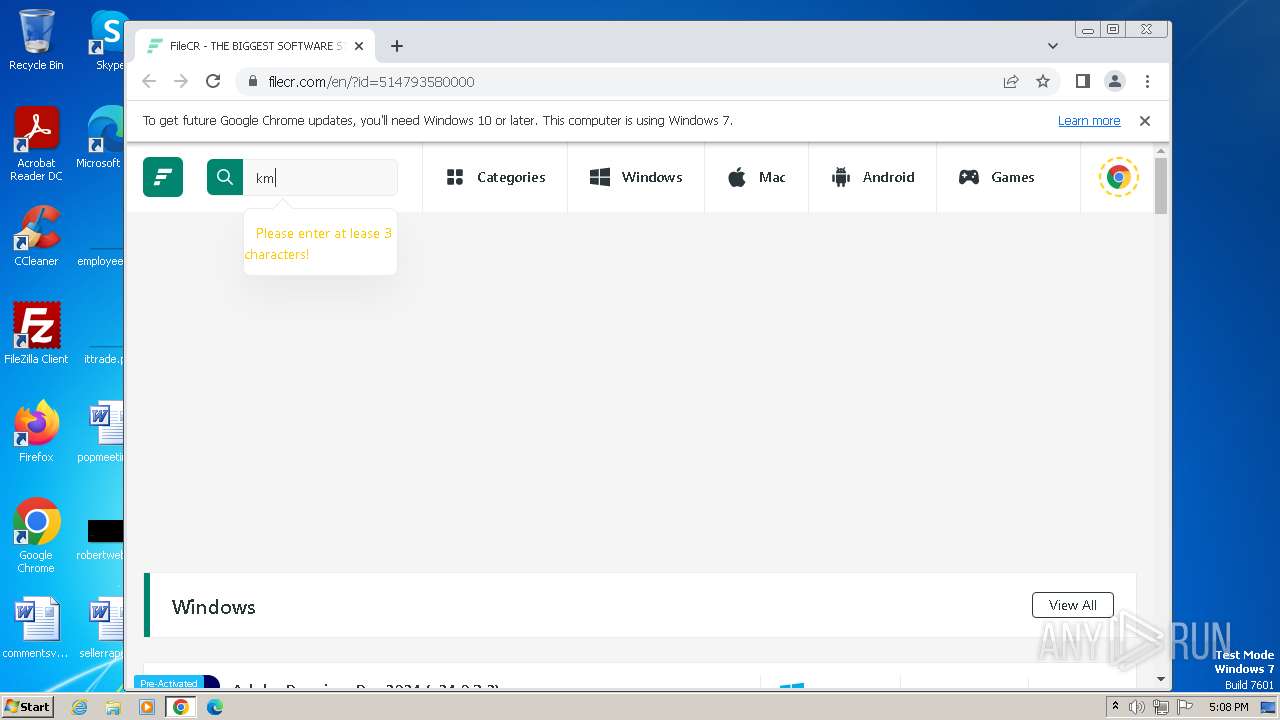
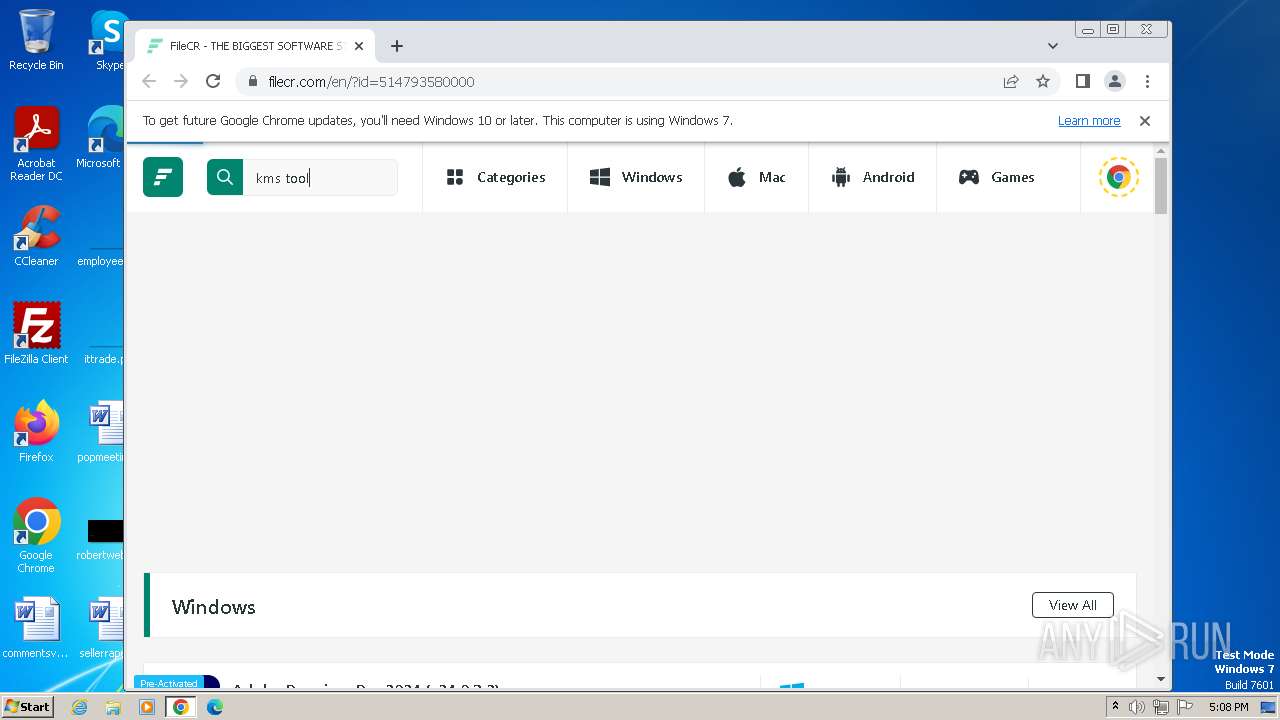
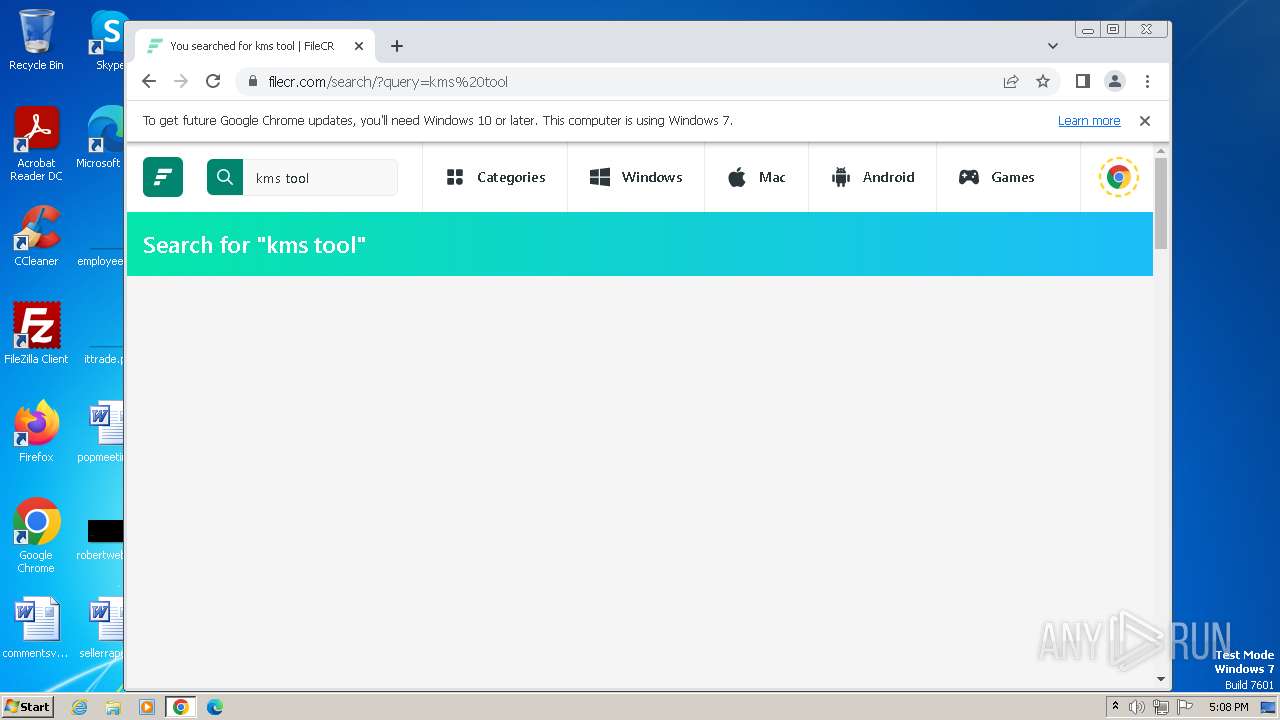
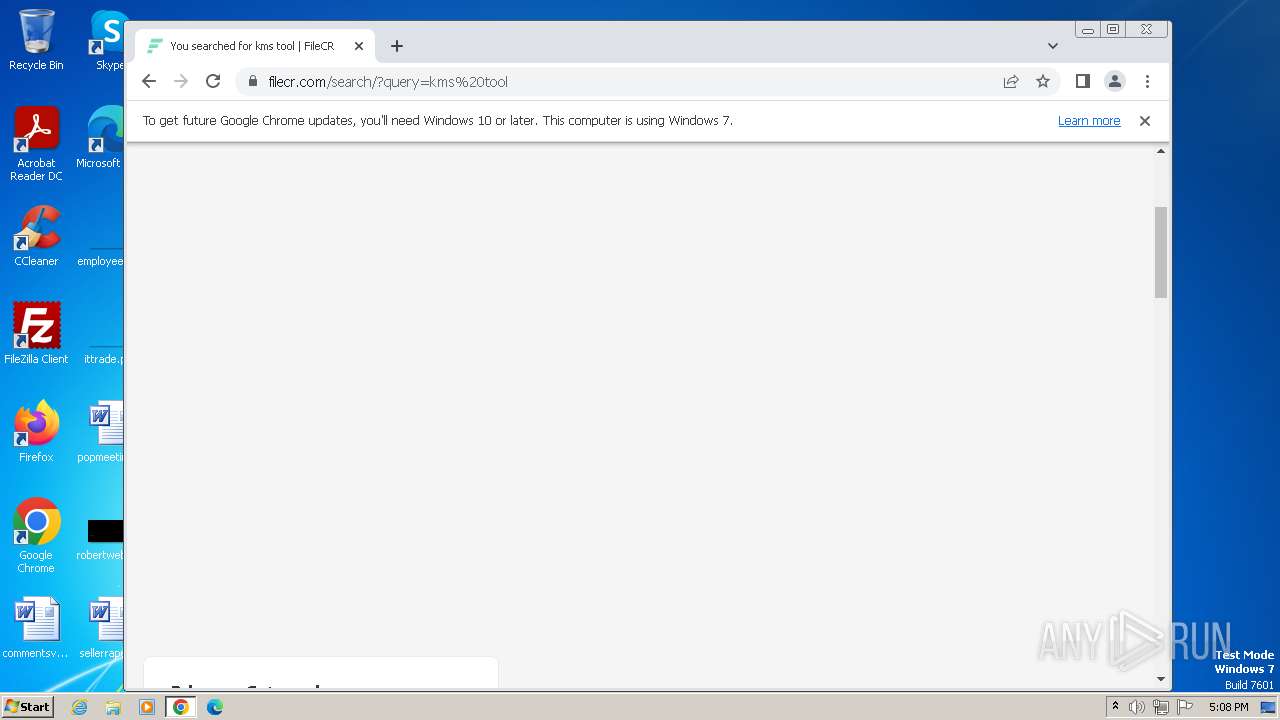
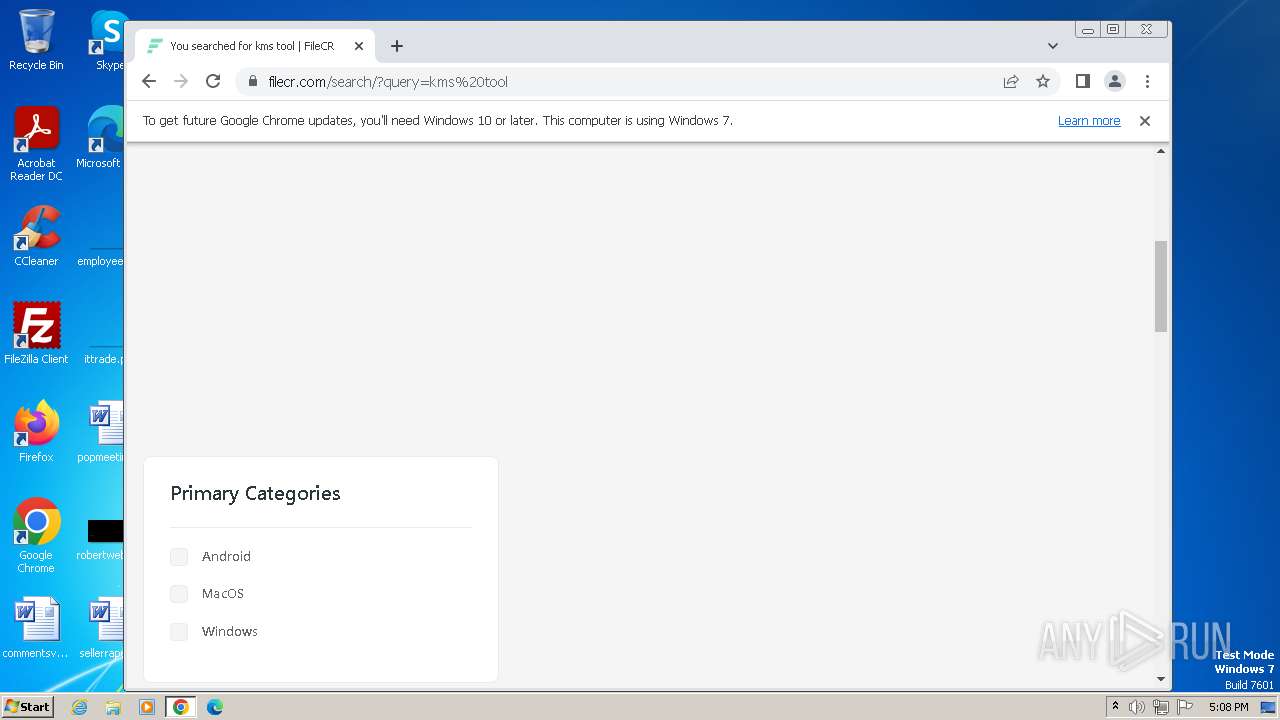
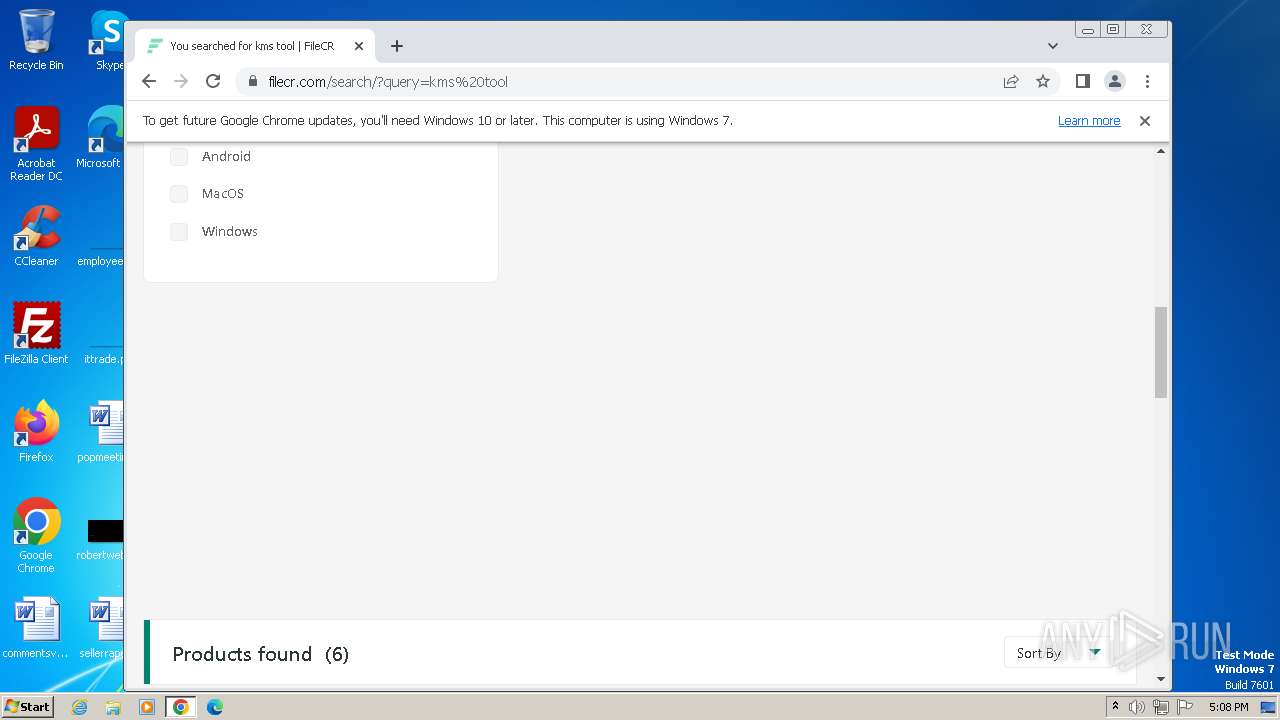
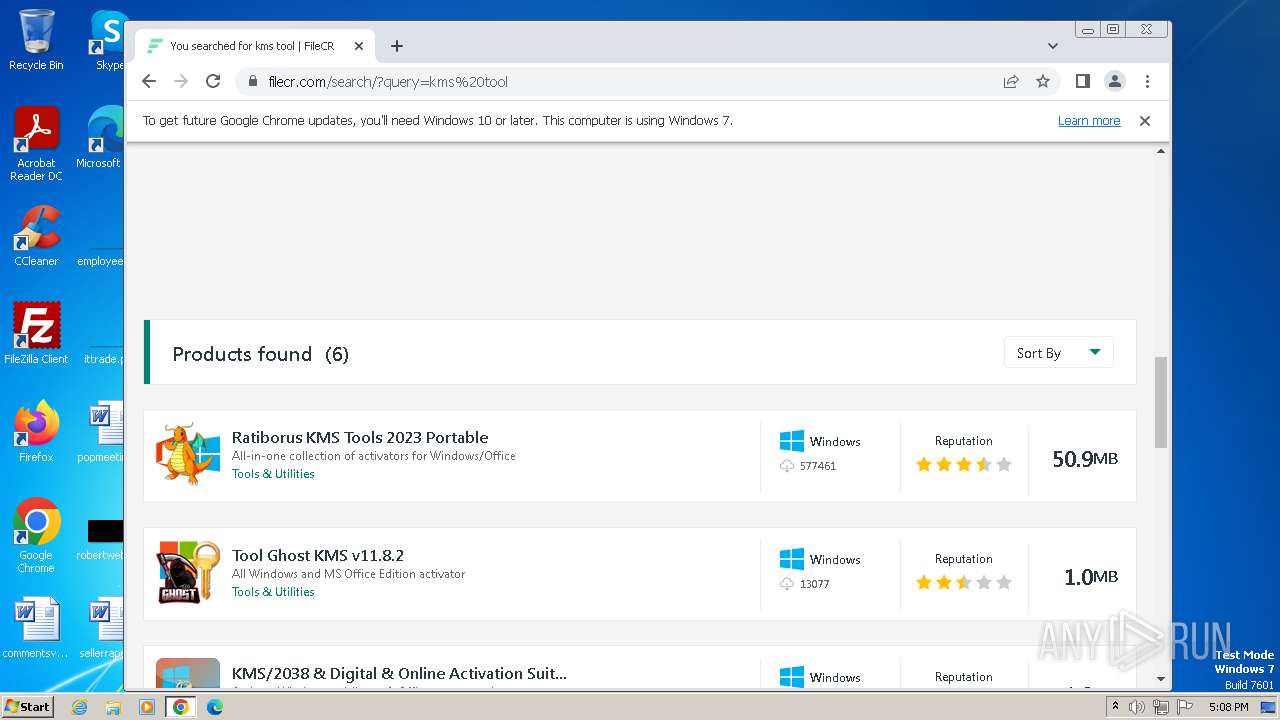
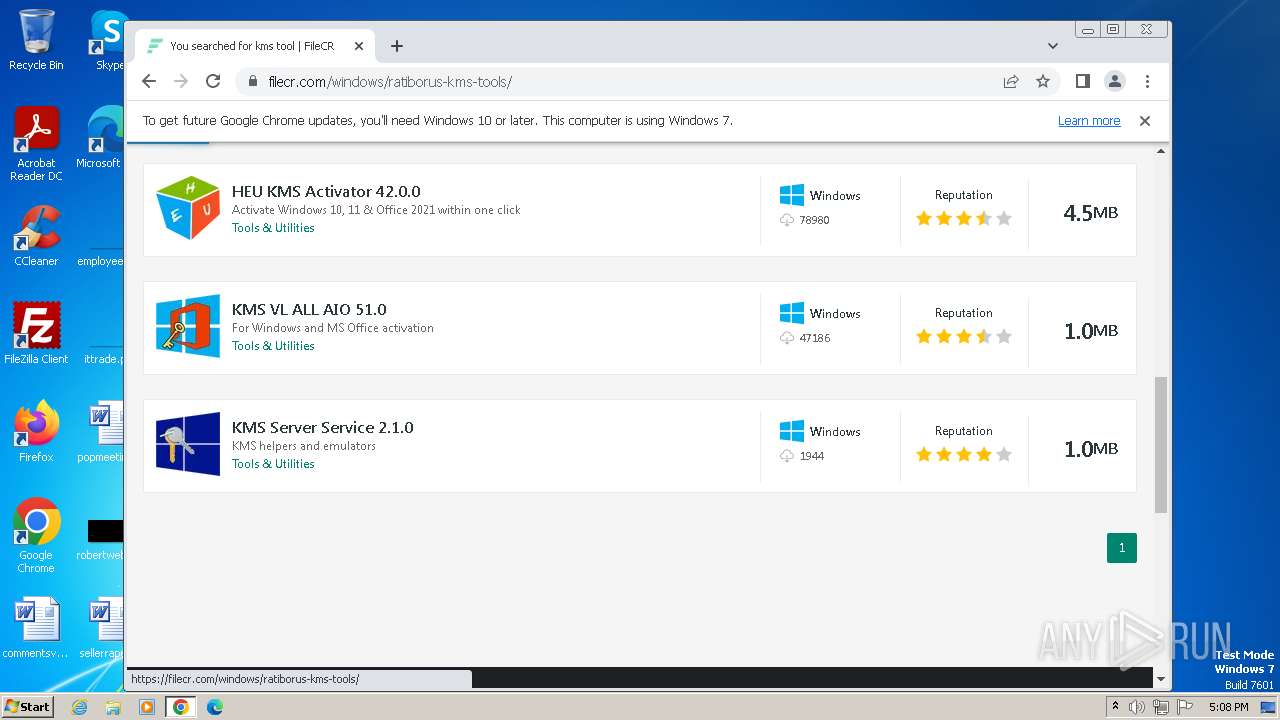
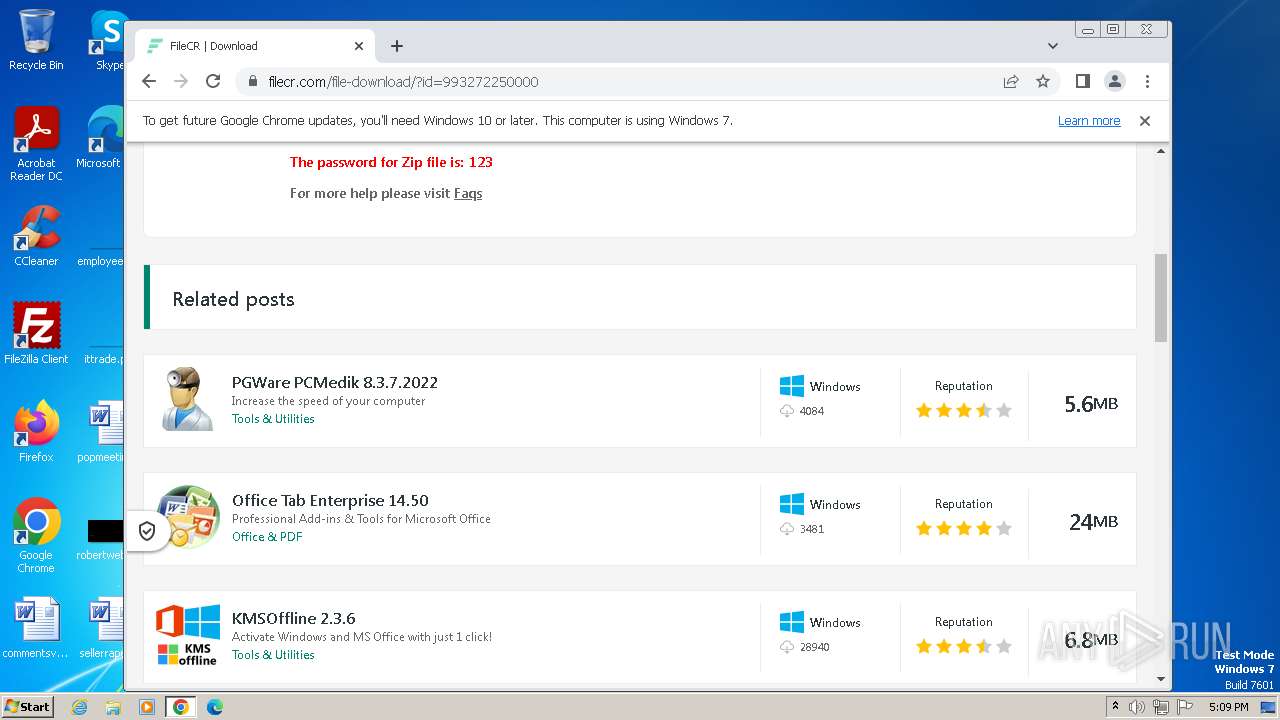
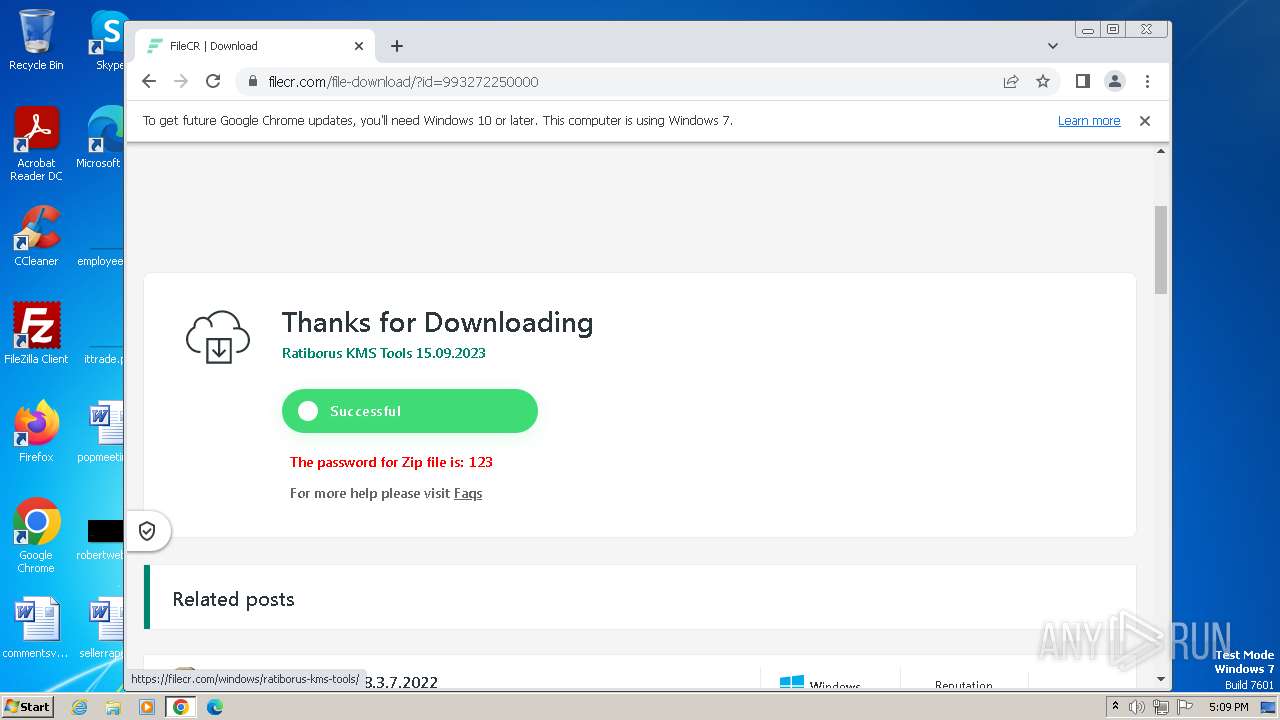
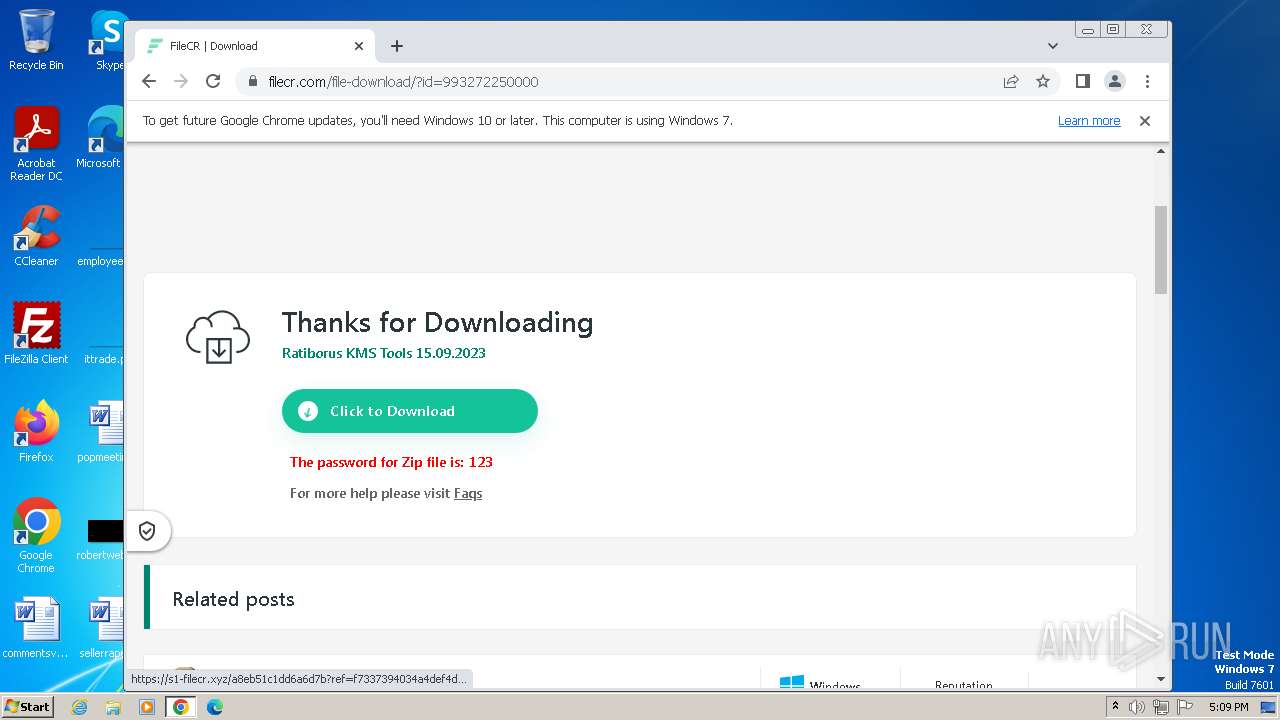
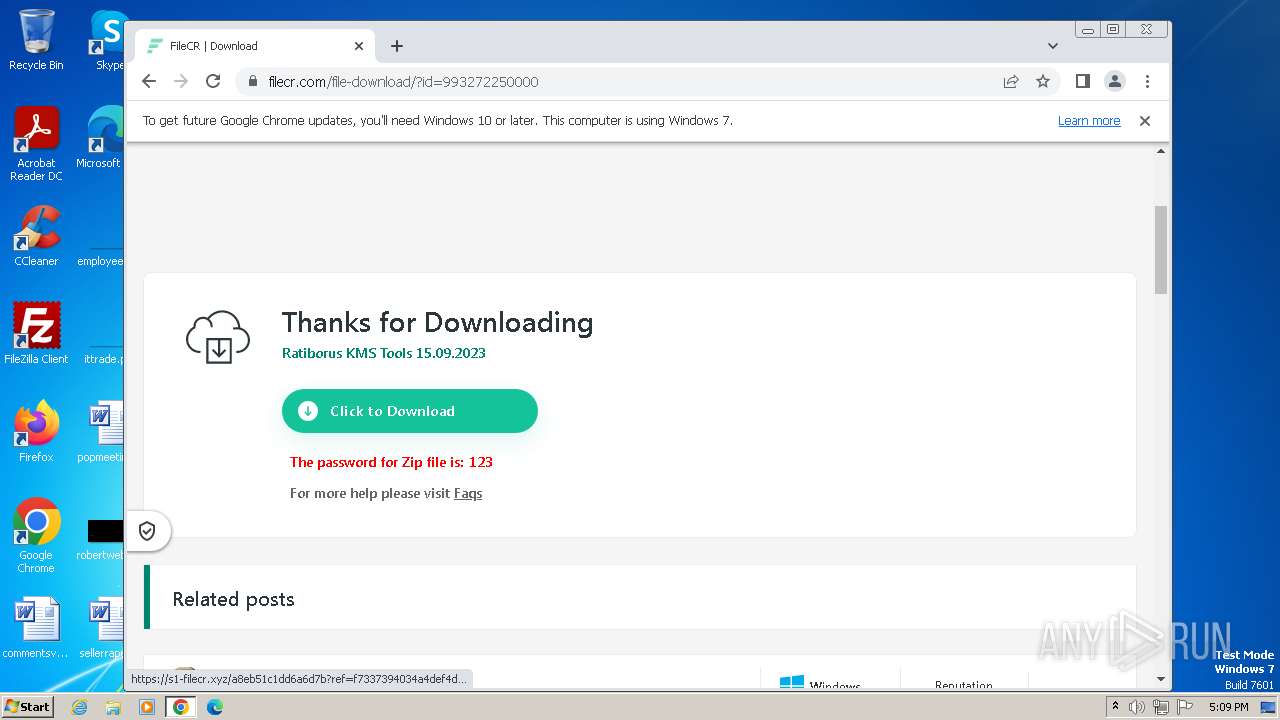
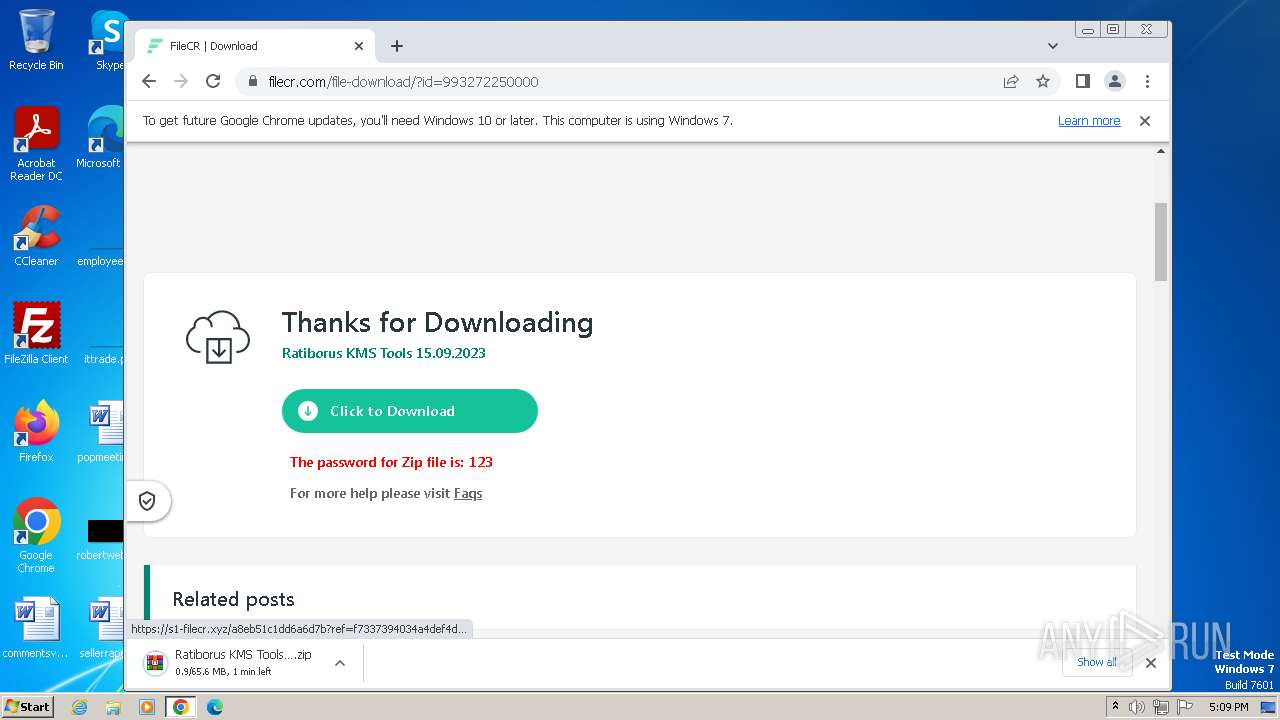
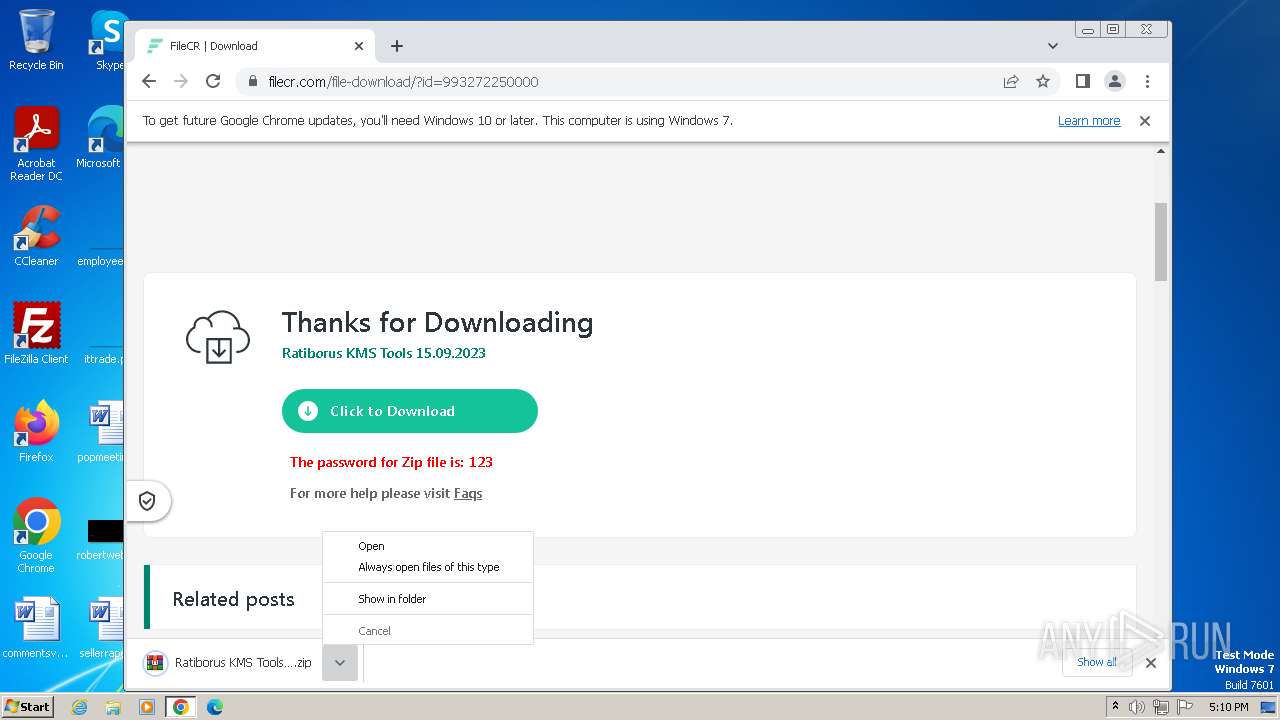
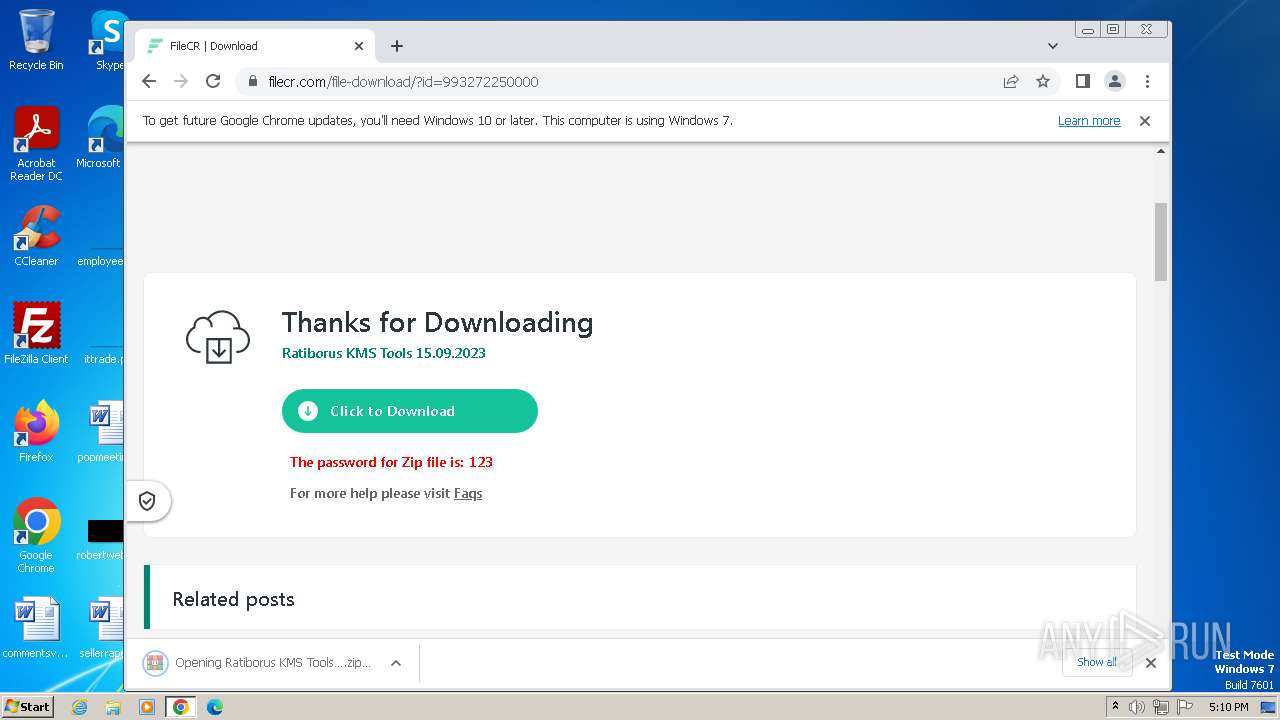
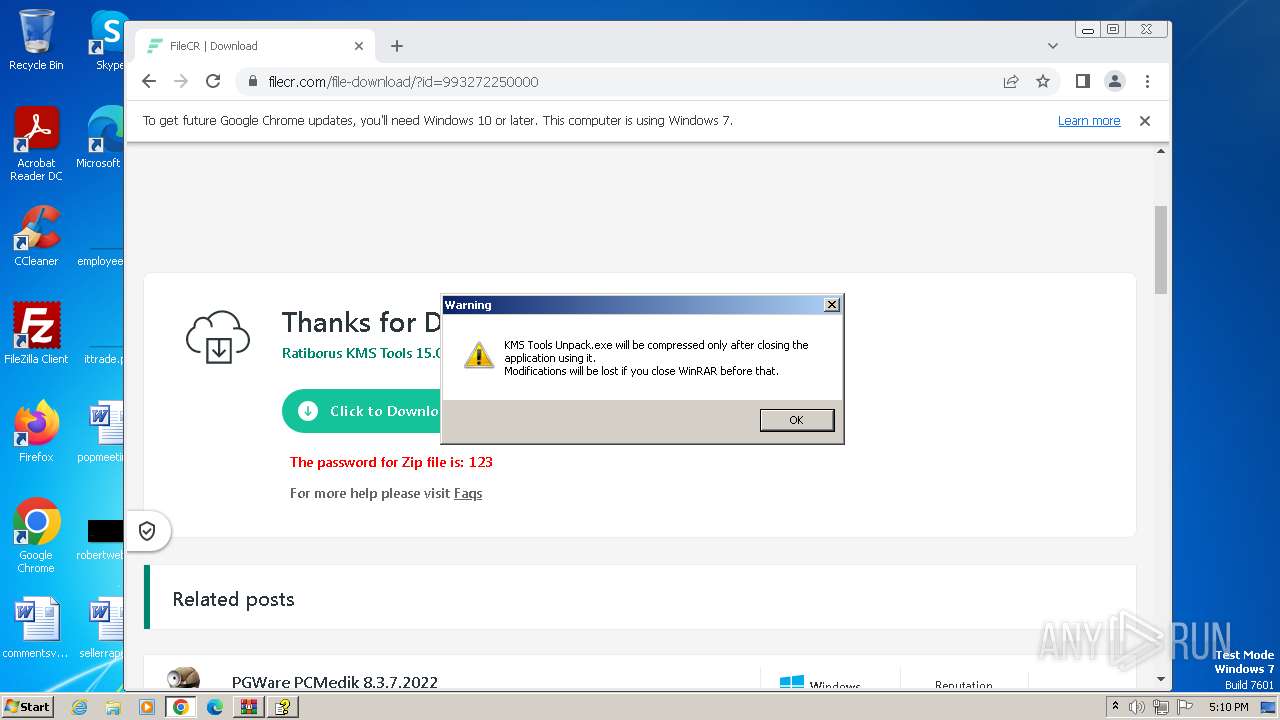
| URL: | filecr.com |
| Full analysis: | https://app.any.run/tasks/17a3b5b2-ef0e-4df2-893c-9610dd412320 |
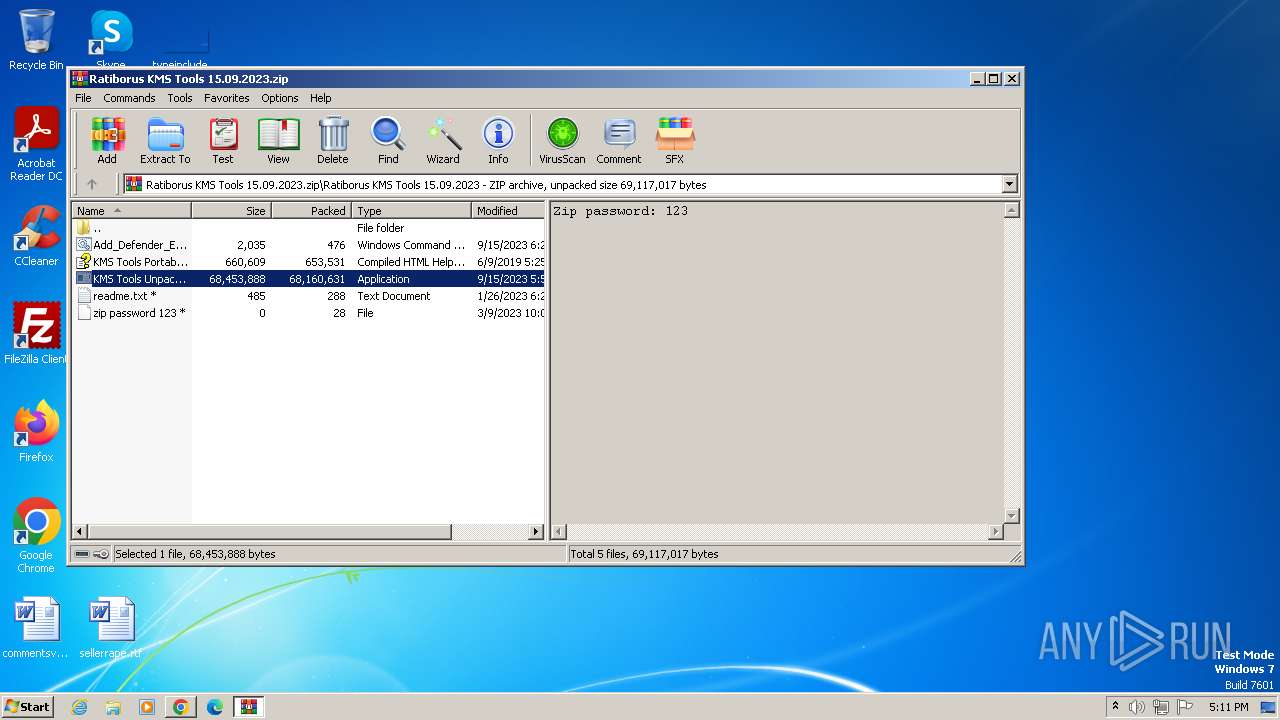
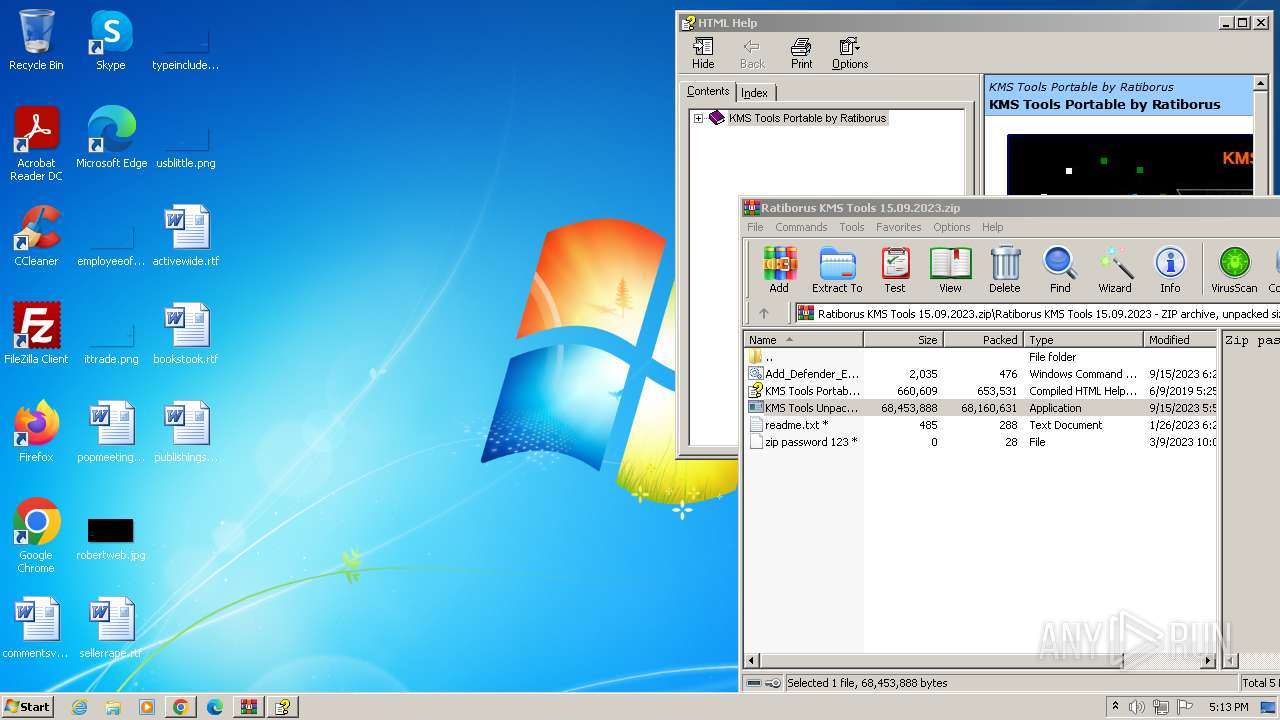
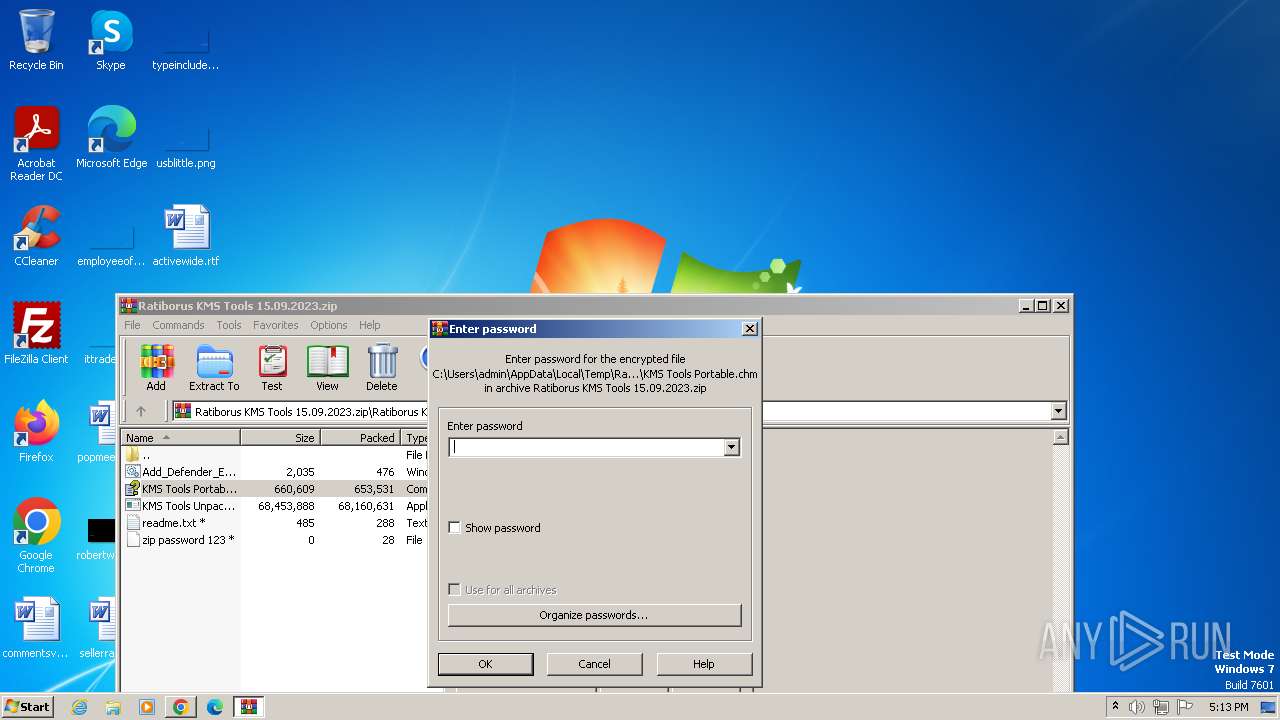
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2023, 17:08:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5C3FB34EF9C6FFA9C201EEB01532A2F7 |
| SHA1: | E71A3D5DA25D6FC6B07B9DA998E90F822E4C646B |
| SHA256: | 3F90F60B97985EAC331F3944BCEEAC8101363E315E372C355C2F38F936992EAA |
| SSDEEP: | 3:xAyTn:xA2n |
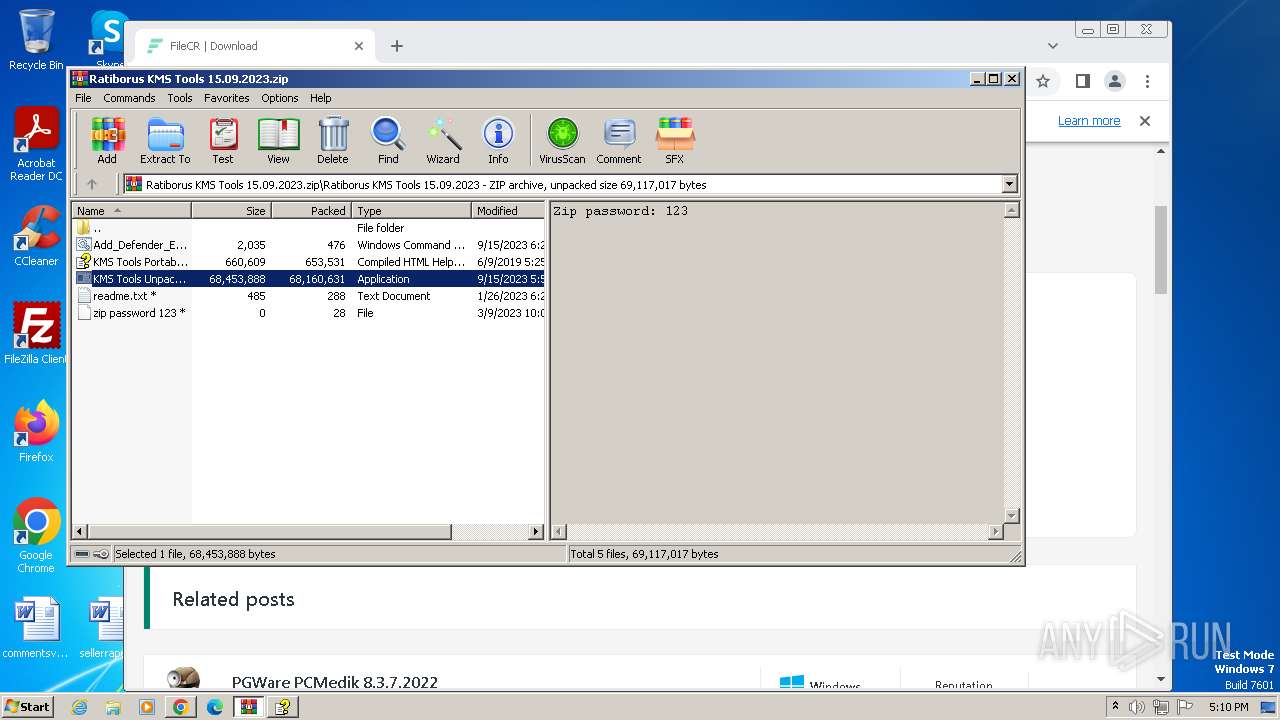
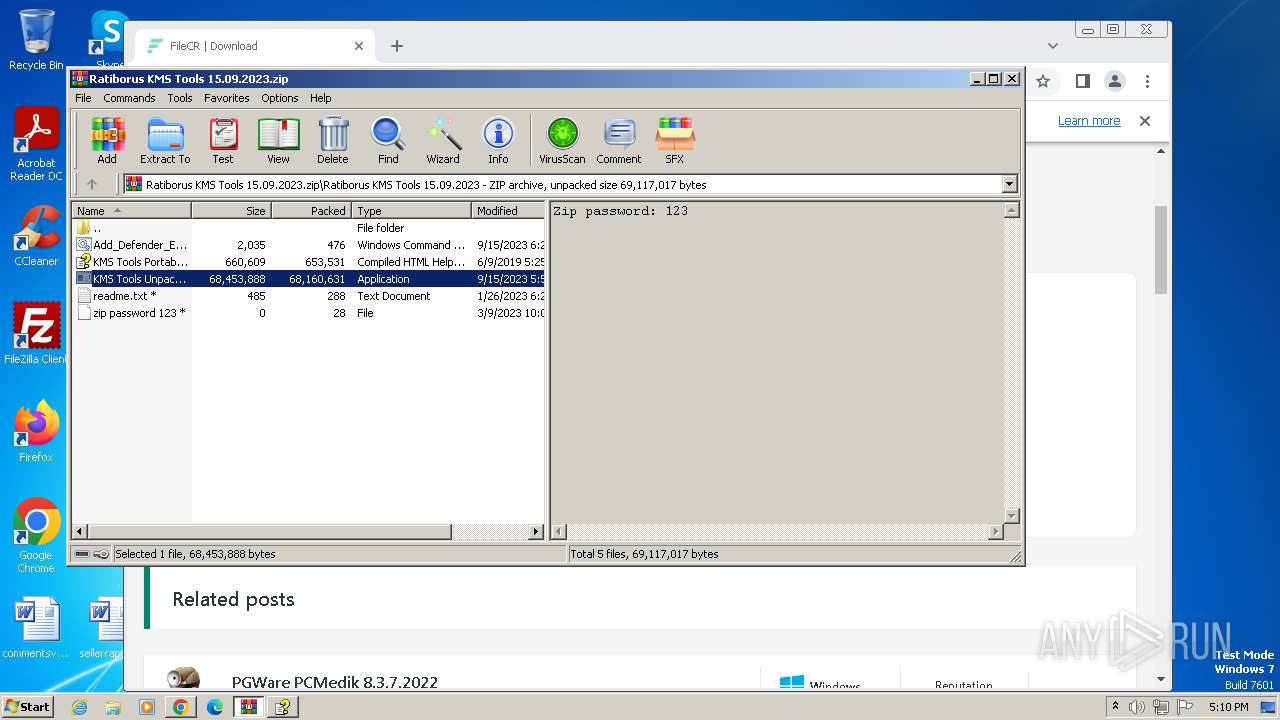
MALICIOUS
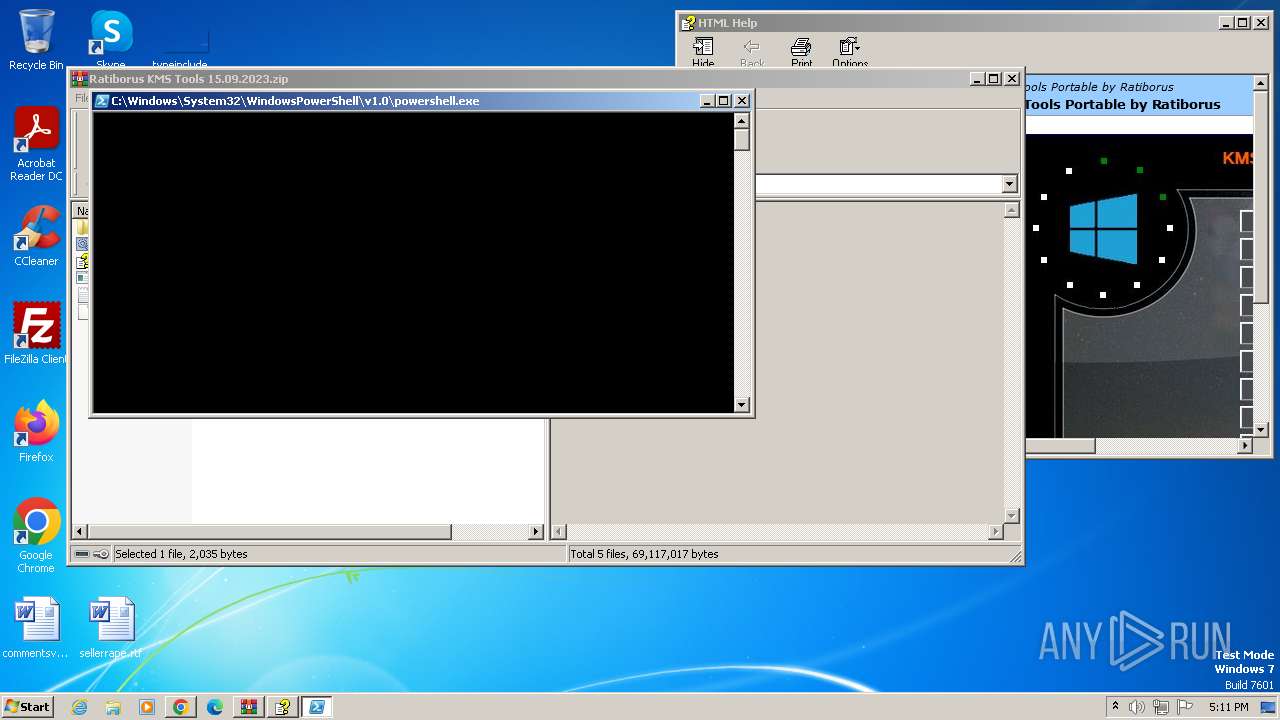
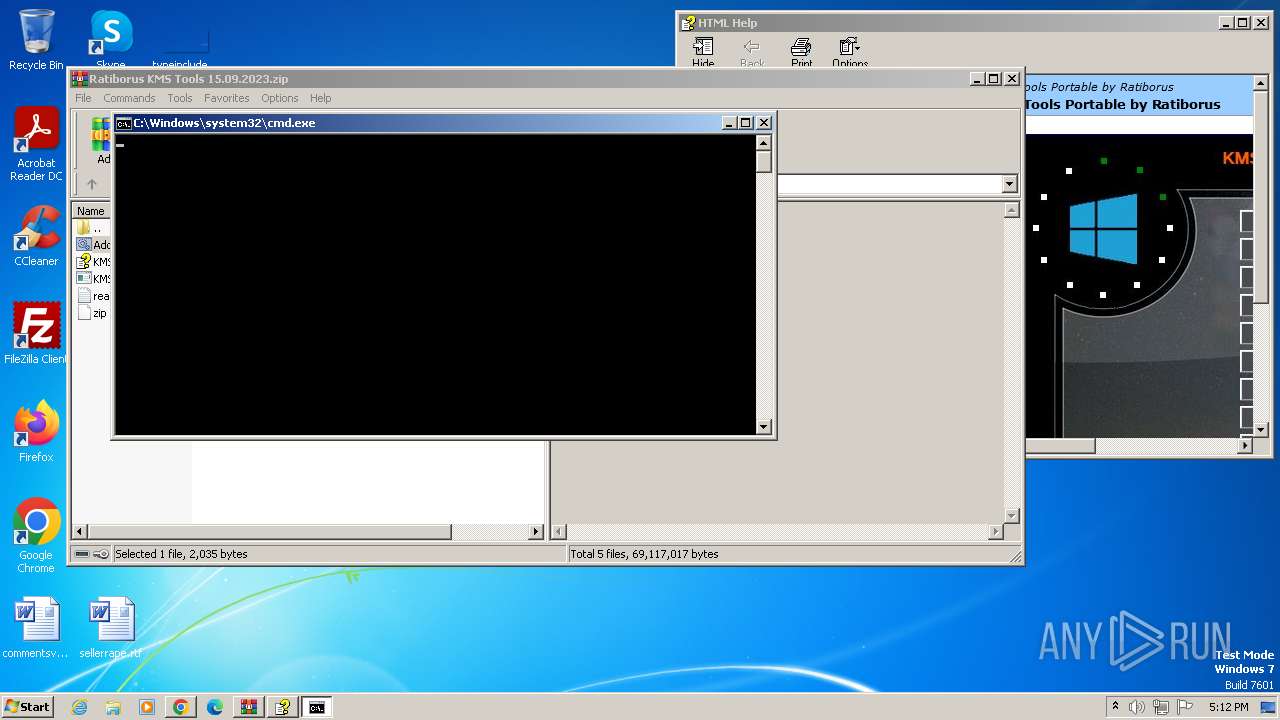
Run PowerShell with an invisible window
- powershell.exe (PID: 3132)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 888)
- powershell.exe (PID: 3996)
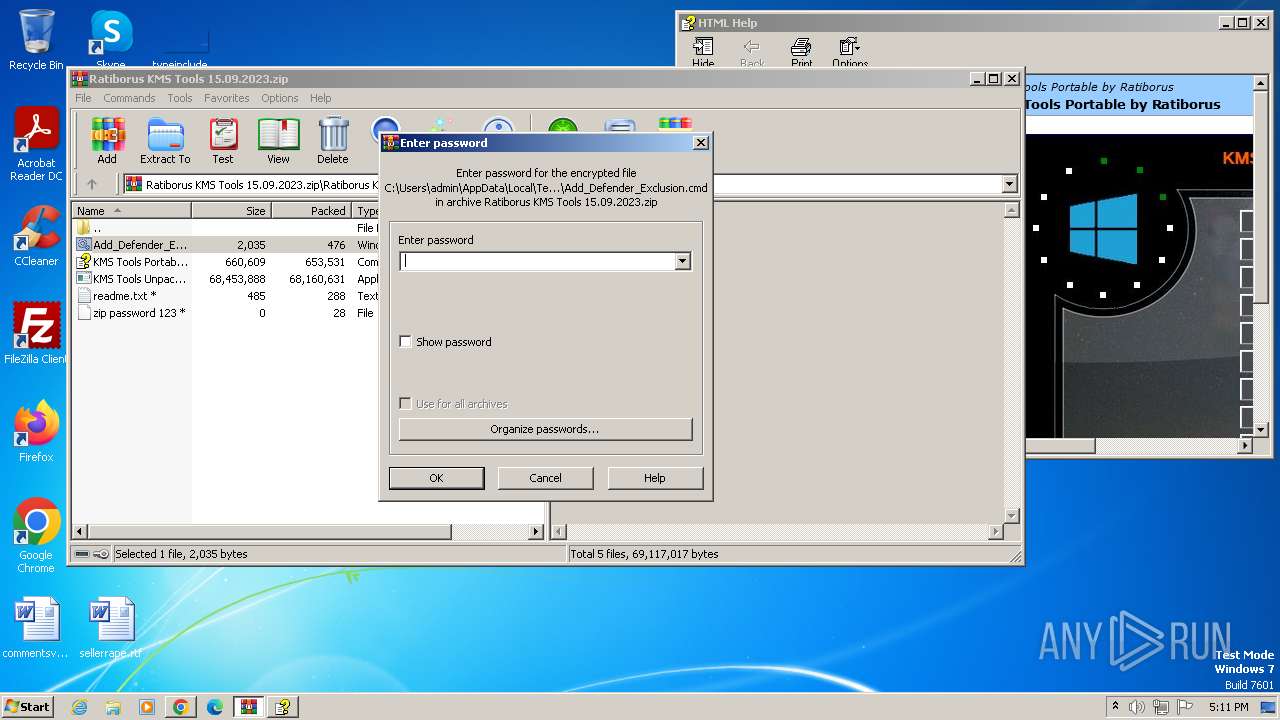
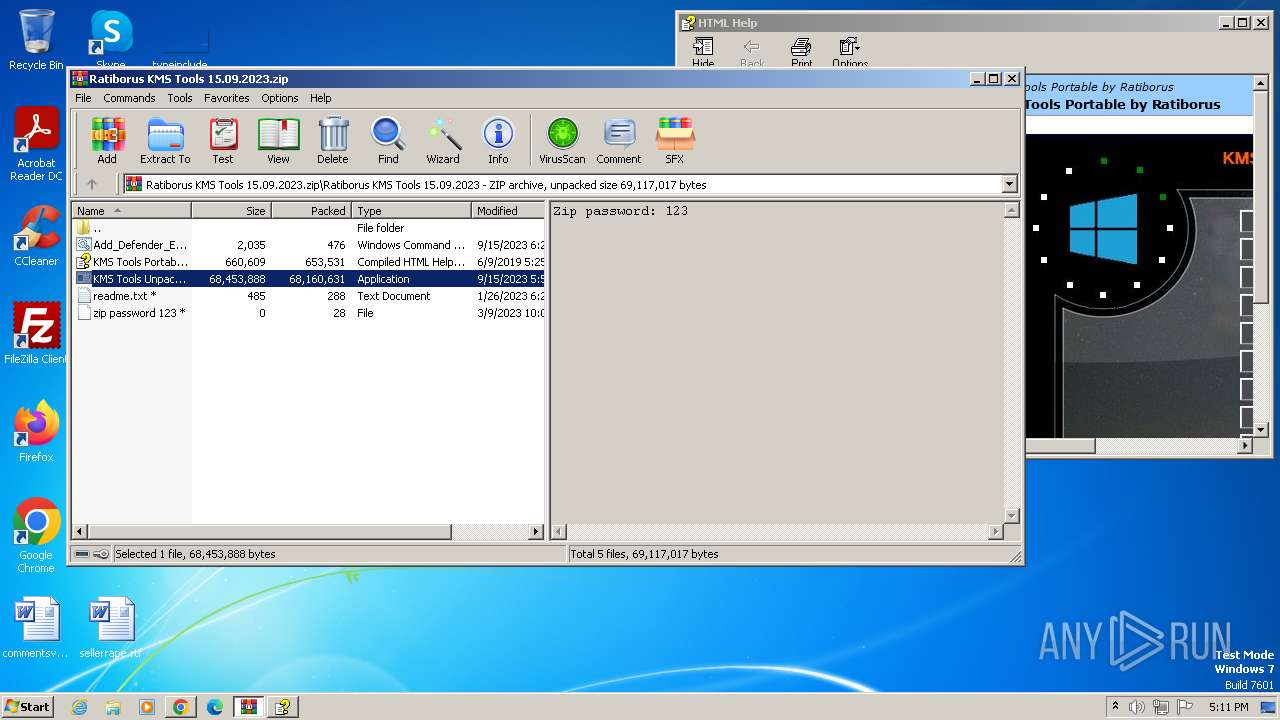
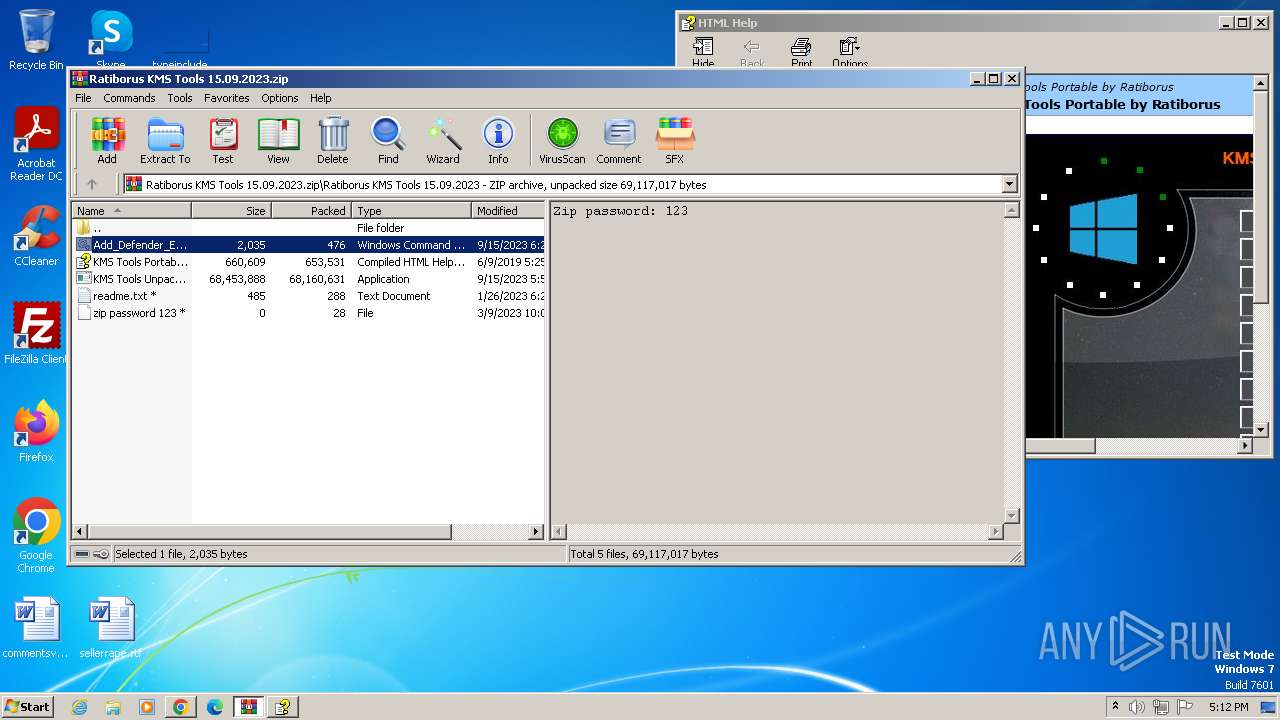
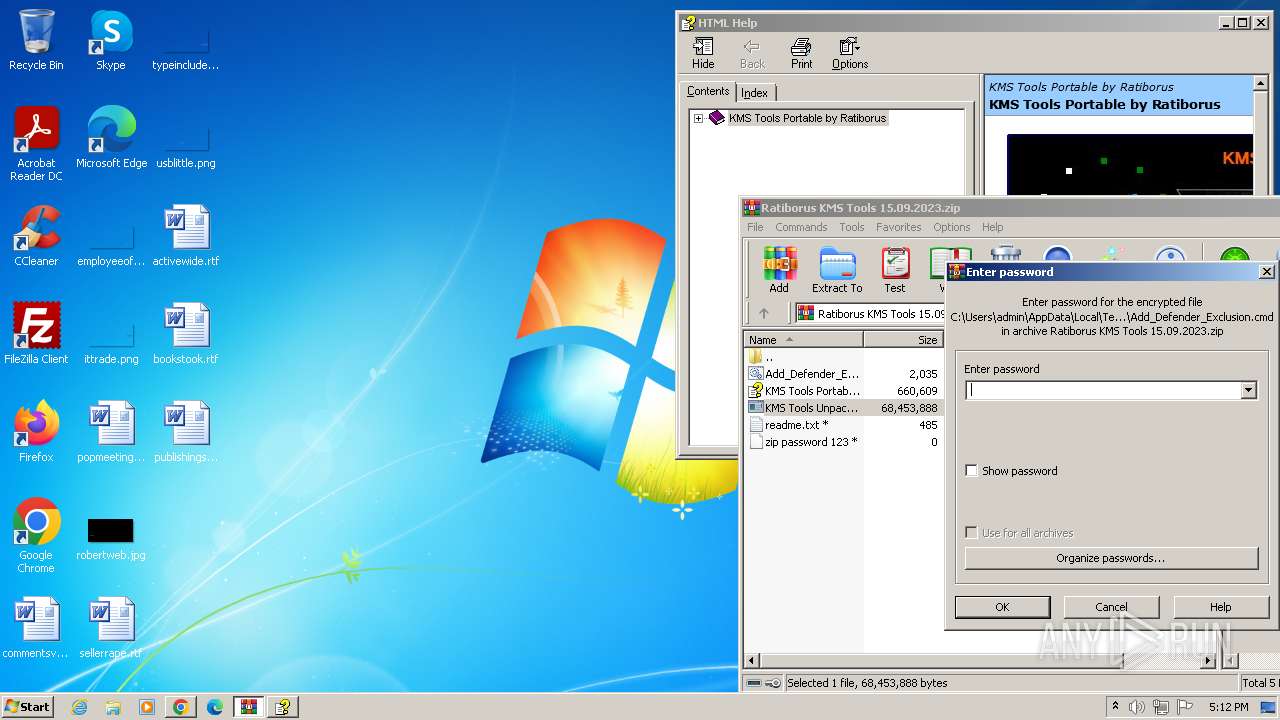
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2128)
SUSPICIOUS
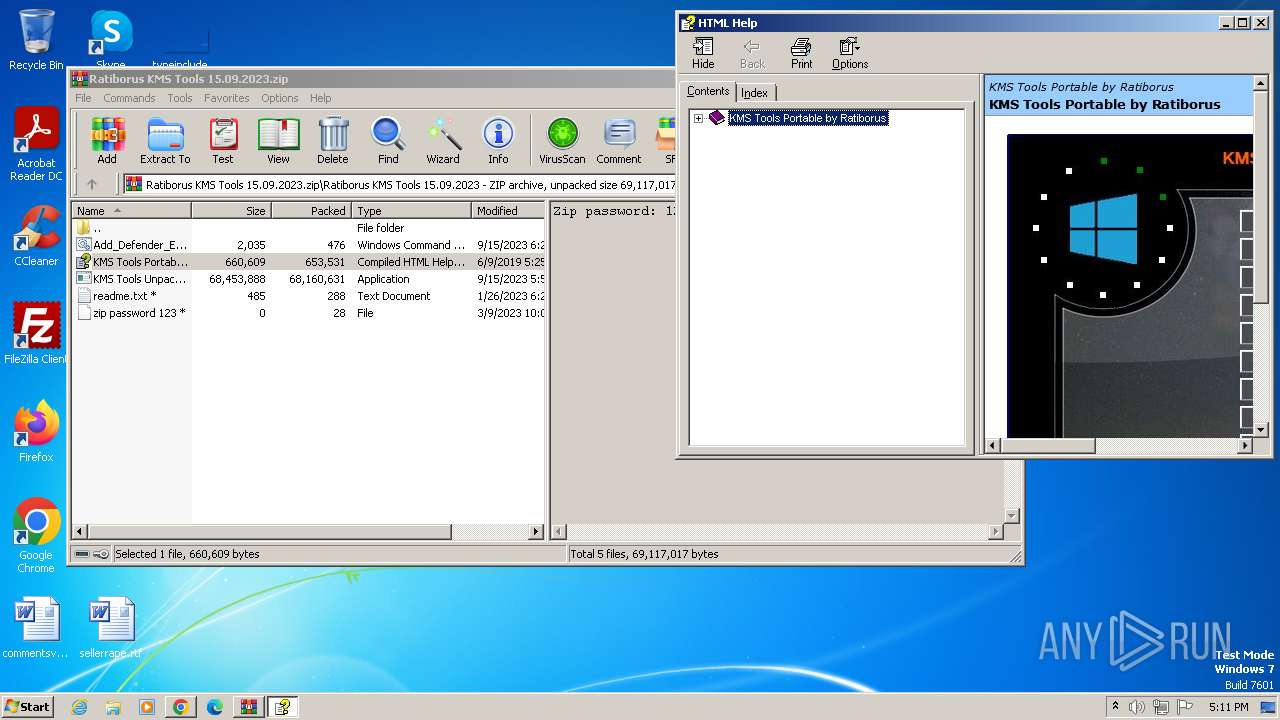
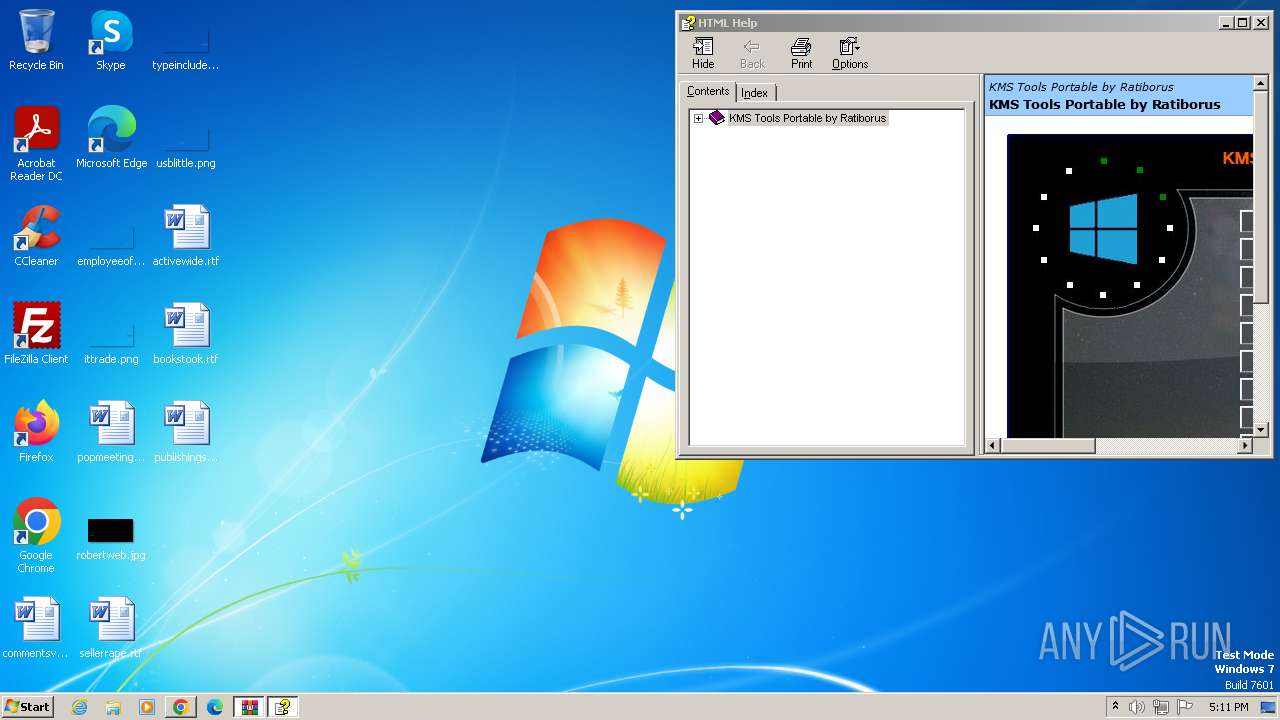
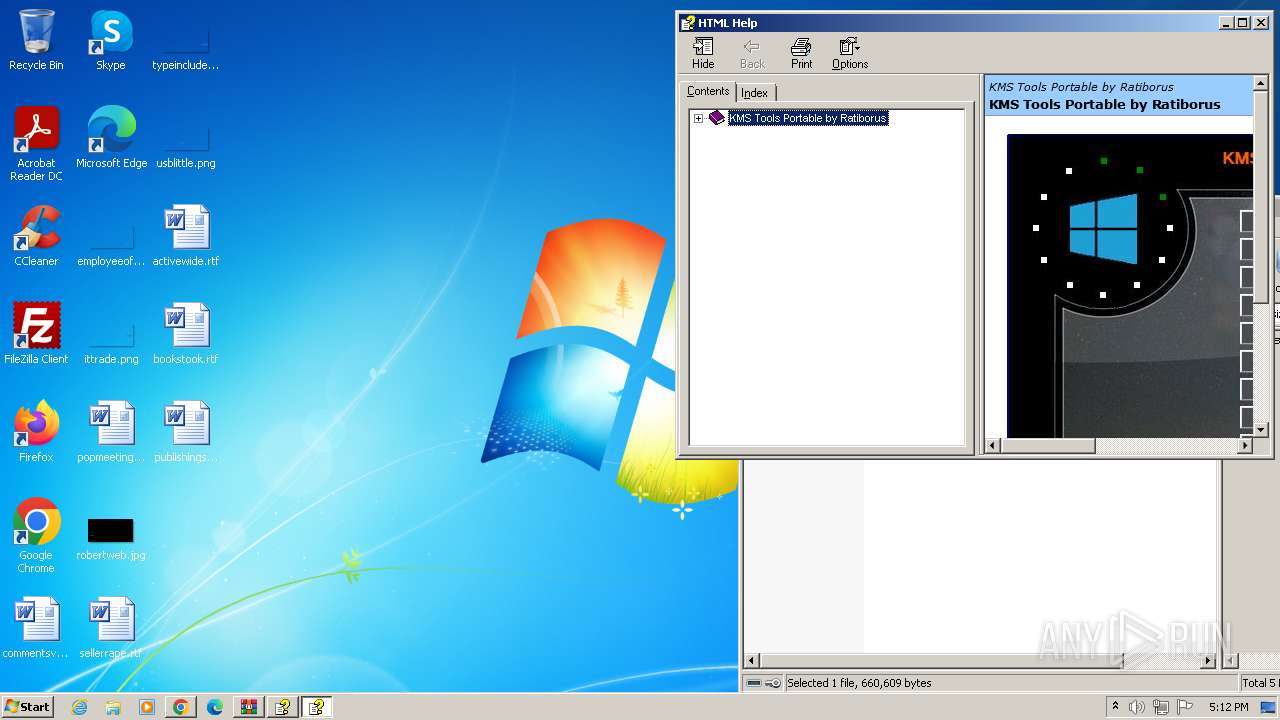
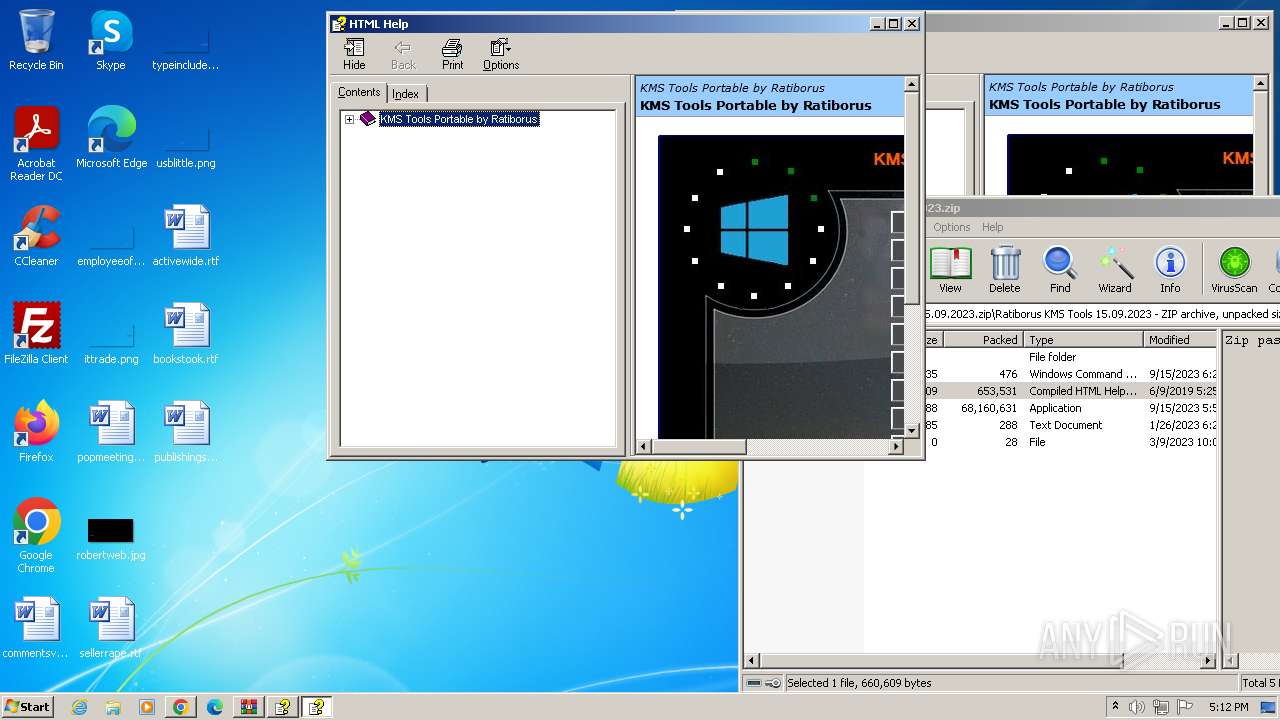
Reads the Internet Settings
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 888)
- hh.exe (PID: 1616)
Reads Microsoft Outlook installation path
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- hh.exe (PID: 1616)
Reads Internet Explorer settings
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- hh.exe (PID: 1616)
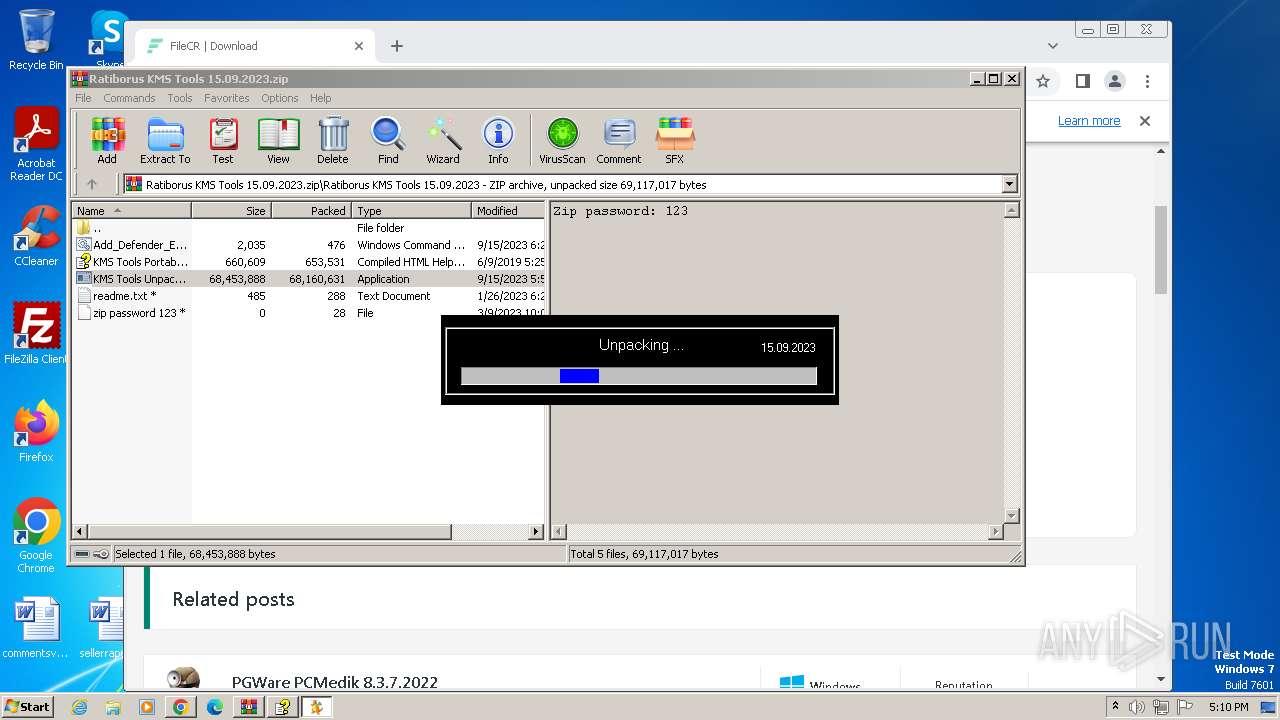
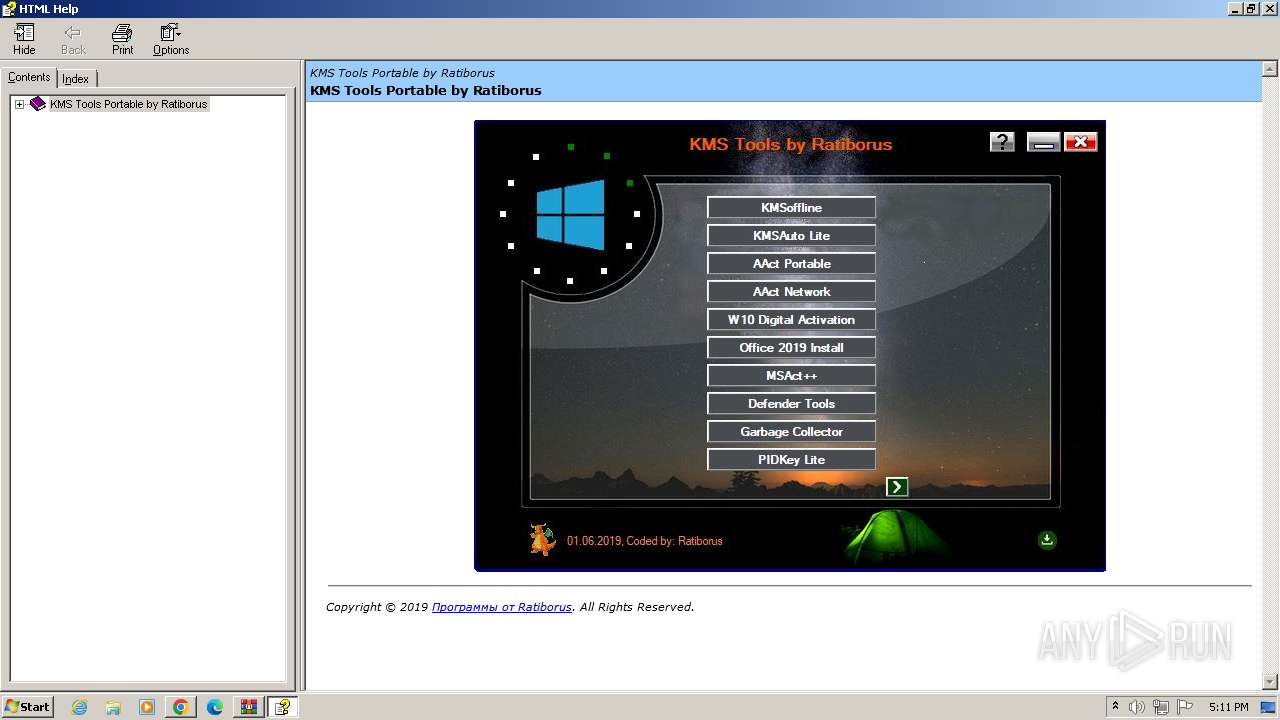
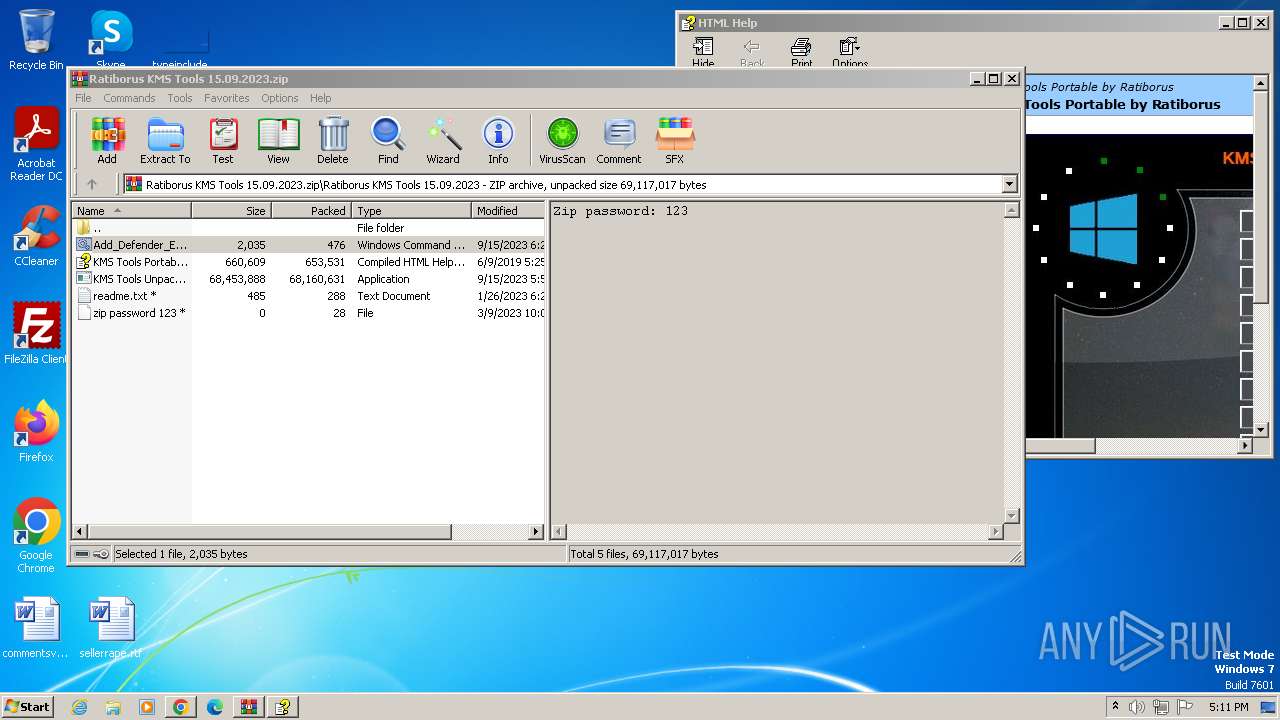
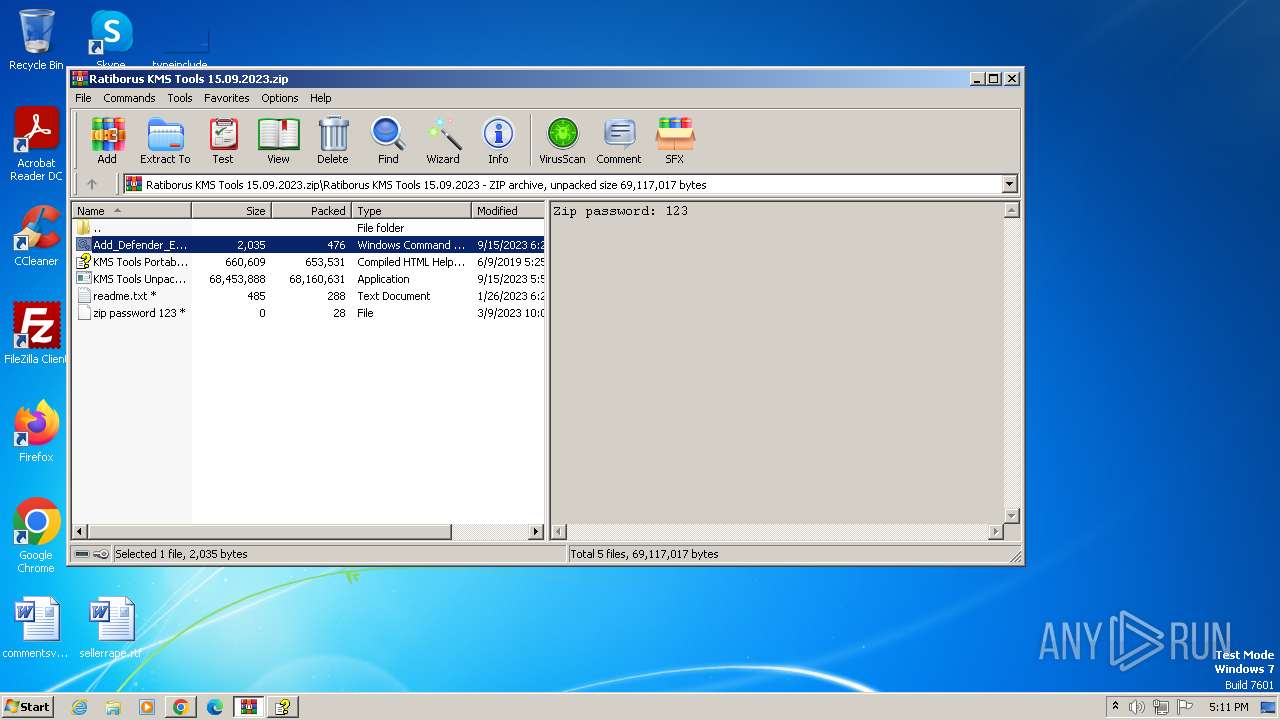
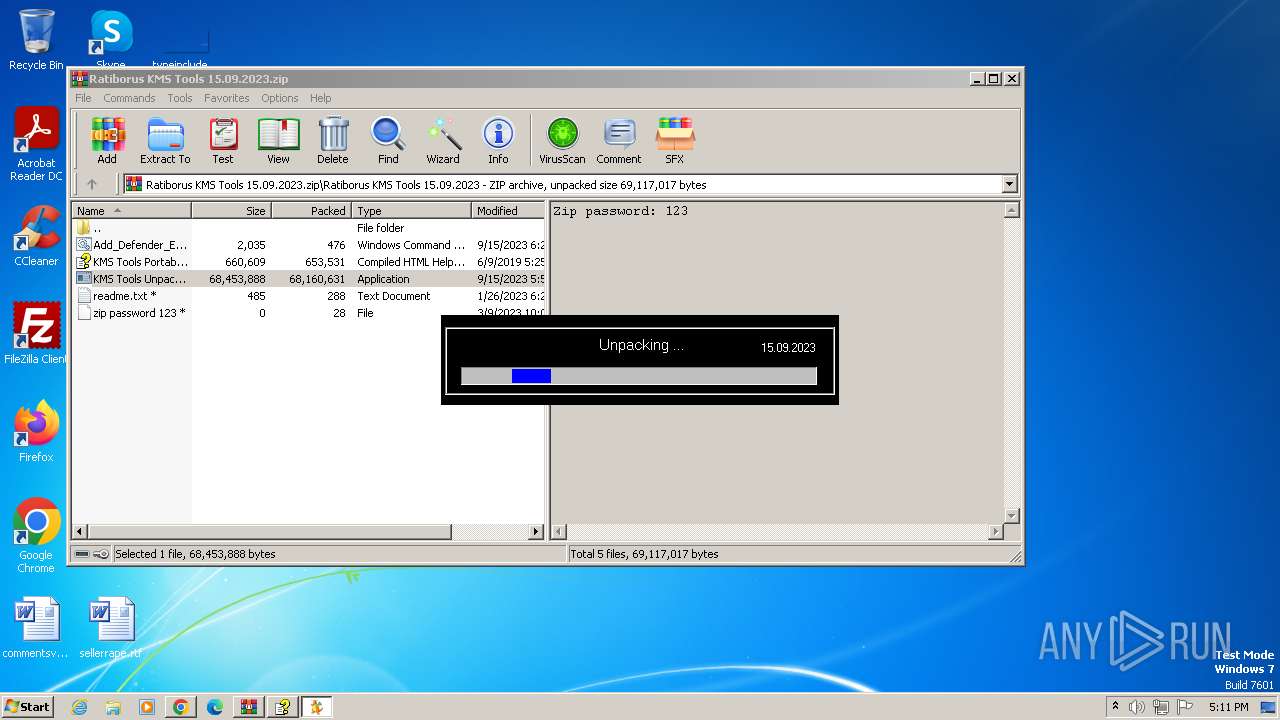
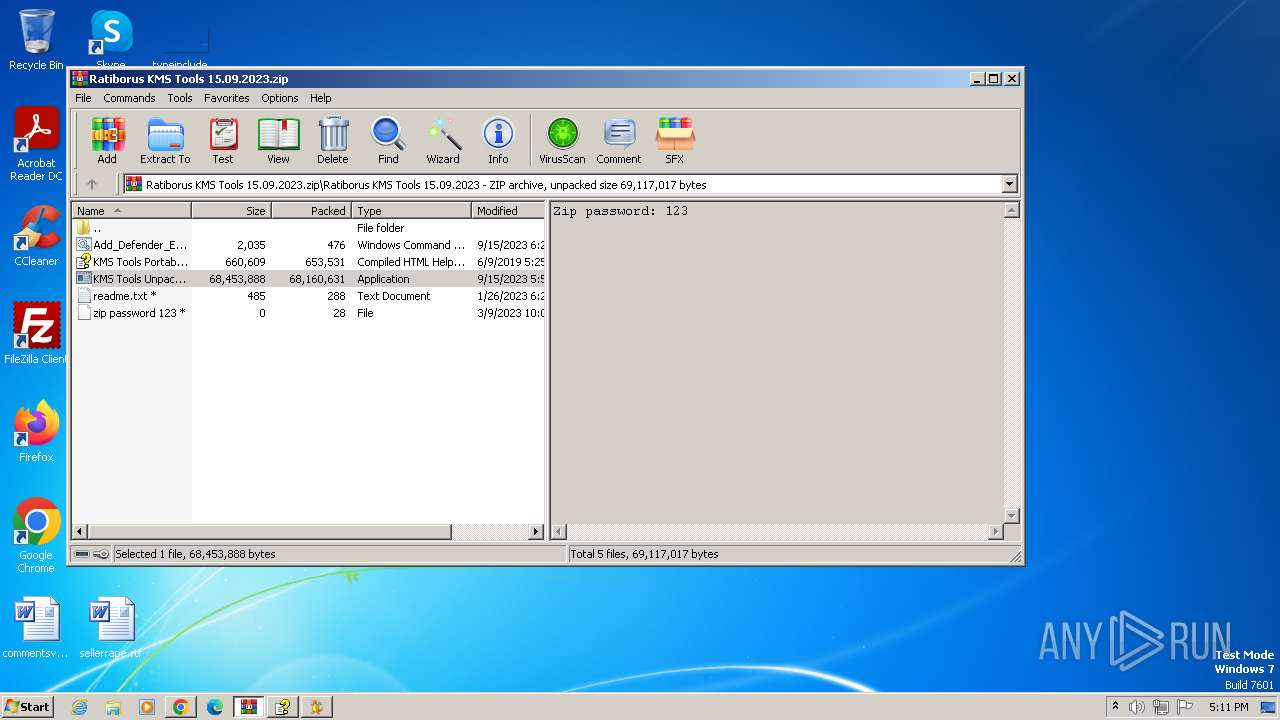
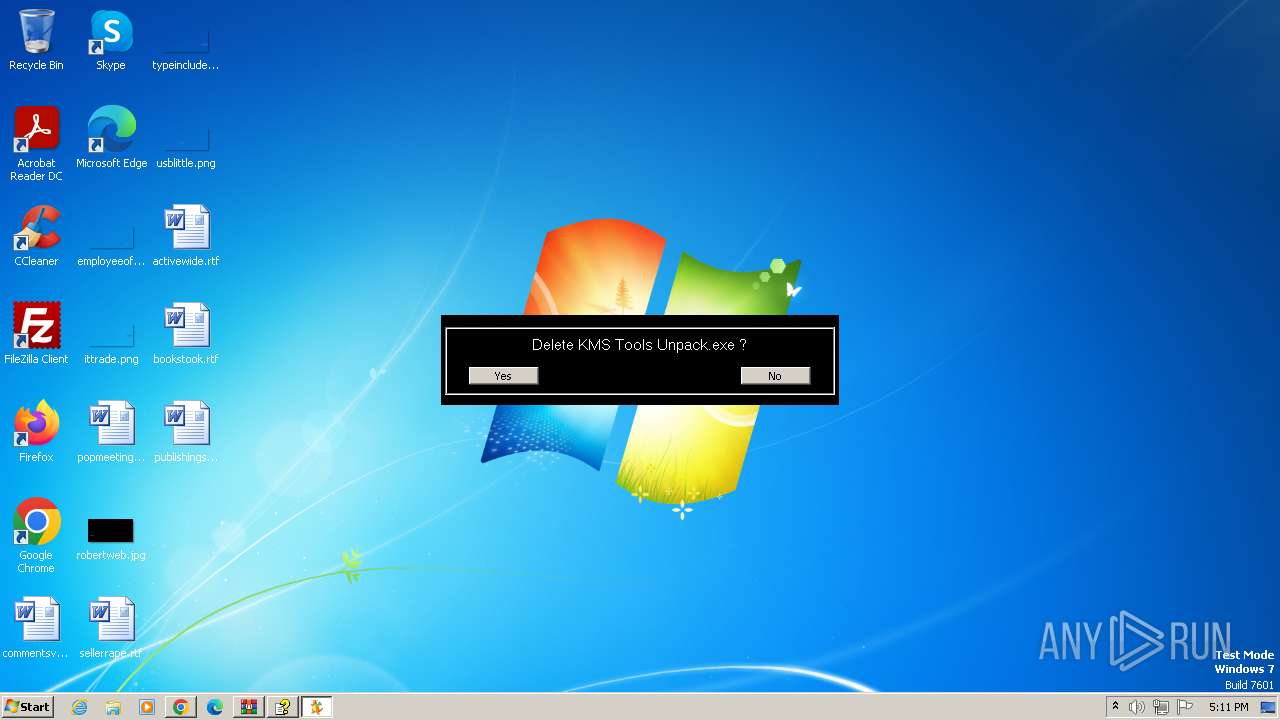
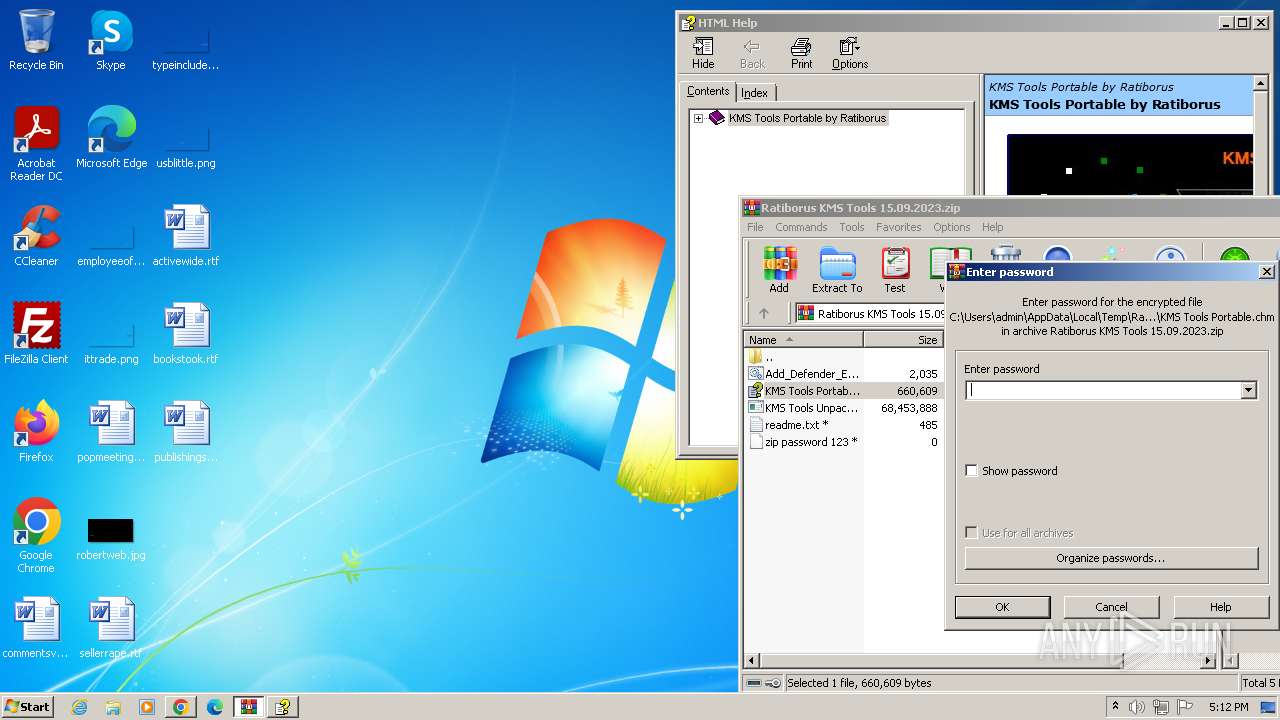
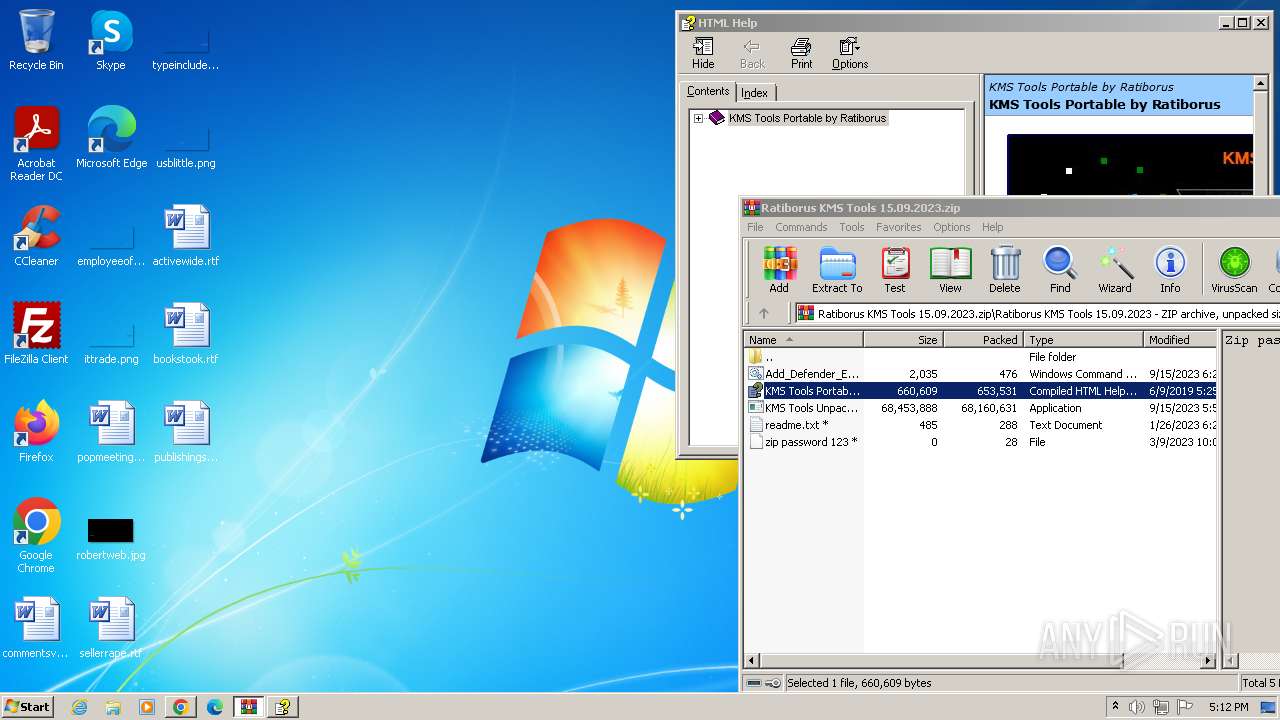
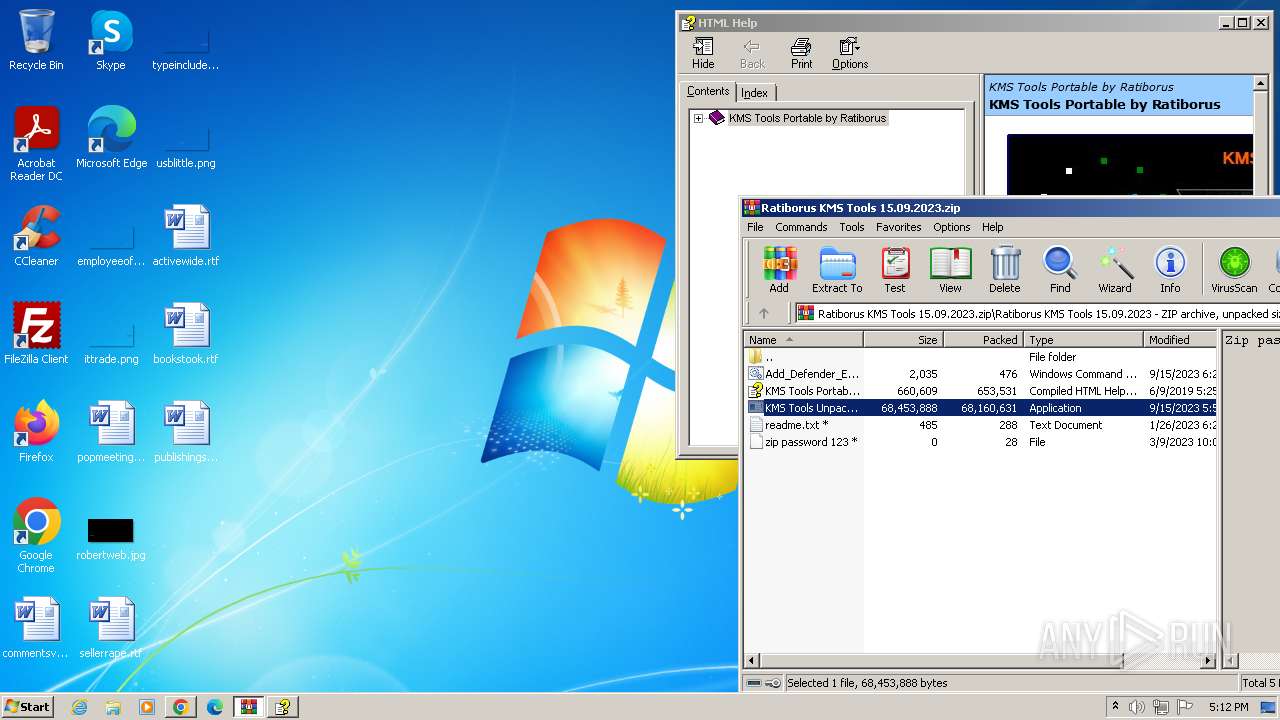
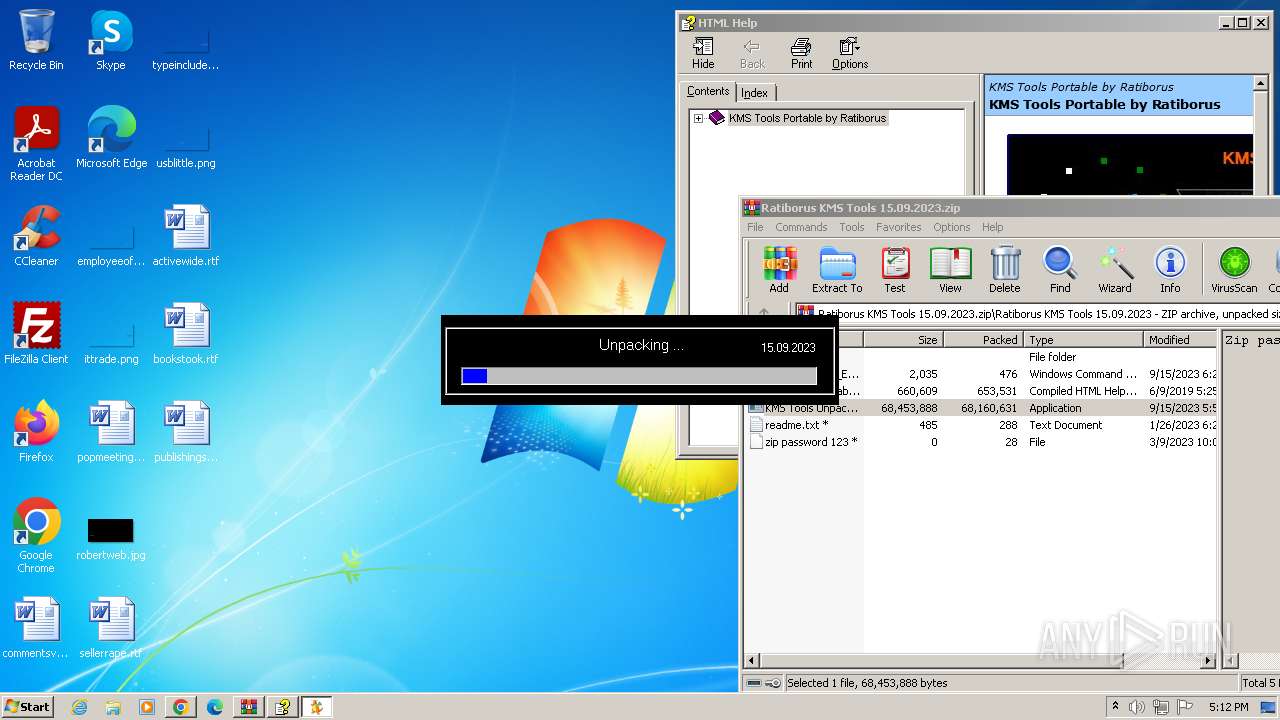
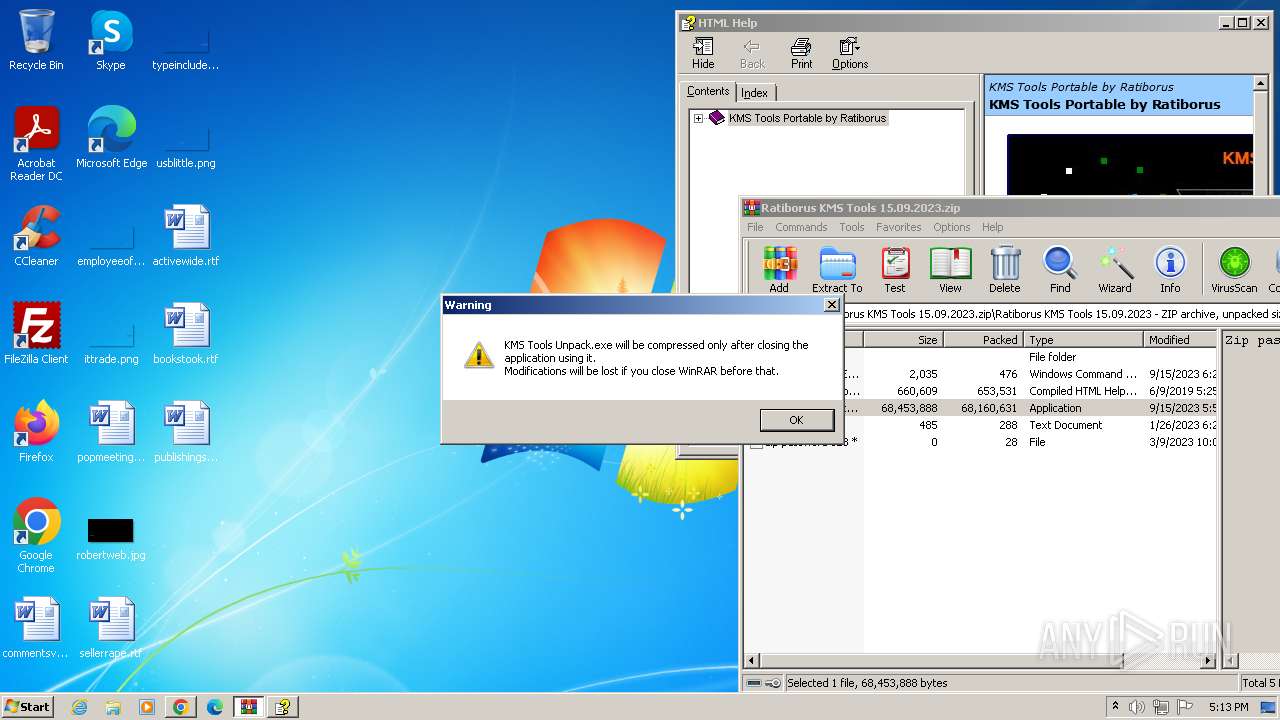
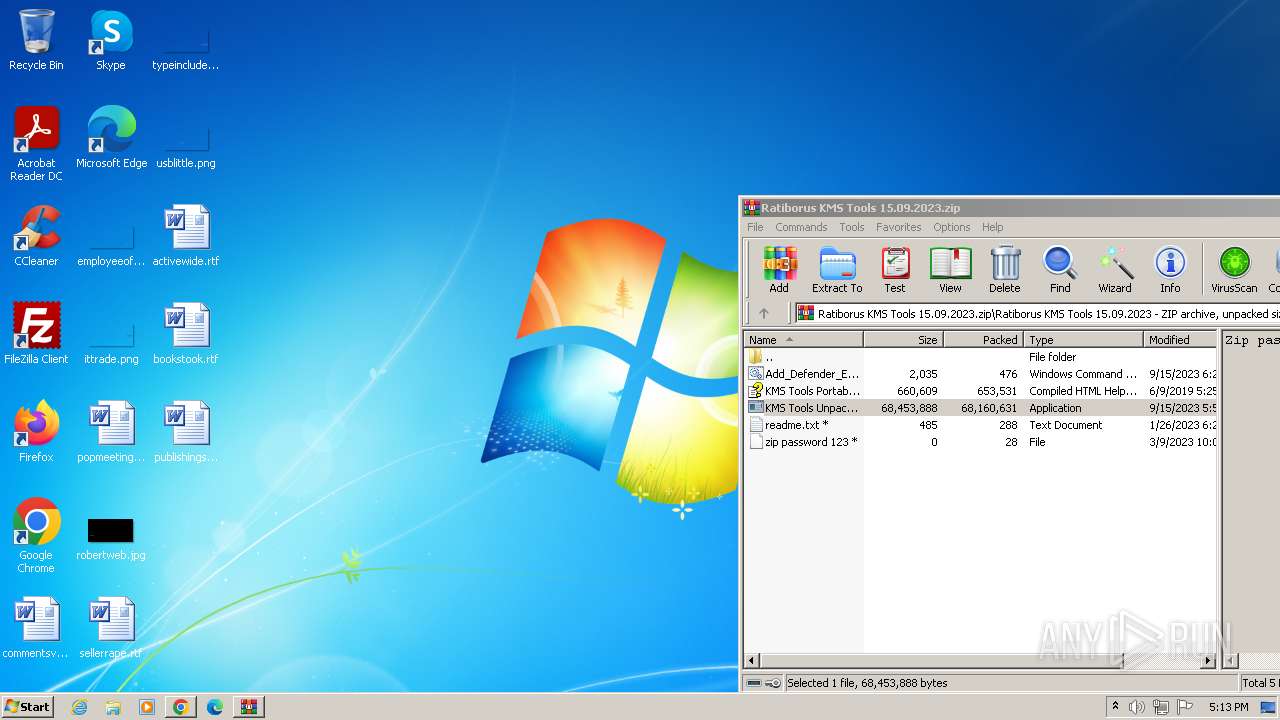
Executing commands from a ".bat" file
- KMS Tools Unpack.exe (PID: 664)
- KMS Tools Unpack.exe (PID: 1840)
Starts CMD.EXE for commands execution
- KMS Tools Unpack.exe (PID: 664)
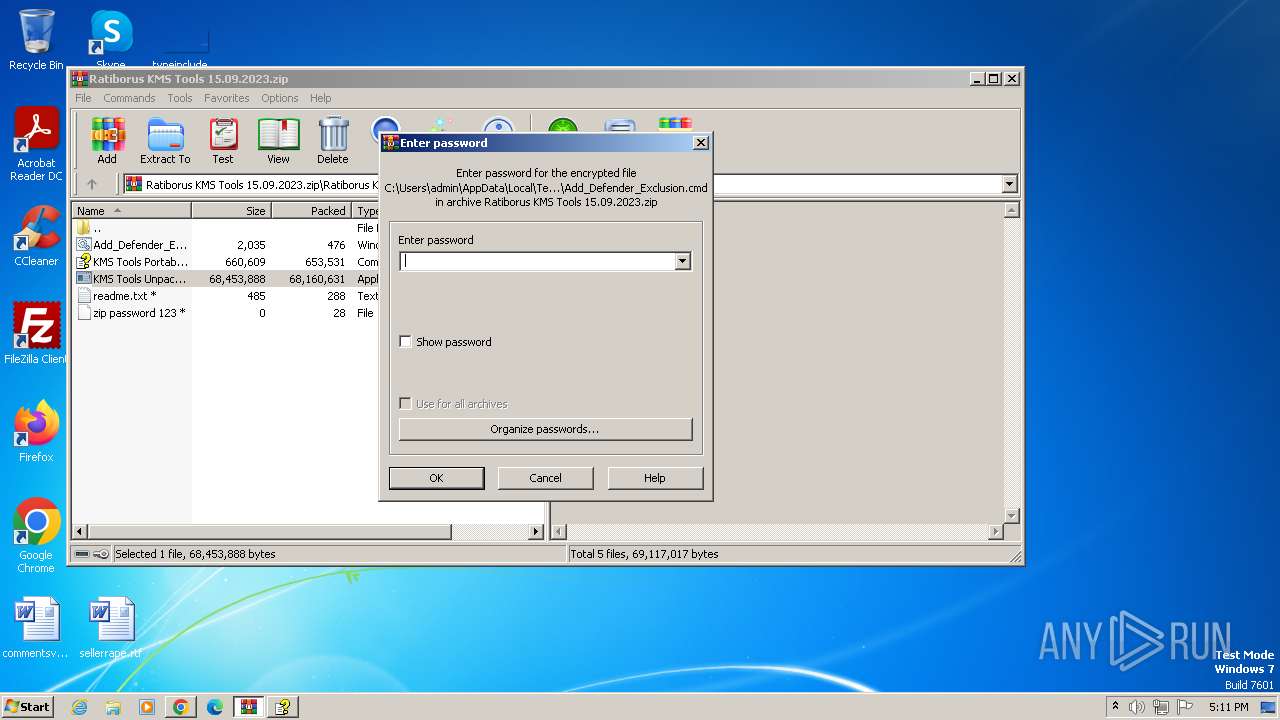
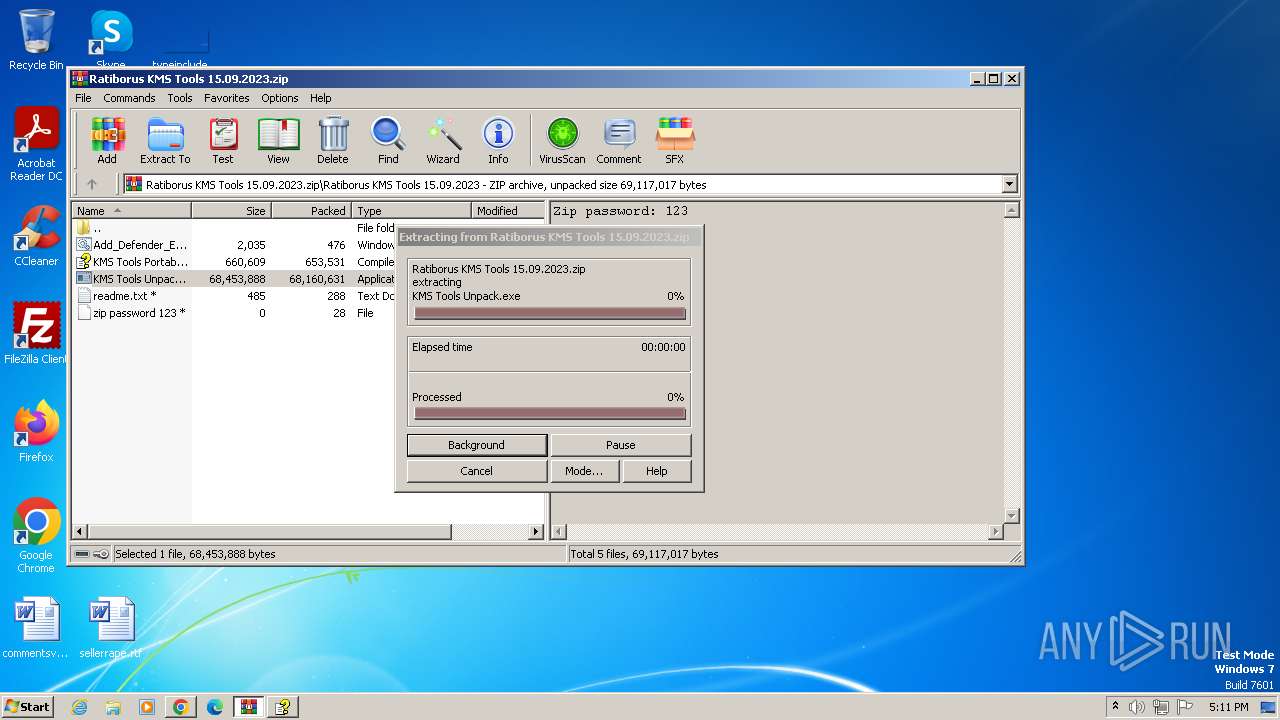
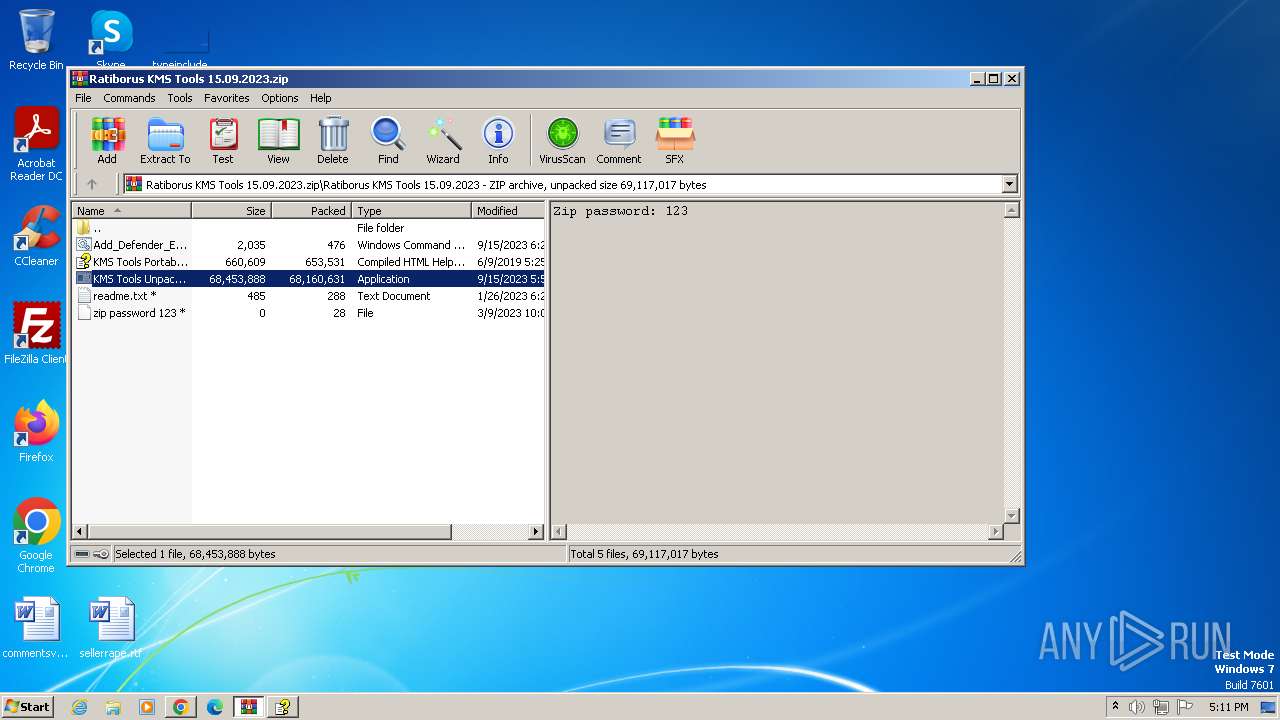
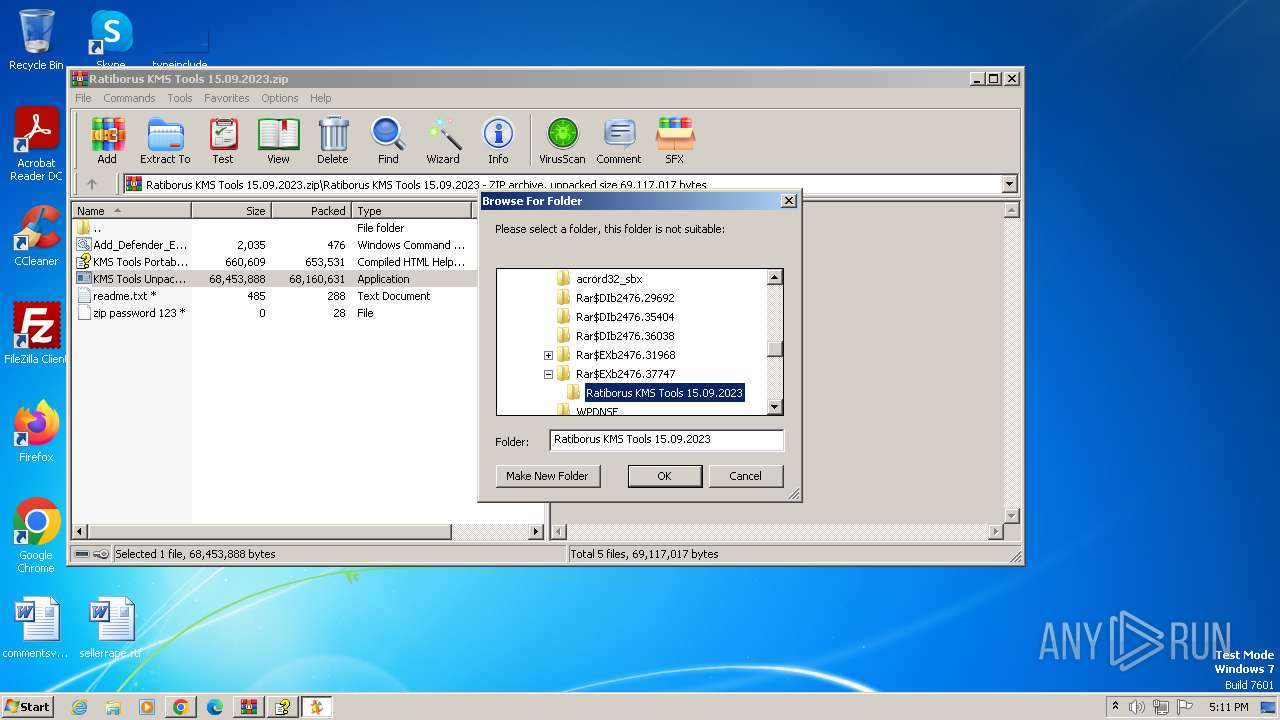
- WinRAR.exe (PID: 2476)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 888)
- KMS Tools Unpack.exe (PID: 1840)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 148)
- cmd.exe (PID: 3784)
Starts application with an unusual extension
- cmd.exe (PID: 148)
- cmd.exe (PID: 3784)
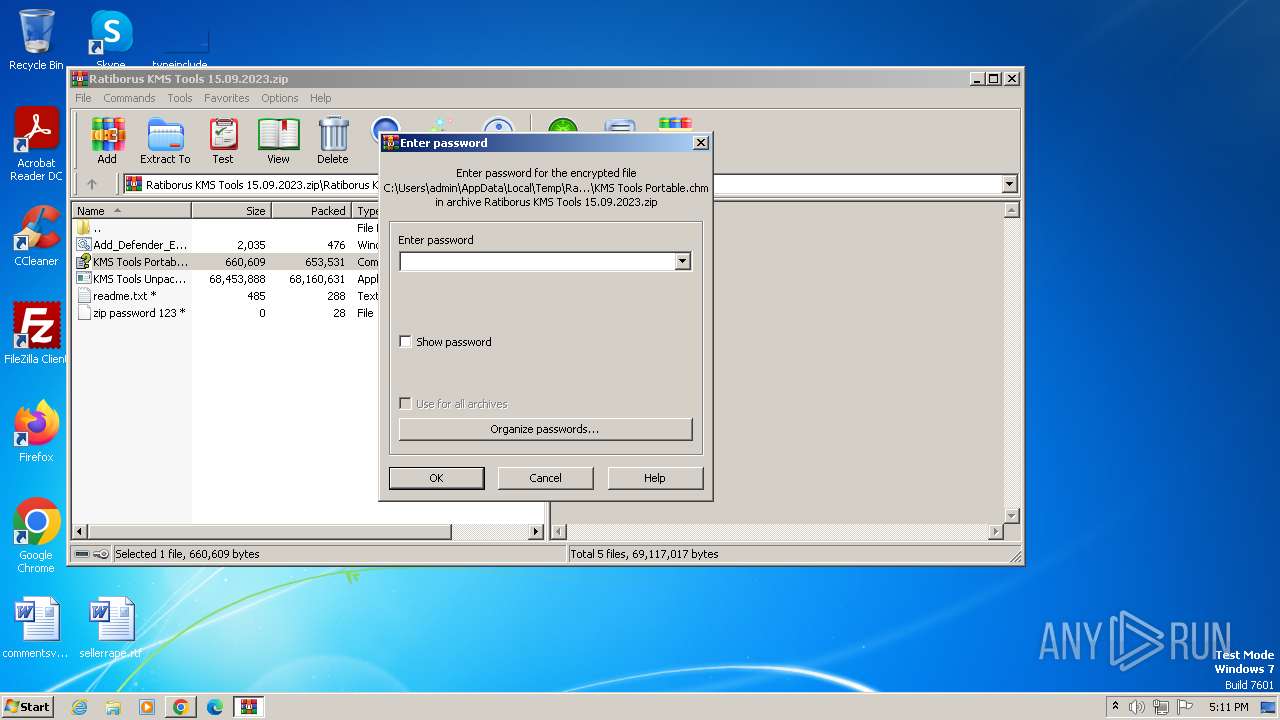
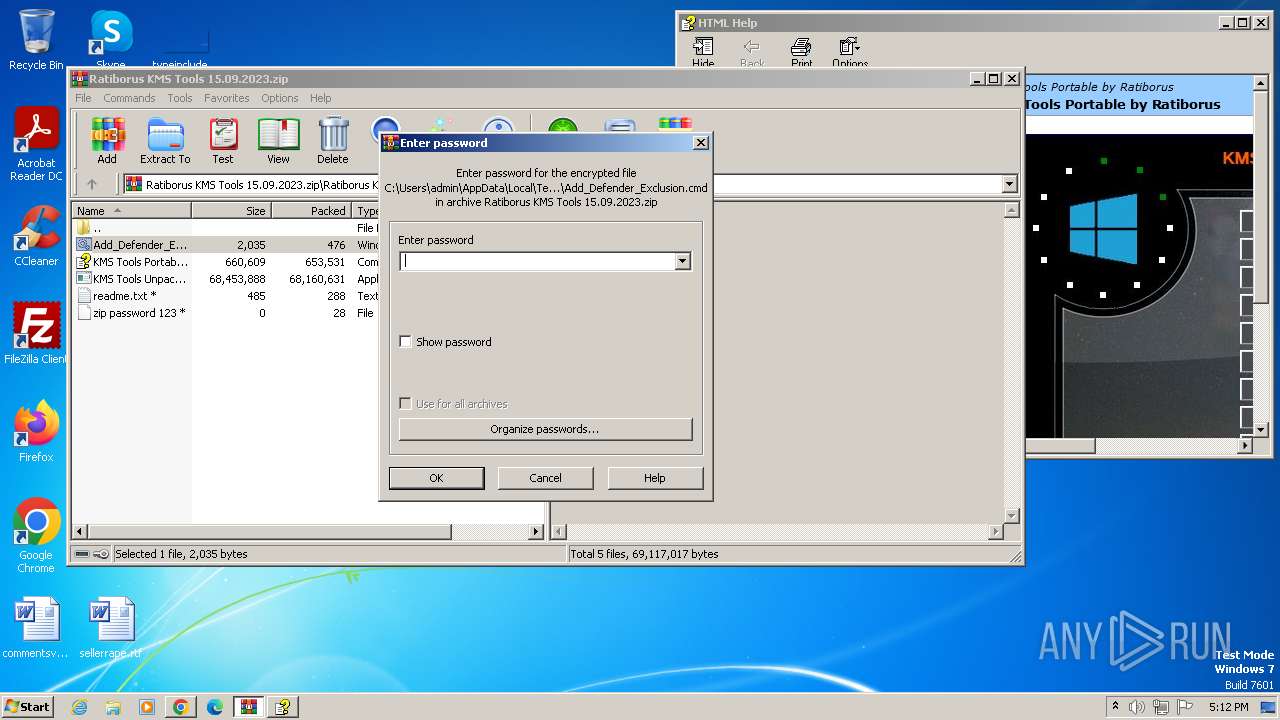
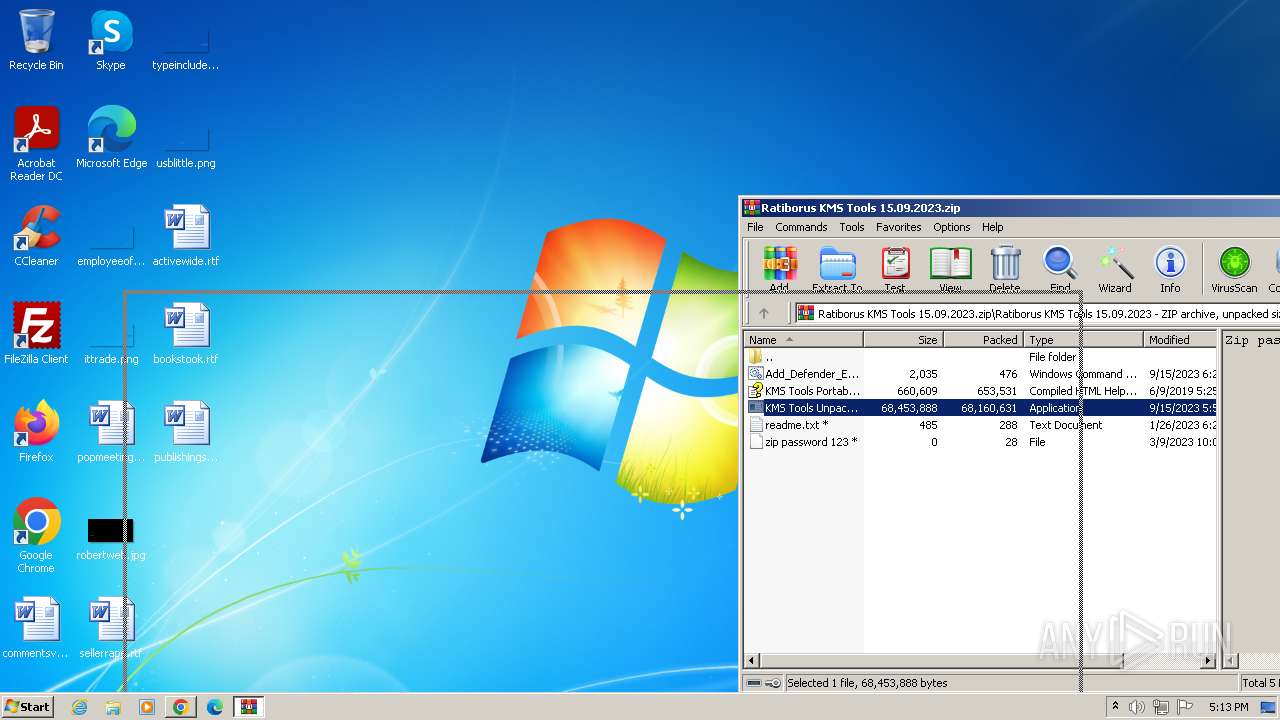
Executing commands from ".cmd" file
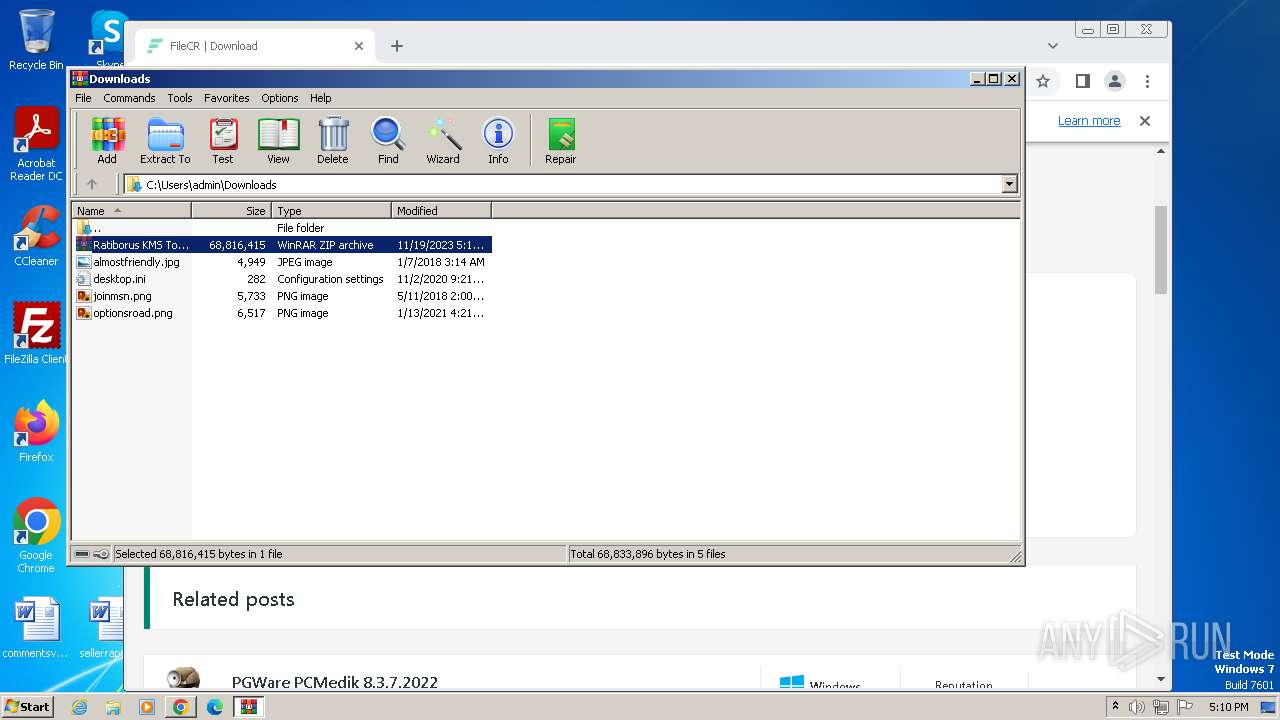
- WinRAR.exe (PID: 2476)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 888)
Found strings related to reading or modifying Windows Defender settings
- WinRAR.exe (PID: 2476)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 888)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 588)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 2128)
Powershell scripting: start process
- cmd.exe (PID: 588)
- cmd.exe (PID: 2096)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 588)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 2128)
Powershell version downgrade attack
- powershell.exe (PID: 3132)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 888)
- powershell.exe (PID: 3996)
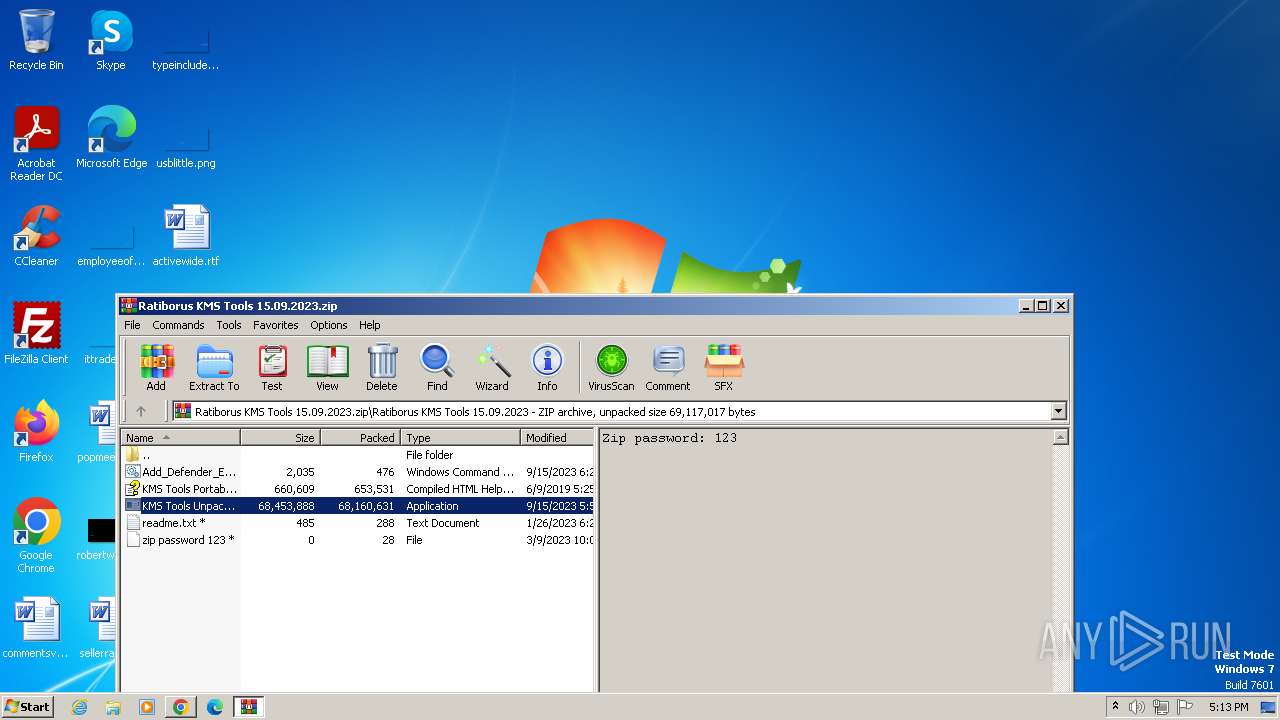
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2128)
Script uses the treat ID number to allow Windows Defender to execute it
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2128)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2128)
The process hide an interactive prompt from the user
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2128)
INFO
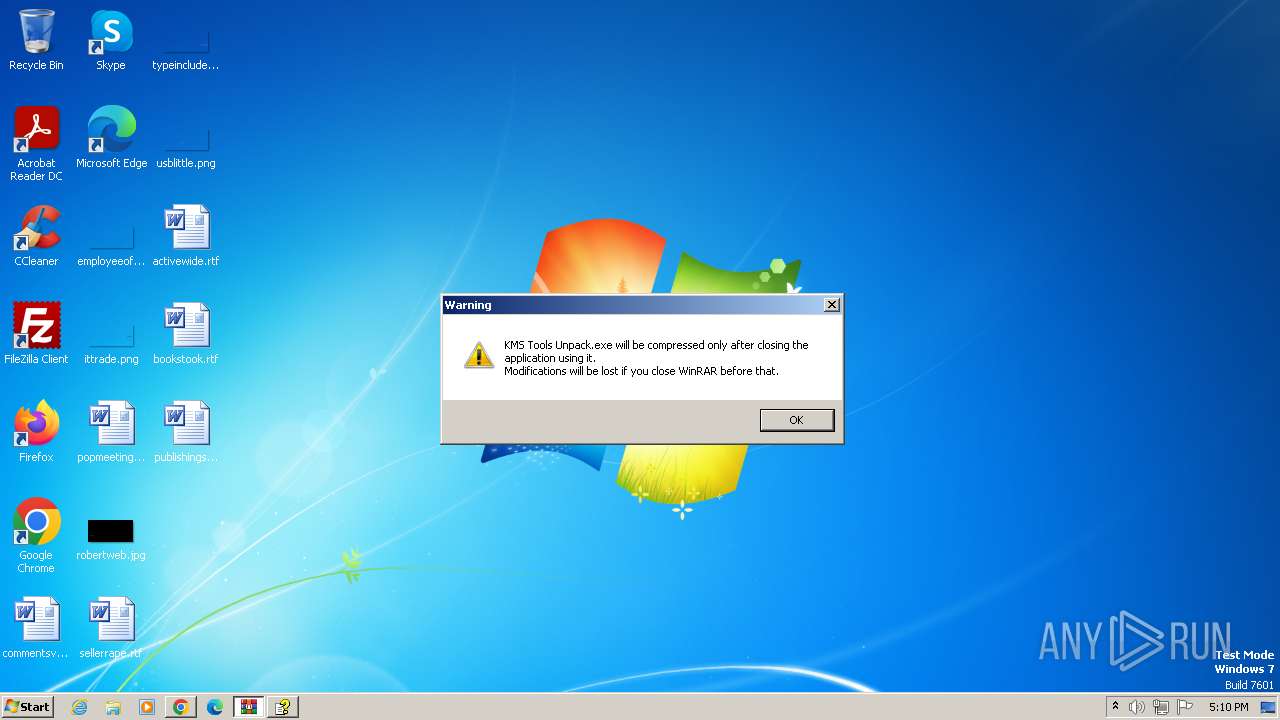
Manual execution by a user
- wmpnscfg.exe (PID: 600)
Application launched itself
- chrome.exe (PID: 3440)
The process uses the downloaded file
- chrome.exe (PID: 752)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3080)
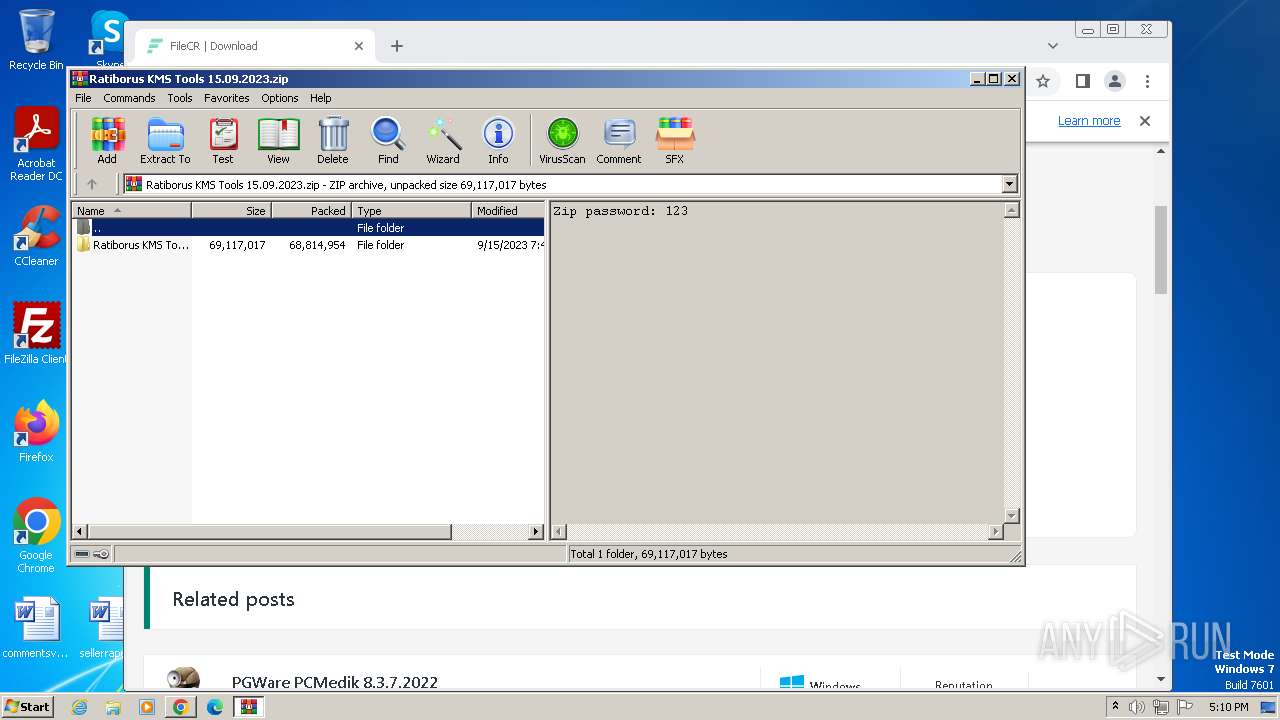
- WinRAR.exe (PID: 2476)
Reads the computer name
- wmpnscfg.exe (PID: 600)
- KMS Tools Unpack.exe (PID: 664)
- KMS Tools Unpack.exe (PID: 3256)
- KMS Tools Unpack.exe (PID: 1840)
Checks supported languages
- wmpnscfg.exe (PID: 600)
- KMS Tools Unpack.exe (PID: 664)
- chcp.com (PID: 1944)
- KMS Tools Unpack.exe (PID: 3256)
- KMS Tools Unpack.exe (PID: 1840)
- chcp.com (PID: 3672)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 600)
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- hh.exe (PID: 1616)
Drops the executable file immediately after the start
- chrome.exe (PID: 3440)
Create files in a temporary directory
- hh.exe (PID: 3060)
- KMS Tools Unpack.exe (PID: 664)
- hh.exe (PID: 2320)
- KMS Tools Unpack.exe (PID: 3256)
- hh.exe (PID: 1616)
- KMS Tools Unpack.exe (PID: 1840)
Checks proxy server information
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- hh.exe (PID: 1616)
Creates files or folders in the user directory
- hh.exe (PID: 3060)
- hh.exe (PID: 2320)
- hh.exe (PID: 1616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
61
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\SelfDelete.bat | C:\Windows\System32\cmd.exe | — | KMS Tools Unpack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2520 --field-trial-handle=1168,i,4749186342194719111,2726581821117538757,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 564 | reg query "HKU\S-1-5-19\Environment" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
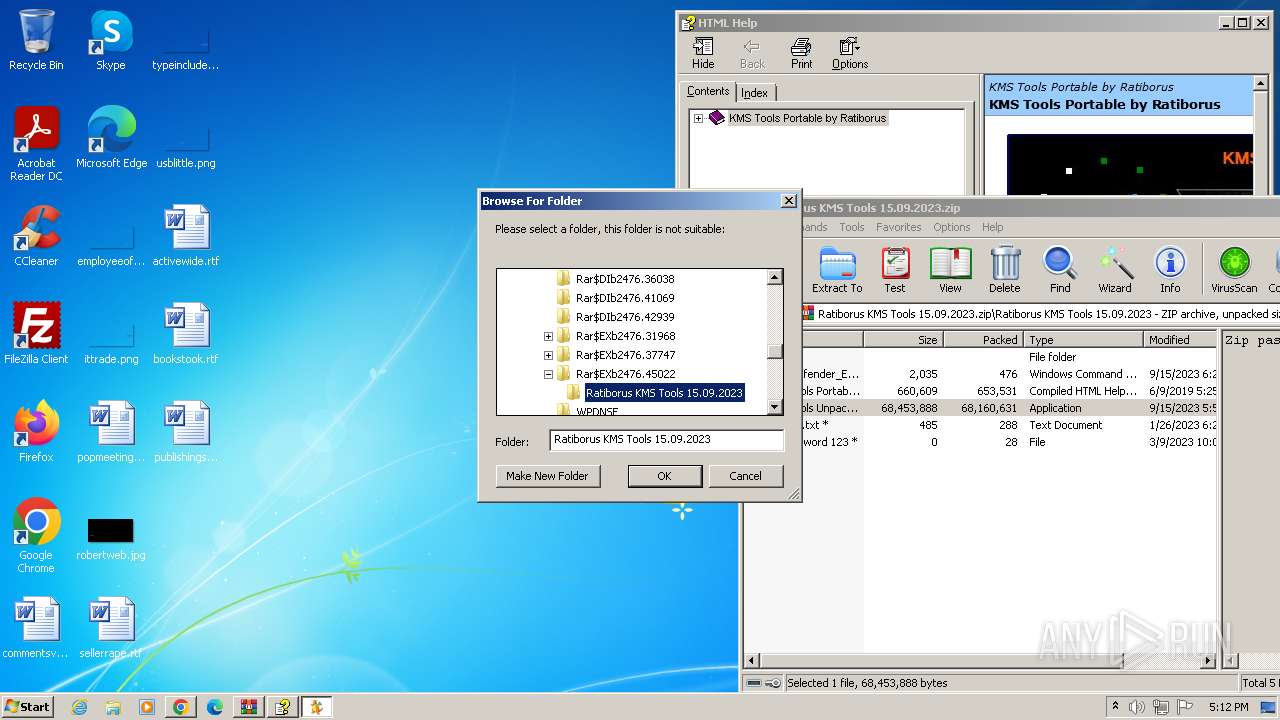
| 588 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIb2476.36038\Add_Defender_Exclusion.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
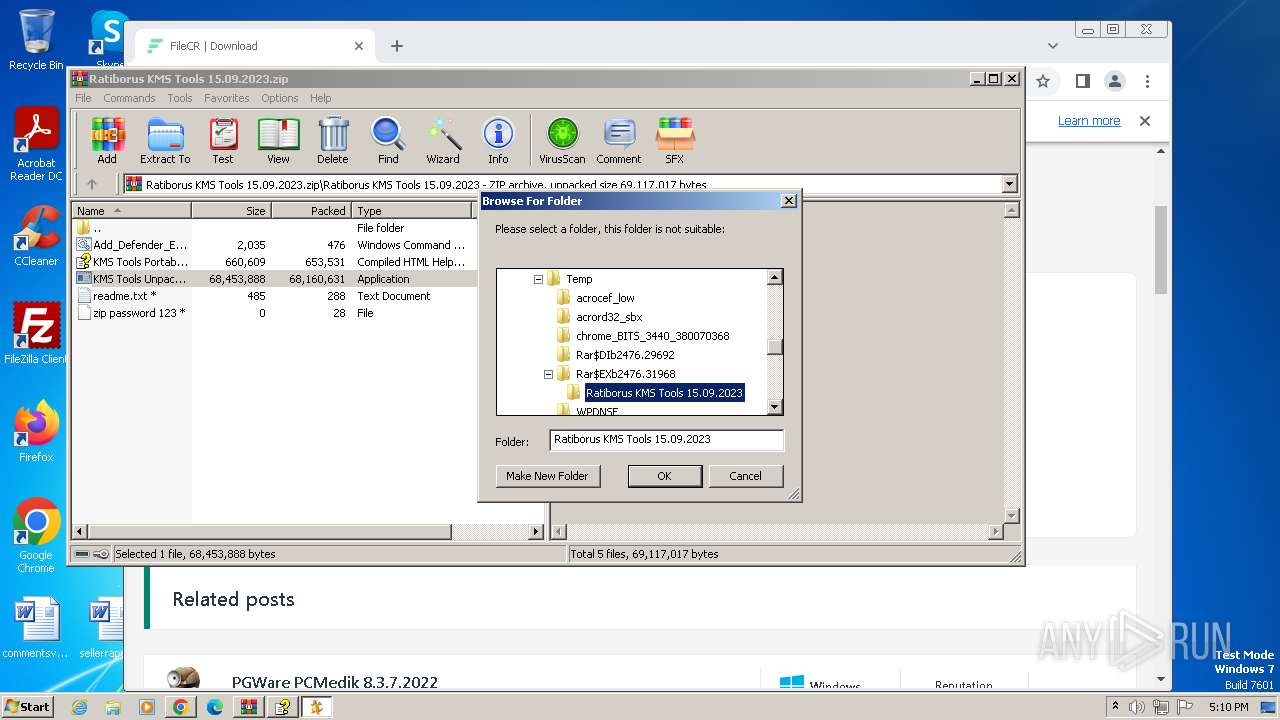
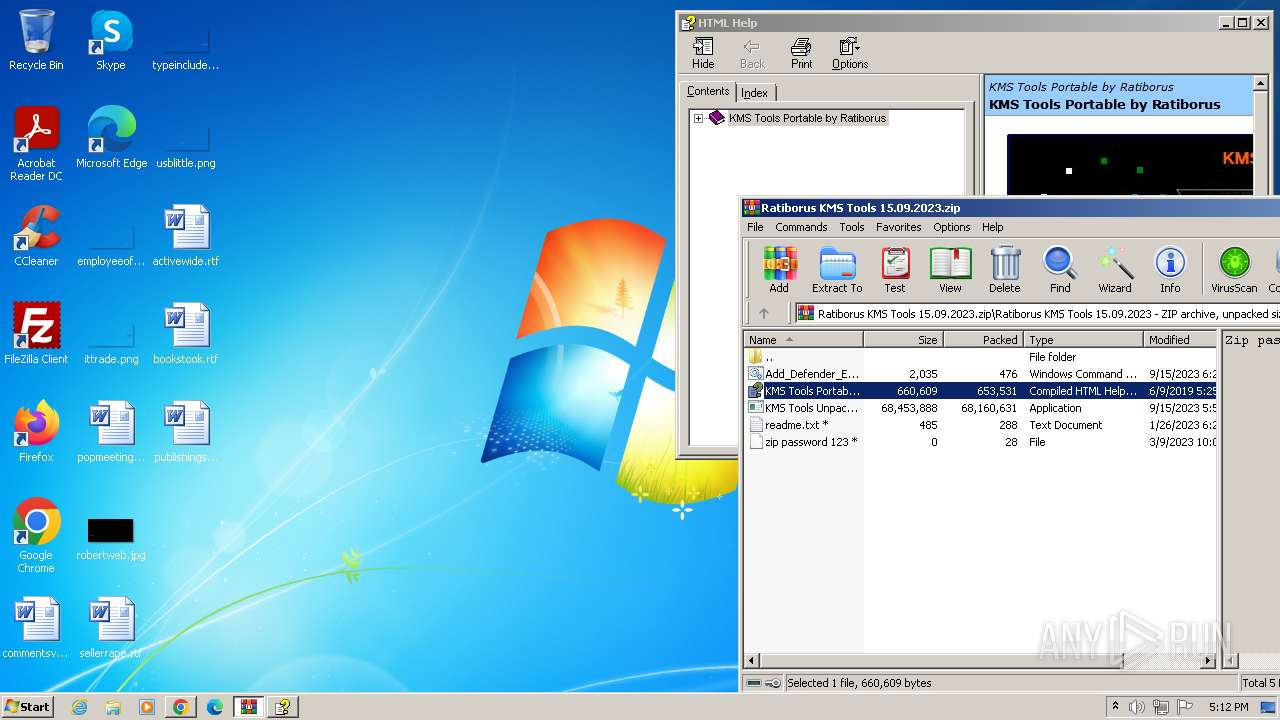
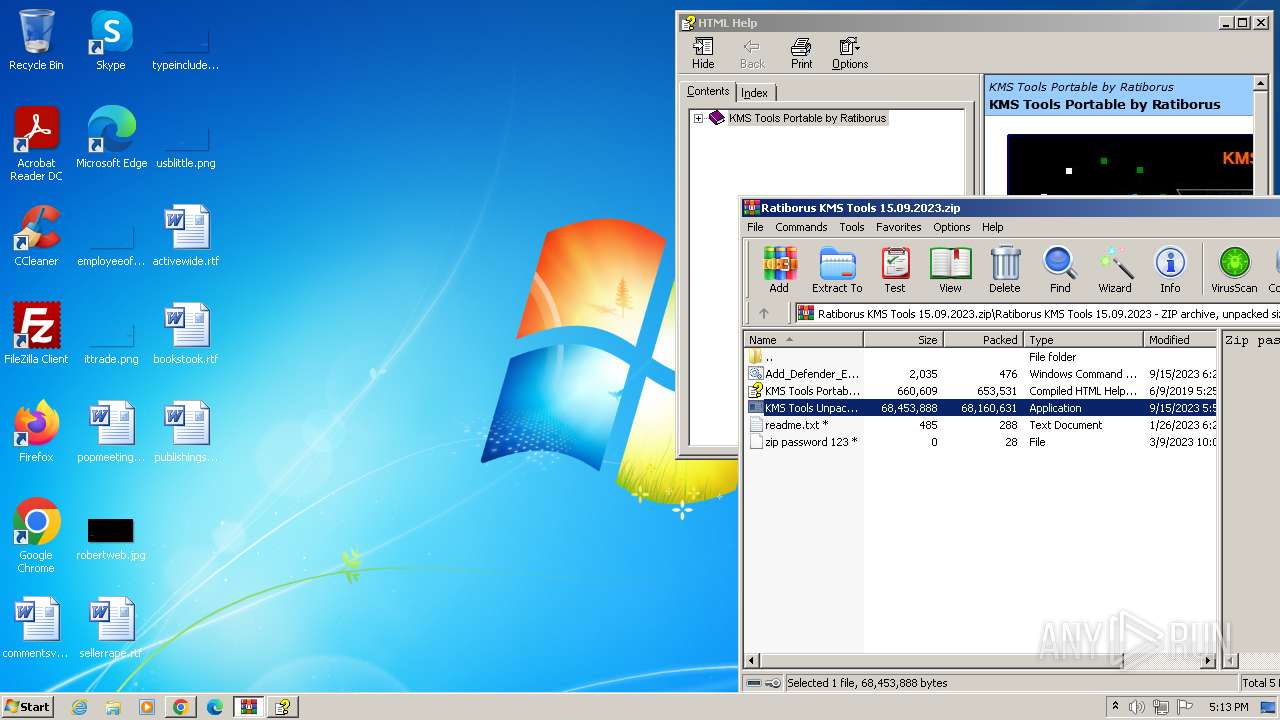
| 664 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2476.31968\Ratiborus KMS Tools 15.09.2023\KMS Tools Unpack.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2476.31968\Ratiborus KMS Tools 15.09.2023\KMS Tools Unpack.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3500 --field-trial-handle=1168,i,4749186342194719111,2726581821117538757,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 888 | powershell.exe -windowstyle hidden -noprofile "Start-Process 'C:\Users\admin\AppData\Local\Temp\Rar$DIb2476.41069\Add_Defender_Exclusion.cmd' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3256 --field-trial-handle=1168,i,4749186342194719111,2726581821117538757,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3216 --field-trial-handle=1168,i,4749186342194719111,2726581821117538757,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
16 998
Read events
16 537
Write events
458
Delete events
3
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
5
Suspicious files
421
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF167081.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16717b.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF16742b.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF167091.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1675e0.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF167218.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF168c56.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
45
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | — | — | unknown |
868 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 136 Kb | unknown |
868 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adjf6wcl4cbrlb2cluyt7lfamsaa_2023.10.13.1141/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.10.13.1141_all_b2zmlptxrzxlqwbi22z542vqne.crx3 | US | binary | 8.70 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 4.88 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 29.2 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 11.7 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 7.44 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 10.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 21.5 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 25.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3440 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3500 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | unknown |
3500 | chrome.exe | 104.26.0.130:443 | filecr.com | CLOUDFLARENET | US | unknown |
3500 | chrome.exe | 142.250.184.202:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3500 | chrome.exe | 172.67.221.181:443 | zintrack.com | — | — | unknown |
3500 | chrome.exe | 142.250.186.98:443 | pagead2.googlesyndication.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filecr.com |
| unknown |
accounts.google.com |
| shared |
content-autofill.googleapis.com |
| whitelisted |
zintrack.com |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
webcrx.io |
| unknown |
googleads.g.doubleclick.net |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |