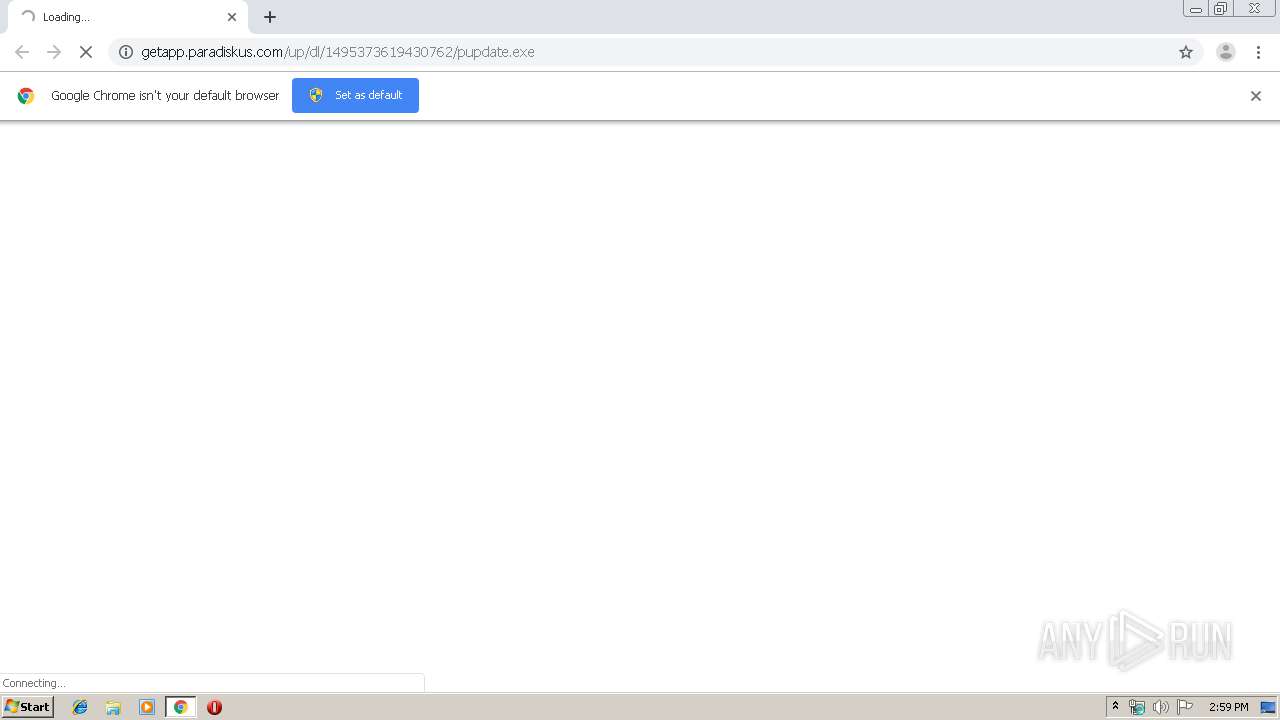
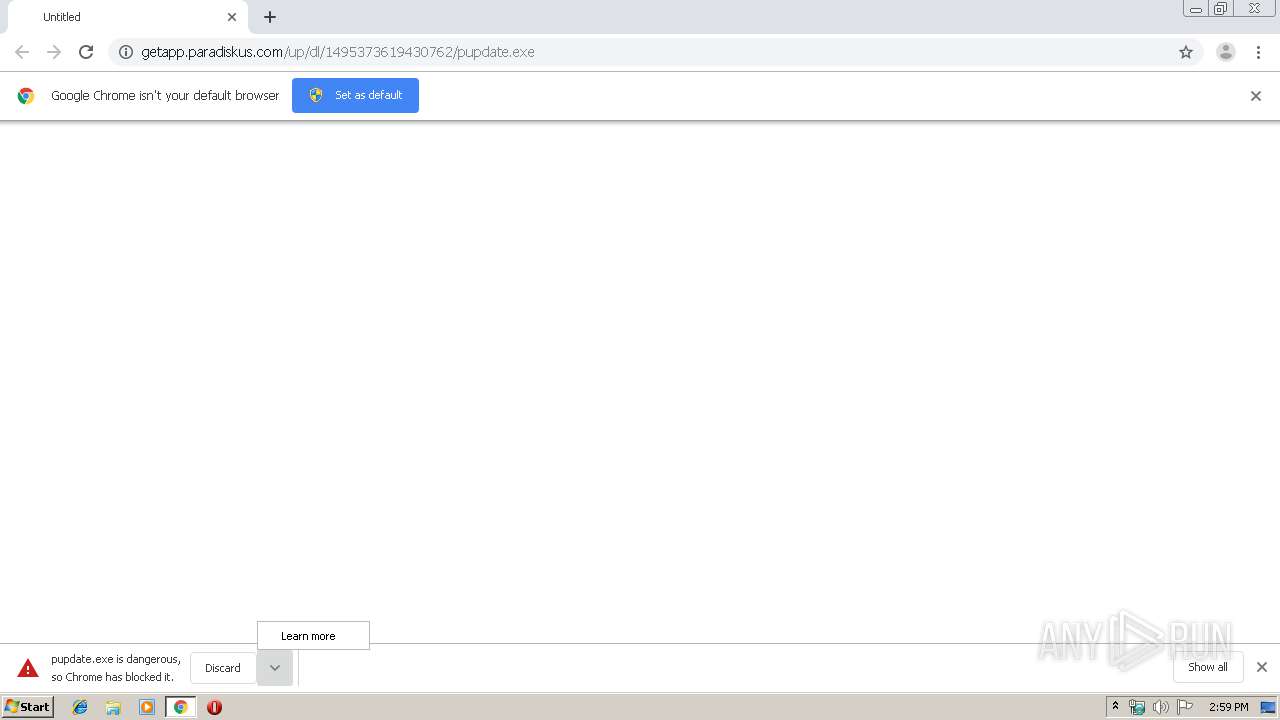
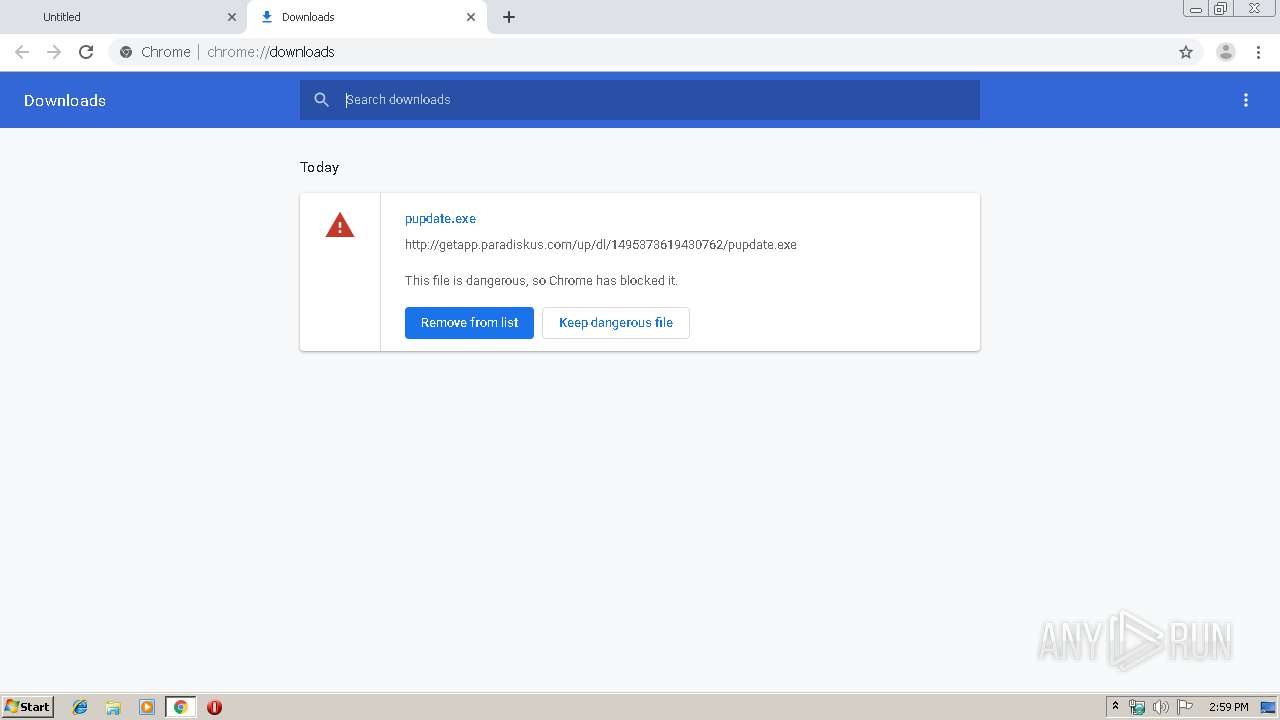
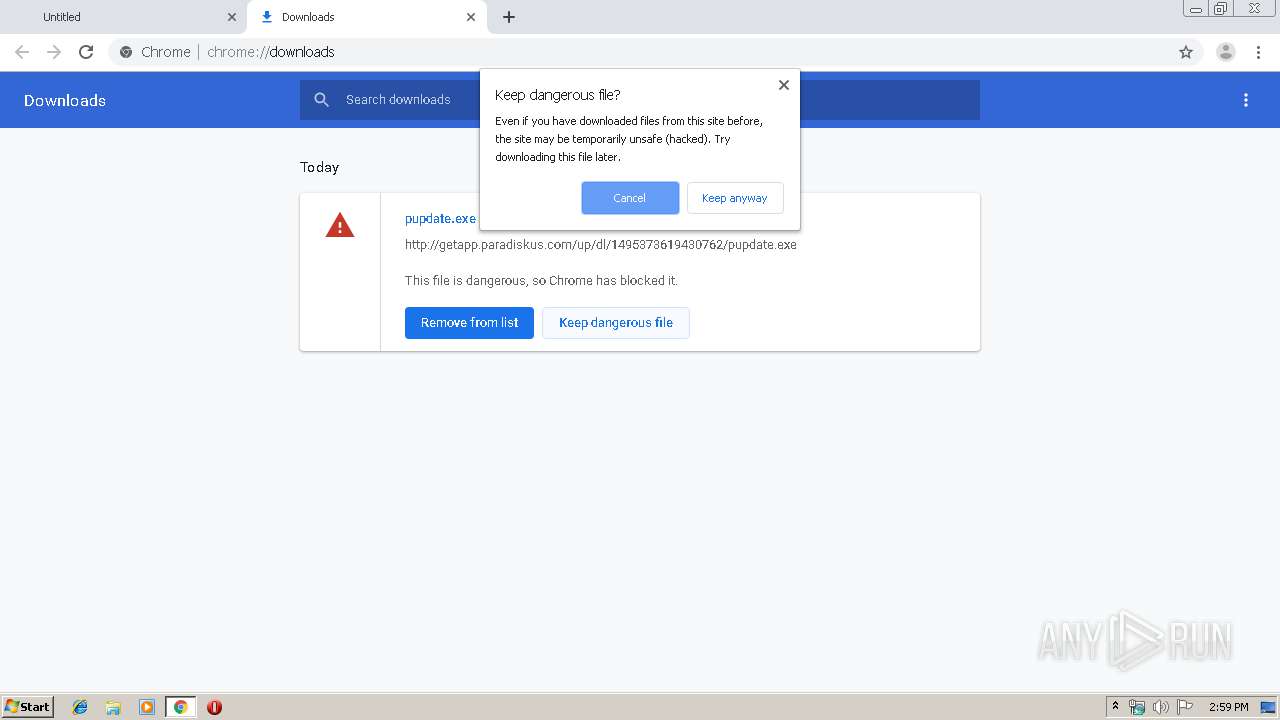
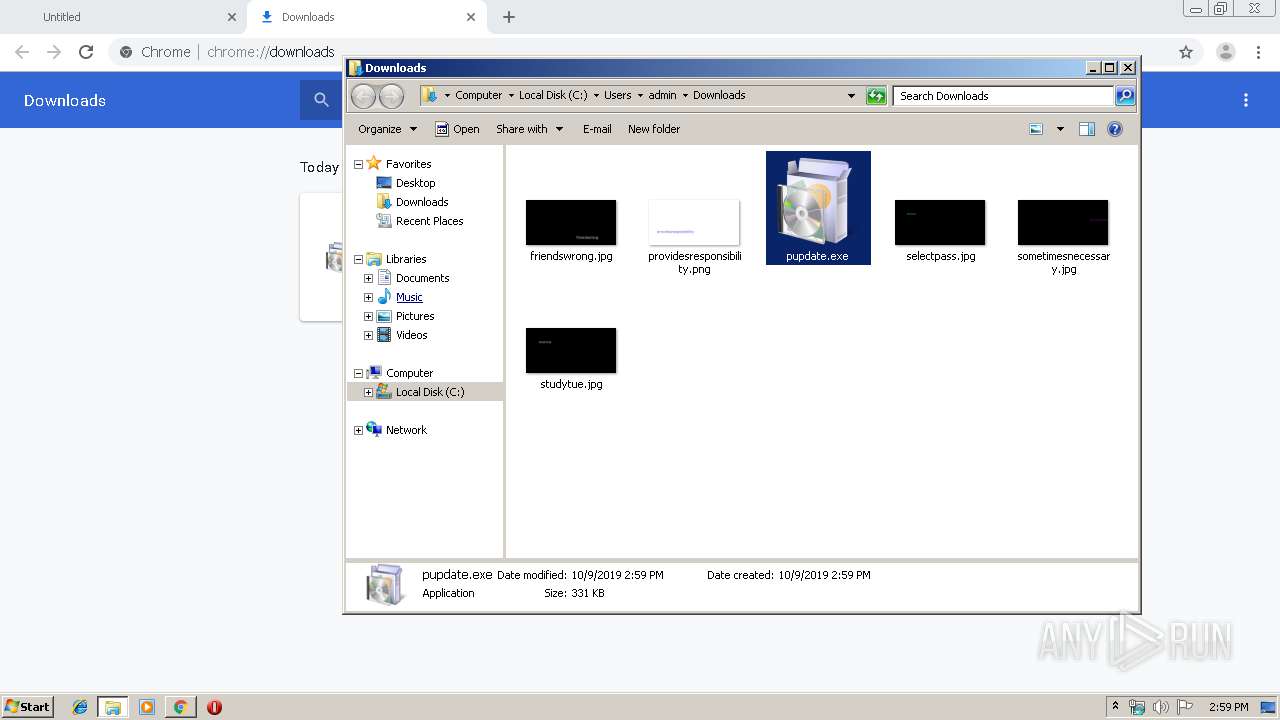
| URL: | http://getapp.paradiskus.com/up/dl/1495373619430762/pupdate.exe |
| Full analysis: | https://app.any.run/tasks/21ce81cd-81c5-48e2-9c48-74e8ab678bf5 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 13:58:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CD4575DA588D462B27A2CDD68A9FB00A |
| SHA1: | 57E5FB45D59A0104452439733218F706D3335D3F |
| SHA256: | 3F86819F1701433AA25299059340288C8A5F802A6AF67B168D978E0EC2F1ADA5 |
| SSDEEP: | 3:N1KZARjYMWUKLEEUANEa:C+3FKLEEfia |
MALICIOUS
Application was dropped or rewritten from another process
- pupdate.exe (PID: 2424)
- ZUpdater.exe (PID: 3248)
- pupdate.exe (PID: 2412)
- ZUpdater.exe (PID: 3156)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 580)
- schtasks.exe (PID: 4044)
Uses Task Scheduler to run other applications
- ZUpdater.exe (PID: 3248)
- ZUpdater.exe (PID: 3156)
Changes the autorun value in the registry
- ZUpdater.exe (PID: 3248)
- ZUpdater.exe (PID: 3156)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3104)
- pupdate.exe (PID: 2424)
- ZUpdater.exe (PID: 3156)
- pupdate.exe (PID: 2412)
- ZUpdater.exe (PID: 3248)
Creates files in the user directory
- ZUpdater.exe (PID: 3248)
INFO
Reads the hosts file
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2540)
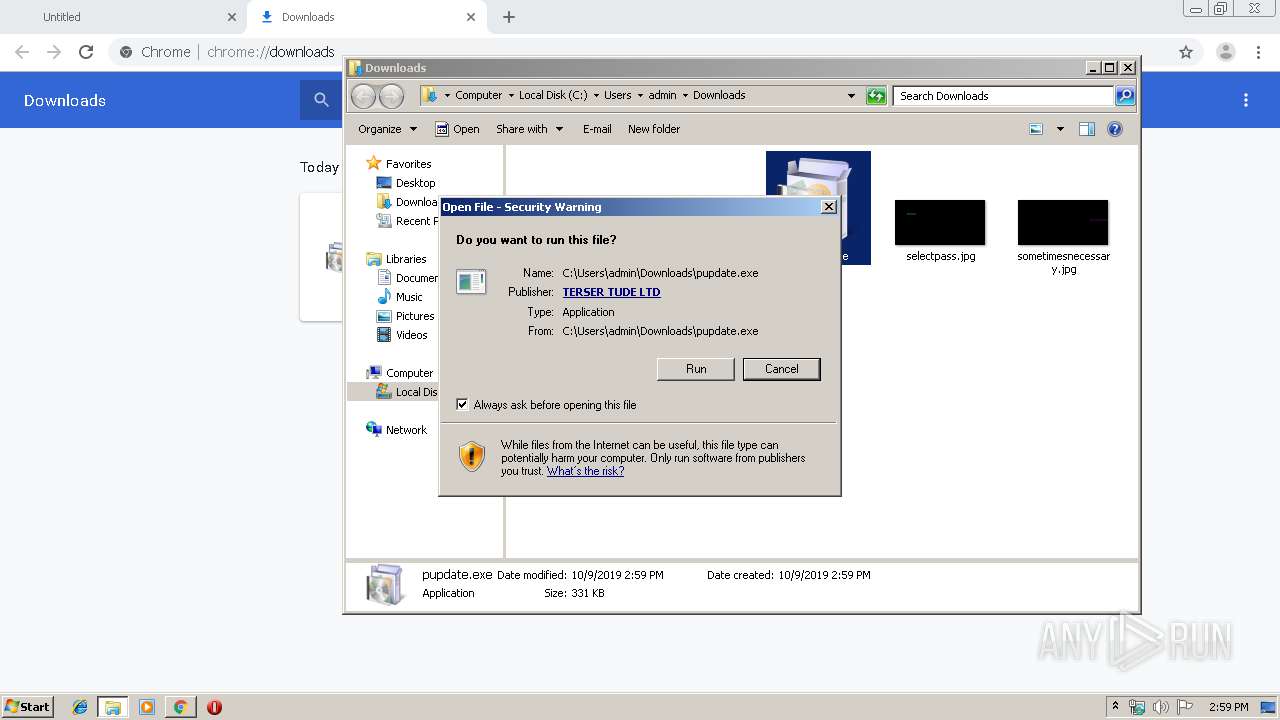
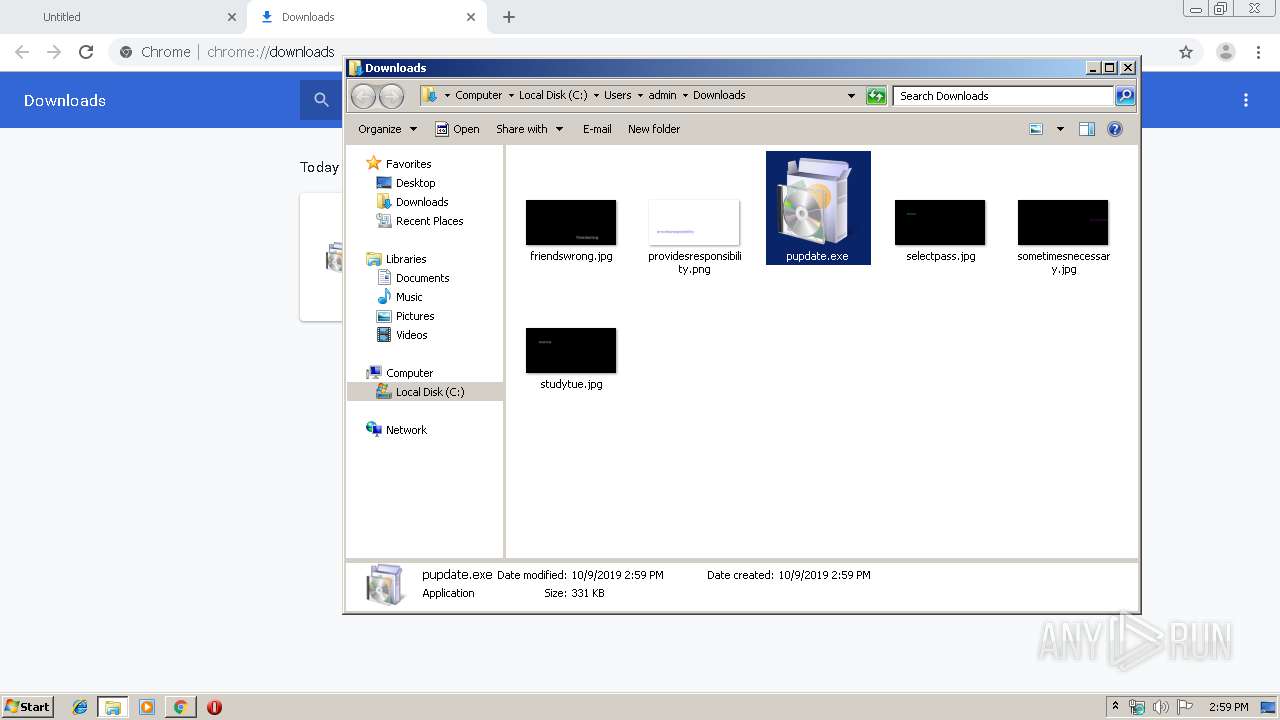
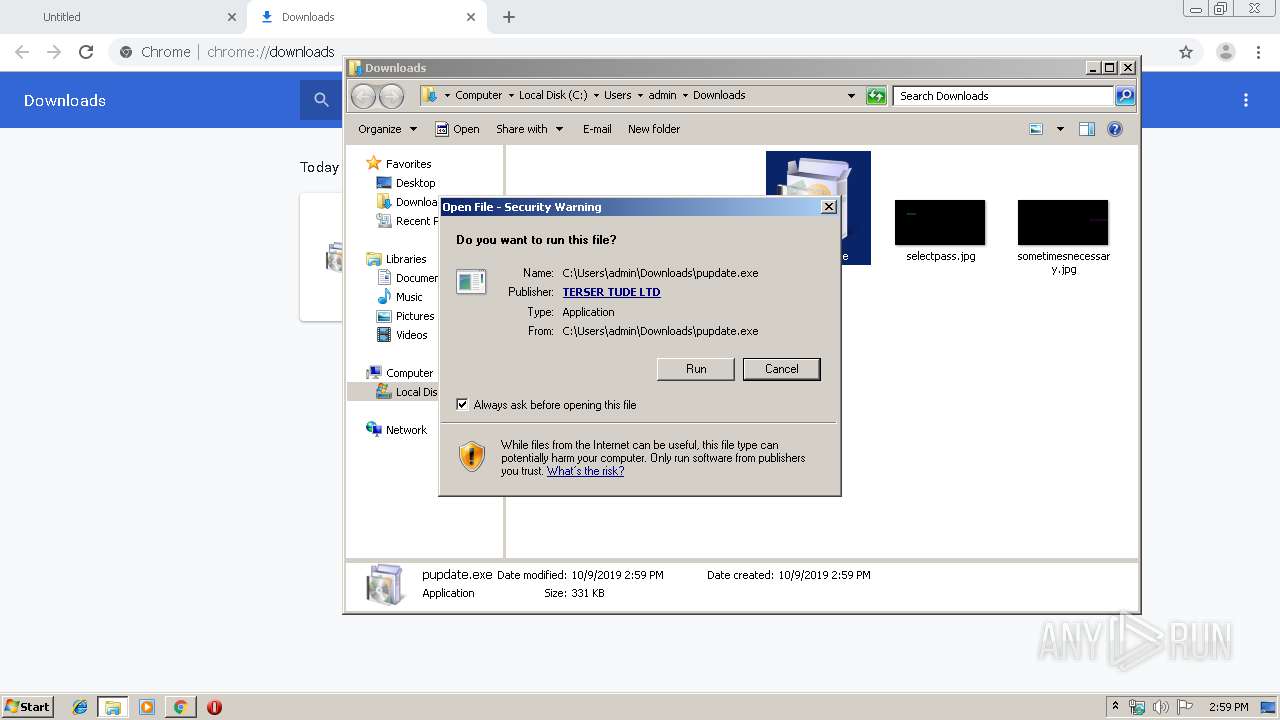
Manual execution by user
- pupdate.exe (PID: 2424)
- pupdate.exe (PID: 2412)
Application launched itself
- chrome.exe (PID: 3104)
Reads Internet Cache Settings
- chrome.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14035277461717465767 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16676563116712328677 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 580 | "schtasks.exe" /create /SC DAILY /TN ZUpdater /TR "\"C:\Users\admin\AppData\Roaming\ZUpdater\ZUpdater.exe\" do://zupdater | C:\Windows\system32\schtasks.exe | — | ZUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10971846976864194171 --mojo-platform-channel-handle=3812 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11084637214467251410 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\Downloads\pupdate.exe" | C:\Users\admin\Downloads\pupdate.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\Downloads\pupdate.exe" | C:\Users\admin\Downloads\pupdate.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5873925787580351848 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2863000220653065848 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15638297057495112508,4860494500005777802,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10425545950984749377 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 089
Read events
1 016
Write events
70
Delete events
3
Modification events
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3104-13215103147291125 |
Value: 259 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3104-13215103147291125 |
Value: 259 | |||
Executable files
9
Suspicious files
7
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\02d65822-e34d-4cf6-814f-9cde524f57b0.tmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF100e88.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF100ec7.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF100e88.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
10
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | ZUpdater.exe | POST | 200 | 62.76.75.168:80 | http://inf.bonnapatit.com/api/report? | RU | — | — | malicious |
3156 | ZUpdater.exe | POST | 200 | 62.76.75.168:80 | http://inf.bonnapatit.com/api/report? | RU | — | — | malicious |
3248 | ZUpdater.exe | POST | — | 62.76.75.168:80 | http://inf.bonnapatit.com/api/report? | RU | — | — | malicious |
3156 | ZUpdater.exe | POST | — | 62.76.75.168:80 | http://inf.bonnapatit.com/api/report? | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 62.76.75.168:80 | getapp.paradiskus.com | OOO Sirius-Project | RU | malicious |
2540 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 62.76.75.168:80 | getapp.paradiskus.com | OOO Sirius-Project | RU | malicious |
2540 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3248 | ZUpdater.exe | 62.76.75.168:80 | getapp.paradiskus.com | OOO Sirius-Project | RU | malicious |
3156 | ZUpdater.exe | 62.76.75.168:80 | getapp.paradiskus.com | OOO Sirius-Project | RU | malicious |
2540 | chrome.exe | 172.217.21.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
getapp.paradiskus.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
inf.bonnapatit.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2540 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2540 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3248 | ZUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Tasker.fqzeya (zupdater base64 xor key takton) |
3156 | ZUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Tasker.fqzeya (zupdater base64 xor key takton) |
3156 | ZUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Tasker.fqzeya (zupdater base64 xor key takton) |
3156 | ZUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Tasker.fqzeya (zupdater base64 xor key takton) |
2540 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |