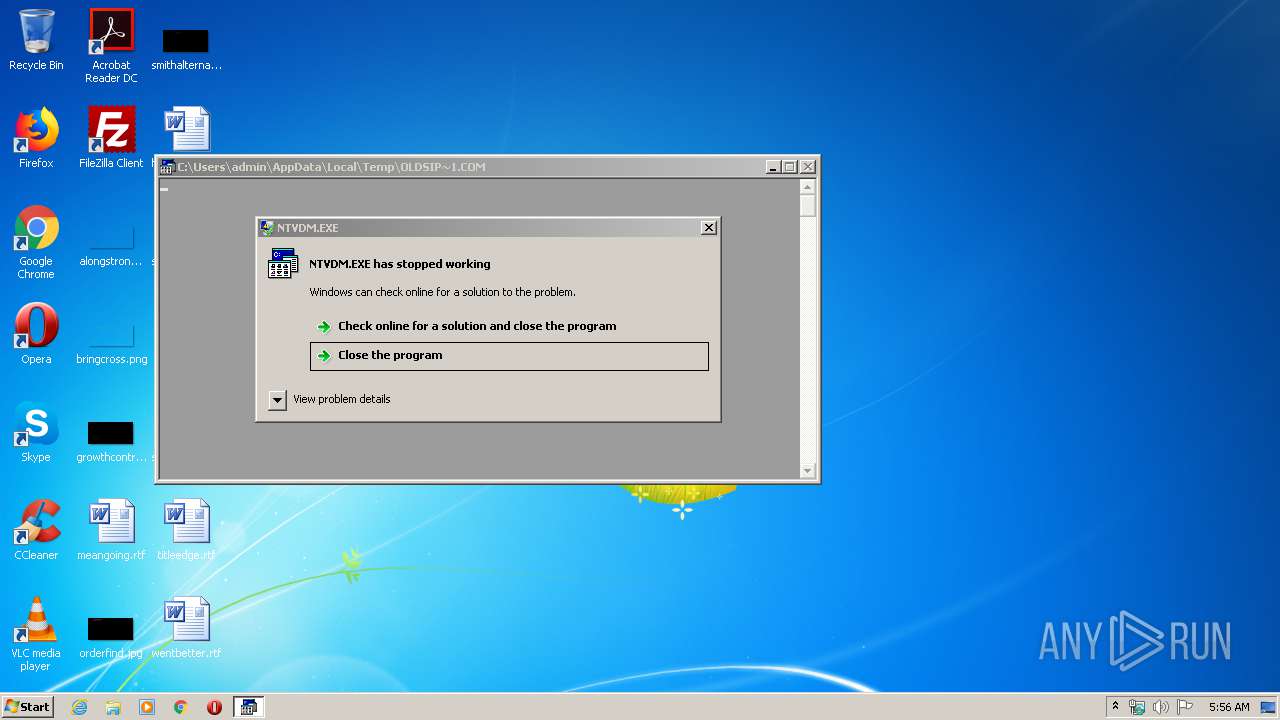
| 968 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16543219359793475934,403592307878548553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18202388459106734543 --mojo-platform-channel-handle=4320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 603
Read events
1 460
Write events
134
Delete events
9
Modification events
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3228-13235288282978250 |
Value: 259 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
23
Suspicious files
142
Text files
457
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 968 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsD981.tmp | — | |
MD5:— | SHA256:— | |||
| 968 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsD9A1.tmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED1E7DB-C9C.pma | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ccca9cfe-b2a1-467f-9e0a-d3a90e532fc4.tmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17949f.TMP | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF1795a8.TMP | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1794ed.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
87
DNS requests
66
Threats
0
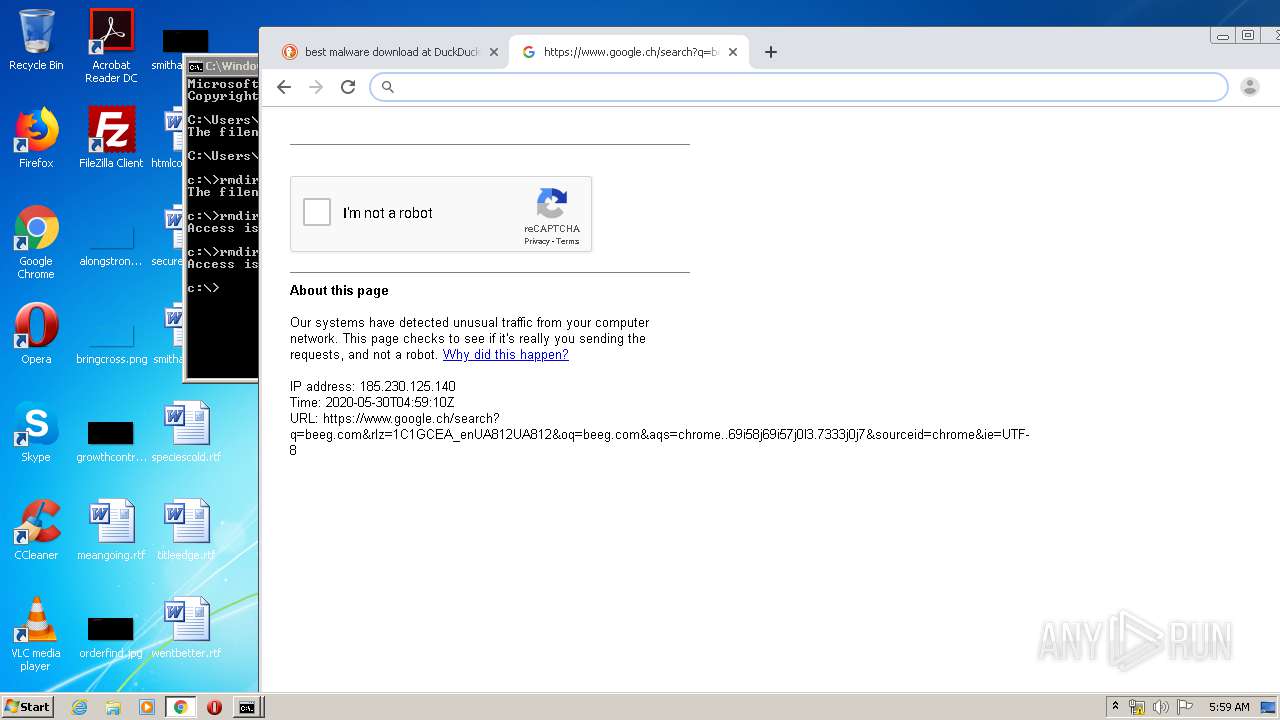
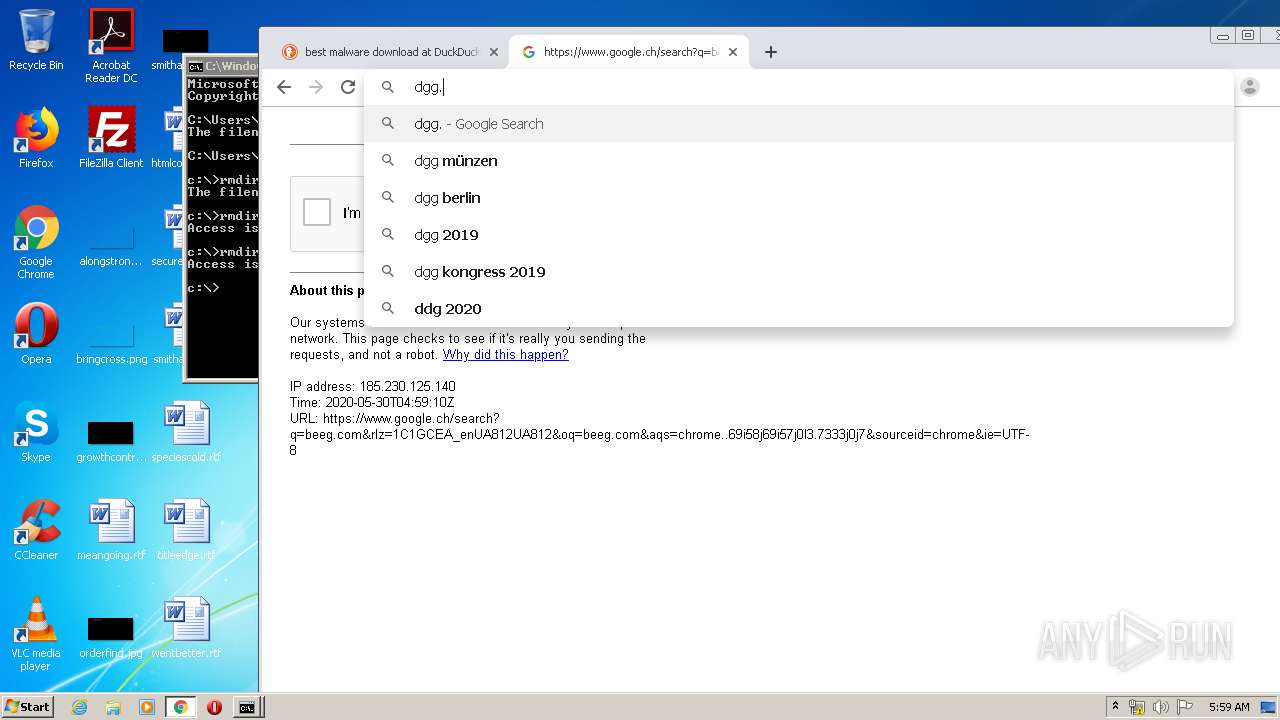
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | chrome.exe | GET | 302 | 108.177.126.100:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
2064 | chrome.exe | GET | 200 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.230.125.140&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1590814582&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2064 | chrome.exe | GET | 302 | 108.177.126.100:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
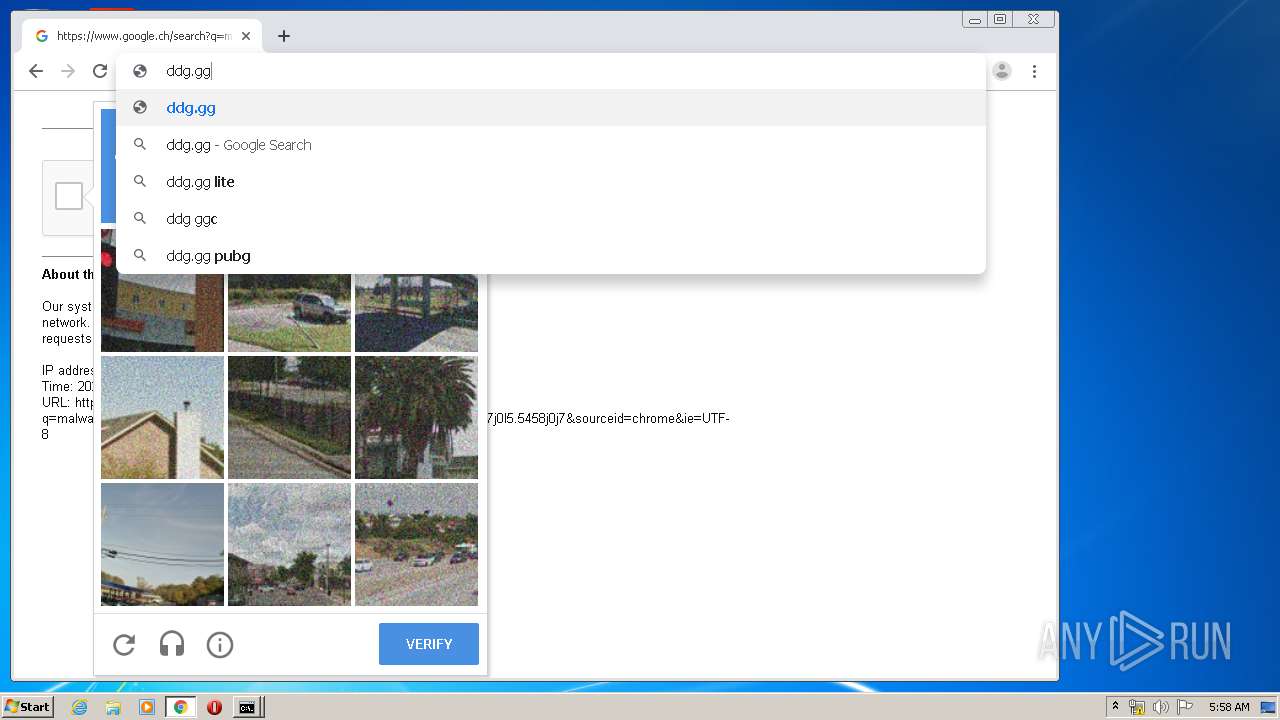
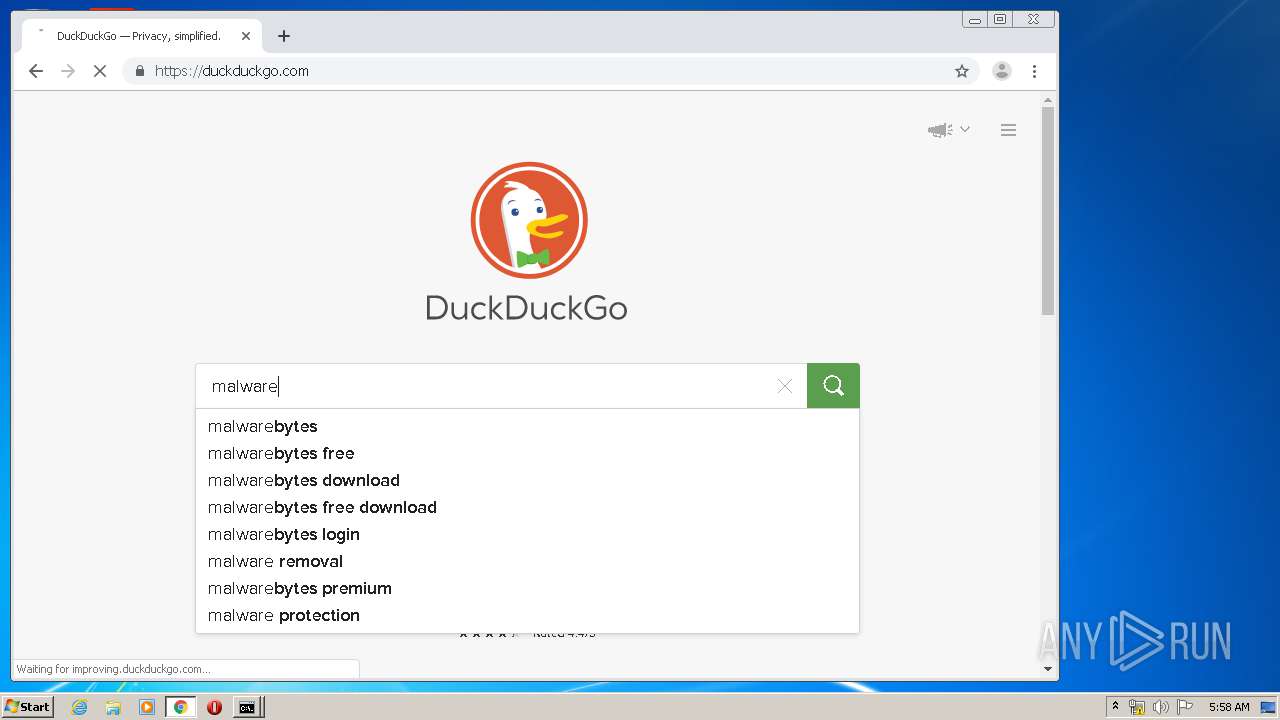
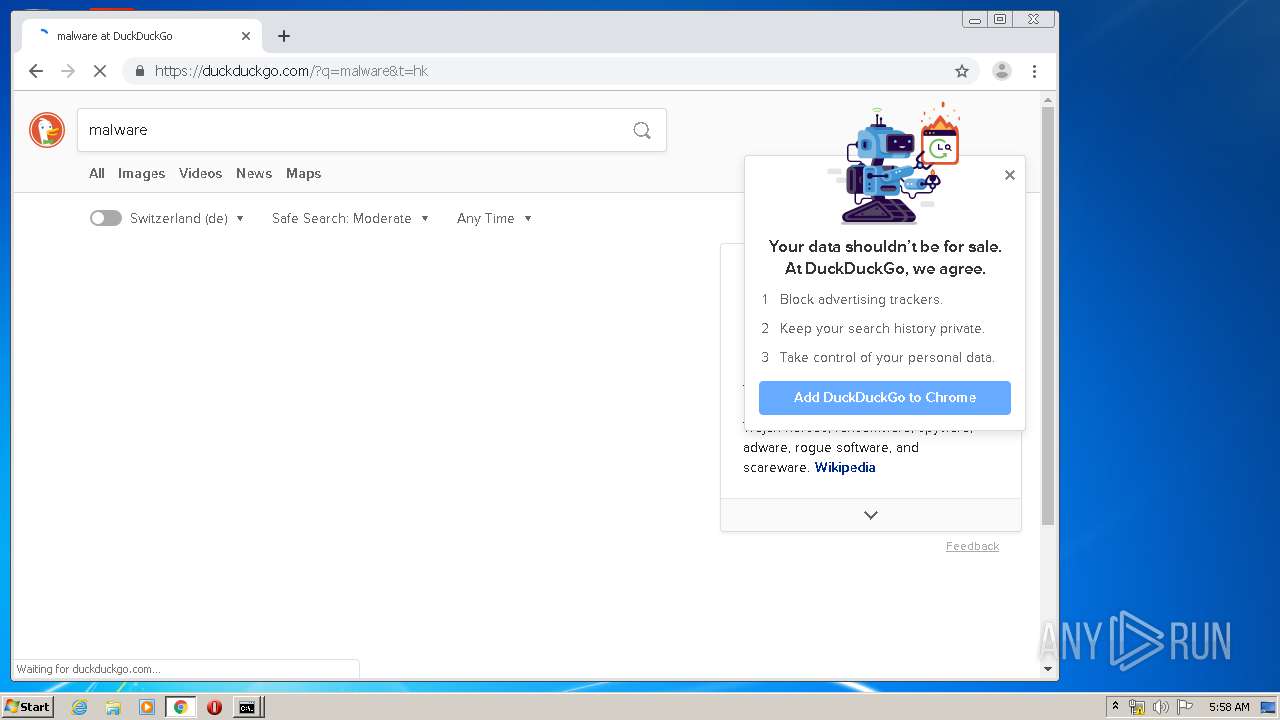
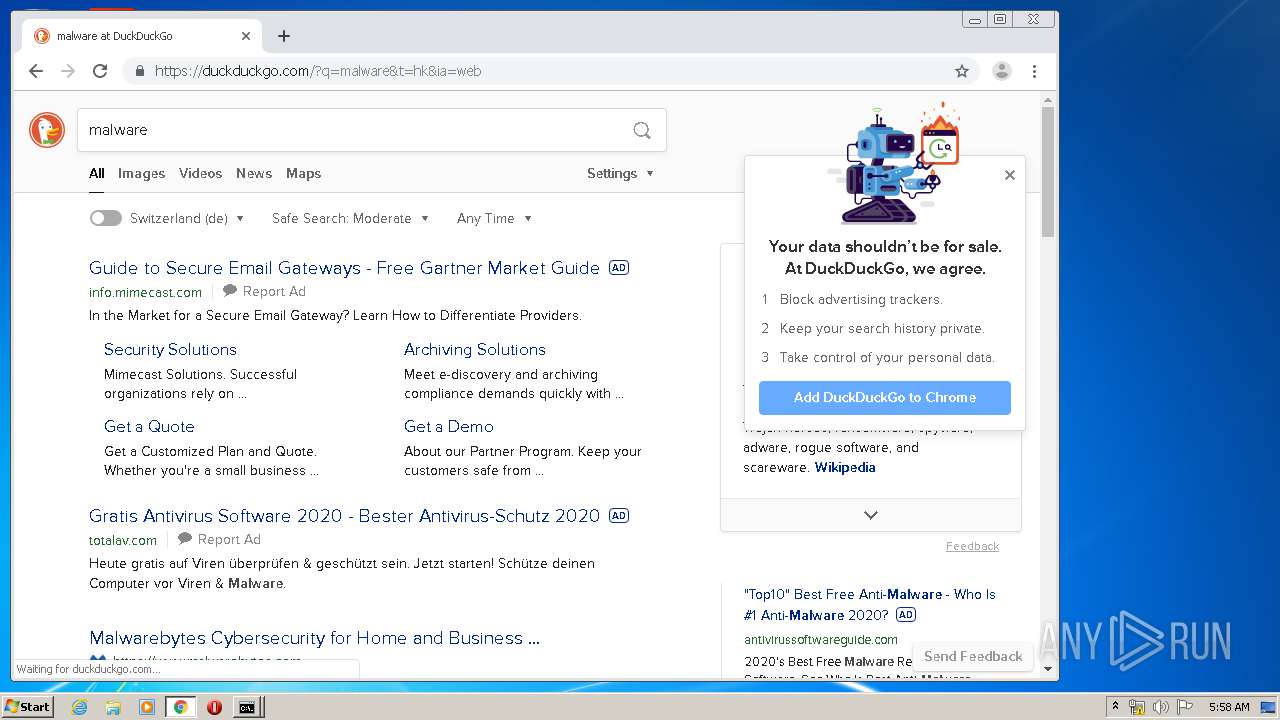
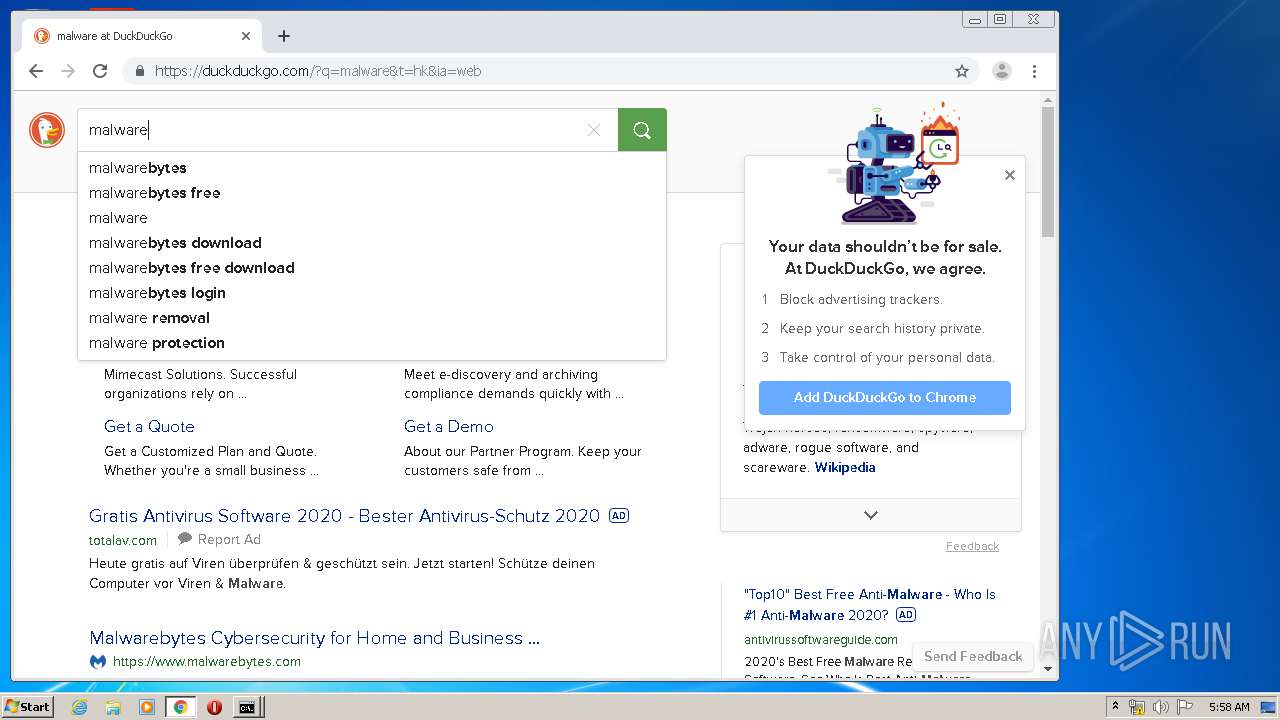
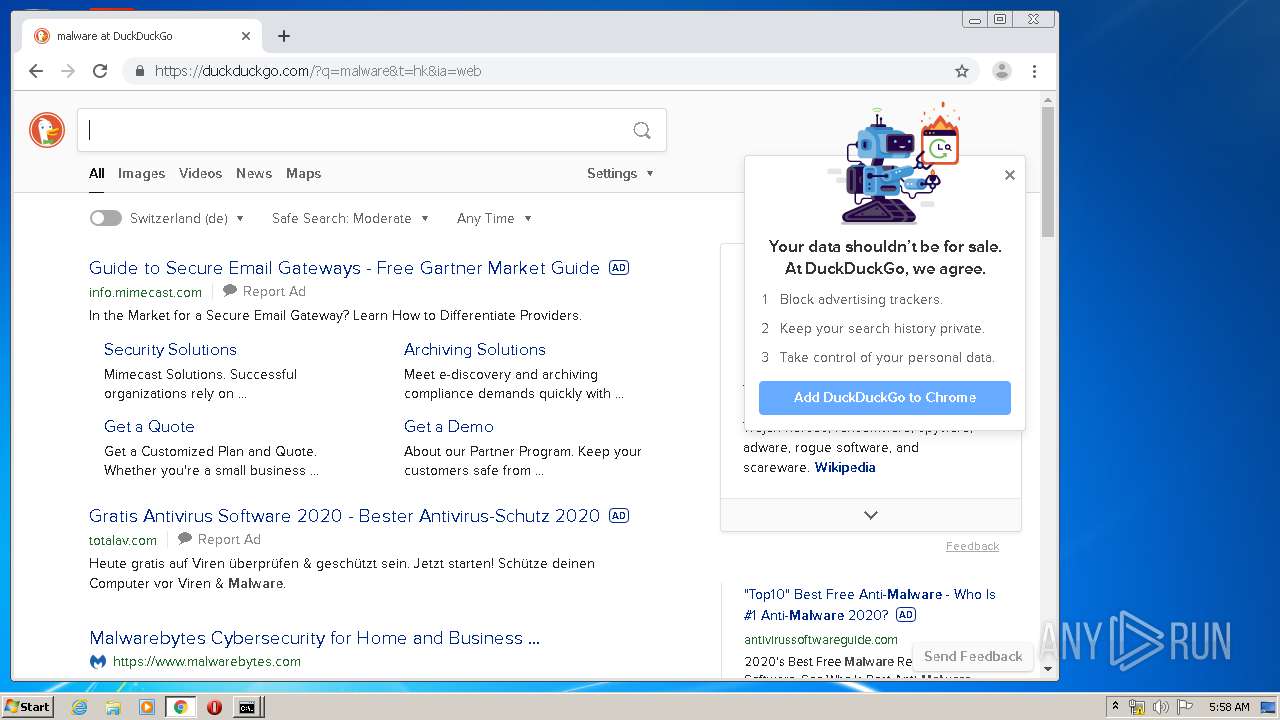
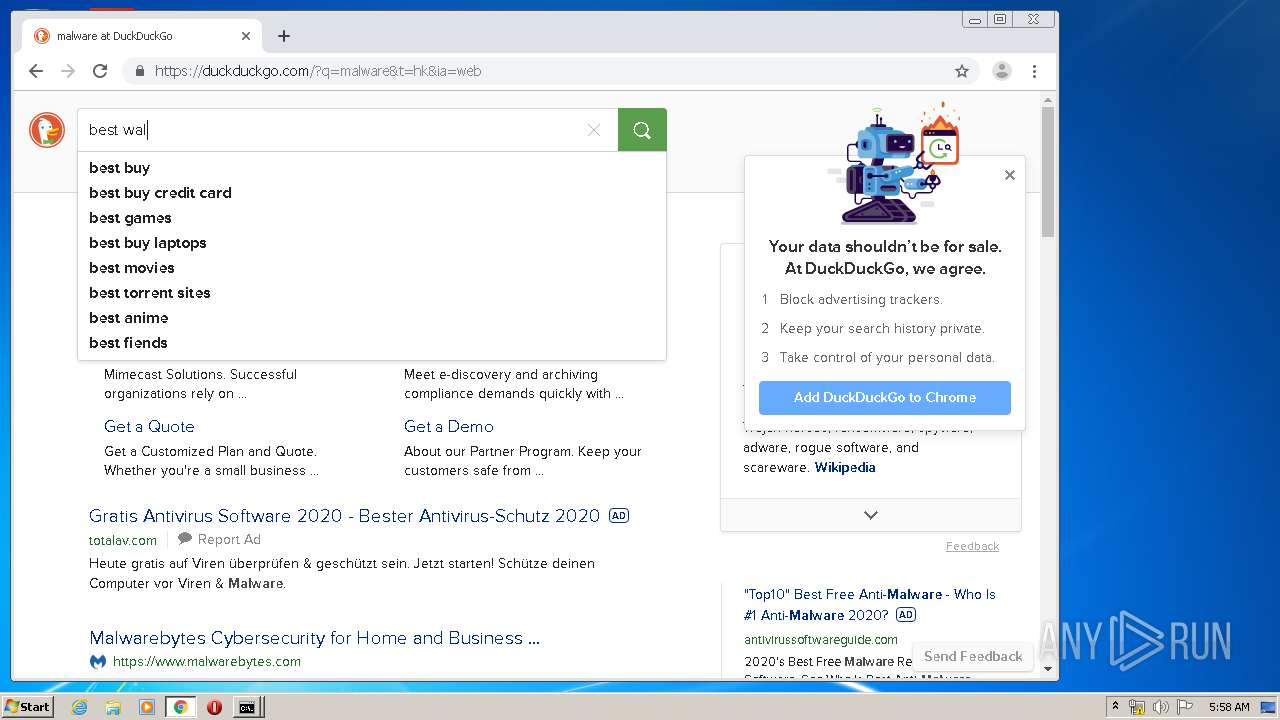
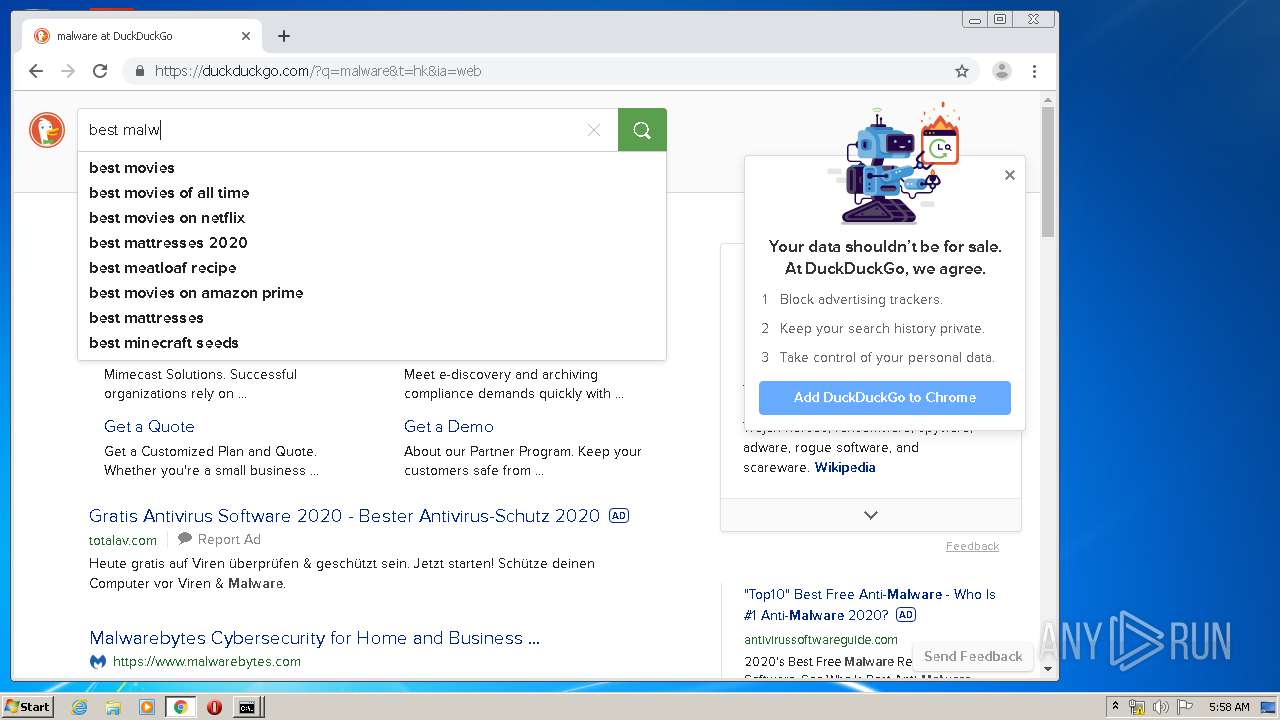
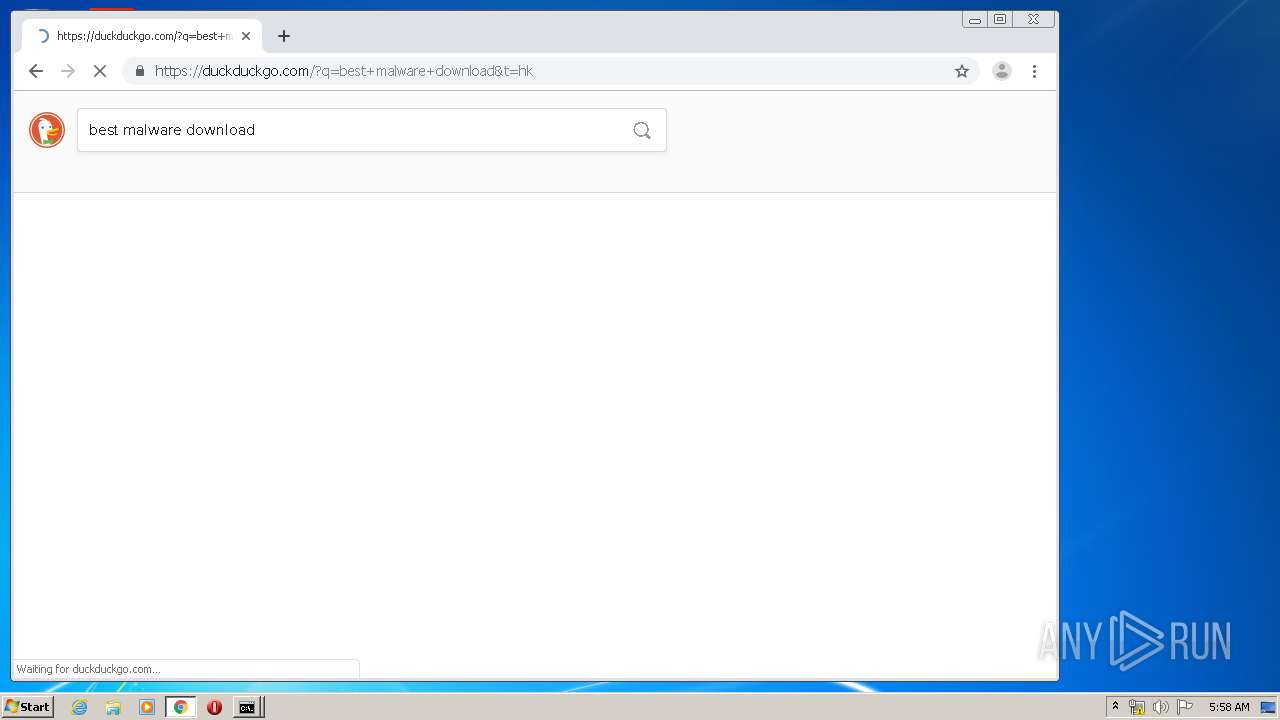
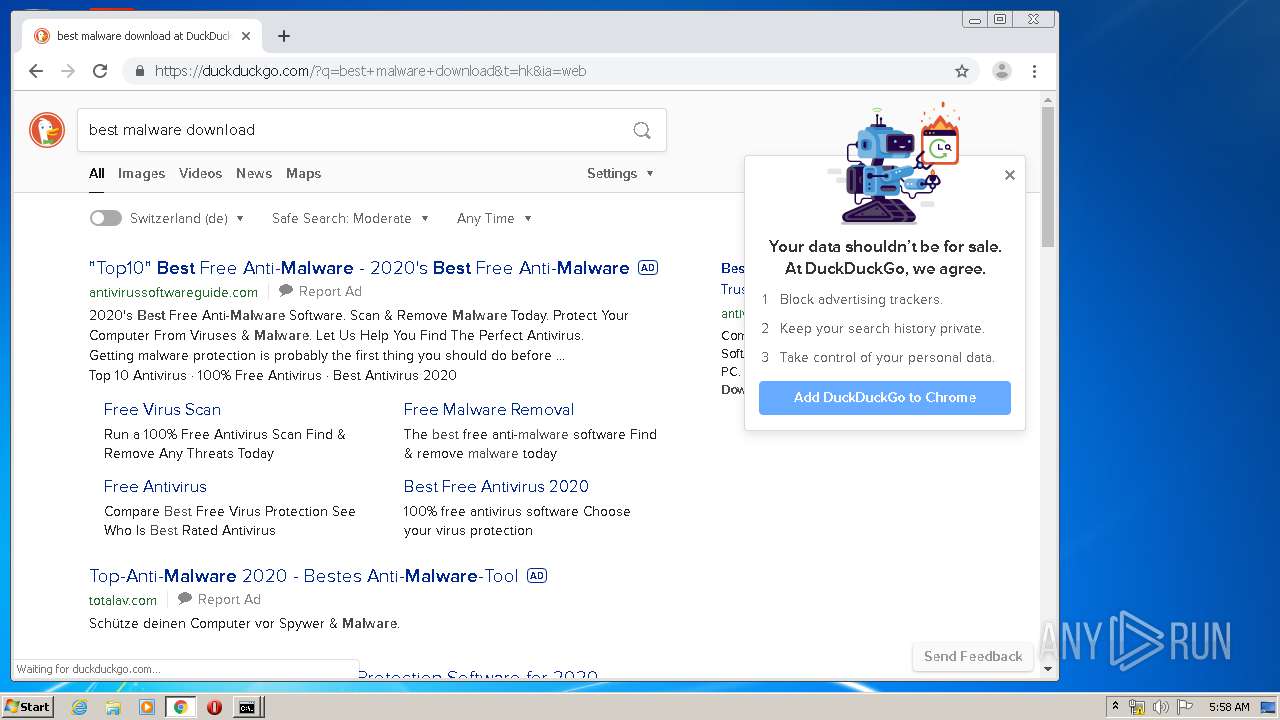
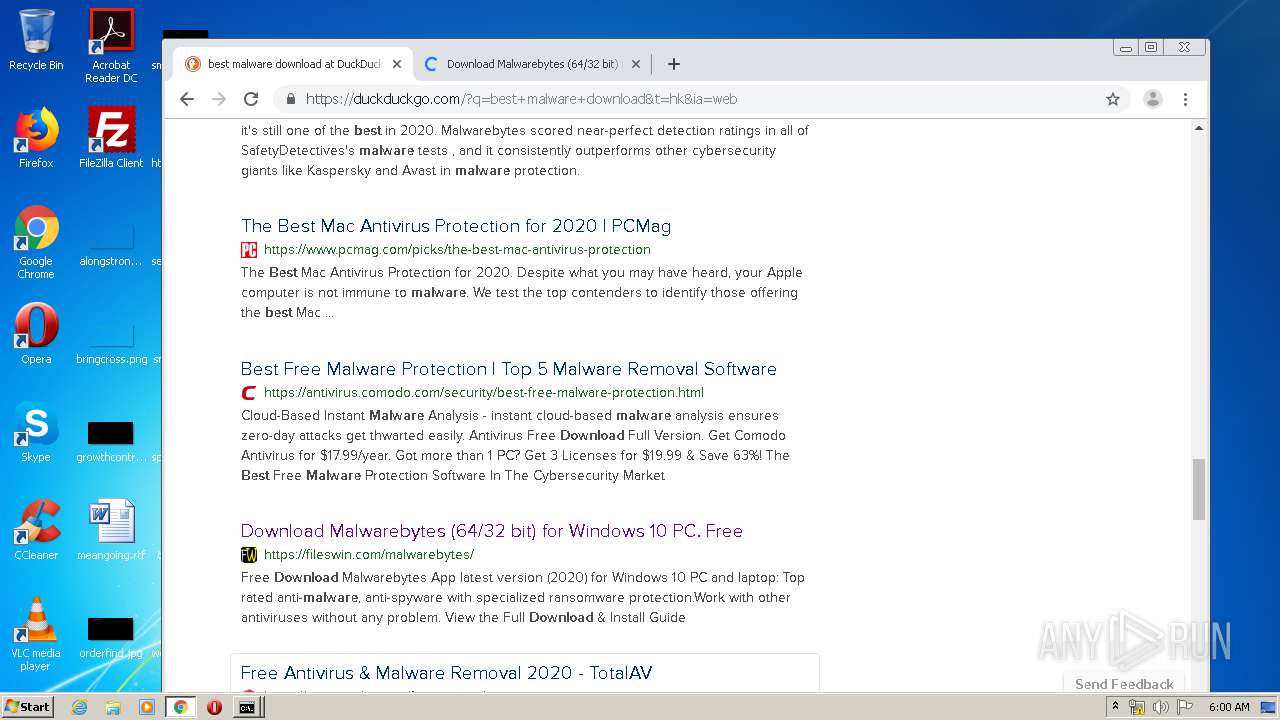
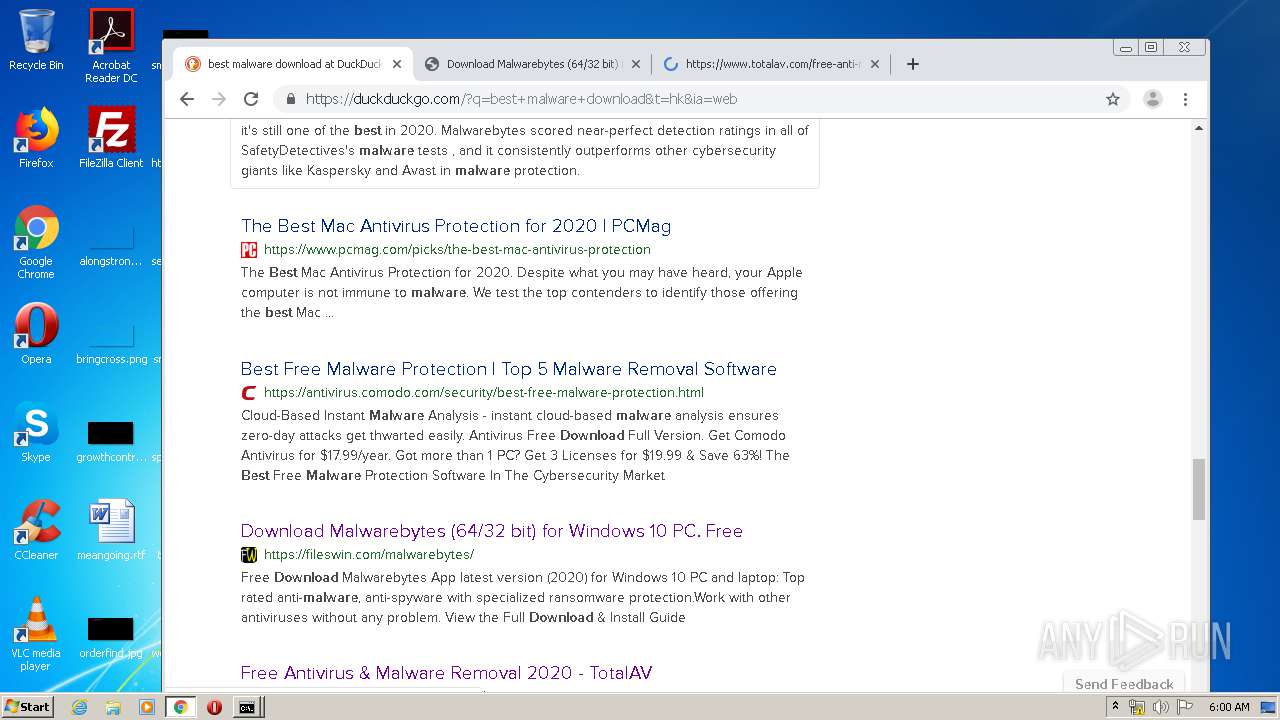
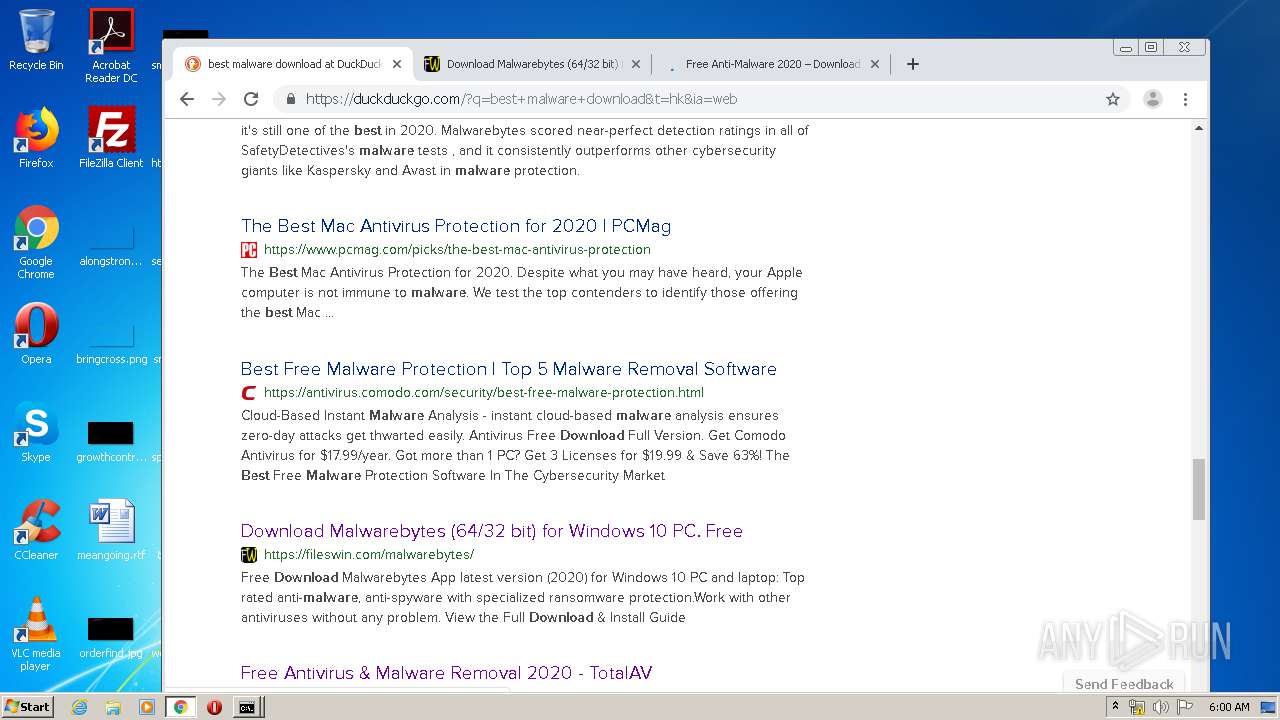
2064 | chrome.exe | GET | 301 | 184.72.104.138:80 | http://dgg.gg/ | US | html | 162 b | suspicious |
2064 | chrome.exe | GET | 301 | 184.72.104.138:80 | http://ddg.gg/ | US | html | 162 b | suspicious |
2064 | chrome.exe | GET | 200 | 74.125.173.170:80 | http://r5---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.230.125.140&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1590814582&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | chrome.exe | 108.177.126.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2064 | chrome.exe | 108.177.126.102:443 | apis.google.com | Google Inc. | US | whitelisted |
2064 | chrome.exe | 173.194.69.94:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2064 | chrome.exe | 173.194.69.100:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
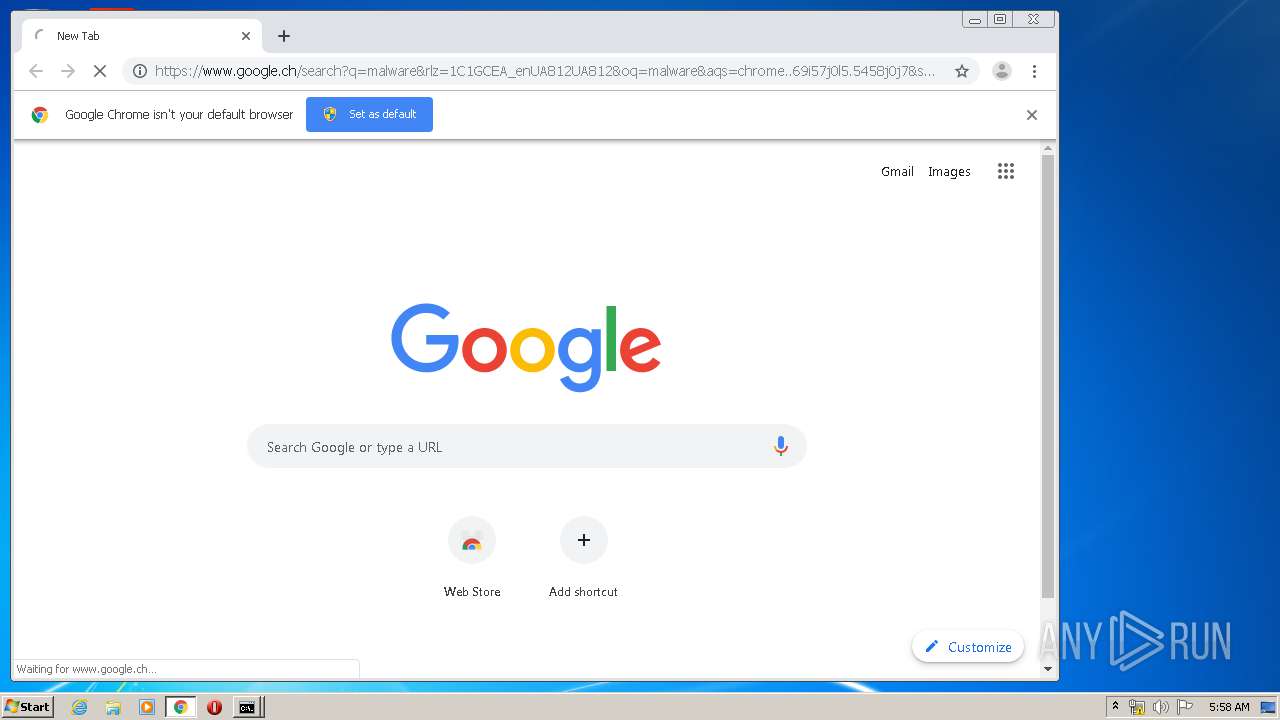
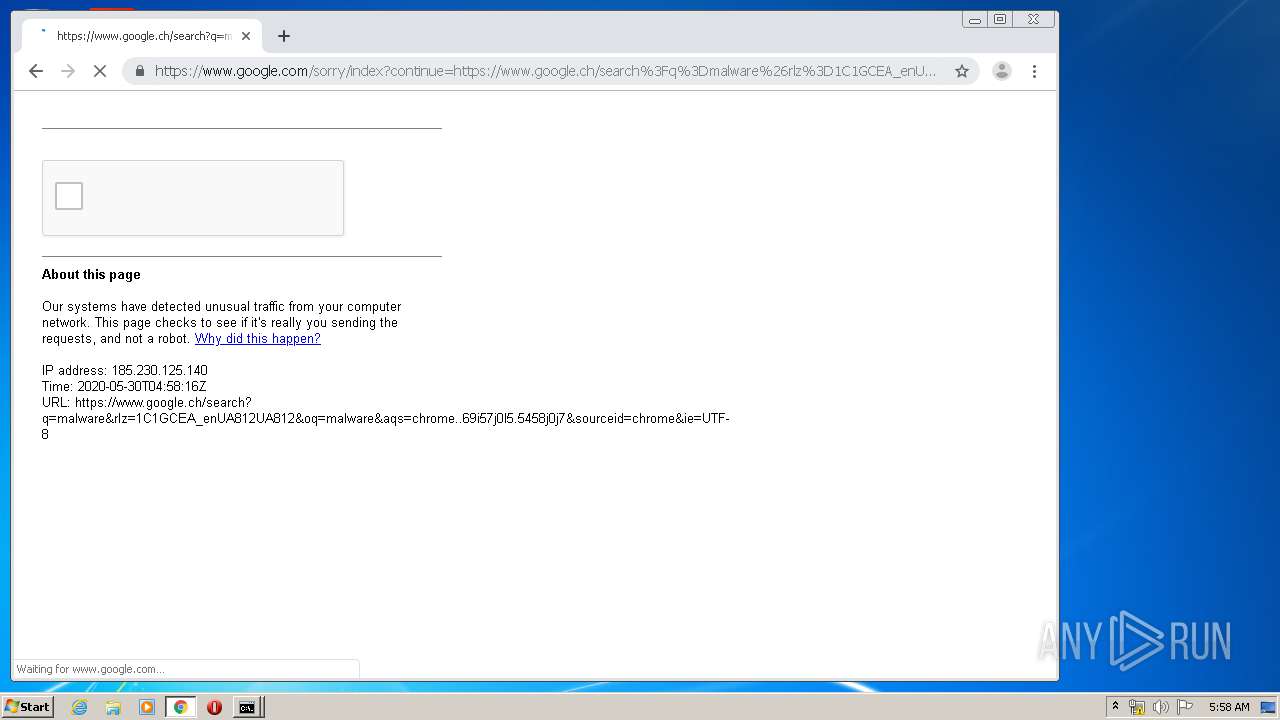
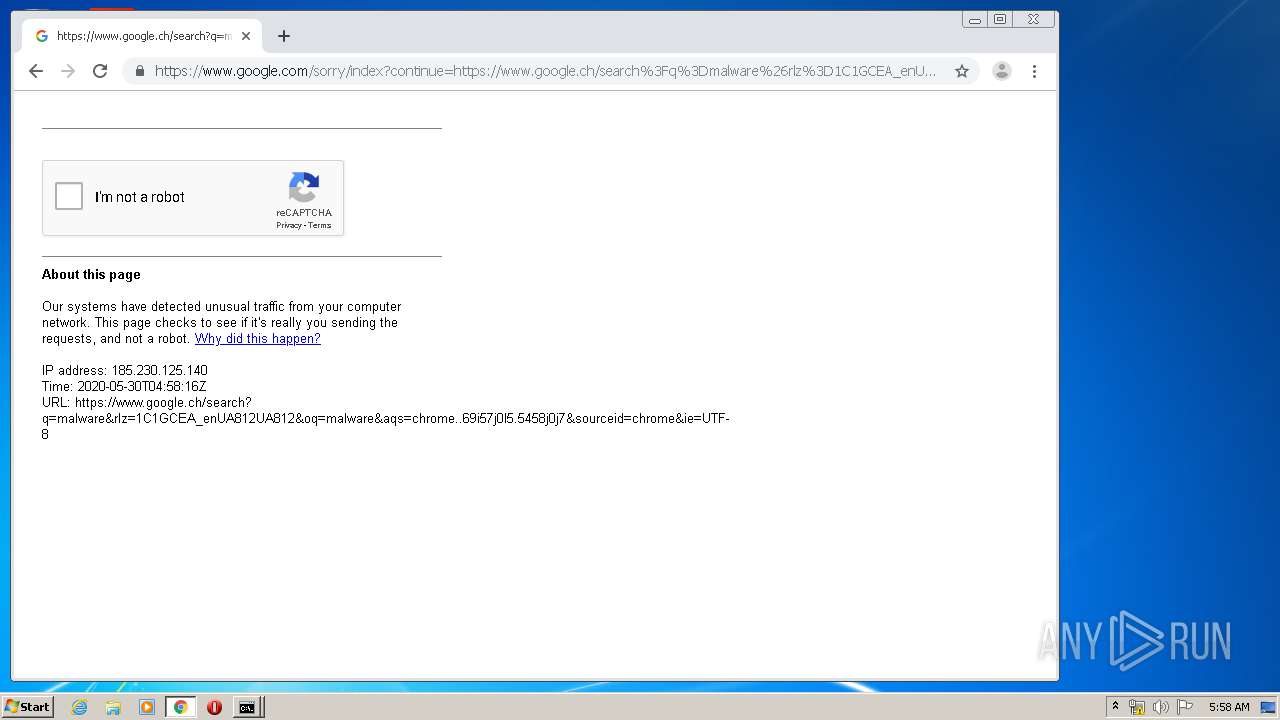
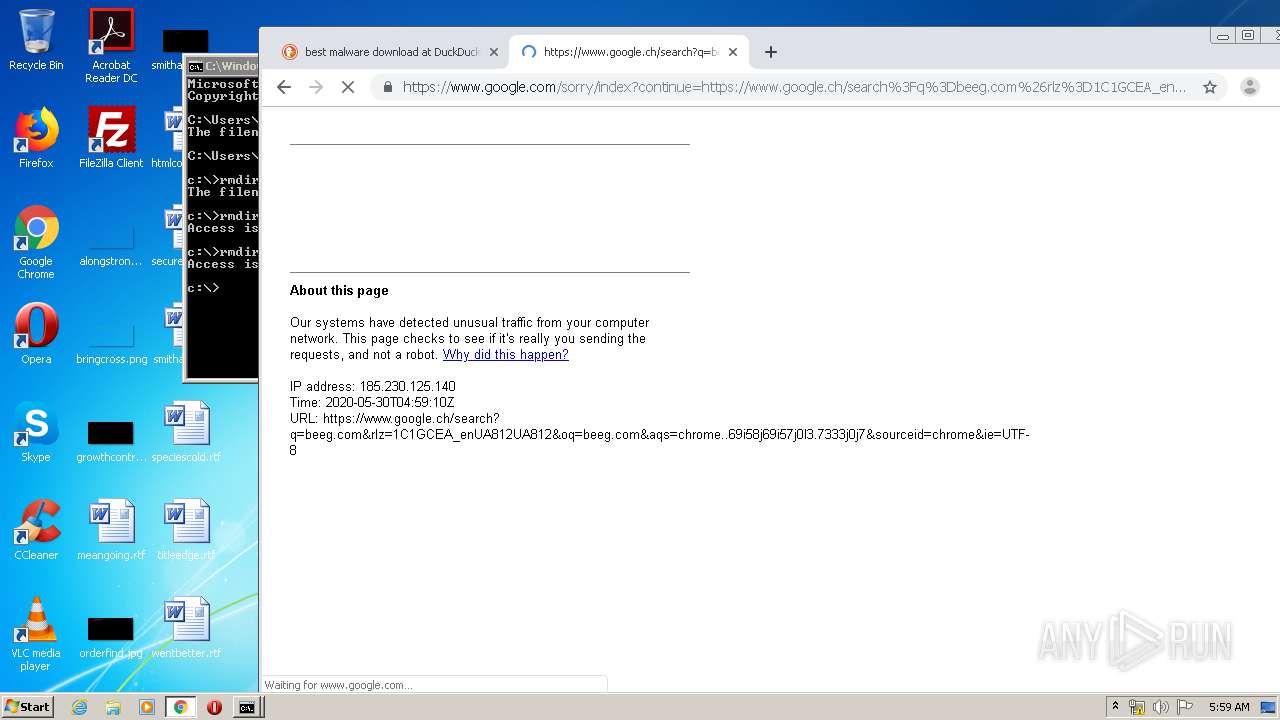
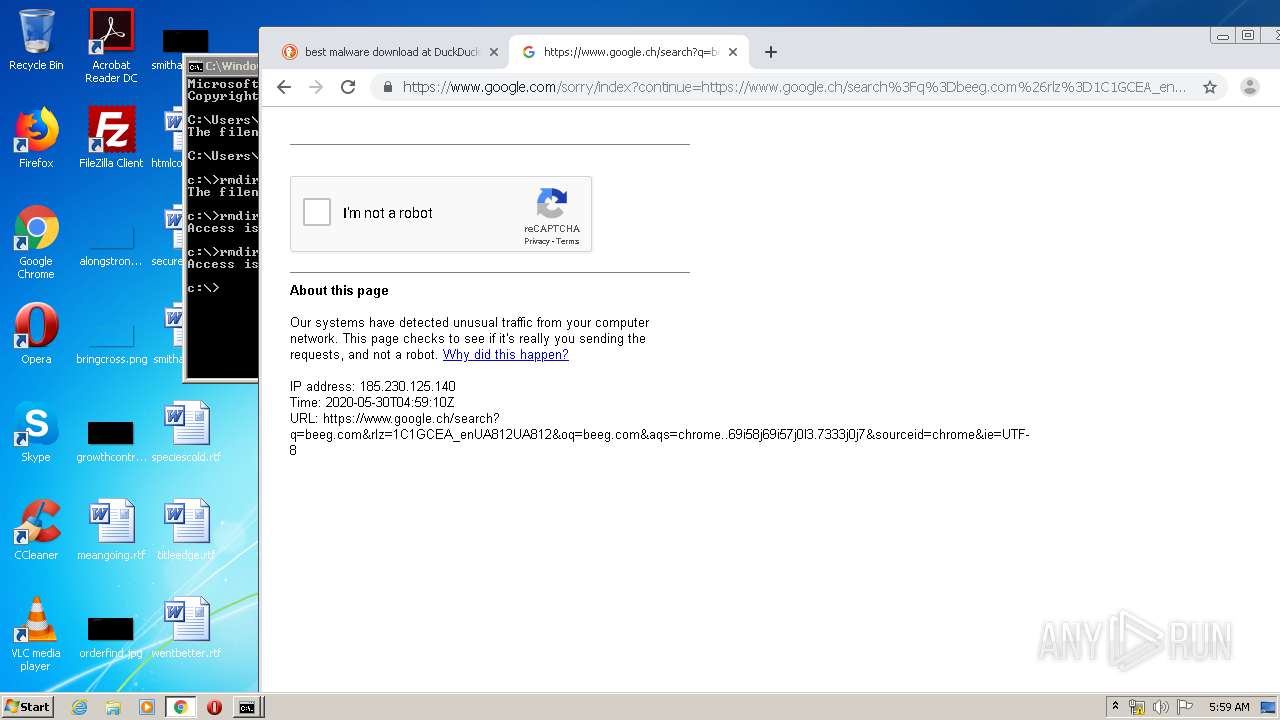
2064 | chrome.exe | 108.177.119.94:443 | www.google.ch | Google Inc. | US | whitelisted |
2064 | chrome.exe | 74.125.128.147:443 | www.google.com | Google Inc. | US | whitelisted |
2064 | chrome.exe | 173.194.69.101:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2064 | chrome.exe | 108.177.126.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 108.177.126.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2064 | chrome.exe | 173.194.79.101:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |