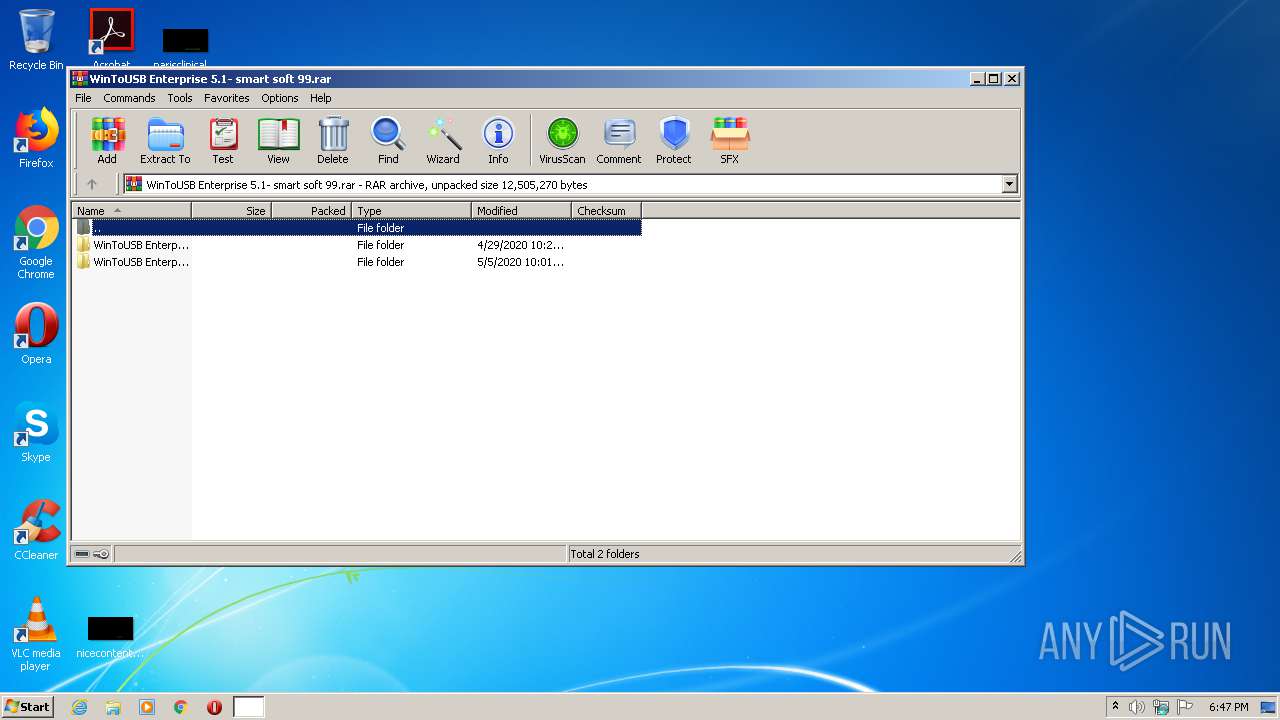
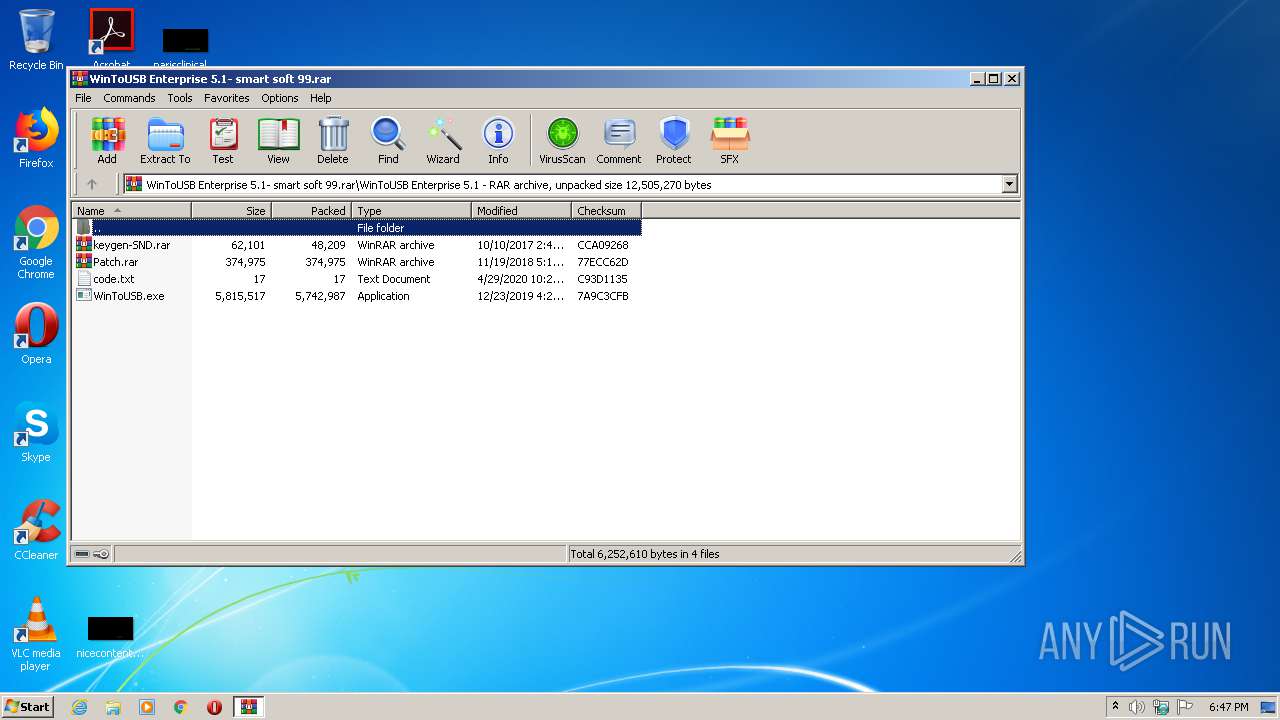
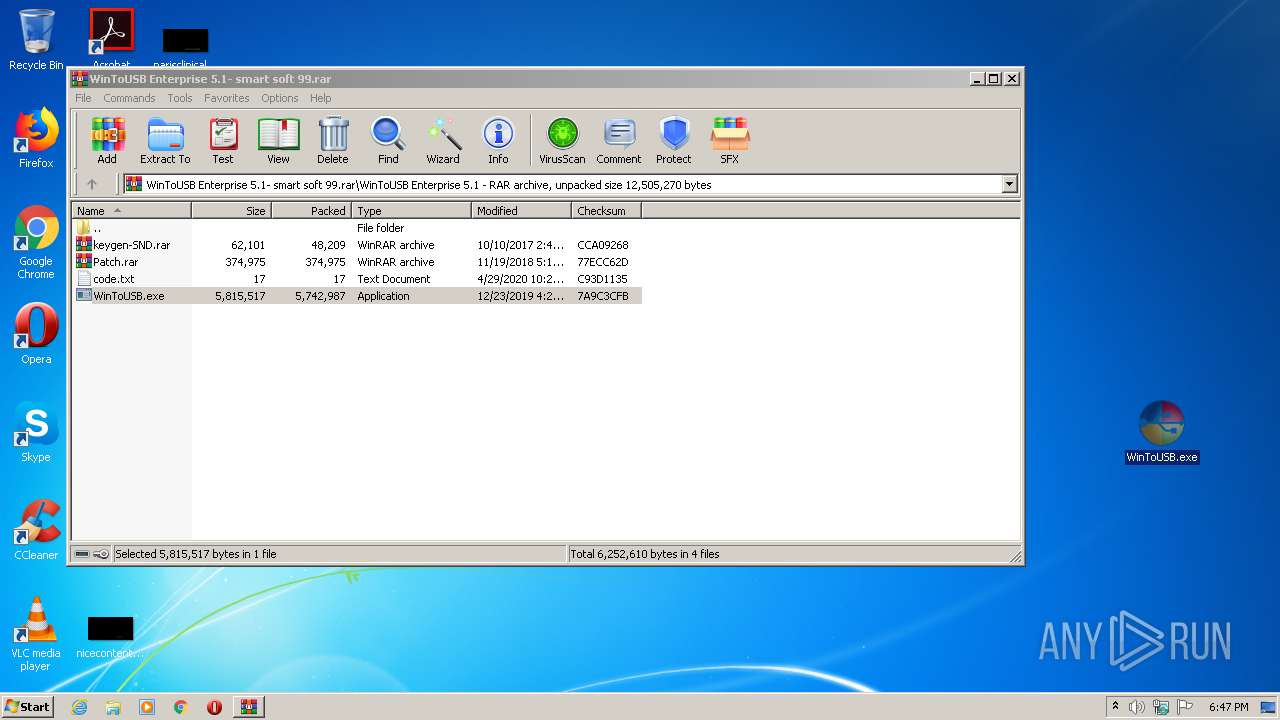
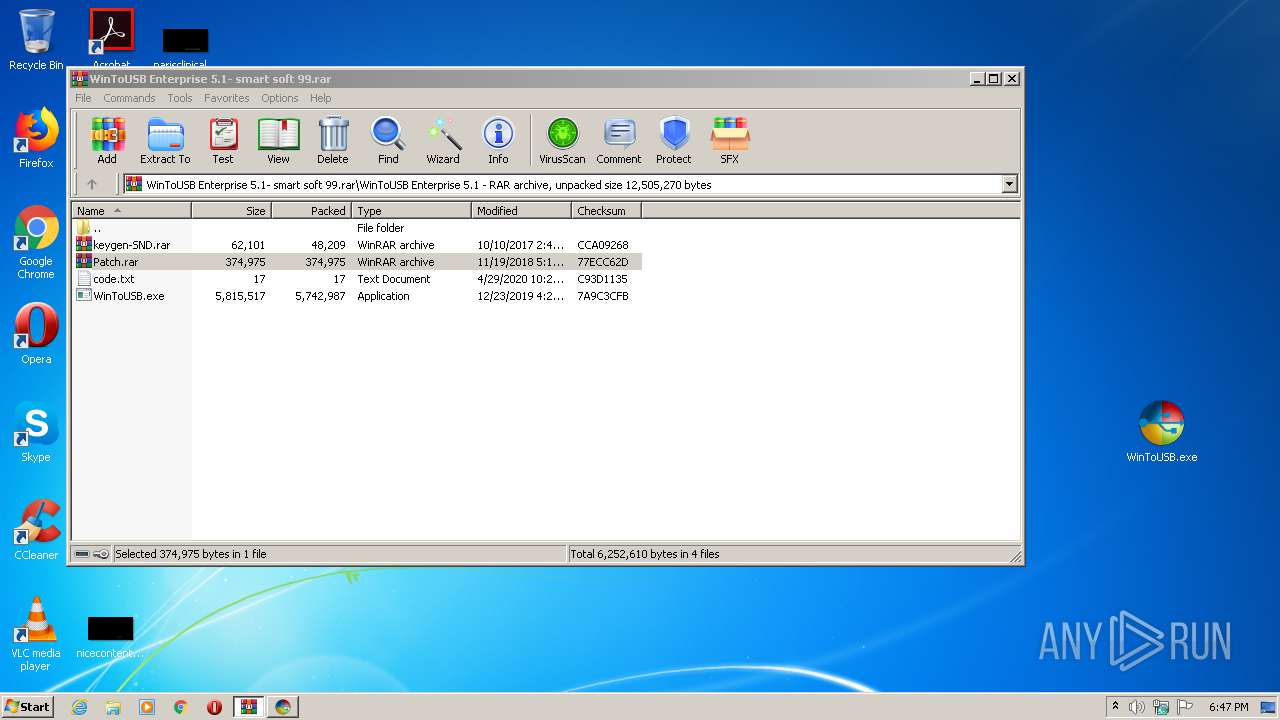
| File name: | WinToUSB Enterprise 5.1- smart soft 99.rar |
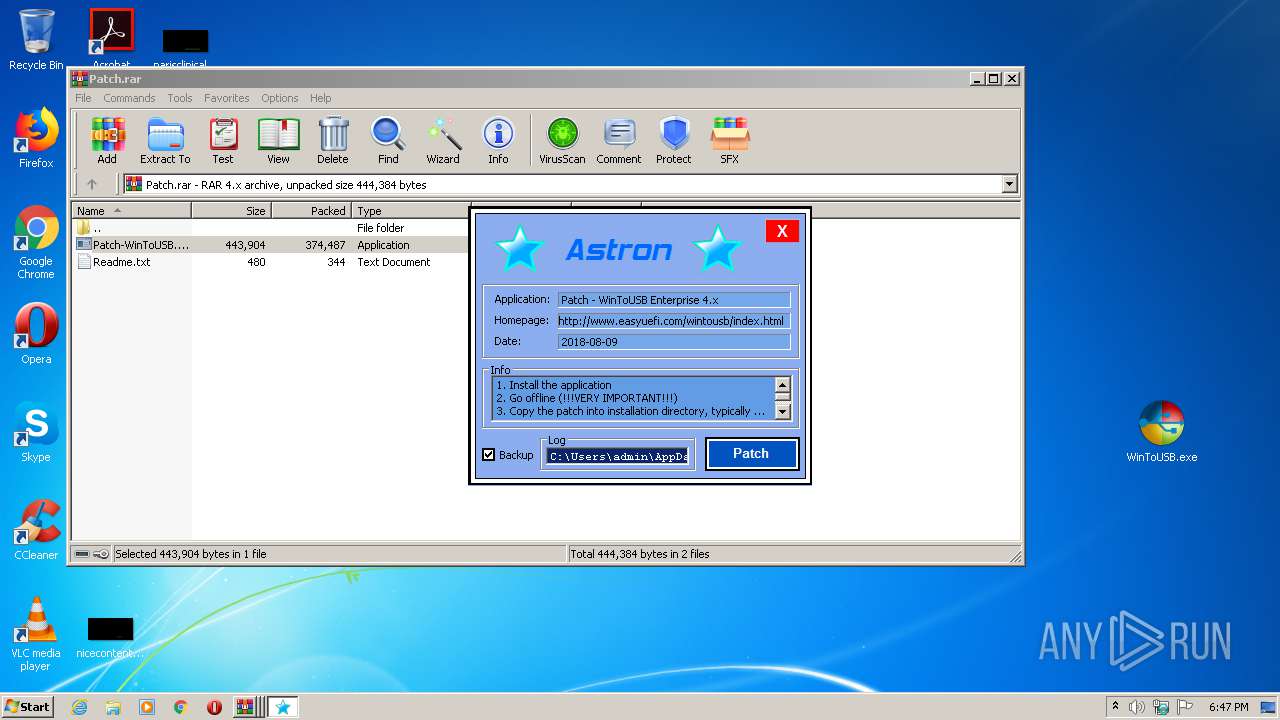
| Full analysis: | https://app.any.run/tasks/38693ff8-00f0-4dbc-a33f-abd195491c1a |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2020, 17:46:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
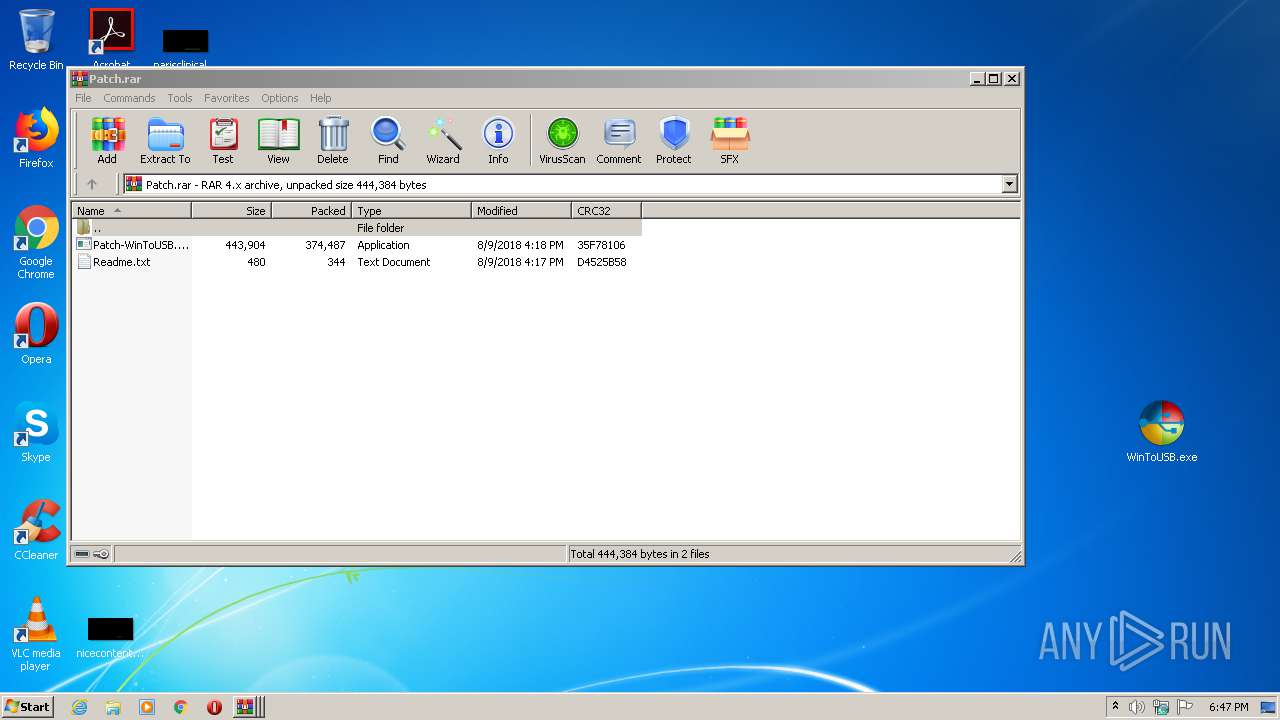
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BAC5C62FEAB3C7C4F13DD2BAFE04B75B |
| SHA1: | 6B2ACE5AA3D0433F7604A03DA9FFFB881B7E6A88 |
| SHA256: | 3F0548D0C5E2310BEAF345D52D410A543EF6C982CF793F0ECB3EA215B7C99DF3 |
| SSDEEP: | 196608:Lf9SKSlHQJTYumDVUG2lvx51Hmm0AcbTobeXx5VNU1xIZY+i/MLyZyT723wJRux/:BSKSlHQuVDVn2lpnHLcW+x5fkxIZY+PM |
MALICIOUS
Application was dropped or rewritten from another process
- WinToUSB.exe (PID: 2336)
- WinToUSB.exe (PID: 1020)
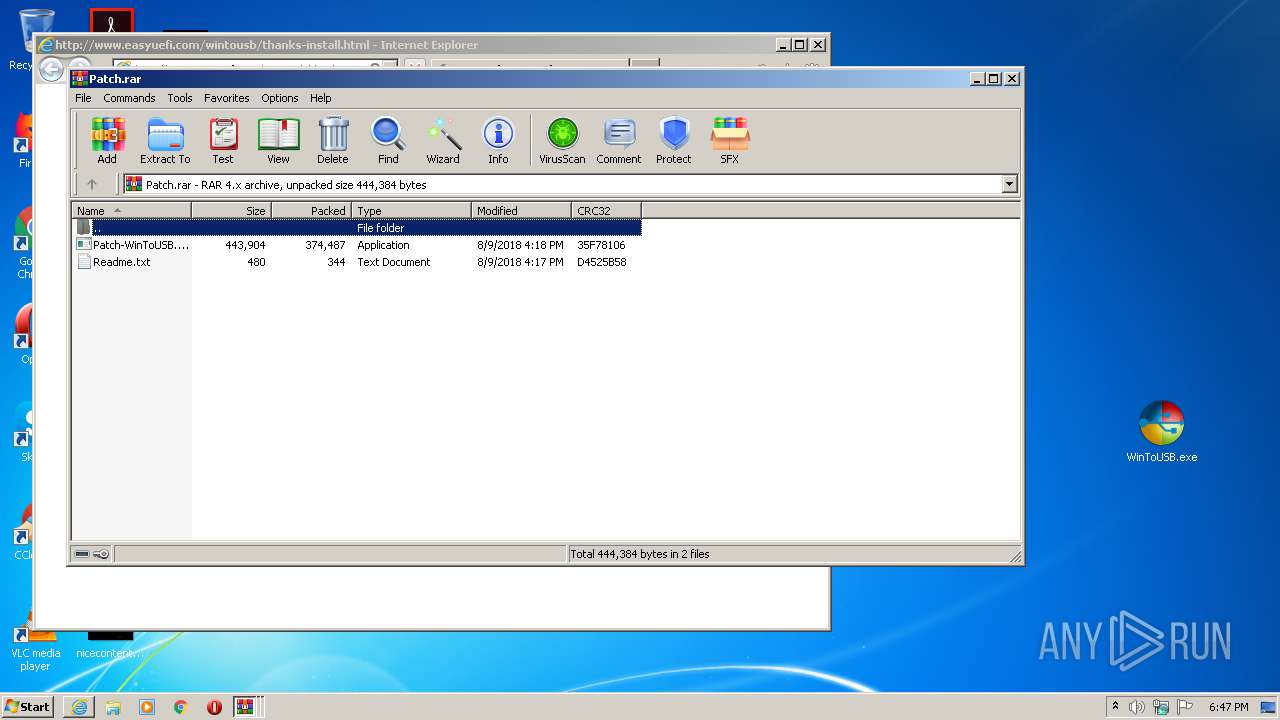
- Patch-WinToUSB.Enterprise.4.x.exe (PID: 1728)
- Patch-WinToUSB.Enterprise.4.x.exe (PID: 1872)
Loads dropped or rewritten executable
- Patch-WinToUSB.Enterprise.4.x.exe (PID: 1872)
SUSPICIOUS
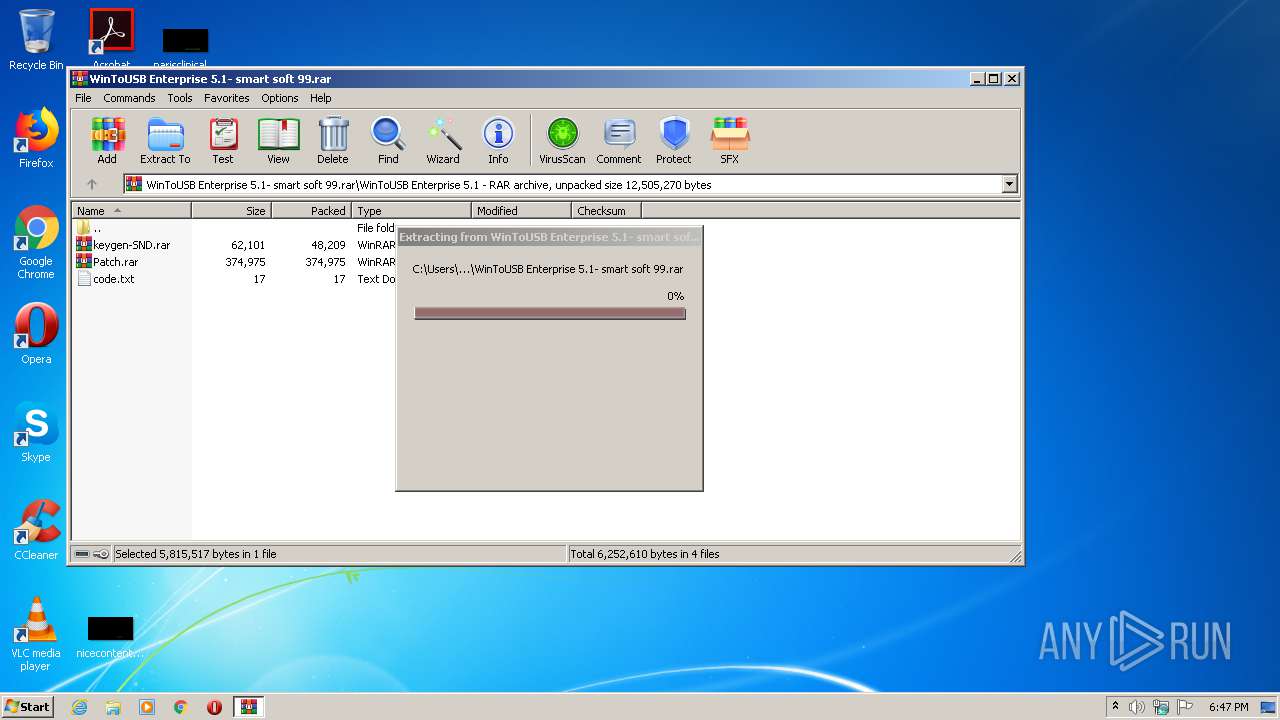
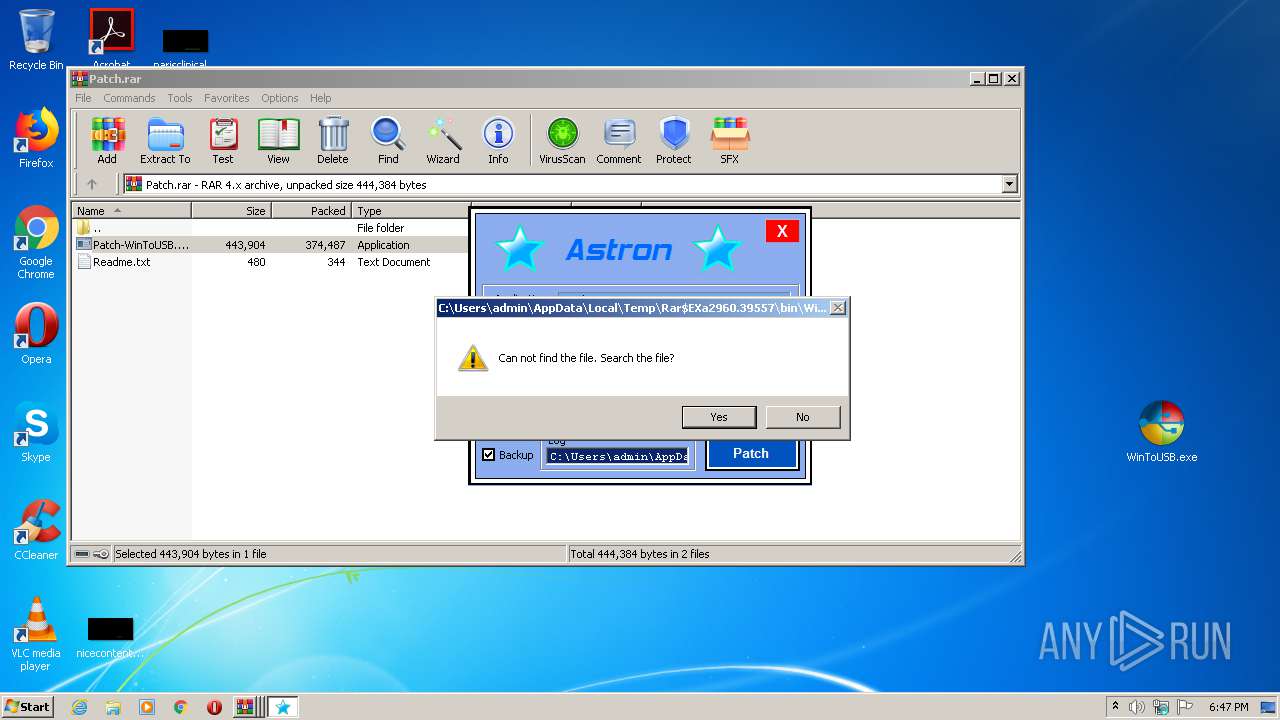
Executable content was dropped or overwritten
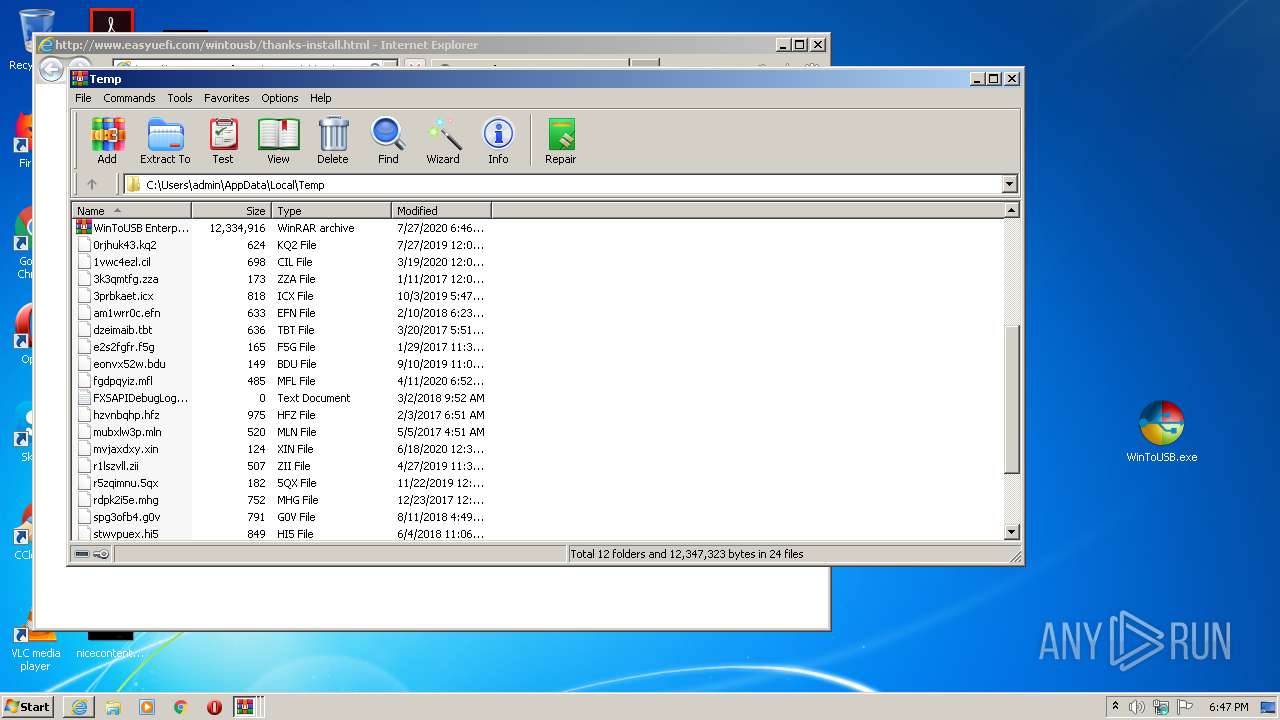
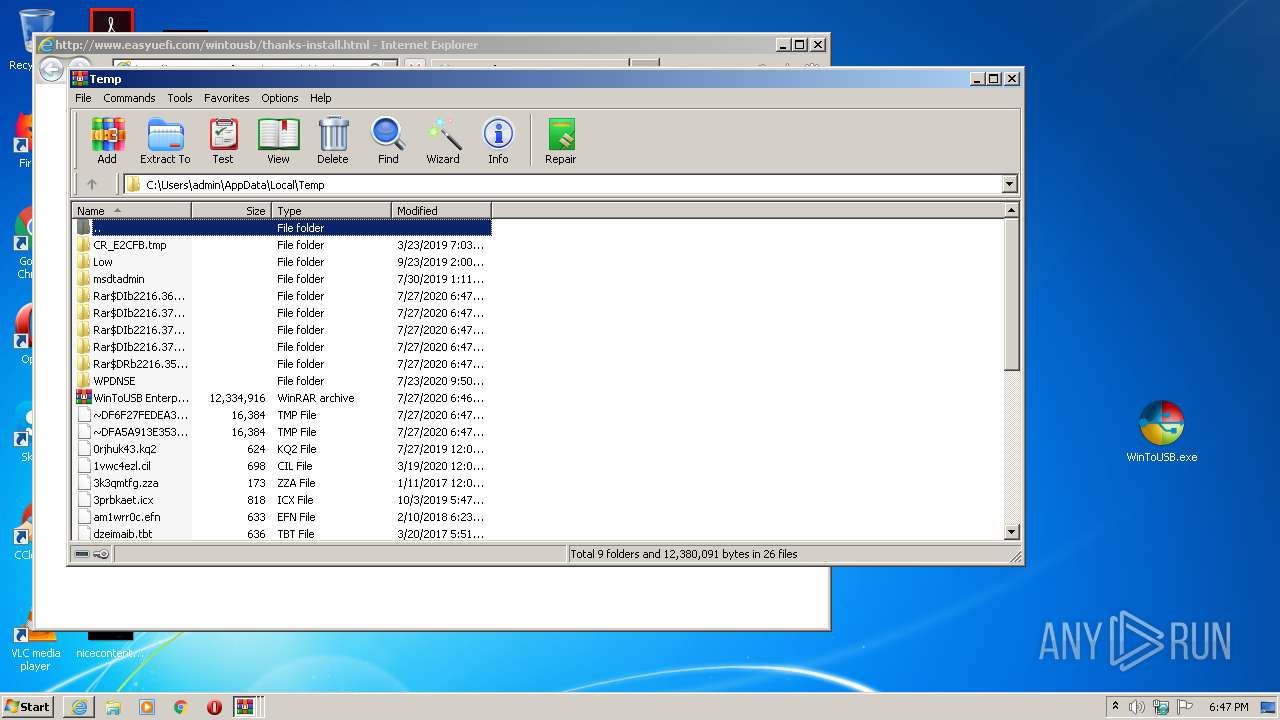
- WinRAR.exe (PID: 2216)
- WinToUSB.exe (PID: 2336)
- WinToUSB.exe (PID: 1020)
- WinToUSB.tmp (PID: 952)
- Patch-WinToUSB.Enterprise.4.x.exe (PID: 1872)
- WinRAR.exe (PID: 2960)
Reads the Windows organization settings
- WinToUSB.tmp (PID: 952)
Reads Windows owner or organization settings
- WinToUSB.tmp (PID: 952)
Application launched itself
- WinRAR.exe (PID: 2216)
Starts Internet Explorer
- WinToUSB.tmp (PID: 952)
INFO
Application was dropped or rewritten from another process
- WinToUSB.tmp (PID: 3120)
- WinToUSB.tmp (PID: 952)
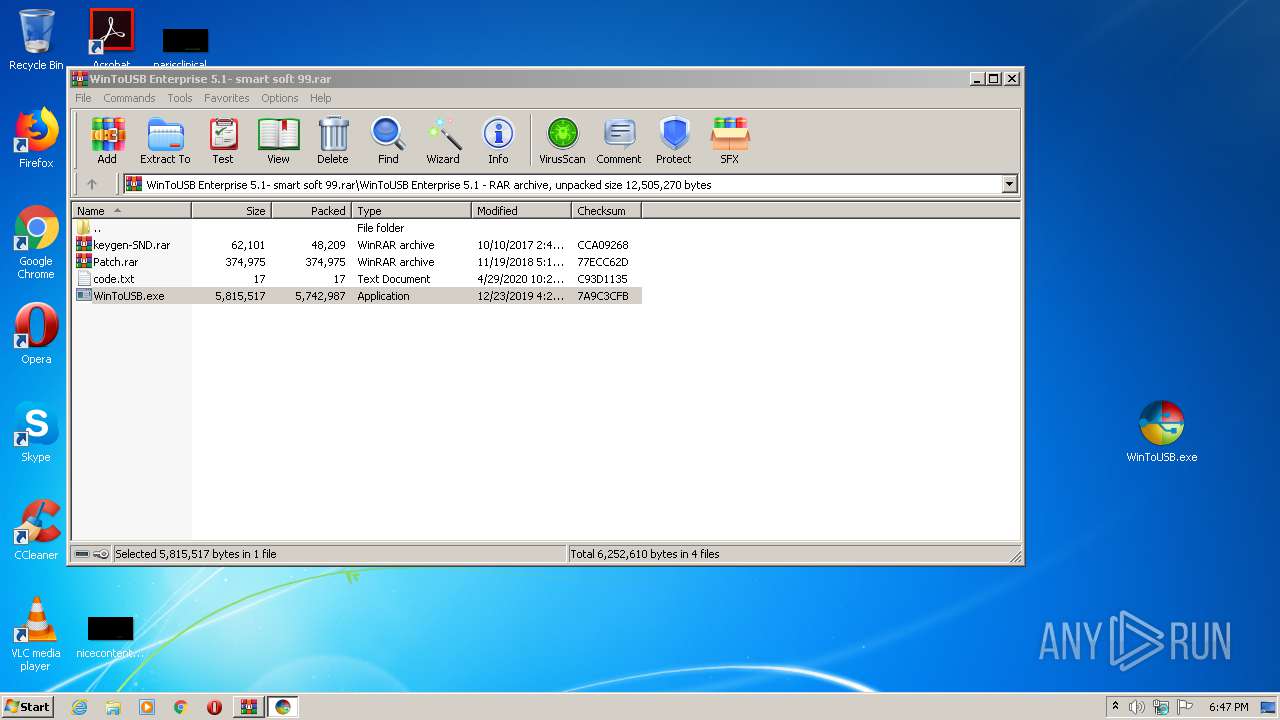
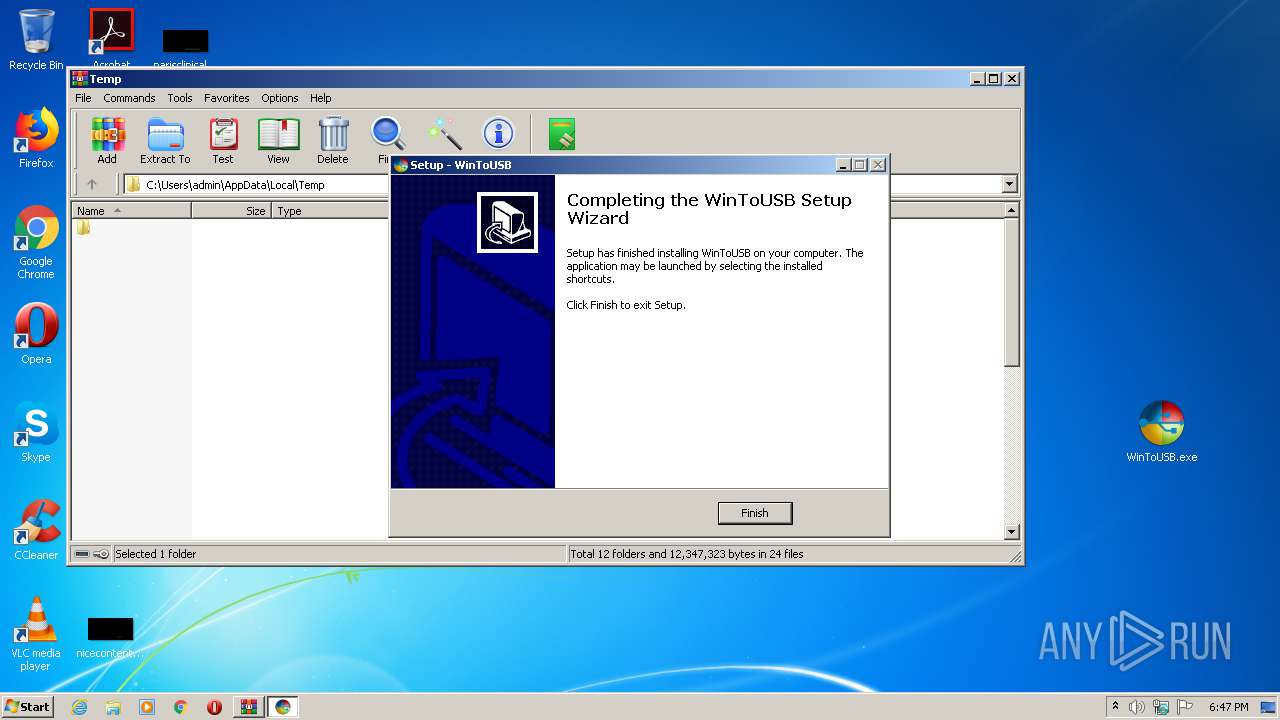
Manual execution by user
- WinToUSB.exe (PID: 2336)
Loads dropped or rewritten executable
- WinToUSB.tmp (PID: 952)
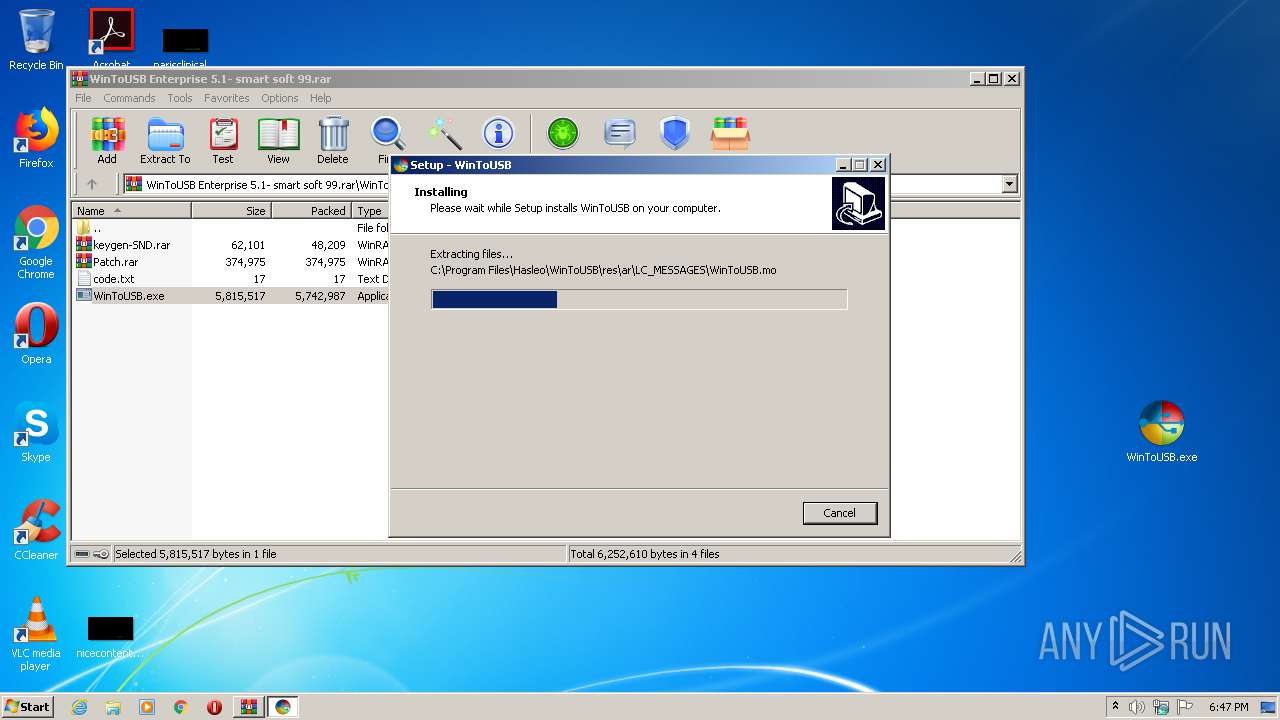
Creates files in the program directory
- WinToUSB.tmp (PID: 952)
Creates a software uninstall entry
- WinToUSB.tmp (PID: 952)
Reads Internet Cache Settings
- iexplore.exe (PID: 1604)
- iexplore.exe (PID: 2532)
Application launched itself
- iexplore.exe (PID: 1604)
Changes internet zones settings
- iexplore.exe (PID: 1604)
Changes settings of System certificates
- iexplore.exe (PID: 2532)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
56
Monitored processes
13
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
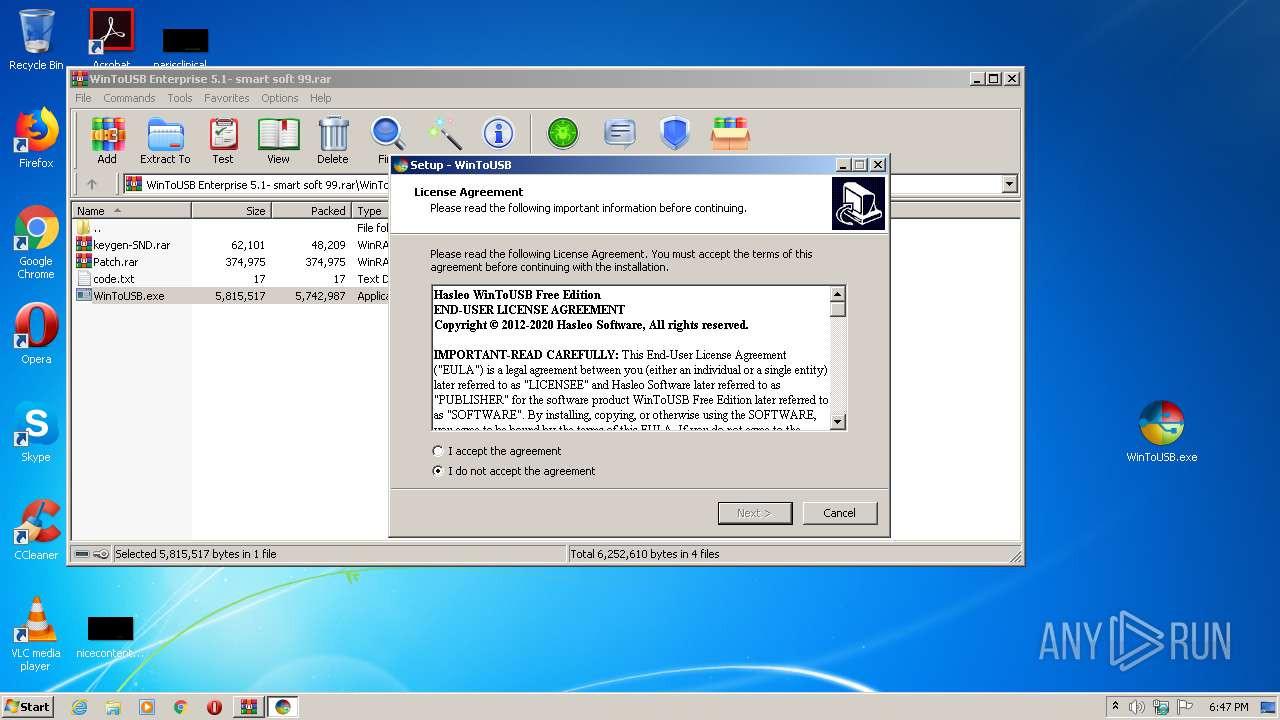
| 952 | "C:\Users\admin\AppData\Local\Temp\is-3DJNB.tmp\WinToUSB.tmp" /SL5="$3016E,5233070,251904,C:\Users\admin\Desktop\WinToUSB.exe" /SPAWNWND=$20170 /NOTIFYWND=$3017A | C:\Users\admin\AppData\Local\Temp\is-3DJNB.tmp\WinToUSB.tmp | WinToUSB.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\Desktop\WinToUSB.exe" /SPAWNWND=$20170 /NOTIFYWND=$3017A | C:\Users\admin\Desktop\WinToUSB.exe | WinToUSB.tmp | ||||||||||||
User: admin Company: Hasleo Software. Integrity Level: HIGH Description: WinToUSB Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.easyuefi.com/wintousb/thanks-install.html | C:\Program Files\Internet Explorer\iexplore.exe | WinToUSB.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
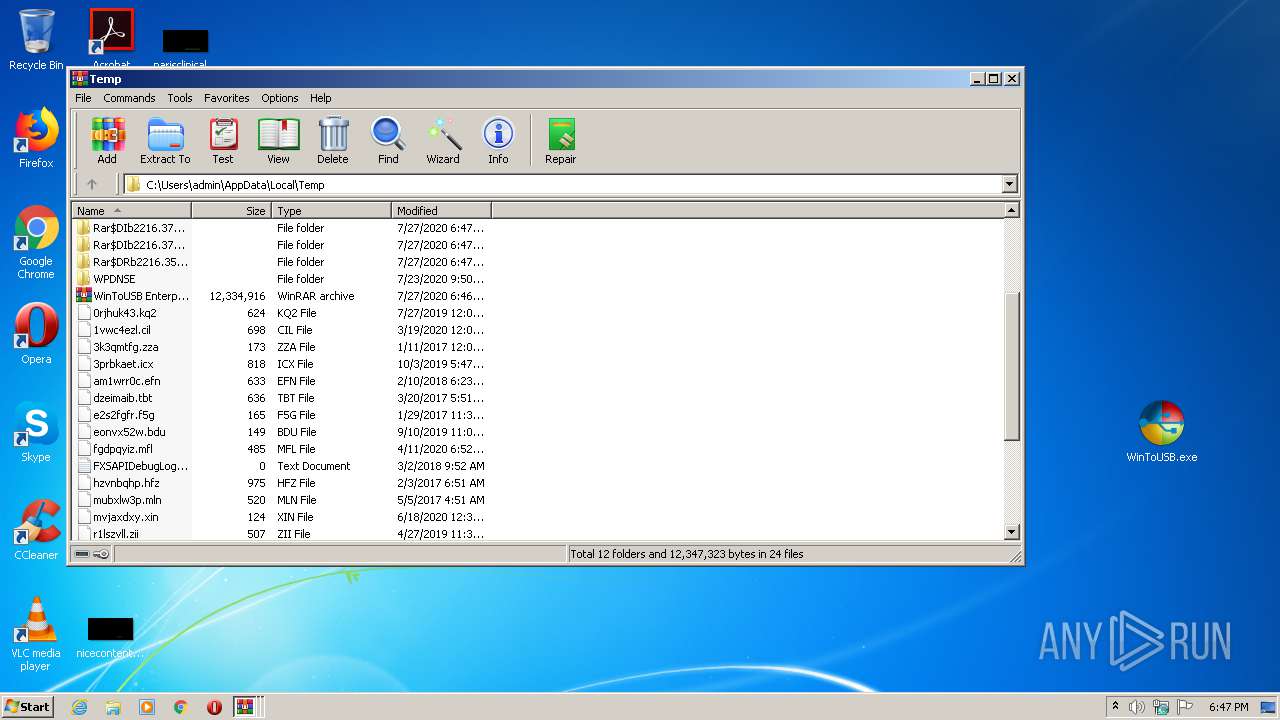
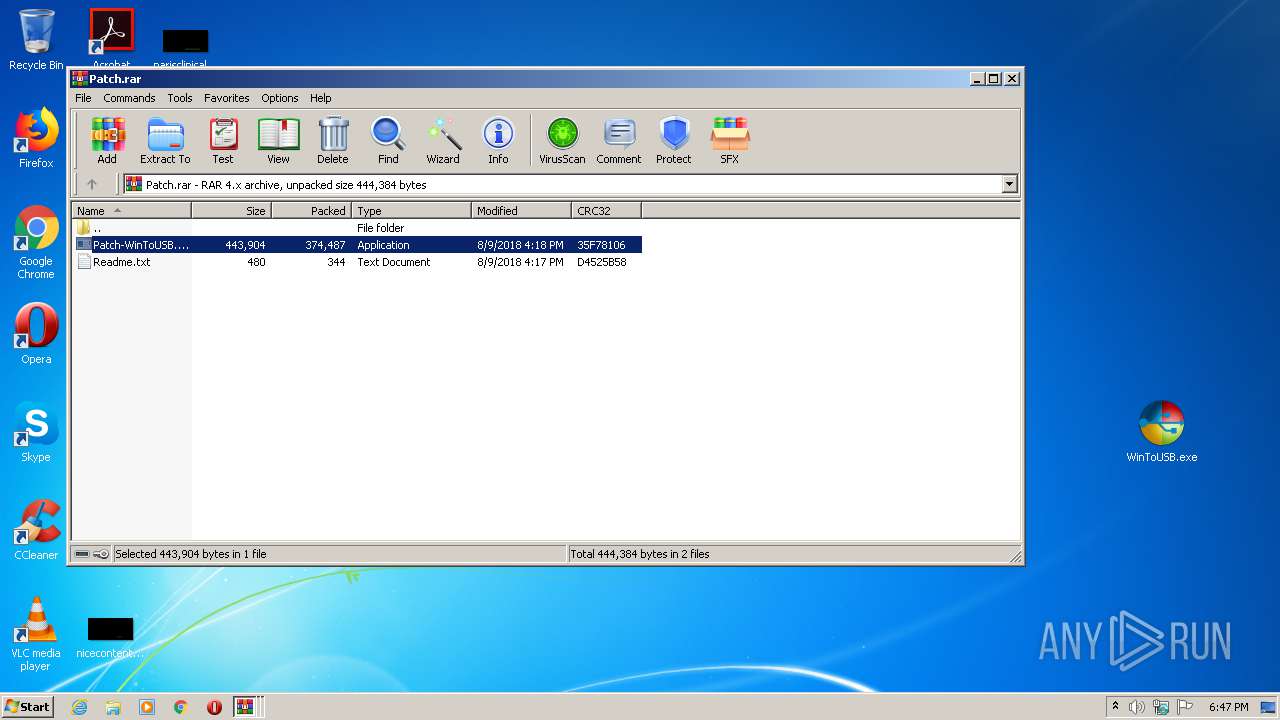
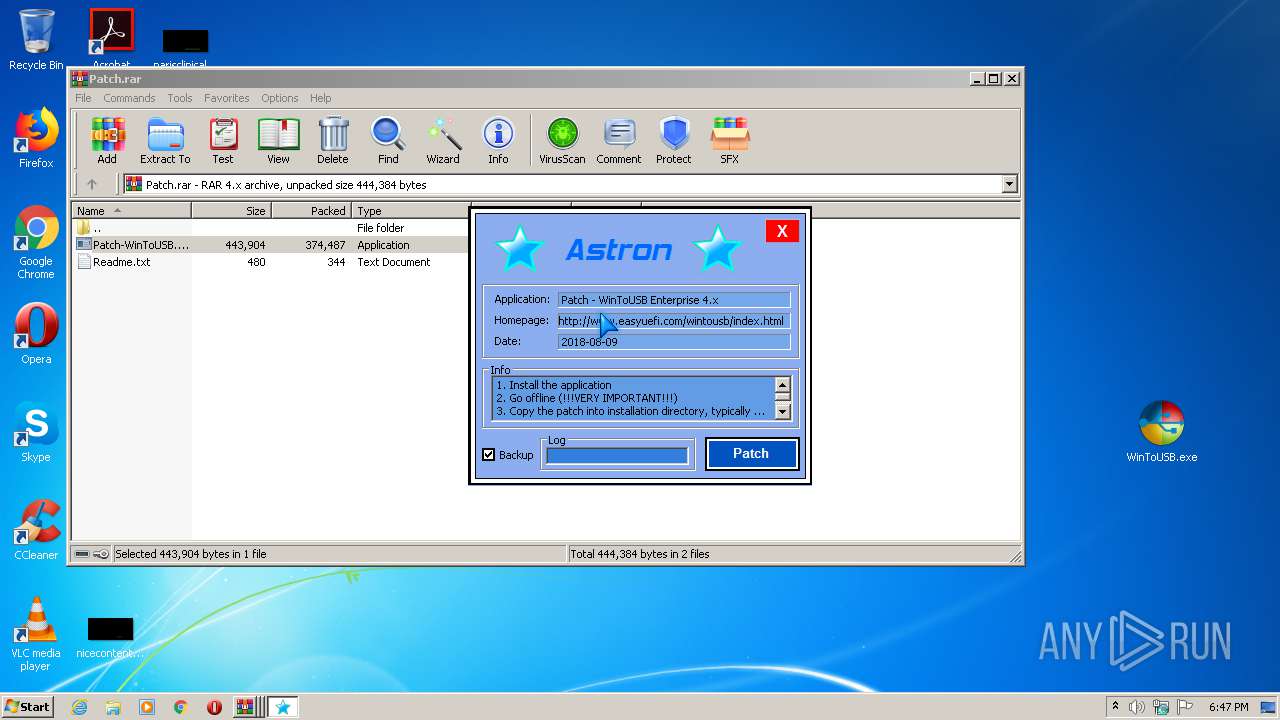
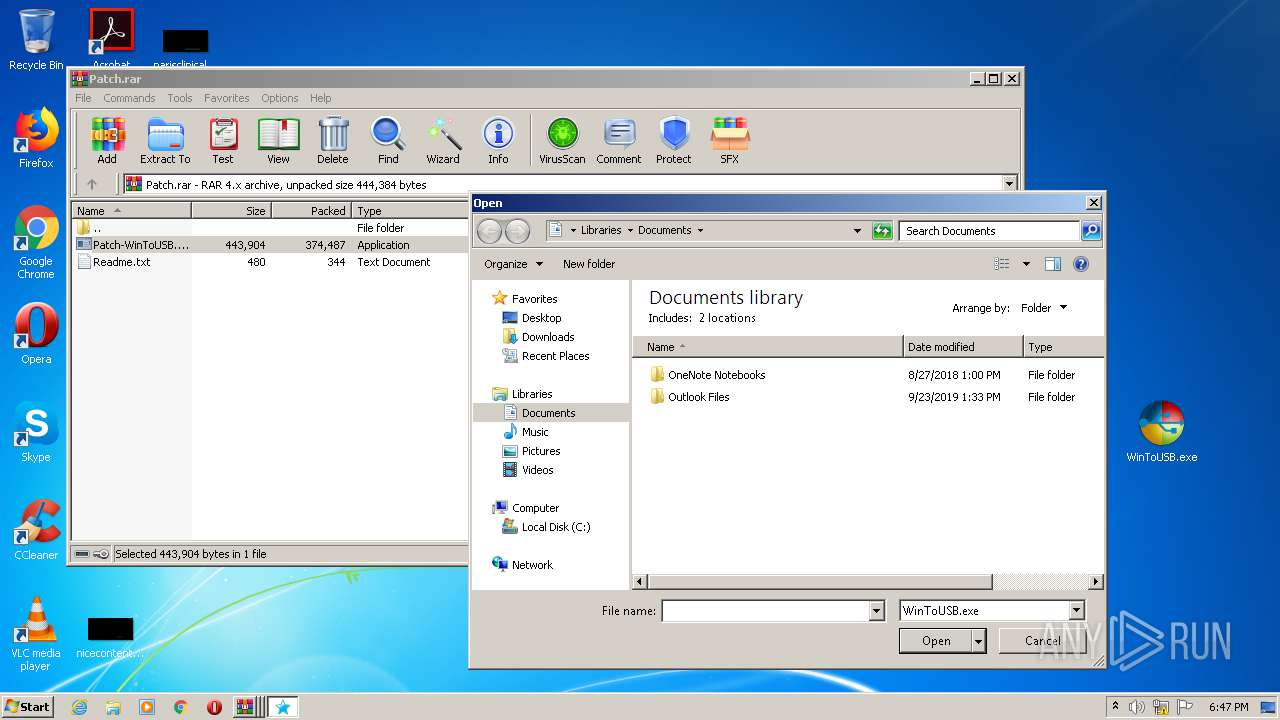
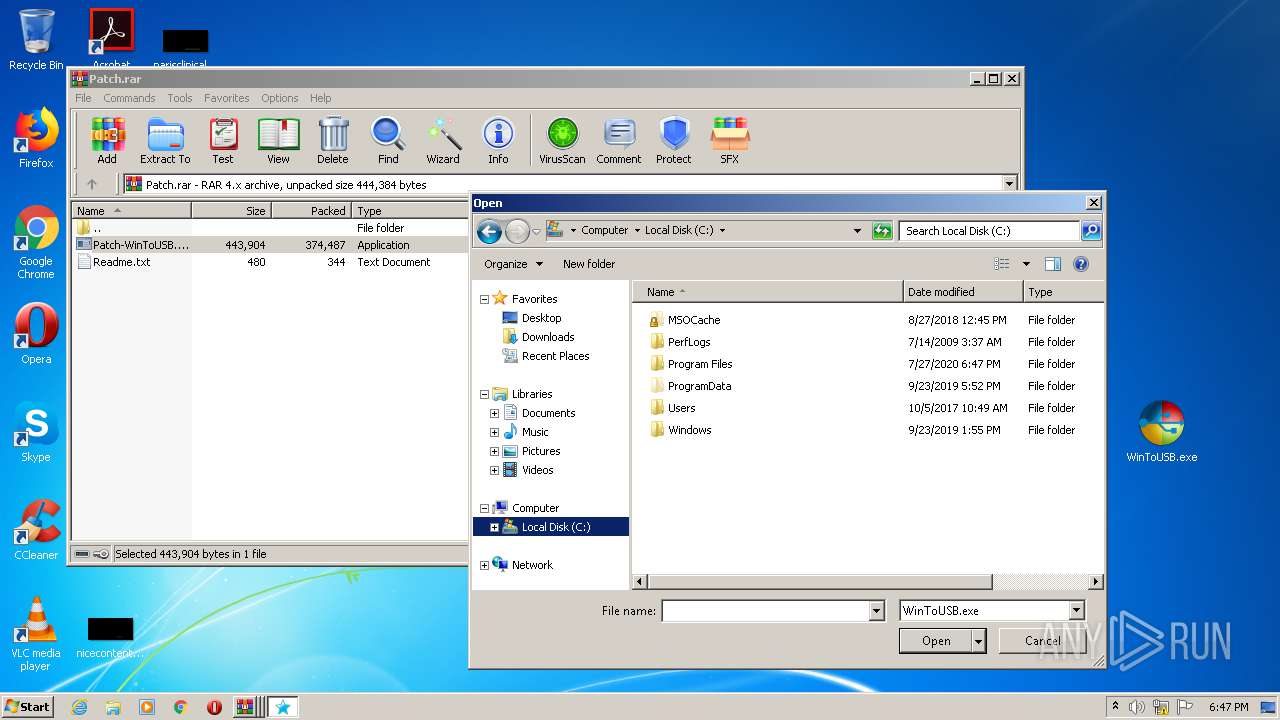
| 1728 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2960.39557\Patch-WinToUSB.Enterprise.4.x.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2960.39557\Patch-WinToUSB.Enterprise.4.x.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2960.39557\Patch-WinToUSB.Enterprise.4.x.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2960.39557\Patch-WinToUSB.Enterprise.4.x.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
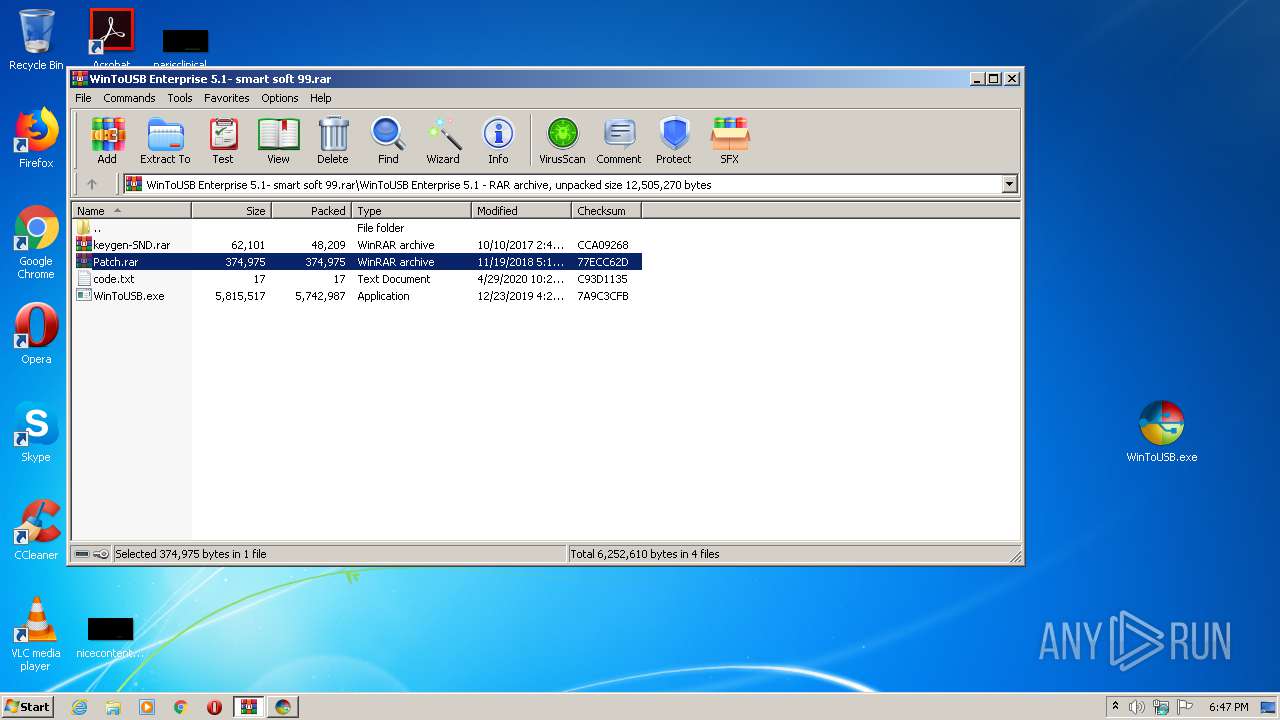
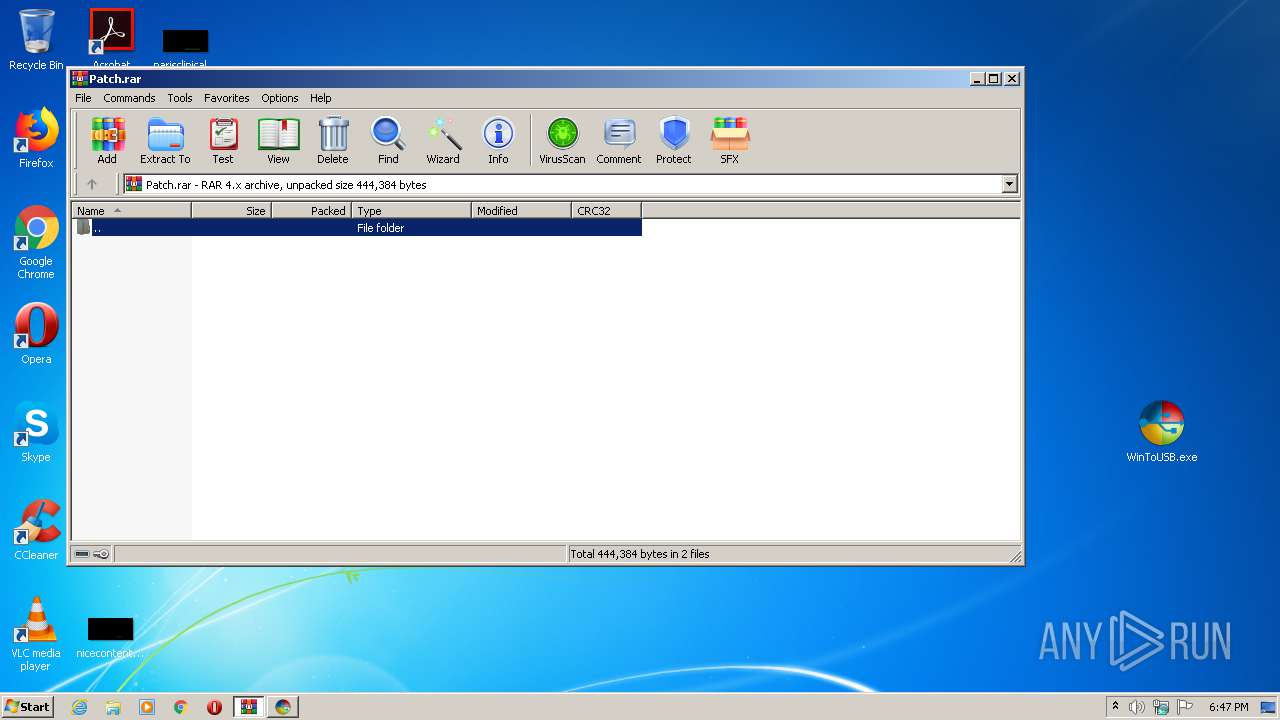
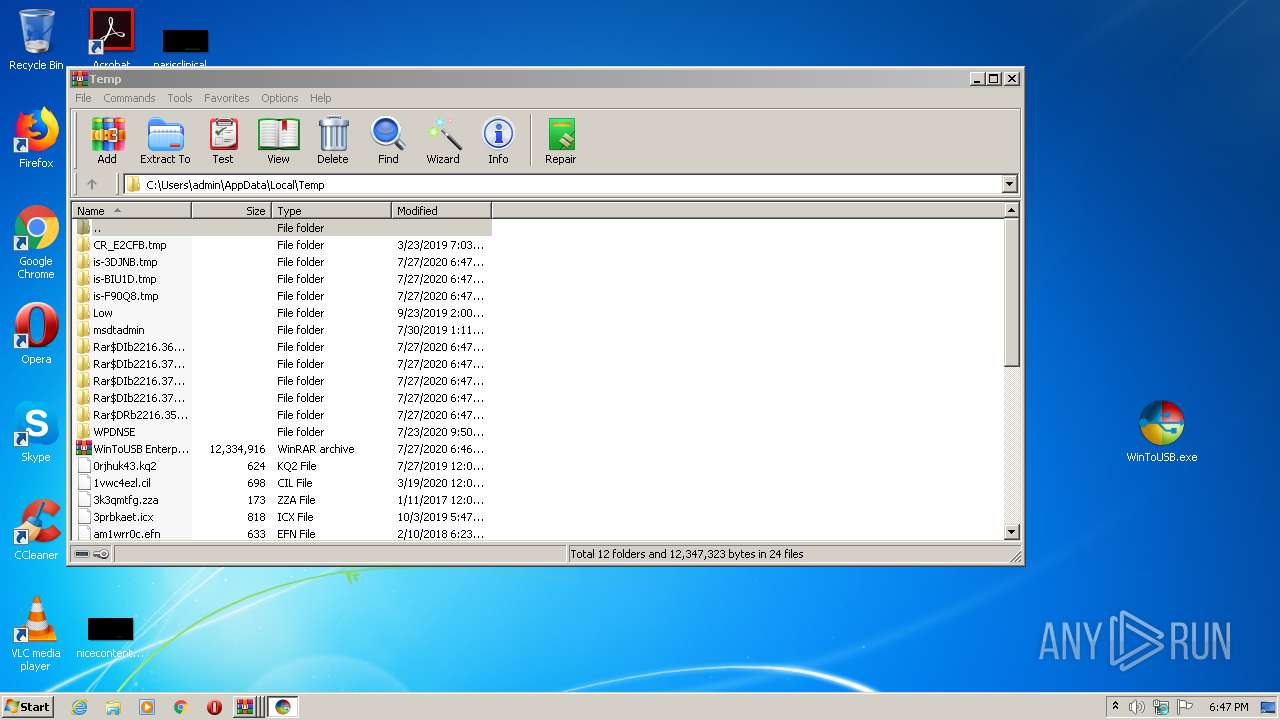
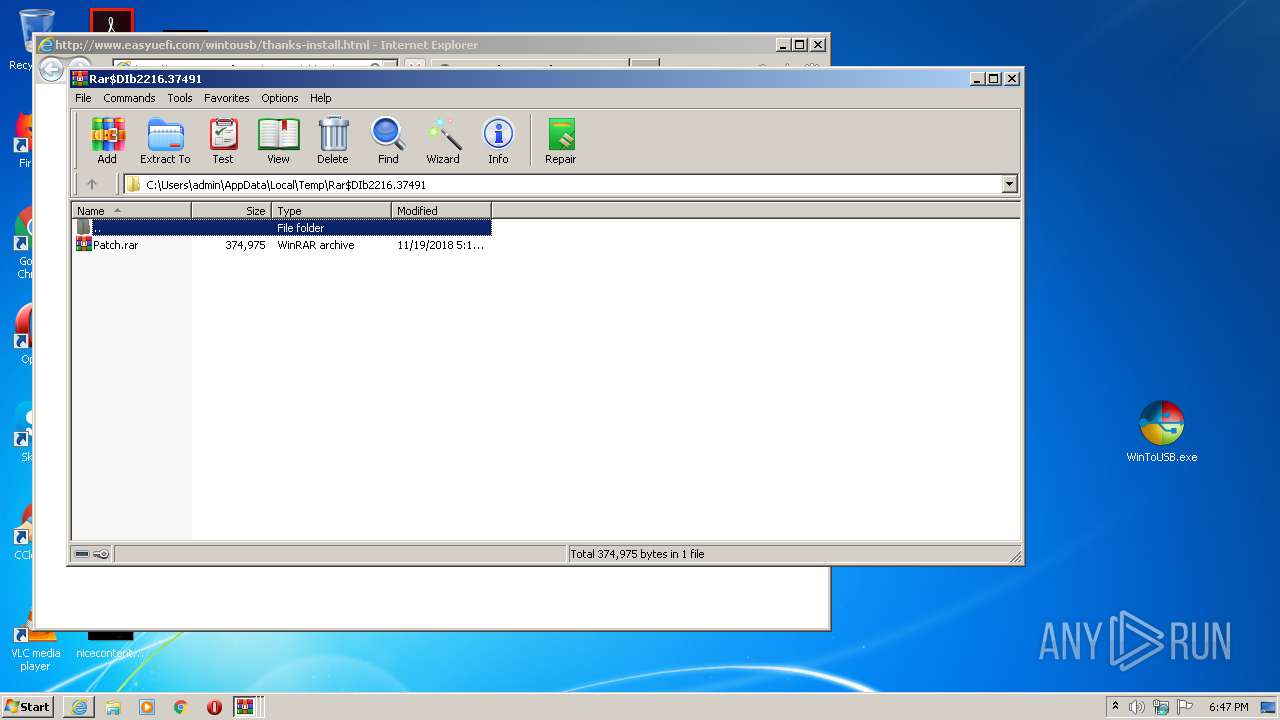
| 2160 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb2216.37459\Patch.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
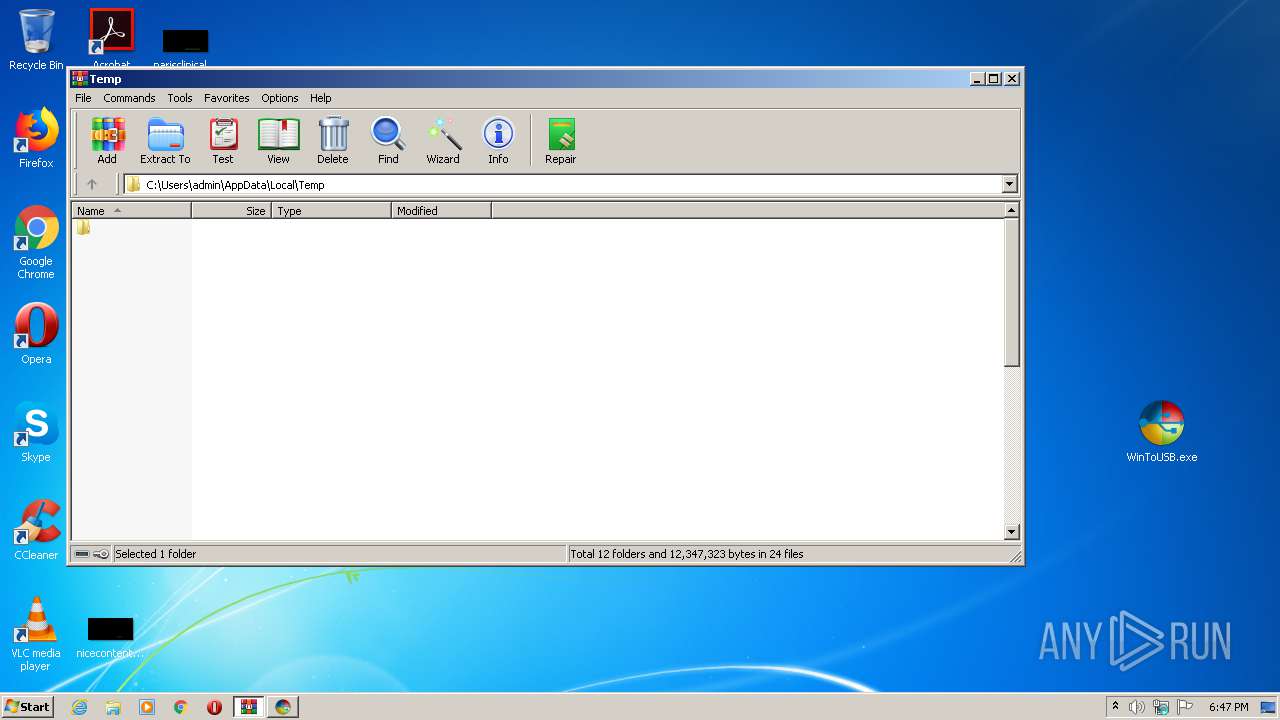
| 2216 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\WinToUSB Enterprise 5.1- smart soft 99.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb2216.37491\Patch.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\Desktop\WinToUSB.exe" | C:\Users\admin\Desktop\WinToUSB.exe | explorer.exe | ||||||||||||
User: admin Company: Hasleo Software. Integrity Level: MEDIUM Description: WinToUSB Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1604 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 426
Read events
3 189
Write events
227
Delete events
10
Modification events
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WinToUSB Enterprise 5.1- smart soft 99.rar | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (952) WinToUSB.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B8030000D0A4C6F43D64D601 | |||
Executable files
35
Suspicious files
8
Text files
16
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\is-JCJ7T.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-F5LKL.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-AJ3HP.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-PBQLH.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-7DE3K.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-HMMIB.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-CRD56.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\bin\is-4K3HM.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\res\ar\LC_MESSAGES\is-3BMNE.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | WinToUSB.tmp | C:\Program Files\Hasleo\WinToUSB\res\bg_BG\LC_MESSAGES\is-2TEOE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2532 | iexplore.exe | GET | 301 | 162.144.177.166:80 | http://www.easyuefi.com/wintousb/thanks-install.html | US | html | 261 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 195.138.255.24:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
1604 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | iexplore.exe | 195.138.255.16:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
2532 | iexplore.exe | 162.144.177.166:443 | www.easyuefi.com | Unified Layer | US | unknown |
2532 | iexplore.exe | 162.144.177.166:80 | www.easyuefi.com | Unified Layer | US | unknown |
2532 | iexplore.exe | 195.138.255.24:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
1604 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.easyuefi.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |