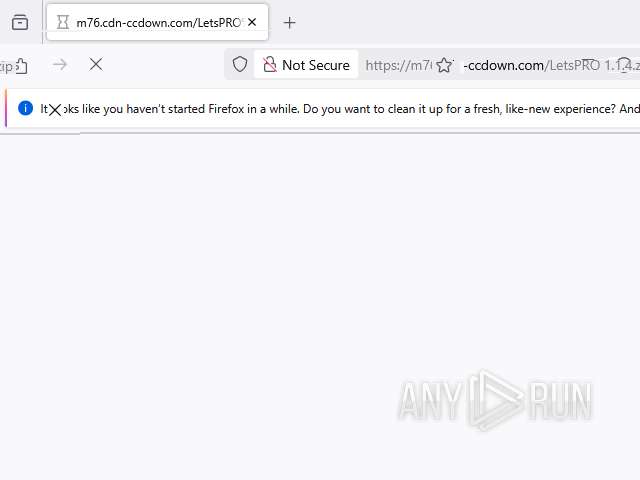
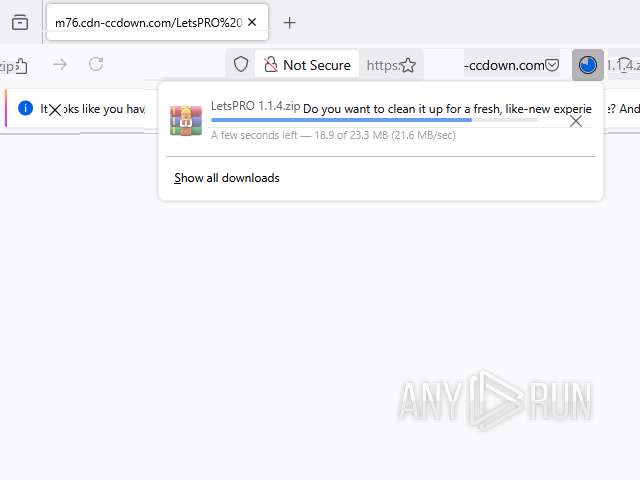
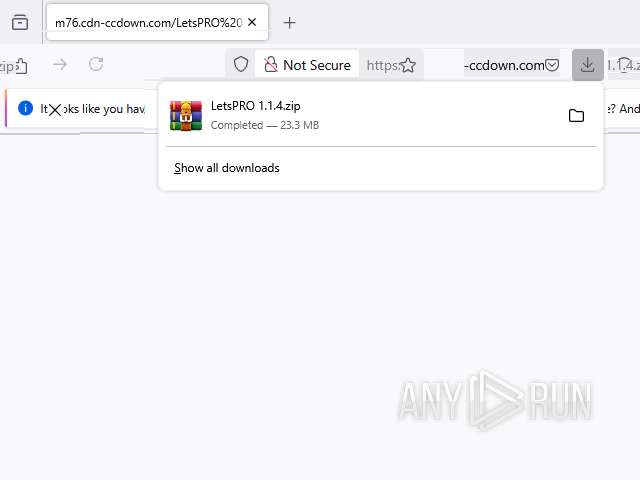
| URL: | https://m76.cdn-ccdown.com/LetsPRO%201.1.4.zip |
| Full analysis: | https://app.any.run/tasks/1f7c429d-35e3-4476-92d8-16fef83975b2 |
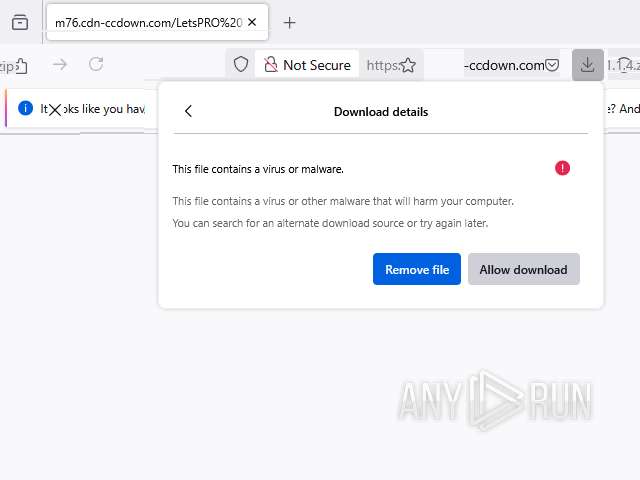
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2026, 01:19:53 |
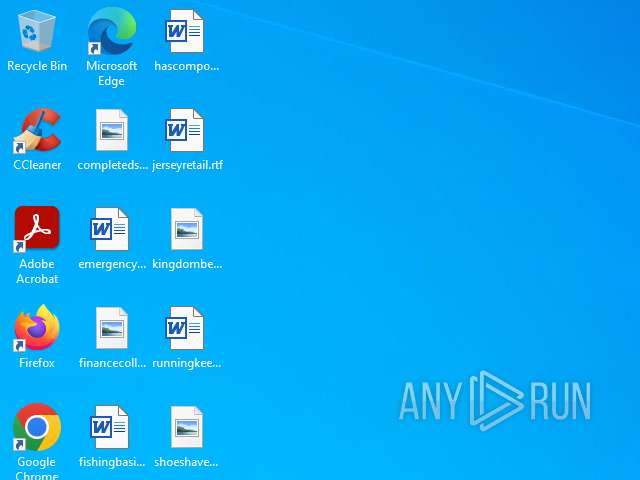
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BDE1124A4C99542B4B6ED101A415BF6C |
| SHA1: | 74B8E061C425A5B8753562B32BFF23664976E41B |
| SHA256: | 3F3AF41CFEC520DDDB978258ACCEC8F63C3A21103723317E834704B7AC7526E6 |
| SSDEEP: | 3:N8Q8RBv3JIyVSSq:2Bp3GGm |
MALICIOUS
Executing a file with an untrusted certificate
- Admin_Syllabu.exe (PID: 8220)
- Admin_Syllabu.exe (PID: 3160)
SUSPICIOUS
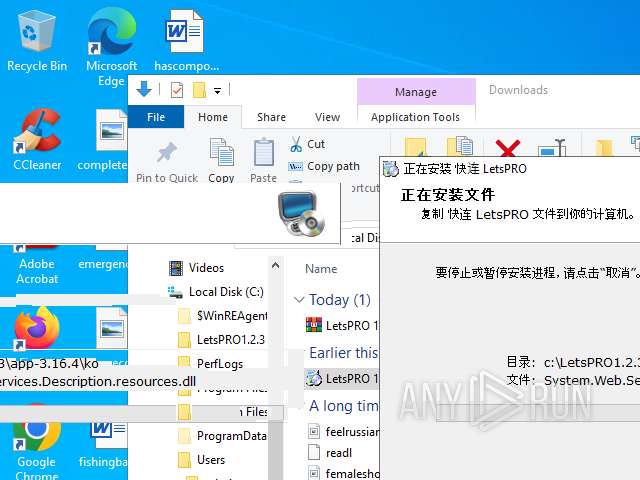
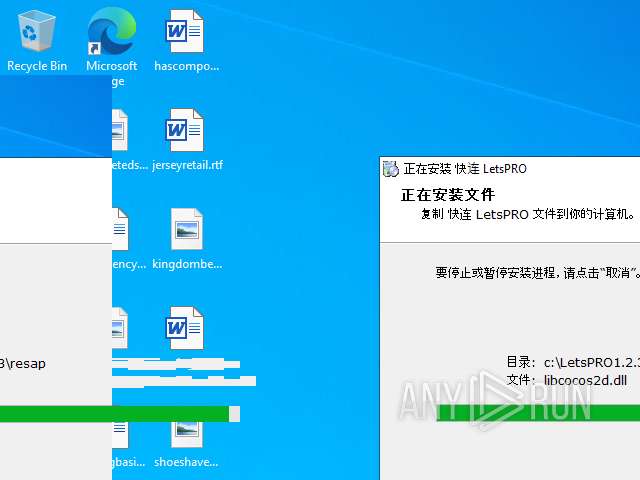
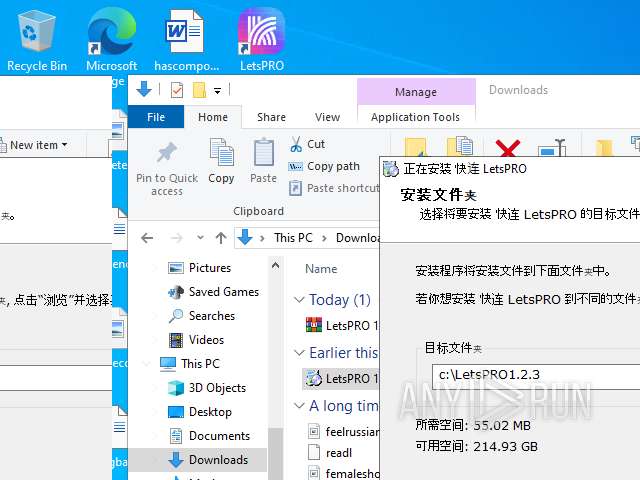
The process creates files with name similar to system file names
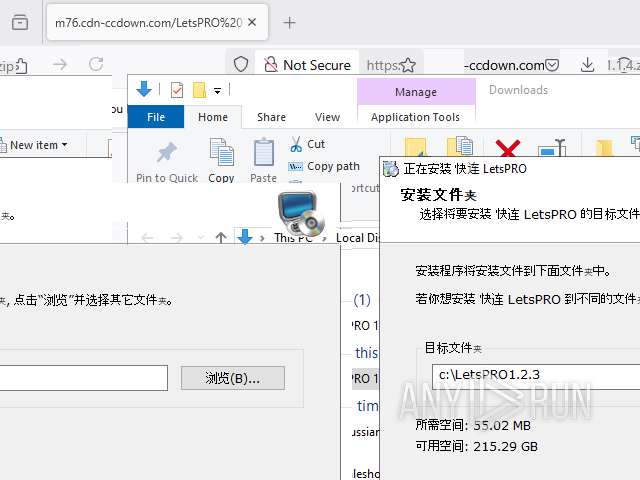
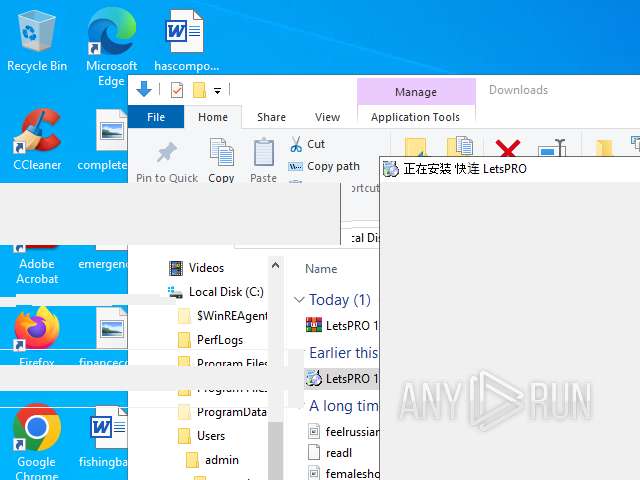
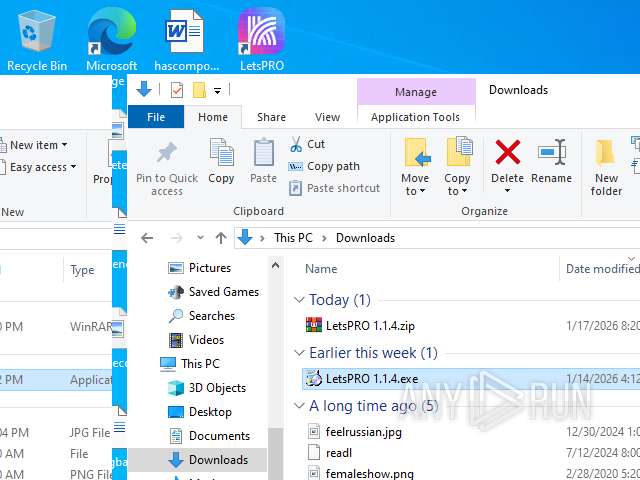
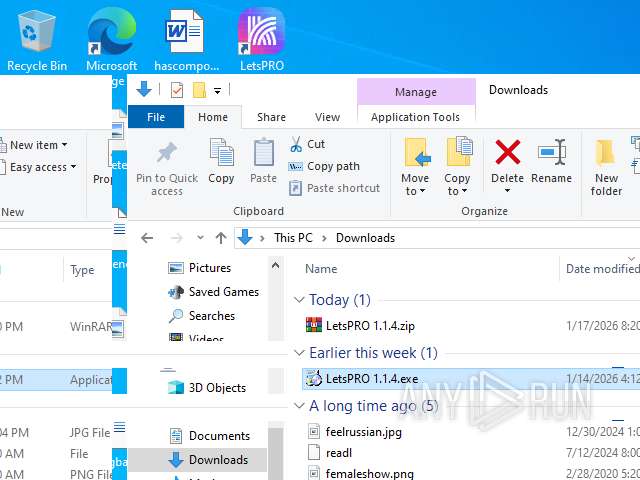
- LetsPRO 1.1.4.exe (PID: 8656)
Drops a system driver (possible attempt to evade defenses)
- LetsPRO 1.1.4.exe (PID: 8656)
- LetsPRO 1.1.4.exe (PID: 7144)
The process drops C-runtime libraries
- LetsPRO 1.1.4.exe (PID: 8656)
- LetsPRO 1.1.4.exe (PID: 7144)
Executing commands from a ".bat" file
- LetsPRO 1.1.4.exe (PID: 8656)
- LetsPRO 1.1.4.exe (PID: 7144)
Starts CMD.EXE for commands execution
- LetsPRO 1.1.4.exe (PID: 8656)
- LetsPRO 1.1.4.exe (PID: 7144)
Reads security settings of Internet Explorer
- Admin_Syllabu.exe (PID: 8220)
- Admin_Syllabu.exe (PID: 3160)
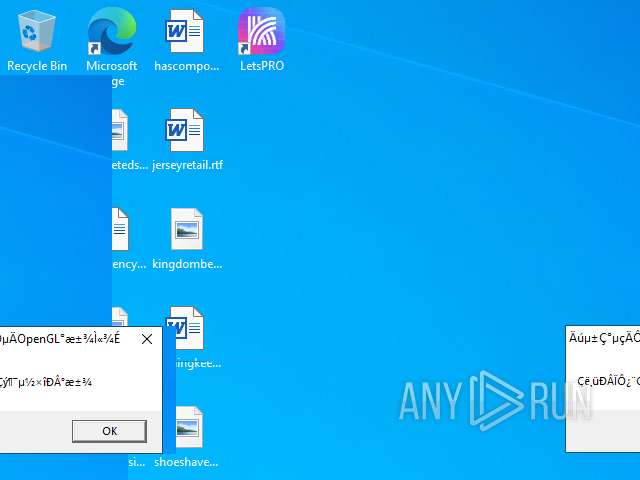
Executes application which crashes
- Admin_Syllabu.exe (PID: 8220)
- Admin_Syllabu.exe (PID: 3160)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4392)
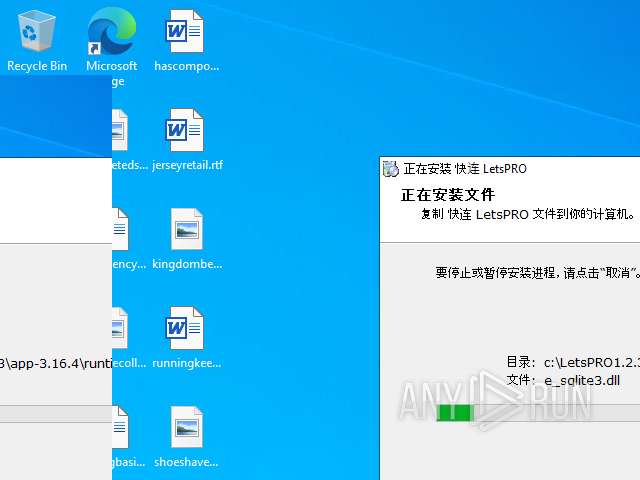
Executable content was dropped or overwritten
- LetsPRO 1.1.4.exe (PID: 7144)
- LetsPRO 1.1.4.exe (PID: 8656)
Process drops legitimate windows executable
- LetsPRO 1.1.4.exe (PID: 7144)
- LetsPRO 1.1.4.exe (PID: 8656)
INFO
Drops script file
- firefox.exe (PID: 7660)
- LetsPRO 1.1.4.exe (PID: 8656)
- cmd.exe (PID: 9040)
- LetsPRO 1.1.4.exe (PID: 7144)
- cmd.exe (PID: 6336)
Application launched itself
- firefox.exe (PID: 7568)
- firefox.exe (PID: 7660)
- msedge.exe (PID: 5900)
- msedge.exe (PID: 8428)
- msedge.exe (PID: 2952)
- msedge.exe (PID: 4128)
- msedge.exe (PID: 6692)
- msedge.exe (PID: 6596)
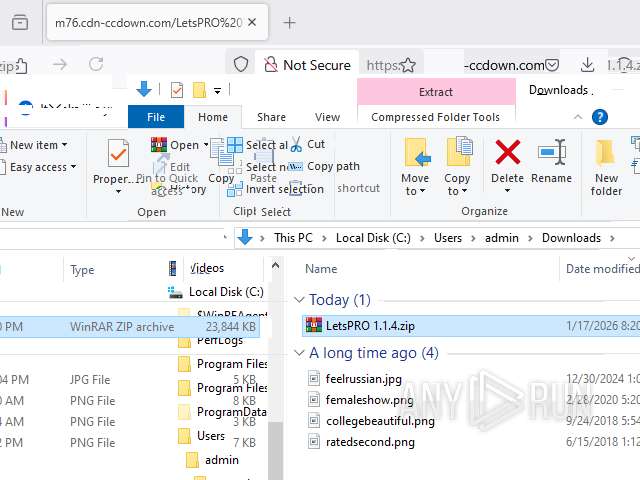
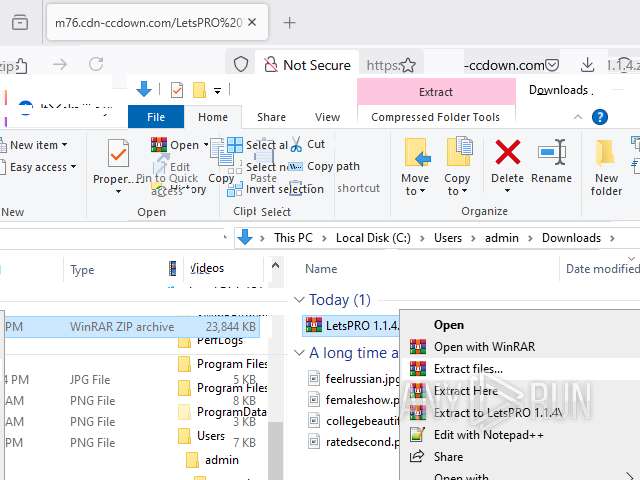
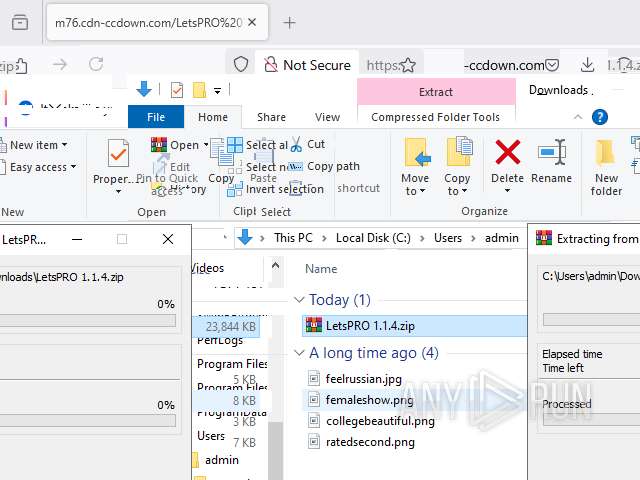
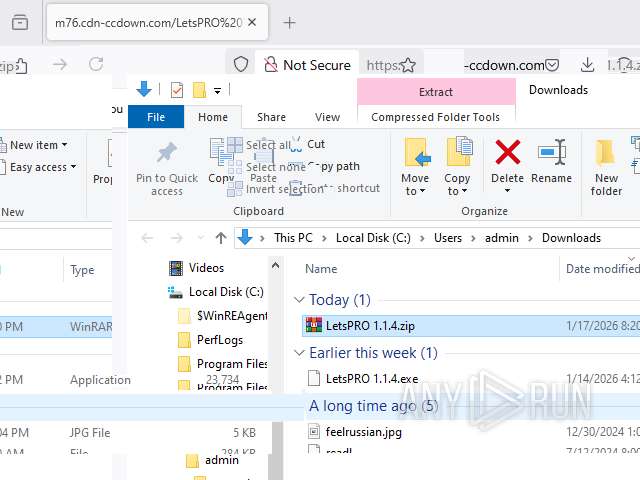
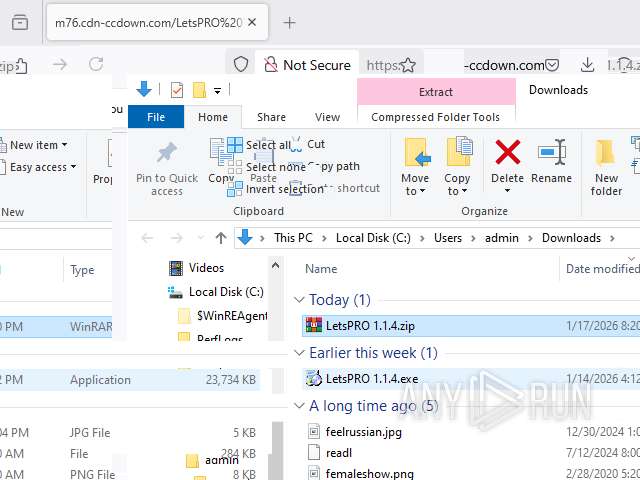
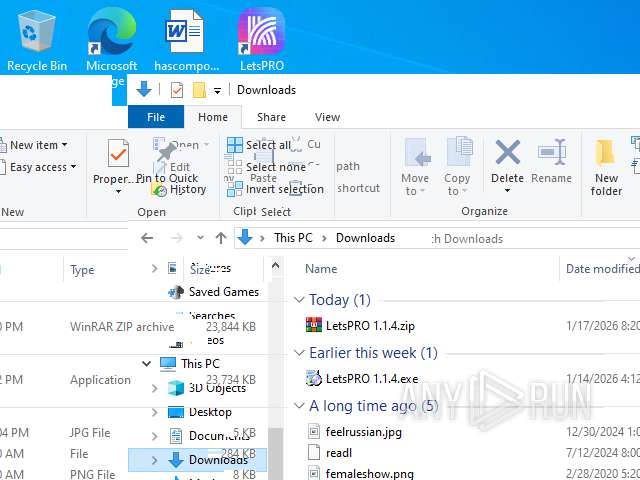
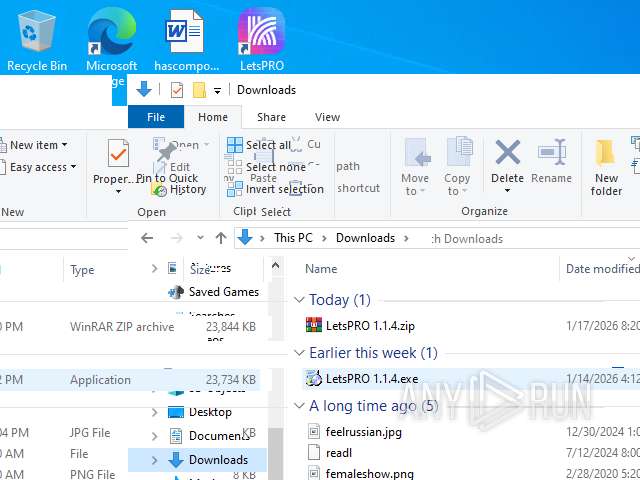
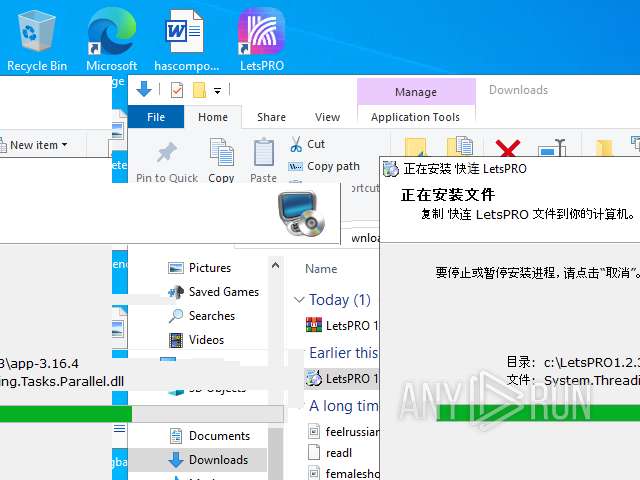
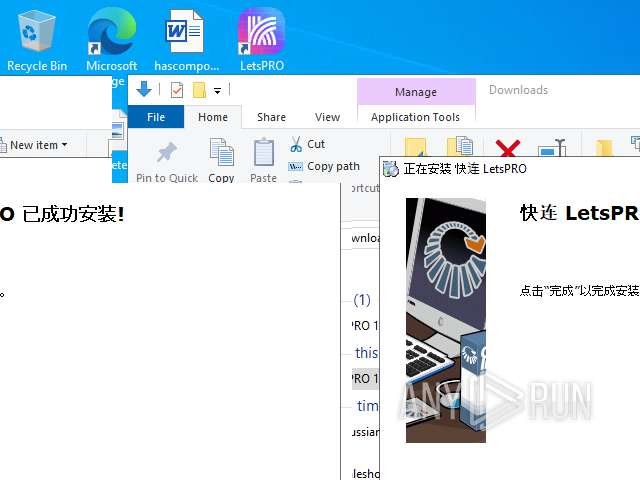
Launching a file from the Downloads directory
- firefox.exe (PID: 7660)
The sample compiled with english language support
- firefox.exe (PID: 7660)
- WinRAR.exe (PID: 8588)
- LetsPRO 1.1.4.exe (PID: 7144)
- LetsPRO 1.1.4.exe (PID: 8656)
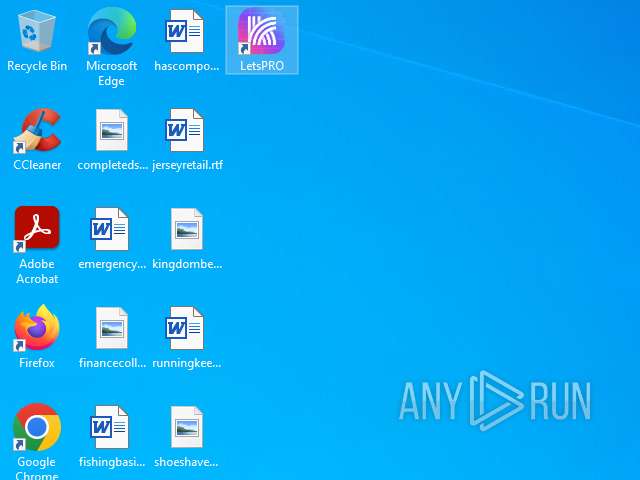
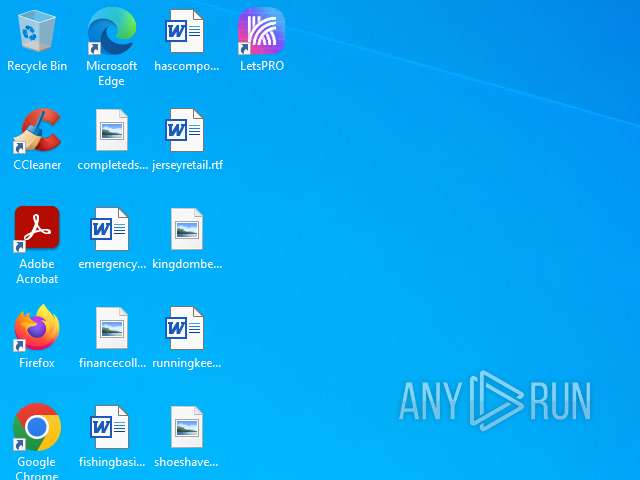
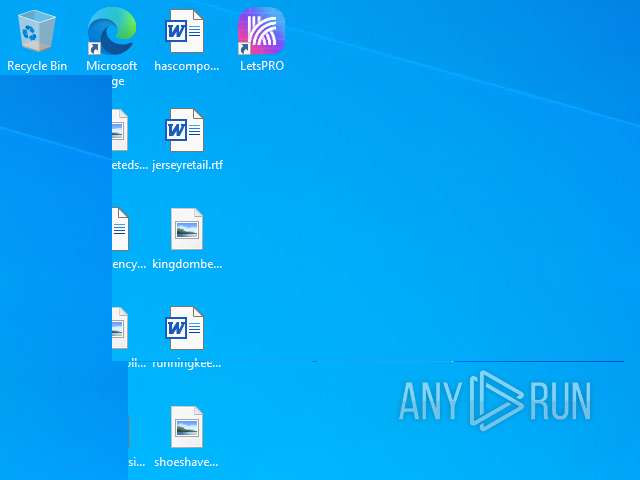
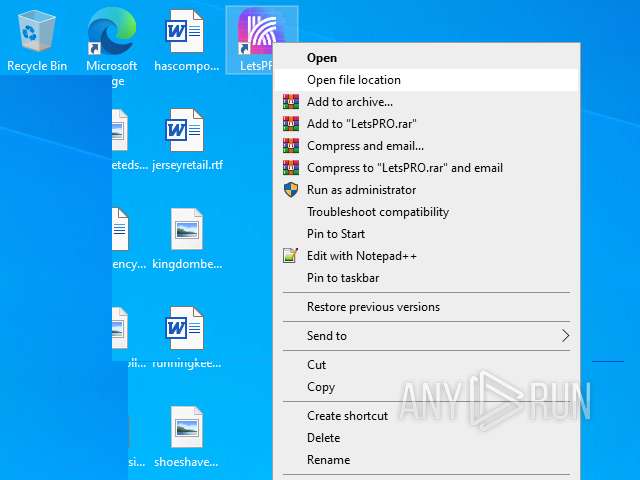
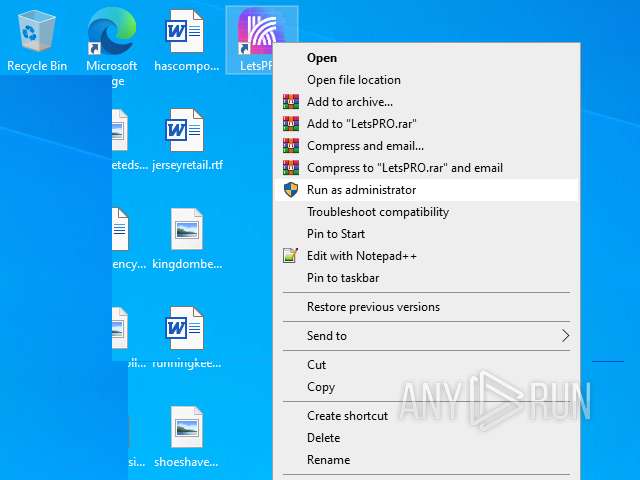
Manual execution by a user
- WinRAR.exe (PID: 8588)
- LetsPRO 1.1.4.exe (PID: 8656)
- Admin_Syllabu.exe (PID: 8220)
- LetsPRO 1.1.4.exe (PID: 7144)
- Admin_Syllabu.exe (PID: 3160)
- msedge.exe (PID: 6692)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8588)
Checks supported languages
- LetsPRO 1.1.4.exe (PID: 8656)
- Admin_Syllabu.exe (PID: 8220)
- TextInputHost.exe (PID: 8056)
- PLUGScheduler.exe (PID: 4392)
- LetsPRO 1.1.4.exe (PID: 7144)
- Admin_Syllabu.exe (PID: 3160)
- identity_helper.exe (PID: 7096)
Reads the computer name
- Admin_Syllabu.exe (PID: 8220)
- PLUGScheduler.exe (PID: 4392)
- TextInputHost.exe (PID: 8056)
- LetsPRO 1.1.4.exe (PID: 7144)
- Admin_Syllabu.exe (PID: 3160)
- identity_helper.exe (PID: 7096)
- LetsPRO 1.1.4.exe (PID: 8656)
Creates files or folders in the user directory
- WerFault.exe (PID: 8464)
- WerFault.exe (PID: 6240)
Checks proxy server information
- WerFault.exe (PID: 8464)
- WerFault.exe (PID: 6240)
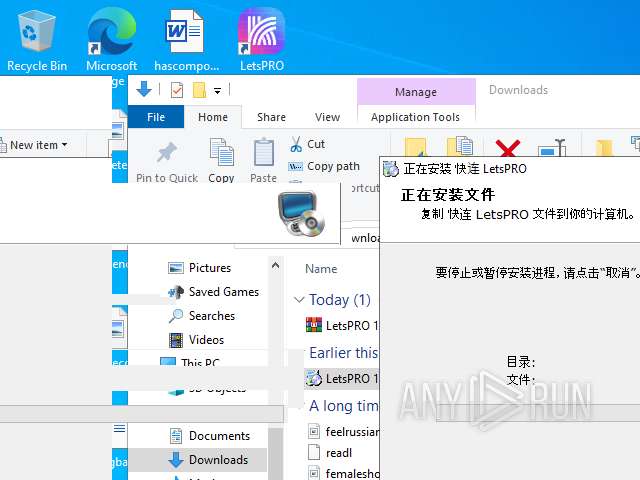
Creates files in the program directory
- PLUGScheduler.exe (PID: 4392)
Create files in a temporary directory
- LetsPRO 1.1.4.exe (PID: 7144)
- LetsPRO 1.1.4.exe (PID: 8656)
The sample compiled with chinese language support
- LetsPRO 1.1.4.exe (PID: 7144)
- LetsPRO 1.1.4.exe (PID: 8656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
378
Monitored processes
71
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4592 -prefsLen 45116 -prefMapHandle 4596 -prefMapSize 273045 -ipcHandle 4456 -initialChannelId {bcd028d8-f6ff-4a75-bbb7-5b718dc006ca} -parentPid 7660 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7660" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 136.0 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5412 -prefsLen 39120 -prefMapHandle 5416 -prefMapSize 273045 -jsInitHandle 5420 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5428 -initialChannelId {96b2235c-0ef8-4554-b397-e457bf564934} -parentPid 7660 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7660" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2236,i,3964412116924144475,7239403416167251320,262144 --variations-seed-version --mojo-platform-channel-handle=2364 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3440,i,12651657176698292413,5583057058370283537,262144 --variations-seed-version --mojo-platform-channel-handle=3536 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2244,i,13521067863176109339,300453768928364245,262144 --variations-seed-version --mojo-platform-channel-handle=2472 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1560 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4768,i,12651657176698292413,5583057058370283537,262144 --variations-seed-version --mojo-platform-channel-handle=4788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3564,i,13521067863176109339,300453768928364245,262144 --variations-seed-version --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5176,i,14588601615884558190,12924641024415824021,262144 --variations-seed-version --mojo-platform-channel-handle=4916 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3572,i,13521067863176109339,300453768928364245,262144 --variations-seed-version --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x264,0x268,0x26c,0x260,0x274,0x7ffe8fcff208,0x7ffe8fcff214,0x7ffe8fcff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
9 462
Read events
9 443
Write events
16
Delete events
3
Modification events
| (PID) Process: | (8588) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8588) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8588) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8588) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8220) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8220) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8220) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3160) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3160) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3160) Admin_Syllabu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
465
Suspicious files
412
Text files
313
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7660 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2055FB2CF8196AB8389BB6B2F0B324CC | SHA256:80706806FC8C02828745CCC5E8096211487CDD379F129537B62F95B28DC40240 | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json | text | |
MD5:88B0EAD66649771200E10D87CFFC1EE7 | SHA256:CD7A5D9CC40625DEB0C00E952DC554F0F96588DF4BBD6C33B5BD79E322BE7D9F | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2055FB2CF8196AB8389BB6B2F0B324CC | SHA256:80706806FC8C02828745CCC5E8096211487CDD379F129537B62F95B28DC40240 | |||
| 7660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
183
TCP/UDP connections
132
DNS requests
149
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7660 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | unknown | — | — | unknown |
7660 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | unknown |
7660 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
7660 | firefox.exe | POST | 200 | 142.251.140.163:80 | http://o.pki.goog/s/wr3/peI | unknown | — | — | whitelisted |
7660 | firefox.exe | POST | 200 | 142.251.140.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7660 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-11-08-08-20-52.chain | unknown | text | 5.18 Kb | unknown |
7660 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-11-08-08-20-52.chain | unknown | text | 5.18 Kb | unknown |
7660 | firefox.exe | GET | 200 | 34.36.137.203:443 | https://contile.services.mozilla.com/v1/tiles | unknown | text | 5.07 Kb | unknown |
7660 | firefox.exe | GET | 200 | 188.114.97.3:443 | https://m76.cdn-ccdown.com/LetsPRO%201.1.4.zip | unknown | compressed | 128 Kb | unknown |
7660 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4828 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4680 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7660 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7660 | firefox.exe | 188.114.97.3:443 | m76.cdn-ccdown.com | CLOUDFLARENET | US | whitelisted |
7660 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7660 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7660 | firefox.exe | 151.101.65.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
m76.cdn-ccdown.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Attempted Information Leak | HUNTING [ANY.RUN] Host CPU Enumeration observed in outbound connection |
— | — | Attempted Information Leak | HUNTING [ANY.RUN] Host CPU Enumeration observed in outbound connection |