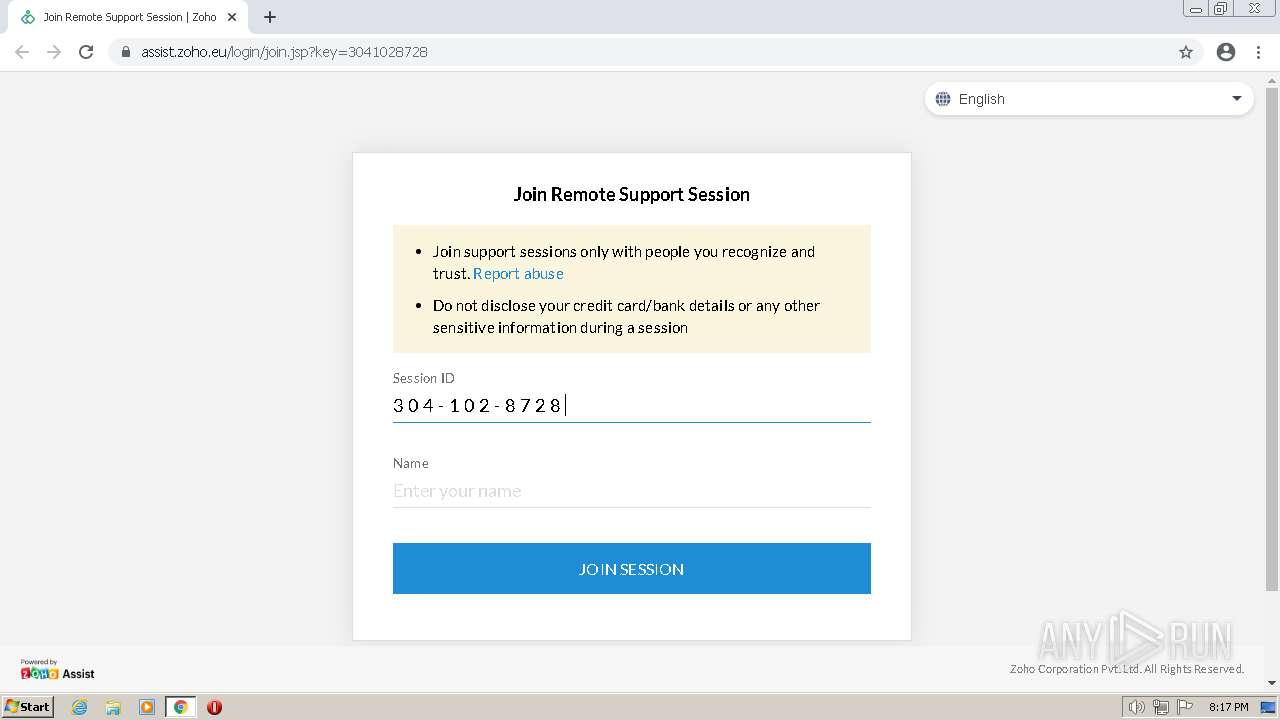
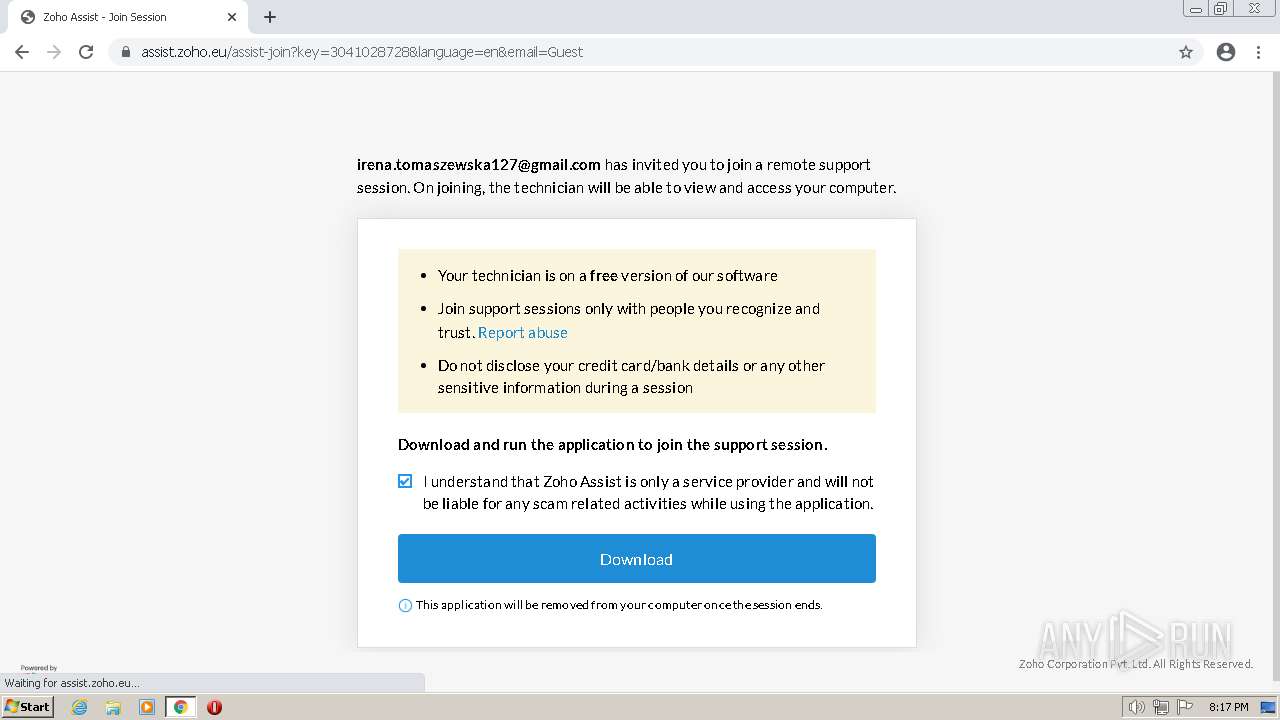
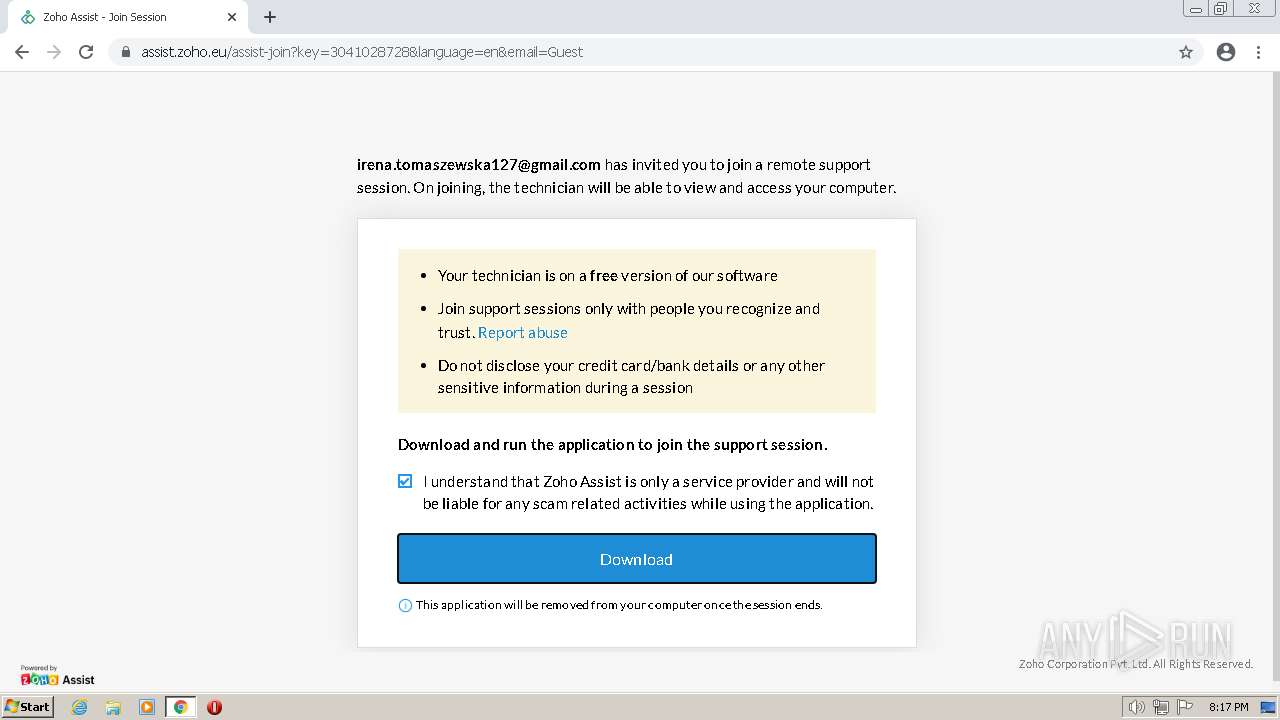
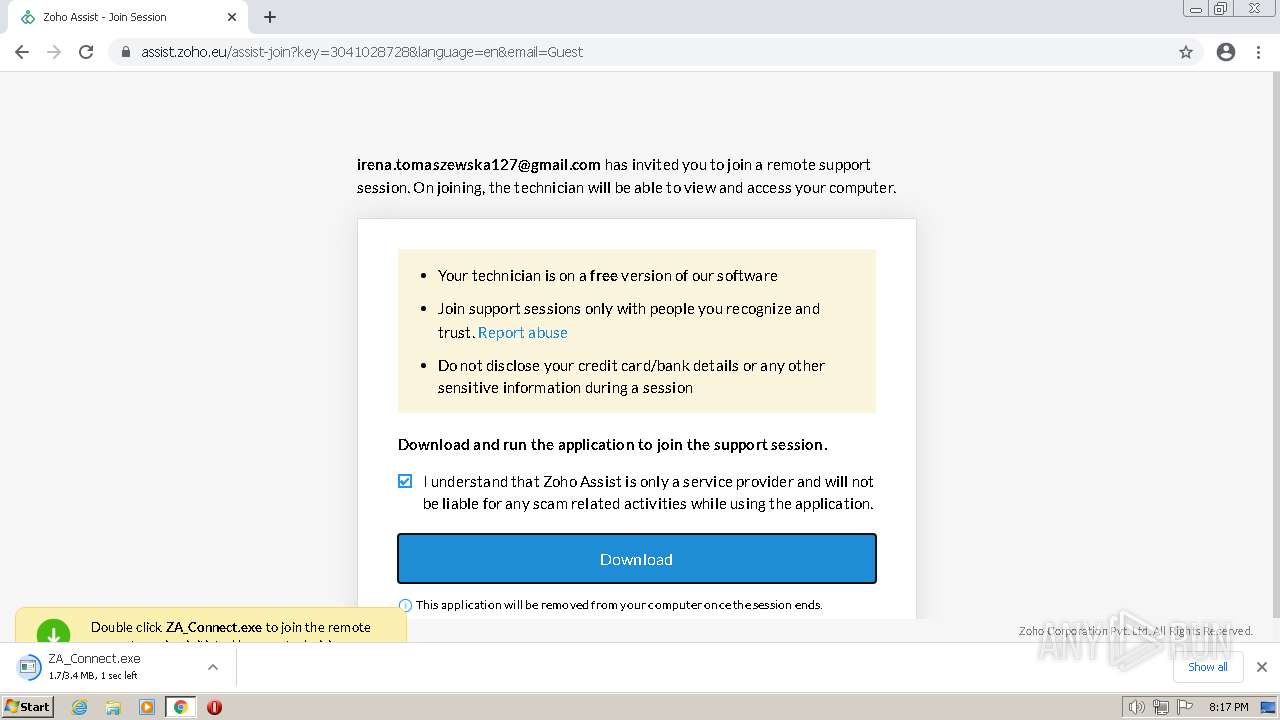
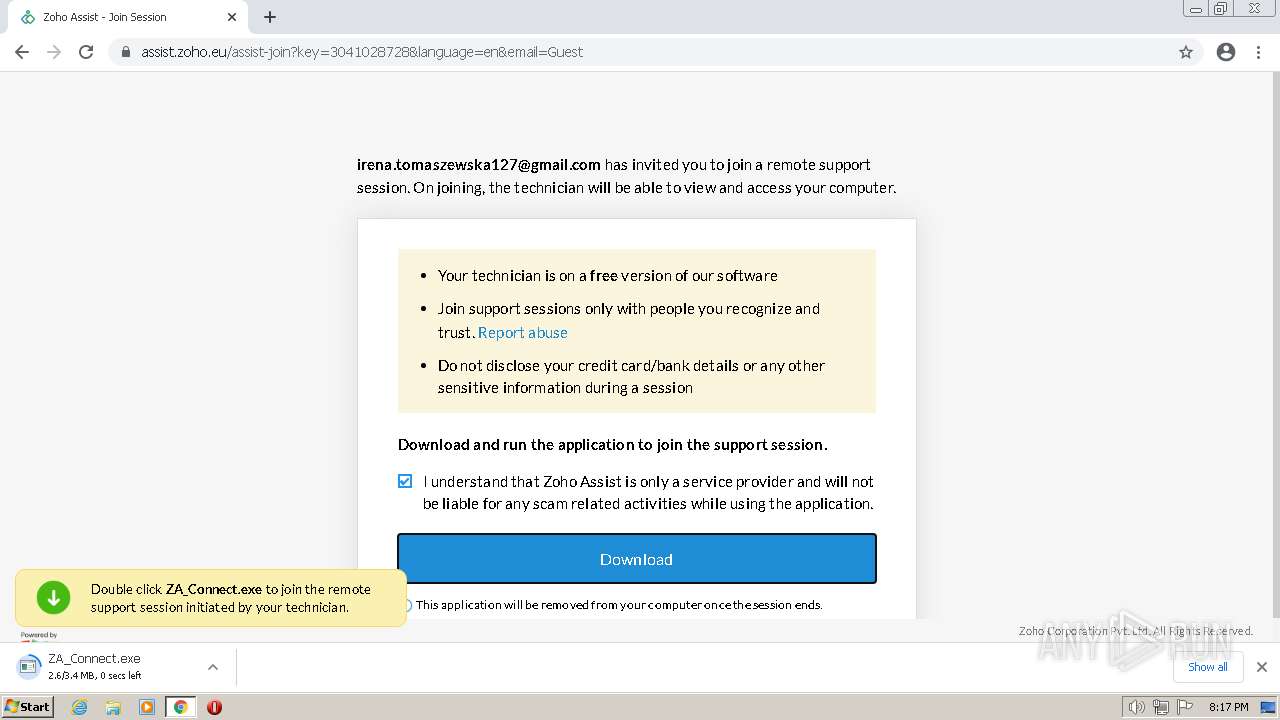
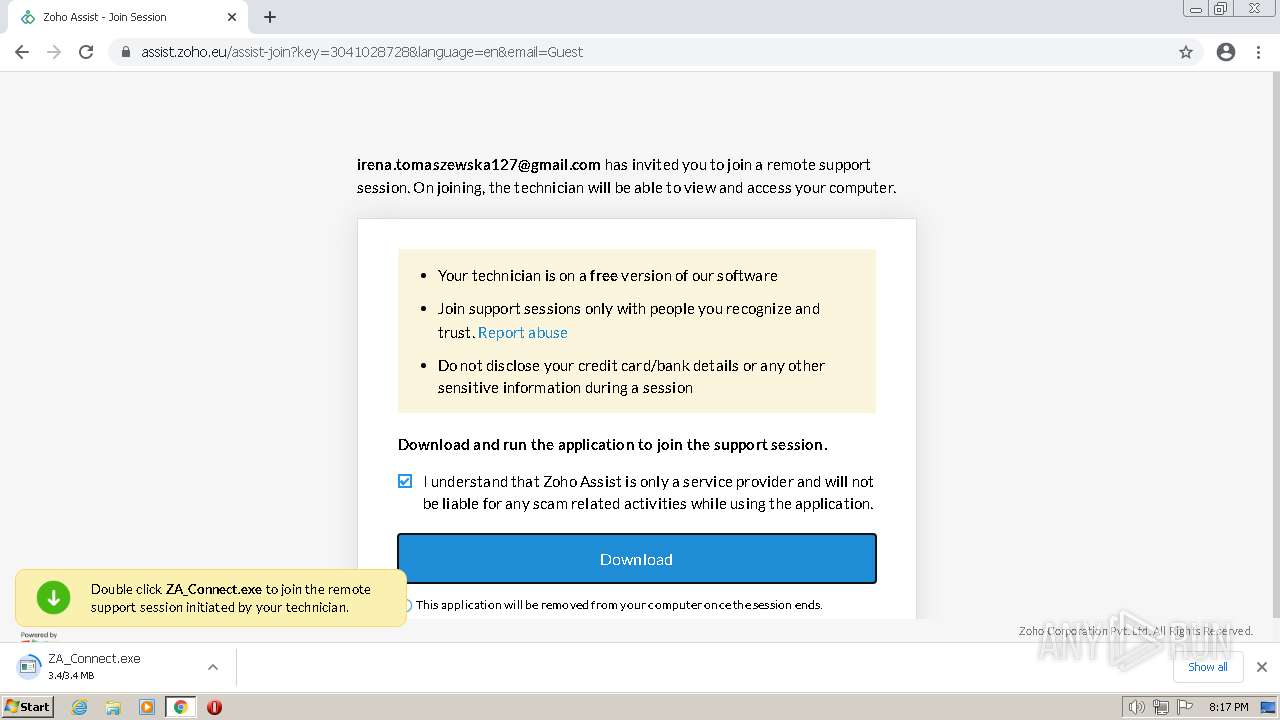
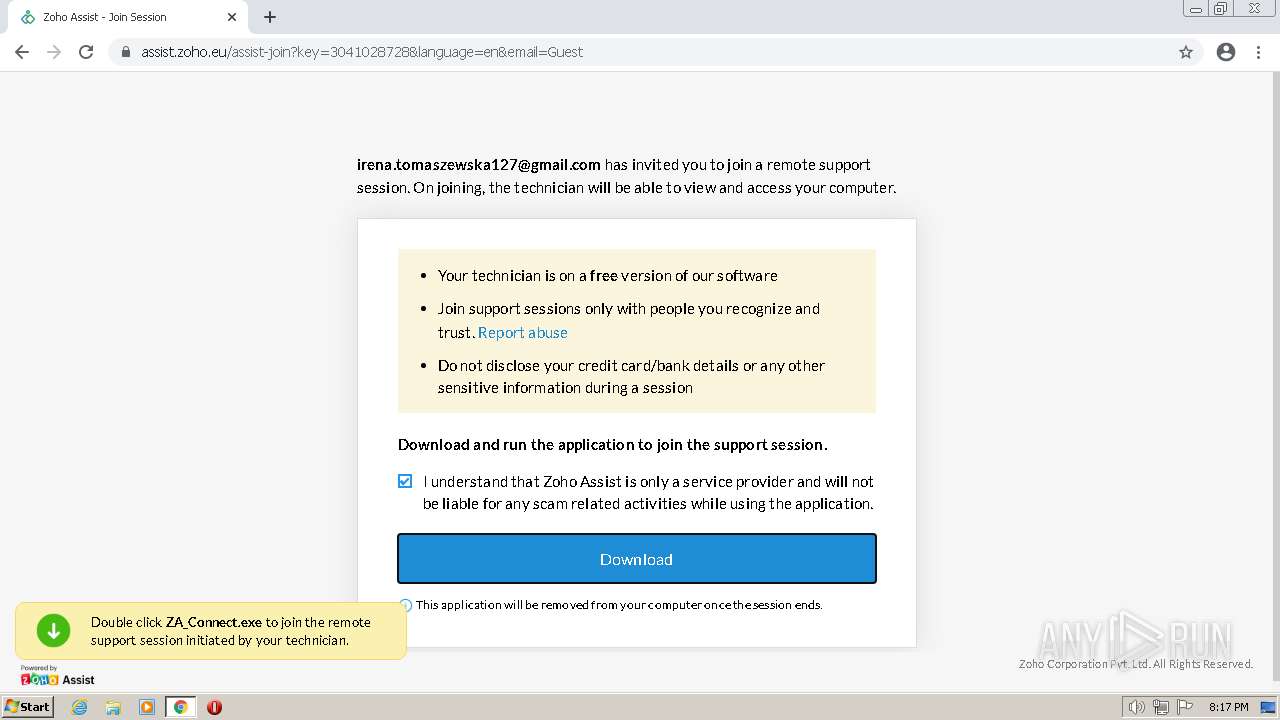
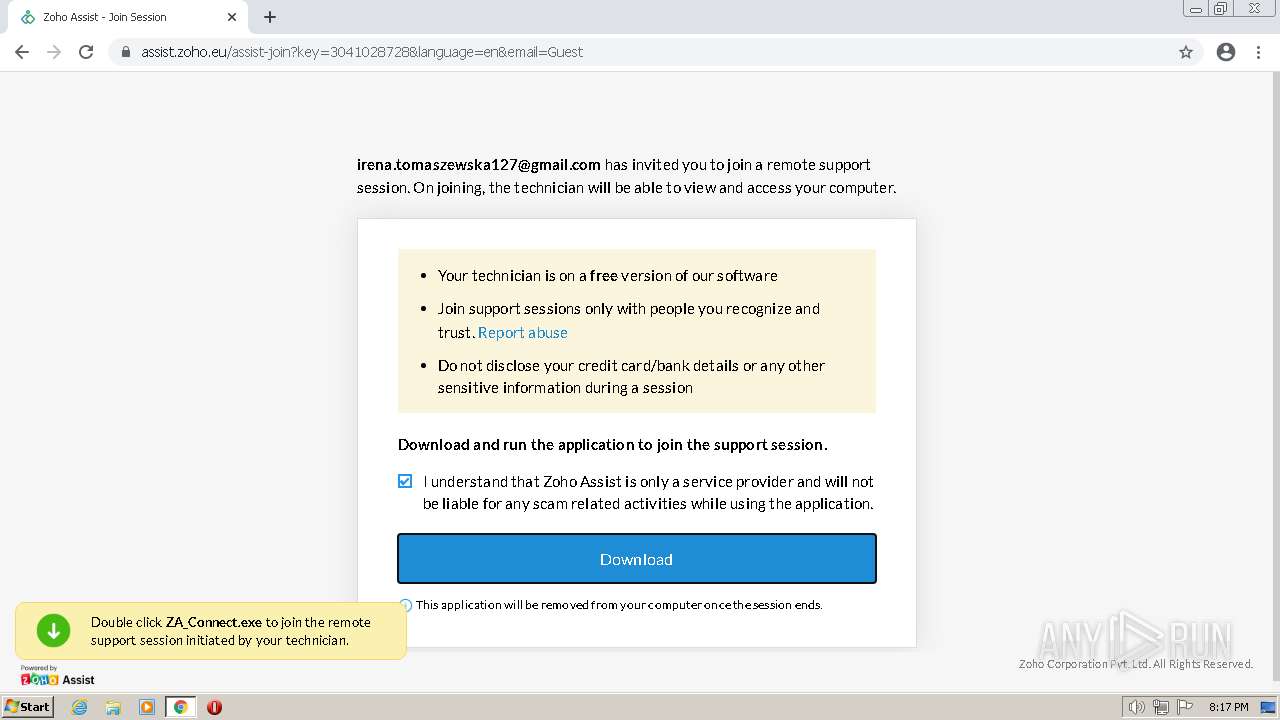
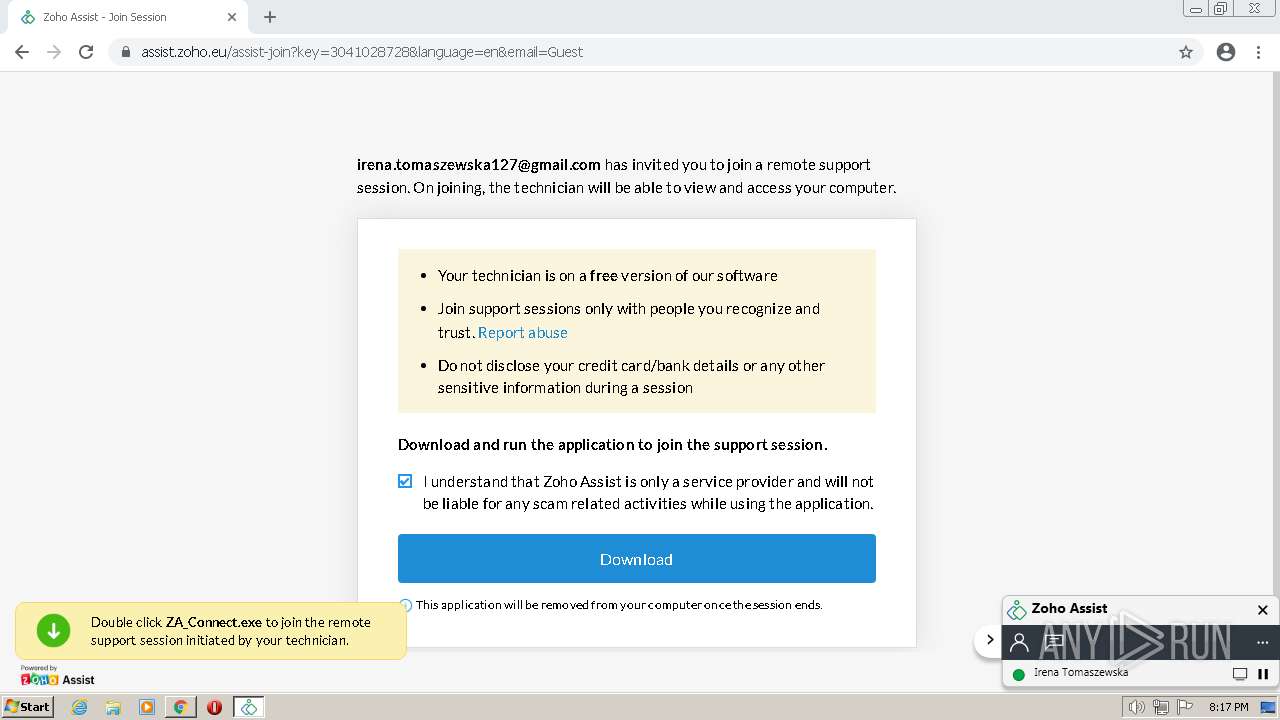
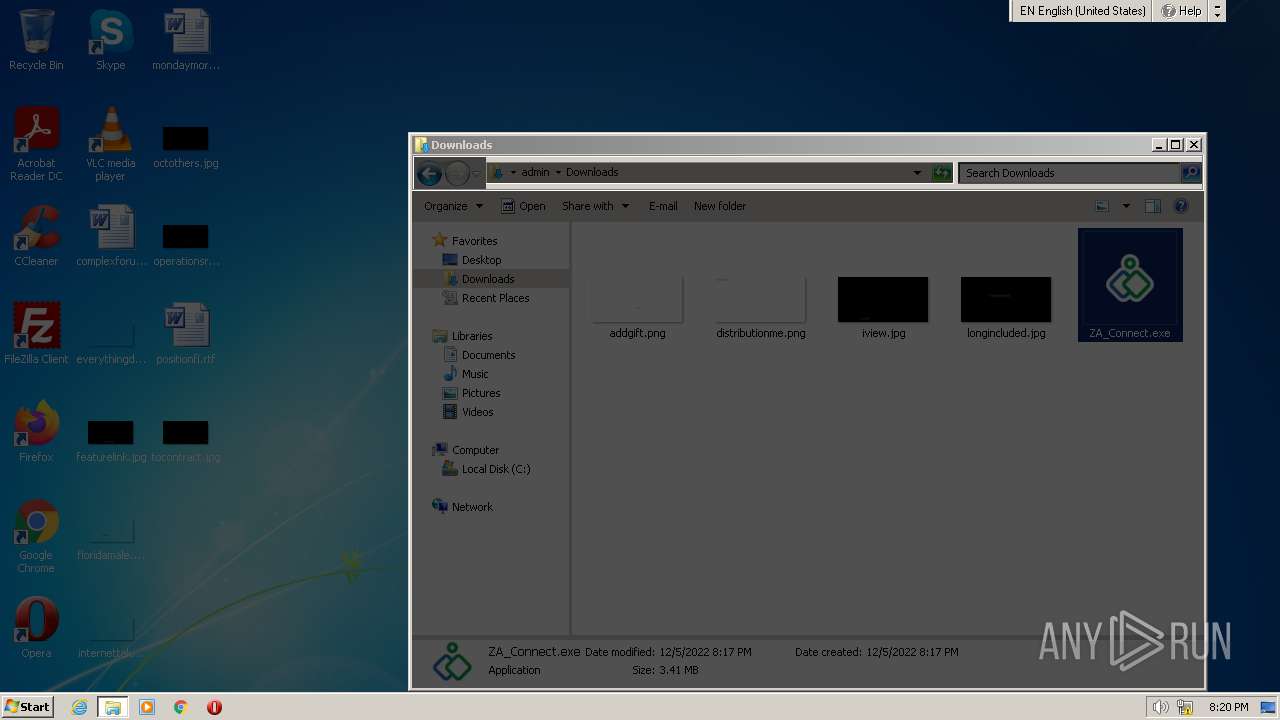
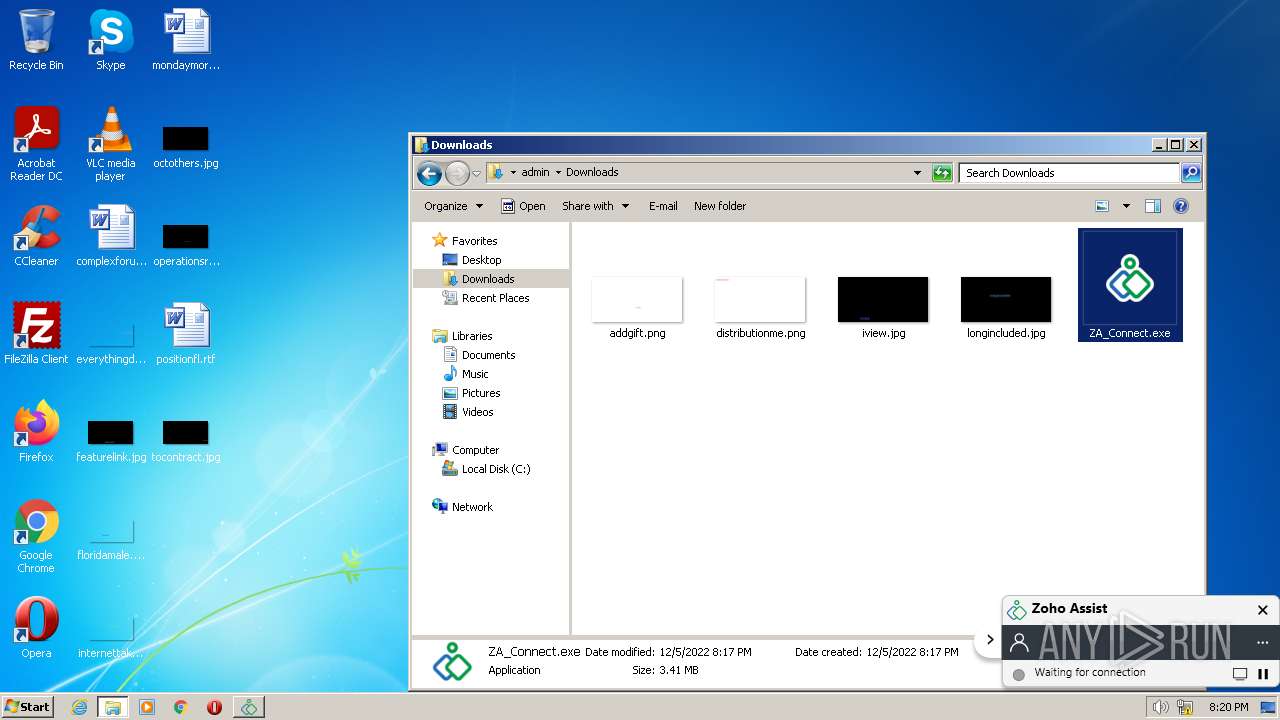
| URL: | https://join.zoho.eu/3041028728 |
| Full analysis: | https://app.any.run/tasks/afb9567d-f4e0-4cc8-9d95-759de8c7b886 |
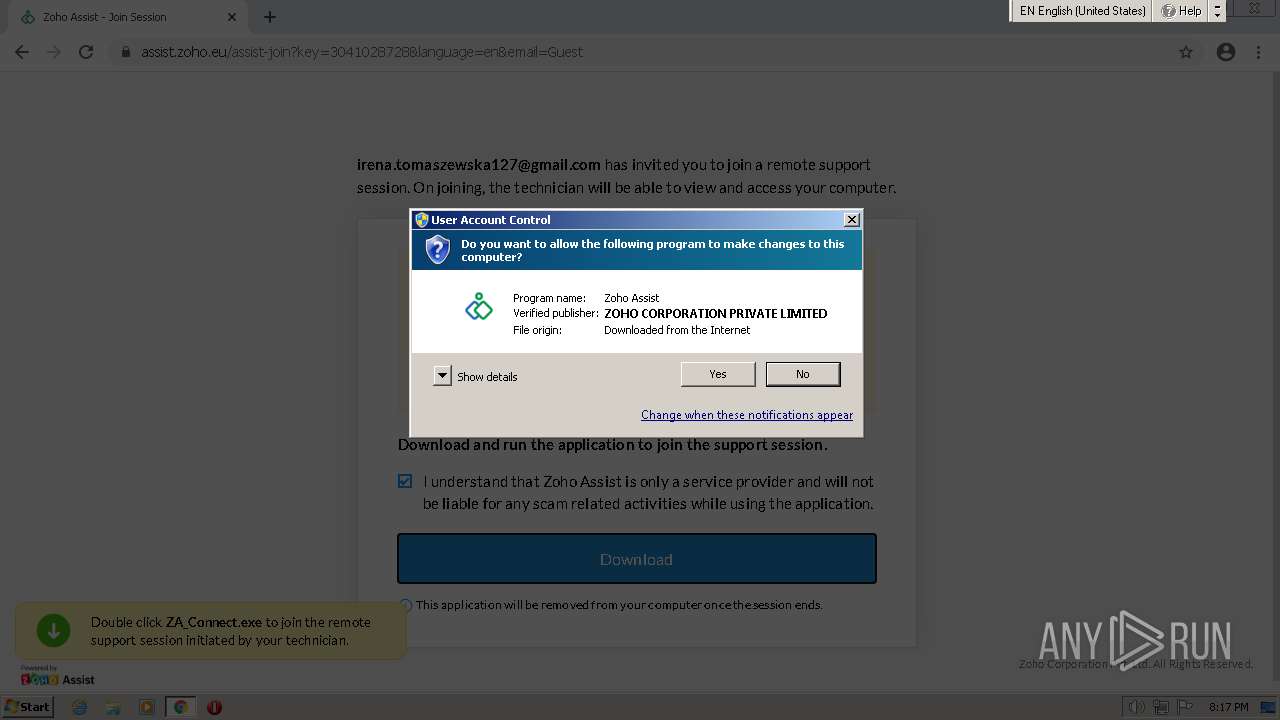
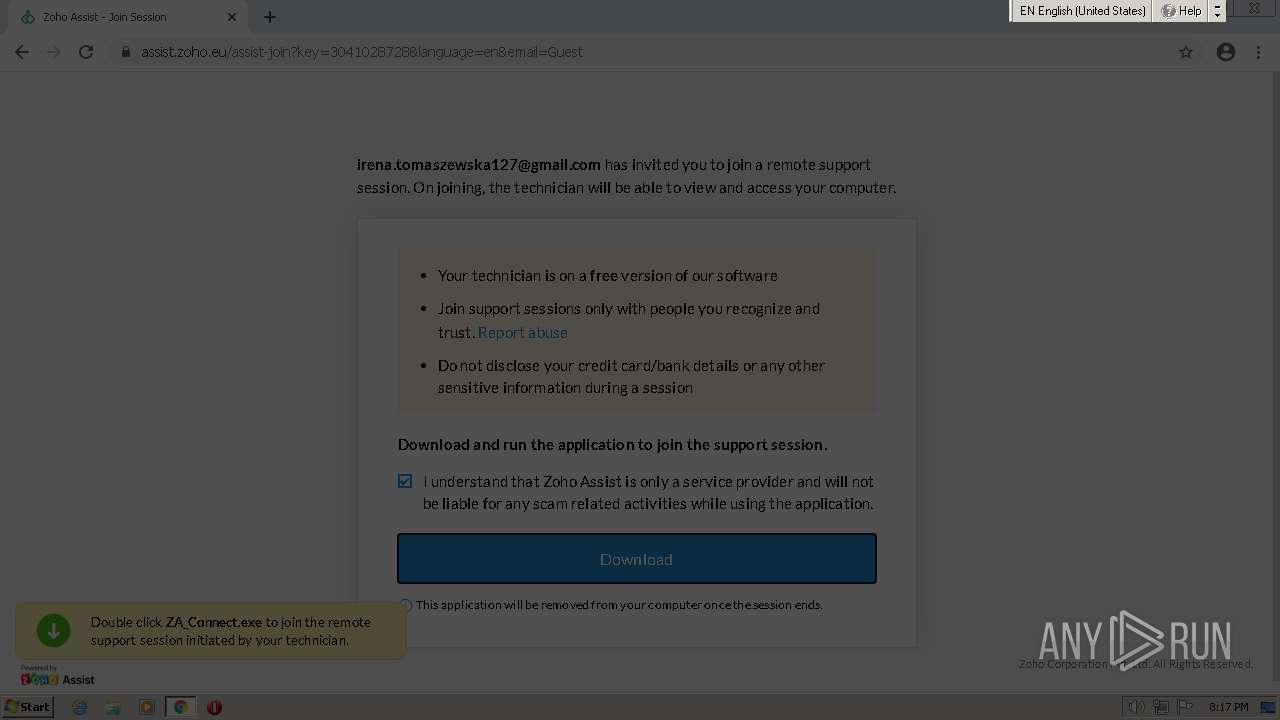
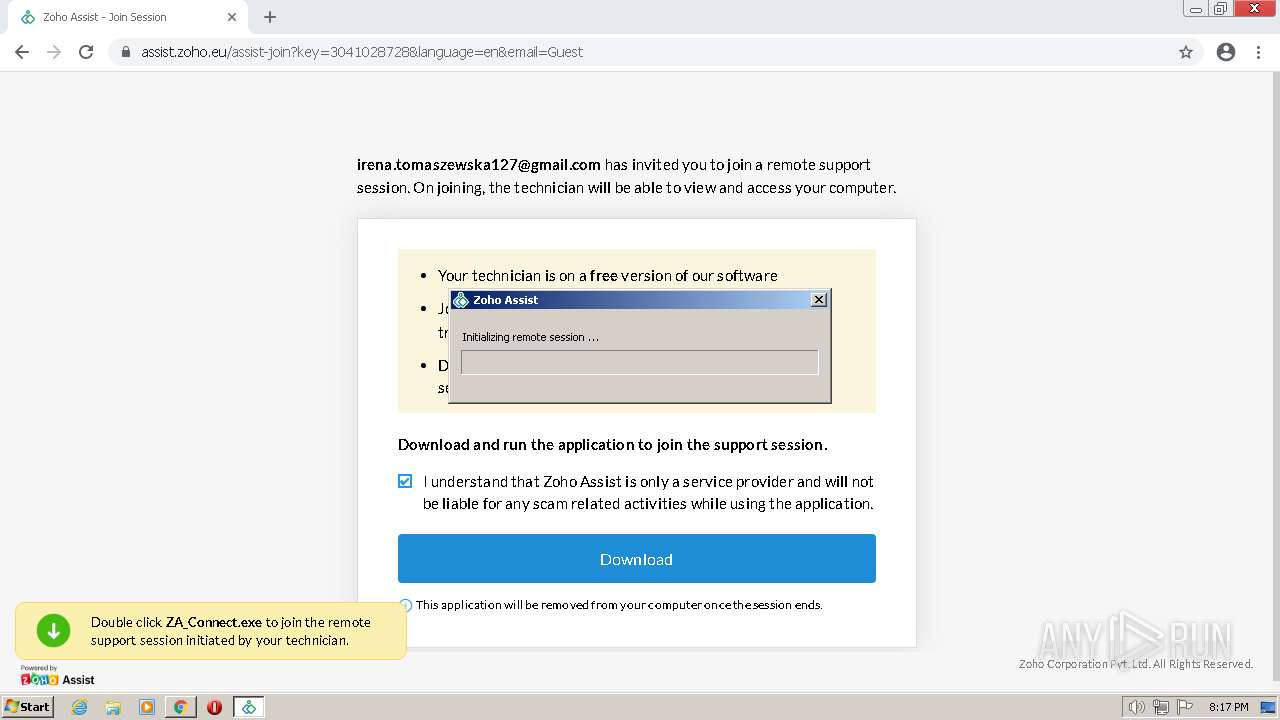
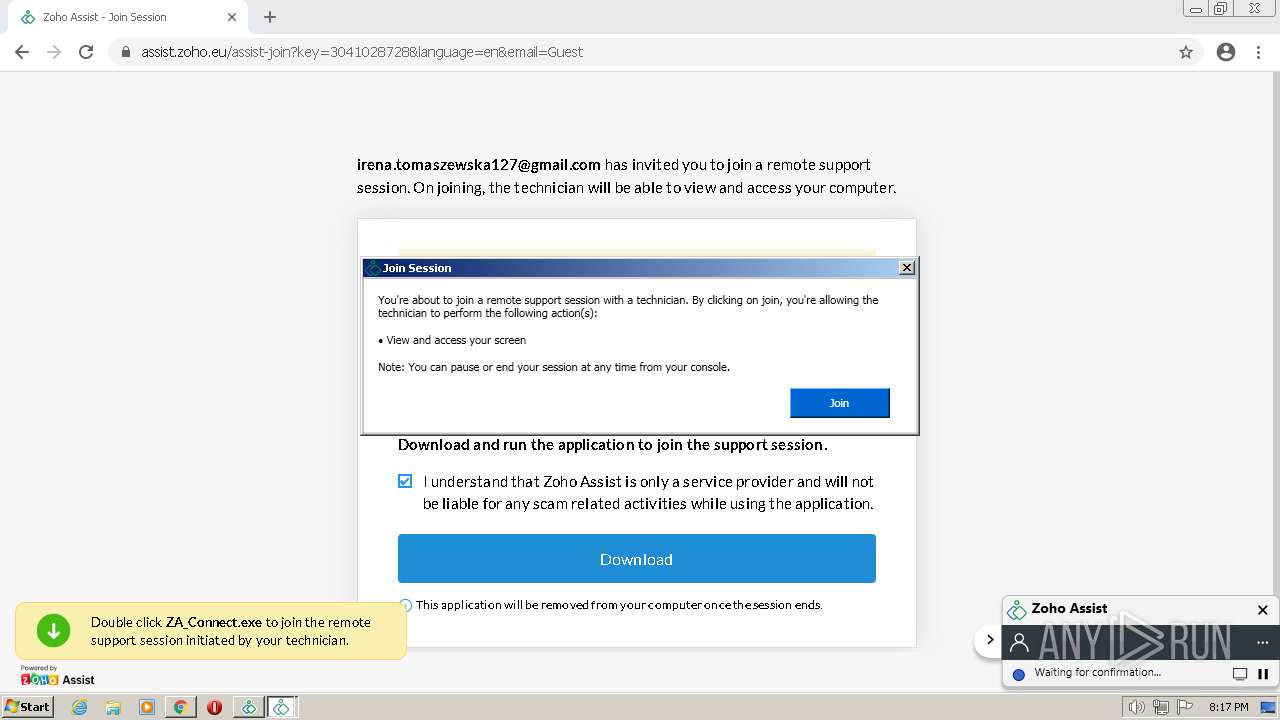
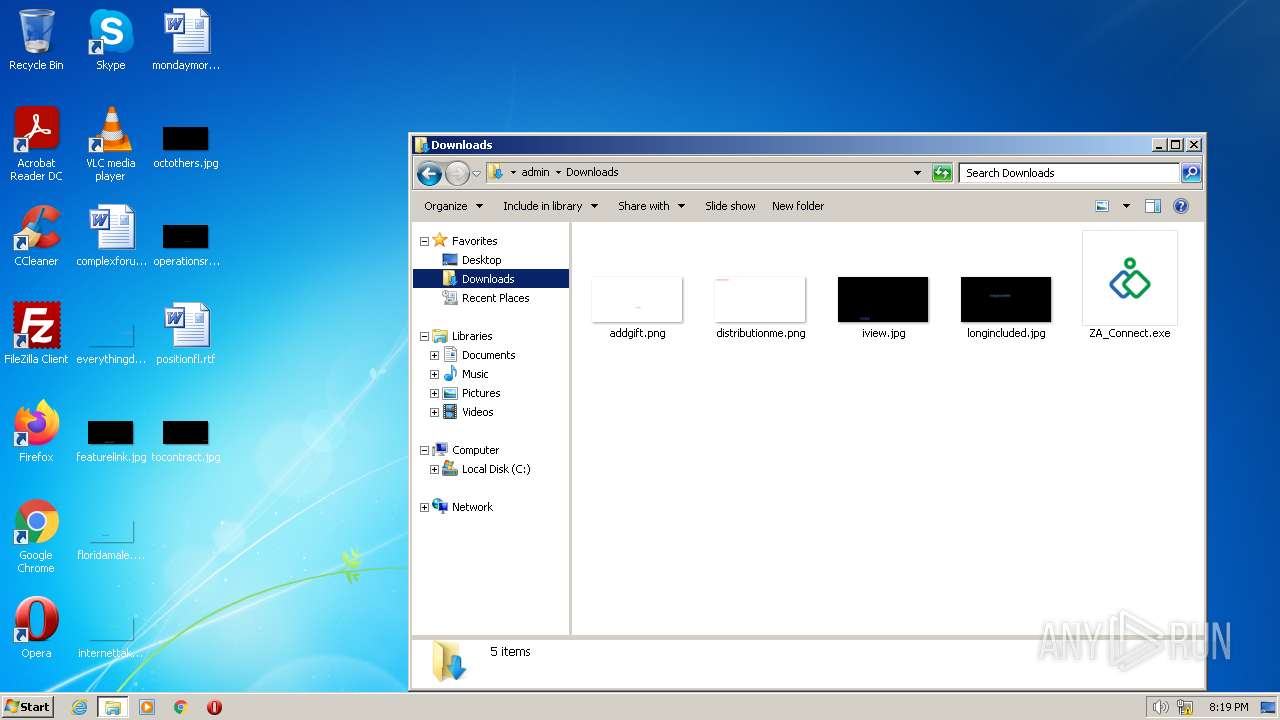
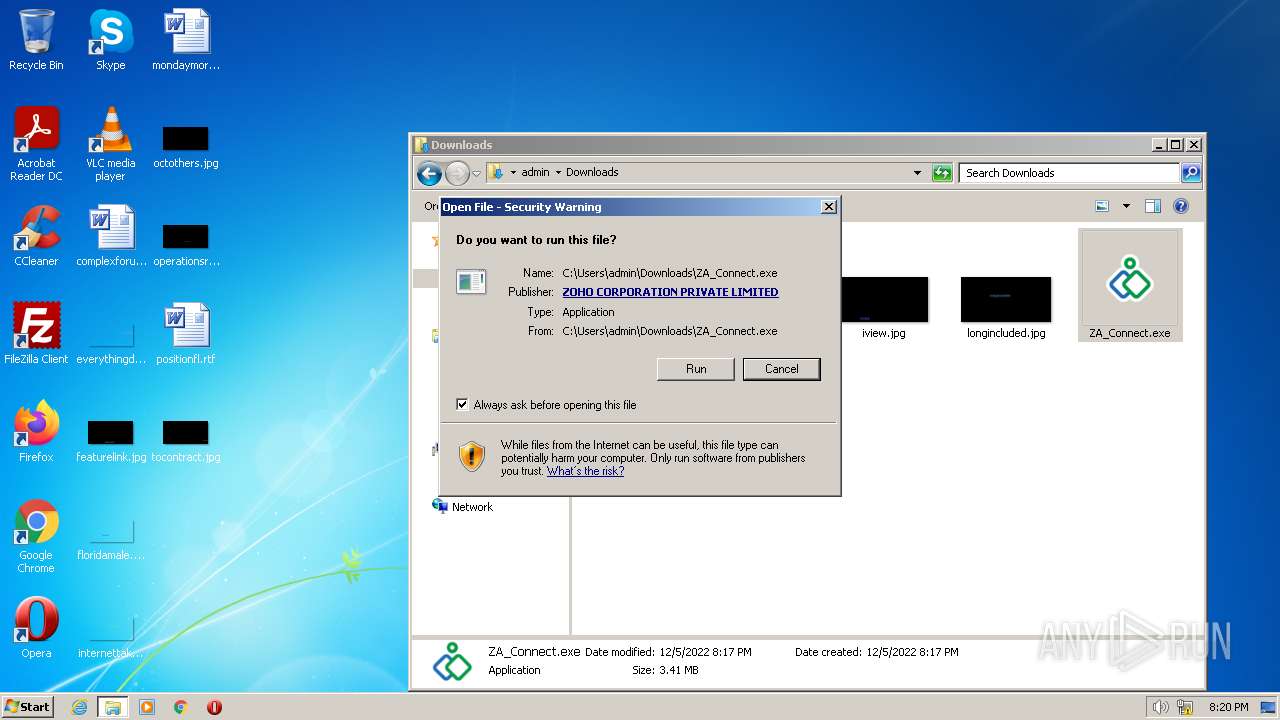
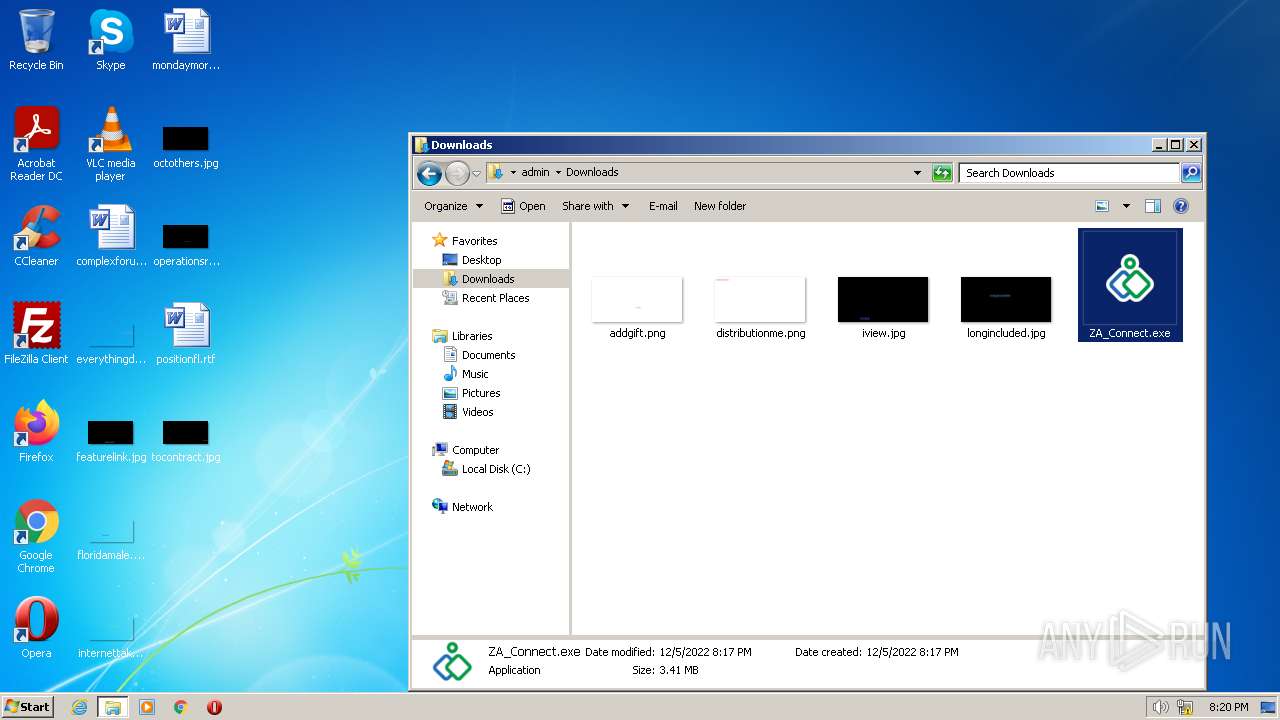
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 20:16:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 26102361C25844A328F0E96E7CE59B0E |
| SHA1: | AA10E76E683BBC7606B2C2827F001633A16A5BA0 |
| SHA256: | 3F448E7FCE4D82B1F17EFA77E1F23518E1FBC81A8701F687F5DDDCD6F9B2B895 |
| SSDEEP: | 3:N8ltX:2/ |
MALICIOUS
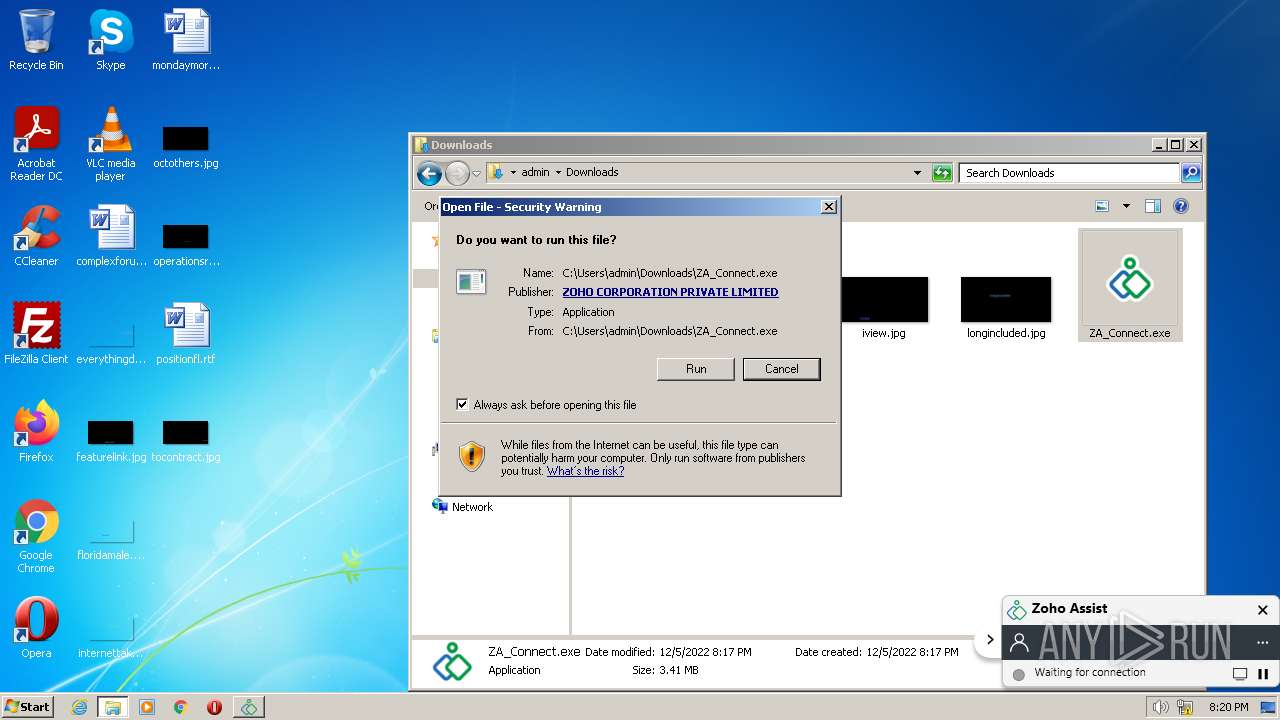
Application was dropped or rewritten from another process
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- agent_ui.exe (PID: 988)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
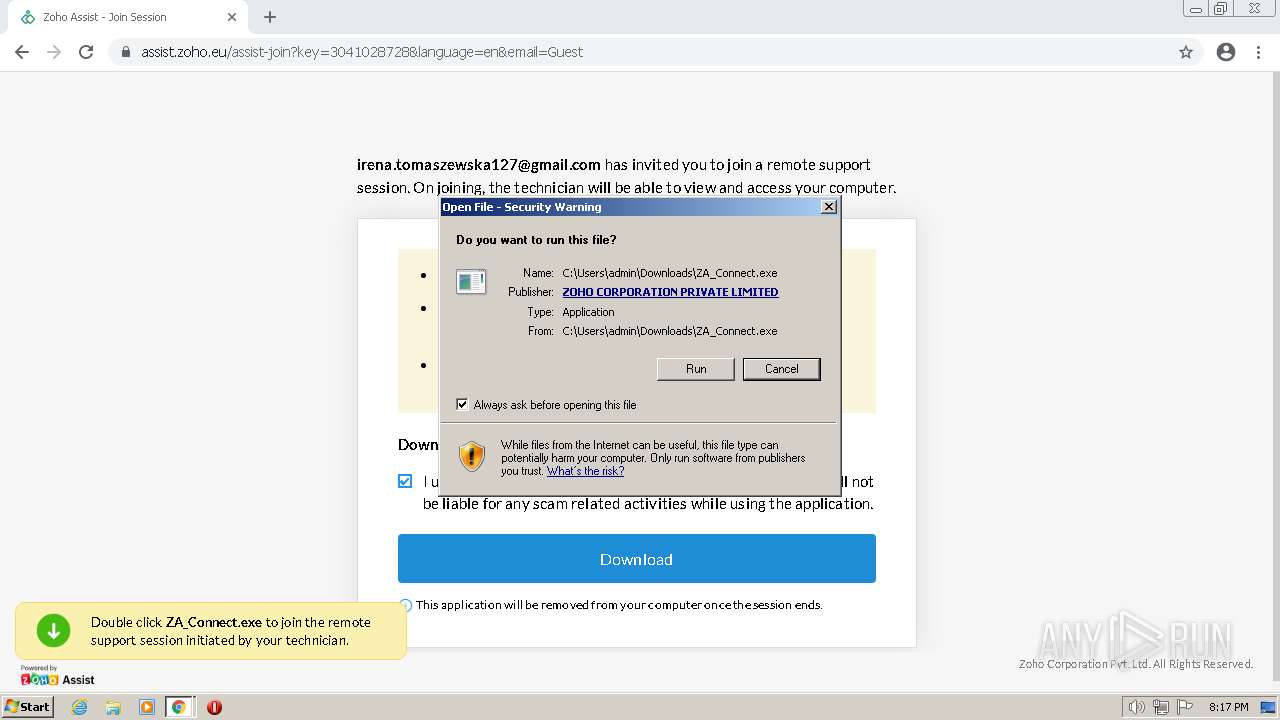
Drops the executable file immediately after the start
- ZA_Connect.exe (PID: 3304)
Loads dropped or rewritten executable
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- csrss.exe (PID: 344)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
- agent_ui.exe (PID: 988)
- csrss.exe (PID: 388)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- ZA_Connect.exe (PID: 2220)
Reads the Internet Settings
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- agent.exe (PID: 2068)
- agent_ui.exe (PID: 988)
- ZAService.exe (PID: 3728)
Application launched itself
- ZA_Connect.exe (PID: 2220)
- agent.exe (PID: 2068)
Creates a directory in Program Files
- ZA_Connect.exe (PID: 3304)
Executable content was dropped or overwritten
- ZA_Connect.exe (PID: 3304)
Drops a file with too old compile date
- ZA_Connect.exe (PID: 3304)
Creates a software uninstall entry
- ZA_Connect.exe (PID: 3304)
Executes as Windows Service
- ZAService.exe (PID: 3728)
Checks Windows Trust Settings
- agent.exe (PID: 2068)
Changes default file association
- ZA_Connect.exe (PID: 3304)
Reads settings of System Certificates
- agent.exe (PID: 2068)
Adds/modifies Windows certificates
- agent.exe (PID: 2068)
INFO
Application launched itself
- chrome.exe (PID: 2884)
Drops the executable file immediately after the start
- chrome.exe (PID: 2884)
Executable content was dropped or overwritten
- chrome.exe (PID: 2884)
Checks supported languages
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
- agent_ui.exe (PID: 988)
Reads the computer name
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
- agent_ui.exe (PID: 988)
Reads Environment values
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
Reads product name
- ZA_Connect.exe (PID: 2220)
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3012)
- ZAService.exe (PID: 3728)
- agent.exe (PID: 2068)
- agent.exe (PID: 2880)
Creates files in the program directory
- ZA_Connect.exe (PID: 3304)
- ZAService.exe (PID: 3728)
- agent.exe (PID: 2880)
- agent_ui.exe (PID: 988)
- agent.exe (PID: 2068)
Checks proxy server information
- ZA_Connect.exe (PID: 3304)
Dropped object may contain Bitcoin addresses
- ZA_Connect.exe (PID: 3304)
Drops a file that was compiled in debug mode
- ZA_Connect.exe (PID: 3304)
Checks Windows language
- agent.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
30
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
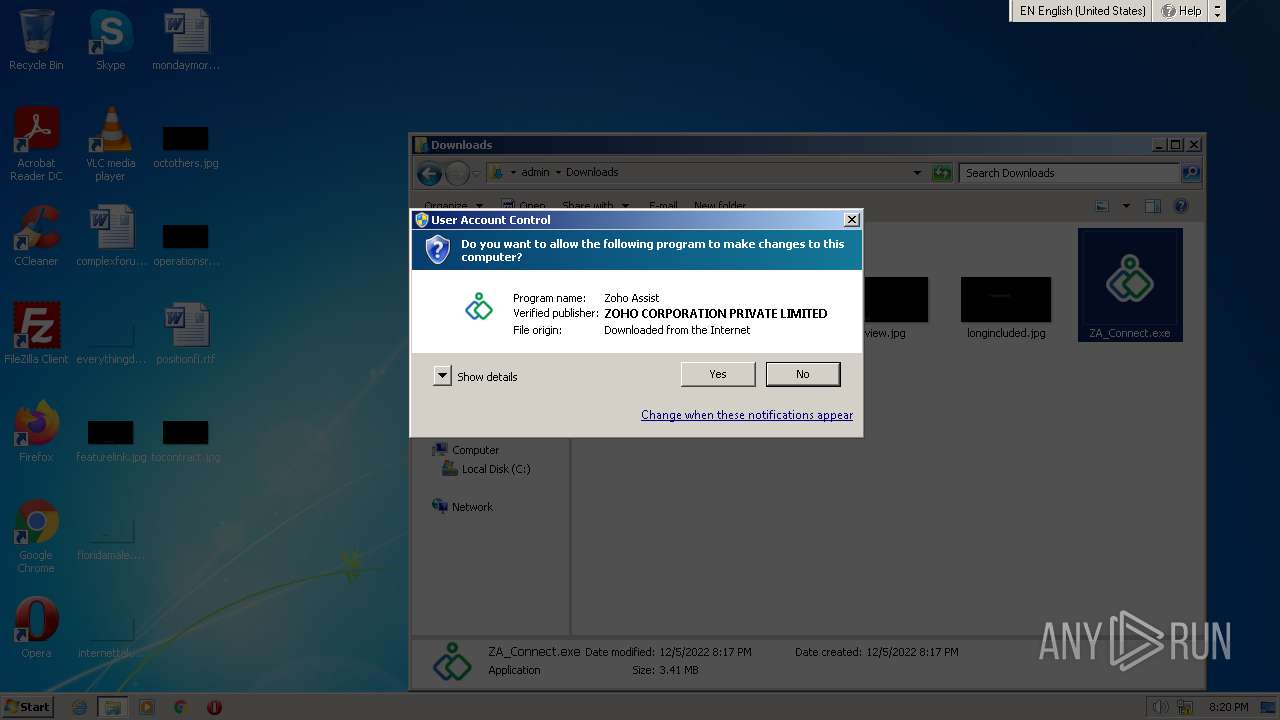
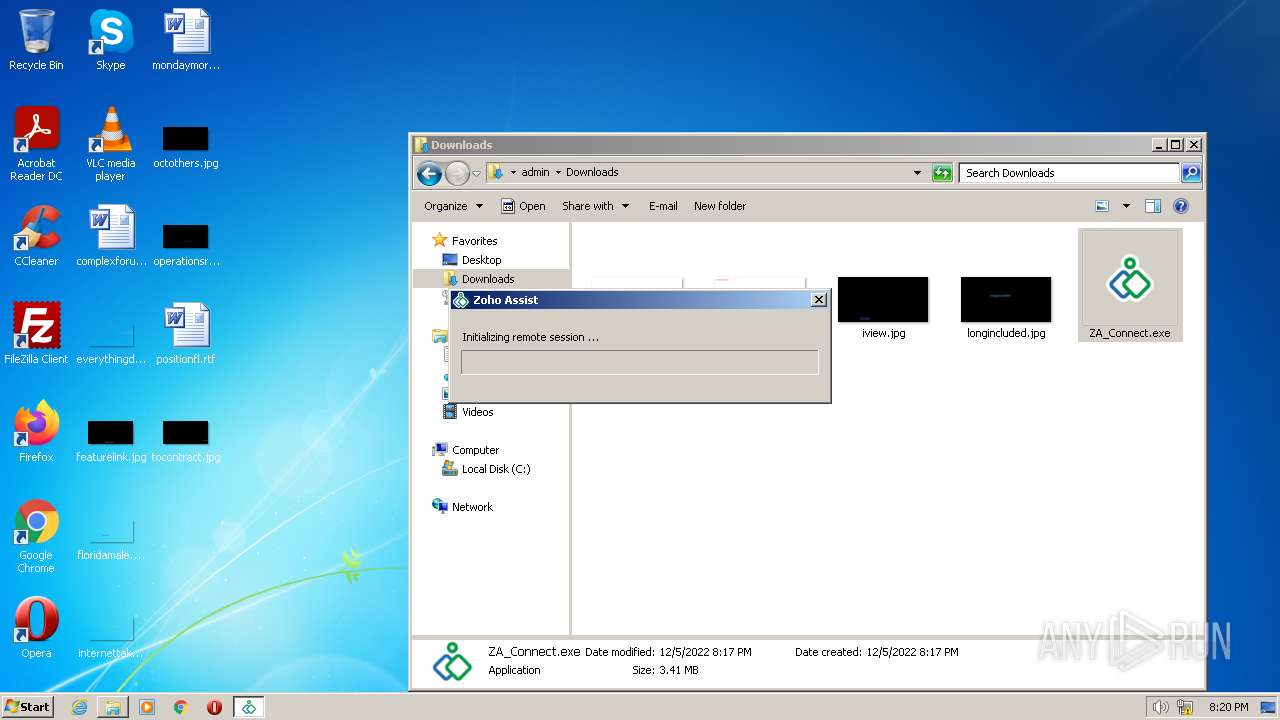
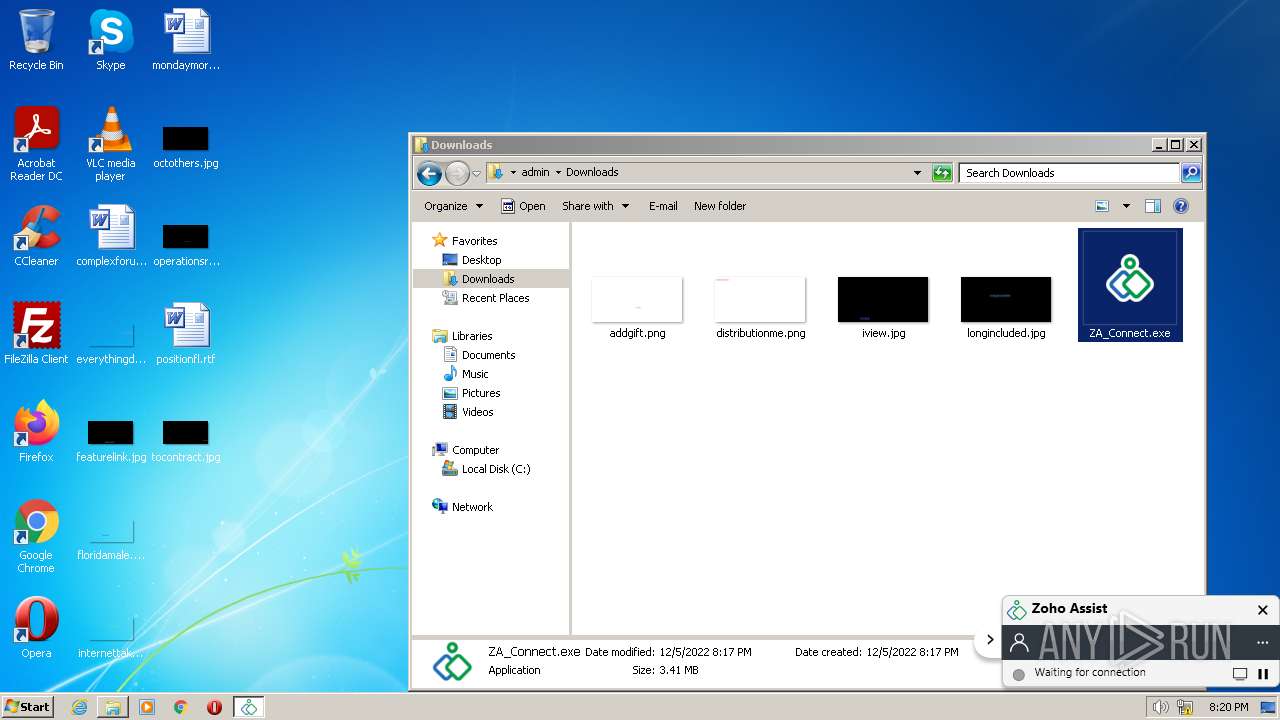
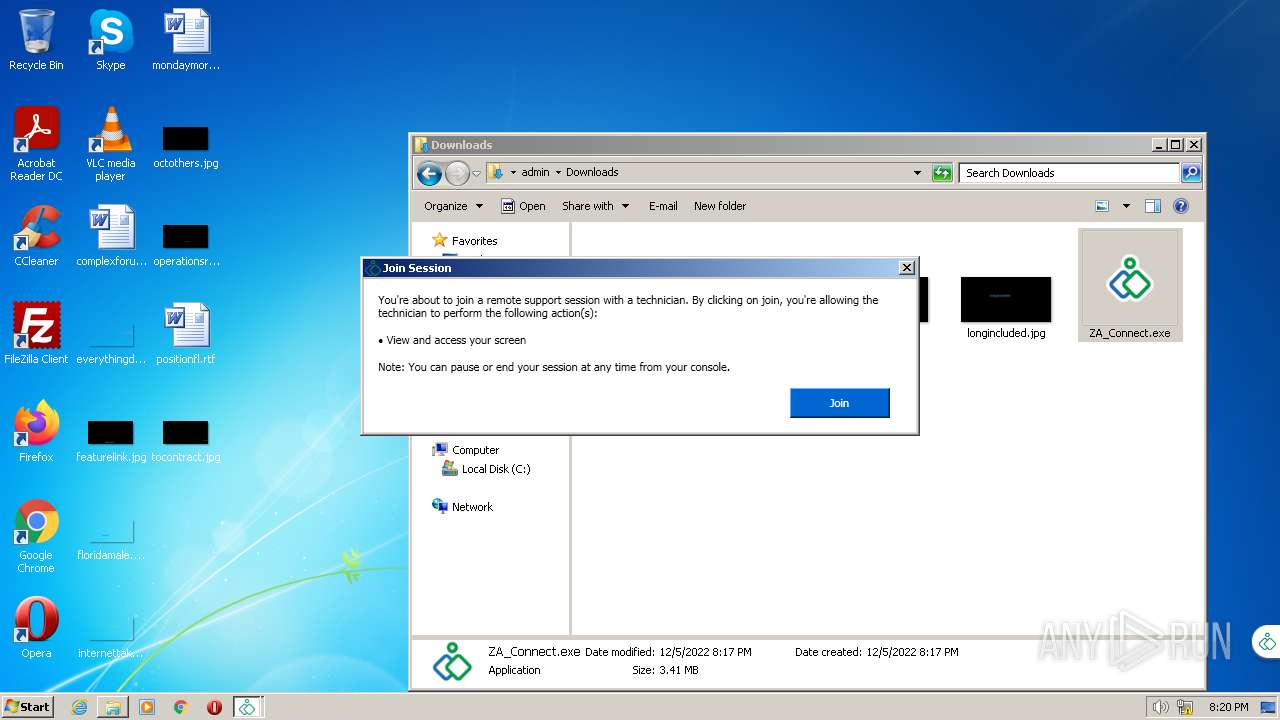
| 988 | 3041028728 ProcessOwner:SYSTEM ProductName:Zoho%20Assist apptype:ATTENDEE | C:\Program Files\ZohoMeeting\agent_ui.exe | — | agent.exe | |||||||||||
User: SYSTEM Company: Zoho Integrity Level: SYSTEM Description: ZohoAssist Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,2718768281398399455,14192351996645582627,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e95d988,0x6e95d998,0x6e95d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,2718768281398399455,14192351996645582627,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,2718768281398399455,14192351996645582627,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\ZohoMeeting\agent.exe" -agent -k 3041028728 -s gwnl5.zohoassist.com -altgw gweu.zohoassist.com -fileTransferGateways ft2-eu2.zohoassist.com -ms assist.zoho.eu -ssl true -email Guest -authkey J1Zcvz5p4439khl7vm2dhQKQ/kcHKp0dQ4YzCt12sAMflaDtcZJ8MDf0rqq0SNrpsJCM3+oKi6M+gHngnTHnfw== -authtype 1 -SERVICEAGENT -clientId -1 -demo_mode false -demo_tech false -ShowInit 0 -group AEP -productID 1 -js join.zoho.eu -c_check false | C:\Program Files\ZohoMeeting\agent.exe | ZAService.exe | ||||||||||||
User: SYSTEM Company: Zoho Corporation Integrity Level: SYSTEM Description: Zoho Assist Exit code: 0 Version: 111.0.3.223 Modules
| |||||||||||||||
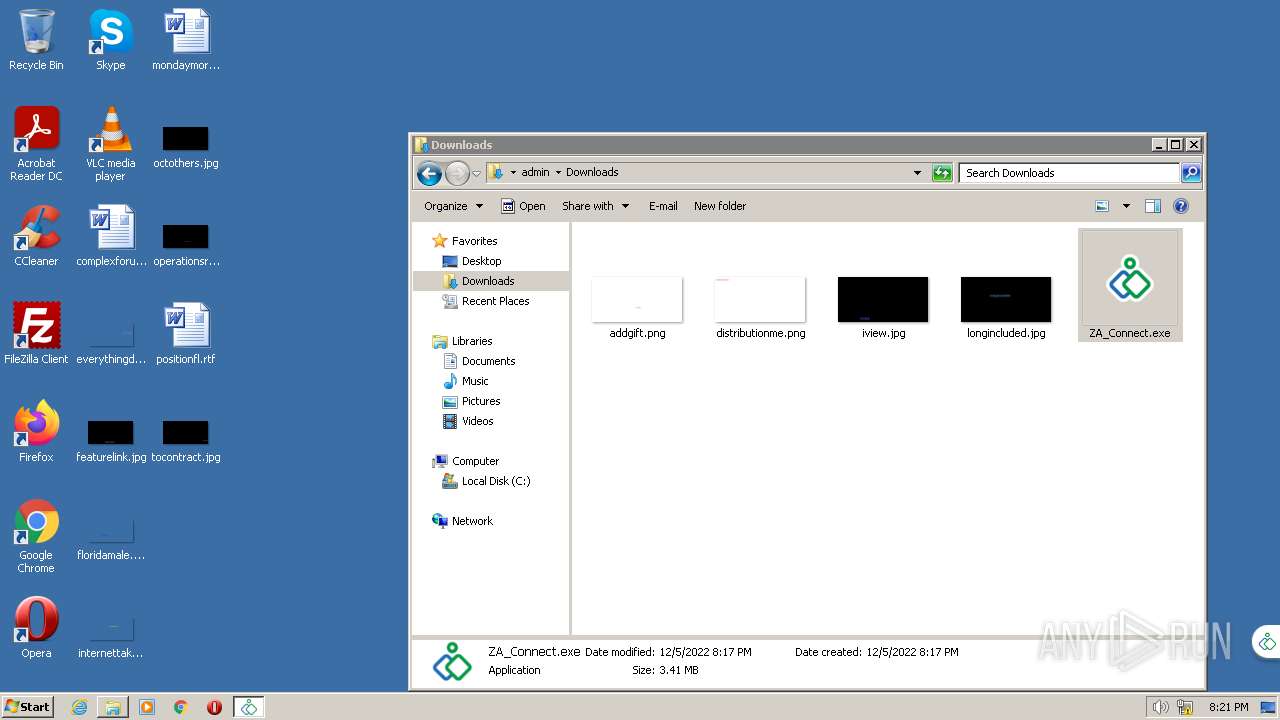
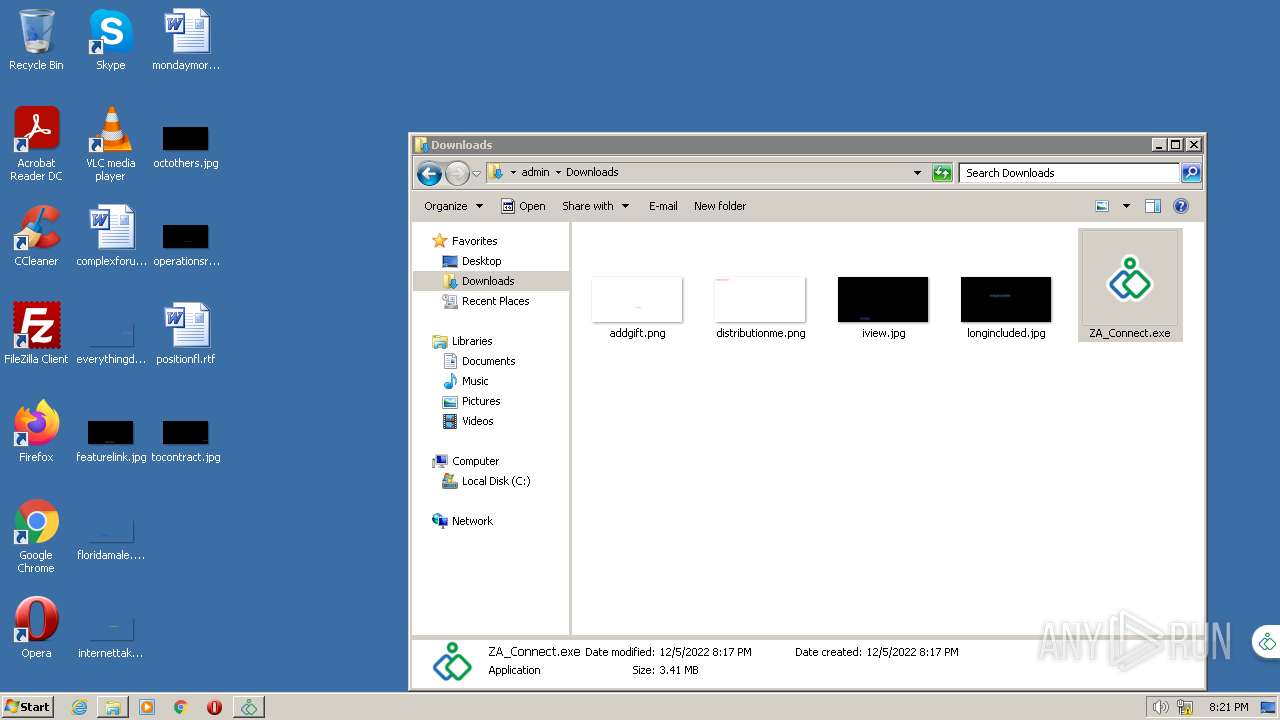
| 2220 | "C:\Users\admin\Downloads\ZA_Connect.exe" | C:\Users\admin\Downloads\ZA_Connect.exe | — | chrome.exe | |||||||||||
User: admin Company: ZOHO Corporation Integrity Level: MEDIUM Description: Zoho Assist Exit code: 0 Version: 1.0.0.79 Modules
| |||||||||||||||
| 2220 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | agent_ui.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Pen and Touch Input Component Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 077
Read events
19 839
Write events
236
Delete events
2
Modification events
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
48
Suspicious files
31
Text files
143
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638E51B0-B44.pma | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\27ee3e56-16ed-4ffe-a9c8-8acf04f90647.tmp | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF106fe0c.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF106fe1c.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
59
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
— | — | HEAD | 200 | 23.203.90.83:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133147451205000000 | US | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.65 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 8.10 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 53.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 34.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 226 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 17.3 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.20 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.186.46:443 | clients2.google.com | GOOGLE | US | whitelisted |
— | — | 185.230.212.83:443 | join.zoho.eu | ZOHO Corporation B.V | NL | unknown |
2976 | chrome.exe | 142.250.186.46:443 | clients2.google.com | GOOGLE | US | whitelisted |
2976 | chrome.exe | 185.230.212.83:443 | join.zoho.eu | ZOHO Corporation B.V | NL | unknown |
2976 | chrome.exe | 143.204.89.59:443 | cdn.pagesense.io | AMAZON-02 | US | unknown |
2976 | chrome.exe | 136.143.190.173:443 | sites.zoho.com | ZOHO-AS | US | unknown |
2976 | chrome.exe | 89.36.170.31:443 | js.zohostatic.eu | Computerline GmbH | CH | unknown |
2976 | chrome.exe | 142.250.184.202:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2976 | chrome.exe | 185.20.209.147:443 | static.zohocdn.com | Computerline GmbH | CH | unknown |
— | — | 142.250.185.77:443 | accounts.google.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
join.zoho.eu |
| unknown |
accounts.google.com |
| shared |
assist.zoho.eu |
| unknown |
sites.zoho.com |
| unknown |
js.zohostatic.eu |
| unknown |
cdn.pagesense.io |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
static.zohocdn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ZA_Connect.exe | CustomURLProtocol::Failed with error 2: The system cannot find the file specified.
|
ZA_Connect.exe | CustomURLProtocol::Failed with error 2: The system cannot find the file specified.
|