| URL: | https://studiobariani-my.sharepoint.com/:o:/g/personal/marta_bussola_studiobariani_eu/EubxEOTLdJ9Is1QZ0nsdXygBnNXbi0qtkxYbqBQDKKnB2A?e=TrpVsL |
| Full analysis: | https://app.any.run/tasks/9dfbb495-6afc-4b4c-9c2d-7d7029f279ae |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 01:03:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B78C680E2FACCD65B31D5FB474F700DE |
| SHA1: | 87333920BF0C7EC870D8B798DC401244F48E15E8 |
| SHA256: | 3F225E58377D99D88C53B028CEB82565964D90634E7A1D9984FC5F0F9B17AEEC |
| SSDEEP: | 3:N8cV1X1iQArL5+KVFSIuTqNRQBoXuiK3UtcztMB+HHbTAY+pn:2cHwQAfNsTqNRUoeicmcMB+H7T9Wn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2456)
INFO
Application launched itself
- iexplore.exe (PID: 2212)
Reads settings of System Certificates
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 2212)
Reads the computer name
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 2456)
- opera.exe (PID: 288)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2212)
Checks supported languages
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 2212)
- opera.exe (PID: 288)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Reads internet explorer settings
- iexplore.exe (PID: 2456)
Checks Windows Trust Settings
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 2212)
Changes settings of System certificates
- iexplore.exe (PID: 2212)
Check for Java to be installed
- opera.exe (PID: 288)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2456)
- opera.exe (PID: 288)
Creates files in the user directory
- iexplore.exe (PID: 2456)
- opera.exe (PID: 288)
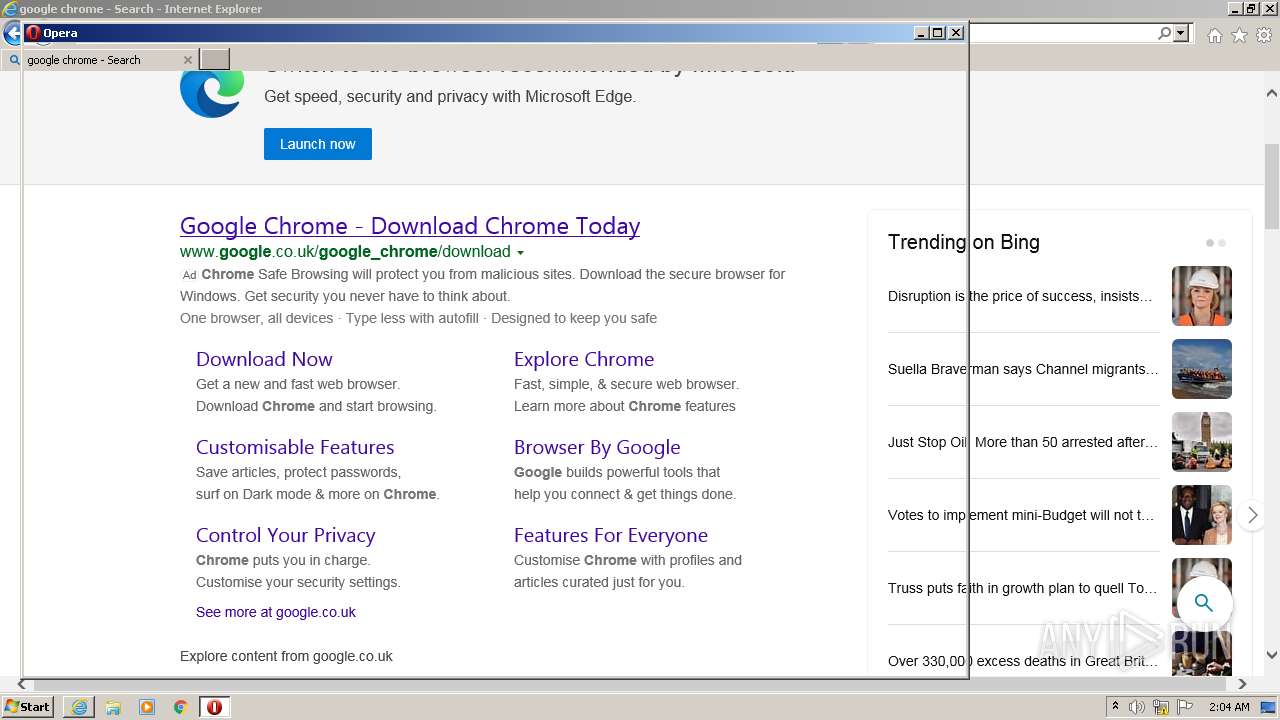
Manual execution by user
- opera.exe (PID: 288)
Reads the date of Windows installation
- opera.exe (PID: 288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
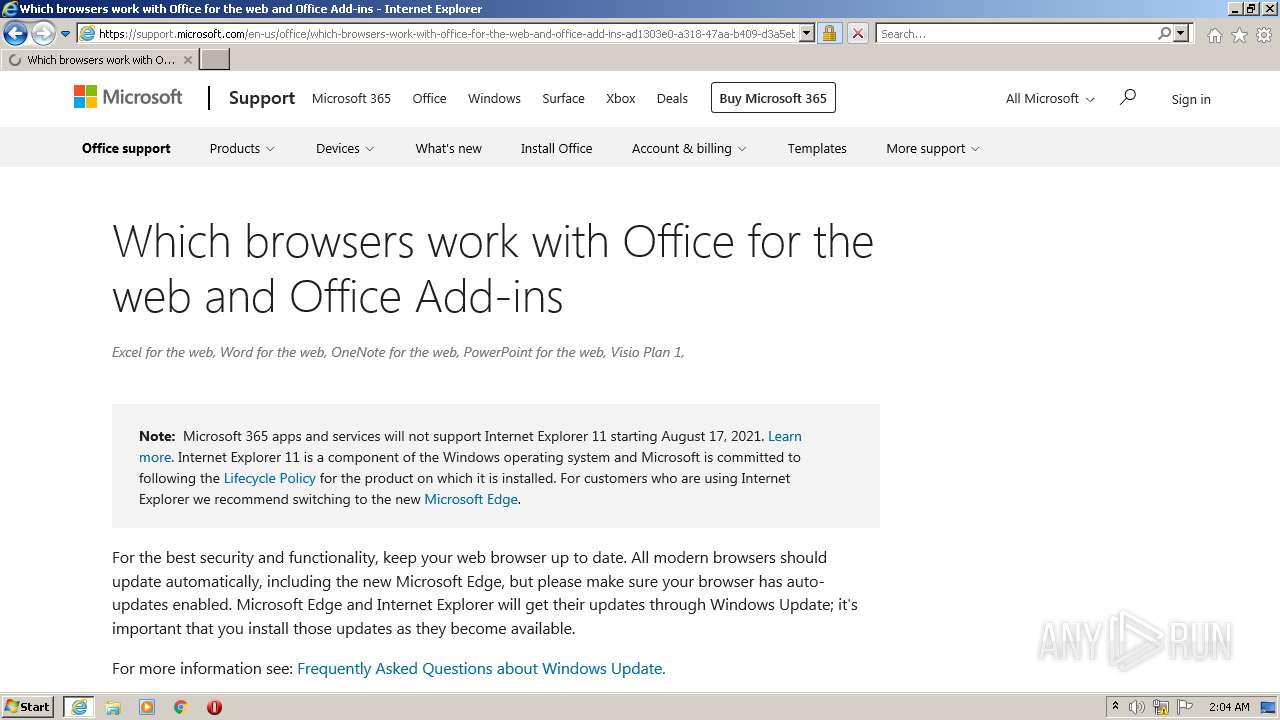
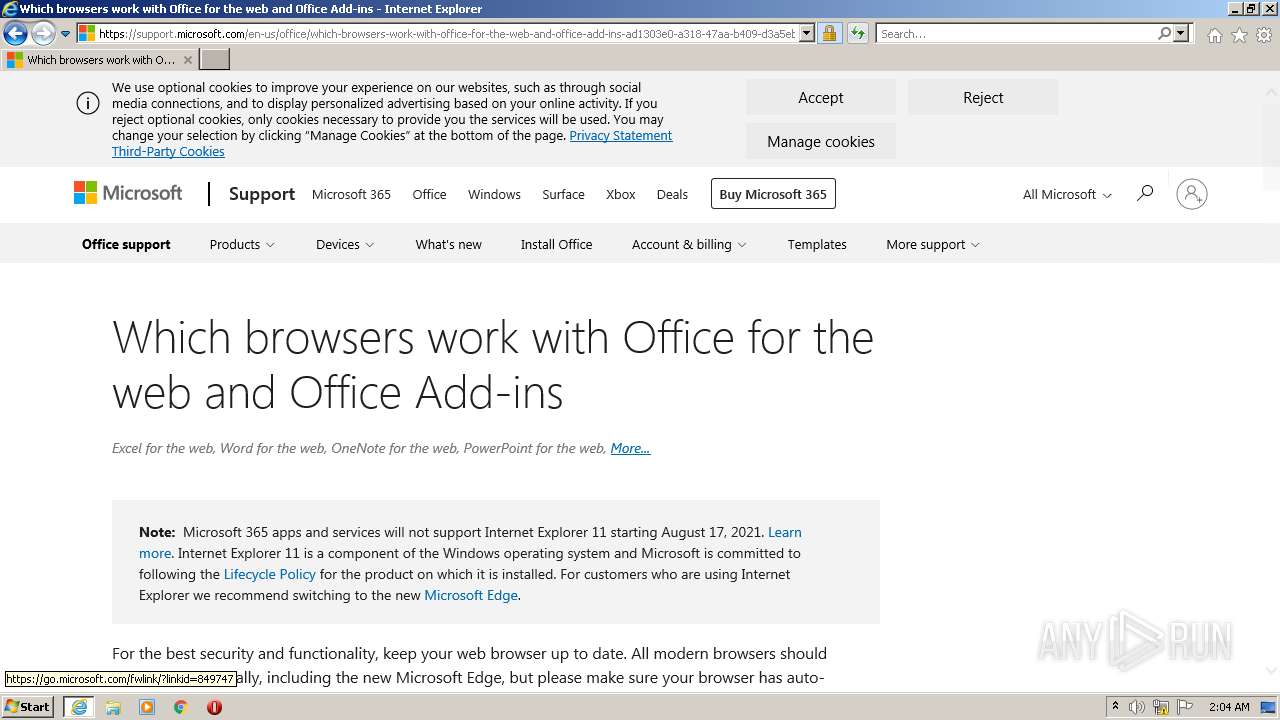
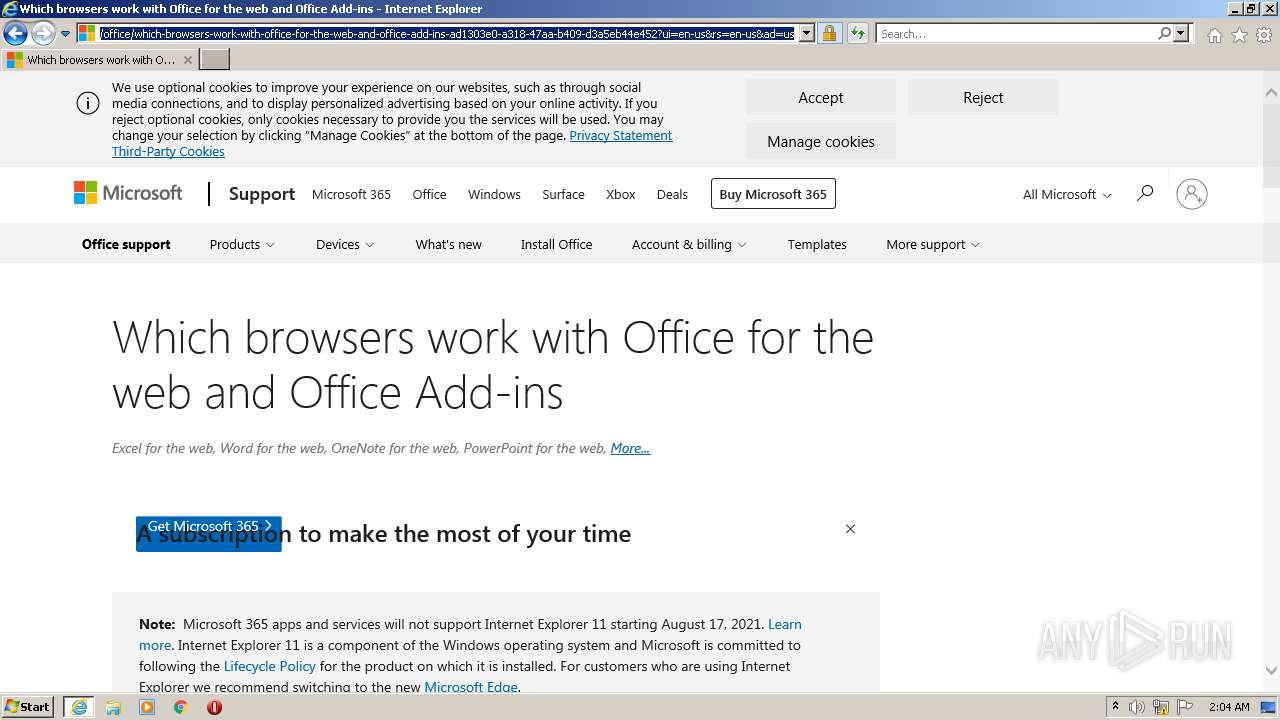
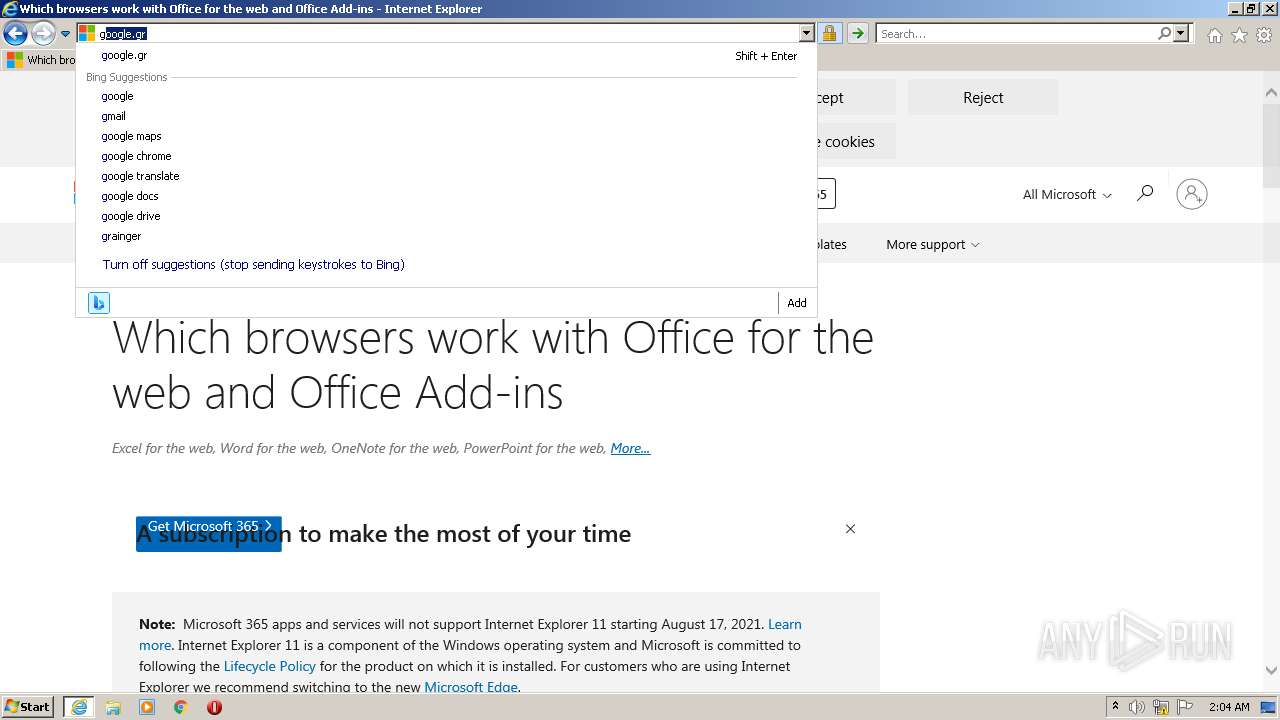
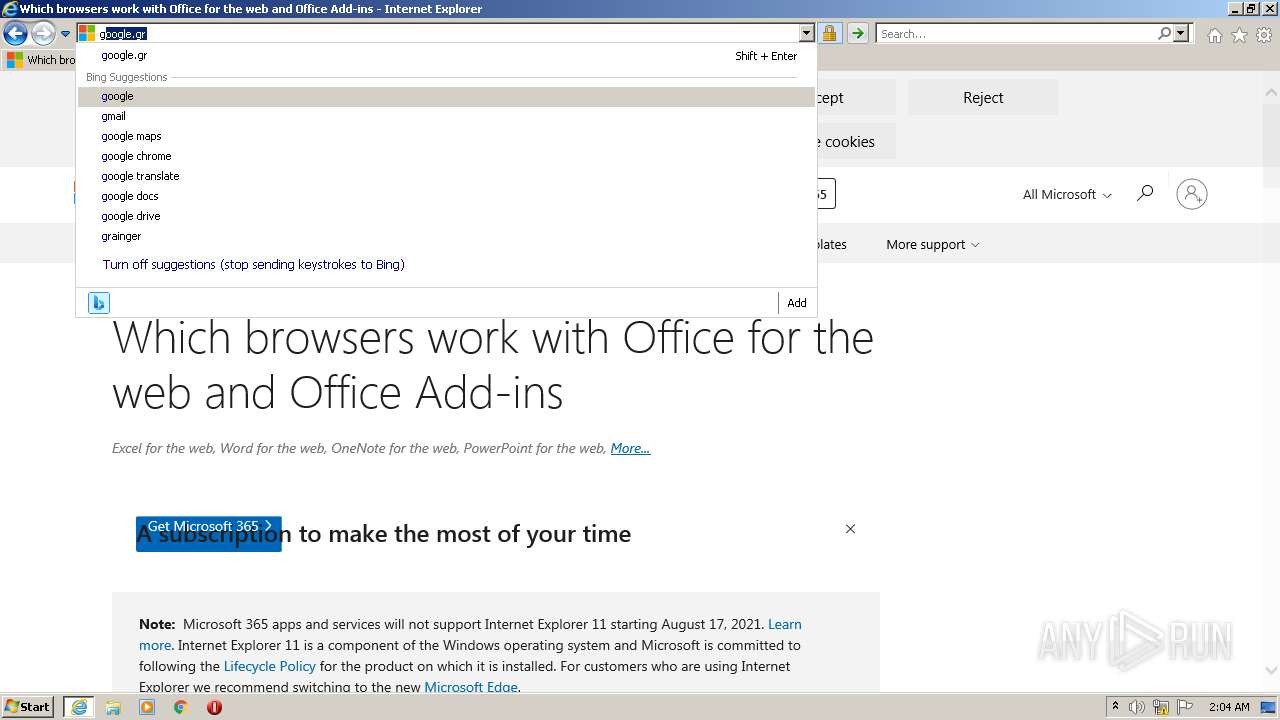
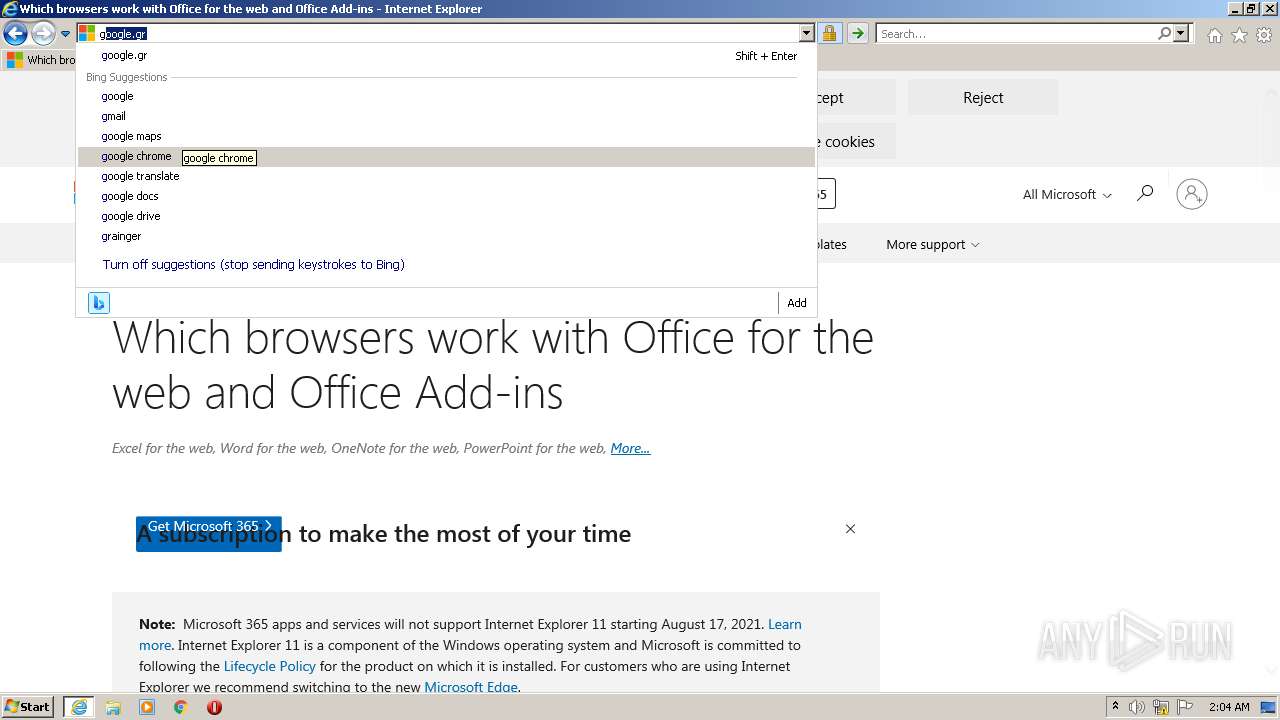
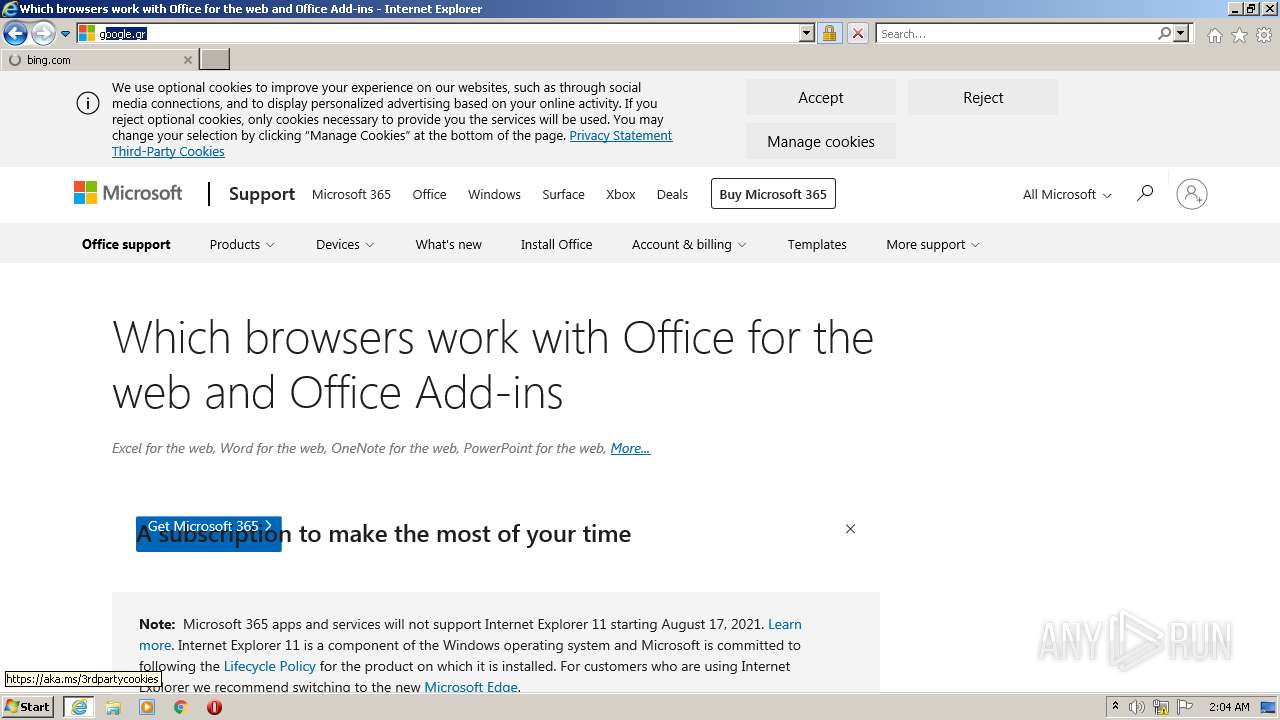
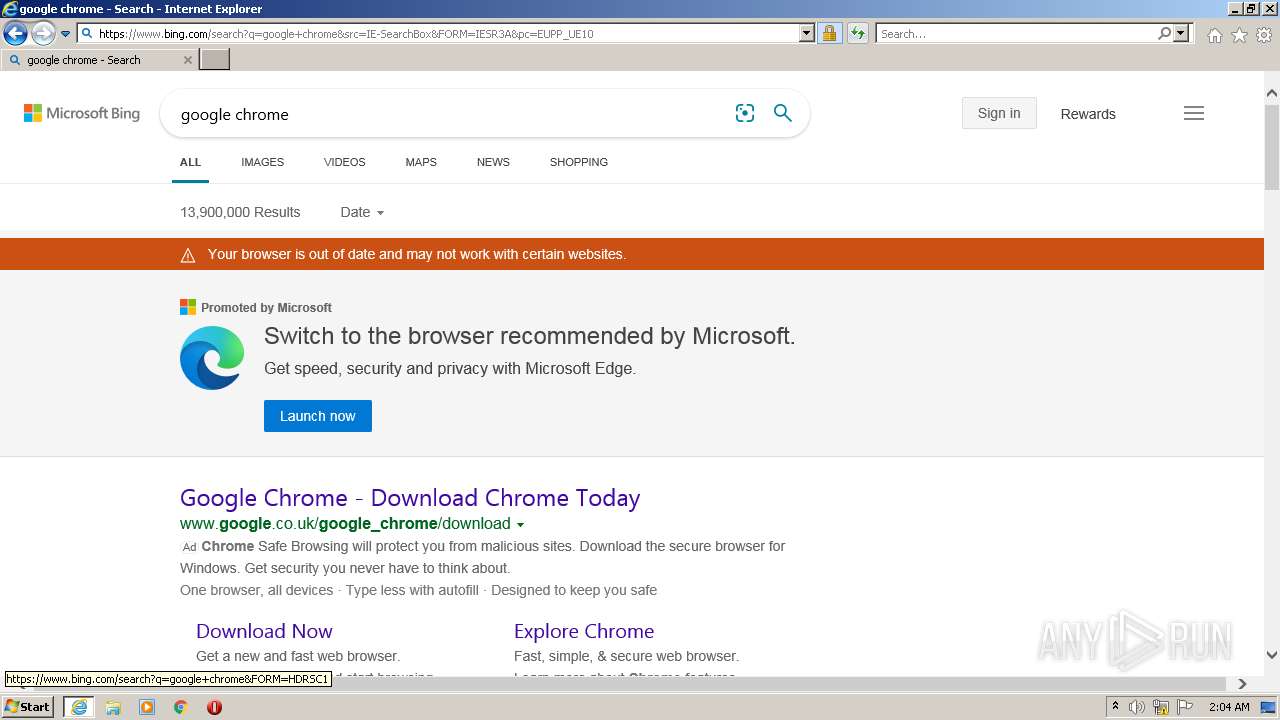
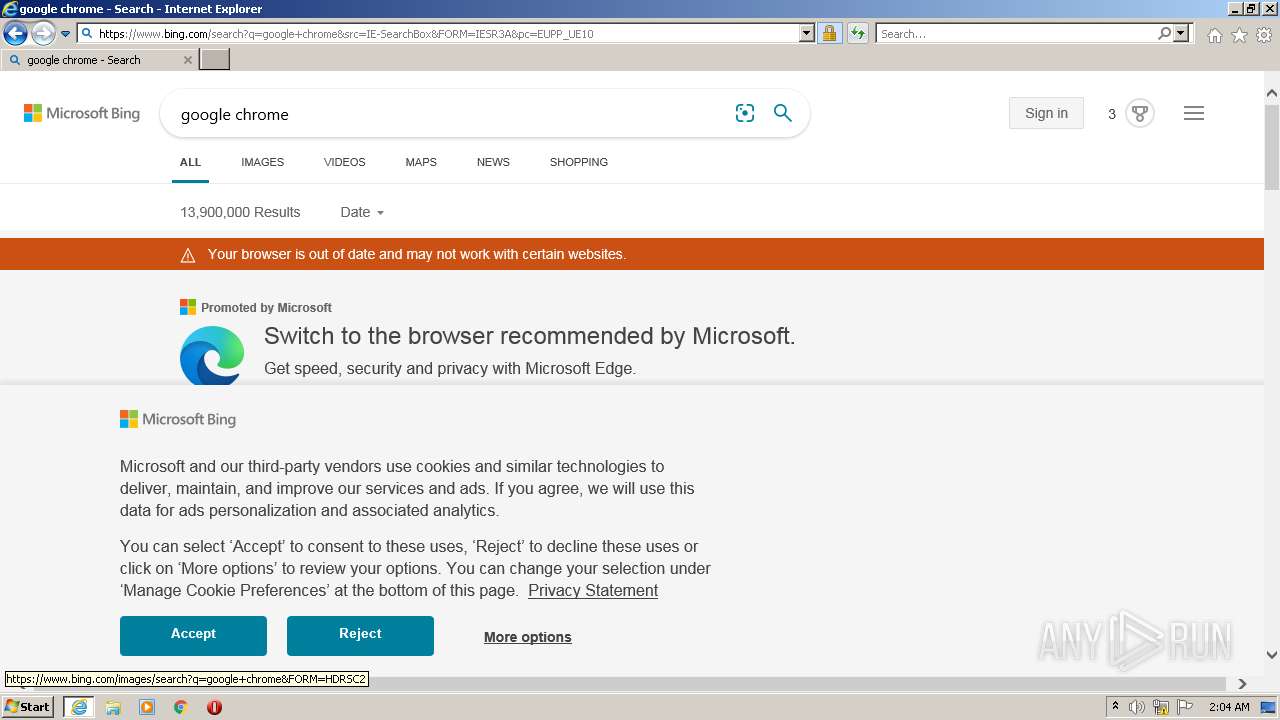
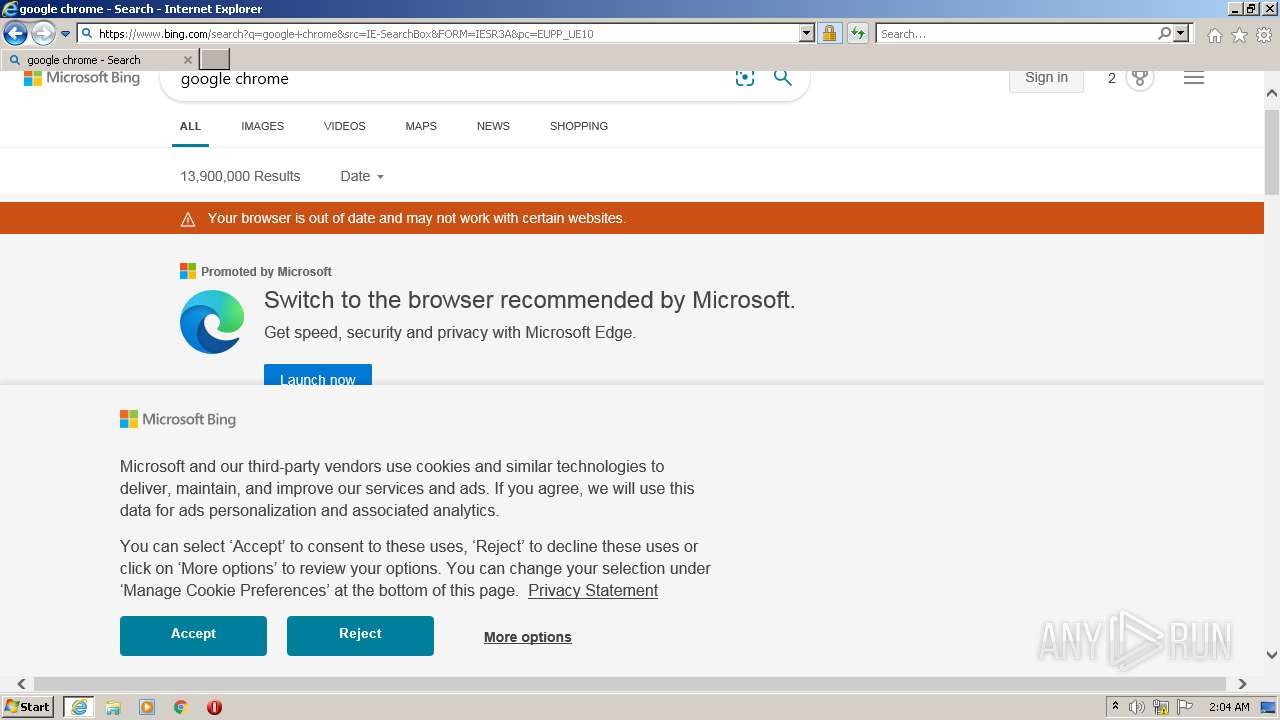
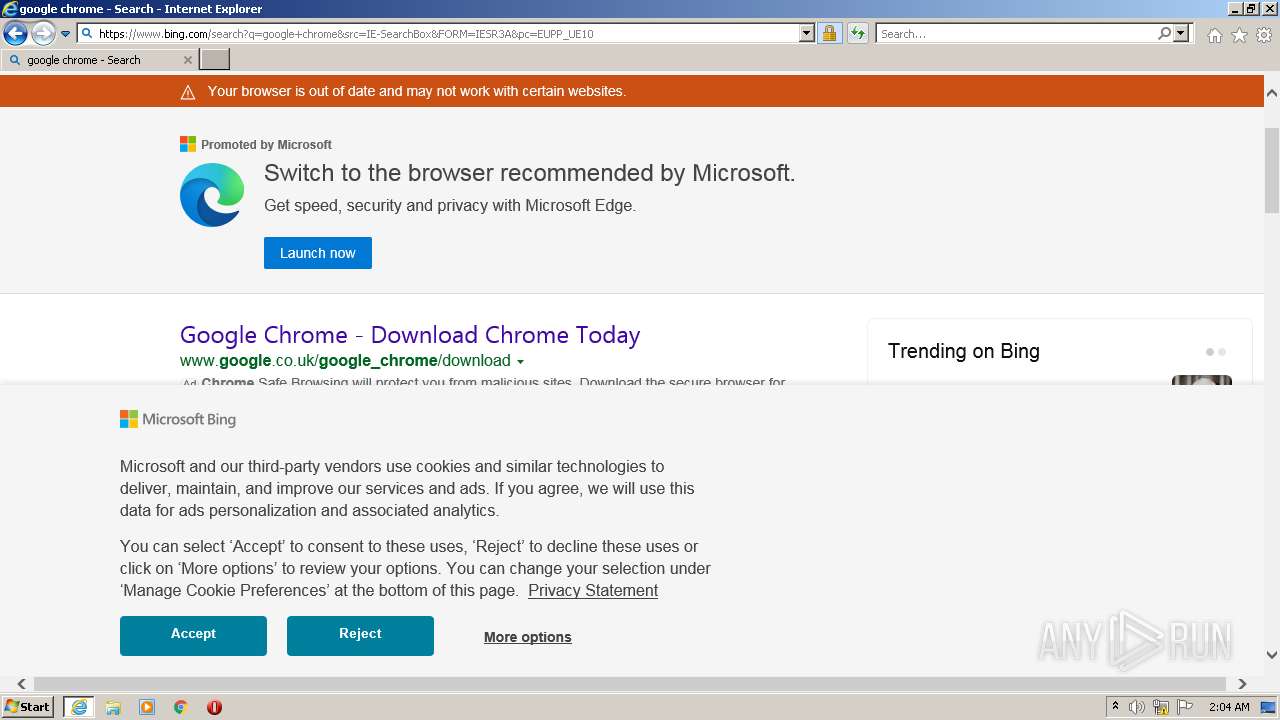
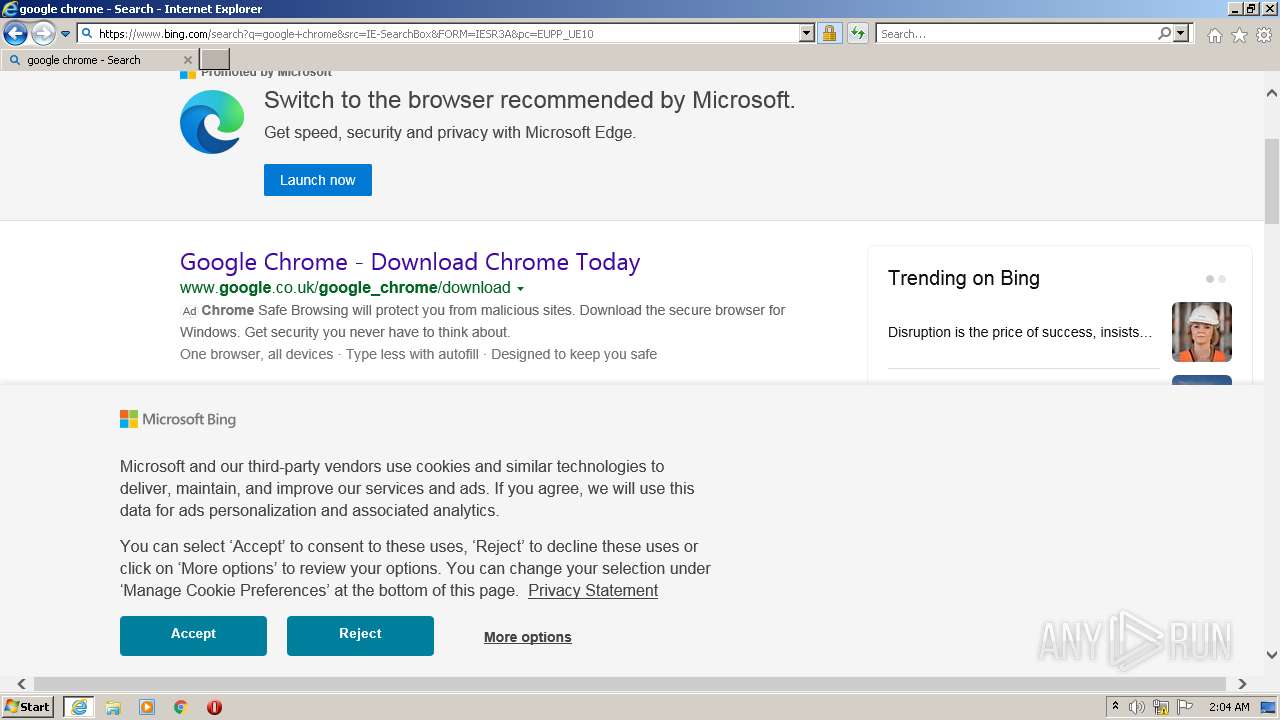
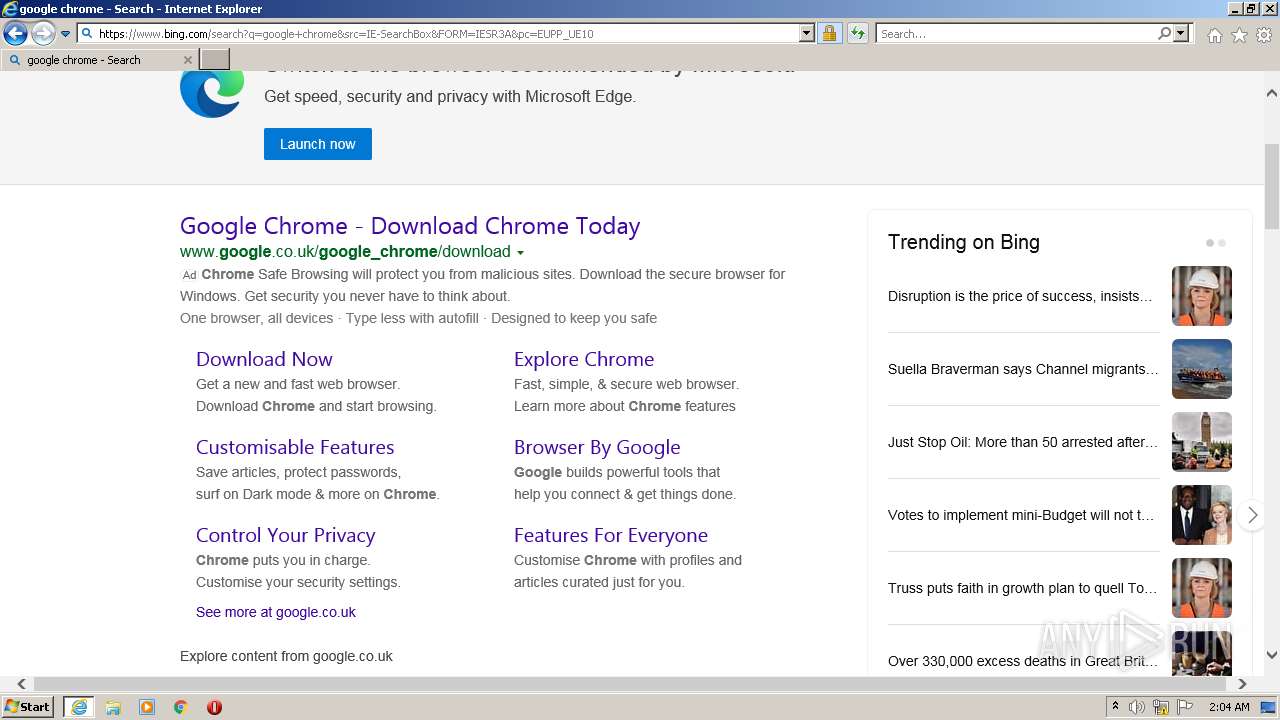
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://studiobariani-my.sharepoint.com/:o:/g/personal/marta_bussola_studiobariani_eu/EubxEOTLdJ9Is1QZ0nsdXygBnNXbi0qtkxYbqBQDKKnB2A?e=TrpVsL" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 687
Read events
16 494
Write events
191
Delete events
2
Modification events
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988374 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988374 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
24
Text files
228
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_1941775A515122A167E3FBACF08992E1 | der | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\BrowserSupport[1].htm | html | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_1941775A515122A167E3FBACF08992E1 | binary | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1ROUAJ12.txt | text | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8A07532D6AAE6A04052D31515DB38D1D_7CCA9233CBE4173C11816F65619AE59E | der | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Doc[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
90
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | — | — | whitelisted |
2212 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEA8XGkjG8iOAkhjNLtbdwOg%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRSHuNsR4EZqcsD%2BrdOV%2BEZevGBiwQUtXYMMBHOx5JCTUzHXCzIqQzoC2QCExIAID0mTAYs5VcQIg4AAAAgPSY%3D | US | der | 1.70 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRS%2FsoQjbTlq1Jokw0nyC%2FyFeJLtQQUAKuR%2FCFiJpeaqHkbYUGQYKliZ%2F0CEzMAS6fmBsZUZUoPvcsAAABLp%2BY%3D | US | der | 1.74 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2212 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2212 | iexplore.exe | 13.107.136.9:443 | studiobariani-my.sharepoint.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2212 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2456 | iexplore.exe | 95.100.208.244:443 | c1-onenote-15.cdn.office.net | AKAMAI-AS | DE | unknown |
2456 | iexplore.exe | 23.35.236.113:443 | res-1.cdn.office.net | AKAMAI-AS | DE | suspicious |
2456 | iexplore.exe | 13.107.6.171:443 | euc-onenote.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 104.18.25.243:80 | ocsp.msocsp.com | CLOUDFLARENET | — | shared |
— | — | 13.107.6.171:443 | euc-onenote.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 23.35.236.113:443 | res-1.cdn.office.net | AKAMAI-AS | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
studiobariani-my.sharepoint.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
c1-onenote-15.cdn.office.net |
| whitelisted |
res-1.cdn.office.net |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
euc-onenote.officeapps.live.com |
| whitelisted |