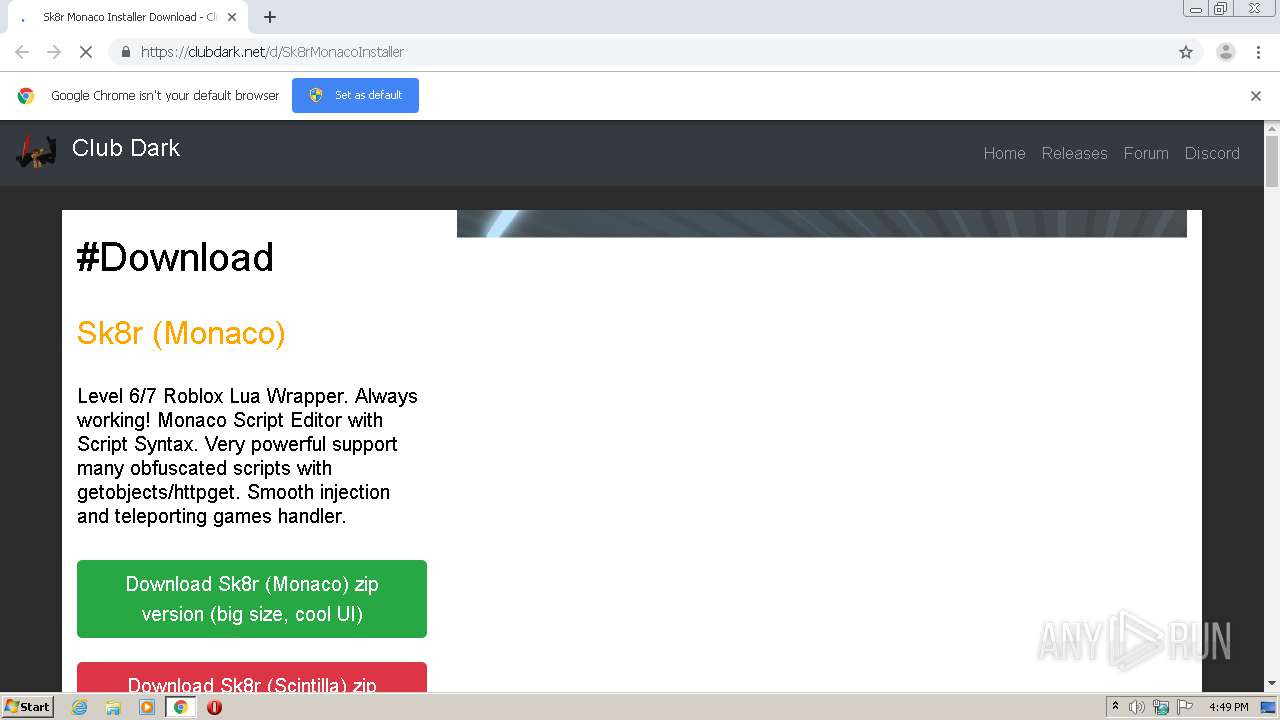
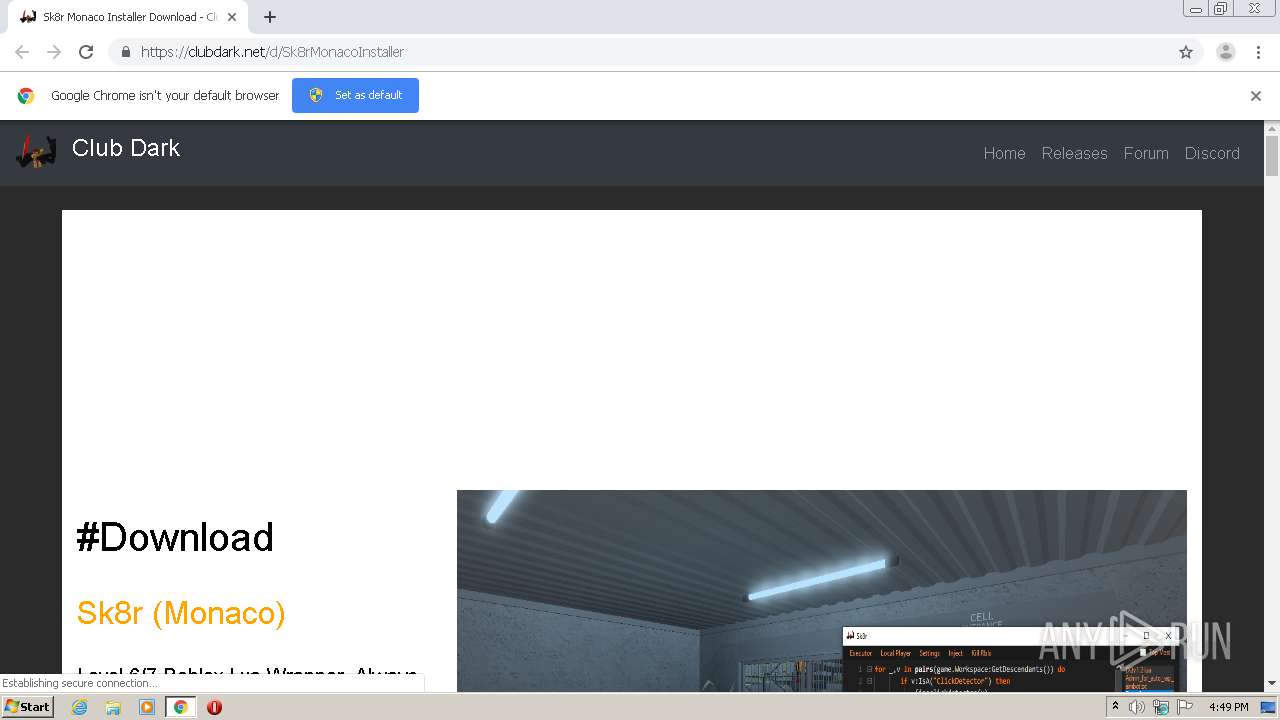
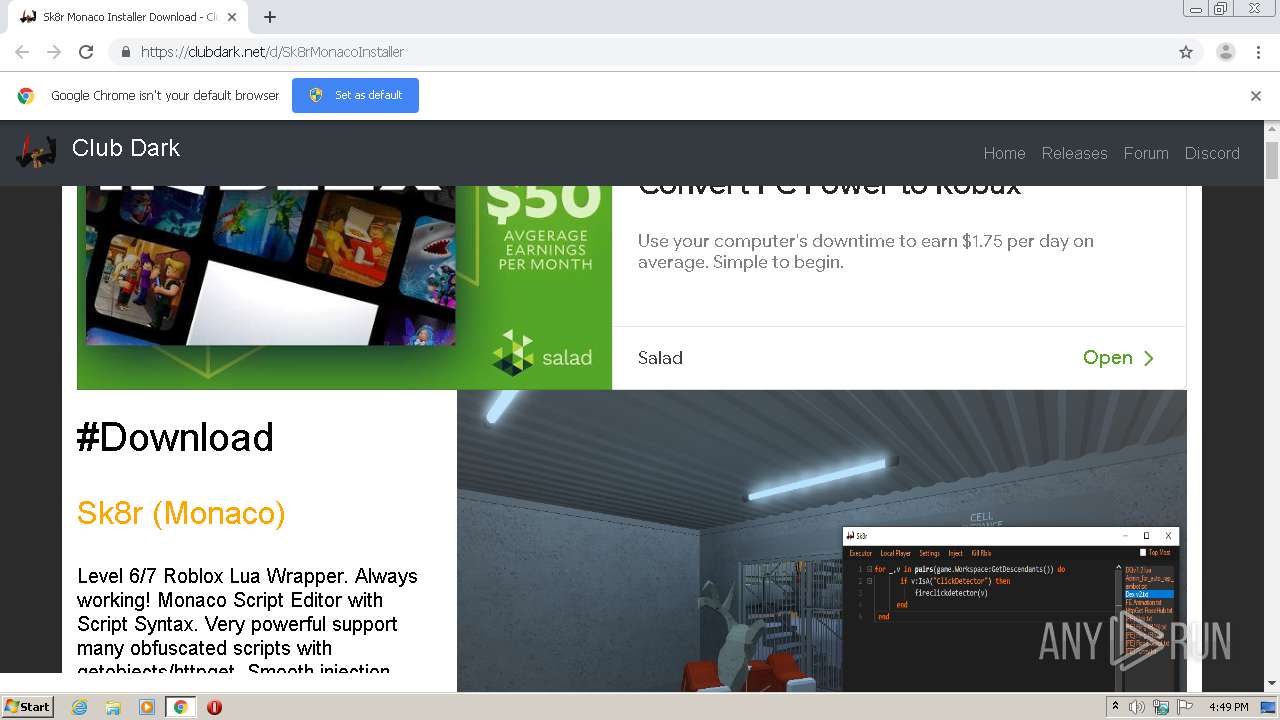
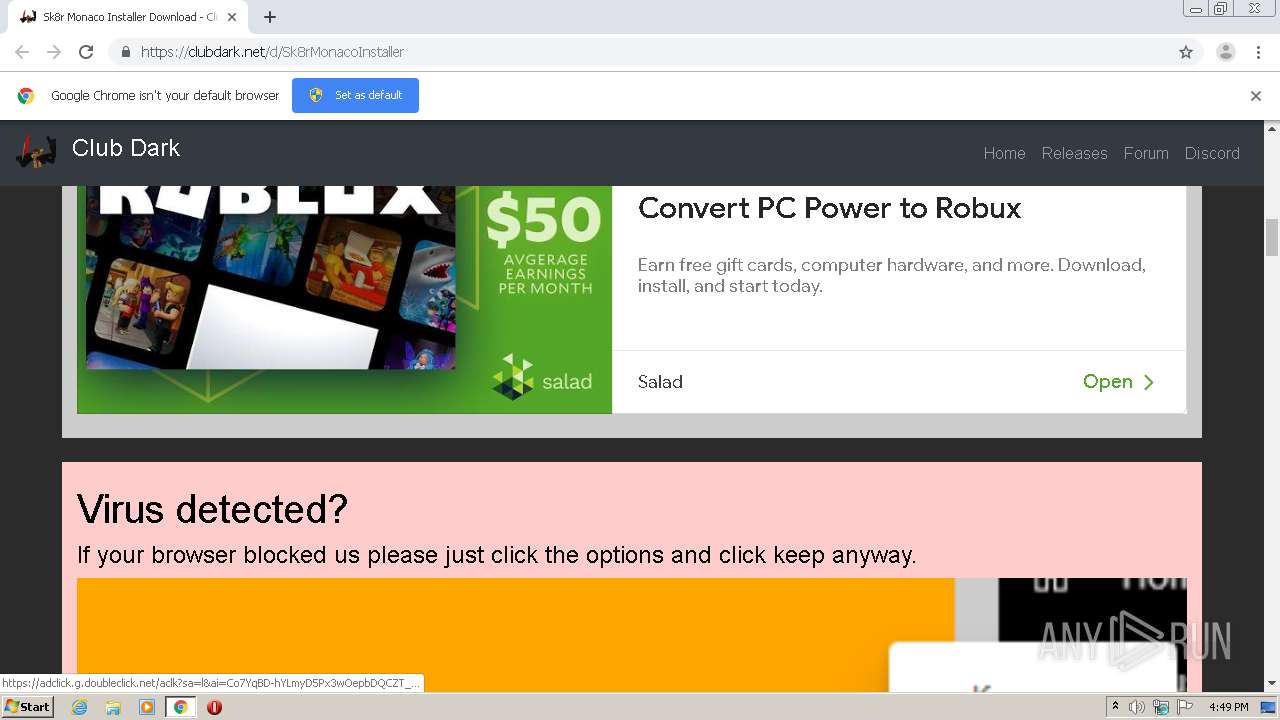
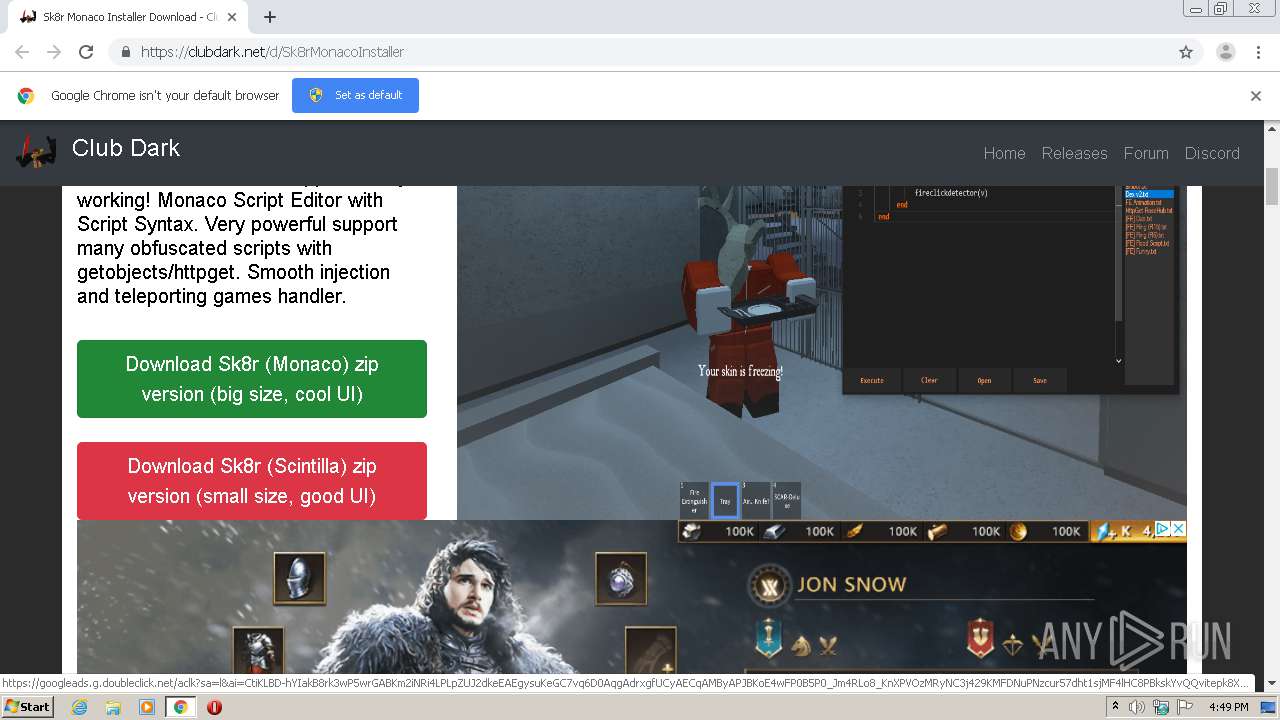
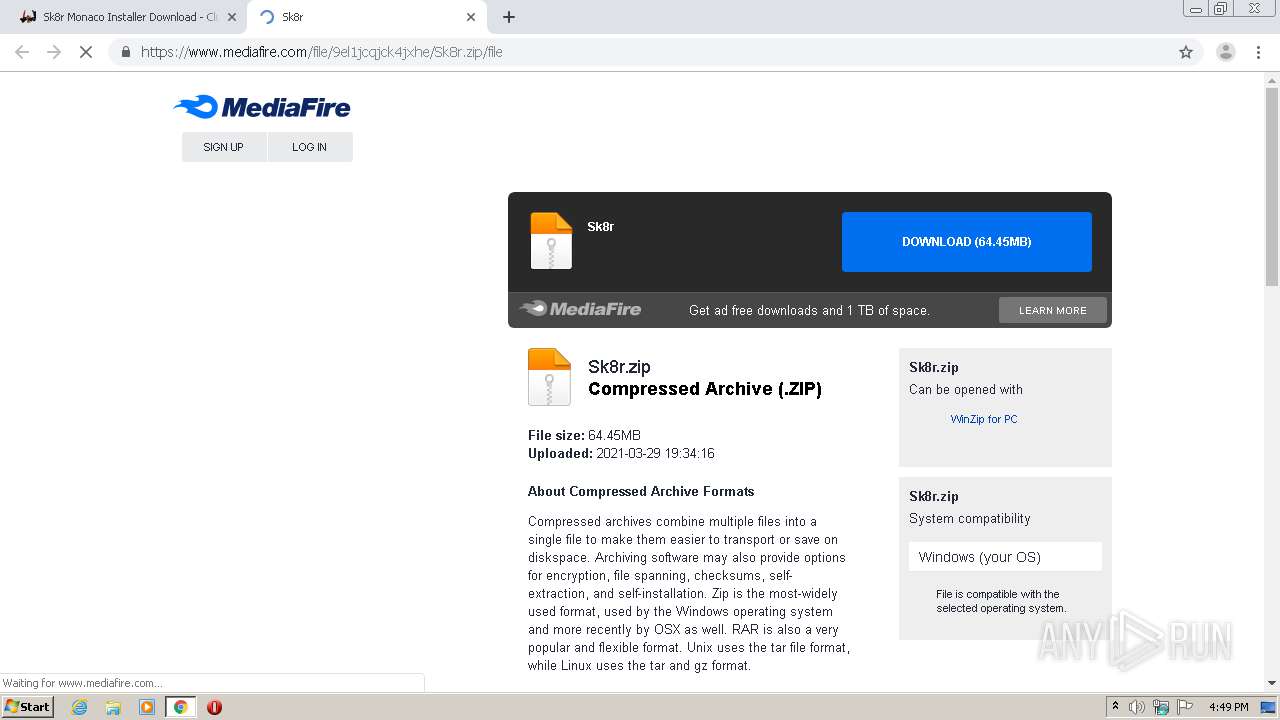
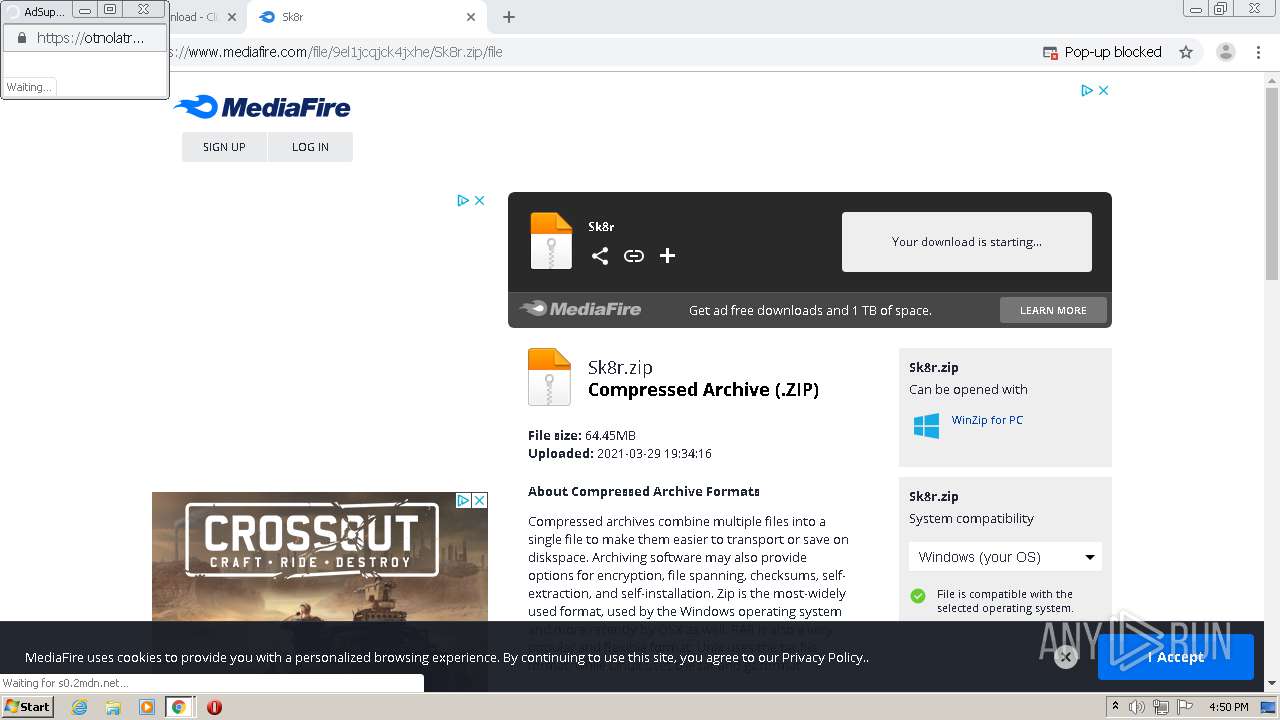
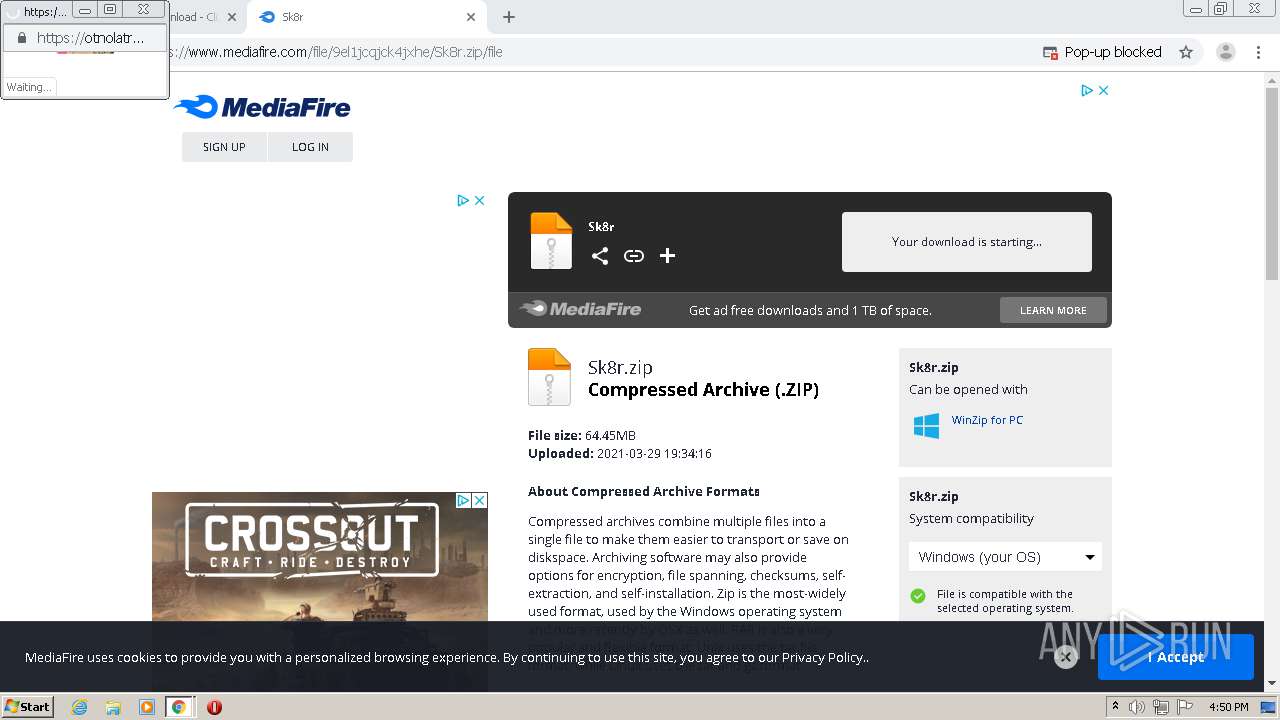
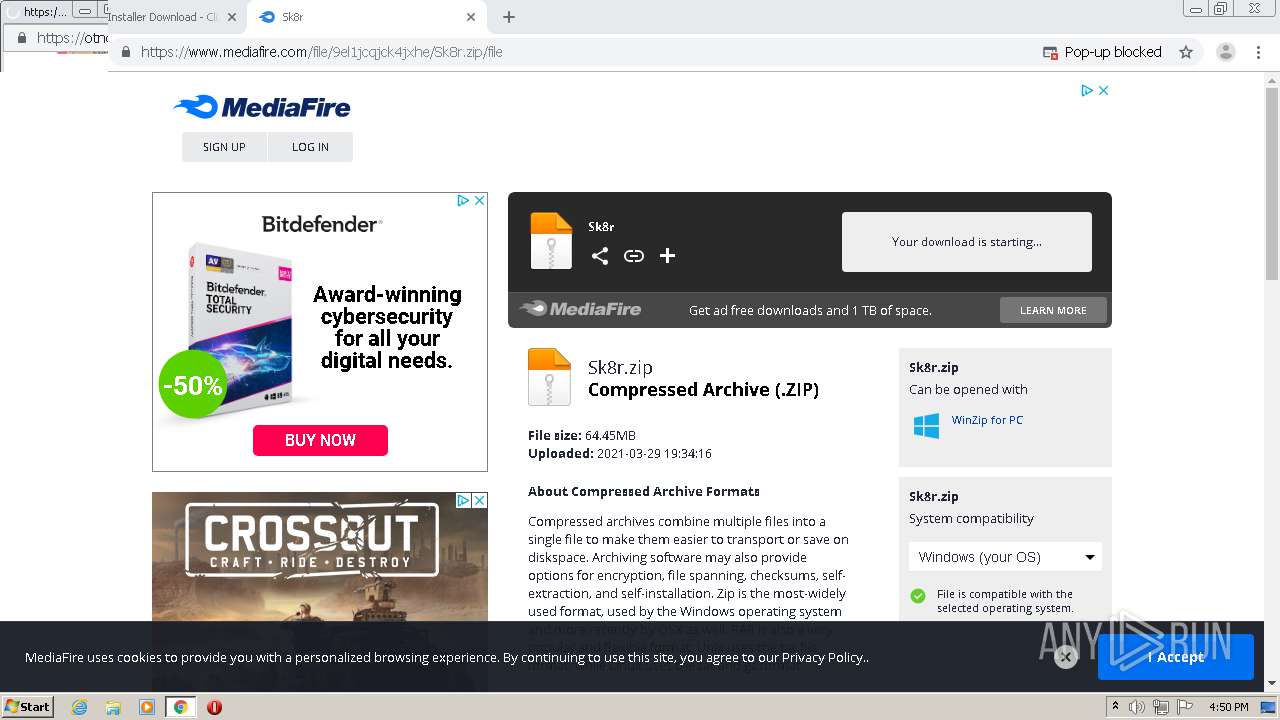
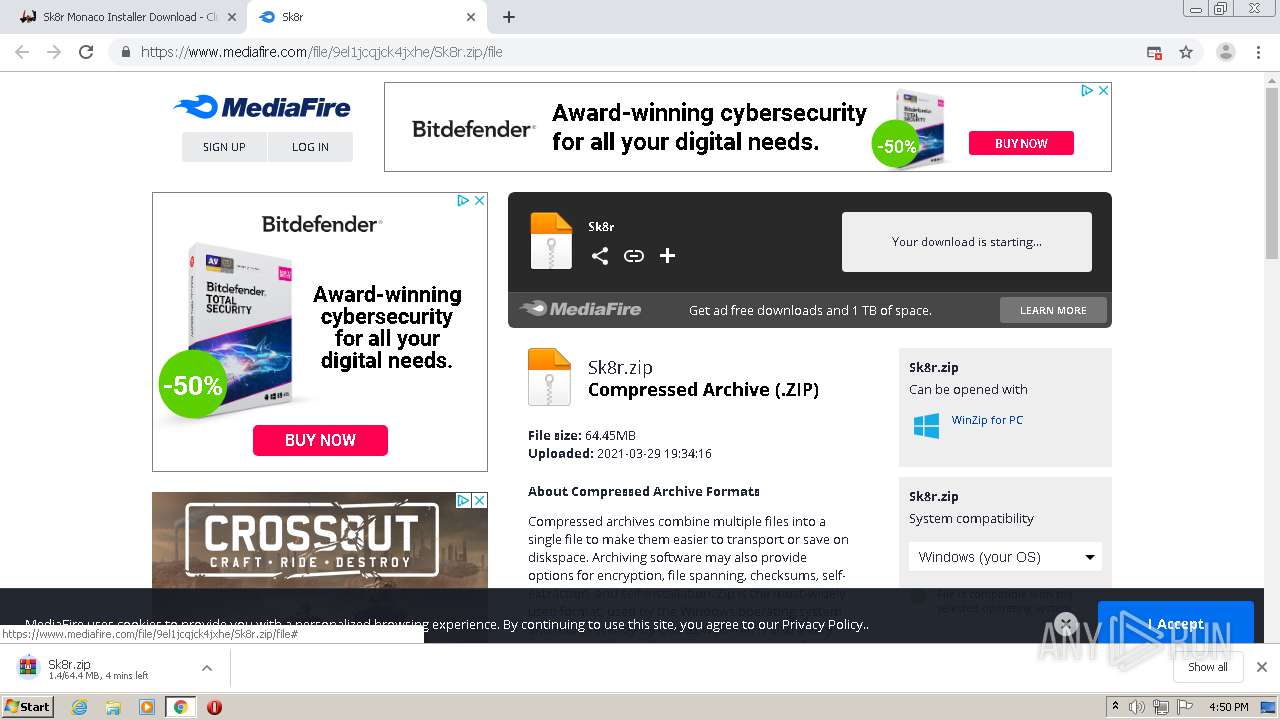
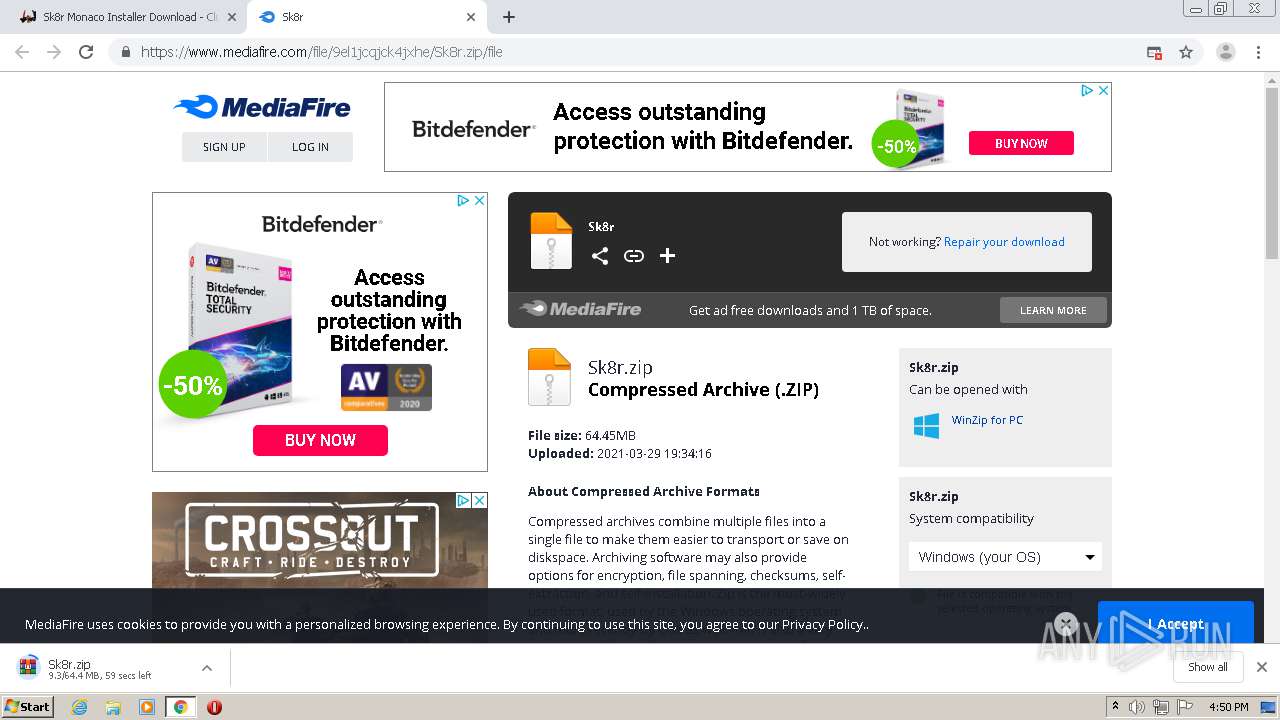
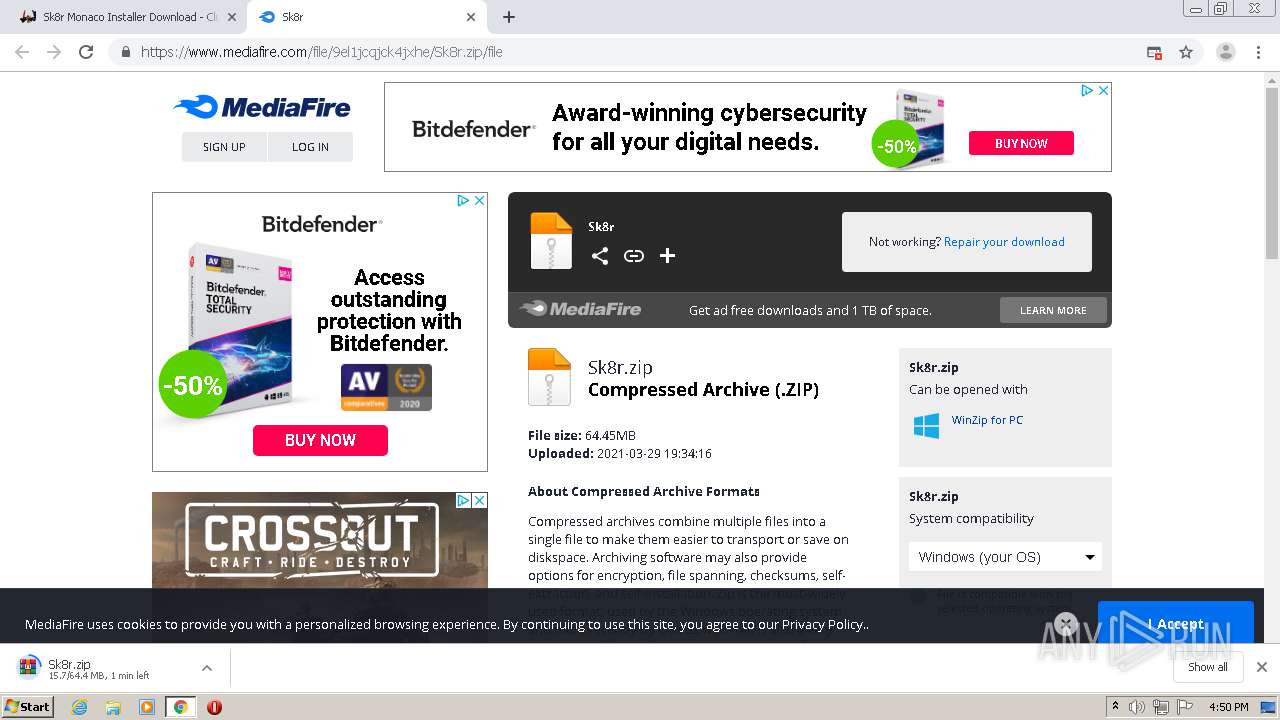
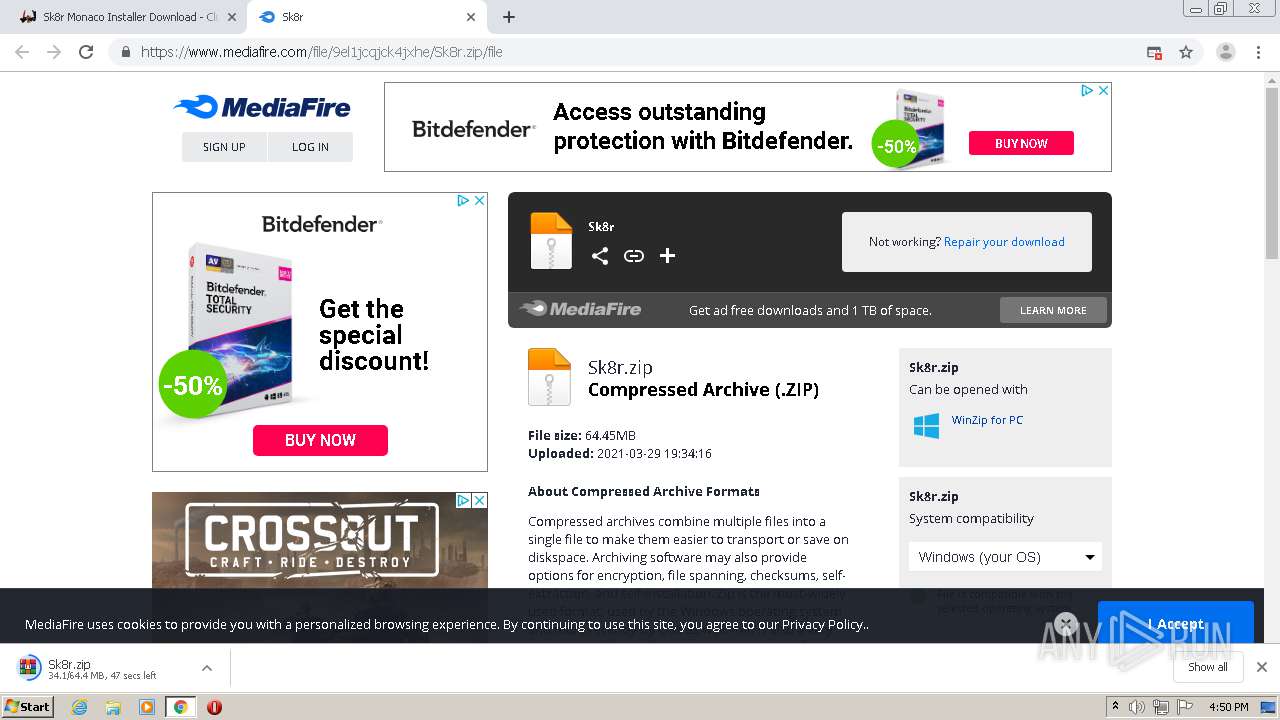
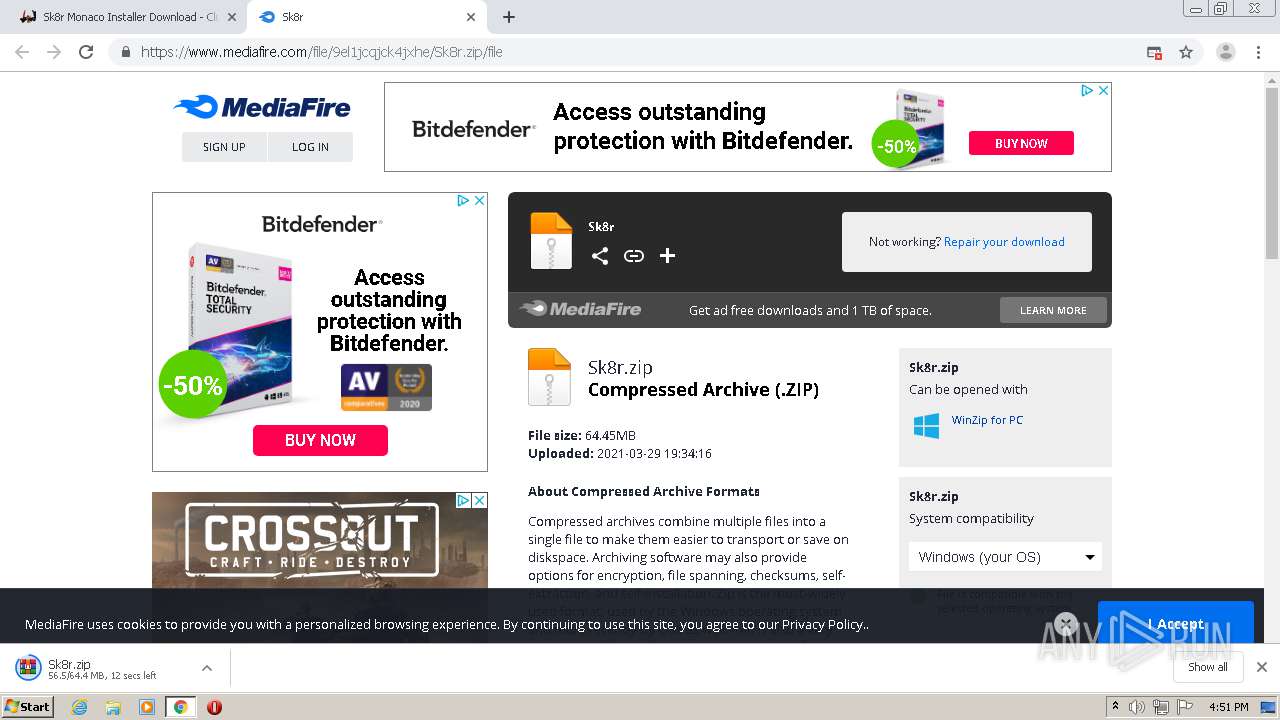
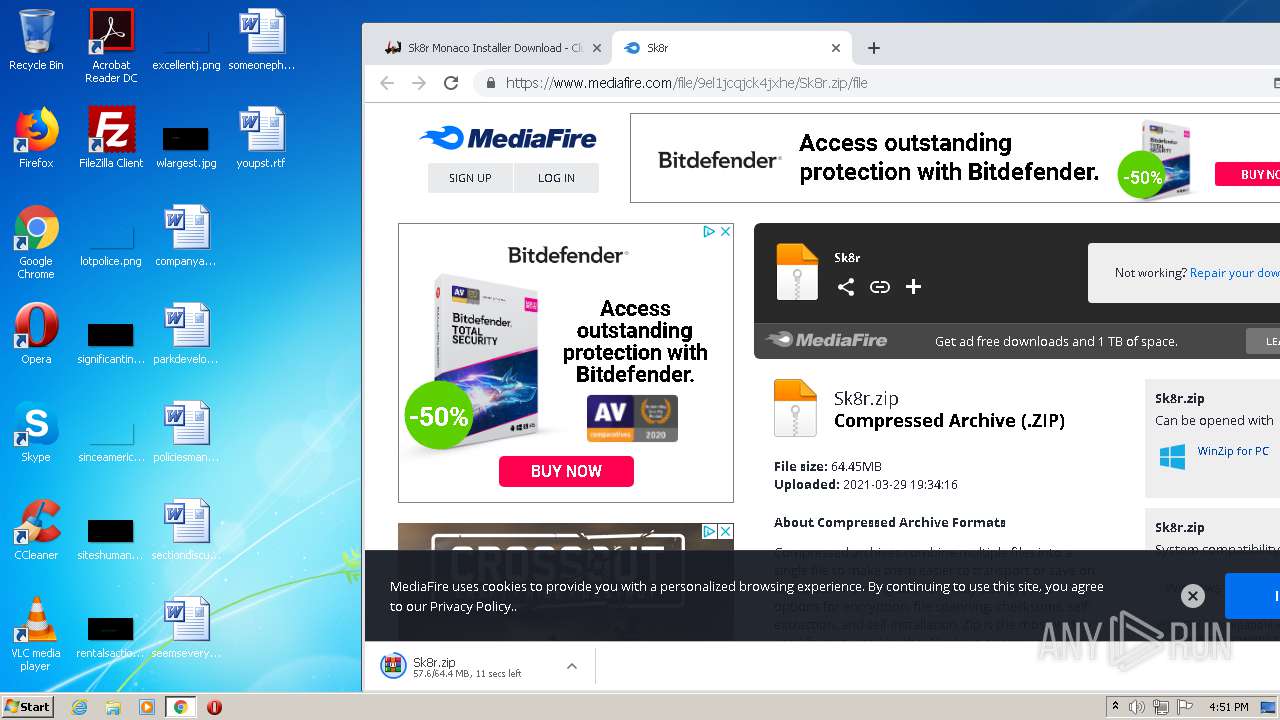
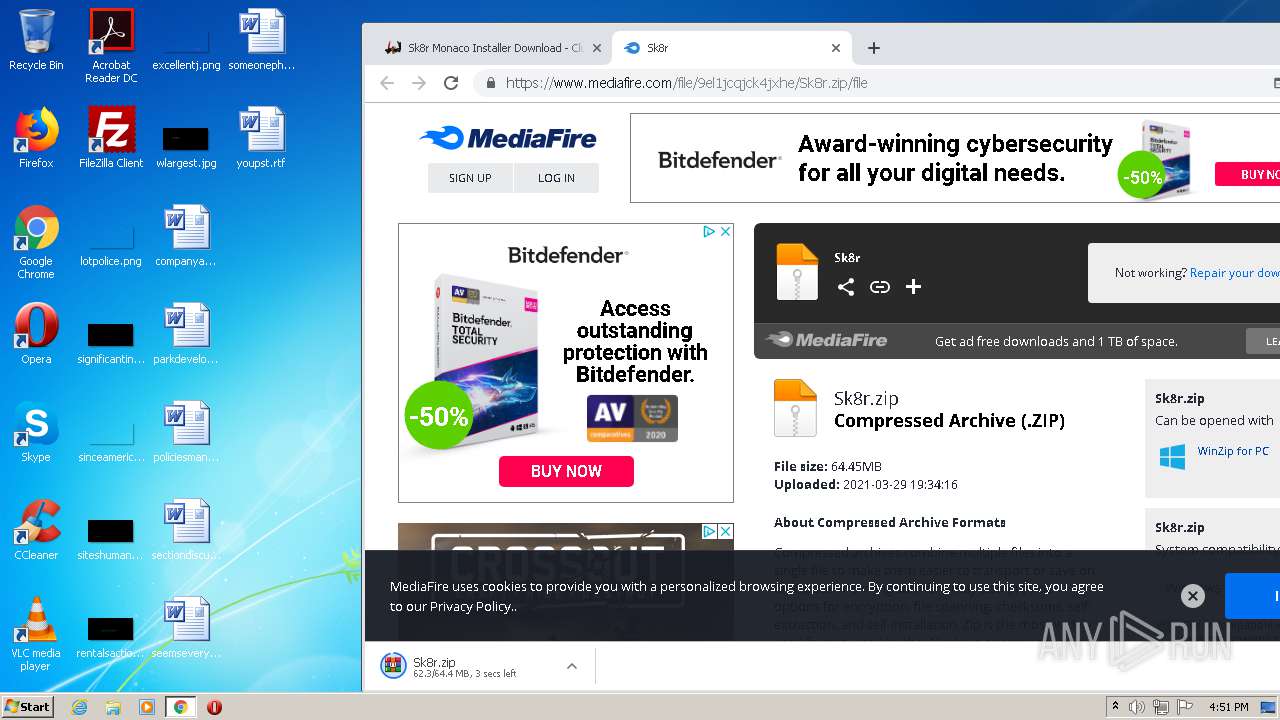
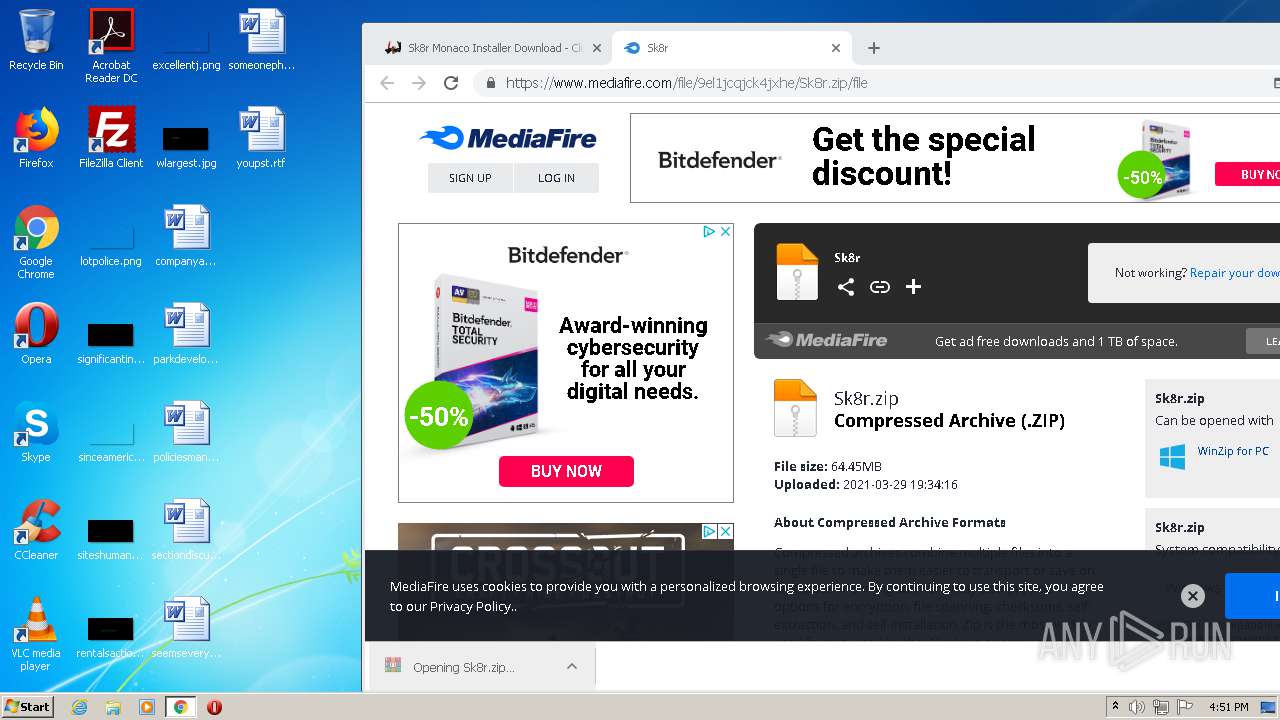
| URL: | https://clubdark.net/d/Sk8rMonacoInstaller |
| Full analysis: | https://app.any.run/tasks/47705df2-3c25-445d-8184-e7d3aea9d8da |
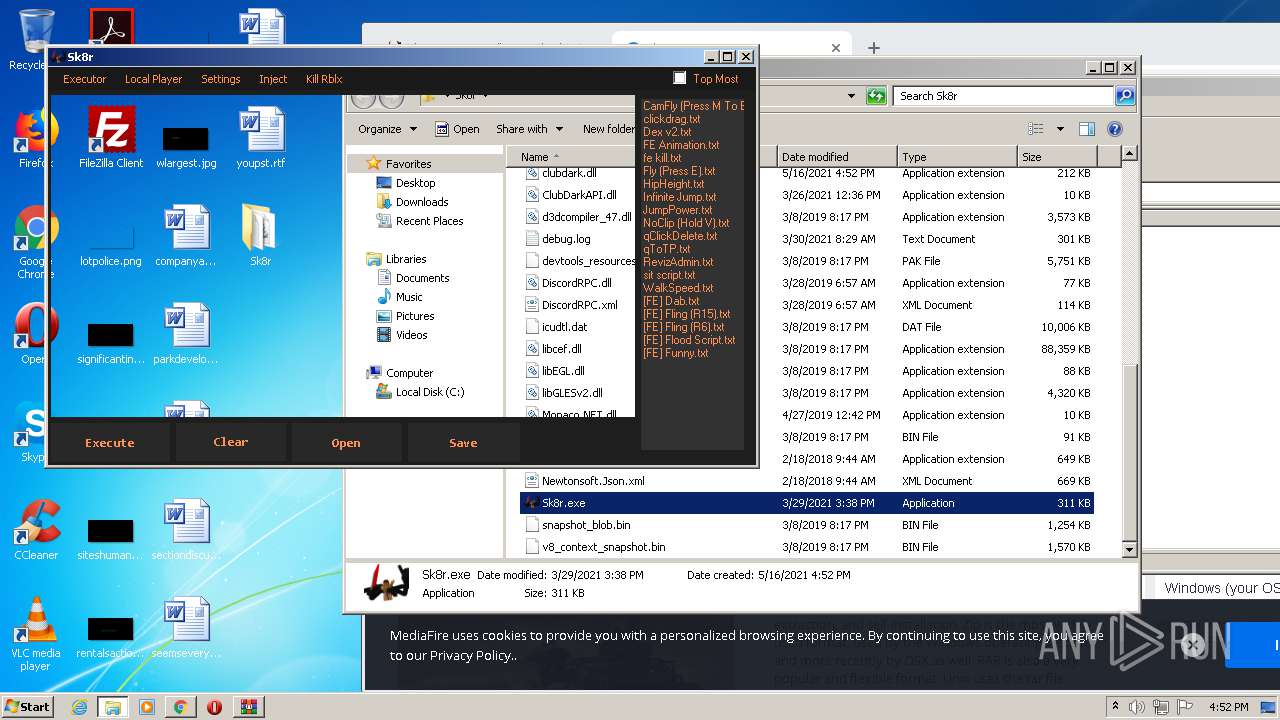
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2021, 15:49:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 13D1186F2C520CCB45649A7431D045BB |
| SHA1: | E9941C045C5305F7B5B3D78D3054FA39834B1830 |
| SHA256: | 3F3CAE7C98BC52ECF3E17B32148F57CF23626D04E447AB49FF8976155FA12890 |
| SSDEEP: | 3:N8UyFBKzXLJOXn:2UyOzX9OXn |
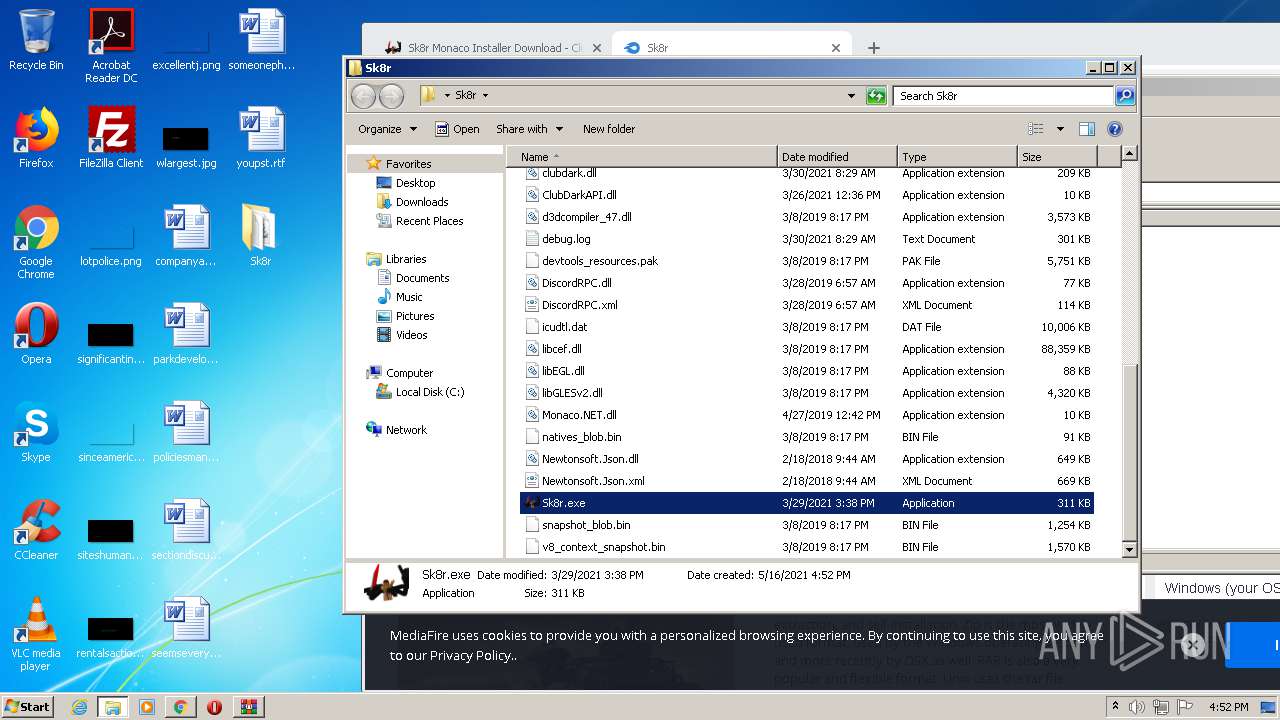
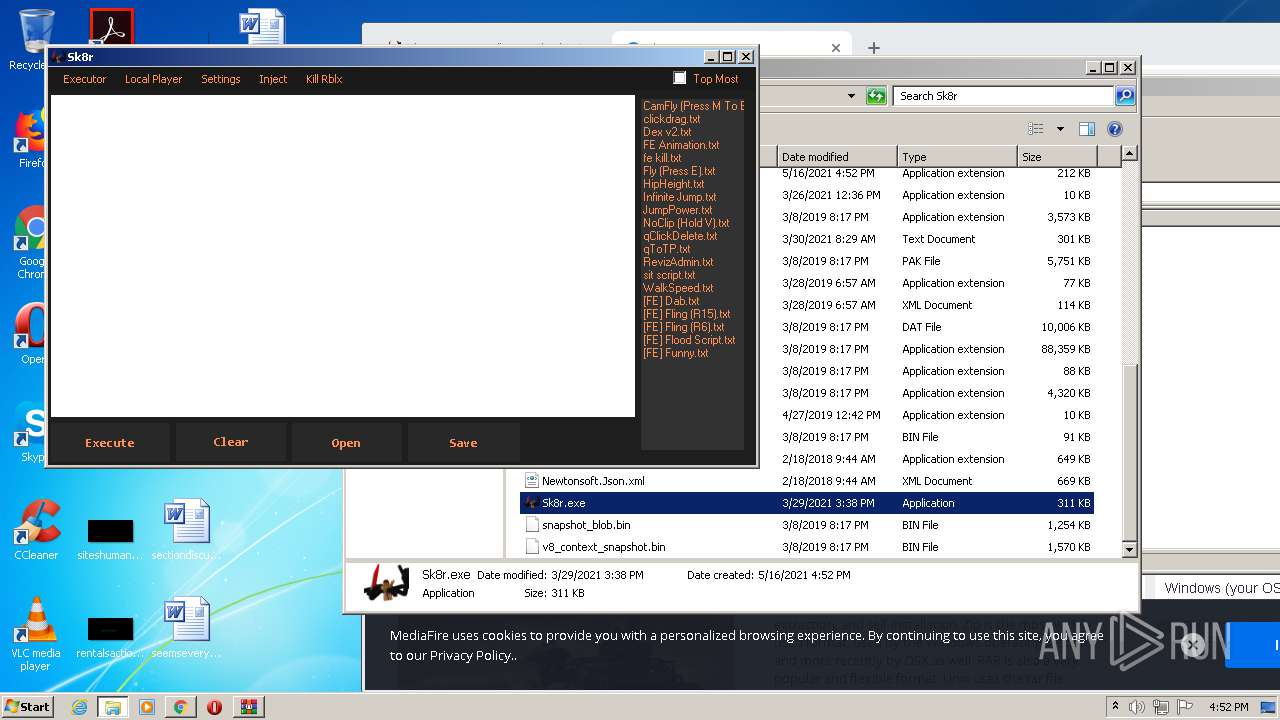
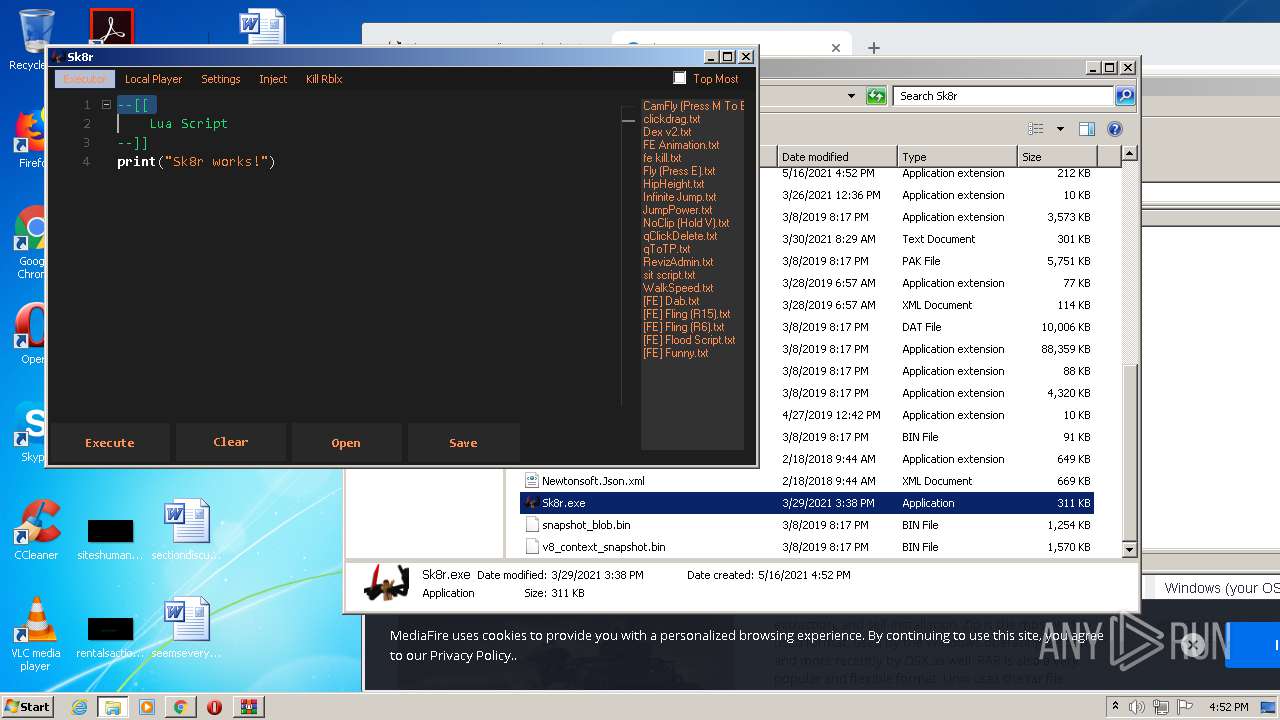
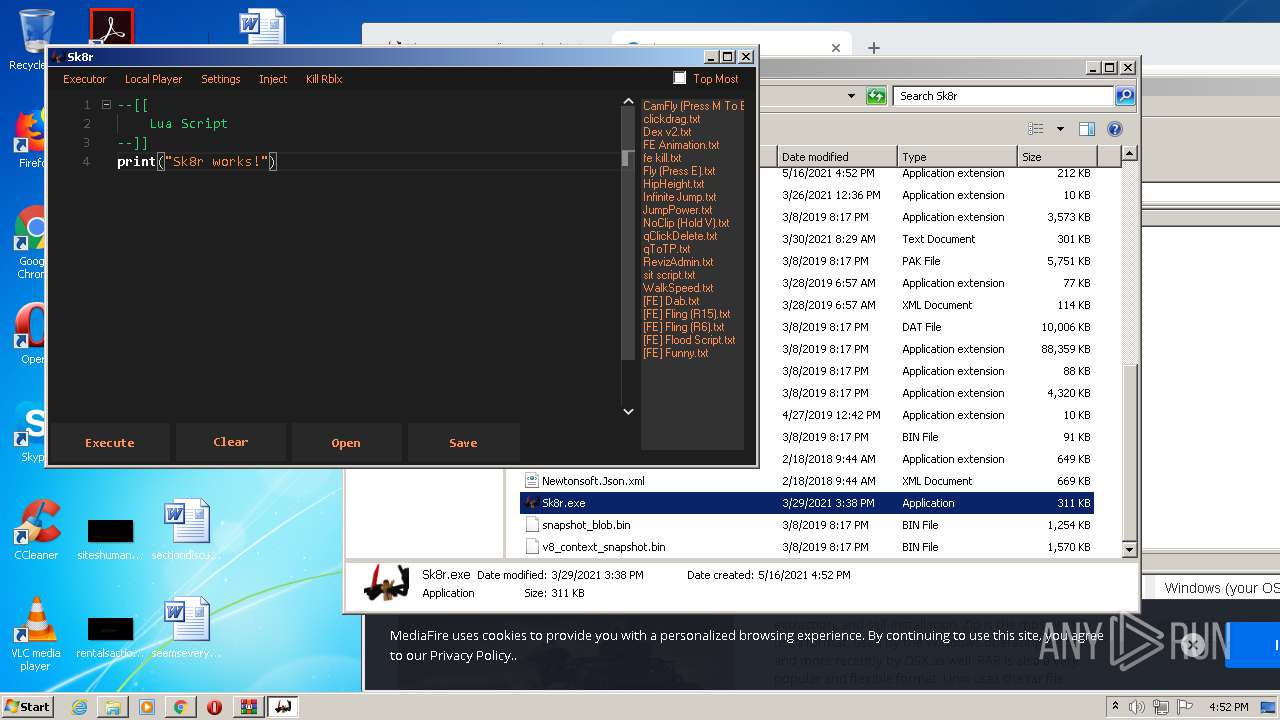
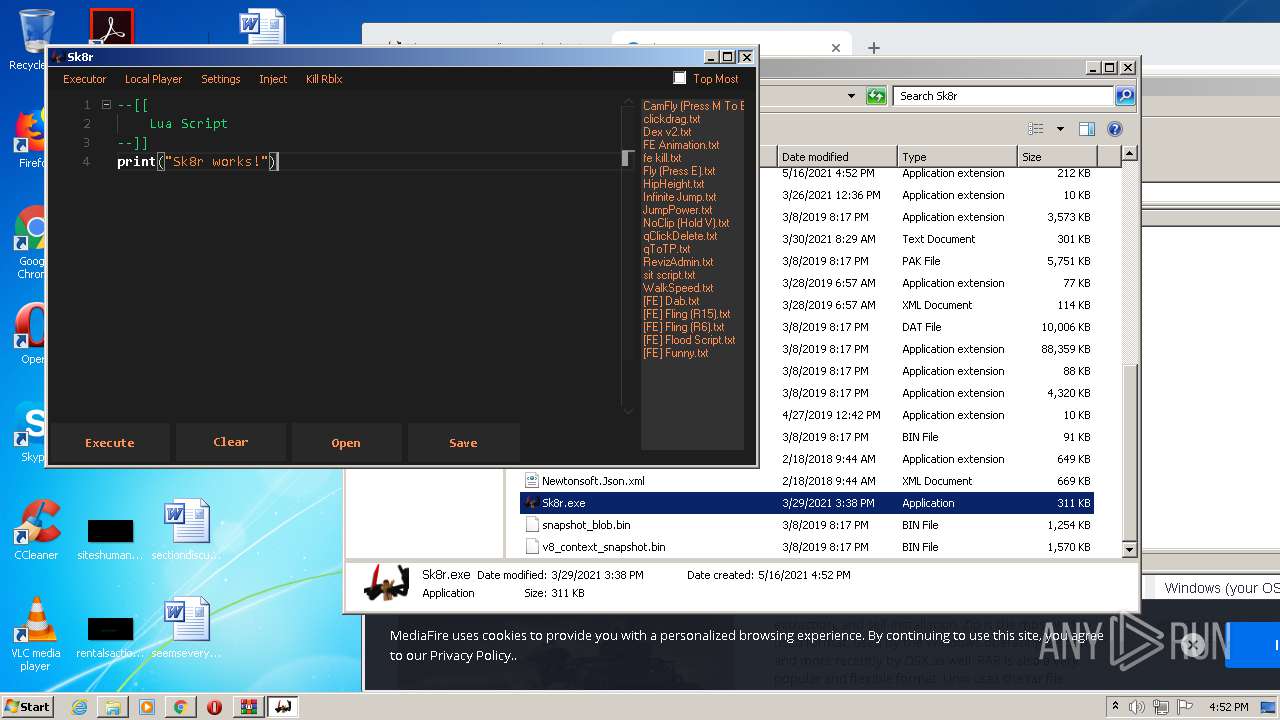
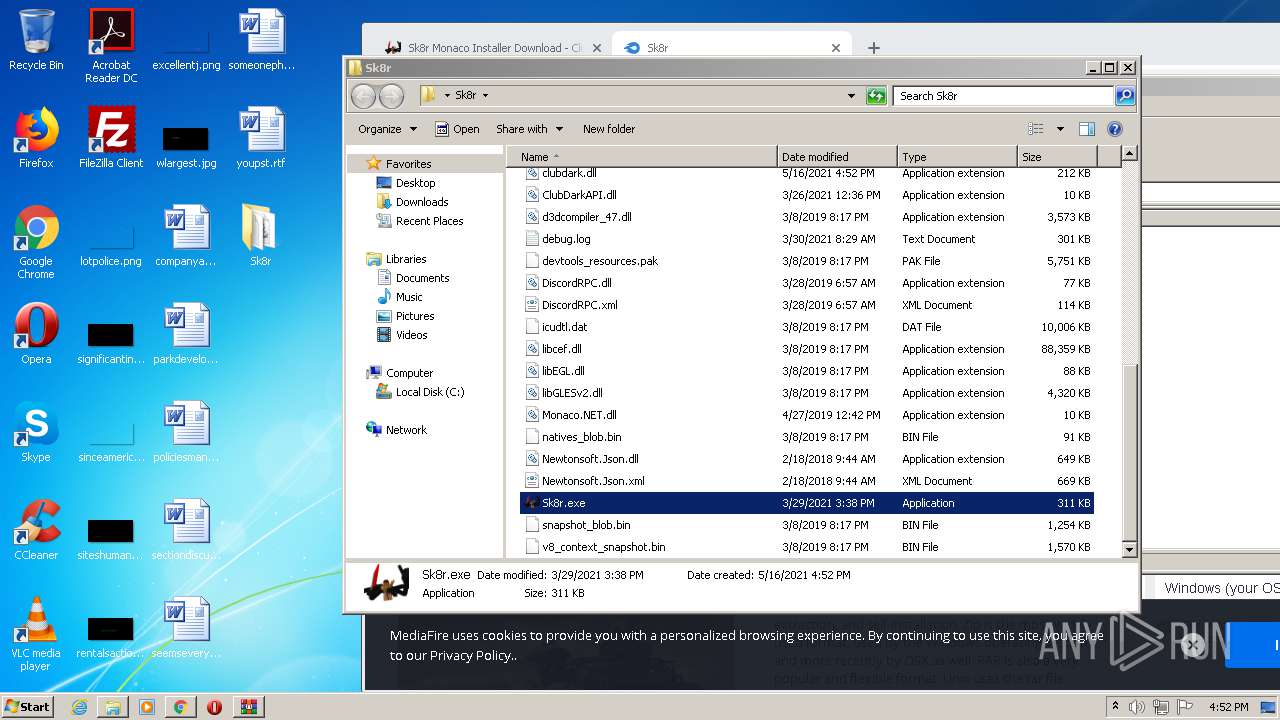
MALICIOUS
Loads dropped or rewritten executable
- Sk8r.exe (PID: 3736)
- CefSharp.BrowserSubprocess.exe (PID: 812)
- CefSharp.BrowserSubprocess.exe (PID: 3532)
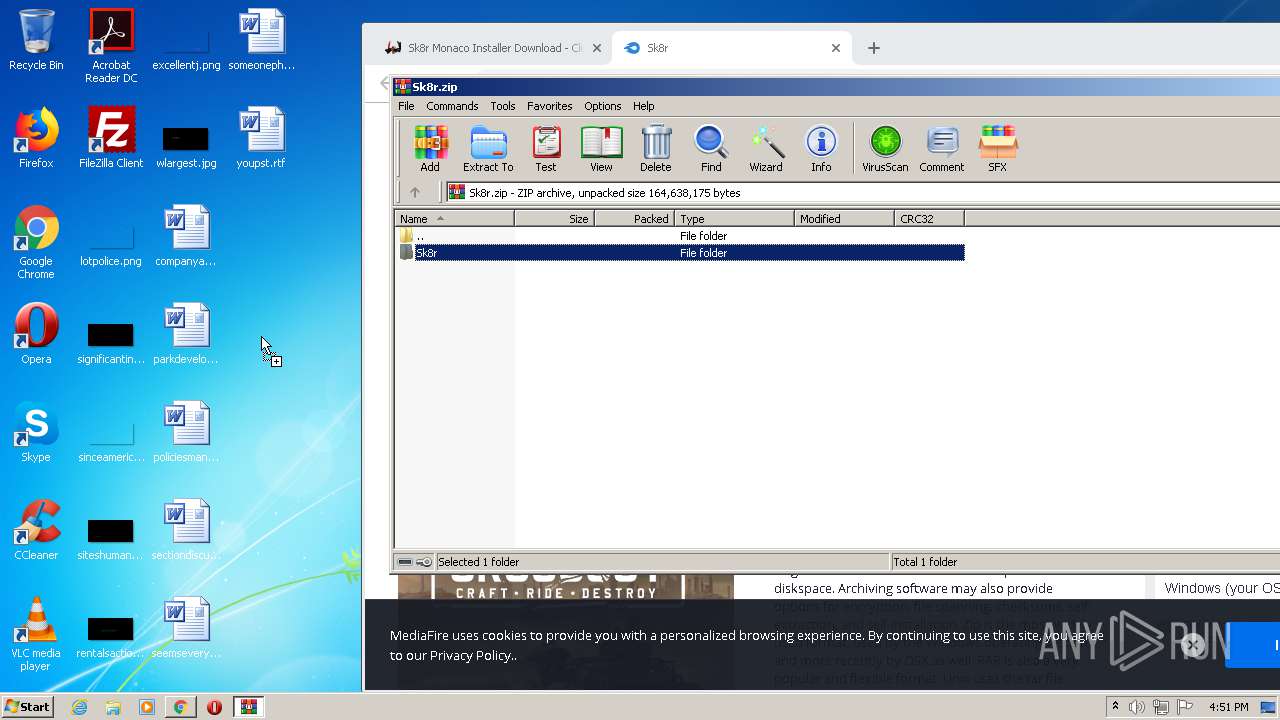
Application was dropped or rewritten from another process
- Sk8r.exe (PID: 3736)
- CefSharp.BrowserSubprocess.exe (PID: 812)
- CefSharp.BrowserSubprocess.exe (PID: 3532)
SUSPICIOUS
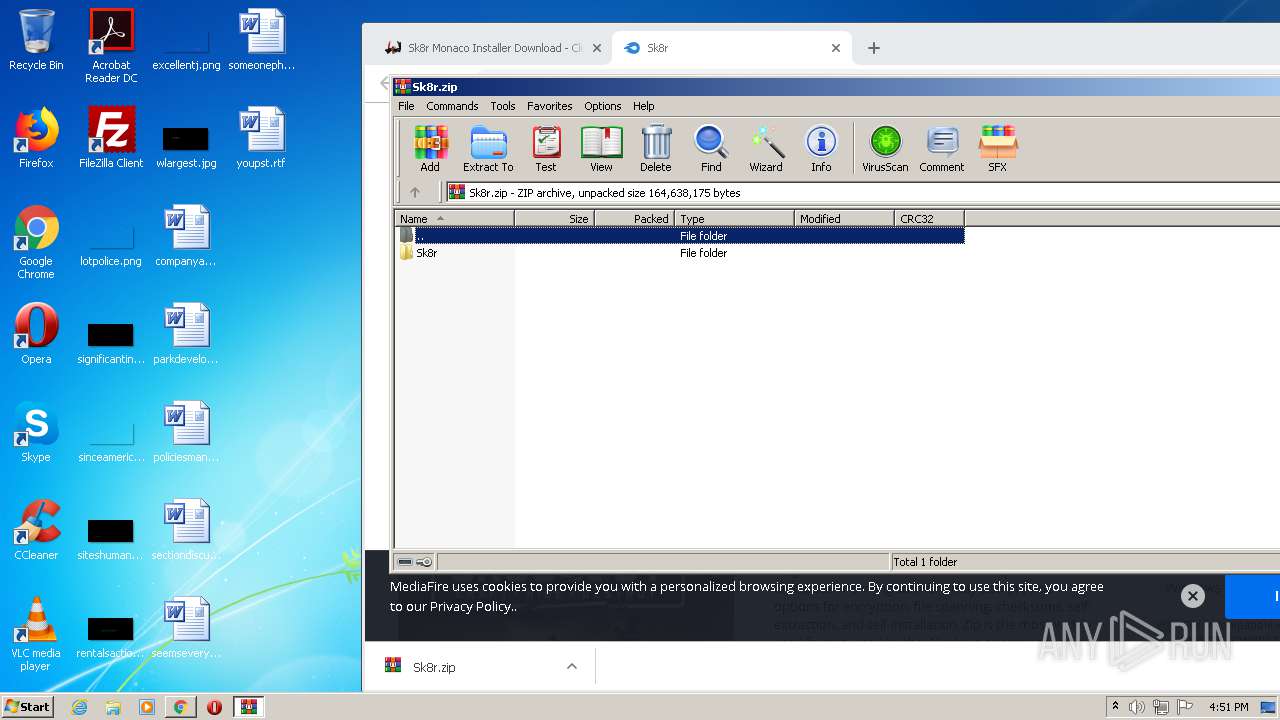
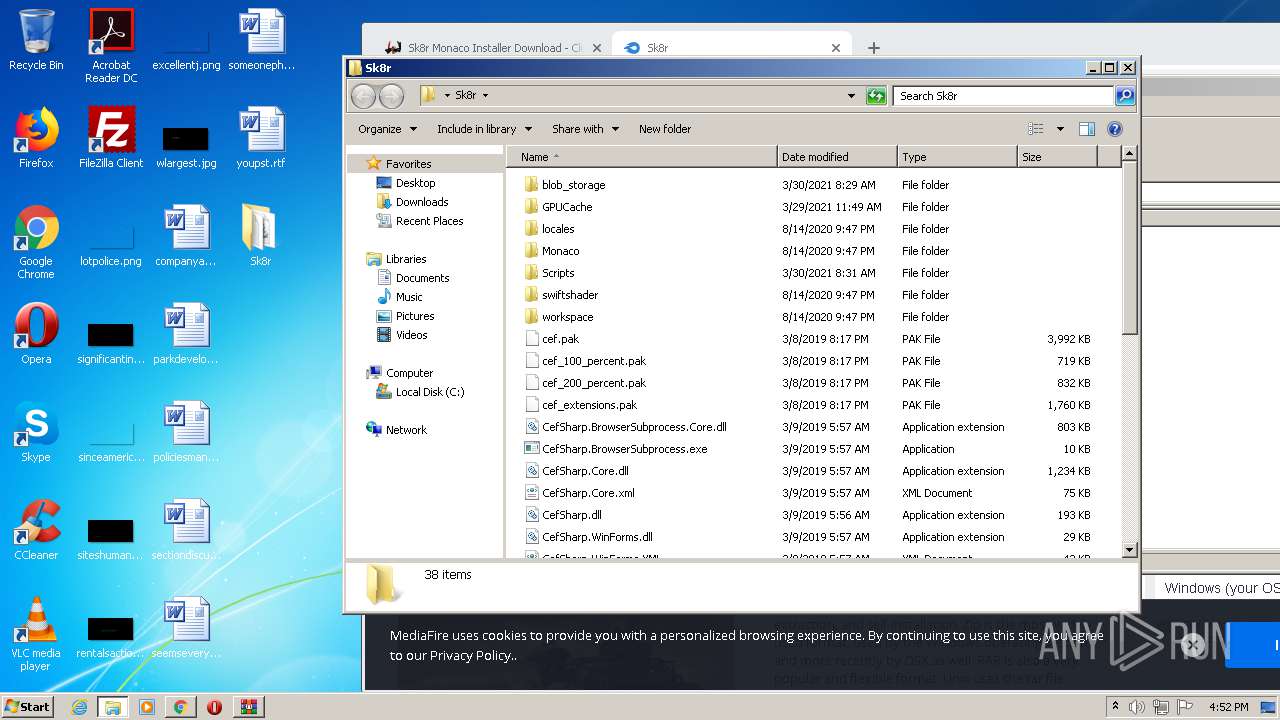
Drops a file with too old compile date
- WinRAR.exe (PID: 3204)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3204)
- Sk8r.exe (PID: 3736)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3204)
- Sk8r.exe (PID: 3736)
Drops a file with a compile date too recent
- Sk8r.exe (PID: 3736)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3808)
Reads the hosts file
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3808)
- Sk8r.exe (PID: 3736)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3204)
Manual execution by user
- Sk8r.exe (PID: 3736)
Application launched itself
- chrome.exe (PID: 1988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
50
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11298546102896630215 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17260328853611111475 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4253769107453779256 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6780381844742440900 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 812 | "C:\Users\admin\Desktop\Sk8r\CefSharp.BrowserSubprocess.exe" --type=gpu-process --field-trial-handle=1344,1041529274344772845,4241406593201378050,131072 --no-sandbox --log-file="C:\Users\admin\Desktop\Sk8r\debug.log" --lang=en-US --cefsharpexitsub --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --log-file="C:\Users\admin\Desktop\Sk8r\debug.log" --lang=en-US --cefsharpexitsub --service-request-channel-token=10265727310868602640 --mojo-platform-channel-handle=1408 /prefetch:2 --host-process-id=3736 --host-process-id=3736 | C:\Users\admin\Desktop\Sk8r\CefSharp.BrowserSubprocess.exe | — | Sk8r.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 71.0.2.0 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18241868191425507103 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5636 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5440282180128823809 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9174424451188228508 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1117562683132295179 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1902747855813284894,17236056058549652606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8392553158310630687 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 607
Read events
1 470
Write events
134
Delete events
3
Modification events
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1988-13265653758442875 |
Value: 259 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
18
Suspicious files
121
Text files
213
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60A13EFF-7C4.pma | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6fee6963-7d71-41fb-b909-dd9f435f0ad9.tmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf0594.TMP | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf0815.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
155
DNS requests
126
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3808 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3808 | chrome.exe | 104.21.70.89:443 | clubdark.net | Cloudflare Inc | US | unknown |
3808 | chrome.exe | 142.250.181.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3808 | chrome.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3808 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3808 | chrome.exe | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3808 | chrome.exe | 104.16.167.35:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
3808 | chrome.exe | 172.217.16.130:443 | partner.googleadservices.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 142.250.185.194:443 | adservice.google.co.uk | Google Inc. | US | suspicious |
3808 | chrome.exe | 142.250.185.130:443 | adservice.google.com | Google Inc. | US | suspicious |
3808 | chrome.exe | 142.250.186.66:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clubdark.net |
| suspicious |
accounts.google.com |
| shared |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.discordapp.com |
| shared |
ajax.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
js.stripe.com |
| shared |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3808 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3808 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |