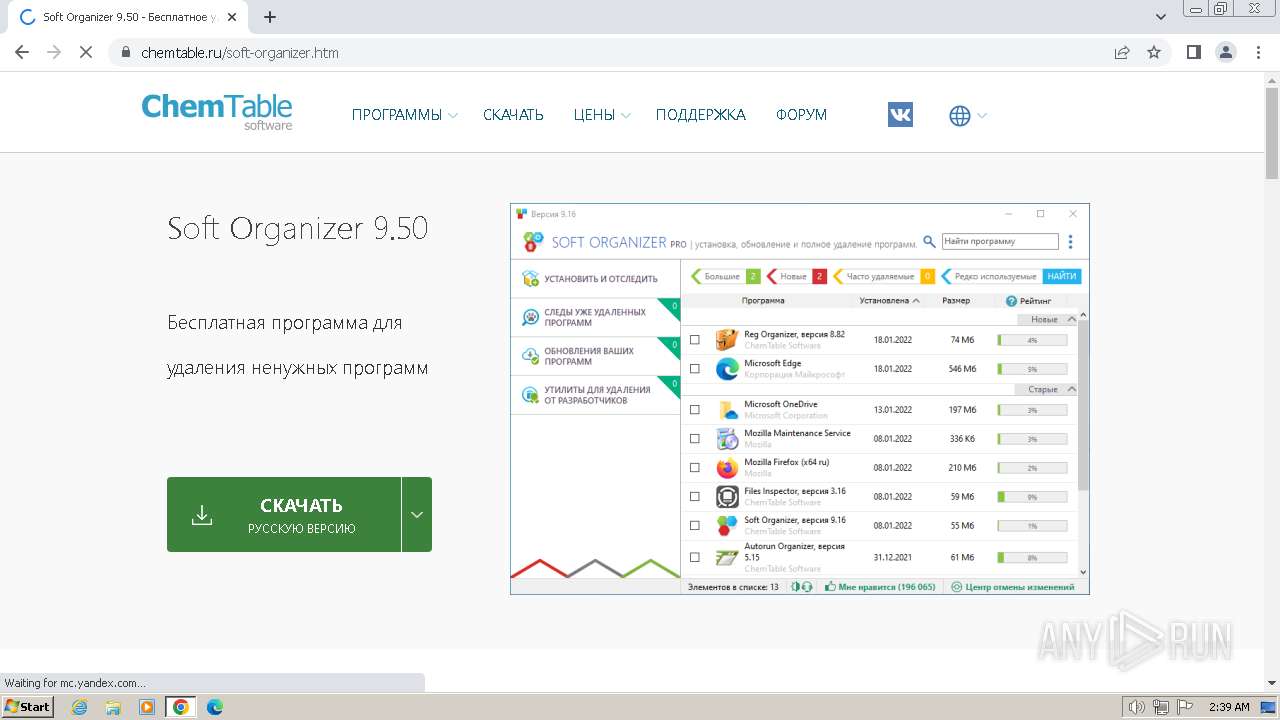
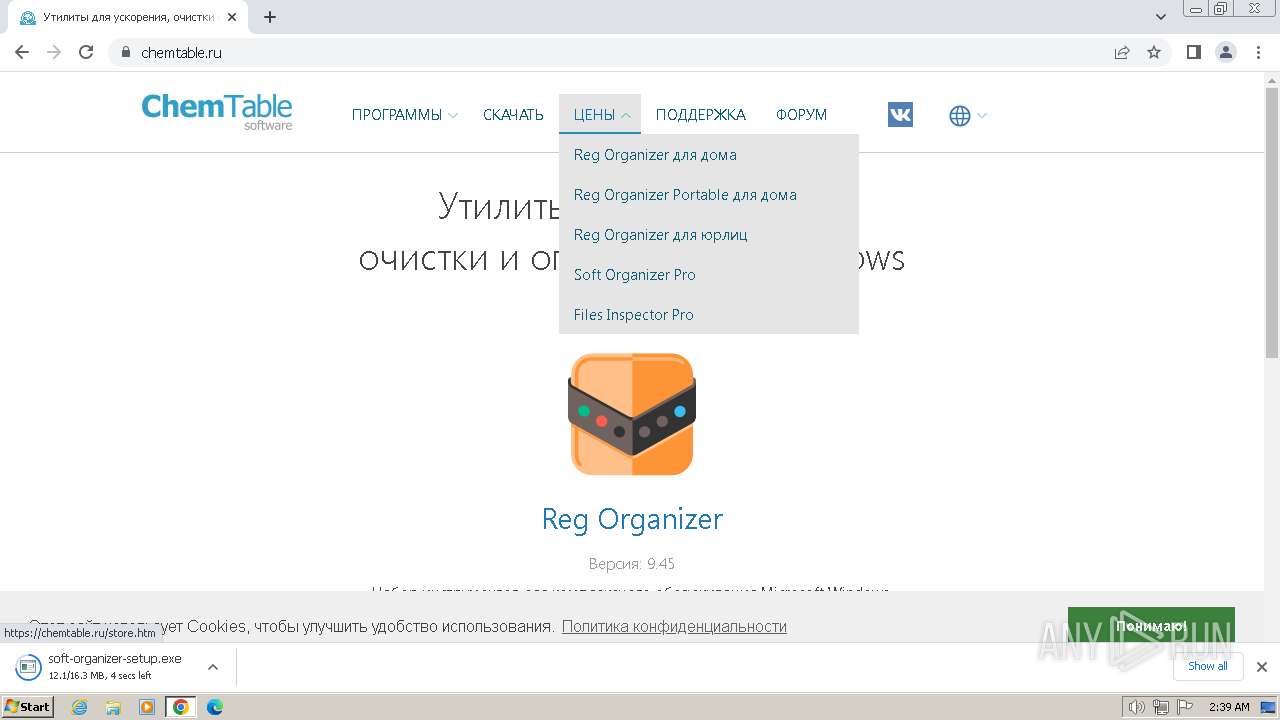
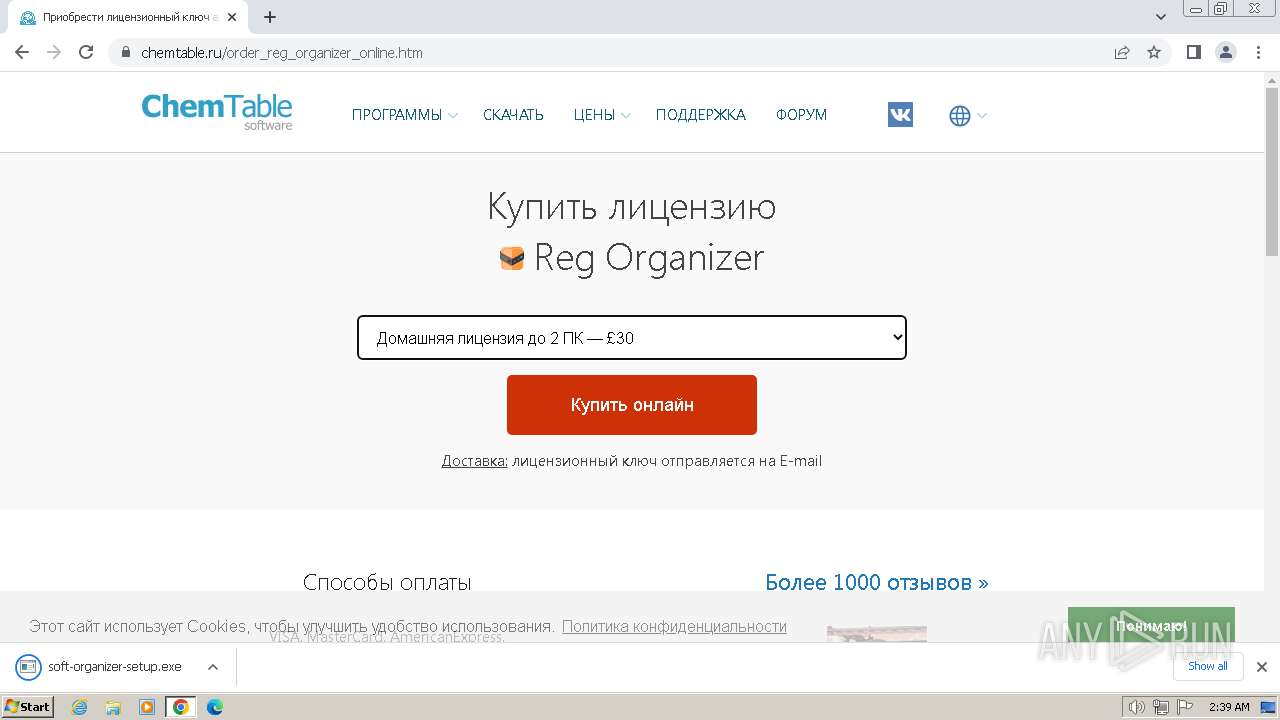
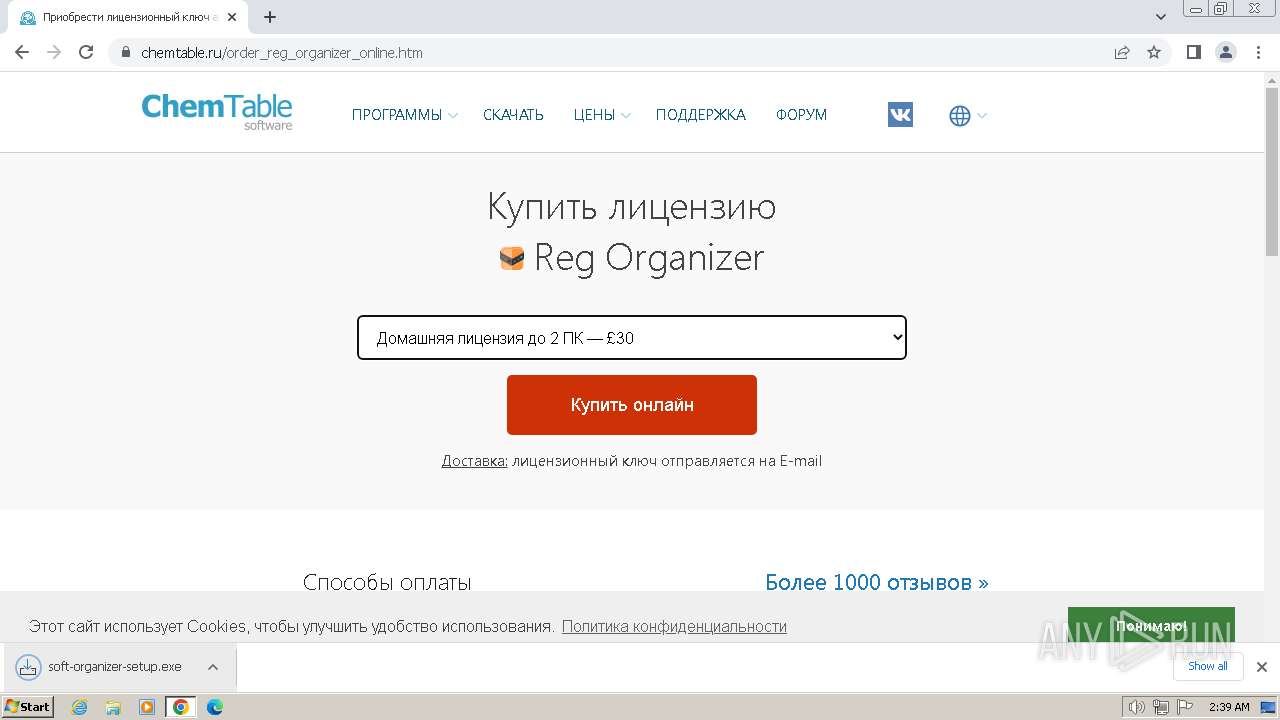
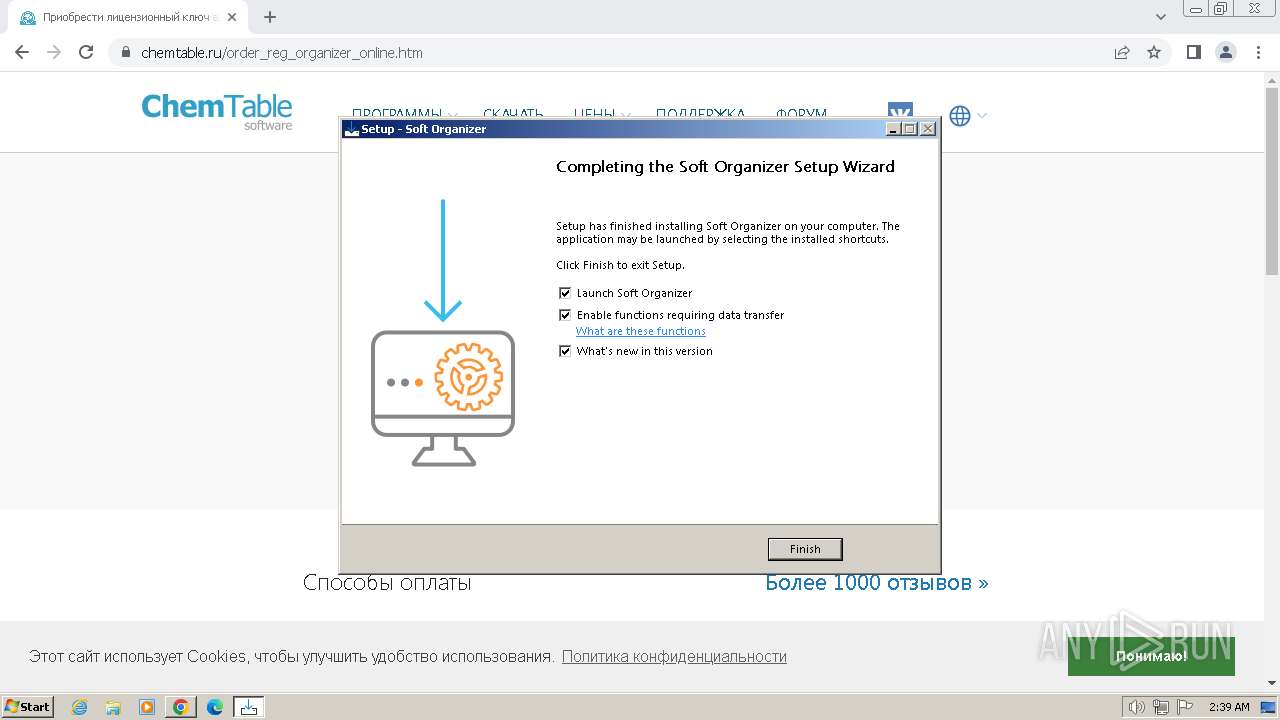
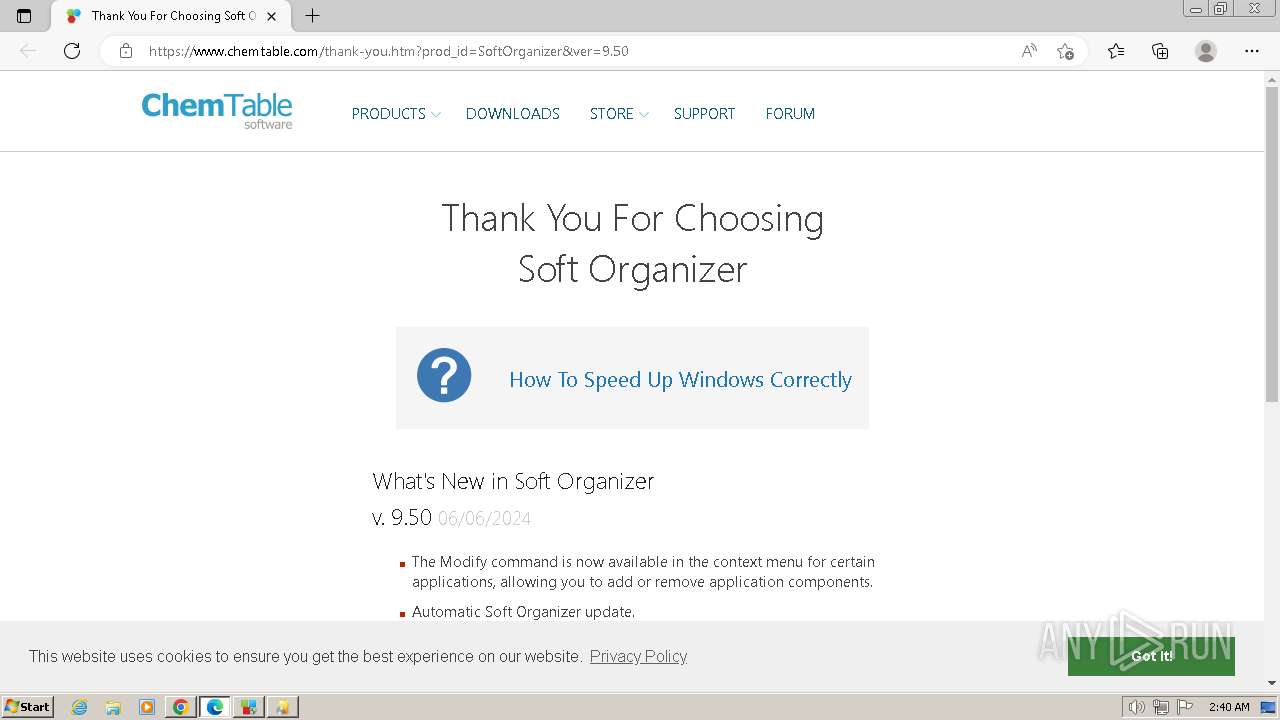
| URL: | chemtable.ru |
| Full analysis: | https://app.any.run/tasks/3db2c82c-0c69-47de-8909-c2e0ad2ef0b6 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2024, 01:39:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 37087E0D12B30DF9A91CDC68629F2F16 |
| SHA1: | 8476F7B4BF0A33416B9507A94A0FDB45148BAD85 |
| SHA256: | 3F9C7B3FB6DA81FD5DC9F928014436C6EAF0EC39AB50A0C47D5B91FC37A52EDB |
| SSDEEP: | 3:Vn:V |
MALICIOUS
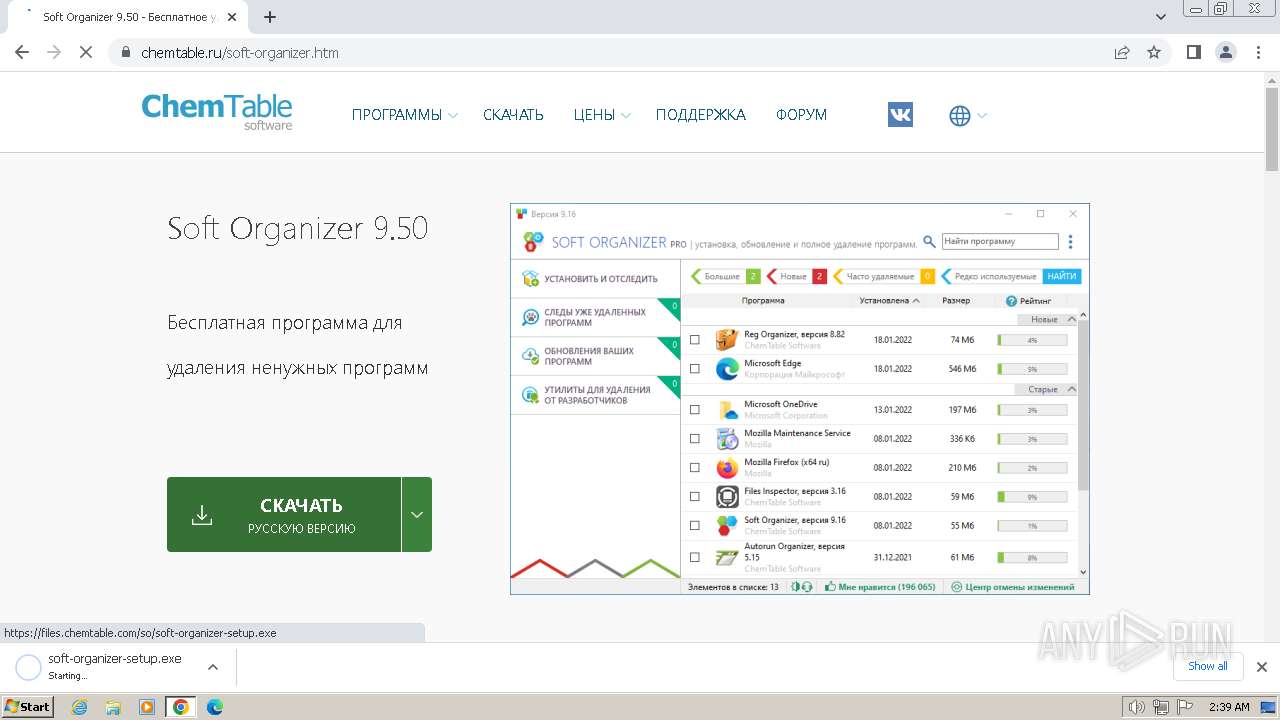
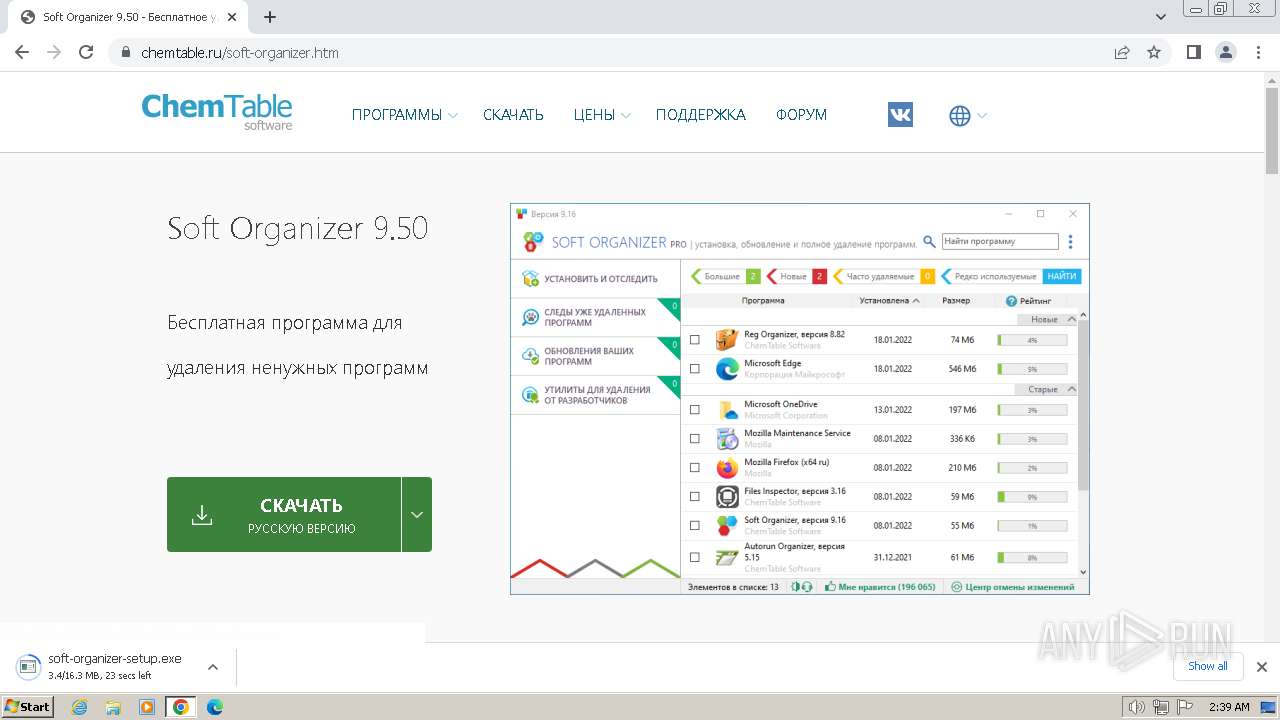
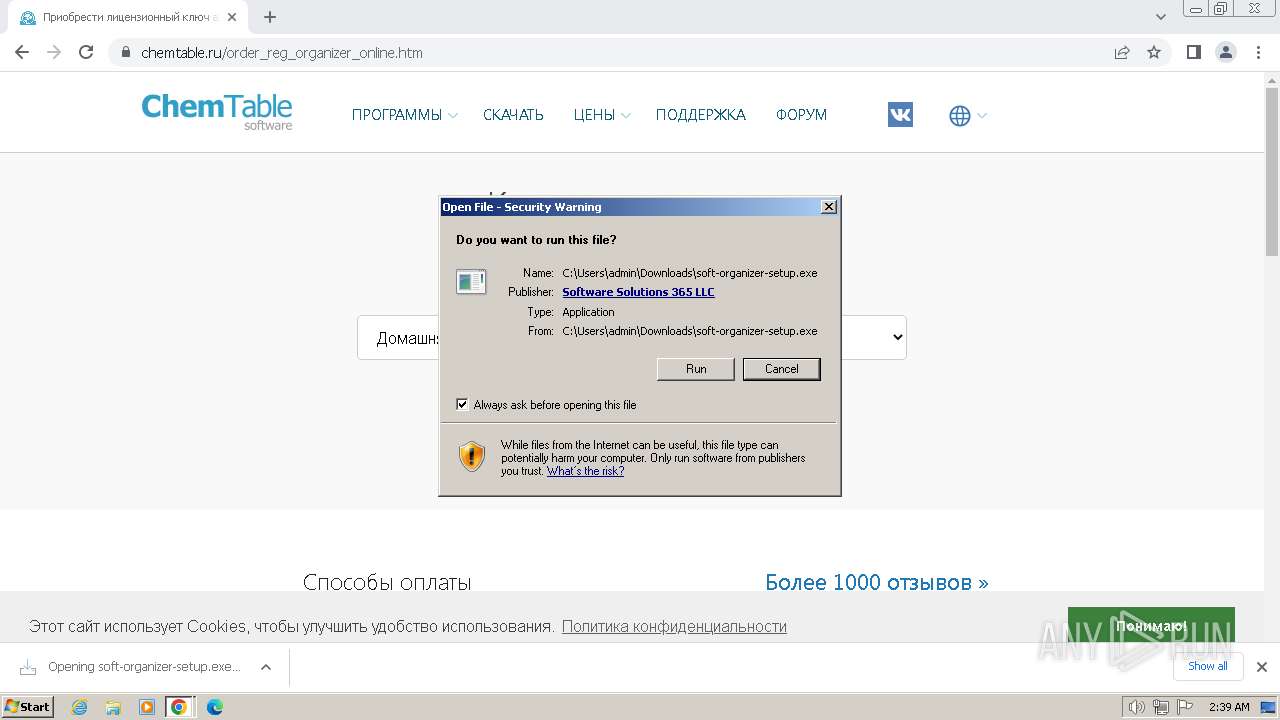
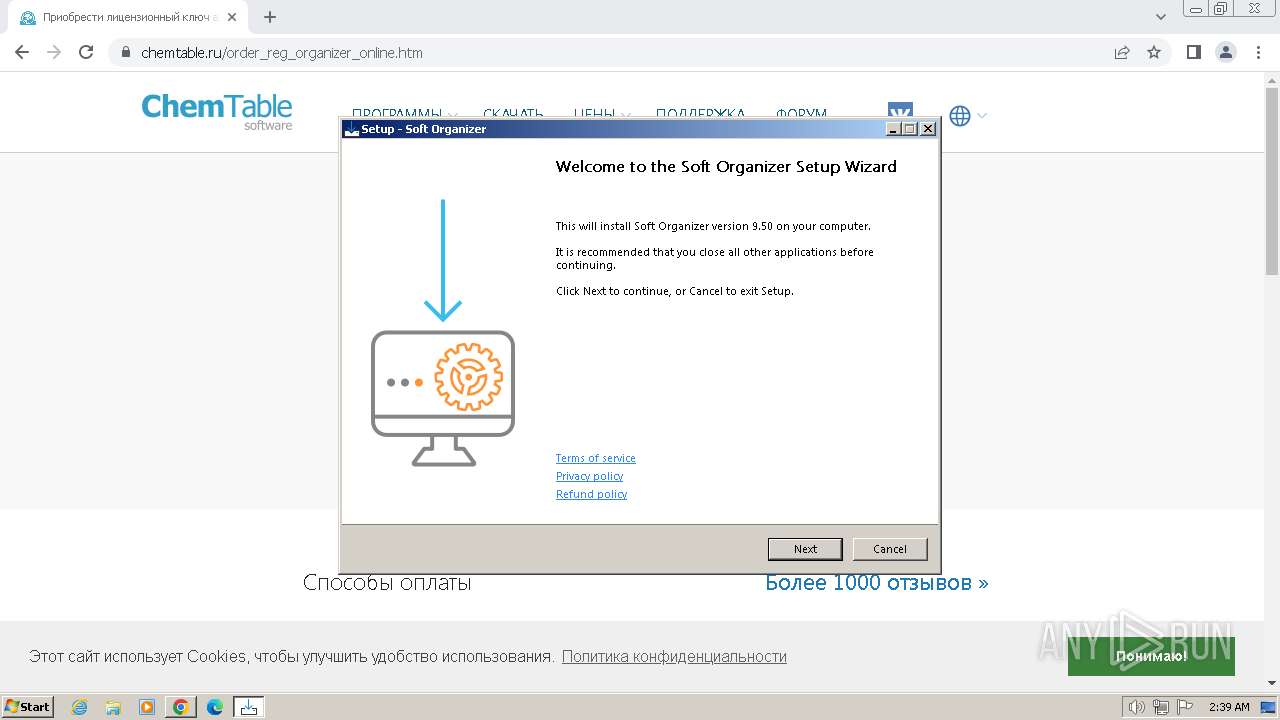
Drops the executable file immediately after the start
- soft-organizer-setup.exe (PID: 1588)
- soft-organizer-setup.exe (PID: 2996)
- soft-organizer-setup.tmp (PID: 3564)
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 596)
- msiexec.exe (PID: 3020)
- OSE.EXE (PID: 3864)
- msiexec.exe (PID: 3680)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 3412)
Registers / Runs the DLL via REGSVR32.EXE
- soft-organizer-setup.tmp (PID: 3564)
Actions looks like stealing of personal data
- SoftOrganizer.exe (PID: 3352)
Changes the autorun value in the registry
- msiexec.exe (PID: 1624)
SUSPICIOUS
Executable content was dropped or overwritten
- soft-organizer-setup.exe (PID: 2996)
- soft-organizer-setup.tmp (PID: 3564)
- Setup.exe (PID: 2280)
- soft-organizer-setup.exe (PID: 1588)
- OSE.EXE (PID: 3864)
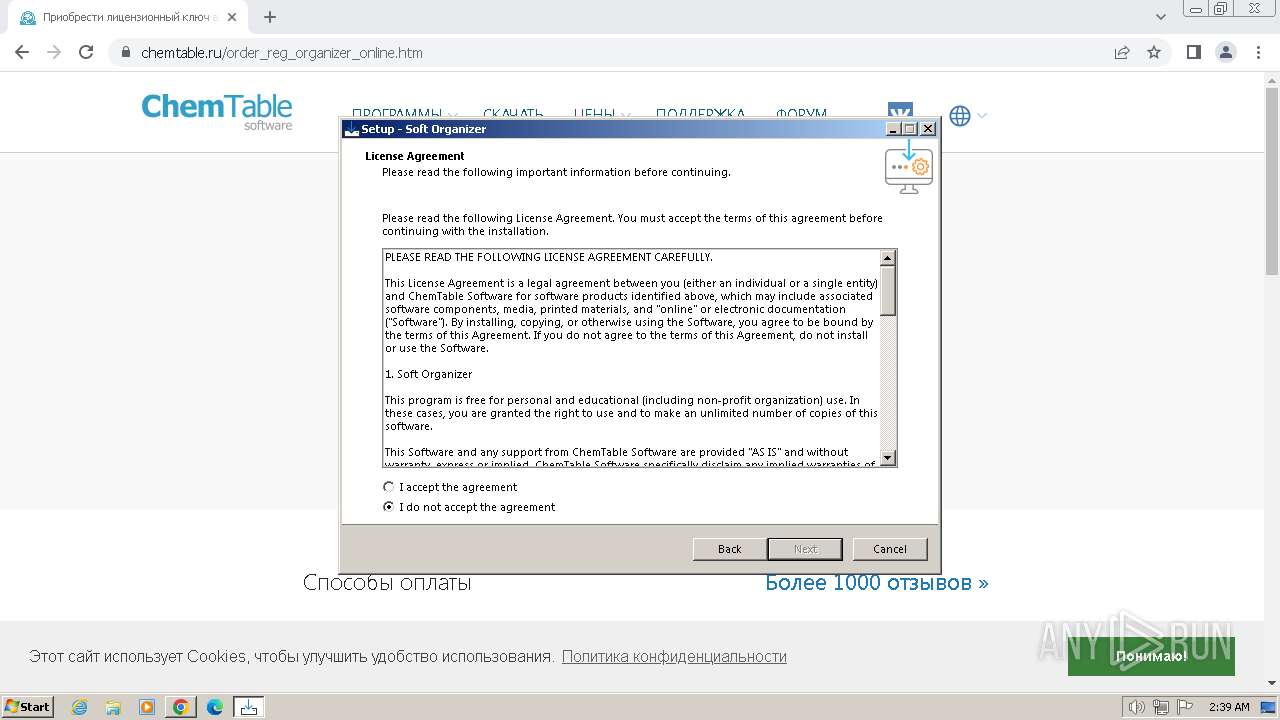
Reads the Windows owner or organization settings
- soft-organizer-setup.tmp (PID: 3564)
- msiexec.exe (PID: 3020)
Reads the Internet Settings
- soft-organizer-setup.tmp (PID: 3564)
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1412)
- SoftOrganizer.exe (PID: 3352)
- msiexec.exe (PID: 3020)
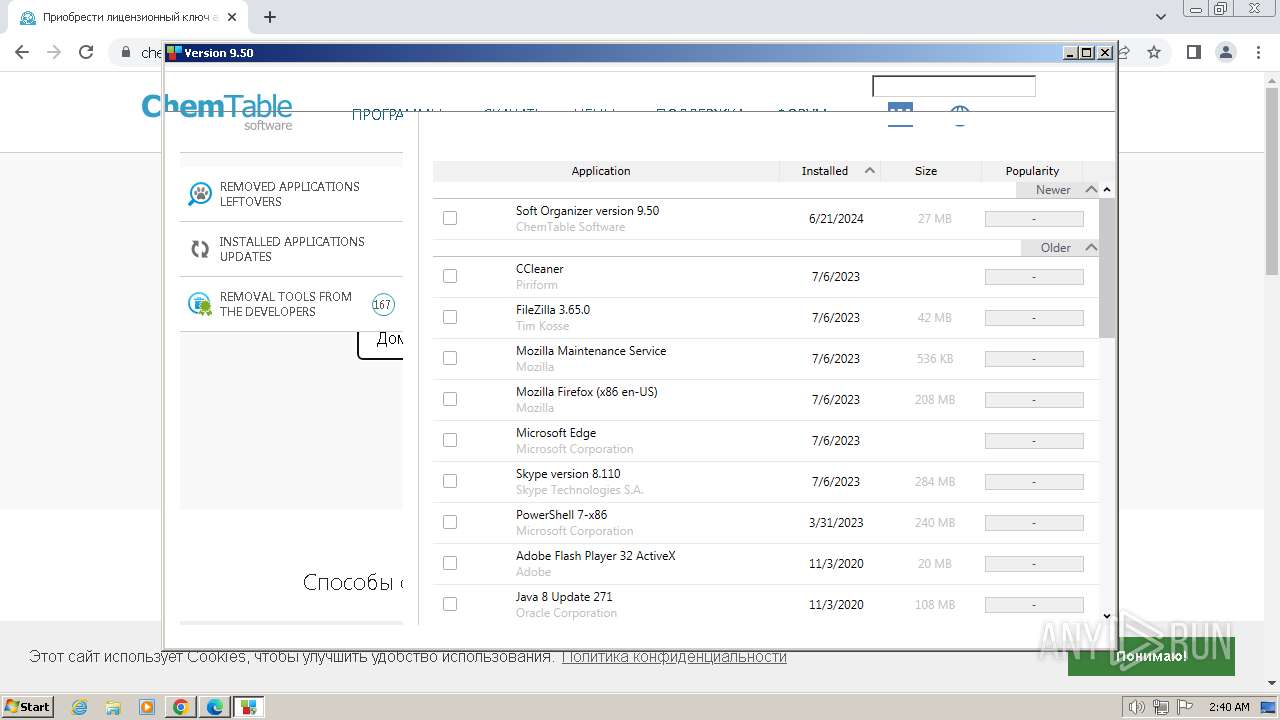
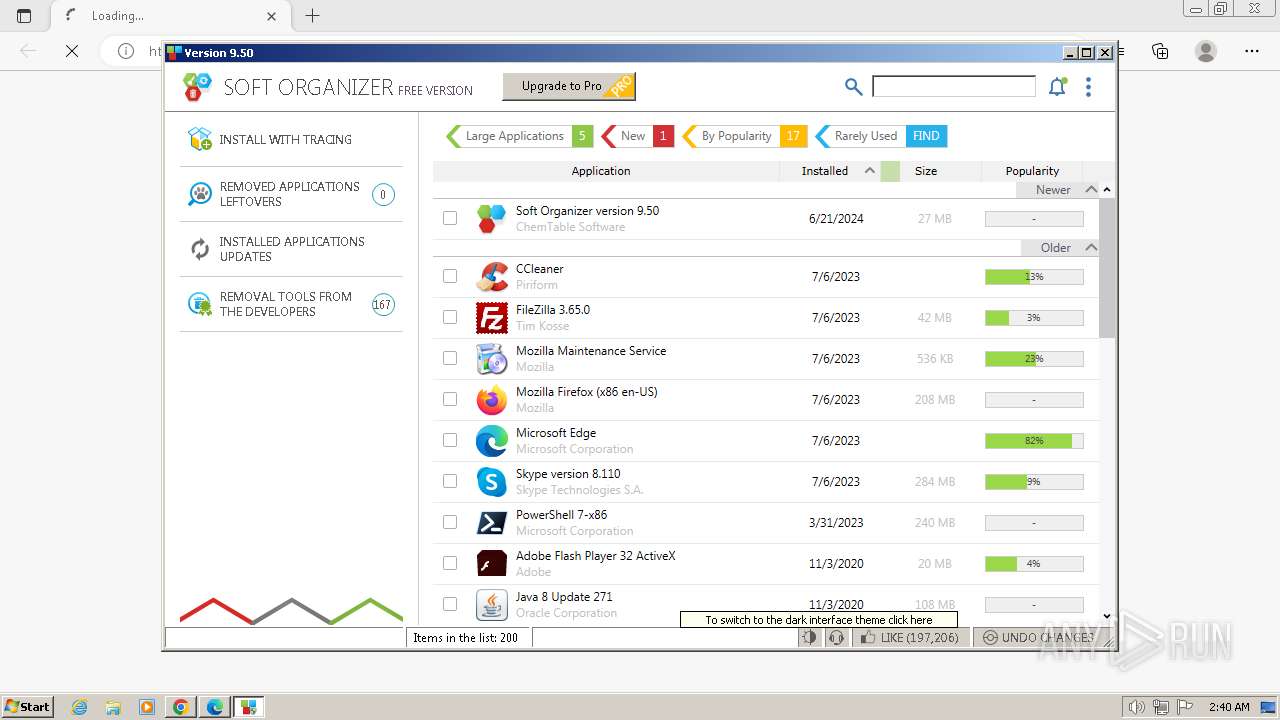
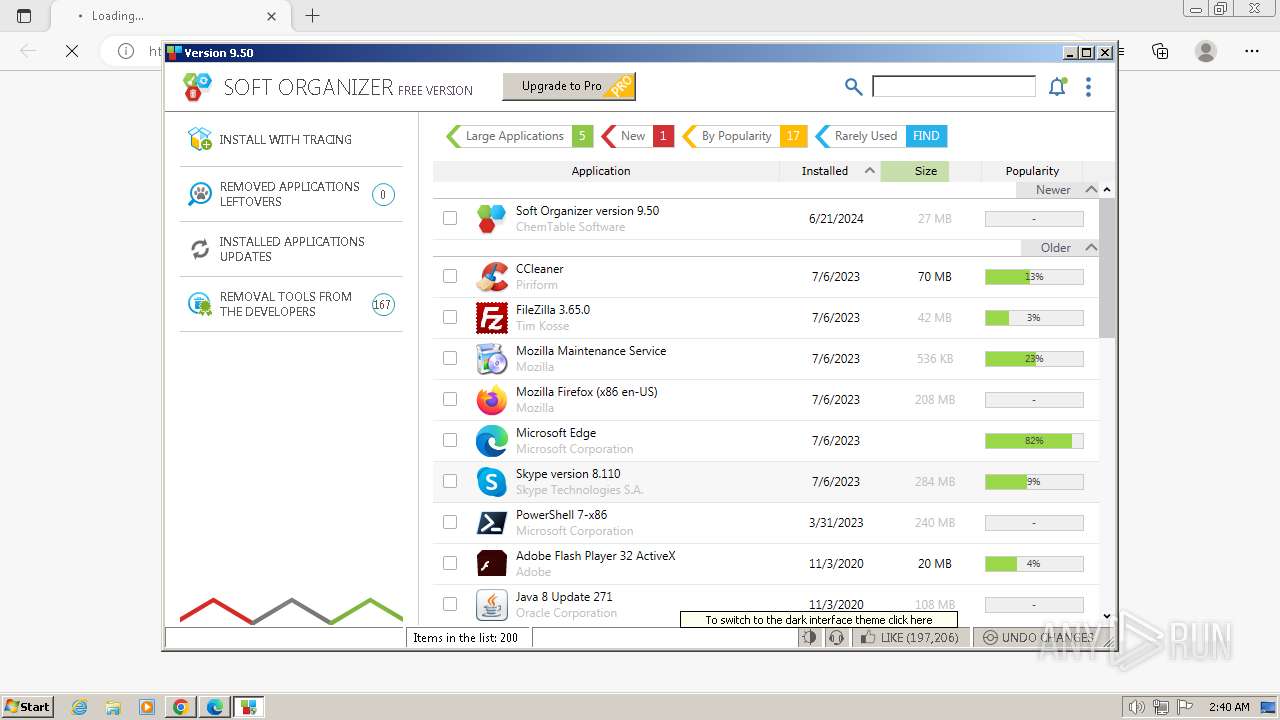
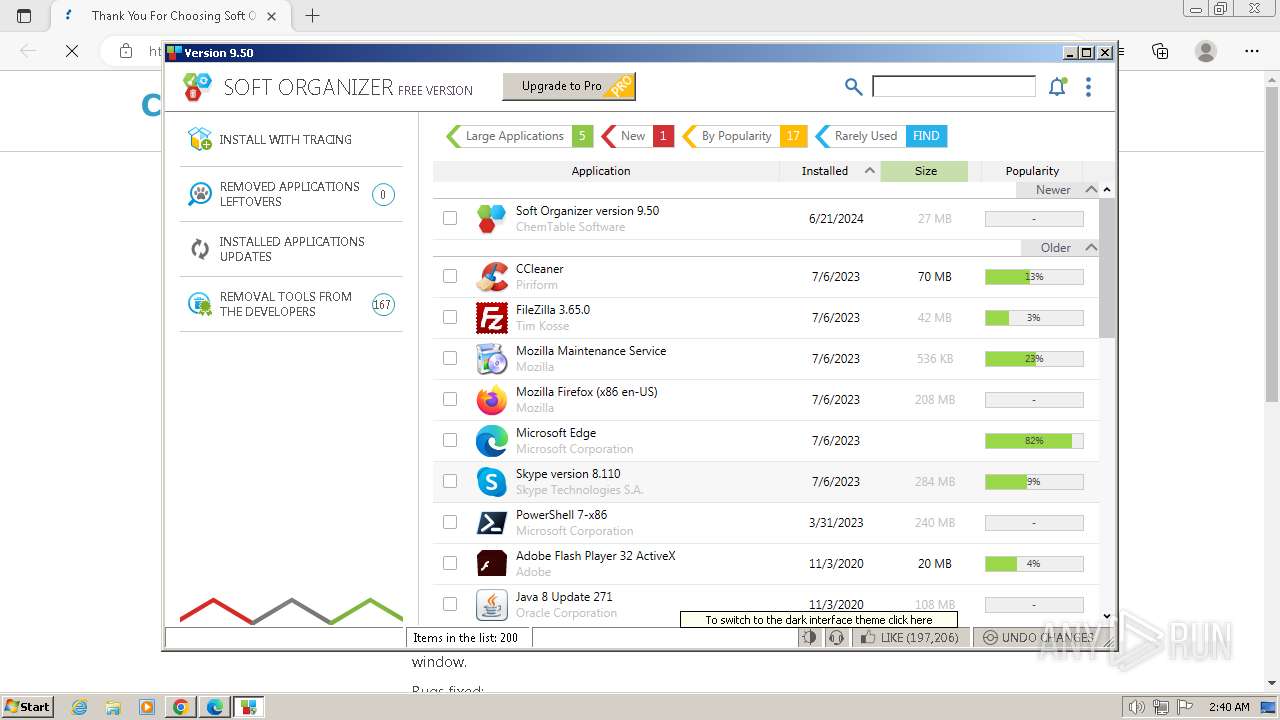
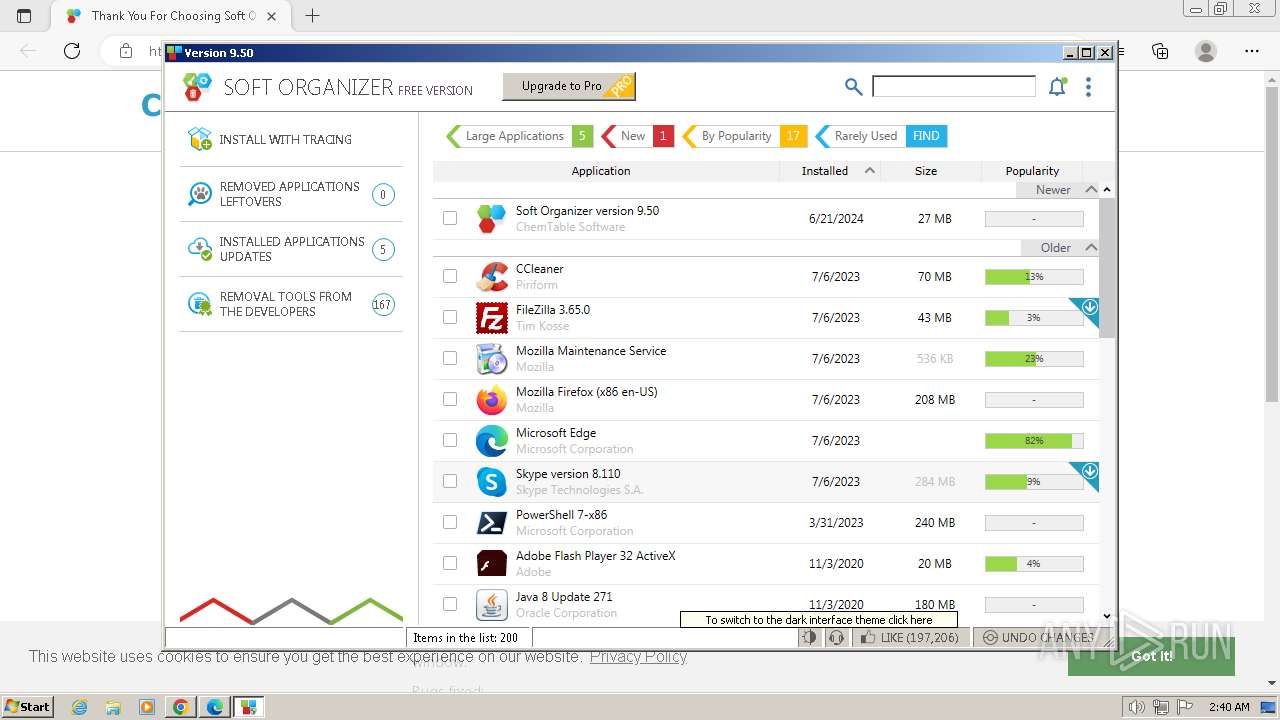
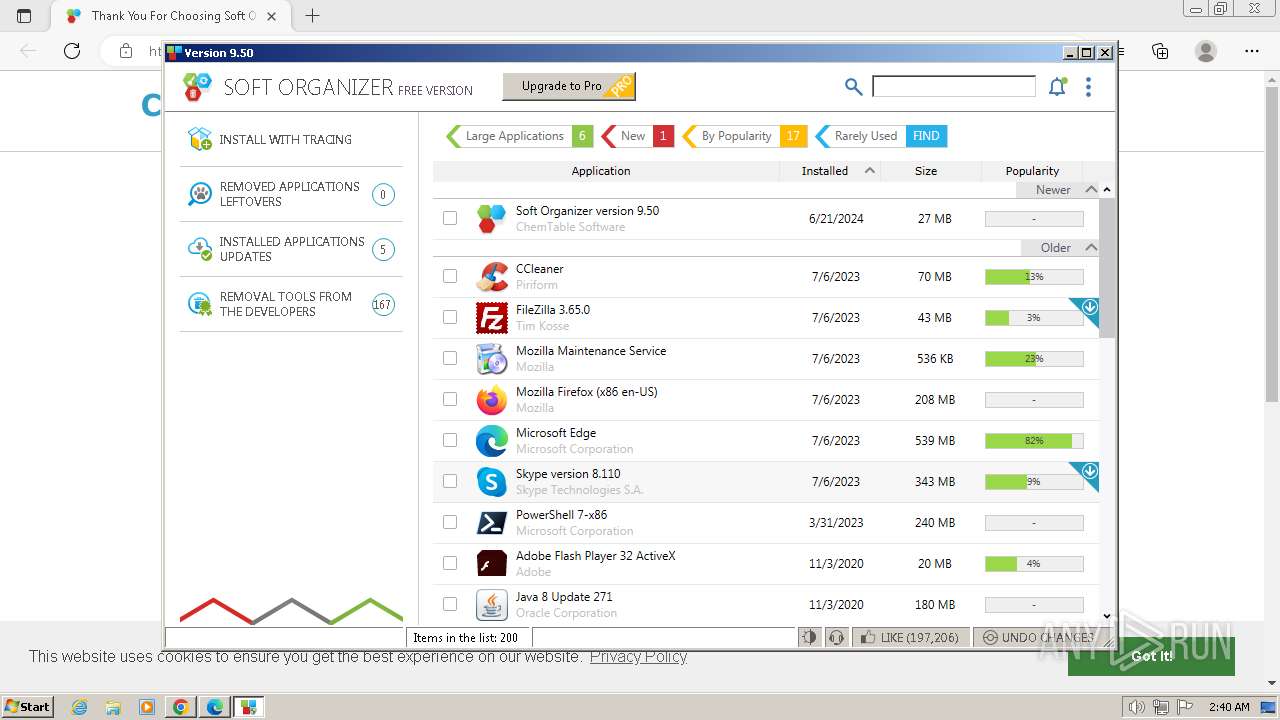
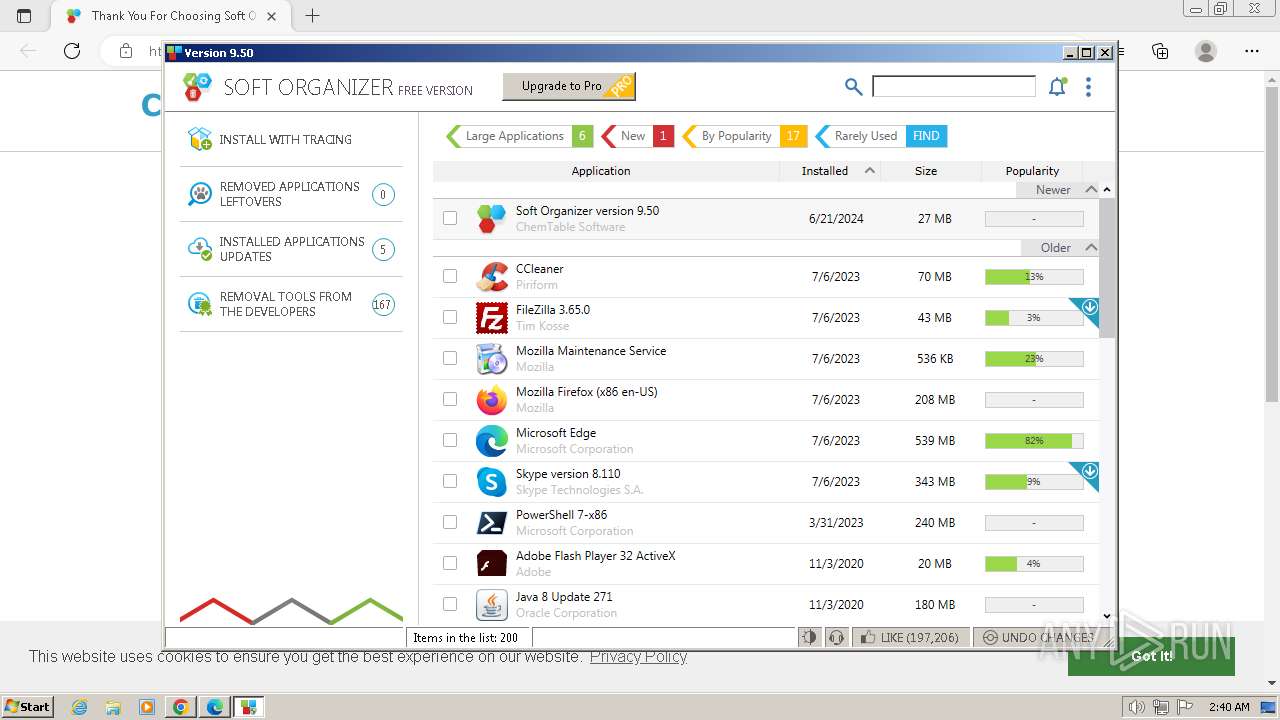
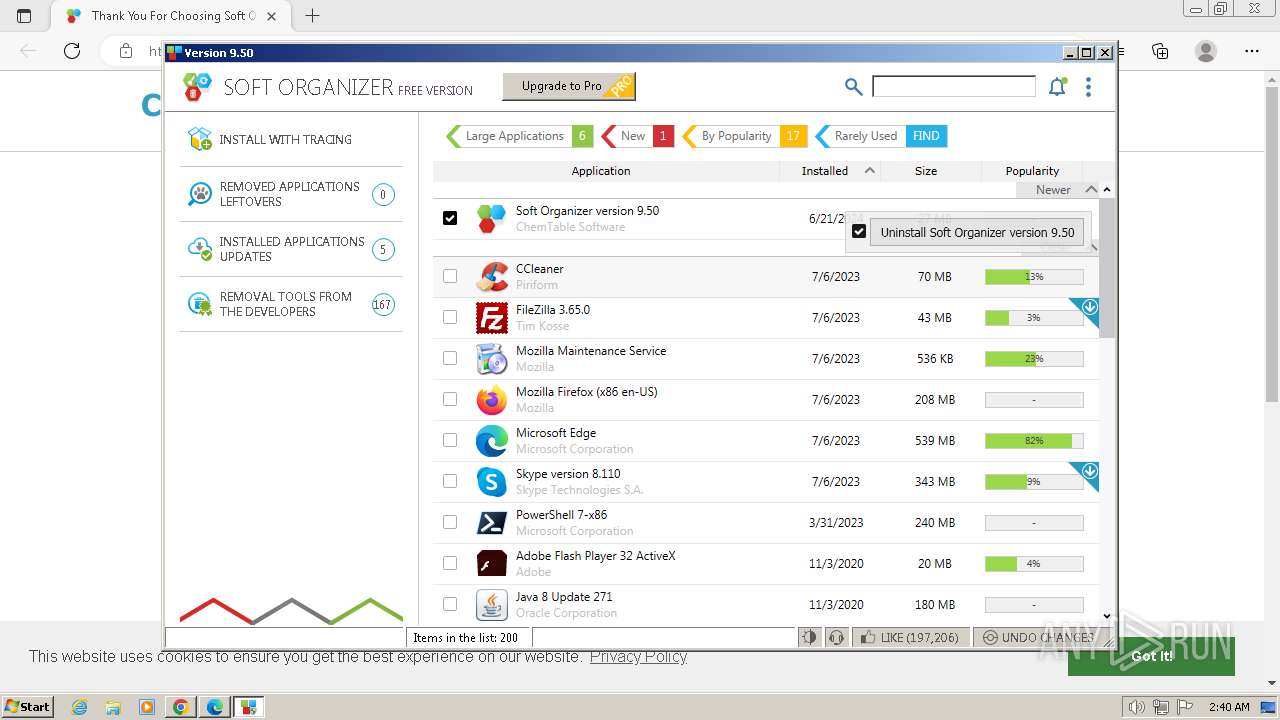
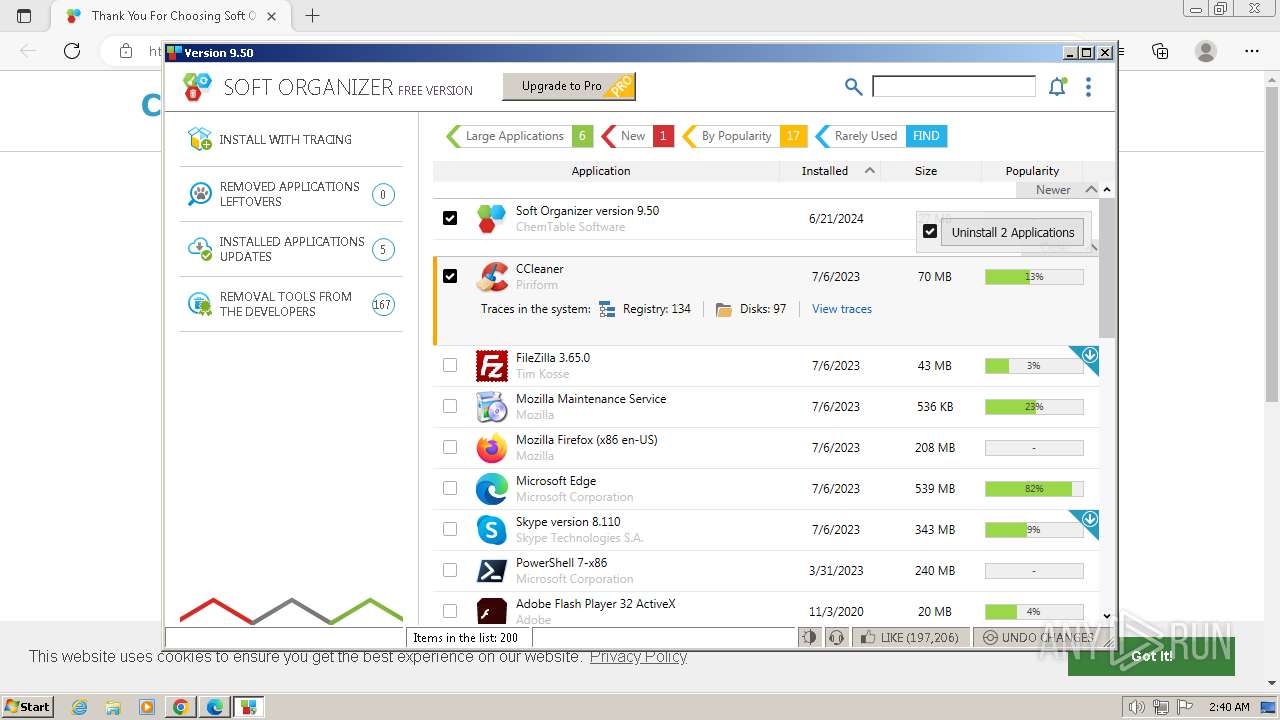
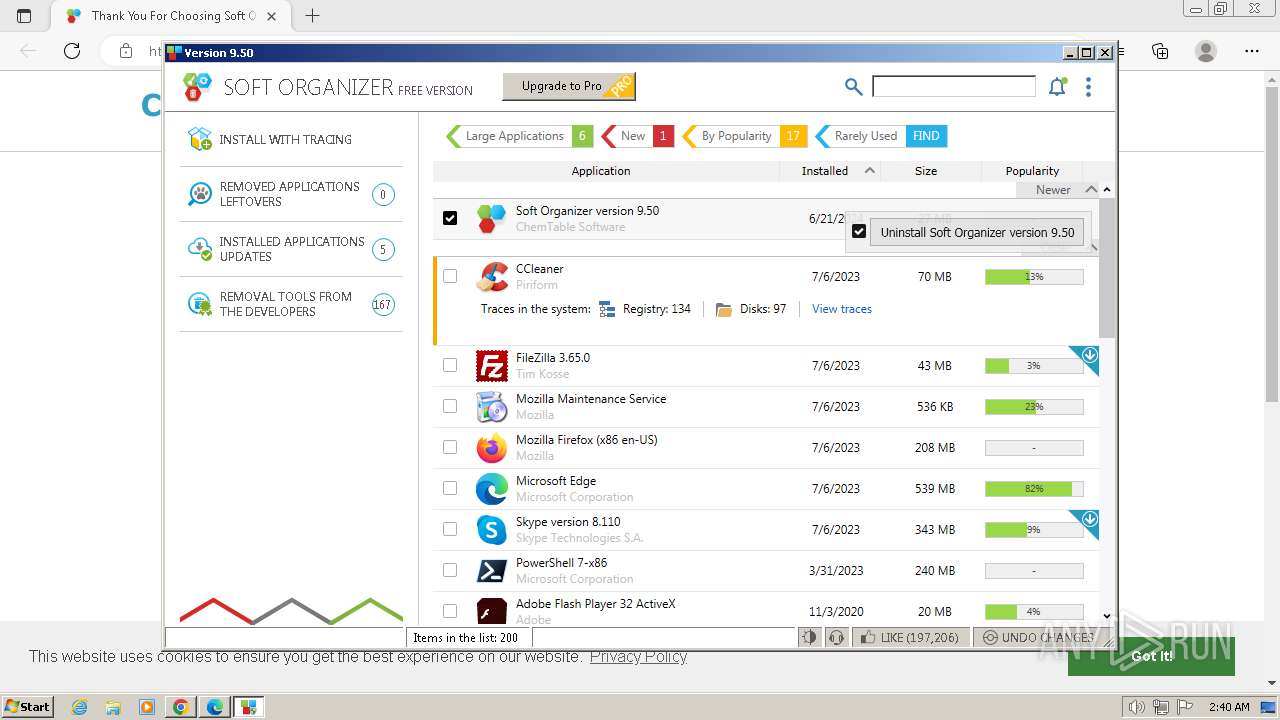
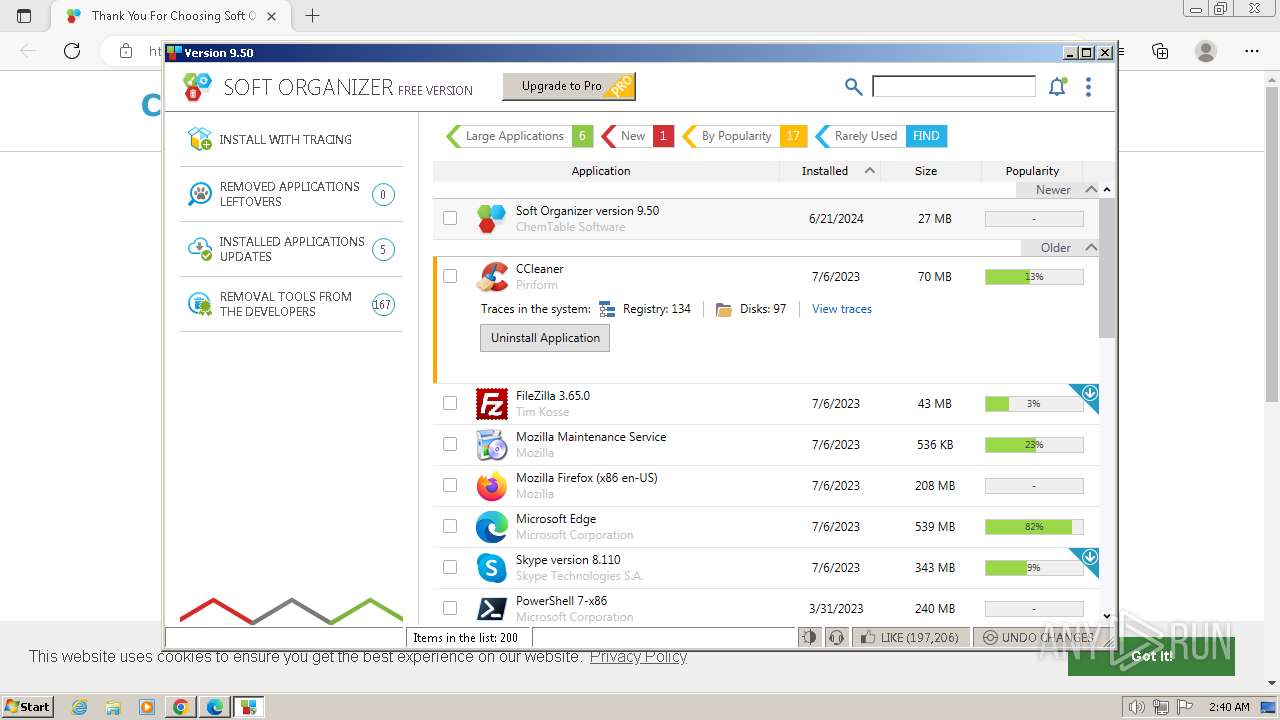
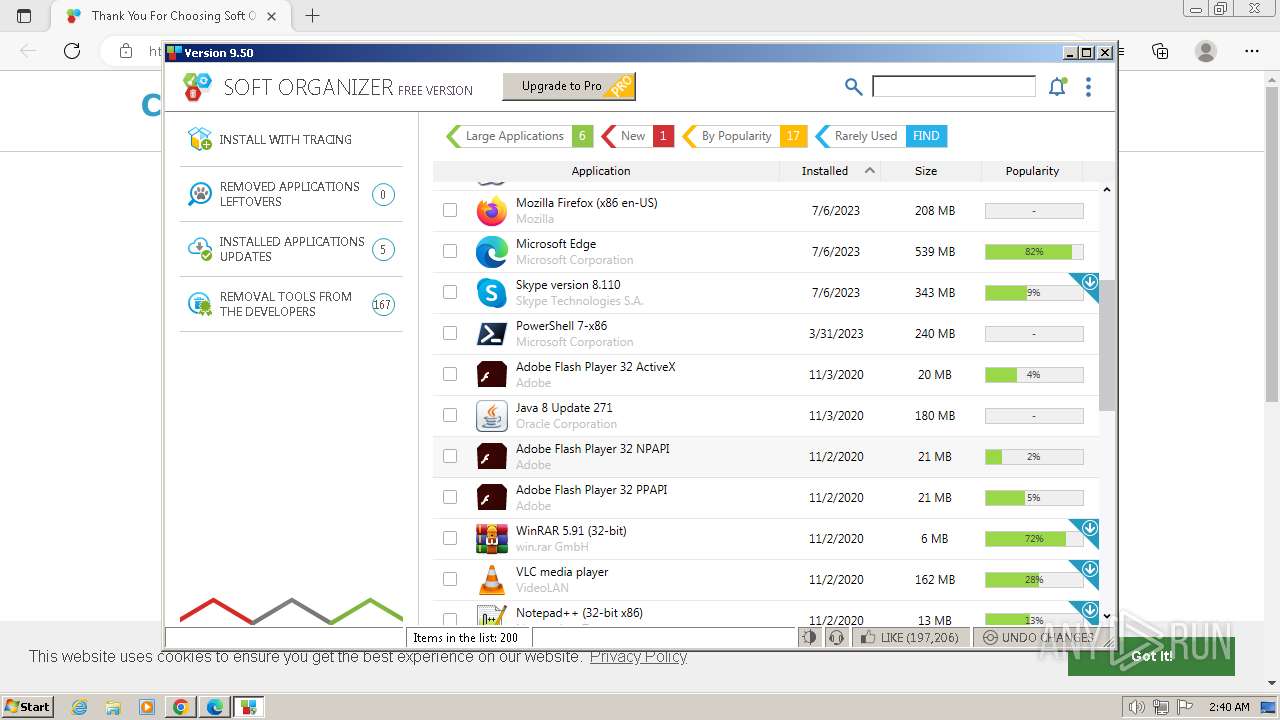
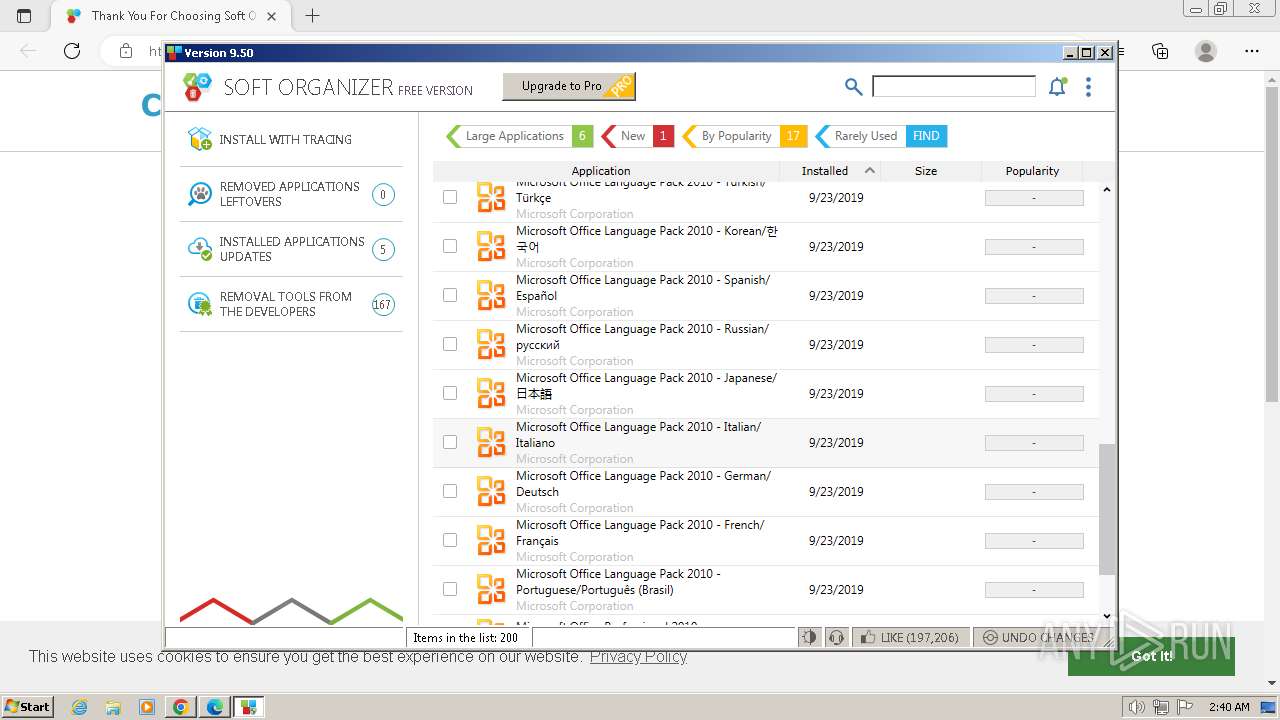
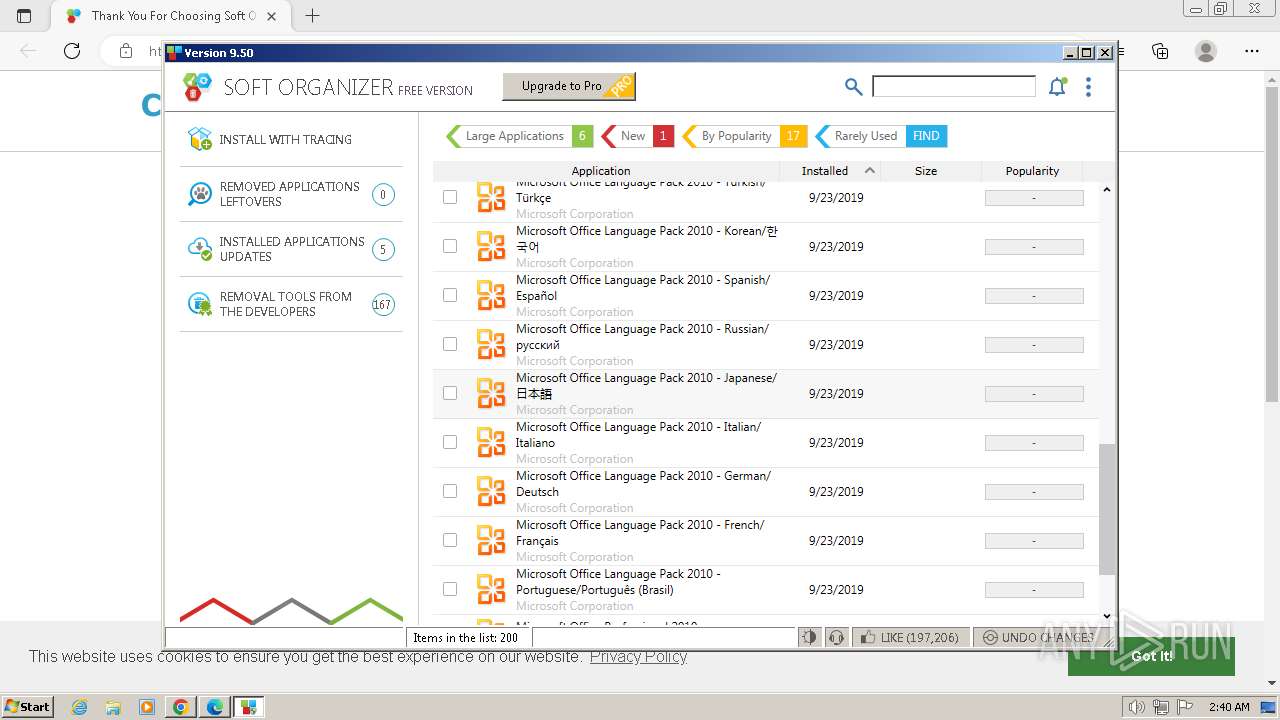
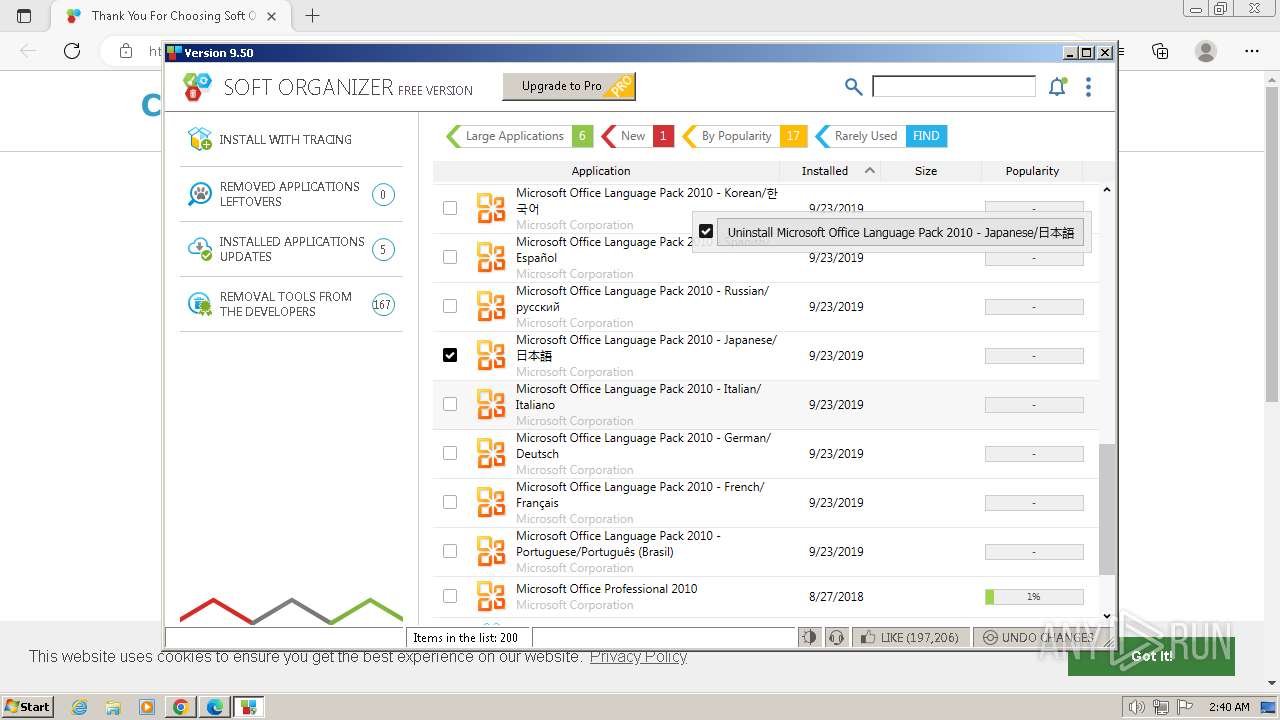
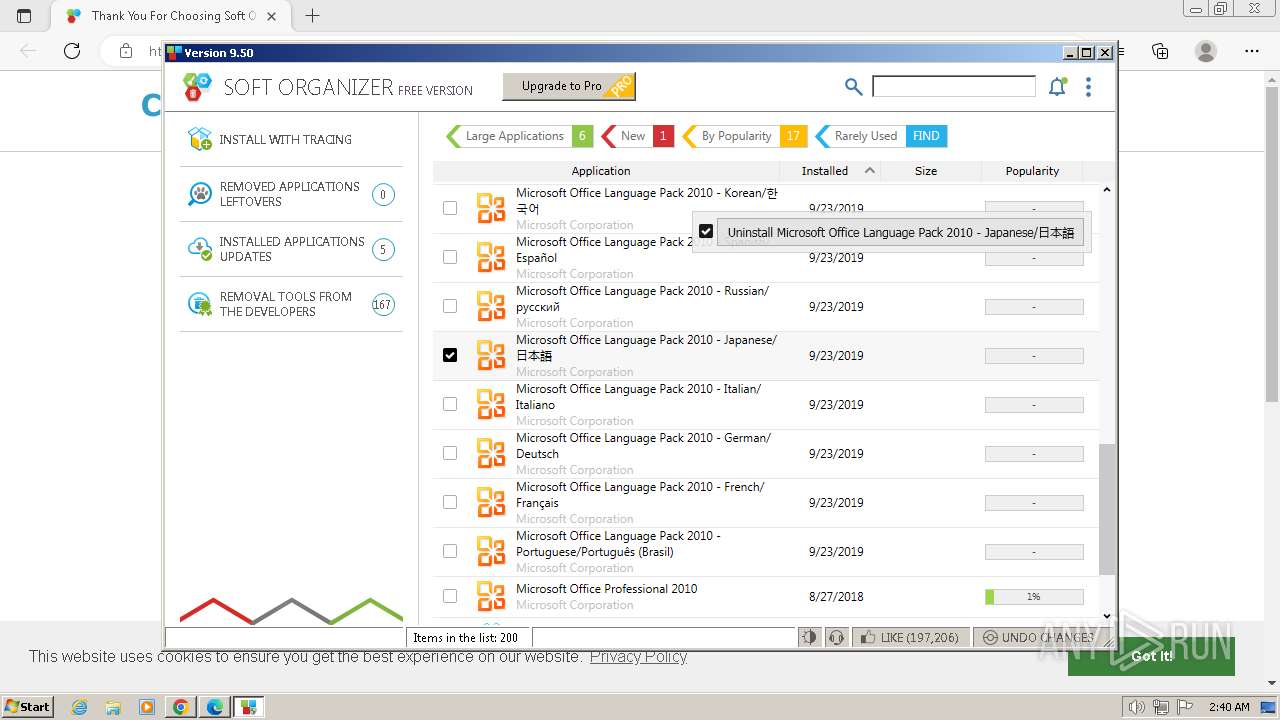
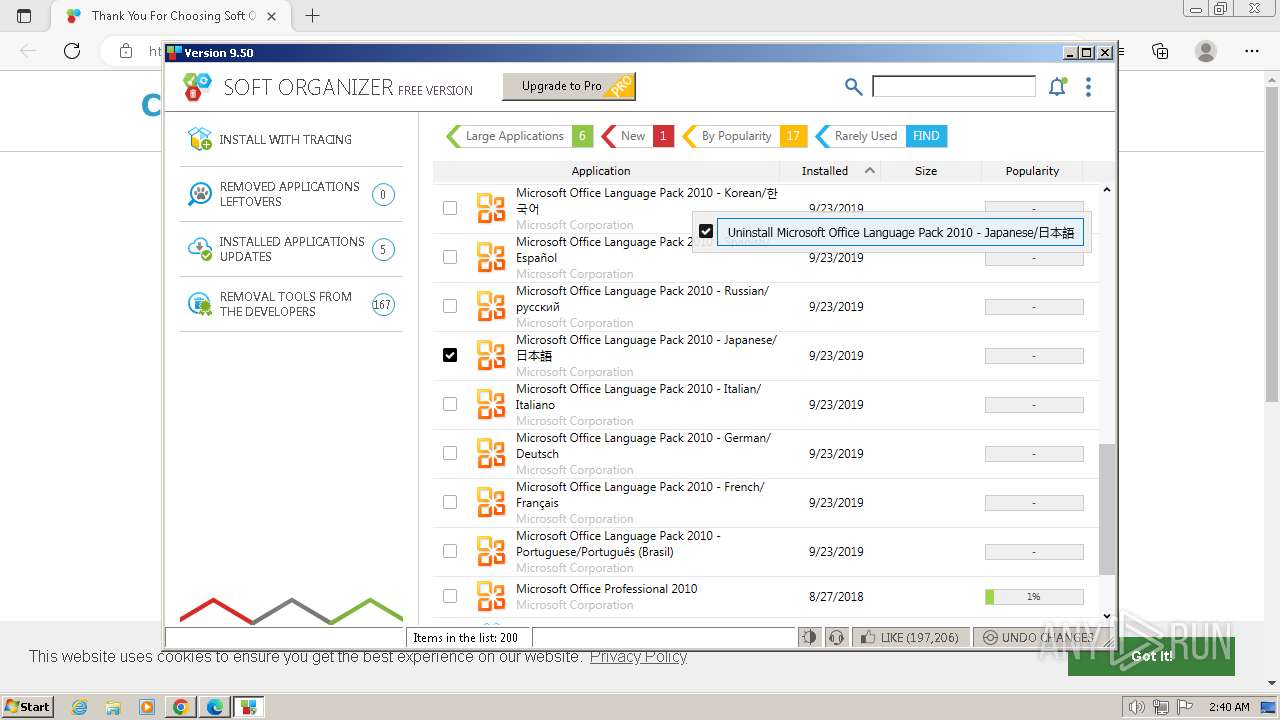
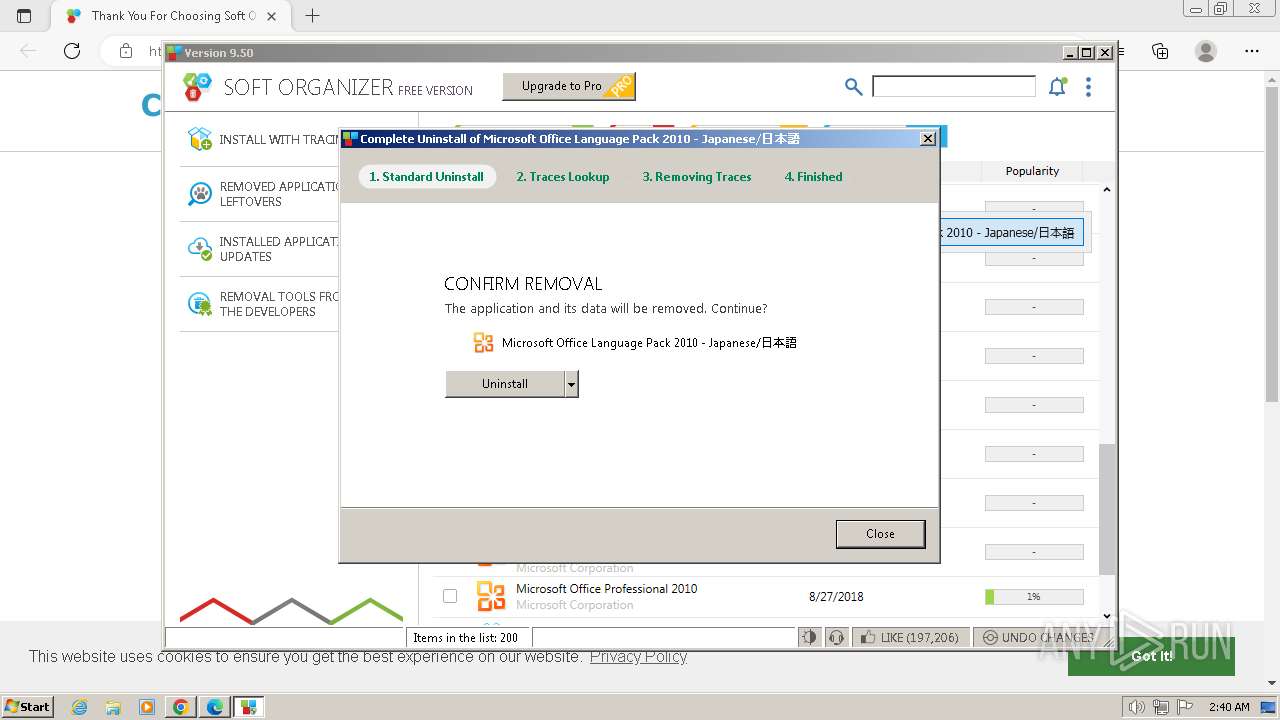
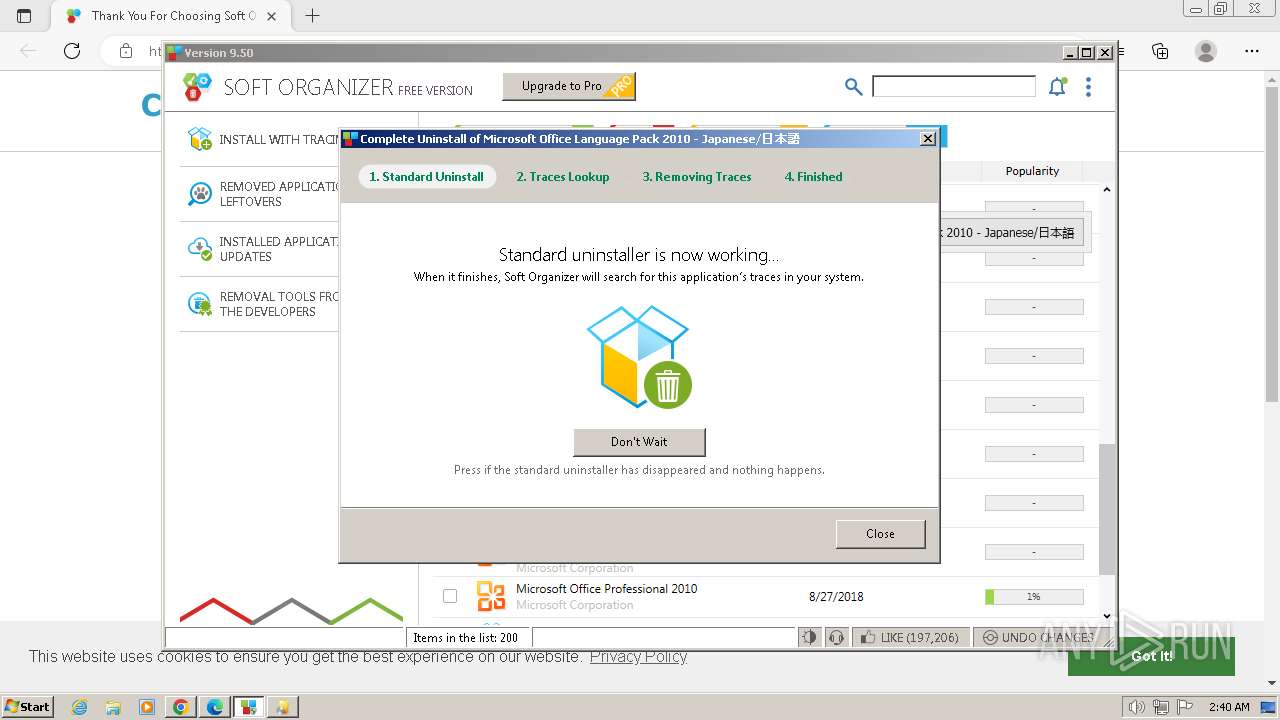
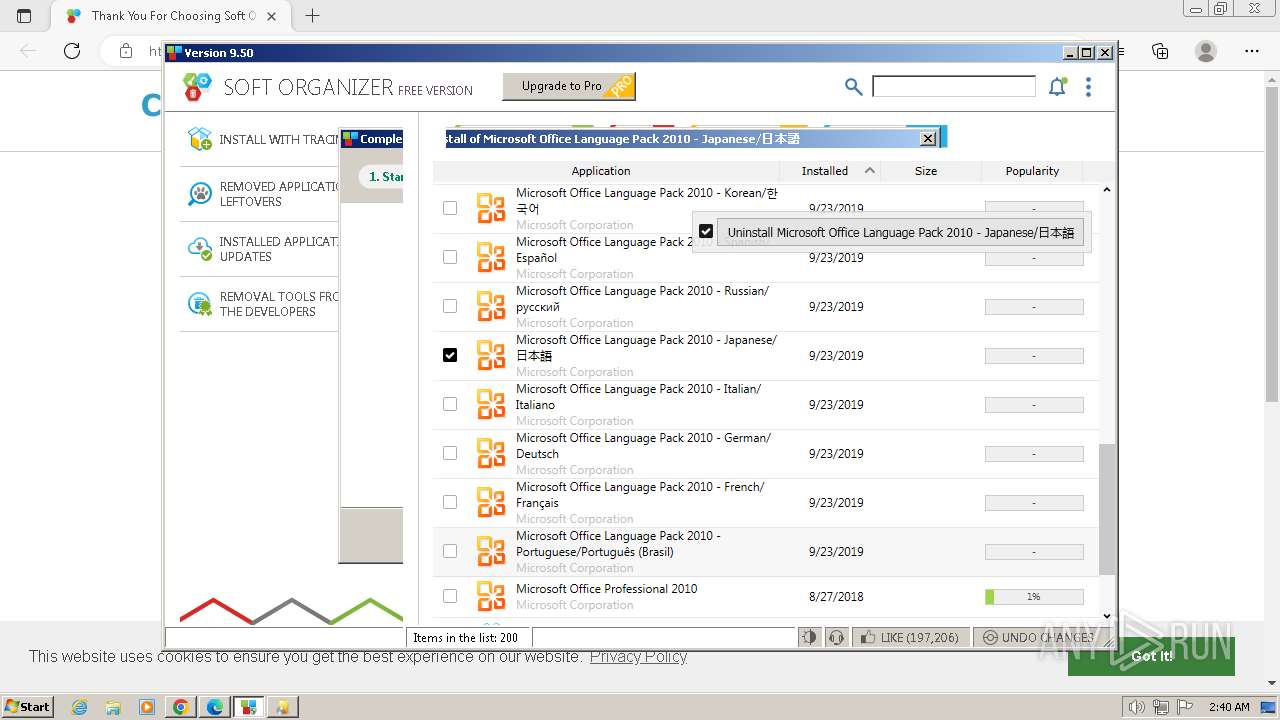
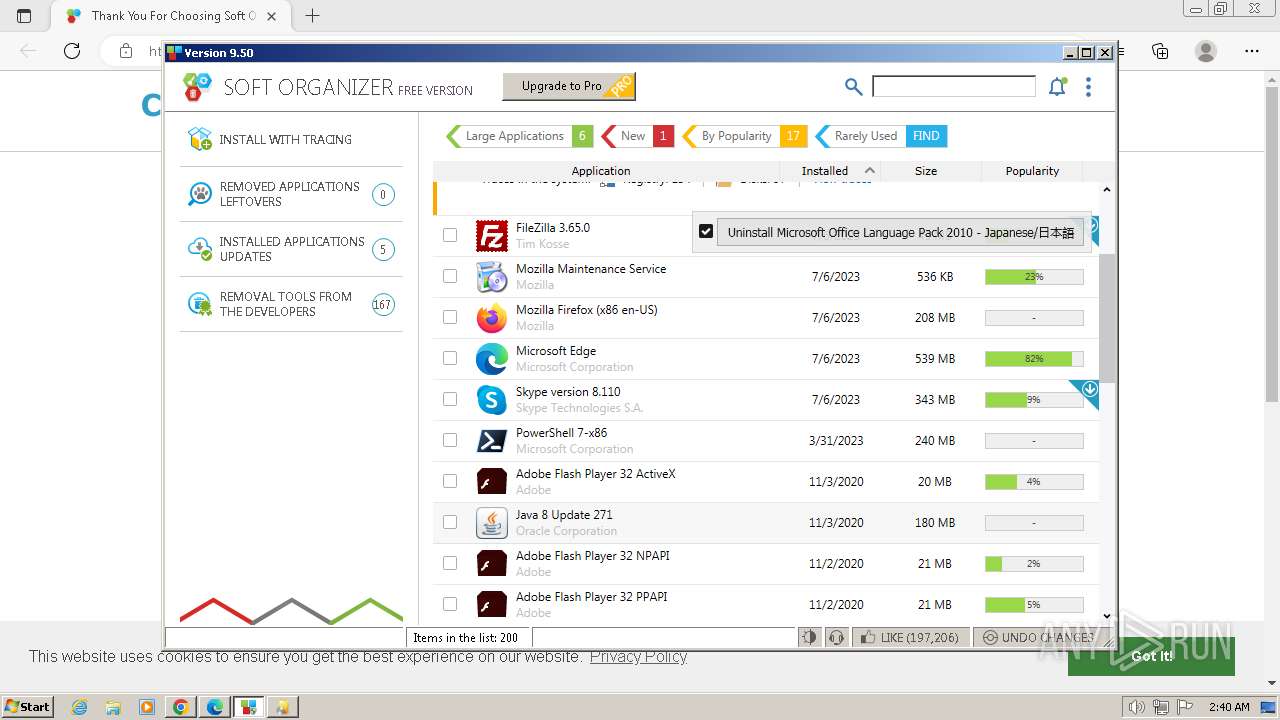
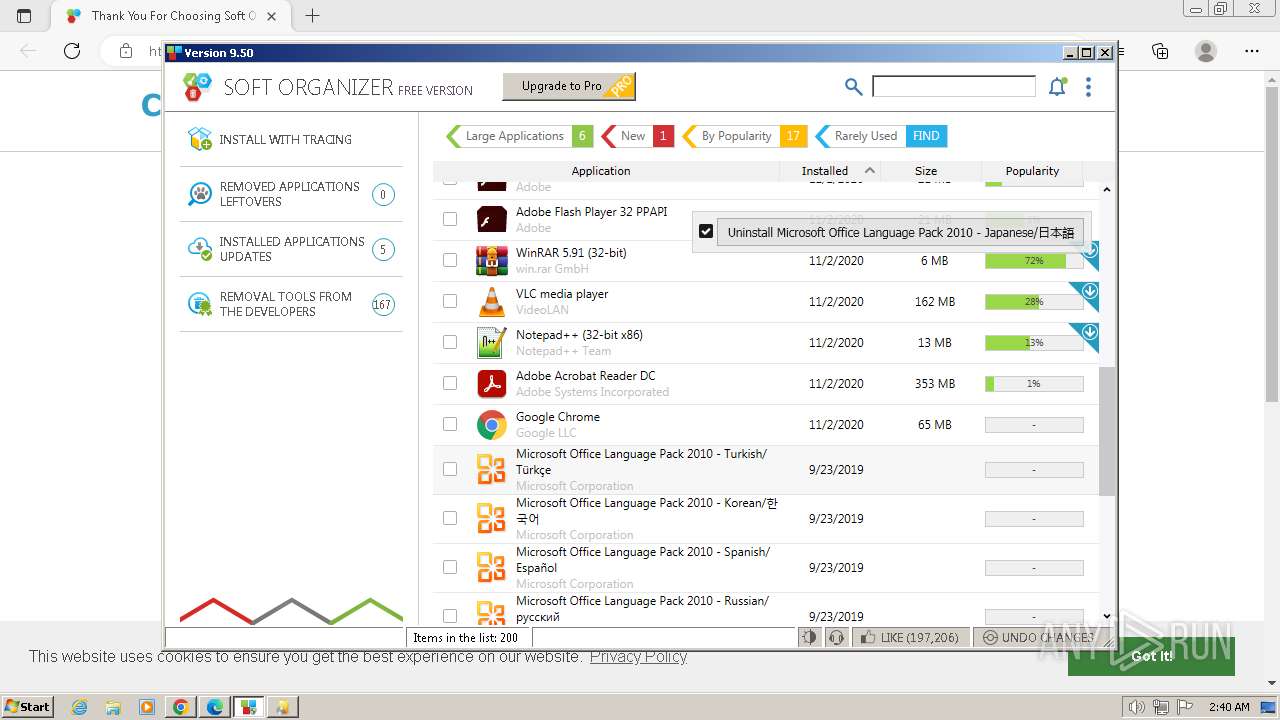
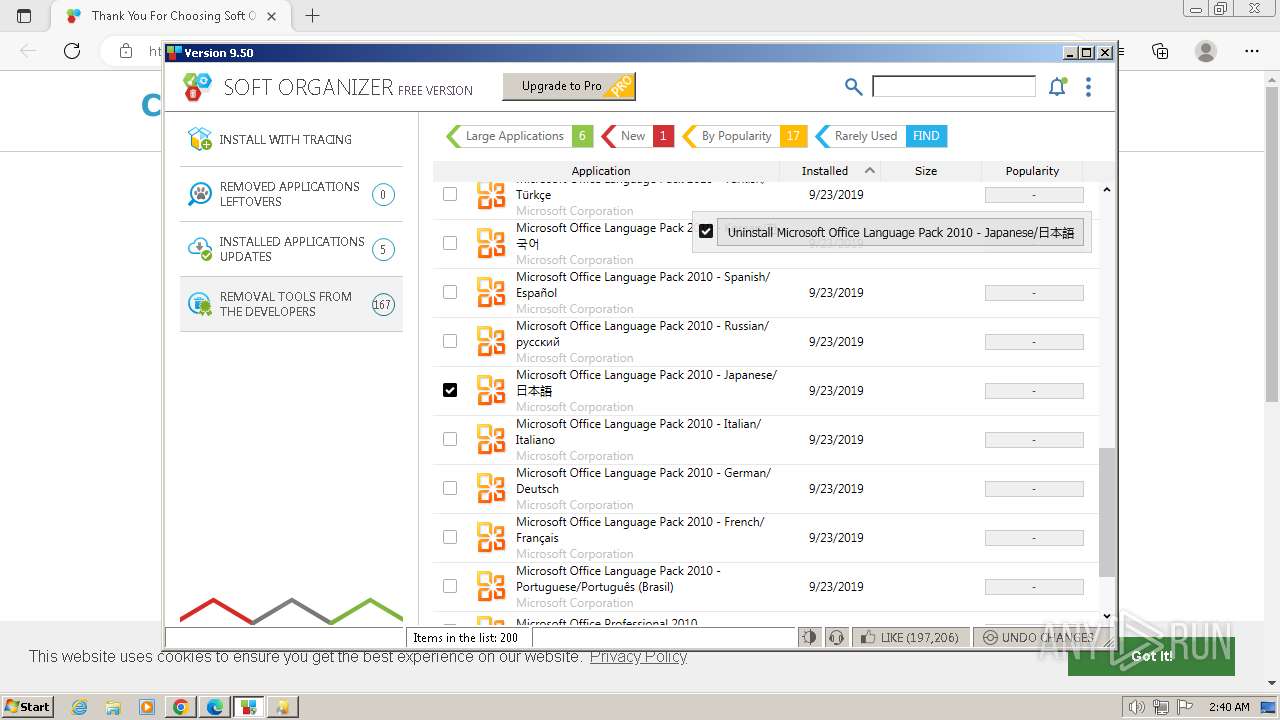
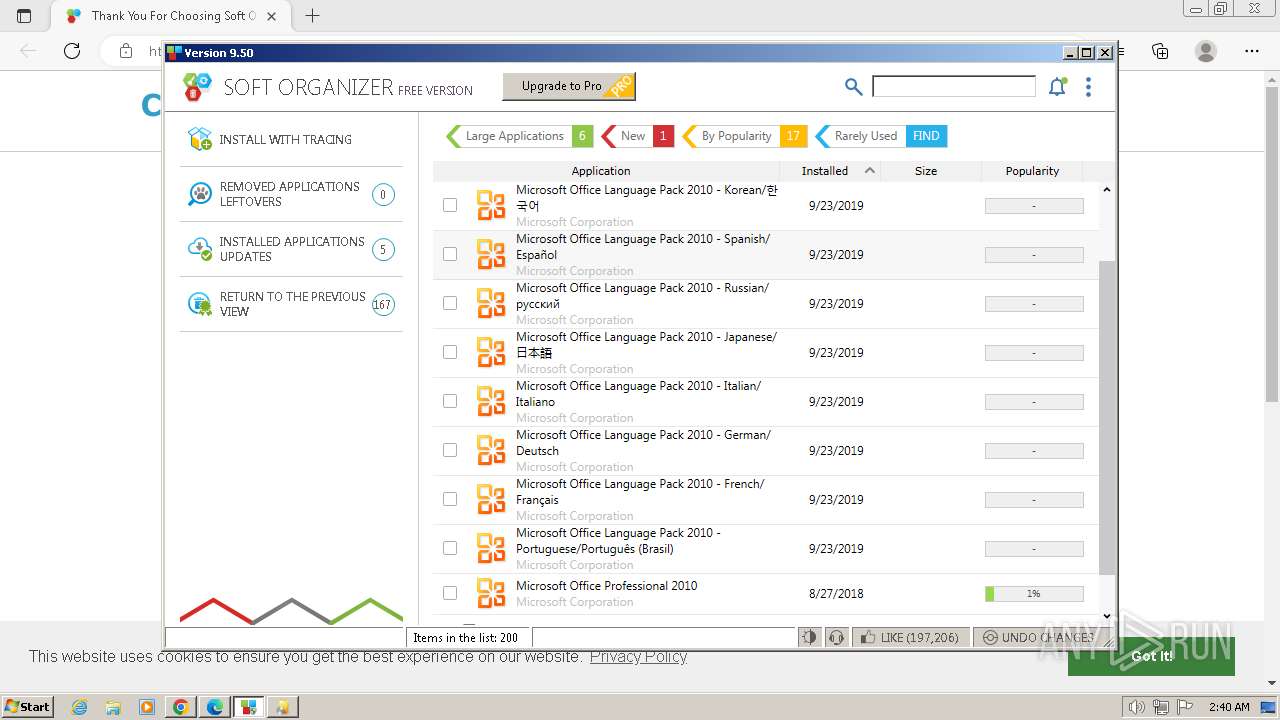
Searches for installed software
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Checks Windows Trust Settings
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Reads security settings of Internet Explorer
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Reads settings of System Certificates
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Adds/modifies Windows certificates
- SoftOrganizer.exe (PID: 3352)
Checks for Java to be installed
- SoftOrganizer.exe (PID: 3352)
Reads Mozilla Firefox installation path
- SoftOrganizer.exe (PID: 3352)
The process verifies whether the antivirus software is installed
- SoftOrganizer.exe (PID: 3352)
Read startup parameters
- SoftOrganizer.exe (PID: 3352)
Process drops legitimate windows executable
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 596)
- OSE.EXE (PID: 3864)
- msiexec.exe (PID: 3680)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 3412)
Executes as Windows Service
- VSSVC.exe (PID: 1908)
Starts itself from another location
- OSE.EXE (PID: 3864)
Starts a Microsoft application from unusual location
- ose00000.exe (PID: 2036)
INFO
Application launched itself
- chrome.exe (PID: 3344)
- msedge.exe (PID: 648)
- msedge.exe (PID: 2864)
- msiexec.exe (PID: 3020)
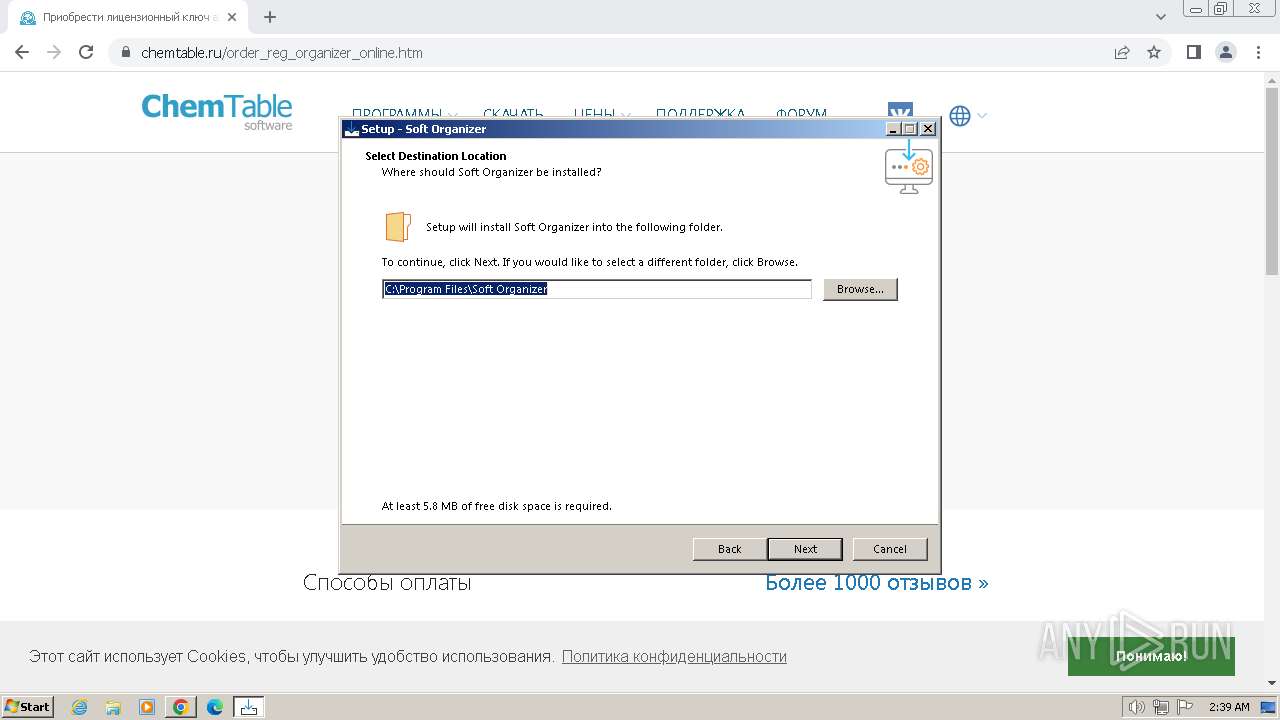
Create files in a temporary directory
- soft-organizer-setup.exe (PID: 2996)
- soft-organizer-setup.exe (PID: 1588)
- soft-organizer-setup.tmp (PID: 3564)
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- OSE.EXE (PID: 3864)
- IMEKLMG.EXE (PID: 1648)
Checks supported languages
- soft-organizer-setup.tmp (PID: 2400)
- soft-organizer-setup.exe (PID: 2996)
- soft-organizer-setup.tmp (PID: 3564)
- wmpnscfg.exe (PID: 3264)
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 3784)
- msiexec.exe (PID: 596)
- ngen.exe (PID: 3376)
- OSE.EXE (PID: 3864)
- ose00000.exe (PID: 2036)
- ngen.exe (PID: 1800)
- soft-organizer-setup.exe (PID: 1588)
- ngen.exe (PID: 3748)
- ngen.exe (PID: 3948)
- ngen.exe (PID: 2376)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 2028)
- ngen.exe (PID: 2688)
- ngen.exe (PID: 1916)
- ngen.exe (PID: 3524)
- ngen.exe (PID: 2368)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 1816)
- ngen.exe (PID: 3480)
- ngen.exe (PID: 1992)
- msiexec.exe (PID: 3680)
- ngen.exe (PID: 1988)
- msiexec.exe (PID: 3216)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 3740)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 3360)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 980)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 1624)
- IMEKLMG.EXE (PID: 1648)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 1156)
- msiexec.exe (PID: 2848)
- msiexec.exe (PID: 3836)
- msiexec.exe (PID: 3412)
- msiexec.exe (PID: 1820)
Reads the computer name
- soft-organizer-setup.tmp (PID: 2400)
- soft-organizer-setup.tmp (PID: 3564)
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 596)
- msiexec.exe (PID: 3784)
- wmpnscfg.exe (PID: 3264)
- ngen.exe (PID: 1800)
- ose00000.exe (PID: 2036)
- ngen.exe (PID: 3748)
- ngen.exe (PID: 3376)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 2376)
- ngen.exe (PID: 3948)
- ngen.exe (PID: 2028)
- ngen.exe (PID: 2688)
- ngen.exe (PID: 1916)
- ngen.exe (PID: 3524)
- ngen.exe (PID: 2368)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 1816)
- ngen.exe (PID: 3480)
- ngen.exe (PID: 1992)
- ngen.exe (PID: 1988)
- msiexec.exe (PID: 3680)
- msiexec.exe (PID: 3216)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3740)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 3360)
- msiexec.exe (PID: 980)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 1624)
- IMEKLMG.EXE (PID: 1648)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 1156)
- msiexec.exe (PID: 2848)
- msiexec.exe (PID: 3412)
- msiexec.exe (PID: 1820)
- msiexec.exe (PID: 3836)
Manual execution by a user
- wmpnscfg.exe (PID: 3264)
- msedge.exe (PID: 2864)
Executable content was dropped or overwritten
- chrome.exe (PID: 3344)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 596)
- msiexec.exe (PID: 3680)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 3412)
Creates files in the program directory
- soft-organizer-setup.tmp (PID: 3564)
Creates a software uninstall entry
- soft-organizer-setup.tmp (PID: 3564)
Creates files or folders in the user directory
- SoftOrganizer.exe (PID: 3352)
Checks proxy server information
- SoftOrganizer.exe (PID: 3352)
Reads the machine GUID from the registry
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 596)
- msiexec.exe (PID: 3784)
- msiexec.exe (PID: 3680)
- msiexec.exe (PID: 3216)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 1036)
- msiexec.exe (PID: 3740)
- msiexec.exe (PID: 3056)
- msiexec.exe (PID: 3904)
- msiexec.exe (PID: 3360)
- msiexec.exe (PID: 980)
- msiexec.exe (PID: 2552)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 3620)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 1624)
- msiexec.exe (PID: 1156)
- msiexec.exe (PID: 3836)
- msiexec.exe (PID: 3412)
- msiexec.exe (PID: 1820)
- msiexec.exe (PID: 2848)
Reads the software policy settings
- SoftOrganizer.exe (PID: 3352)
- Setup.exe (PID: 2280)
Reads Microsoft Office registry keys
- Setup.exe (PID: 2280)
- msiexec.exe (PID: 3020)
- ose00000.exe (PID: 2036)
Drops the executable file immediately after the start
- chrome.exe (PID: 3344)
The process uses the downloaded file
- chrome.exe (PID: 684)
- chrome.exe (PID: 3344)
Process checks whether UAC notifications are on
- msiexec.exe (PID: 2600)
- IMEKLMG.EXE (PID: 1648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
188
Monitored processes
93
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | C:\Windows\system32\MsiExec.exe -Embedding DFC10EF1A8632EFC5CDBA7528CC020A1 | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
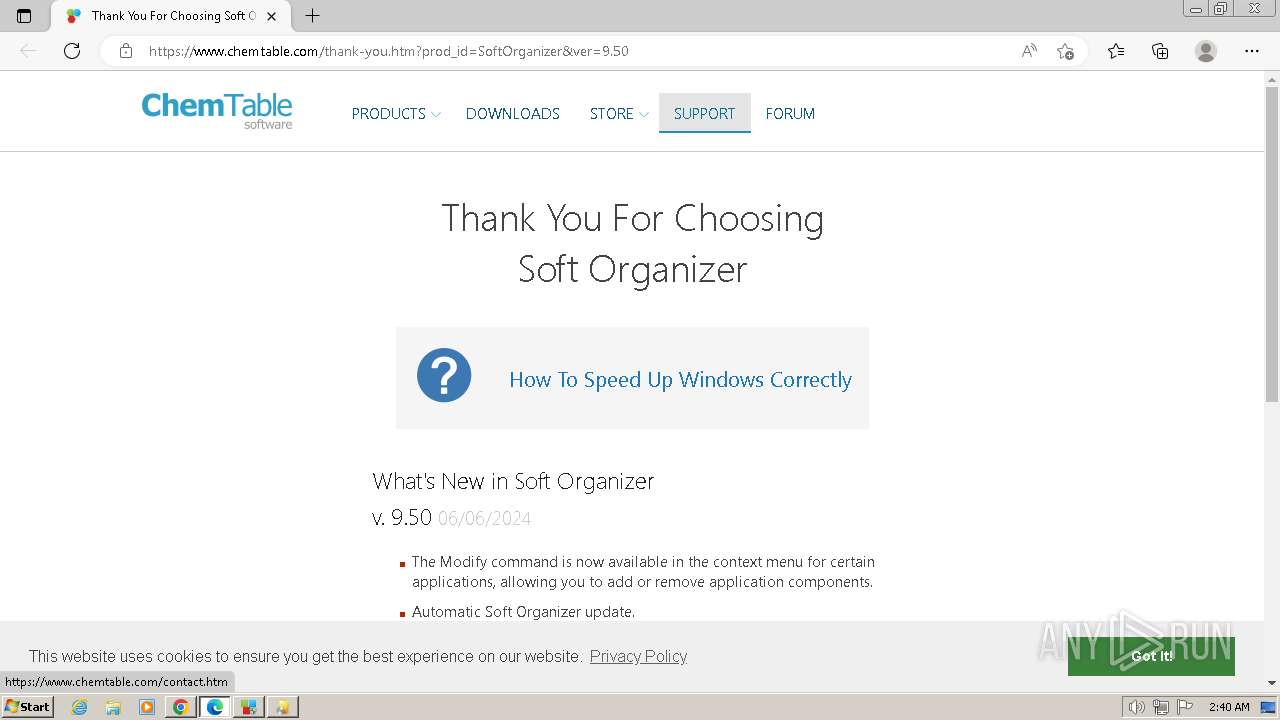
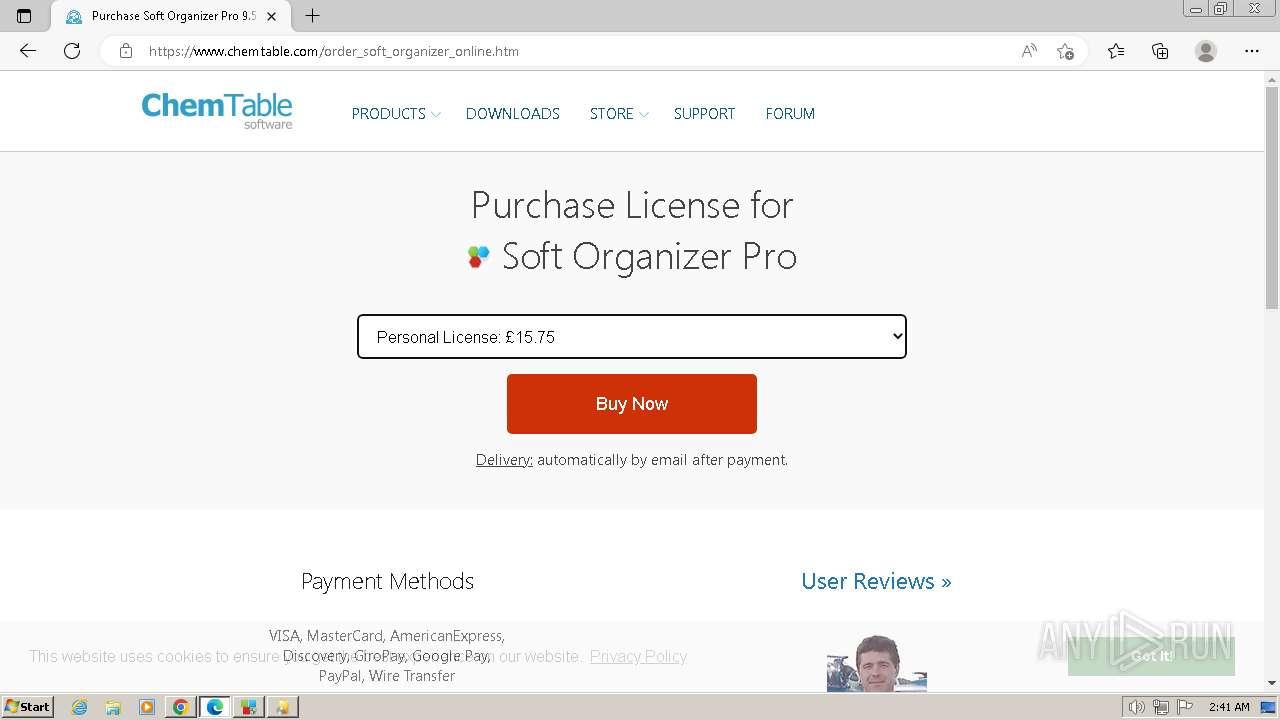
| 648 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.chemtable.com/thank-you.htm?prod_id=SoftOrganizer&ver=9.50 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | soft-organizer-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4156 --field-trial-handle=1128,i,2994710715342097024,1192547668505364448,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1564 --field-trial-handle=1328,i,263992236249144787,15745815125805884479,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 980 | C:\Windows\system32\MsiExec.exe -Embedding 5B1CF086691C0DCCA2D79AF4B7B4B33A E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | C:\Windows\system32\MsiExec.exe -Embedding 2EA48E9C690695109BC205220C4F24A6 | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\System32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3964 --field-trial-handle=1436,i,12216280802206106975,7705780182098362103,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1812 --field-trial-handle=1128,i,2994710715342097024,1192547668505364448,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1156 | C:\Windows\system32\MsiExec.exe -Embedding 40B38A28E9E58176F096E8A388017D78 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
333 809
Read events
326 462
Write events
3 365
Delete events
3 982
Modification events
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
397
Suspicious files
868
Text files
484
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4e710.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF4e8d6.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4eaca.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF4e914.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF4e943.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
111
DNS requests
126
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2956 | chrome.exe | GET | 301 | 87.242.71.148:80 | http://chemtable.ru/ | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pcexe23cbpdsyxil3k3azbydzu_20240429.634529504.14/obedbbhbpmojnkanicioggnmelmoomoc_20240429.634529504.14_all_ENUS500000_jtpqgijs6dadhfri2u4vxcrx3e.crx3 | unknown | — | — | unknown |
3352 | SoftOrganizer.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPHCzpuLuKhDPUvpxGnEH8zVA%3D%3D | unknown | — | — | unknown |
3352 | SoftOrganizer.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pcexe23cbpdsyxil3k3azbydzu_20240429.634529504.14/obedbbhbpmojnkanicioggnmelmoomoc_20240429.634529504.14_all_ENUS500000_jtpqgijs6dadhfri2u4vxcrx3e.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pcexe23cbpdsyxil3k3azbydzu_20240429.634529504.14/obedbbhbpmojnkanicioggnmelmoomoc_20240429.634529504.14_all_ENUS500000_jtpqgijs6dadhfri2u4vxcrx3e.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3344 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2956 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2956 | chrome.exe | 87.242.71.148:80 | chemtable.ru | LLC masterhost | RU | unknown |
2956 | chrome.exe | 87.242.71.148:443 | chemtable.ru | LLC masterhost | RU | unknown |
2956 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
chemtable.ru |
| unknown |
www.googletagmanager.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
www.clarity.ms |
| whitelisted |
top-fwz1.mail.ru |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
privacy-cs.mail.ru |
| unknown |
mc.yandex.com |
| whitelisted |
i.clarity.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2956 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3608 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3608 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3608 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
Process | Message |
|---|---|
SoftOrganizer.exe | start module
|
SoftOrganizer.exe | end module
|
SoftOrganizer.exe | start CustomTagBorder
|
SoftOrganizer.exe | start InnerTagContent
|
SoftOrganizer.exe | start CustomTagBorder
|
SoftOrganizer.exe | start InnerTagContent
|
SoftOrganizer.exe | start CustomTagBorder
|
SoftOrganizer.exe | start InnerTagContent
|
SoftOrganizer.exe | start CustomTagBorder
|
SoftOrganizer.exe | start InnerTagContent
|