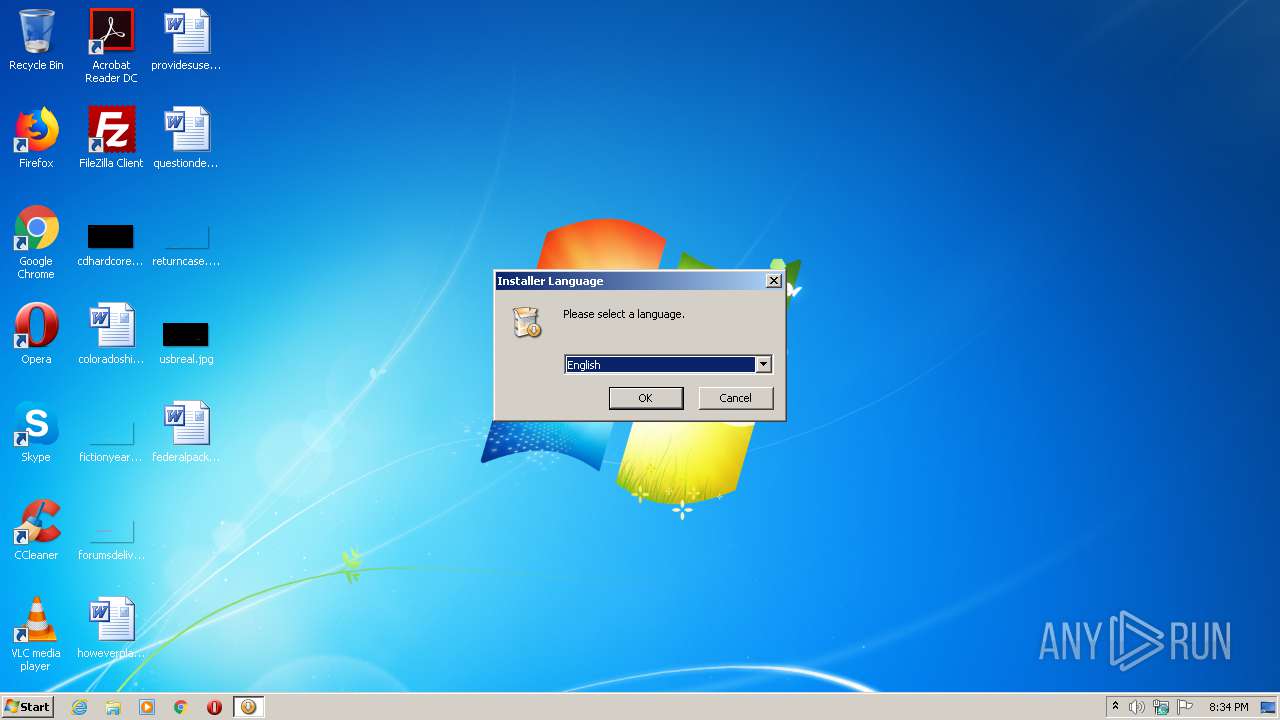
| File name: | kamino-webcam-ui_x32.exe%3f& |
| Full analysis: | https://app.any.run/tasks/dc314752-5ed7-405d-8d1a-225107750f2c |
| Verdict: | Suspicious activity |
| Analysis date: | June 06, 2020, 19:33:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2394FF9821289BEC4EFB7403D06D83AC |
| SHA1: | E17B35C75C1A2EE258A8B12B8351E65144713790 |
| SHA256: | 3EFFC0C159D3FC3B68398C24D4845658197BEFEFAA9FD50229E8F4CCDADDC8F4 |
| SSDEEP: | 6144:MzZZxgKVD6acQH08Bhuhqkc6rfA9TlM432GZRTi0zY108OC:MzZzHm0H0YhWq0oBMJ0BeVOC |
MALICIOUS
Loads dropped or rewritten executable
- d5846e96-4788-485b-a371-0d4d2e4e084b.exe (PID: 2316)
SUSPICIOUS
Executable content was dropped or overwritten
- d5846e96-4788-485b-a371-0d4d2e4e084b.exe (PID: 2316)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:09:09 15:23:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3415 |
| OSVersion: | 5 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.15.0 |
| ProductVersionNumber: | 1.0.15.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Logitech |
| CompanyWebsite: | http://www.logitech.com |
| FileDescription: | - |
| FileVersion: | 1 |
| LegalCopyright: | - |
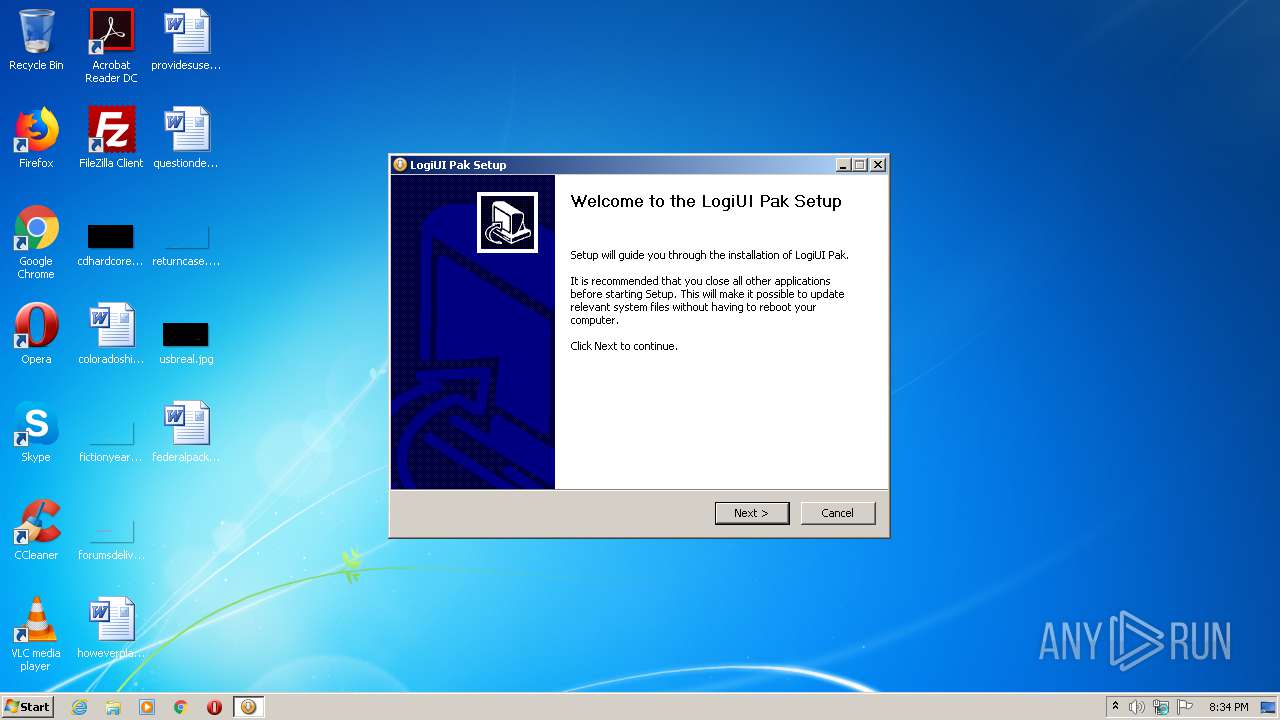
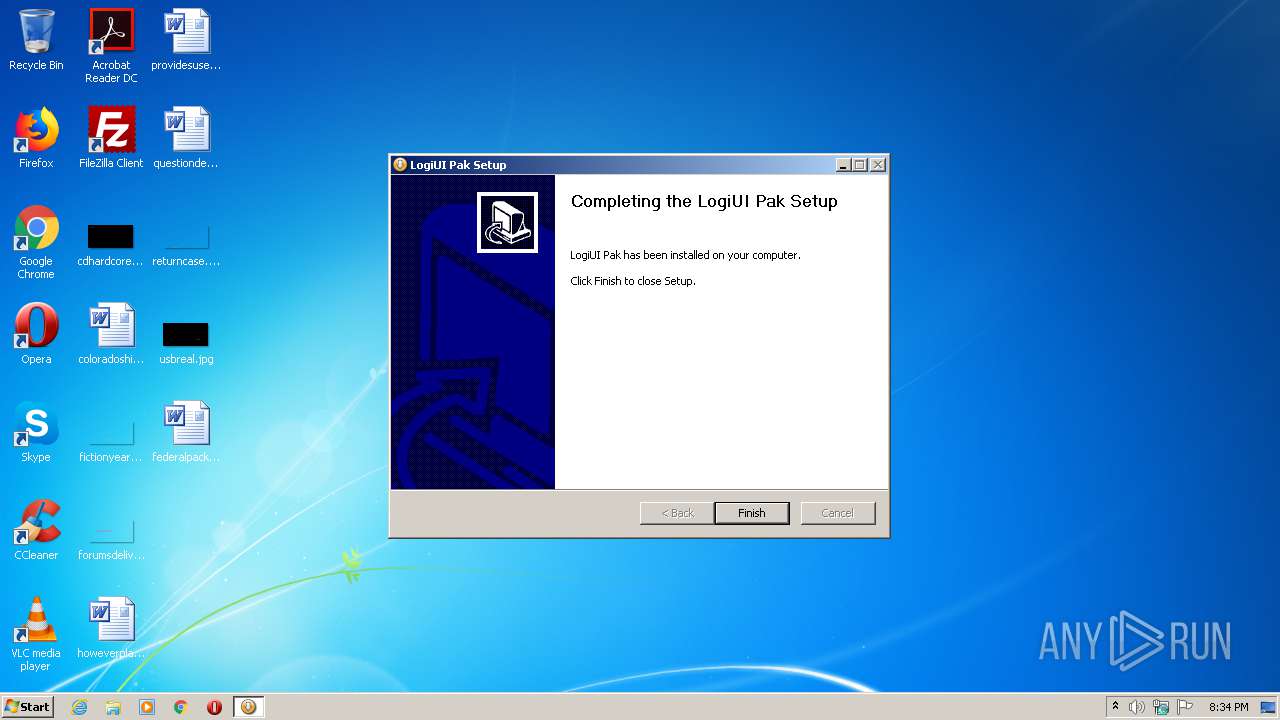
| ProductName: | LogiUI Pak |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2009 13:23:33 |
| Detected languages: |
|
| CompanyName: | Logitech |
| CompanyWebsite: | http://www.logitech.com |
| FileDescription: | - |
| FileVersion: | 1.00 |
| LegalCopyright: | - |
| ProductName: | LogiUI Pak |
| ProductVersion: | 1.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Sep-2009 13:23:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000671C | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50461 |
.rdata | 0x00008000 | 0x000019D6 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02684 |
.data | 0x0000A000 | 0x0007139C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.73601 |
.ndata | 0x0007C000 | 0x00149000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001C5000 | 0x00008768 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.42479 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22409 | 955 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.91942 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.58096 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.73226 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2316 | "C:\Users\admin\AppData\Local\Temp\d5846e96-4788-485b-a371-0d4d2e4e084b.exe" | C:\Users\admin\AppData\Local\Temp\d5846e96-4788-485b-a371-0d4d2e4e084b.exe | explorer.exe | ||||||||||||
User: admin Company: Logitech Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
347
Read events
341
Write events
6
Delete events
0
Modification events
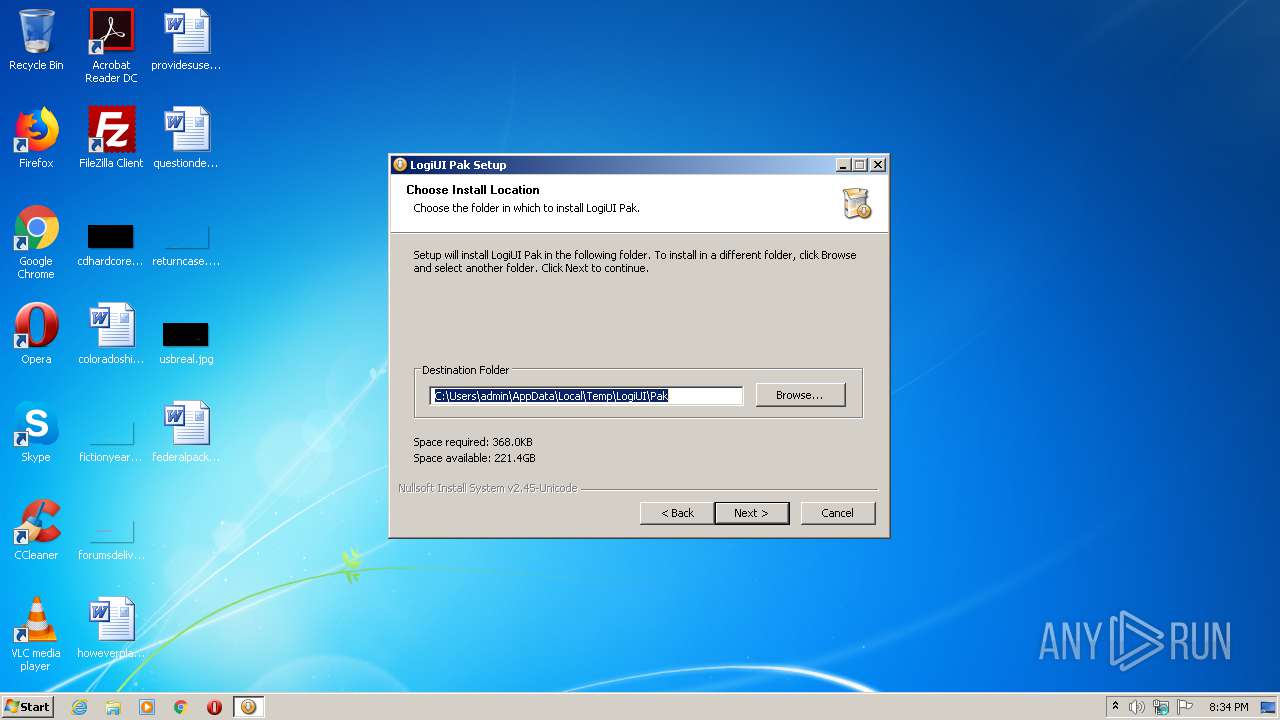
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiShrd\DownloadAssistant |
| Operation: | write | Name: | UIPath |
Value: C:\Users\admin\AppData\Local\Temp\LogiUI\Pak | |||
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiShrd\DownloadAssistant |
| Operation: | write | Name: | UIRemove |
Value: C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\uninstall.exe | |||
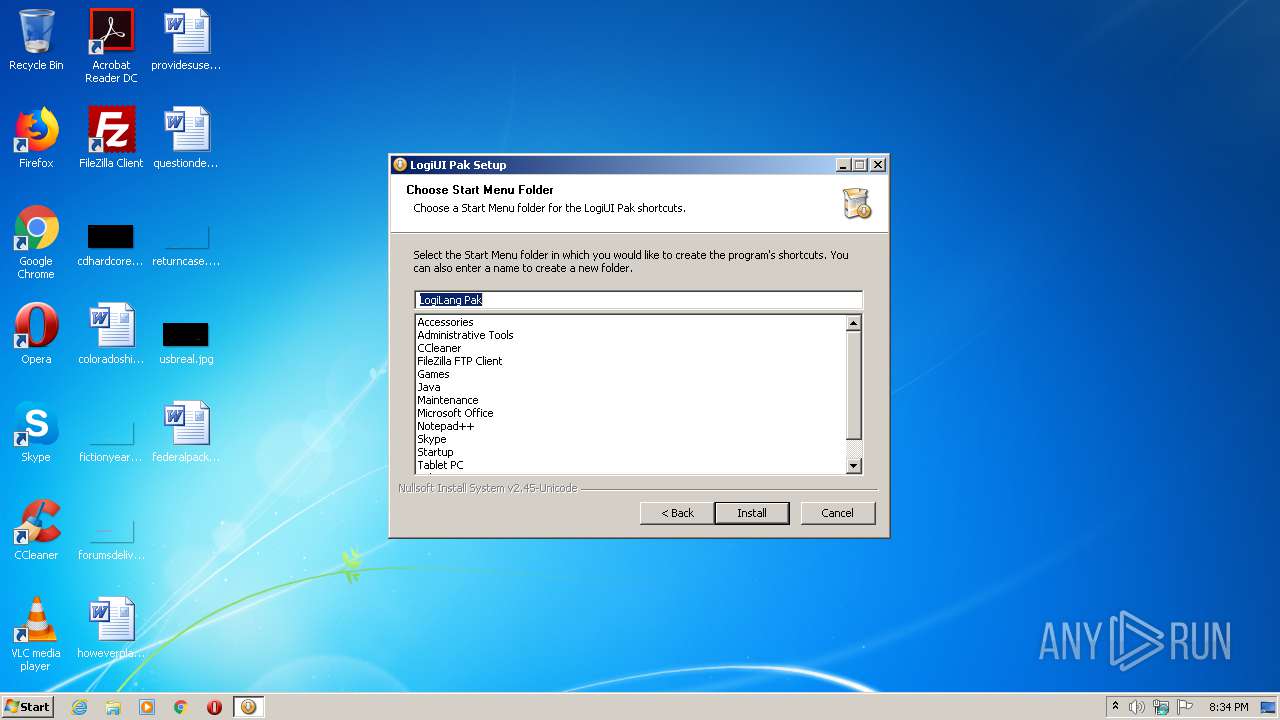
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiUI Pak\Components |
| Operation: | write | Name: | UI |
Value: 1 | |||
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiUI Pak |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\AppData\Local\Temp\LogiUI\Pak | |||
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiUI Pak |
| Operation: | write | Name: | StartMenuGroup |
Value: LogiLang Pak | |||
| (PID) Process: | (2316) d5846e96-4788-485b-a371-0d4d2e4e084b.exe | Key: | HKEY_CURRENT_USER\Software\LogiUI Pak |
| Operation: | write | Name: | InstallerLanguage |
Value: 1033 | |||
Executable files
5
Suspicious files
0
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\css\basic-quickflips.css | text | |
MD5:B45F172DE46B34D12E19D6F9409F9B08 | SHA256:D2D539E6B2D3895FC9E9B3E36E0A71BFF20686EB6205CC4D6B78A92804A62DE5 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\nse6951.tmp\nsDialogs.dll | executable | |
MD5:7823FC560926DCD8741DE6F0B900083F | SHA256:CA869D6C6752AA4A8A6C874A694B543442992D7E854D0C48A1B60BCA01A8C8C6 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\Ini\directives.ini | text | |
MD5:F0A34CC525425A3FE90DD86B796C3A61 | SHA256:B40D83BE9204E57ED0FE40F84F38293D34B4EF6F06874C2F486EAAADCDF1CDB3 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\nse6951.tmp\StartMenu.dll | executable | |
MD5:5CE52C5C52C7ECE604CB5B07FAF234DF | SHA256:96AC4EF189260D5D6137C27C9470AFBBDE382F771FEF040E9A6FA3F0CA2E4ECC | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\html\finish.html | html | |
MD5:C18E66764A77FEF7FB739916BC5FD80C | SHA256:8DCF58EE7EB4BC151D53CC2A4A30781210D439C9517A92272653810D40BE701B | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\nse6951.tmp\LangDLL.dll | executable | |
MD5:8E806EA2E205DC508A2FB5ADDA3419DB | SHA256:86A55734B8802051BBBD0E8C9C506D0CA985BC5C99113E99B309469046133937 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\css\smart.css | text | |
MD5:DE67BB253C9DE352A4A336393DC66CB8 | SHA256:D6194AF64C93454FC4493F387E7C501D18F7C7CD71FE22577FA82F5C4AAA1326 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\nse6951.tmp\System.dll | executable | |
MD5:B9F430F71C7144D8FF4AB94BE2785AA6 | SHA256:B496E81A74CE871236ABCD096FB9A6B210B456BEBAA7464FA844B3241E51A655 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\html\download.html | html | |
MD5:B755A70BAA8DD25BEF28B6292D6F019E | SHA256:740400332C2EDAA236CB42488CAB07DF04DE19218BBB8F61BC9BDB950B6AD142 | |||
| 2316 | d5846e96-4788-485b-a371-0d4d2e4e084b.exe | C:\Users\admin\AppData\Local\Temp\LogiUI\Pak\html\welcome.html | html | |
MD5:142FC29158DC02C302C95ACE9C39F110 | SHA256:CE3B5B2A5CD5E2092D84FB494A8D02EC9F35F01F23632AABF67689526FB89950 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report