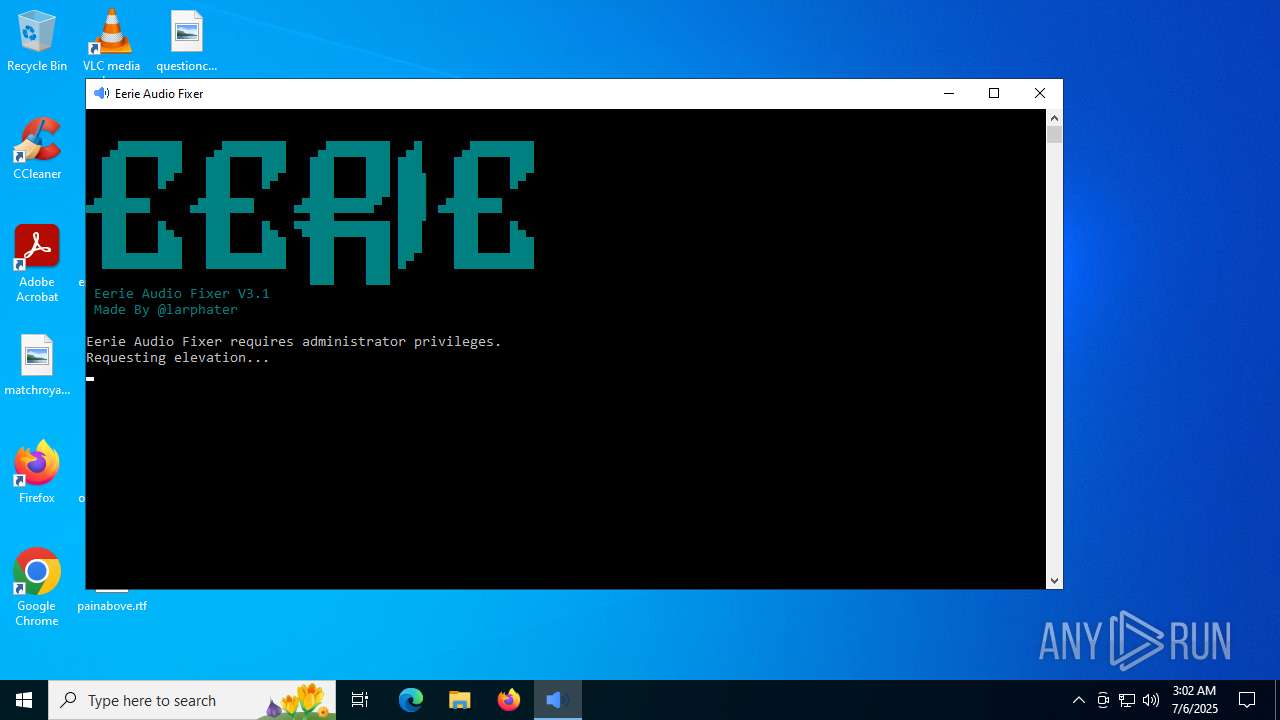
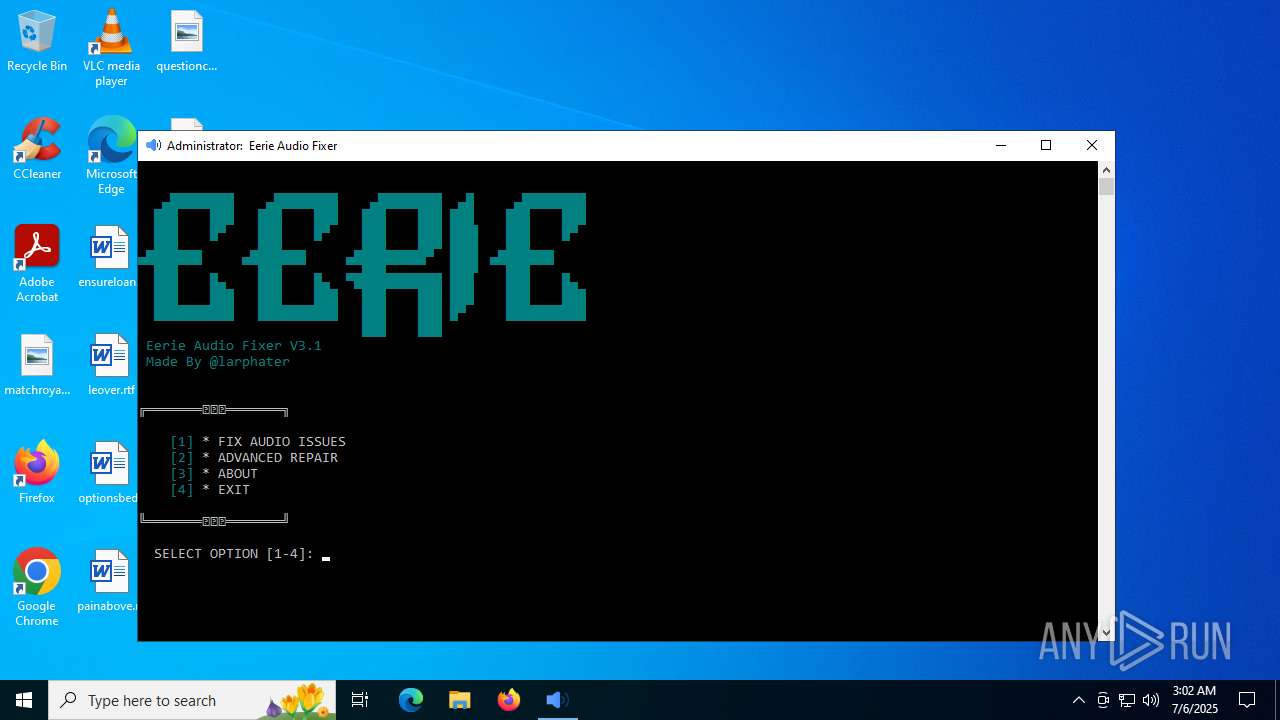
| File name: | EerieAFX.exe |
| Full analysis: | https://app.any.run/tasks/48c5b4a5-2d73-4363-af1e-9797cb0ec347 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2025, 03:02:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 3B53F3962386049421397525A2F2E62C |
| SHA1: | E885B82EF58BDF71A795FEC98075A62A9538510F |
| SHA256: | 3F6A4CFA73396BA7BB2EFFBC71D23673844186930E27B6A1219D4080BC24E4A3 |
| SSDEEP: | 98304:R/0CMhZwlB4N+wcTAScUCYDSPzrET1sBbPqV/0htD+w7UJDZ2pli9TZIATPSkO2k:SLTyJwnGoG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
Process drops python dynamic module
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
The process drops C-runtime libraries
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
Executable content was dropped or overwritten
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
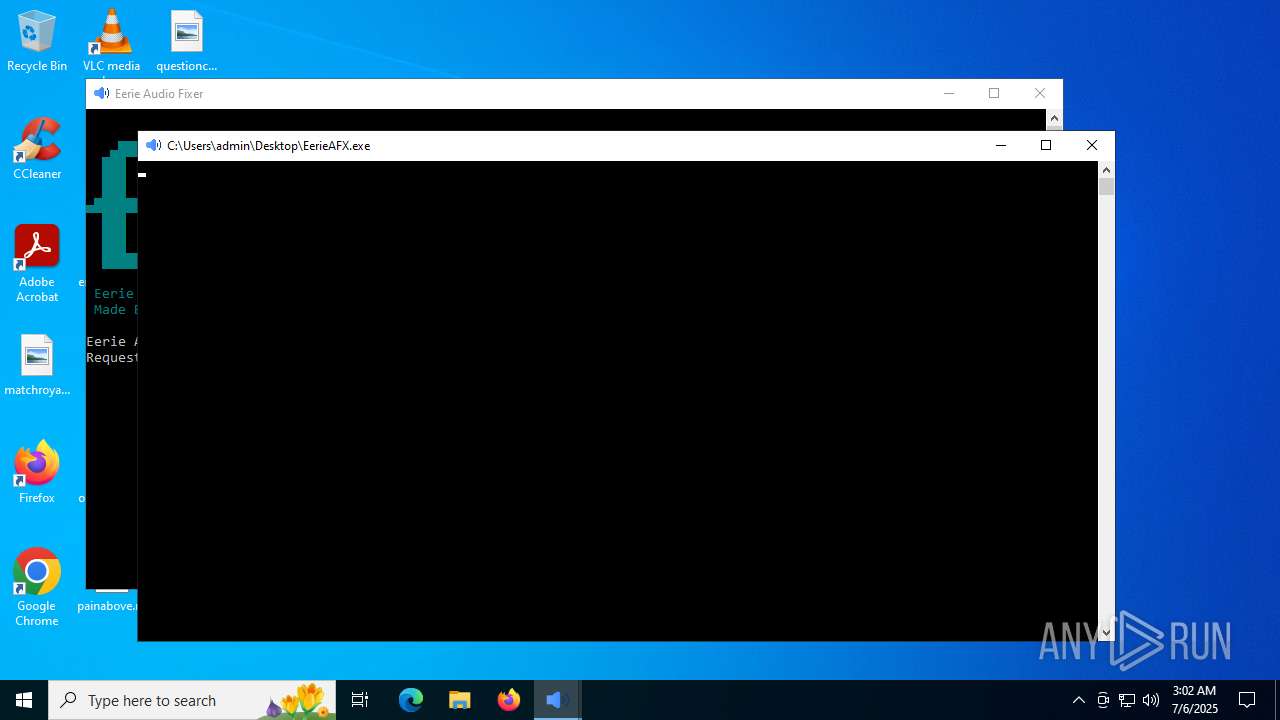
Application launched itself
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 4380)
- EerieAFX.exe (PID: 3288)
Loads Python modules
- EerieAFX.exe (PID: 4380)
- EerieAFX.exe (PID: 6720)
Reads the date of Windows installation
- EerieAFX.exe (PID: 4380)
Reads security settings of Internet Explorer
- EerieAFX.exe (PID: 4380)
Starts CMD.EXE for commands execution
- EerieAFX.exe (PID: 4380)
- EerieAFX.exe (PID: 6720)
INFO
Create files in a temporary directory
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
Reads the computer name
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 4380)
- EerieAFX.exe (PID: 3288)
The sample compiled with english language support
- EerieAFX.exe (PID: 4788)
- EerieAFX.exe (PID: 3288)
Checks supported languages
- EerieAFX.exe (PID: 4380)
- EerieAFX.exe (PID: 3288)
- EerieAFX.exe (PID: 6720)
- EerieAFX.exe (PID: 4788)
Process checks computer location settings
- EerieAFX.exe (PID: 4380)
Checks proxy server information
- slui.exe (PID: 3940)
PyInstaller has been detected (YARA)
- EerieAFX.exe (PID: 3288)
- EerieAFX.exe (PID: 6720)
Reads the software policy settings
- slui.exe (PID: 3940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:29 20:56:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 178688 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
145
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1976 | C:\WINDOWS\system32\cmd.exe /c title Eerie Audio Fixer | C:\Windows\System32\cmd.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\Desktop\EerieAFX.exe" "C:\Users\admin\AppData\Local\Temp\_MEI47882\optimized_audio_fixer.py" | C:\Users\admin\Desktop\EerieAFX.exe | EerieAFX.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3924 | C:\WINDOWS\system32\cmd.exe /c title Eerie Audio Fixer | C:\Windows\System32\cmd.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3940 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4380 | "C:\Users\admin\Desktop\EerieAFX.exe" | C:\Users\admin\Desktop\EerieAFX.exe | — | EerieAFX.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4788 | "C:\Users\admin\Desktop\EerieAFX.exe" | C:\Users\admin\Desktop\EerieAFX.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4960 | C:\WINDOWS\system32\cmd.exe /c color 0B | C:\Windows\System32\cmd.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | C:\WINDOWS\system32\cmd.exe /c color 0B | C:\Windows\System32\cmd.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | EerieAFX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 873
Read events
3 873
Write events
0
Delete events
0
Modification events
Executable files
24
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\_hashlib.pyd | executable | |
MD5:32D76C9ABD65A5D2671AEEDE189BC290 | SHA256:838D5C8B7C3212C8429BAF612623ABBBC20A9023EEC41E34E5461B76A285B86C | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\_decimal.pyd | executable | |
MD5:F3377F3DE29579140E2BBAEEFD334D4F | SHA256:B715D1C18E9A9C1531F21C02003B4C6726742D1A2441A1893BC3D79D7BB50E91 | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\libffi-8.dll | executable | |
MD5:0F8E4992CA92BAAF54CC0B43AACCCE21 | SHA256:EFF52743773EB550FCC6CE3EFC37C85724502233B6B002A35496D828BD7B280A | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\_bz2.pyd | executable | |
MD5:CB8C06C8FA9E61E4AC5F22EEBF7F1D00 | SHA256:FC3B481684B926350057E263622A2A5335B149A0498A8D65C4F37E39DD90B640 | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\_ctypes.pyd | executable | |
MD5:A55E57D7594303C89B5F7A1D1D6F2B67 | SHA256:F63C6C7E71C342084D8F1A108786CA6975A52CEFEF8BE32CC2589E6E2FE060C8 | |||
| 4788 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI47882\unicodedata.pyd | executable | |
MD5:0902D299A2A487A7B0C2D75862B13640 | SHA256:2693C7EE4FBA55DC548F641C0CB94485D0E18596FFEF16541BD43A5104C28B20 | |||
| 3288 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\_socket.pyd | executable | |
MD5:FE896371430BD9551717EF12A3E7E818 | SHA256:35246B04C6C7001CA448554246445A845CE116814A29B18B617EA38752E4659B | |||
| 3288 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 3288 | EerieAFX.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\_bz2.pyd | executable | |
MD5:CB8C06C8FA9E61E4AC5F22EEBF7F1D00 | SHA256:FC3B481684B926350057E263622A2A5335B149A0498A8D65C4F37E39DD90B640 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7092 | RUXIMICS.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7092 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7092 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
7092 | RUXIMICS.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7092 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |