| File name: | SetupFA.exe |
| Full analysis: | https://app.any.run/tasks/bca65cd7-4414-4933-818d-afa18bb5900e |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2020, 08:03:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 6C685E04456F4354CF5E9A7D862EE97D |
| SHA1: | E802B06CDEF89596F240AB4E560E0378D3CF5CCB |
| SHA256: | 3F68F7FF284FC3D240D12405FFC79F13E1BF4D099DCFD64F8B03EAD2EFDF25B1 |
| SSDEEP: | 6144:ynx1QXNVH6vrvaa6TYo+5WoEXVSUfQlgt8/P+lPccMOEb5h8MHgOMlrvaa6TYo+b:zX36vrMk5NcZQSt8YPfMO0h3srMk5NcY |
MALICIOUS
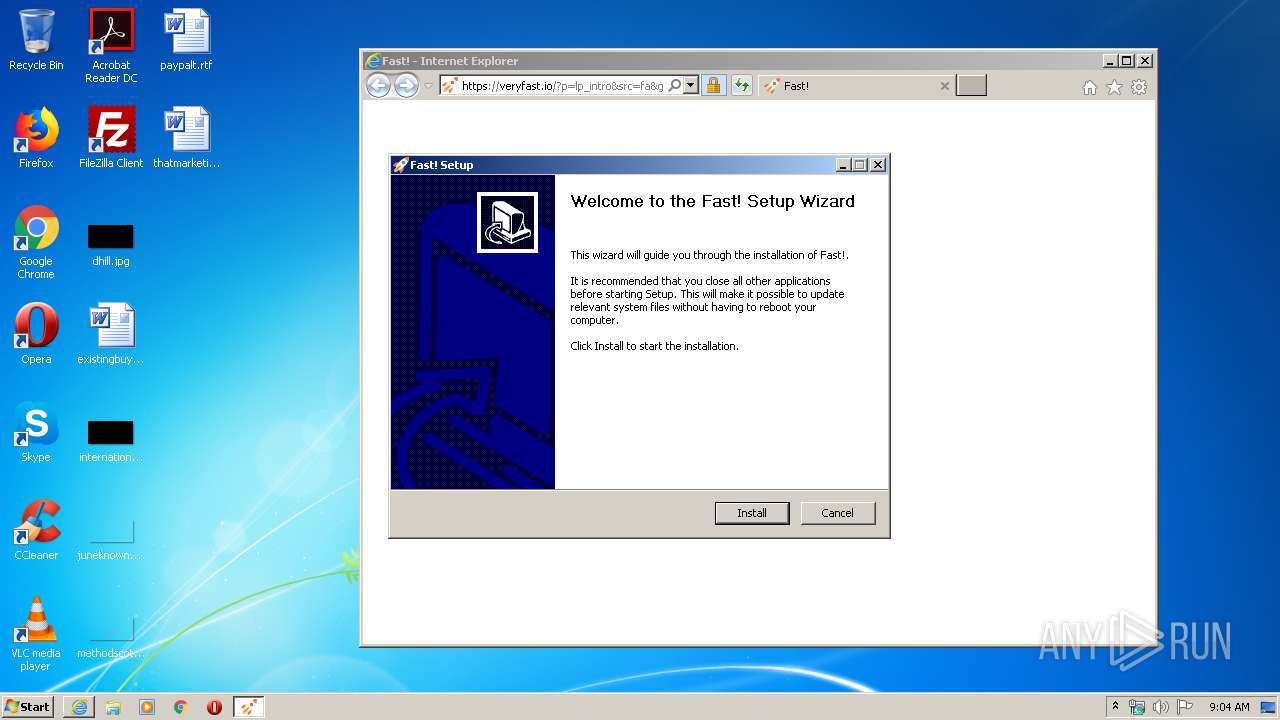
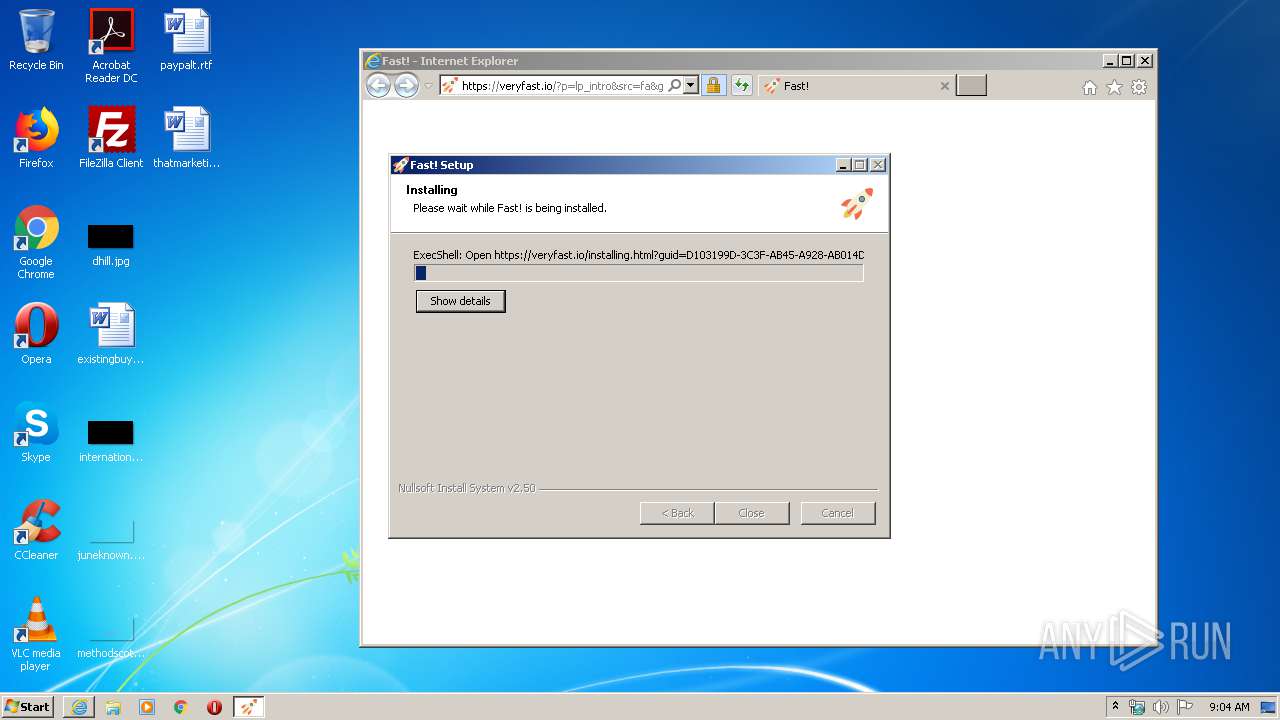
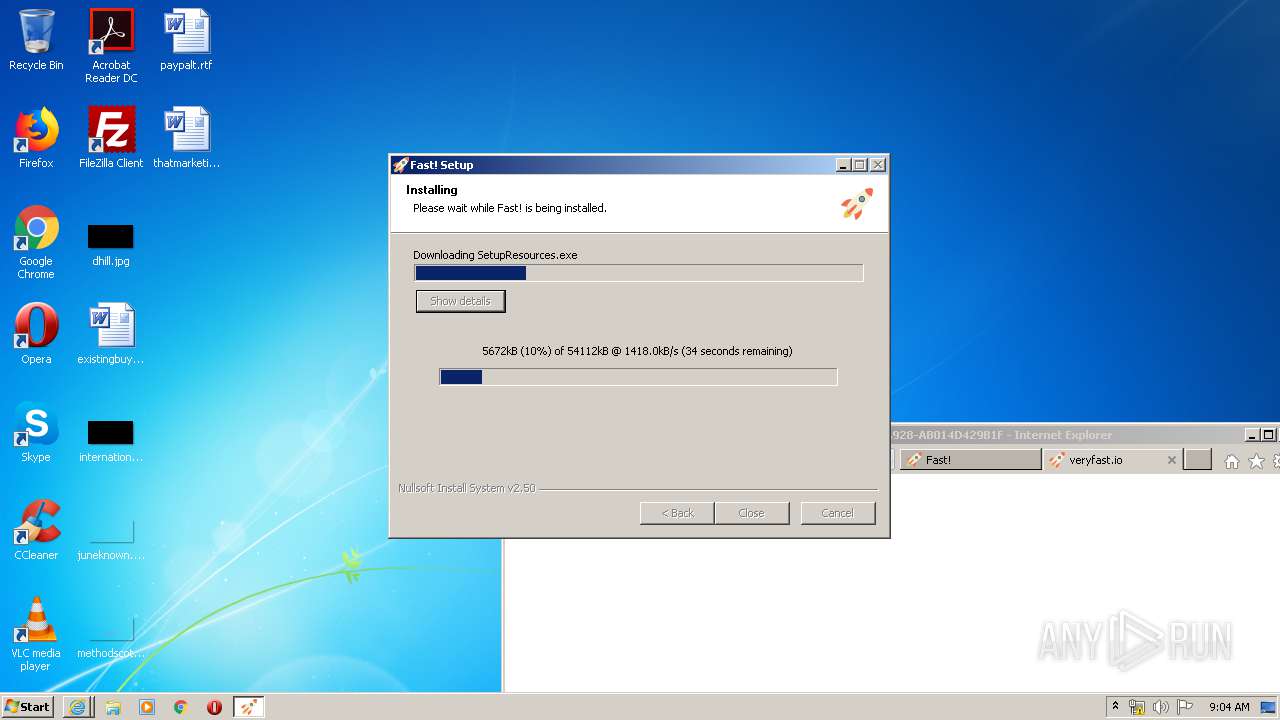
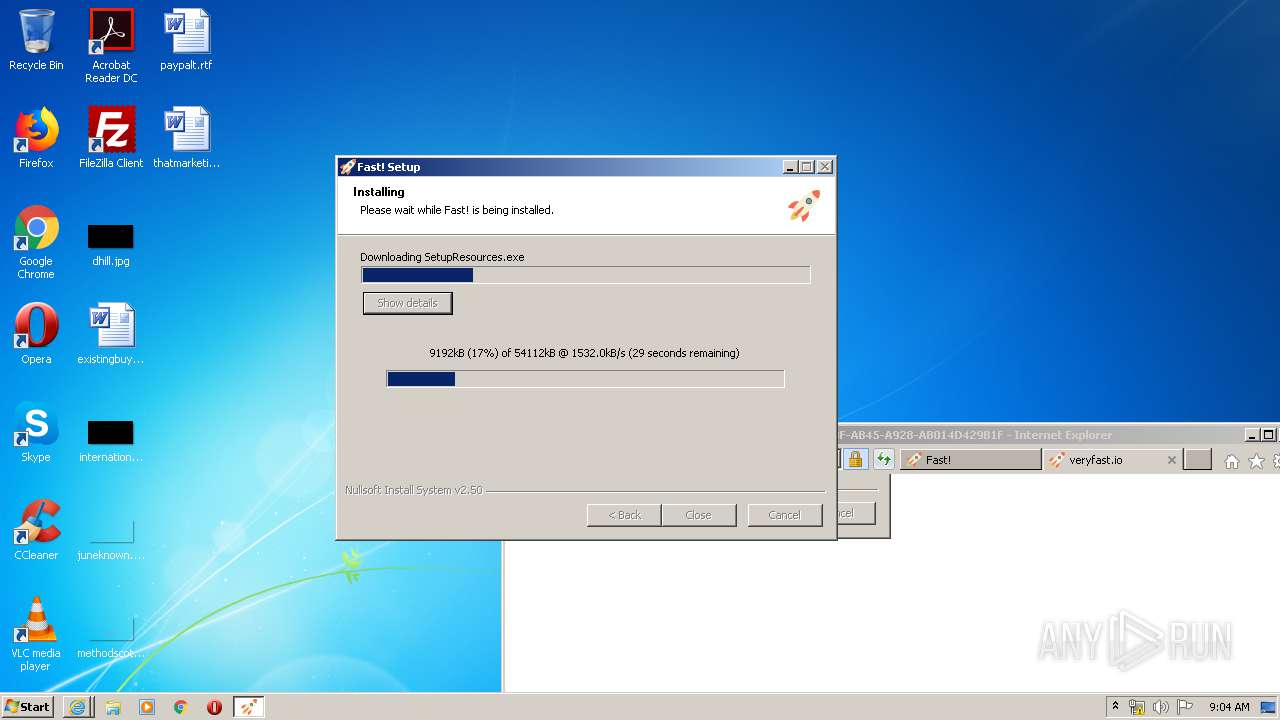
Loads dropped or rewritten executable
- SetupFA.exe (PID: 3612)
- Fast! Installer.exe (PID: 1884)
- SetupEngine.exe (PID: 272)
Changes the autorun value in the registry
- SetupFA.exe (PID: 3612)
Application was dropped or rewritten from another process
- fa_rss.exe (PID: 2572)
- Fast! Installer.exe (PID: 1204)
- Fast! Installer.exe (PID: 1884)
- ns39E0.tmp (PID: 2996)
- SetupEngine.exe (PID: 272)
- diskspd.exe (PID: 2100)
- FastSRV.exe (PID: 2756)
- fast!.exe (PID: 1392)
- Fast!.exe (PID: 3672)
Changes settings of System certificates
- Fast! Installer.exe (PID: 1884)
SUSPICIOUS
Reads Internet Cache Settings
- SetupFA.exe (PID: 3612)
- fa_rss.exe (PID: 2572)
- Fast! Installer.exe (PID: 1884)
- SetupEngine.exe (PID: 272)
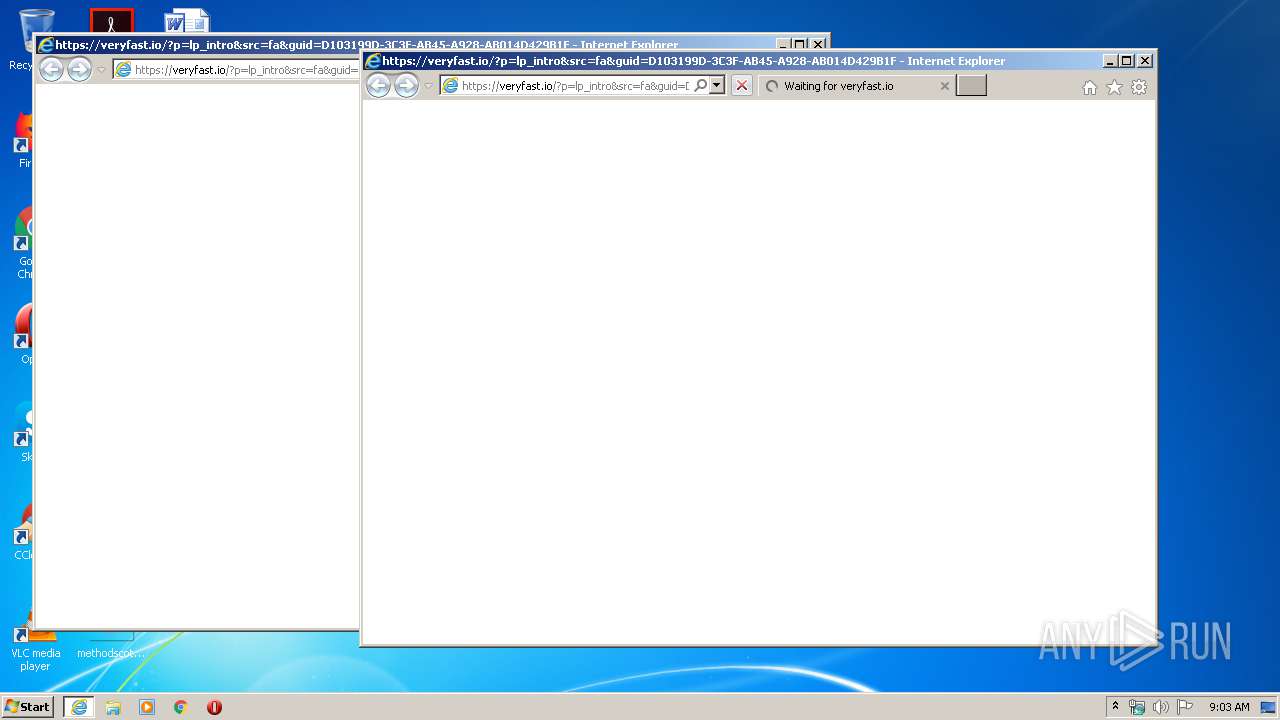
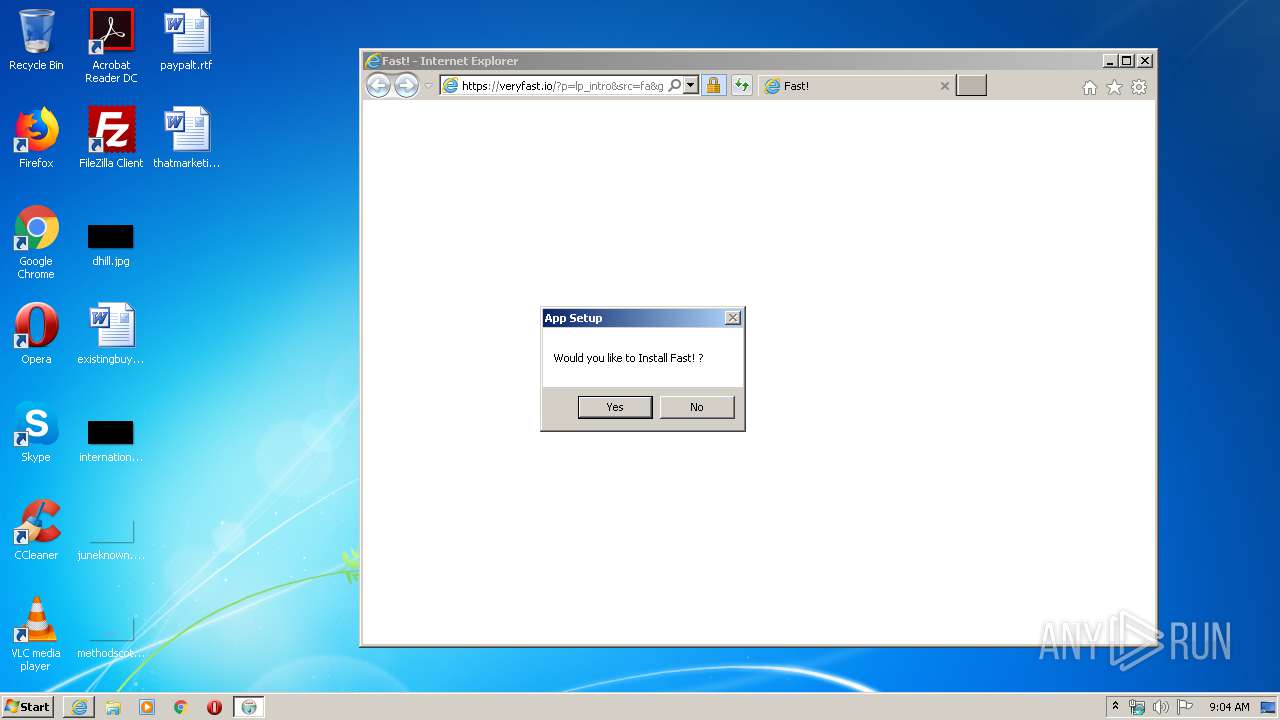
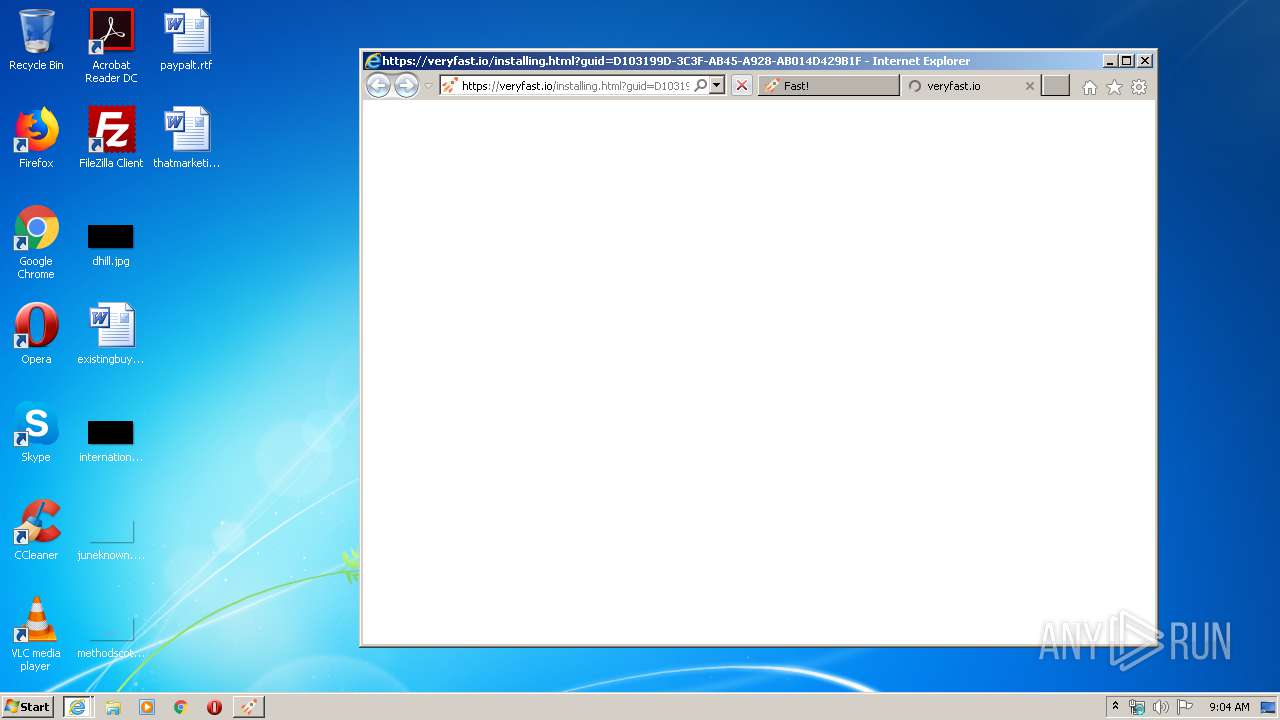
Starts Internet Explorer
- SetupFA.exe (PID: 3612)
Creates a software uninstall entry
- SetupFA.exe (PID: 3612)
- SetupEngine.exe (PID: 272)
Executable content was dropped or overwritten
- SetupFA.exe (PID: 3612)
- Fast! Installer.exe (PID: 1884)
- SetupResources.exe (PID: 3696)
- SetupEngine.exe (PID: 272)
Creates files in the user directory
- SetupFA.exe (PID: 3612)
- SetupEngine.exe (PID: 272)
Starts CMD.EXE for commands execution
- ns39E0.tmp (PID: 2996)
Starts application with an unusual extension
- SetupEngine.exe (PID: 272)
Creates files in the program directory
- SetupEngine.exe (PID: 272)
- SetupResources.exe (PID: 3696)
Executed as Windows Service
- FastSRV.exe (PID: 2756)
Adds / modifies Windows certificates
- Fast! Installer.exe (PID: 1884)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2444)
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 3992)
Creates files in the user directory
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 2444)
Reads internet explorer settings
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 4028)
Reads settings of System Certificates
- SetupFA.exe (PID: 3612)
- Fast! Installer.exe (PID: 1884)
- SetupEngine.exe (PID: 272)
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 2444)
- iexplore.exe (PID: 2480)
Changes internet zones settings
- iexplore.exe (PID: 2444)
Application launched itself
- iexplore.exe (PID: 2444)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2444)
Changes settings of System certificates
- iexplore.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:38:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x310d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2015 05:38:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2015 05:38:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E3C | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4323 |
.rdata | 0x00007000 | 0x0000126A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00589 |
.data | 0x00009000 | 0x00025D38 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29176 |
.ndata | 0x0002F000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x00004168 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.98531 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22347 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
59
Monitored processes
16
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Local\Temp\SetupEngine.exe" | C:\Users\admin\AppData\Local\Temp\SetupEngine.exe | Fast! Installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\AppData\Local\Temp\Fast! Installer.exe" | C:\Users\admin\AppData\Local\Temp\Fast! Installer.exe | — | SetupFA.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\fast!\fast!.exe" | C:\Program Files\fast!\fast!.exe | — | FastSRV.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1872 | cmd /c "C:\Users\admin\AppData\Local\Temp\diskspd.exe -c100M -b4K -t1 -r -o32 -d10 -ag -h -Rxml C:\Users\admin\AppData\Local\Temp\testfile.temp" > C:\Users\admin\AppData\Local\Temp\dskres.xml | C:\Windows\system32\cmd.exe | — | ns39E0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1884 | "C:\Users\admin\AppData\Local\Temp\Fast! Installer.exe" | C:\Users\admin\AppData\Local\Temp\Fast! Installer.exe | SetupFA.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2100 | C:\Users\admin\AppData\Local\Temp\diskspd.exe -c100M -b4K -t1 -r -o32 -d10 -ag -h -Rxml C:\Users\admin\AppData\Local\Temp\testfile.temp | C:\Users\admin\AppData\Local\Temp\diskspd.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Internet Explorer\iexplore.exe" https://veryfast.io/?p=lp_intro&src=fa&guid=D103199D-3C3F-AB45-A928-AB014D429B1F | C:\Program Files\Internet Explorer\iexplore.exe | SetupFA.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2444 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Roaming\FA\fa_rss.exe" /init default | C:\Users\admin\AppData\Roaming\FA\fa_rss.exe | SetupFA.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Fast!\FastSRV.exe" | C:\Program Files\Fast!\FastSRV.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
8 768
Read events
2 188
Write events
4 844
Delete events
1 736
Modification events
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3612) SetupFA.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
25
Suspicious files
59
Text files
69
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | SetupFA.exe | C:\Users\admin\AppData\Local\Temp\CabD899.tmp | — | |
MD5:— | SHA256:— | |||
| 3612 | SetupFA.exe | C:\Users\admin\AppData\Local\Temp\TarD89A.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFA67.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFA68.tmp | — | |
MD5:— | SHA256:— | |||
| 2444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3612 | SetupFA.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 3612 | SetupFA.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 3612 | SetupFA.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7EE68568A64252FD257717694104EA3E_851262BD44A7B3DEB4AA387001DAADC8 | binary | |
MD5:— | SHA256:— | |||
| 3612 | SetupFA.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
67
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3612 | SetupFA.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3612 | SetupFA.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2480 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3612 | SetupFA.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCstTtBUz6Jww%3D%3D | US | der | 1.74 Kb | whitelisted |
2480 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDmAVio3Q%2FBtwgAAAAAPr2V | US | der | 472 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDEKiK1zGWeAwgAAAAAPr4Q | US | der | 472 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDvkDzv2QYa2AgAAAABnMwk%3D | US | der | 471 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCOh6fBrF41tAgAAAAAPr4g | US | der | 472 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDmAVio3Q%2FBtwgAAAAAPr2V | US | der | 472 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3612 | SetupFA.exe | 34.195.48.210:443 | veryfast.io | Amazon.com, Inc. | US | suspicious |
3612 | SetupFA.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2480 | iexplore.exe | 34.195.48.210:443 | veryfast.io | Amazon.com, Inc. | US | suspicious |
2444 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2480 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2480 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2480 | iexplore.exe | 104.22.25.131:443 | embed.tawk.to | Cloudflare Inc | US | unknown |
2480 | iexplore.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
2480 | iexplore.exe | 172.217.18.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2480 | iexplore.exe | 172.217.18.3:443 | www.google.ch | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
veryfast.io |
| malicious |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
d1uyoz7mfvzv4e.cloudfront.net |
| whitelisted |
embed.tawk.to |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |