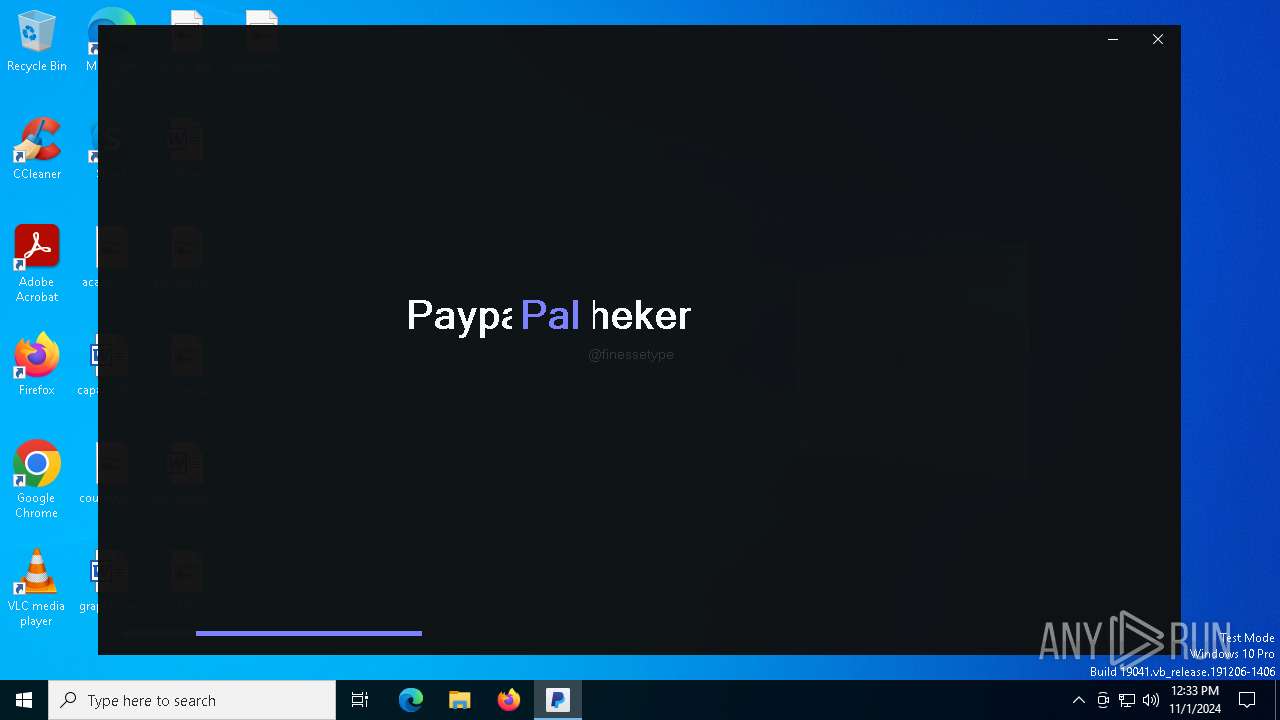
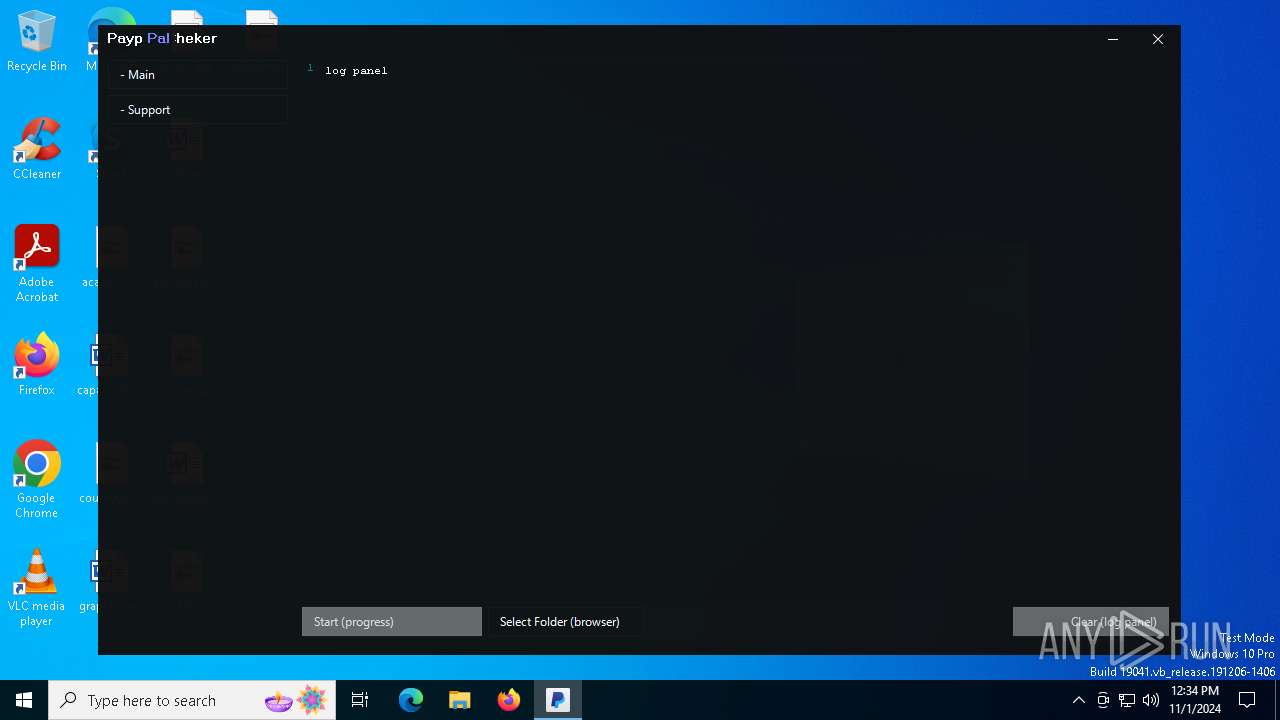
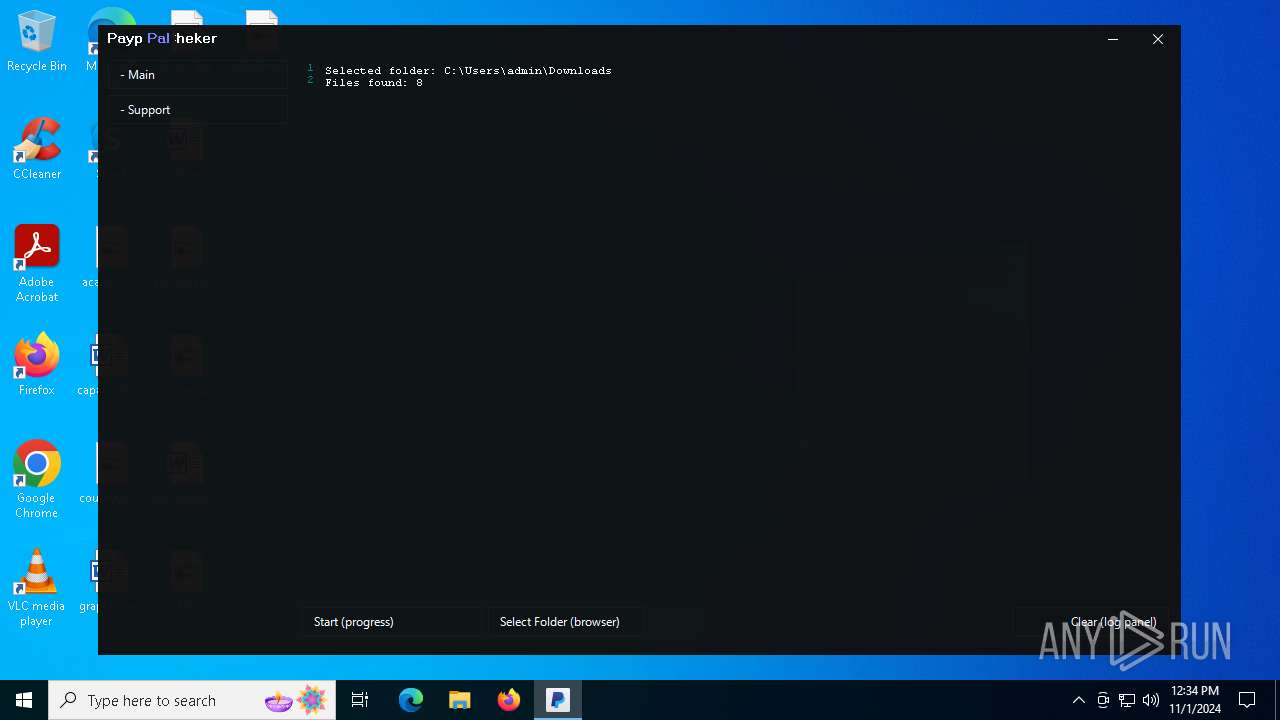
| File name: | PayPal Cheker.exe |
| Full analysis: | https://app.any.run/tasks/2a1ea20f-404b-48e1-9cfd-ed5094c01584 |
| Verdict: | Malicious activity |
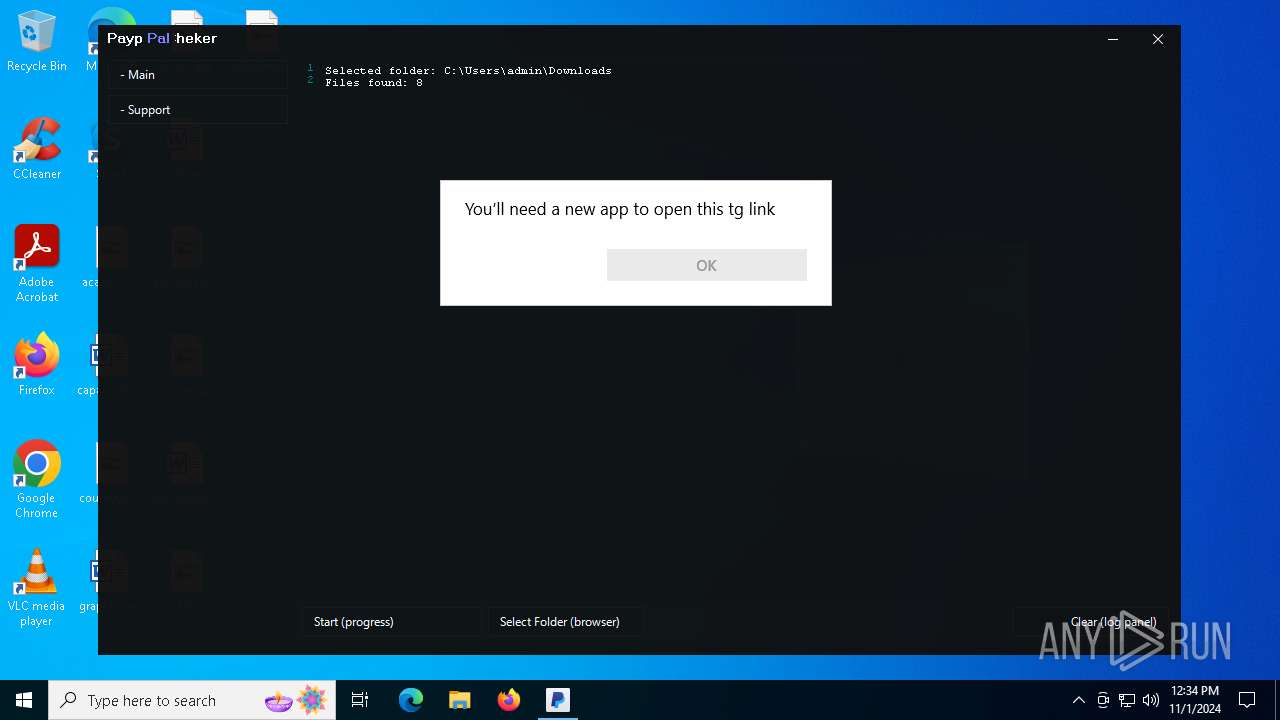
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | November 01, 2024, 12:33:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 9641D0D3D3190E8A13E83A05108071F1 |
| SHA1: | C19ED3DFF349DFEF466D0B6A19F572602B57AF2D |
| SHA256: | 3FB25758BF7FC6A4AA23F3D39F2ECD78ACE62E76EB879BE23D28A21E41F3DE35 |
| SSDEEP: | 24576:G4YpOACIVVzKnb7X9ae8qvAGn8zUltjnYIy4v2XG5j0f0zN+3FAGFc/J:G4YpOACIVV2nb7X9ae8qvAGn8zUltjnR |
MALICIOUS
DARKCRYSTAL has been detected (SURICATA)
- MoUsoCoreWorker.exe (PID: 4236)
Connects to the CnC server
- MoUsoCoreWorker.exe (PID: 4236)
SUSPICIOUS
Reads security settings of Internet Explorer
- PayPal Cheker.exe (PID: 2432)
Executable content was dropped or overwritten
- PayPal Cheker.exe (PID: 2432)
- Checker.exe (PID: 5220)
- AgentprovidercomponentFontdhcp.exe (PID: 5832)
- MoUsoCoreWorker.exe (PID: 4236)
Executing commands from a ".bat" file
- wscript.exe (PID: 6720)
- AgentprovidercomponentFontdhcp.exe (PID: 5832)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6720)
- AgentprovidercomponentFontdhcp.exe (PID: 5832)
There is functionality for taking screenshot (YARA)
- PayPal Cheker.exe (PID: 2432)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 1744)
Connects to the server without a host name
- MoUsoCoreWorker.exe (PID: 4236)
Starts application with an unusual extension
- cmd.exe (PID: 1744)
INFO
Reads the computer name
- PayPal Cheker.exe (PID: 2432)
Reads the machine GUID from the registry
- PayPal Cheker.exe (PID: 2432)
Checks proxy server information
- PayPal Cheker.exe (PID: 2432)
Creates files or folders in the user directory
- PayPal Cheker.exe (PID: 2432)
Disables trace logs
- PayPal Cheker.exe (PID: 2432)
Checks supported languages
- PayPal Cheker.exe (PID: 2432)
- Checker.exe (PID: 5220)
Reads the software policy settings
- PayPal Cheker.exe (PID: 2432)
Create files in a temporary directory
- PayPal Cheker.exe (PID: 2432)
The process uses the downloaded file
- PayPal Cheker.exe (PID: 2432)
Process checks computer location settings
- PayPal Cheker.exe (PID: 2432)
Changes the display of characters in the console
- cmd.exe (PID: 1744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2087:06:02 04:06:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 809984 |
| InitializedDataSize: | 13312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc7b8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 15.0.3.0 |
| ProductVersionNumber: | 15.0.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 15.0.3.0 |
| InternalName: | PayPal Cheker.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | PayPal Cheker.exe |
| ProductName: | - |
| ProductVersion: | 15.0.3.0 |
| AssemblyVersion: | 7.0.3.1 |
Total processes
142
Monitored processes
13
Malicious processes
4
Suspicious processes
2
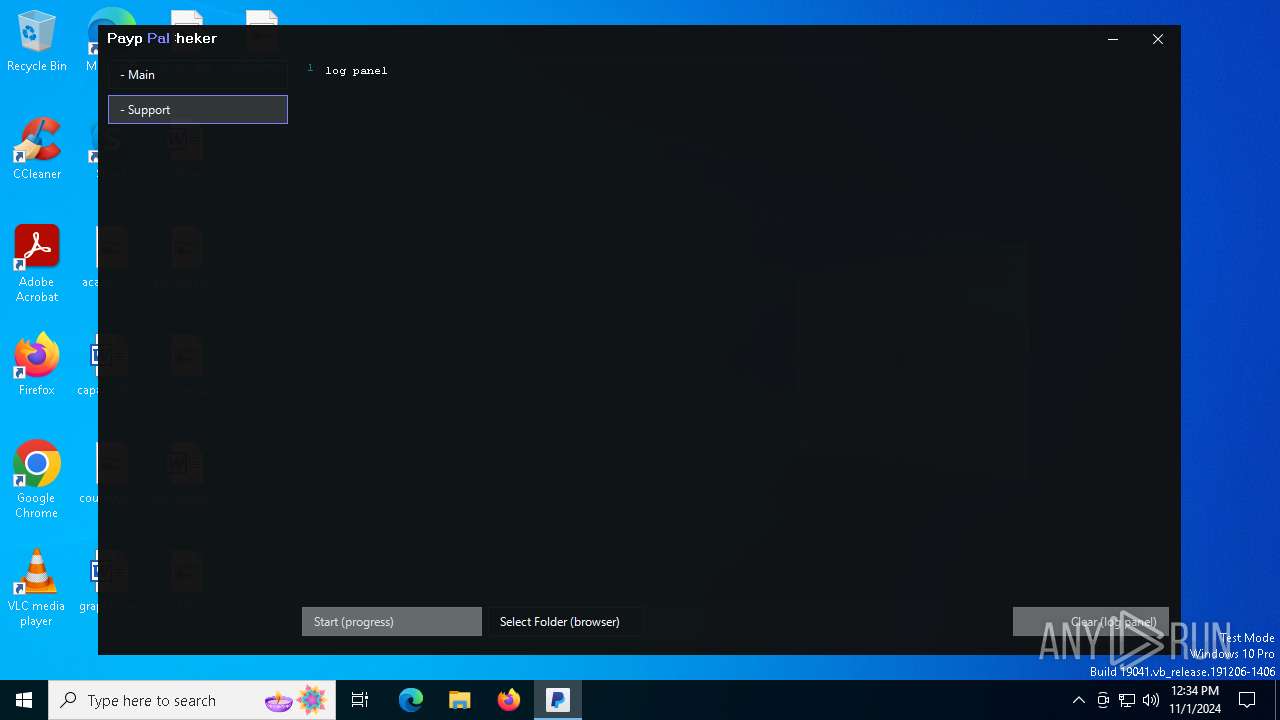
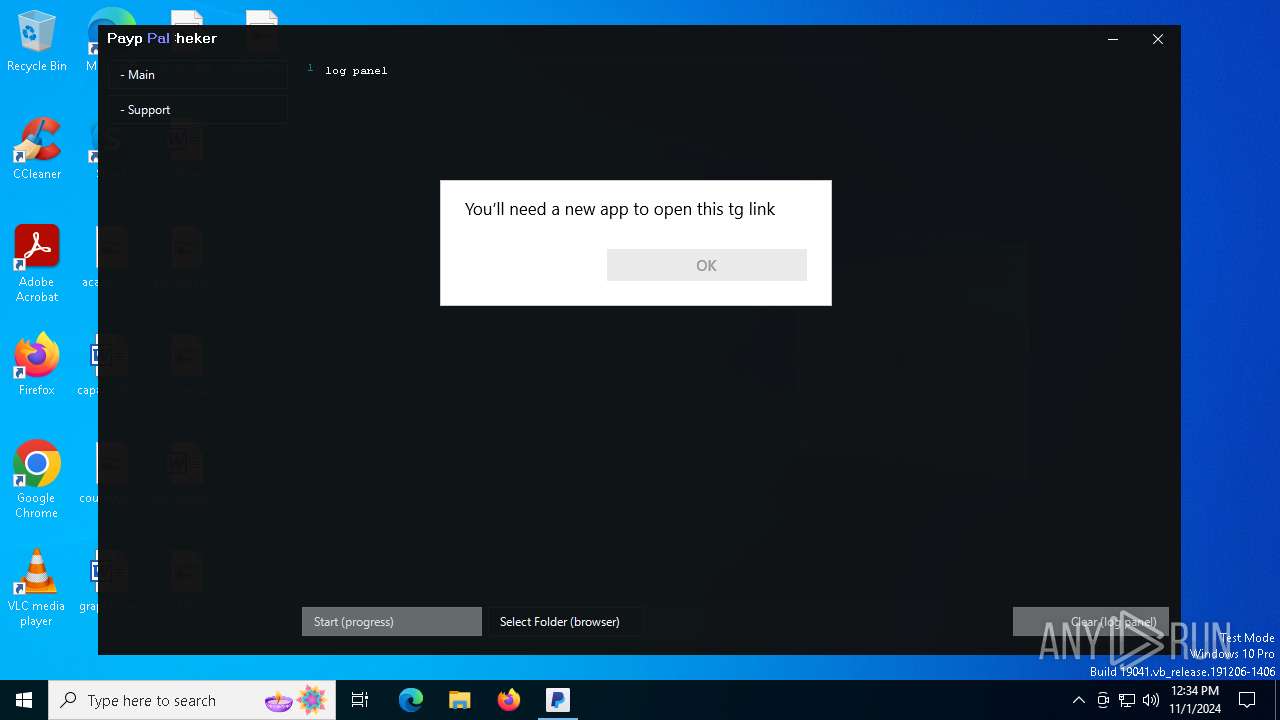
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\2ELWo9J84H.bat" " | C:\Windows\System32\cmd.exe | — | AgentprovidercomponentFontdhcp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Local\Temp\PayPal Cheker.exe" | C:\Users\admin\AppData\Local\Temp\PayPal Cheker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 15.0.3.0 Modules
| |||||||||||||||
| 4236 | "C:\Users\Default\Documents\My Pictures\MoUsoCoreWorker.exe" | C:\Users\Default\Pictures\MoUsoCoreWorker.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 16.10.31418.88 Modules
| |||||||||||||||
| 4312 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5220 | "C:\Users\admin\AppData\Roaming\PayPalCheker\Checker.exe" | C:\Users\admin\AppData\Roaming\PayPalCheker\Checker.exe | PayPal Cheker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5516 | C:\WINDOWS\system32\cmd.exe /c ""C:\ChainServerPerfdlldhcp\D54KT32uo.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5832 | "C:\ChainServerPerfdlldhcp/AgentprovidercomponentFontdhcp.exe" | C:\ChainServerPerfdlldhcp\AgentprovidercomponentFontdhcp.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 16.10.31418.88 Modules
| |||||||||||||||
| 6308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 565
Read events
7 520
Write events
45
Delete events
0
Modification events
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2432) PayPal Cheker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\PayPal Cheker_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
59
Suspicious files
28
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5220 | Checker.exe | C:\ChainServerPerfdlldhcp\D54KT32uo.bat | text | |
MD5:6249A40F53D81ED66103CC0A7527BFF0 | SHA256:0C639B87A33BE4E5B6C0EFE8FE0F0AFF5BEF49C250DBBA9399280CB04FA5CBE2 | |||
| 5220 | Checker.exe | C:\ChainServerPerfdlldhcp\rE4aALXnoNUh7Fe.vbe | binary | |
MD5:36883979031DC58B33A0758B7BB4A049 | SHA256:B7630B161D1FAB73C8174F0486D32BD09DFF31E28DCBC592785E31DF707B808A | |||
| 2432 | PayPal Cheker.exe | C:\Users\admin\AppData\Roaming\PayPalCheker\Checker.exe | executable | |
MD5:A670047C394E6D25294BAD11BD9C641B | SHA256:02D1C49FFC02B1BE87ABF02A2840BA60BFFC89438DFE3F3178DD8CB8FFE095C3 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\SCRndKLq.log | executable | |
MD5:16B480082780CC1D8C23FB05468F64E7 | SHA256:7A080D8BD178EC02C7F39F7F941479074C450C4FDD8E963C993D2FB5537C7708 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\HftPHUKK.log | executable | |
MD5:9E910782CA3E88B3F87826609A21A54E | SHA256:3B311986251EE5A303671108AFBAF43E0255C4CAE1C26CC9600BB0C7D22D3864 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\OErerekr.log | executable | |
MD5:F4B38D0F95B7E844DD288B441EBC9AAF | SHA256:AAB95596475CA74CEDE5BA50F642D92FA029F6F74F6FAEAE82A9A07285A5FB97 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\qzmzvcLo.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
| 5220 | Checker.exe | C:\ChainServerPerfdlldhcp\AgentprovidercomponentFontdhcp.exe | executable | |
MD5:939D73F313A52187CA51C5D8B447B636 | SHA256:27F3F440BB27C4052FDF41319D7BDB2E09B3A1AD84D7A7CBB92AB7C7688201C6 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\UwUDUKpg.log | executable | |
MD5:A4F19ADB89F8D88DBDF103878CF31608 | SHA256:D0613773A711634434DB30F2E35C6892FF54EBEADF49CD254377CAECB204EAA4 | |||
| 5832 | AgentprovidercomponentFontdhcp.exe | C:\Users\admin\Desktop\NYWokzPz.log | executable | |
MD5:2E116FC64103D0F0CF47890FD571561E | SHA256:25EEEA99DCA05BF7651264FA0C07E0E91D89E0DA401C387284E9BE9AFDF79625 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
40
DNS requests
23
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4236 | MoUsoCoreWorker.exe | POST | 200 | 80.87.196.99:80 | http://80.87.196.99/cdn8/SqlTraffic/Default/6/Dumpsqldownloads7/pipeLongpoll0/Mariadb0Proton/mariadb/5Process/cpu/http4uploads/Linux/pipeGeoProcessorTrackdatalife.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2432 | PayPal Cheker.exe | 193.109.246.100:443 | antiloxss.usite.pro | Compubyte Limited | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
antiloxss.usite.pro |
| whitelisted |
finessetypy.ucoz.site |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4236 | MoUsoCoreWorker.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4236 | MoUsoCoreWorker.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4236 | MoUsoCoreWorker.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible DarkCrystal Rat Encrypted Connection |
4236 | MoUsoCoreWorker.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Exfiltration (POST) |
4236 | MoUsoCoreWorker.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Exfiltration (POST) |