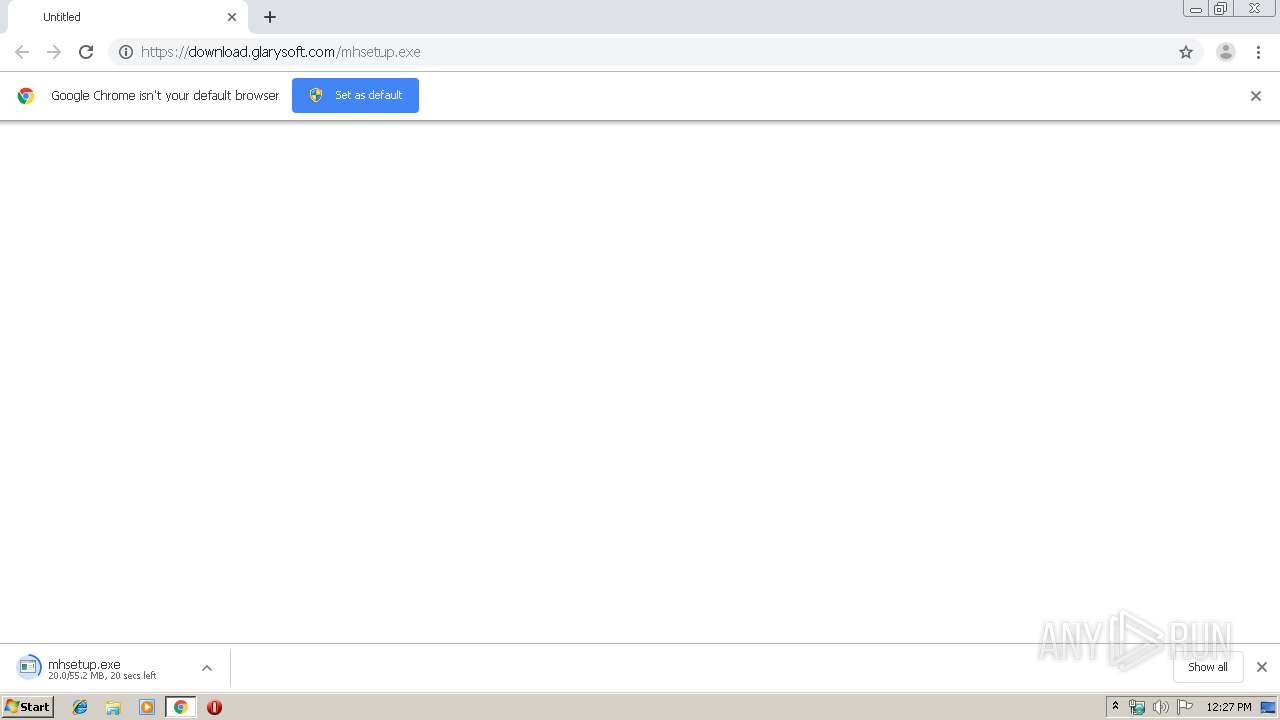
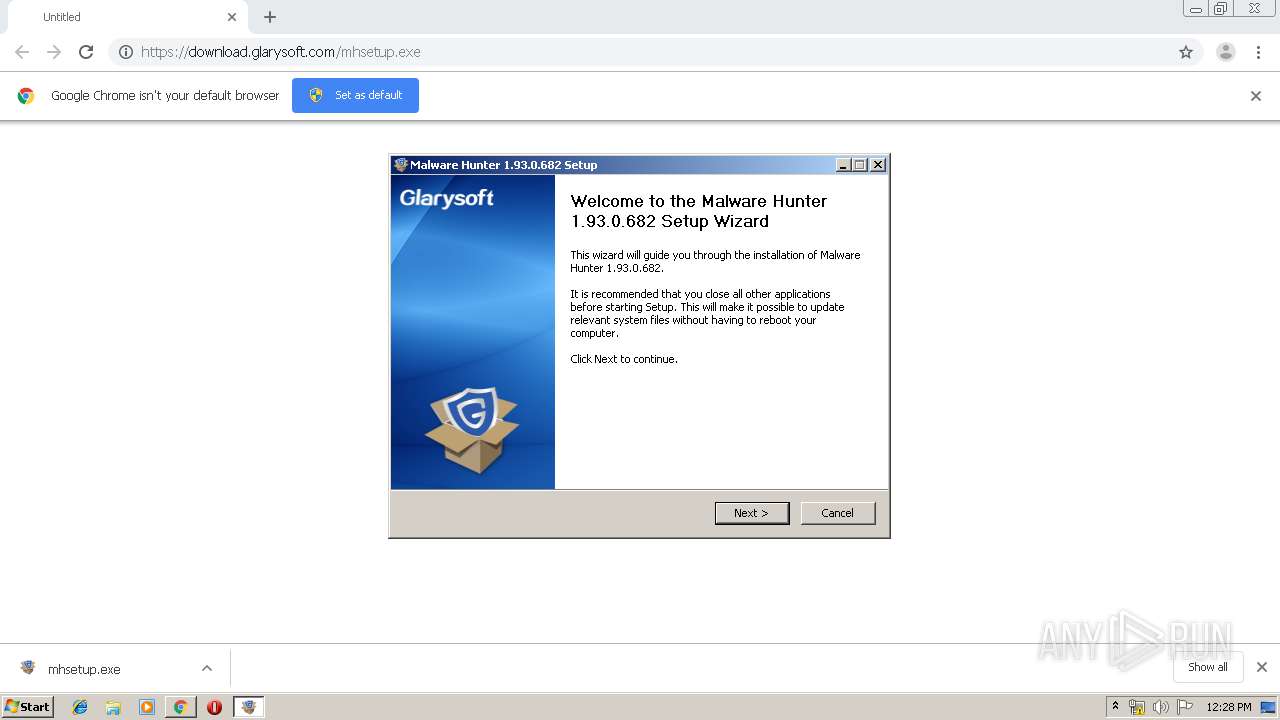
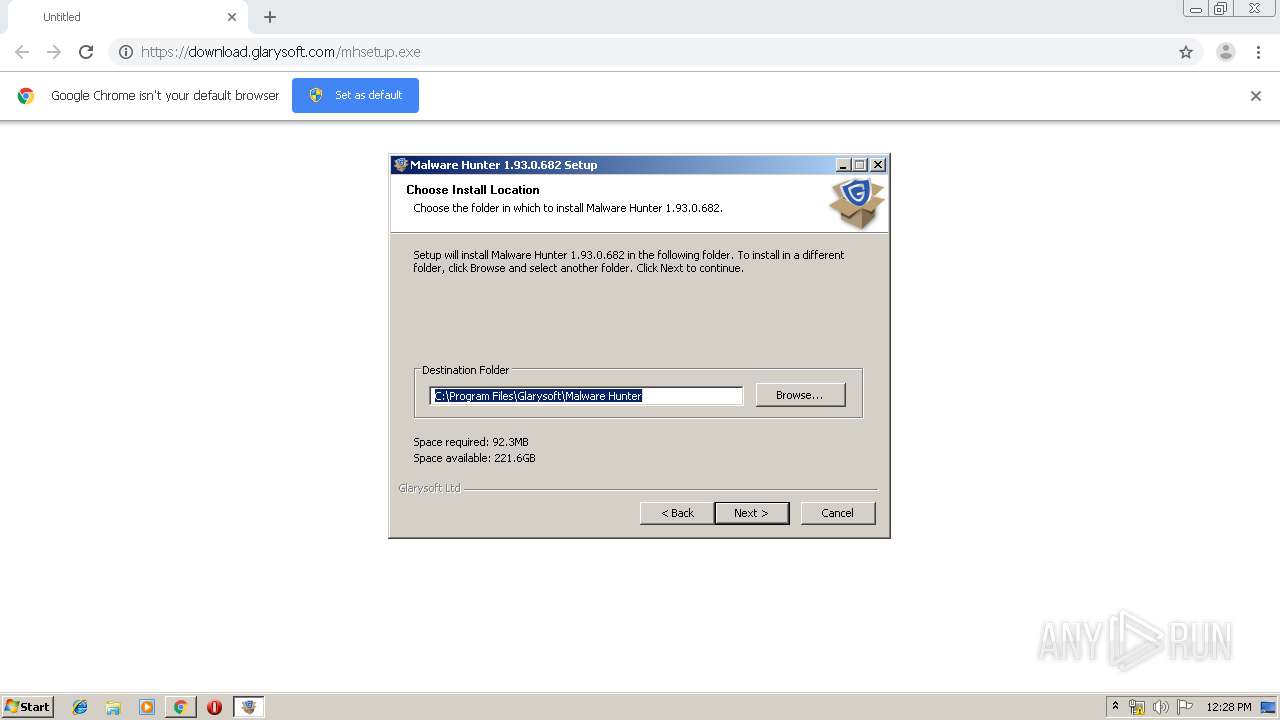
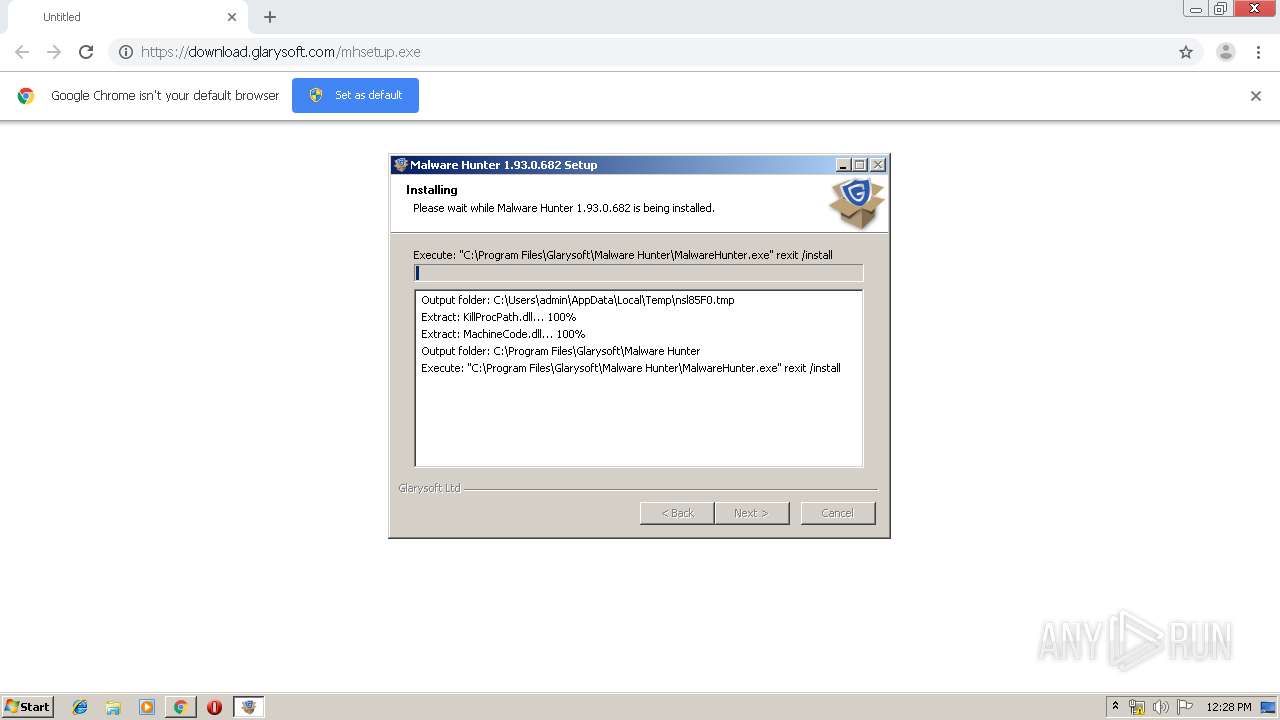
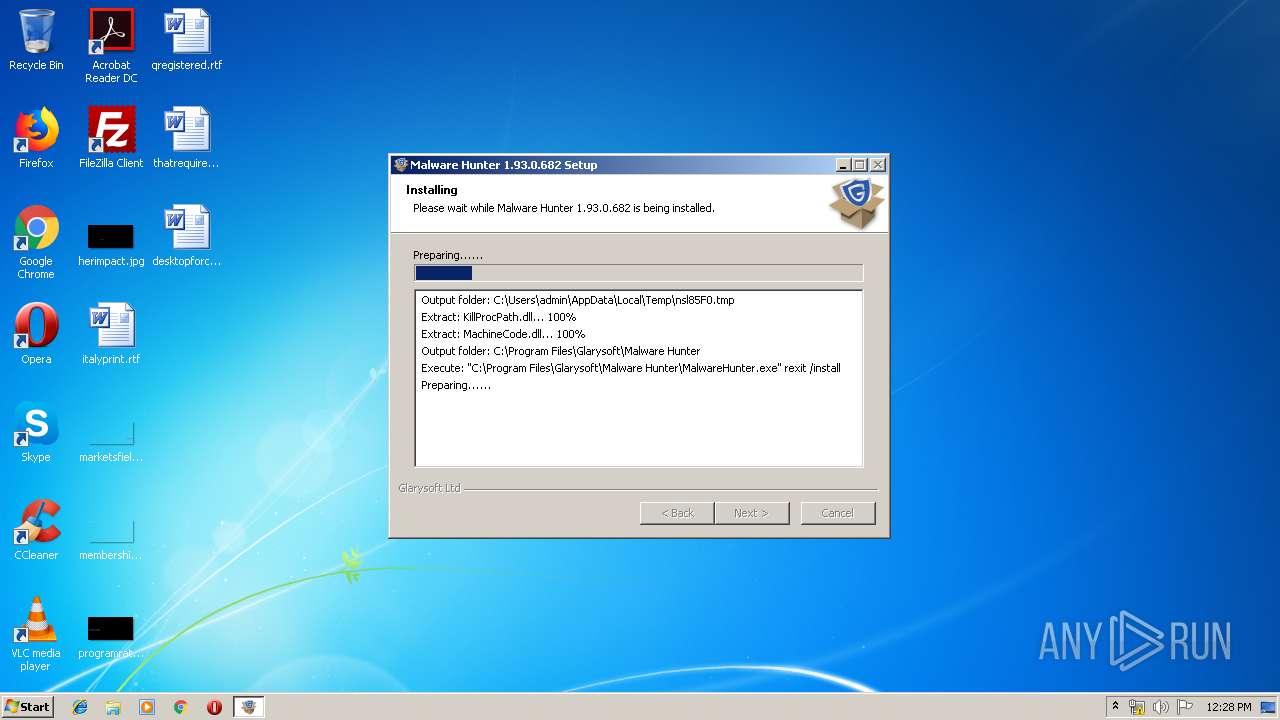
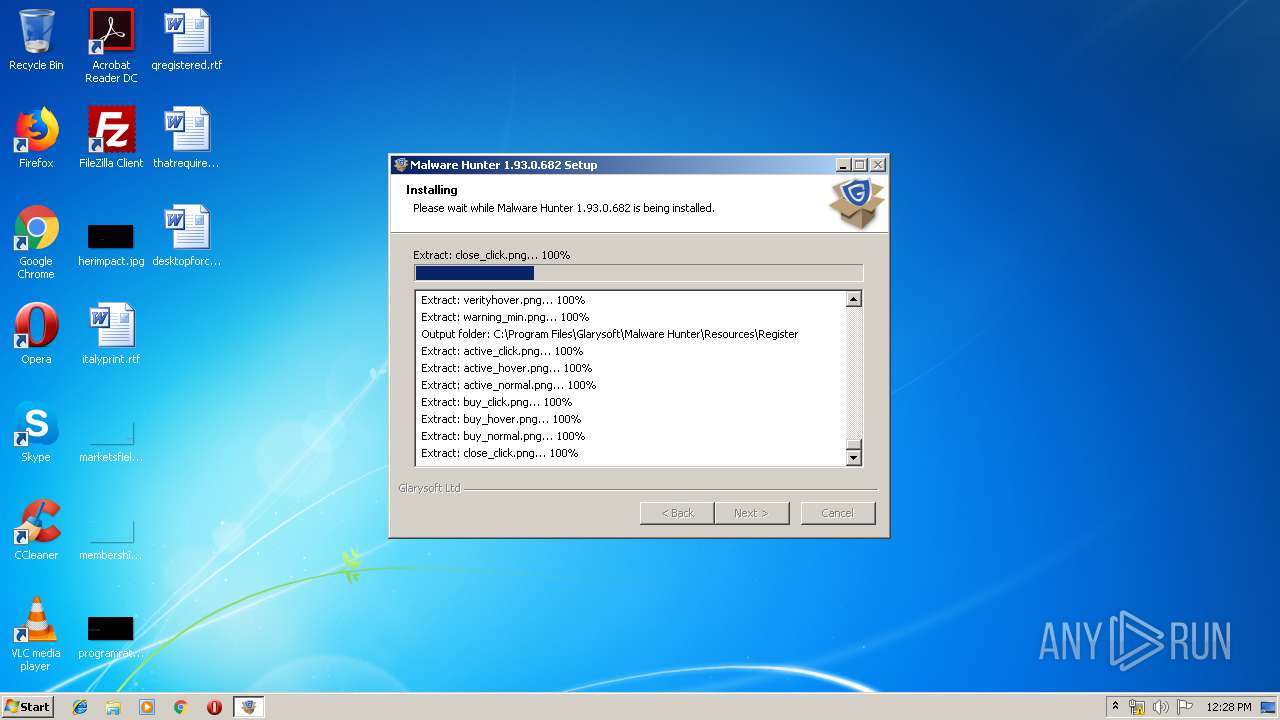
| URL: | https://download.glarysoft.com/mhsetup.exe |
| Full analysis: | https://app.any.run/tasks/6e3111ea-4b12-443f-87ab-21196efb6837 |
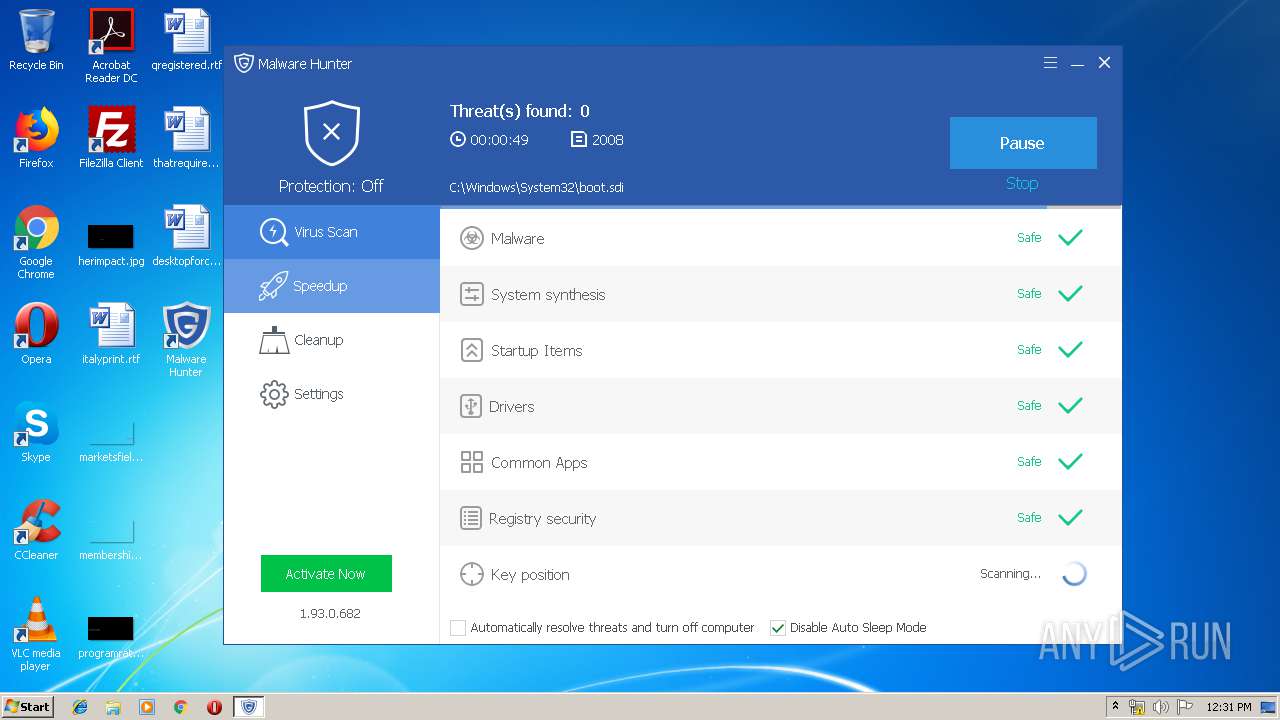
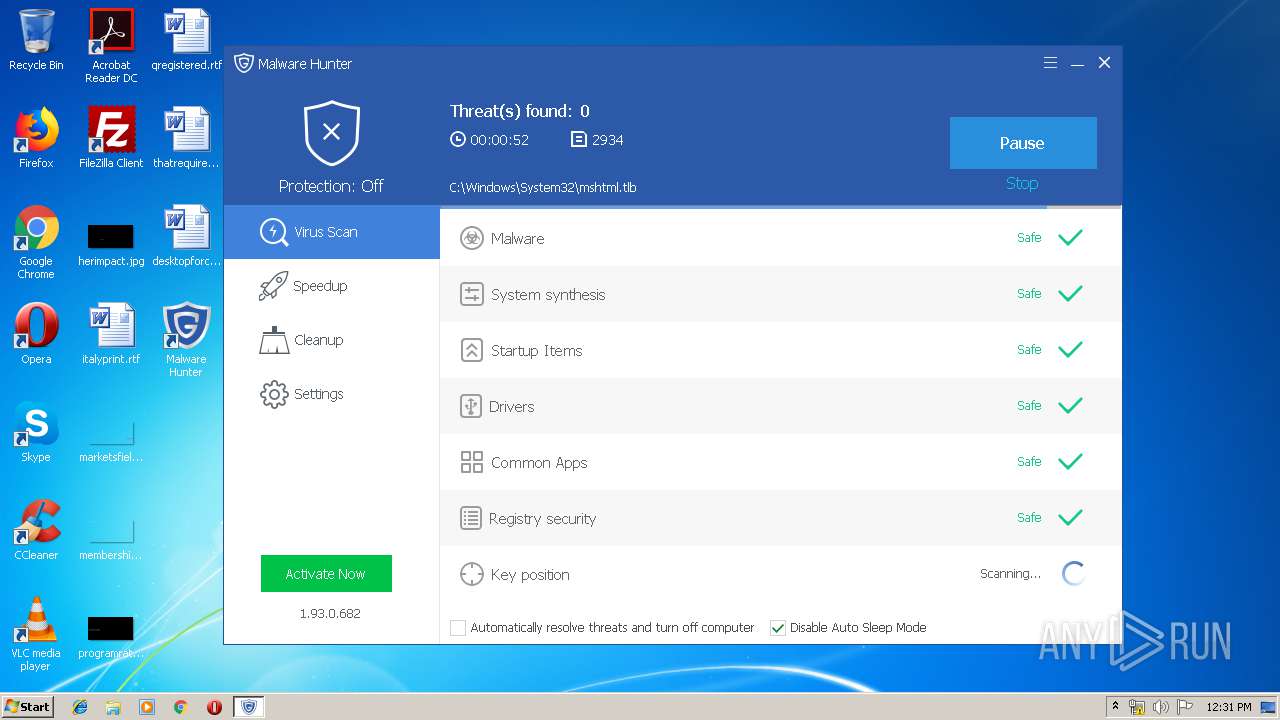
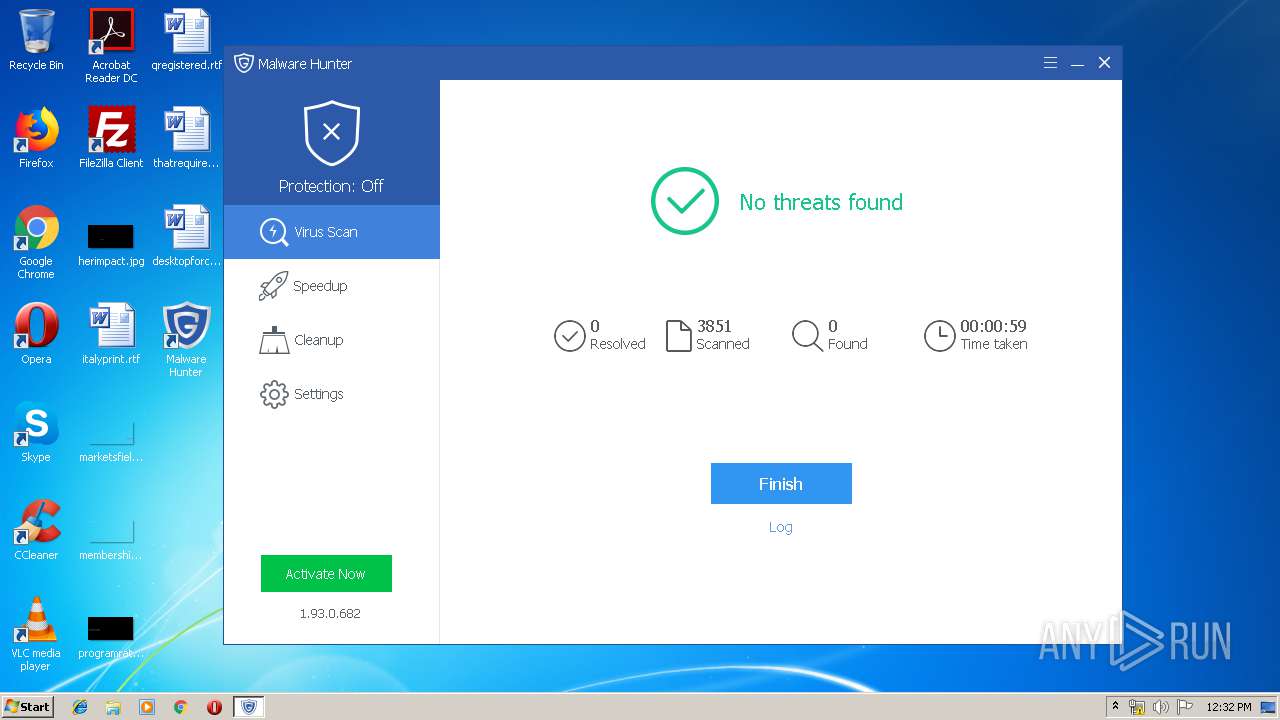
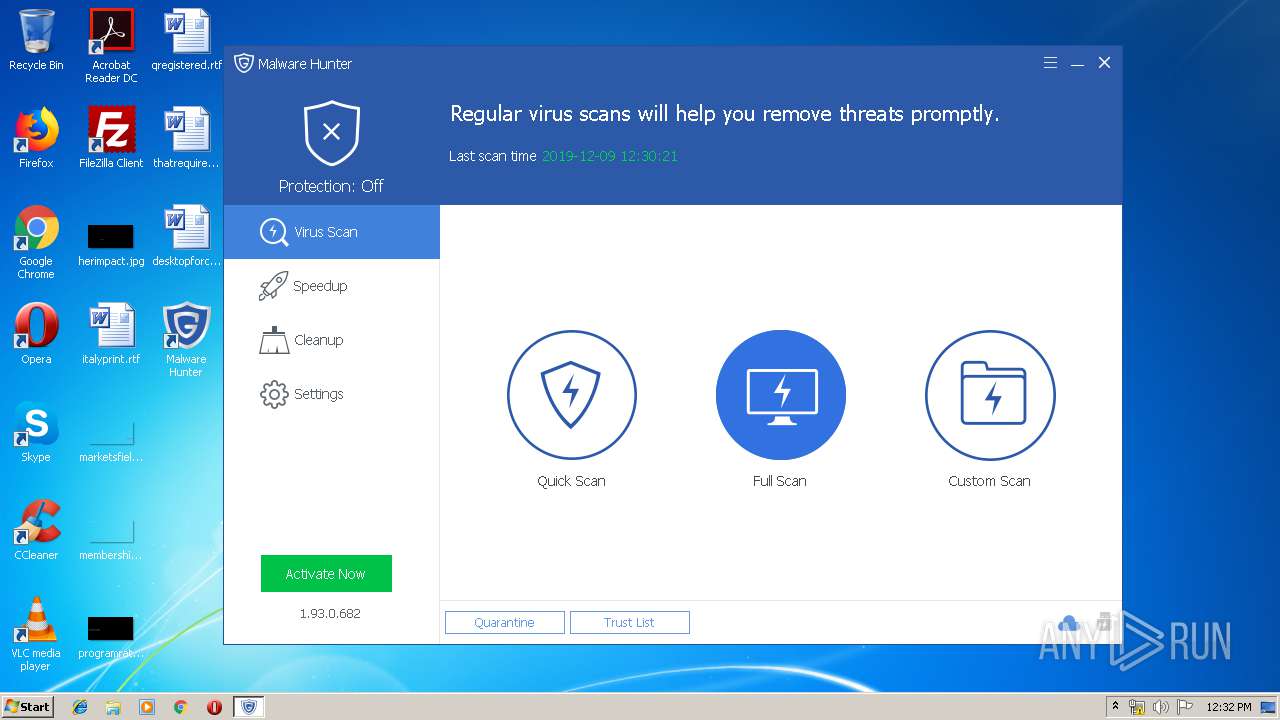
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2019, 12:27:06 |
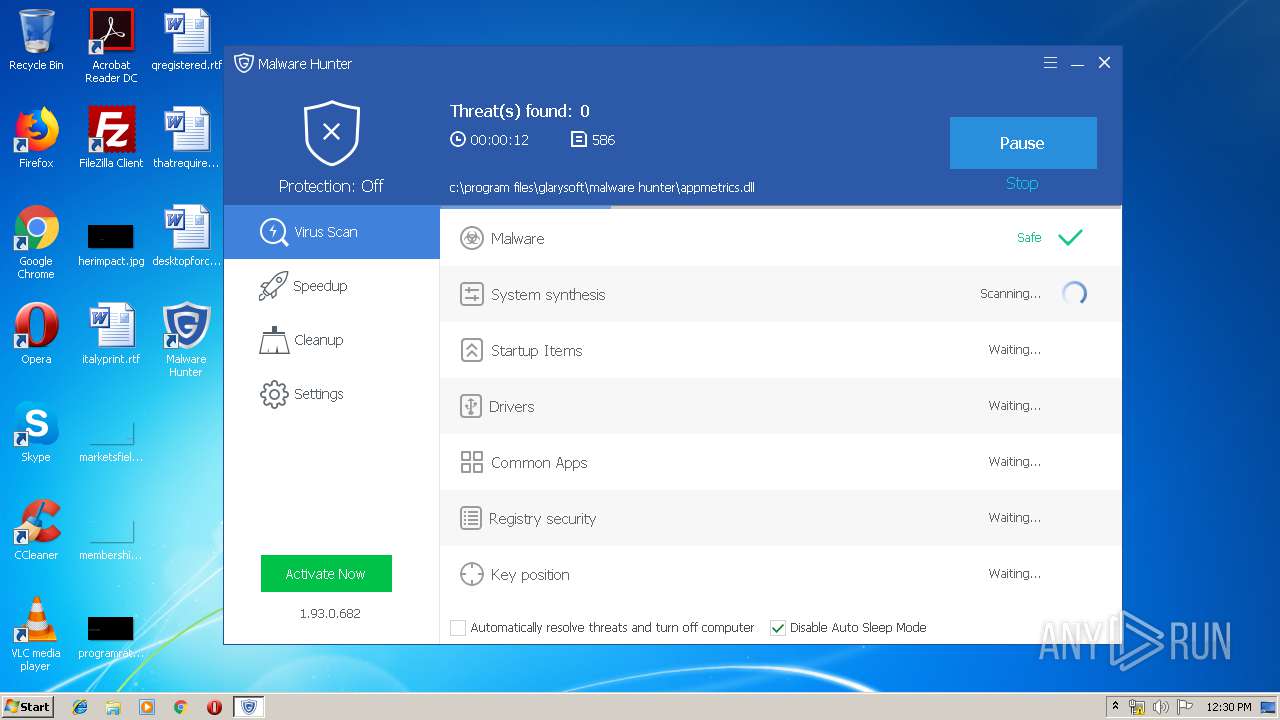
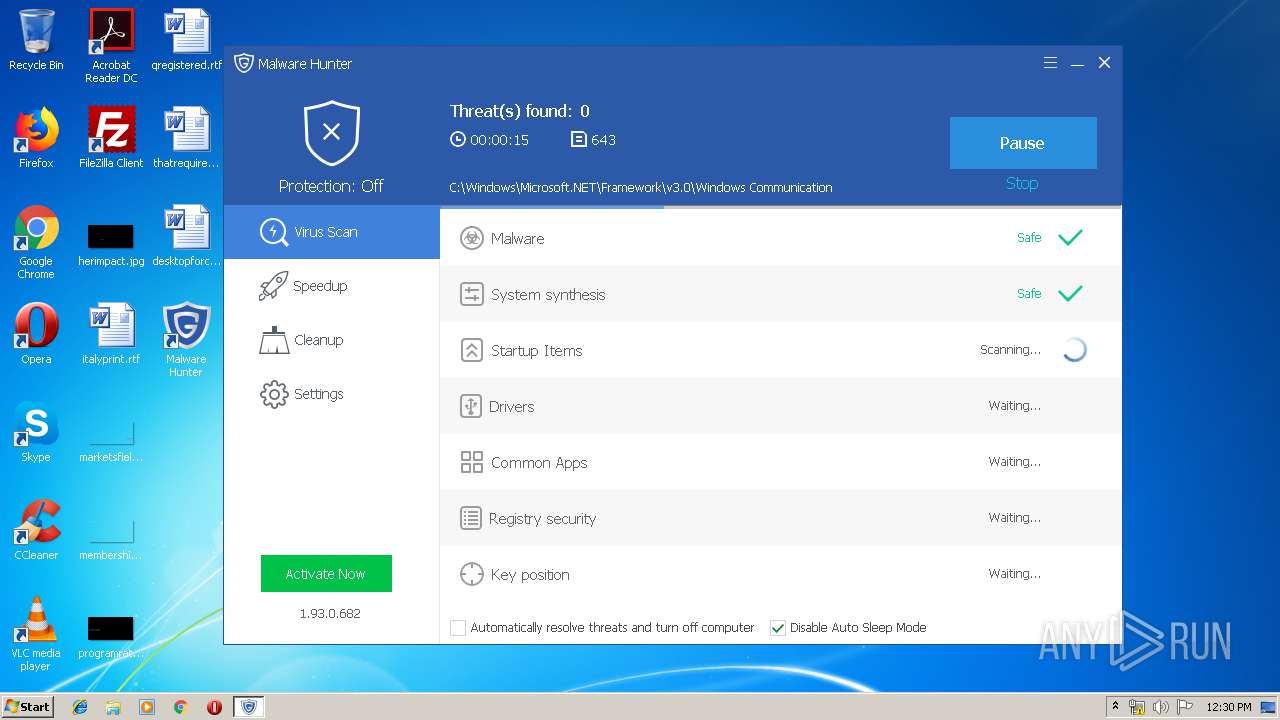
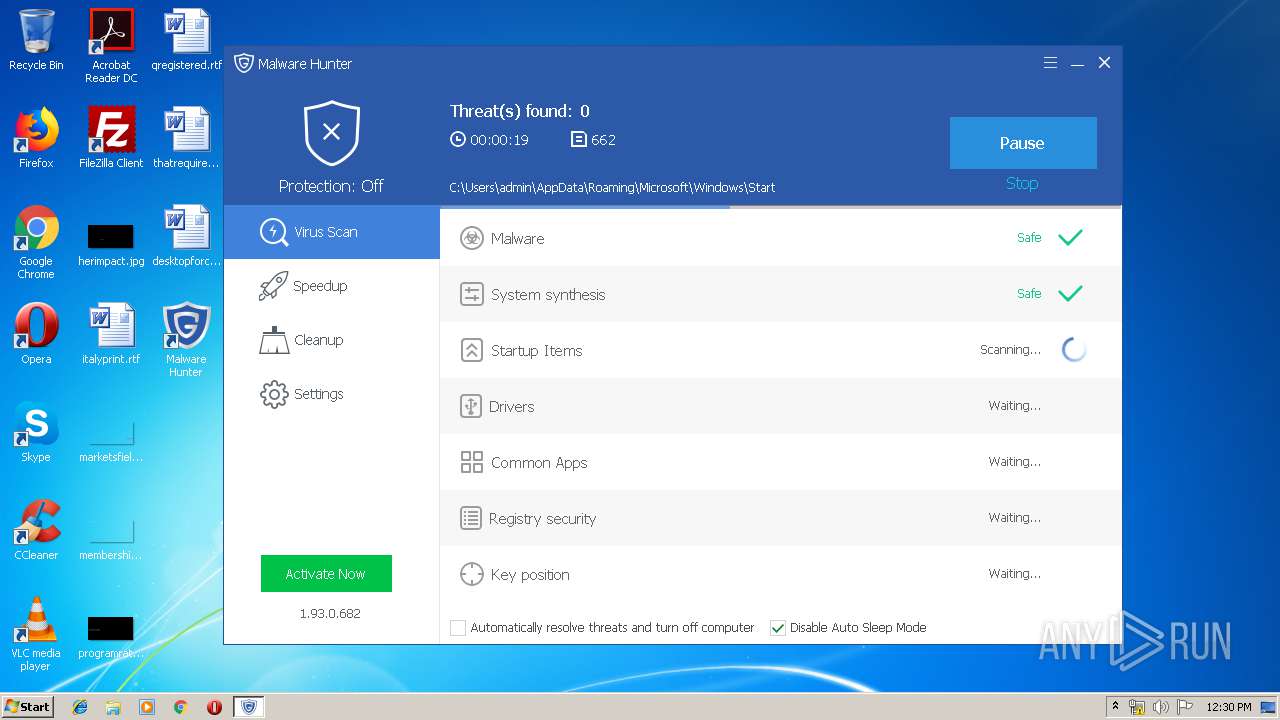
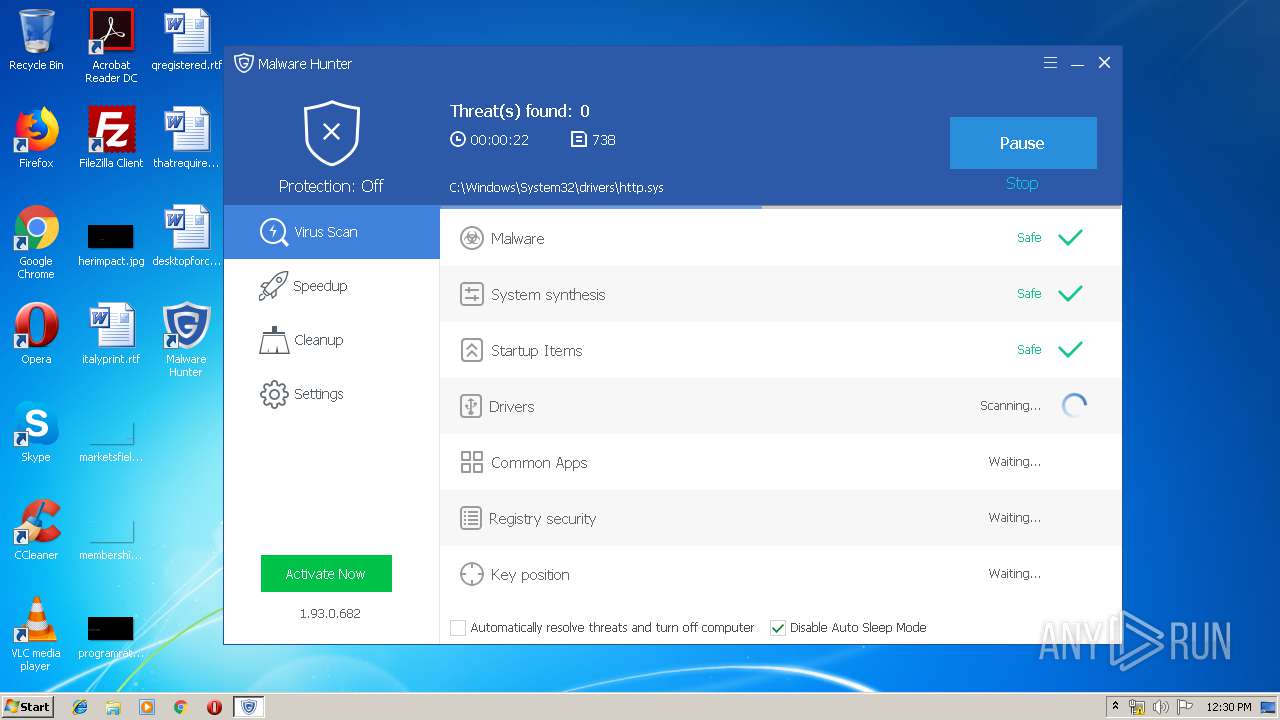
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1571B11E2C25C06AC257BC255F4A402D |
| SHA1: | 771D3CFE67EB17152B403FBDAC65FEA8C965BFE7 |
| SHA256: | 3F6A6F8BA3F12ECB618C55F7AFF8A5B024484CD8C6D3C9A81DDD9E8B0D58E80D |
| SSDEEP: | 3:N8SElyXj4A:2SKIj4A |
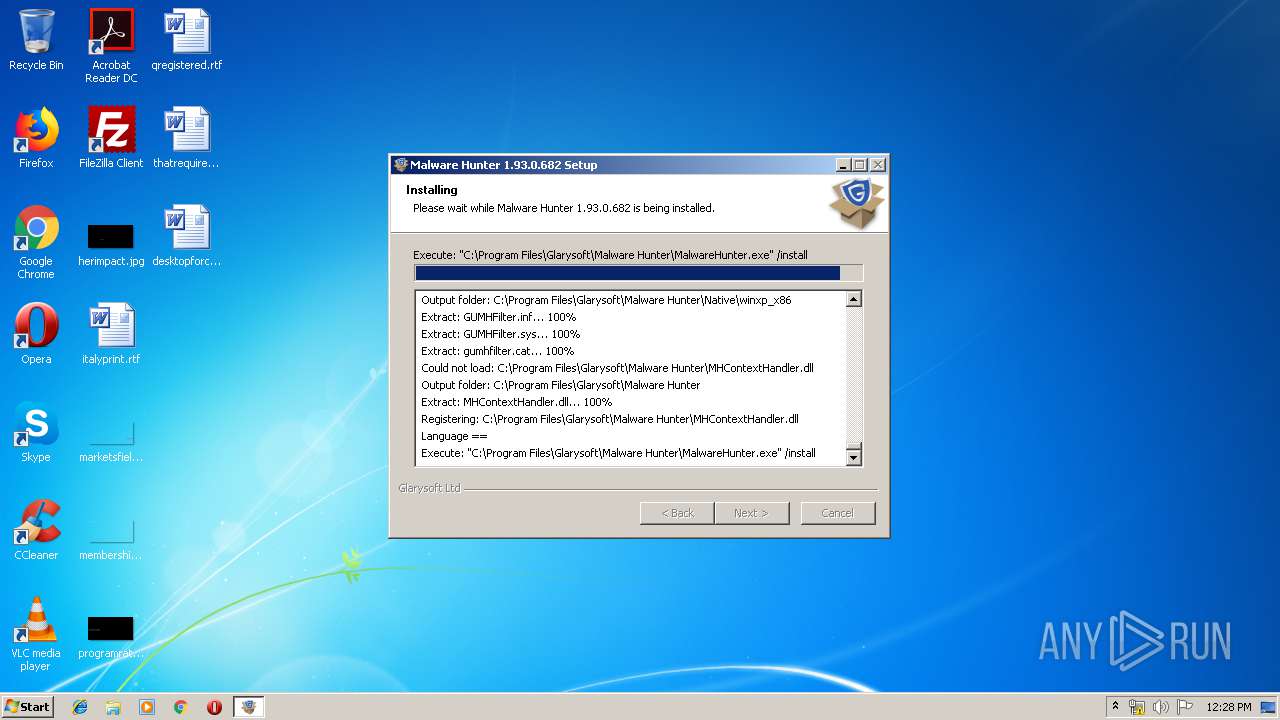
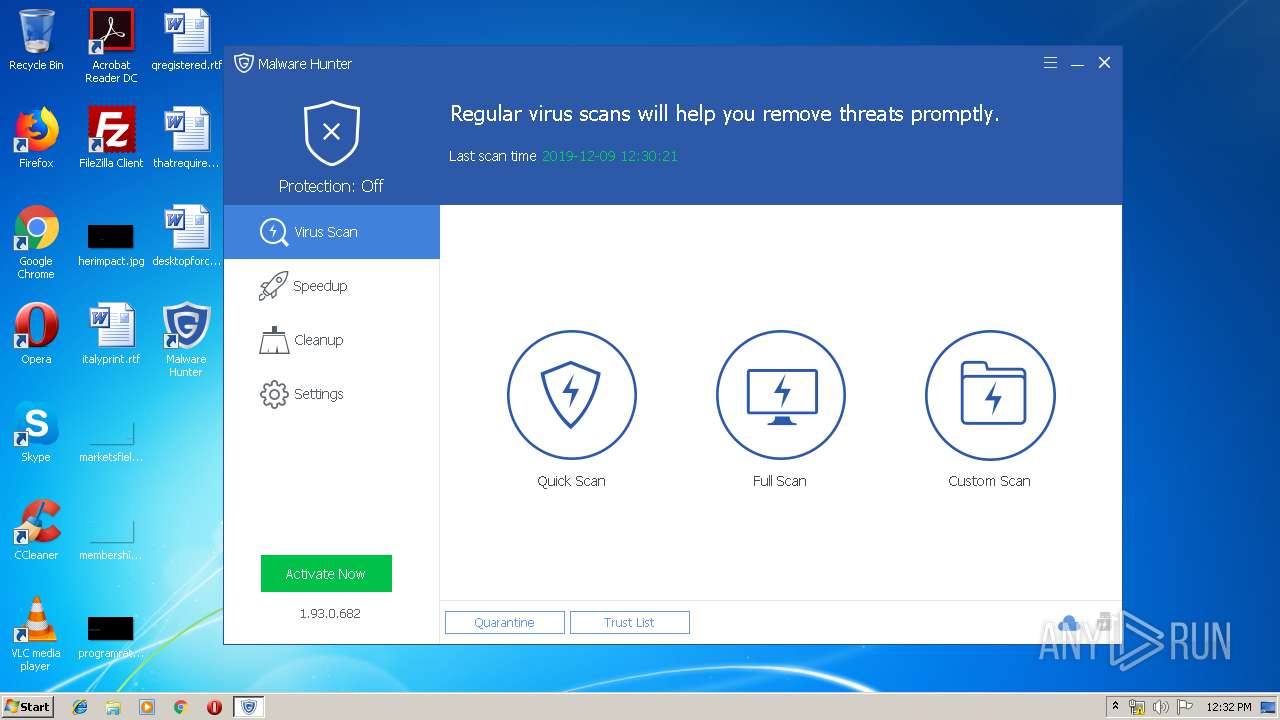
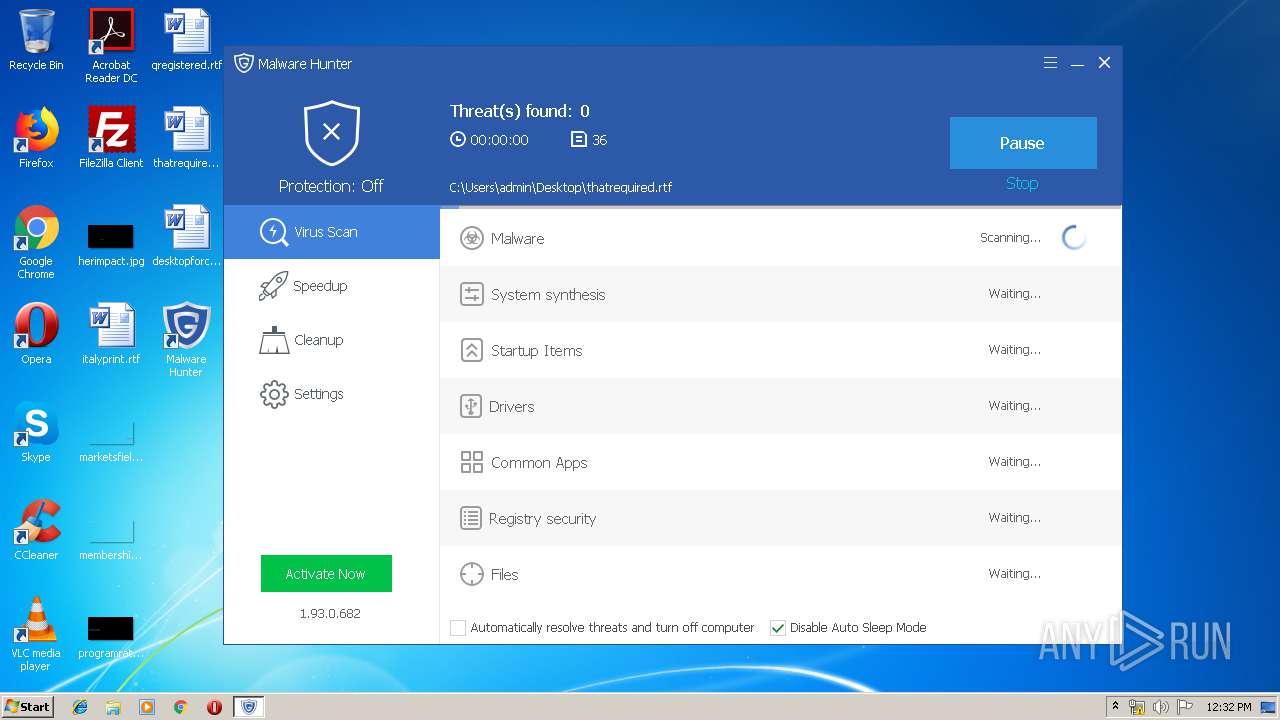
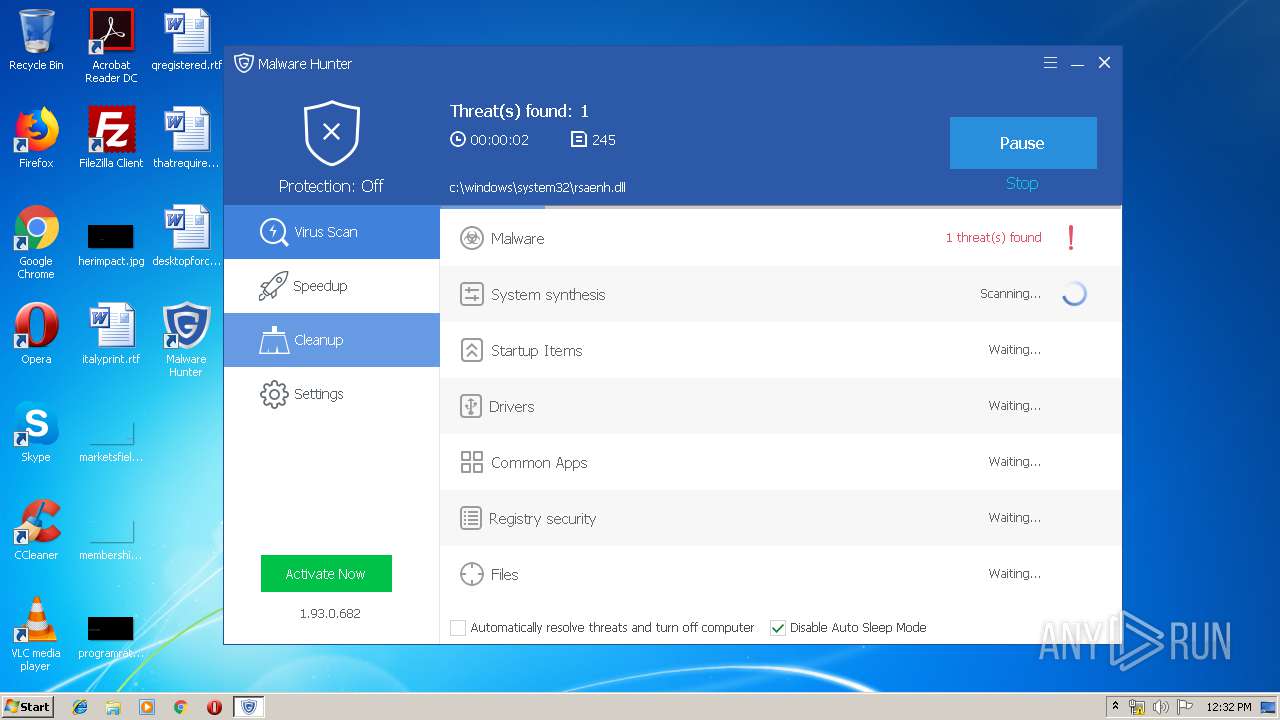
MALICIOUS
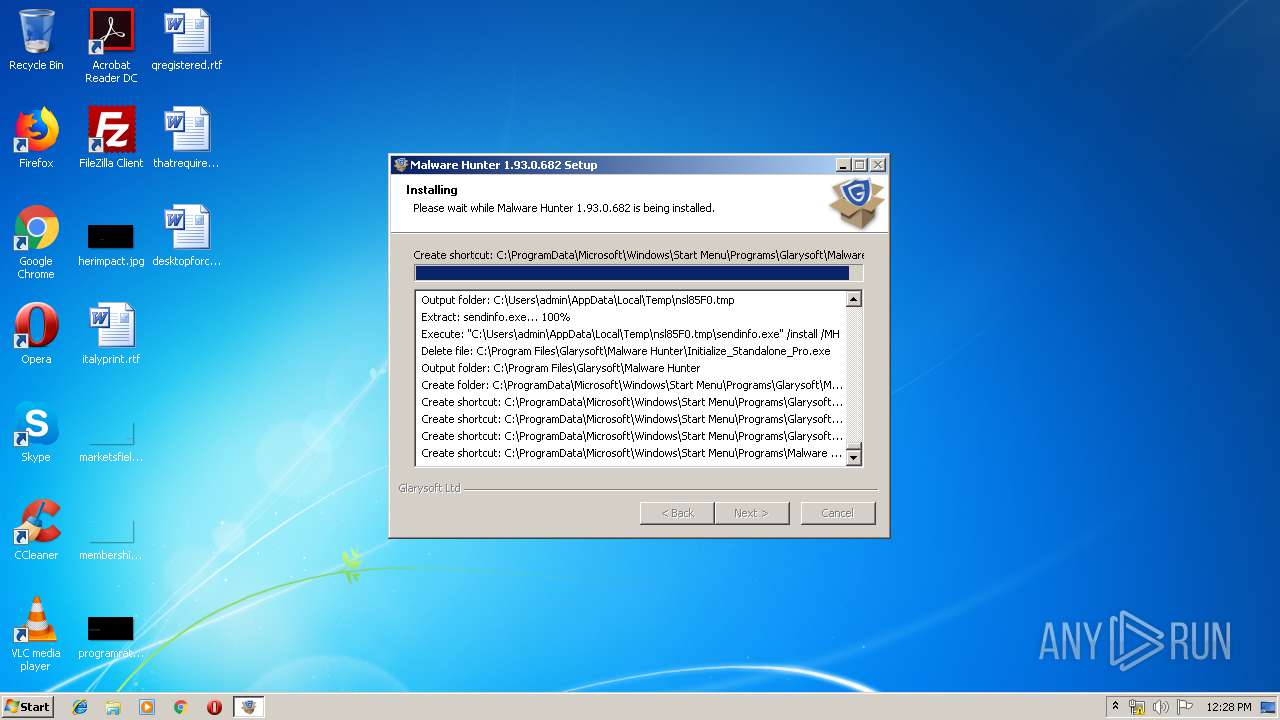
Loads dropped or rewritten executable
- mhsetup.exe (PID: 3088)
- MalwareHunter.exe (PID: 1780)
- Initialize_Standalone_Pro.exe (PID: 2188)
- MHCloudSvc.exe (PID: 2744)
- sendinfo.exe (PID: 1940)
- MalwareHunter.exe (PID: 2124)
- MHCloudSvc.exe (PID: 3820)
- mhtray.exe (PID: 2816)
- MalwareHunter.exe (PID: 2784)
- PCBooster.exe (PID: 2424)
- QuickSearch.exe (PID: 3356)
- MemfilesService.exe (PID: 2308)
Application was dropped or rewritten from another process
- mhsetup.exe (PID: 3088)
- mhsetup.exe (PID: 2120)
- MalwareHunter.exe (PID: 1780)
- MHCloudSvc.exe (PID: 2744)
- Initialize_Standalone_Pro.exe (PID: 2188)
- sendinfo.exe (PID: 1940)
- MHCloudSvc.exe (PID: 3820)
- MalwareHunter.exe (PID: 2124)
- mhtray.exe (PID: 2816)
- MalwareHunter.exe (PID: 2784)
- PCBooster.exe (PID: 2424)
- QuickSearch.exe (PID: 3356)
- MemfilesService.exe (PID: 2308)
Changes settings of System certificates
- MalwareHunter.exe (PID: 1780)
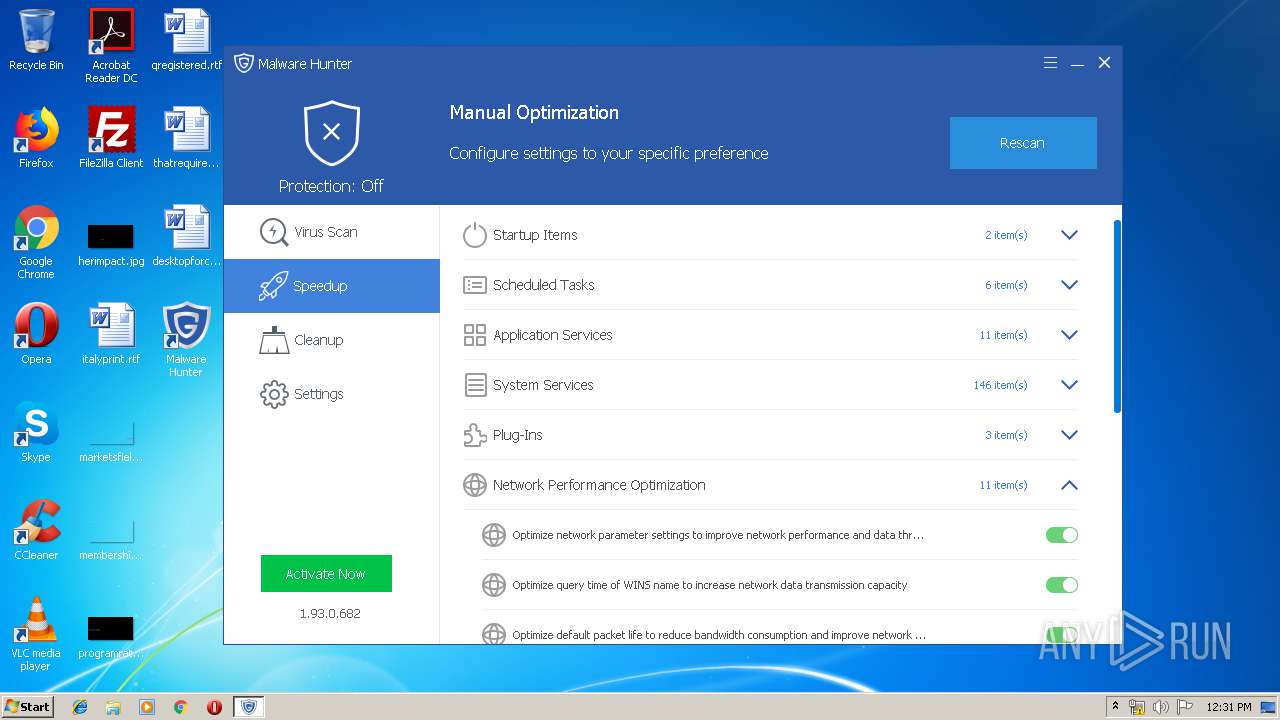
Loads the Task Scheduler COM API
- MalwareHunter.exe (PID: 1780)
- MalwareHunter.exe (PID: 2124)
Changes the autorun value in the registry
- mhtray.exe (PID: 2816)
SUSPICIOUS
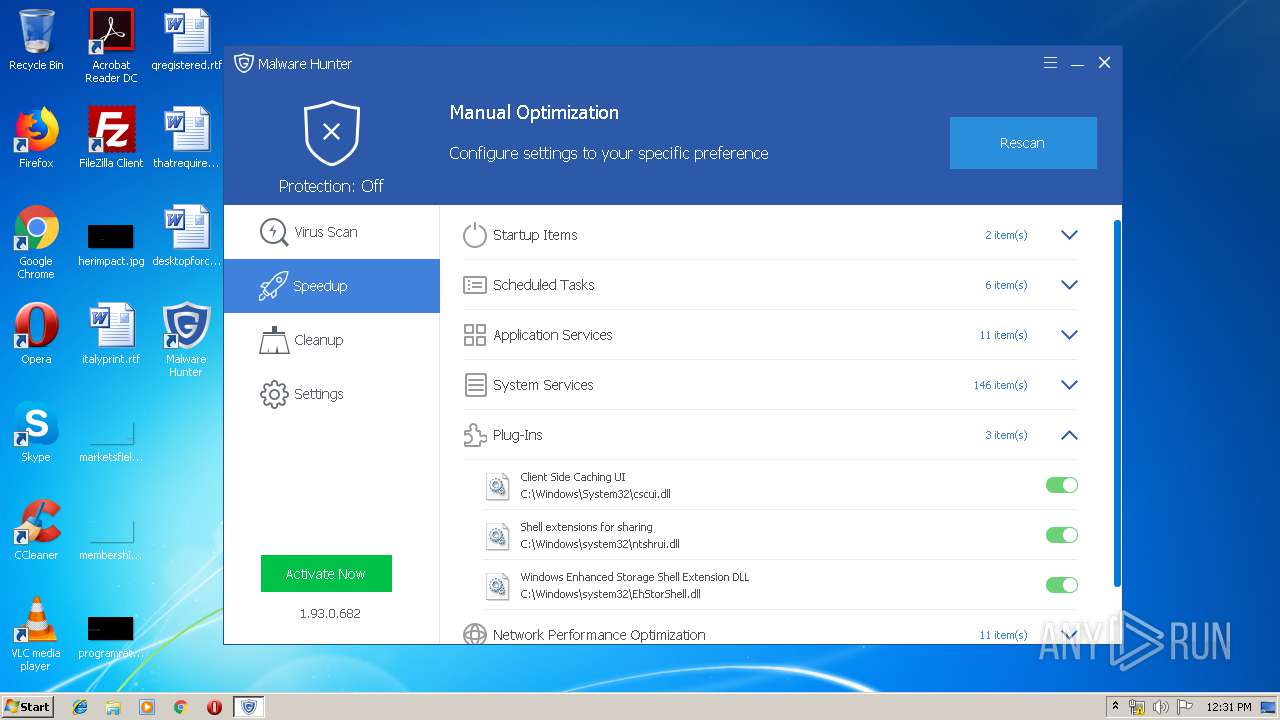
Executable content was dropped or overwritten
- mhsetup.exe (PID: 3088)
- chrome.exe (PID: 1972)
- MalwareHunter.exe (PID: 1780)
- sendinfo.exe (PID: 1940)
Creates COM task schedule object
- mhsetup.exe (PID: 3088)
Creates files in the program directory
- MalwareHunter.exe (PID: 1780)
- MalwareHunter.exe (PID: 2124)
- MHCloudSvc.exe (PID: 3820)
- PCBooster.exe (PID: 2424)
- mhsetup.exe (PID: 3088)
- MemfilesService.exe (PID: 2308)
Creates files in the Windows directory
- MalwareHunter.exe (PID: 1780)
Creates files in the driver directory
- MalwareHunter.exe (PID: 1780)
Adds / modifies Windows certificates
- MalwareHunter.exe (PID: 1780)
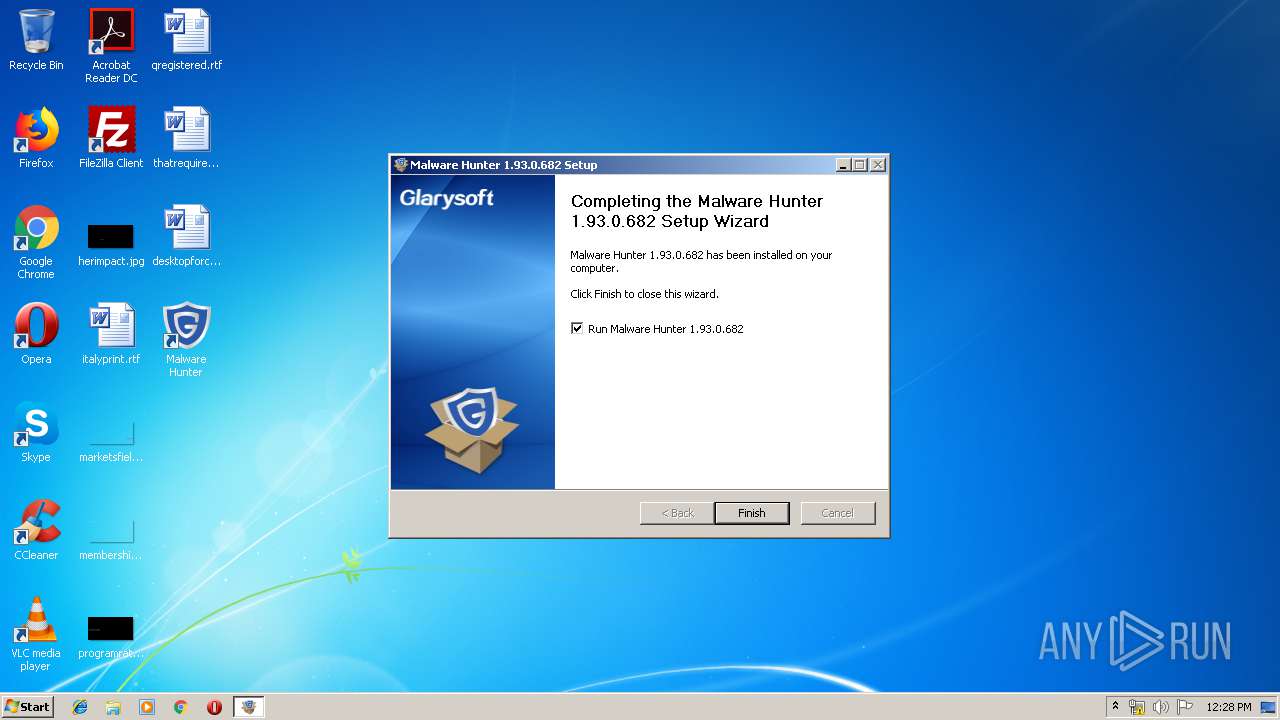
Creates a software uninstall entry
- mhsetup.exe (PID: 3088)
- sendinfo.exe (PID: 1940)
Creates files in the user directory
- mhsetup.exe (PID: 3088)
- PCBooster.exe (PID: 2424)
- MalwareHunter.exe (PID: 2124)
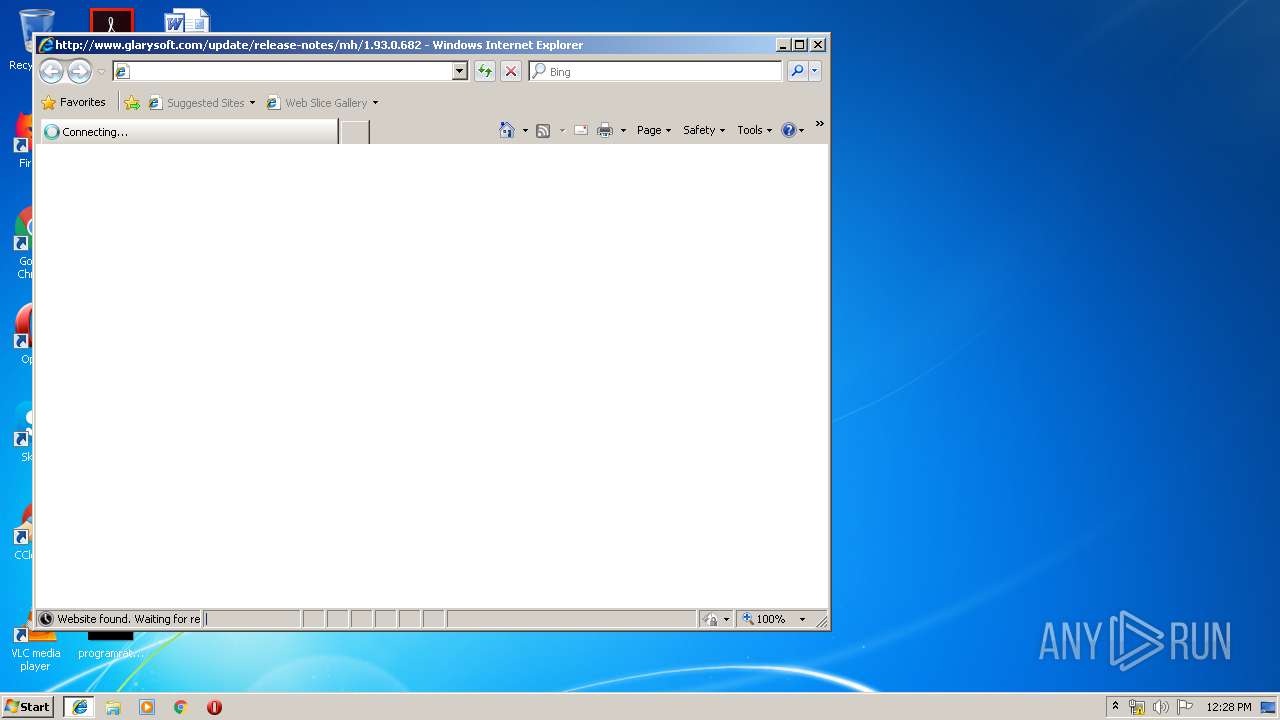
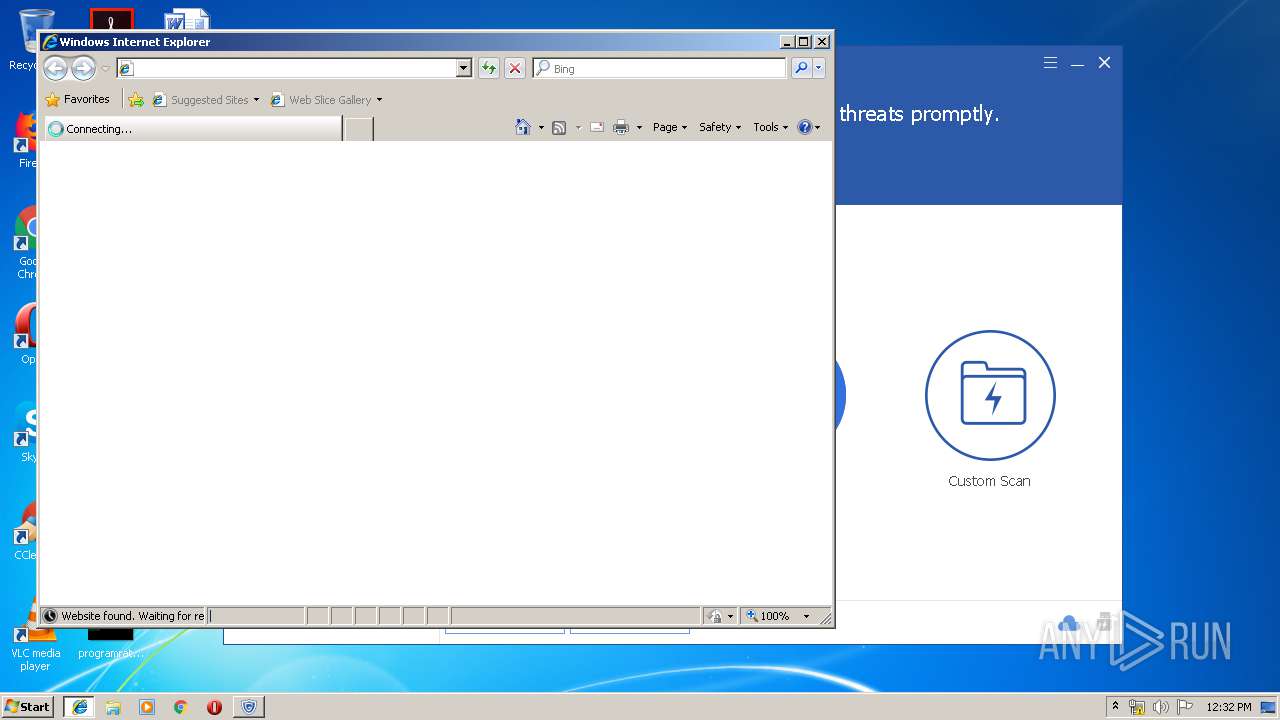
Starts Internet Explorer
- mhsetup.exe (PID: 3088)
- MalwareHunter.exe (PID: 2124)
Executed via COM
- MHCloudSvc.exe (PID: 3820)
Reads internet explorer settings
- QuickSearch.exe (PID: 3356)
Searches for installed software
- MalwareHunter.exe (PID: 2124)
Removes files from Windows directory
- MalwareHunter.exe (PID: 2124)
INFO
Dropped object may contain Bitcoin addresses
- mhsetup.exe (PID: 3088)
Reads Internet Cache Settings
- chrome.exe (PID: 1972)
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2376)
Reads settings of System Certificates
- chrome.exe (PID: 3940)
Reads the hosts file
- chrome.exe (PID: 3940)
- chrome.exe (PID: 1972)
Application launched itself
- chrome.exe (PID: 1972)
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 3576)
Changes internet zones settings
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 3576)
Reads internet explorer settings
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2376)
Creates files in the user directory
- iexplore.exe (PID: 2684)
Changes settings of System certificates
- iexplore.exe (PID: 2376)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
27
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11079048332627542001 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1928 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
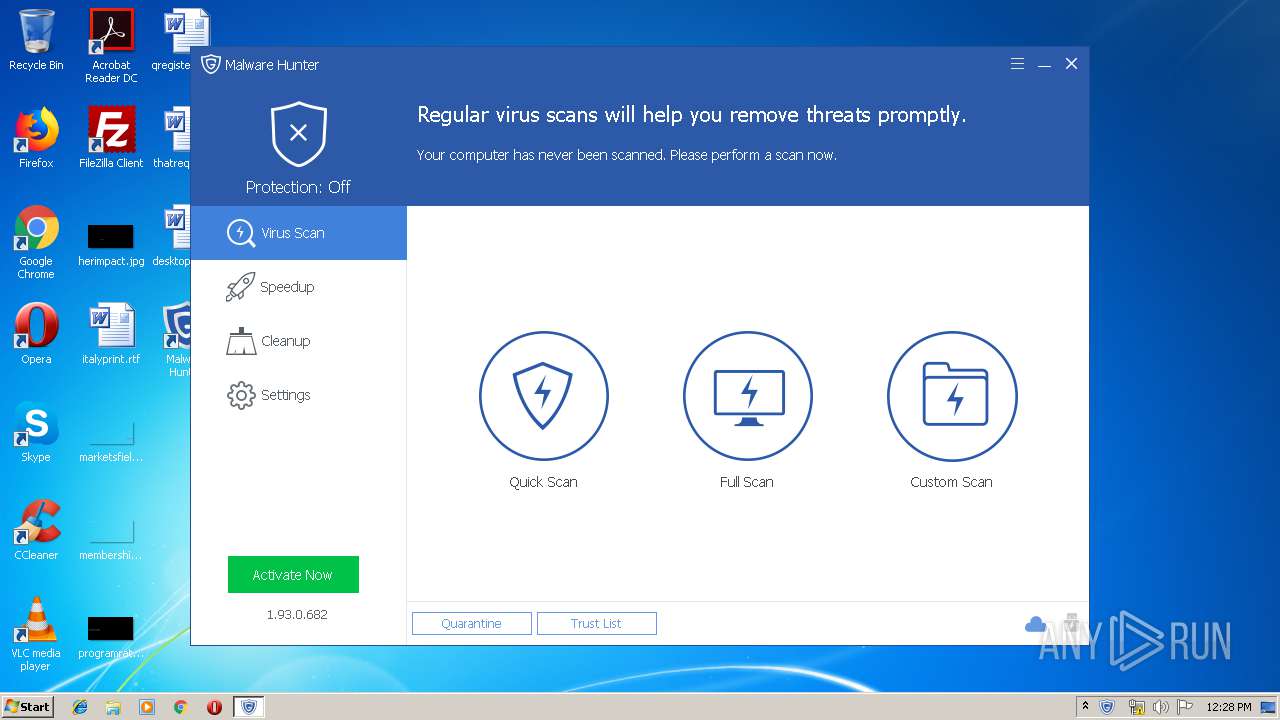
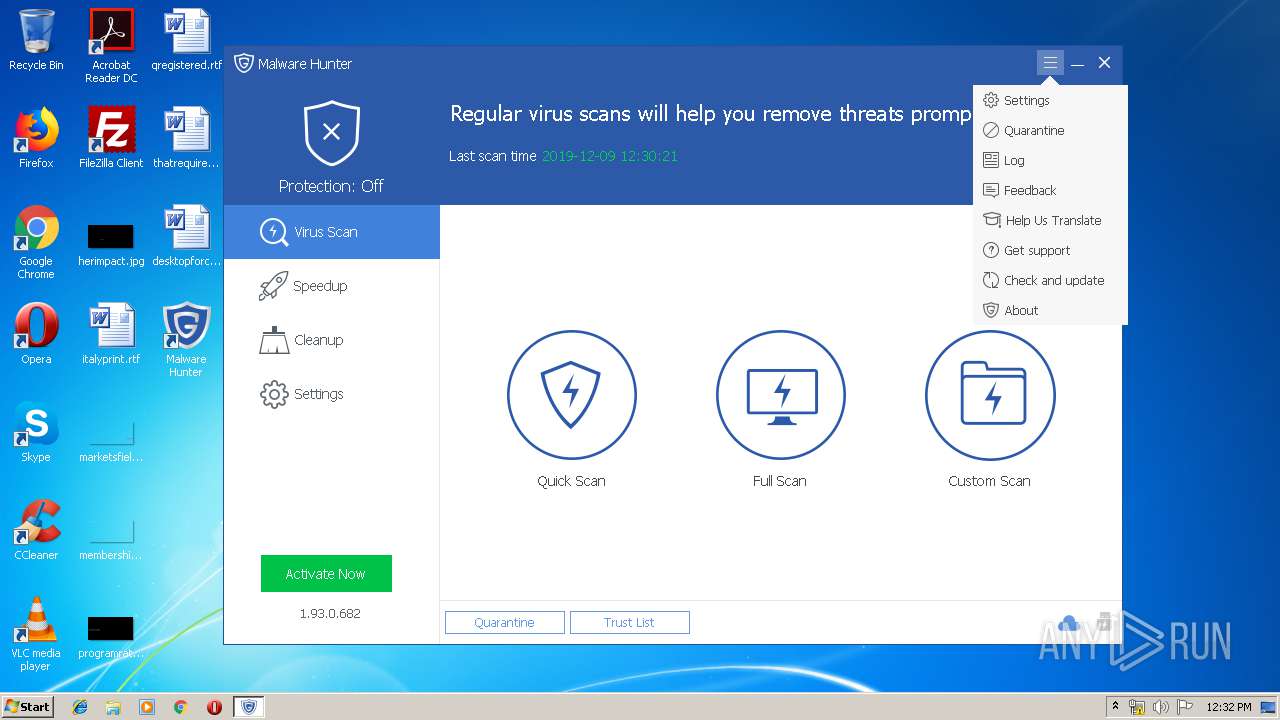
| 1780 | "C:\Program Files\Glarysoft\Malware Hunter\MalwareHunter.exe" /install | C:\Program Files\Glarysoft\Malware Hunter\MalwareHunter.exe | mhsetup.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glarysoft Malware Hunter Exit code: 0 Version: 1.93.0.682 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16556315593784804160 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Users\admin\AppData\Local\Temp\nsl85F0.tmp\sendinfo.exe" /install /MH | C:\Users\admin\AppData\Local\Temp\nsl85F0.tmp\sendinfo.exe | mhsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://download.glarysoft.com/mhsetup.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\Downloads\mhsetup.exe" | C:\Users\admin\Downloads\mhsetup.exe | — | chrome.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: MEDIUM Description: Malware Hunter Installer Exit code: 3221226540 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Glarysoft\Malware Hunter\MalwareHunter.exe" | C:\Program Files\Glarysoft\Malware Hunter\MalwareHunter.exe | mhsetup.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glarysoft Malware Hunter Exit code: 0 Version: 1.93.0.682 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Glarysoft\Malware Hunter\Initialize_Standalone_Pro.exe" /installinit productid=15 | C:\Program Files\Glarysoft\Malware Hunter\Initialize_Standalone_Pro.exe | — | mhsetup.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Initialize Exit code: 0 Version: 5, 0, 0, 46 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Glarysoft\Malware Hunter\MemfilesService.exe" | C:\Program Files\Glarysoft\Malware Hunter\MemfilesService.exe | — | QuickSearch.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: MemfilesService Exit code: 0 Version: 5.18.1.21 Modules
| |||||||||||||||
Total events
3 909
Read events
3 216
Write events
584
Delete events
109
Modification events
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1972-13220368052264000 |
Value: 259 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
68
Suspicious files
45
Text files
524
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\49542cf3-f736-49e6-9536-349d1ed0fcb4.tmp | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39be97.TMP | text | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39bfdf.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
43
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | MHCloudSvc.exe | POST | 200 | 54.226.84.60:80 | http://mh.glarysoft.com/openapi/get_auth_code.php | US | text | 896 b | unknown |
2684 | iexplore.exe | GET | 200 | 54.243.205.134:80 | http://www.glarysoft.com/update/release-notes/mh/1.93.0.682 | US | html | 26.6 Kb | whitelisted |
1940 | sendinfo.exe | POST | 200 | 54.186.7.180:80 | http://metrics.glarysoft.com/install.php | US | — | — | whitelisted |
1940 | sendinfo.exe | POST | 200 | 54.186.7.180:80 | http://metrics.glarysoft.com/install.php | US | — | — | whitelisted |
2684 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/content.css?18011003 | US | html | 258 b | whitelisted |
2684 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/js/index.js?191202 | US | html | 252 b | whitelisted |
2684 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/global.css?1912021231 | US | html | 259 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 172.217.22.106:80 | http://fonts.googleapis.com/css?family=Open+Sans:400,300,600,800,700 | US | text | 167 b | whitelisted |
2124 | MalwareHunter.exe | GET | 200 | 13.224.197.11:80 | http://avira.glarysoft.com/like.txt | US | text | 6 b | whitelisted |
2124 | MalwareHunter.exe | POST | 200 | 54.225.78.163:80 | http://myaccount.glarysoft.com/openapi.php/lr/expire_time | US | text | 44 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3940 | chrome.exe | 13.225.78.11:443 | download.glarysoft.com | — | US | unknown |
3940 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 143.204.98.54:80 | x.ss2.us | — | US | suspicious |
3940 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 172.217.21.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 8.248.141.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1940 | sendinfo.exe | 54.186.7.180:80 | metrics.glarysoft.com | Amazon.com, Inc. | US | whitelisted |
2684 | iexplore.exe | 54.243.205.134:80 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.glarysoft.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
metrics.glarysoft.com |
| whitelisted |
www.glarysoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1940 | sendinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1940 | sendinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |