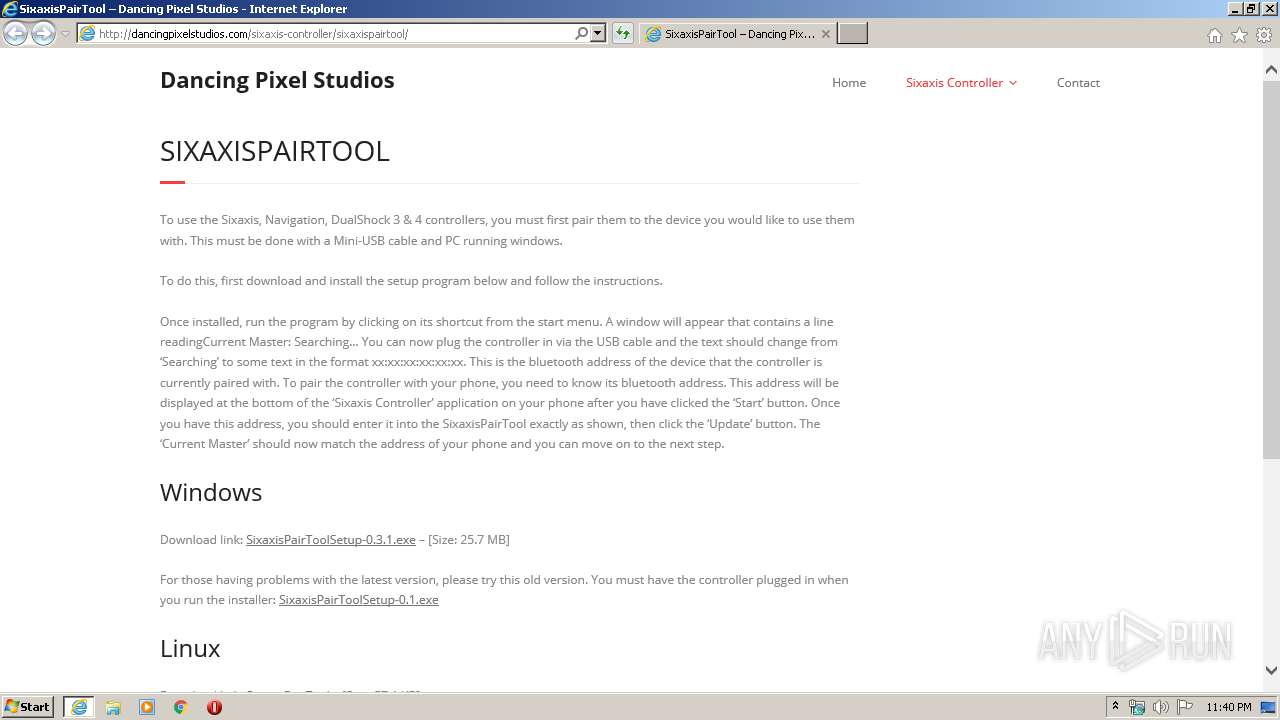
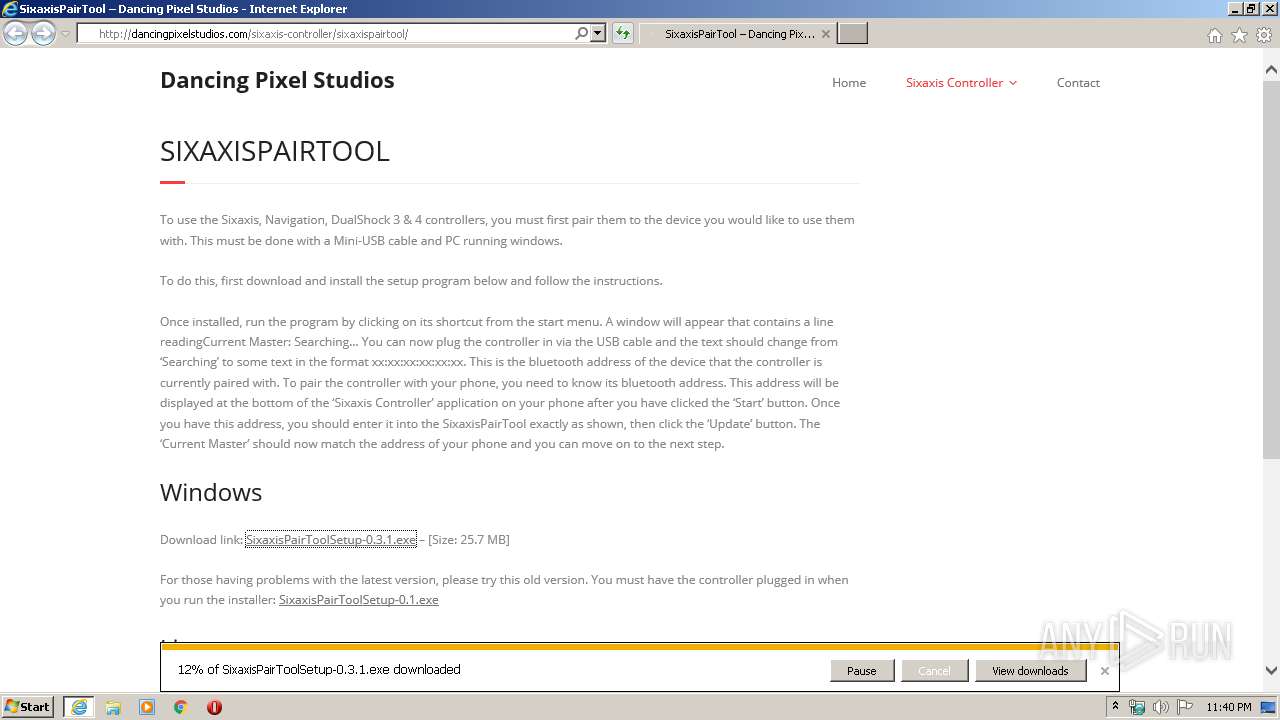
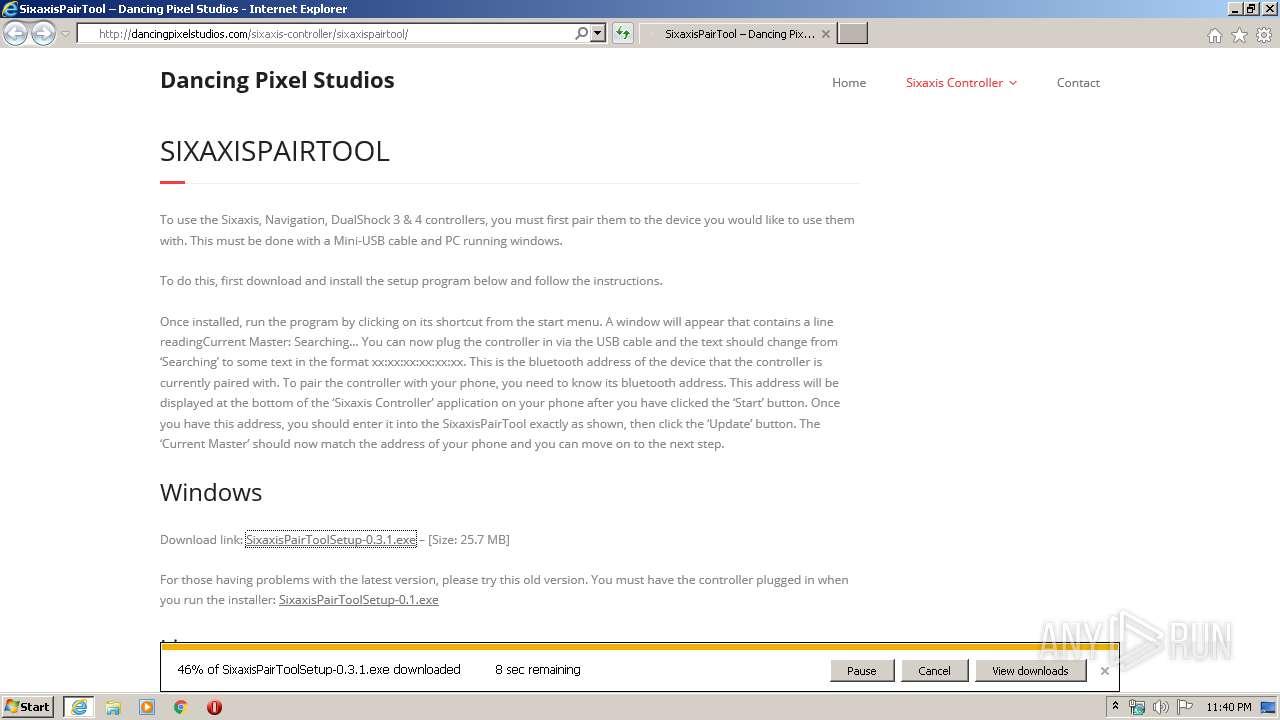
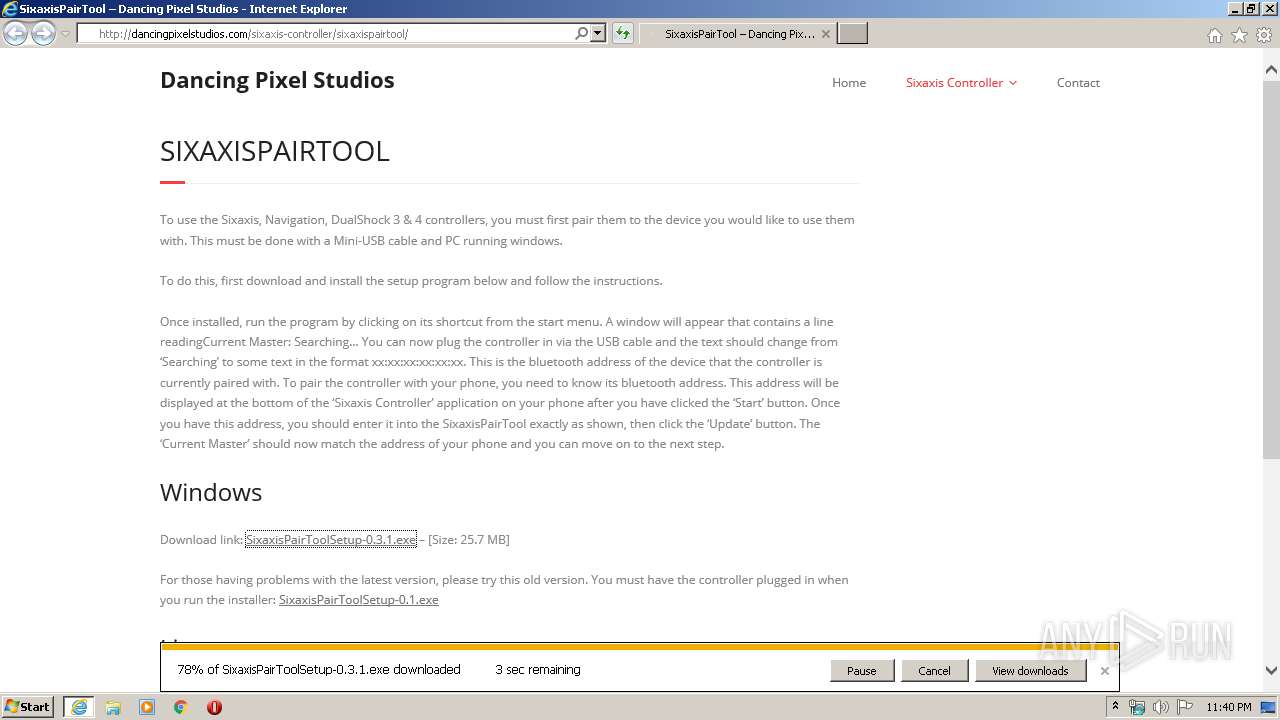
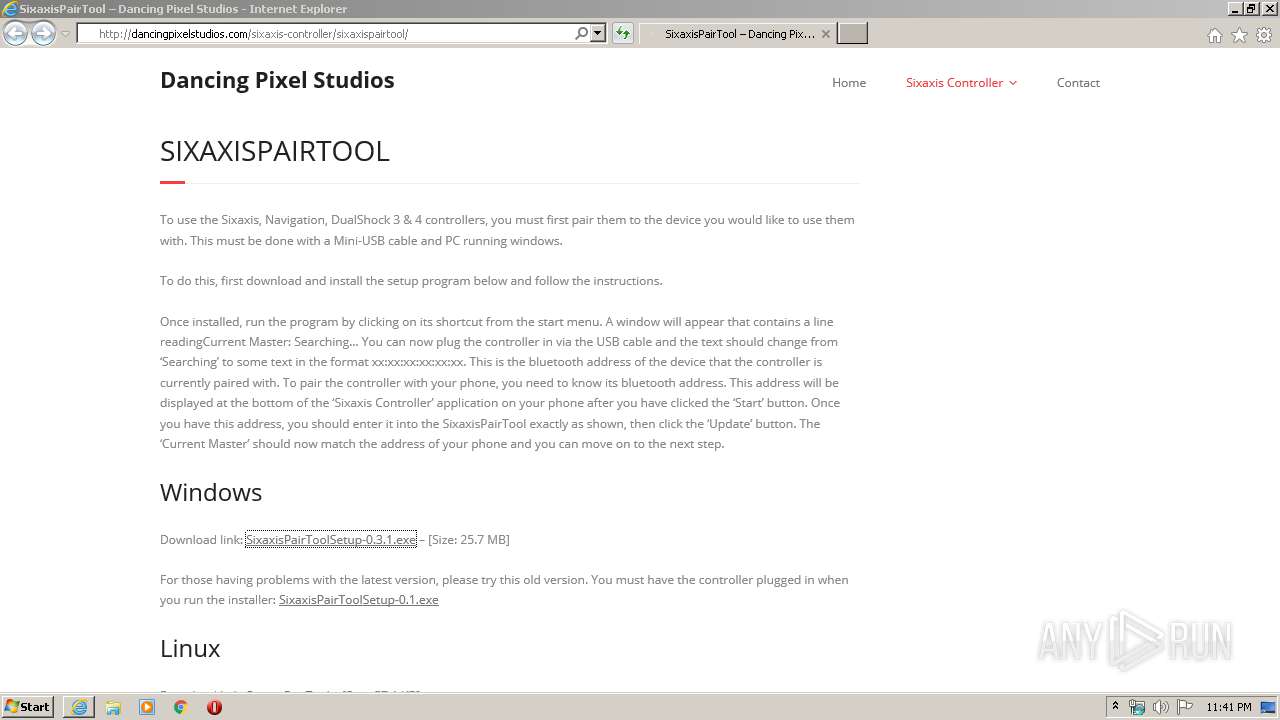
| URL: | http://dancingpixelstudios.com/sixaxis-controller/sixaxispairtool/ |
| Full analysis: | https://app.any.run/tasks/fd0d6437-95d0-4f27-949f-4a485a124c91 |
| Verdict: | No threats detected |
| Analysis date: | March 31, 2020, 22:40:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2B1CC55DE07D74531E8FEB2103D7EFD8 |
| SHA1: | 2F3A1179869D4A801EB94ECA312228D94775E5C8 |
| SHA256: | 3F4B5F71A854AD384F73A9658F621284BCF9BFD308542C13D60642A606F9183C |
| SSDEEP: | 3:N1KaELvC7YRQBMKHBMd0YfagysK5:CaMC7YRQBMGc0hN |
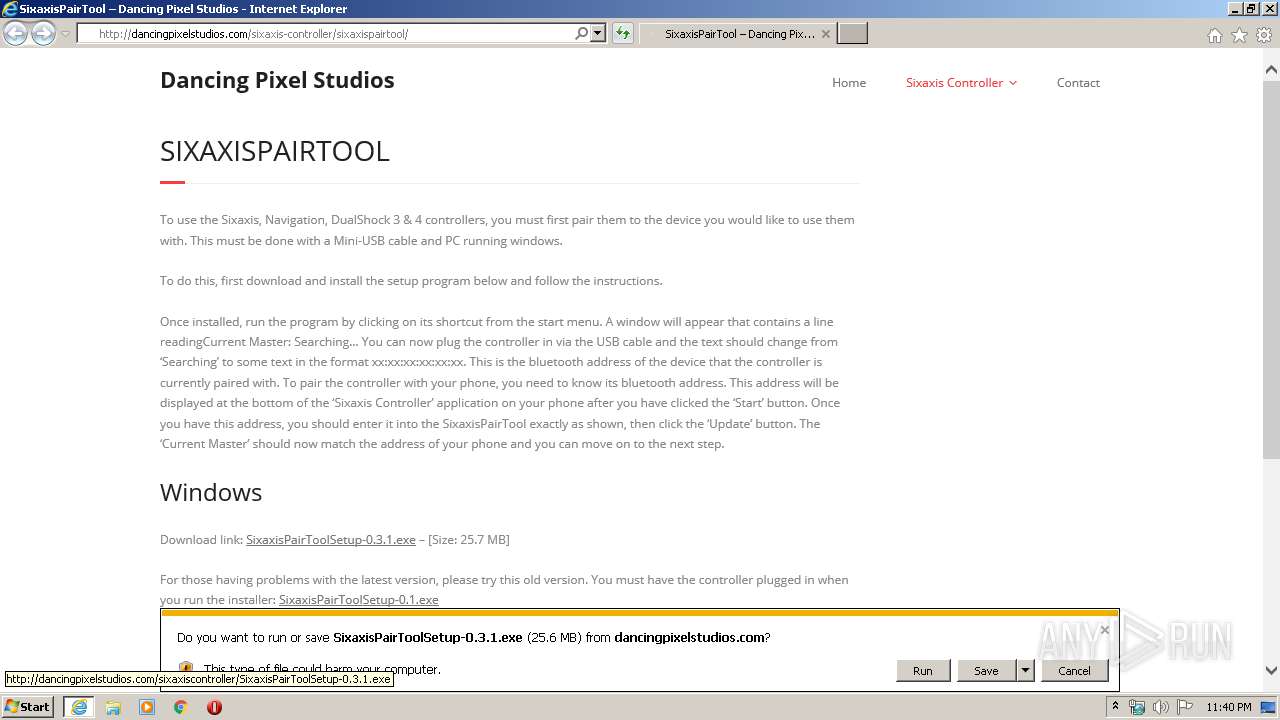
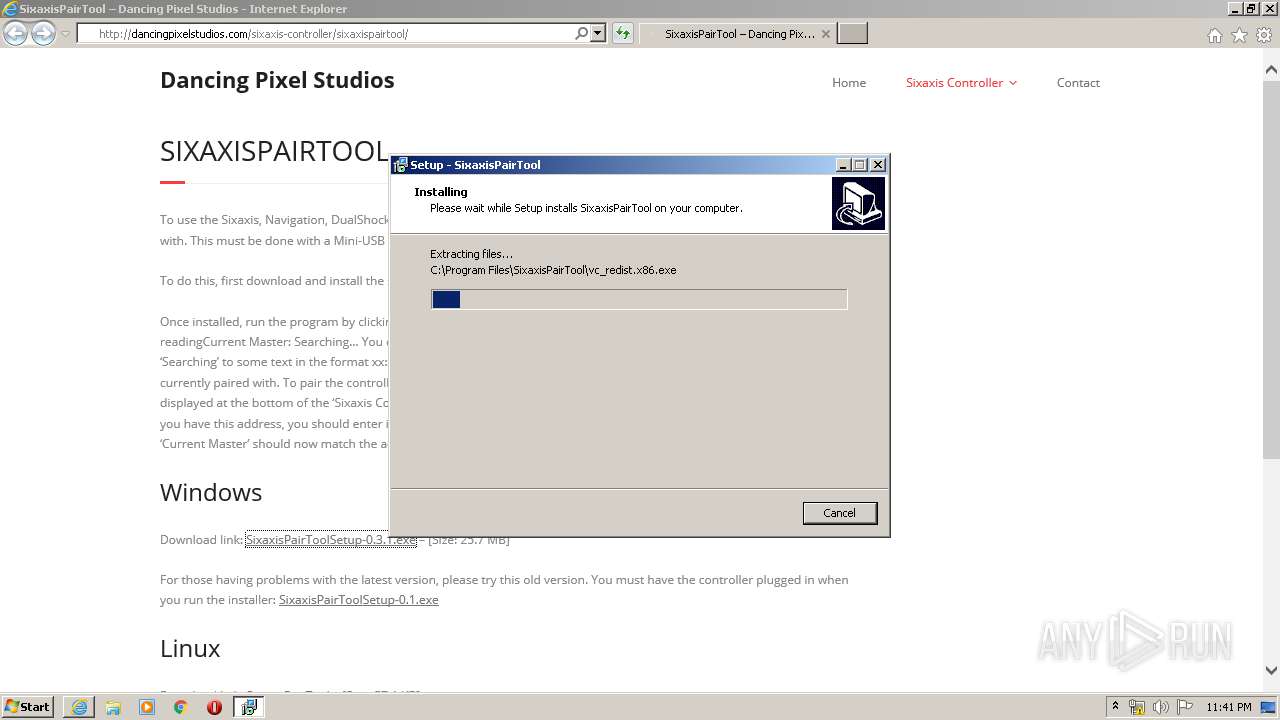
MALICIOUS
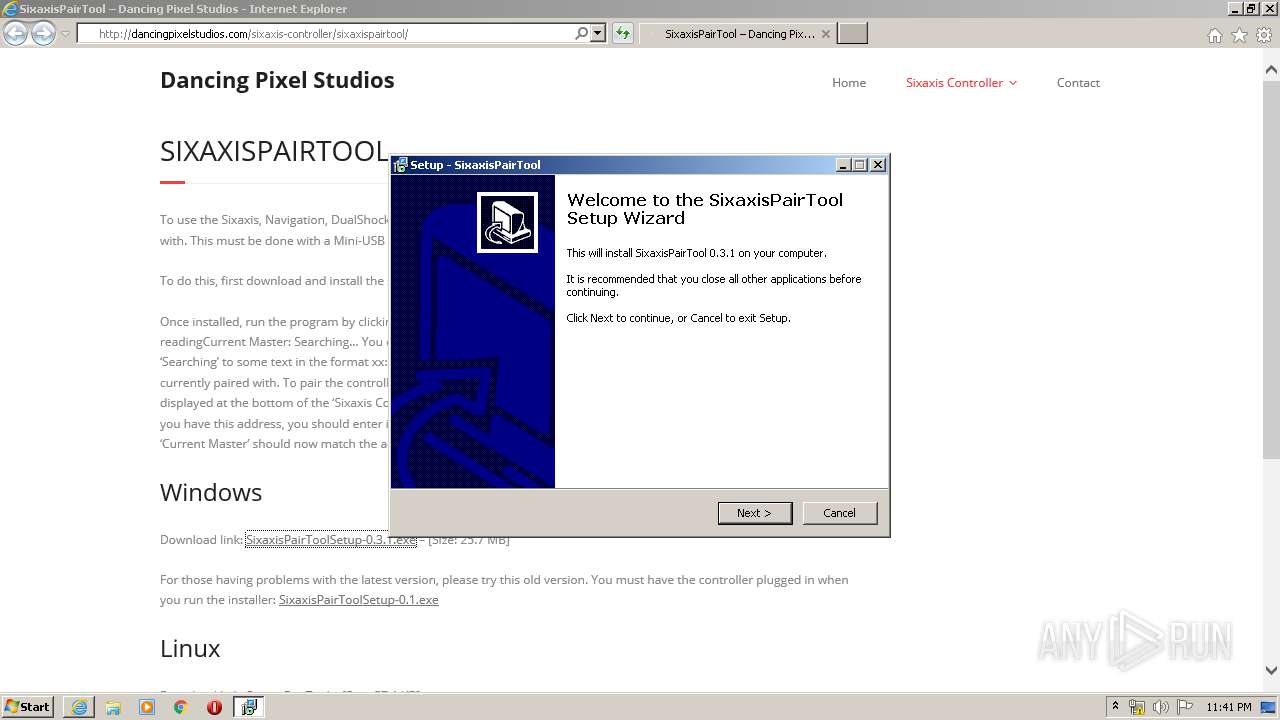
Application was dropped or rewritten from another process
- SixaxisPairToolSetup-0.3.1.exe (PID: 3468)
- SixaxisPairToolSetup-0.3.1.exe (PID: 3312)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 3512)
- SixaxisPairToolSetup-0.3.1.exe (PID: 3468)
- SixaxisPairToolSetup-0.3.1.exe (PID: 3312)
- SixaxisPairToolSetup-0.3.1.tmp (PID: 3100)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3512)
- iexplore.exe (PID: 3968)
Changes internet zones settings
- iexplore.exe (PID: 3512)
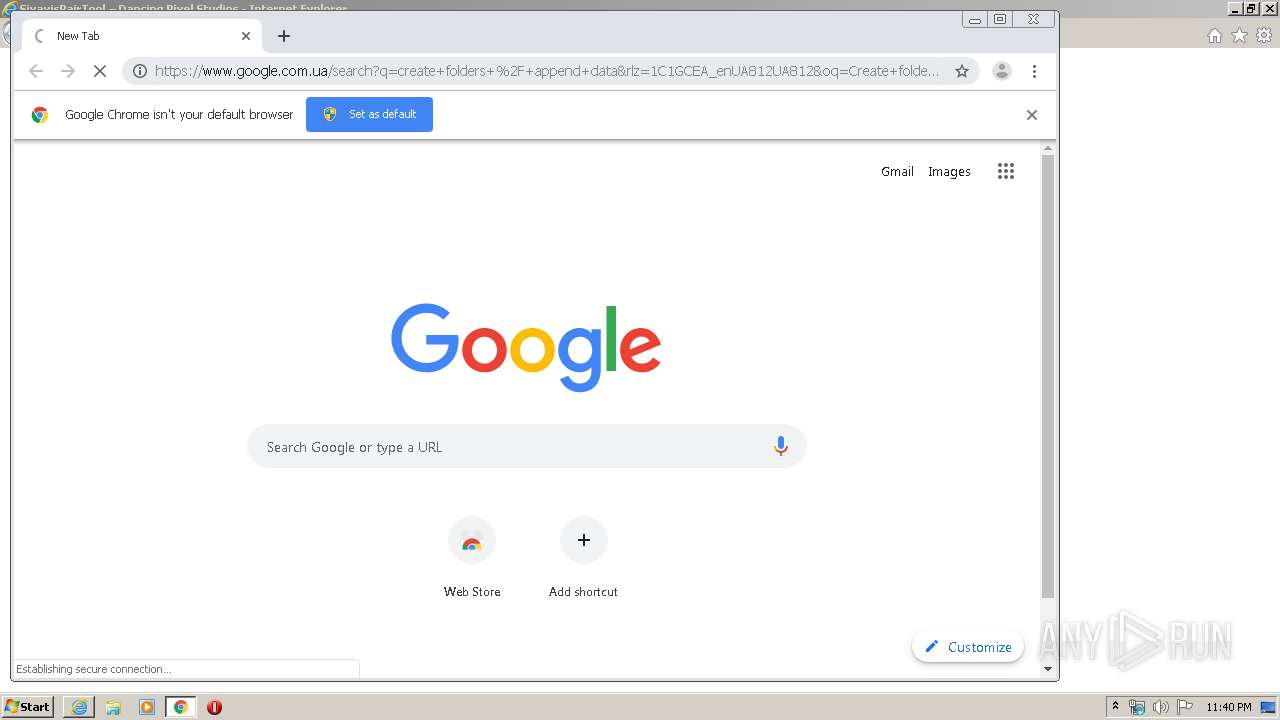
Manual execution by user
- chrome.exe (PID: 312)
Reads the hosts file
- chrome.exe (PID: 312)
- chrome.exe (PID: 2132)
Application launched itself
- chrome.exe (PID: 312)
Reads internet explorer settings
- iexplore.exe (PID: 3968)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3512)
Application was dropped or rewritten from another process
- SixaxisPairToolSetup-0.3.1.tmp (PID: 3636)
- SixaxisPairToolSetup-0.3.1.tmp (PID: 3100)
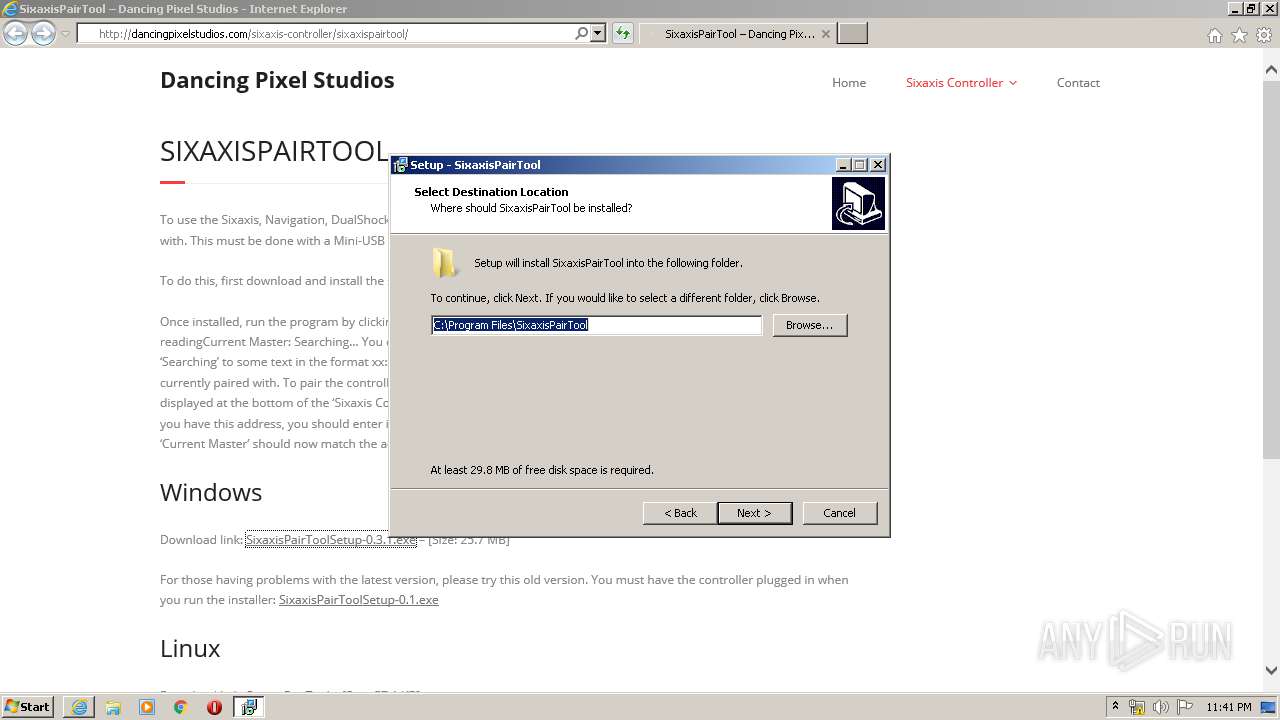
Creates files in the program directory
- SixaxisPairToolSetup-0.3.1.tmp (PID: 3100)
Loads dropped or rewritten executable
- SixaxisPairToolSetup-0.3.1.tmp (PID: 3100)
Reads settings of System Certificates
- iexplore.exe (PID: 3512)
- chrome.exe (PID: 2132)
Changes settings of System certificates
- iexplore.exe (PID: 3512)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10595506455028956137 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3313666446010284543 --mojo-platform-channel-handle=3392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5789816476517217407 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6682799049023278790 --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4626725266332327238 --mojo-platform-channel-handle=3300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\is-PIL3U.tmp\SixaxisPairToolSetup-0.3.1.tmp" /SL5="$D01D8,26672273,56832,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\SixaxisPairToolSetup-0.3.1.exe" /SPAWNWND=$14025A /NOTIFYWND=$150196 | C:\Users\admin\AppData\Local\Temp\is-PIL3U.tmp\SixaxisPairToolSetup-0.3.1.tmp | SixaxisPairToolSetup-0.3.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13237187642944644230,2624228517805137663,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12944649287753544189 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\SixaxisPairToolSetup-0.3.1.exe" /SPAWNWND=$14025A /NOTIFYWND=$150196 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\SixaxisPairToolSetup-0.3.1.exe | SixaxisPairToolSetup-0.3.1.tmp | ||||||||||||
User: admin Company: Dancing Pixel Studios Integrity Level: HIGH Description: SixaxisPairTool Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
7 251
Read events
2 062
Write events
3 490
Delete events
1 699
Modification events
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1794178790 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803885 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3512) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
7
Suspicious files
31
Text files
92
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\sixaxispairtool[1].htm | html | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\thinkup-right-sidebar[1].css | text | |
MD5:— | SHA256:— | |||
| 3512 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style-shortcodes[1].css | text | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\bootstrap.min[1].css | text | |
MD5:90CB1507C3AF20339F9E8F06F7DE96D8 | SHA256:2B25DE735BA1557E9E694BC2301897F1B7A8EEAF49B503E8E8D52E3A52F6A800 | |||
| 312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E83C6DC-138.pma | — | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\front[1].css | text | |
MD5:6318148A3048681AB6BE927A2DAE7C21 | SHA256:3CDE7327C67A2BDE4B077CE381CDA87E1CDBC5B0E7EAB38F7C4AB06078F97ED5 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery[1].js | text | |
MD5:207ABEB83412721D556FAEBA36E00822 | SHA256:CA32702F36DA9BDBAA5463F8E3DB9B18D82F3CE8A630D18E8BDE6B30A2582D20 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\wp-emoji-release.min[1].js | text | |
MD5:B22CA0BB06142D867F03BD0D89642997 | SHA256:40F0F2B6FB558157E1F065445B213802AAE1D65E46CF436098844F0347CAFB46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
33
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/sixaxis-controller/sixaxispairtool/ | US | html | 4.63 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/styles/style-shortcodes.css?ver=1.1 | US | text | 10.9 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/style.css?ver=1.3.6 | US | text | 16.6 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/styles/layouts/thinkup-right-sidebar.css?ver=1.1 | US | text | 157 b | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/lib/extentions/font-awesome/css/font-awesome.min.css?ver=4.2.0 | US | text | 4.95 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-includes/js/jquery/jquery.js?ver=1.11.3 | US | text | 41.4 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-includes/js/wp-emoji-release.min.js?ver=4.4.18 | US | text | 7.07 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/lib/extentions/prettyPhoto/js/jquery.prettyPhoto.js?ver=3.1.6 | US | html | 11.8 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-content/themes/minamaze/styles/style-responsive.css?ver=1.1 | US | text | 2.44 Kb | malicious |
3968 | iexplore.exe | GET | 200 | 74.220.219.222:80 | http://dancingpixelstudios.com/wordpress/wp-includes/js/jquery/jquery-migrate.min.js?ver=1.2.1 | US | text | 3.19 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | iexplore.exe | 74.220.219.222:80 | dancingpixelstudios.com | Unified Layer | US | malicious |
3968 | iexplore.exe | 172.217.18.170:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3512 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
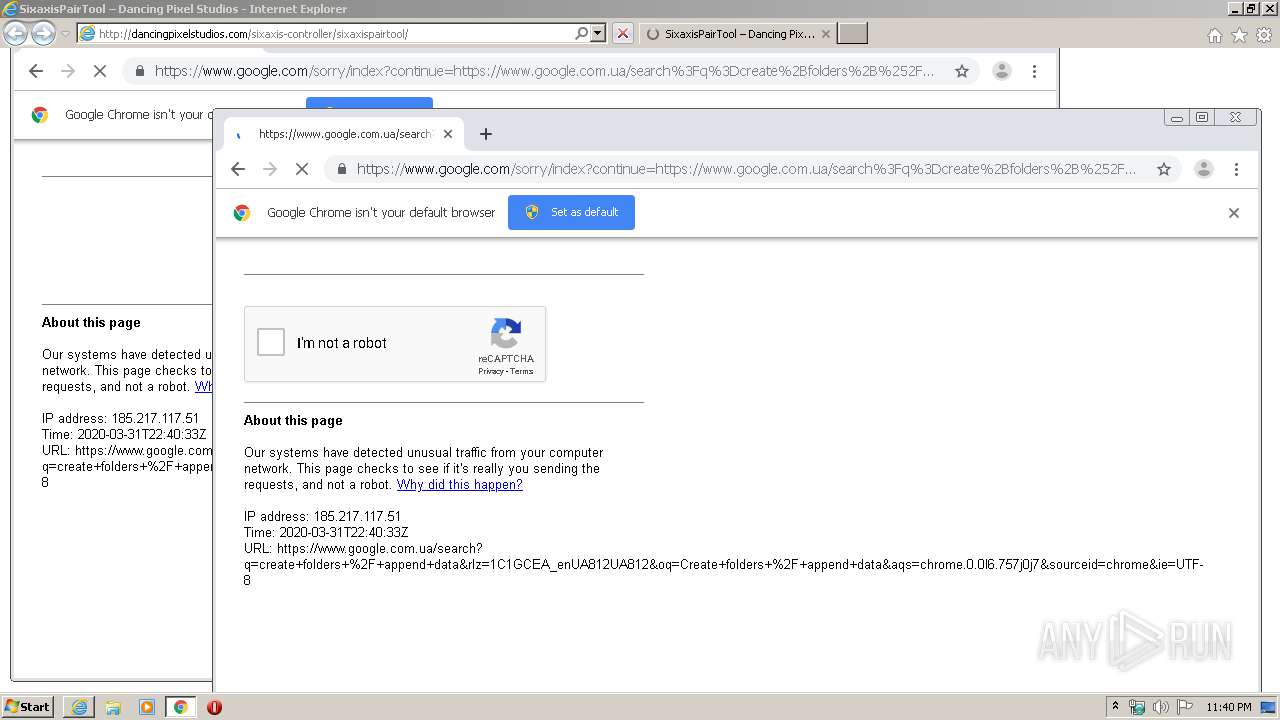
2132 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2132 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3968 | iexplore.exe | 172.217.18.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3512 | iexplore.exe | 74.220.219.222:80 | dancingpixelstudios.com | Unified Layer | US | malicious |
3512 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3512 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dancingpixelstudios.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |