| File name: | 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe |
| Full analysis: | https://app.any.run/tasks/4f7ff009-7c1d-4c03-a34e-1e34d6ee3066 |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2024, 09:30:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
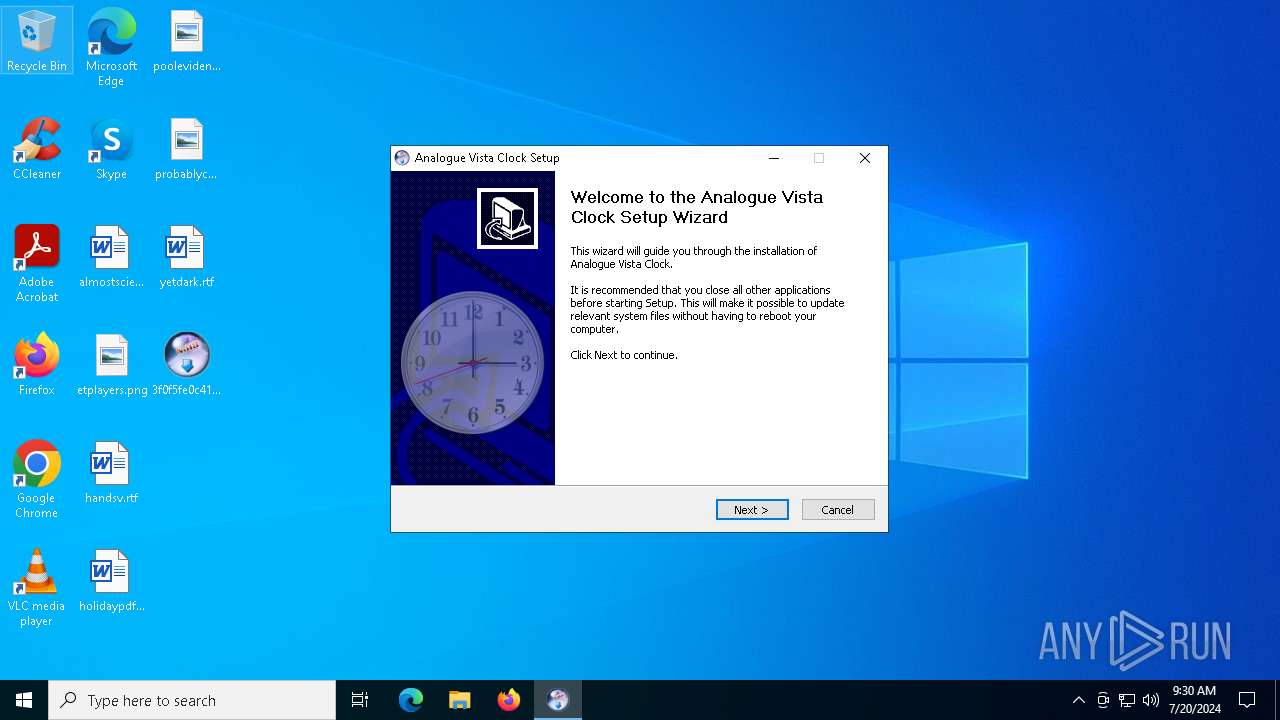
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 24A3A33C218DC82755C503B13059430C |
| SHA1: | C3DBDDF800D1ACC3F32E1C790262C34E9F97C982 |
| SHA256: | 3F0F5FE0C41A0366CA2D5E7A7783C9E4D644973010E9E6AB7B408FD5469C7520 |
| SSDEEP: | 24576:MTXraO04850Cr4bqD51YeZuHLhaX/QLdyfUCQ50RarcVcx25O899C/:MTXraO04850EqqD51YeZuHLhe/QZyfUT |
MALICIOUS
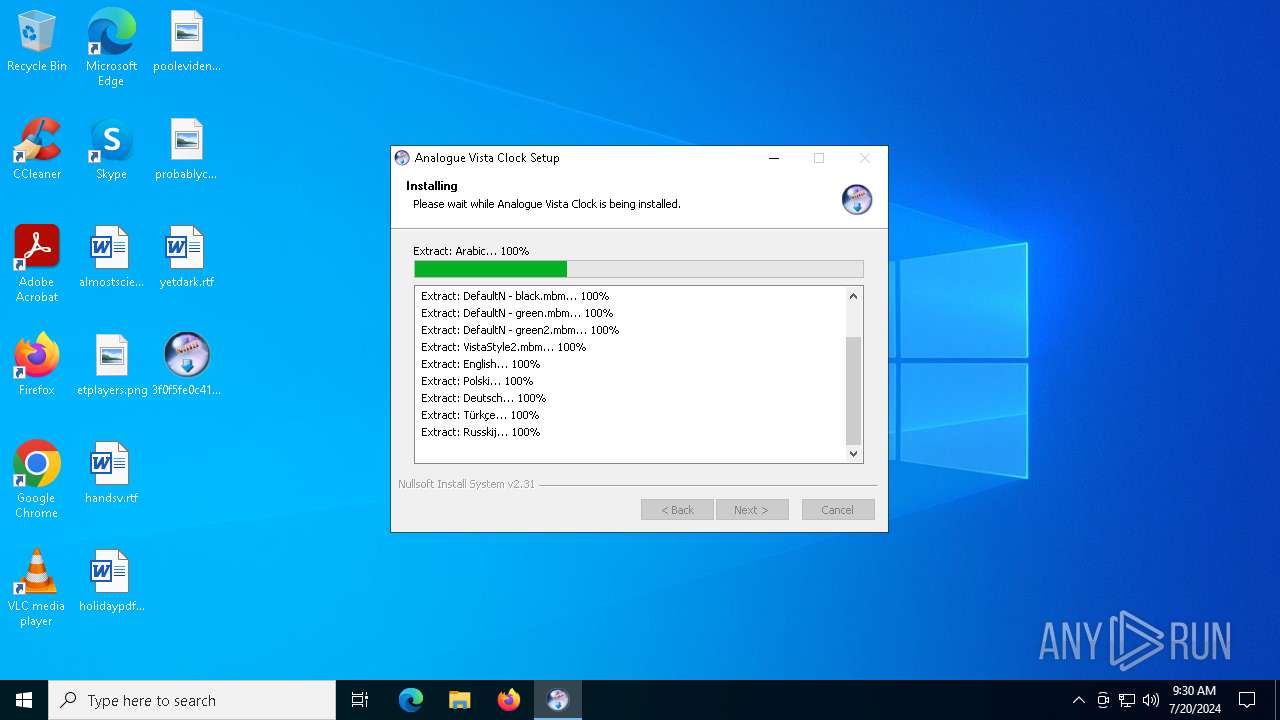
Drops the executable file immediately after the start
- 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe (PID: 7612)
- ClockInstall.exe (PID: 6868)
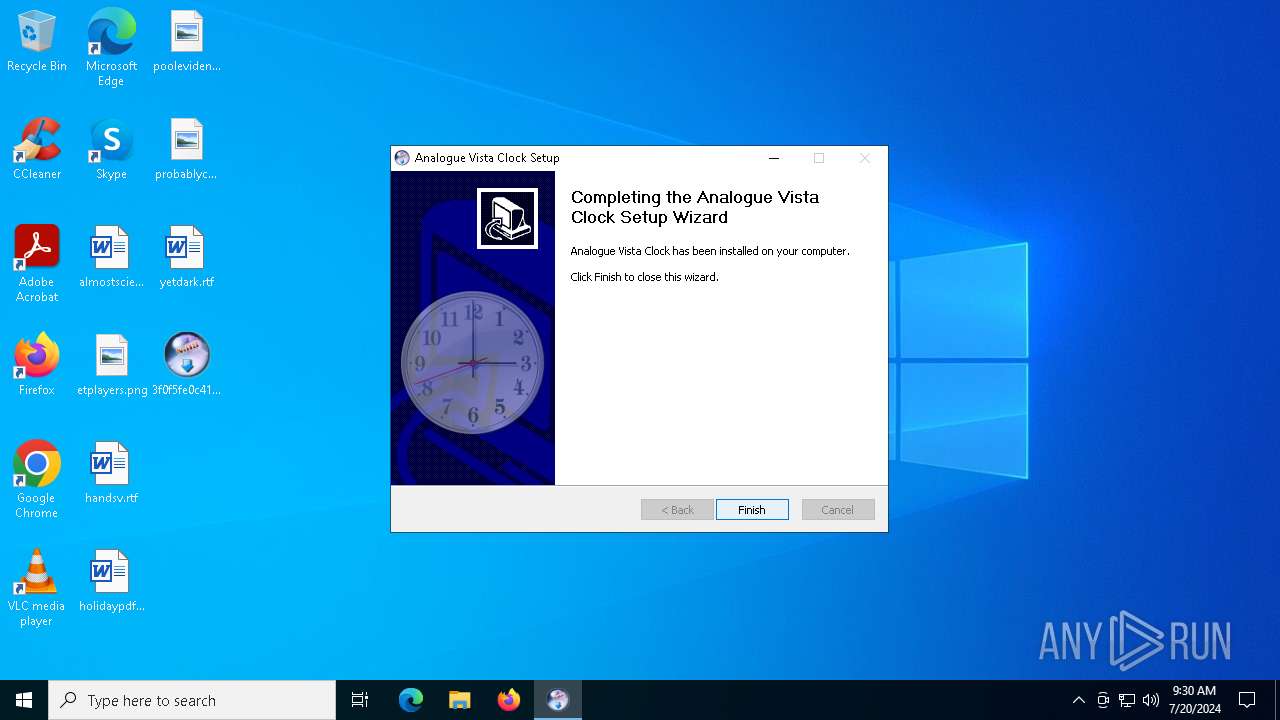
Changes the autorun value in the registry
- ClockInstall.exe (PID: 6868)
SUSPICIOUS
Executable content was dropped or overwritten
- 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe (PID: 7612)
- ClockInstall.exe (PID: 6868)
Malware-specific behavior (creating "System.dll" in Temp)
- ClockInstall.exe (PID: 6868)
Reads security settings of Internet Explorer
- ExecShellWait.exe (PID: 7204)
The process creates files with name similar to system file names
- ClockInstall.exe (PID: 6868)
Creates a software uninstall entry
- ClockInstall.exe (PID: 6868)
Reads the date of Windows installation
- ExecShellWait.exe (PID: 7204)
INFO
Checks supported languages
- 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe (PID: 7612)
- ExecShellWait.exe (PID: 7204)
- ClockInstall.exe (PID: 6868)
- Analogue Vista Clock.exe (PID: 1492)
Reads the computer name
- ExecShellWait.exe (PID: 7204)
- ClockInstall.exe (PID: 6868)
- Analogue Vista Clock.exe (PID: 1492)
Create files in a temporary directory
- ClockInstall.exe (PID: 6868)
- 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe (PID: 7612)
Process checks computer location settings
- ExecShellWait.exe (PID: 7204)
Creates files in the program directory
- ClockInstall.exe (PID: 6868)
Creates files or folders in the user directory
- ClockInstall.exe (PID: 6868)
- Analogue Vista Clock.exe (PID: 1492)
Checks proxy server information
- slui.exe (PID: 7840)
Reads the software policy settings
- slui.exe (PID: 7840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:09:29 12:50:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22528 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30c4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.34.0.0 |
| ProductVersionNumber: | 1.34.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Analogue Vista Clock Installer |
| CompanyName: | 4Neurons |
| FileDescription: | ClockInstall.exe |
| FileVersion: | 1.34 |
| LegalCopyright: | Copyright © 2013 4Neurons |
| OriginalFileName: | ClockInstall.exe |
| ProductName: | Analogue Vista Clock |
| ProductVersion: | 1.34 |
Total processes
144
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | "C:\Program Files (x86)\Analogue Vista Clock\Analogue Vista Clock.exe" /setlocale | C:\Program Files (x86)\Analogue Vista Clock\Analogue Vista Clock.exe | — | 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe | |||||||||||
User: admin Company: 4 Neurons Integrity Level: MEDIUM Description: Analogue Vista Clock Version: 1, 35, 0, 0 Modules
| |||||||||||||||
| 6868 | "C:\Users\admin\AppData\Local\Temp\ClockInstall.exe" | C:\Users\admin\AppData\Local\Temp\ClockInstall.exe | ExecShellWait.exe | ||||||||||||
User: admin Company: 4Neurons Integrity Level: HIGH Description: ClockInstall.exe Exit code: 0 Version: 1.35 Modules
| |||||||||||||||
| 7112 | "C:\Users\admin\AppData\Local\Temp\ClockInstall.exe" | C:\Users\admin\AppData\Local\Temp\ClockInstall.exe | — | ExecShellWait.exe | |||||||||||
User: admin Company: 4Neurons Integrity Level: MEDIUM Description: ClockInstall.exe Exit code: 3221226540 Version: 1.35 Modules
| |||||||||||||||
| 7204 | C:\Users\admin\AppData\Local\Temp\ExecShellWait.exe C:\Users\admin\AppData\Local\Temp\ClockInstall.exe | C:\Users\admin\AppData\Local\Temp\ExecShellWait.exe | — | 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7612 | "C:\Users\admin\Desktop\3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe" | C:\Users\admin\Desktop\3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe | explorer.exe | ||||||||||||
User: admin Company: 4Neurons Integrity Level: MEDIUM Description: ClockInstall.exe Exit code: 0 Version: 1.34 Modules
| |||||||||||||||
| 7840 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 482
Read events
10 467
Write events
15
Delete events
0
Modification events
| (PID) Process: | (7204) ExecShellWait.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7204) ExecShellWait.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7204) ExecShellWait.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7204) ExecShellWait.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Analogue Vista Clock |
Value: C:\Program Files (x86)\Analogue Vista Clock\Analogue Vista Clock.exe | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Analogue Vista Clock |
| Operation: | write | Name: | DisplayName |
Value: Analogue Vista Clock 1.35 | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Analogue Vista Clock |
| Operation: | write | Name: | DisplayVersion |
Value: 1.35 | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Analogue Vista Clock |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.4neurons.com/ | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Analogue Vista Clock |
| Operation: | write | Name: | Publisher |
Value: 4Neurons | |||
| (PID) Process: | (6868) ClockInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Analogue Vista Clock |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\Analogue Vista Clock\Uninst.exe | |||
Executable files
7
Suspicious files
16
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\DefaultN.mbm | binary | |
MD5:B55CCC2A160DE3B7CAB194CF9351EB9A | SHA256:C483DC8E17FE4A733C7006814B79065DFC76926D33D1A078908664E81F194F66 | |||
| 6868 | ClockInstall.exe | C:\Users\admin\AppData\Local\Temp\nsb9C8E.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 6868 | ClockInstall.exe | C:\Users\admin\AppData\Local\Temp\nsb9C8E.tmp\System.dll | executable | |
MD5:CFBAE93F361E2B430743E423709A483F | SHA256:0F4AAC375087F0A5DF393D7463BD462193008922136A2ABA8619736223BA7ADD | |||
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\Analogue Vista Clock.exe | executable | |
MD5:F088023B77DD4D4FAA078DE89B7B4CCD | SHA256:E7CEFD70B6F6F16DDFE59FCDF77E2D551F9DE8F15EF708BFE3868090437DF074 | |||
| 6868 | ClockInstall.exe | C:\Users\admin\AppData\Local\Temp\nsb9C8E.tmp\InstallOptions.dll | executable | |
MD5:79BE350C8381293ABB045BBD2A7B5F0A | SHA256:3091623495D6E81BC0AA9182A55B0F93D3B2238102A44FD66943E46ED7EEAF51 | |||
| 7612 | 3f0f5fe0c41a0366ca2d5e7a7783c9e4d644973010e9e6ab7b408fd5469c7520.exe | C:\Users\admin\AppData\Local\Temp\ClockInstall.exe | executable | |
MD5:4338B3849FBDB51D7943167C0F48AADA | SHA256:A54E1C3C47D5A09E6C641590FC5E199DE47DEC4CB9921C1DA41B75BD94384F9B | |||
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\Russkij | text | |
MD5:BF6BE8CC2776F88DEF95428E850E9F9A | SHA256:A08DF364B060B87A005319BD5CAB403A314247619CD3B2B71C5D49BEBF94B44D | |||
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\DefaultN - green.mbm | binary | |
MD5:405C1AA9D847460312D362756C27D43B | SHA256:456539178C996AA0ADF07065A9D827BE6C357E8000B313FE6941285D84921DA5 | |||
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\Türkçe | text | |
MD5:71F184EB3B588028FC17DE7262343344 | SHA256:EB7A235585B67DD6B9C29CC16B294536A254AAB4E4E5231245B26A5FCB641B2C | |||
| 6868 | ClockInstall.exe | C:\Program Files (x86)\Analogue Vista Clock\DefaultN - green2.mbm | binary | |
MD5:8E476FA43CD987BCC179FC15CE9E2E5B | SHA256:02C837733F2054EBCF56249F885CA547DCEB5A5F46582D6263A7DE7270C476DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
40
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
— | — | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | GET | 200 | 20.31.169.57:443 | https://fd.api.iris.microsoft.com/v4/api/selection?&asid=A8E4E8D0DB264AF88378883CD7EEDCC4&nct=1&placement=88000677&bcnt=30&country=US&locale=en-US&poptin=0&fmt=json&arch=AMD64&chassis=1&concp=0&d3dfl=D3D_FEATURE_LEVEL_12_1&devfam=Windows.Desktop&devosver=10.0.19045.4046&dinst=1661339444&dmret=0&flightbranch=&flightring=Retail&icluc=0&localid=w%3AAC7699B0-48EA-FD22-C8DC-06A02098A0F0&oem=DELL&osbranch=vb_release&oslocale=en-US&osret=1&ossku=Professional&osskuid=48&prccn=4&prccs=3094&prcmf=AuthenticAMD&procm=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&ram=4096&tinst=Client&tl=1&pat=0&smc=0&sac=0&disphorzres=1280&dispsize=15.3&dispvertres=720&ldisphorzres=1280&ldispvertres=720&moncnt=1&cpdsk=260281&frdsk=218542&lo=3611610&tsu=1002140 | unknown | binary | 102 b | unknown |
— | — | POST | 200 | 20.199.58.43:443 | https://arc.msn.com/v4/api/register?asid=1C68D6E95E69431185F7064524ED40E1&placement=cdmdevreg&country=US&locale=en-US&poptin=0&fmt=json&arch=AMD64&chassis=1&concp=0&d3dfl=D3D_FEATURE_LEVEL_12_1&devfam=Windows.Desktop&devosver=10.0.19045.4046&dinst=1661339444&dmret=0&flightbranch=&flightring=Retail&icluc=0&localid=w%3AAC7699B0-48EA-FD22-C8DC-06A02098A0F0&oem=DELL&osbranch=vb_release&oslocale=en-US&osret=1&ossku=Professional&osskuid=48&prccn=4&prccs=3094&prcmf=AuthenticAMD&procm=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&ram=4096&tinst=Client&tl=1&pat=0&smc=0&sac=0&disphorzres=1280&dispsize=15.3&dispvertres=720&ldisphorzres=1280&ldispvertres=720&moncnt=1&cpdsk=260281&frdsk=218542&lo=3611610&tsu=1002140 | unknown | — | — | unknown |
— | — | GET | 200 | 104.126.37.171:443 | https://www.bing.com/client/config?cc=US&setlang=en-US | unknown | binary | 2.15 Kb | unknown |
— | — | GET | 200 | 20.31.169.57:443 | https://fd.api.iris.microsoft.com/v4/api/selection?&asid=E3F3635EC2774FE4805B9DD2C73A504A&nct=1&placement=88000677&bcnt=30&country=US&locale=en-US&poptin=0&fmt=json&arch=AMD64&chassis=1&concp=0&d3dfl=D3D_FEATURE_LEVEL_12_1&devfam=Windows.Desktop&devosver=10.0.19045.4046&dinst=1661339444&dmret=0&flightbranch=&flightring=Retail&icluc=0&localid=w%3AAC7699B0-48EA-FD22-C8DC-06A02098A0F0&oem=DELL&osbranch=vb_release&oslocale=en-US&osret=1&ossku=Professional&osskuid=48&prccn=4&prccs=3094&prcmf=AuthenticAMD&procm=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&ram=4096&tinst=Client&tl=1&pat=0&smc=0&sac=0&disphorzres=1280&dispsize=15.3&dispvertres=720&ldisphorzres=1280&ldispvertres=720&moncnt=1&cpdsk=260281&frdsk=218542&lo=3611610&tsu=1002139 | unknown | binary | 102 b | unknown |
— | — | POST | 200 | 20.199.58.43:443 | https://arc.msn.com/v4/api/register?asid=371DBB2CB4FB45EA8DC9C8E4693897EE&placement=cdmdevreg&country=US&locale=en-US&poptin=0&fmt=json&arch=AMD64&chassis=1&concp=0&d3dfl=D3D_FEATURE_LEVEL_12_1&devfam=Windows.Desktop&devosver=10.0.19045.4046&dinst=1661339444&dmret=0&flightbranch=&flightring=Retail&icluc=0&localid=w%3AAC7699B0-48EA-FD22-C8DC-06A02098A0F0&oem=DELL&osbranch=vb_release&oslocale=en-US&osret=1&ossku=Professional&osskuid=48&prccn=4&prccs=3094&prcmf=AuthenticAMD&procm=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&ram=4096&tinst=Client&tl=1&pat=0&smc=0&sac=0&disphorzres=1280&dispsize=15.3&dispvertres=720&ldisphorzres=1280&ldispvertres=720&moncnt=1&cpdsk=260281&frdsk=218542&lo=3611609&tsu=1002139 | unknown | — | — | unknown |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 24.8 Kb | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7856 | svchost.exe | 4.208.221.206:443 | licensing.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6556 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7220 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7292 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |