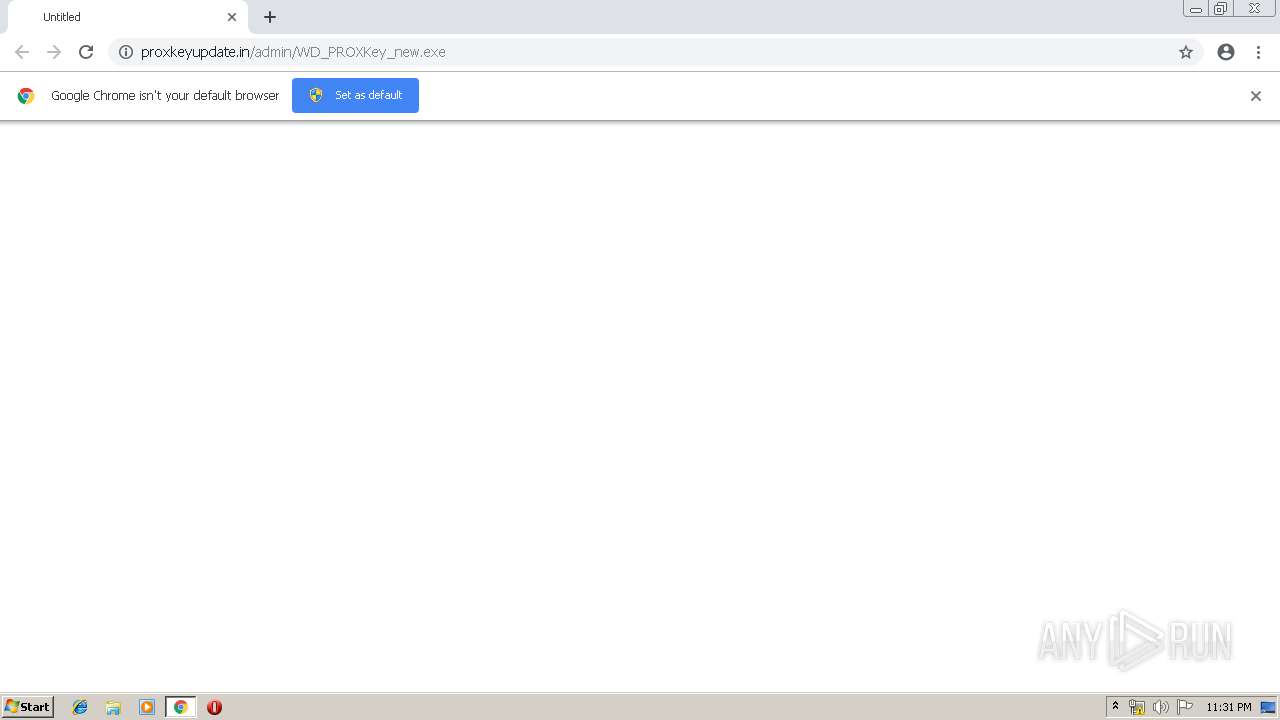
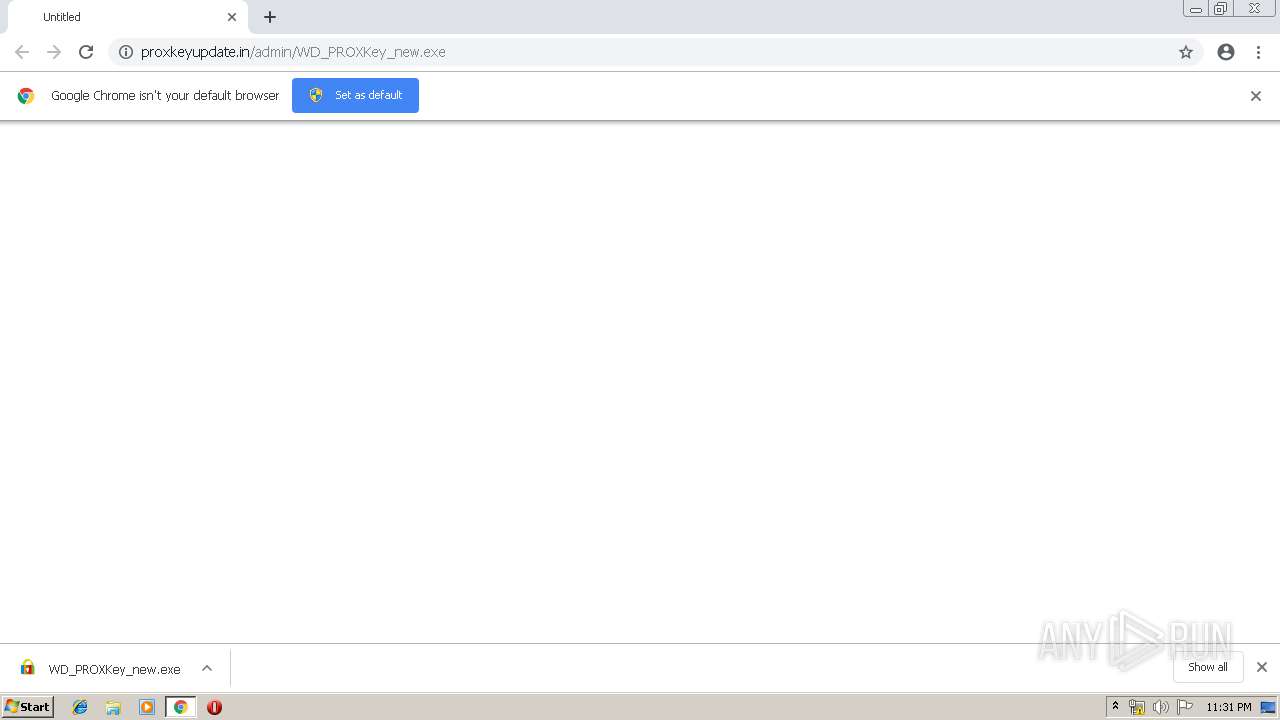
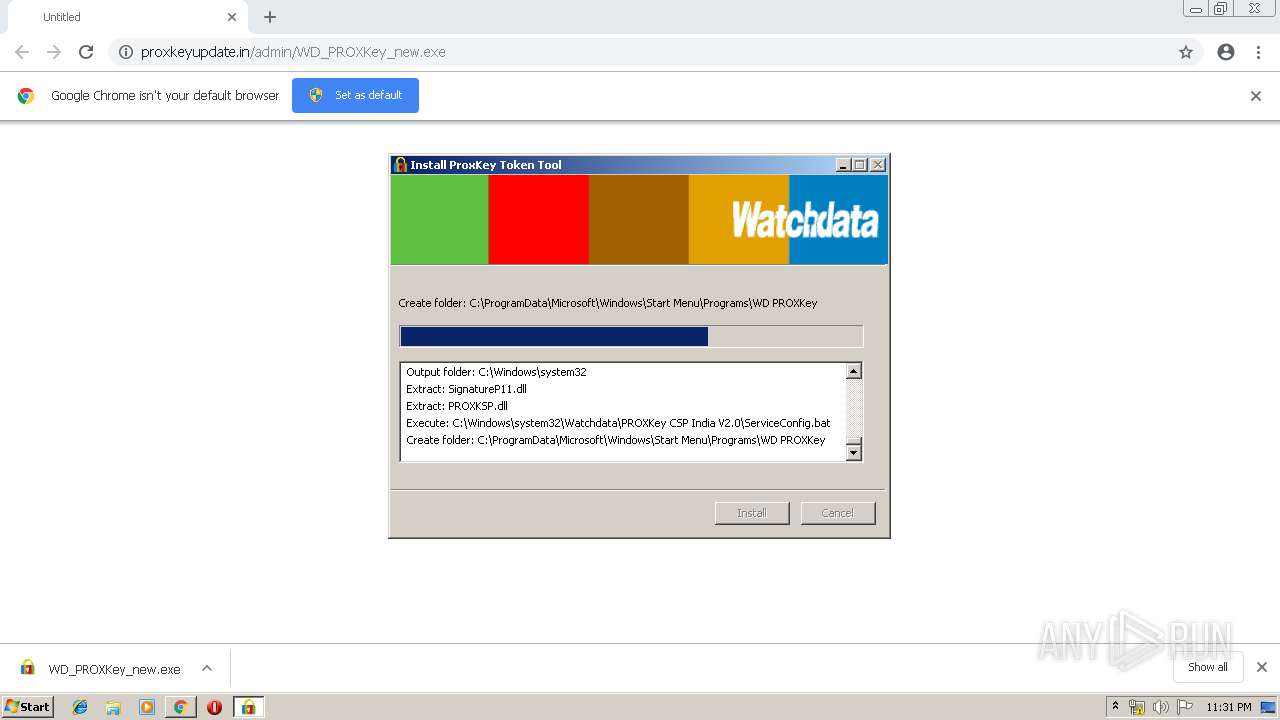
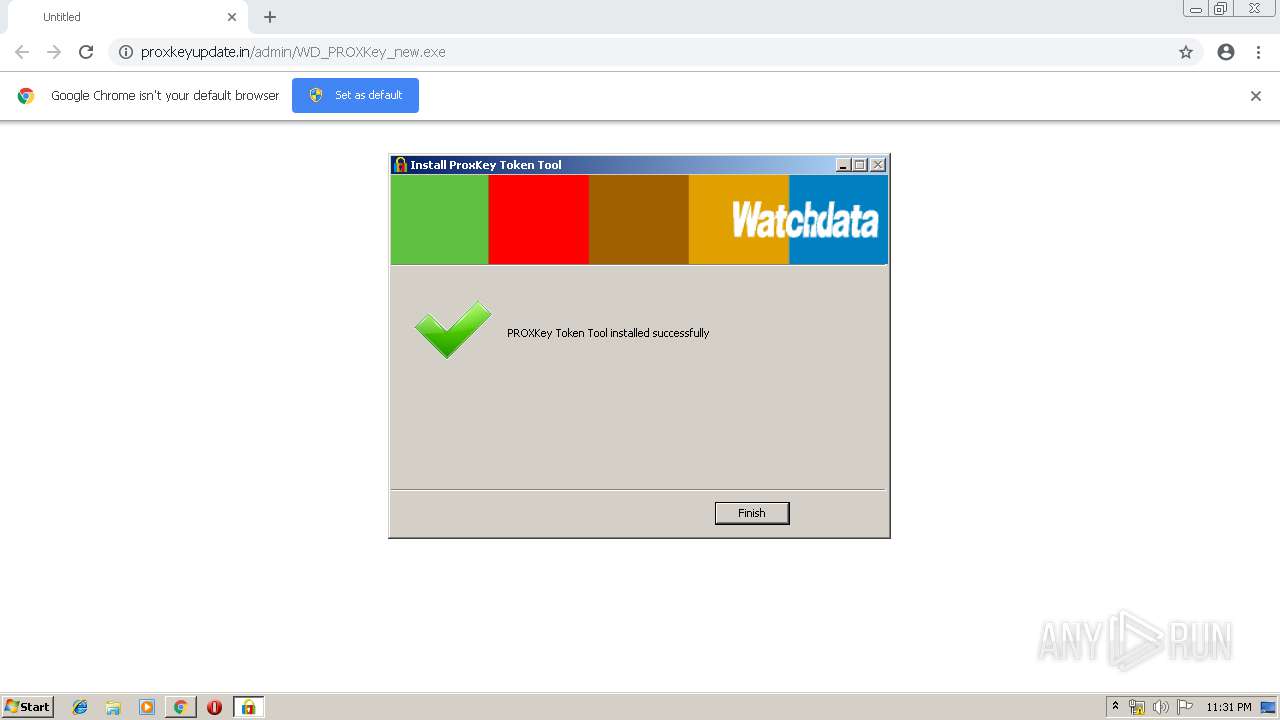
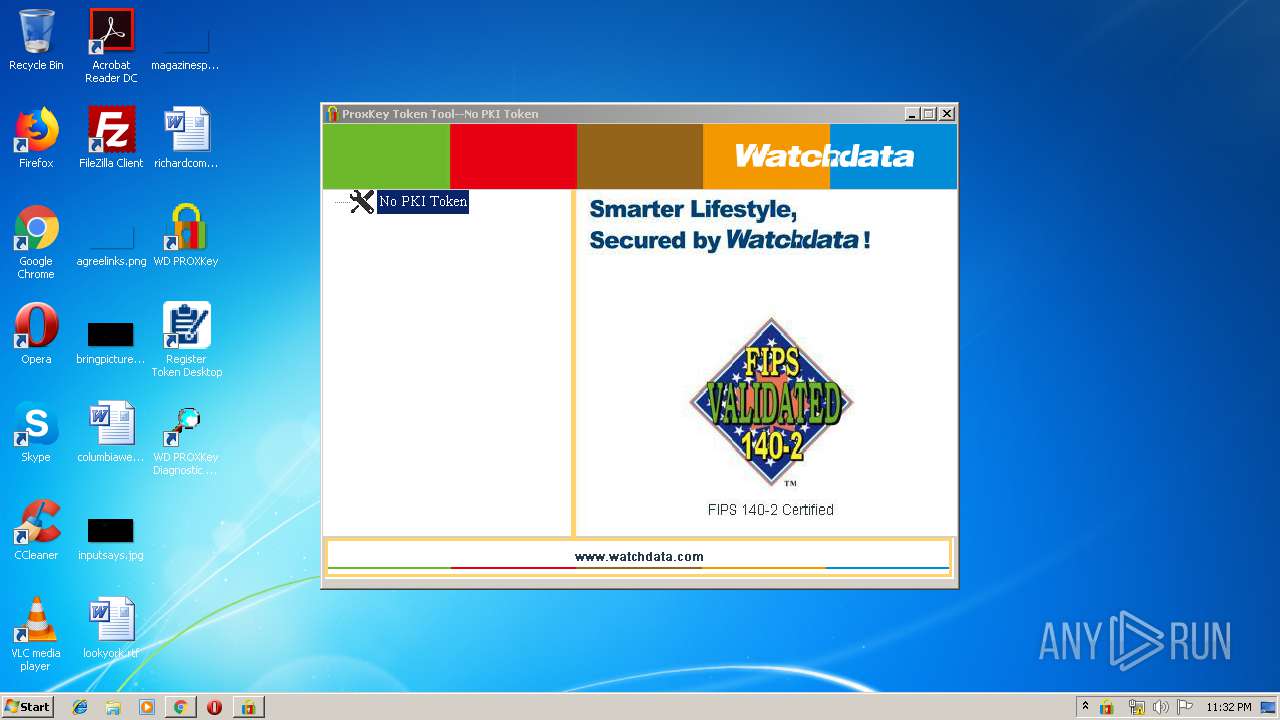
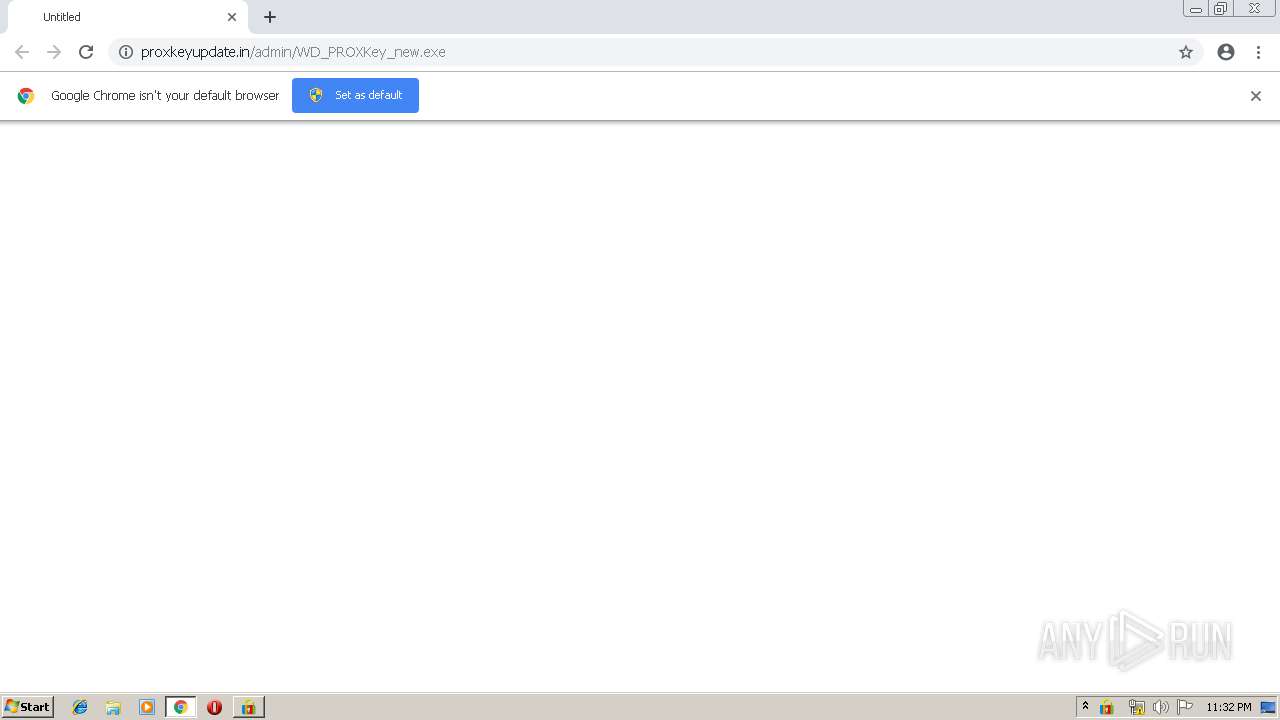
| URL: | http://proxkeyupdate.in/admin/WD_PROXKey_new.exe |
| Full analysis: | https://app.any.run/tasks/8f3cb9d8-6d95-4a3c-a477-9e131a162a54 |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2019, 22:31:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 51DCBF1C7E46C799AA9462B72C8F81E6 |
| SHA1: | A87F7F57AC8EEA95E4A378A4B906A97C994B858A |
| SHA256: | 3F88D1196B3A80F7A330978CCB8A2D176889D9615E67C2F42E1DCCC20D12D6FE |
| SSDEEP: | 3:N1KOXGvhpZyh3Bc6LA44A:COX+JylBI4 |
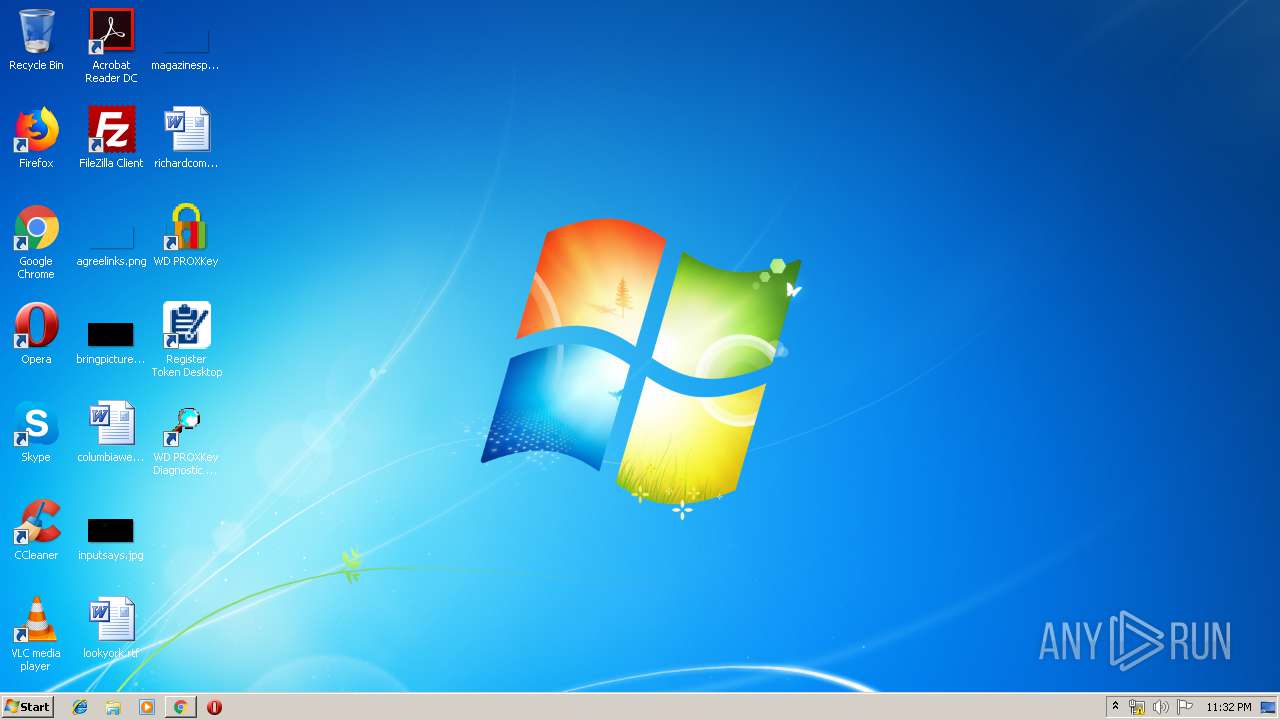
MALICIOUS
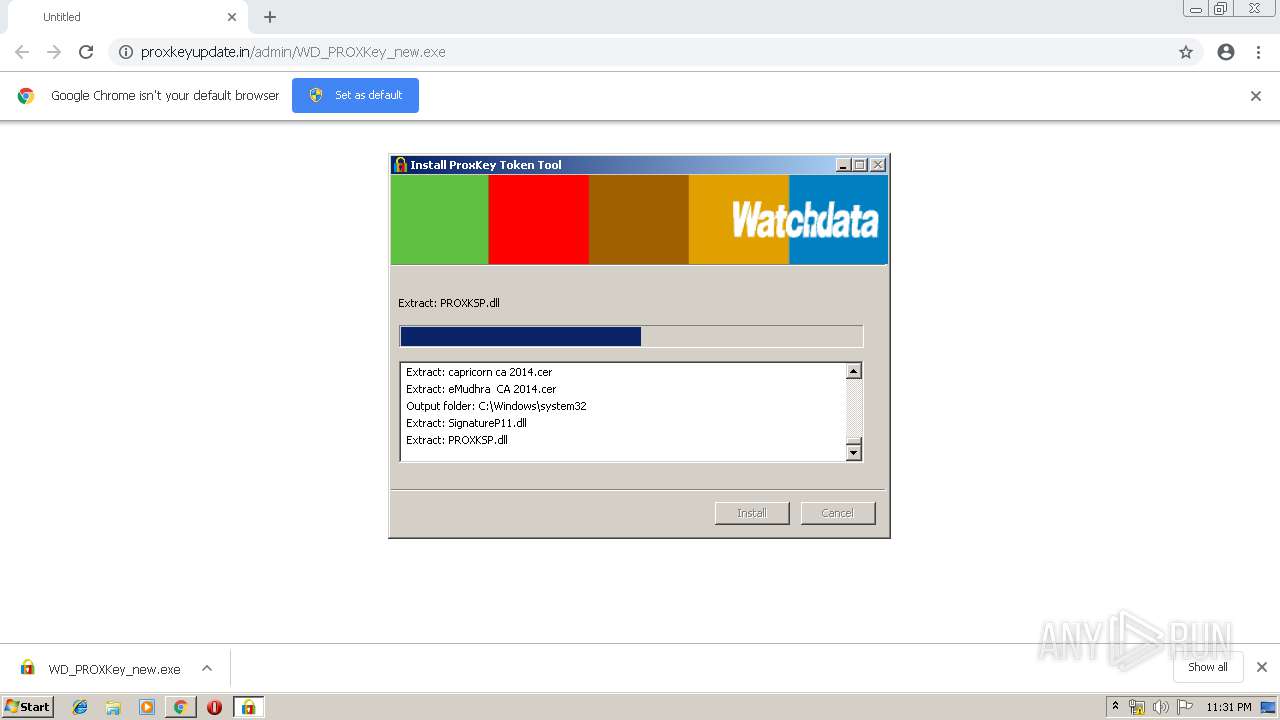
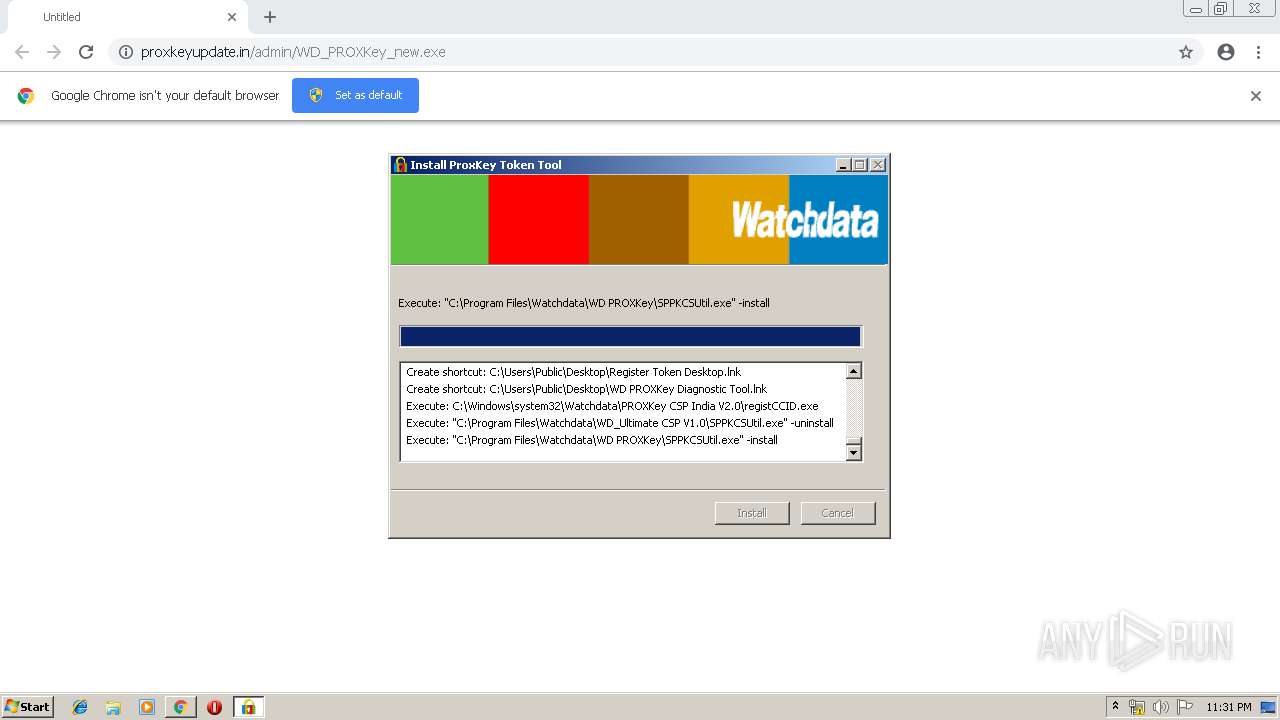
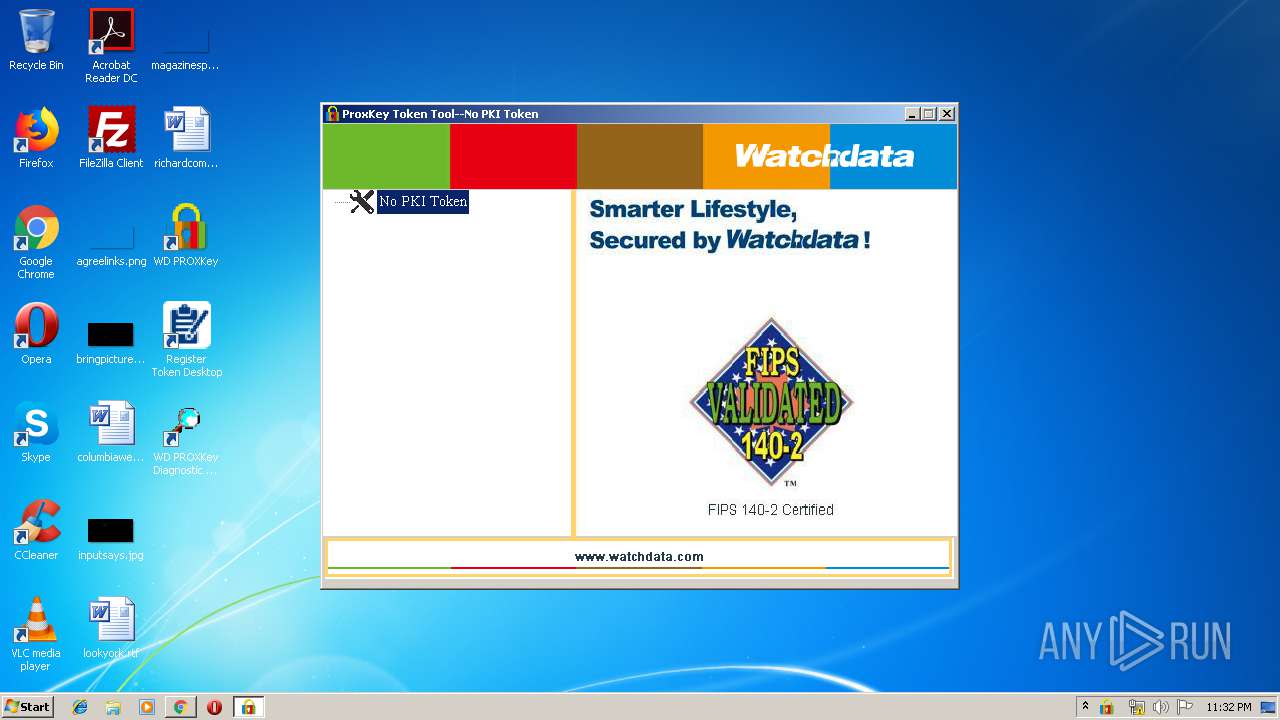
Loads dropped or rewritten executable
- WD_PROXKey_new.exe (PID: 1160)
- regsvr32.exe (PID: 3164)
- SPMonitor.exe (PID: 3088)
- WDAdmintool.exe (PID: 2656)
- SP_CertMND.exe (PID: 2336)
Changes the autorun value in the registry
- WD_PROXKey_new.exe (PID: 1160)
Application was dropped or rewritten from another process
- registCCID.exe (PID: 2108)
- WD_PROXKey_new.exe (PID: 2236)
- WD_PROXKey_new.exe (PID: 1160)
- SPMonitor.exe (PID: 3088)
- nsB8B0.tmp (PID: 1908)
- SP_CertMND.exe (PID: 2336)
- WDKSPconfig.exe (PID: 3872)
- SPSocketServer.exe (PID: 3676)
- SPPKCSUtil.exe (PID: 3640)
- SPPKCSUtil.exe (PID: 2592)
- WDAdmintool.exe (PID: 2656)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 3808)
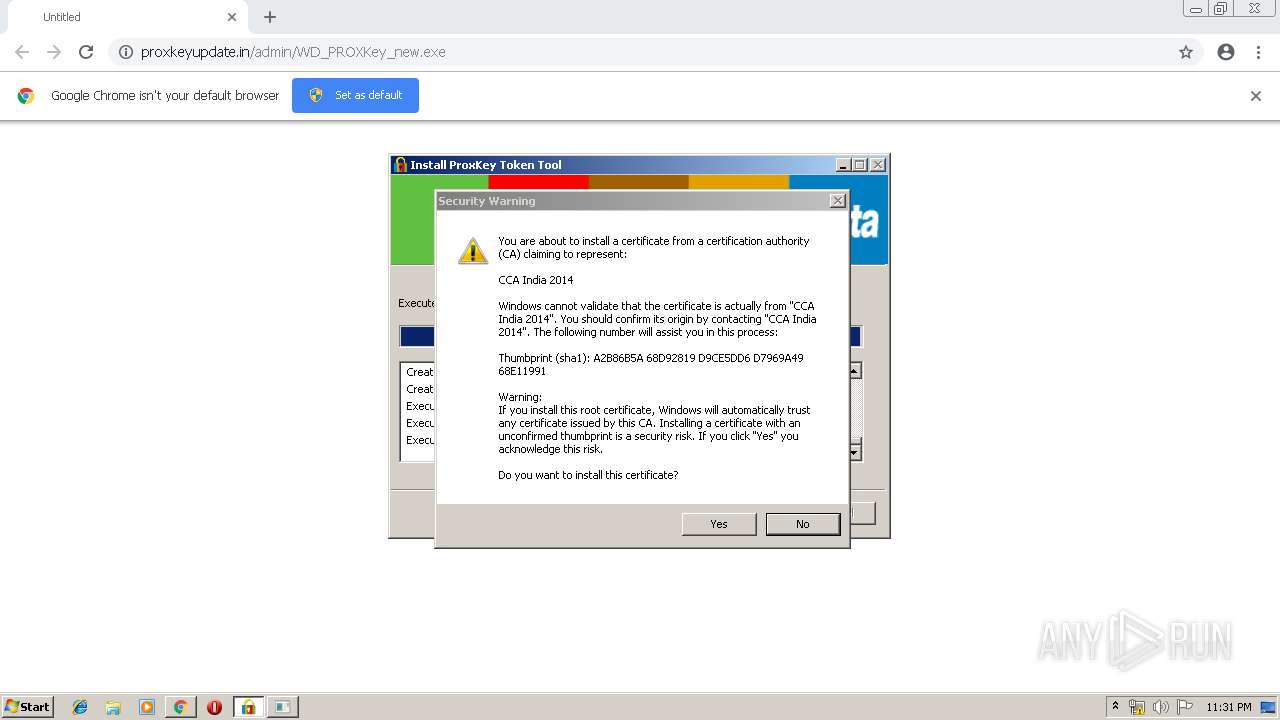
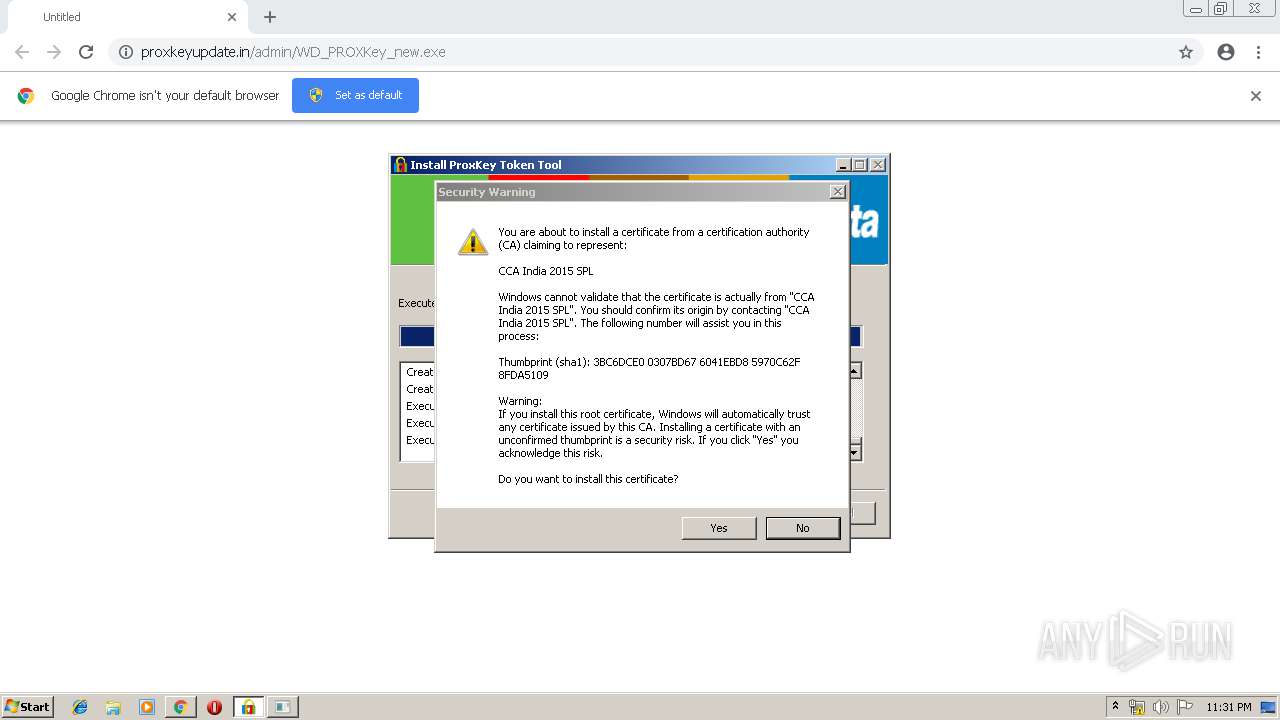
Changes settings of System certificates
- SPPKCSUtil.exe (PID: 2592)
Actions looks like stealing of personal data
- SPPKCSUtil.exe (PID: 2592)
- SPPKCSUtil.exe (PID: 3640)
SUSPICIOUS
Executable content was dropped or overwritten
- WD_PROXKey_new.exe (PID: 1160)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3884)
Creates files in the Windows directory
- WD_PROXKey_new.exe (PID: 1160)
Starts application with an unusual extension
- WD_PROXKey_new.exe (PID: 1160)
Creates files in the program directory
- WD_PROXKey_new.exe (PID: 1160)
Starts CMD.EXE for commands execution
- WD_PROXKey_new.exe (PID: 1160)
- nsB8B0.tmp (PID: 1908)
Starts SC.EXE for service management
- cmd.exe (PID: 1136)
Creates COM task schedule object
- regsvr32.exe (PID: 3164)
Creates a software uninstall entry
- WD_PROXKey_new.exe (PID: 1160)
Loads DLL from Mozilla Firefox
- SPPKCSUtil.exe (PID: 2592)
- SPPKCSUtil.exe (PID: 3640)
Creates files in the user directory
- SPPKCSUtil.exe (PID: 2592)
- SPPKCSUtil.exe (PID: 3640)
INFO
Creates files in the user directory
- chrome.exe (PID: 1796)
Dropped object may contain Bitcoin addresses
- WD_PROXKey_new.exe (PID: 1160)
Application launched itself
- chrome.exe (PID: 1796)
Reads settings of System Certificates
- SPPKCSUtil.exe (PID: 2592)
Changes settings of System certificates
- chrome.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
26
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --service-pipe-token=7965430550474175083 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7965430550474175083 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16773946424149449236 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1136 | cmd /c ""C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\ServiceConfig.bat"" | C:\Windows\system32\cmd.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1160 | "C:\Users\admin\Downloads\WD_PROXKey_new.exe" | C:\Users\admin\Downloads\WD_PROXKey_new.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2954331721418160012 --mojo-platform-channel-handle=1896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --service-pipe-token=17268044137345751525 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17268044137345751525 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://proxkeyupdate.in/admin/WD_PROXKey_new.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Users\admin\AppData\Local\Temp\nsbB227.tmp\nsB8B0.tmp" C:\Windows\system32\cmd.exe /C regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\WDCtr.dll" | C:\Users\admin\AppData\Local\Temp\nsbB227.tmp\nsB8B0.tmp | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2108 | "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\registCCID.exe" | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\registCCID.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\Downloads\WD_PROXKey_new.exe" | C:\Users\admin\Downloads\WD_PROXKey_new.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 328
Read events
1 162
Write events
163
Delete events
3
Modification events
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1796-13198890683411000 |
Value: 259 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
40
Suspicious files
30
Text files
70
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ad0aa7b-9306-424e-a427-8fdbc268989d.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3884 | chrome.exe | GET | — | 103.211.217.79:80 | http://proxkeyupdate.in/admin/WD_PROXKey_new.exe | IN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3884 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3884 | chrome.exe | 103.211.217.79:80 | proxkeyupdate.in | PDR | IN | suspicious |
3884 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3884 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3884 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3884 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3884 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
proxkeyupdate.in |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3884 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
SPMonitor.exe | [3088]:Enter GetCCIDDriverFile...
|
SPMonitor.exe | [3088]:Out GetCCIDDriverFile, succeed!
|
SPMonitor.exe | [3088]:Enter SetupDiEnumDeviceInfo...
|
SPMonitor.exe | [3088]:Out SetupDiEnumDeviceInfo, iWaitUpdateTime = 0
|
WDAdmintool.exe | [2656]:NDGetSlotList:0
|
WDAdmintool.exe | [2656]:g_DeviceNum:0
|
WDAdmintool.exe | [2656]:NDGetSlotList:0
|
WDAdmintool.exe | [2656]:g_DeviceNum:0
|